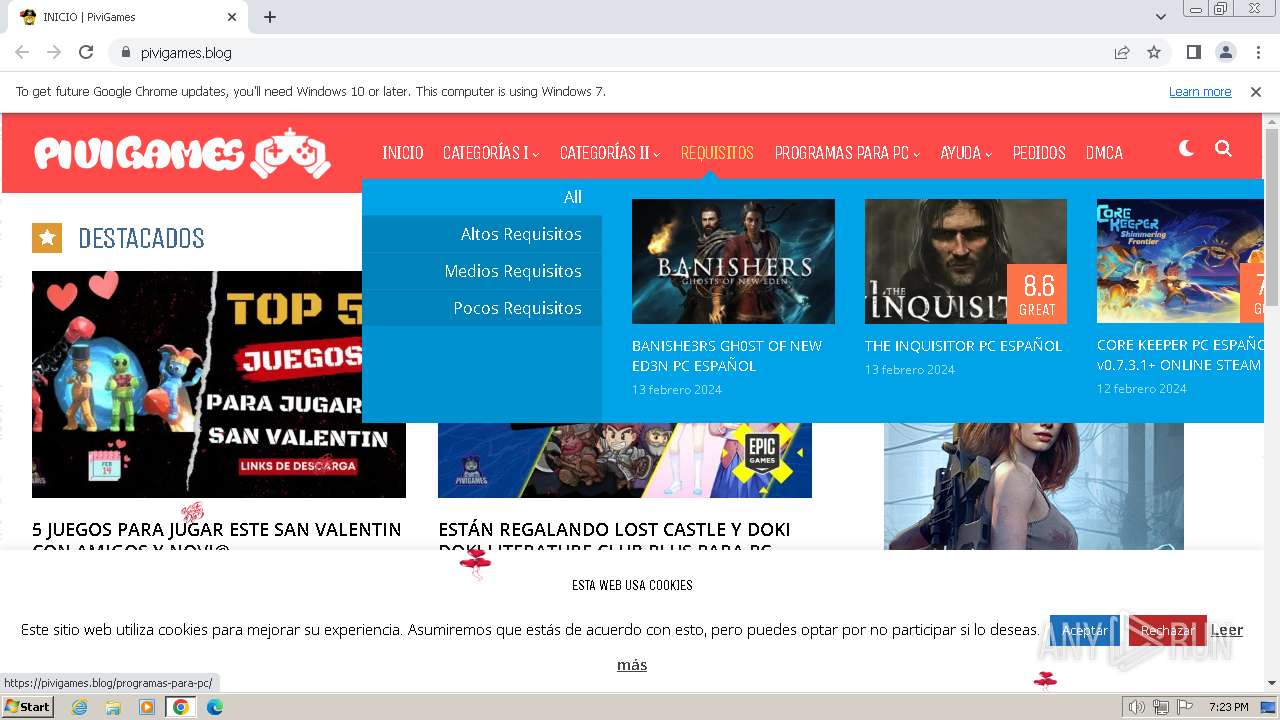
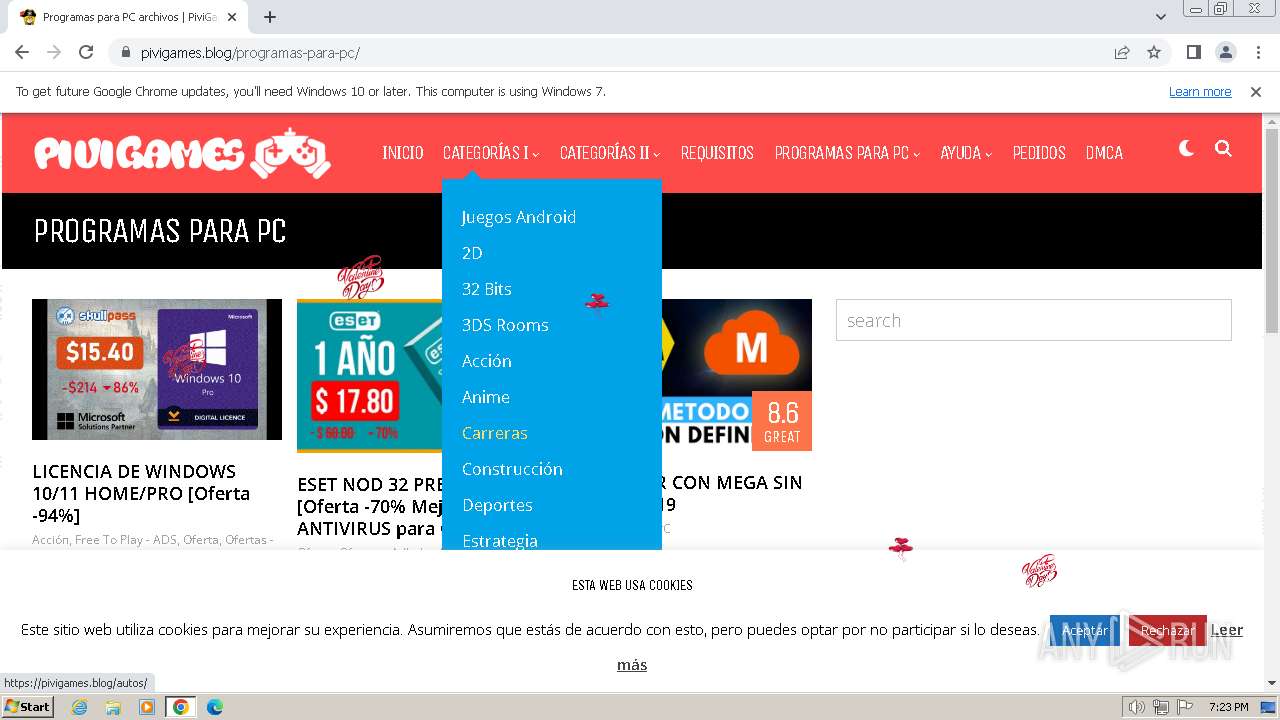
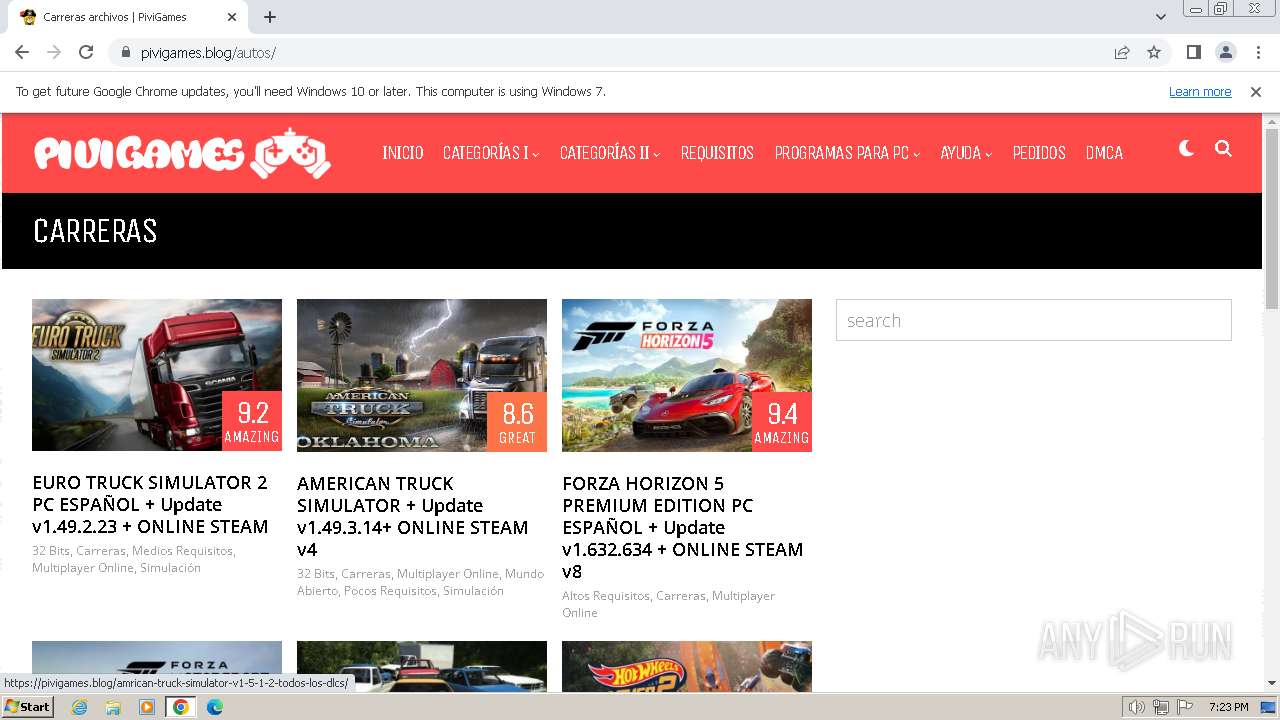
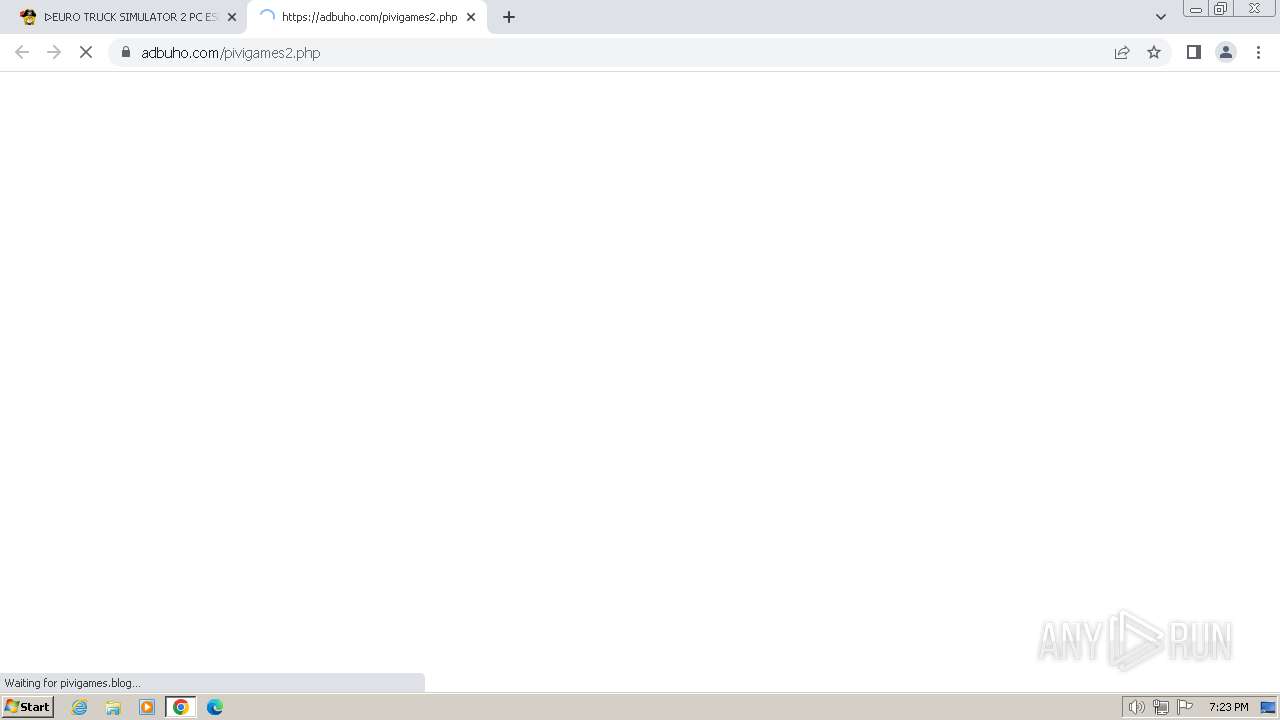
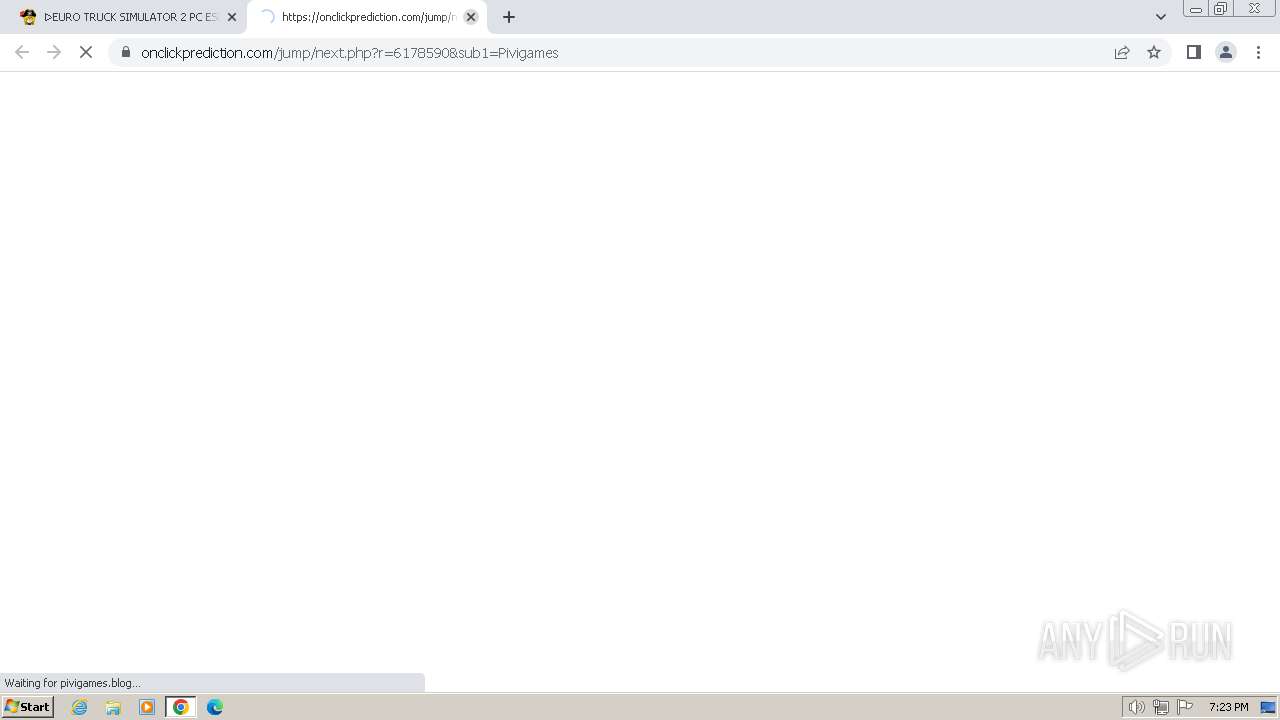
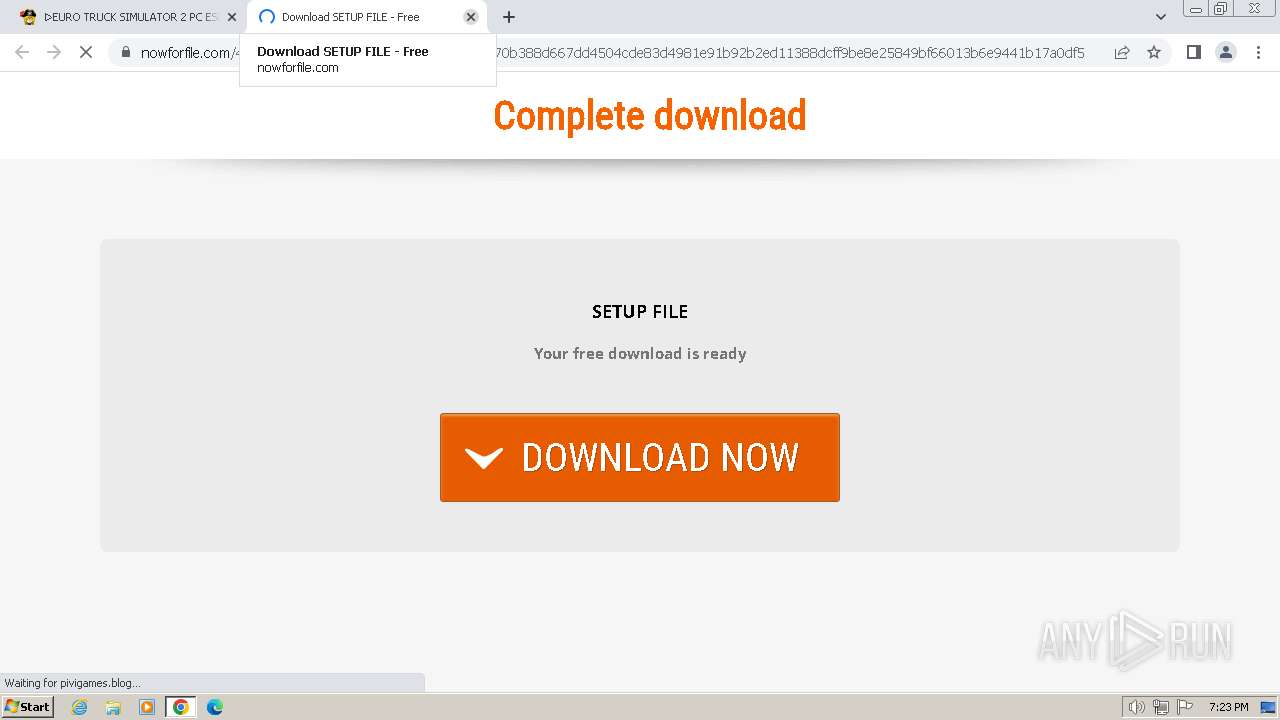
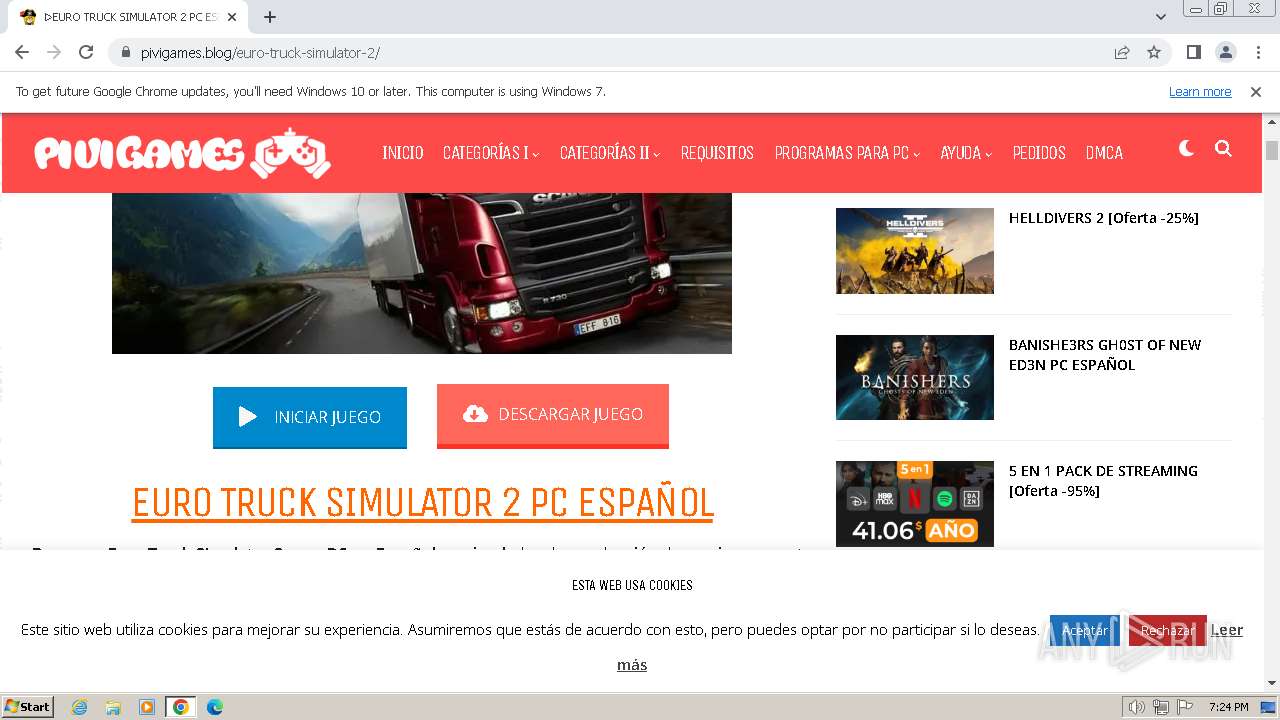
| URL: | https://pivigames.blog/ |
| Full analysis: | https://app.any.run/tasks/5940f8e0-ebd1-49cf-8097-d78131e89da9 |
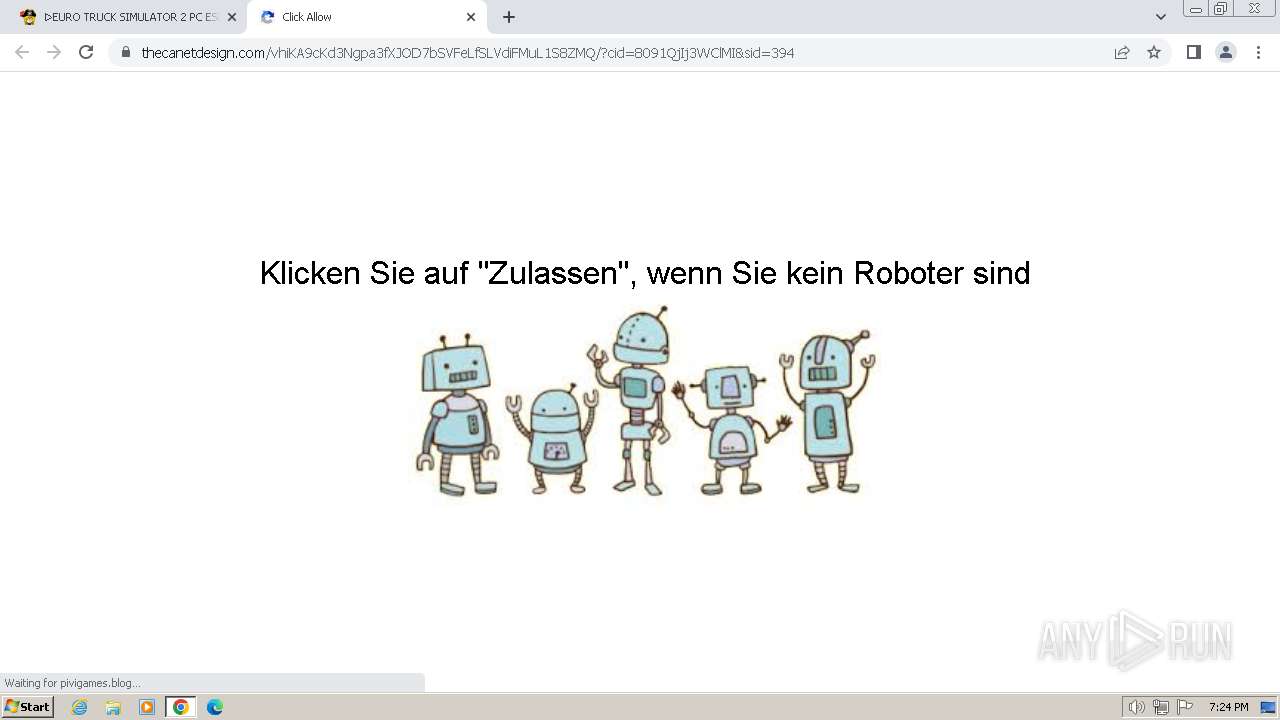
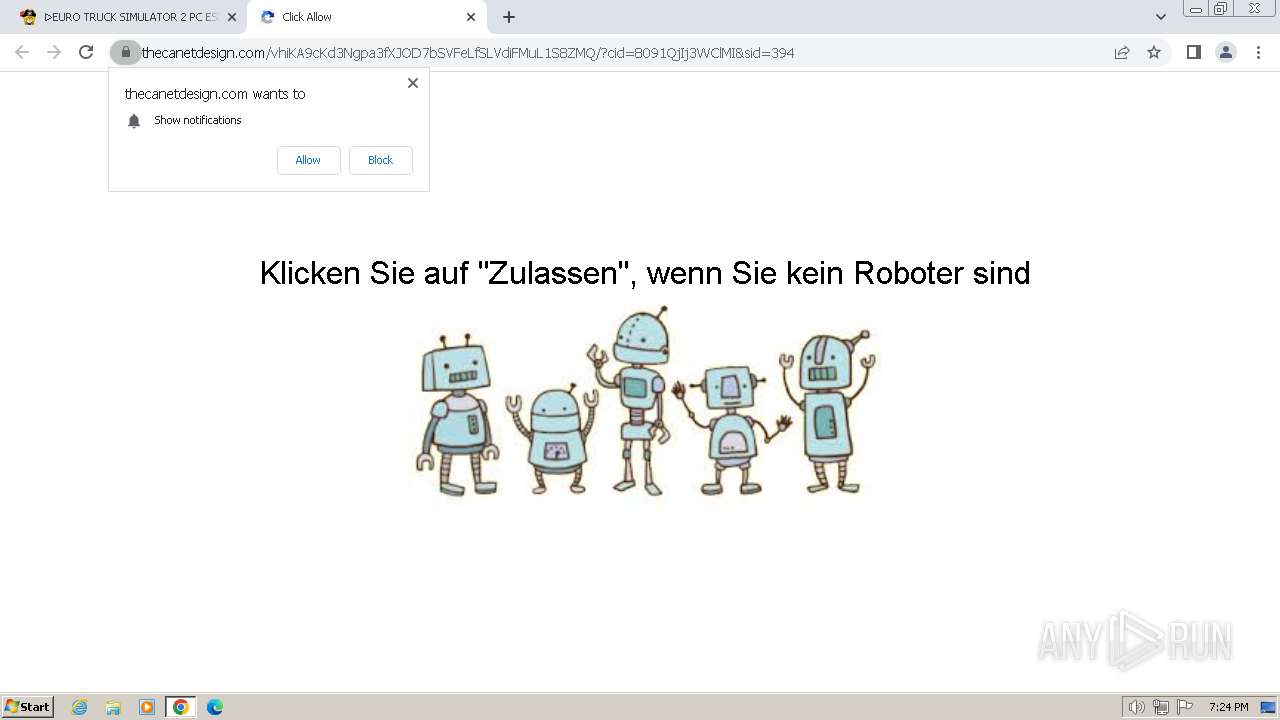
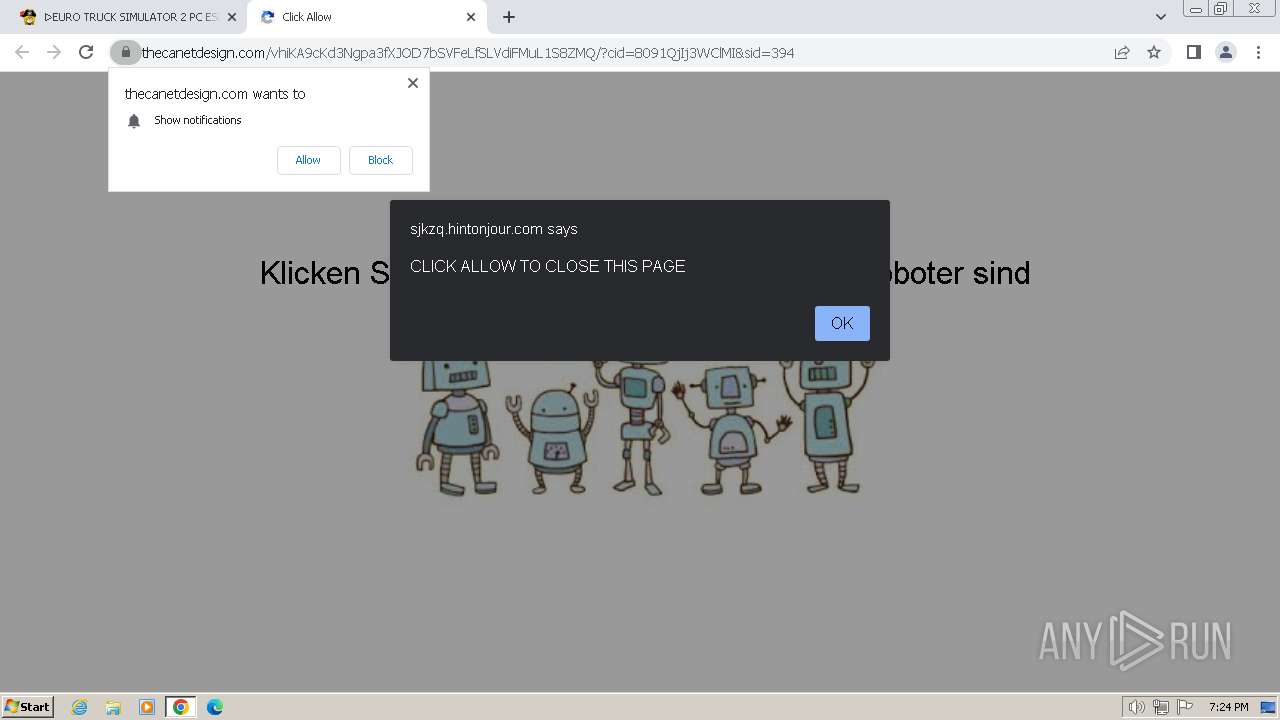
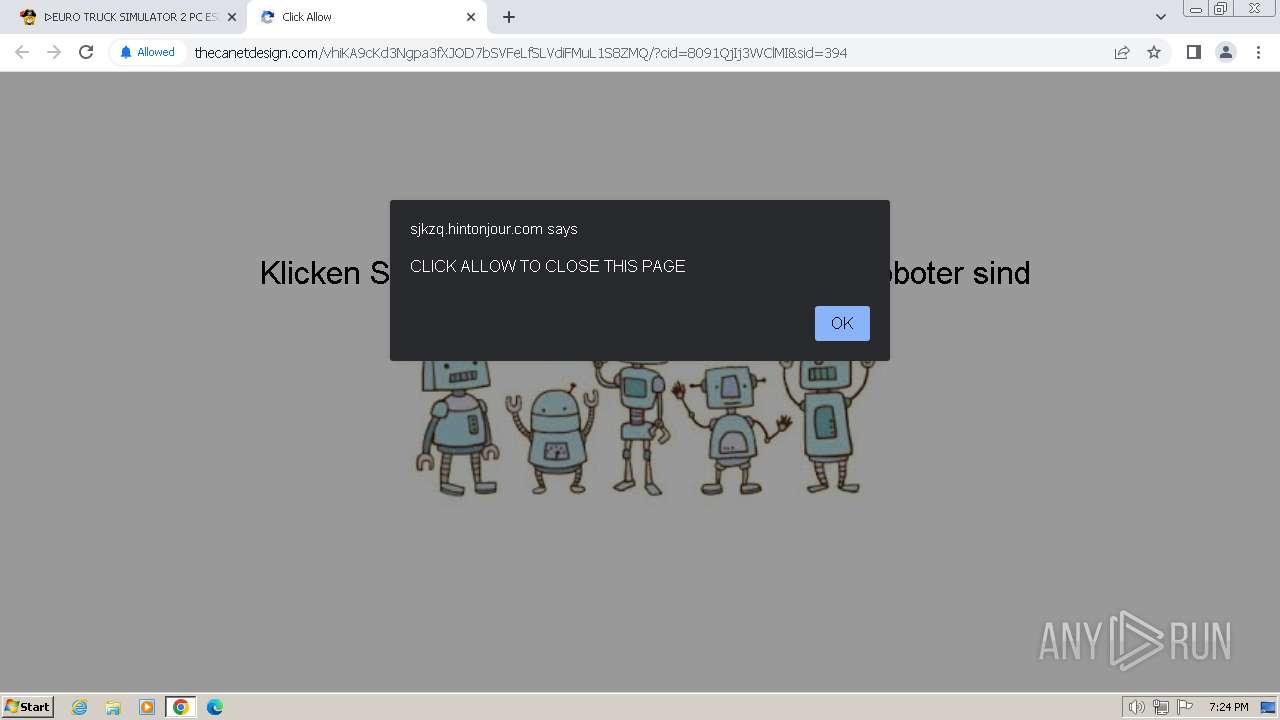
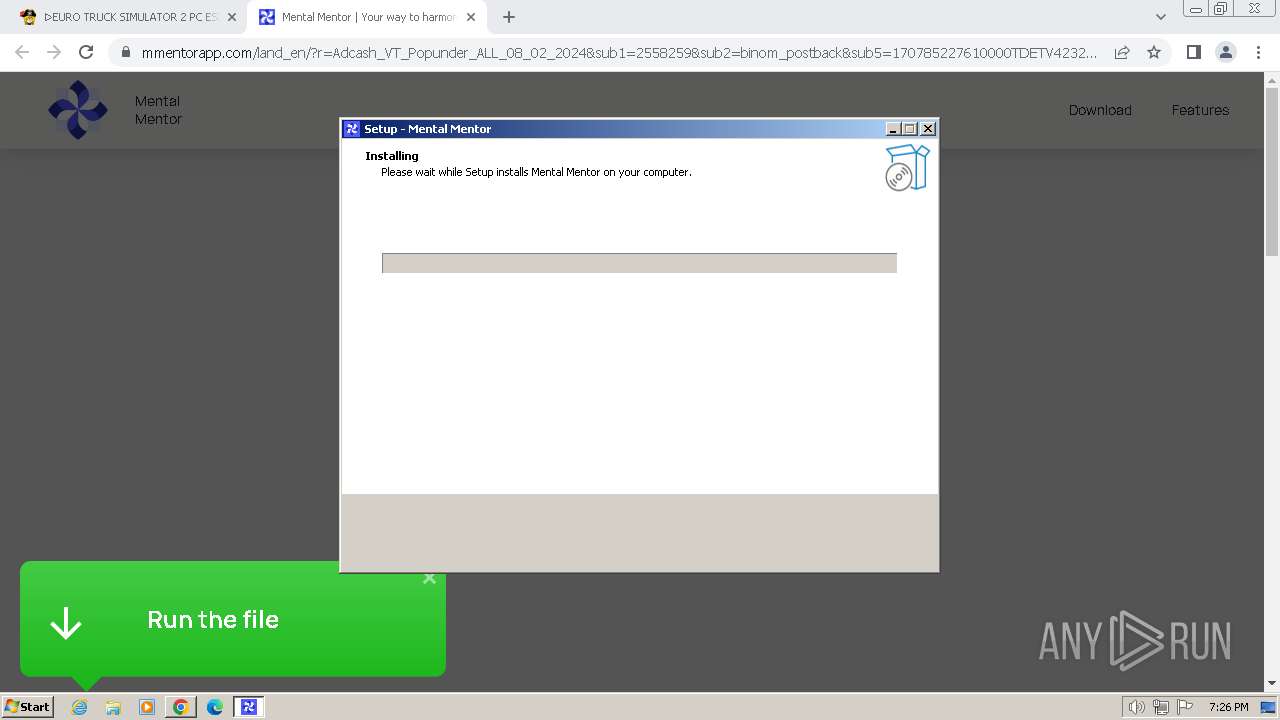
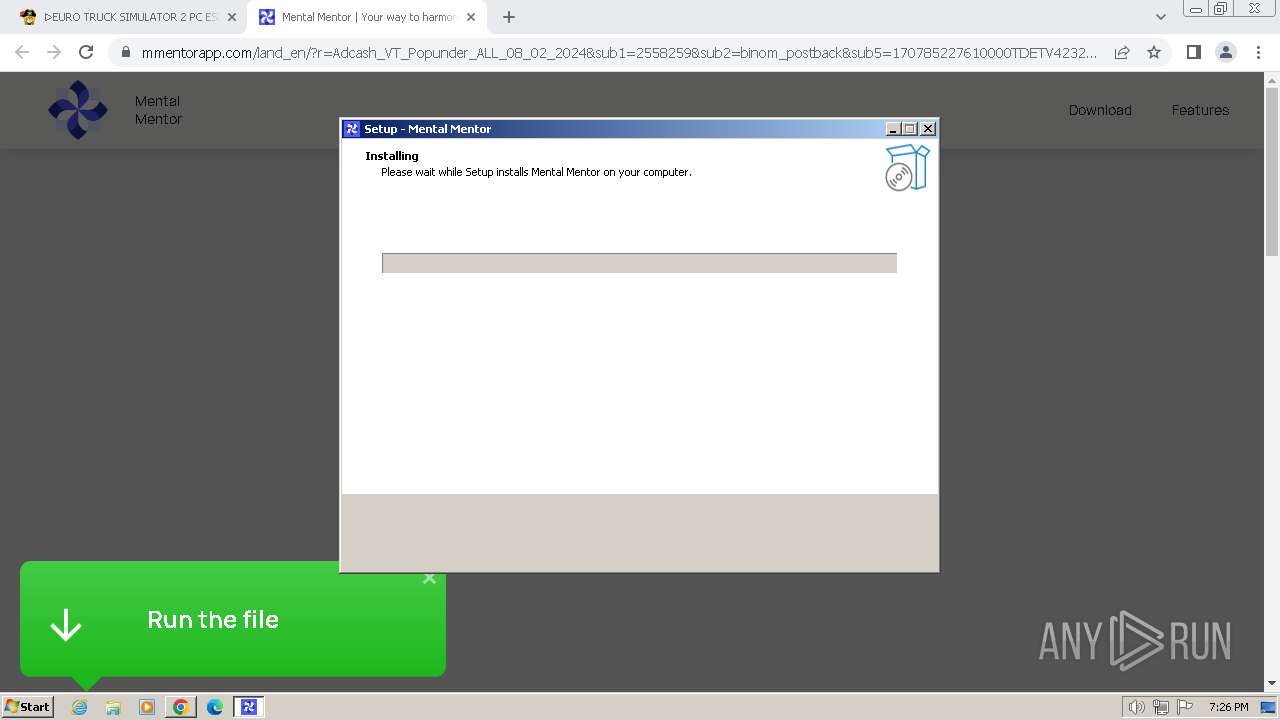
| Verdict: | Malicious activity |
| Analysis date: | February 13, 2024, 19:22:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 117AE13E8DE8F2FEFD5B0C8B69E89CE9 |
| SHA1: | 16D8B33467F68D81883869C7C6D85560F22E39DF |
| SHA256: | A69853BC16CE924455224633E6FA95F52692C137C4A54EF6AAFDB71E283751AD |
| SSDEEP: | 3:N8IAdWlZKn:2IWoK |
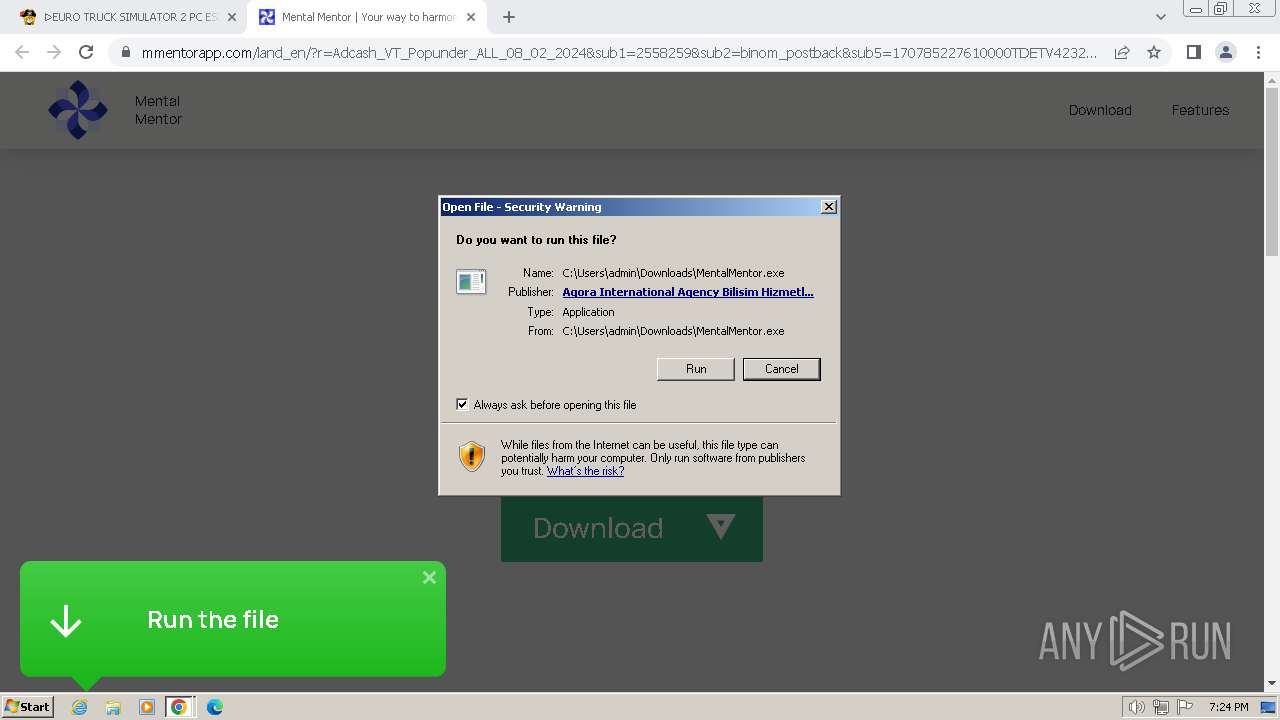
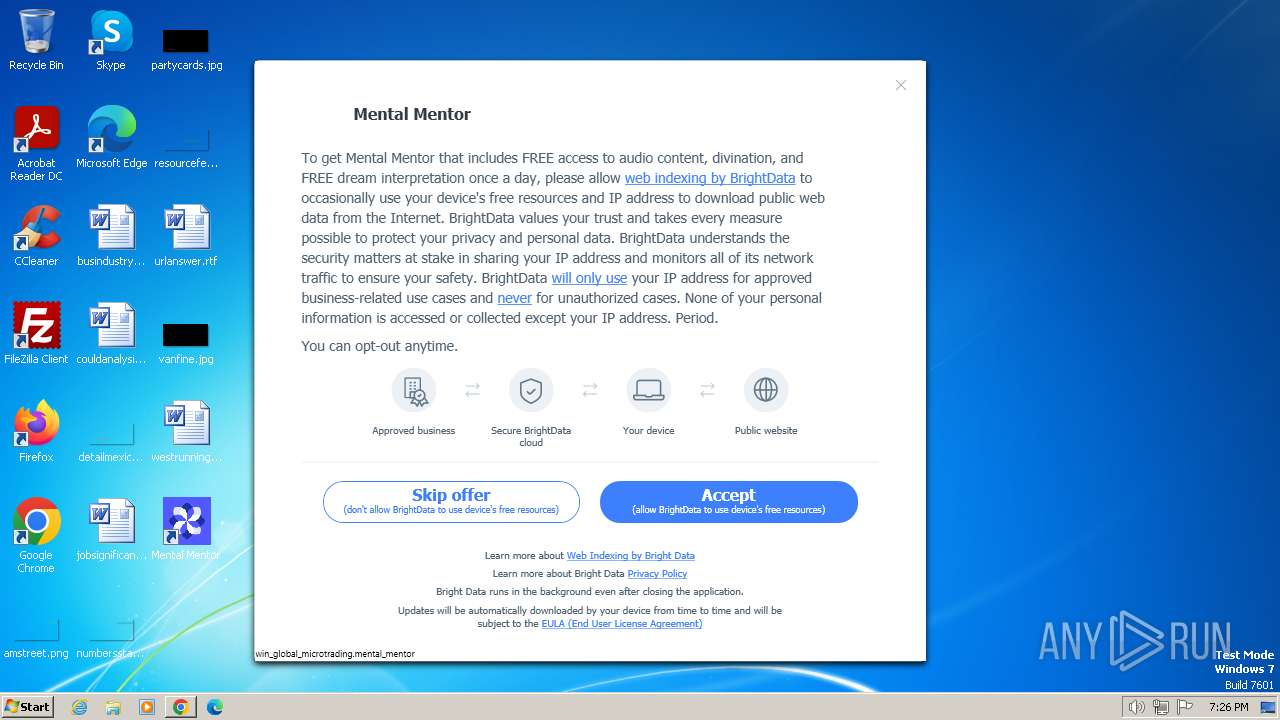
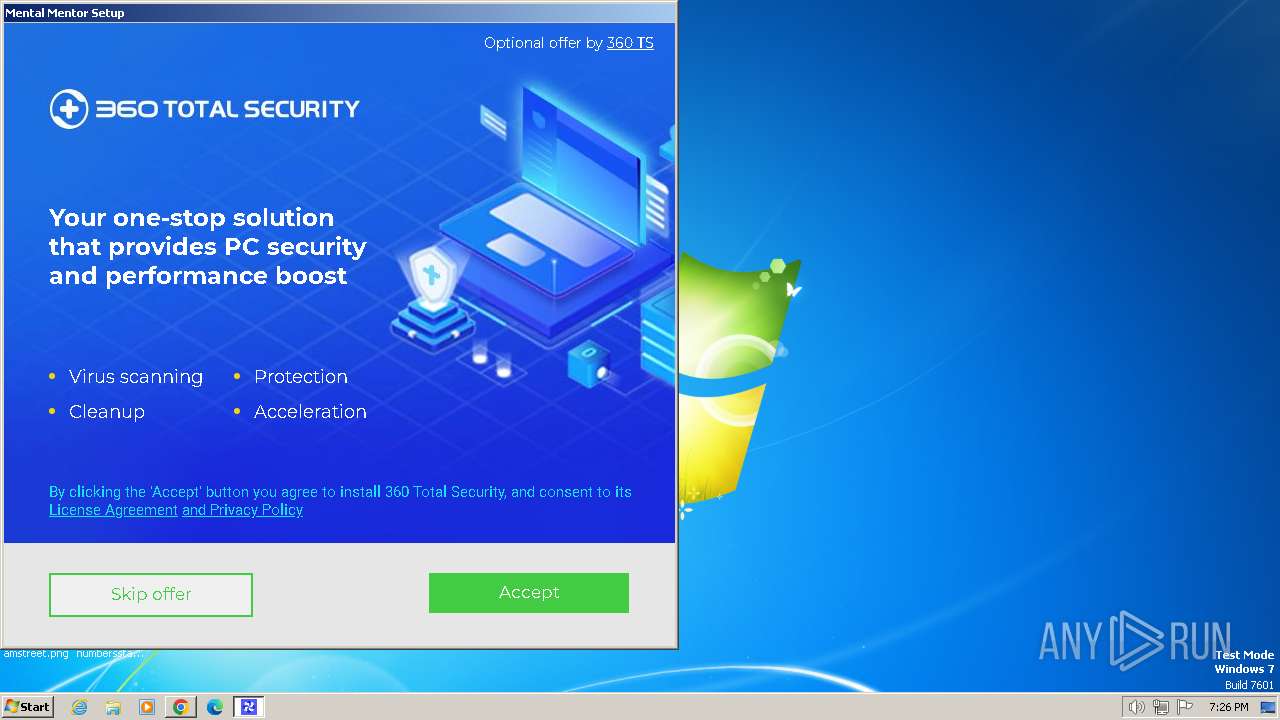
MALICIOUS
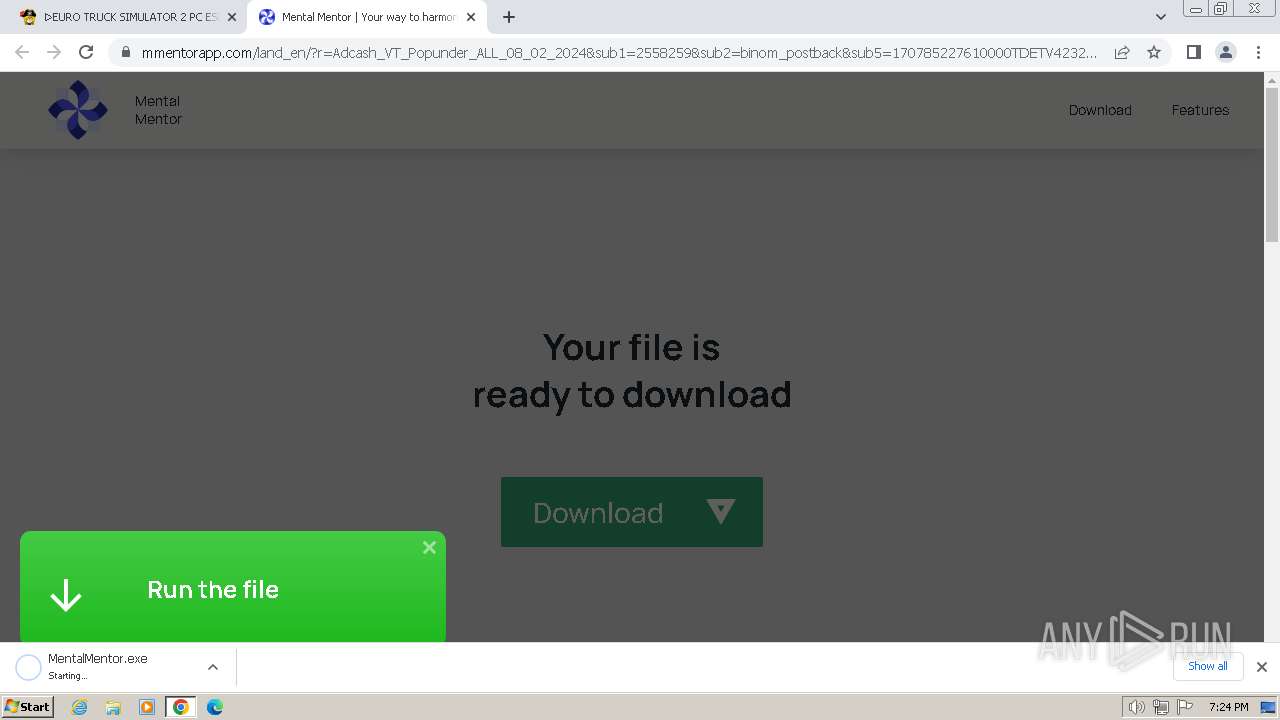
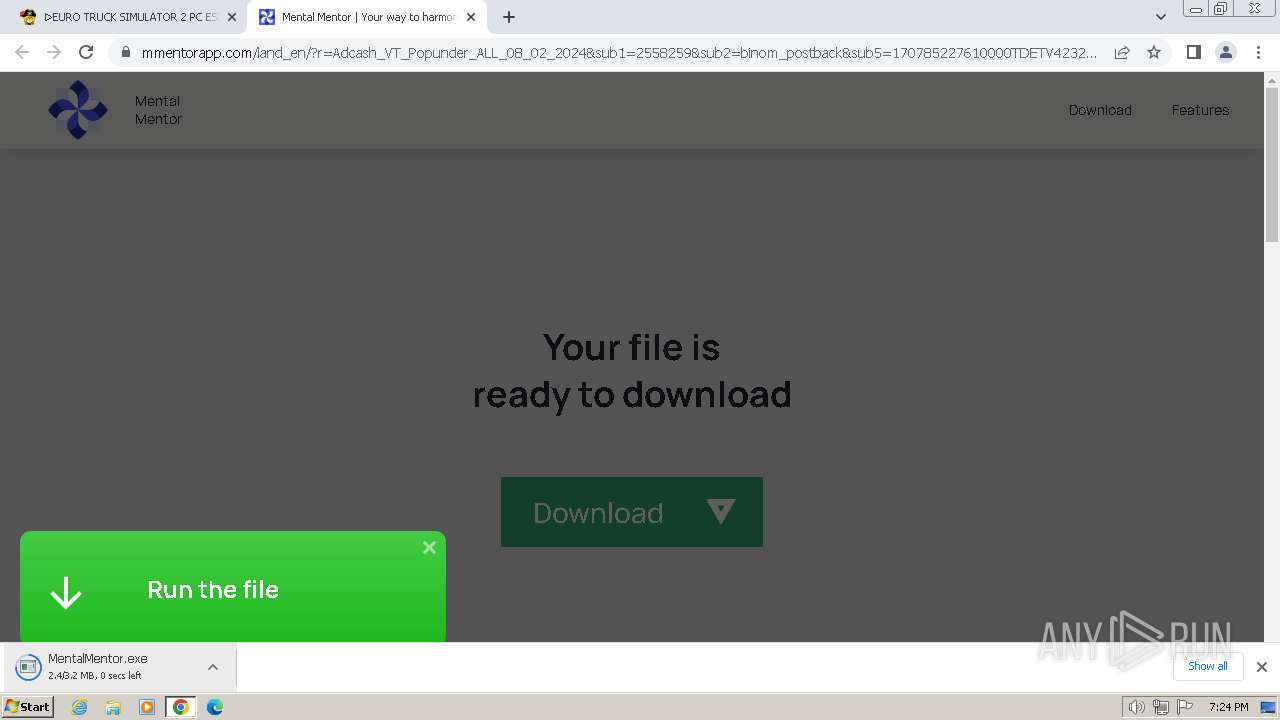
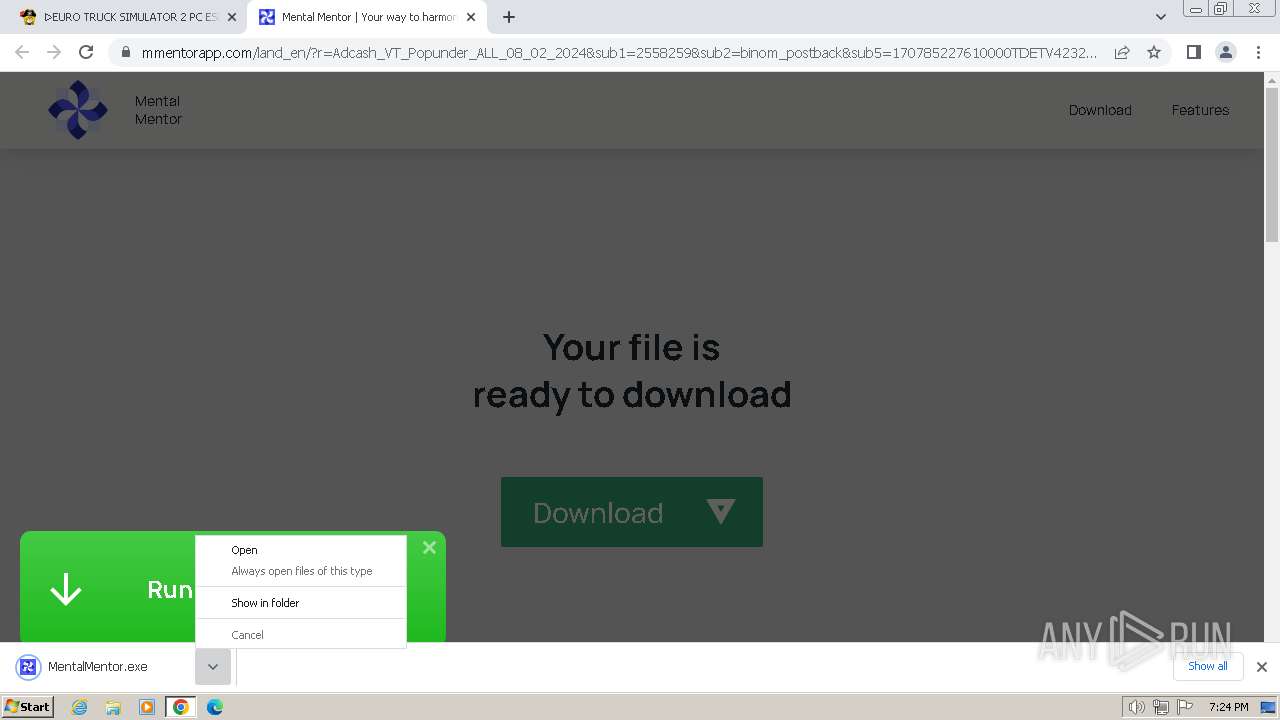
Drops the executable file immediately after the start
- MentalMentor.exe (PID: 3000)
- MentalMentor.exe (PID: 2944)
- MentalMentor.tmp (PID: 2368)
- 7z.exe (PID: 1768)
- 7z.exe (PID: 2184)
- 7z.exe (PID: 3680)
- luminati.exe (PID: 2536)
- net_updater32.exe (PID: 1848)
- luminati.exe (PID: 3356)
- luminati.exe (PID: 3548)
- luminati.exe (PID: 2156)
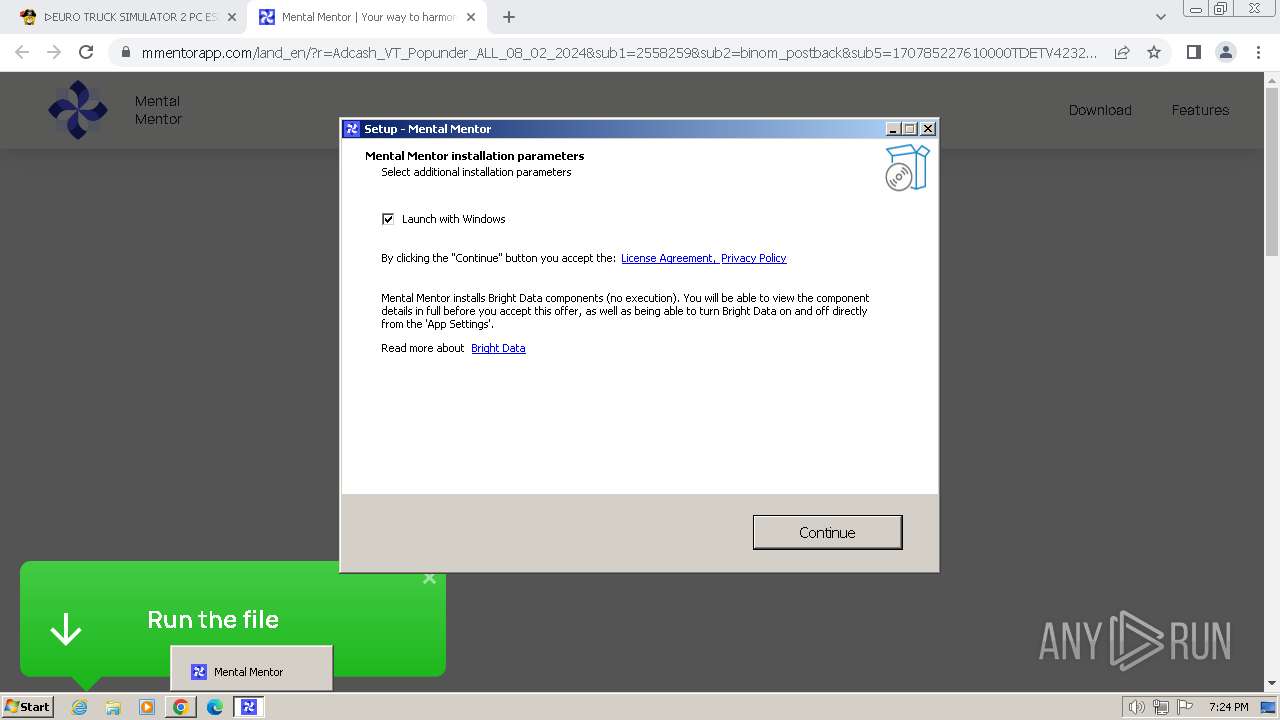
Changes the autorun value in the registry
- mentalmentor.exe (PID: 2004)
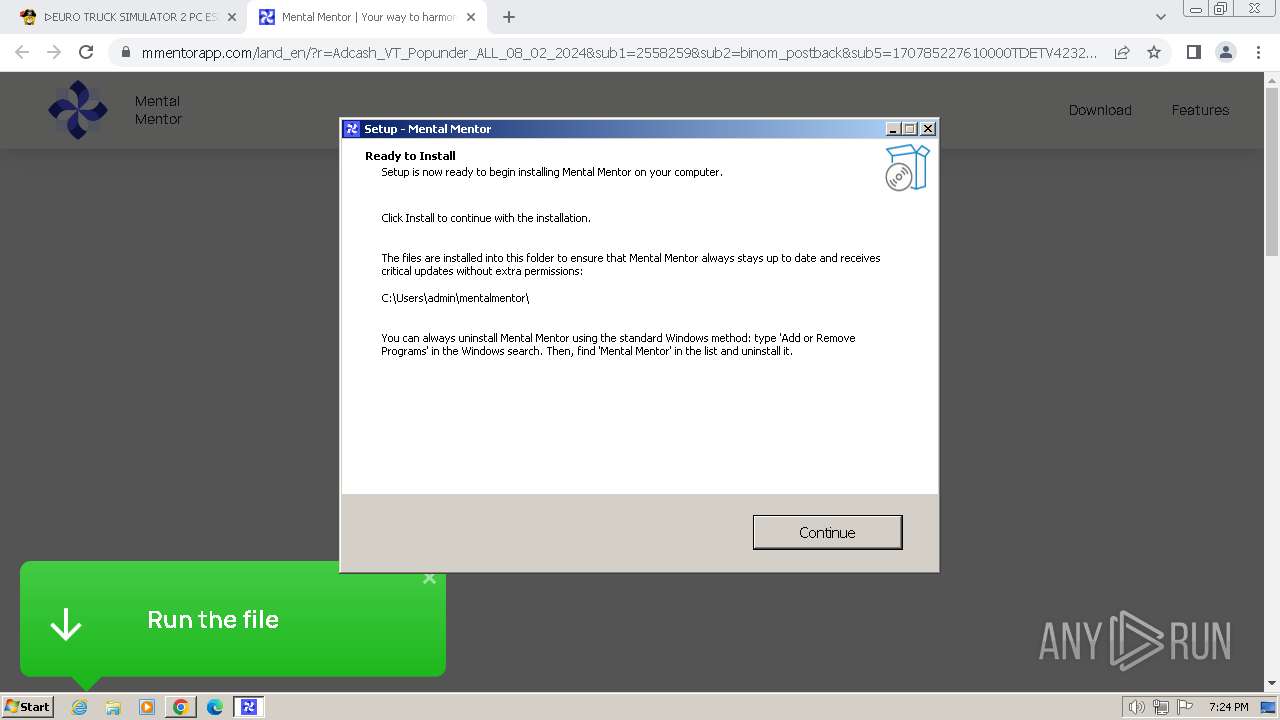
Creates a writable file in the system directory
- net_updater32.exe (PID: 1848)
SUSPICIOUS
Executable content was dropped or overwritten
- MentalMentor.exe (PID: 3000)
- MentalMentor.exe (PID: 2944)
- MentalMentor.tmp (PID: 2368)
- 7z.exe (PID: 1768)
- 7z.exe (PID: 2184)
- 7z.exe (PID: 3680)
- luminati.exe (PID: 2536)
- net_updater32.exe (PID: 1848)
- luminati.exe (PID: 3356)
- luminati.exe (PID: 3548)
- luminati.exe (PID: 2156)
Reads the Windows owner or organization settings
- MentalMentor.tmp (PID: 2368)
Drops 7-zip archiver for unpacking
- MentalMentor.tmp (PID: 2368)
Process drops legitimate windows executable
- 7z.exe (PID: 1768)
- luminati.exe (PID: 2536)
The process drops C-runtime libraries
- 7z.exe (PID: 1768)
- luminati.exe (PID: 2536)
Reads the Internet Settings
- mentalmentor.exe (PID: 2004)
- QtWebEngineProcess.exe (PID: 4064)
- luminati.exe (PID: 2536)
- luminati.exe (PID: 3356)
- luminati.exe (PID: 3548)
- luminati.exe (PID: 2156)
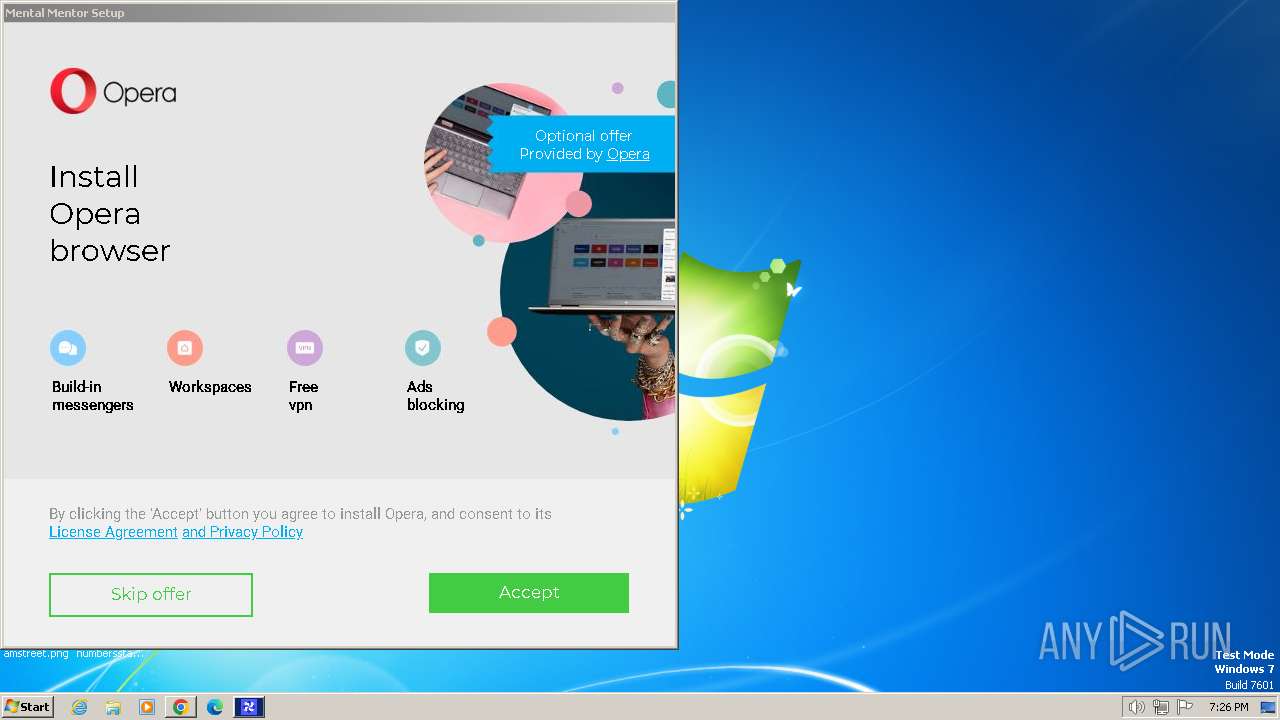
Searches for installed software
- MentalMentor.tmp (PID: 2368)
Uses NETSH.EXE to add a firewall rule or allowed programs
- MentalMentor.tmp (PID: 2368)
Reads settings of System Certificates
- mentalmentor.exe (PID: 2004)
- QtWebEngineProcess.exe (PID: 4064)
- luminati.exe (PID: 2536)
- net_updater32.exe (PID: 2804)
Reads the date of Windows installation
- mentalmentor.exe (PID: 2004)
Reads security settings of Internet Explorer
- mentalmentor.exe (PID: 2004)
- luminati.exe (PID: 2536)
Adds/modifies Windows certificates
- QtWebEngineProcess.exe (PID: 4064)
- luminati.exe (PID: 2536)
Detected use of alternative data streams (AltDS)
- luminati.exe (PID: 2536)
- net_updater32.exe (PID: 1848)
- luminati.exe (PID: 3548)
- luminati.exe (PID: 2156)
- luminati.exe (PID: 3356)
Executes as Windows Service
- net_updater32.exe (PID: 1848)
Checks Windows Trust Settings
- net_updater32.exe (PID: 1848)
INFO
Manual execution by a user
- wmpnscfg.exe (PID: 3500)
Reads the computer name
- wmpnscfg.exe (PID: 3500)
- MentalMentor.tmp (PID: 3316)
- MentalMentor.tmp (PID: 2368)
- mentalmentor.exe (PID: 2004)
- QtWebEngineProcess.exe (PID: 4064)
- test_wpf.exe (PID: 3432)
- luminati.exe (PID: 2536)
- net_updater32.exe (PID: 2804)
- net_updater32.exe (PID: 1848)
- test_wpf.exe (PID: 2772)
- idle_report.exe (PID: 3476)
- test_wpf.exe (PID: 1692)
- luminati.exe (PID: 3356)
- test_wpf.exe (PID: 2780)
- luminati.exe (PID: 3548)
- test_wpf.exe (PID: 3540)
- idle_report.exe (PID: 2204)
- luminati.exe (PID: 2156)
- brightdata.exe (PID: 3472)
Checks supported languages
- wmpnscfg.exe (PID: 3500)
- MentalMentor.exe (PID: 3000)
- MentalMentor.tmp (PID: 3316)
- MentalMentor.exe (PID: 2944)
- MentalMentor.tmp (PID: 2368)
- 7z.exe (PID: 1768)
- 7z.exe (PID: 2184)
- 7z.exe (PID: 4088)
- 7z.exe (PID: 3680)
- mentalmentor_crashpad_handler.exe (PID: 2784)
- mentalmentor.exe (PID: 2004)
- QtWebEngineProcess.exe (PID: 2544)
- QtWebEngineProcess.exe (PID: 4064)
- luminati.exe (PID: 2536)
- test_wpf.exe (PID: 3432)
- QtWebEngineProcess.exe (PID: 1044)
- net_updater32.exe (PID: 2804)
- net_updater32.exe (PID: 1848)
- idle_report.exe (PID: 3476)
- test_wpf.exe (PID: 2772)
- brightdata.exe (PID: 3472)
- luminati.exe (PID: 3356)
- test_wpf.exe (PID: 1692)
- luminati.exe (PID: 3548)
- luminati.exe (PID: 2156)
- test_wpf.exe (PID: 2780)
- test_wpf.exe (PID: 3540)
- idle_report.exe (PID: 2204)
Executable content was dropped or overwritten
- chrome.exe (PID: 3136)
- chrome.exe (PID: 3668)
- chrome.exe (PID: 3688)
Drops the executable file immediately after the start
- chrome.exe (PID: 3668)
- chrome.exe (PID: 3136)
- chrome.exe (PID: 3688)
Create files in a temporary directory
- MentalMentor.exe (PID: 3000)
- MentalMentor.exe (PID: 2944)
- MentalMentor.tmp (PID: 2368)
- QtWebEngineProcess.exe (PID: 4064)
The process uses the downloaded file
- chrome.exe (PID: 568)
- chrome.exe (PID: 3668)
- chrome.exe (PID: 1792)
Connects to unusual port
- chrome.exe (PID: 3848)
Application launched itself
- chrome.exe (PID: 3668)
Reads the machine GUID from the registry
- MentalMentor.tmp (PID: 2368)
- mentalmentor.exe (PID: 2004)
- luminati.exe (PID: 2536)
- QtWebEngineProcess.exe (PID: 4064)
- test_wpf.exe (PID: 3432)
- net_updater32.exe (PID: 2804)
- net_updater32.exe (PID: 1848)
- idle_report.exe (PID: 3476)
- test_wpf.exe (PID: 2772)
- brightdata.exe (PID: 3472)
- luminati.exe (PID: 3356)
- test_wpf.exe (PID: 1692)
- test_wpf.exe (PID: 2780)
- luminati.exe (PID: 2156)
- test_wpf.exe (PID: 3540)
- idle_report.exe (PID: 2204)
- luminati.exe (PID: 3548)
Creates a software uninstall entry
- MentalMentor.tmp (PID: 2368)
Process checks computer location settings
- QtWebEngineProcess.exe (PID: 2544)
- luminati.exe (PID: 2536)
- QtWebEngineProcess.exe (PID: 1044)
- net_updater32.exe (PID: 1848)
- luminati.exe (PID: 3548)
- luminati.exe (PID: 2156)
- luminati.exe (PID: 3356)
Creates files in the program directory
- luminati.exe (PID: 2536)
- net_updater32.exe (PID: 2804)
- net_updater32.exe (PID: 1848)
- brightdata.exe (PID: 3472)
- luminati.exe (PID: 3356)
- luminati.exe (PID: 3548)
- luminati.exe (PID: 2156)
Reads the software policy settings
- QtWebEngineProcess.exe (PID: 4064)
- luminati.exe (PID: 2536)
- net_updater32.exe (PID: 2804)
- net_updater32.exe (PID: 1848)
Reads Environment values
- luminati.exe (PID: 2536)
- net_updater32.exe (PID: 1848)
- brightdata.exe (PID: 3472)
- luminati.exe (PID: 3548)
- luminati.exe (PID: 2156)
- luminati.exe (PID: 3356)
Creates files or folders in the user directory
- luminati.exe (PID: 2536)
- QtWebEngineProcess.exe (PID: 4064)
Checks proxy server information
- luminati.exe (PID: 2536)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
142
Monitored processes
86
Malicious processes
12
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 552 | "netsh" advfirewall firewall add rule name="Mental Mentor" dir=in action=allow program="C:\Users\admin\mentalmentor\QtWebEngineProcess.exe" enable=yes | C:\Windows\System32\netsh.exe | — | MentalMentor.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=4456 --field-trial-handle=1164,i,17793998731703400664,10656873348266242389,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=39 --mojo-platform-channel-handle=4580 --field-trial-handle=1164,i,17793998731703400664,10656873348266242389,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --mojo-platform-channel-handle=3548 --field-trial-handle=1164,i,17793998731703400664,10656873348266242389,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=4856 --field-trial-handle=1164,i,17793998731703400664,10656873348266242389,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3364 --field-trial-handle=1164,i,17793998731703400664,10656873348266242389,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3628 --field-trial-handle=1164,i,17793998731703400664,10656873348266242389,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --mojo-platform-channel-handle=2088 --field-trial-handle=1164,i,17793998731703400664,10656873348266242389,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1044 | "C:\Users\admin\mentalmentor\QtWebEngineProcess.exe" --type=renderer --disable-speech-api --enable-threaded-compositing --enable-features=AllowContentInitiatedDataUrlNavigations,TracingServiceInProcess --disable-features=BackgroundFetch,ConsolidatedMovementXY,DnsOverHttpsUpgrade,FormControlsRefresh,MojoVideoCapture,PictureInPicture,SmsReceiver,UseSkiaRenderer,WebPayments,WebUSB --disable-gpu-compositing --lang=en-US --webengine-schemes=qrc:sLV --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --mojo-platform-channel-handle=2640 /prefetch:1 | C:\Users\admin\mentalmentor\QtWebEngineProcess.exe | — | mentalmentor.exe | |||||||||||
User: admin Company: The Qt Company Ltd. Integrity Level: LOW Description: C++ Application Development Framework Exit code: 0 Version: 5.15.2.0 Modules
| |||||||||||||||
| 1092 | "netsh" advfirewall firewall add rule name="Mental Mentor" dir=in action=allow program="C:\Users\admin\mentalmentor\mentalmentor.exe" enable=yes | C:\Windows\System32\netsh.exe | — | MentalMentor.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
72 985
Read events
72 402
Write events
545
Delete events
38
Modification events
| (PID) Process: | (3668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3668) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
61
Suspicious files
111
Text files
130
Unknown types
127
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF17f1f1.TMP | — | |
MD5:— | SHA256:— | |||
| 3668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:358570F689377CE6838812643E03734B | SHA256:5B41FCC2E1A843AEAB9437B06E27B798870FF10D86A51B163BF48862BCD32590 | |||
| 3668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF17f201.TMP | text | |
MD5:05CF4C3C5148DA6355D3561A9EAA5E8A | SHA256:8D720243F6876898E4F197C8867C4CEE69F1C7335C55B8A29C120B1028D93E41 | |||
| 3668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF17f3c6.TMP | text | |
MD5:C5B082BC8EA6A9BD1DC6782C00A79605 | SHA256:6168A9E585264DE05DEE1B67427B1BC277F1B83B9297184EFACC5D3BB061ABDE | |||
| 3668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF17f935.TMP | — | |
MD5:— | SHA256:— | |||
| 3668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 3668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\45bab064-ed8e-4564-9ed3-95f740f64d73.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
50
TCP/UDP connections
234
DNS requests
225
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 9.37 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 9.39 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 11.7 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 21.4 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 38.1 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 64.7 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 5.75 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 160 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 734 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3848 | chrome.exe | 74.125.71.84:443 | accounts.google.com | GOOGLE | US | unknown |
3668 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
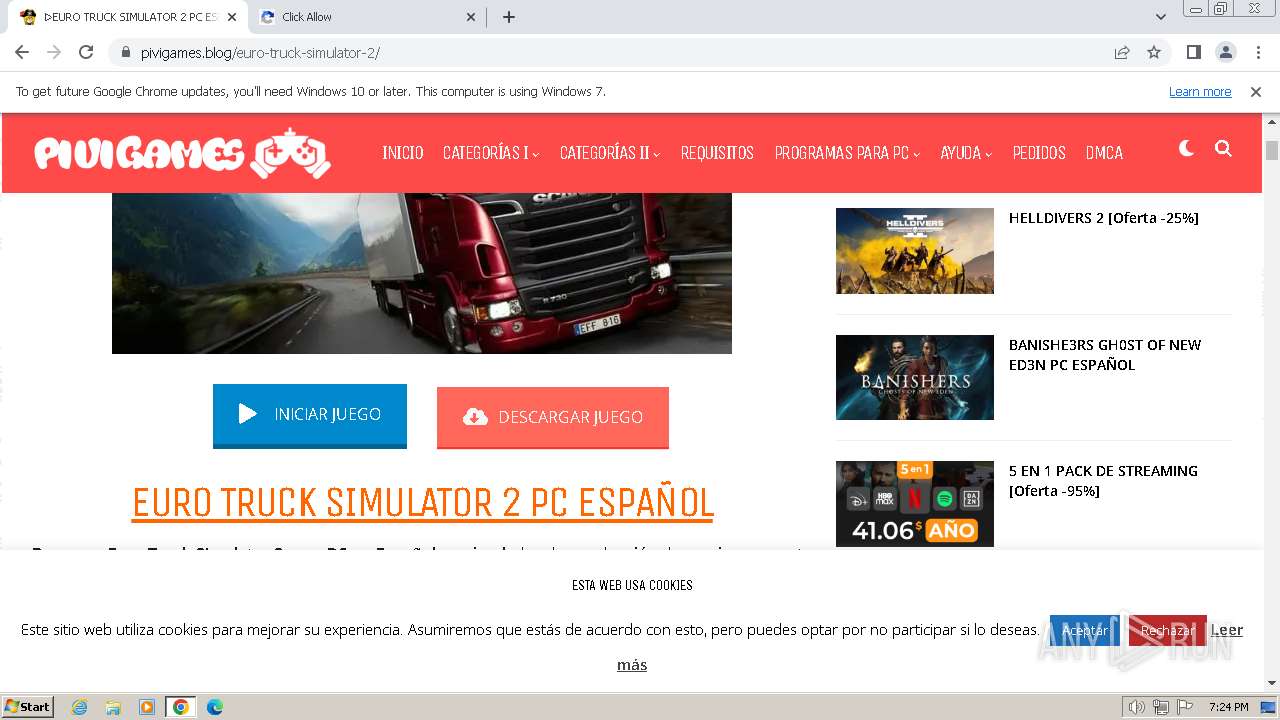
3848 | chrome.exe | 104.21.17.80:443 | pivigames.blog | CLOUDFLARENET | — | unknown |
3848 | chrome.exe | 192.0.77.37:443 | c0.wp.com | AUTOMATTIC | US | unknown |
3848 | chrome.exe | 192.0.77.2:443 | i0.wp.com | AUTOMATTIC | US | unknown |
3848 | chrome.exe | 172.217.16.200:443 | www.googletagmanager.com | GOOGLE | US | whitelisted |
3848 | chrome.exe | 104.18.214.59:443 | cdn.onesignal.com | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
pivigames.blog |
| whitelisted |
c0.wp.com |
| whitelisted |
i0.wp.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
cdn.onesignal.com |
| whitelisted |
stats.wp.com |
| whitelisted |
analytics.marketcat.net |
| unknown |
content-autofill.googleapis.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3848 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
3848 | chrome.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1848 | net_updater32.exe | Potential Corporate Privacy Violation | ET POLICY Dropbox.com Offsite File Backup in Use |
1848 | net_updater32.exe | Misc activity | ET INFO DropBox User Content Download Access over SSL M2 |
Process | Message |
|---|---|
mentalmentor.exe | QWindowsEGLStaticContext::create: Could not initialize EGL display: error 0x3001
|
mentalmentor.exe | QWindowsEGLStaticContext::create: When using ANGLE, check if d3dcompiler_4x.dll is available
|