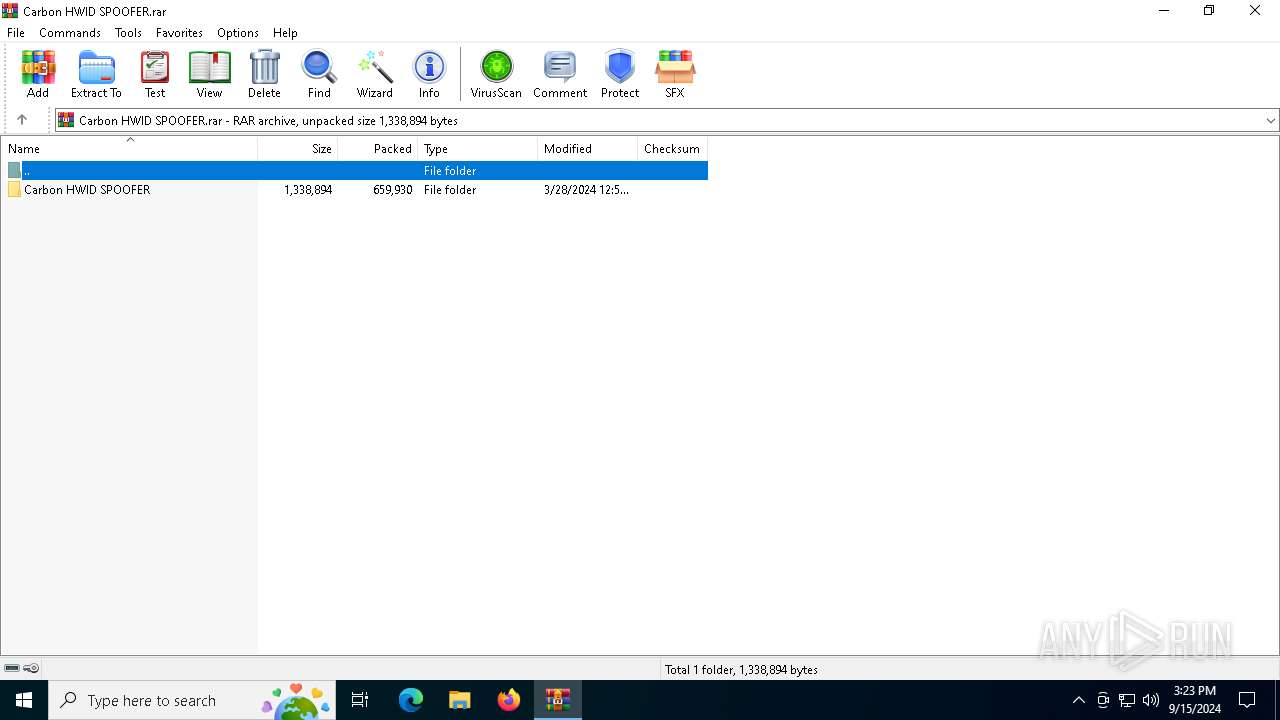
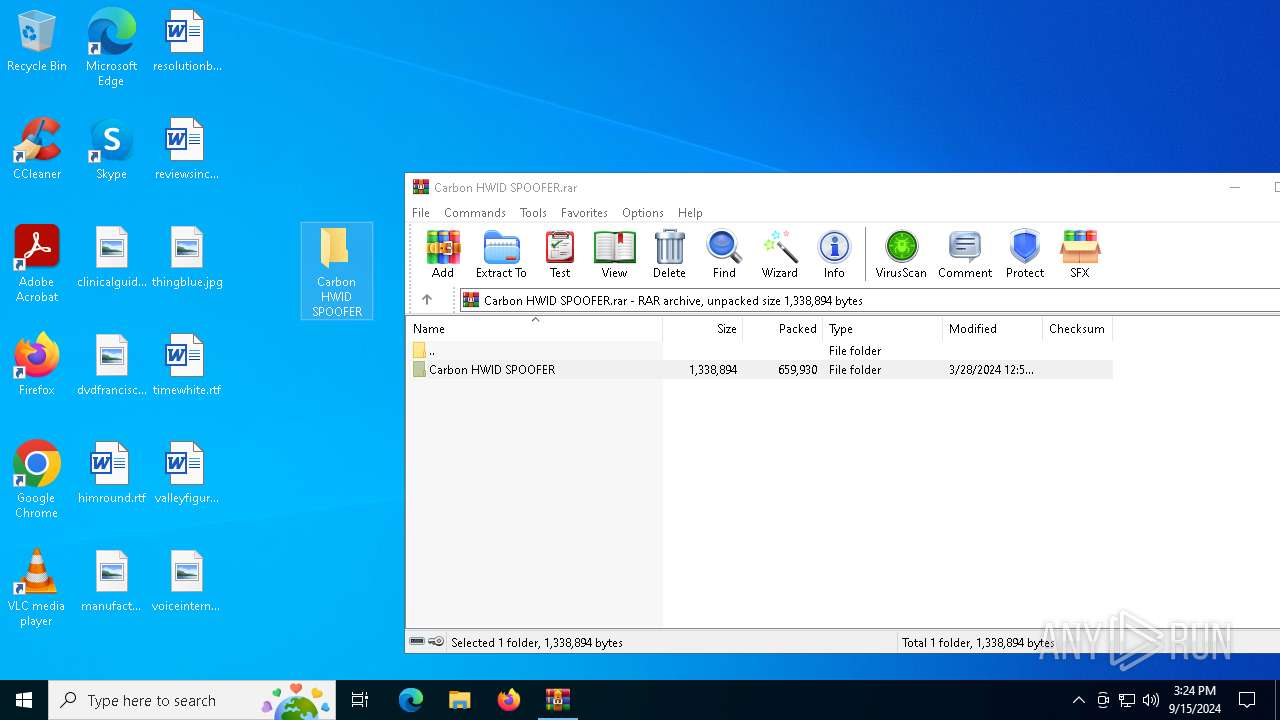
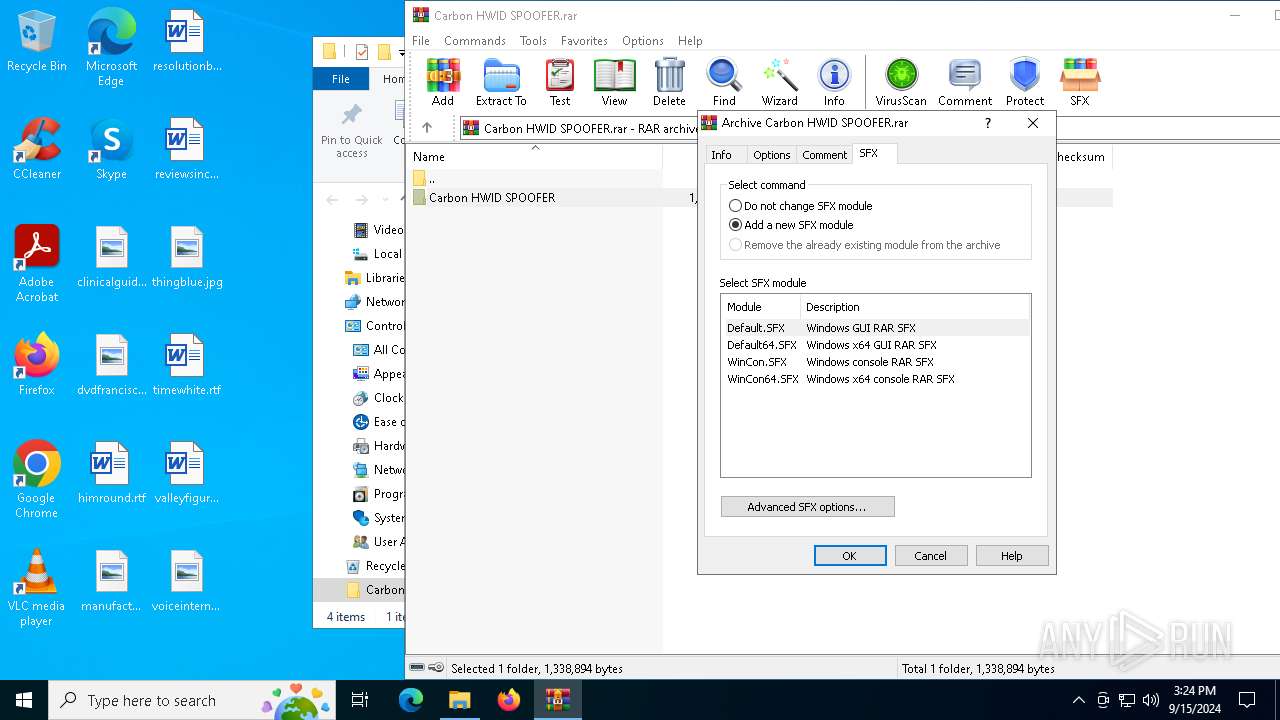
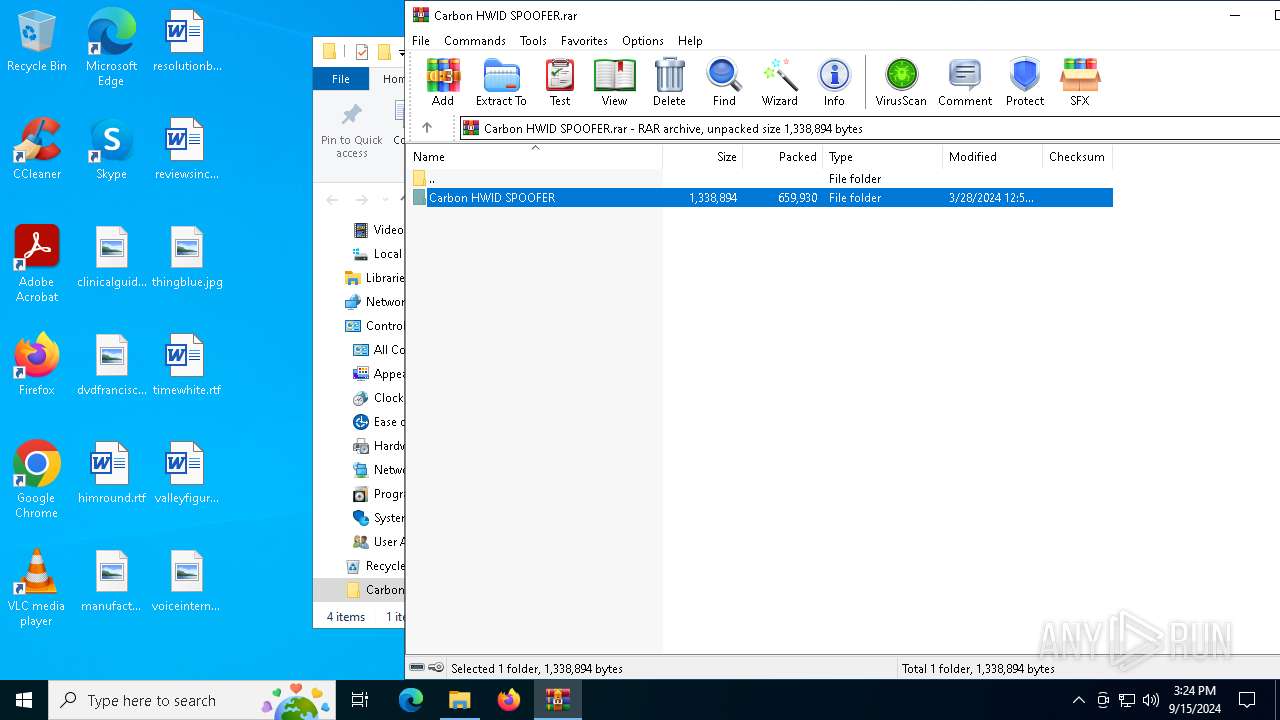
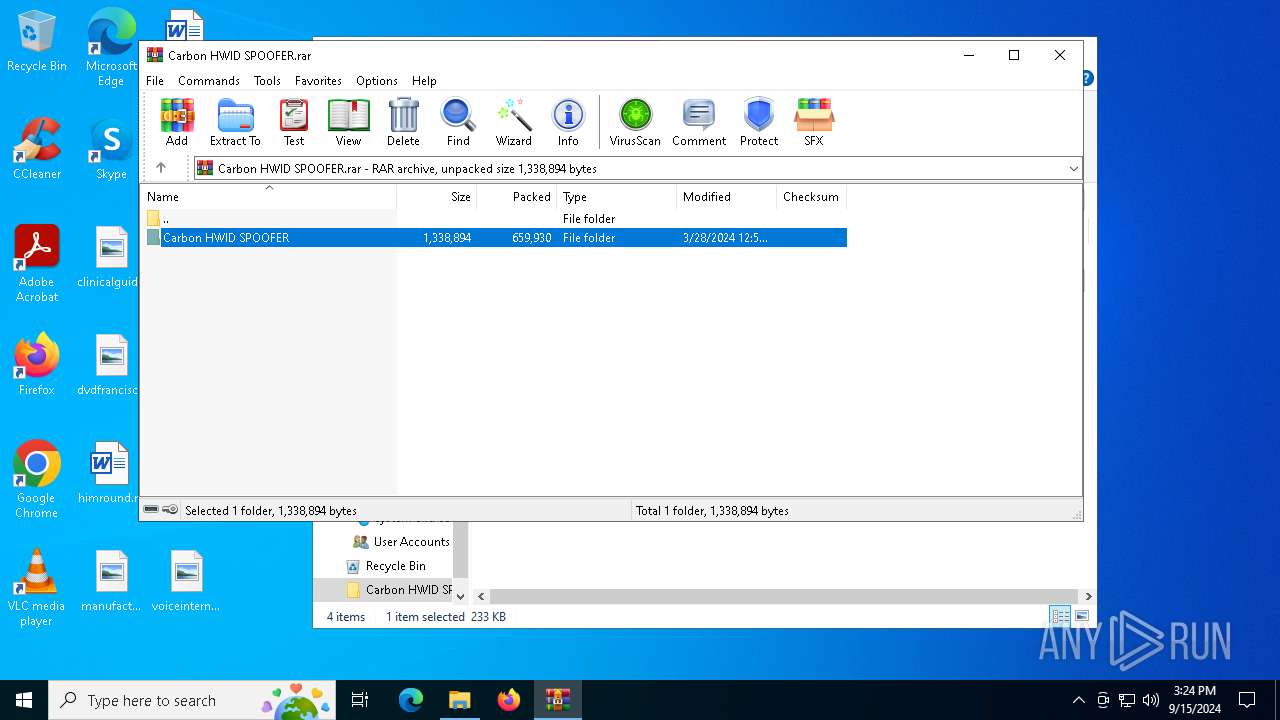
| File name: | Carbon HWID SPOOFER.rar |
| Full analysis: | https://app.any.run/tasks/31354c4a-393f-400e-94a5-7c5c1b152d42 |
| Verdict: | Malicious activity |
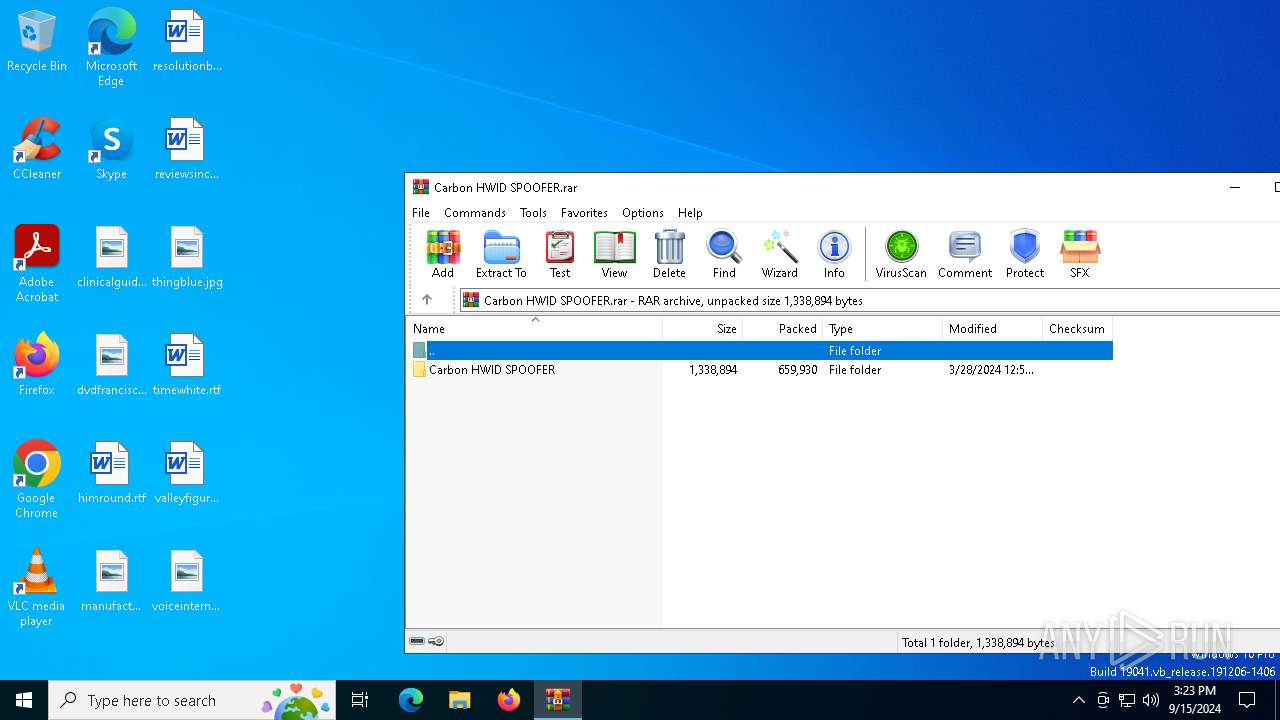
| Analysis date: | September 15, 2024, 15:23:50 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 1EFFF79ED1860036E34459EBD312854B |
| SHA1: | F2C052BC6A1012CA69EA476D0A7241E6D7682459 |
| SHA256: | A68DEF7FACCB3C9F75BA6076E01F68D9005FF8B86ACF667EB23345AF6506EF75 |
| SSDEEP: | 24576:eQsEgCRIWN4GjUoNYHug32mmqy1tdT5Bg/iap0r19NWXWbcIQ/3CRIWN48b:eQsEgCRF4GjUoeHugmmmqy1tdT5Bg/iD |
MALICIOUS
Adds path to the Windows Defender exclusion list
- Launcher.exe (PID: 6460)
- Runtime Explorer.exe (PID: 6280)
Create files in the Startup directory
- Launcher.exe (PID: 6460)
Changes the autorun value in the registry
- Launcher.exe (PID: 6460)
- Runtime Explorer.exe (PID: 6280)
SUSPICIOUS
Reads security settings of Internet Explorer
- Carbon HWID SPOOFER.exe (PID: 3584)
- Launcher.exe (PID: 6460)
- Windows Services.exe (PID: 5624)
- Runtime Explorer.exe (PID: 6280)
Script adds exclusion path to Windows Defender
- Launcher.exe (PID: 6460)
- Runtime Explorer.exe (PID: 6280)
Starts POWERSHELL.EXE for commands execution
- Launcher.exe (PID: 6460)
- Runtime Explorer.exe (PID: 6280)
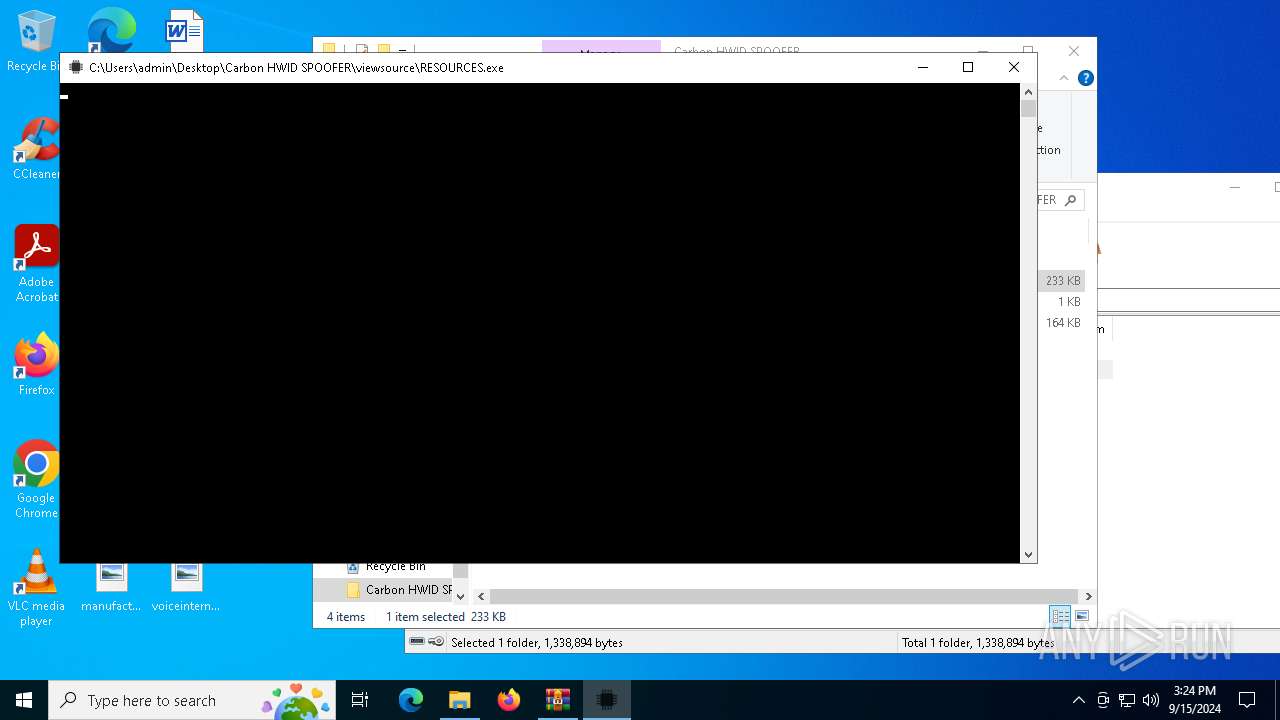
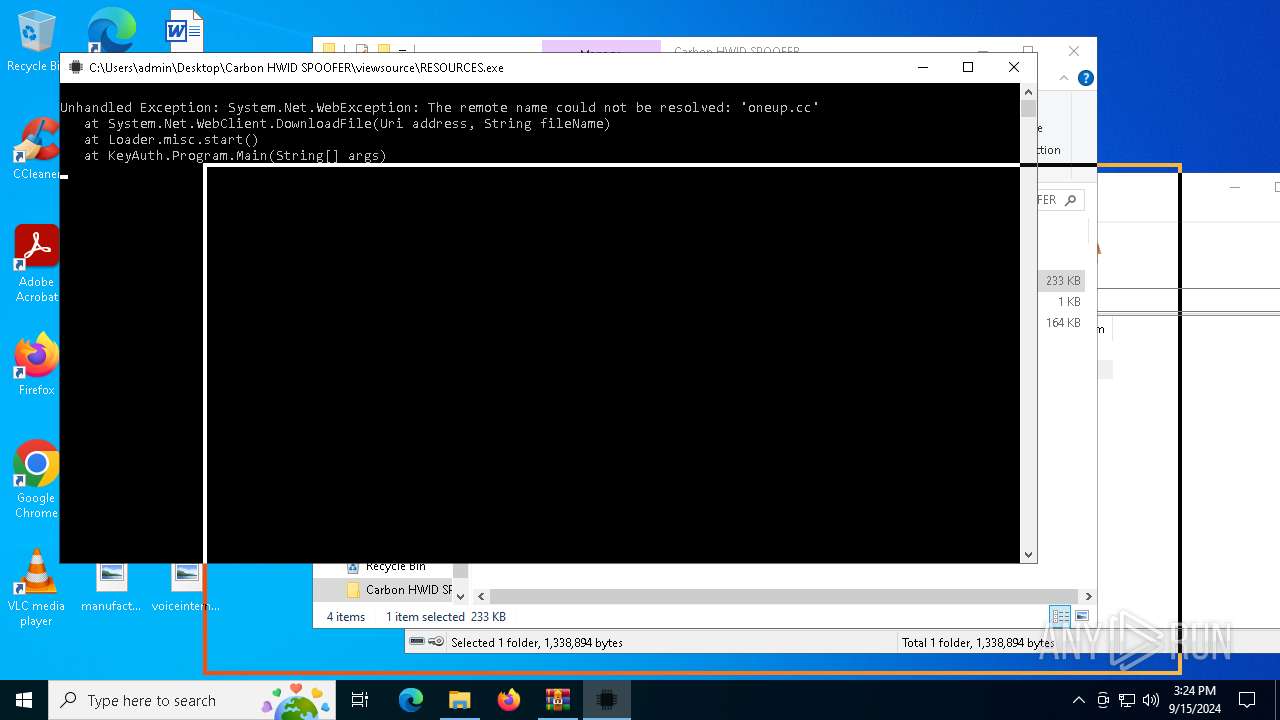
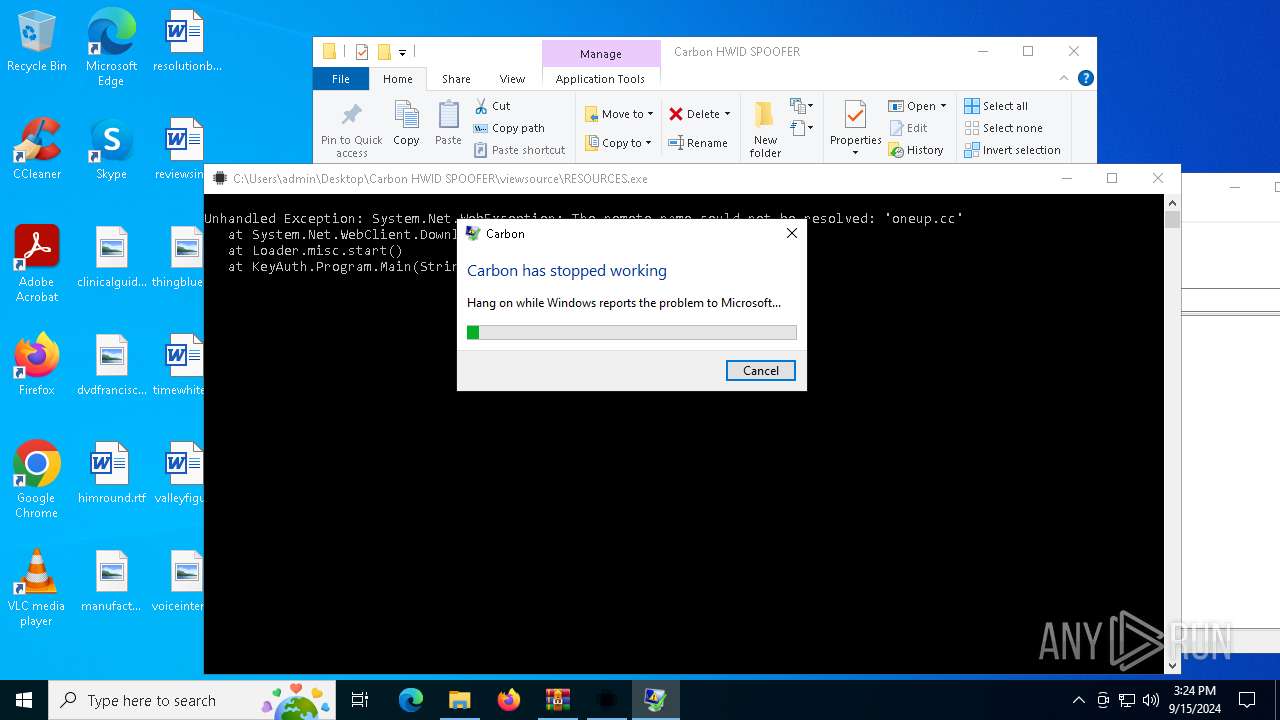
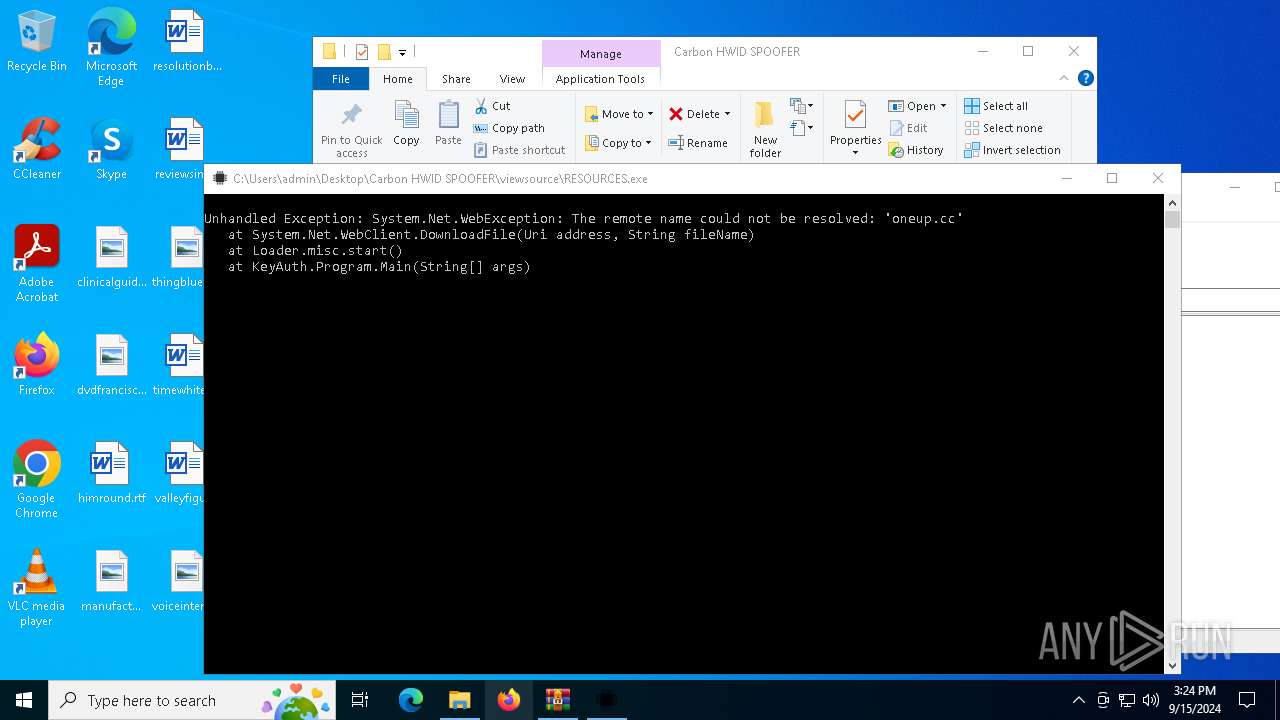
Executes application which crashes
- RESOURCES.exe (PID: 6876)
Executable content was dropped or overwritten
- Launcher.exe (PID: 6460)
- Runtime Explorer.exe (PID: 6280)
The process creates files with name similar to system file names
- Launcher.exe (PID: 6460)
- Runtime Explorer.exe (PID: 6280)
INFO
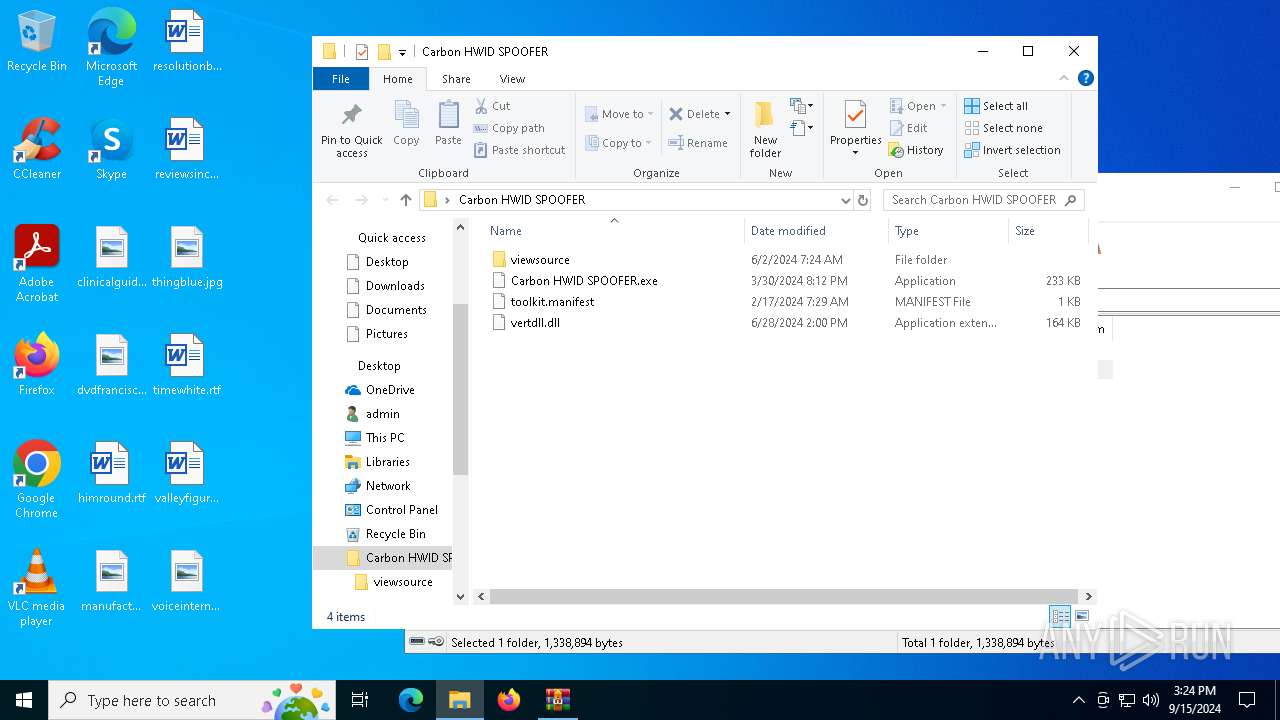
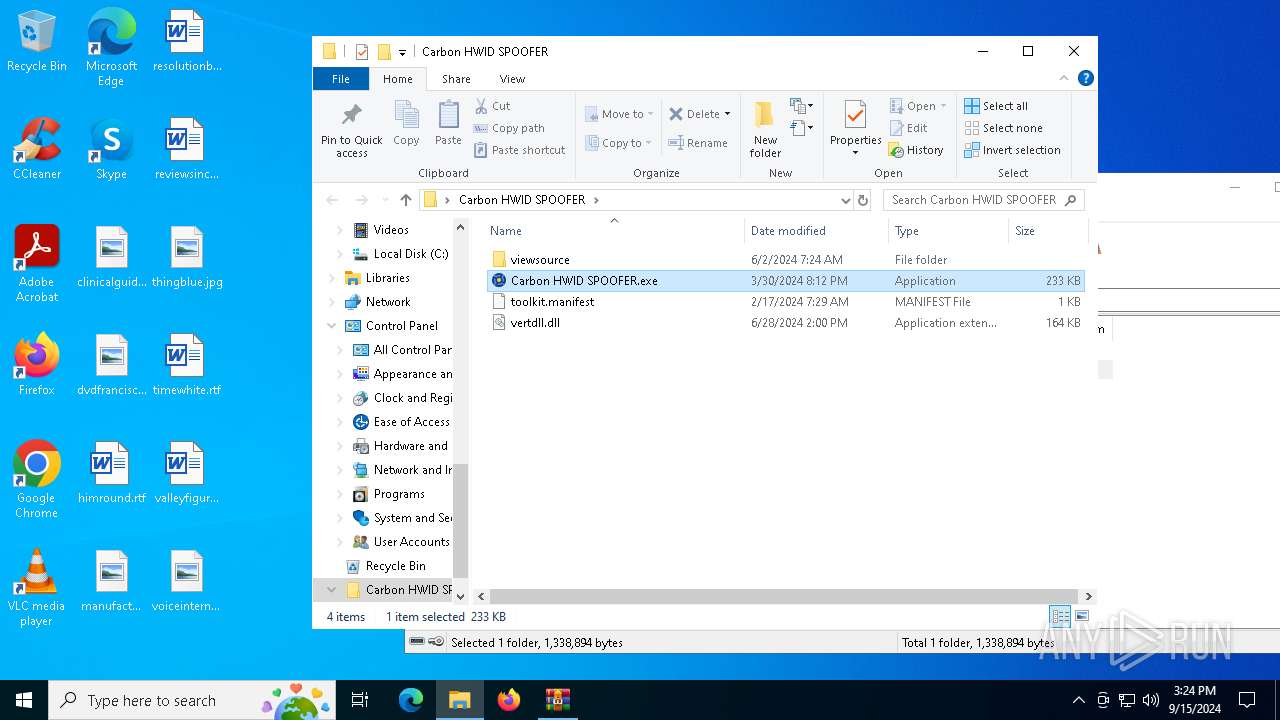
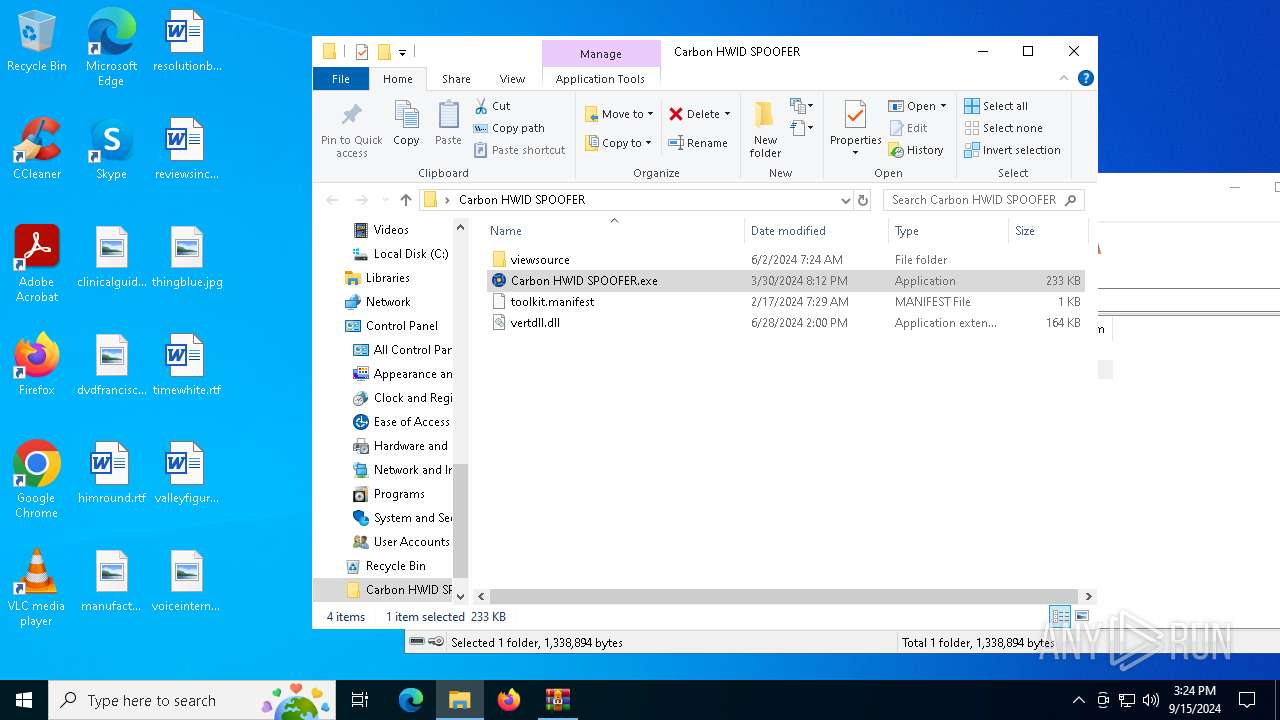
Manual execution by a user
- Carbon HWID SPOOFER.exe (PID: 3584)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6844)
Checks supported languages
- Carbon HWID SPOOFER.exe (PID: 3584)
- Launcher.exe (PID: 6460)
- RESOURCES.exe (PID: 6876)
- Windows Services.exe (PID: 5624)
- Secure System Shell.exe (PID: 6260)
- Runtime Explorer.exe (PID: 6280)
The process uses the downloaded file
- WinRAR.exe (PID: 6844)
- Carbon HWID SPOOFER.exe (PID: 3584)
- Launcher.exe (PID: 6460)
- Windows Services.exe (PID: 5624)
- Runtime Explorer.exe (PID: 6280)
- powershell.exe (PID: 3384)
- powershell.exe (PID: 6596)
Reads the machine GUID from the registry
- Carbon HWID SPOOFER.exe (PID: 3584)
- Launcher.exe (PID: 6460)
- RESOURCES.exe (PID: 6876)
- Windows Services.exe (PID: 5624)
- Secure System Shell.exe (PID: 6260)
Reads the computer name
- Carbon HWID SPOOFER.exe (PID: 3584)
- Launcher.exe (PID: 6460)
- RESOURCES.exe (PID: 6876)
- Windows Services.exe (PID: 5624)
- Secure System Shell.exe (PID: 6260)
- Runtime Explorer.exe (PID: 6280)
Process checks computer location settings
- Carbon HWID SPOOFER.exe (PID: 3584)
- Launcher.exe (PID: 6460)
- Windows Services.exe (PID: 5624)
- Runtime Explorer.exe (PID: 6280)
Creates files or folders in the user directory
- RESOURCES.exe (PID: 6876)
- Launcher.exe (PID: 6460)
- Runtime Explorer.exe (PID: 6280)
- WerFault.exe (PID: 4976)
Reads Environment values
- RESOURCES.exe (PID: 6876)
Checks proxy server information
- RESOURCES.exe (PID: 6876)
Disables trace logs
- RESOURCES.exe (PID: 6876)
Create files in a temporary directory
- Runtime Explorer.exe (PID: 6280)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 3384)
- powershell.exe (PID: 6596)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6596)
- powershell.exe (PID: 3384)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
146
Monitored processes
17
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 8 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2256 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2576 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3384 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" add-mppreference -exclusionpath C:\Users\admin\AppData\Roaming\ | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | Runtime Explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3584 | "C:\Users\admin\Desktop\Carbon HWID SPOOFER\Carbon HWID SPOOFER.exe" | C:\Users\admin\Desktop\Carbon HWID SPOOFER\Carbon HWID SPOOFER.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Launcher Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 4976 | C:\WINDOWS\system32\WerFault.exe -u -p 6876 -s 1372 | C:\Windows\System32\WerFault.exe | — | RESOURCES.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5532 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5624 | "C:\Windows\IMF\Windows Services.exe" {Arguments If Needed} | C:\Windows\IMF\Windows Services.exe | — | Launcher.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Windows Services Version: 1.0.0.0 Modules
| |||||||||||||||
| 6128 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6236 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
18 652
Read events
18 605
Write events
44
Delete events
3
Modification events
| (PID) Process: | (6844) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6844) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Carbon HWID SPOOFER.rar | |||
| (PID) Process: | (6844) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6844) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6844) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6844) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6876) RESOURCES.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RESOURCES_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6876) RESOURCES.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RESOURCES_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6876) RESOURCES.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RESOURCES_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6876) RESOURCES.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RESOURCES_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
Executable files
13
Suspicious files
7
Text files
14
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6844 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6844.15006\Carbon HWID SPOOFER\Carbon HWID SPOOFER.exe | executable | |
MD5:A8FAC10F4A26603BBE6BC31568549D02 | SHA256:F3B517BB73805BCEDDDF681E6966089D24851972B5348CC69E07BDD6B932B35D | |||
| 6844 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6844.15006\Carbon HWID SPOOFER\viewsource\ua.css | text | |
MD5:F41CD1E91B86B97DD2D28CA108F5166D | SHA256:9E56E19DB8DC215E6112FDCBA75A76CA27EBF3B9FC15A1D5EA4C1C89D3F586C7 | |||
| 6844 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6844.15006\Carbon HWID SPOOFER\viewsource\toolkit.manifest | text | |
MD5:F730F2D4B0342A6C1010FACCE56E4173 | SHA256:FCCB4C33EA0BB4A8F85FCC5596E6A4FF85ADF522CC352F5FC9FA685AB0975AC9 | |||
| 6596 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_dixwezdv.ufj.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6460 | Launcher.exe | C:\Windows\IMF\Windows Services.exe | executable | |
MD5:AD0CE1302147FBDFECAEC58480EB9CF9 | SHA256:2C339B52B82E73B4698A0110CDFE310C00C5C69078E9E1BD6FA1308652BF82A3 | |||
| 6844 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6844.15006\Carbon HWID SPOOFER\viewsource\xhtml11.dtd | text | |
MD5:7F7B2F0922918714B3CADCB21EB30DE4 | SHA256:9D595ACD4EDCC171ED84213328736337D3A8265AD22EBA3B28F09FA514DE7FFB | |||
| 6844 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6844.15006\Carbon HWID SPOOFER\viewsource\RESOURCES.exe | executable | |
MD5:321C269C0791A5F99E61E5351499FD32 | SHA256:61A55B69CF1DDCFA21A74A4F496C9AFFAD2BE76C8DFB2C76AD9612751BF2D172 | |||
| 6460 | Launcher.exe | C:\Windows\IMF\LICENCE.dat | compressed | |
MD5:5180046F168DFD684B5BF268F5A0FA56 | SHA256:4139BAA8BEEBCDE4504C33BC88CF13B9AB9F32E4A054871EBEB82BE6B84EDC01 | |||
| 6460 | Launcher.exe | C:\Windows\IMF\Runtime Explorer.exe | executable | |
MD5:03F5E0141F4519F0C5AC26CE0B036A0F | SHA256:78A408C628E33E3332645F480EE7CE01B5DC24FC96CF16FFA0868D43F3D421EF | |||
| 6596 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ej4wgqmj.wr5.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
25
DNS requests
16
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1712 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1184 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6224 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1184 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6224 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6412 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6224 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6224 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3260 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1712 | svchost.exe | 40.126.32.76:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1712 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
oneup.cc |
| unknown |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |