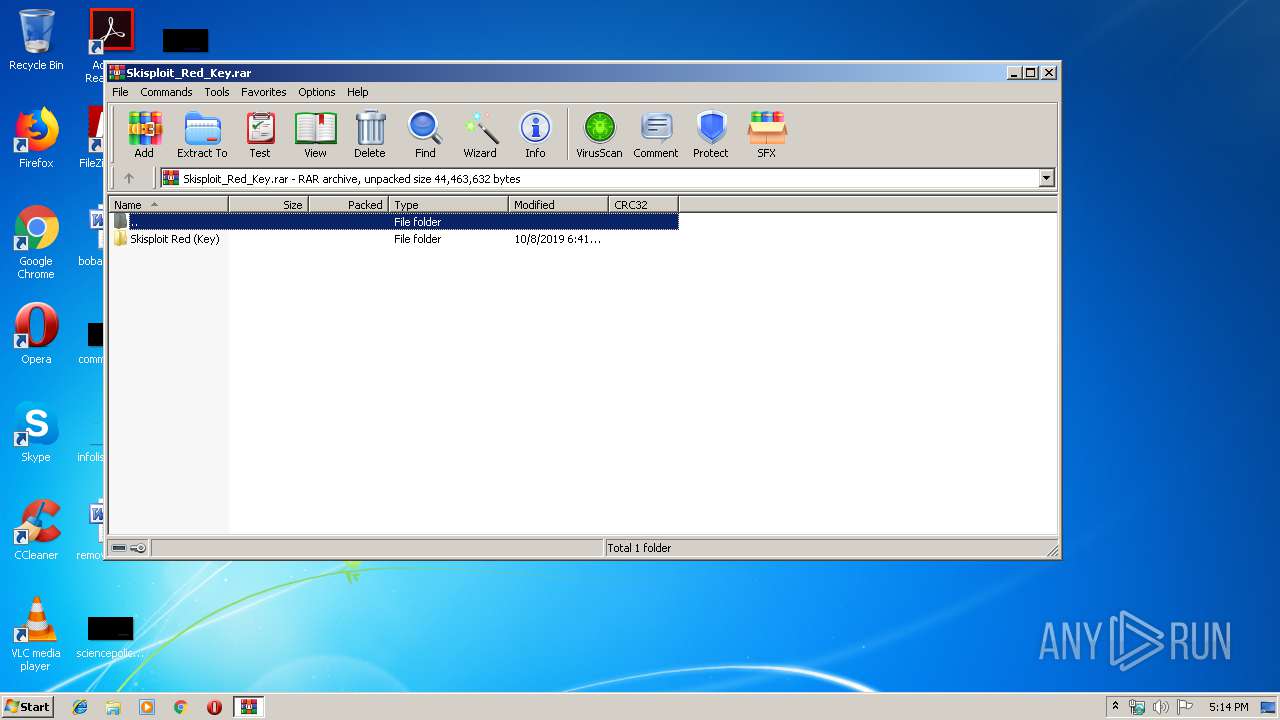
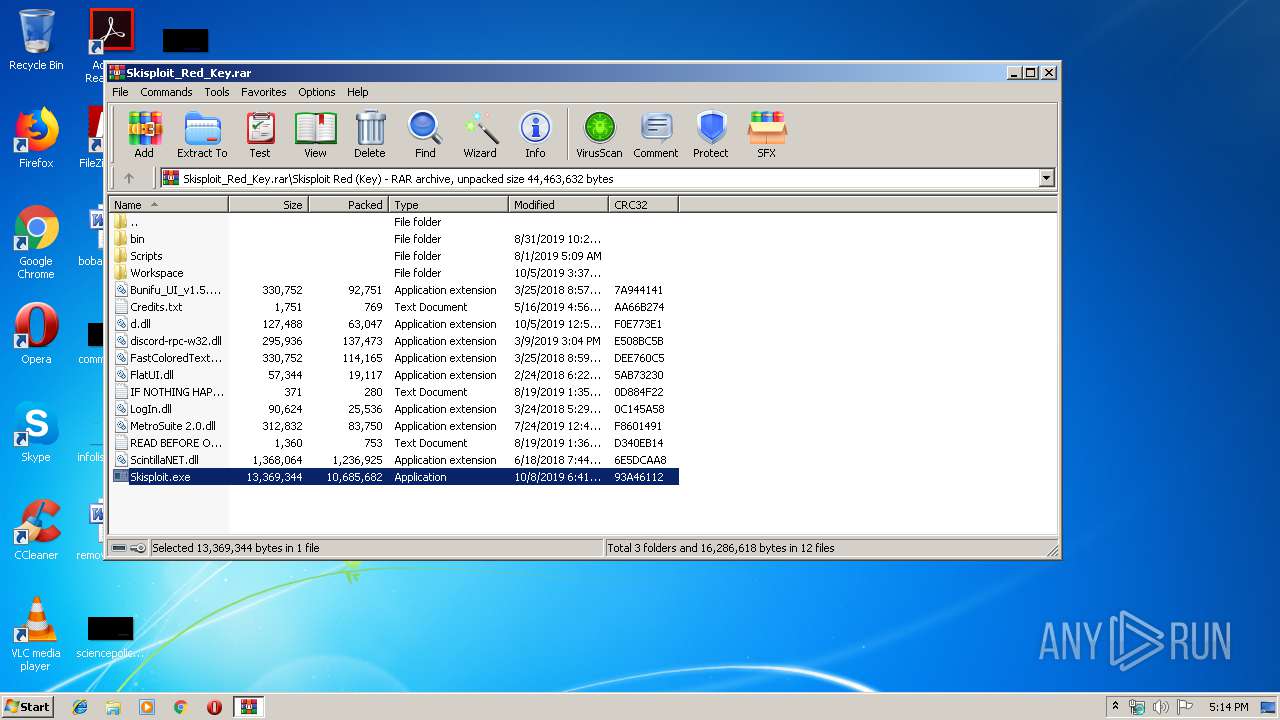
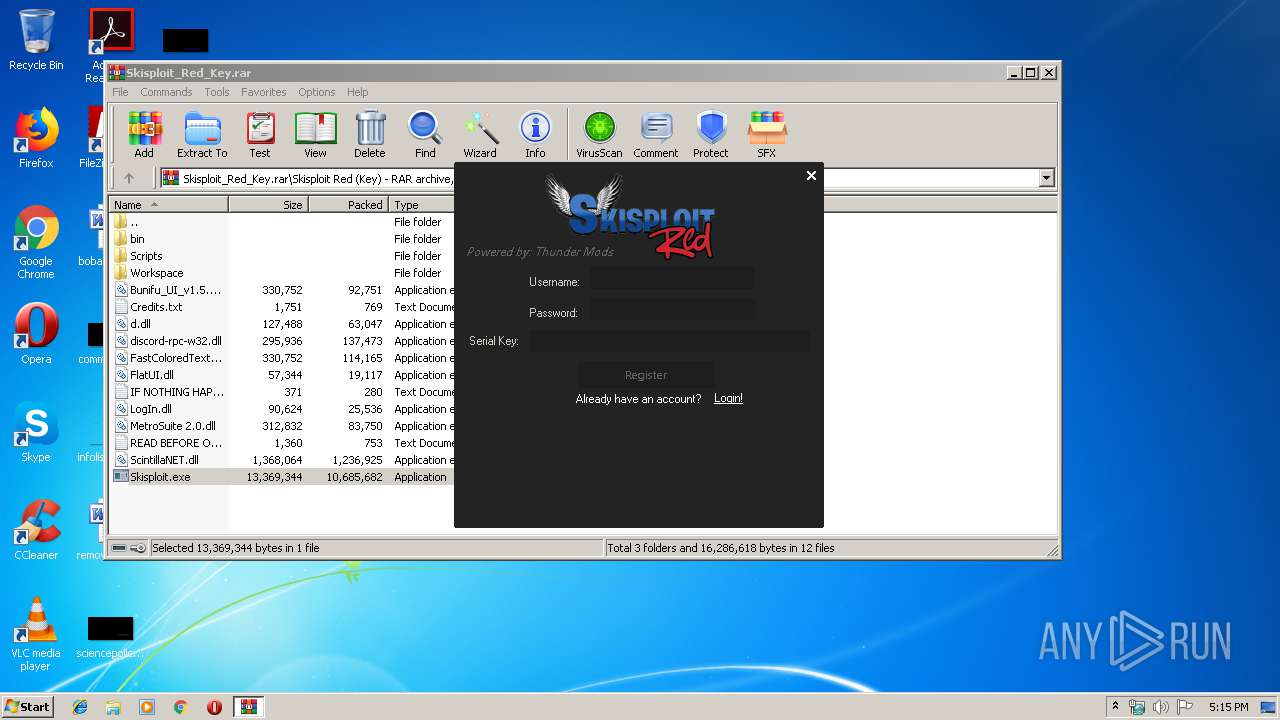
| download: | Skisploit_Red_Key.rar |
| Full analysis: | https://app.any.run/tasks/d25c09aa-e0dc-4c88-9ae9-6db978d868b4 |
| Verdict: | Malicious activity |
| Analysis date: | October 13, 2019, 16:13:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 11DA83CC1E91CC29137240E11D999BE9 |
| SHA1: | A74D3EF83A644B6B15DFB910F3DB1834917CD82E |
| SHA256: | A67BCAD0467390B0552E1F57DBF35FD85EF80298B019F20D37B3778545C86062 |
| SSDEEP: | 393216:JYSBdr4sqcisBwN4BtZQ5z/naGkaNWIqZCJEsqARLqXQYYc+RIGen2rRixvvvPeu:J3ssqtCBtK5zyz1ZCq+RLqXZN52rRixv |
MALICIOUS
Application was dropped or rewritten from another process
- Skisploit.exe (PID: 2240)
- Skisploit.exe (PID: 1884)
Loads dropped or rewritten executable
- Skisploit.exe (PID: 1884)
Changes settings of System certificates
- Skisploit.exe (PID: 1884)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3652)
Adds / modifies Windows certificates
- Skisploit.exe (PID: 1884)
Creates files in the program directory
- Skisploit.exe (PID: 1884)
INFO
Reads settings of System Certificates
- Skisploit.exe (PID: 1884)
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 3652)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
40
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
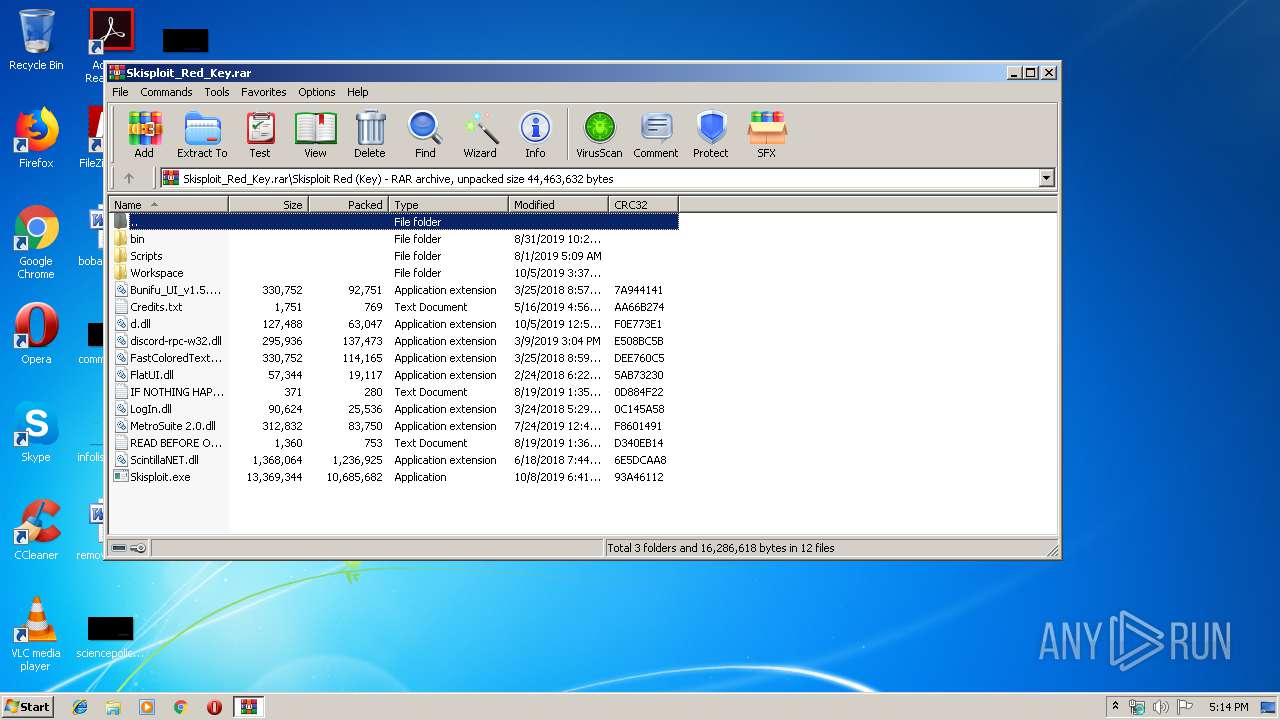
| 1884 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3652.27206\Skisploit Red (Key)\Skisploit.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3652.27206\Skisploit Red (Key)\Skisploit.exe | WinRAR.exe | ||||||||||||
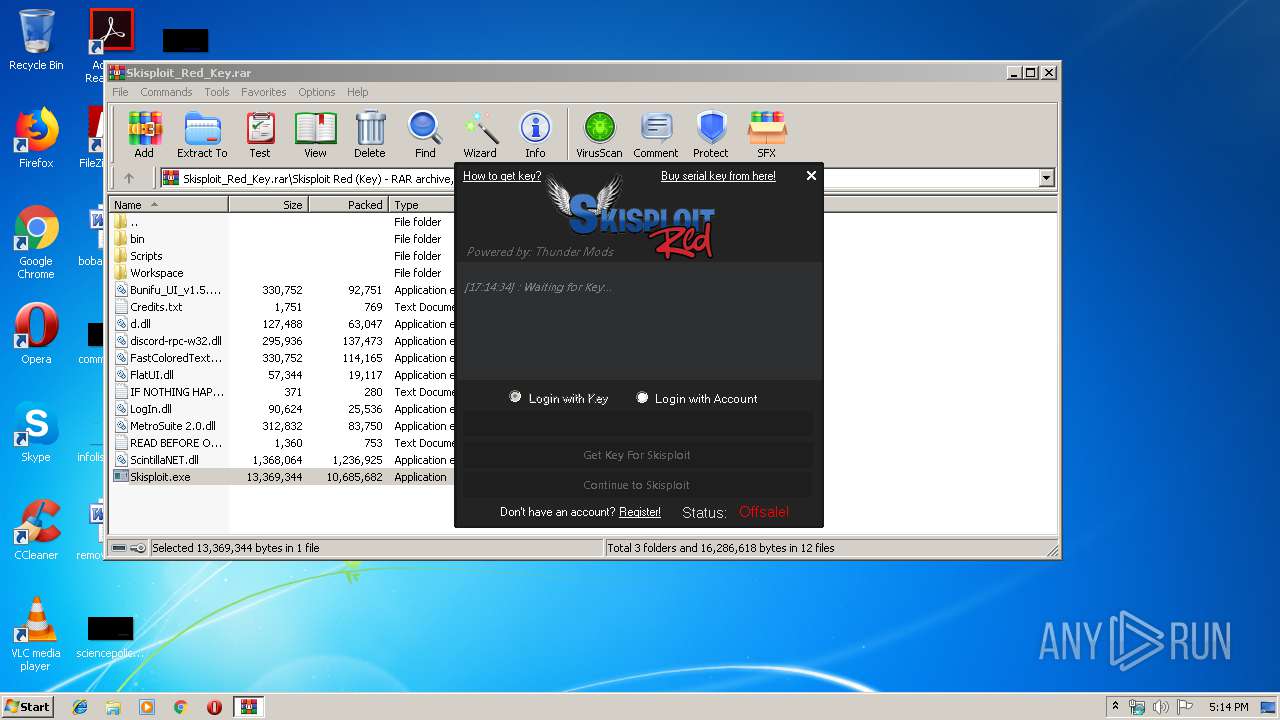
User: admin Integrity Level: HIGH Description: Skisploit Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 2240 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3652.27206\Skisploit Red (Key)\Skisploit.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3652.27206\Skisploit Red (Key)\Skisploit.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Skisploit Exit code: 3221226540 Version: 1.0.0.1 Modules
| |||||||||||||||
| 3652 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Skisploit_Red_Key.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
514
Read events
478
Write events
36
Delete events
0
Modification events
| (PID) Process: | (3652) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3652) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3652) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3652) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Skisploit_Red_Key.rar | |||
| (PID) Process: | (3652) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3652) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3652) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3652) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3652) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3652) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
10
Suspicious files
0
Text files
13
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3652 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3652.27206\Skisploit Red (Key)\bin\sounds\tune.wav | — | |
MD5:— | SHA256:— | |||
| 3652 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3652.27206\Skisploit Red (Key)\Credits.txt | text | |
MD5:A88D150D227510740253F6738A03AC32 | SHA256:69224E05A93FF331A59899E1B096F3760578AD40293BE9EE53F520AD16C1428F | |||
| 3652 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3652.27206\Skisploit Red (Key)\FlatUI.dll | executable | |
MD5:797261F587BB9C6B223B81D31D3B1507 | SHA256:EE5AA955CC297FD7ADBE641EE3A913D08FC0013C239B9710C9C87E10002DB089 | |||
| 3652 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3652.27206\Skisploit Red (Key)\Workspace\IY_FE.iy | text | |
MD5:— | SHA256:— | |||
| 1884 | Skisploit.exe | C:\Program Files (x86)\Skisploit\AutoInject.txt | text | |
MD5:— | SHA256:— | |||
| 1884 | Skisploit.exe | C:\Program Files (x86)\Skisploit\UsernameValue.txt | text | |
MD5:— | SHA256:— | |||
| 1884 | Skisploit.exe | C:\Program Files (x86)\Skisploit\UsernameCheck.txt | text | |
MD5:— | SHA256:— | |||
| 1884 | Skisploit.exe | C:\Program Files (x86)\Skisploit\AntiAFK.txt | text | |
MD5:— | SHA256:— | |||
| 1884 | Skisploit.exe | C:\Program Files (x86)\Skisploit\PasswordValue.txt | text | |
MD5:— | SHA256:— | |||
| 3652 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3652.27206\Skisploit Red (Key)\LogIn.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
4
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
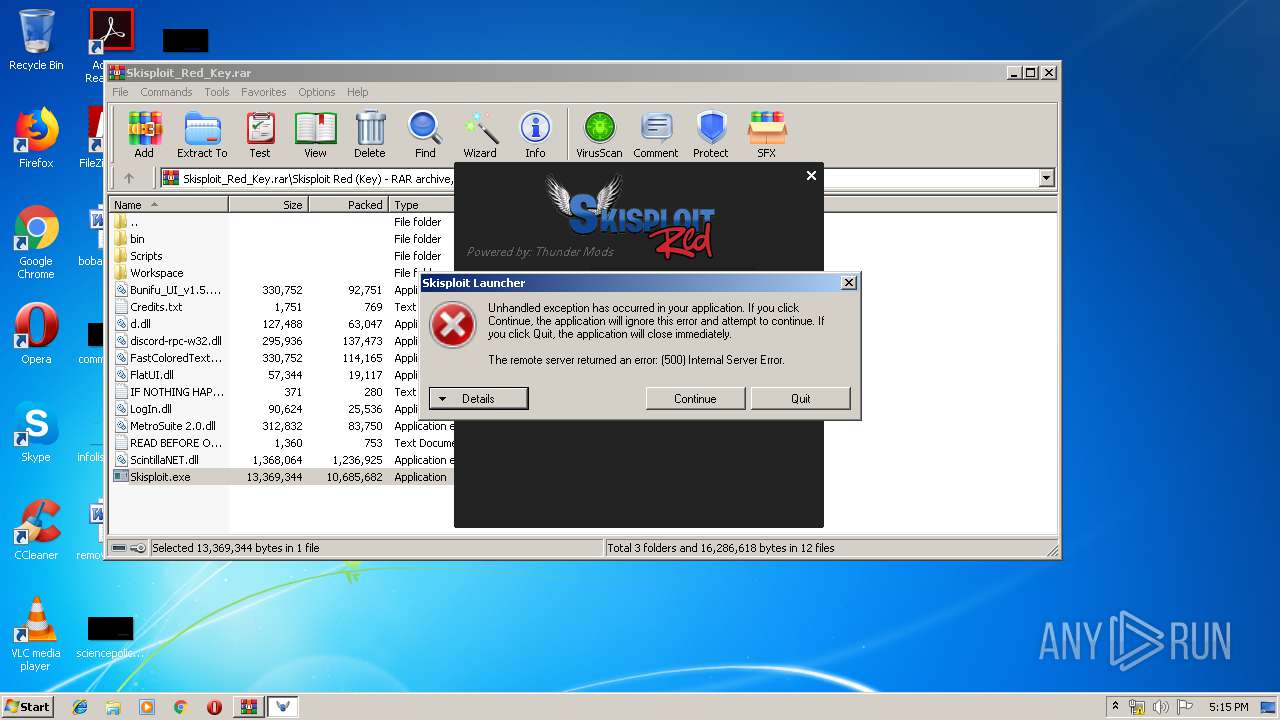
1884 | Skisploit.exe | GET | 200 | 76.74.235.180:80 | http://api.thundermods.com/invite.txt | CA | text | 26 b | malicious |
1884 | Skisploit.exe | GET | 200 | 76.74.235.180:80 | http://api.thundermods.com/onsale.txt | CA | text | 14 b | malicious |
1884 | Skisploit.exe | GET | 200 | 76.74.235.180:80 | http://api.thundermods.com/version.txt | CA | text | 7 b | malicious |
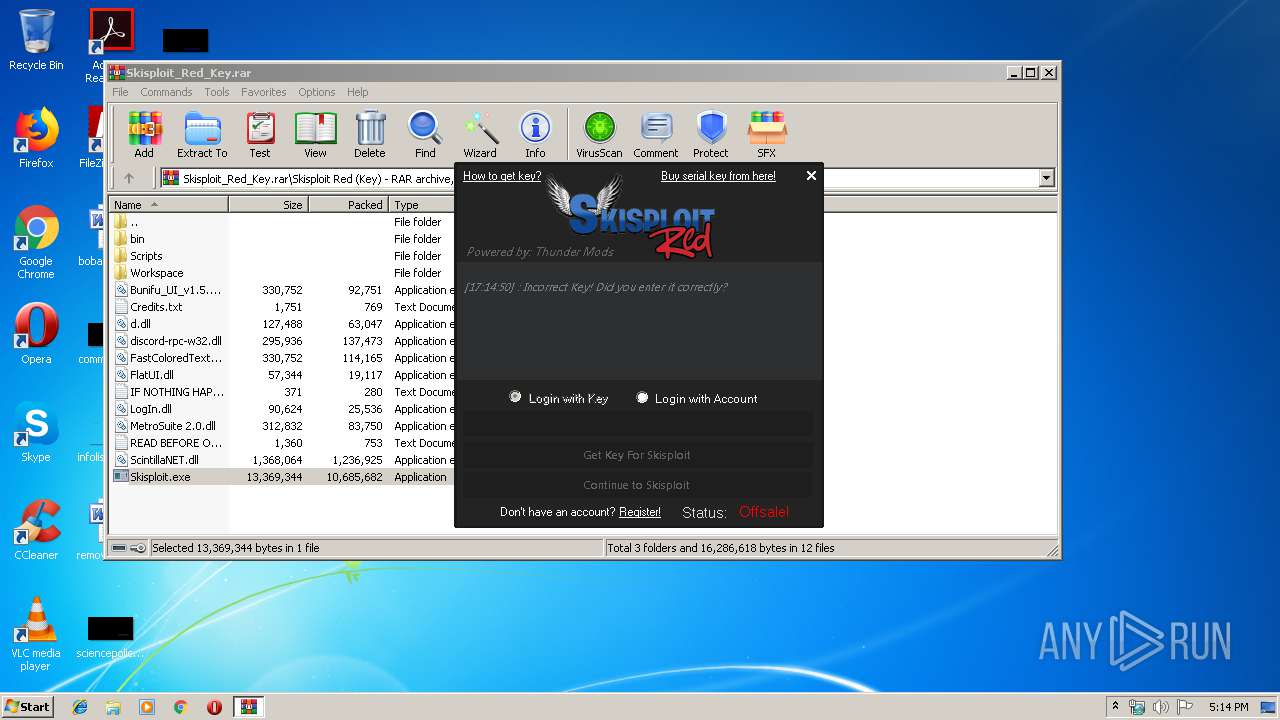
1884 | Skisploit.exe | GET | 500 | 76.74.235.180:80 | http://api.thundermods.com/skisploit/KJbhksdDSsdS.php?action=register&username=fasf&password=E6425994236DDD01A8ED24852D5F0EC19E70D701&hwid=1F8BFBFF000506E3&serialKey=fasfsffsa | CA | text | 7 b | malicious |
1884 | Skisploit.exe | GET | 200 | 76.74.235.180:80 | http://api.thundermods.com/version.txt | CA | text | 7 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1884 | Skisploit.exe | 76.74.235.180:80 | api.thundermods.com | Peer 1 Network (USA) Inc. | CA | unknown |
1884 | Skisploit.exe | 76.74.235.180:443 | api.thundermods.com | Peer 1 Network (USA) Inc. | CA | unknown |
1884 | Skisploit.exe | 104.22.3.84:443 | pastebin.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.thundermods.com |
| malicious |
pastebin.com |
| malicious |
thundermodsalt.website |
| unknown |