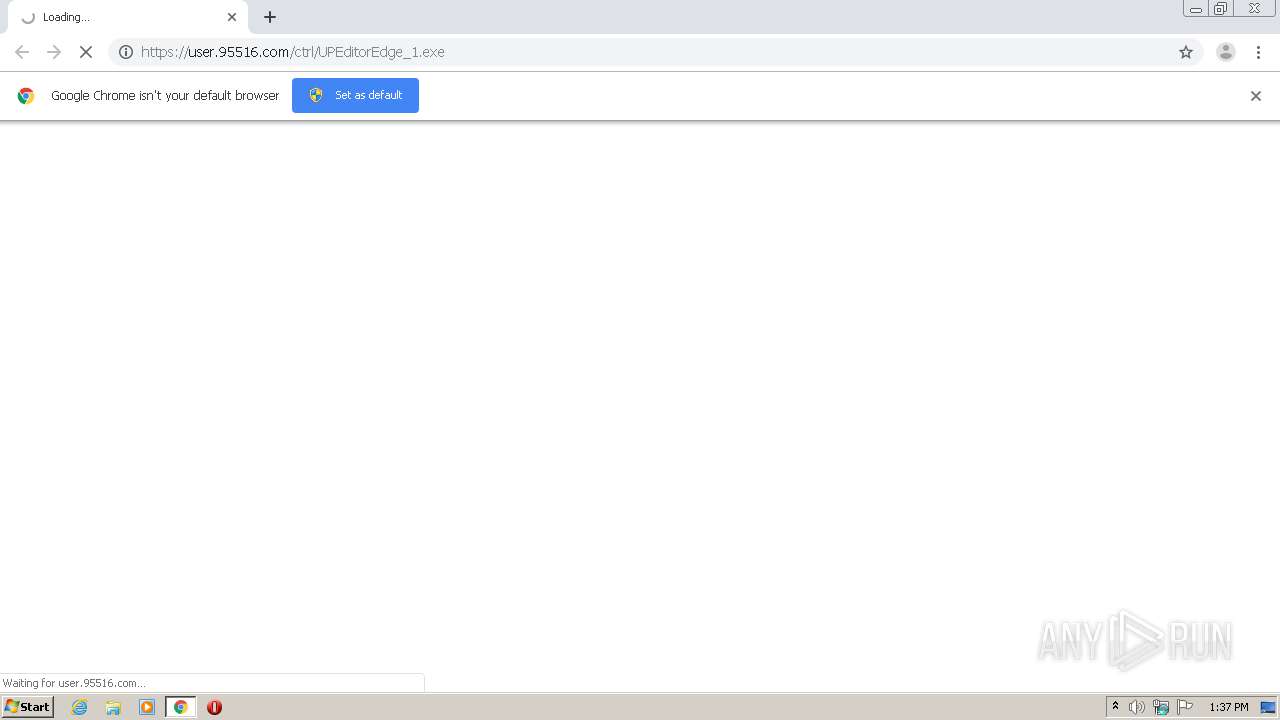
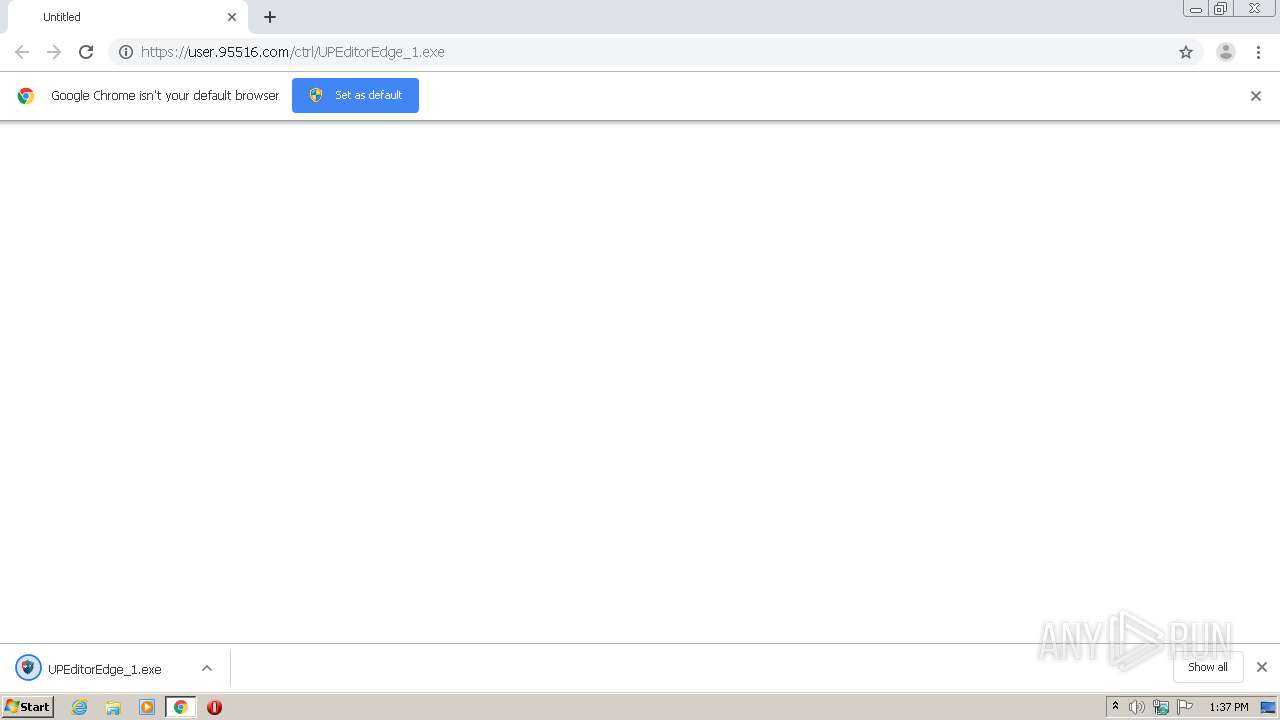
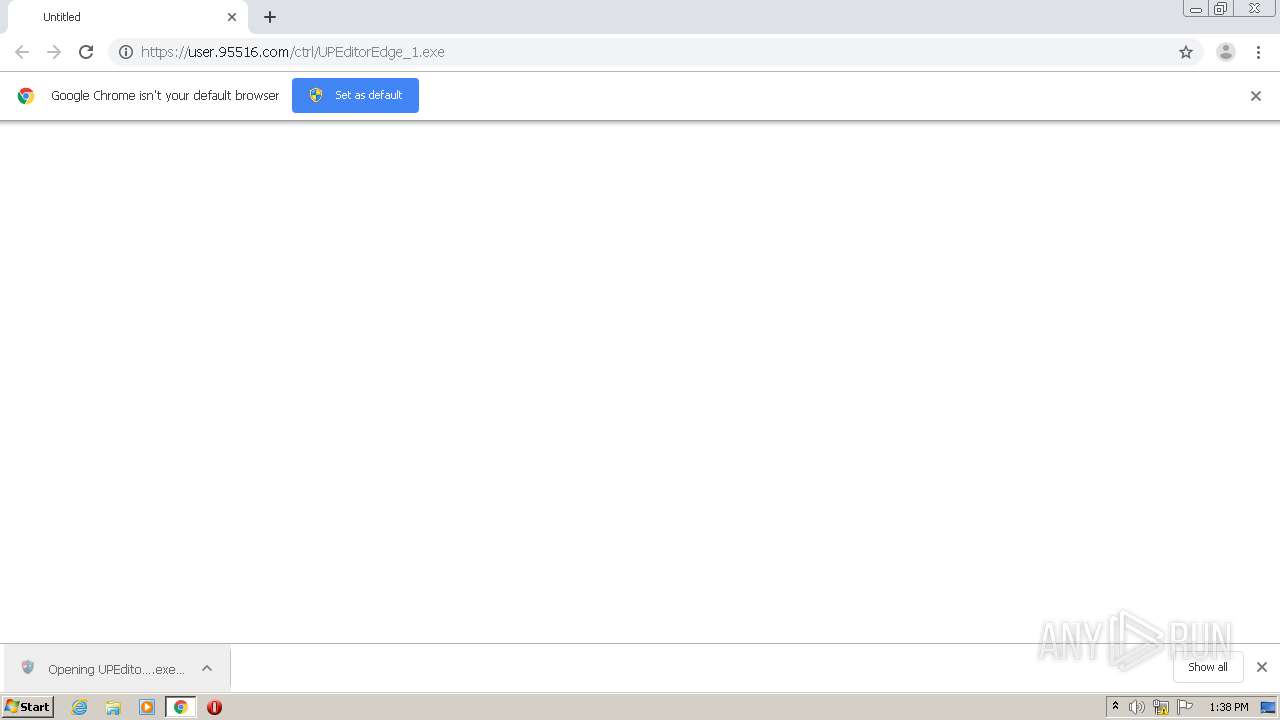
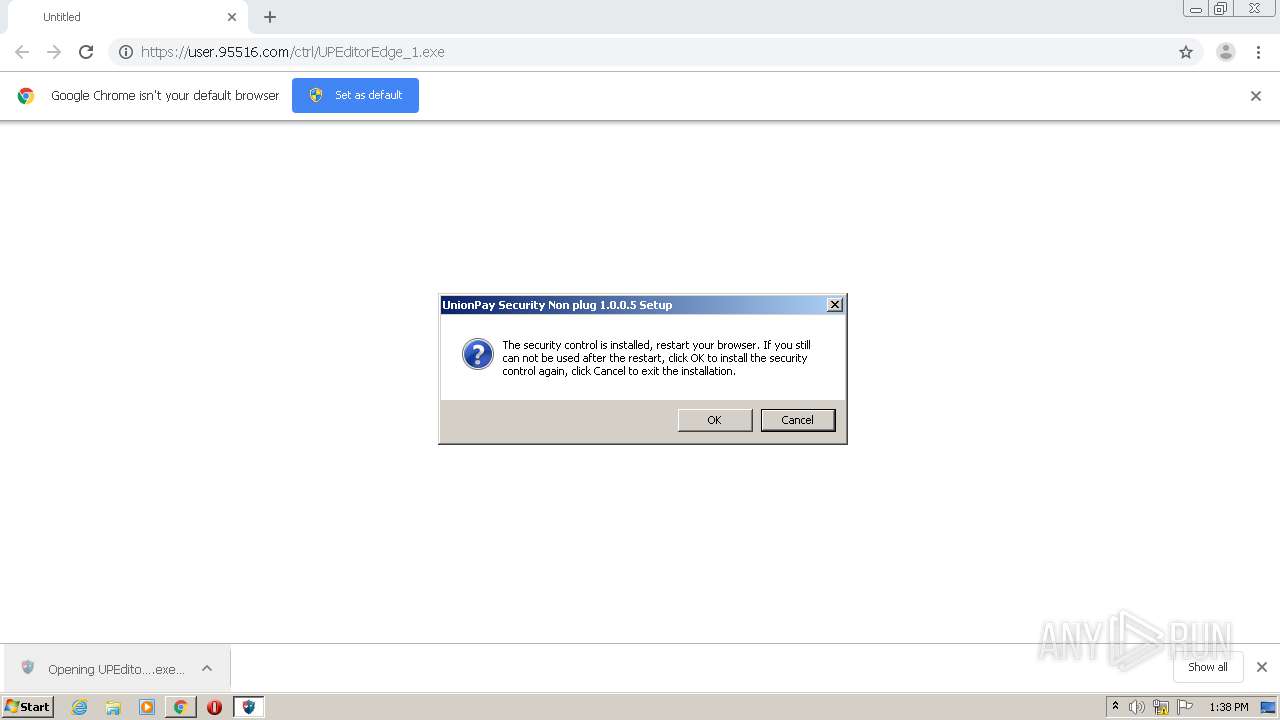
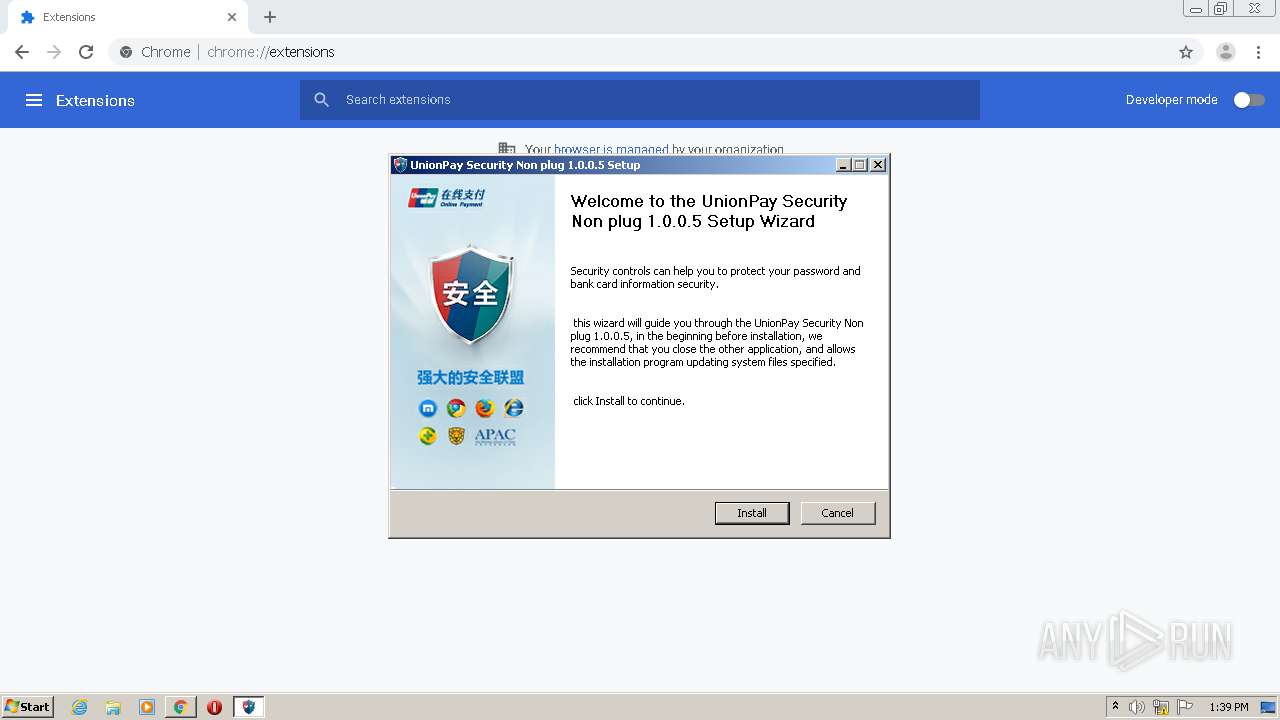
| URL: | https://user.95516.com/ctrl/UPEditorEdge_1.exe |
| Full analysis: | https://app.any.run/tasks/ca69dce4-59c8-4f3e-a295-e6667c1fb354 |
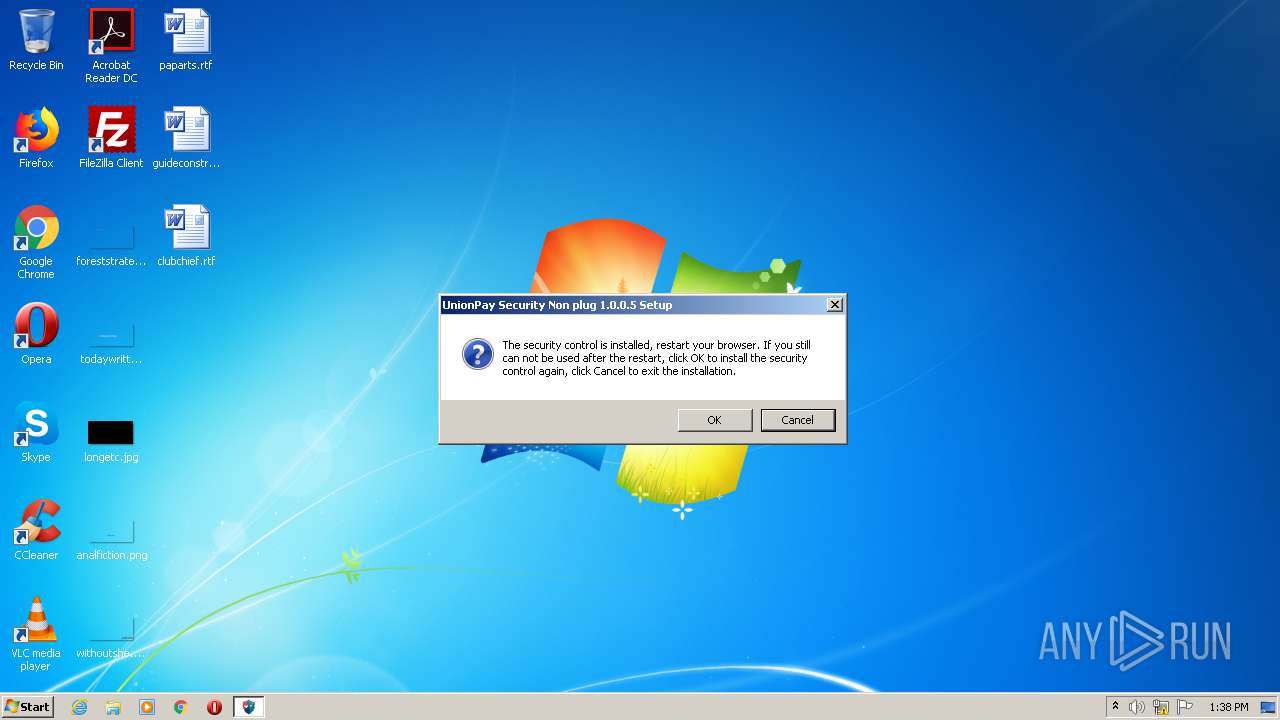
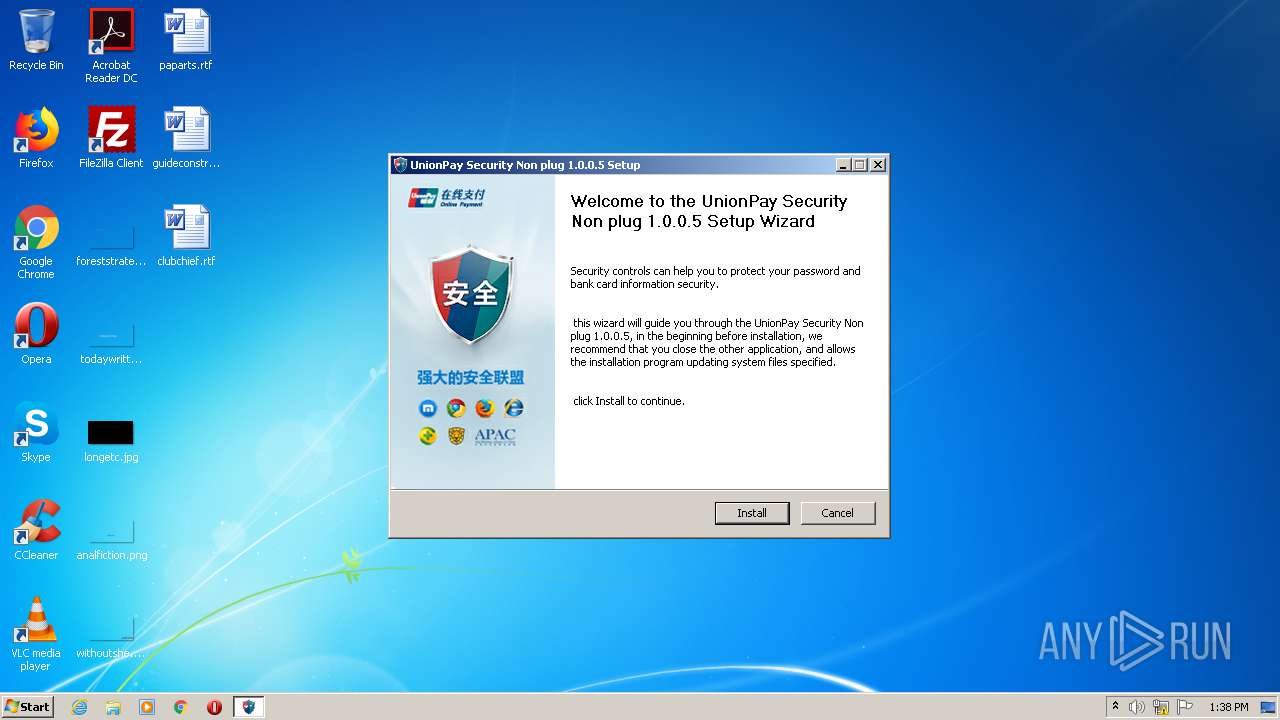
| Verdict: | Malicious activity |
| Analysis date: | April 07, 2021, 12:36:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 6093E7CC4E25BC30DBC414A71F4B50B1 |
| SHA1: | D3E60968A01028C9FBC62A778D52E03728622213 |
| SHA256: | A676909A67C97C6EE77DD115E4E208DA4CDC018BA35E03EDA959A537C2F9BB04 |
| SSDEEP: | 3:N8mPLG3XJVh0u:2h3Xh0u |
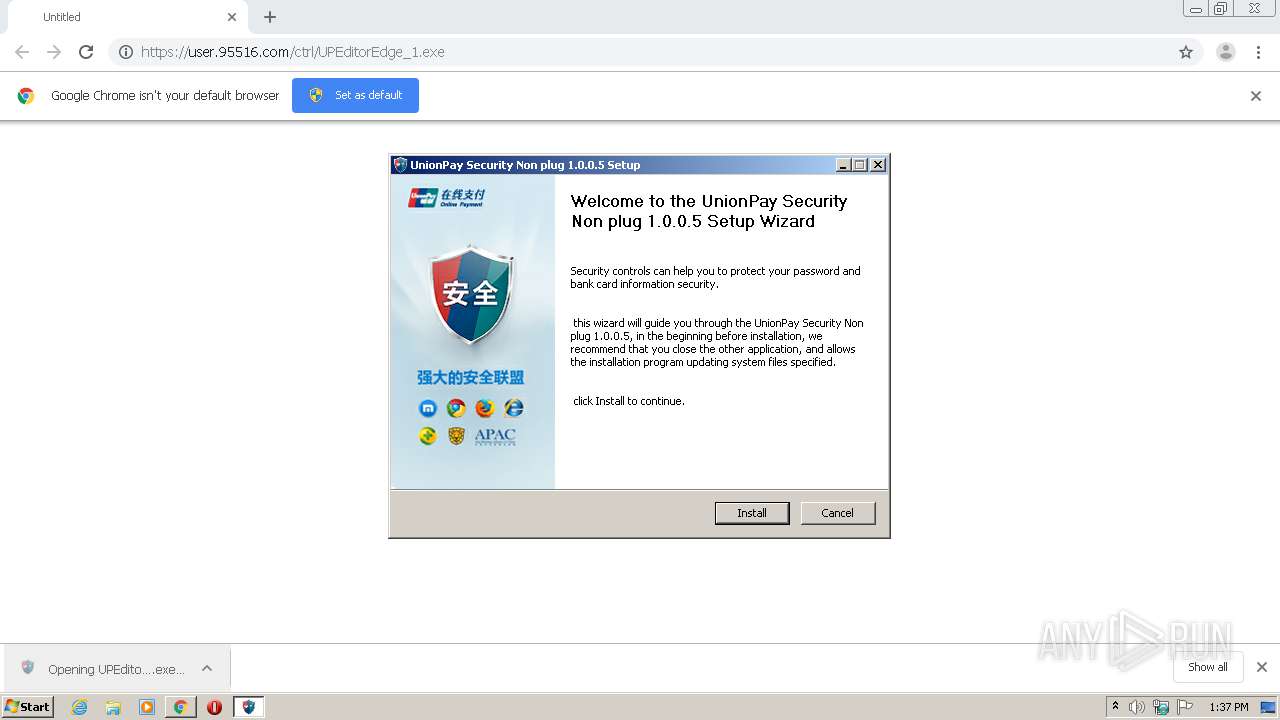
MALICIOUS
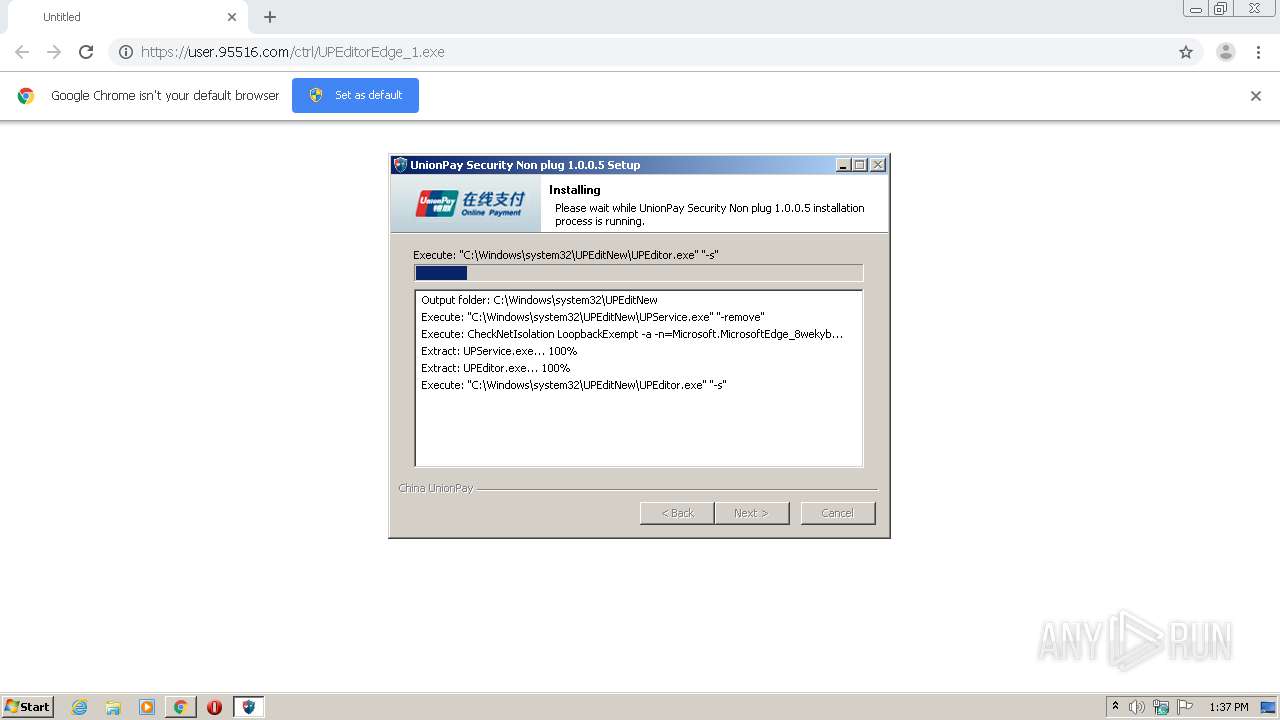
Application was dropped or rewritten from another process
- UPEditorEdge_1.exe (PID: 2880)
- UPEditorEdge_1.exe (PID: 3356)
- UPEditor.exe (PID: 4000)
- UPService.exe (PID: 2228)
- UPService.exe (PID: 3124)
- UPService.exe (PID: 2620)
- UPSecurityInput.exe (PID: 2608)
- certmgr.exe (PID: 2868)
- certmgr.exe (PID: 2504)
- UPEditorEdge_1 (1).exe (PID: 2692)
- UPEditorEdge_1 (1).exe (PID: 4036)
- UPService.exe (PID: 3812)
- UPService.exe (PID: 2304)
- UPService.exe (PID: 2876)
- UPEditor.exe (PID: 2560)
- UPSecurityInput.exe (PID: 988)
- UPService.exe (PID: 816)
- certmgr.exe (PID: 928)
- certmgr.exe (PID: 3820)
Loads dropped or rewritten executable
- UPEditorEdge_1.exe (PID: 2880)
- UPEditorEdge_1 (1).exe (PID: 4036)
Drops executable file immediately after starts
- UPEditor.exe (PID: 4000)
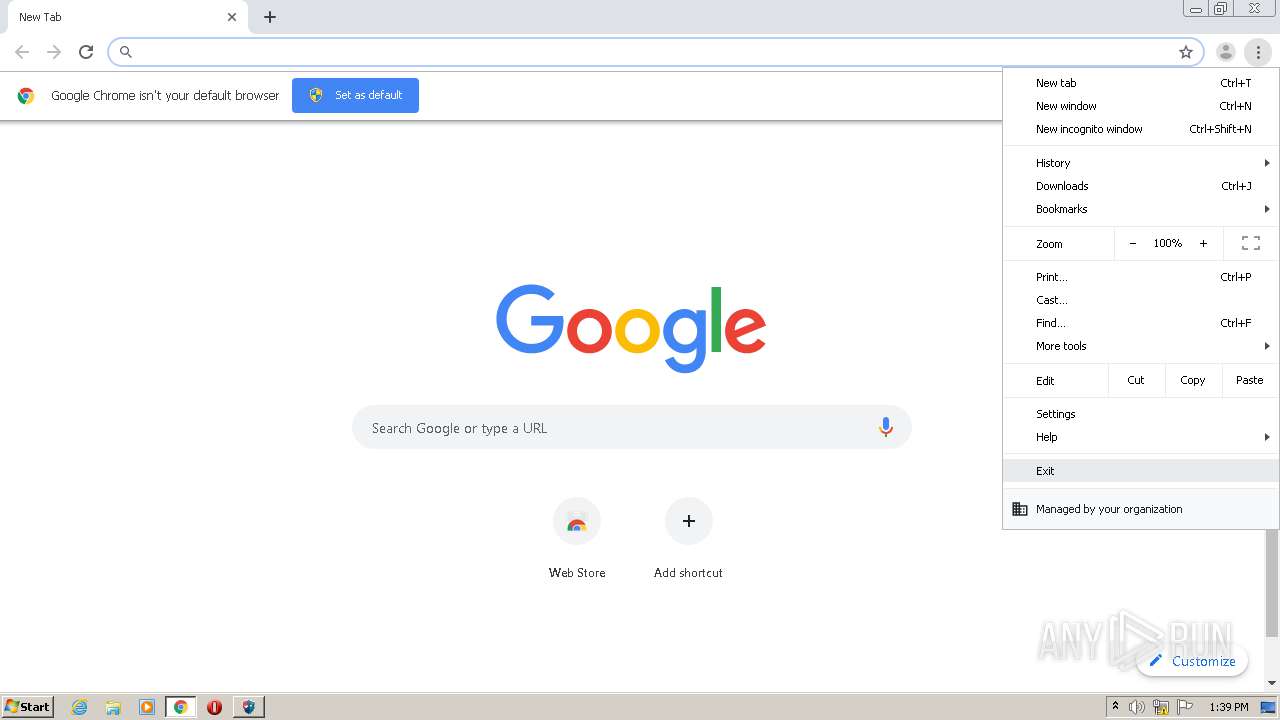
Uses Task Scheduler to autorun other applications
- UPSecurityInput.exe (PID: 2608)
- UPSecurityInput.exe (PID: 988)
Uses Task Scheduler to run other applications
- UPSecurityInput.exe (PID: 2608)
- UPSecurityInput.exe (PID: 988)
Writes to the hosts file
- UPService.exe (PID: 2620)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3932)
- schtasks.exe (PID: 3276)
- schtasks.exe (PID: 2712)
- schtasks.exe (PID: 3112)
Changes settings of System certificates
- certmgr.exe (PID: 2868)
- certmgr.exe (PID: 2504)
- certmgr.exe (PID: 928)
- certmgr.exe (PID: 3820)
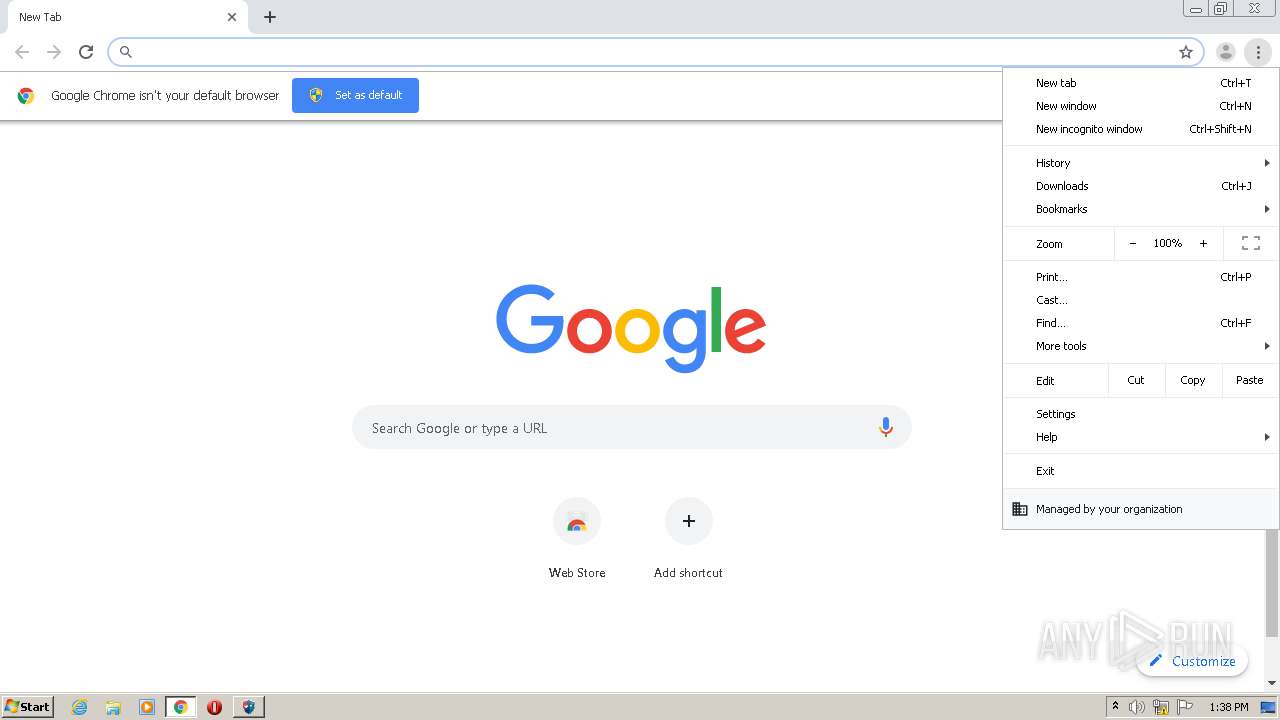
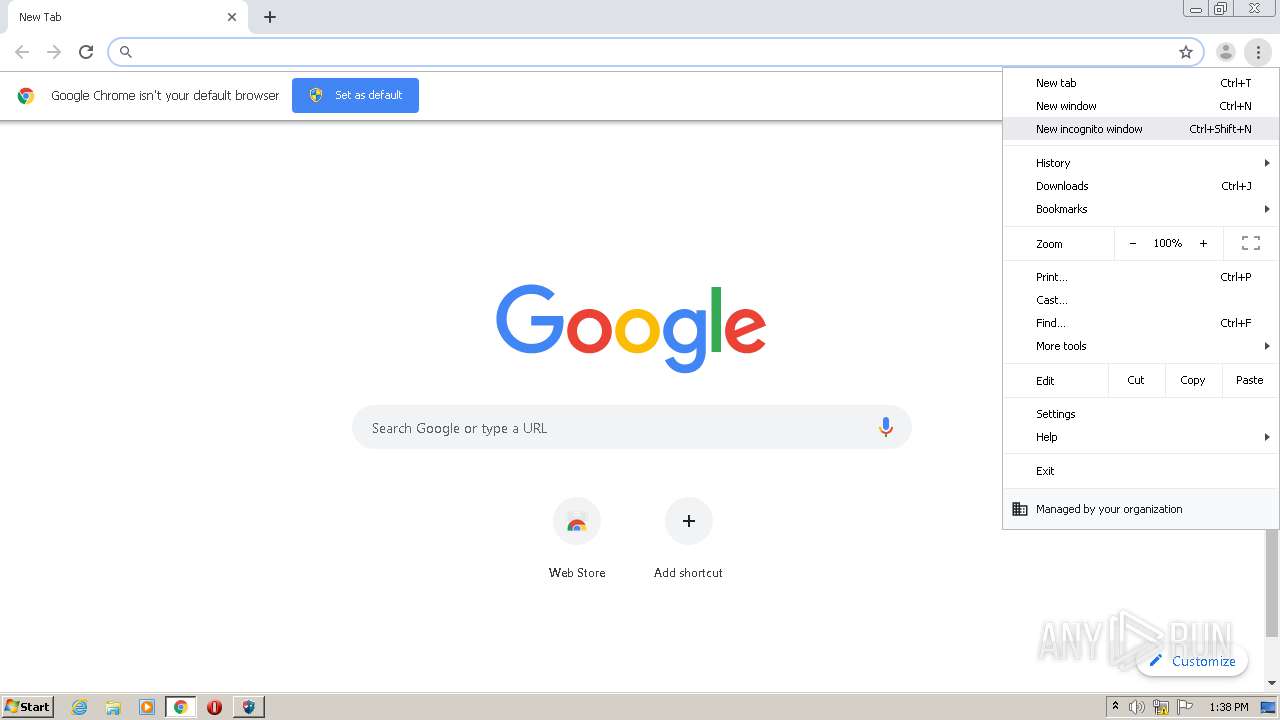
Steals credentials from Web Browsers
- UPSecurityInput.exe (PID: 988)
Actions looks like stealing of personal data
- UPSecurityInput.exe (PID: 988)
SUSPICIOUS
Executable content was dropped or overwritten
- UPEditorEdge_1.exe (PID: 2880)
- chrome.exe (PID: 2808)
- UPEditor.exe (PID: 4000)
- UPEditorEdge_1 (1).exe (PID: 4036)
- UPEditor.exe (PID: 2560)
Drops a file with too old compile date
- UPEditorEdge_1.exe (PID: 2880)
- UPEditorEdge_1 (1).exe (PID: 4036)
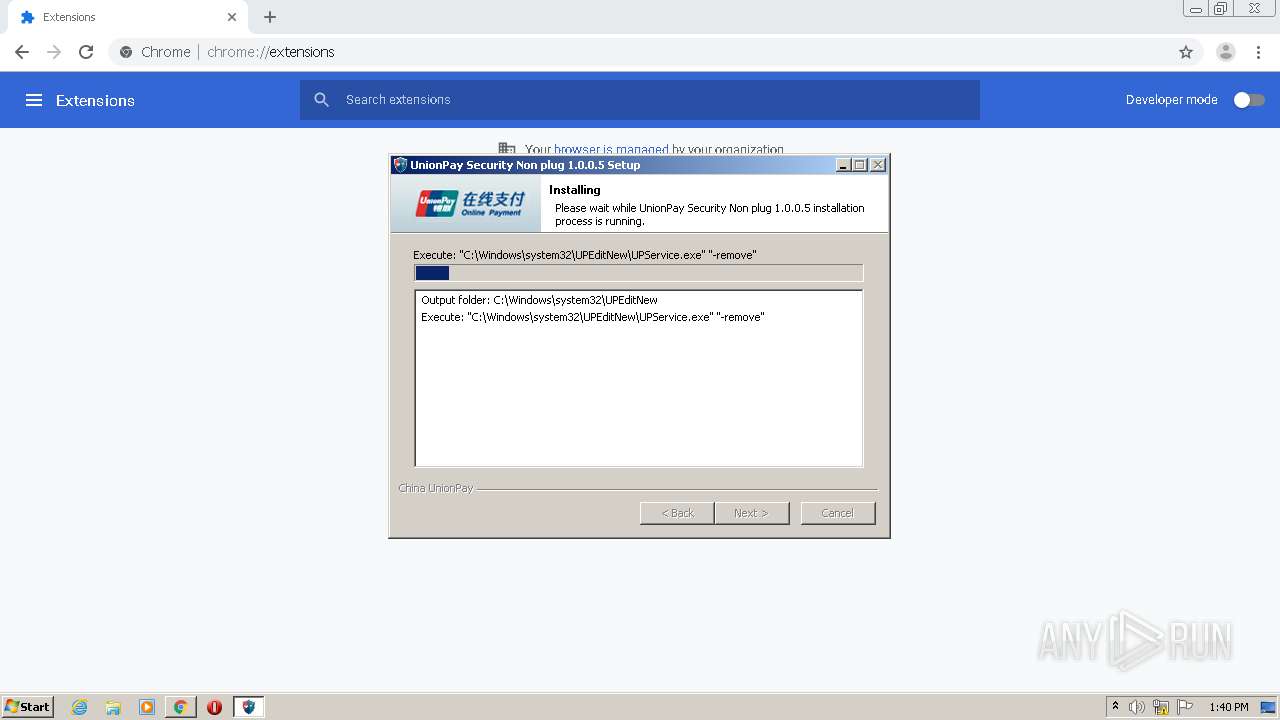
Creates files in the Windows directory
- UPEditorEdge_1.exe (PID: 2880)
- UPEditor.exe (PID: 4000)
Executed as Windows Service
- UPService.exe (PID: 2620)
- UPService.exe (PID: 3812)
Creates files in the driver directory
- UPEditor.exe (PID: 4000)
Drops a file that was compiled in debug mode
- UPEditorEdge_1.exe (PID: 2880)
- UPEditor.exe (PID: 4000)
- UPEditorEdge_1 (1).exe (PID: 4036)
- UPEditor.exe (PID: 2560)
Creates files in the user directory
- UPSecurityInput.exe (PID: 2608)
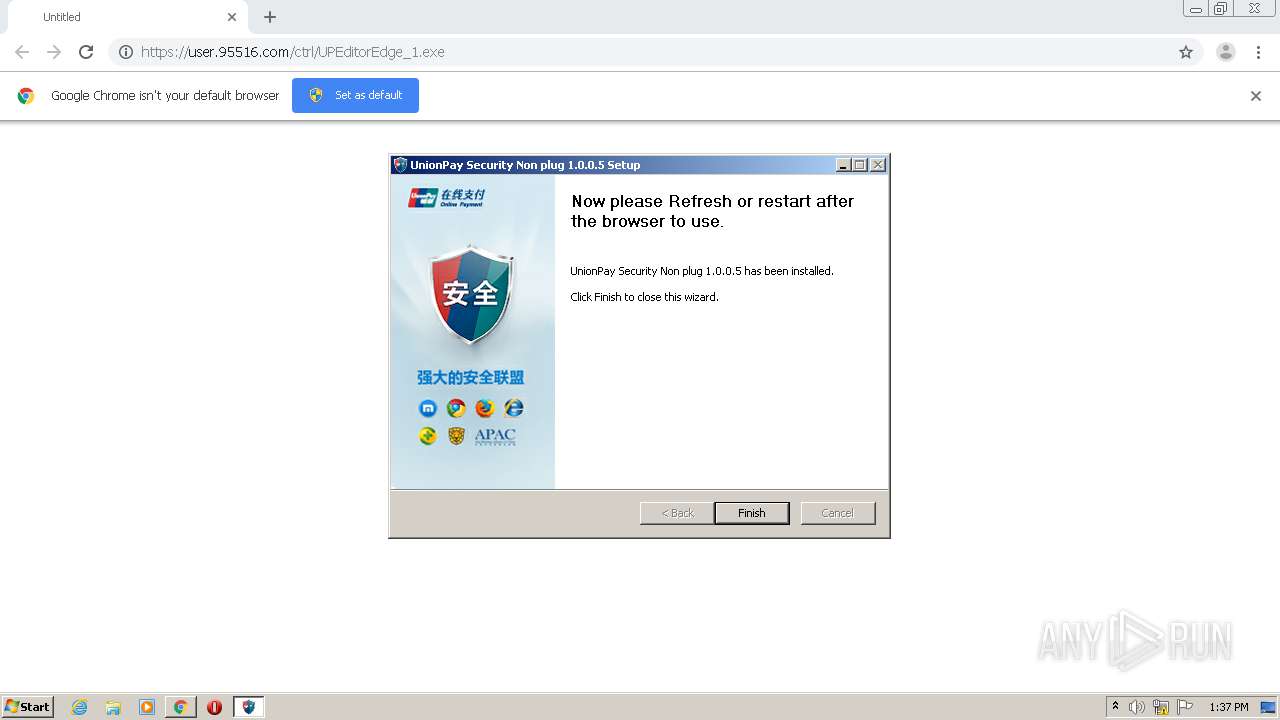
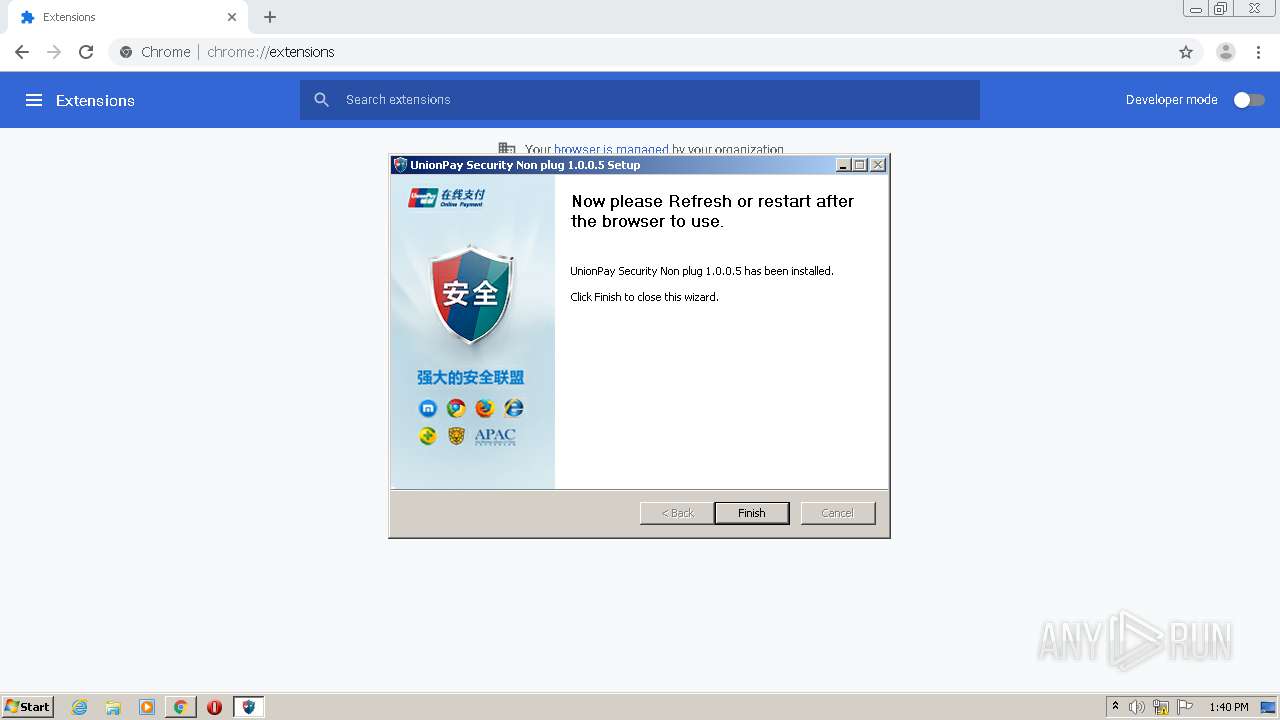
Creates a software uninstall entry
- UPEditorEdge_1.exe (PID: 2880)
- UPEditorEdge_1 (1).exe (PID: 4036)
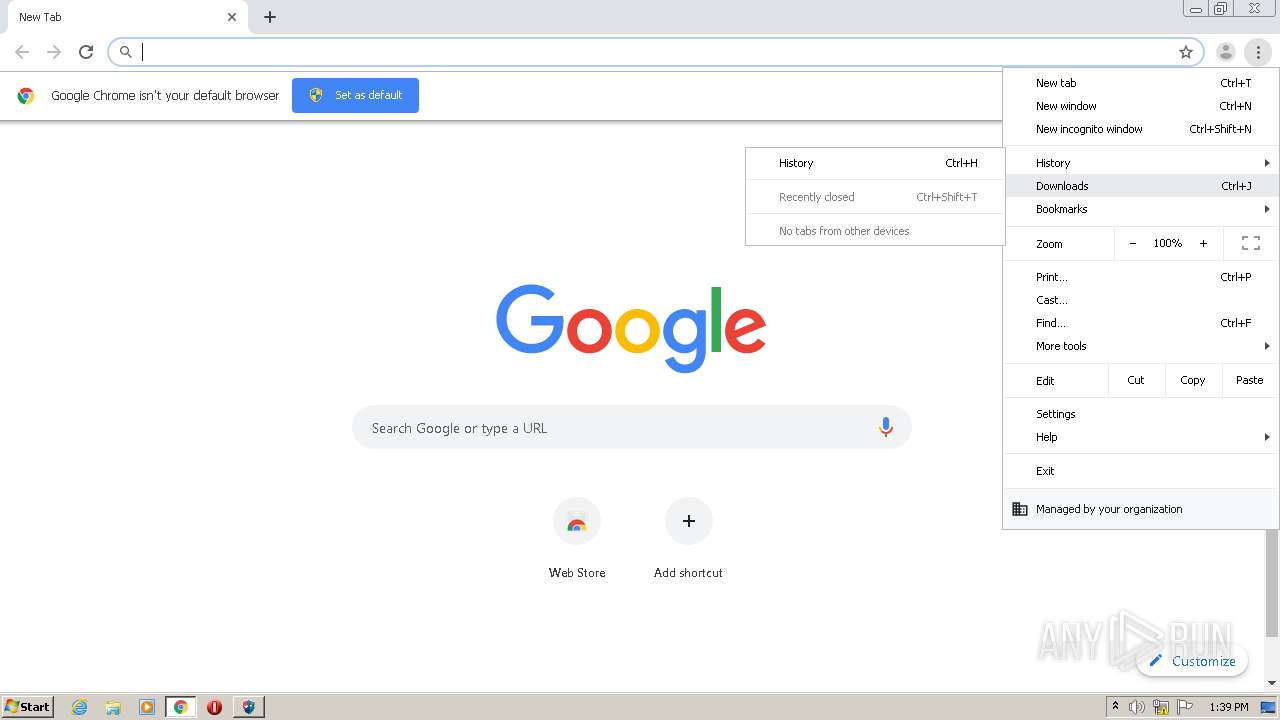
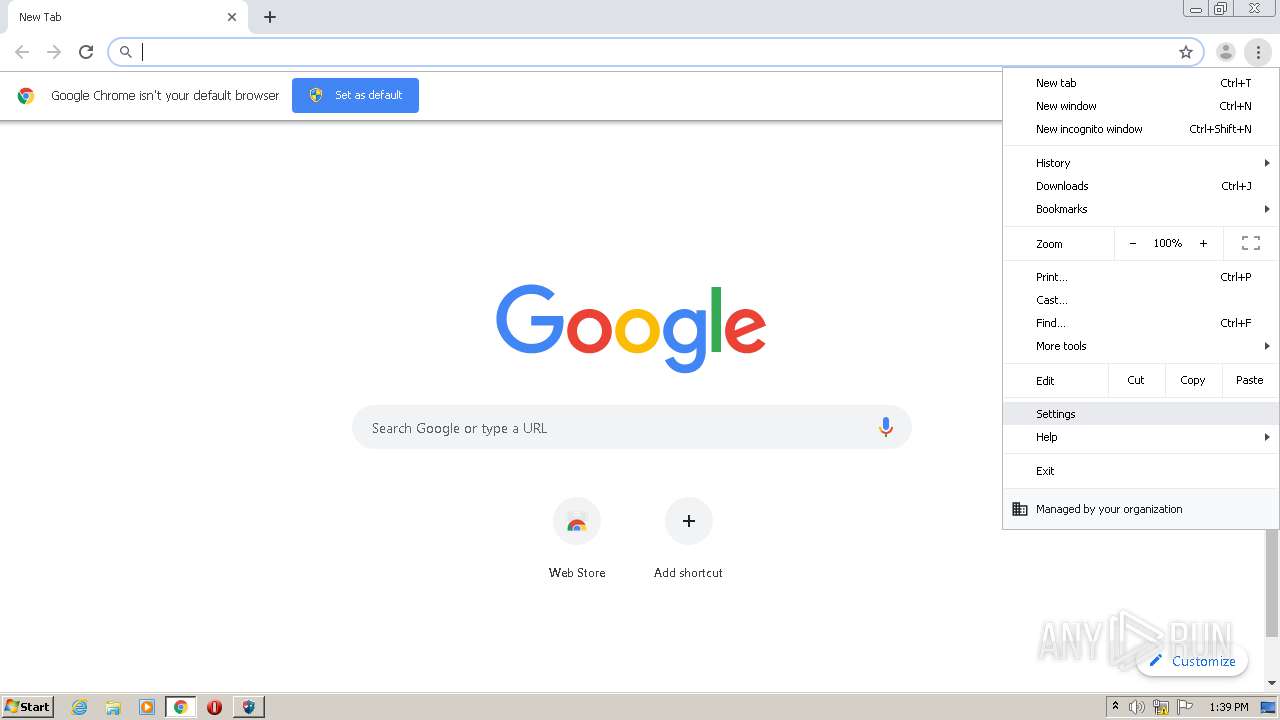
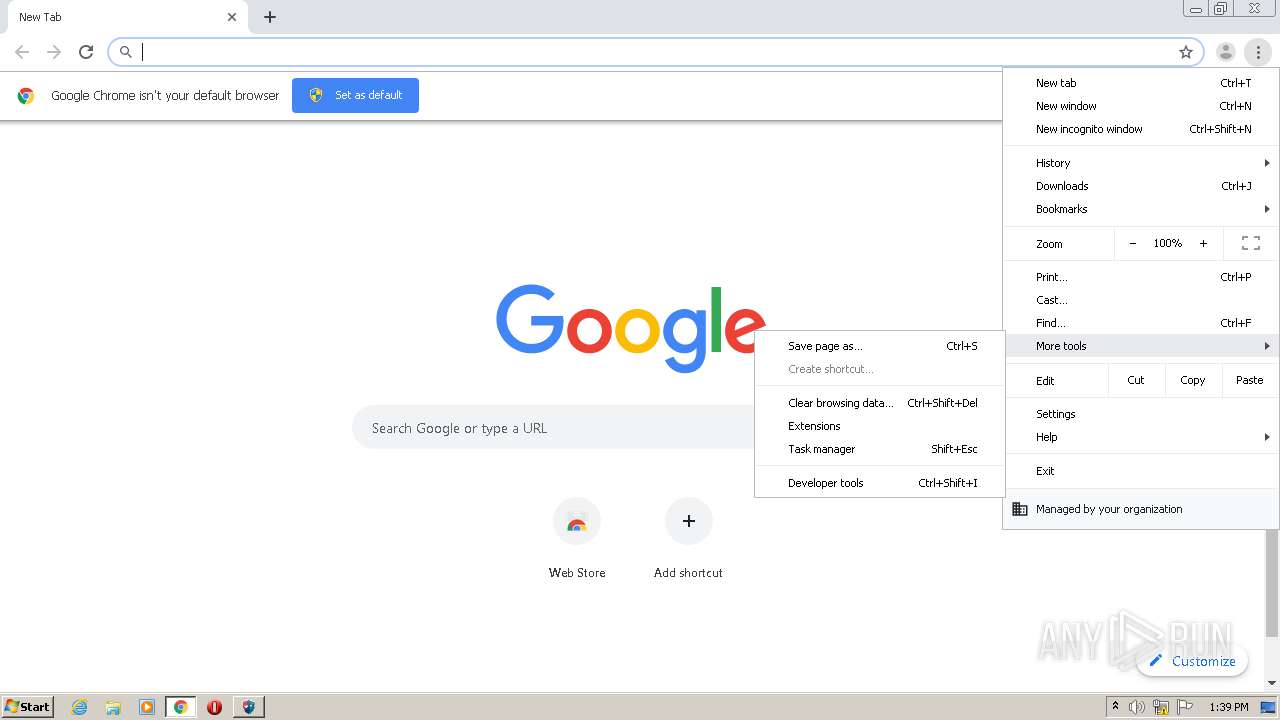
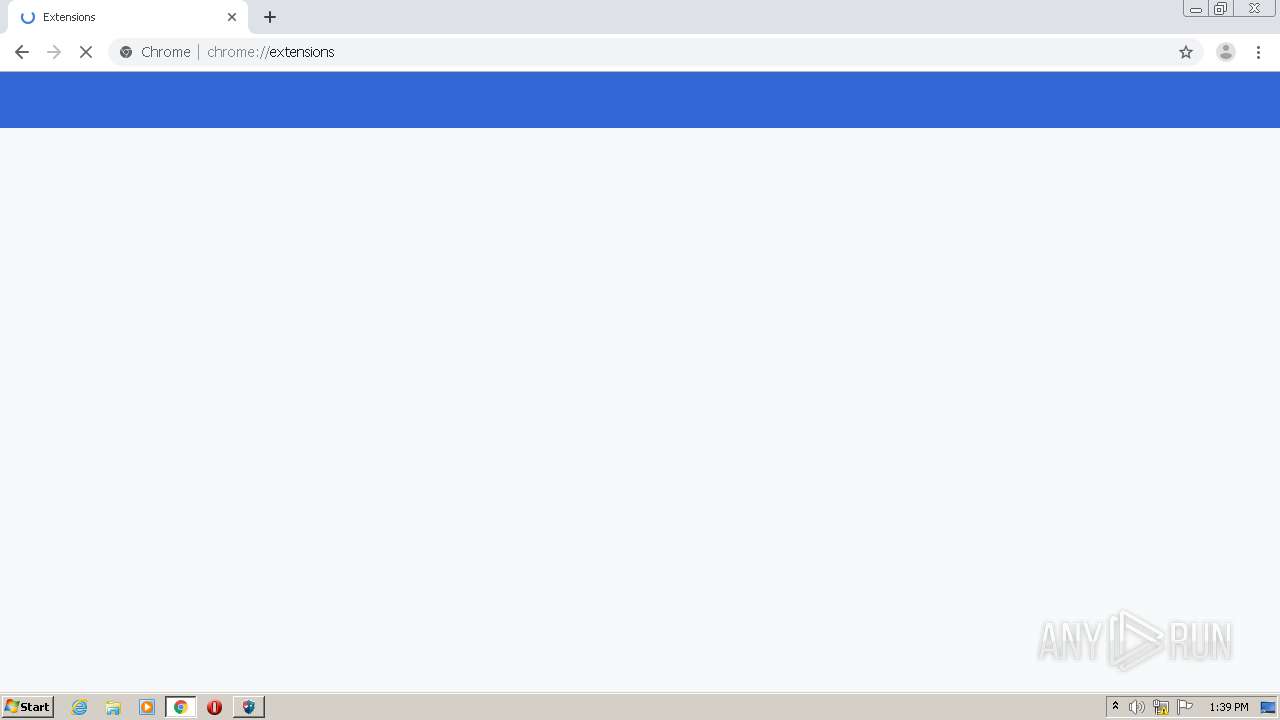
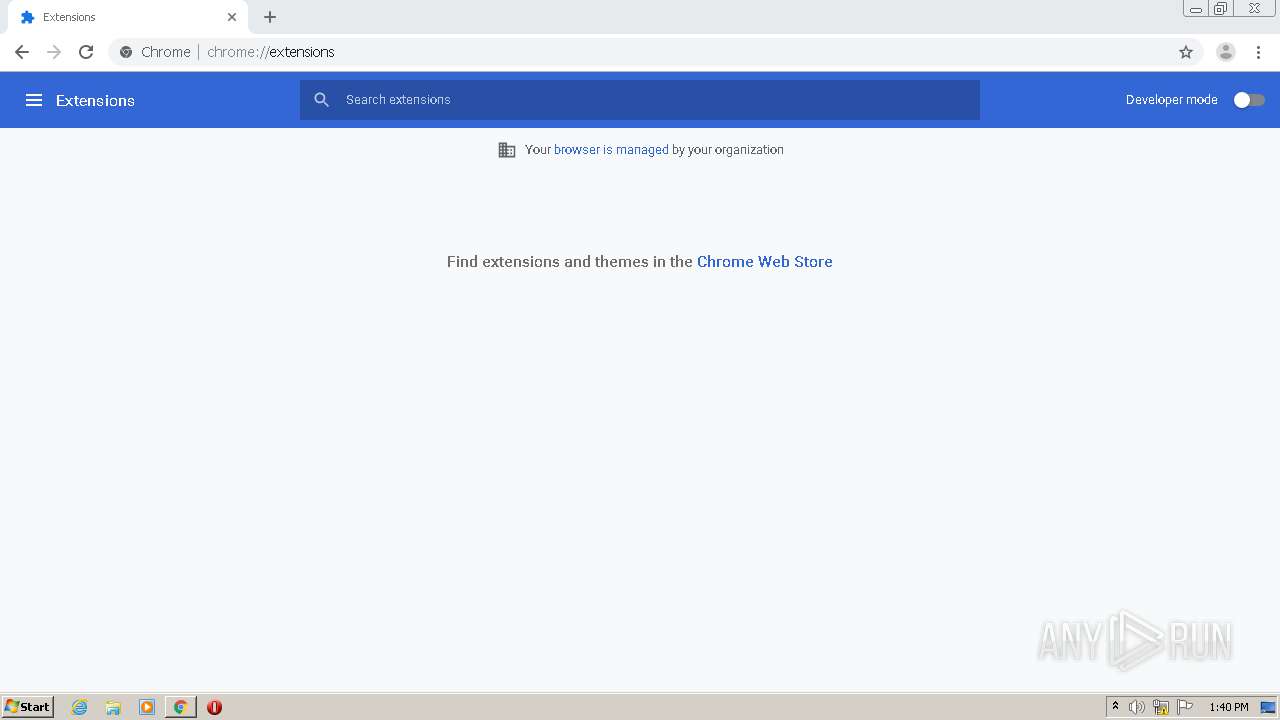
Modifies files in Chrome extension folder
- chrome.exe (PID: 3092)
INFO
Reads the hosts file
- chrome.exe (PID: 2808)
- chrome.exe (PID: 3008)
- UPService.exe (PID: 2620)
- chrome.exe (PID: 3092)
- chrome.exe (PID: 1524)
- UPService.exe (PID: 3812)
Application launched itself
- chrome.exe (PID: 2808)
- chrome.exe (PID: 3092)
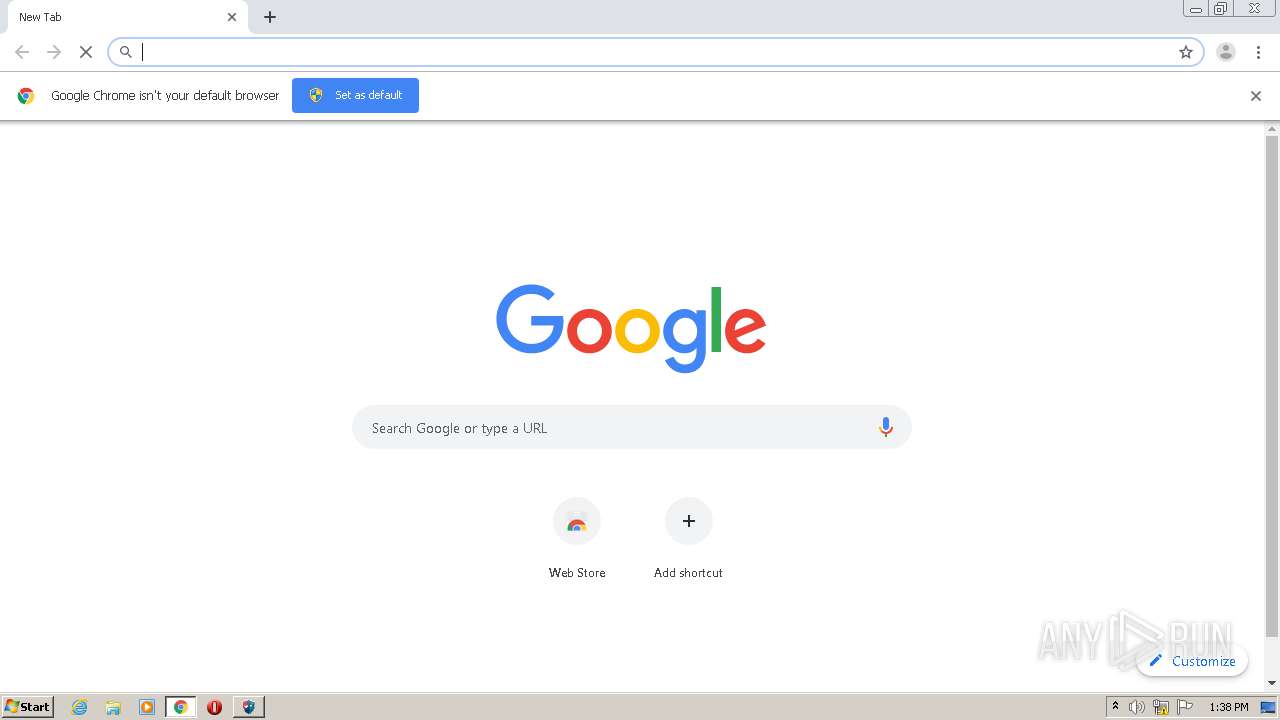
Manual execution by user
- chrome.exe (PID: 3092)
Reads settings of System Certificates
- chrome.exe (PID: 1524)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
122
Monitored processes
68
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,1308114908540679166,7343746504578661254,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8874211620417629019 --mojo-platform-channel-handle=3652 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 792 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,1308114908540679166,7343746504578661254,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9099382173485738036 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2504 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 816 | "C:\Windows\system32\UPEditNew\UPService.exe" "-control" "UPSecurityInputService" "start" | C:\Windows\system32\UPEditNew\UPService.exe | — | UPEditorEdge_1 (1).exe | |||||||||||
User: admin Company: 中国银联股份有限公司 Integrity Level: HIGH Description: UPSecurityInputService Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3364 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 928 | "C:\Users\admin\AppData\Local\Temp\certmgr.exe" -add "C:\Users\admin\AppData\Local\Temp\wosign.cer" -c -s -r localMachine Root | C:\Users\admin\AppData\Local\Temp\certmgr.exe | — | UPEditorEdge_1 (1).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ECM Certificate Manager Exit code: 0 Version: 6.2.9200.16384 (win8_rtm.120725-1247) Modules
| |||||||||||||||
| 960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1004,1308114908540679166,7343746504578661254,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=4966445854892826317 --mojo-platform-channel-handle=3972 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 988 | C:\Windows\system32\UPEditNew\UPSecurityInput.exe | C:\Windows\system32\UPEditNew\UPSecurityInput.exe | UPEditorEdge_1 (1).exe | ||||||||||||
User: admin Company: 中国银联股份有限公司 Integrity Level: HIGH Description: UPSecurityInput Exit code: 0 Version: 1.0.0.5 Modules
| |||||||||||||||
| 1220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,1308114908540679166,7343746504578661254,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15615519937769592720 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2952 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,1308114908540679166,7343746504578661254,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6244234195167620385 --mojo-platform-channel-handle=3436 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1472 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,1308114908540679166,7343746504578661254,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13710577198827244071 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3504 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 597
Read events
2 416
Write events
171
Delete events
10
Modification events
| (PID) Process: | (2808) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2808) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2808) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2808) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2808) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3280) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2808-13262272622257875 |
Value: 259 | |||
| (PID) Process: | (2808) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2808) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2808) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2808) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
28
Suspicious files
59
Text files
401
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-606DA76F-AF8.pma | — | |
MD5:— | SHA256:— | |||
| 2808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF14f0c7.TMP | — | |
MD5:— | SHA256:— | |||
| 2808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d4fad3ee-45be-444c-a64c-3b1719808c03.tmp | — | |
MD5:— | SHA256:— | |||
| 2808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF14f079.TMP | text | |
MD5:— | SHA256:— | |||
| 2808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF14f088.TMP | text | |
MD5:— | SHA256:— | |||
| 2808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF14f396.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
32
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1524 | chrome.exe | GET | 302 | 216.58.212.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 518 b | whitelisted |
1524 | chrome.exe | GET | 200 | 173.194.151.121:80 | http://r3---sn-4g5edn7y.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=e_&mip=157.97.122.7&mm=28&mn=sn-4g5edn7y&ms=nvh&mt=1617798979&mv=m&mvi=3&pl=24&shardbypass=yes | US | crx | 242 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3008 | chrome.exe | 142.250.186.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
3008 | chrome.exe | 42.81.144.148:443 | user.95516.com | Yueyang | CN | unknown |
3008 | chrome.exe | 142.250.185.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3008 | chrome.exe | 142.250.185.142:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
3008 | chrome.exe | 142.250.185.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
1524 | chrome.exe | 142.250.185.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1524 | chrome.exe | 142.250.185.205:443 | accounts.google.com | Google Inc. | US | suspicious |
1524 | chrome.exe | 142.250.185.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
1524 | chrome.exe | 142.250.186.110:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
1524 | chrome.exe | 142.250.185.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
user.95516.com |
| unknown |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
clients1.google.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
Process | Message |
|---|---|
UPEditor.exe | Ö÷°æ±¾ = 6 |
UPEditor.exe | ¸±°æ±¾ = 1 |
UPEditor.exe | buildnumber = 7601 |
UPEditor.exe | Ö÷°æ±¾ = 6 |
UPEditor.exe | ¸±°æ±¾ = 1 |
UPEditor.exe | buildnumber = 7601 |