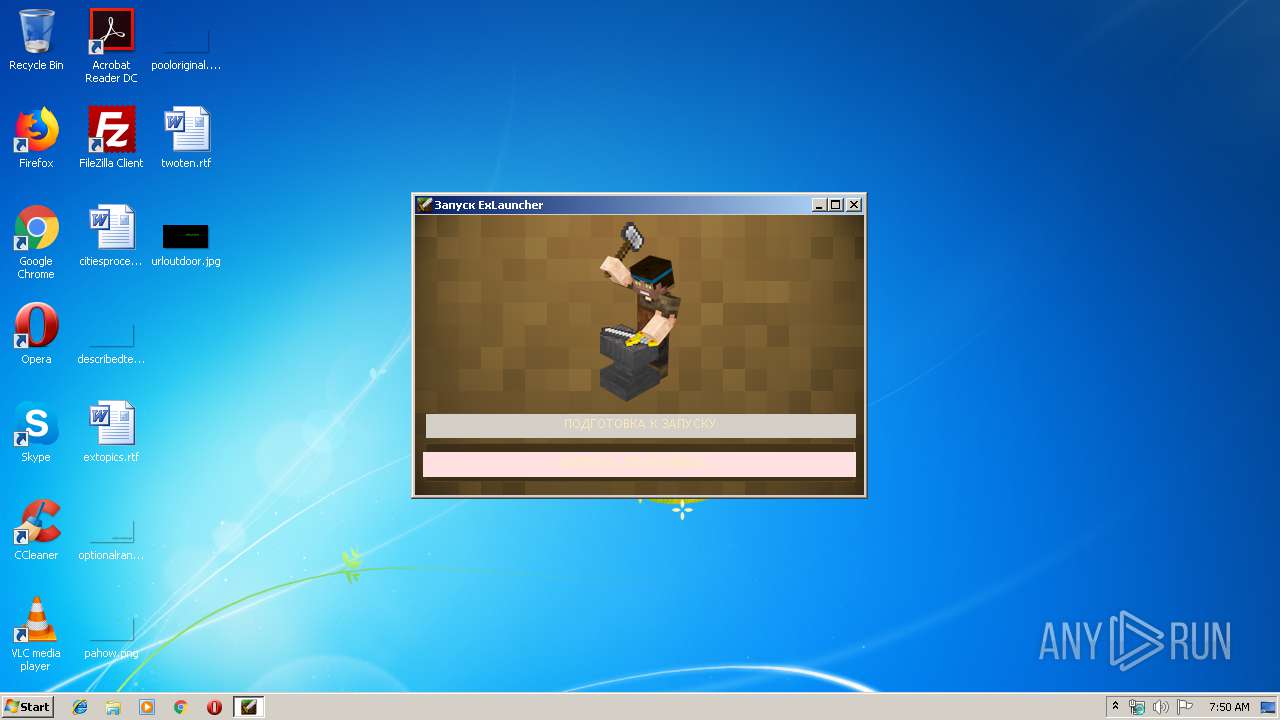
| File name: | Excalibur-Launcher4.1.exe |
| Full analysis: | https://app.any.run/tasks/fc87aff7-eafc-417e-8aab-6958dcc8080e |
| Verdict: | Malicious activity |
| Analysis date: | August 23, 2019, 06:50:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 078E800293AD8C1758928476DAC9F10C |
| SHA1: | 19D821F393D8C162C6008795BD308E1CFAFBF367 |
| SHA256: | A660BE07E704BCD19452B8813D1308C5A3F96D904ECE04DB37D37A568862B806 |
| SSDEEP: | 49152:VxJgqHSL0S6Pzfobj0VMBlLZ48nEgTOAWsJcqwL2Q2S:VTHDP4K+hnE3qM2Q2 |
MALICIOUS
Application was dropped or rewritten from another process
- javaw.exe (PID: 3584)
Loads dropped or rewritten executable
- javaw.exe (PID: 3584)
- Excalibur-Launcher4.1.exe (PID: 3768)
SUSPICIOUS
Creates files in the program directory
- javaw.exe (PID: 3584)
Uses IPCONFIG.EXE to discover IP address
- javaw.exe (PID: 3584)
Uses ICACLS.EXE to modify access control list
- javaw.exe (PID: 3584)
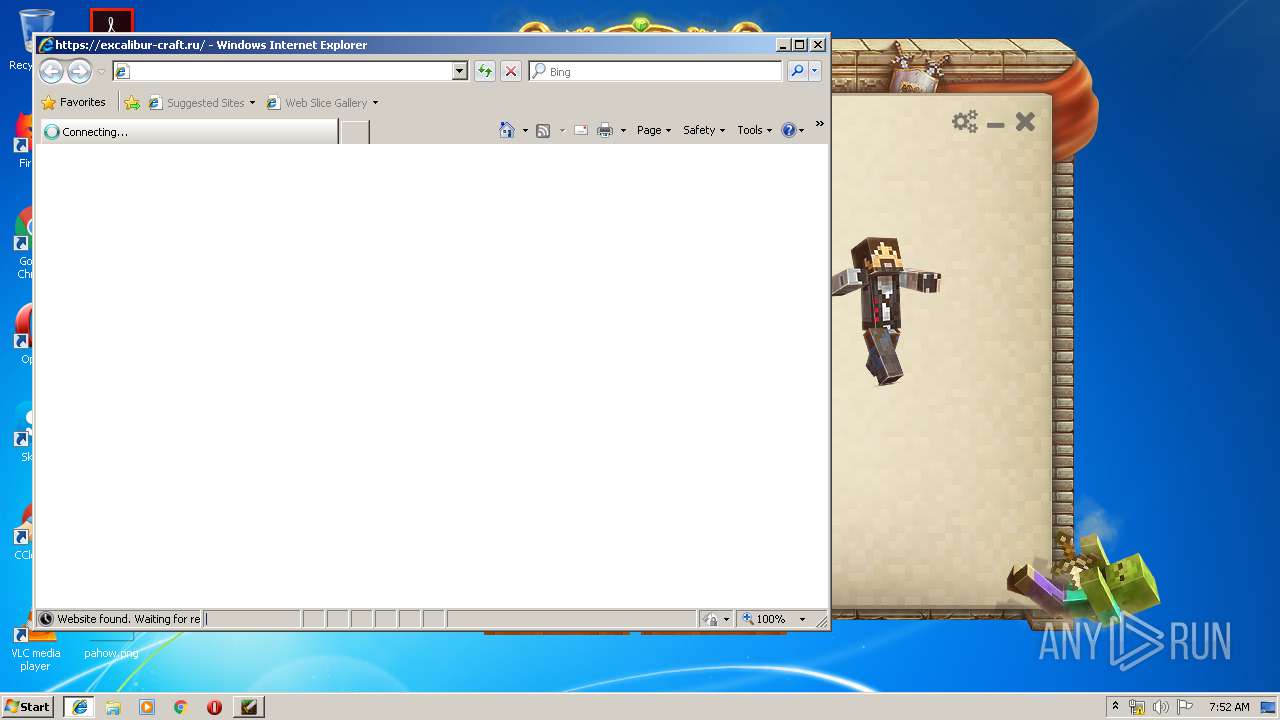
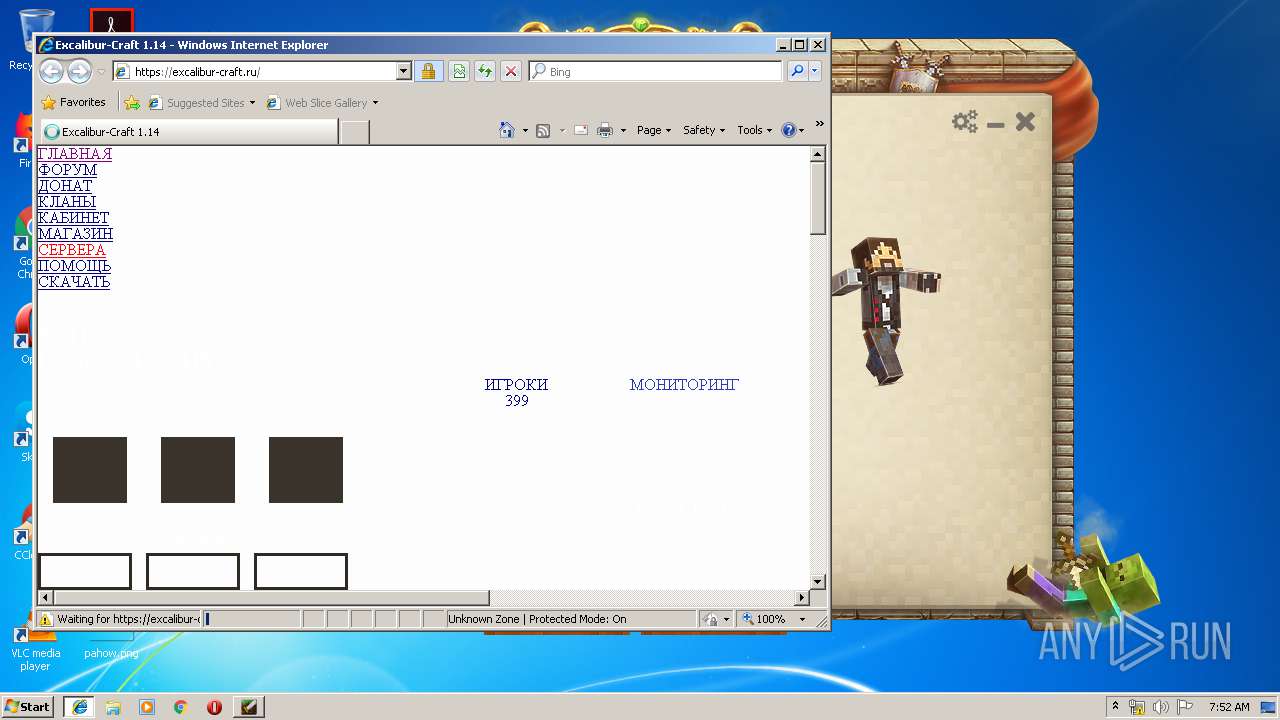
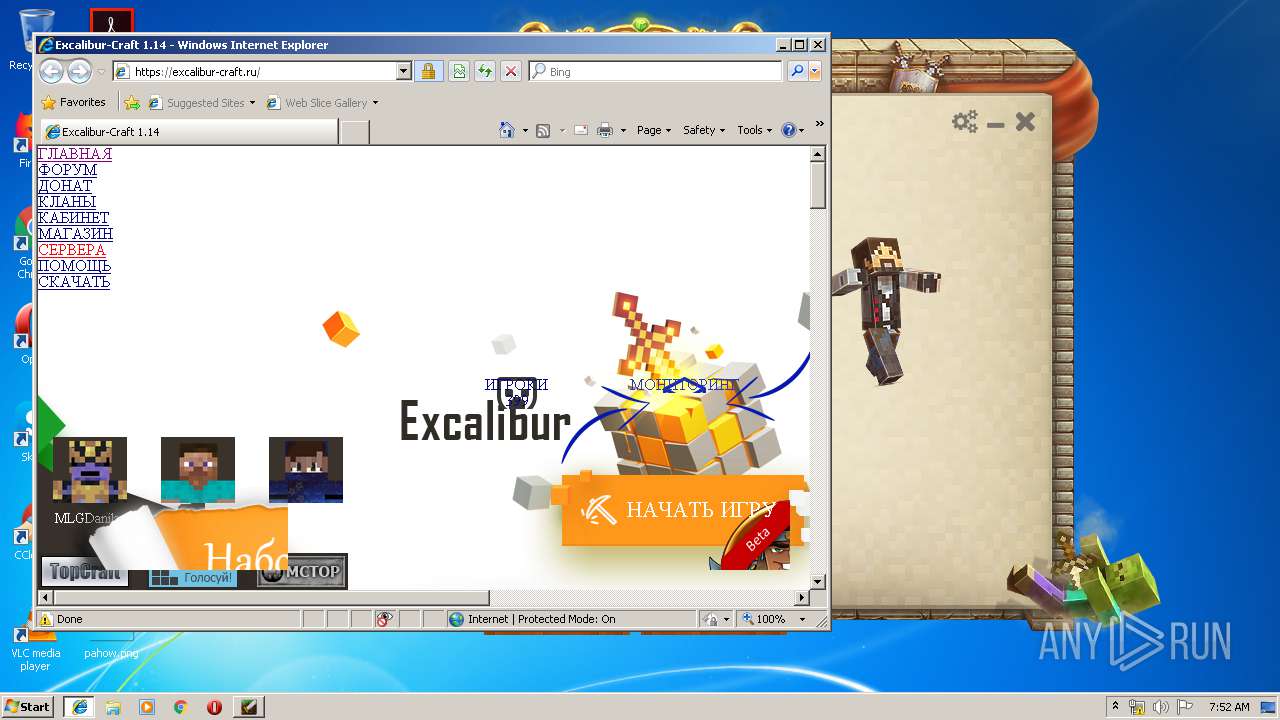
Starts Internet Explorer
- javaw.exe (PID: 3584)
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3648)
Executable content was dropped or overwritten
- Excalibur-Launcher4.1.exe (PID: 3768)
- javaw.exe (PID: 3584)
Creates files in the user directory
- Excalibur-Launcher4.1.exe (PID: 3768)
- javaw.exe (PID: 3584)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2864)
Changes internet zones settings
- iexplore.exe (PID: 2644)
Creates files in the user directory
- iexplore.exe (PID: 2864)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3648)
Reads internet explorer settings
- iexplore.exe (PID: 2864)
Reads settings of System Certificates
- iexplore.exe (PID: 2644)
Dropped object may contain Bitcoin addresses
- javaw.exe (PID: 3584)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .scr | | | Windows screen saver (60.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (20.8) |
| .exe | | | Generic Win/DOS Executable (9.2) |
| .exe | | | DOS Executable Generic (9.2) |
| .vxd | | | VXD Driver (0.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:01:13 17:40:00+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 5 |
| CodeSize: | 4001792 |
| InitializedDataSize: | 217088 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x25fc |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.1.0.13 |
| ProductVersionNumber: | 4.1.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
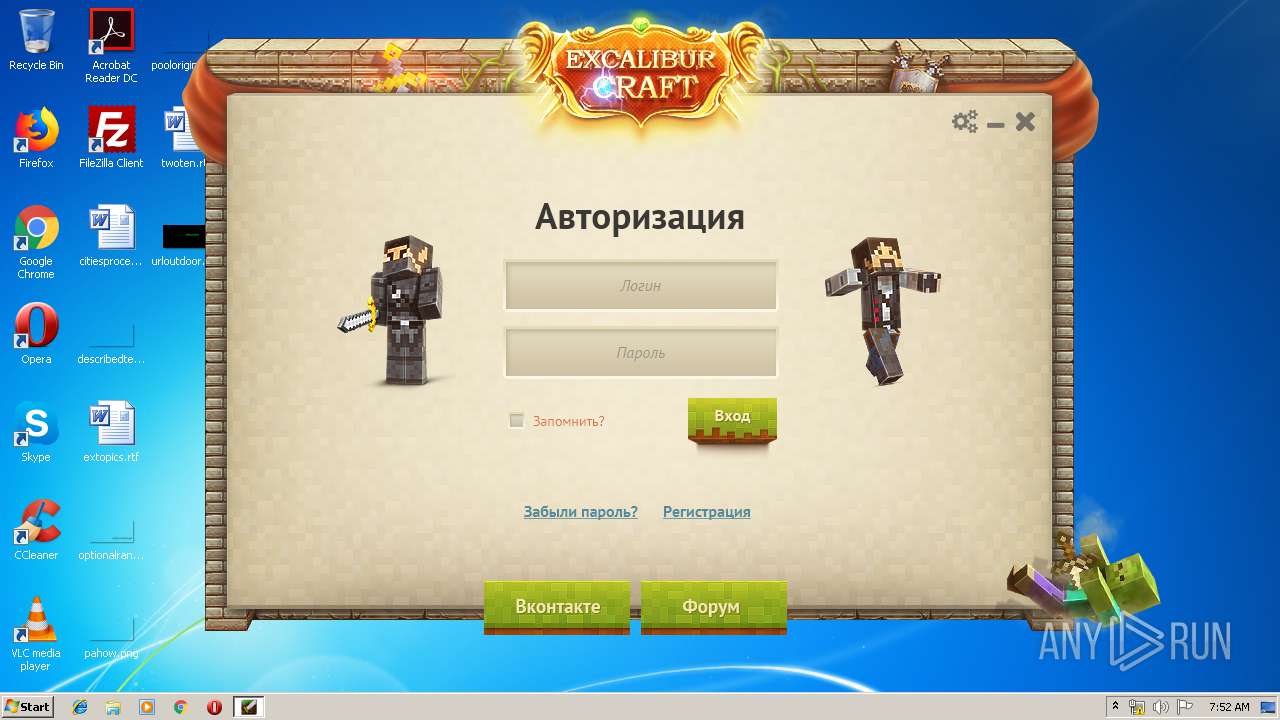
| LanguageCode: | Russian |
| CharacterSet: | Windows, Cyrillic |
| CompanyName: | Excalibur-Craft |
| FileDescription: | Excalibur-Launcher |
| FileVersion: | 4.1.0.13 |
| ProductName: | Excalibur-Launcher |
| ProductVersion: | 4.1.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Jan-2015 16:40:00 |
| Detected languages: |
|
| CompanyName: | Excalibur-Craft |
| FileDescription: | Excalibur-Launcher |
| FileVersion: | 4.1.0.13 |
| ProductName: | Excalibur-Launcher |
| ProductVersion: | 4.1.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000200 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 13-Jan-2015 16:40:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x003D1000 | 0x003D0A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44011 |
.data | 0x003D2000 | 0x00035000 | 0x00016C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.48573 |
.tls | 0x00407000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00408000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.idata | 0x00409000 | 0x00004000 | 0x00003C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.26602 |
.didata | 0x0040D000 | 0x00001000 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.75331 |
.edata | 0x0040E000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.46921 |
.rsrc | 0x0040F000 | 0x00161000 | 0x00160A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.41722 |
.reloc | 0x00570000 | 0x00051000 | 0x00050200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.73538 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.86531 | 714 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 6.42474 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 6.46326 | 9640 | UNKNOWN | English - United States | RT_ICON |
4 | 6.34221 | 16936 | UNKNOWN | English - United States | RT_ICON |
5 | 6.21658 | 67624 | UNKNOWN | English - United States | RT_ICON |
6 | 2.62527 | 308 | UNKNOWN | English - United States | RT_CURSOR |
7 | 2.91604 | 308 | UNKNOWN | English - United States | RT_CURSOR |
8 | 2.6633 | 308 | UNKNOWN | English - United States | RT_CURSOR |
4053 | 3.24638 | 920 | UNKNOWN | UNKNOWN | RT_STRING |
4054 | 3.2415 | 868 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
ADVAPI32.DLL |
BLUETOOTHAPIS.DLL |
BTHPROPS.DLL |
COMCTL32.DLL |
DWMAPI.DLL |
GDI32.DLL |
IMM32.DLL |
KERNEL32.DLL |
MSIMG32.DLL |
OLE32.DLL |
Exports
Title | Ordinal | Address |
|---|---|---|
__GetExceptDLLinfo | 1 | 0x0000265B |
@@Mainunit@Initialize | 2 | 0x00003ACC |
@@Mainunit@Finalize | 3 | 0x00003ADC |
@@Updaterunit@Initialize | 4 | 0x00011CE0 |
@@Updaterunit@Finalize | 5 | 0x00011CF8 |
TMethodImplementationIntercept | 6 | 0x000796D0 |
___CPPdebugHook | 7 | 0x003D20AC |
_MainForm | 8 | 0x003E8B0C |
Total processes
40
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2644 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | javaw.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2760 | C:\Windows\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\system32\icacls.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2864 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2644 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3380 | ipconfig /all | C:\Windows\system32\ipconfig.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
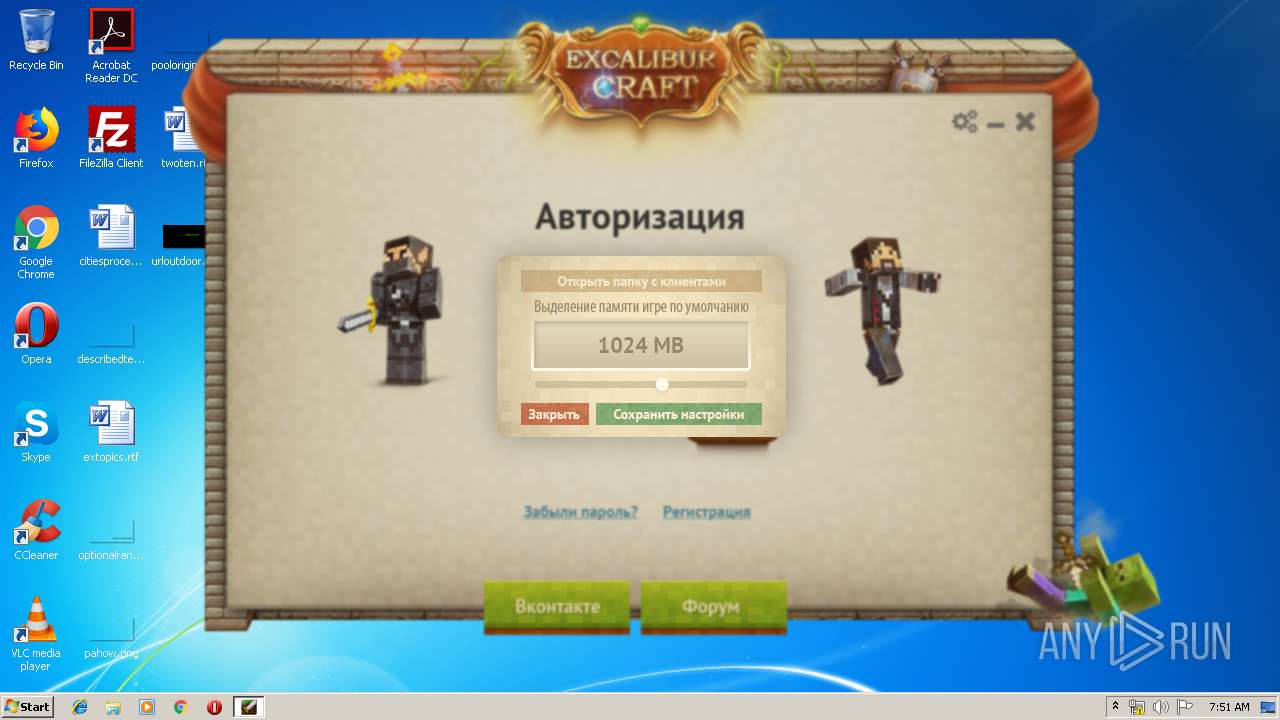
| 3584 | C:\Users\admin\AppData\Roaming\exjava\\jvm\\bin\\javaw.exe -jar launcher.jar | C:\Users\admin\AppData\Roaming\exjava\jvm\bin\javaw.exe | Excalibur-Launcher4.1.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2210.11 Modules
| |||||||||||||||
| 3648 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 3768 | "C:\Users\admin\AppData\Local\Temp\Excalibur-Launcher4.1.exe" | C:\Users\admin\AppData\Local\Temp\Excalibur-Launcher4.1.exe | explorer.exe | ||||||||||||
User: admin Company: Excalibur-Craft Integrity Level: MEDIUM Description: Excalibur-Launcher Exit code: 0 Version: 4.1.0.13 Modules
| |||||||||||||||
Total events
488
Read events
437
Write events
50
Delete events
1
Modification events
| (PID) Process: | (3584) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
| (PID) Process: | (2644) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2644) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2644) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2644) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2644) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2644) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2644) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {85141E35-C572-11E9-B86F-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2644) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2644) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
Executable files
189
Suspicious files
304
Text files
810
Unknown types
602
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3768 | Excalibur-Launcher4.1.exe | C:\Users\admin\AppData\Roaming\exjava\javawin32.zip | — | |
MD5:— | SHA256:— | |||
| 3768 | Excalibur-Launcher4.1.exe | C:\Users\admin\AppData\Roaming\exjava\jvm\bin\api-ms-win-core-heap-l1-1-0.dll | executable | |
MD5:2EA3901D7B50BF6071EC8732371B821C | SHA256:44F6DF4280C8ECC9C6E609B1A4BFEE041332D337D84679CFE0D6678CE8F2998A | |||
| 3768 | Excalibur-Launcher4.1.exe | C:\Users\admin\AppData\Roaming\exjava\jvm\bin\api-ms-win-core-console-l1-1-0.dll | executable | |
MD5:502263C56F931DF8440D7FD2FA7B7C00 | SHA256:94A5DF1227818EDBFD0D5091C6A48F86B4117C38550343F780C604EEE1CD6231 | |||
| 3768 | Excalibur-Launcher4.1.exe | C:\Users\admin\AppData\Roaming\exjava\jvm\release | text | |
MD5:5078EA61CE8DECAE6BD8D8A1F1E78593 | SHA256:09532C59F96BA2F745C7634EE203233090419B5D0C283CF0B0B15195057DCE42 | |||
| 3768 | Excalibur-Launcher4.1.exe | C:\Users\admin\AppData\Roaming\exjava\jvm\bin\api-ms-win-core-file-l1-2-0.dll | executable | |
MD5:E2F648AE40D234A3892E1455B4DBBE05 | SHA256:C8C499B012D0D63B7AFC8B4CA42D6D996B2FCF2E8B5F94CACFBEC9E6F33E8A03 | |||
| 3768 | Excalibur-Launcher4.1.exe | C:\Users\admin\AppData\Roaming\exjava\jvm\bin\api-ms-win-core-file-l2-1-0.dll | executable | |
MD5:E479444BDD4AE4577FD32314A68F5D28 | SHA256:C85DC081B1964B77D289AAC43CC64746E7B141D036F248A731601EB98F827719 | |||
| 3768 | Excalibur-Launcher4.1.exe | C:\Users\admin\AppData\Roaming\exjava\jvm\COPYRIGHT | text | |
MD5:9C7F71E1A16138E1C9FD6B7843F912A5 | SHA256:F11ACBCCAD1F3BFE66A0D14E157820015D395A0BFB16AC89C72A928532DA8BD8 | |||
| 3768 | Excalibur-Launcher4.1.exe | C:\Users\admin\AppData\Roaming\exjava\jvm\bin\api-ms-win-core-datetime-l1-1-0.dll | executable | |
MD5:CB978304B79EF53962408C611DFB20F5 | SHA256:90FAE0E7C3644A6754833C42B0AC39B6F23859F9A7CF4B6C8624820F59B9DAD3 | |||
| 3768 | Excalibur-Launcher4.1.exe | C:\Users\admin\AppData\Roaming\exjava\jvm\bin\api-ms-win-core-errorhandling-l1-1-0.dll | executable | |
MD5:6D778E83F74A4C7FE4C077DC279F6867 | SHA256:A97DCCA76CDB12E985DFF71040815F28508C655AB2B073512E386DD63F4DA325 | |||
| 3768 | Excalibur-Launcher4.1.exe | C:\Users\admin\AppData\Roaming\exjava\jvm\bin\api-ms-win-core-namedpipe-l1-1-0.dll | executable | |
MD5:6F6796D1278670CCE6E2D85199623E27 | SHA256:C4F60F911068AB6D7F578D449BA7B5B9969F08FC683FD0CE8E2705BBF061F507 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
197
TCP/UDP connections
136
DNS requests
15
Threats
65
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
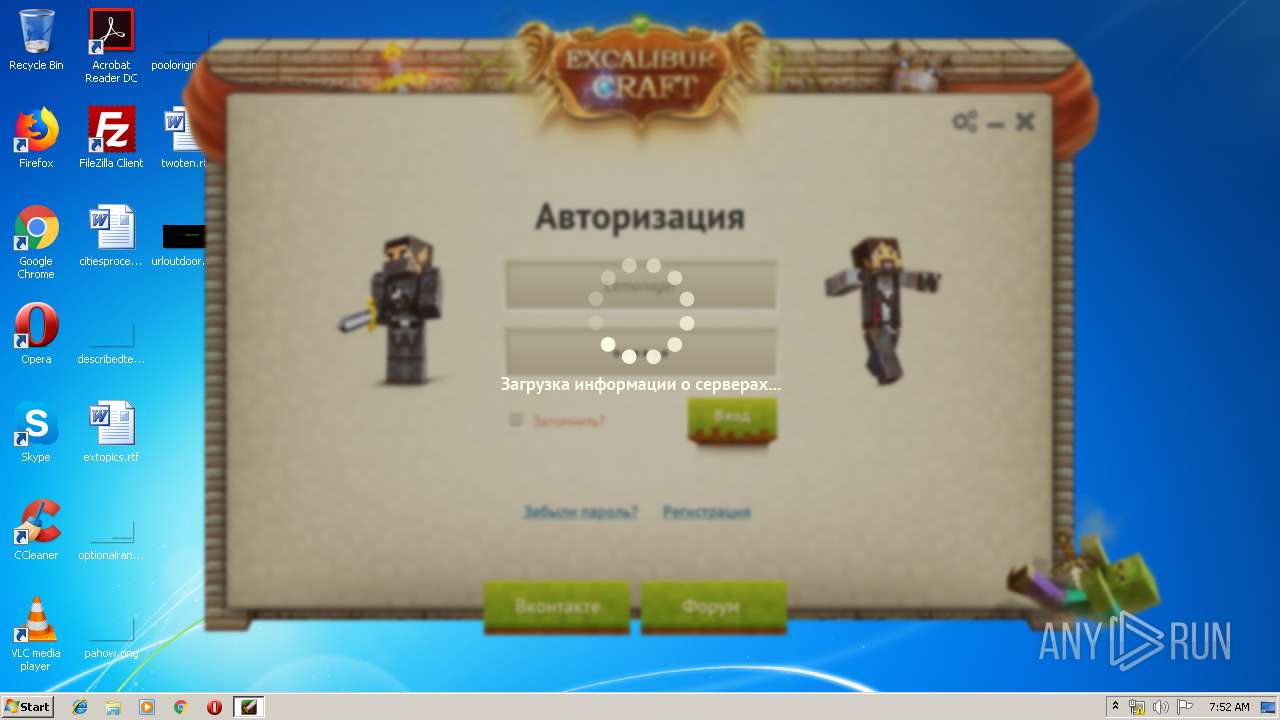
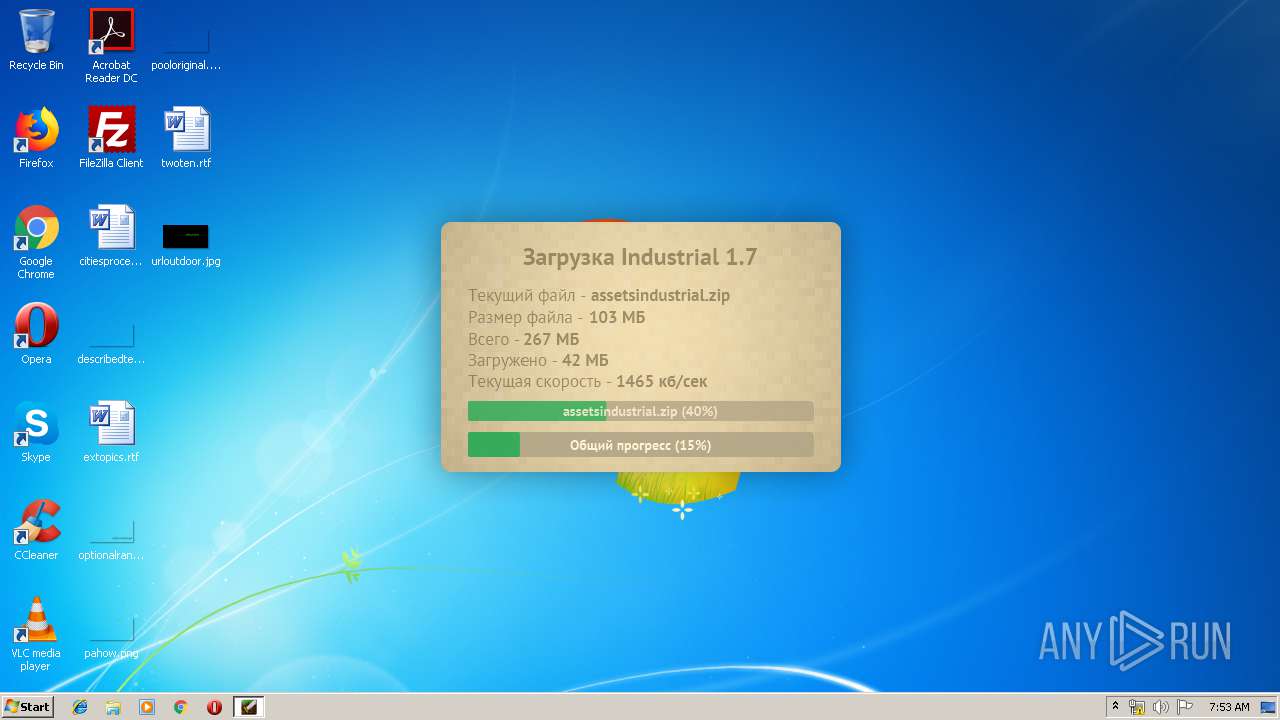
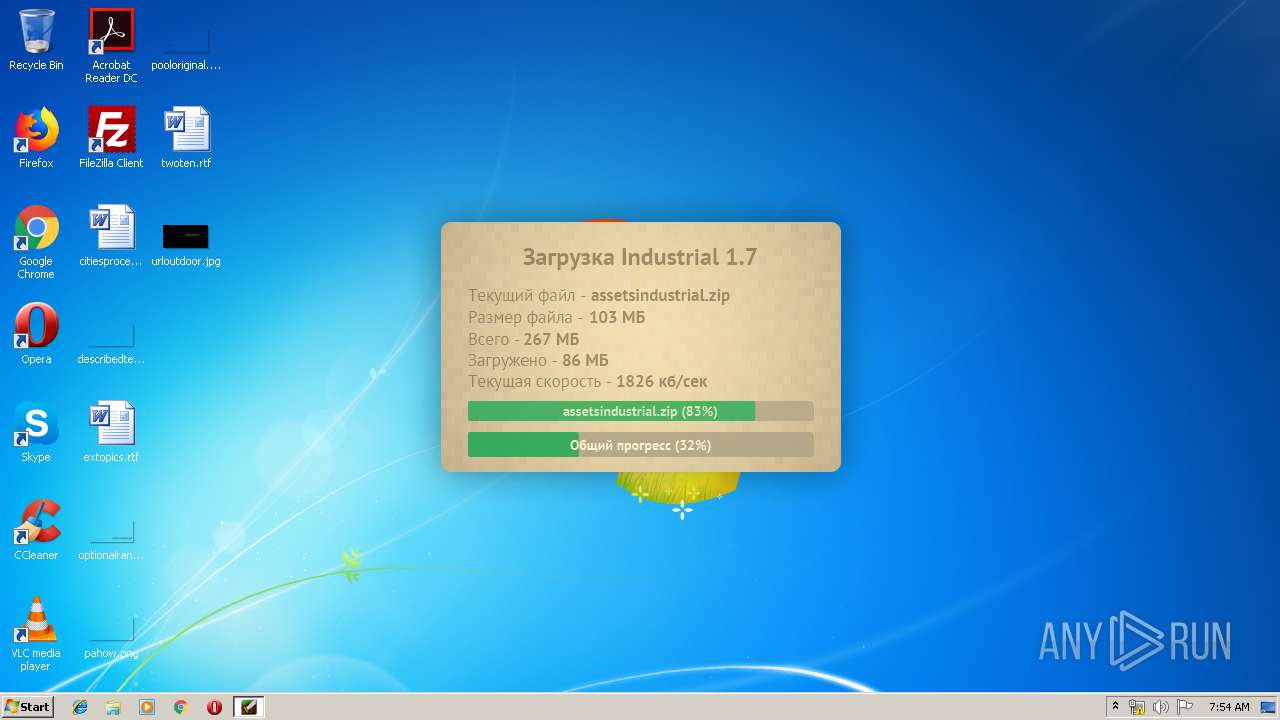
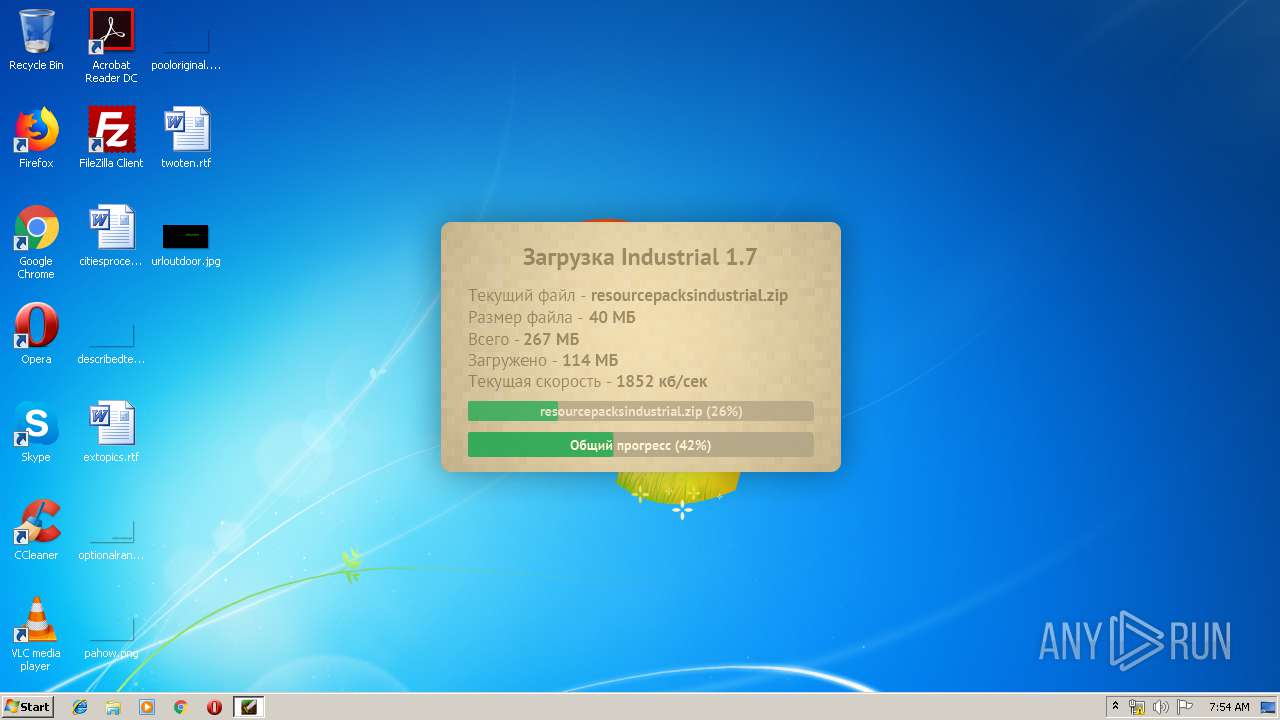
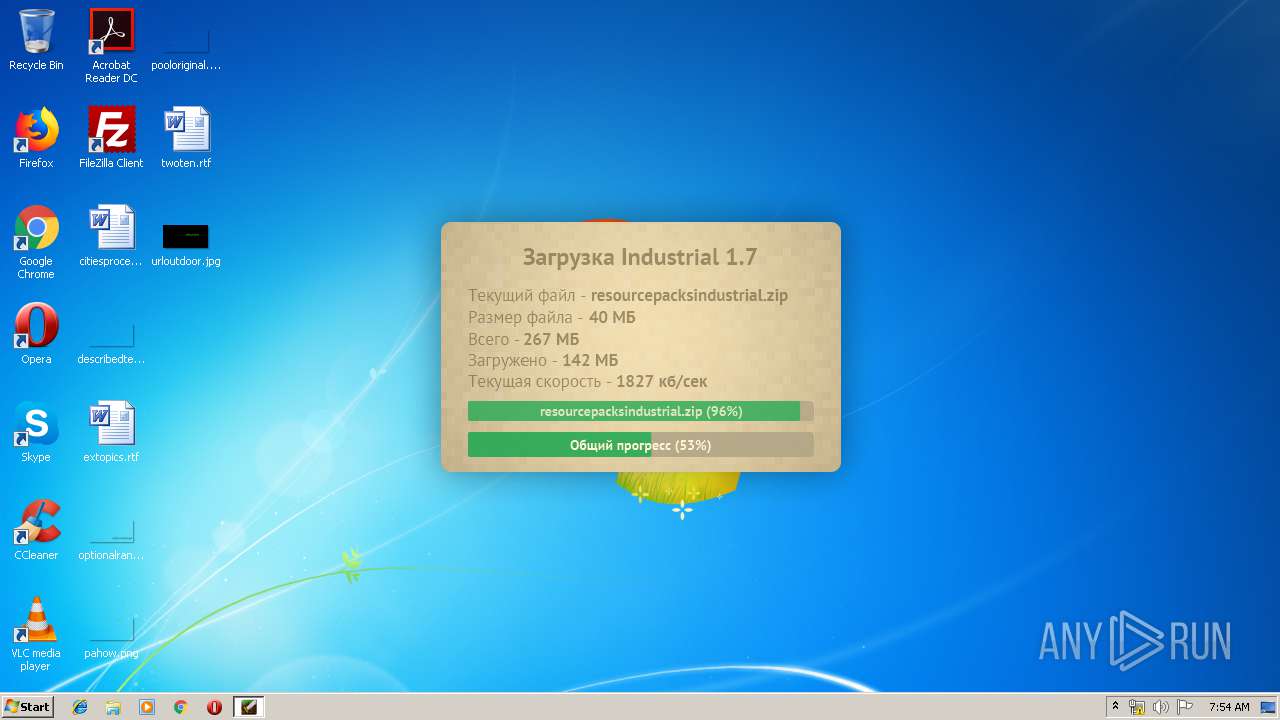
3584 | javaw.exe | GET | 200 | 164.132.67.160:80 | http://ex-server.ru/configlauncher.xml | FR | xml | 16.5 Kb | suspicious |
3584 | javaw.exe | GET | 200 | 164.132.67.158:80 | http://ex-serwer.ru/clients/img/classic.png | FR | image | 9.69 Kb | suspicious |
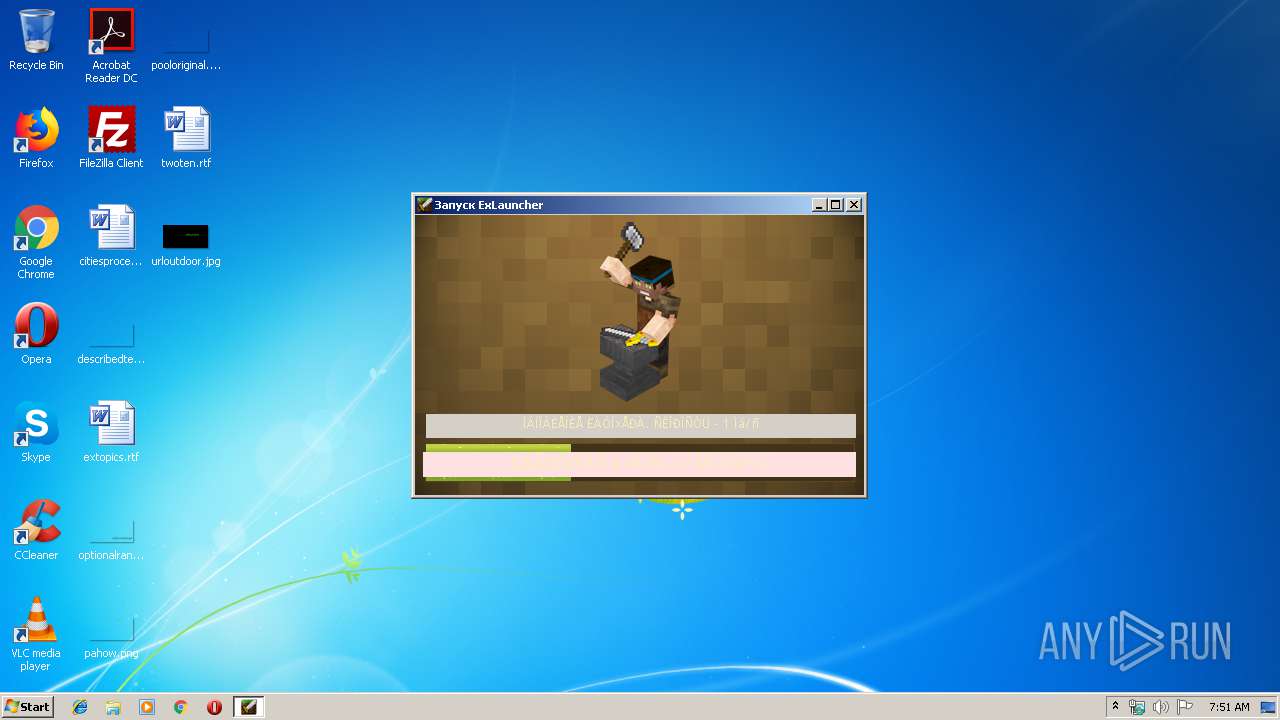
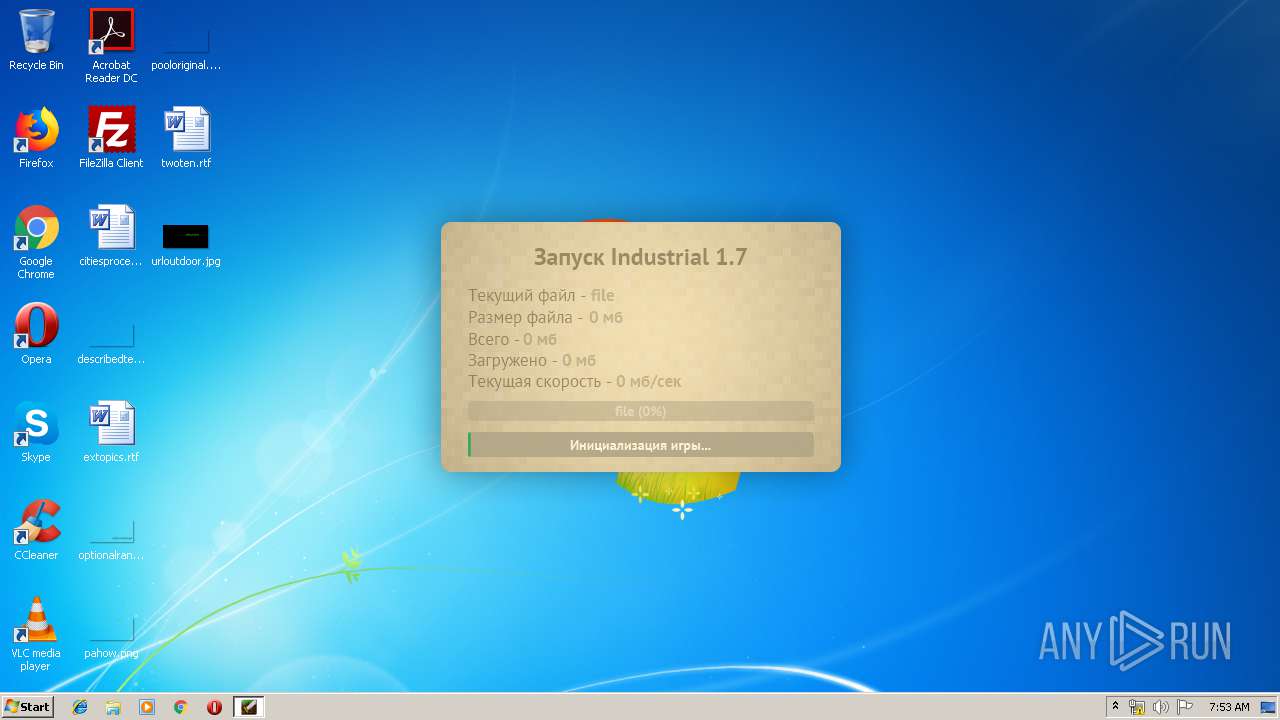
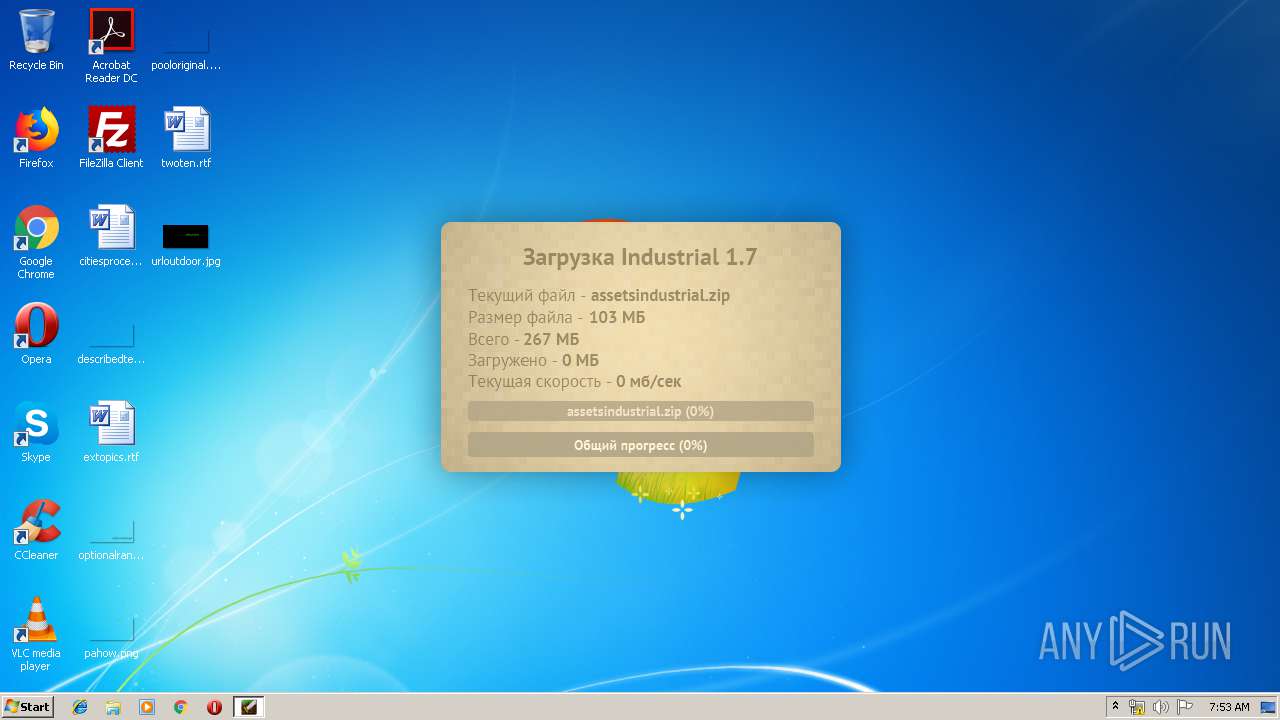
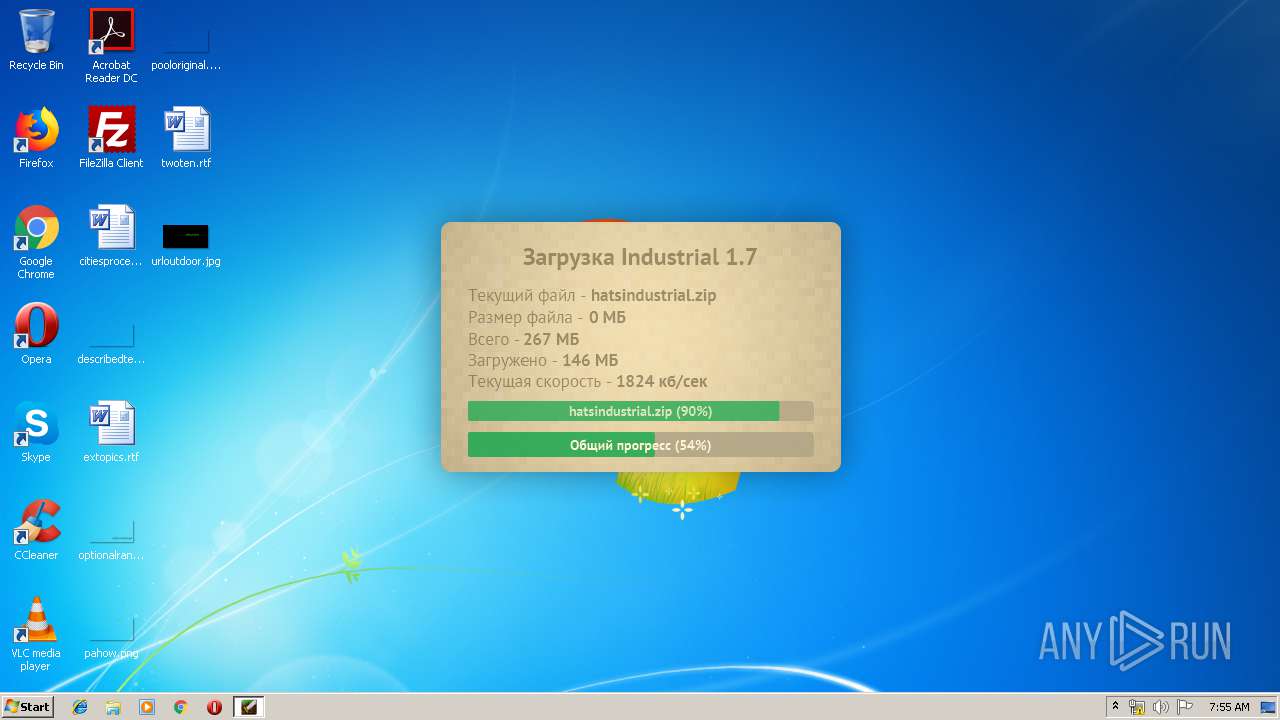
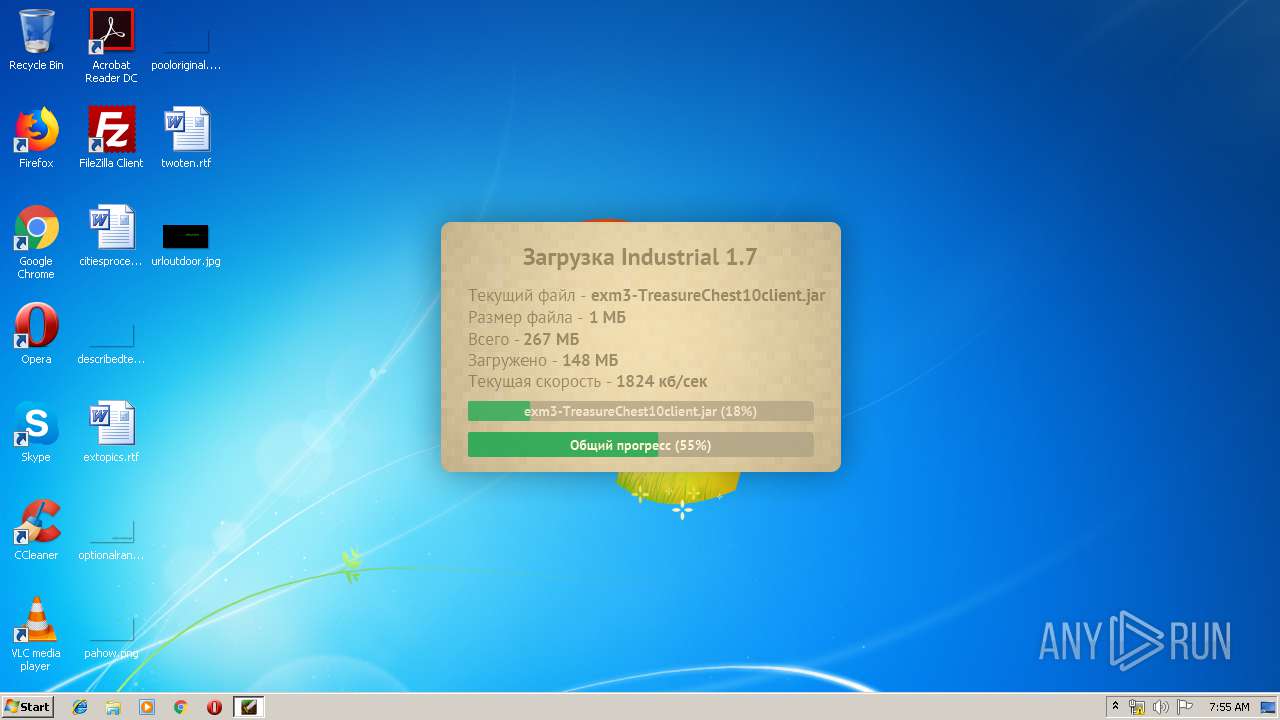
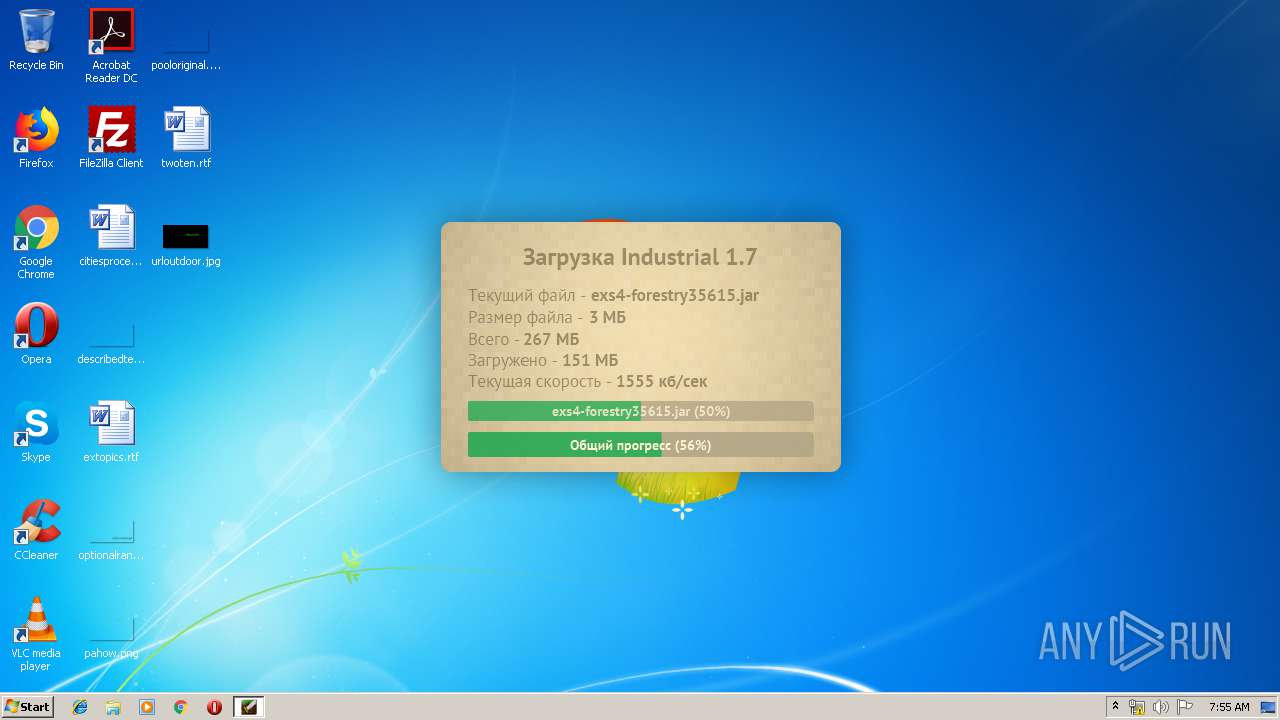
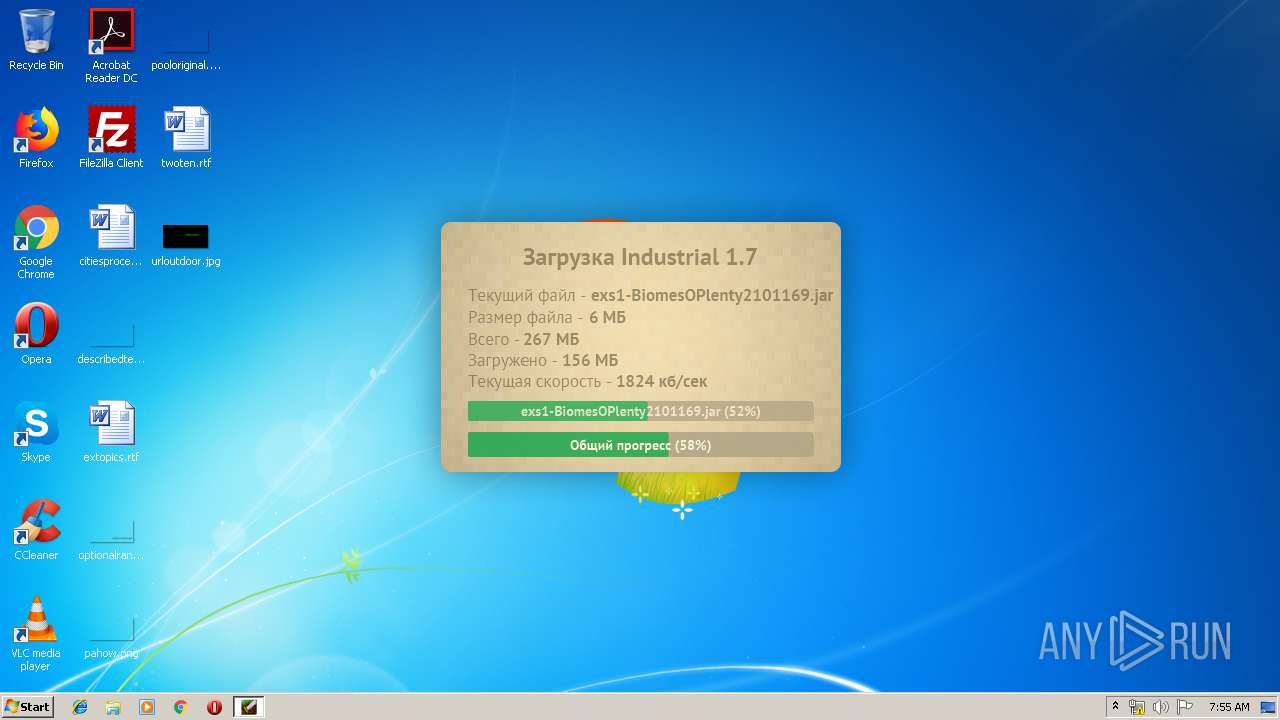
3768 | Excalibur-Launcher4.1.exe | GET | 200 | 164.132.67.158:80 | http://ex-serwer.ru/exlauncher/launcher.jar | FR | compressed | 12.3 Mb | suspicious |
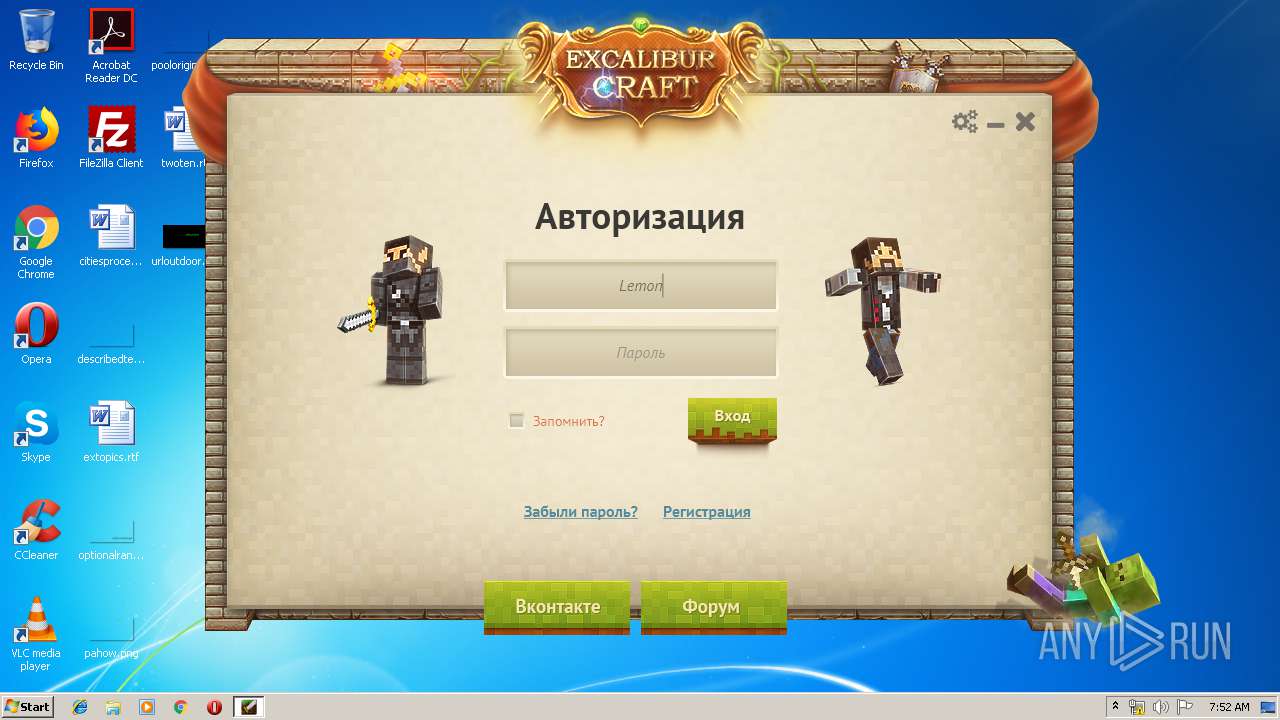
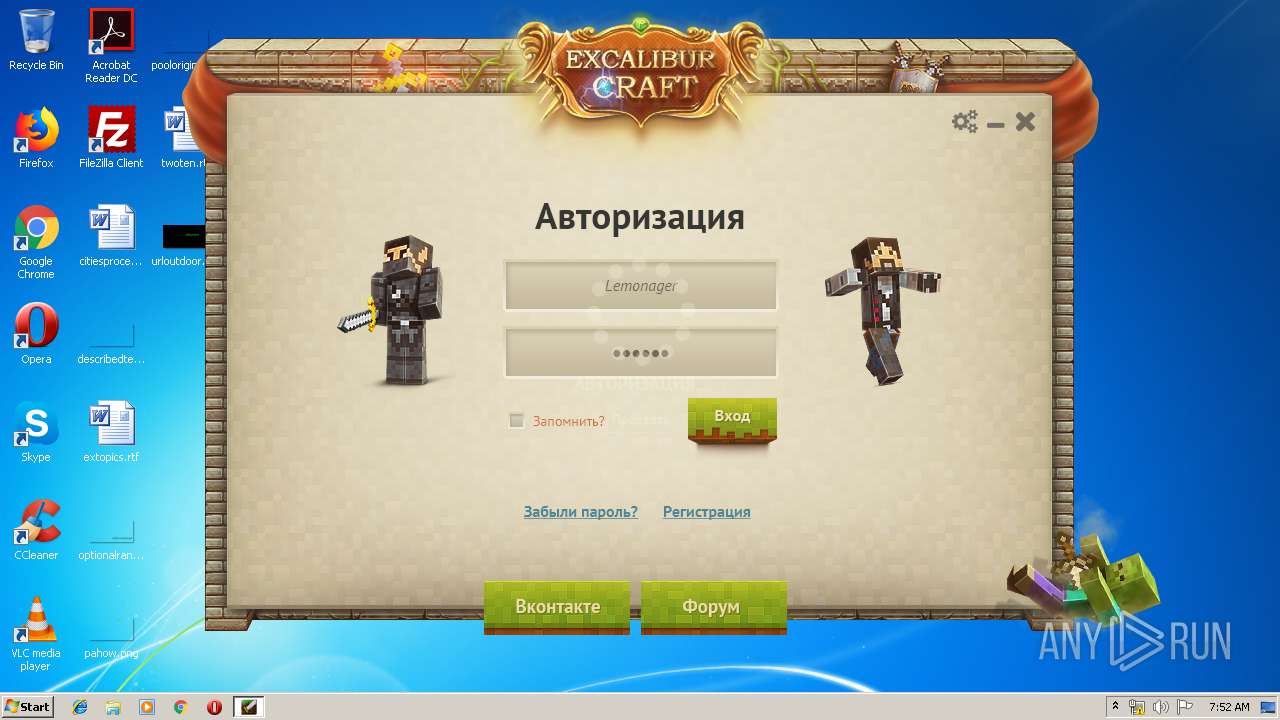
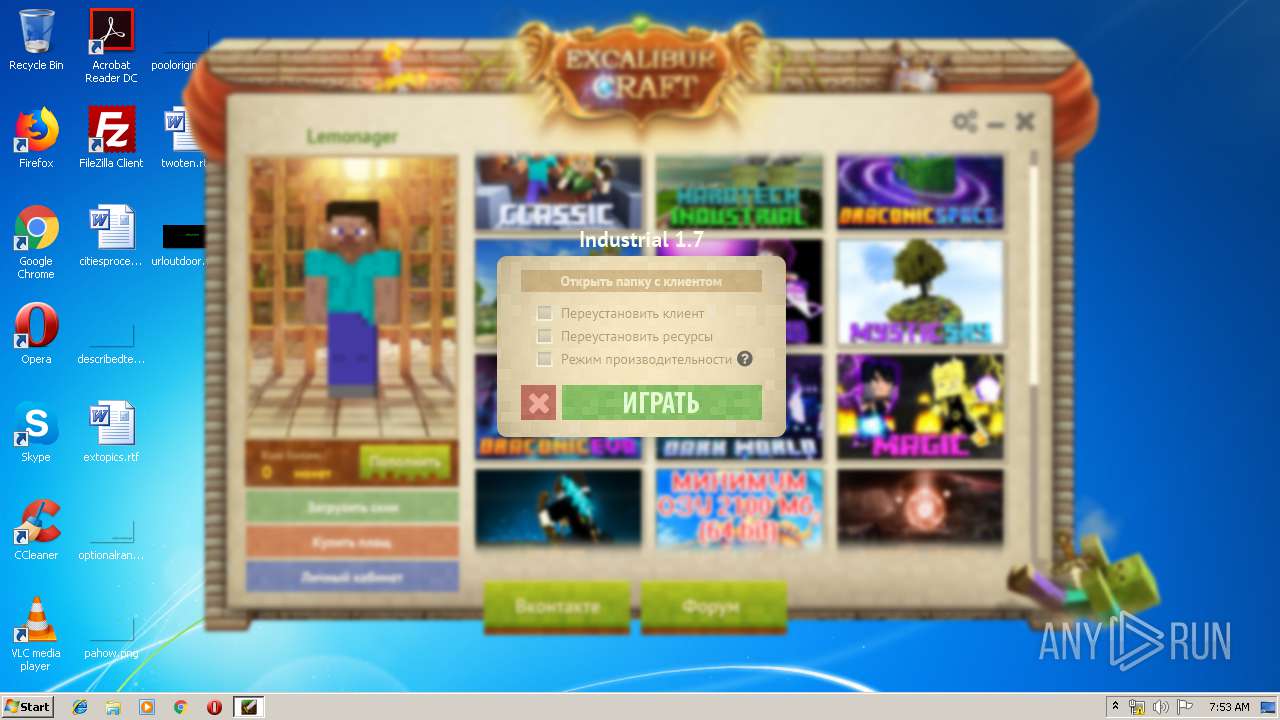
3584 | javaw.exe | GET | 200 | 164.132.67.160:80 | http://ex-server.ru/skin3d.php?login=Lemonager&a=-4&w=-8&wt=0&abg=0&abd=0&ajg=0&ajd=0&ratio=8 | FR | image | 2.48 Kb | suspicious |
3584 | javaw.exe | GET | 200 | 164.132.67.158:80 | http://ex-serwer.ru/clients/img/sandbox.png | FR | image | 39.0 Kb | suspicious |
3584 | javaw.exe | GET | 200 | 164.132.67.158:80 | http://ex-serwer.ru/clients/img/darkworld.png | FR | image | 14.4 Kb | suspicious |
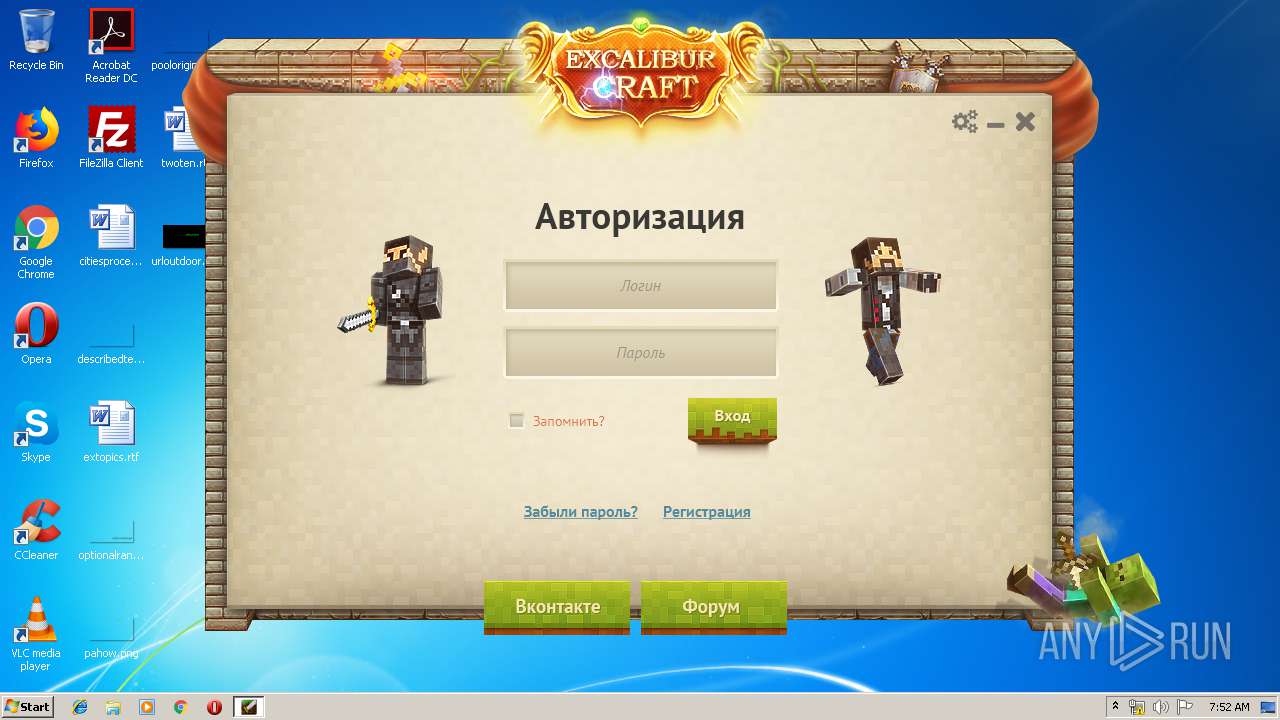
3584 | javaw.exe | POST | 200 | 164.132.67.160:80 | http://ex-server.ru/exAuthLogin.php | FR | xml | 200 b | suspicious |
3584 | javaw.exe | GET | 200 | 164.132.67.158:80 | http://ex-serwer.ru/clients/img/rpg.png | FR | image | 8.90 Kb | suspicious |
3768 | Excalibur-Launcher4.1.exe | GET | 200 | 164.132.67.158:80 | http://ex-serwer.ru/exlauncher/jvm/javawin322019.zip | FR | compressed | 68.8 Mb | suspicious |
3584 | javaw.exe | GET | 200 | 164.132.67.158:80 | http://ex-serwer.ru/clients/img/draconicspace.png | FR | image | 14.1 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2864 | iexplore.exe | 104.19.197.151:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | shared |
2864 | iexplore.exe | 172.217.16.168:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
2864 | iexplore.exe | 87.240.190.67:443 | vk.com | VKontakte Ltd | RU | suspicious |
3768 | Excalibur-Launcher4.1.exe | 164.132.67.160:80 | ex-server.ru | OVH SAS | FR | suspicious |
3768 | Excalibur-Launcher4.1.exe | 164.132.67.158:80 | ex-serwer.ru | OVH SAS | FR | suspicious |
2864 | iexplore.exe | 162.159.133.233:443 | discordapp.com | Cloudflare Inc | — | shared |
2864 | iexplore.exe | 217.182.78.61:443 | www.webmoney.ru | OVH SAS | PL | unknown |
2864 | iexplore.exe | 151.101.36.193:443 | i.imgur.com | Fastly | US | unknown |
2864 | iexplore.exe | 109.235.165.142:443 | money.yandex.ru | Yandex.Money NBCO LLC | RU | whitelisted |
2864 | iexplore.exe | 172.217.18.110:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ex-server.ru |
| suspicious |
ex-serwer.ru |
| suspicious |
www.bing.com |
| whitelisted |
excalibur-craft.ru |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
vk.com |
| whitelisted |
www.webmoney.ru |
| suspicious |
money.yandex.ru |
| whitelisted |
discordapp.com |
| whitelisted |
counter.yadro.ru |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3584 | javaw.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pass= in cleartext |
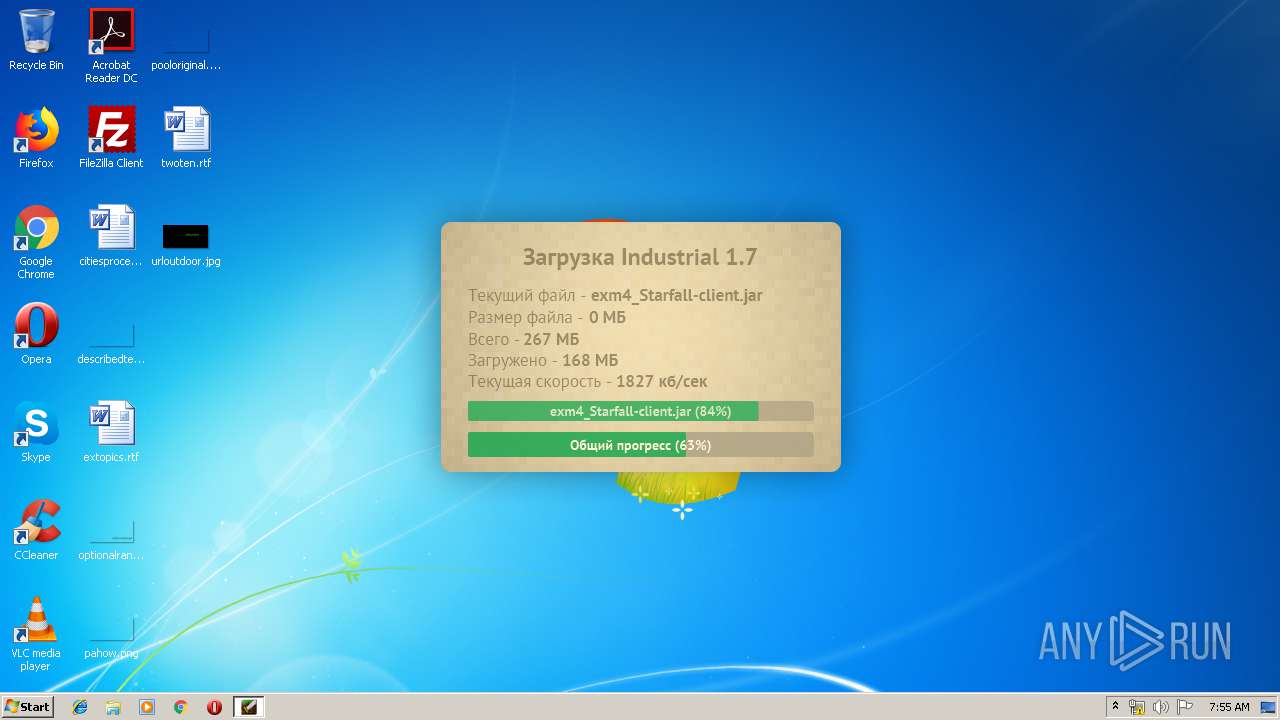
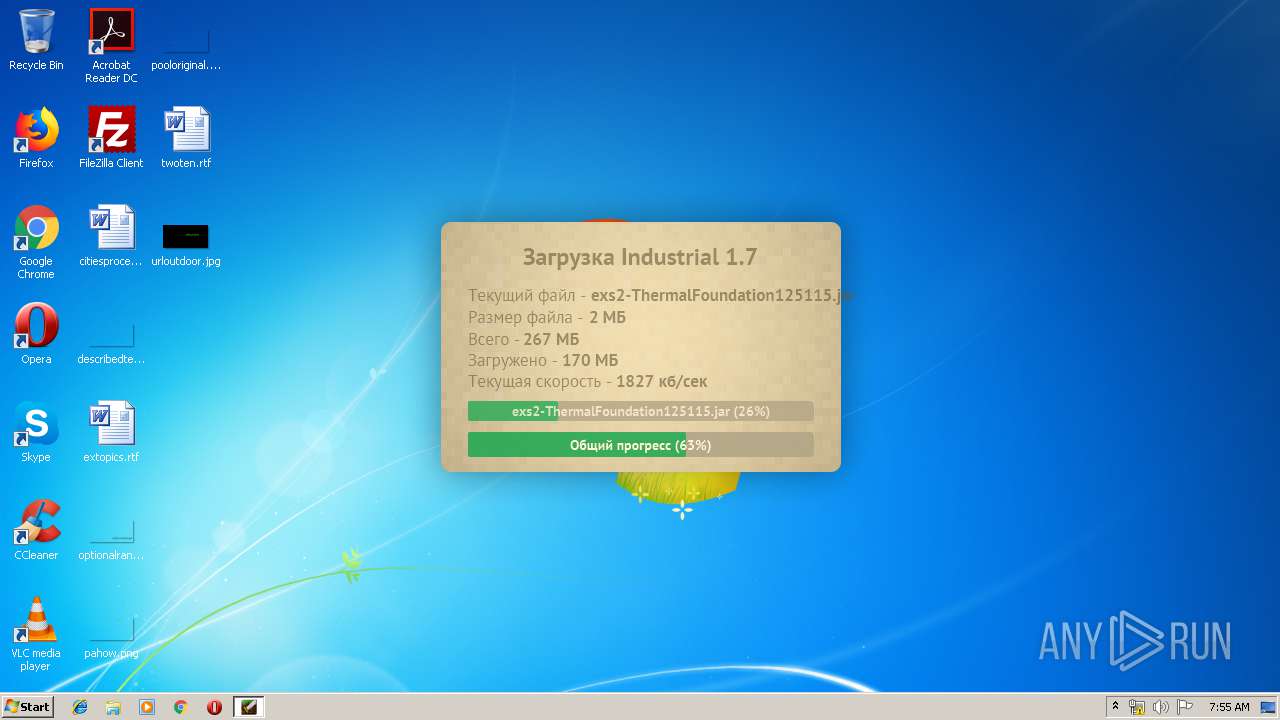
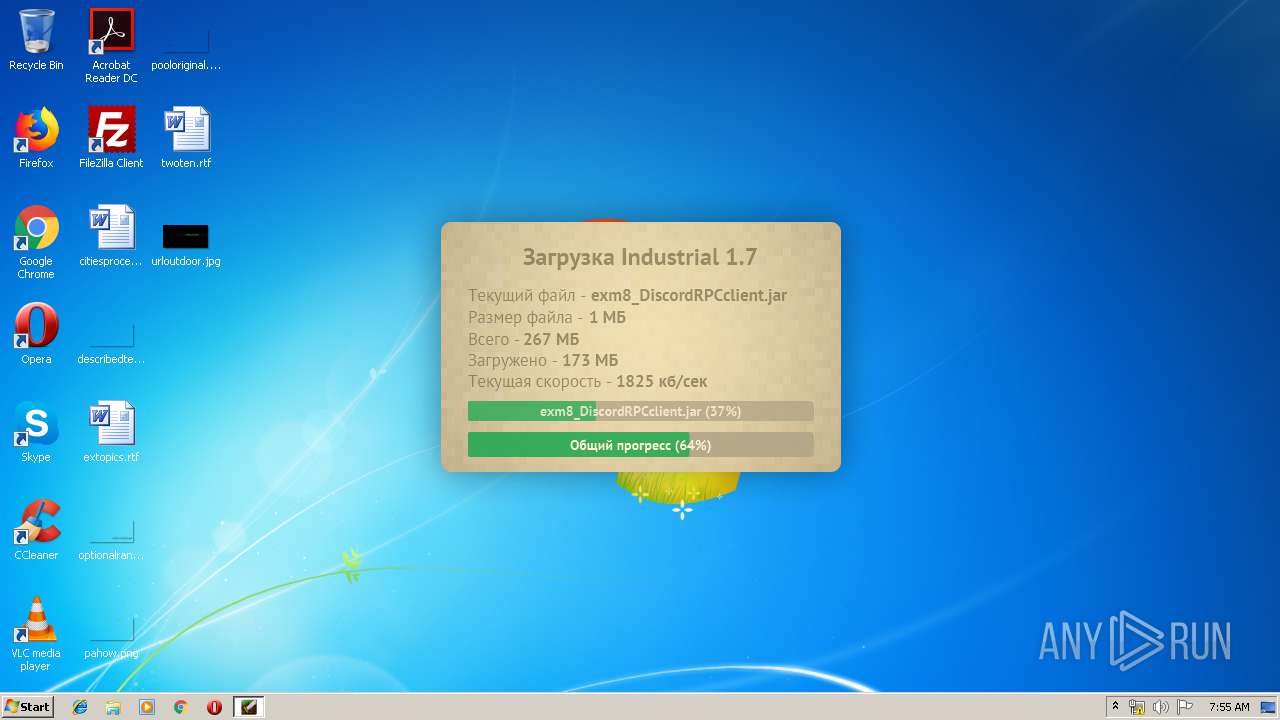
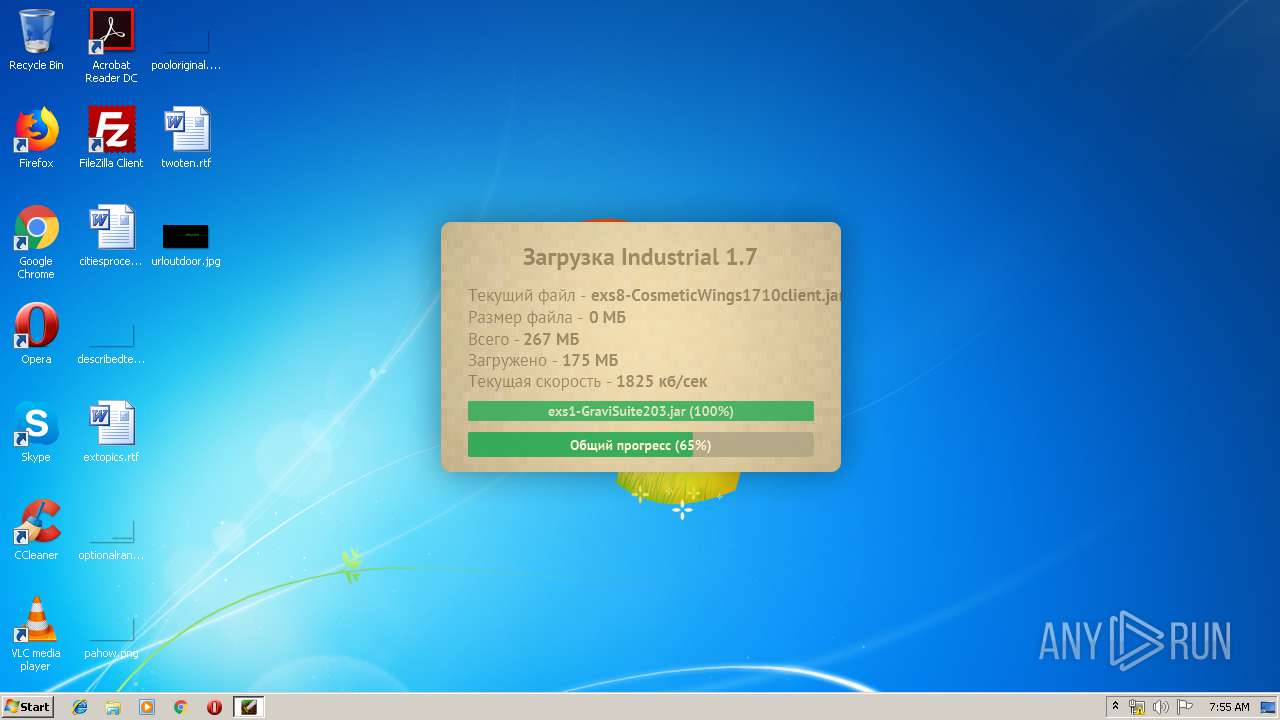
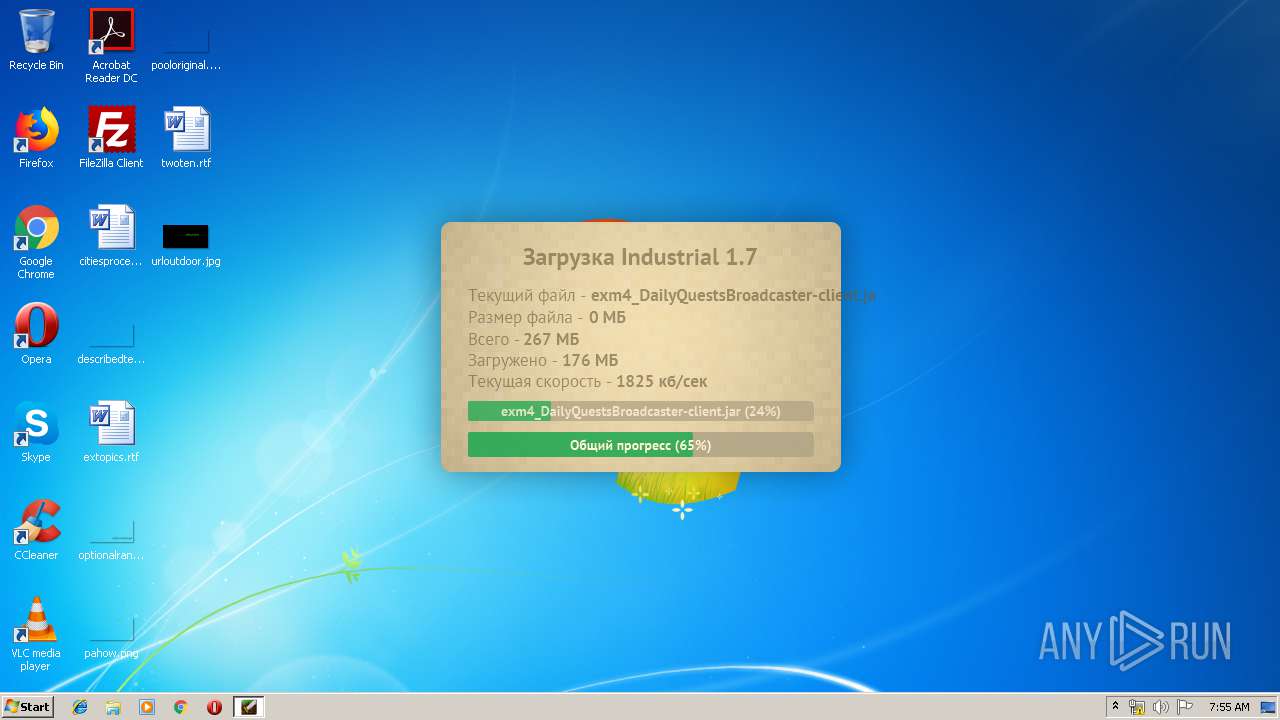
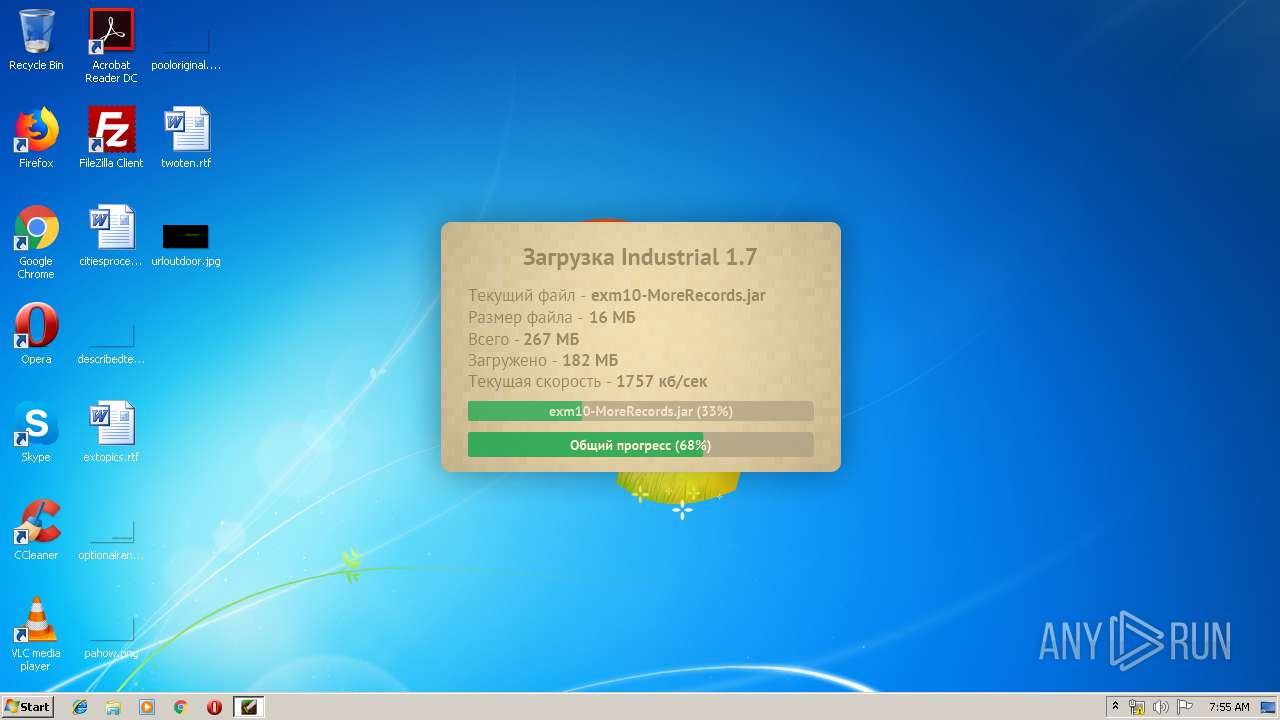
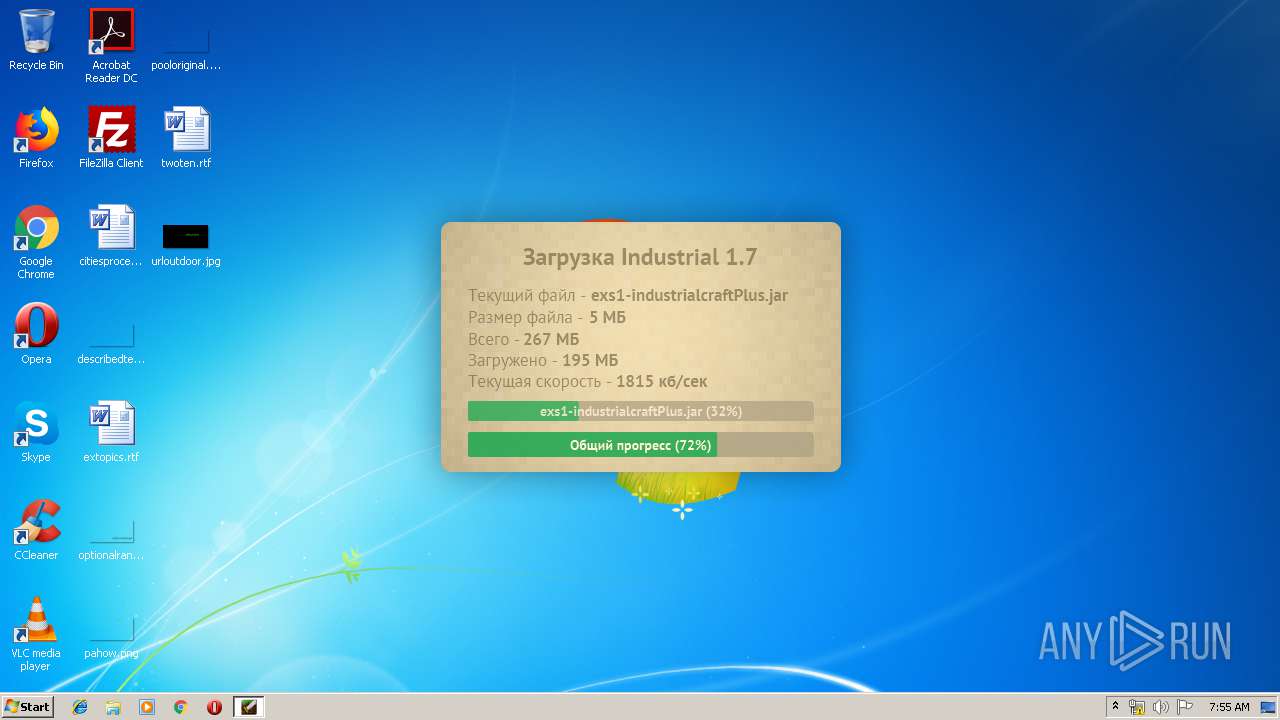
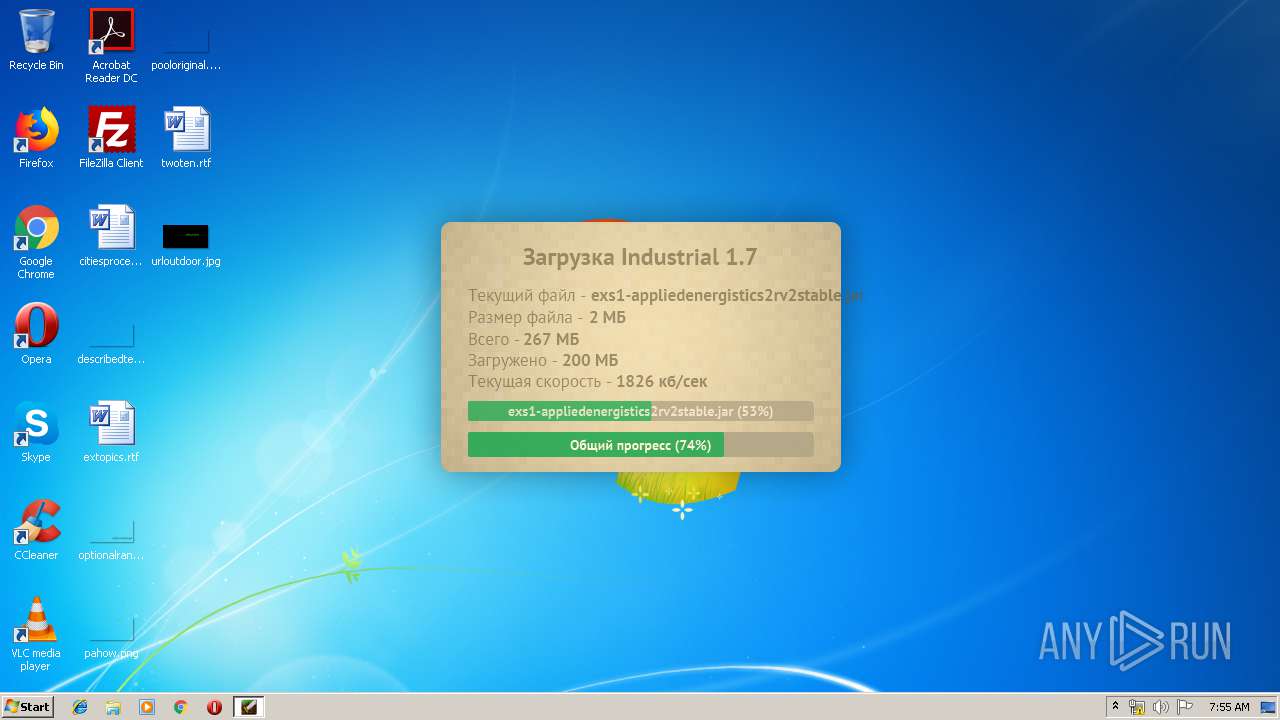
3584 | javaw.exe | Potentially Bad Traffic | ET CURRENT_EVENTS SUSPICIOUS JAR Download by Java UA with non JAR EXT matches various EKs |
3584 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
3584 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
3584 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
3584 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
3584 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
3584 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
3584 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
3584 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |