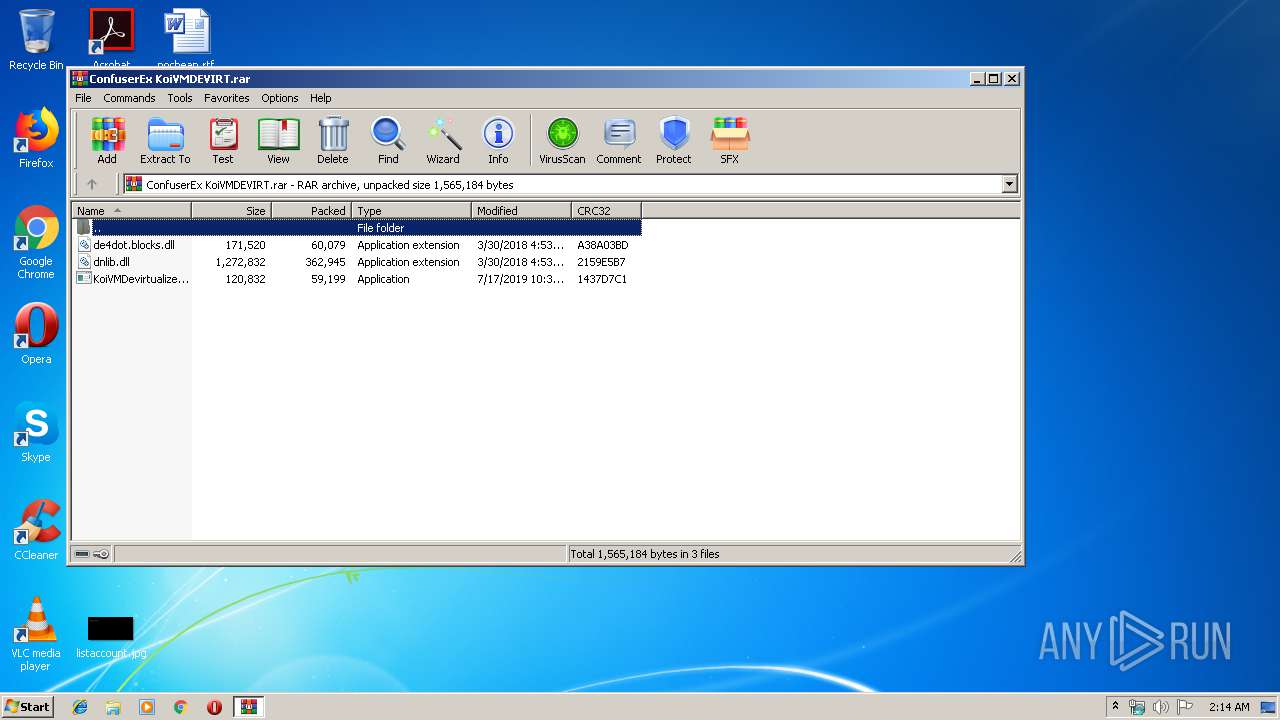
| File name: | ConfuserEx KoiVMDEVIRT.rar |
| Full analysis: | https://app.any.run/tasks/2822c51b-8bf4-4946-bceb-c6600fb9cb7e |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 01:14:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | E63E0A1F538B8CE778714BF2CE74933A |
| SHA1: | 2468EAD952ACF7E75E10CE5F56672D9FCB7CB62E |
| SHA256: | A651846310FEB6A6973E4F9AFA3DEE6D0401F74C58AC11DC2837B7F24C0FC755 |
| SSDEEP: | 6144:F5EdWOz7JU2DxdCnLl5/f1obf3ILZqGfCd7tiJ4b/+VxZeszPFNeIf7e7DKC0KjH:BUS2DHYf1o73KaCJEEx0szmITe2Kj6I |
MALICIOUS
Loads dropped or rewritten executable
- explorer.exe (PID: 304)
- SearchProtocolHost.exe (PID: 1724)
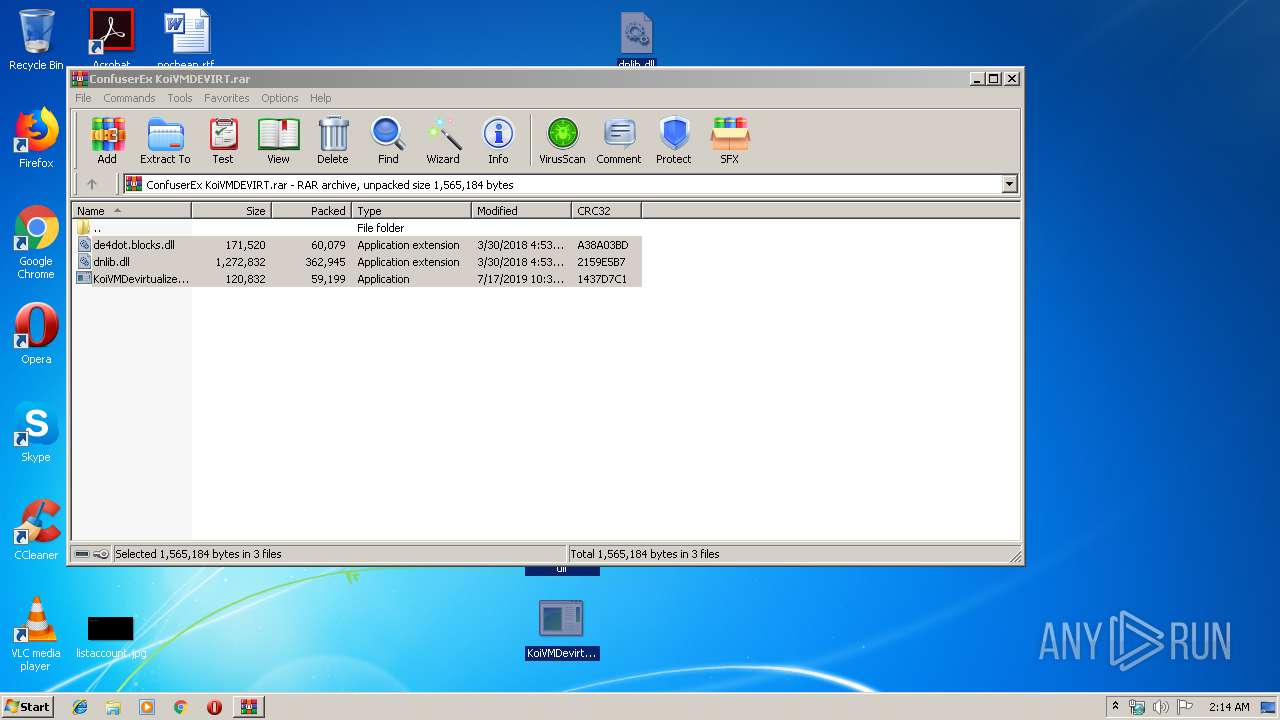
Application was dropped or rewritten from another process
- KoiVMDevirtualizer.exe (PID: 2200)
- KoiVMDevirtualizer.exe (PID: 3020)
SUSPICIOUS
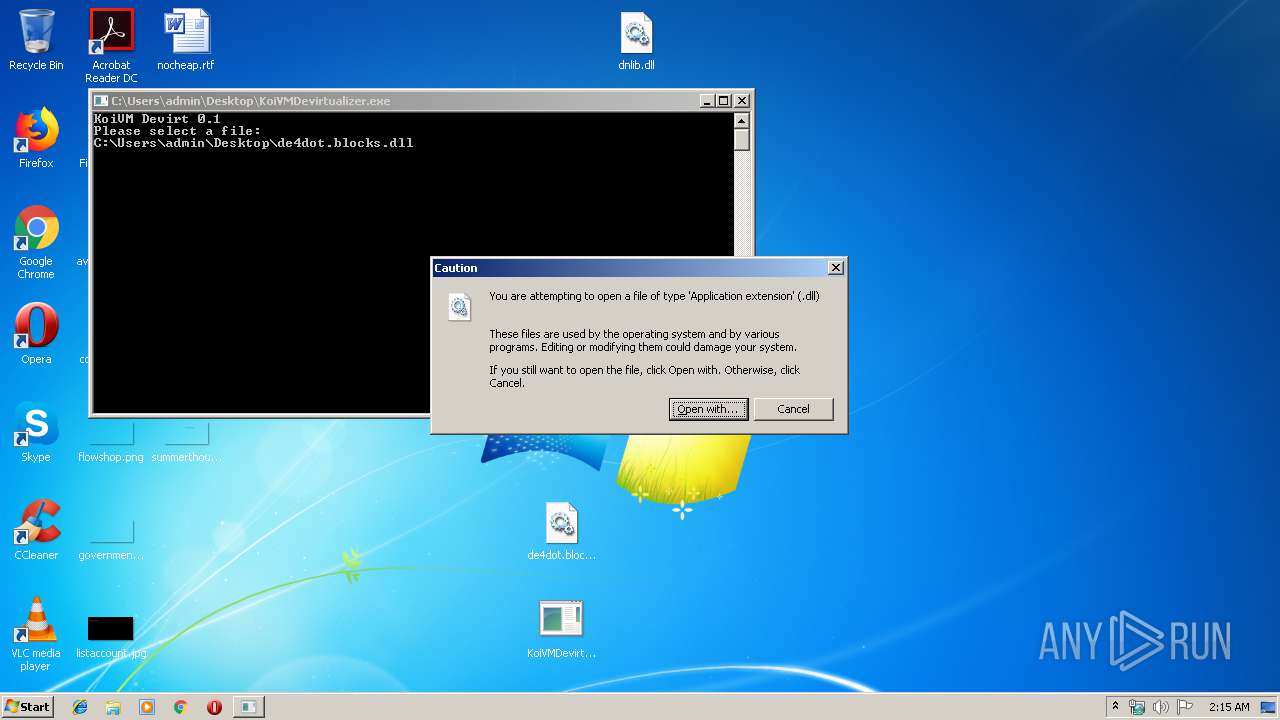
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 304)
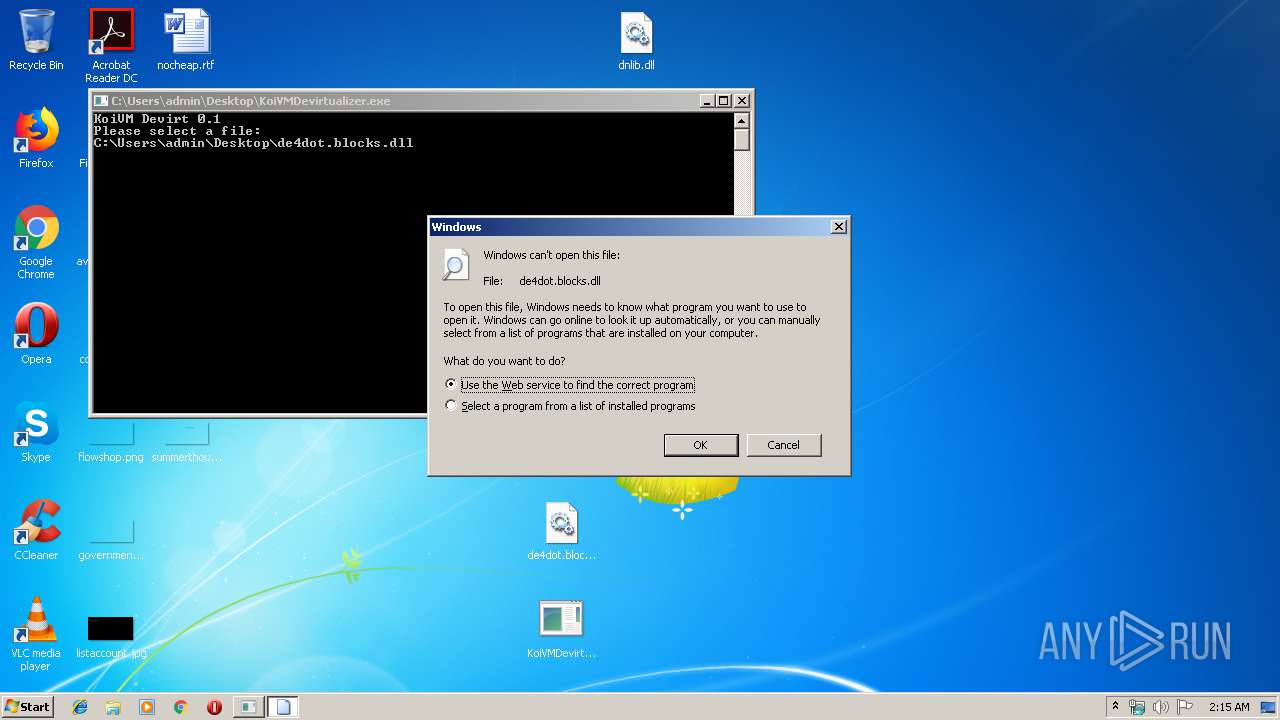
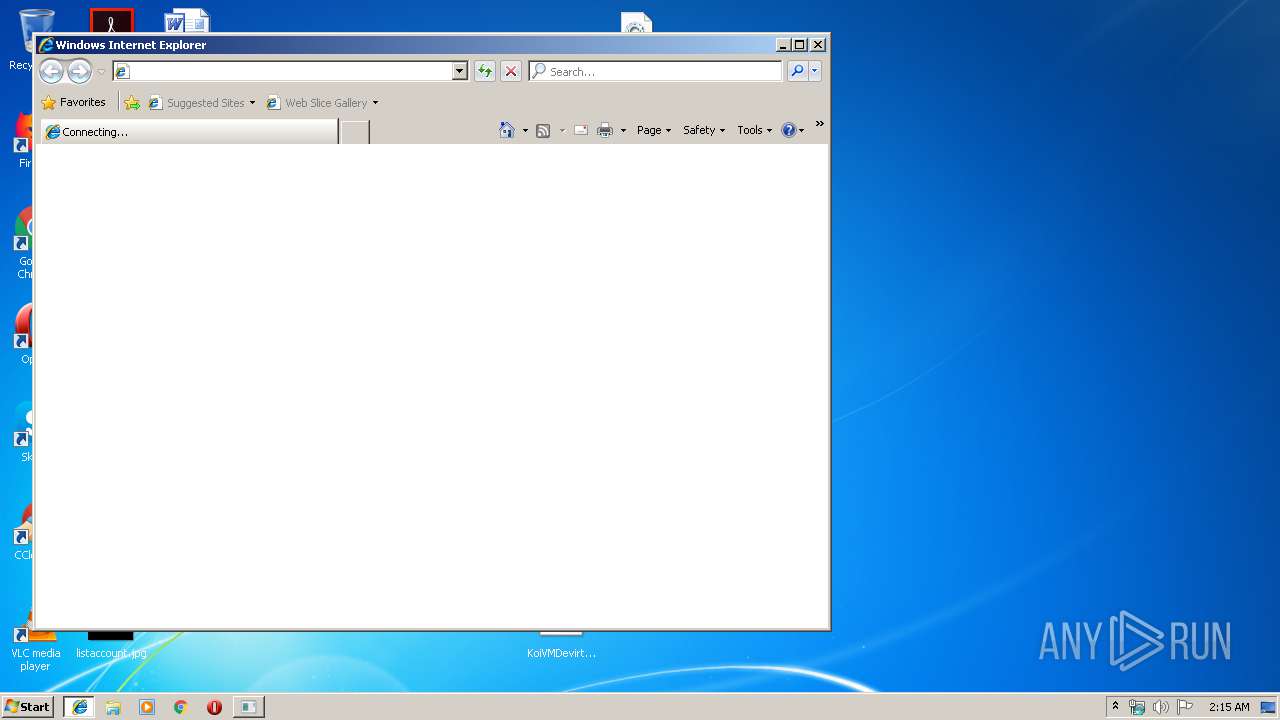
Starts Internet Explorer
- rundll32.exe (PID: 692)
Reads Internet Cache Settings
- explorer.exe (PID: 304)
INFO
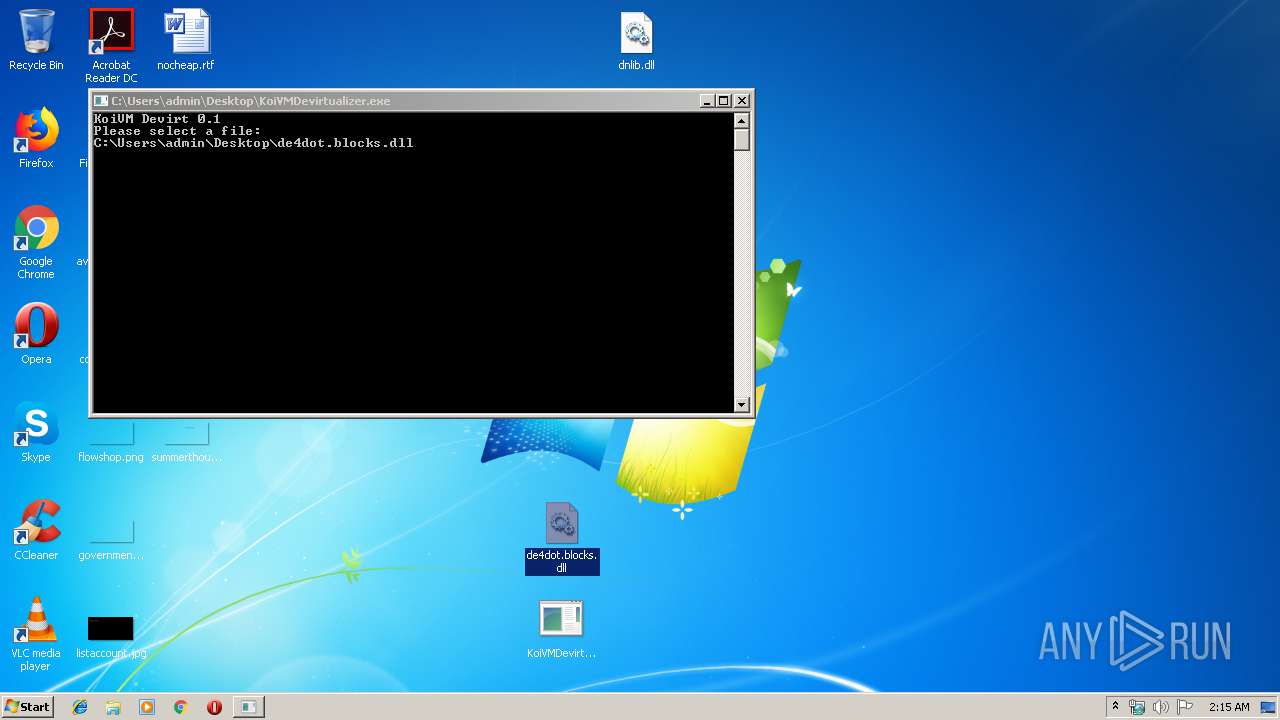
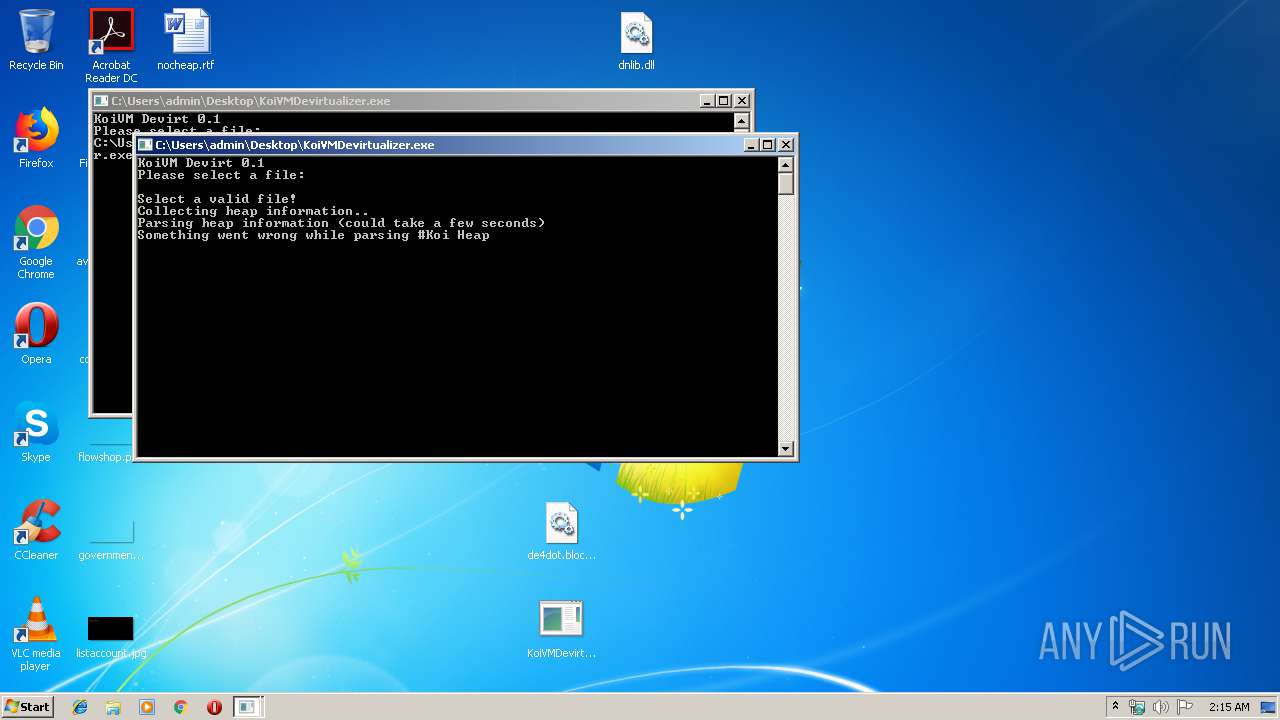
Manual execution by user
- KoiVMDevirtualizer.exe (PID: 2200)
Changes internet zones settings
- iexplore.exe (PID: 3852)
Creates files in the user directory
- iexplore.exe (PID: 4044)
Reads Internet Cache Settings
- iexplore.exe (PID: 4044)
Reads settings of System Certificates
- iexplore.exe (PID: 3852)
Reads internet explorer settings
- iexplore.exe (PID: 4044)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3852)
Changes settings of System certificates
- iexplore.exe (PID: 3852)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 4044)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
41
Monitored processes
8
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 692 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\de4dot.blocks.dll | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1724 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe8_ Global\UsGthrCtrlFltPipeMssGthrPipe8 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2200 | "C:\Users\admin\Desktop\KoiVMDevirtualizer.exe" | C:\Users\admin\Desktop\KoiVMDevirtualizer.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: KoivmDevirt Exit code: 3221225786 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3020 | "C:\Users\admin\Desktop\KoiVMDevirtualizer.exe" | C:\Users\admin\Desktop\KoiVMDevirtualizer.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: KoivmDevirt Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3456 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\ConfuserEx KoiVMDEVIRT.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3852 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4044 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3852 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 820
Read events
1 706
Write events
110
Delete events
4
Modification events
| (PID) Process: | (3456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3456) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\ConfuserEx KoiVMDEVIRT.rar | |||
| (PID) Process: | (3456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (304) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.rar\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
| (PID) Process: | (304) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.rar\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
Executable files
3
Suspicious files
2
Text files
31
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
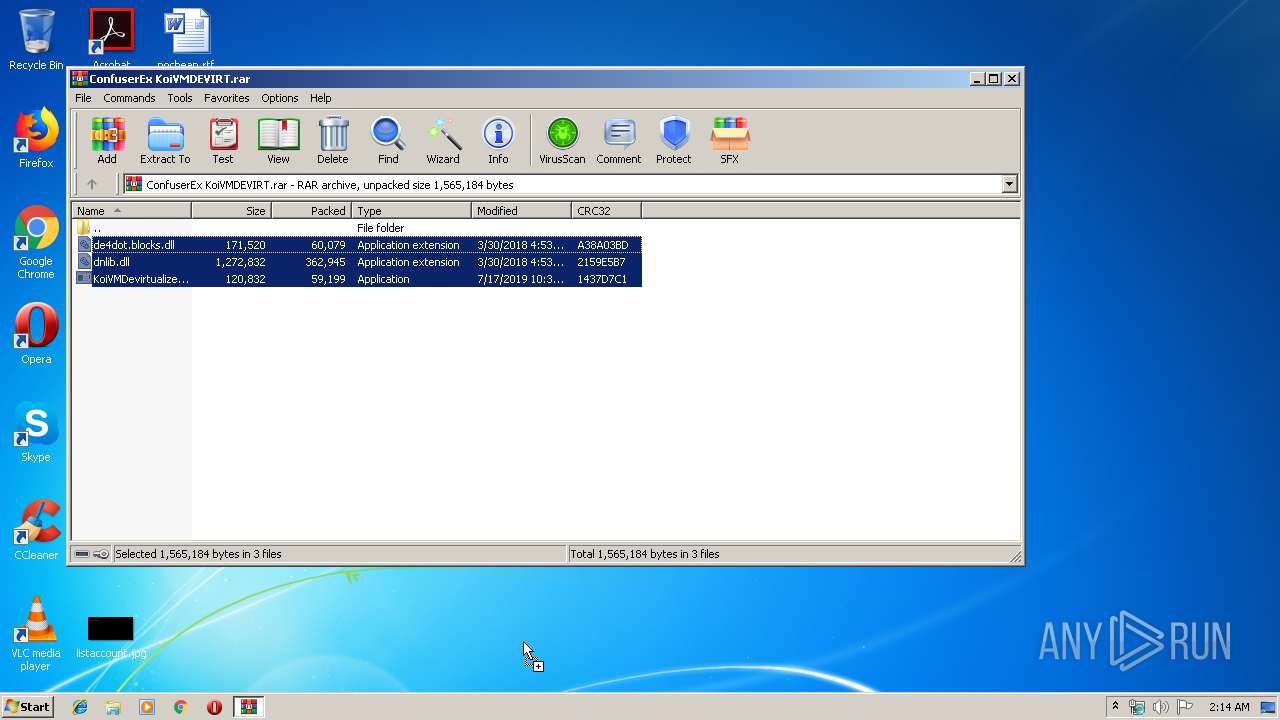
| 3456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3456.49424\KoiVMDevirtualizer.exe | — | |
MD5:— | SHA256:— | |||
| 3456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3456.49424\dnlib.dll | — | |
MD5:— | SHA256:— | |||
| 3456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3456.49424\de4dot.blocks.dll | — | |
MD5:— | SHA256:— | |||
| 3852 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3852 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 4044 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@bing[2].txt | — | |
MD5:— | SHA256:— | |||
| 4044 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\E6O7JV3K\search[1].txt | — | |
MD5:— | SHA256:— | |||
| 304 | explorer.exe | C:\Users\admin\Desktop\de4dot.blocks.dll | executable | |
MD5:— | SHA256:— | |||
| 304 | explorer.exe | C:\Users\admin\Desktop\KoiVMDevirtualizer.exe | executable | |
MD5:— | SHA256:— | |||
| 4044 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
11
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4044 | iexplore.exe | GET | 302 | 2.19.38.59:80 | http://go.microsoft.com/fwlink/?LinkId=57426&Ext=dll | unknown | — | — | whitelisted |
4044 | iexplore.exe | GET | 301 | 2.16.186.27:80 | http://shell.windows.com/fileassoc/fileassoc.asp?Ext=dll | unknown | — | — | whitelisted |
3852 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3852 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
4044 | iexplore.exe | 2.19.38.59:80 | go.microsoft.com | Akamai International B.V. | — | whitelisted |
4044 | iexplore.exe | 2.16.186.27:80 | shell.windows.com | Akamai International B.V. | — | whitelisted |
4044 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3852 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
4044 | iexplore.exe | 40.90.23.236:443 | login.live.com | Microsoft Corporation | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
shell.windows.com |
| whitelisted |
login.live.com |
| whitelisted |