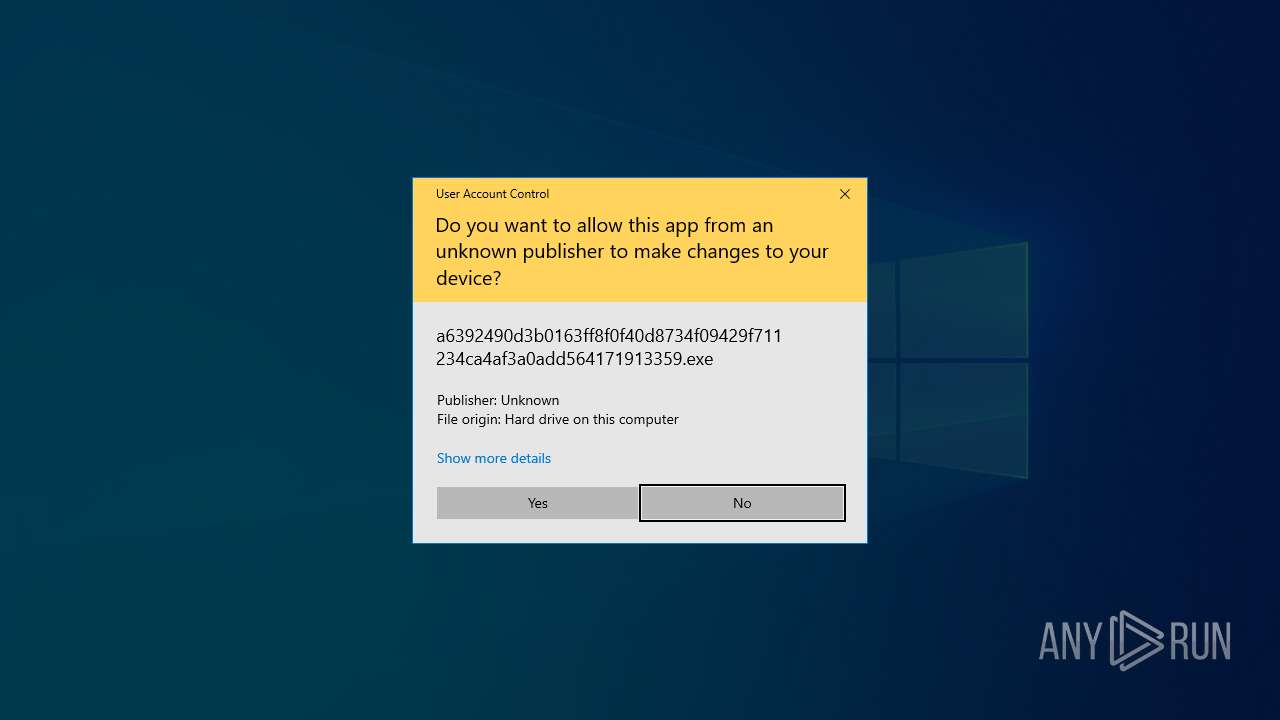
| File name: | a6392490d3b0163ff8f0f40d8734f09429f711234ca4af3a0add564171913359.exe |
| Full analysis: | https://app.any.run/tasks/734ac7e1-b637-425b-a1cc-c3b416e583a4 |
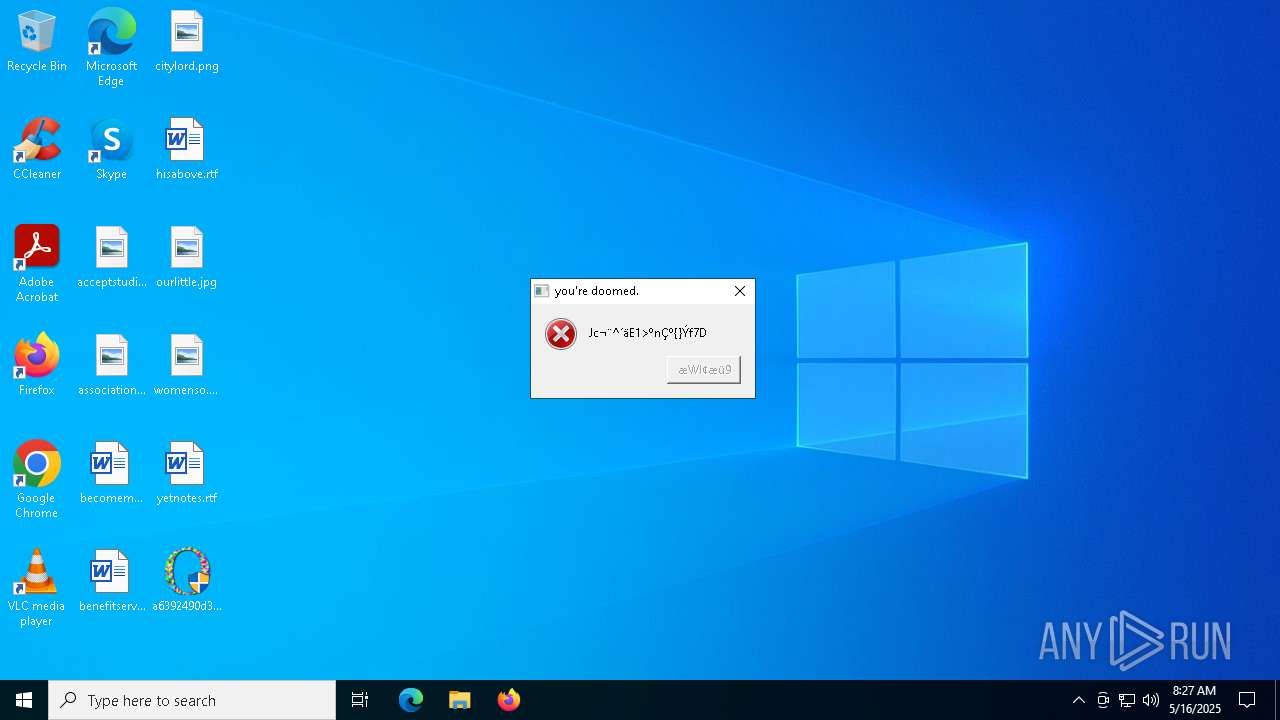
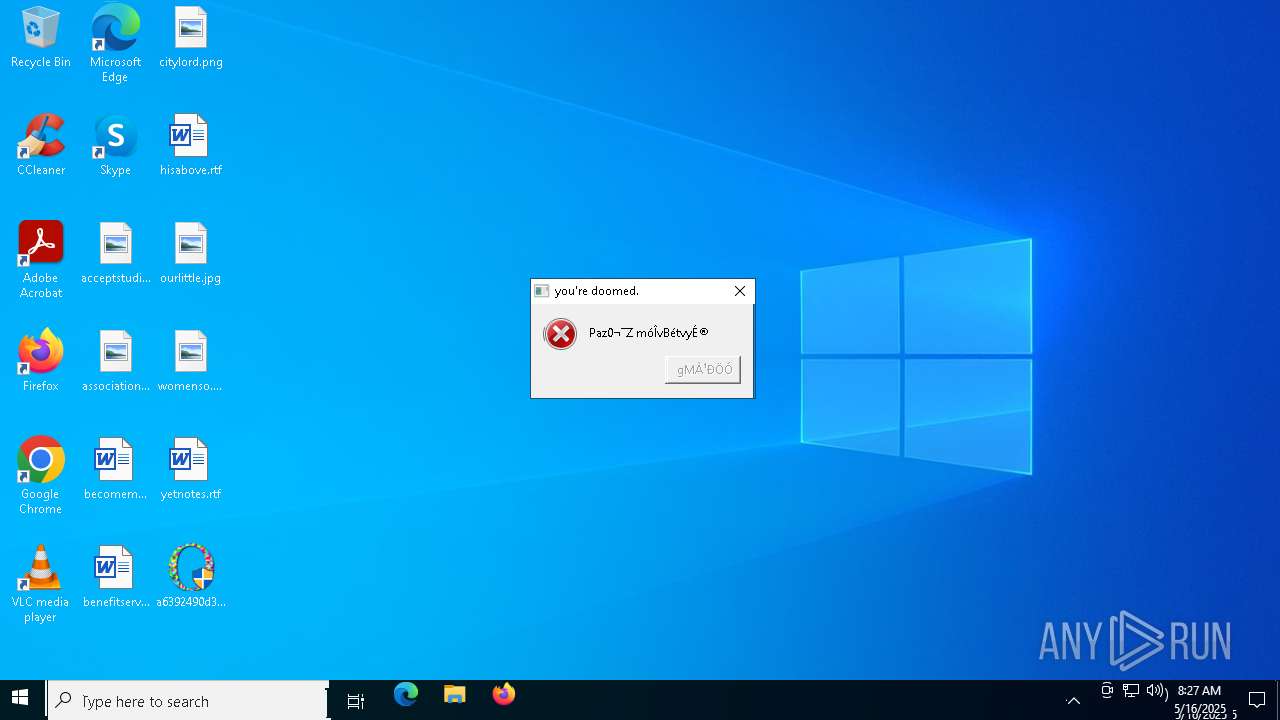
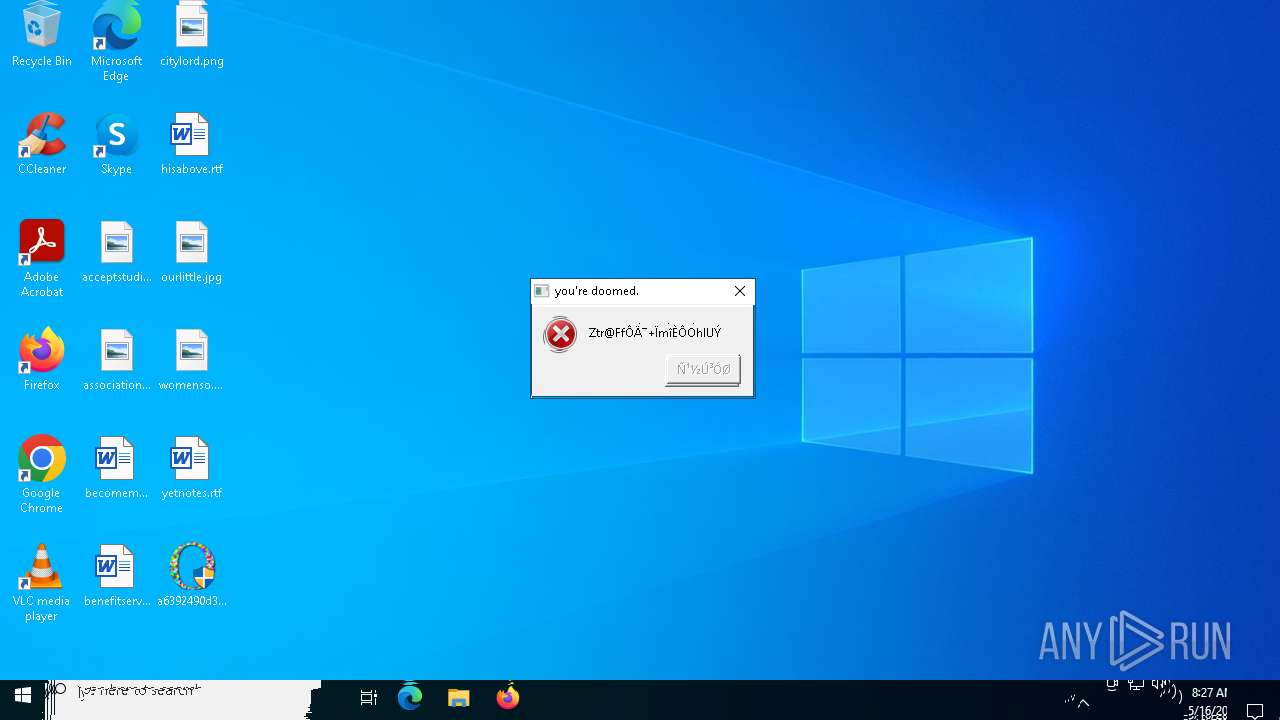
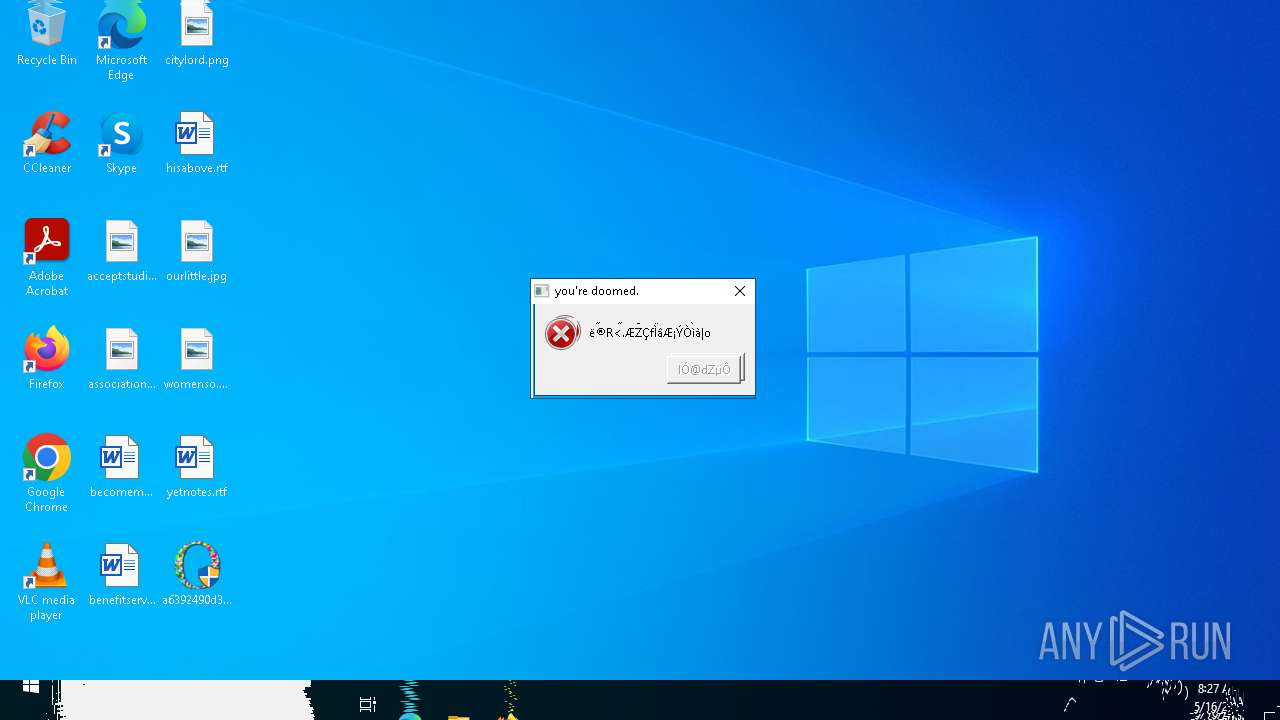
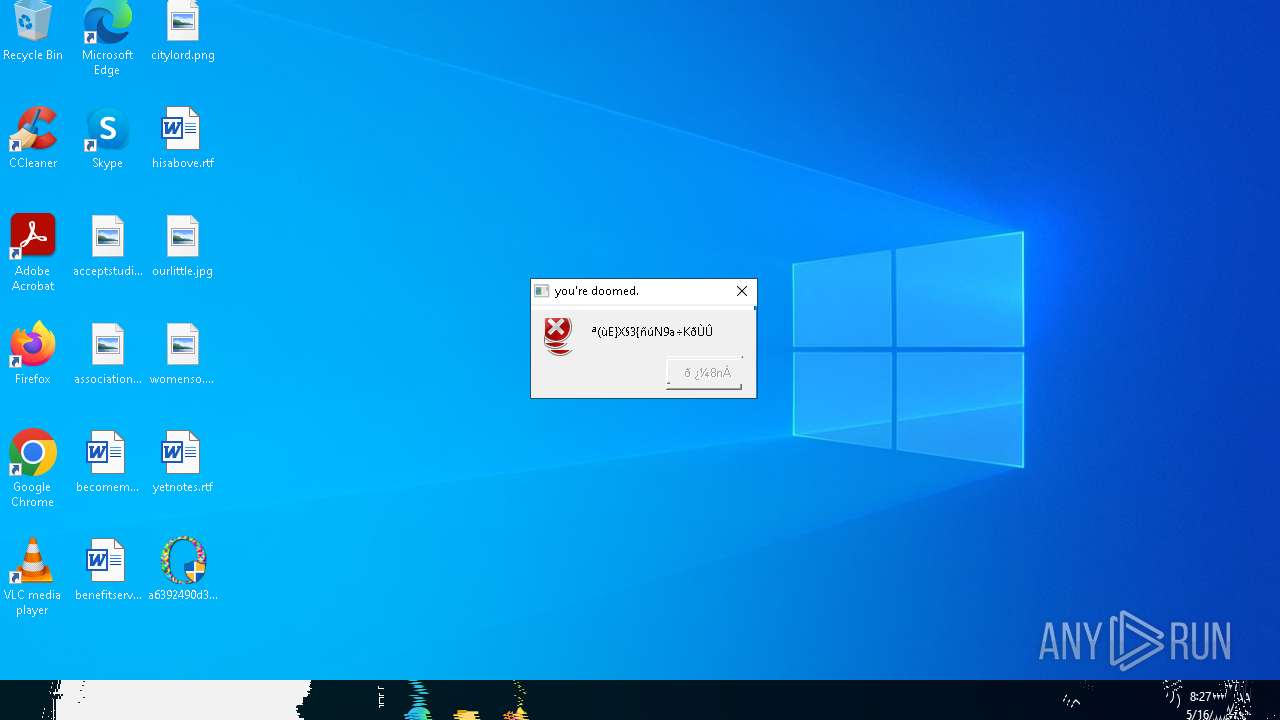
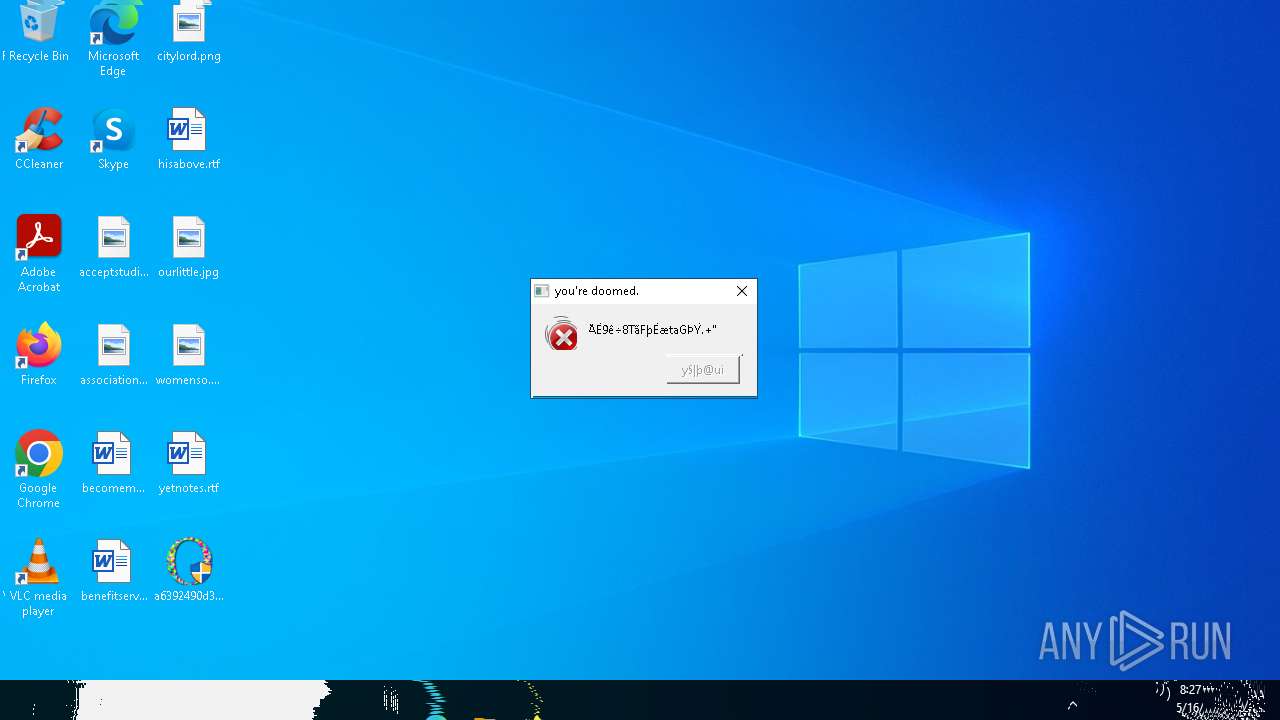
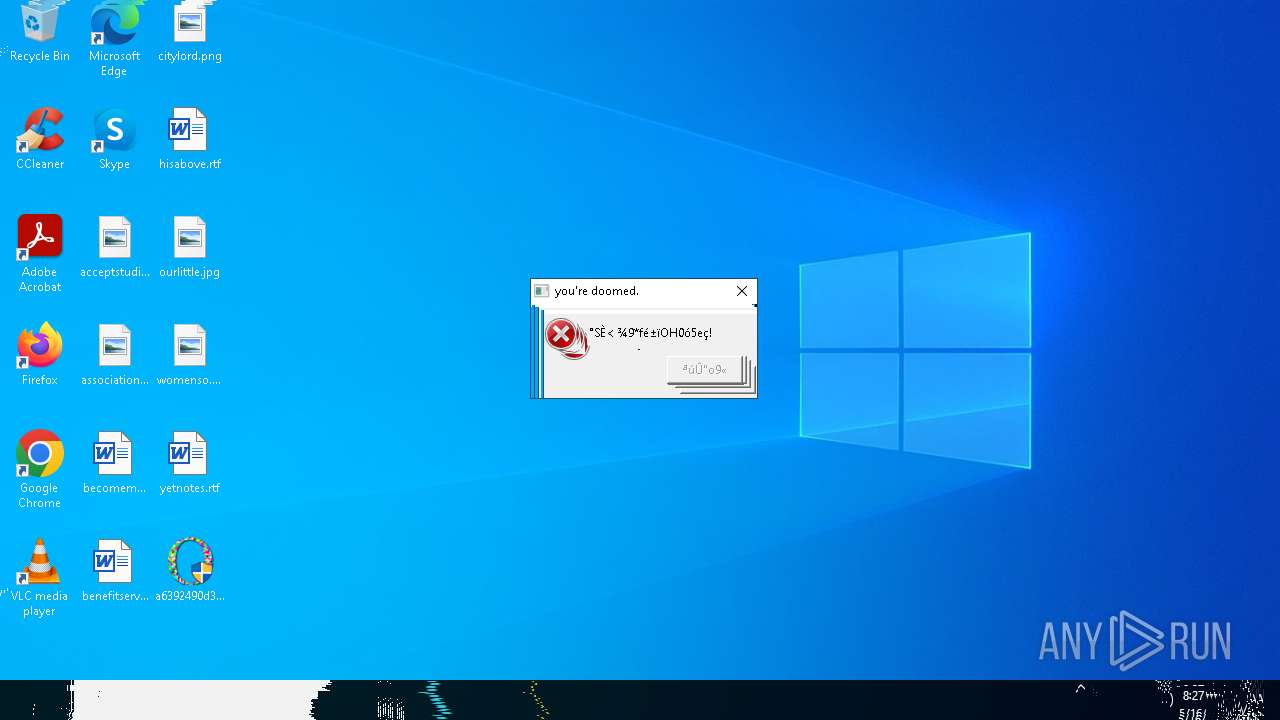
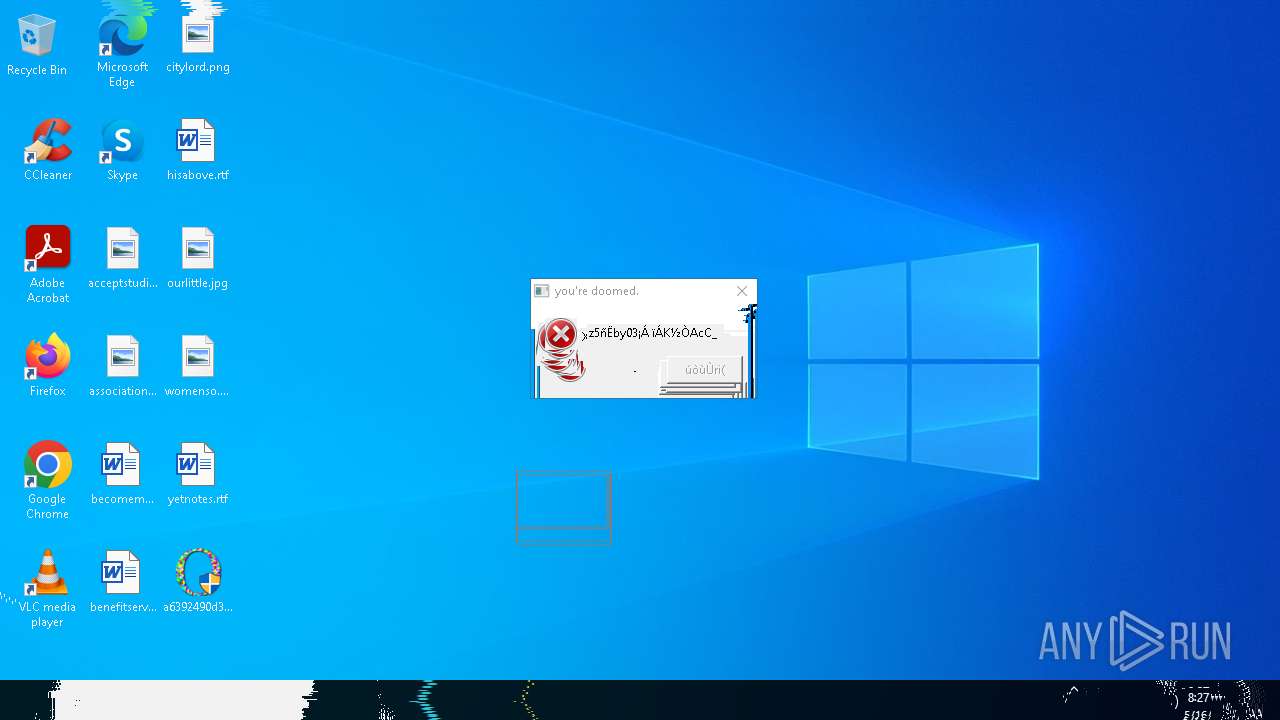
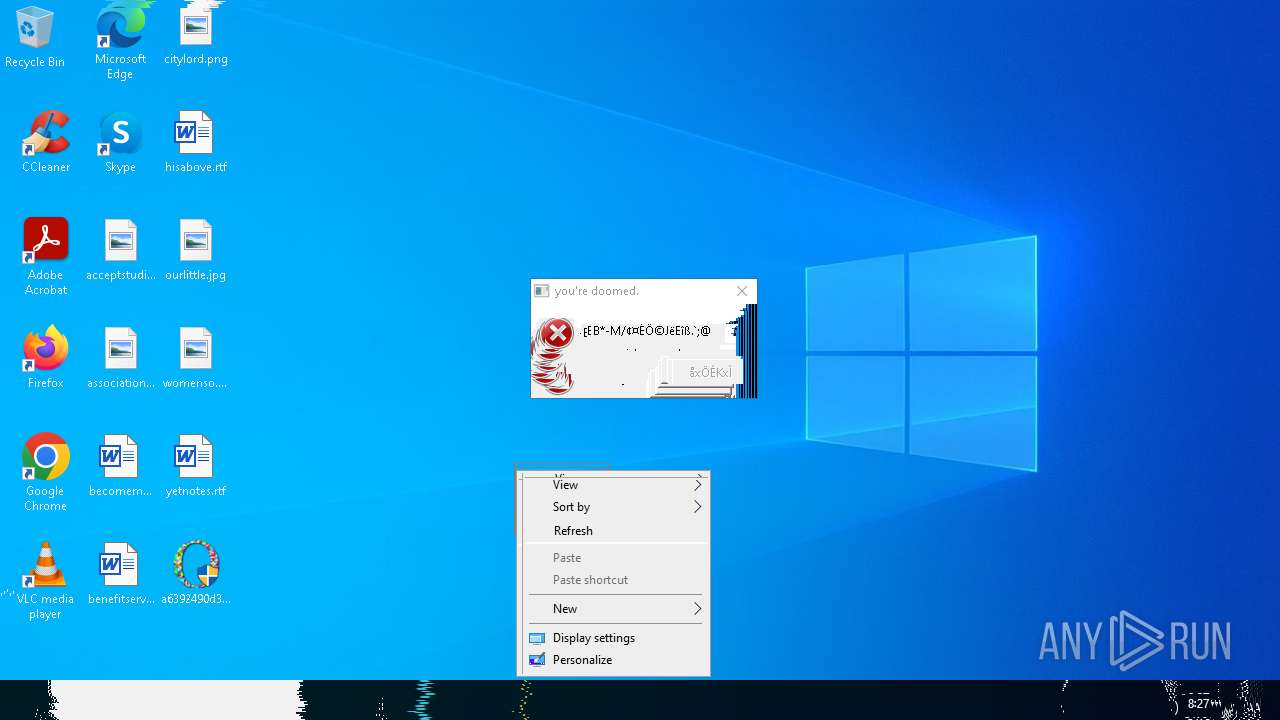
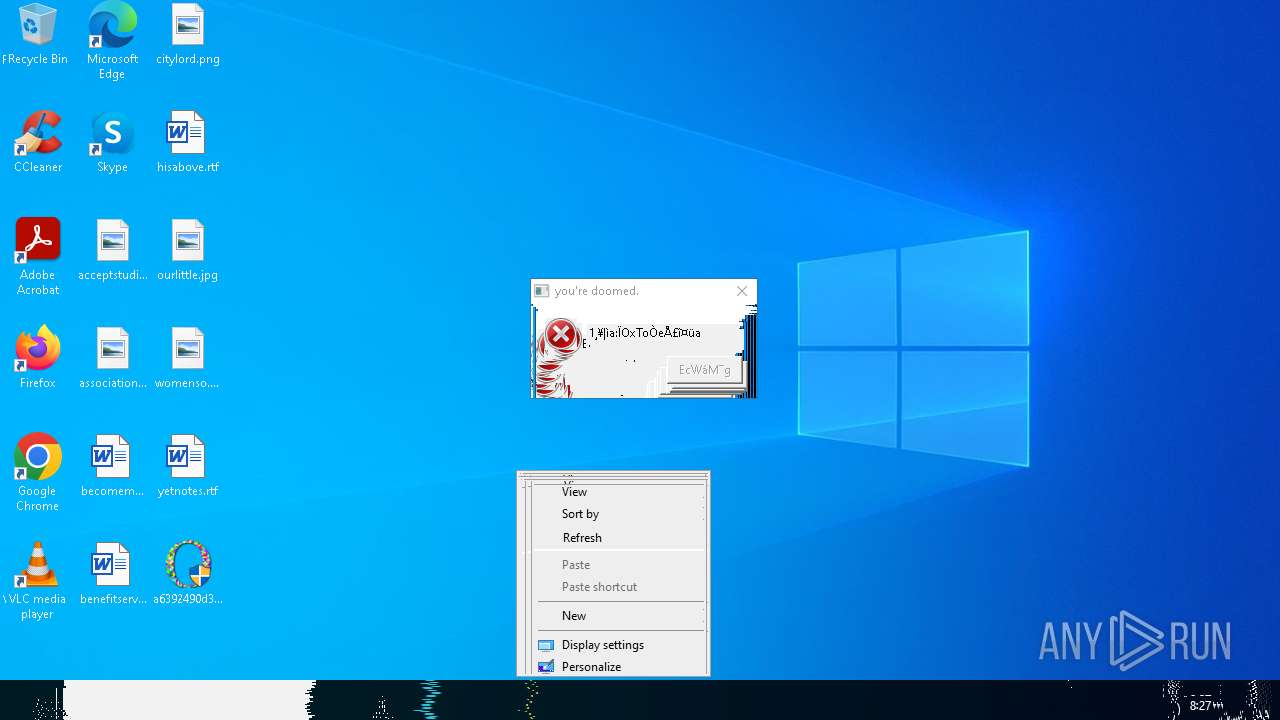
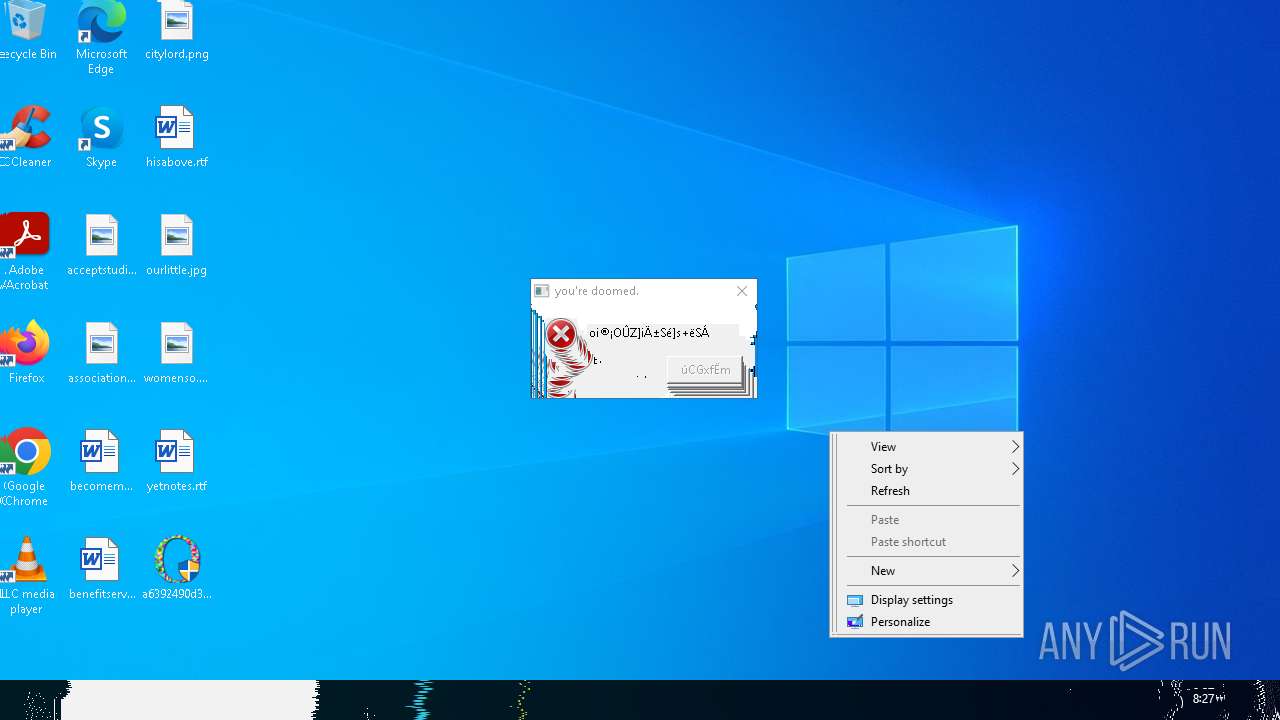
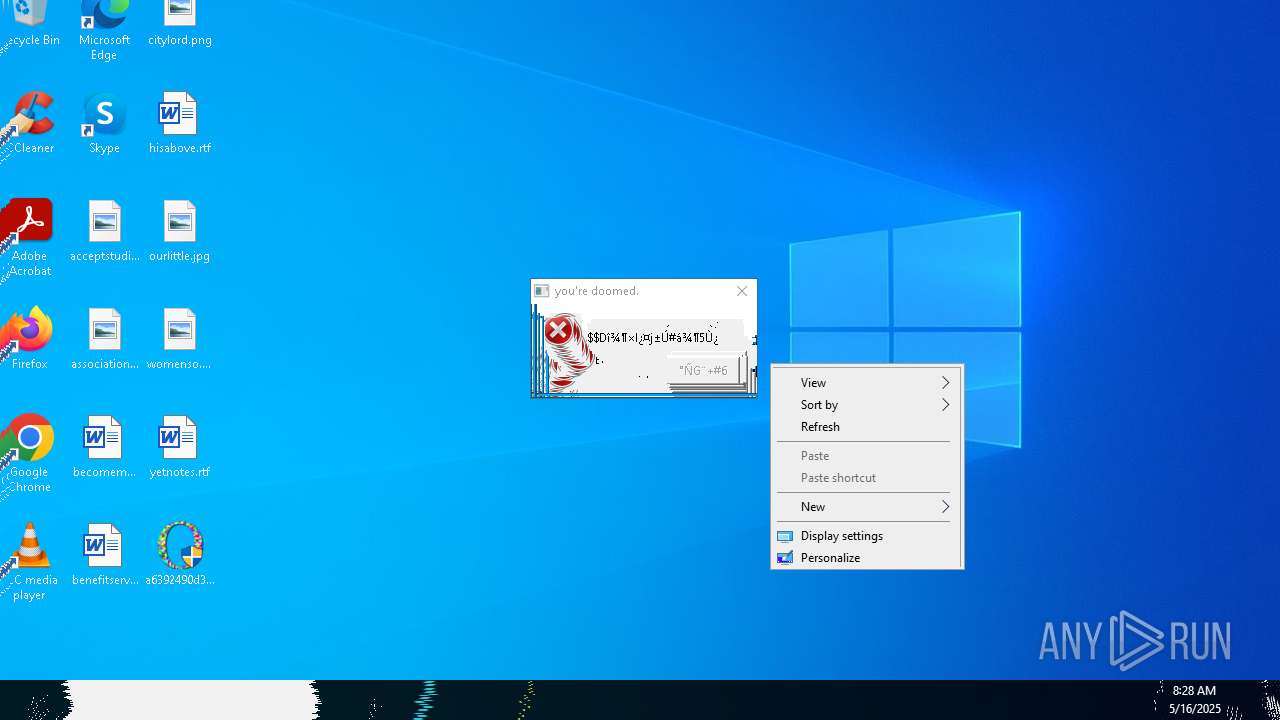
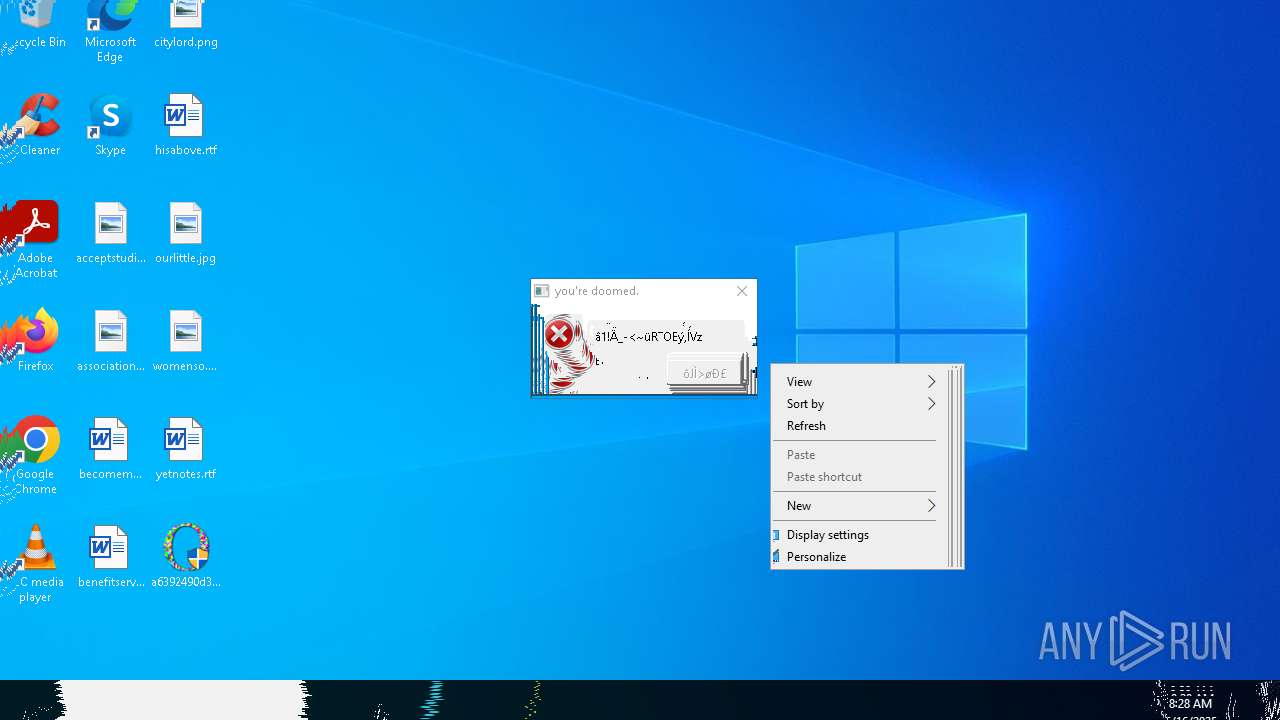
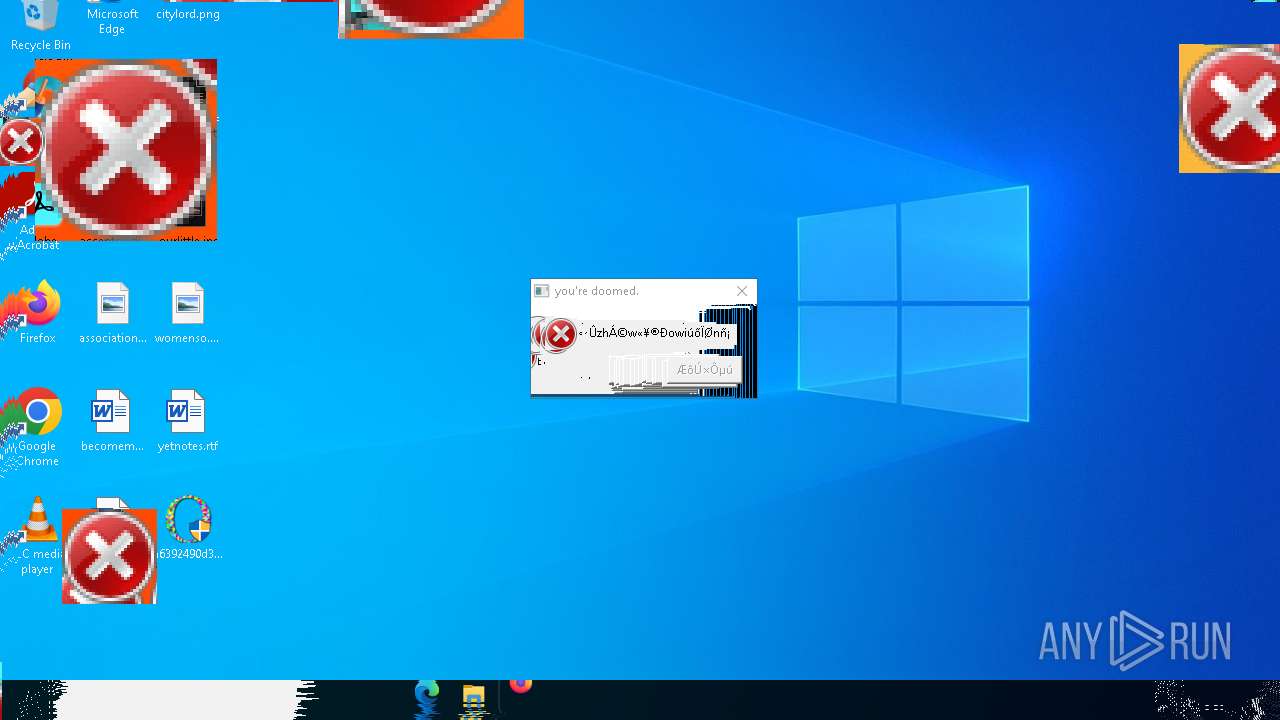
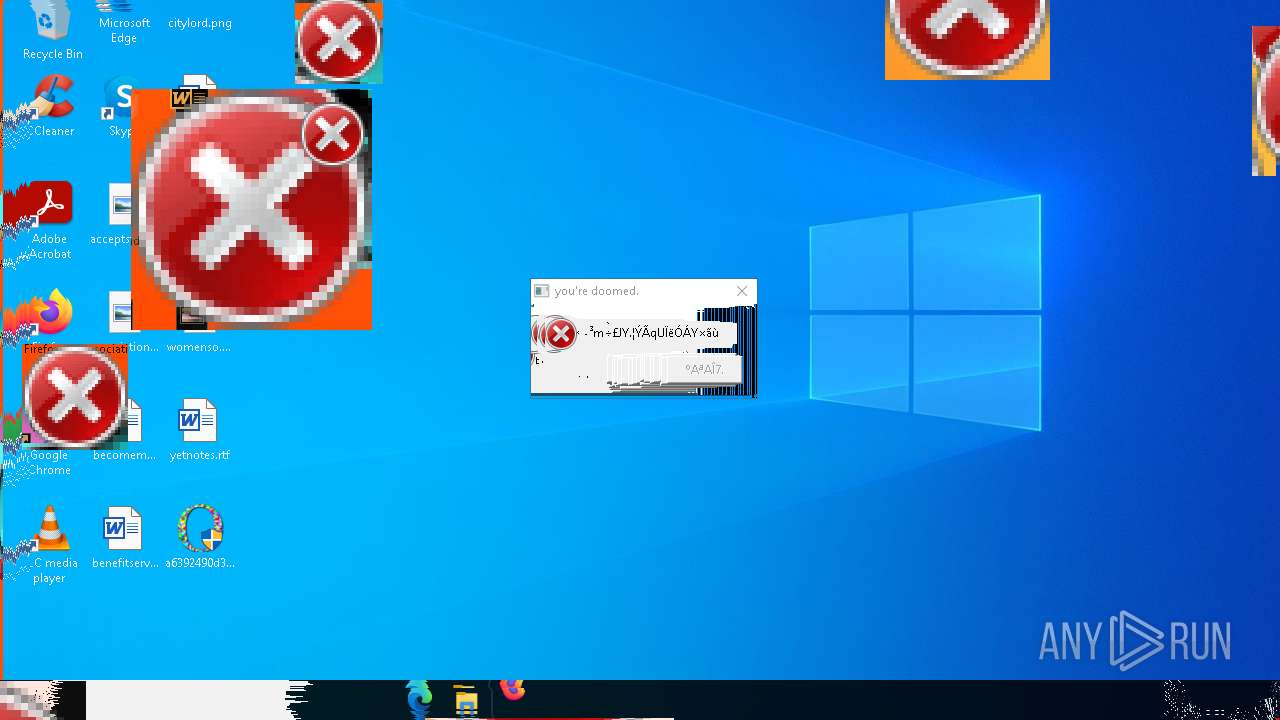
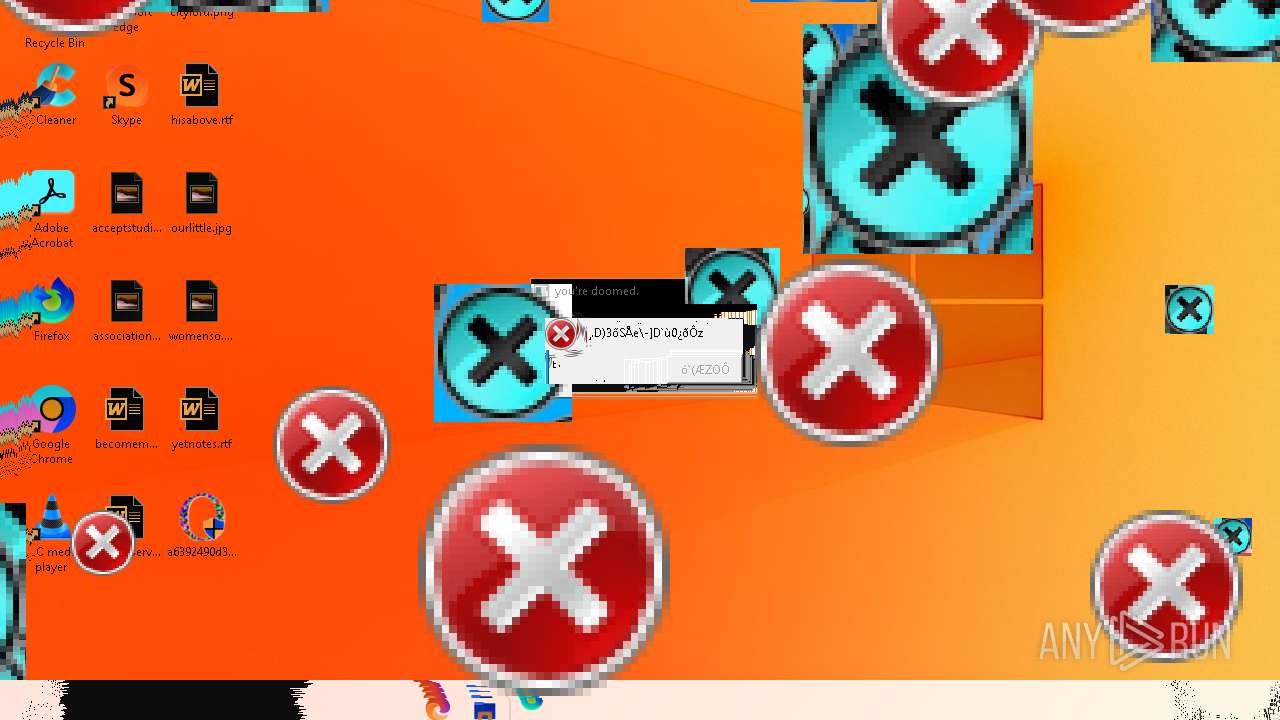
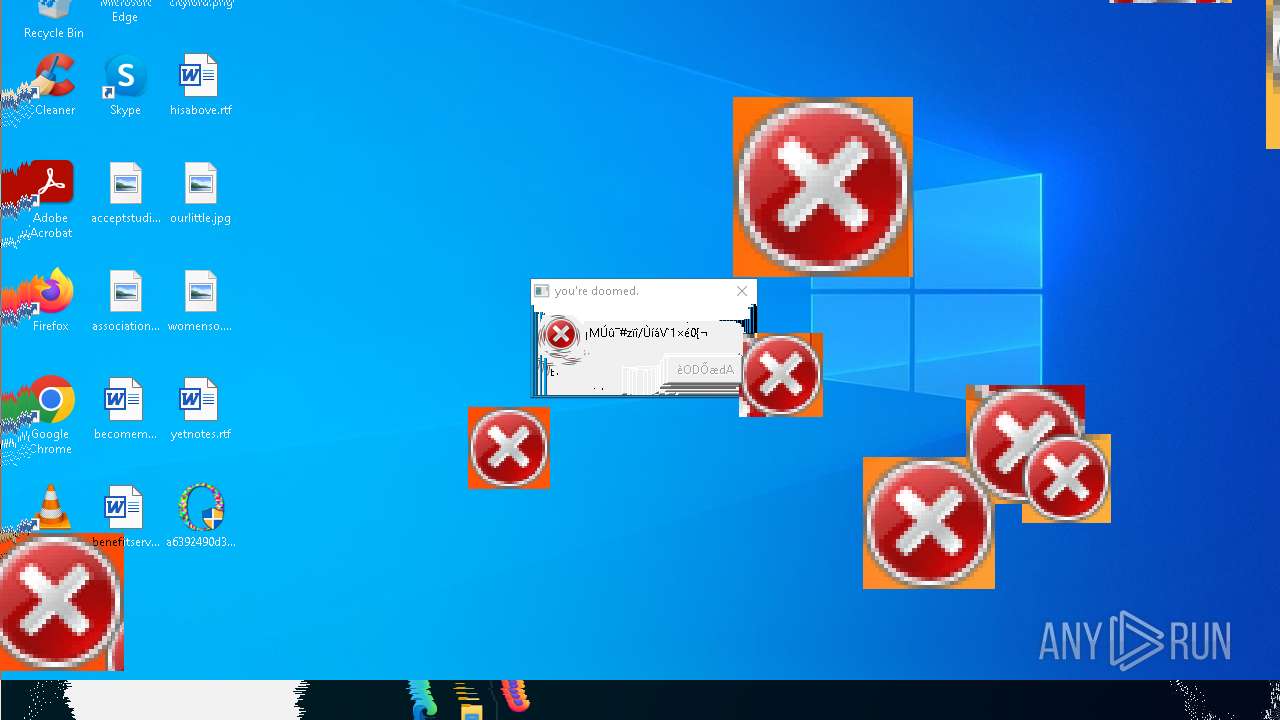
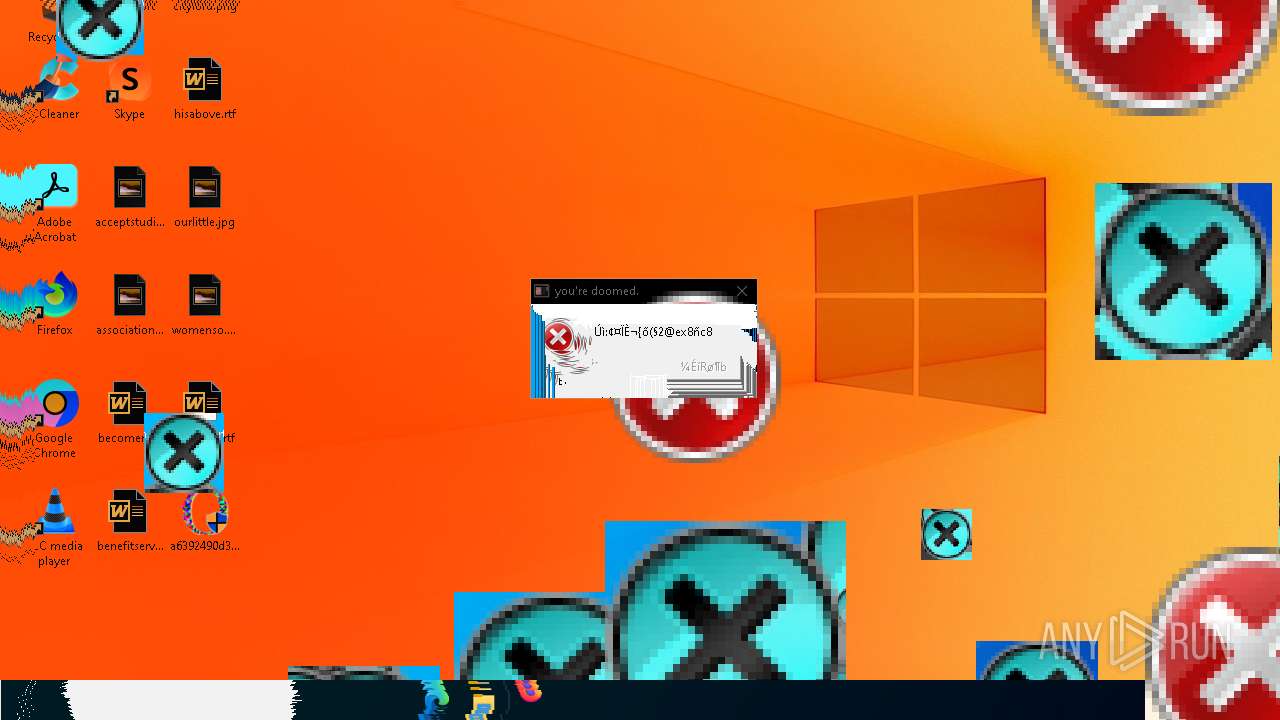
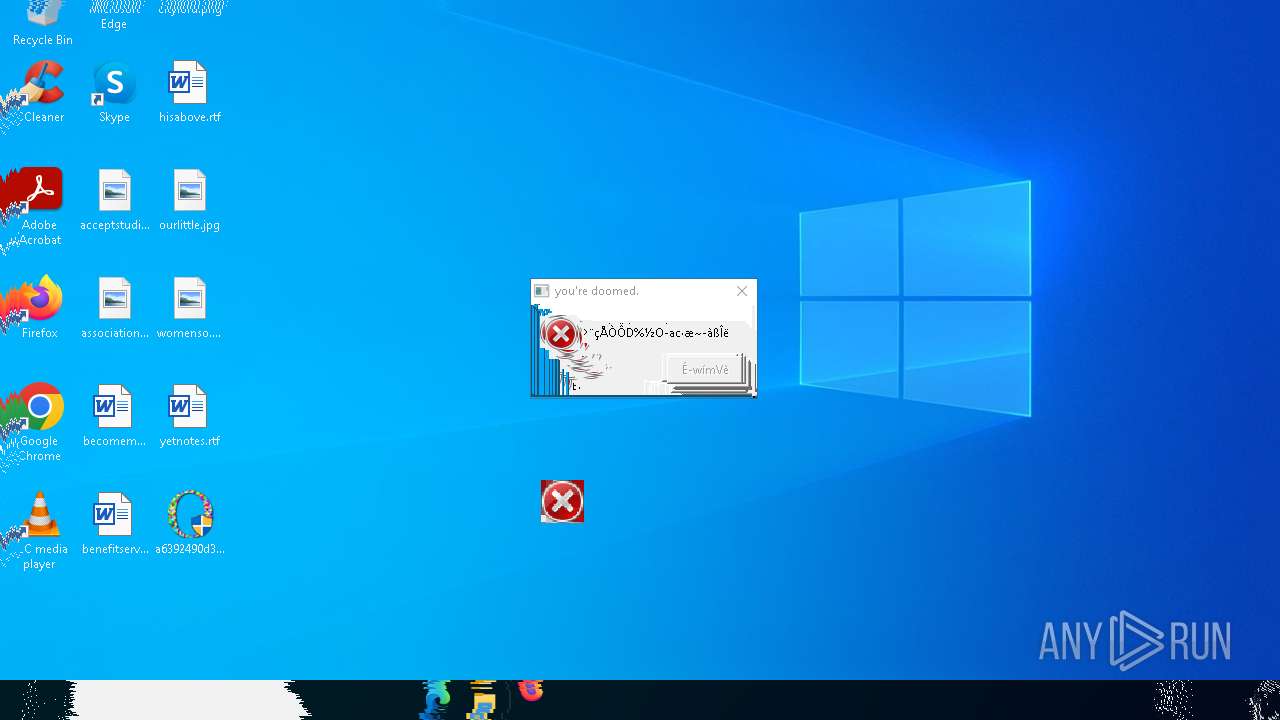
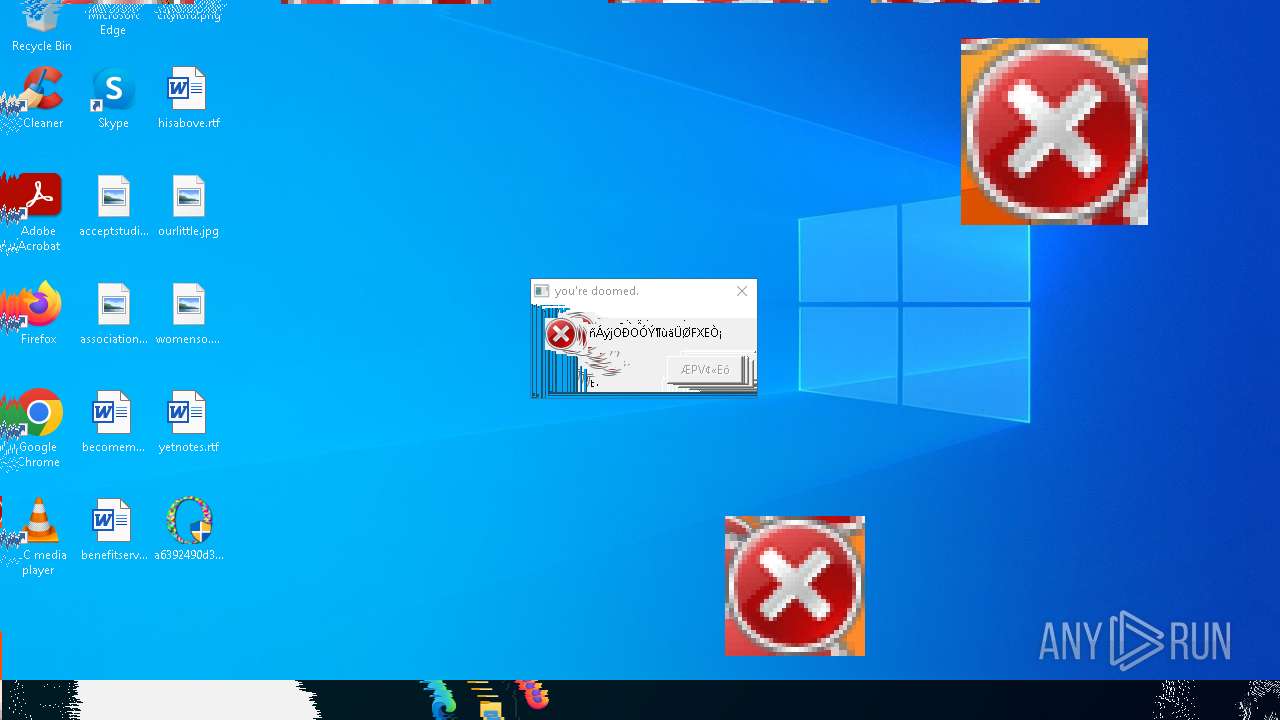
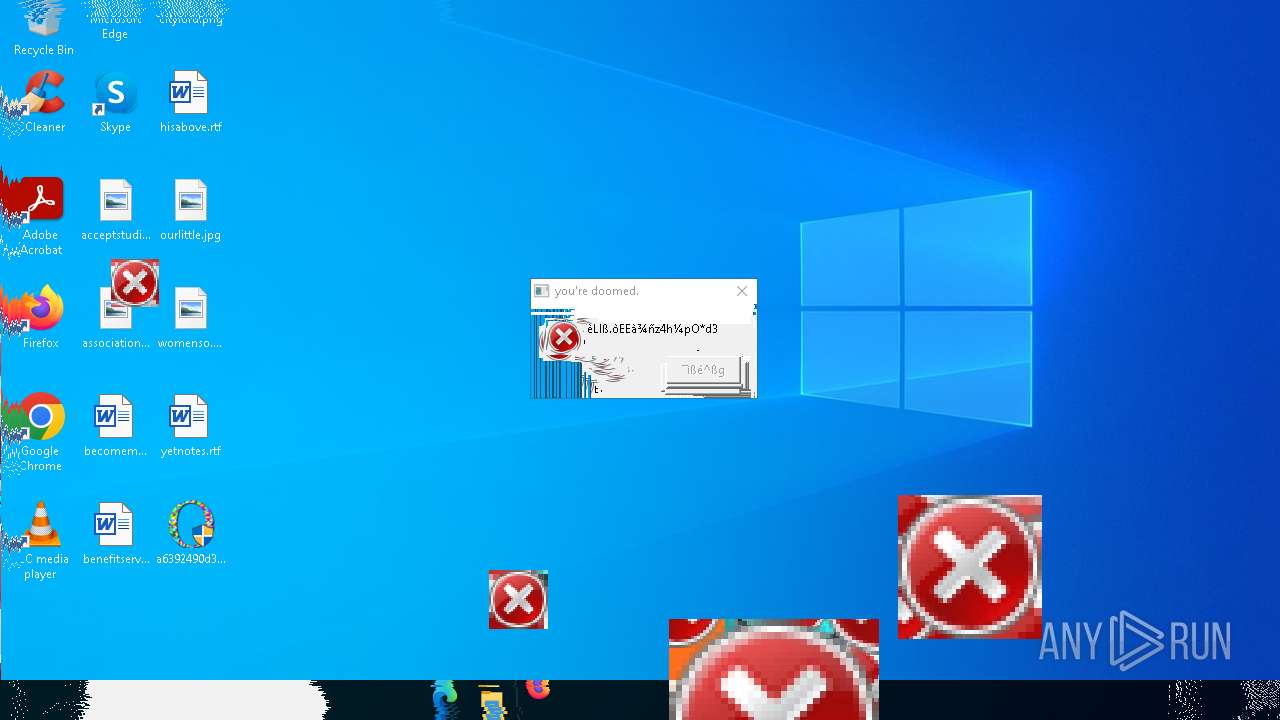
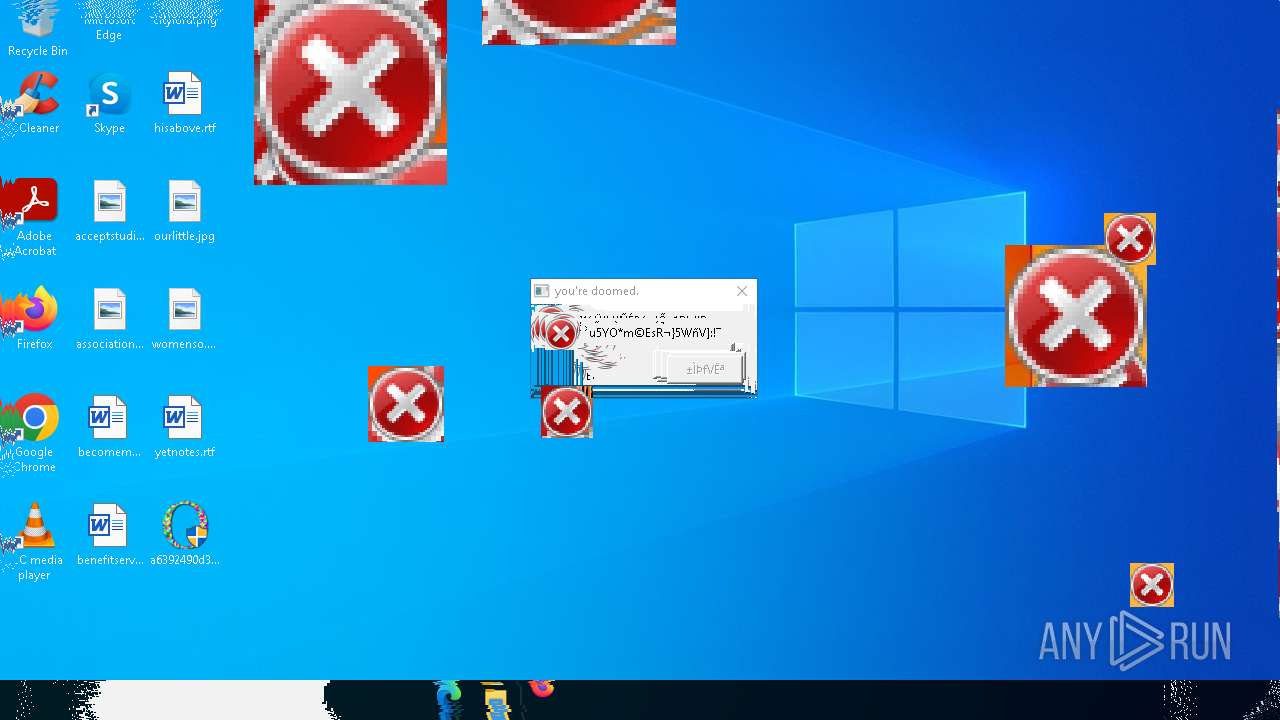
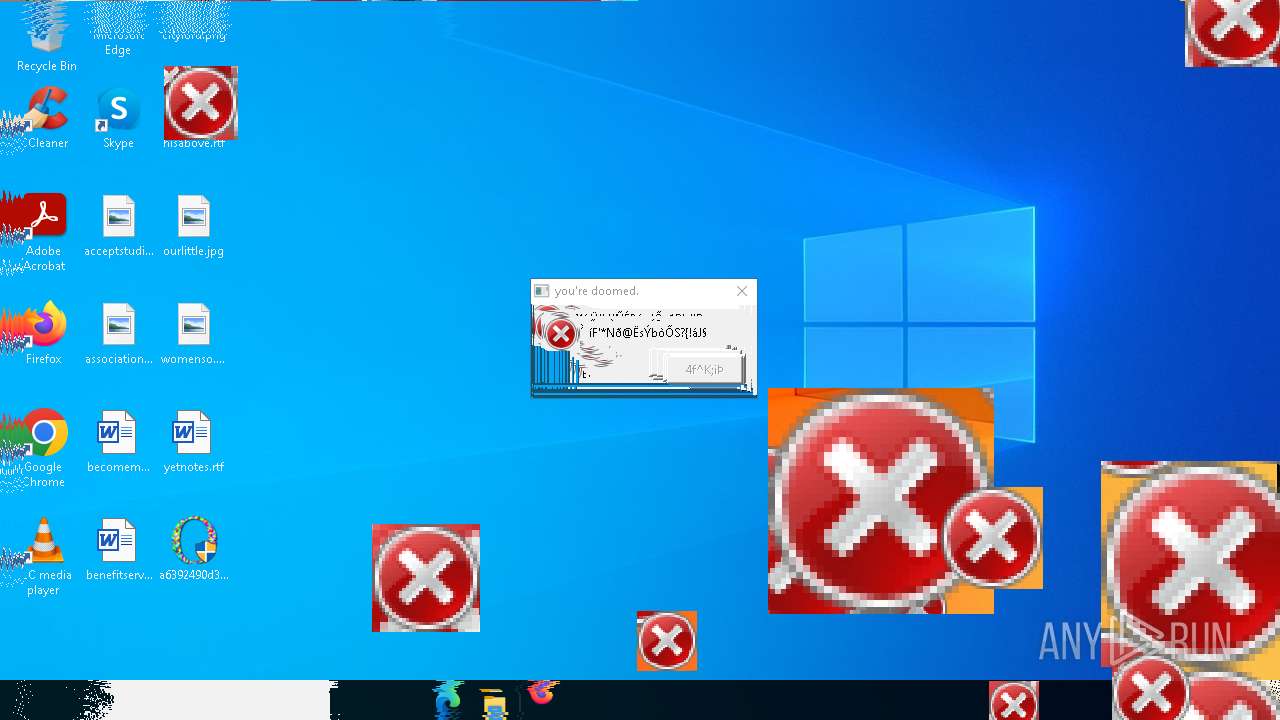
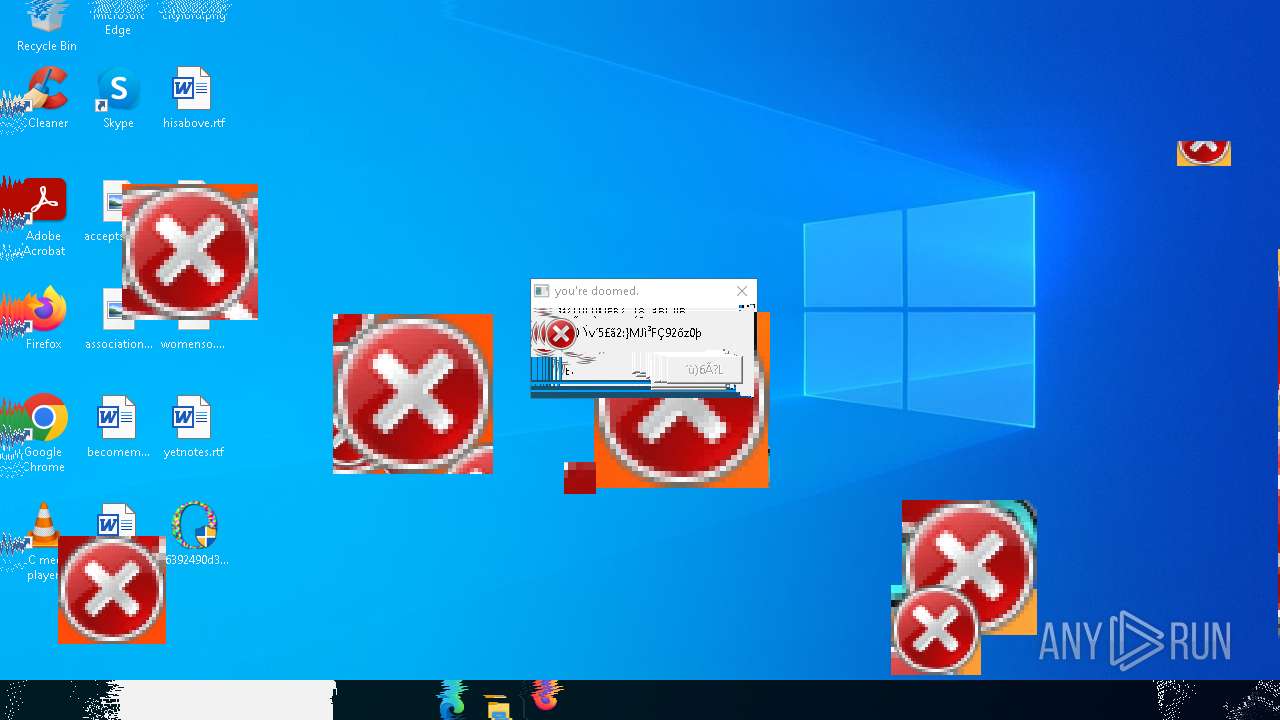
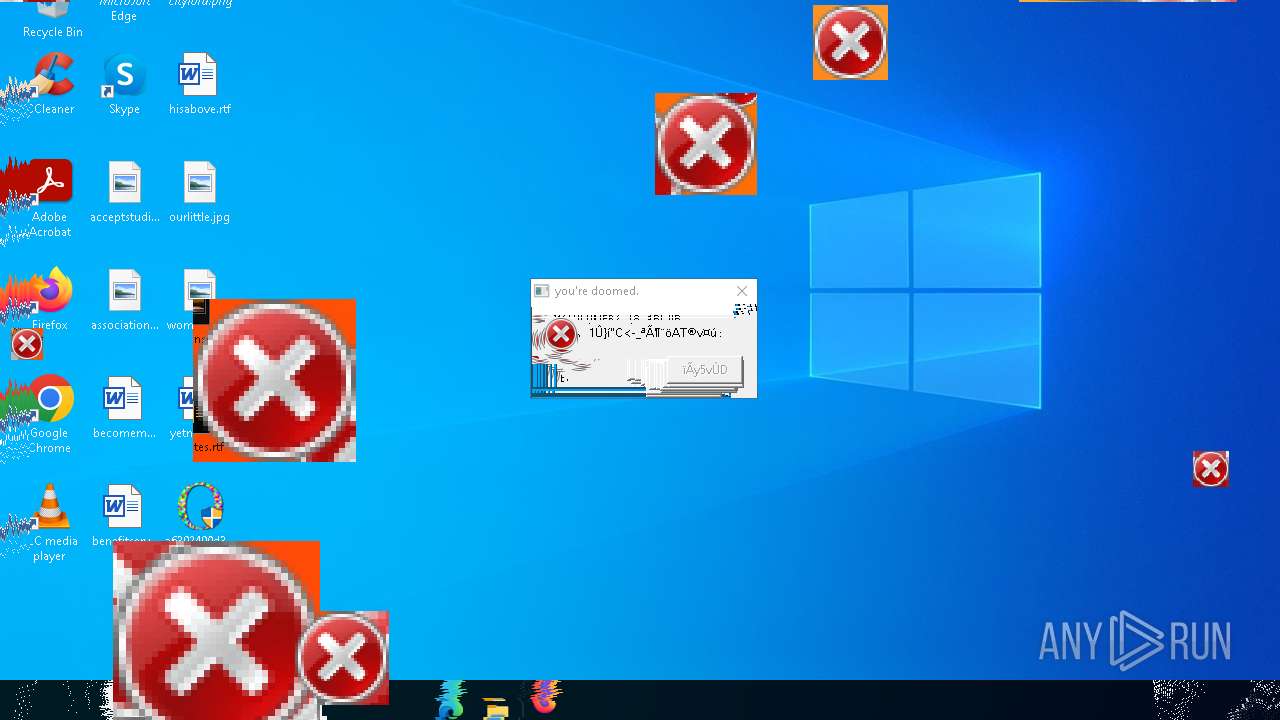
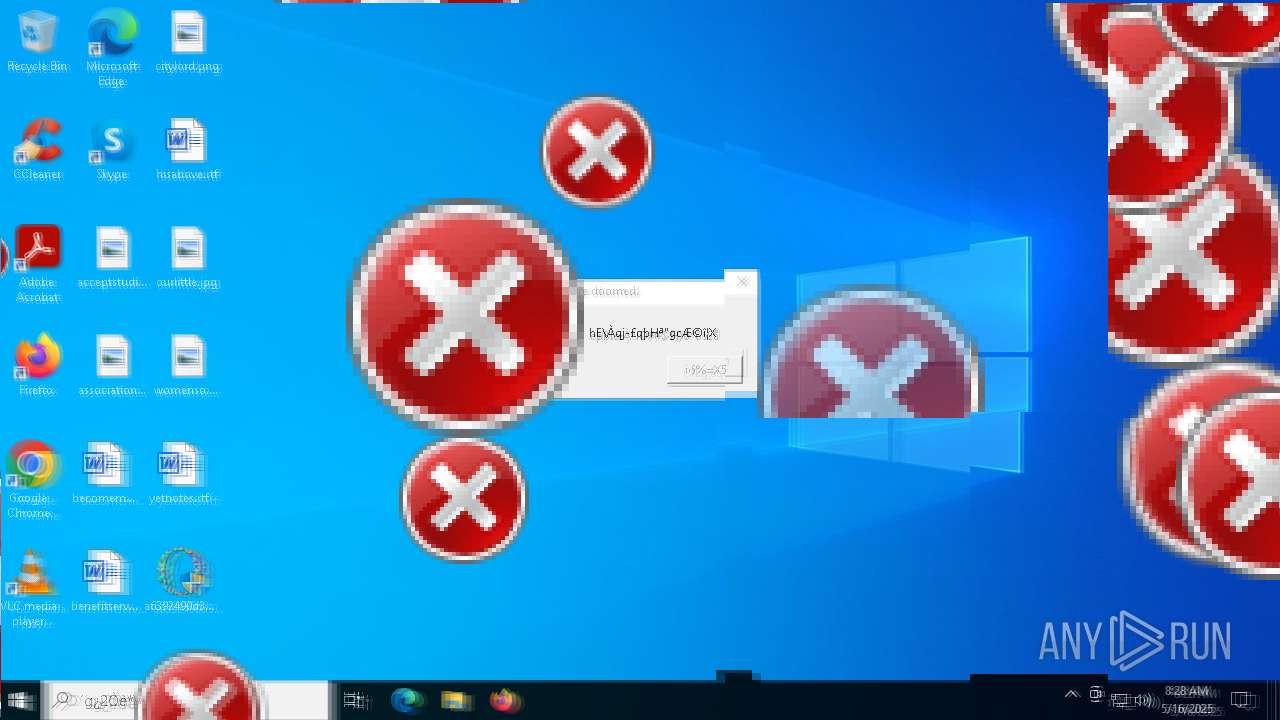
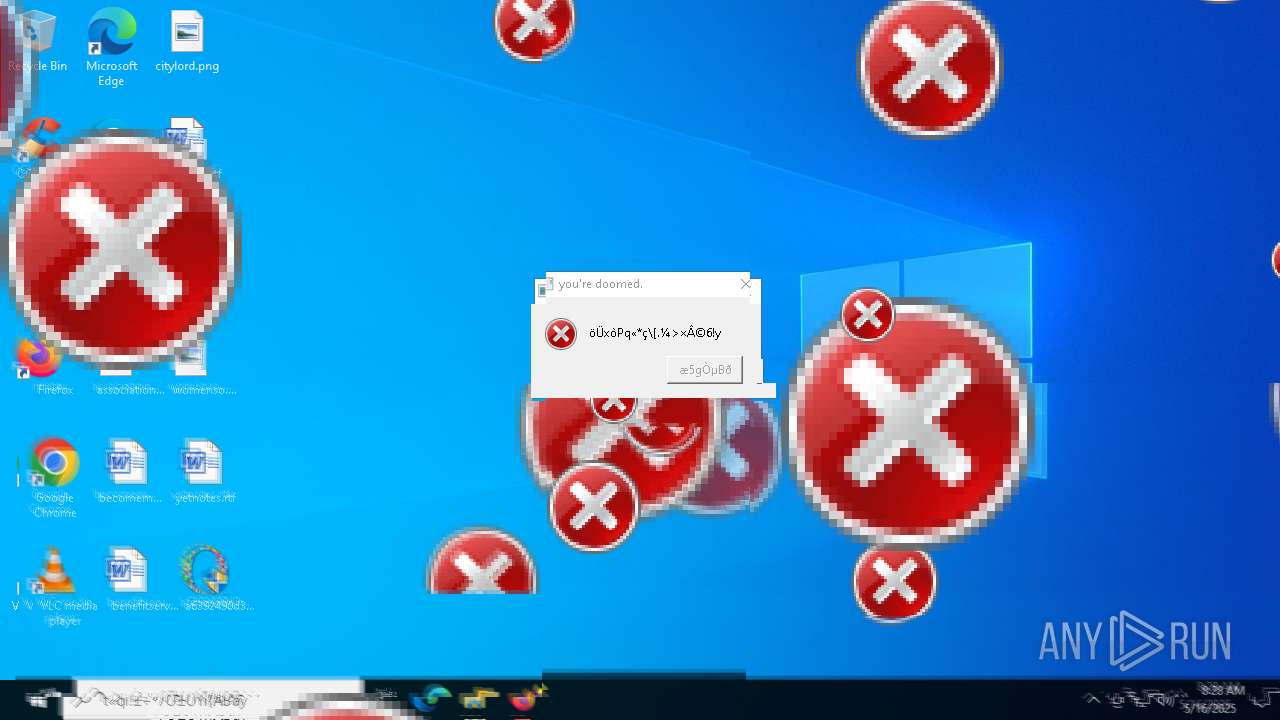
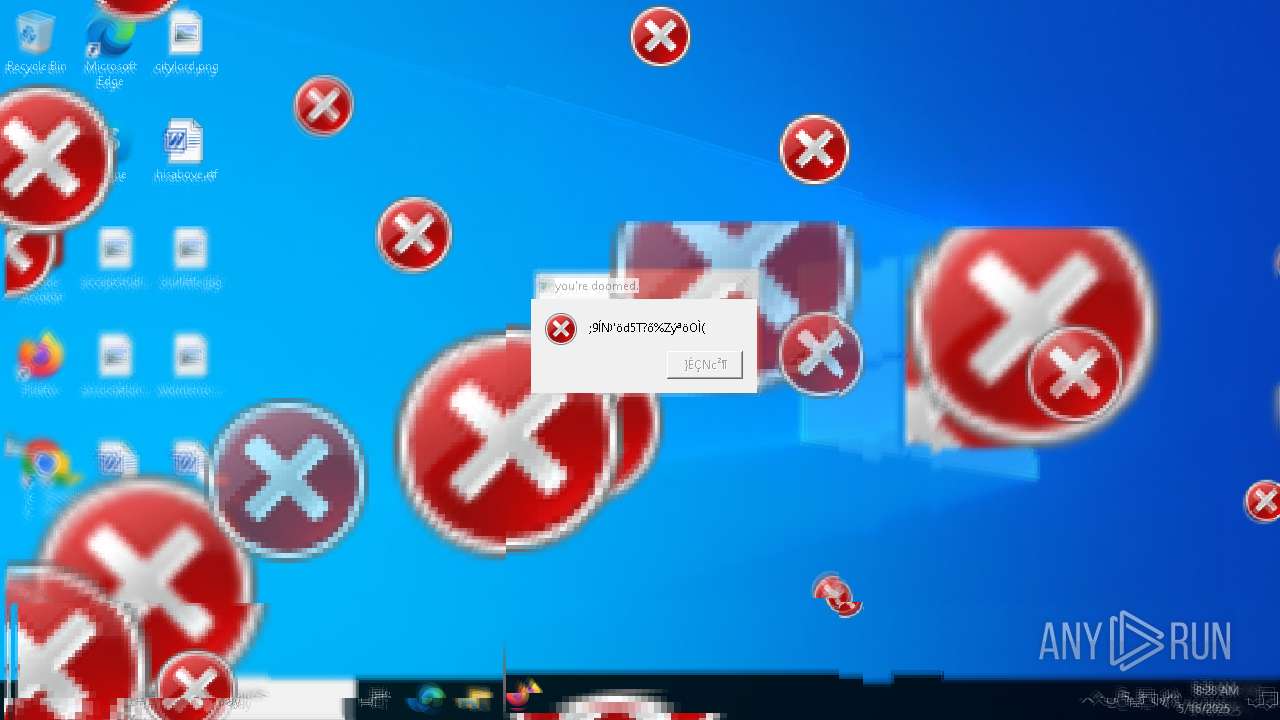
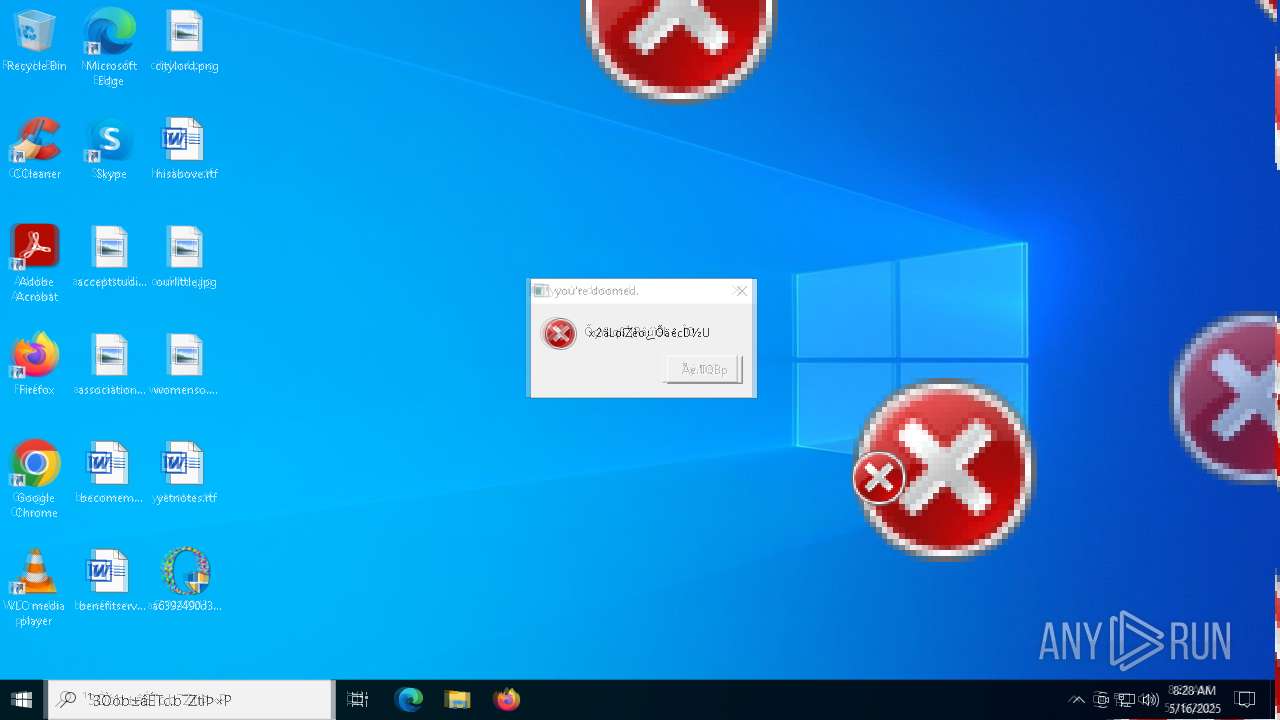
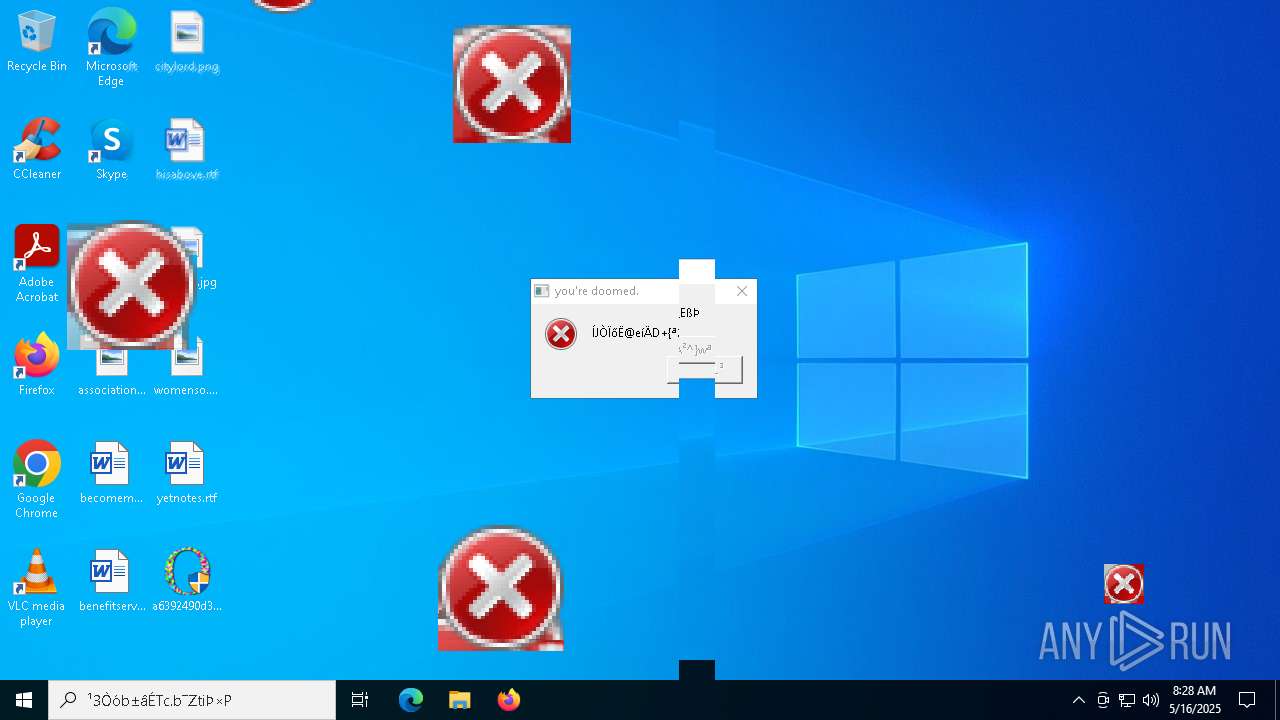
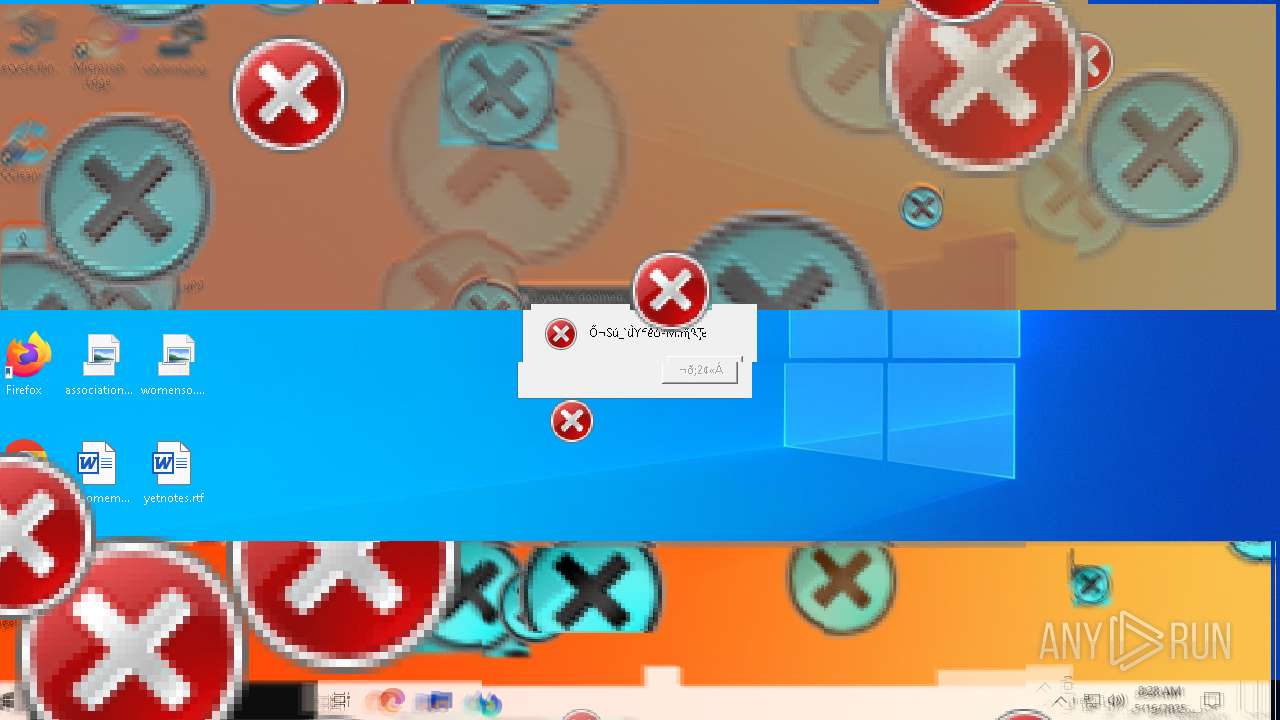
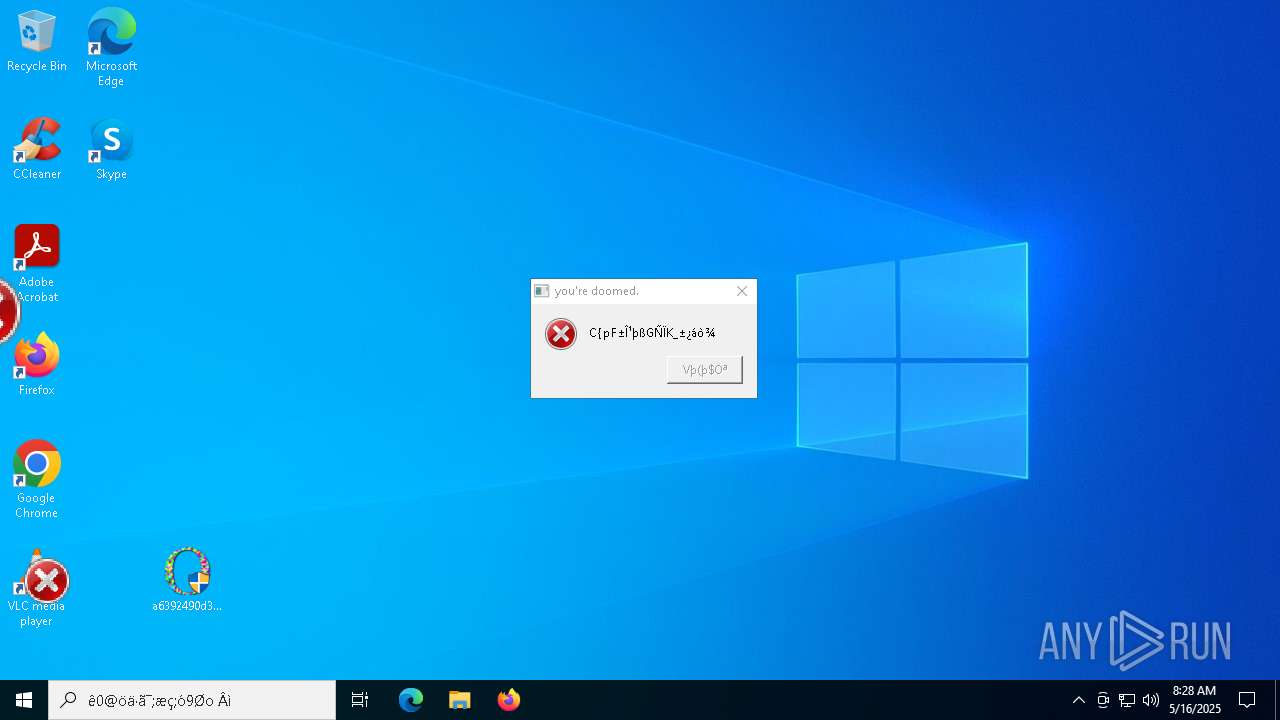
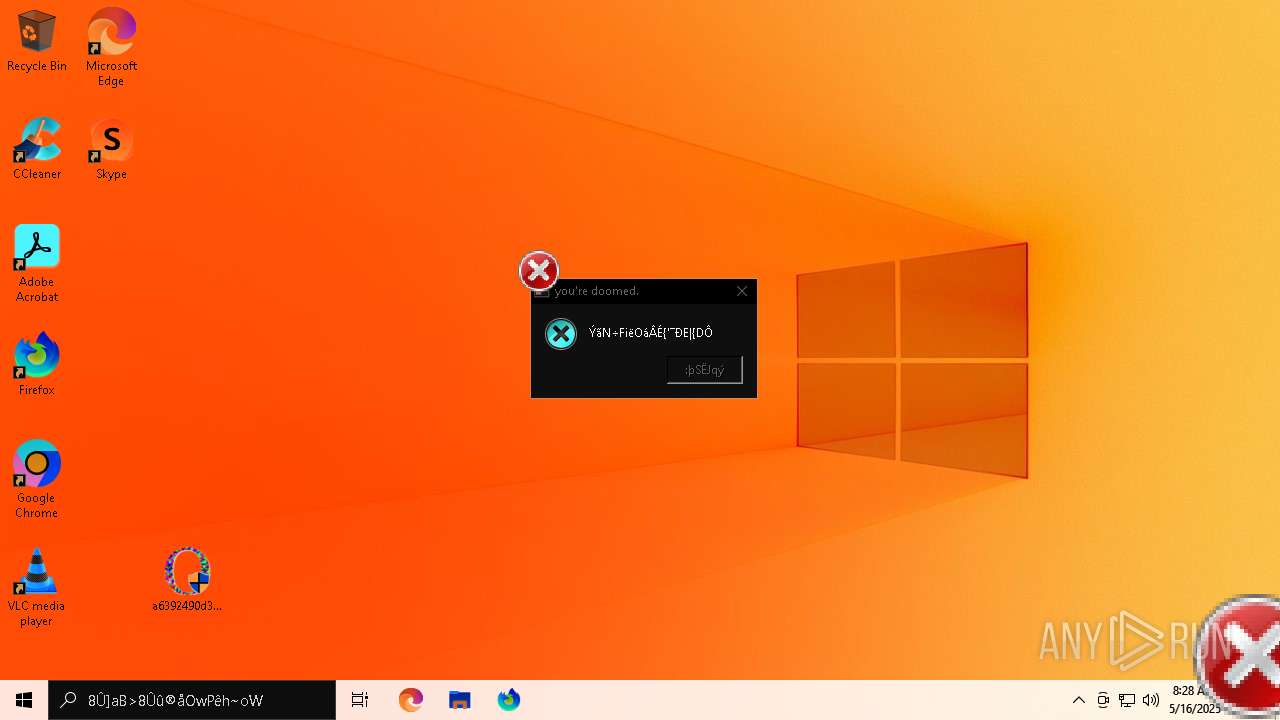
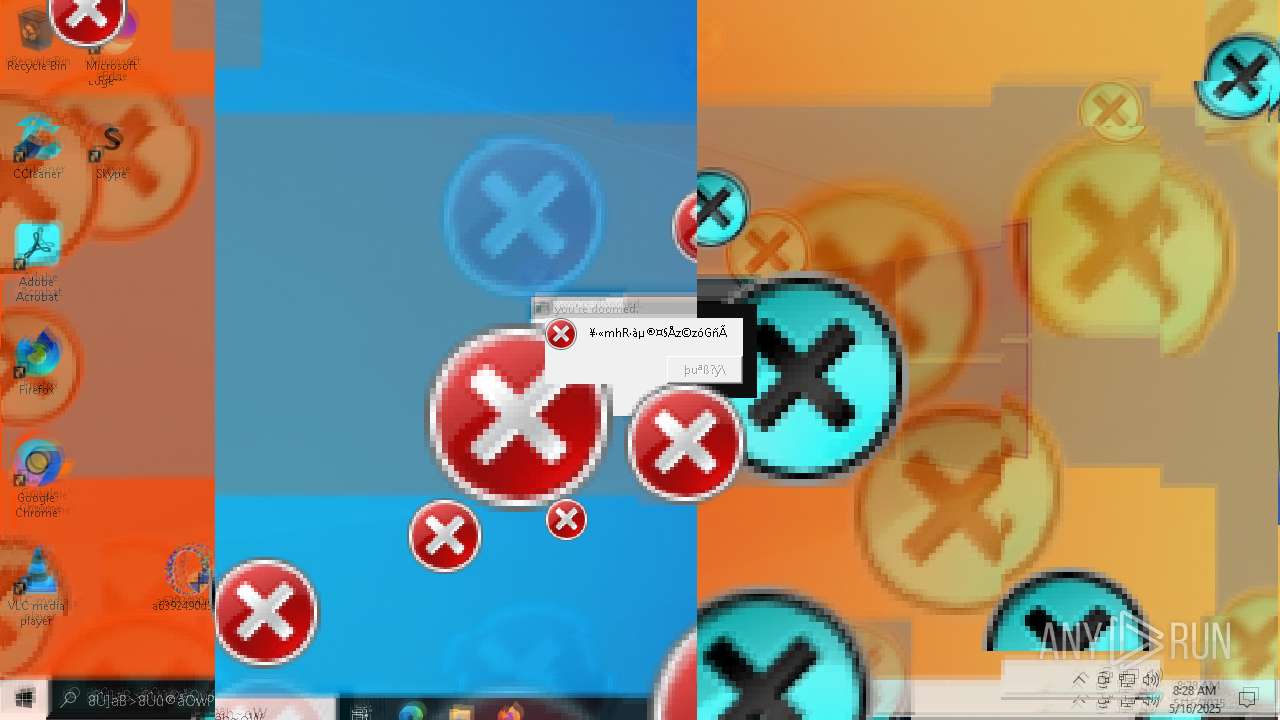
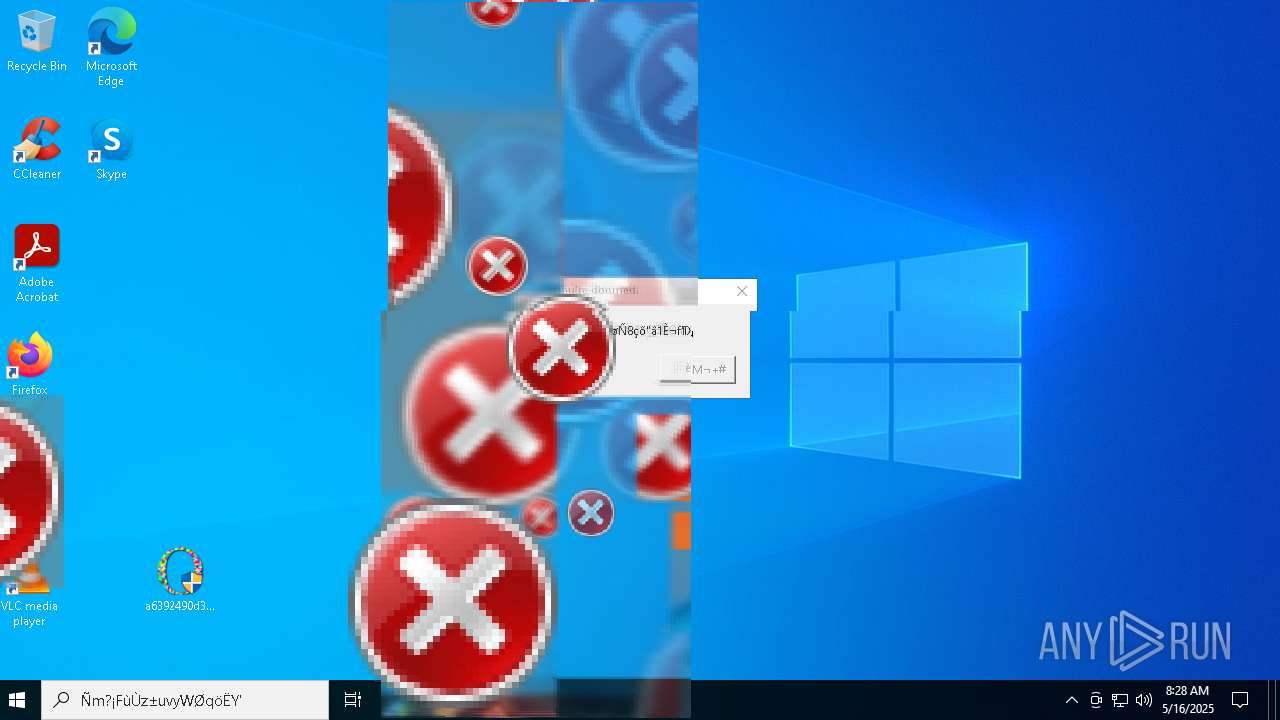
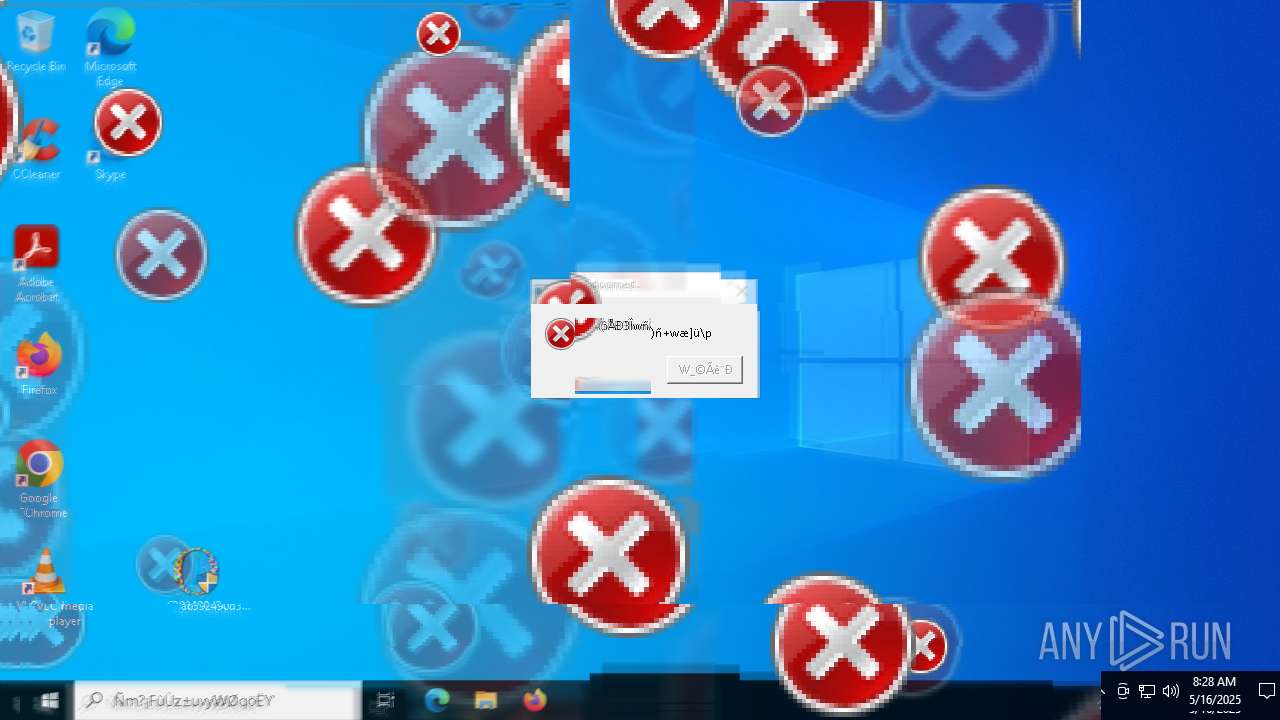
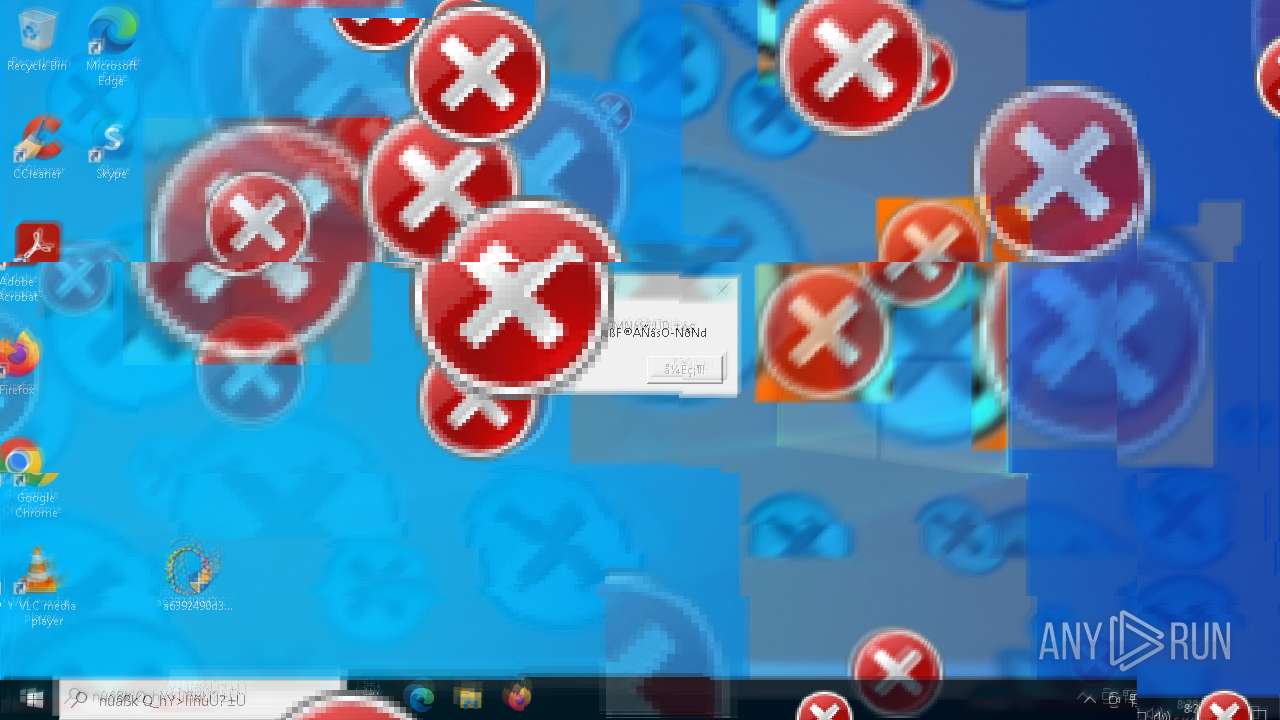
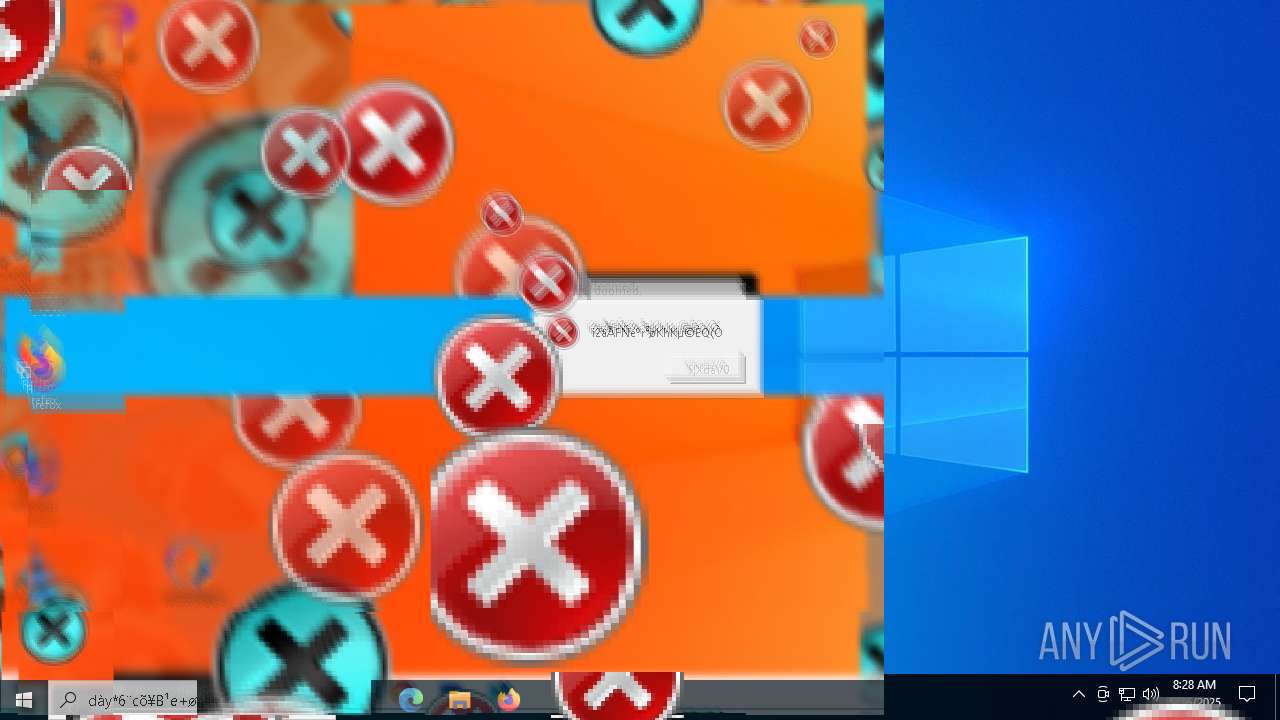
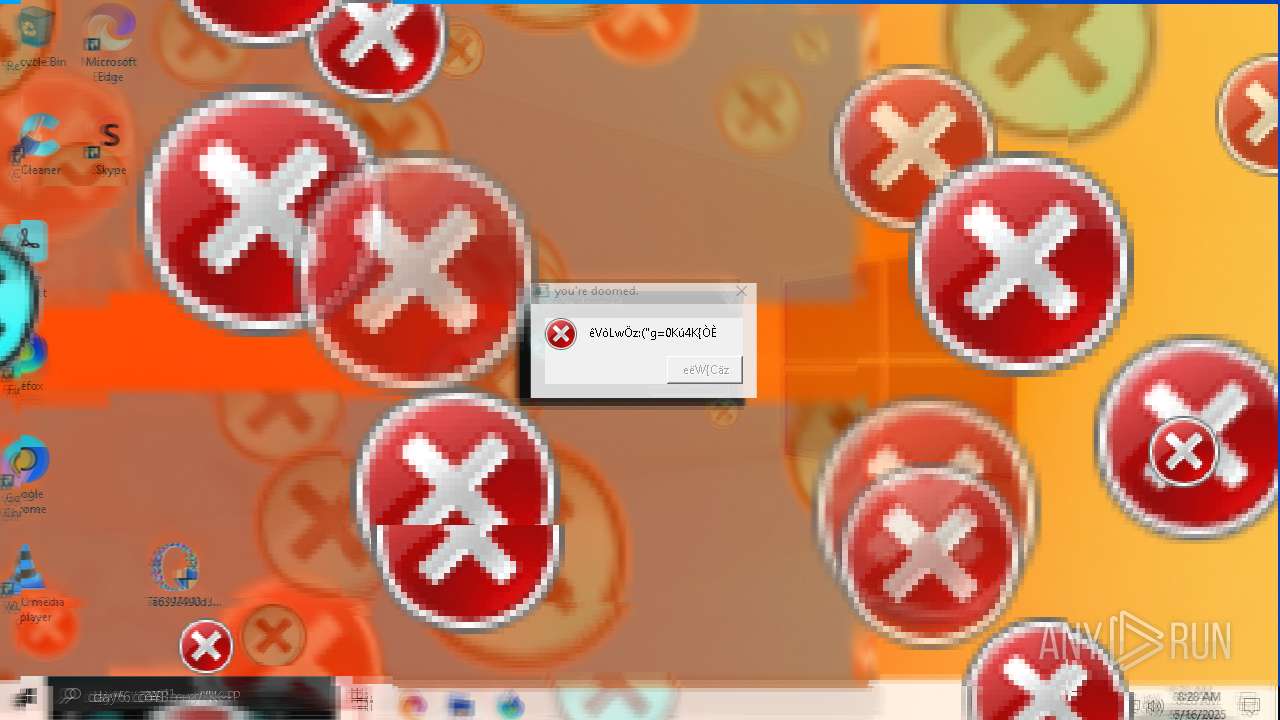
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2025, 08:27:25 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 292EA56DEFD8561F16D4FD74A6D242DD |
| SHA1: | D82A089F259F74A4C40FA46DAD5E457627F0894C |
| SHA256: | A6392490D3B0163FF8F0F40D8734F09429F711234CA4AF3A0ADD564171913359 |
| SSDEEP: | 3072:sO9to0Fh8bZVVQYL29kDIQwRSCy1MFvIqY:sG8bZVVQYL299QwTy1M+q |
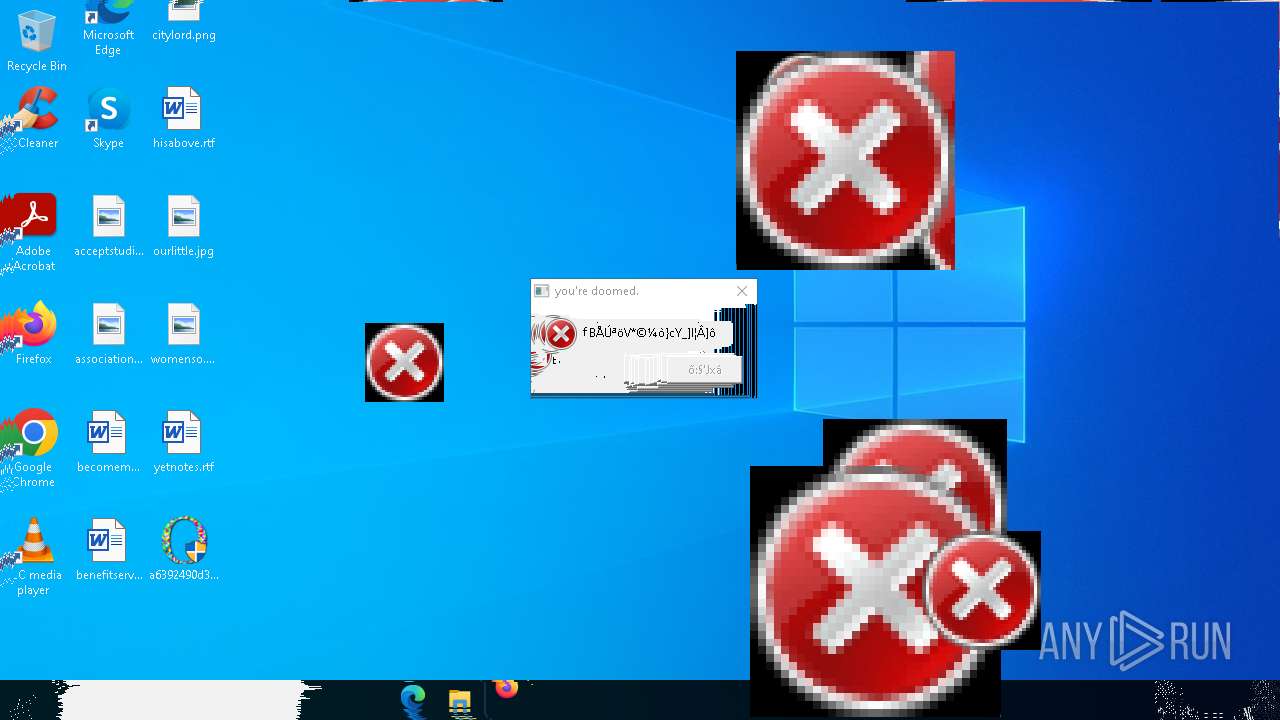
MALICIOUS
DISKWRITER has been found (auto)
- a6392490d3b0163ff8f0f40d8734f09429f711234ca4af3a0add564171913359.exe (PID: 7540)
SUSPICIOUS
Reads security settings of Internet Explorer
- a6392490d3b0163ff8f0f40d8734f09429f711234ca4af3a0add564171913359.exe (PID: 7540)
Reads the date of Windows installation
- a6392490d3b0163ff8f0f40d8734f09429f711234ca4af3a0add564171913359.exe (PID: 7540)
Takes ownership (TAKEOWN.EXE)
- cmd.exe (PID: 7868)
- cmd.exe (PID: 7940)
- cmd.exe (PID: 7892)
- cmd.exe (PID: 7992)
- cmd.exe (PID: 8032)
Starts CMD.EXE for commands execution
- a6392490d3b0163ff8f0f40d8734f09429f711234ca4af3a0add564171913359.exe (PID: 7540)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 3100)
There is functionality for taking screenshot (YARA)
- a6392490d3b0163ff8f0f40d8734f09429f711234ca4af3a0add564171913359.exe (PID: 7540)
Executes application which crashes
- SearchApp.exe (PID: 7488)
- SearchApp.exe (PID: 5600)
- SearchApp.exe (PID: 5344)
INFO
Process checks computer location settings
- a6392490d3b0163ff8f0f40d8734f09429f711234ca4af3a0add564171913359.exe (PID: 7540)
Reads the computer name
- a6392490d3b0163ff8f0f40d8734f09429f711234ca4af3a0add564171913359.exe (PID: 7540)
Checks supported languages
- a6392490d3b0163ff8f0f40d8734f09429f711234ca4af3a0add564171913359.exe (PID: 7540)
Reads the machine GUID from the registry
- a6392490d3b0163ff8f0f40d8734f09429f711234ca4af3a0add564171913359.exe (PID: 7540)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2068:09:08 20:36:12+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 29696 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9202 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | malware |
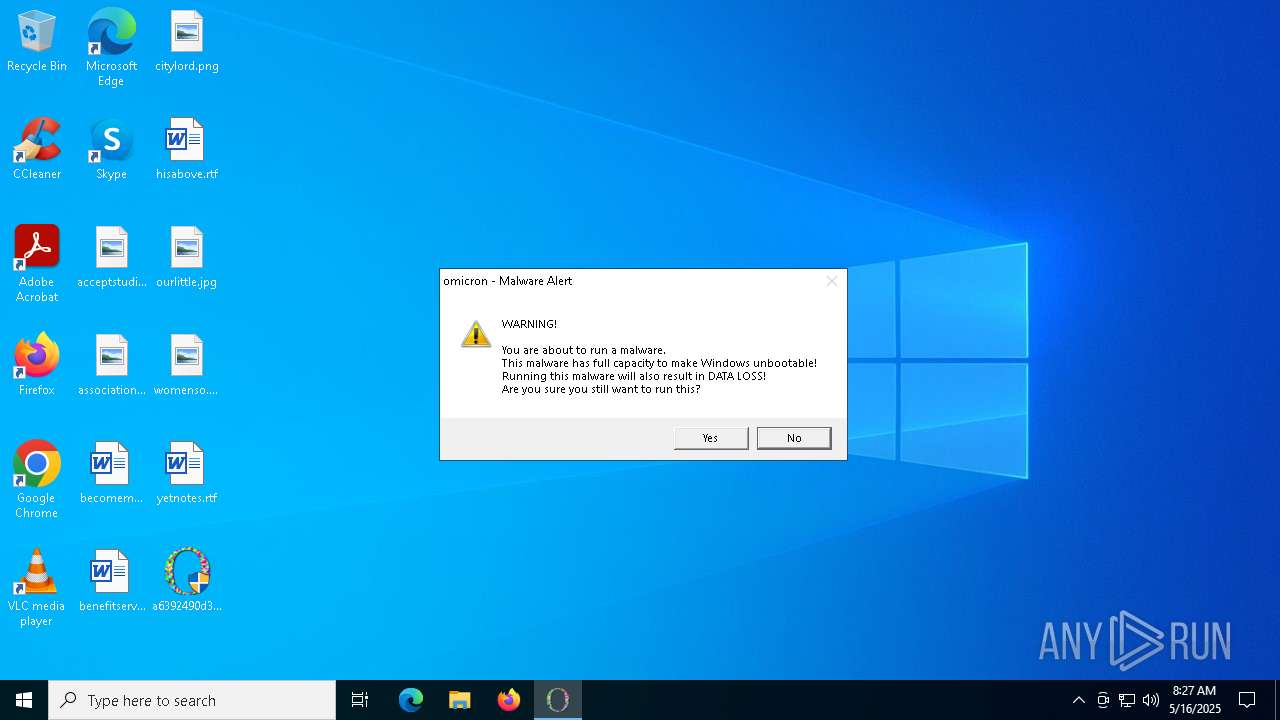
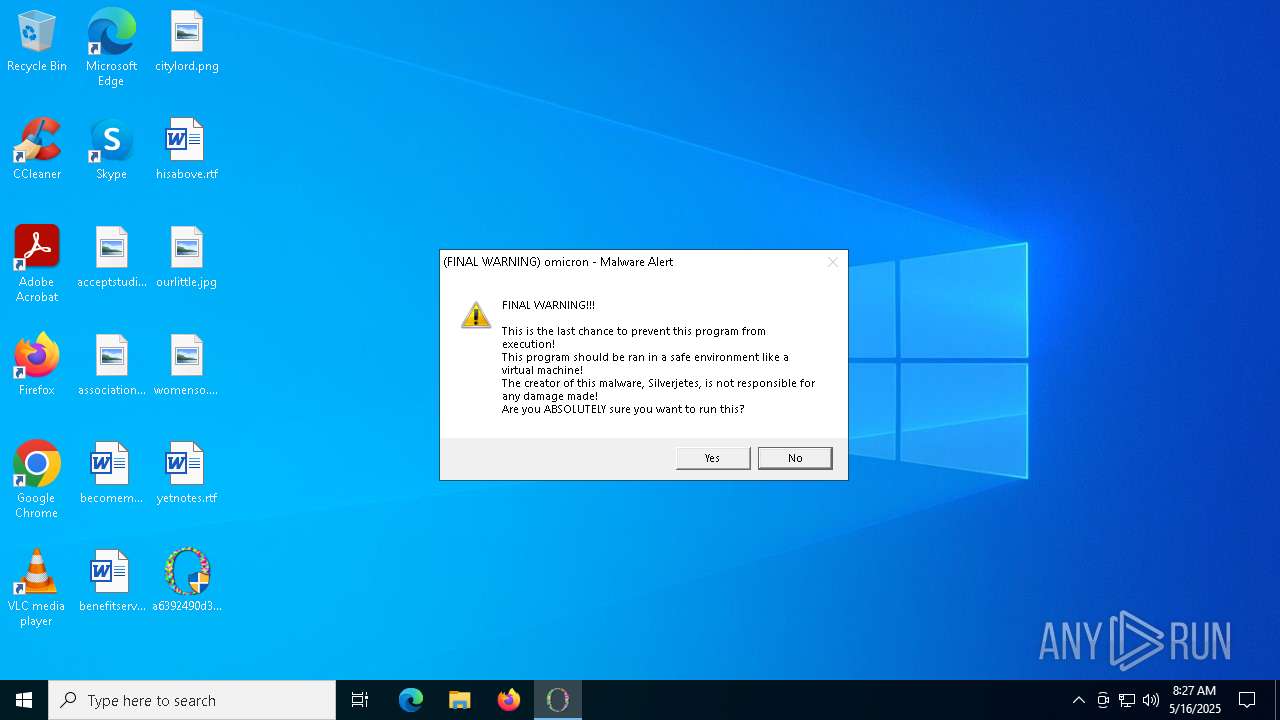
| CompanyName: | Silverjetes |
| FileDescription: | omicron.exe |
| FileVersion: | 1.0.0.0 |
| InternalName: | omicron.exe |
| LegalCopyright: | Copyright © Silverjetes, 2025 |
| LegalTrademarks: | - |
| OriginalFileName: | omicron.exe |
| ProductName: | omicron.exe |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
186
Monitored processes
44
Malicious processes
0
Suspicious processes
1
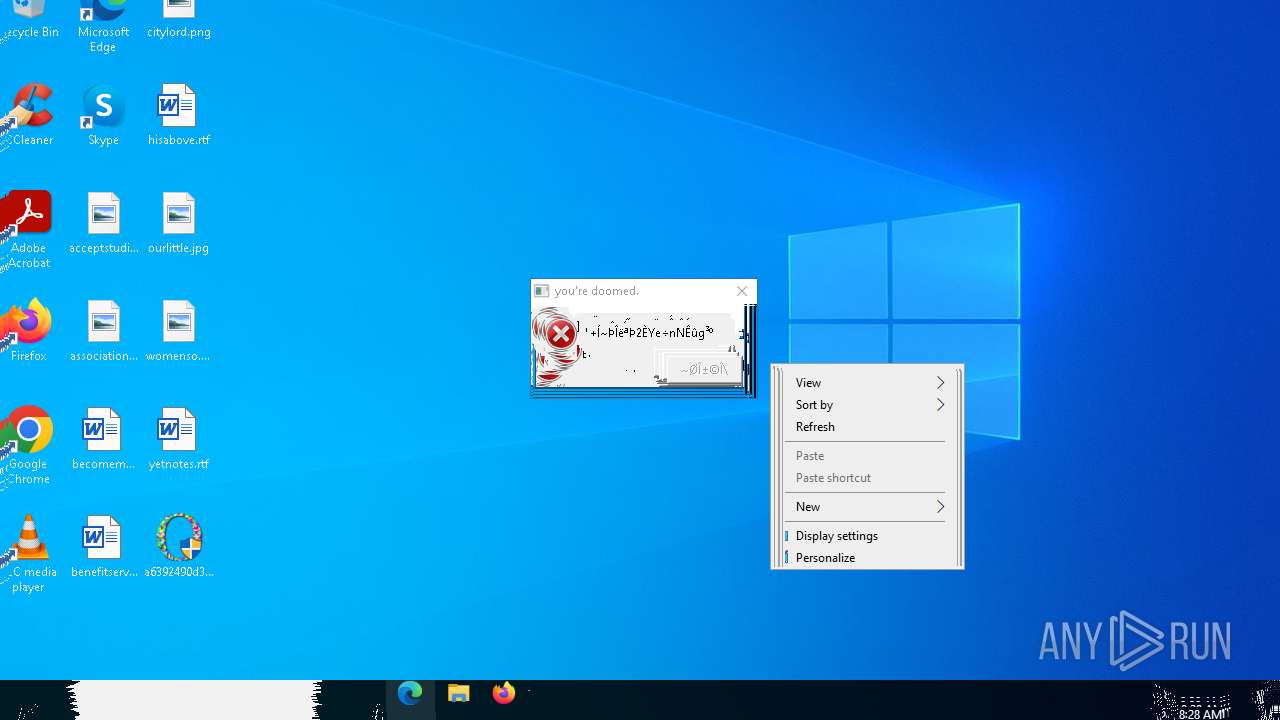
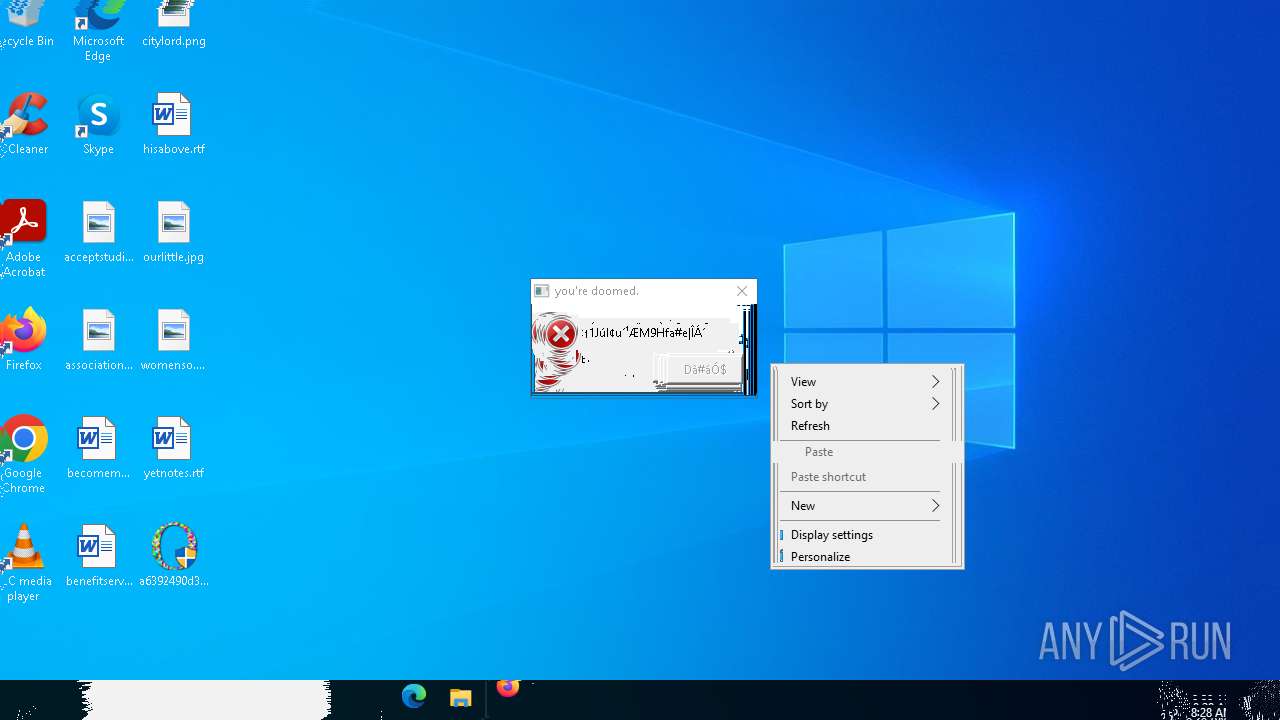
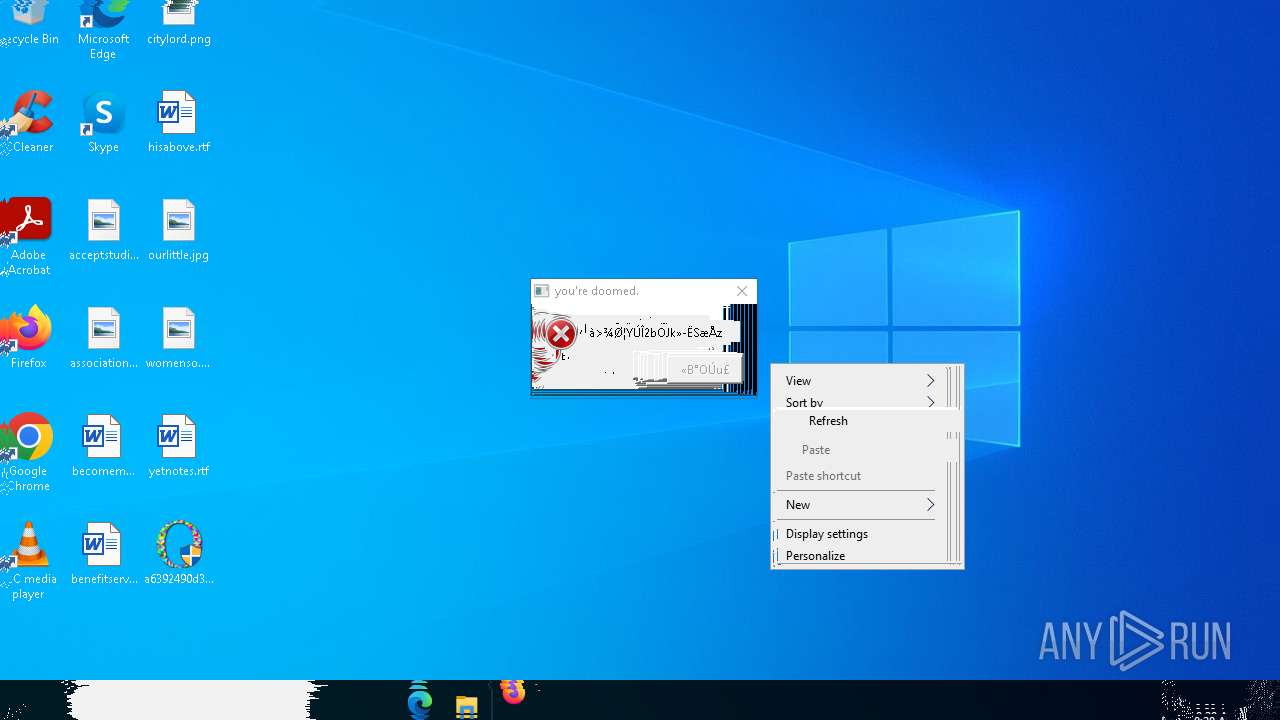
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 660 | "C:\WINDOWS\system32\wermgr.exe" "-outproc" "0" "6156" "3560" "1832" "1864" "0" "0" "0" "0" "0" "0" "0" "0" | C:\Windows\System32\wermgr.exe | — | SearchApp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | "C:\WINDOWS\system32\wermgr.exe" "-outproc" "0" "6644" "3604" "3420" "3600" "0" "0" "0" "0" "0" "0" "0" "0" | C:\Windows\System32\wermgr.exe | — | SearchApp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1188 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | takeown /f "C:\Program Files (x86)"*.* | C:\Windows\System32\takeown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1280 | "C:\Windows\System32\cmd.exe" /c del "%PROGRAMFILES%"/s /q | C:\Windows\System32\cmd.exe | — | a6392490d3b0163ff8f0f40d8734f09429f711234ca4af3a0add564171913359.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2320 | "C:\Users\admin\Desktop\a6392490d3b0163ff8f0f40d8734f09429f711234ca4af3a0add564171913359.exe" | C:\Users\admin\Desktop\a6392490d3b0163ff8f0f40d8734f09429f711234ca4af3a0add564171913359.exe | — | explorer.exe | |||||||||||
User: admin Company: Silverjetes Integrity Level: MEDIUM Description: omicron.exe Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3100 | "C:\Windows\System32\cmd.exe" /c reg delete HKLM\SYSTEM\CurrentControlSet\Services /f | C:\Windows\System32\cmd.exe | — | a6392490d3b0163ff8f0f40d8734f09429f711234ca4af3a0add564171913359.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4756 | takeown /f "C:\Program Files"*.* | C:\Windows\System32\takeown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4988 | "C:\Windows\System32\cmd.exe" /c del "%SYSTEMROOT%" /s /q | C:\Windows\System32\cmd.exe | — | a6392490d3b0163ff8f0f40d8734f09429f711234ca4af3a0add564171913359.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
26 107
Read events
22 915
Write events
419
Delete events
2 773
Modification events
| (PID) Process: | (5064) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\.NET CLR Networking 4.0.0.0 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5064) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\AarSvc_136e52\Security |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5064) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\AarSvc_136e52 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5064) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\ACPI\Parameters\WakeUp |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5064) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\ACPI\Parameters |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5064) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\ACPI\Enum |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5064) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\ACPI |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5064) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\AcpiDev |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5064) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\acpiex\Parameters\Wdf |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5064) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\acpiex\Parameters |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
3
Suspicious files
20
Text files
49
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7488 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\TempState\CortanaUnifiedTileModelCache.dat~RF11725e.TMP | — | |
MD5:— | SHA256:— | |||
| 7968 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_Microsoft.Window_39fd55c4ee7446c589da1ab3e959162ed453fcb_ce03743e_f63c4b71-2b24-40c4-87dd-926af767b9a8\Report.wer | — | |
MD5:— | SHA256:— | |||
| 7968 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\SearchApp.exe.7488.dmp | — | |
MD5:— | SHA256:— | |||
| 6644 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\LocalState\DeviceSearchCache\AppCache133918577041691686.txt~RF11874e.TMP | — | |
MD5:— | SHA256:— | |||
| 7488 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\TempState\CortanaUnifiedTileModelCache.dat | binary | |
MD5:8E240A454B23534A5D4E20837AD42FFE | SHA256:98DFD3CFF9FD85E1724D0689EBD908A6B04A2A75F653182A00818A01C386A45A | |||
| 7968 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER74FE.tmp.dmp | binary | |
MD5:43FDA7DCA343E986C6459E9752C0576B | SHA256:F837BB7C097C4BC4B05A84D17EA5DF01F0E99C17DEC925EB939B4E7987E22434 | |||
| 6644 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\LocalState\ConstraintIndex\Input_{62c4e63b-3377-4507-9cda-00c06fca65cd}\apps.schema | text | |
MD5:1659677C45C49A78F33551DA43494005 | SHA256:5AF0FC2A0B5CCECDC04E54B3C60F28E3FF5C7D4E1809C6D7C8469F0567C090BB | |||
| 4988 | cmd.exe | C:\Windows\Logs\waasmediccapsule\WaasRemediation.001.etl | binary | |
MD5:9FFB9DB73D18C59BF3E3F048710EA6EF | SHA256:8C49A9E2ACC9FD5A2DD6E640AEE84D5EA54D1C6FA6AF7425EB5364B4298C47D7 | |||
| 7488 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\TempState\~ortanaUnifiedTileModelCache.tmp | binary | |
MD5:8E240A454B23534A5D4E20837AD42FFE | SHA256:98DFD3CFF9FD85E1724D0689EBD908A6B04A2A75F653182A00818A01C386A45A | |||
| 6644 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\GEH\POF-6644.dmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
14
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2656 | RUXIMICS.exe | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2656 | RUXIMICS.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2656 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2656 | RUXIMICS.exe | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
2656 | RUXIMICS.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
5496 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 40.126.31.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |