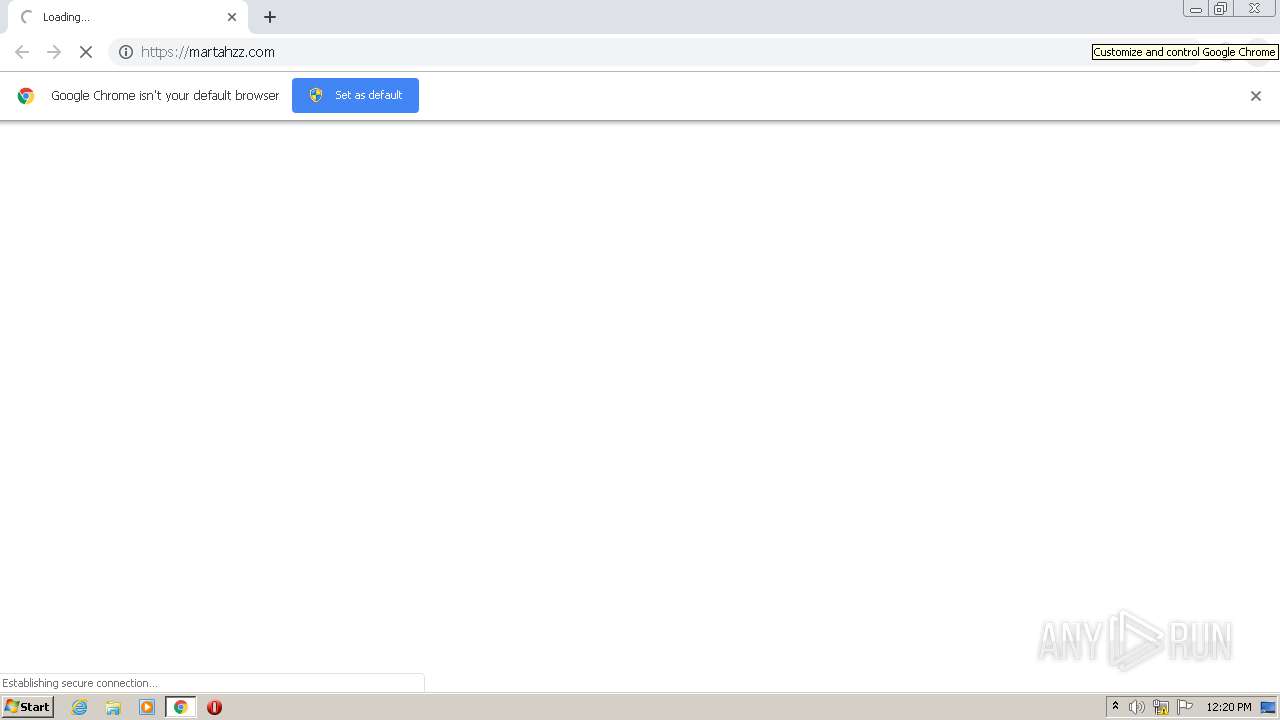
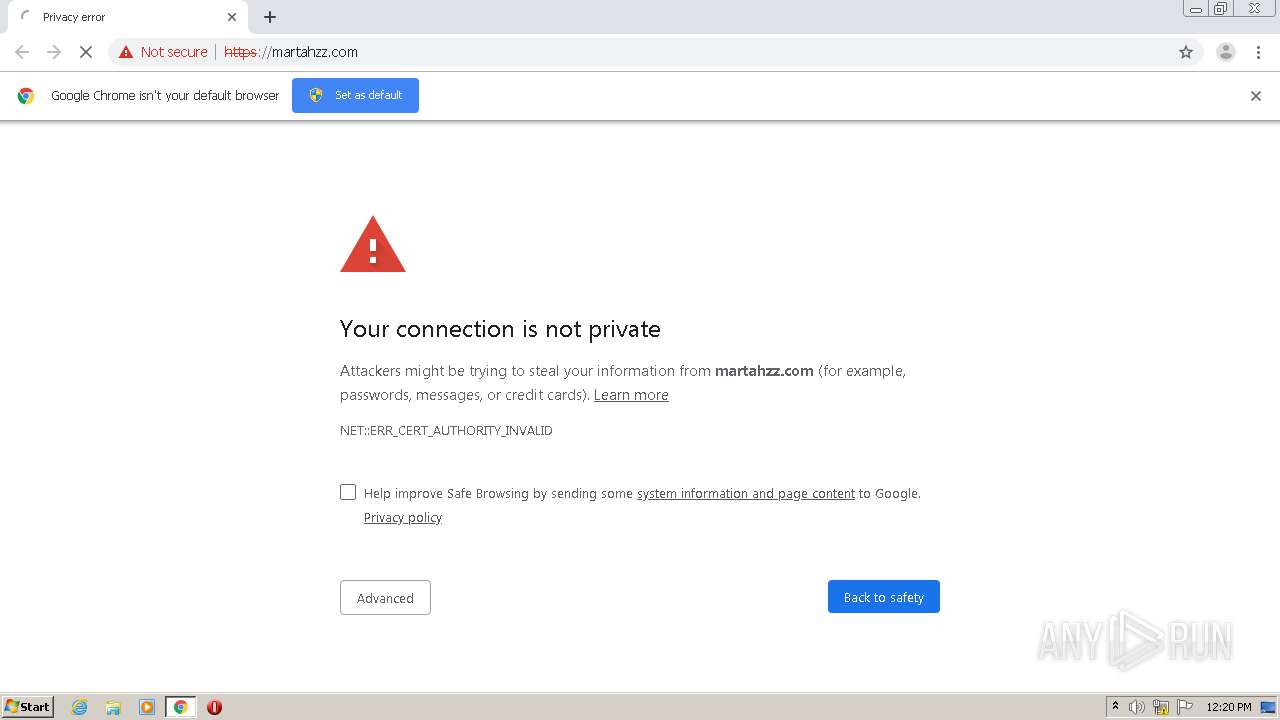
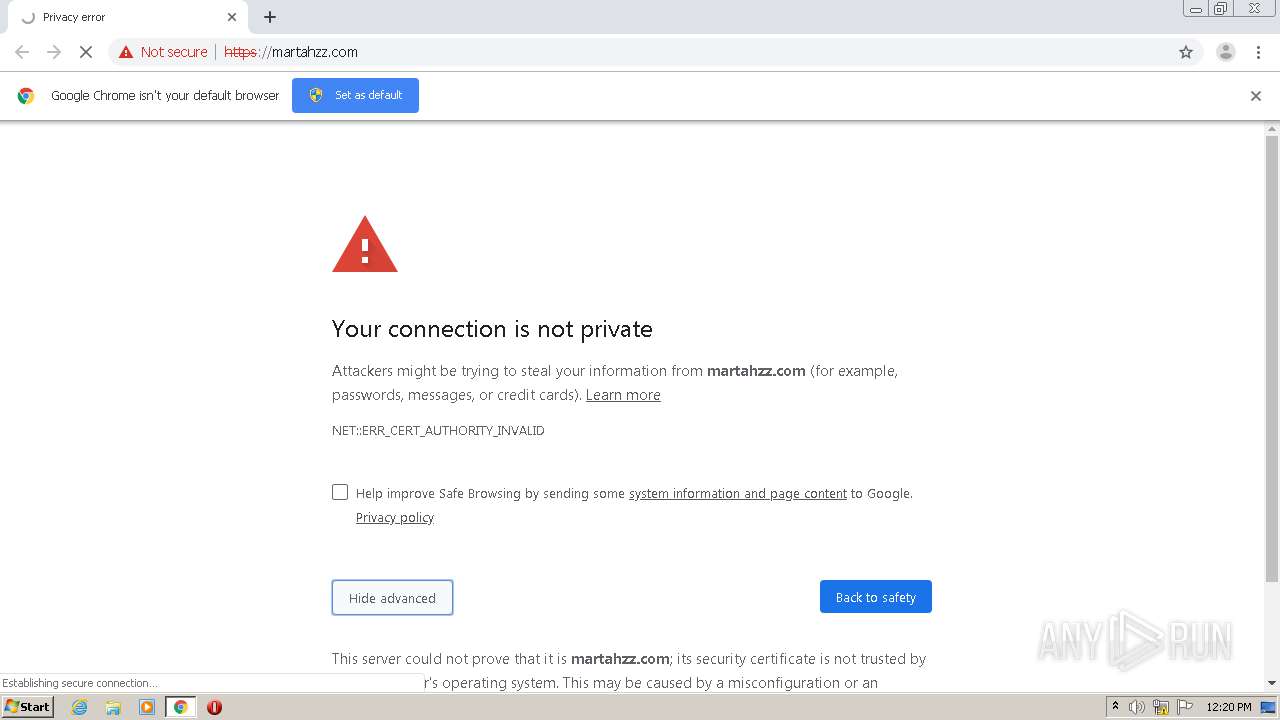
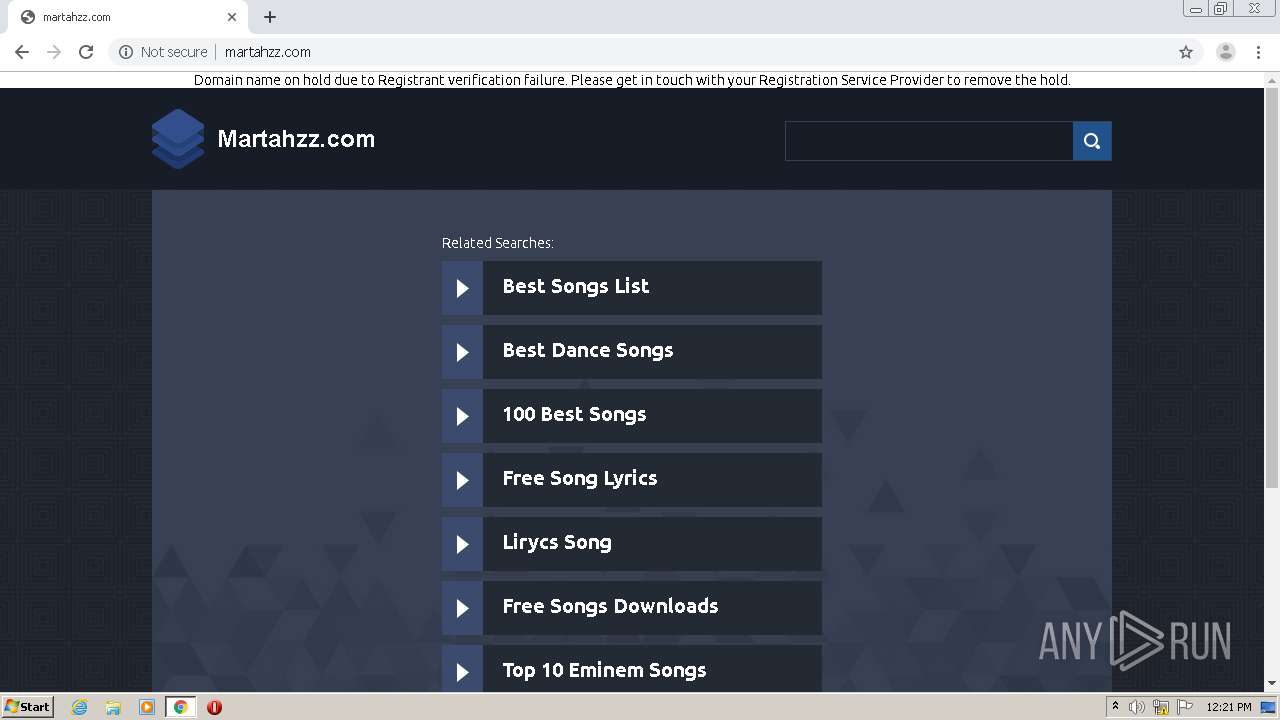
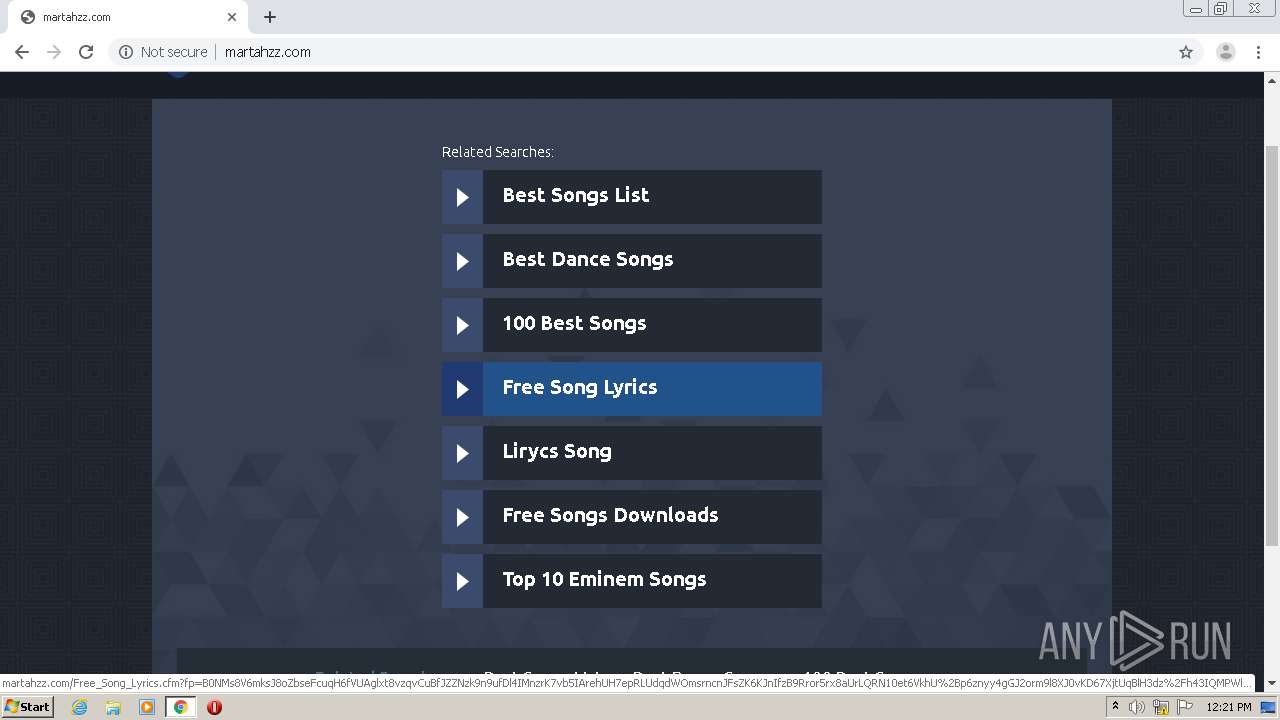
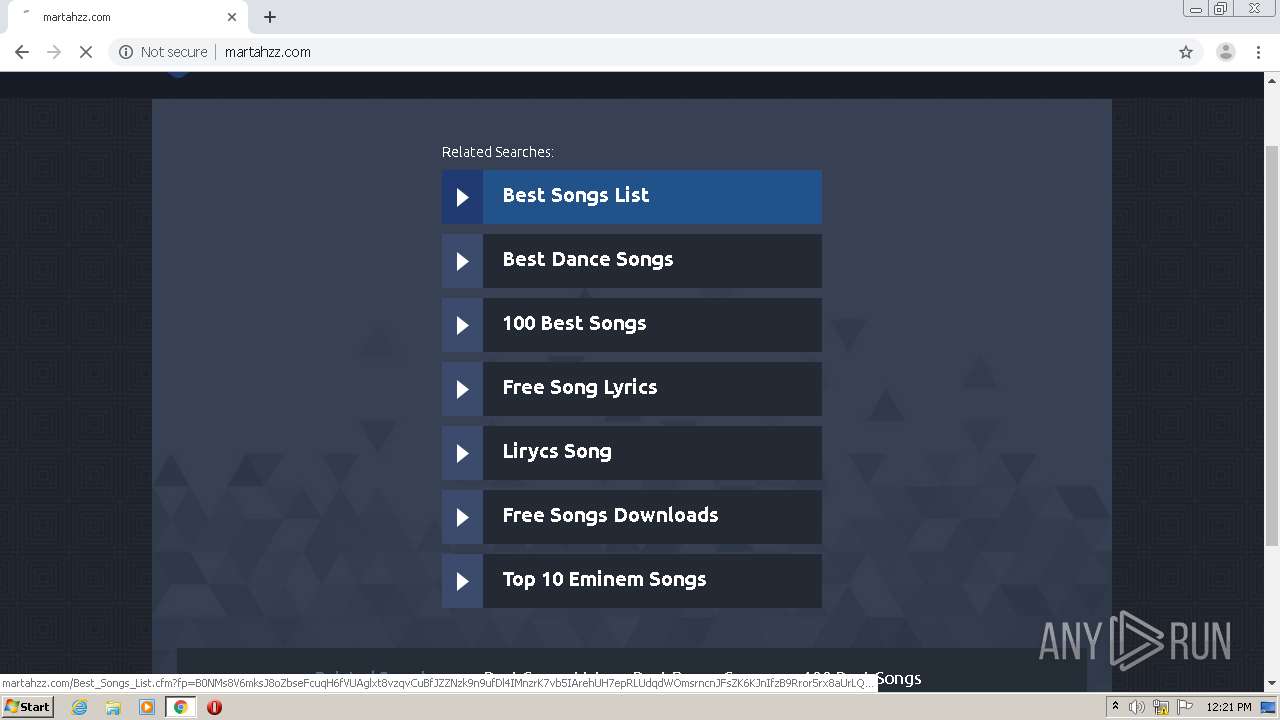
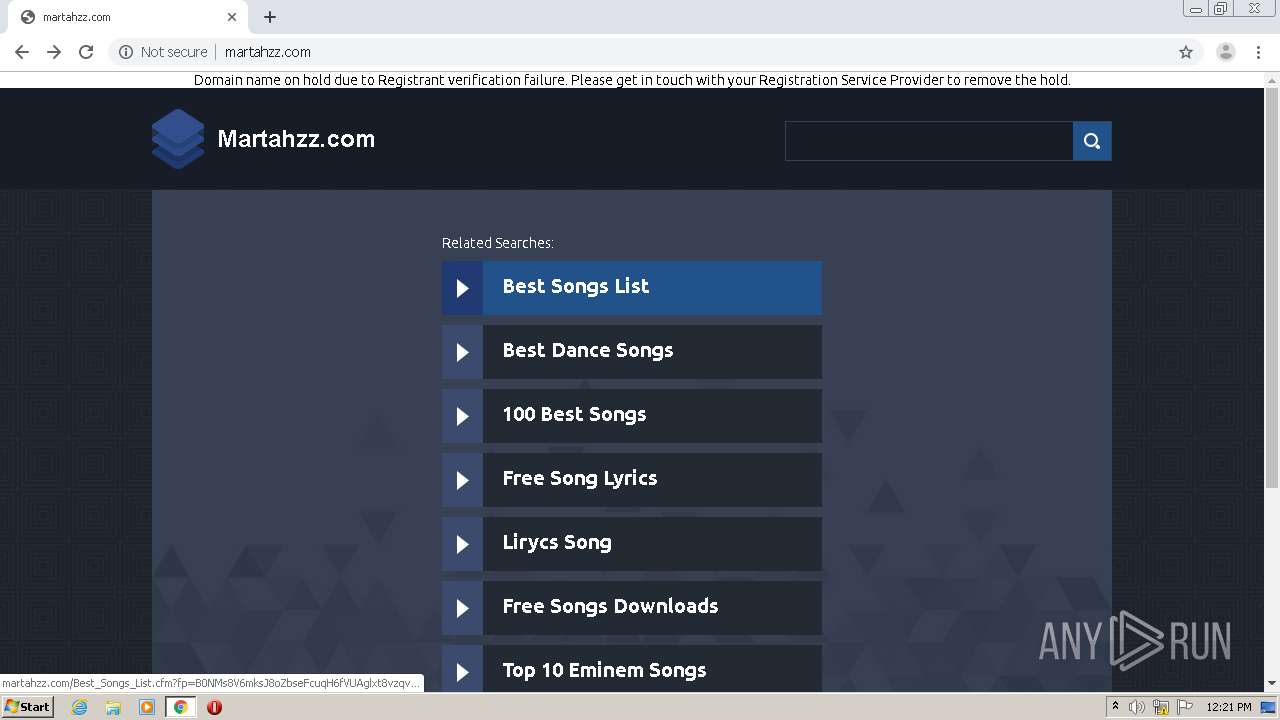
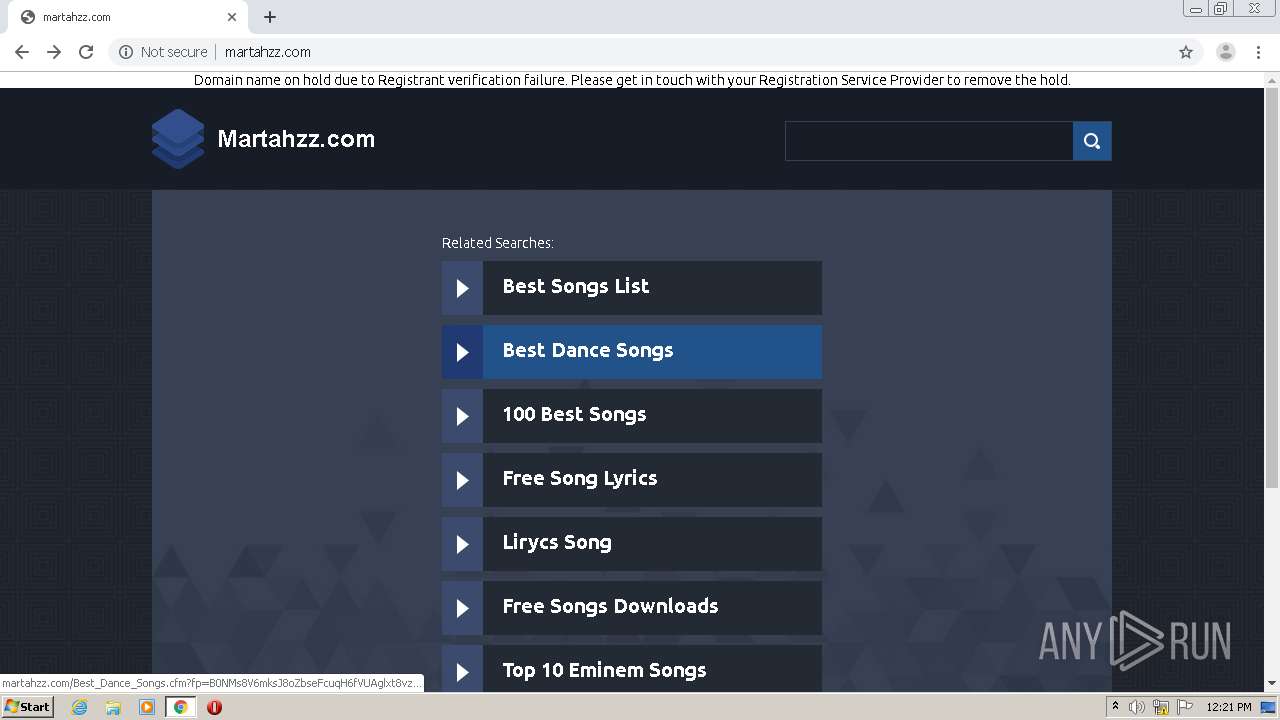
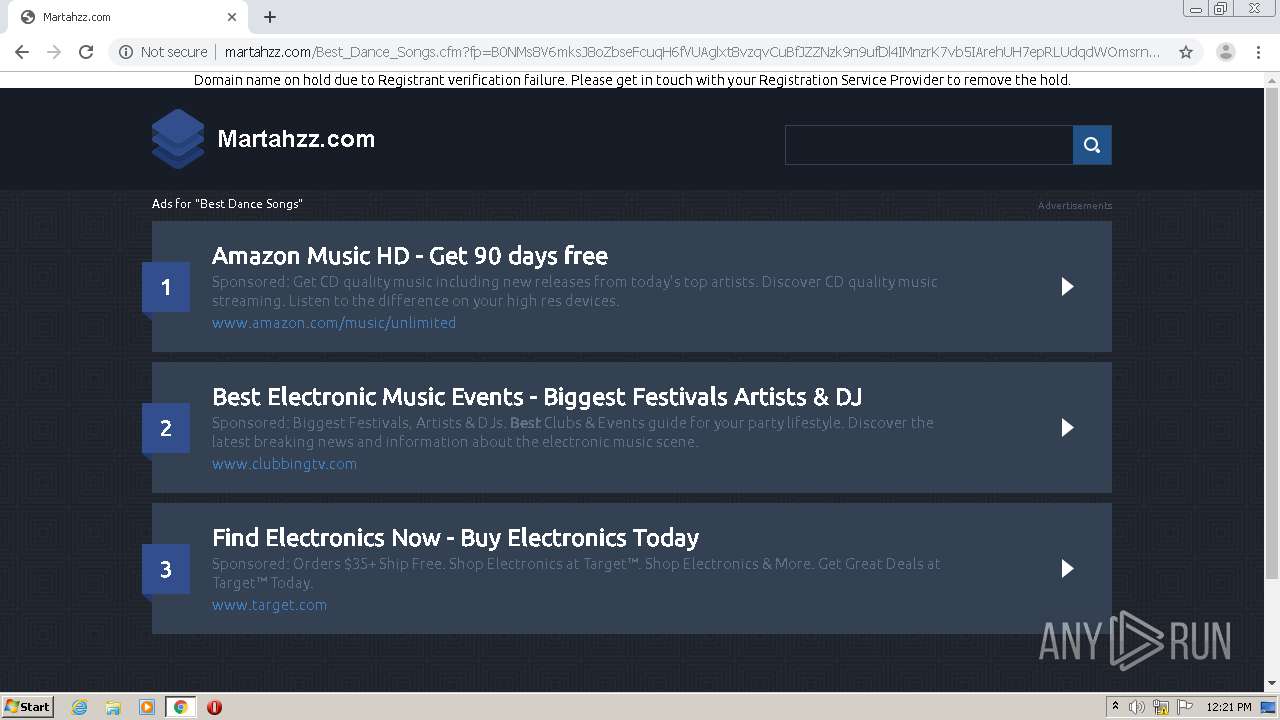
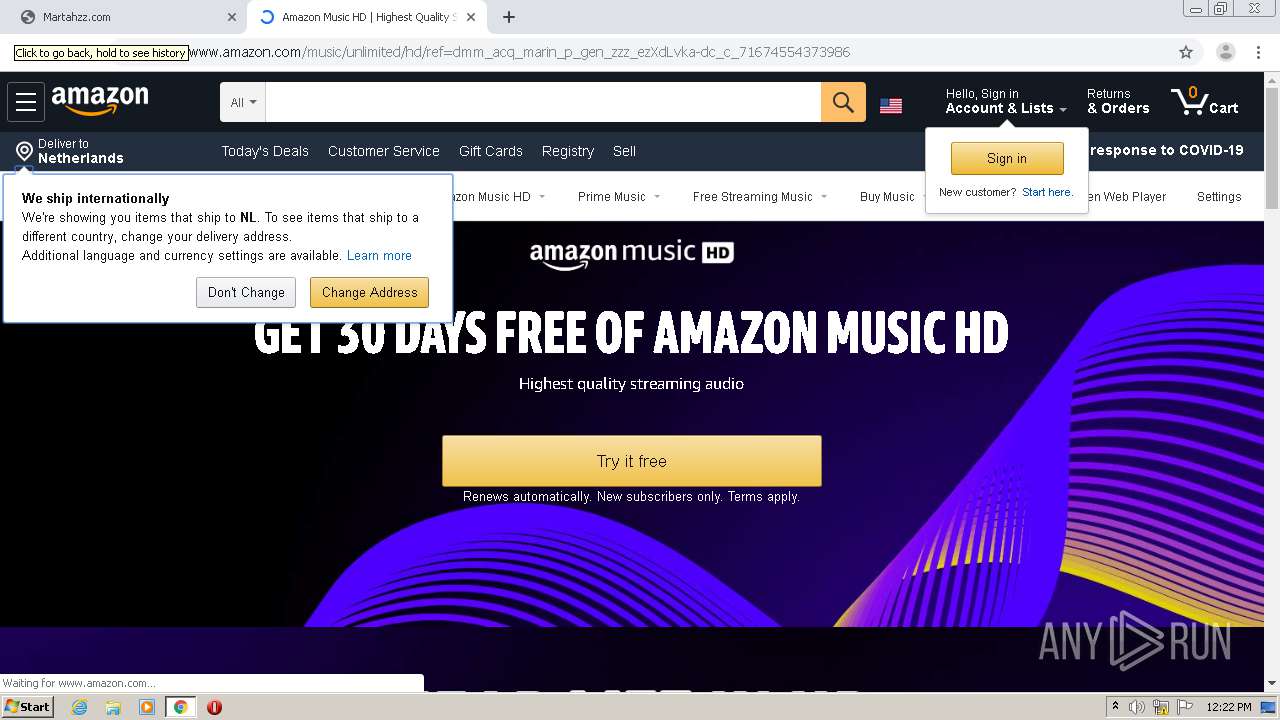
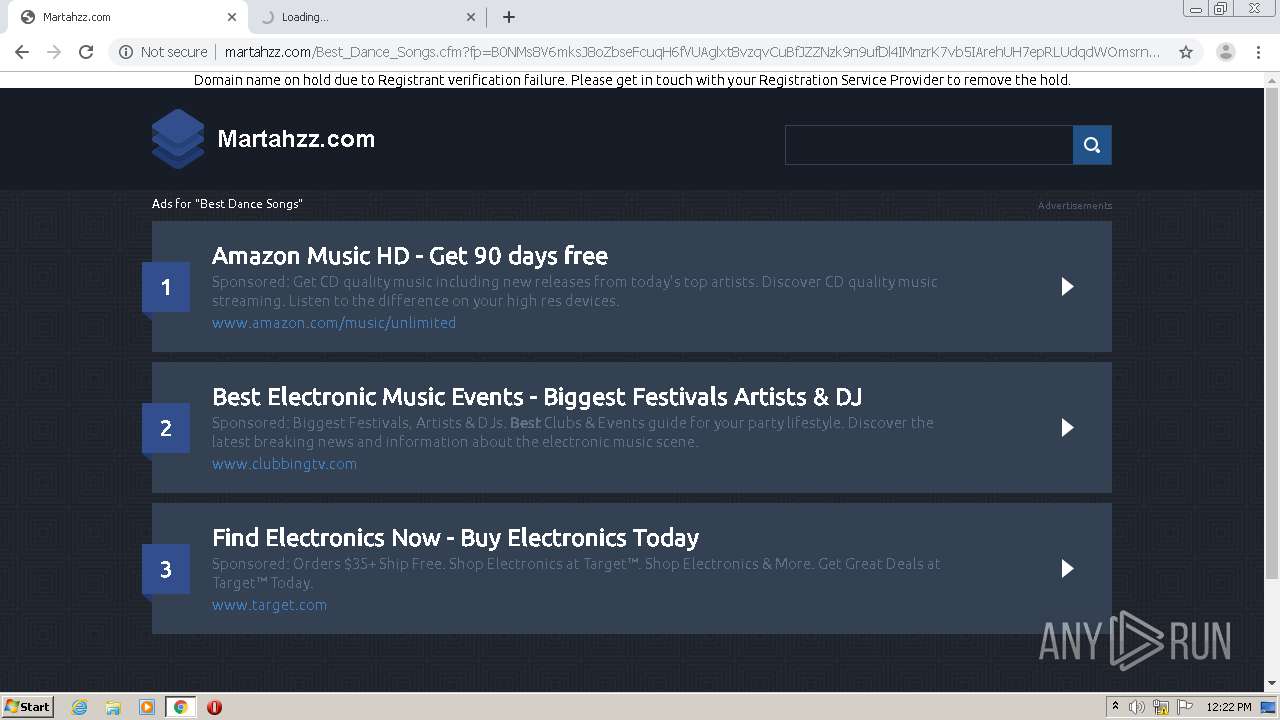
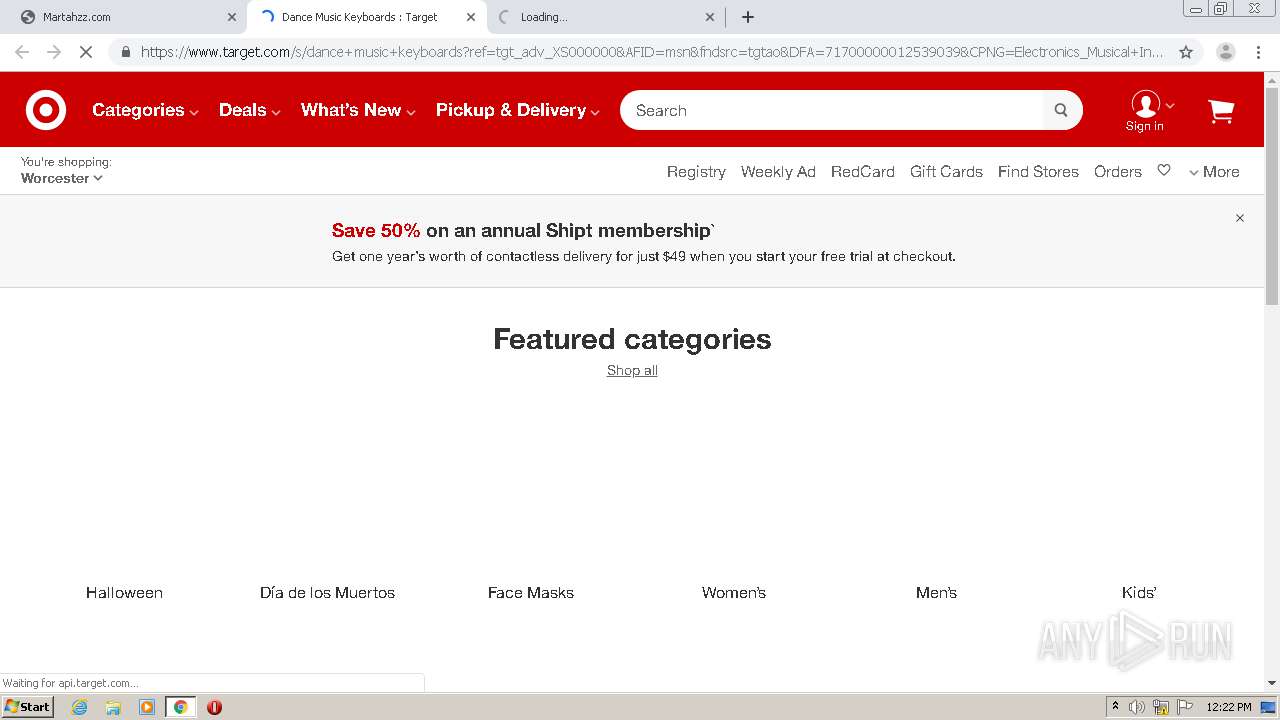
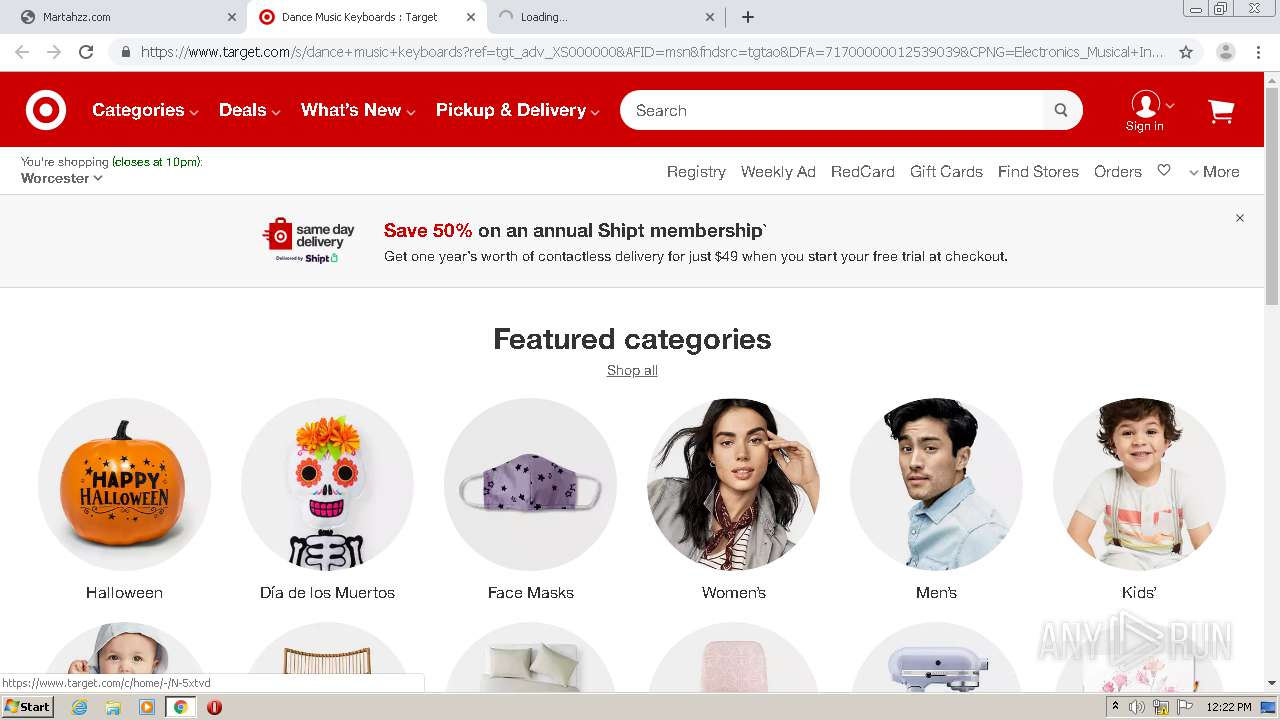
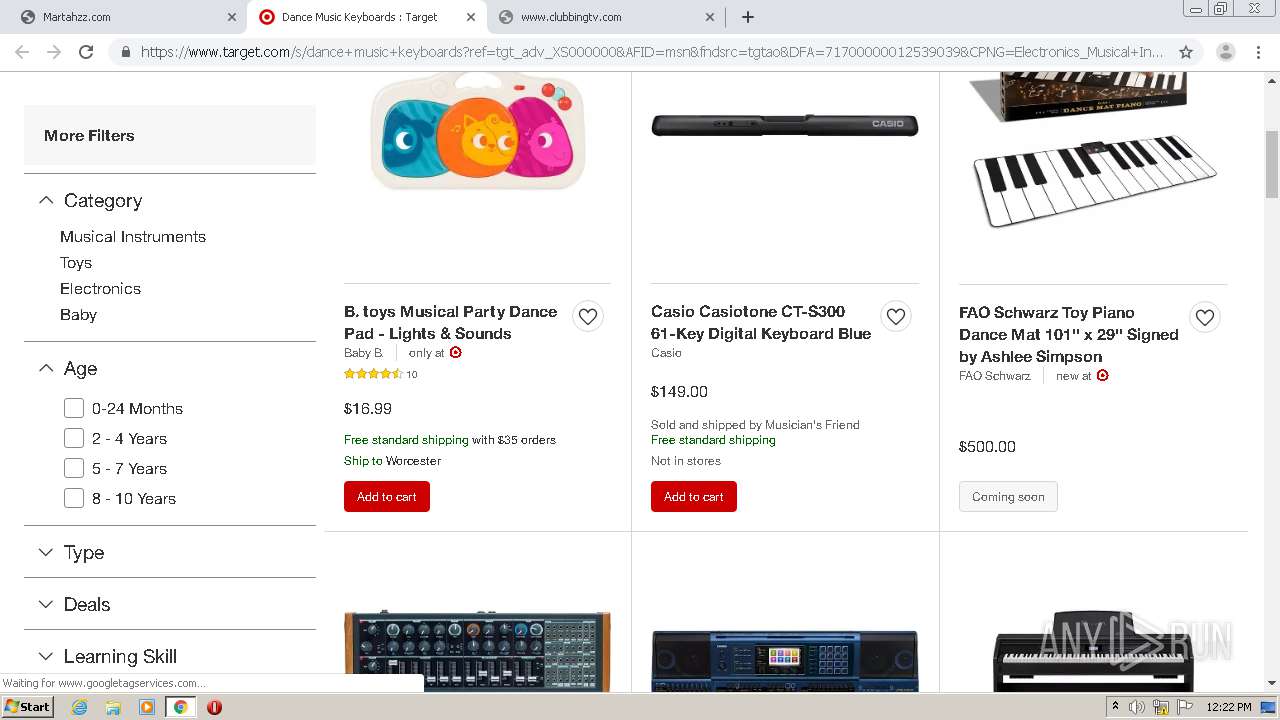
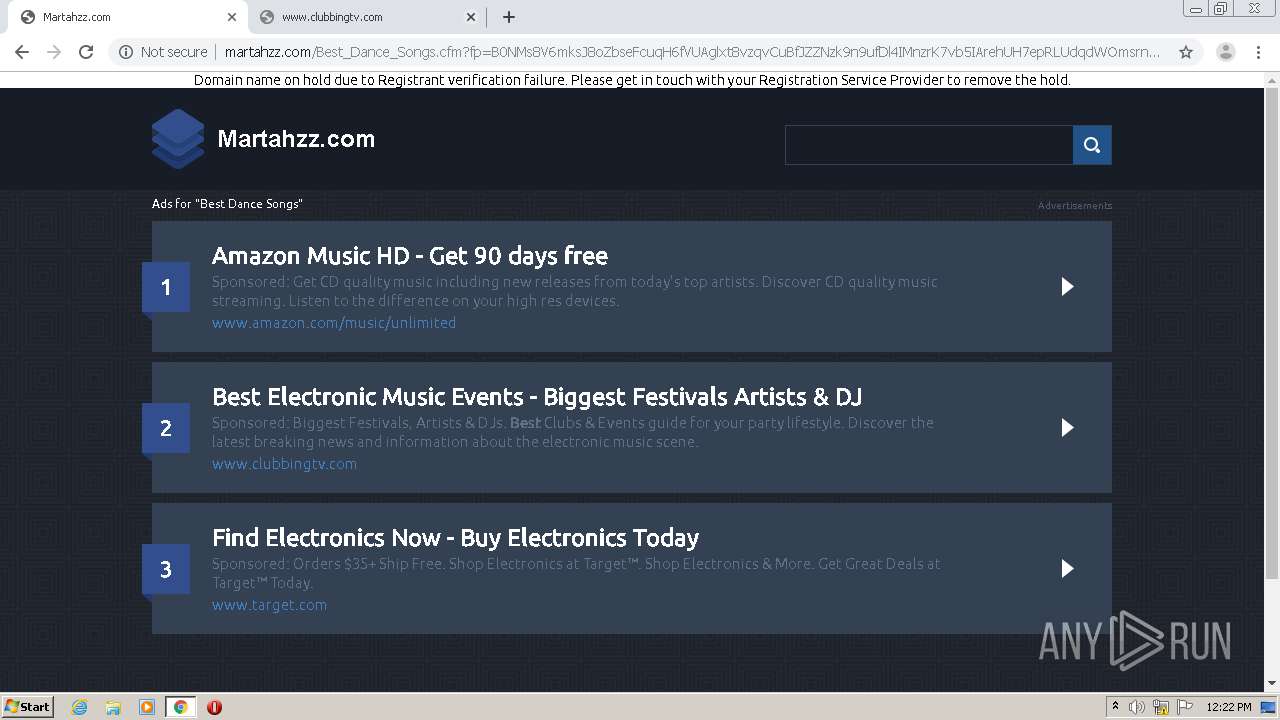
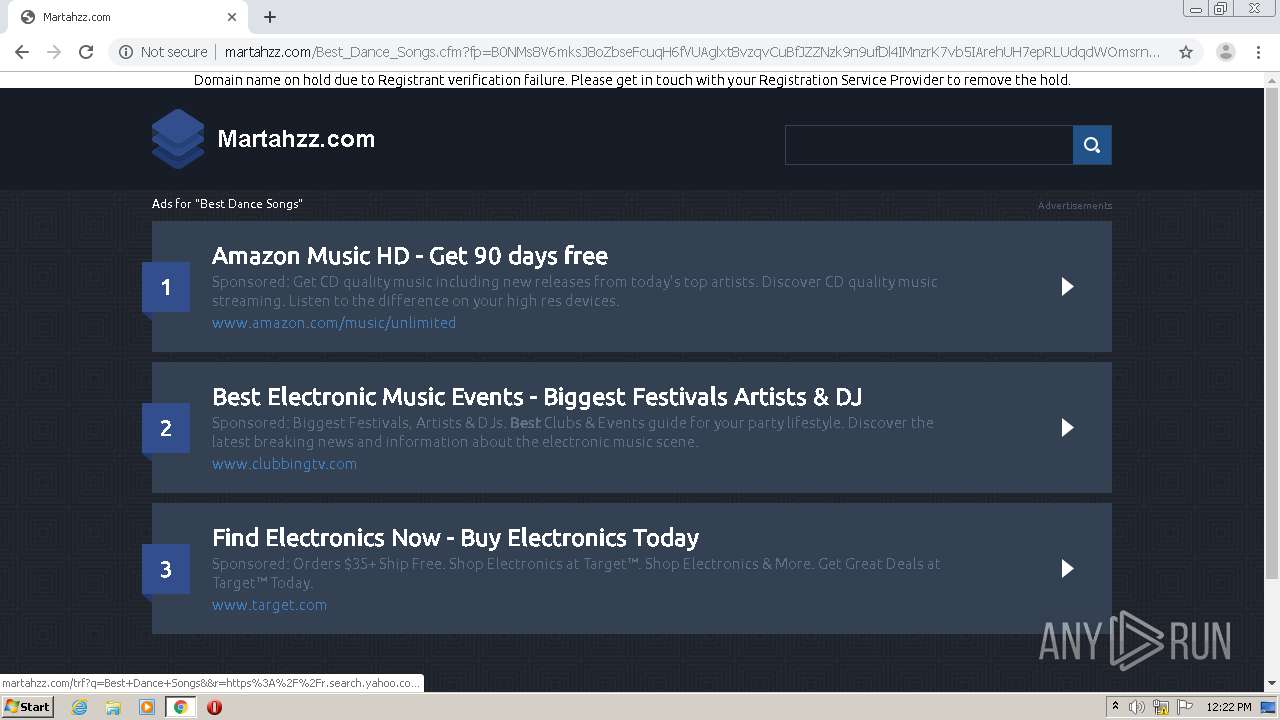
| URL: | https://martahzz.com |
| Full analysis: | https://app.any.run/tasks/18000568-bd02-4fd5-a2ed-8d1406725ca5 |
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 11:20:07 |
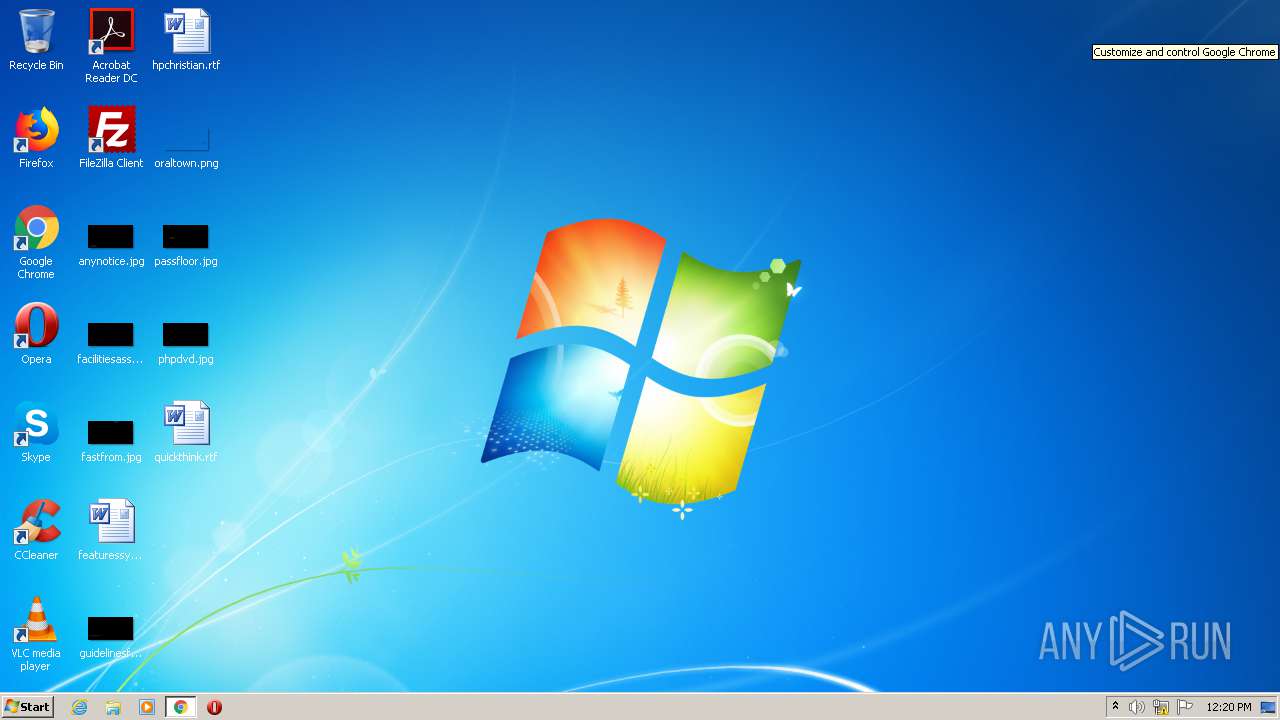
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 983346A2E08934C4A90E6DE6E6EB2B07 |
| SHA1: | BBB6439790F606F484F3658D4D3FED4CB0536DA3 |
| SHA256: | A638C62F25B84905BEAF6AF72EE055167764FC5C57D9245E2EEAED01CD296656 |
| SSDEEP: | 3:N8VENjK:2uNe |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads the hosts file
- chrome.exe (PID: 2504)
- chrome.exe (PID: 1044)
Application launched itself
- chrome.exe (PID: 2504)
Reads settings of System Certificates
- chrome.exe (PID: 1044)
Creates files in the user directory
- chrome.exe (PID: 2504)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
65
Monitored processes
28
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,3603471138826646063,16387016814188915107,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10475553235513198255 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3168 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 716 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,3603471138826646063,16387016814188915107,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=14518983530731350885 --mojo-platform-channel-handle=3584 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,3603471138826646063,16387016814188915107,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8448401612087851147 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2644 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,3603471138826646063,16387016814188915107,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=5057844194670113346 --mojo-platform-channel-handle=1616 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,3603471138826646063,16387016814188915107,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=788745227762507506 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1844 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,3603471138826646063,16387016814188915107,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1732333767279549639 --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3536 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2192 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,3603471138826646063,16387016814188915107,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=4745858185069316444 --mojo-platform-channel-handle=3112 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6c57a9d0,0x6c57a9e0,0x6c57a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,3603471138826646063,16387016814188915107,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2496909198605251110 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2148 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://martahzz.com" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
703
Read events
598
Write events
101
Delete events
4
Modification events
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2504-13247666423002625 |
Value: 259 | |||
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
165
Text files
147
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F8EC7F7-9C8.pma | — | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\267ac050-d069-4ed9-ac04-5bf87af74949.tmp | — | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT~RF2d422e.TMP | — | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF2d422e.TMP | — | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF2d4144.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
163
DNS requests
159
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
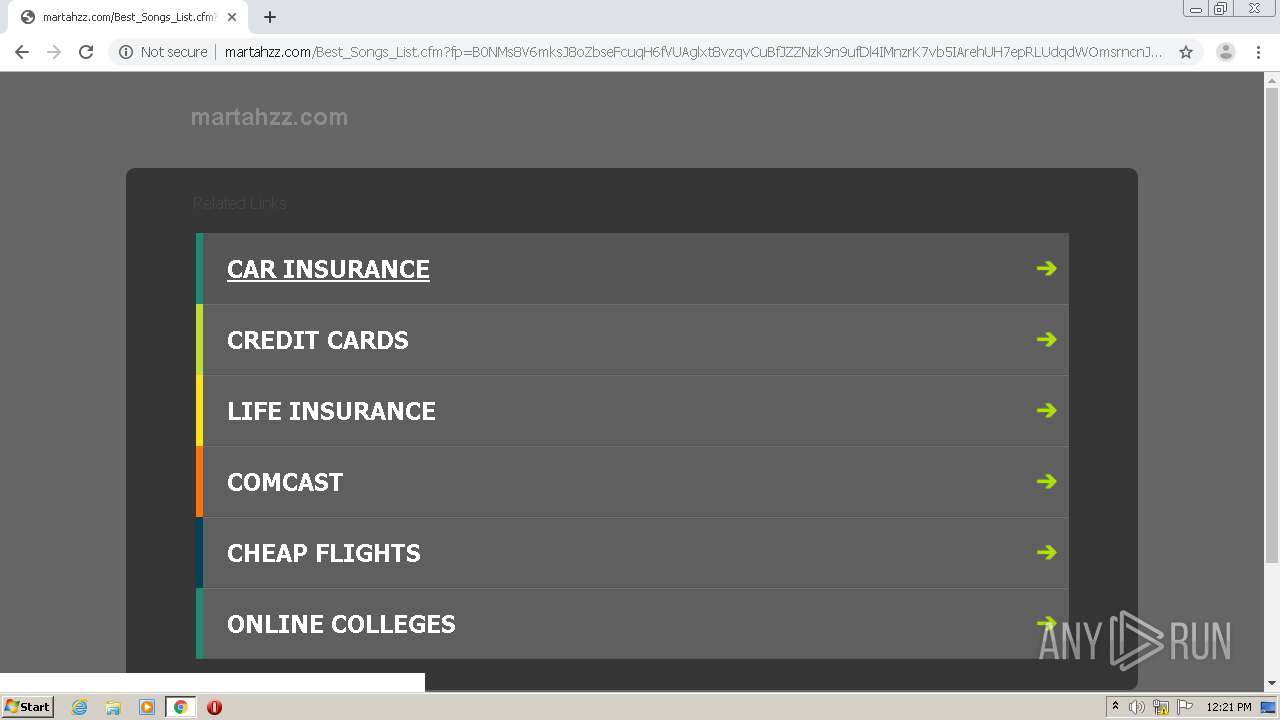
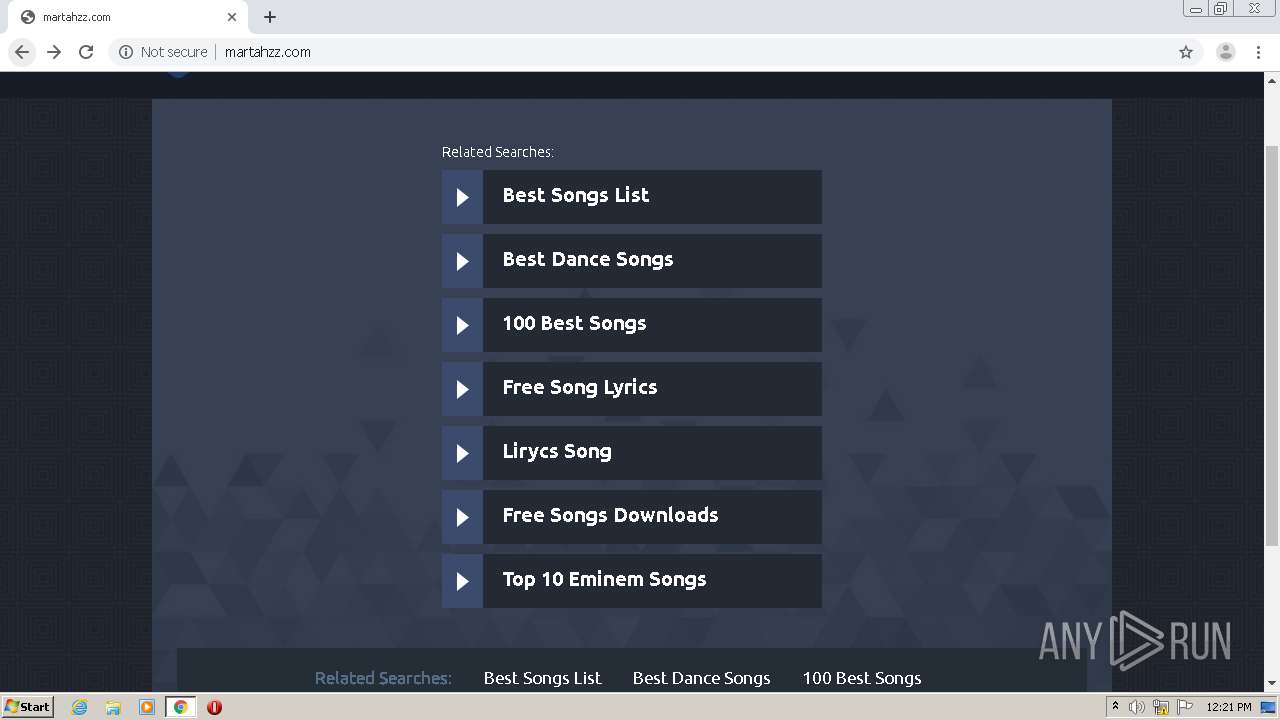
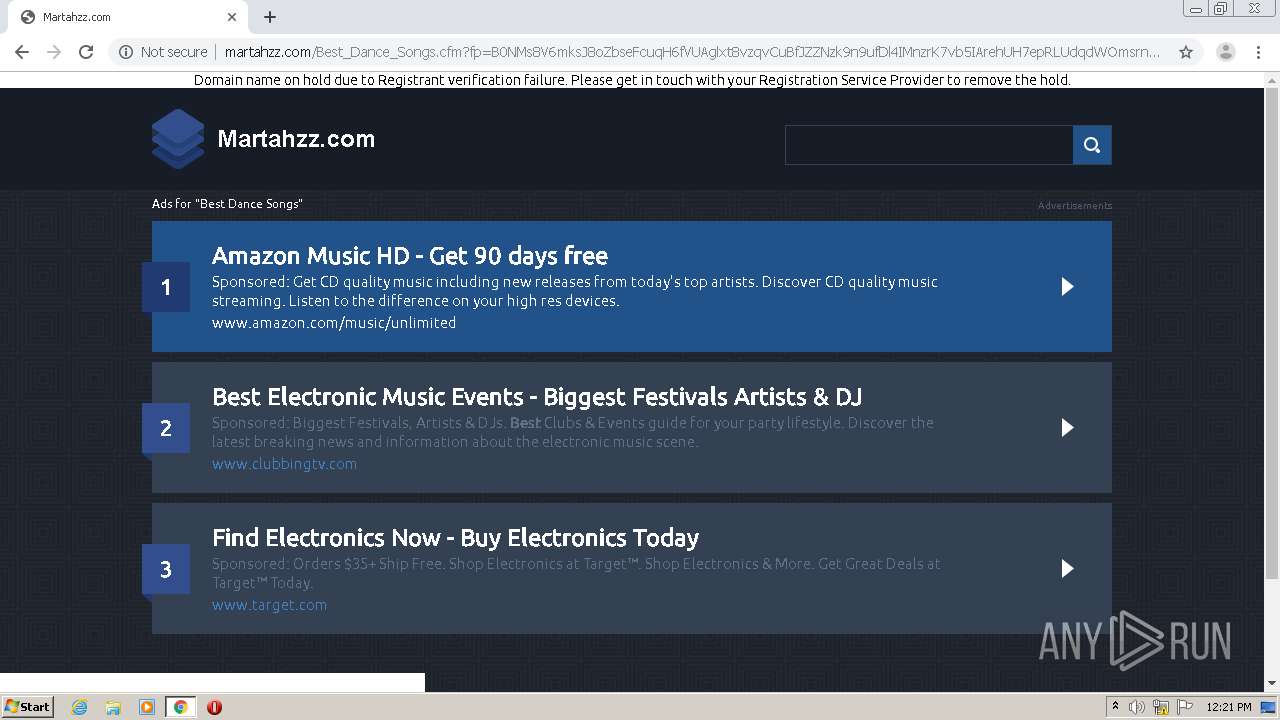
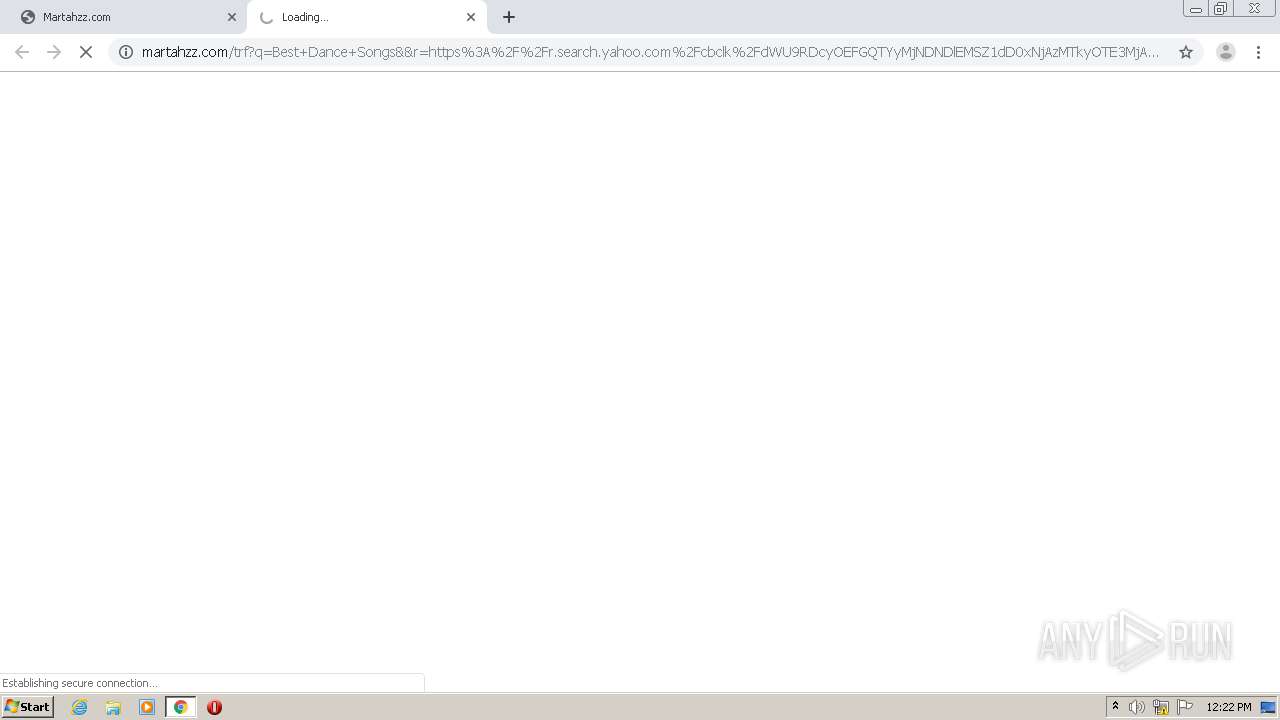
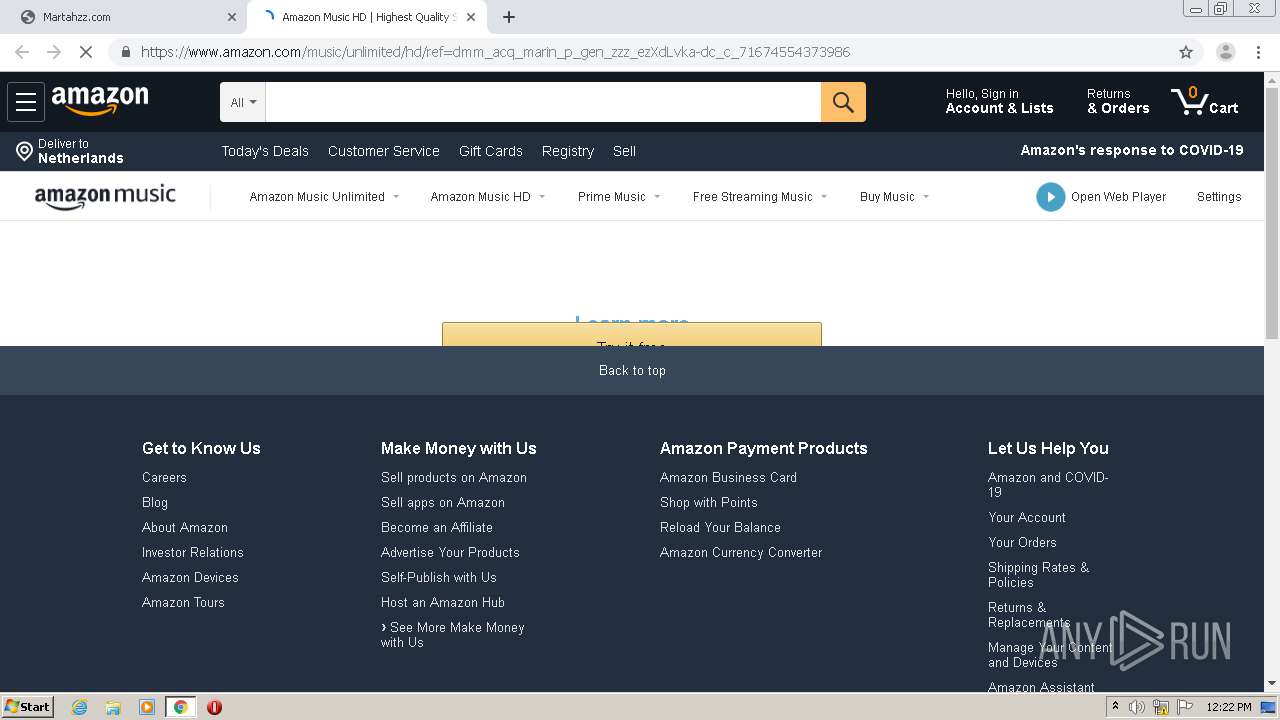
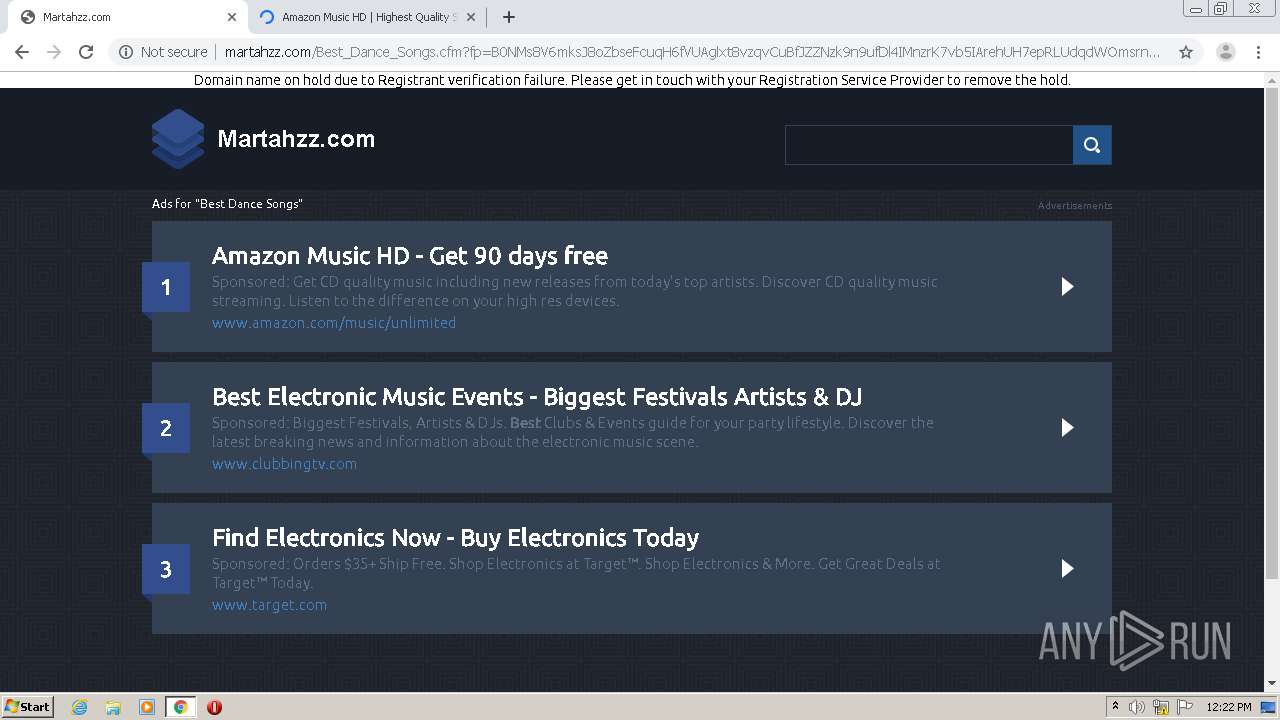
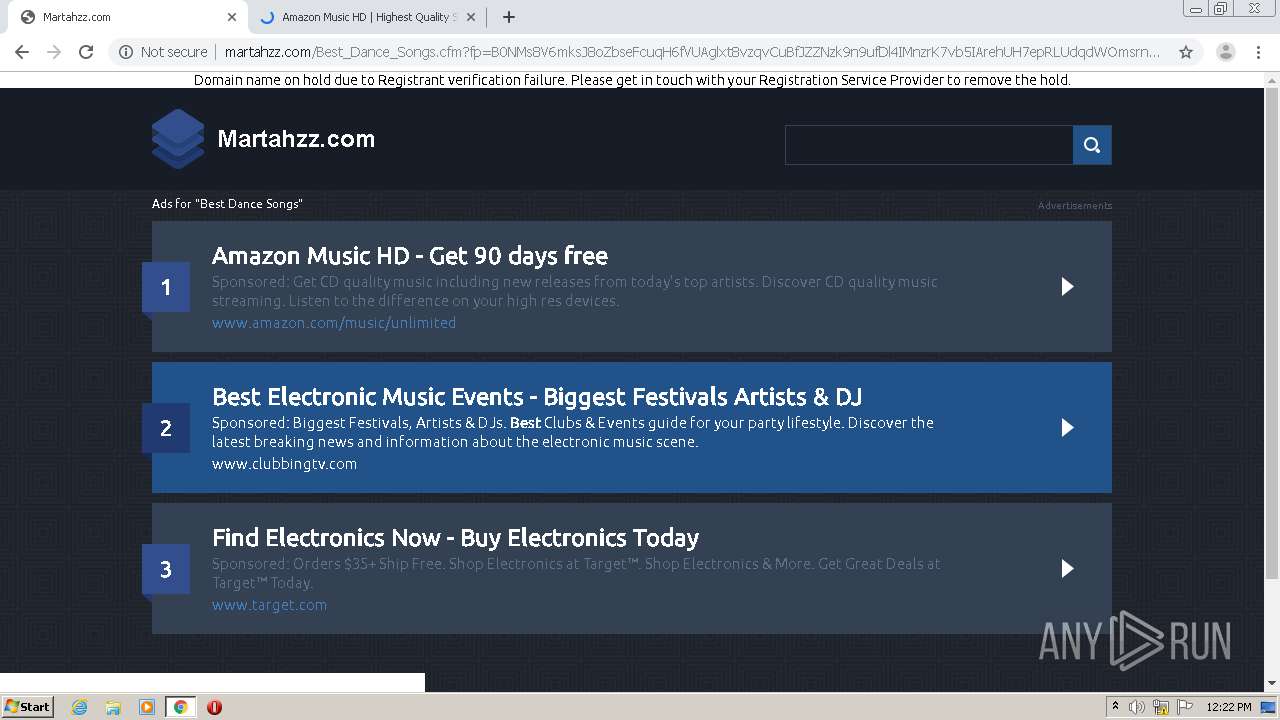
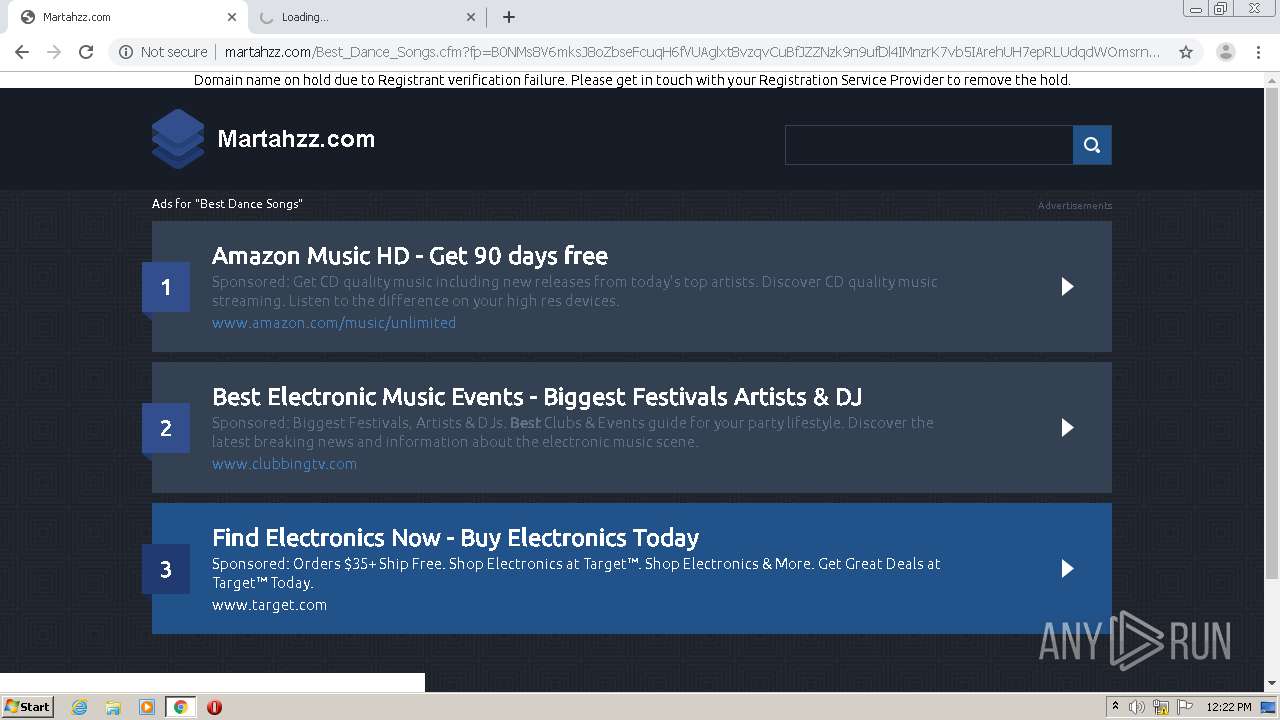
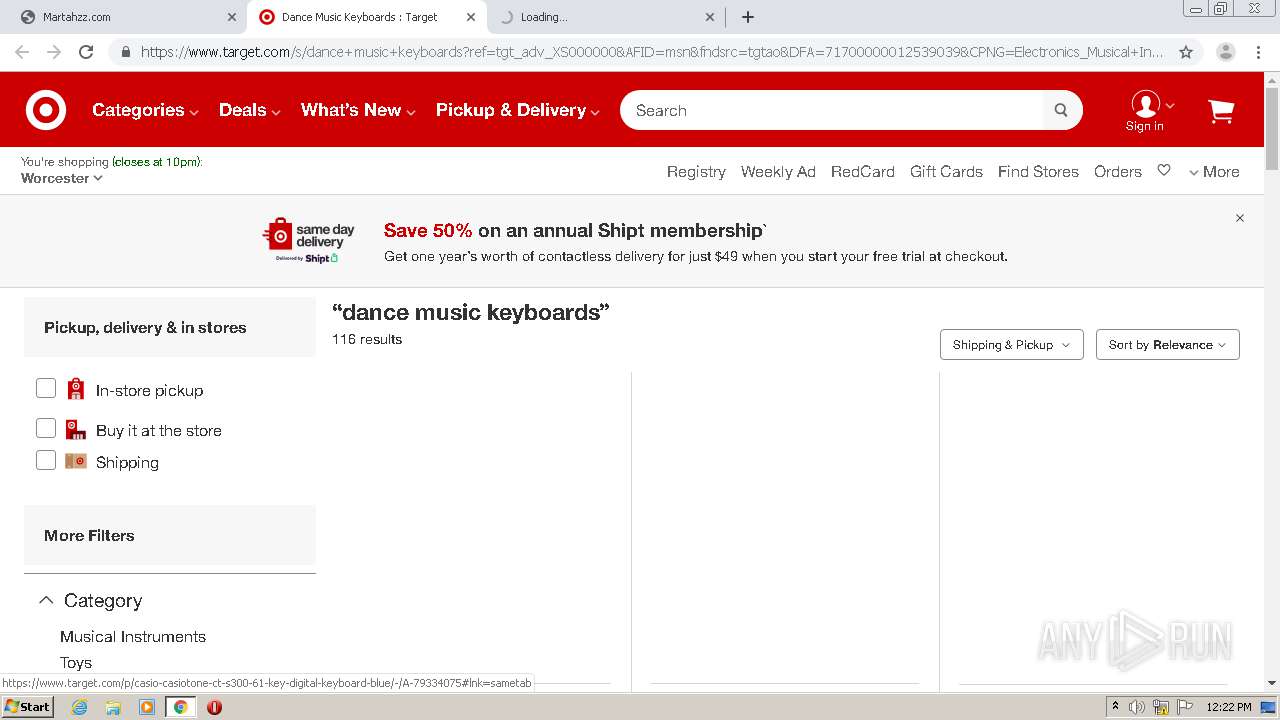
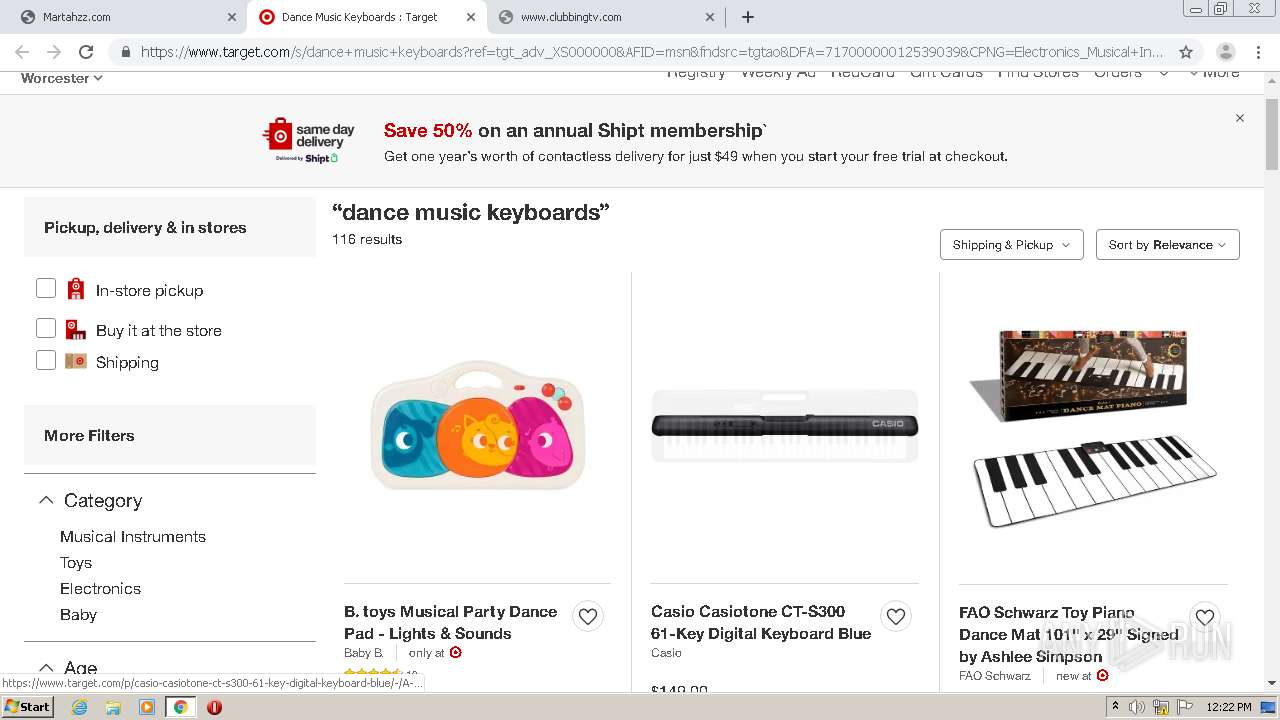
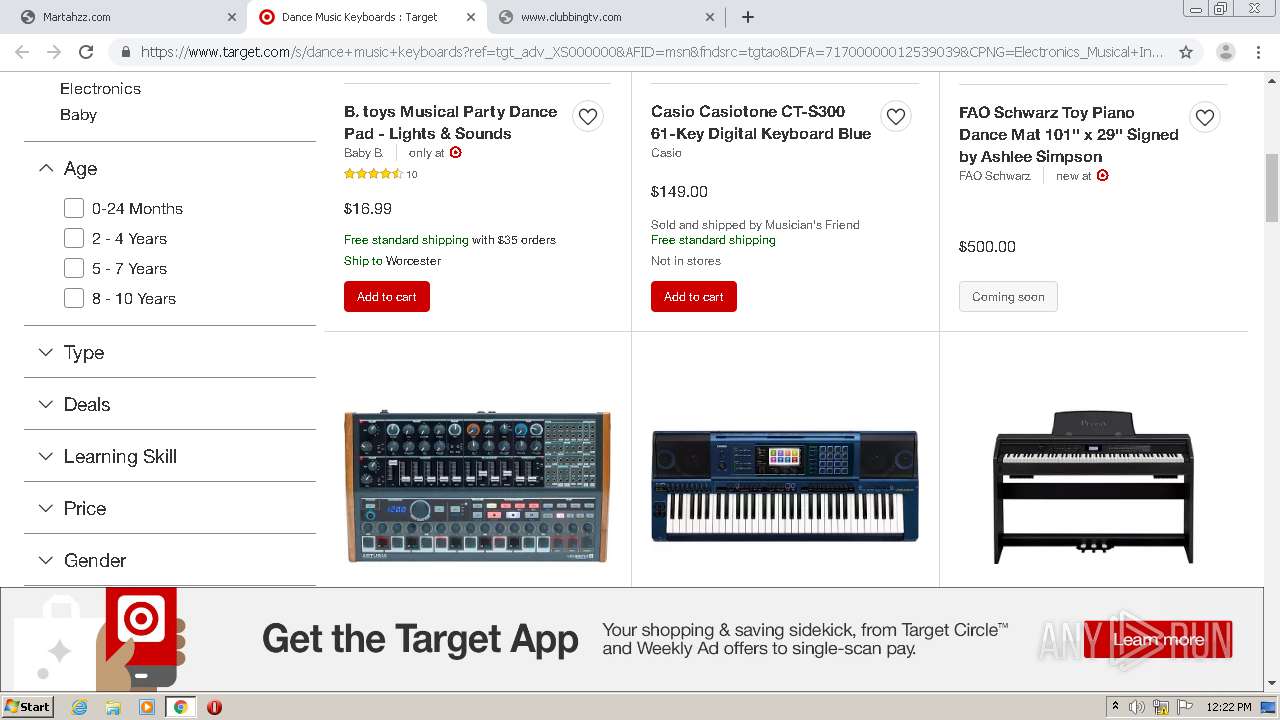
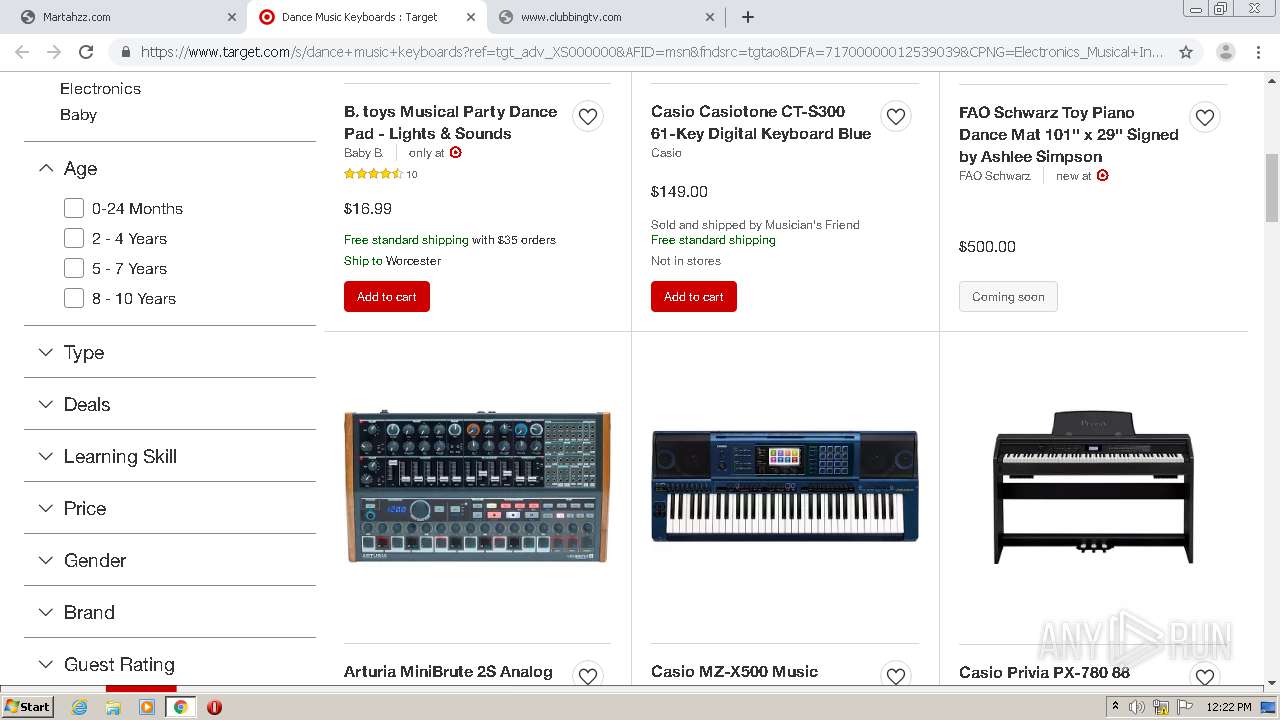
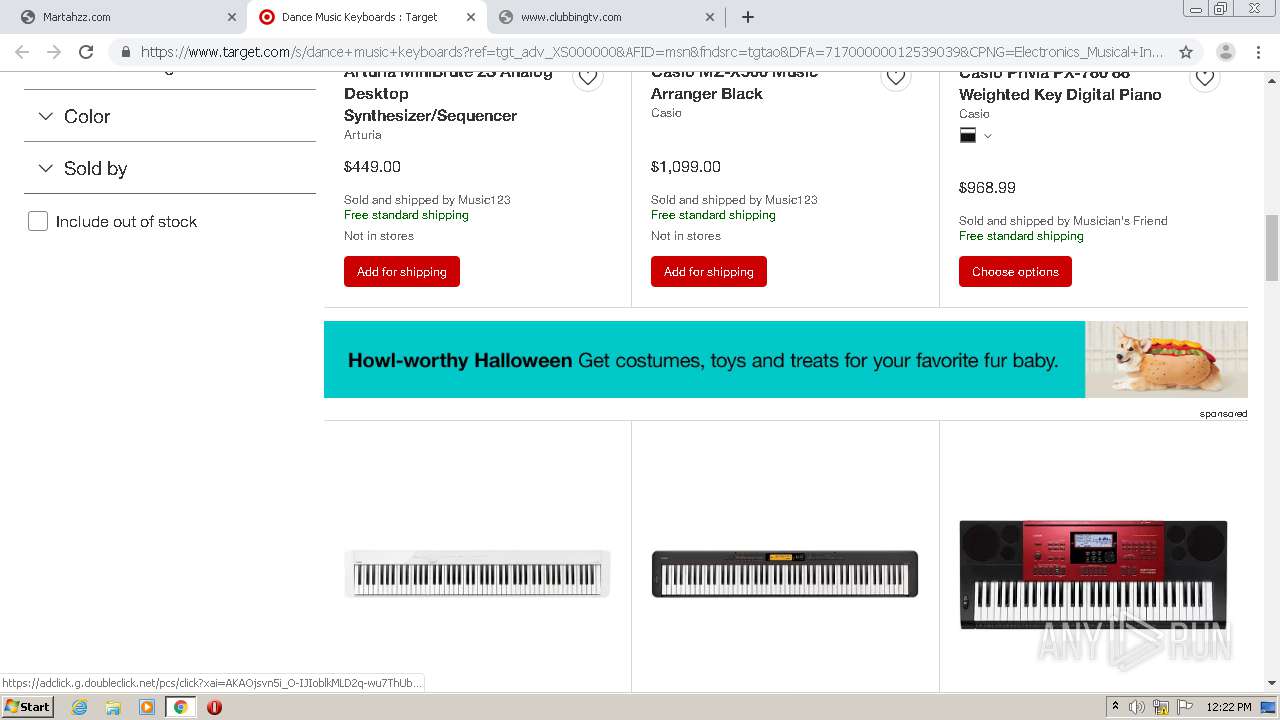
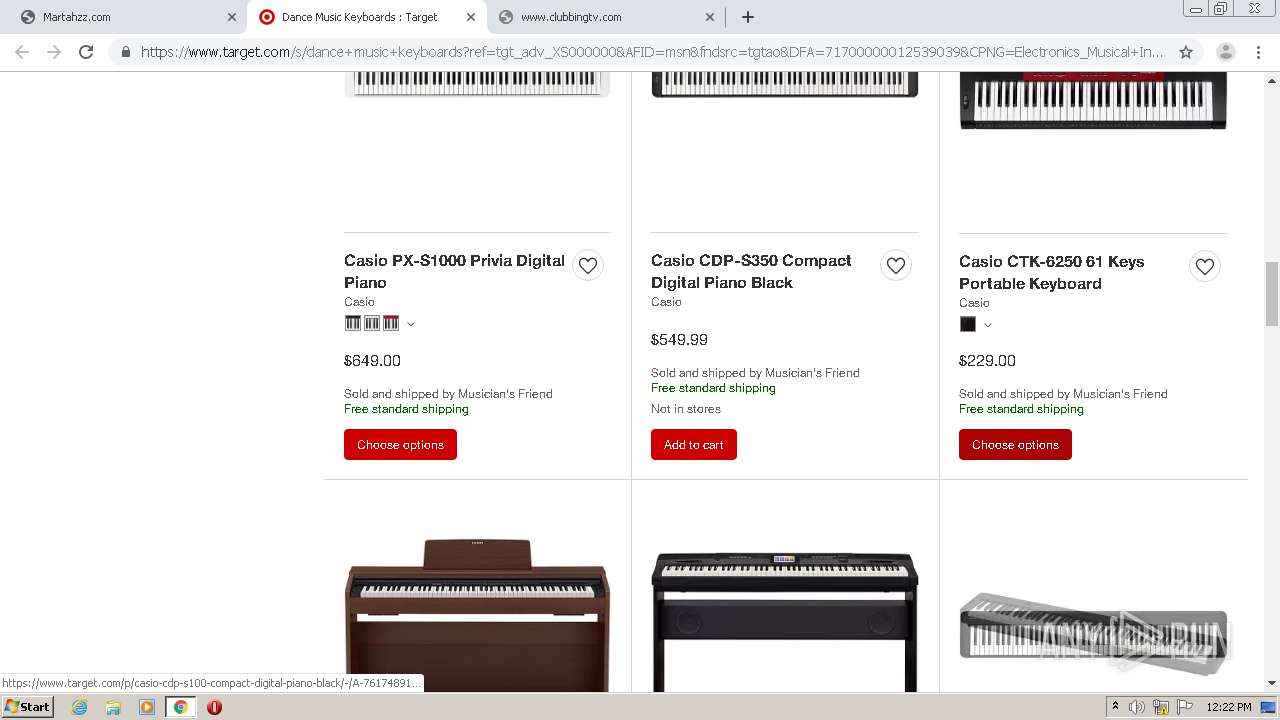
1044 | chrome.exe | GET | 200 | 209.99.64.76:80 | http://martahzz.com/ | US | html | 1.05 Kb | malicious |
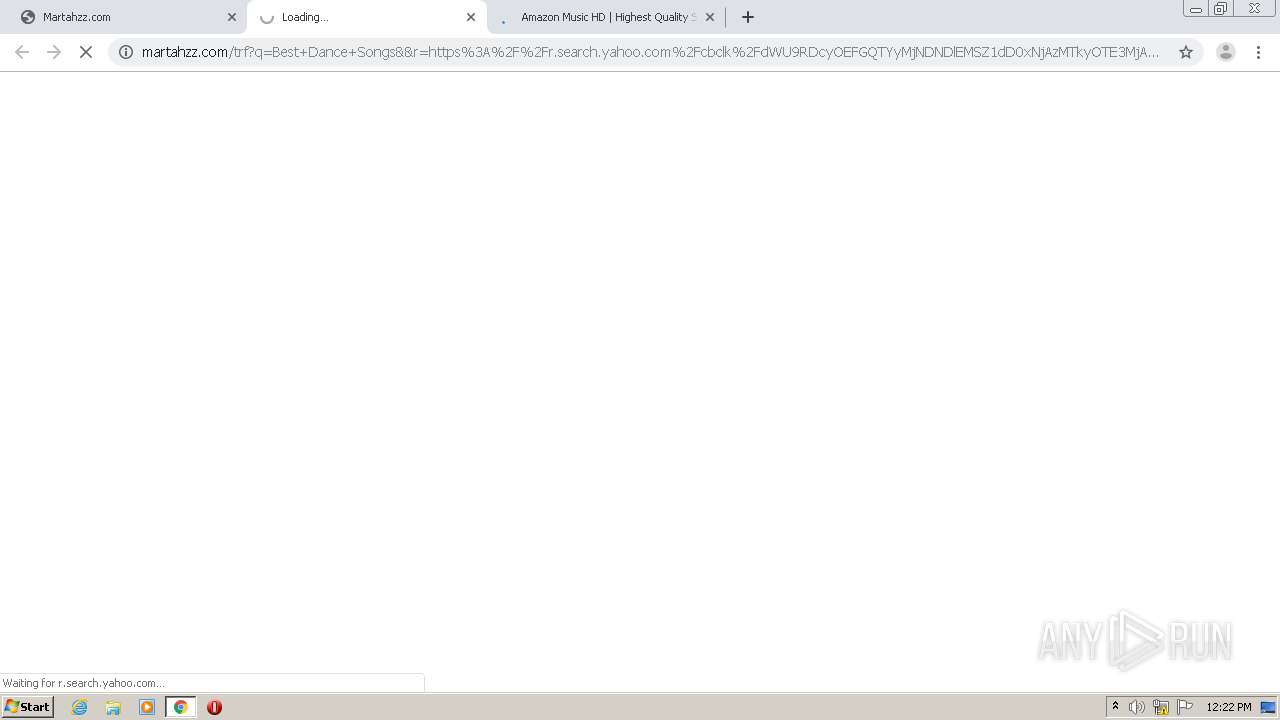
1044 | chrome.exe | GET | 200 | 209.99.64.76:80 | http://martahzz.com/?fp=IPRjMrc9VW1AXcjdAxtRGmD6n3%2FXJQ039VkAaPI%2BhIxj0M2uopIZMhTE6vzoLCfAfffRBGGOBIknxnFHO7a09%2F3GeLwQ4CyC%2BIB4wTwnfSJDTi1fklQMy%2FsL7B0ZPBZ5lpmNKUmGgjDlVrLAKjJSpKQ9XsusYpjm5kkBz8GlGek%3D&prvtof=obXZkzoDtfVnhaZjUznNYh57%2BTM9wHs6e%2F1Pe3FggpA%3D&poru=xdubdDNz5rhhjTqr14L1DlQT%2Fak8g%2BbAd7Y0EiJLT4CHs%2BPCWg79TRXhXbULCGuA& | US | html | 6.56 Kb | malicious |
1044 | chrome.exe | GET | 200 | 2.16.186.106:80 | http://i1.cdn-image.com/__media__/js/min.js?v2.2 | unknown | text | 2.97 Kb | whitelisted |
1044 | chrome.exe | GET | 200 | 91.195.240.136:80 | http://sedoparking.com/frmpark/martahzz.com/Skenzor4/park.js | DE | compressed | 617 b | whitelisted |
1044 | chrome.exe | GET | 200 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.5 Kb | whitelisted |
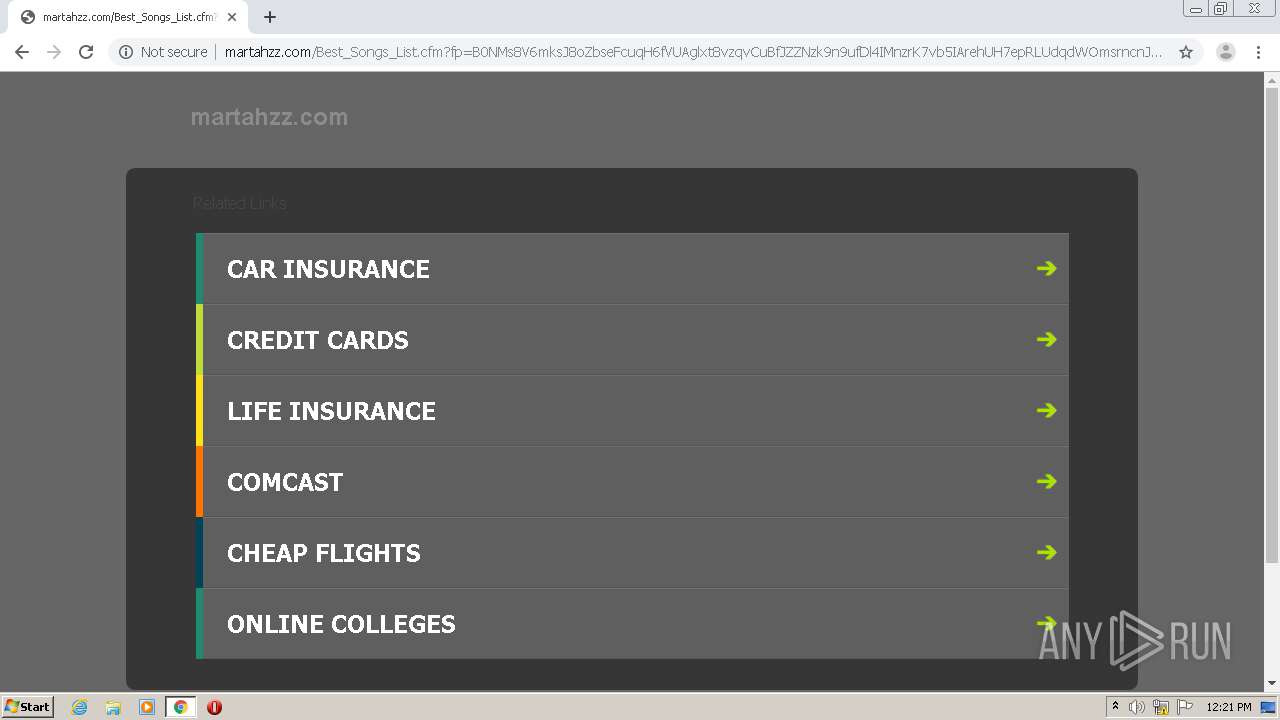
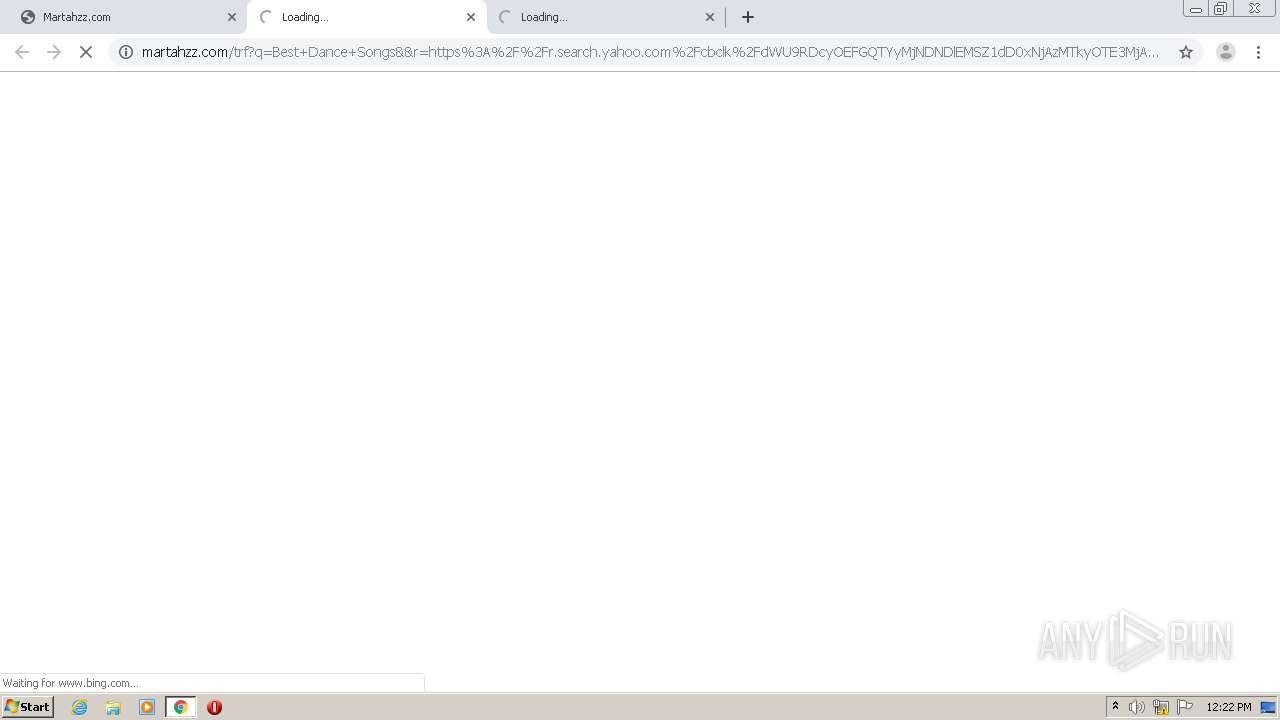
1044 | chrome.exe | GET | 200 | 209.99.64.76:80 | http://martahzz.com/Best_Songs_List.cfm?fp=B0NMs8V6mksJ8oZbseFcuqH6fVUAglxt8vzqvCuBfJZZNzk9n9ufDl4IMnzrK7vb5IArehUH7epRLUdqdWOmsrncnJFsZK6KJnIfzB9Rror5rx8aUrLQRN10et6VkhU%2Bp6znyy4gGJ2orm9l8XJ0vKD67XjtUqBlH3dz%2Fh43IQMPWlN3t%2BxqMwsD11dsOr8CQ3xnSWzi6b8GBX4d8bhfeQ%3D%3D&yep=fG7fwLOKKSW%2FFzcIsc%2FOUx5CWpF5s6mlwC64iO9J70N67l5phyjNch35TL9s541r5BP%2B6Mk86%2FaBUOfIU3FgoSd9cIxRwu2CpL1CG4Ti4AccBJpEkXqqUNjFdNKtspfOmAFBWYlwrFQ4Q7sLS%2BOPi42RfAc0vTPdgkoS7ykrGnux7nUu1qDF2kND7jHuI5Rfk8jmHT5ZAnFanq%2FtXAsOK6WmSy%2FD0RjjBlByUllEwyko%2BYtEQ67ijzl524FbMd3wttzh9hjTD7hF7TNzeg8pcpEDWClPhB28z7OKk0bQ1SGBISD3VUHZ5HwV%2BCA%2BTUe4owwPOlTmans8FB17xdsiosD9FUuZEYbeHE18E1ni17I4w0fQj70l8zmvFlekY%2BqaUCTRkguVx%2BrZy44CQWZLX%2B85JivoI6SZN92LcJ1TzXUdPK6S6UTbNy1O5fKc47VRvEqCb0%2FkZvKwOKkz1eKbzVf38hSo34cYehZBLdpO0FULDH4VaSGSDnKC%2FaMGD3CzPsERygKEDn2zRrMAwWOm4d1YpGj6iUwP1vsdL1LmoZTKMjF8x8rCr2iA%2FynOmXg0>np=0>pp=0&kbetu=0&maxads=0&kld=1061&yprpnd=vncuanDpHbwkoiHXmC5QPCAwwgJNBu13%2B1f4vQ3CtbM%3D&prvtof=obXZkzoDtfVnhaZjUznNYh57%2BTM9wHs6e%2F1Pe3FggpA%3D&>np=0>pp=0&kt=339&&kbc=111423&ki=3490415&ktd=256&kld=1061&kp=1&bd=1%23720%231280%231%230%23570%23215 | US | html | 1.15 Kb | malicious |
1044 | chrome.exe | GET | 200 | 172.217.22.34:80 | http://pagead2.googlesyndication.com/apps/domainpark/show_afd_ads.js | US | text | 1.28 Kb | whitelisted |
1044 | chrome.exe | GET | 200 | 209.99.64.76:80 | http://martahzz.com/px.js?ch=1 | US | text | 346 b | malicious |
1044 | chrome.exe | GET | 200 | 209.99.64.76:80 | http://martahzz.com/px.js?ch=2 | US | text | 346 b | malicious |
1044 | chrome.exe | GET | 200 | 2.16.186.106:80 | http://i1.cdn-image.com/__media__/pics/12471/kwbg.jpg | unknown | image | 36.3 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1044 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
1044 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1044 | chrome.exe | 209.99.64.76:443 | martahzz.com | Confluence Networks Inc | US | malicious |
1044 | chrome.exe | 205.185.216.42:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
1044 | chrome.exe | 216.58.205.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1044 | chrome.exe | 172.217.22.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
1044 | chrome.exe | 205.185.216.10:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
1044 | chrome.exe | 216.58.212.132:443 | www.google.com | Google Inc. | US | whitelisted |
1044 | chrome.exe | 209.99.64.76:80 | martahzz.com | Confluence Networks Inc | US | malicious |
1044 | chrome.exe | 172.217.16.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
martahzz.com |
| malicious |
accounts.google.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
www.google.com |
| malicious |
www.gstatic.com |
| whitelisted |
i1.cdn-image.com |
| whitelisted |
i4.cdn-image.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |