| URL: | https://gumblar.cn |
| Full analysis: | https://app.any.run/tasks/1adfc290-3c78-41bd-8d02-a2cf9384bd4e |
| Verdict: | Malicious activity |
| Analysis date: | April 13, 2020, 13:16:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F7B4111B149EDFE22D0C0250696F17E8 |
| SHA1: | DF798CB343F299A6BFA3A10A43DC728A1B72D776 |
| SHA256: | A637EAA60D3347A4EEF1167F8E96AE74C3C4E5610880AA0465C5F8628AAF564B |
| SSDEEP: | 3:N8xnbcn:2dbcn |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 3552)
Changes internet zones settings
- iexplore.exe (PID: 3552)
Reads Internet Cache Settings
- iexplore.exe (PID: 1348)
- iexplore.exe (PID: 3552)
Reads internet explorer settings
- iexplore.exe (PID: 1348)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 1348)
Creates files in the user directory
- iexplore.exe (PID: 1348)
Reads settings of System Certificates
- iexplore.exe (PID: 1348)
- iexplore.exe (PID: 3552)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3552)
Changes settings of System certificates
- iexplore.exe (PID: 3552)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1348 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3552 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3552 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://gumblar.cn" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
6 233
Read events
955
Write events
3 562
Delete events
1 716
Modification events
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3398723634 | |||
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30806421 | |||
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3552) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
88
Text files
253
Unknown types
41
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3552 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1348 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\C5MD1VIC.txt | — | |
MD5:— | SHA256:— | |||
| 1348 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\SNJQQ1QI.txt | — | |
MD5:— | SHA256:— | |||
| 1348 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\qsml[1].htm | — | |
MD5:— | SHA256:— | |||
| 1348 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\86FAP2B5.txt | — | |
MD5:— | SHA256:— | |||
| 1348 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\-nK5HAtc03YD_-fIE4Q-t8DnnZY[1].js | — | |
MD5:— | SHA256:— | |||
| 1348 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\qsml[2].xml | xml | |
MD5:— | SHA256:— | |||
| 1348 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\errorPageStrings[1] | text | |
MD5:— | SHA256:— | |||
| 1348 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\E3EW7NPP.txt | text | |
MD5:— | SHA256:— | |||
| 1348 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\qsml[3].xml | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
122
TCP/UDP connections
138
DNS requests
54
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1348 | iexplore.exe | GET | — | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=gumbla&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
1348 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/30/2V/cj,nj/GTd5evTp2v9quFX_8_4U14MoprA.js | US | text | 816 b | whitelisted |
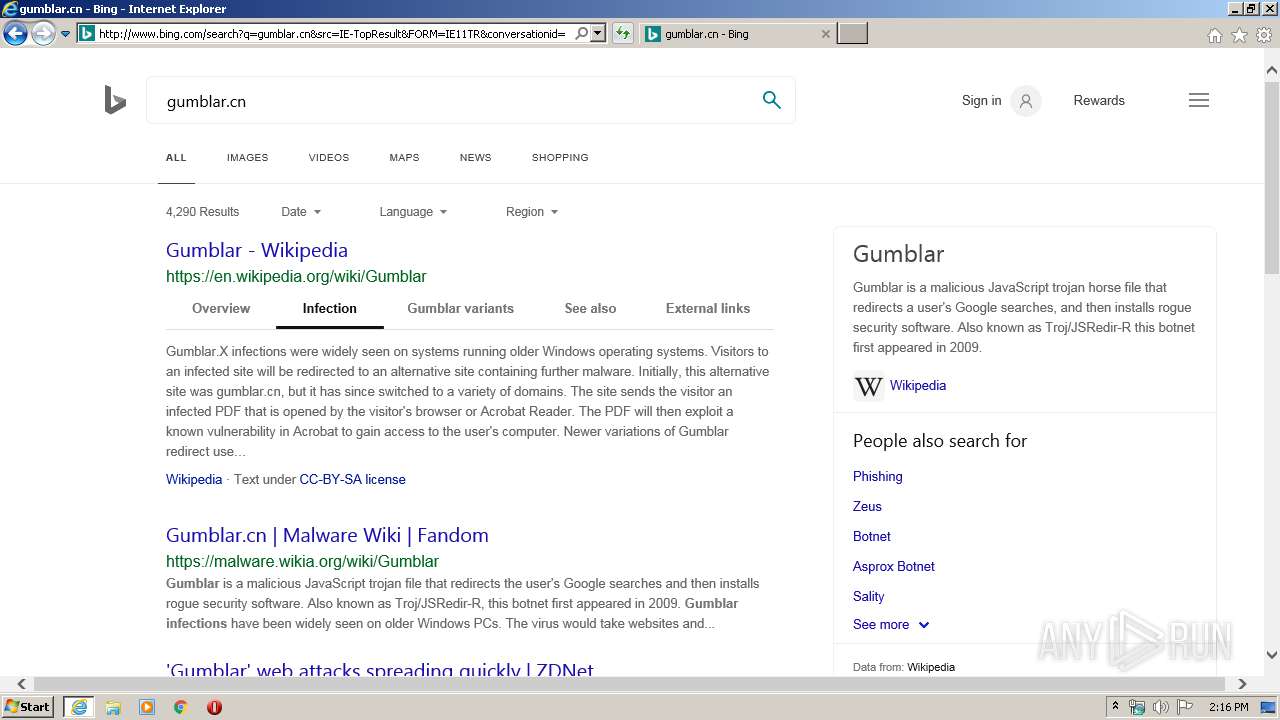
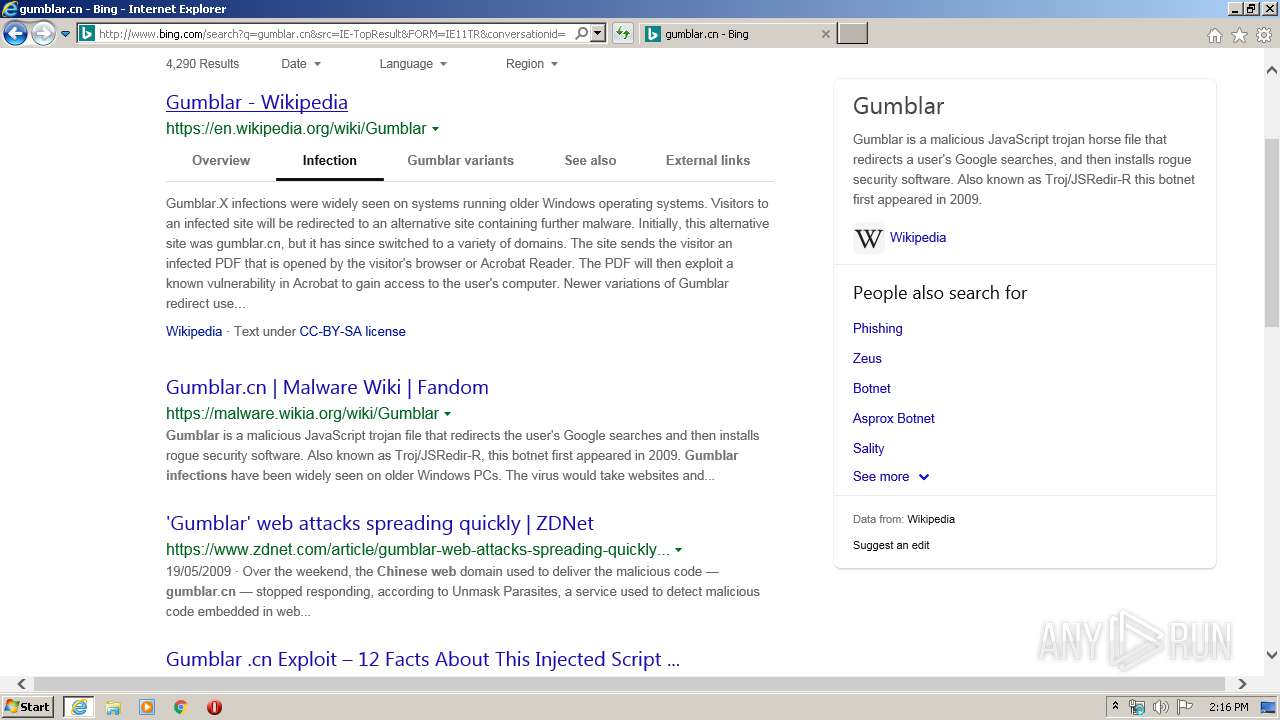
1348 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/search?q=gumblar.cn&src=IE-TopResult&FORM=IE11TR&conversationid= | US | html | 58.7 Kb | whitelisted |
1348 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rb/5h/cj,nj/HFaO5LQxx7XVmFXIaSdEImHAAPM.js?bu=E54hsiHdIOggrAX3IPkgyiH7IIoh_iCvIawhuCGXIKYfqR-aIJ4M | US | text | 5.57 Kb | whitelisted |
1348 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/6C/ww/nj/IoGu84dxcNh7wQyayqOk_R7kai4.js | US | text | 353 b | whitelisted |
1348 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/6h/14W/cj,nj/JOVKK9CwtlLttGBW-c2T2aVxX_U.js | US | text | 297 b | whitelisted |
1348 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=gumblar.cn&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 194 b | whitelisted |
1348 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/30/3i/cj,nj/zqF1NsFR7vS1hEarPv8Ova9tpdA.js | US | text | 177 b | whitelisted |
1348 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=gumb&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 224 b | whitelisted |
1348 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rb/14/cj,nj/-nK5HAtc03YD_-fIE4Q-t8DnnZY.js?bu=DiovYnJ3em9laLEBswEvngEv | US | text | 7.65 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1348 | iexplore.exe | 204.79.197.222:80 | fp.msedge.net | Microsoft Corporation | US | whitelisted |
3552 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1348 | iexplore.exe | 13.107.5.80:80 | api.bing.com | Microsoft Corporation | US | whitelisted |
1348 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1348 | iexplore.exe | 20.190.129.130:443 | login.microsoftonline.com | Microsoft Corporation | US | malicious |
1348 | iexplore.exe | 40.90.137.124:443 | login.live.com | Microsoft Corporation | US | unknown |
1348 | iexplore.exe | 74.120.188.204:443 | slot1-images.wikia.nocookie.net | — | US | suspicious |
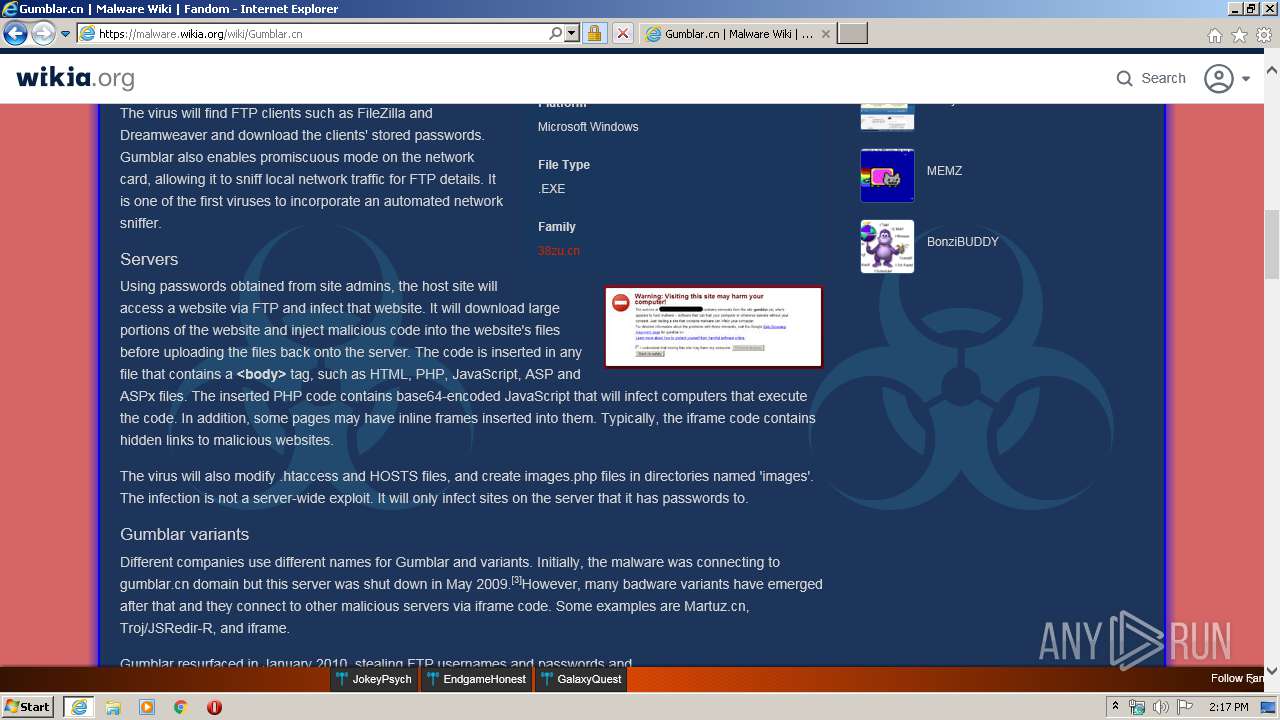
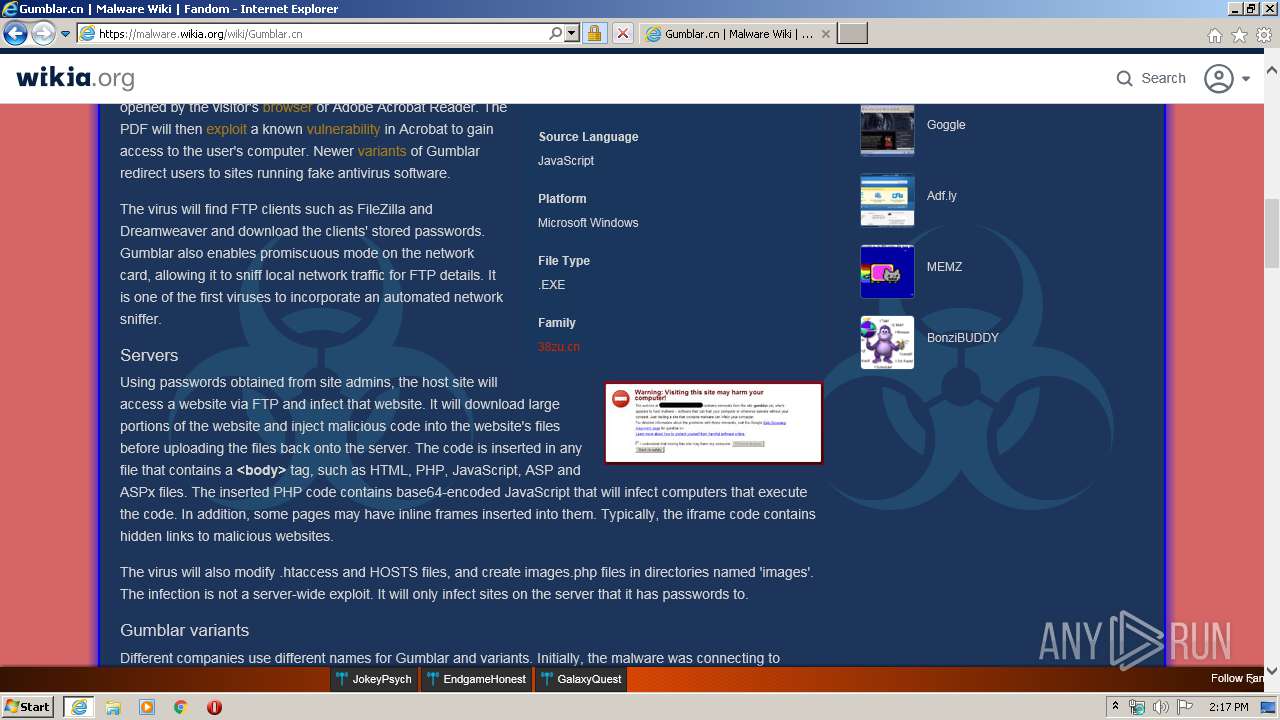
1348 | iexplore.exe | 151.101.0.194:443 | malware.wikia.org | Fastly | US | suspicious |
1348 | iexplore.exe | 104.18.21.226:80 | ocsp.globalsign.com | Cloudflare Inc | US | shared |
1348 | iexplore.exe | 151.101.2.66:443 | www.fastly-insights.com | Fastly | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
gumblar.cn |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.microsoftonline.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp.msocsp.com |
| whitelisted |
967d4454fb89e57927228acaedb2549e.clo.footprintdns.com |
| unknown |
51835bae39cff272261c3a9caee1ef40.clo.footprintdns.com |
| unknown |
www2.bing.com |
| whitelisted |