| File name: | csrs.exe |
| Full analysis: | https://app.any.run/tasks/a84f3f7a-b4c0-4186-9bf0-916558b0faea |
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2024, 10:45:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | ED43F6043F51FBA6B2A8A4062256154D |
| SHA1: | 4CF081FDE15F702C434B588F0556D28227AE1F1A |
| SHA256: | A62C67BB2C90D79FFC64D3862C73EA77255581D224A8736C470DC72A6716C6E3 |
| SSDEEP: | 98304:jjMfI4FnJvEd/4SiLjnTCyUcYvDG2KuNVTid/h2ygXZ8joBSx7xmL0Oj+XzLLdZo:mxS0RI5Fi5w5ULD |
MALICIOUS
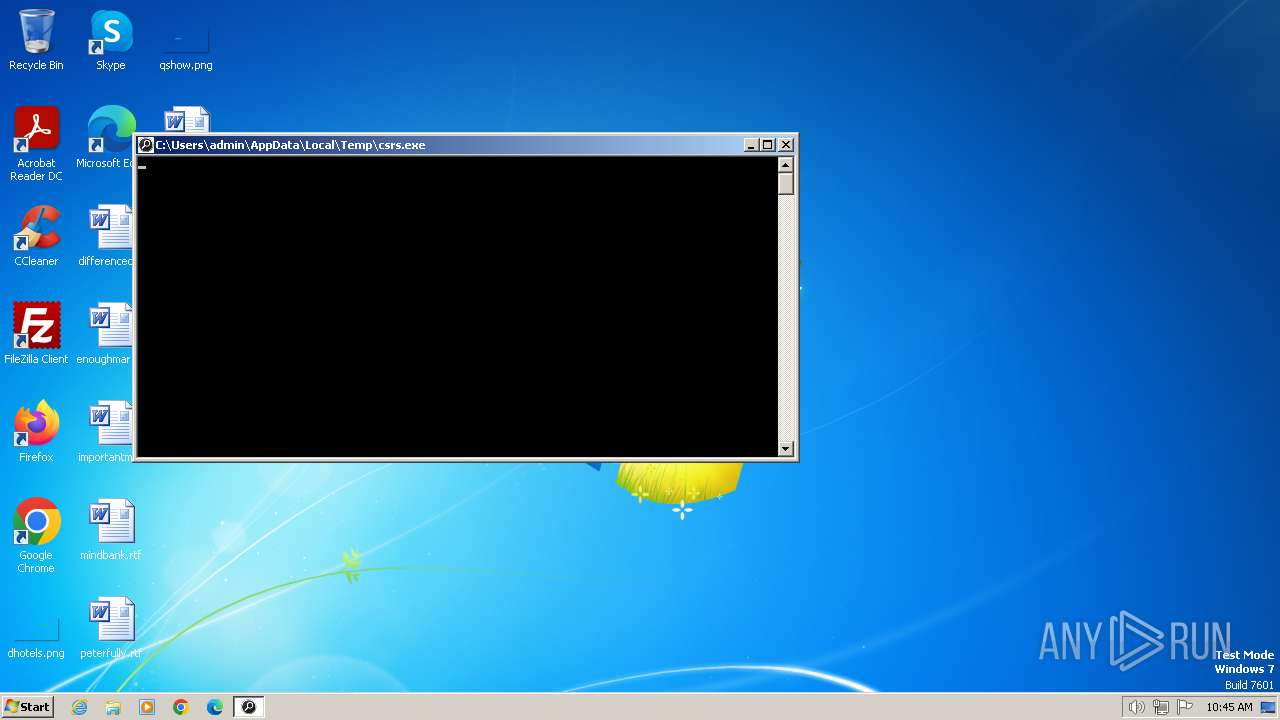
Drops the executable file immediately after the start
- csrs.exe (PID: 2124)
SUSPICIOUS
Process drops legitimate windows executable
- csrs.exe (PID: 2124)
Process drops python dynamic module
- csrs.exe (PID: 2124)
Starts a Microsoft application from unusual location
- csrs.exe (PID: 1696)
- csrs.exe (PID: 2124)
Application launched itself
- csrs.exe (PID: 2124)
The process drops C-runtime libraries
- csrs.exe (PID: 2124)
Executable content was dropped or overwritten
- csrs.exe (PID: 2124)
INFO
Checks supported languages
- csrs.exe (PID: 2124)
- csrs.exe (PID: 1696)
Reads the machine GUID from the registry
- csrs.exe (PID: 1696)
Create files in a temporary directory
- csrs.exe (PID: 2124)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (50.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (32.2) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.6) |
| .exe | | | Win32 Executable (generic) (5.2) |
| .exe | | | Generic Win/DOS Executable (2.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:09:04 14:42:13+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 128000 |
| InitializedDataSize: | 116224 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x779a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.1 |
| ProductVersionNumber: | 1.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Registry Editor |
| FileVersion: | 1.0.0.1 (win7_rtm.090713-1255) |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 1.0.0.1 |
Total processes
38
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1696 | "C:\Users\admin\AppData\Local\Temp\csrs.exe" | C:\Users\admin\AppData\Local\Temp\csrs.exe | — | csrs.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Editor Exit code: 4294967295 Version: 1.0.0.1 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2124 | "C:\Users\admin\AppData\Local\Temp\csrs.exe" | C:\Users\admin\AppData\Local\Temp\csrs.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Editor Exit code: 4294967295 Version: 1.0.0.1 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
213
Read events
213
Write events
0
Delete events
0
Modification events
Executable files
24
Suspicious files
0
Text files
13
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2124 | csrs.exe | C:\Users\admin\AppData\Local\Temp\_MEI21242\Crypto.Cipher._AES.pyd | executable | |
MD5:B56AAF0210BFB85F07CB3596CF697CF6 | SHA256:A70ADC762AF5C358078BDA565F3072741A1FE7EFFBE4939C6635F6118B7B9203 | |||
| 2124 | csrs.exe | C:\Users\admin\AppData\Local\Temp\_MEI21242\_socket.pyd | executable | |
MD5:D41582EF0068483DC80EE8932EC867A0 | SHA256:C036C613E3AE35AA168597FDAEEA4A171A6AFF6FA91A429E098B457B8B531C7A | |||
| 2124 | csrs.exe | C:\Users\admin\AppData\Local\Temp\_MEI21242\Crypto.Random.OSRNG.winrandom.pyd | executable | |
MD5:BDACC99B02FE99511FA074B93FCB513B | SHA256:2E015B1C57B7A0E4E631023888376CB66704845BE38F0A66FDEE39D250A70157 | |||
| 2124 | csrs.exe | C:\Users\admin\AppData\Local\Temp\_MEI21242\Crypto.Util._counter.pyd | executable | |
MD5:63A2837BCDF80EABF42E035DD0033CB6 | SHA256:01F4468ABC18529611387F18DCDA33C04A0E38DAF8934603292B450684247F8A | |||
| 2124 | csrs.exe | C:\Users\admin\AppData\Local\Temp\_MEI21242\Crypto.Util.strxor.pyd | executable | |
MD5:00463E5FB0A05F2F664EC47E13D5DF42 | SHA256:EF506015E3E596A9416DFBF001FA551586BCF99EC4D672D9A73120F4F5997D41 | |||
| 2124 | csrs.exe | C:\Users\admin\AppData\Local\Temp\_MEI21242\Microsoft.VC90.CRT.manifest | xml | |
MD5:7D36F7F779B92DC3CF7B930F519005D1 | SHA256:0B3C3E0DE20A553C59DFB19A23219D3526CE19EB2F6007315A987F4609A4D0BA | |||
| 2124 | csrs.exe | C:\Users\admin\AppData\Local\Temp\_MEI21242\Crypto.Hash._MD4.pyd | executable | |
MD5:8F892DD81E95D2EB665664BEC25A81C0 | SHA256:E9E7192BE4D2E97CF4C5079FB1CA6452513FCCDD822ABDF1AD9C189B33EEC026 | |||
| 2124 | csrs.exe | C:\Users\admin\AppData\Local\Temp\_MEI21242\bz2.pyd | executable | |
MD5:D9B4C951D50BFDFD5ABAF6711685674D | SHA256:BE7E19131EAF2D4F5C5CDF8636341055D257918DB1EACBA0022E6805A542B27D | |||
| 2124 | csrs.exe | C:\Users\admin\AppData\Local\Temp\_MEI21242\MyExploiter.exe.manifest | xml | |
MD5:969F66EA868DC6EB44D6D009D41953D3 | SHA256:B7660B47D54FA972D90BCE643ED6E10574729669DF40505F9E9F91C769A3F1DE | |||
| 2124 | csrs.exe | C:\Users\admin\AppData\Local\Temp\_MEI21242\_ssl.pyd | executable | |
MD5:B23BAF85B894C6531A027CA1D2C13AF8 | SHA256:04904526E533CC3F6658F90955827B2C569B70352A76725F507553409BF6A498 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |