| File name: | vctool_setup.exe |
| Full analysis: | https://app.any.run/tasks/c91aac2b-a9b1-450d-bdd4-50476e3fd1f7 |
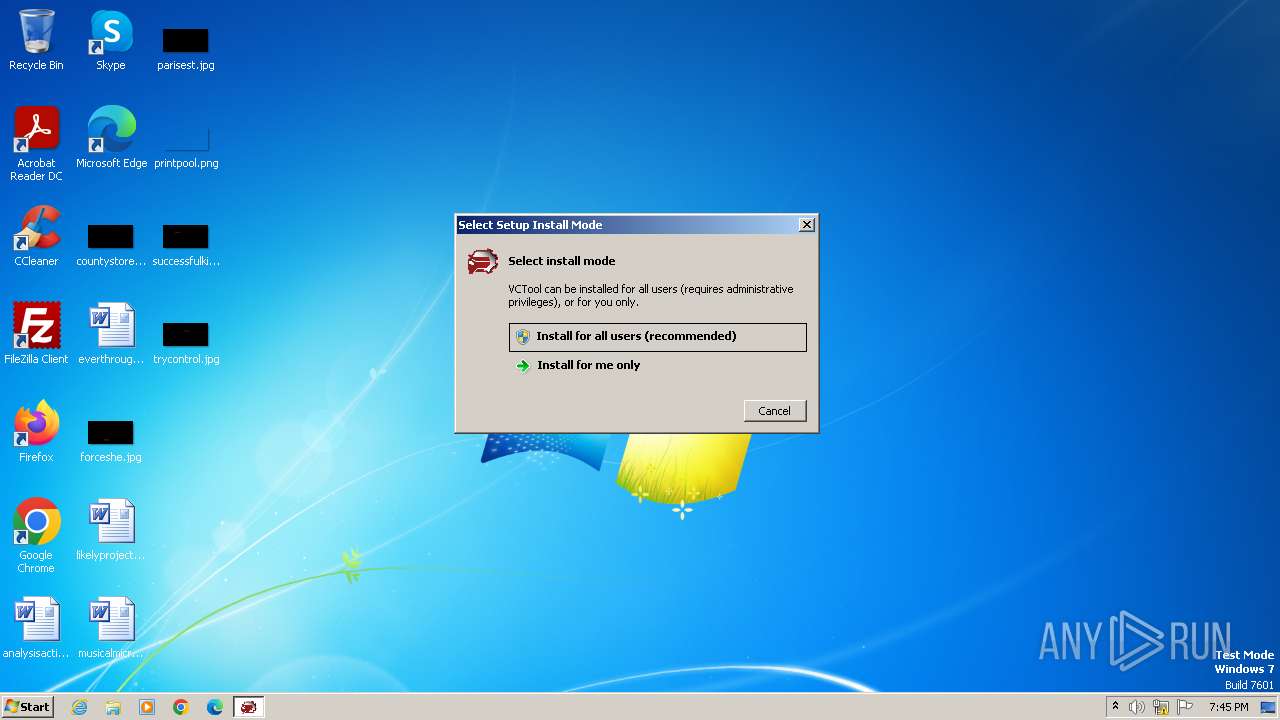
| Verdict: | Malicious activity |
| Analysis date: | December 05, 2023, 19:45:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | FEC66952C78EB66A89689CFC12F0C4E6 |
| SHA1: | D1D59EB2E2F42385E58977F43D01C73466DBE5D3 |
| SHA256: | A61EA9AA7DE44ACC3B7E12CEFC057D9B0042A9490E18CD4DD4607FC3B1A42BE0 |
| SSDEEP: | 98304:p+QqZ8f0HsHzrY2bi19klKPmqSRY71acufmC8YmxP+d0qoL4nbWuh6nplMnBsWiE:HDPeAYO4cEYU/XUPiFl6 |
MALICIOUS
Drops the executable file immediately after the start
- vctool_setup.exe (PID: 1556)
- vctool_setup.tmp (PID: 2076)
Actions looks like stealing of personal data
- vctool_setup.tmp (PID: 2076)
SUSPICIOUS
Reads the Windows owner or organization settings
- vctool_setup.tmp (PID: 2076)
Process drops legitimate windows executable
- vctool_setup.tmp (PID: 2076)
Reads security settings of Internet Explorer
- VCTool.exe (PID: 1036)
Reads the Internet Settings
- VCTool.exe (PID: 1036)
Reads settings of System Certificates
- VCTool.exe (PID: 1036)
Checks Windows Trust Settings
- VCTool.exe (PID: 1036)
INFO
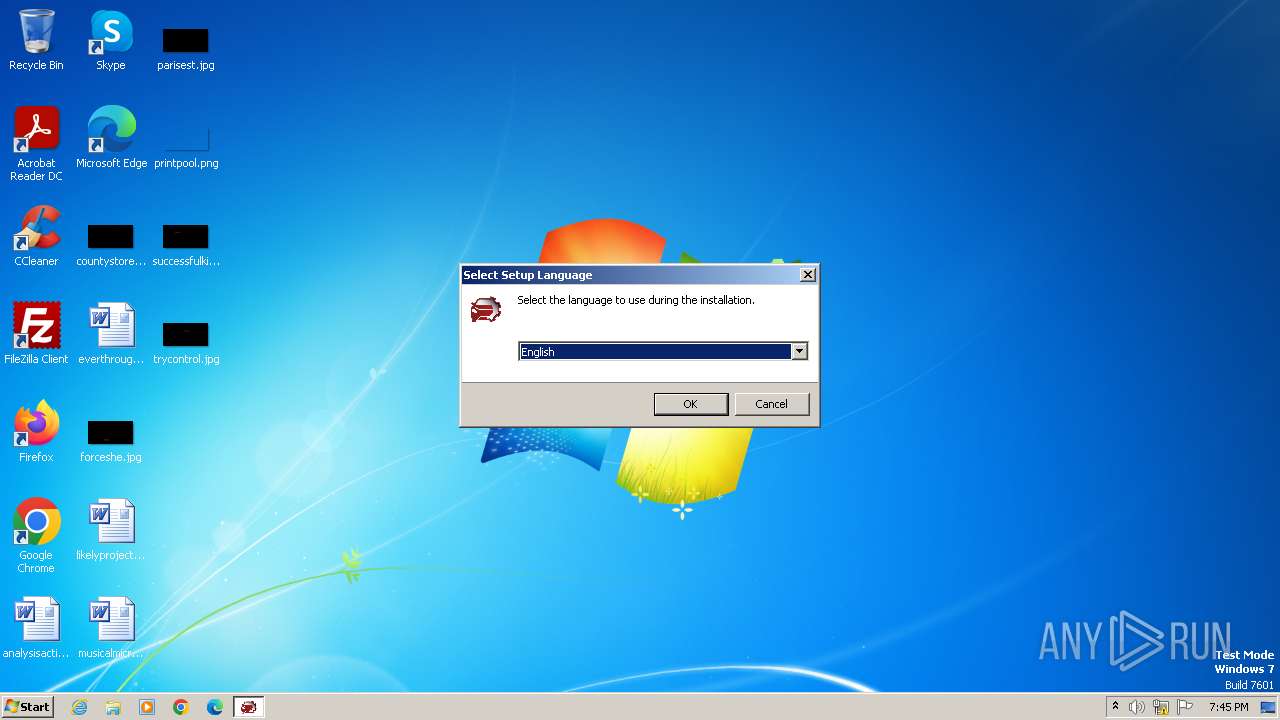
Checks supported languages
- vctool_setup.exe (PID: 1556)
- vctool_setup.tmp (PID: 2076)
- VCTool.exe (PID: 1036)
Create files in a temporary directory
- vctool_setup.exe (PID: 1556)
- VCTool.exe (PID: 1036)
Reads the computer name
- vctool_setup.tmp (PID: 2076)
- VCTool.exe (PID: 1036)
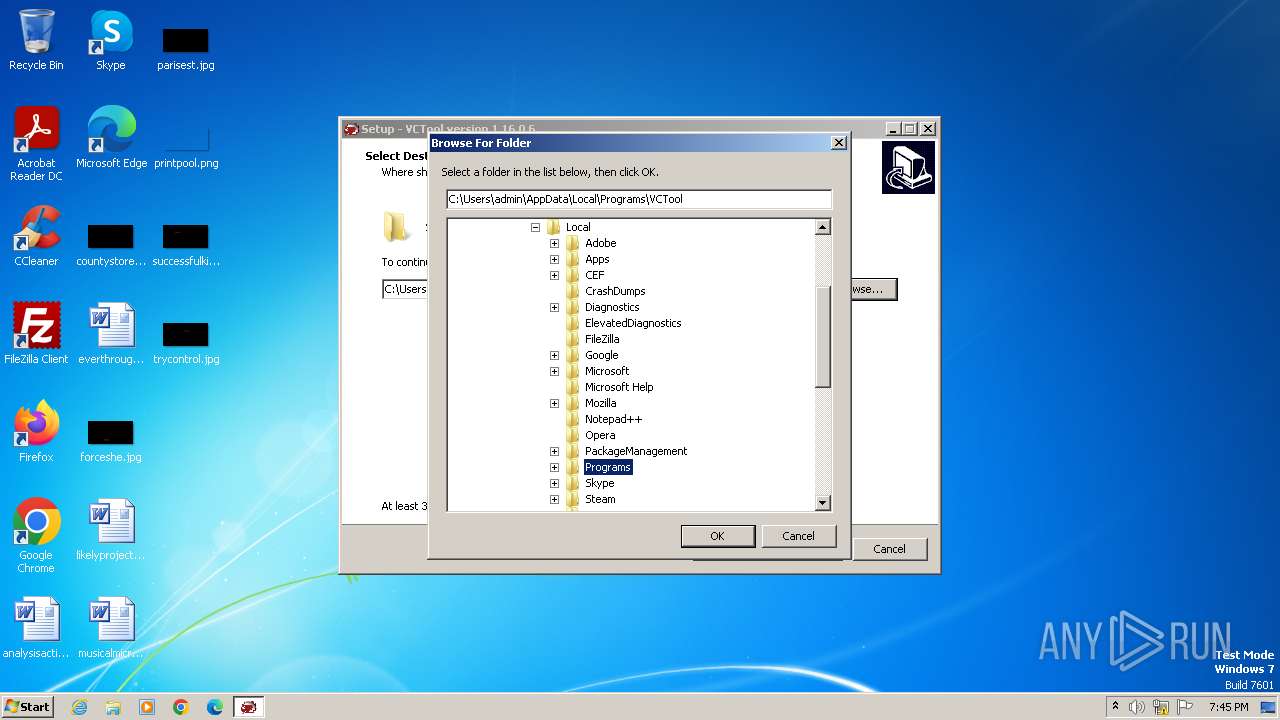
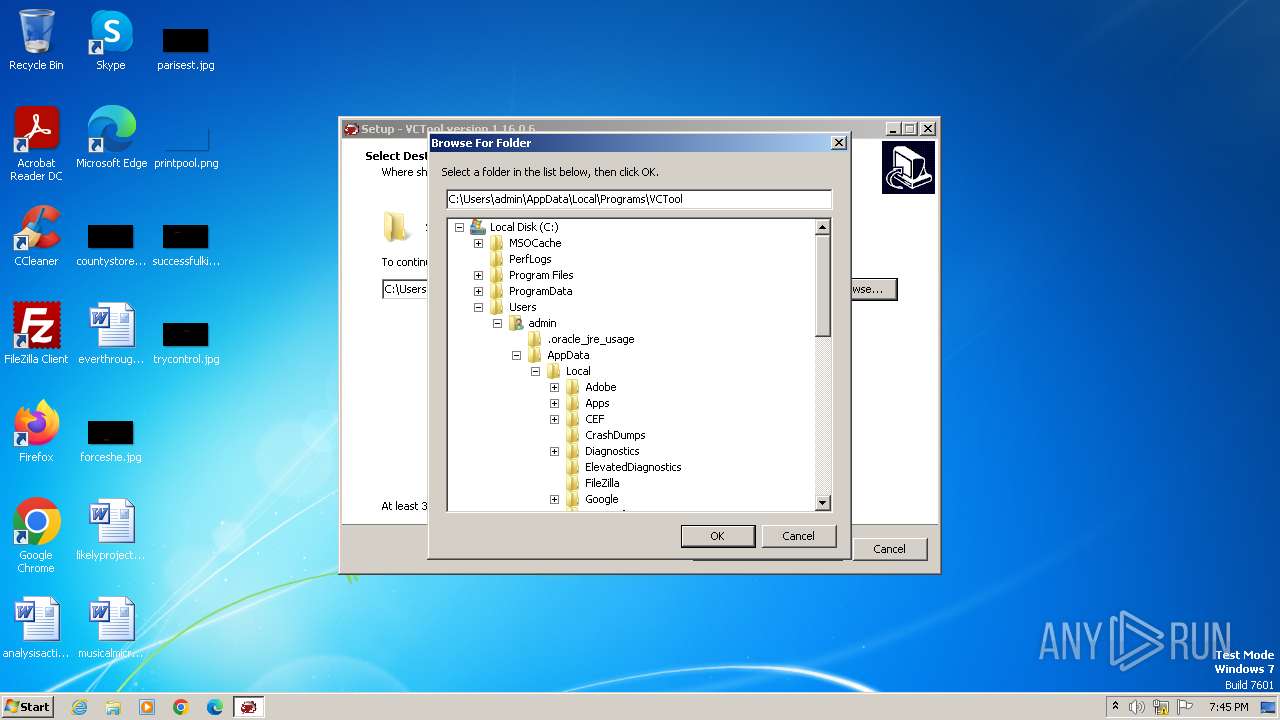
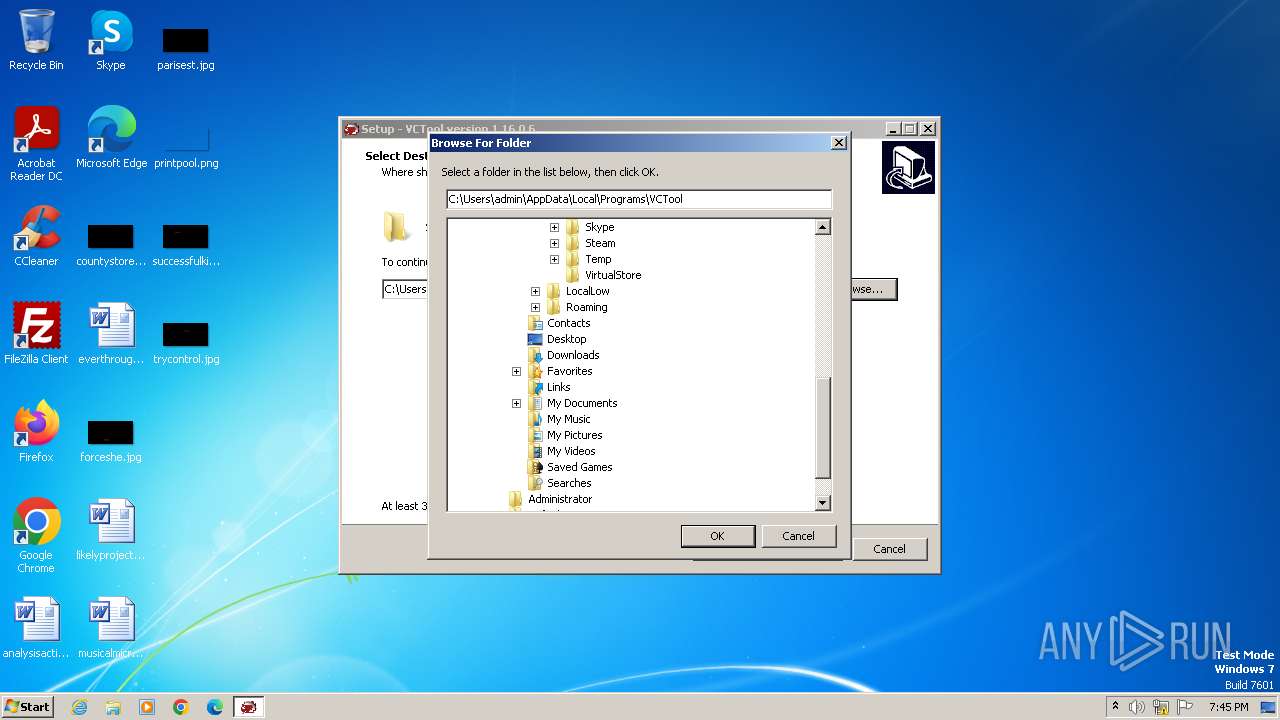
Creates files or folders in the user directory
- vctool_setup.tmp (PID: 2076)
- VCTool.exe (PID: 1036)
Reads the machine GUID from the registry
- VCTool.exe (PID: 1036)
Reads Environment values
- VCTool.exe (PID: 1036)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (65.1) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (24.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.9) |
| .exe | | | Win32 Executable (generic) (2.6) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:11:15 10:48:30+01:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 741376 |
| InitializedDataSize: | 56320 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb5eec |
| OSVersion: | 6.1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
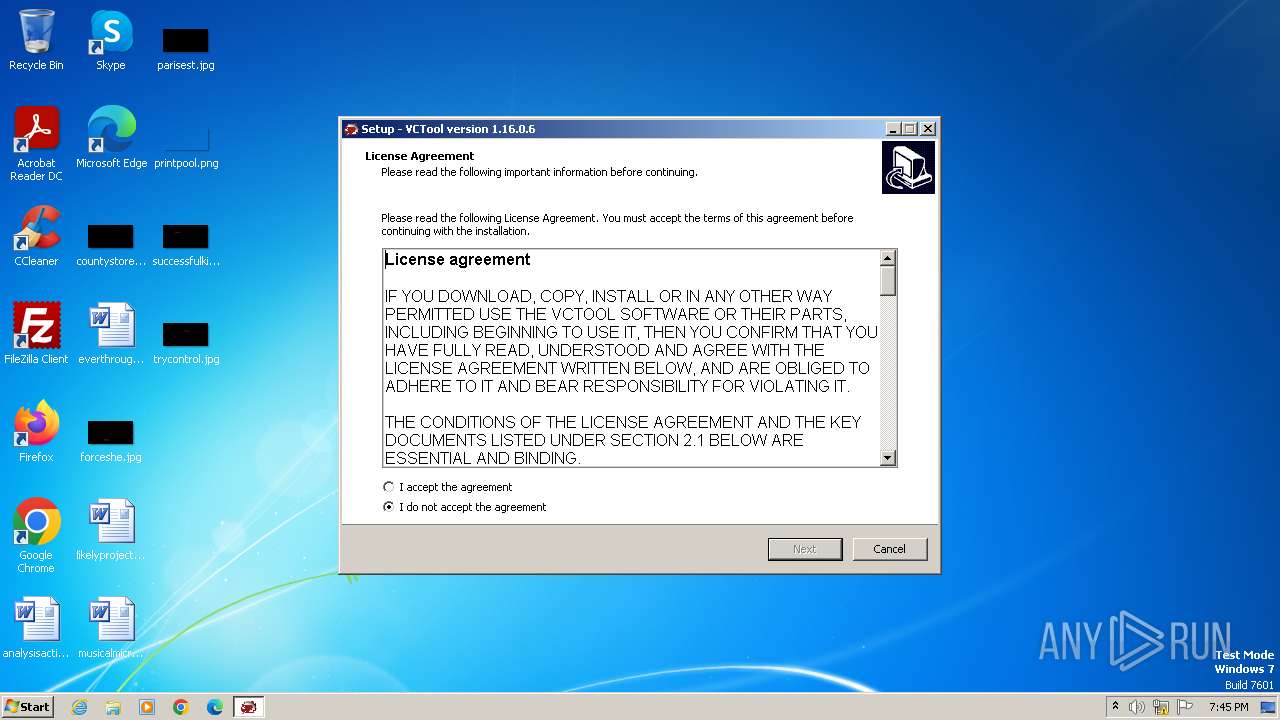
| Comments: | This installation was built with Inno Setup. |
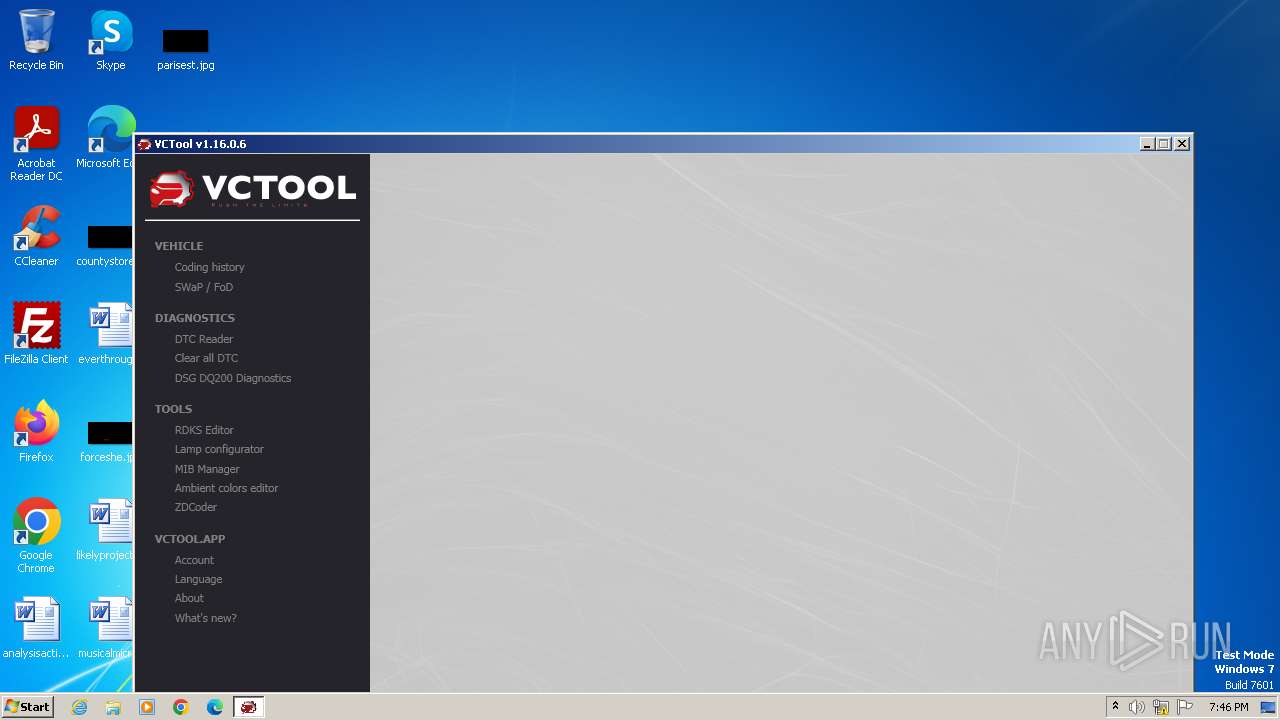
| CompanyName: | Aleksei Sysoev |
| FileDescription: | VCTool Setup |
| FileVersion: | |
| LegalCopyright: | |
| OriginalFileName: | |
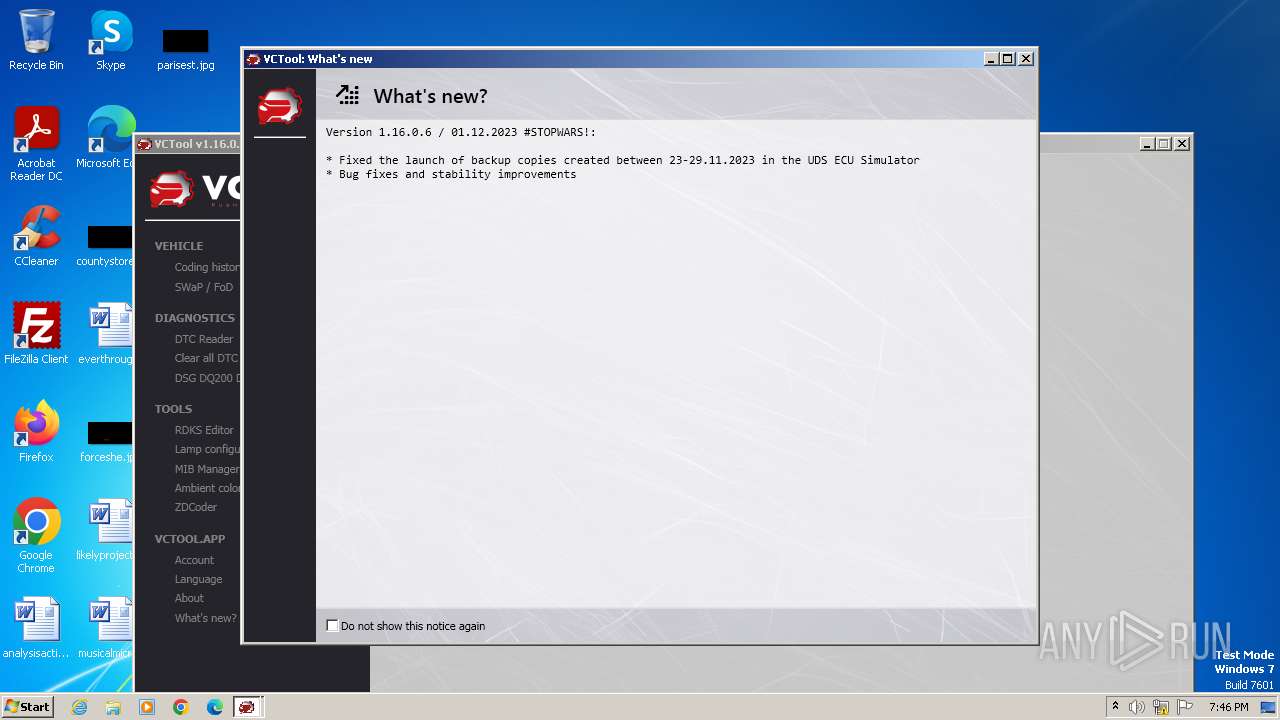
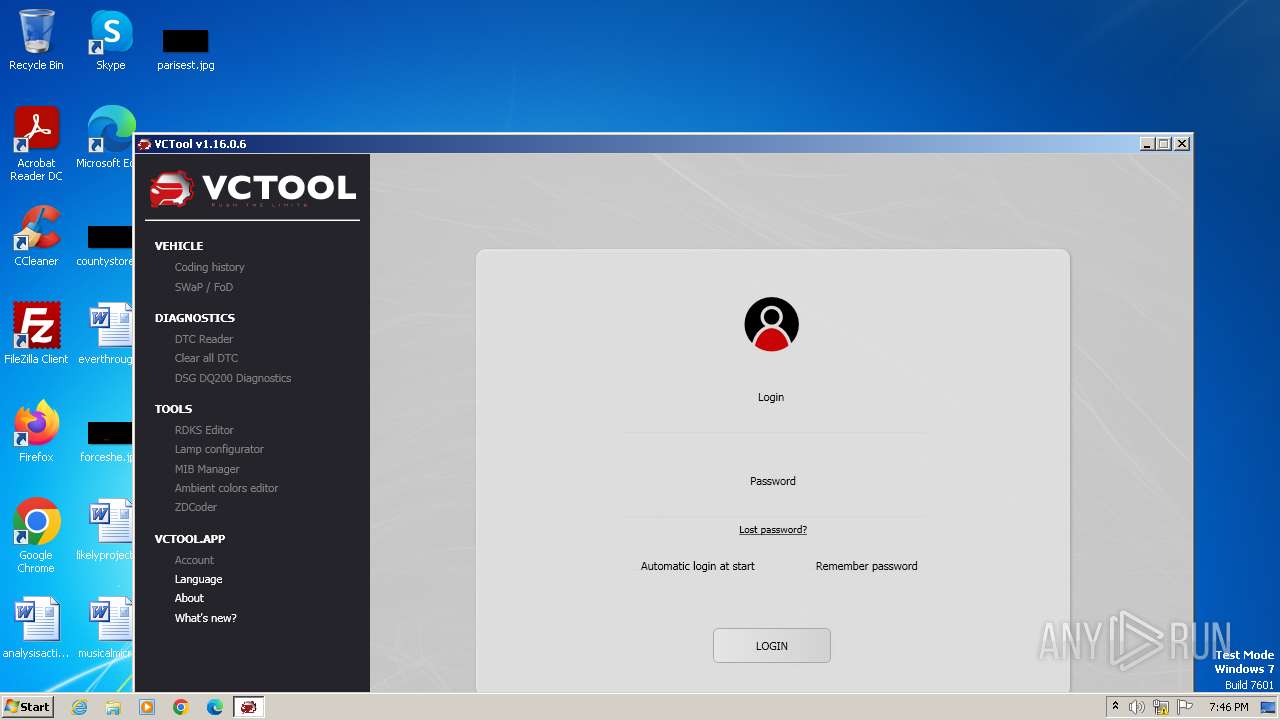
| ProductName: | VCTool |
| ProductVersion: | 1.16.0.6 |
Total processes
40
Monitored processes
3
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
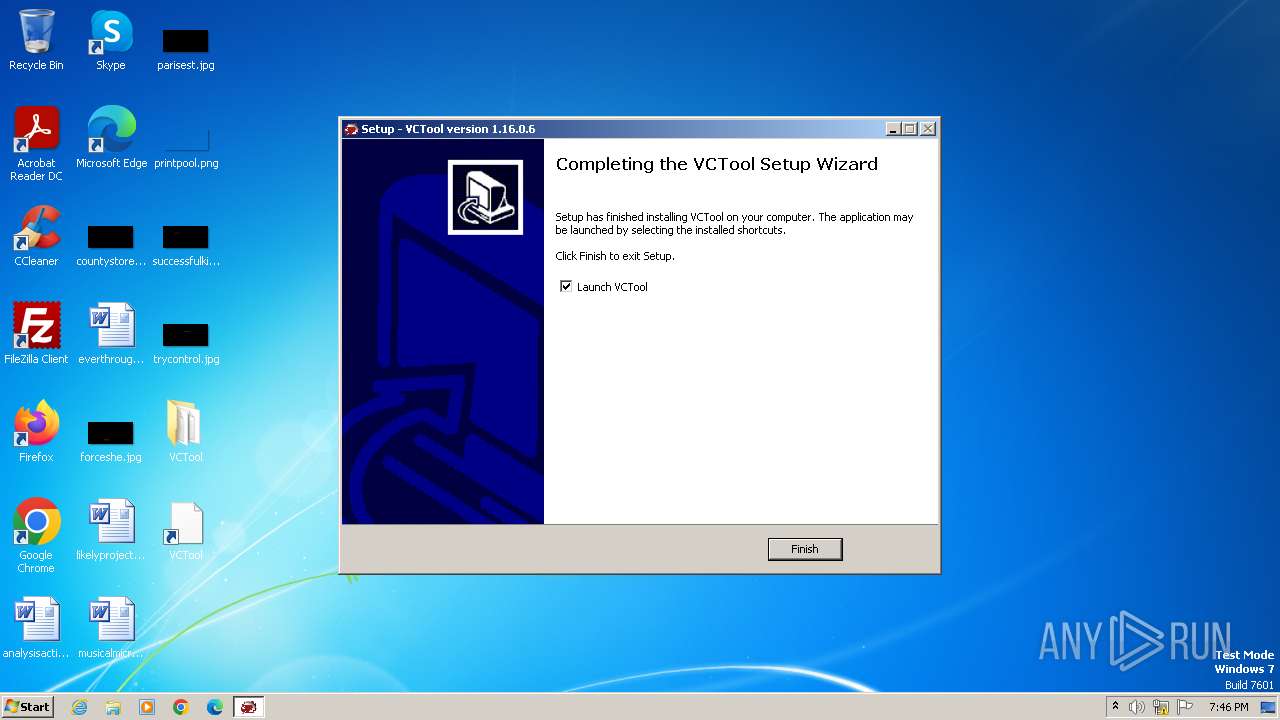
| 1036 | "C:\Users\admin\Desktop\VCTool\VCTool.exe" | C:\Users\admin\Desktop\VCTool\VCTool.exe | — | vctool_setup.tmp | |||||||||||
User: admin Company: Aleksei Sysoev Integrity Level: MEDIUM Description: VCTool Exit code: 0 Version: 1.16.0.6 Modules
| |||||||||||||||
| 1556 | "C:\Users\admin\AppData\Local\Temp\vctool_setup.exe" | C:\Users\admin\AppData\Local\Temp\vctool_setup.exe | — | explorer.exe | |||||||||||
User: admin Company: Aleksei Sysoev Integrity Level: MEDIUM Description: VCTool Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 2076 | "C:\Users\admin\AppData\Local\Temp\is-5HGT1.tmp\vctool_setup.tmp" /SL5="$1B0142,11756707,798720,C:\Users\admin\AppData\Local\Temp\vctool_setup.exe" | C:\Users\admin\AppData\Local\Temp\is-5HGT1.tmp\vctool_setup.tmp | vctool_setup.exe | ||||||||||||
User: admin Company: Aleksei Sysoev Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
5 121
Read events
5 093
Write events
22
Delete events
6
Modification events
| (PID) Process: | (2076) vctool_setup.tmp | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1036) VCTool.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1036) VCTool.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1036) VCTool.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1036) VCTool.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1036) VCTool.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1036) VCTool.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: Explorer.EXE | |||
| (PID) Process: | (2076) vctool_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | RegFilesHash |
Value: 21D5F32C4748763CBD0591173BCA0BBD2CB603A5005D5FA6046A1C483ACA1454 | |||
| (PID) Process: | (2076) vctool_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | RegFiles0000 |
Value: C:\Users\admin\Desktop\VCTool\VCTool.exe | |||
| (PID) Process: | (2076) vctool_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | Sequence |
Value: 1 | |||
Executable files
85
Suspicious files
7
Text files
24
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
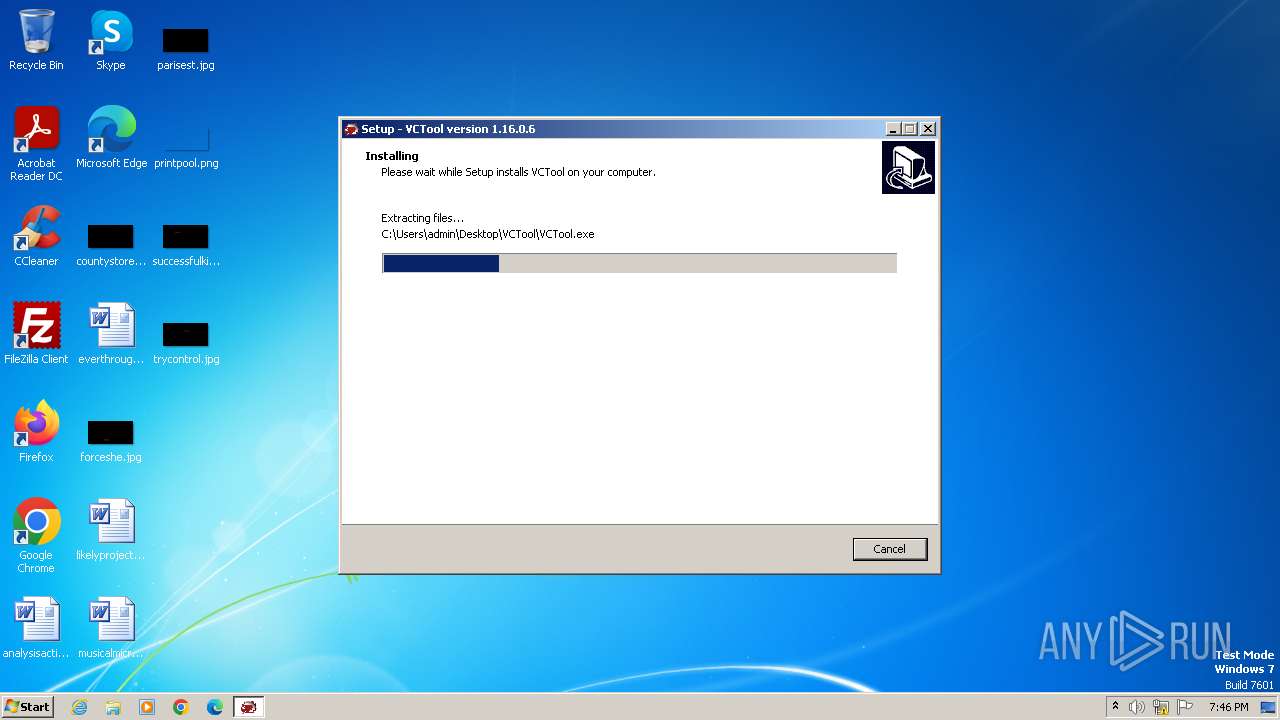
| 2076 | vctool_setup.tmp | C:\Users\admin\Desktop\VCTool\is-AGMT7.tmp | executable | |
MD5:6760D6302D5DF1EE1315D73DD5C60881 | SHA256:5FB0B2E3BF95827077B9601E4A209F52D411579FD4936995683423CBEDB9EBC2 | |||
| 1556 | vctool_setup.exe | C:\Users\admin\AppData\Local\Temp\is-5HGT1.tmp\vctool_setup.tmp | executable | |
MD5:6760D6302D5DF1EE1315D73DD5C60881 | SHA256:5FB0B2E3BF95827077B9601E4A209F52D411579FD4936995683423CBEDB9EBC2 | |||
| 2076 | vctool_setup.tmp | C:\Users\admin\Desktop\VCTool\VCTool.exe | executable | |
MD5:6B9BB4CBEFF97C3629F27FE2E767EFF2 | SHA256:DEA9A6A590600C96A7F41BB222853FE8FD2EFA93CD0F9266F3E7FE11CC046877 | |||
| 2076 | vctool_setup.tmp | C:\Users\admin\Desktop\VCTool\is-RCO7B.tmp | executable | |
MD5:6A9F2D63760838E65ACE15CE9803E51C | SHA256:26E57D35DB20A84D6466E4E9DF251712AB0597C0FBDFD5AD58666E76D5685549 | |||
| 2076 | vctool_setup.tmp | C:\Users\admin\Desktop\VCTool\is-E6EIH.tmp | executable | |
MD5:3AF5617DFB0A052E693AFF10CE80D5F4 | SHA256:BC4E4CFE276FB97E70978E1D484E806C5A1C9301D1F9752C6D39840840118723 | |||
| 2076 | vctool_setup.tmp | C:\Users\admin\Desktop\VCTool\DotNetZip.dll | executable | |
MD5:A999D7F3807564CC816C16F862A60BBE | SHA256:8E9C0362E9BFB3C49AF59E1B4D376D3E85B13AED0FBC3F5C0E1EBC99C07345F3 | |||
| 2076 | vctool_setup.tmp | C:\Users\admin\Desktop\VCTool\is-N9RBQ.tmp | executable | |
MD5:A999D7F3807564CC816C16F862A60BBE | SHA256:8E9C0362E9BFB3C49AF59E1B4D376D3E85B13AED0FBC3F5C0E1EBC99C07345F3 | |||
| 2076 | vctool_setup.tmp | C:\Users\admin\Desktop\VCTool\VCToolDoip.dll | executable | |
MD5:BEDF31B1DFC0B27610D85372AAD9F203 | SHA256:5FB15F80BE9289FEABC0C6C2859B50267323A3C224DCB9792F207B7B09941BF0 | |||
| 2076 | vctool_setup.tmp | C:\Users\admin\Desktop\VCTool\is-ME9QG.tmp | executable | |
MD5:D8F0E3940B5BBE9599EE0A84B541D50F | SHA256:202A4719E4B879DA67445AB50901D80A259F8680B5D16BC0F929E0A6F6FAD199 | |||
| 2076 | vctool_setup.tmp | C:\Users\admin\Desktop\VCTool\Microsoft.CodeAnalysis.CSharp.dll | executable | |
MD5:3AF5617DFB0A052E693AFF10CE80D5F4 | SHA256:BC4E4CFE276FB97E70978E1D484E806C5A1C9301D1F9752C6D39840840118723 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |