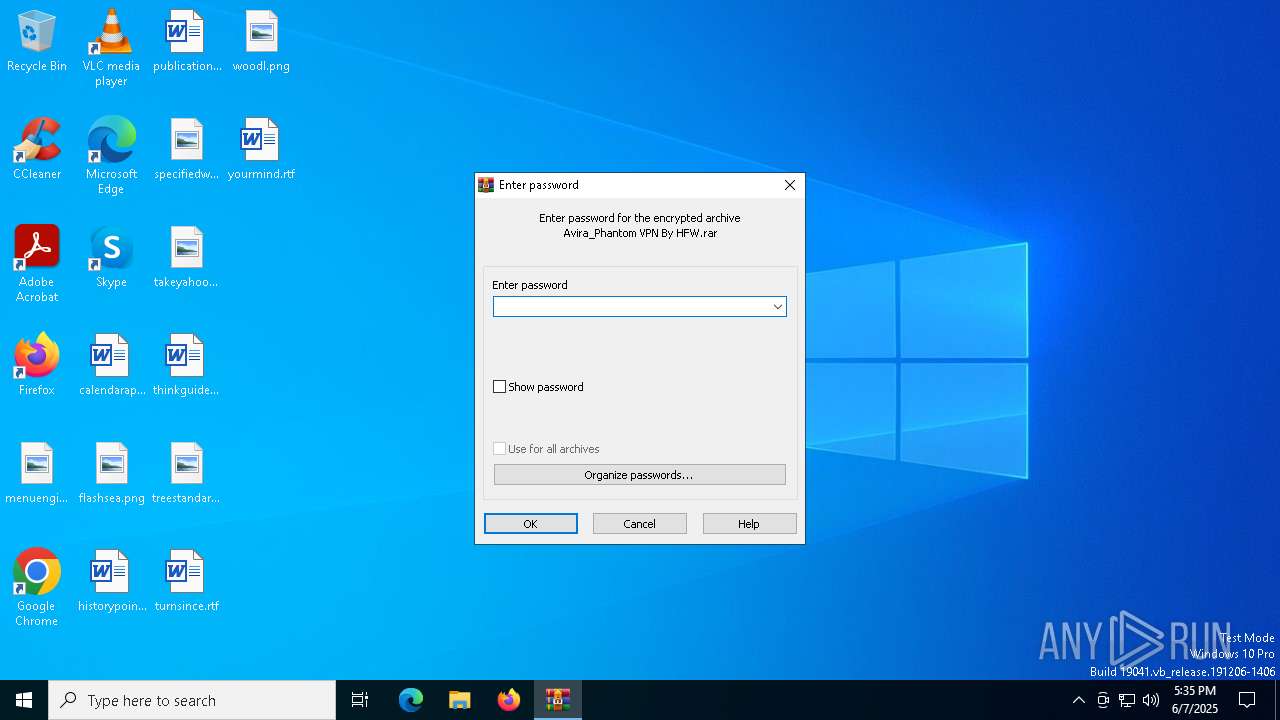
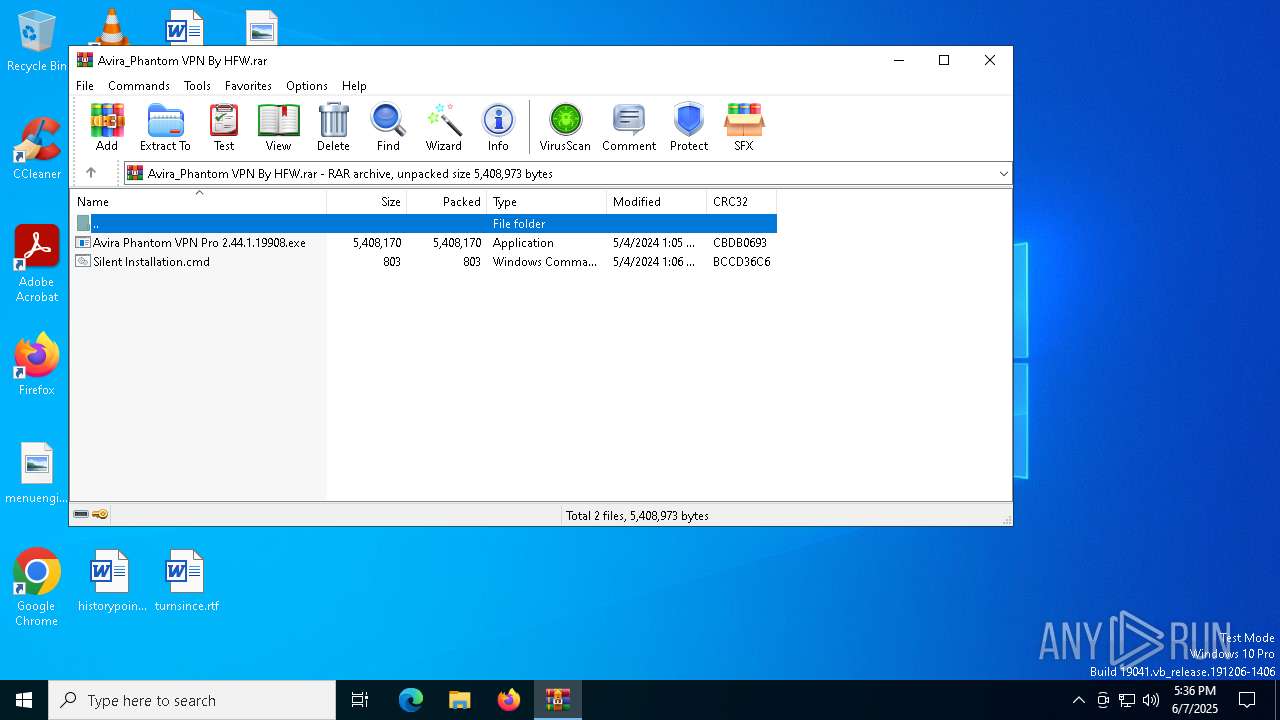
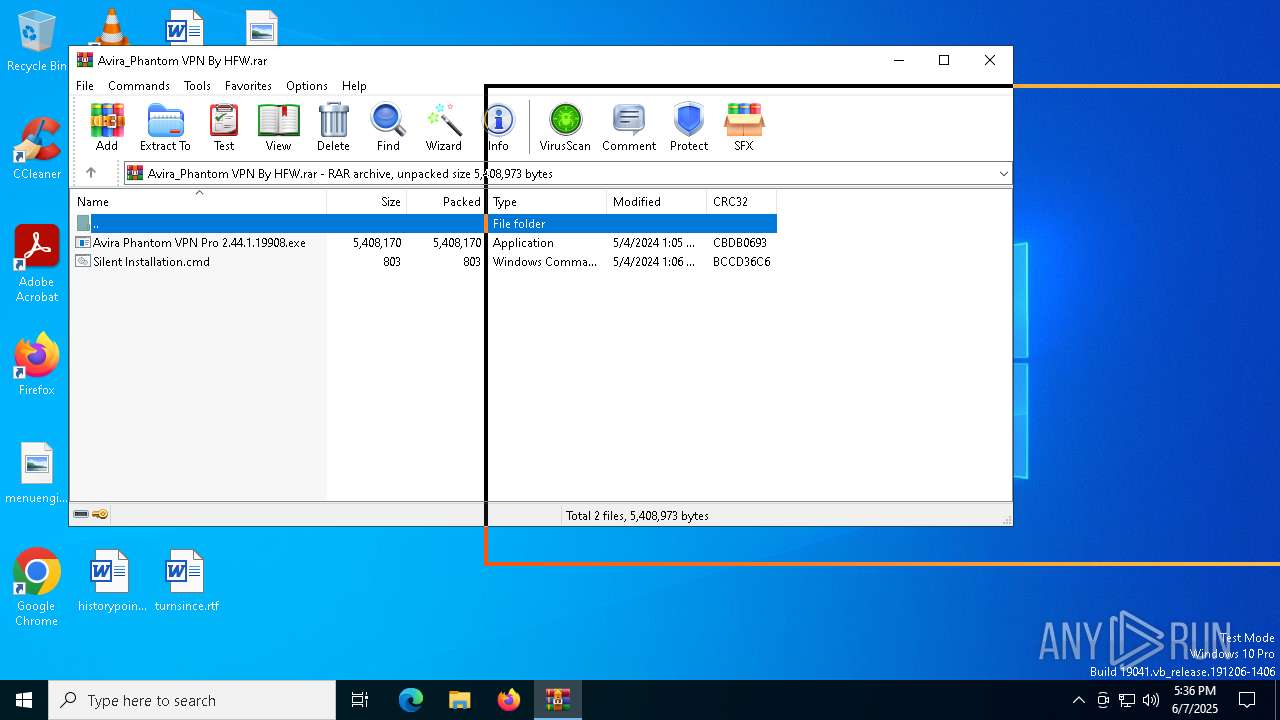
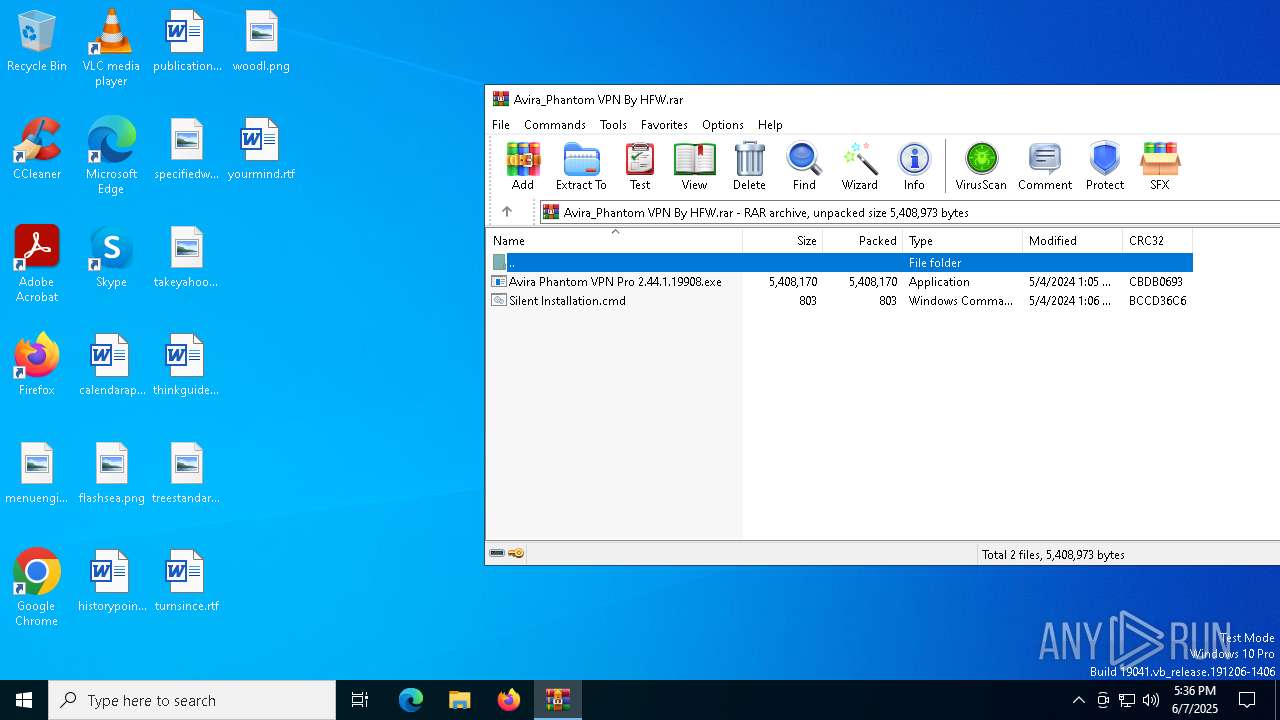
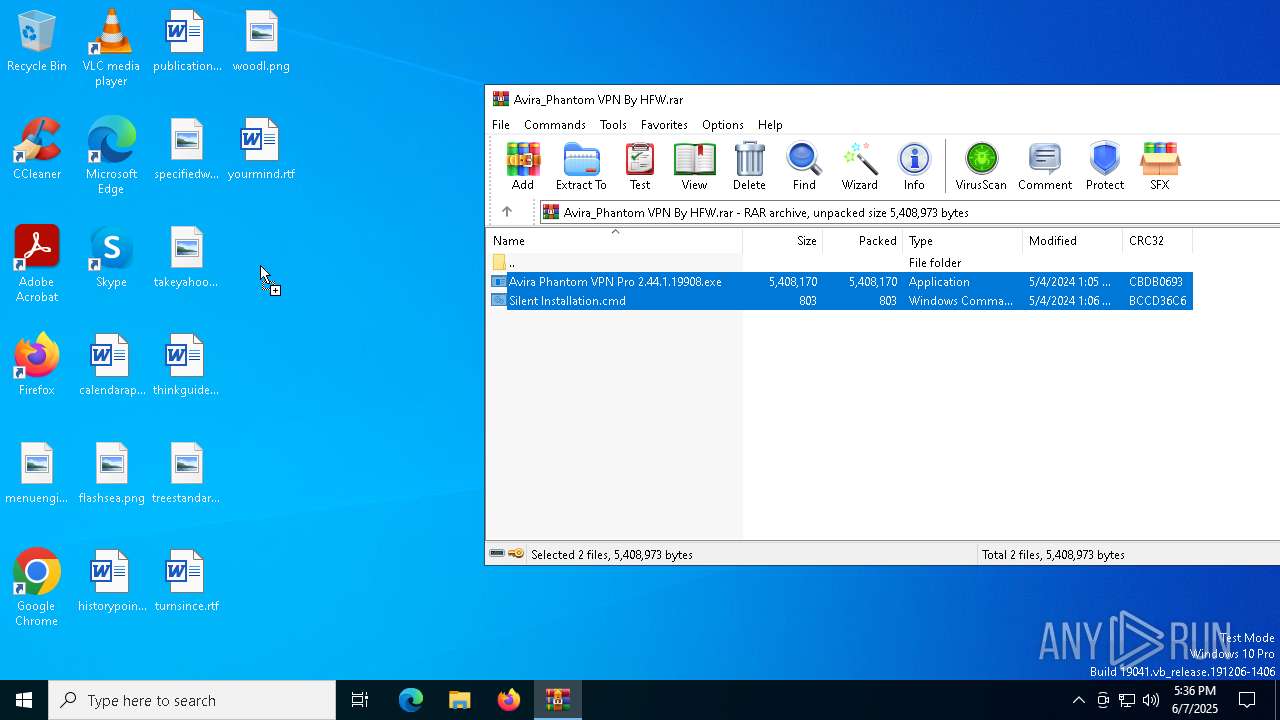
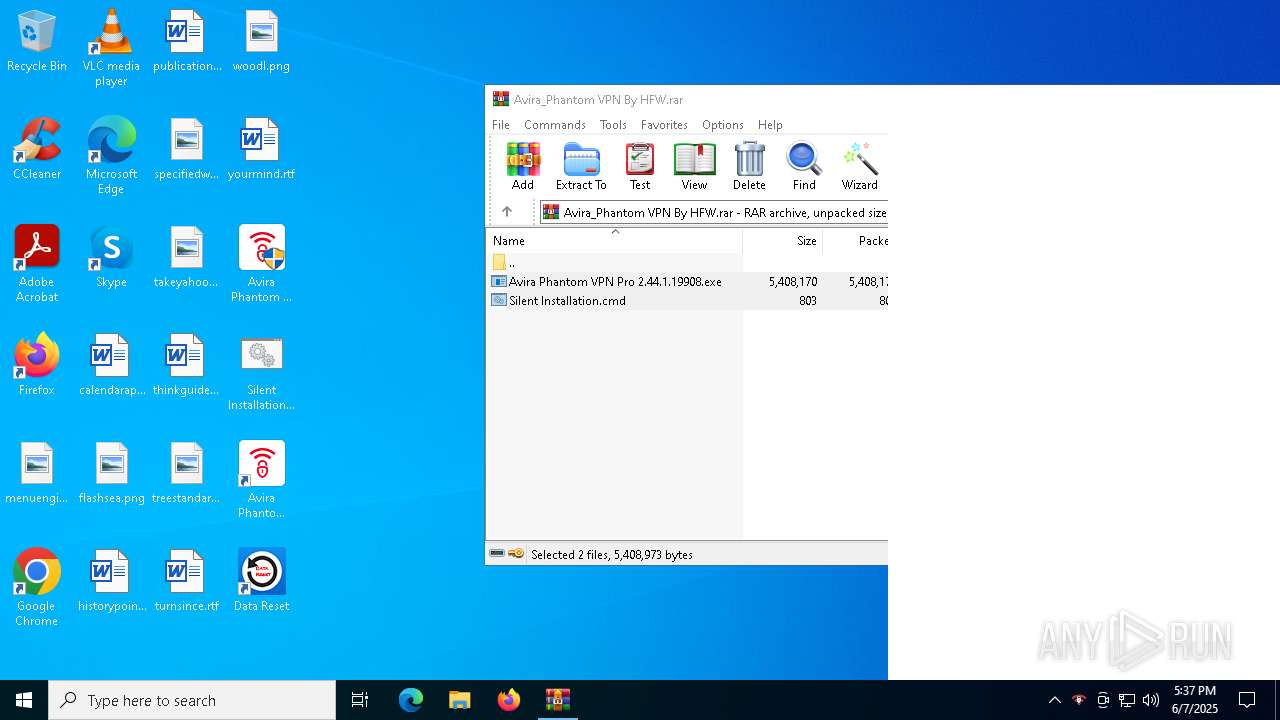
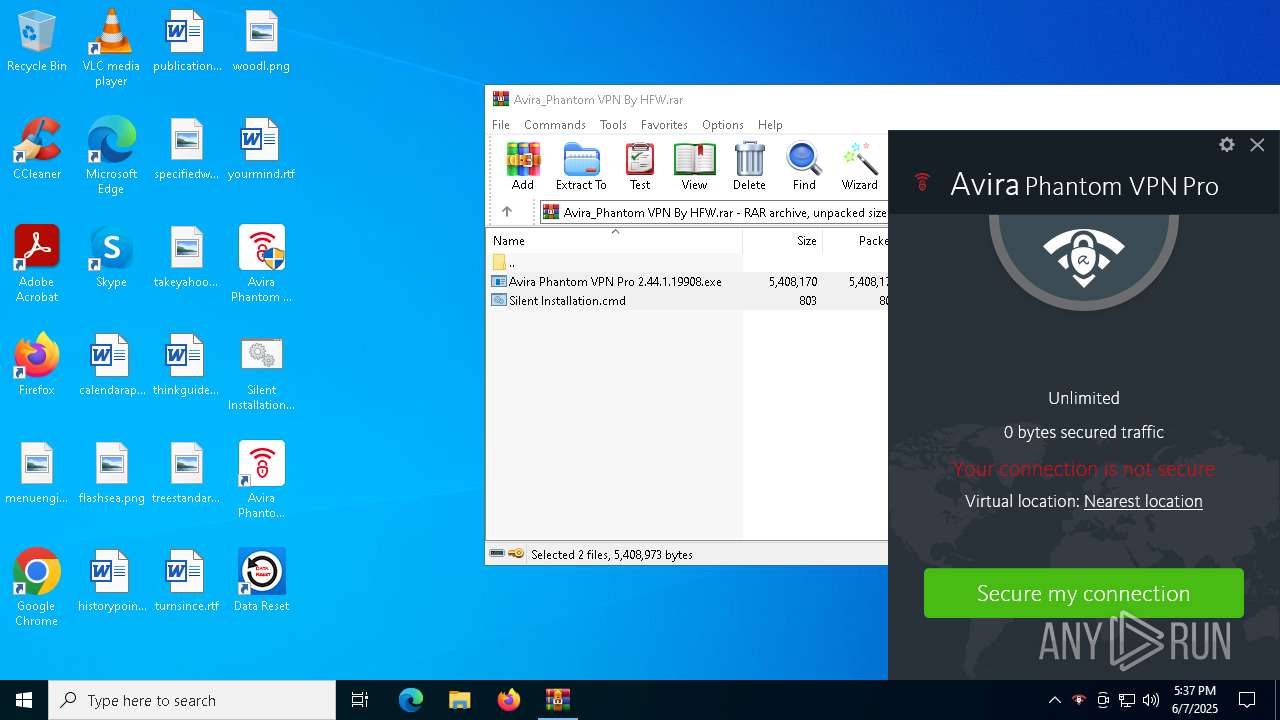
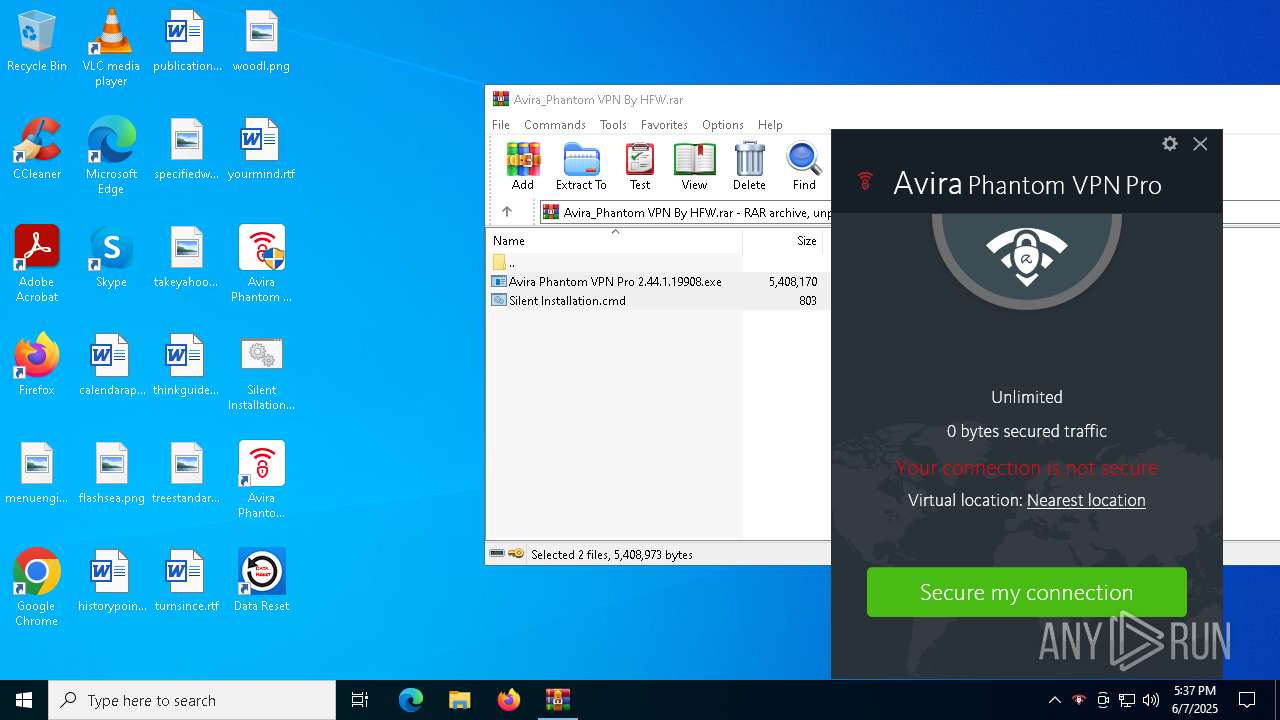
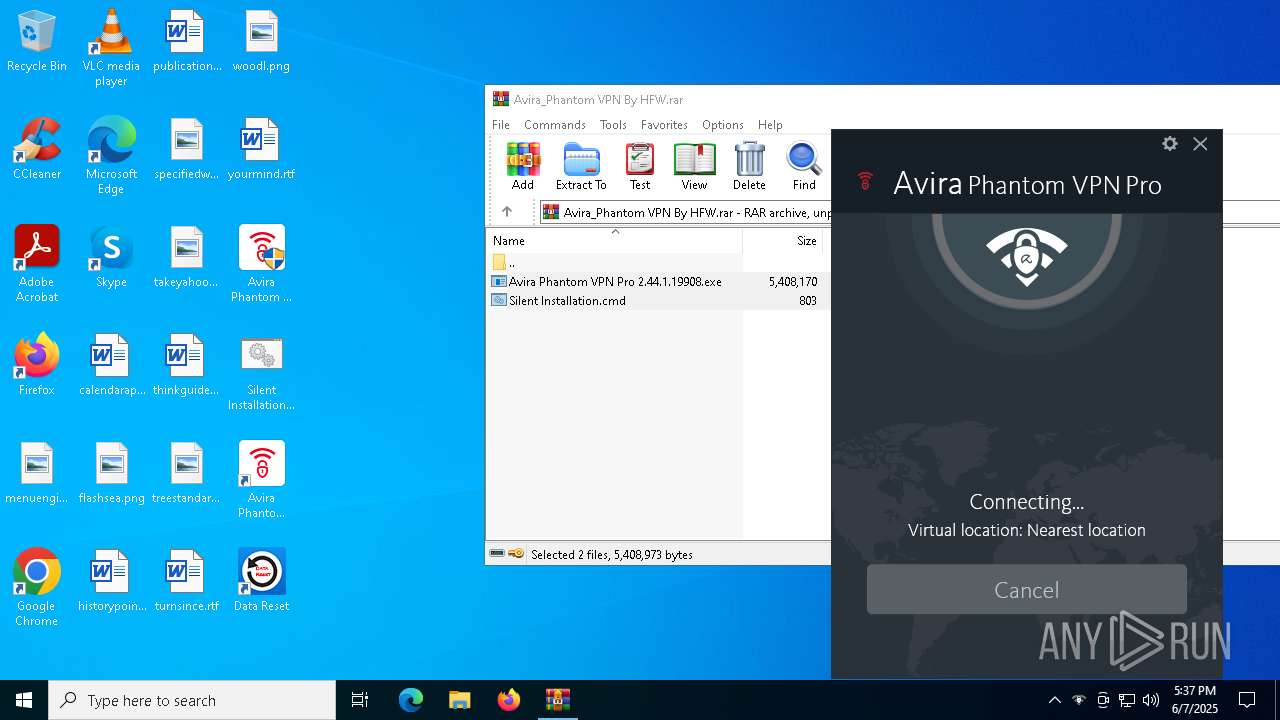
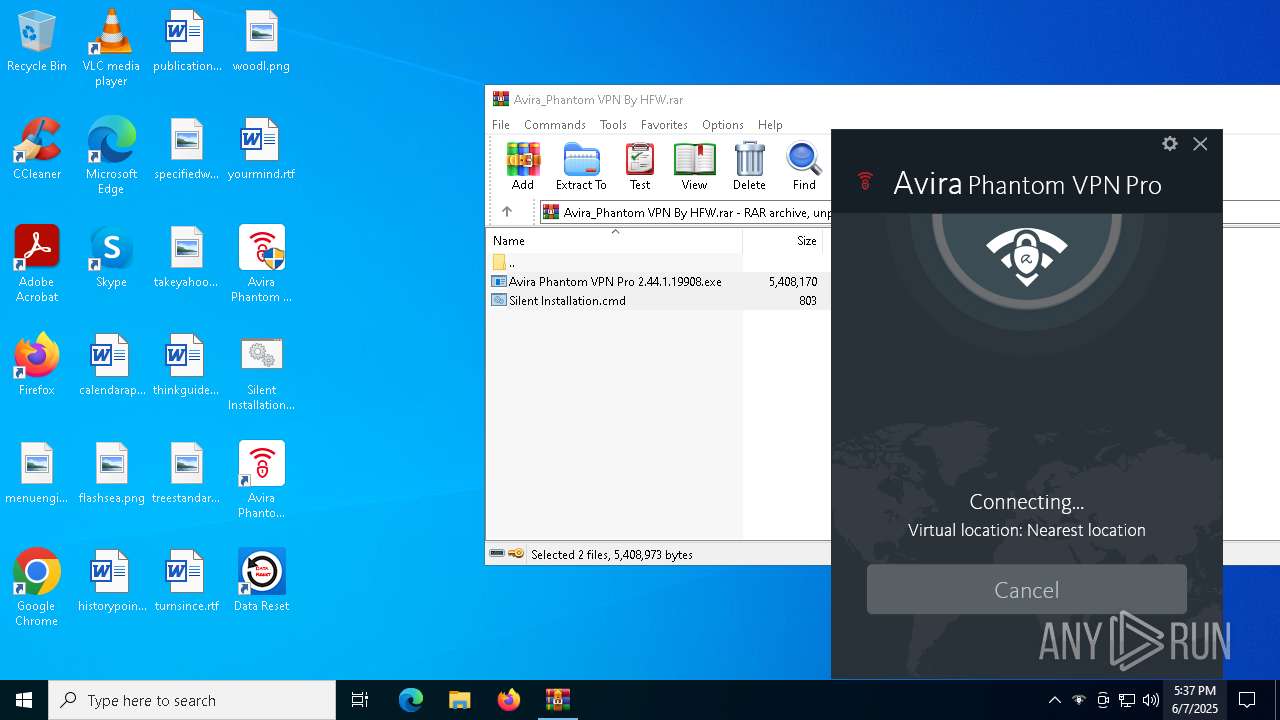
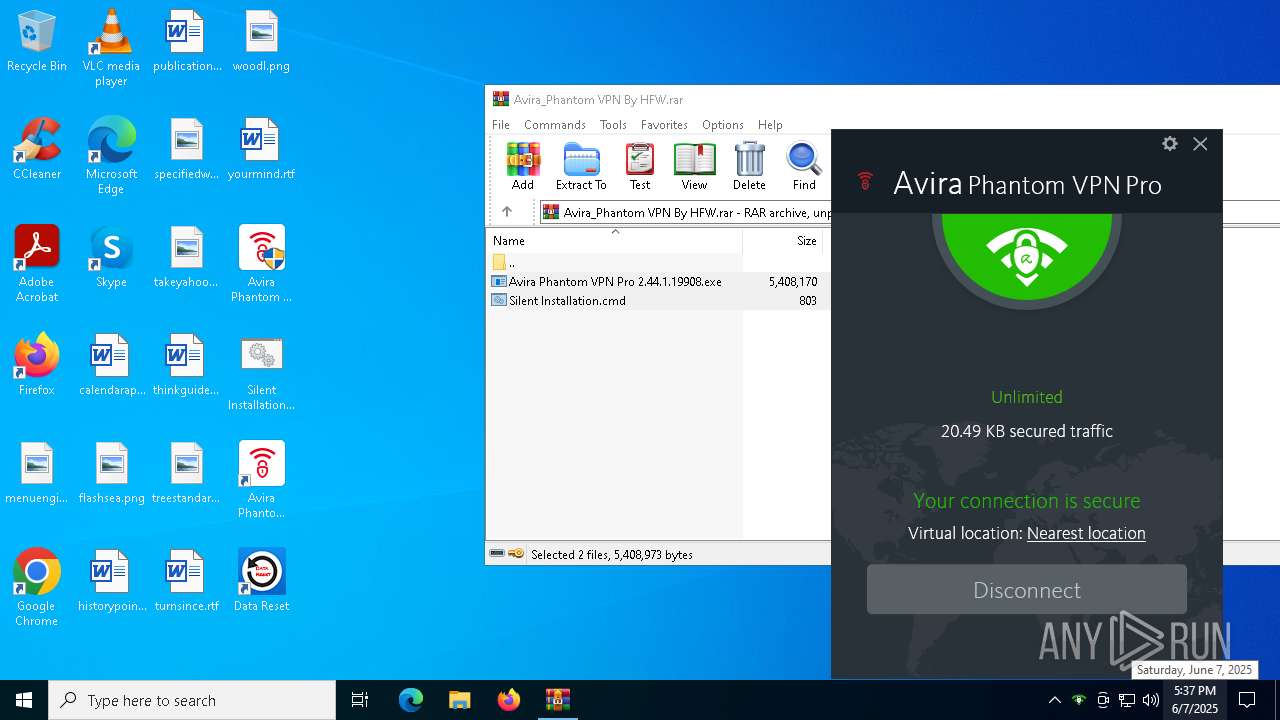
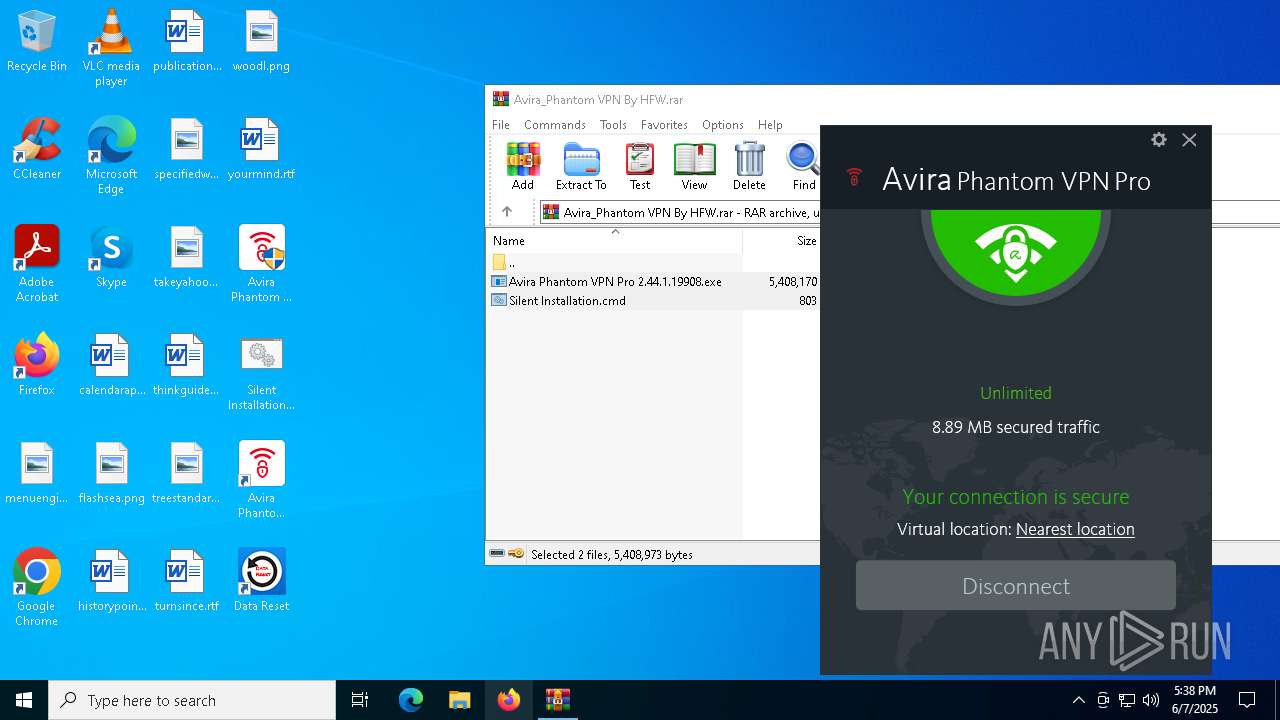
| File name: | Avira_Phantom VPN By HFW.rar |
| Full analysis: | https://app.any.run/tasks/ac112eb2-5b40-4512-b133-42bcc668a0ea |
| Verdict: | Malicious activity |
| Analysis date: | June 07, 2025, 17:35:46 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 27EE38BB1916497802CA52C215D6A8D6 |
| SHA1: | A1F7BD2BBBB1A3144FDB64B93ACBB843501FA1E5 |
| SHA256: | A6134BA3E6C39049036A50D061FD0101779808292509F7741ADD1C6F9BC9AECF |
| SSDEEP: | 98304:hKn3TtVcm2h5SC6az3DoyUfAtSYSGtCEMAiihAzFc6GWEX9+90VYa55e2BK6Qoi9:YTXkBGh3 |
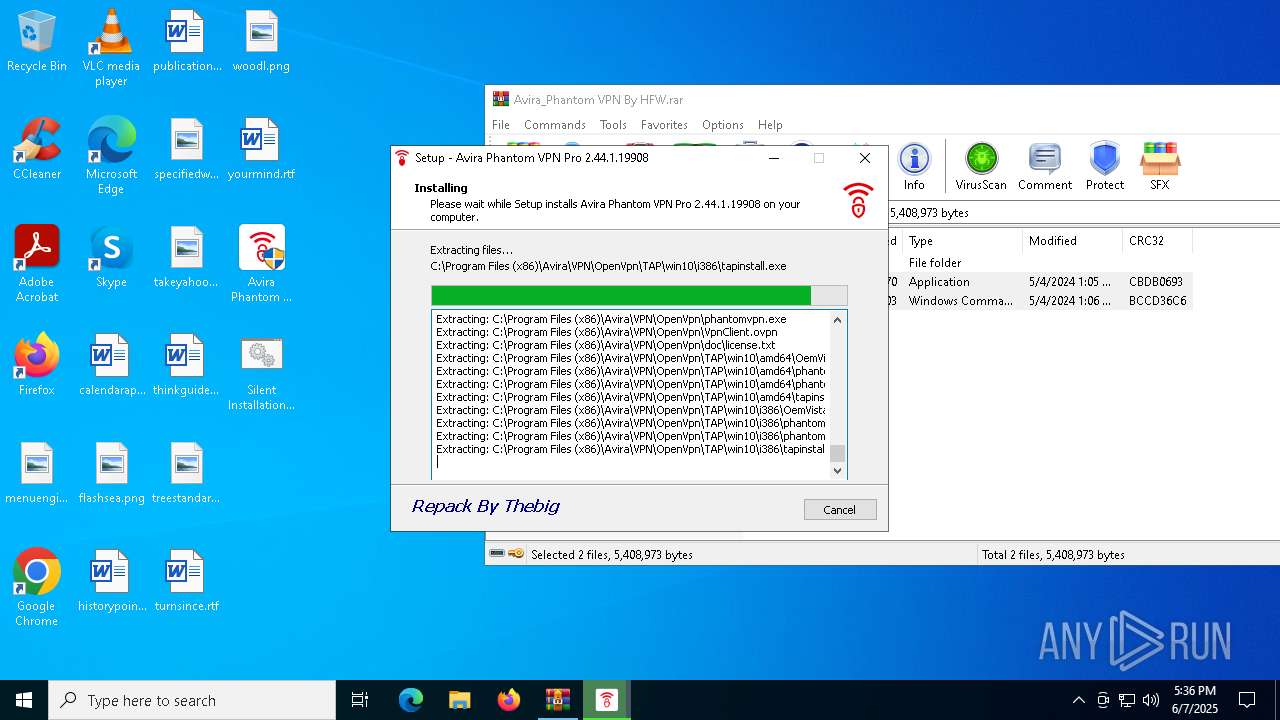
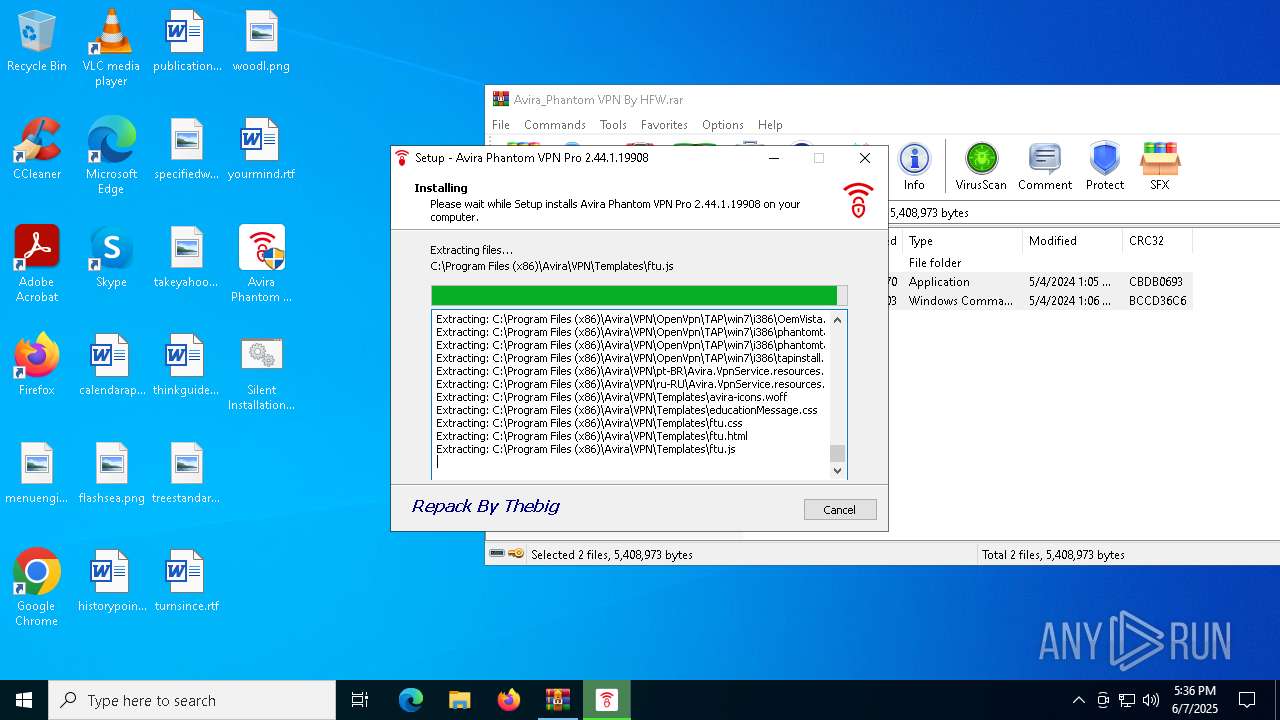
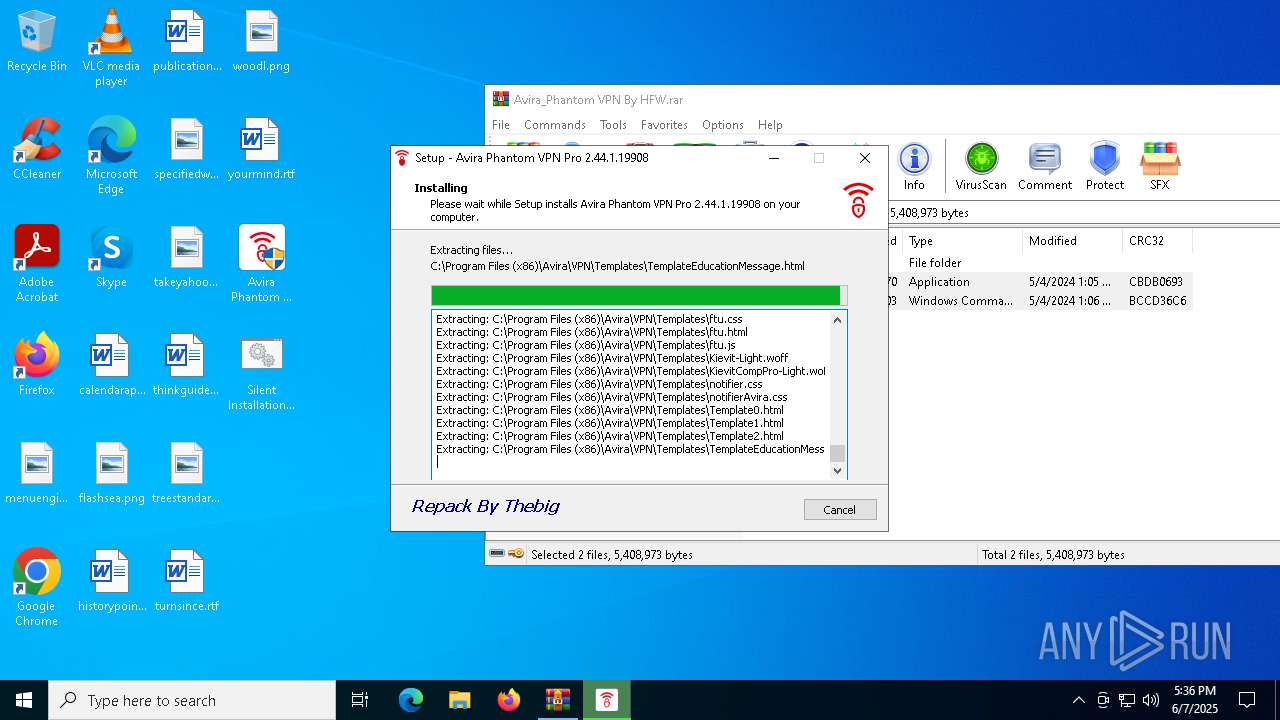
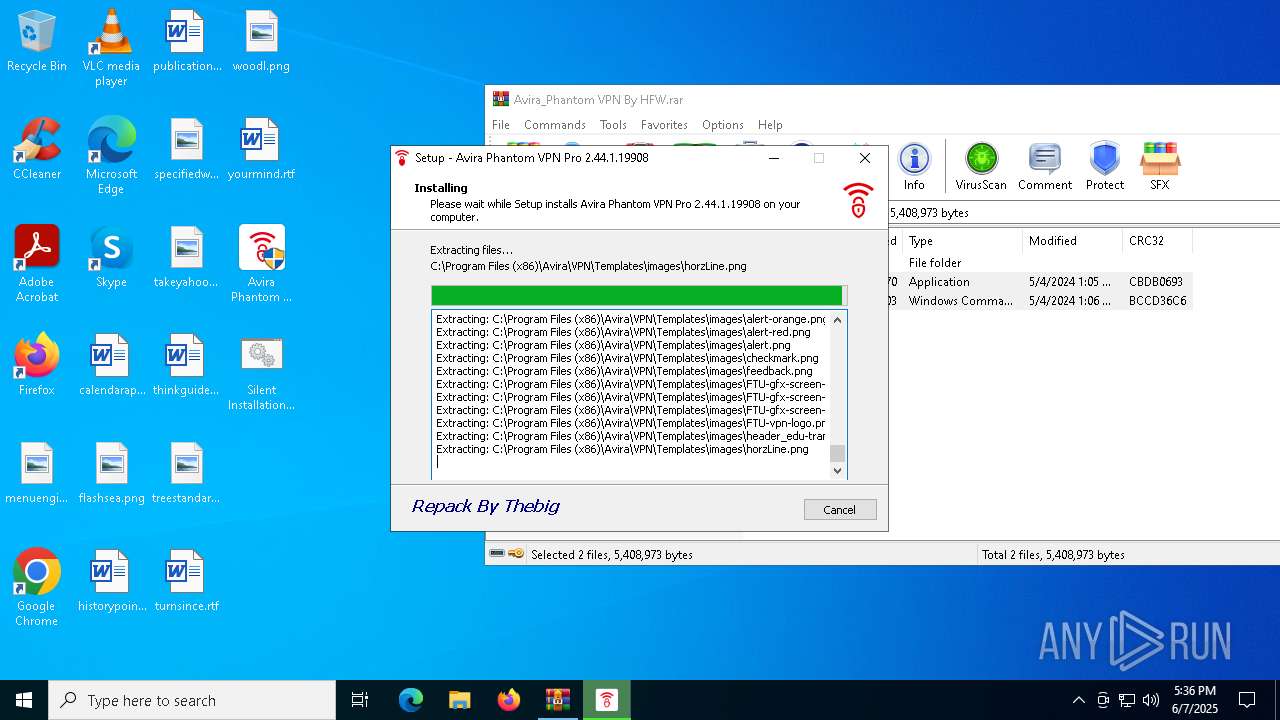
MALICIOUS
Executing a file with an untrusted certificate
- tapinstall.exe (PID: 4400)
- tapinstall.exe (PID: 6476)
- tapinstall.exe (PID: 6192)
- tapinstall.exe (PID: 3308)
SUSPICIOUS
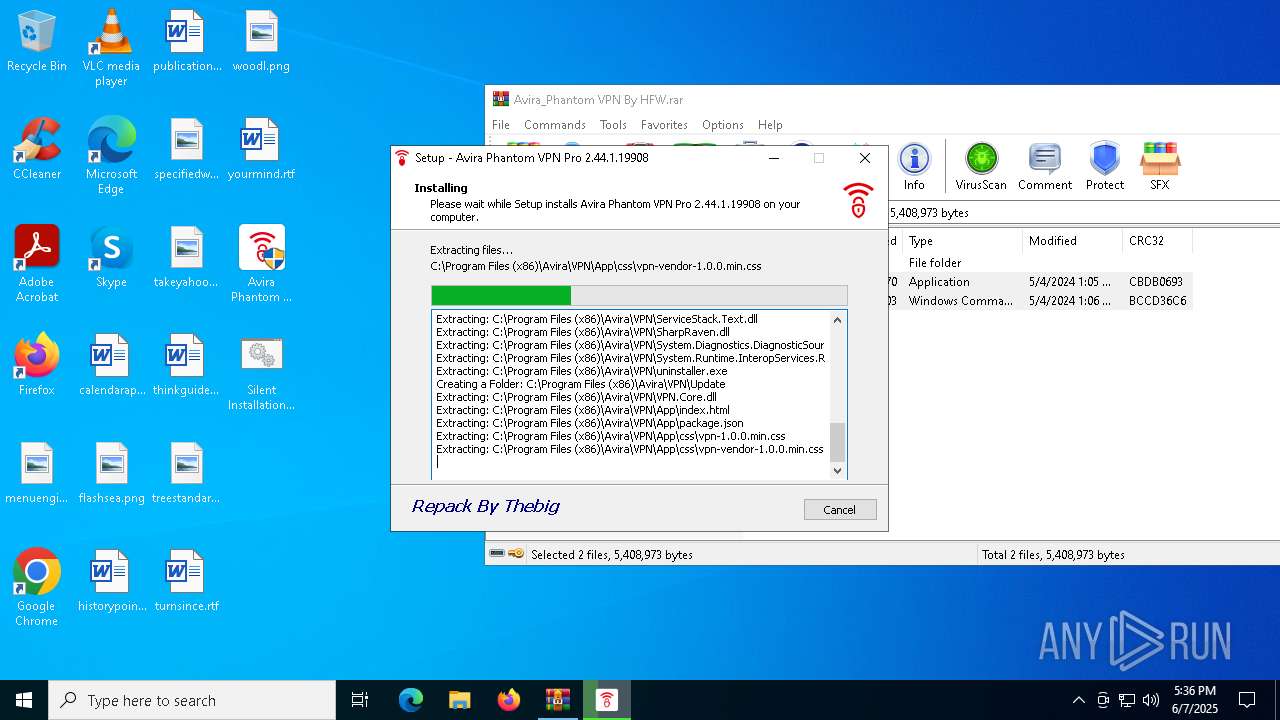
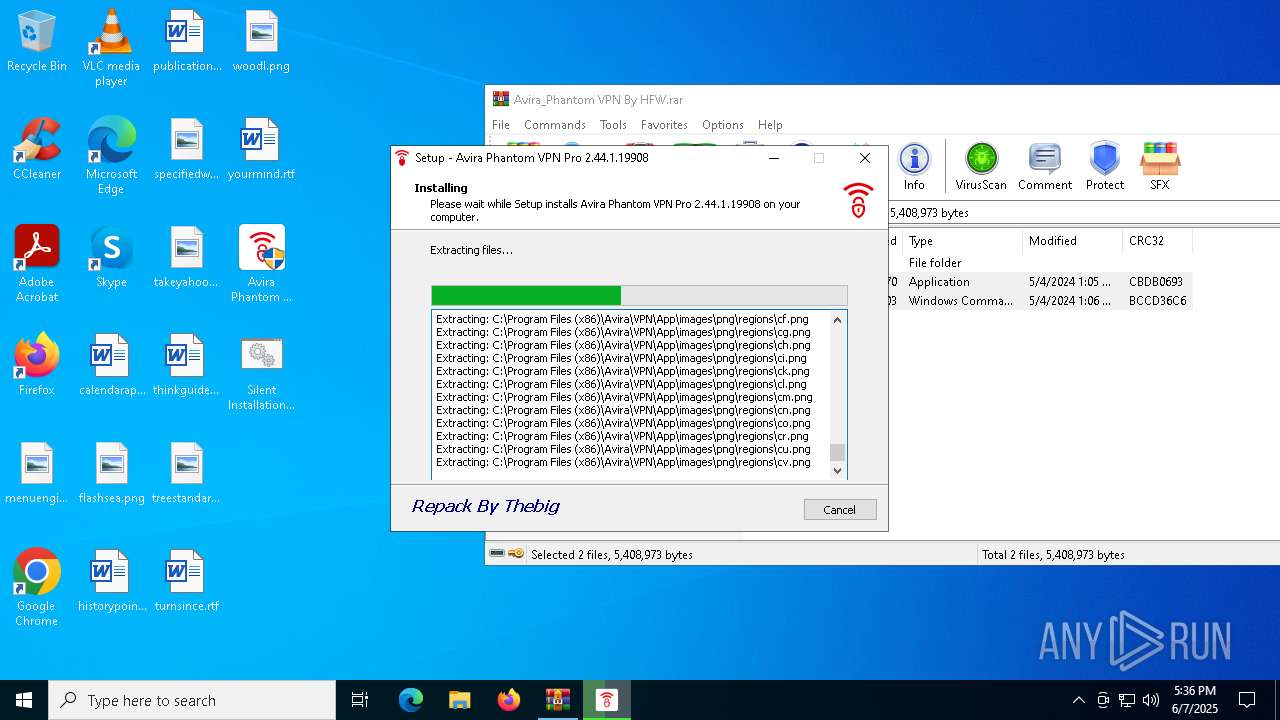
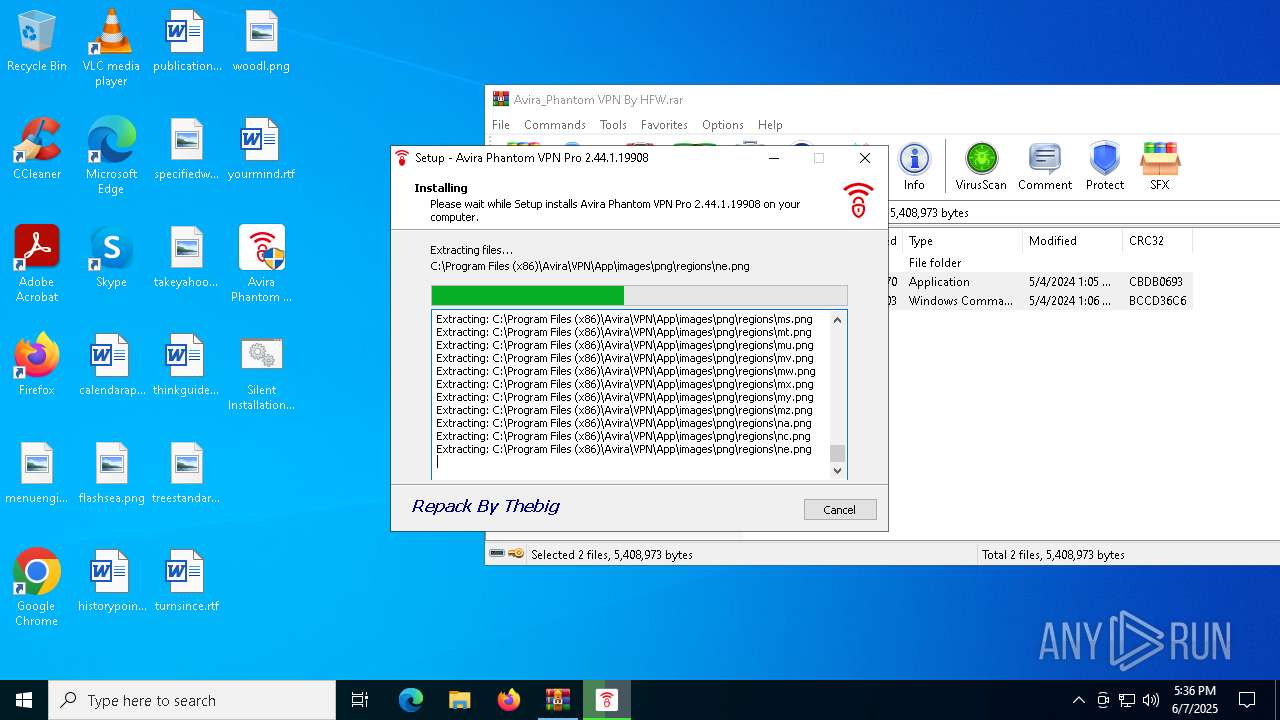
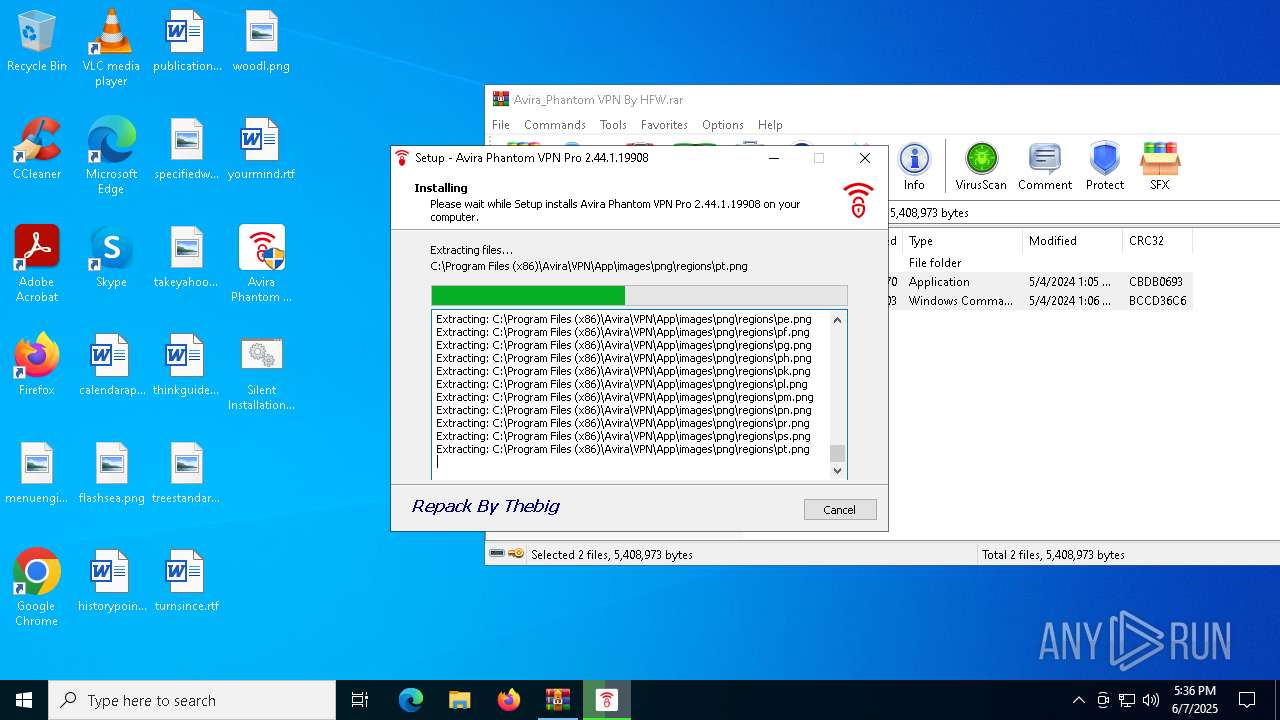
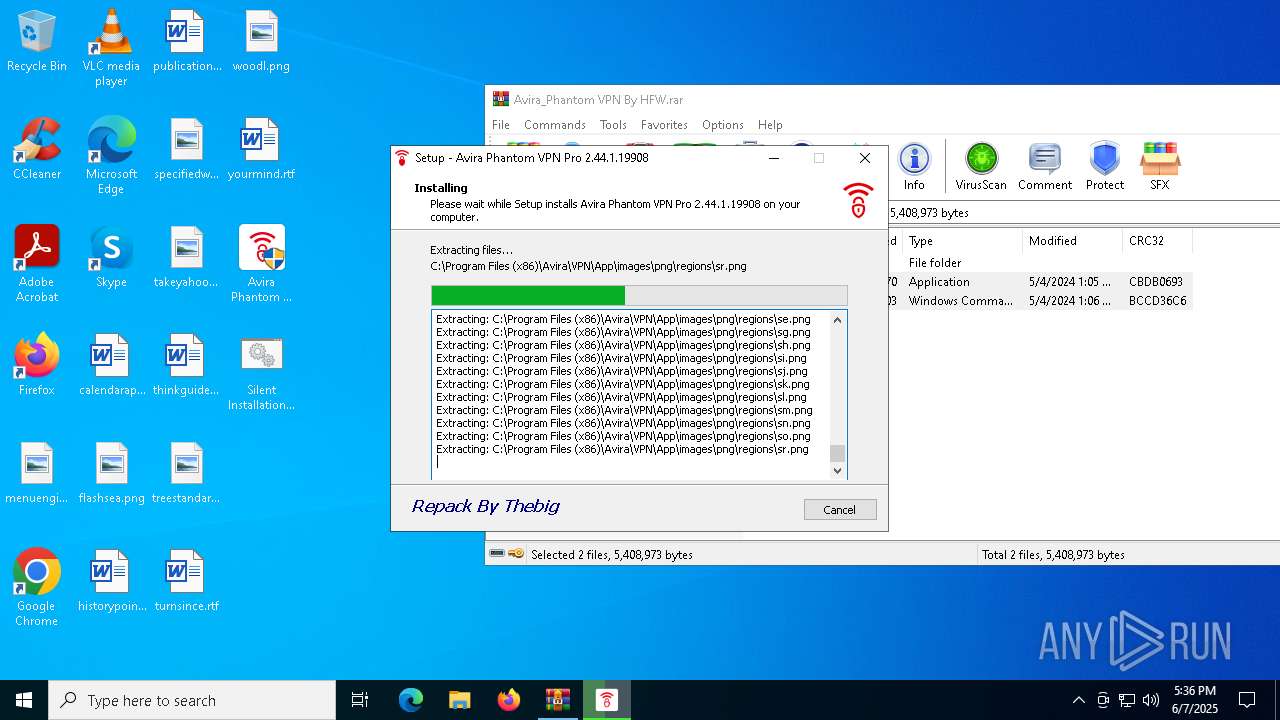
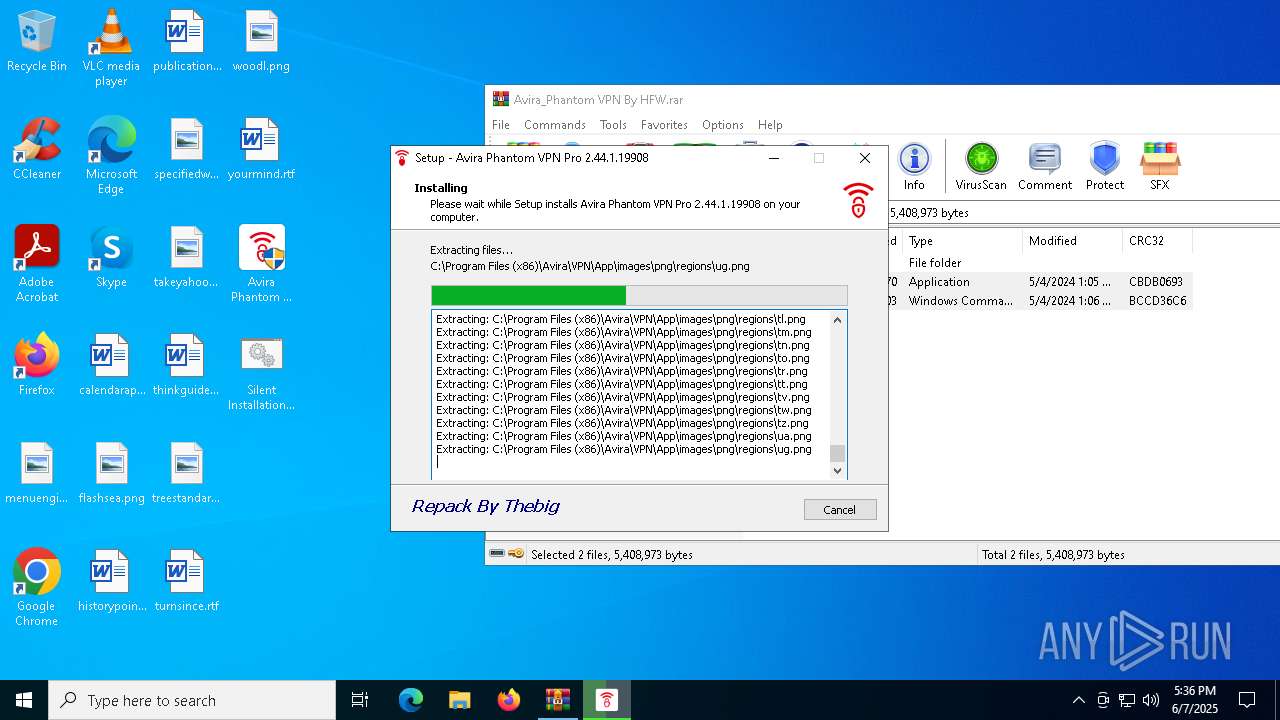
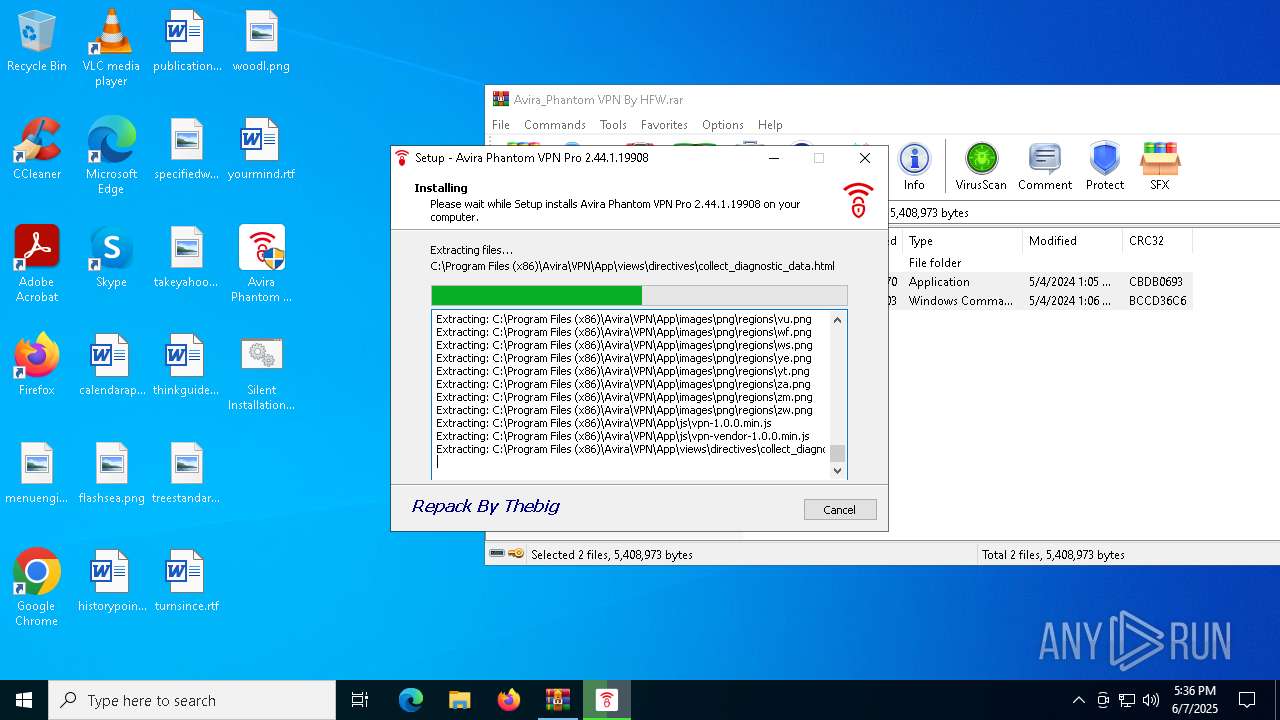
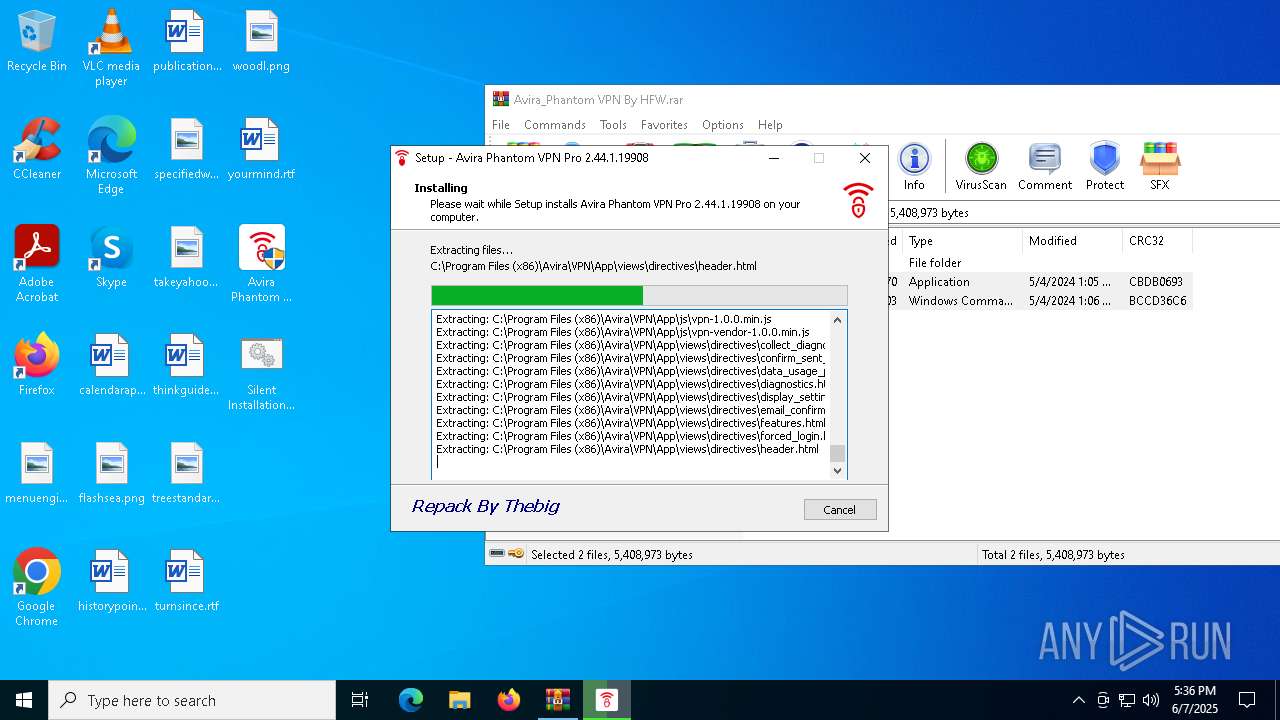
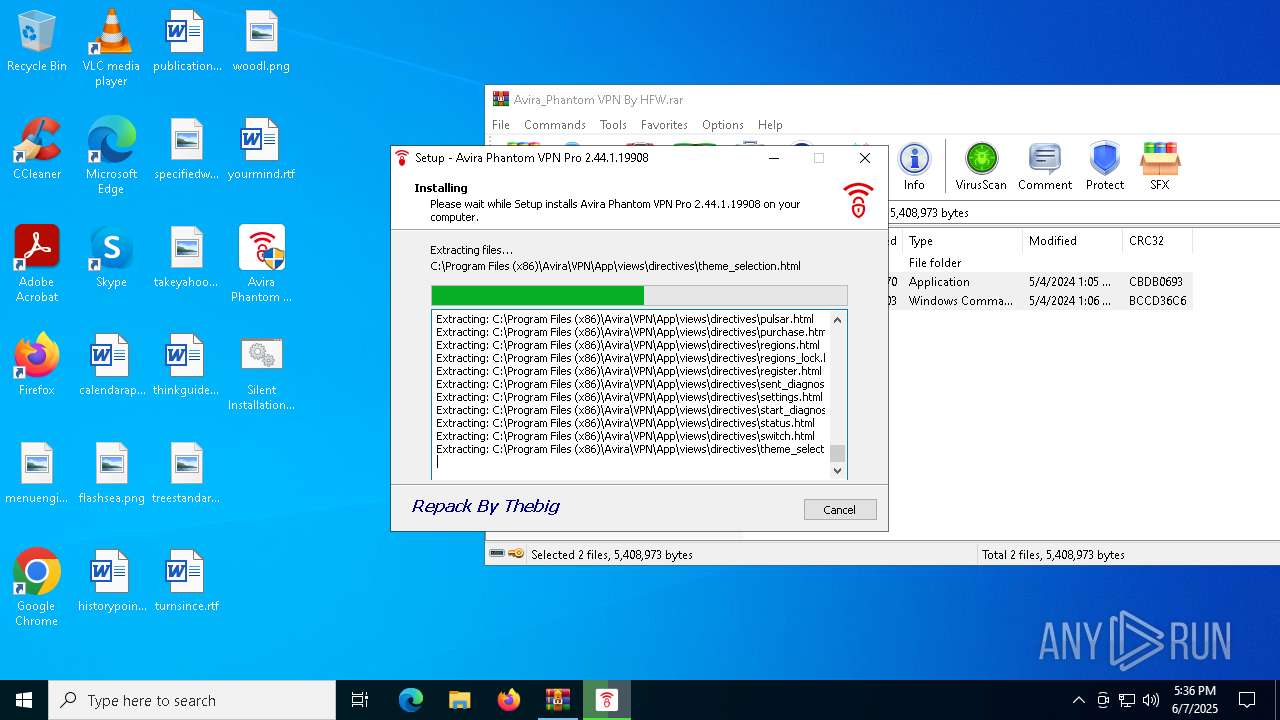
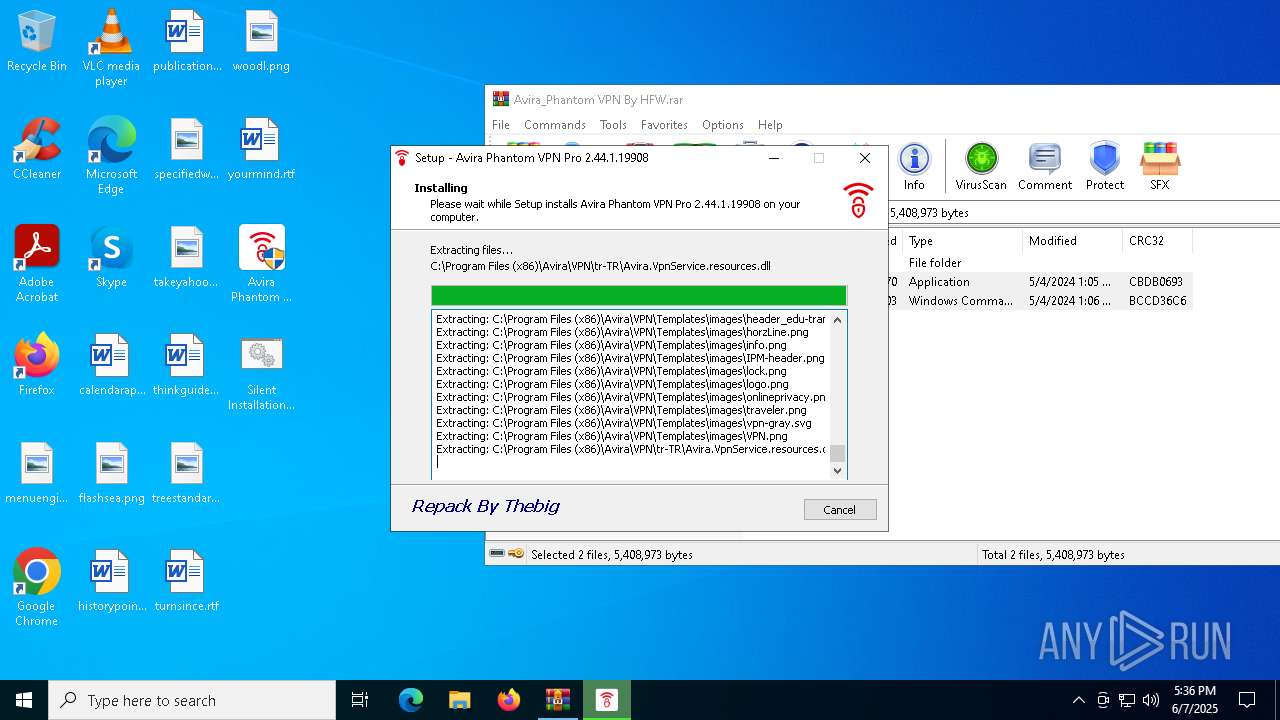
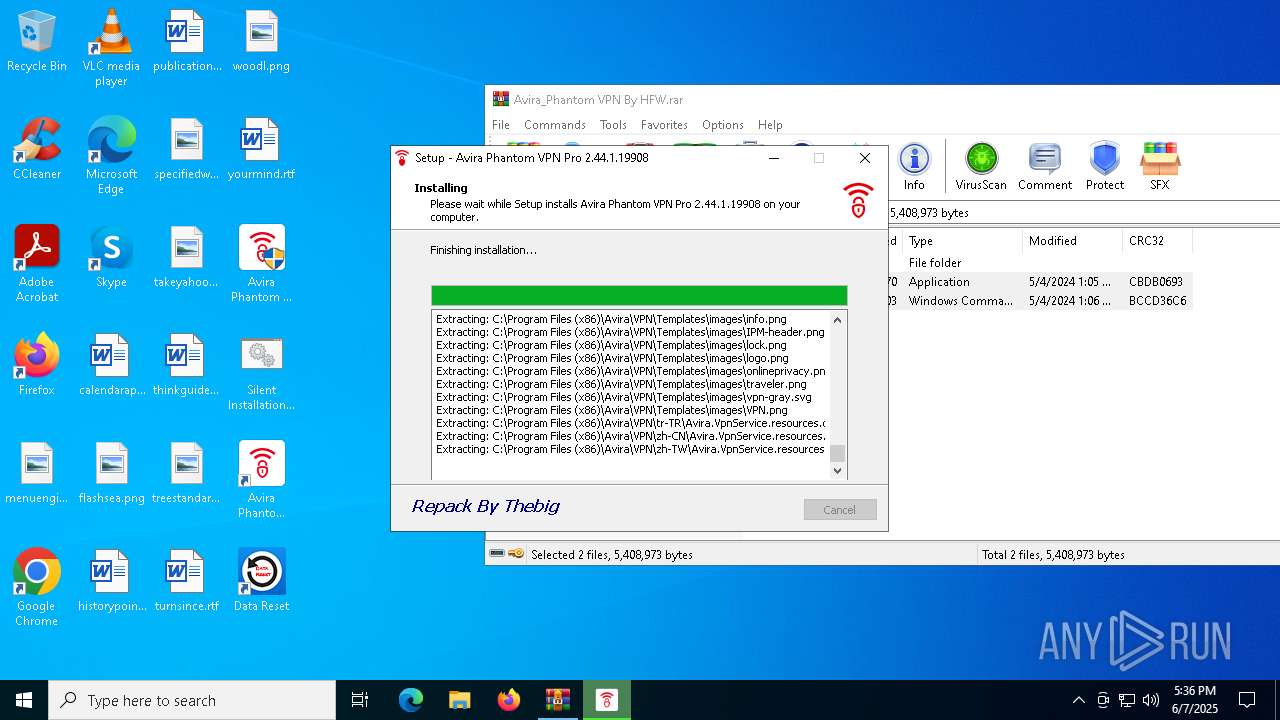
Executable content was dropped or overwritten
- Avira Phantom VPN Pro 2.44.1.19908.tmp (PID: 1472)
- Avira Phantom VPN Pro 2.44.1.19908.exe (PID: 8016)
- drvinst.exe (PID: 8088)
- tapinstall.exe (PID: 4400)
- drvinst.exe (PID: 8136)
Reads the Windows owner or organization settings
- Avira Phantom VPN Pro 2.44.1.19908.tmp (PID: 1472)
- Avira.VpnService.exe (PID: 7588)
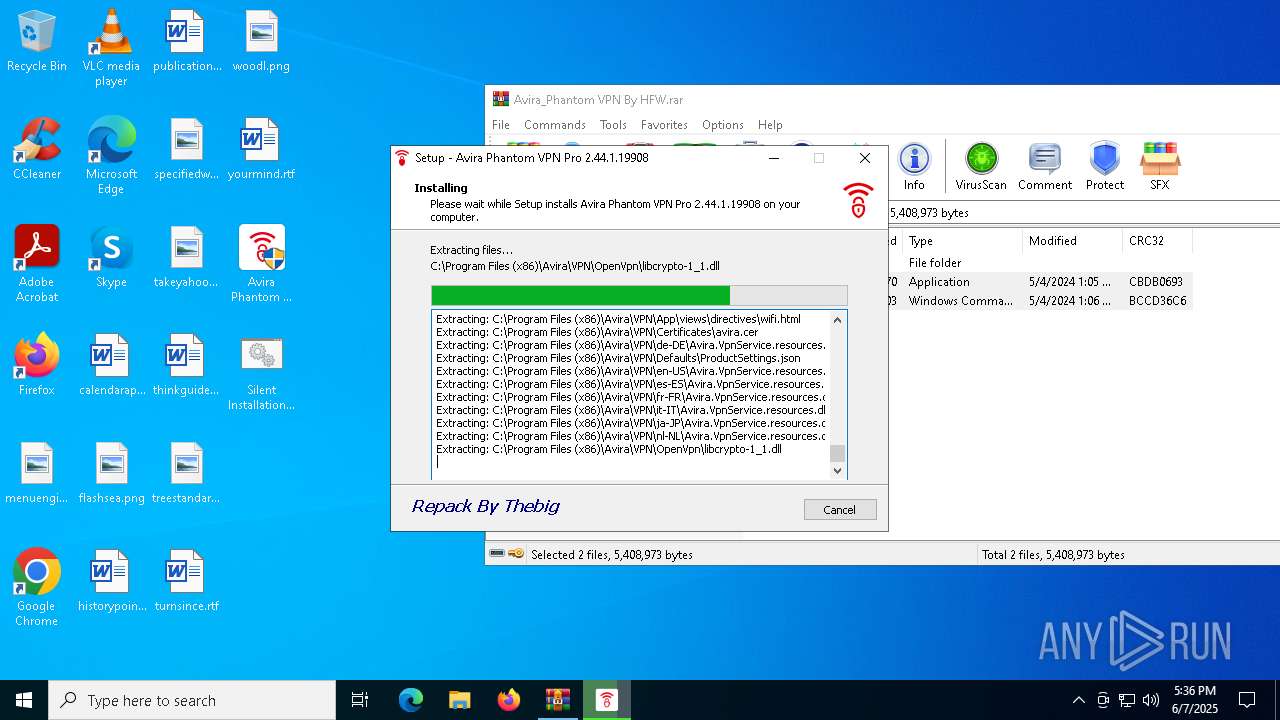
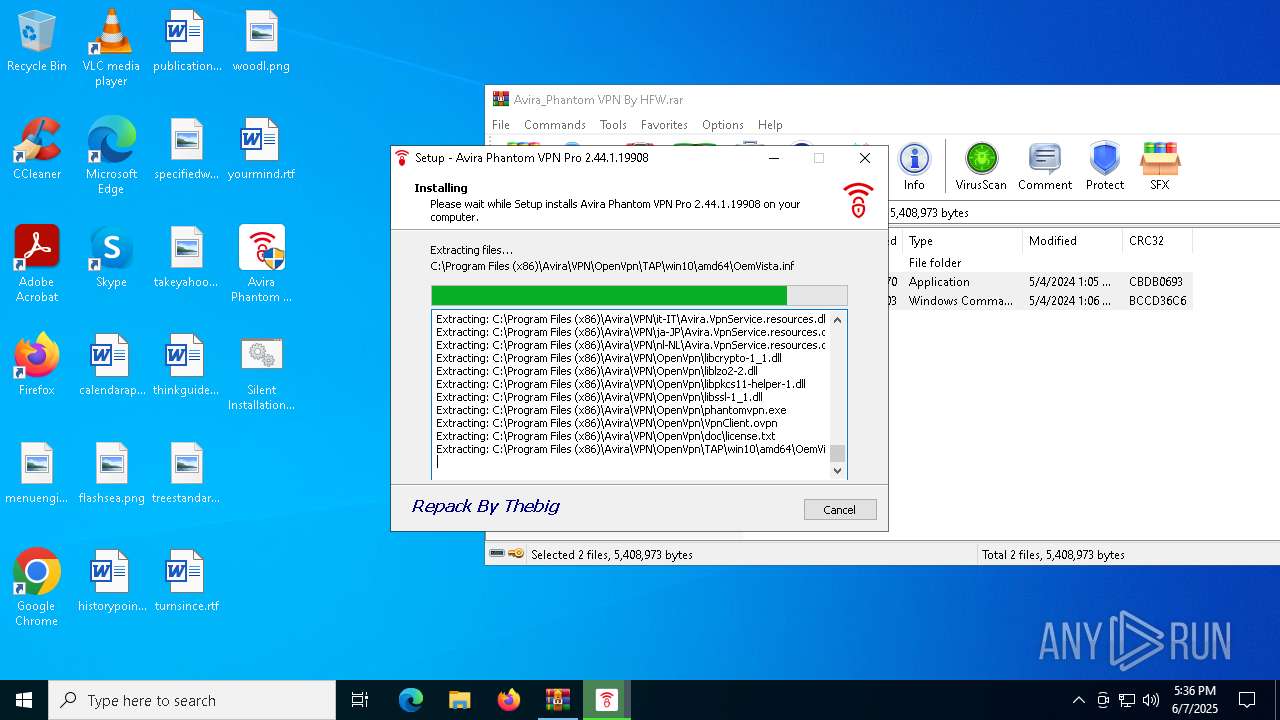
Drops a system driver (possible attempt to evade defenses)
- Avira Phantom VPN Pro 2.44.1.19908.tmp (PID: 1472)
- tapinstall.exe (PID: 4400)
- drvinst.exe (PID: 8088)
- drvinst.exe (PID: 8136)
Process drops legitimate windows executable
- Avira Phantom VPN Pro 2.44.1.19908.tmp (PID: 1472)
Reads security settings of Internet Explorer
- Avira Phantom VPN Pro 2.44.1.19908.tmp (PID: 1472)
- tapinstall.exe (PID: 4400)
- Avira.VpnService.exe (PID: 7588)
- Avira.WebAppHost.exe (PID: 8064)
- Avira.WebAppHost.exe (PID: 7856)
The process verifies whether the antivirus software is installed
- Avira Phantom VPN Pro 2.44.1.19908.tmp (PID: 1472)
- tapinstall.exe (PID: 4400)
- Avira.VpnService.exe (PID: 7588)
- Avira.NetworkBlocker.exe (PID: 5592)
- Avira.WebAppHost.exe (PID: 7856)
- Avira.WebAppHost.exe (PID: 8064)
- tapinstall.exe (PID: 3308)
- tapinstall.exe (PID: 6192)
- tapinstall.exe (PID: 6476)
- conhost.exe (PID: 7448)
- conhost.exe (PID: 8128)
- netsh.exe (PID: 4844)
- phantomvpn.exe (PID: 3396)
- conhost.exe (PID: 6676)
- netsh.exe (PID: 7512)
- netsh.exe (PID: 2136)
- phantomvpn.exe (PID: 7732)
- conhost.exe (PID: 1544)
- ipconfig.exe (PID: 1548)
- ipconfig.exe (PID: 5328)
- conhost.exe (PID: 2124)
- Avira.NetworkBlocker.exe (PID: 5592)
- netsh.exe (PID: 3008)
- conhost.exe (PID: 7128)
Uses TASKKILL.EXE to kill process
- Avira Phantom VPN Pro 2.44.1.19908.tmp (PID: 1472)
Stops a currently running service
- sc.exe (PID: 1116)
Creates files in the driver directory
- drvinst.exe (PID: 8088)
- drvinst.exe (PID: 8136)
Creates or modifies Windows services
- drvinst.exe (PID: 8136)
Windows service management via SC.EXE
- sc.exe (PID: 7220)
- sc.exe (PID: 2284)
Creates a new Windows service
- sc.exe (PID: 7424)
Executes as Windows Service
- Avira.VpnService.exe (PID: 7588)
Uses NETSH.EXE to add a firewall rule or allowed programs
- Avira Phantom VPN Pro 2.44.1.19908.tmp (PID: 1472)
Starts CMD.EXE for commands execution
- Avira Phantom VPN Pro 2.44.1.19908.tmp (PID: 1472)
Restarts service on failure
- sc.exe (PID: 232)
Reads Microsoft Outlook installation path
- Avira.WebAppHost.exe (PID: 8064)
Searches for installed software
- Avira.VpnService.exe (PID: 7588)
Reads Internet Explorer settings
- Avira.WebAppHost.exe (PID: 8064)
Suspicious use of NETSH.EXE
- phantomvpn.exe (PID: 3396)
Application launched itself
- phantomvpn.exe (PID: 3396)
Process uses IPCONFIG to clear DNS cache
- phantomvpn.exe (PID: 7732)
Process uses IPCONFIG to get network configuration information
- phantomvpn.exe (PID: 7732)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 3140)
INFO
Create files in a temporary directory
- Avira Phantom VPN Pro 2.44.1.19908.exe (PID: 8016)
- Avira Phantom VPN Pro 2.44.1.19908.tmp (PID: 1472)
- tapinstall.exe (PID: 4400)
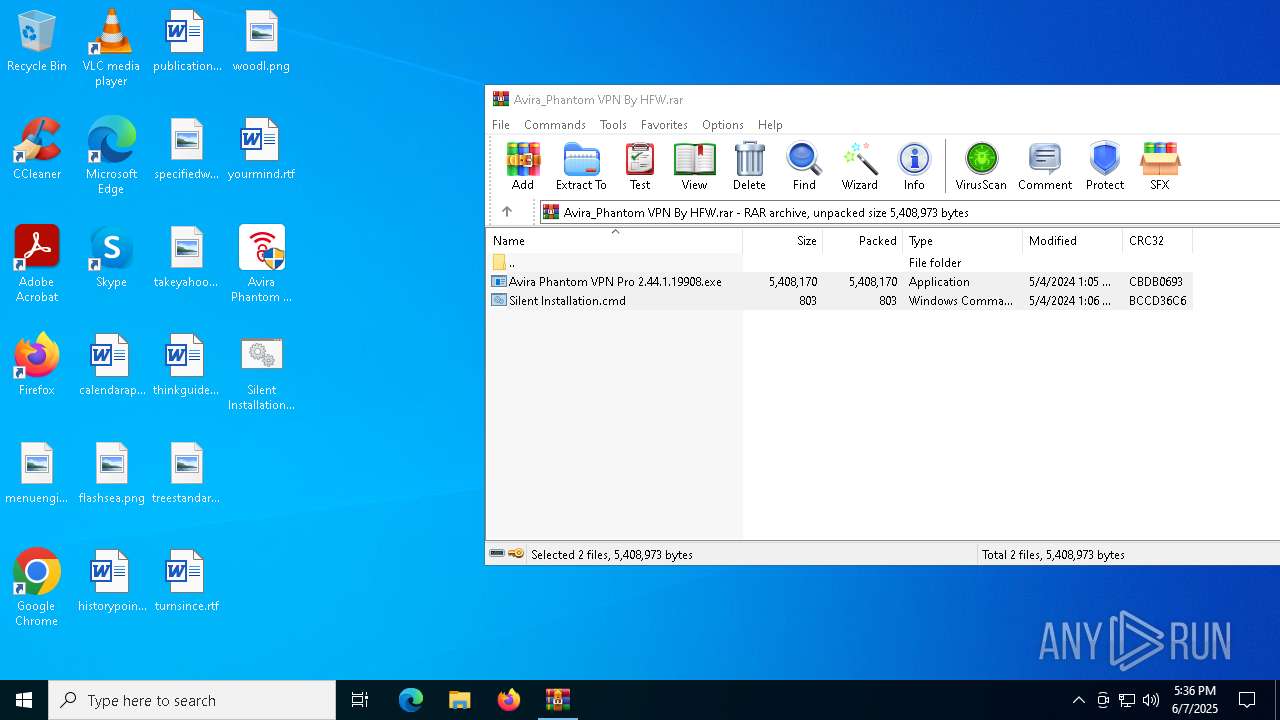
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6300)
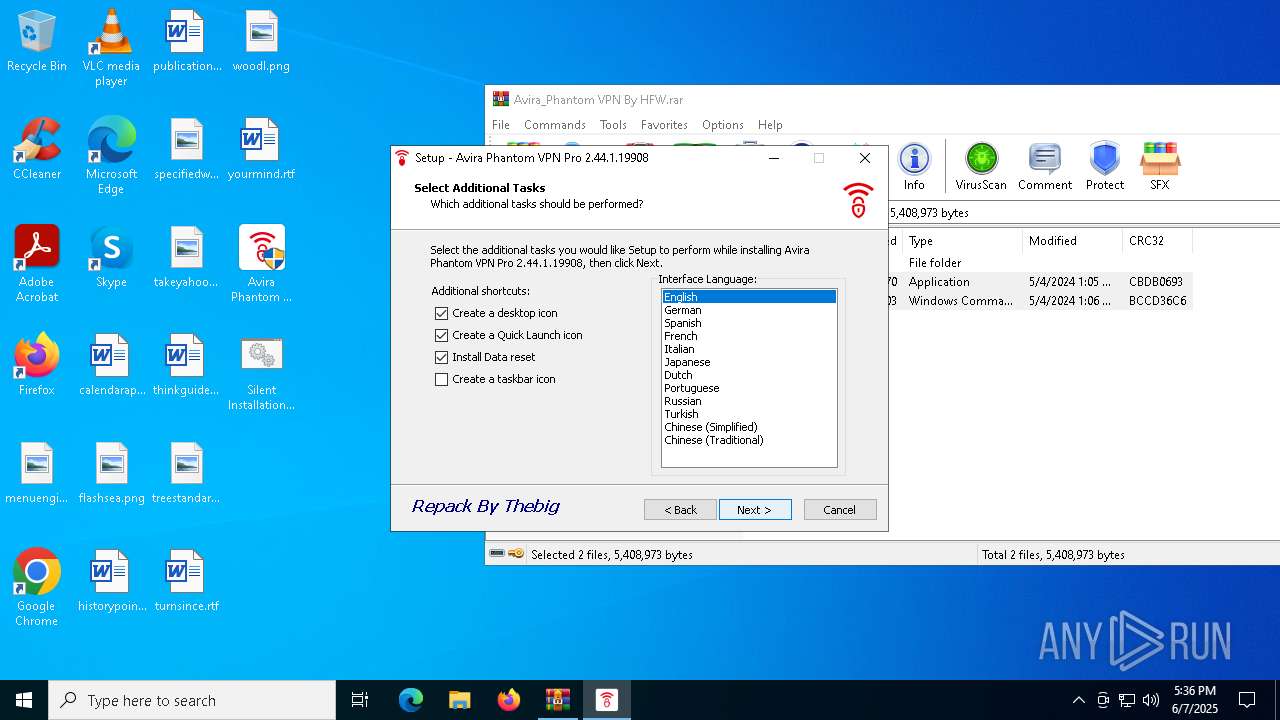
Checks supported languages
- Avira Phantom VPN Pro 2.44.1.19908.exe (PID: 8016)
- Avira Phantom VPN Pro 2.44.1.19908.tmp (PID: 1472)
- drvinst.exe (PID: 8088)
- drvinst.exe (PID: 8136)
- Avira.VpnService.exe (PID: 7588)
- Avira.WebAppHost.exe (PID: 7856)
- Avira.NetworkBlocker.exe (PID: 5592)
- Avira.WebAppHost.exe (PID: 8064)
- tapinstall.exe (PID: 6192)
- tapinstall.exe (PID: 3308)
- tapinstall.exe (PID: 6476)
- phantomvpn.exe (PID: 3396)
- tapinstall.exe (PID: 4400)
- phantomvpn.exe (PID: 7732)
- Avira.NetworkBlocker.exe (PID: 5592)
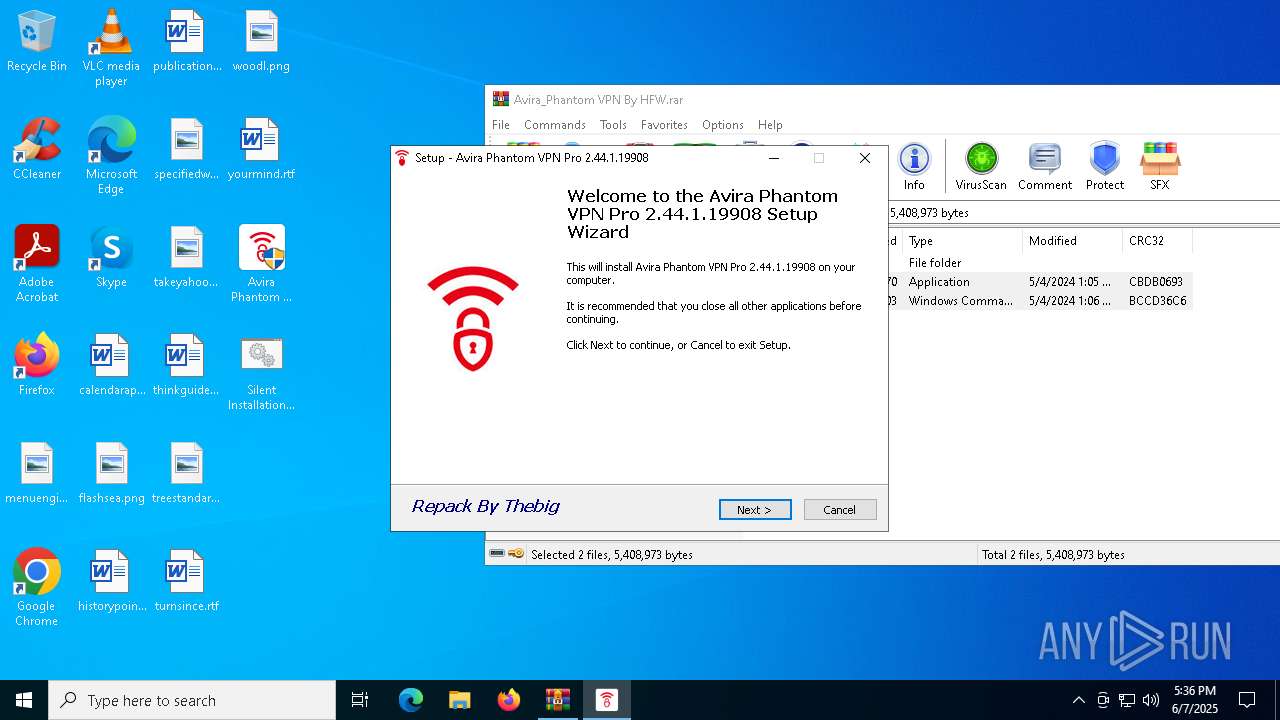
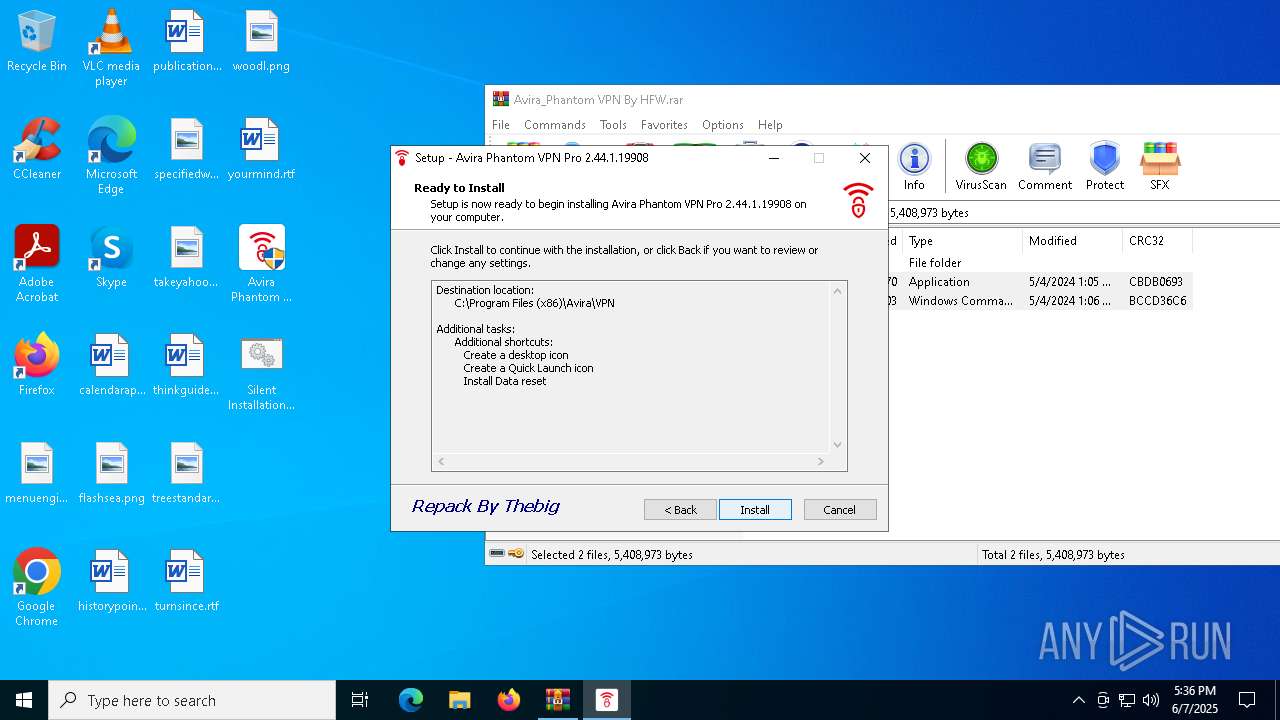
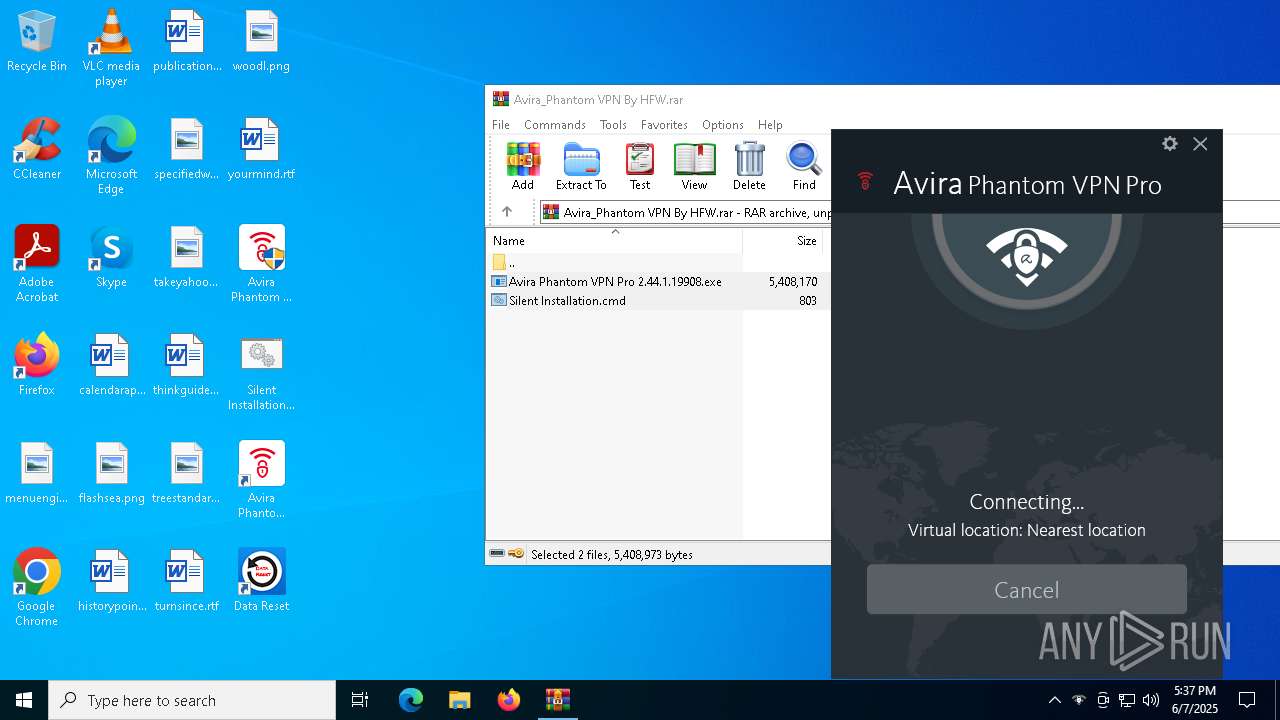
Manual execution by a user
- Avira Phantom VPN Pro 2.44.1.19908.exe (PID: 8016)
- Avira Phantom VPN Pro 2.44.1.19908.exe (PID: 5400)
- firefox.exe (PID: 1812)
- firefox.exe (PID: 1116)
Reads the computer name
- Avira Phantom VPN Pro 2.44.1.19908.tmp (PID: 1472)
- tapinstall.exe (PID: 4400)
- Avira.VpnService.exe (PID: 7588)
- drvinst.exe (PID: 8088)
- drvinst.exe (PID: 8136)
- Avira.NetworkBlocker.exe (PID: 5592)
- Avira.WebAppHost.exe (PID: 8064)
- Avira.WebAppHost.exe (PID: 7856)
- phantomvpn.exe (PID: 3396)
- Avira.NetworkBlocker.exe (PID: 5592)
Compiled with Borland Delphi (YARA)
- Avira Phantom VPN Pro 2.44.1.19908.exe (PID: 8016)
- Avira Phantom VPN Pro 2.44.1.19908.tmp (PID: 1472)
Creates files or folders in the user directory
- Avira Phantom VPN Pro 2.44.1.19908.tmp (PID: 1472)
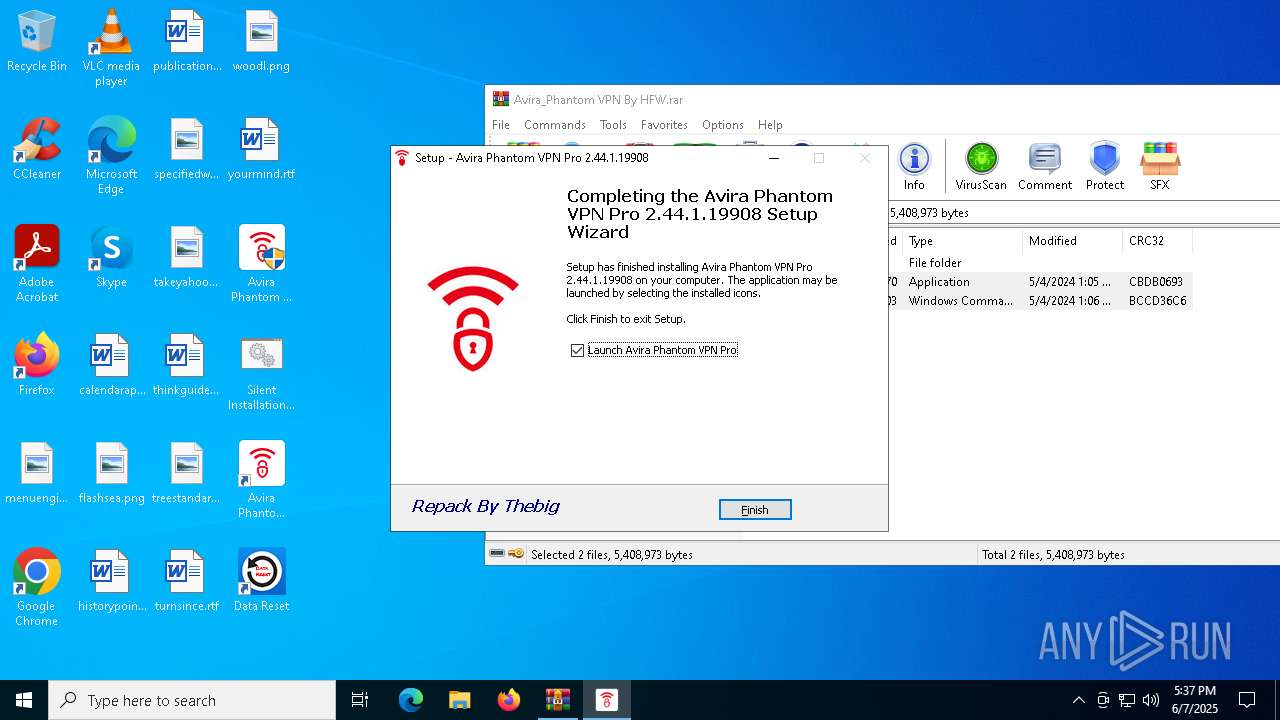
Creates a software uninstall entry
- Avira Phantom VPN Pro 2.44.1.19908.tmp (PID: 1472)
Process checks computer location settings
- Avira Phantom VPN Pro 2.44.1.19908.tmp (PID: 1472)
The sample compiled with english language support
- Avira Phantom VPN Pro 2.44.1.19908.tmp (PID: 1472)
- tapinstall.exe (PID: 4400)
- drvinst.exe (PID: 8088)
- drvinst.exe (PID: 8136)
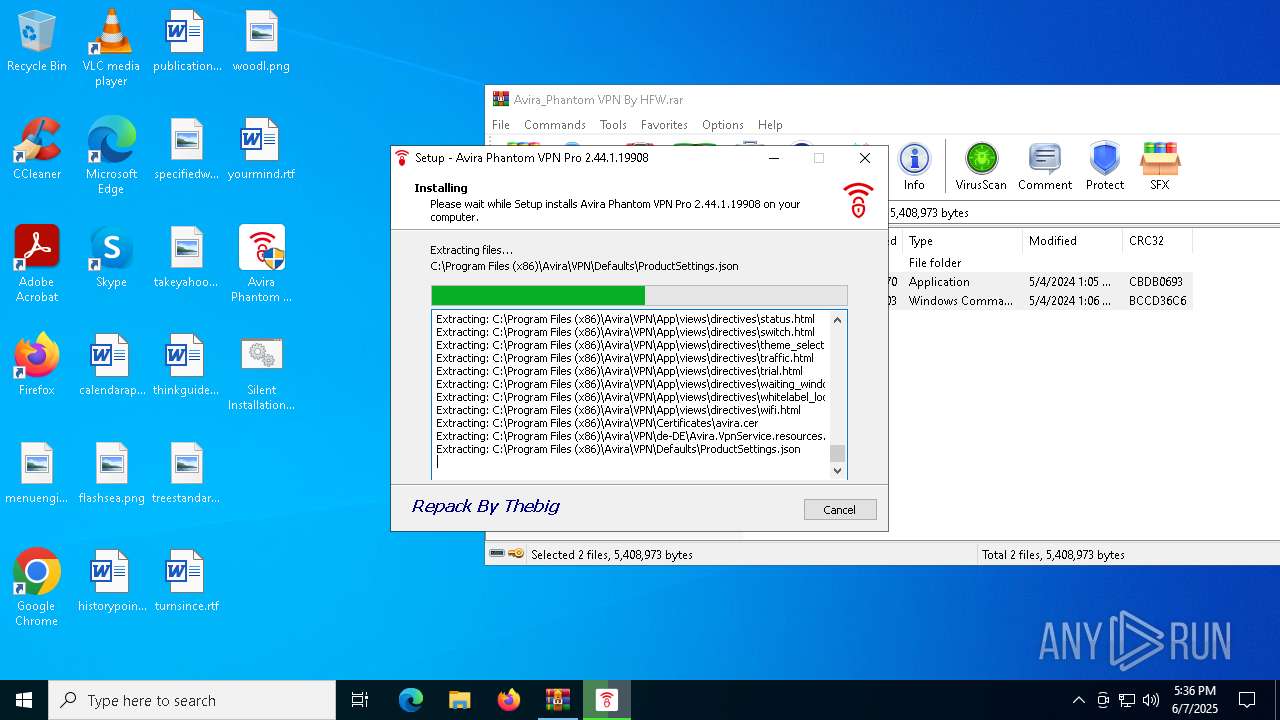
Creates files in the program directory
- Avira Phantom VPN Pro 2.44.1.19908.tmp (PID: 1472)
- Avira.VpnService.exe (PID: 7588)
Detects InnoSetup installer (YARA)
- Avira Phantom VPN Pro 2.44.1.19908.exe (PID: 8016)
- Avira Phantom VPN Pro 2.44.1.19908.tmp (PID: 1472)
Reads the machine GUID from the registry
- tapinstall.exe (PID: 4400)
- drvinst.exe (PID: 8088)
- Avira.VpnService.exe (PID: 7588)
- Avira.WebAppHost.exe (PID: 7856)
- Avira.WebAppHost.exe (PID: 8064)
- phantomvpn.exe (PID: 3396)
Reads the software policy settings
- drvinst.exe (PID: 8088)
- tapinstall.exe (PID: 4400)
- Avira.VpnService.exe (PID: 7588)
Reads Environment values
- Avira.VpnService.exe (PID: 7588)
- Avira.WebAppHost.exe (PID: 8064)
Disables trace logs
- Avira.VpnService.exe (PID: 7588)
- Avira.WebAppHost.exe (PID: 8064)
- netsh.exe (PID: 4844)
- netsh.exe (PID: 2136)
- netsh.exe (PID: 7512)
- netsh.exe (PID: 3008)
Reads product name
- Avira.VpnService.exe (PID: 7588)
Reads CPU info
- Avira.VpnService.exe (PID: 7588)
Checks proxy server information
- Avira.WebAppHost.exe (PID: 8064)
- Avira.VpnService.exe (PID: 7588)
Application launched itself
- firefox.exe (PID: 1116)
- firefox.exe (PID: 5164)
- firefox.exe (PID: 1812)
- firefox.exe (PID: 7280)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|
Total processes
213
Monitored processes
80
Malicious processes
13
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | "C:\Windows\System32\taskkill.exe" /f /im Avira.WebAppHost.exe | C:\Windows\SysWOW64\taskkill.exe | — | Avira Phantom VPN Pro 2.44.1.19908.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 232 | "sc" failure AviraPhantomVPN reset= 86400 actions= restart/5000/restart/10000//1000 | C:\Windows\SysWOW64\sc.exe | — | Avira Phantom VPN Pro 2.44.1.19908.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 960 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | tapinstall.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1116 | "C:\Windows\System32\sc.exe" stop AviraPhantomVPN | C:\Windows\SysWOW64\sc.exe | — | Avira Phantom VPN Pro 2.44.1.19908.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1116 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 1196 | "C:\WINDOWS\system32\netsh.exe" advfirewall firewall add rule dir=out action=allow program="C:\Program Files (x86)\Avira\VPN\OpenVpn\phantomvpn.exe" enable=yes profile=any name="Avira Phantom VPN" | C:\Windows\SysWOW64\netsh.exe | — | Avira Phantom VPN Pro 2.44.1.19908.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1300 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | tapinstall.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1452 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5168 -parentBuildID 20240213221259 -sandboxingKind 0 -prefsHandle 5160 -prefMapHandle 5156 -prefsLen 36642 -prefMapSize 244583 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {19bfc061-3c8e-4ff4-a358-c529d2d6190c} 7280 "\\.\pipe\gecko-crash-server-pipe.7280" 1a0b1189710 utility | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 123.0 Modules
| |||||||||||||||
| 1472 | "C:\Users\admin\AppData\Local\Temp\is-B50IM.tmp\Avira Phantom VPN Pro 2.44.1.19908.tmp" /SL5="$F034A,4884611,248832,C:\Users\admin\Desktop\Avira Phantom VPN Pro 2.44.1.19908.exe" | C:\Users\admin\AppData\Local\Temp\is-B50IM.tmp\Avira Phantom VPN Pro 2.44.1.19908.tmp | Avira Phantom VPN Pro 2.44.1.19908.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1544 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | ipconfig.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
46 773
Read events
46 654
Write events
112
Delete events
7
Modification events
| (PID) Process: | (6300) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (6300) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6300) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6300) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6300) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Avira_Phantom VPN By HFW.rar | |||
| (PID) Process: | (6300) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6300) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6300) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6300) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4400) tapinstall.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.dev.log |
Value: 4096 | |||
Executable files
117
Suspicious files
240
Text files
750
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1472 | Avira Phantom VPN Pro 2.44.1.19908.tmp | C:\Users\admin\AppData\Local\Temp\is-LNLQL.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 1472 | Avira Phantom VPN Pro 2.44.1.19908.tmp | C:\Users\admin\AppData\Local\Temp\is-LNLQL.tmp\_isetup\_setup64.tmp | executable | |
MD5:4FF75F505FDDCC6A9AE62216446205D9 | SHA256:A4C86FC4836AC728D7BD96E7915090FD59521A9E74F1D06EF8E5A47C8695FD81 | |||
| 6300 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6300.7720\Silent Installation.cmd | text | |
MD5:D153BDA77C7F2C282DD68E6D3126258F | SHA256:BE3DDA89063E6E6CEFBA5C8242BB33F0979A7CF2BF09CBE47FF2EE8F62A217D5 | |||
| 6300 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6300.7720\Avira Phantom VPN Pro 2.44.1.19908.exe | executable | |
MD5:0FE5732C15E8150C8F107A0E73DB4E45 | SHA256:940EC4012984218F6E314D793C995B3CB3C3366AABBA0308FECE77FE2ED7ABB7 | |||
| 1472 | Avira Phantom VPN Pro 2.44.1.19908.tmp | C:\Program Files (x86)\Avira\VPN\unins000.exe | executable | |
MD5:F019D7BE022910406834AE32E6F3417E | SHA256:7597B3DBF0FCE4D5CE61285D7702F067E04C00025F6AE6E9378227B060AB4CEF | |||
| 1472 | Avira Phantom VPN Pro 2.44.1.19908.tmp | C:\Program Files (x86)\Avira\VPN\is-226GO.tmp | xml | |
MD5:0D46BDC17F97E662981FD6AC11888307 | SHA256:A2B68CD7AD5E1158D182D59131488A0AA84C106F142AB62451BC284C72218216 | |||
| 8016 | Avira Phantom VPN Pro 2.44.1.19908.exe | C:\Users\admin\AppData\Local\Temp\is-B50IM.tmp\Avira Phantom VPN Pro 2.44.1.19908.tmp | executable | |
MD5:0C1C8EB89026AF3BC48B56D10759C400 | SHA256:02FEBFFFCAC96296E9CBAD84CCCF0153A11C051E0F2421E86360ECCFC21F7F4D | |||
| 1472 | Avira Phantom VPN Pro 2.44.1.19908.tmp | C:\Program Files (x86)\Avira\VPN\is-590SM.tmp | executable | |
MD5:F019D7BE022910406834AE32E6F3417E | SHA256:7597B3DBF0FCE4D5CE61285D7702F067E04C00025F6AE6E9378227B060AB4CEF | |||
| 1472 | Avira Phantom VPN Pro 2.44.1.19908.tmp | C:\Program Files (x86)\Avira\VPN\is-PHRD2.tmp | image | |
MD5:00EF5795980D6286FDB6B228341169B5 | SHA256:127BF7B231CA20E9805B28F3521E88A311D03BC5B4FD1EDFF52AC6CBD1B091D3 | |||
| 1472 | Avira Phantom VPN Pro 2.44.1.19908.tmp | C:\Users\admin\AppData\Local\Temp\is-LNLQL.tmp\English.rtf | text | |
MD5:B0533AFC5844AF4513E46CC4E451DBBA | SHA256:A5ECF679013A334DAC5E2D264F8F45D38CCBF4752C4B4F8DA3DD41DE0EAE17DA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
42
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.20.245.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4164 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7232 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.20.245.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7232 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7588 | Avira.VpnService.exe | GET | 200 | 184.24.77.24:80 | http://www.msftncsi.com/ncsi.txt | unknown | — | — | whitelisted |
7588 | Avira.VpnService.exe | GET | 200 | 184.24.77.24:80 | http://www.msftncsi.com/ncsi.txt | unknown | — | — | whitelisted |
7588 | Avira.VpnService.exe | GET | 200 | 184.24.77.24:80 | http://www.msftncsi.com/ncsi.txt | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2516 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.20.245.139:80 | crl.microsoft.com | Akamai International B.V. | SE | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4164 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |