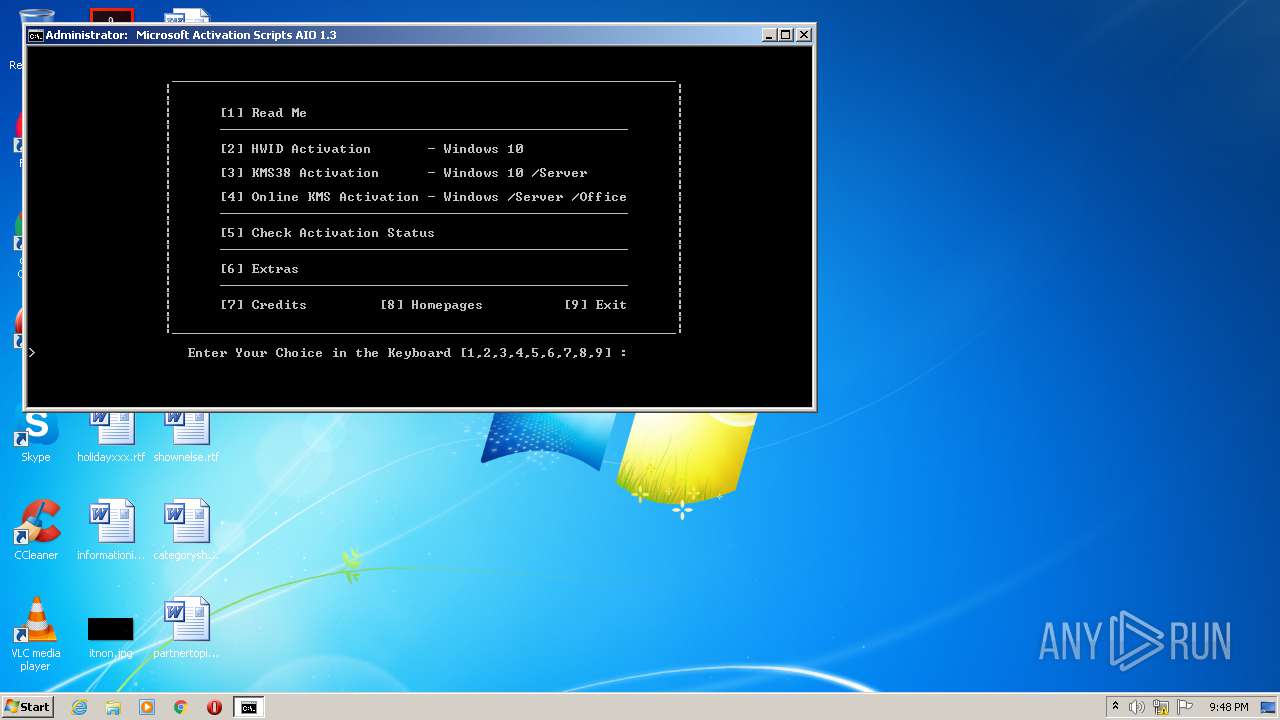
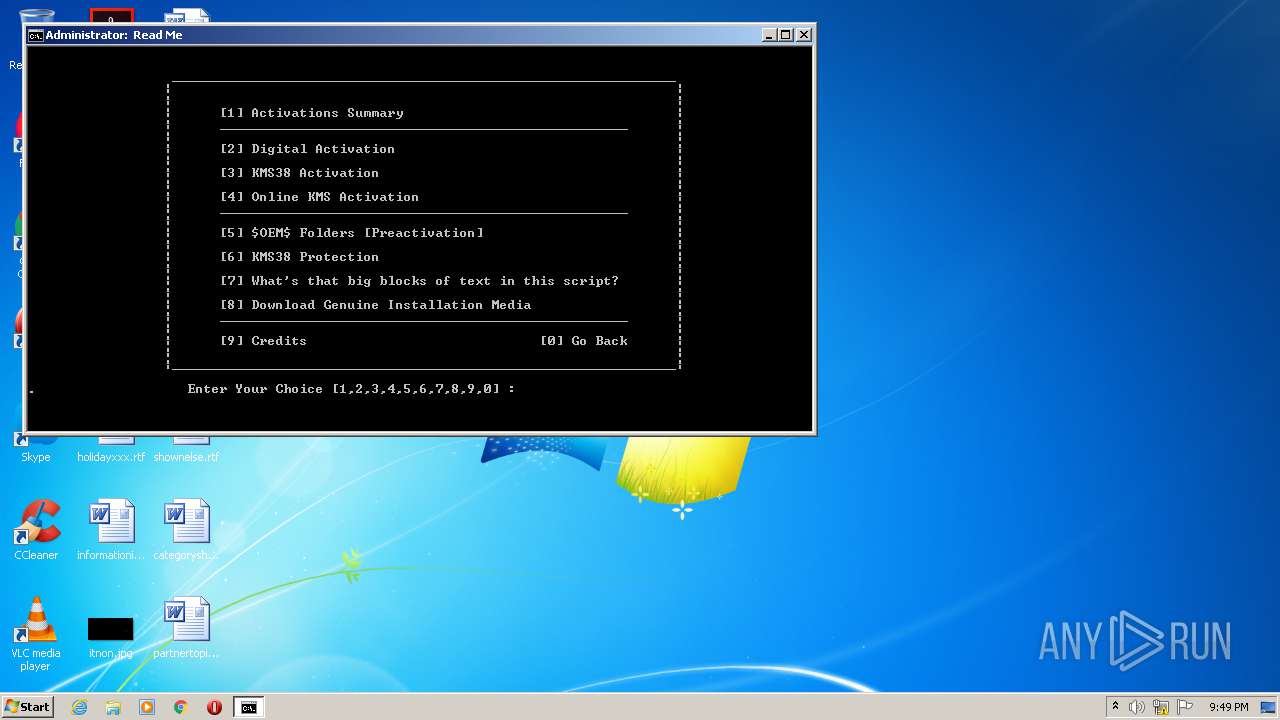
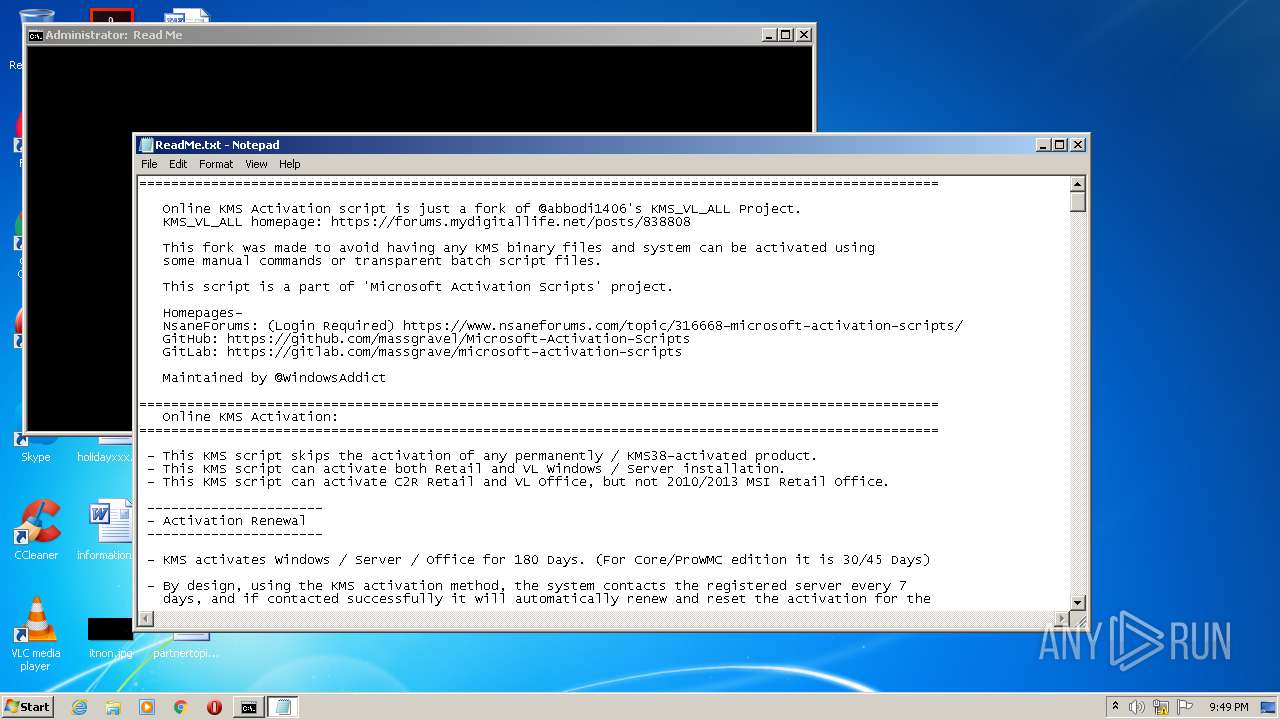
| File name: | MAS_1.3_AIO.cmd |
| Full analysis: | https://app.any.run/tasks/c60d4423-a27e-4293-ab8e-ebcbbebfc63b |
| Verdict: | Malicious activity |
| Analysis date: | December 10, 2020, 21:48:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | EB1145F4E71690E3F8FDAC24521C968A |
| SHA1: | A36C310E4C0C05EB416EBF4FFEF93FC2A17A5777 |
| SHA256: | A60B948941577293E07FF2707855DC448996713B47CAFF4193D91AFDEA4E8EF4 |
| SSDEEP: | 49152:8day1I0JxlXsyZ6/mDbR56nAfl5P/r/Kk:up/eyZ6/mDlTfbp |
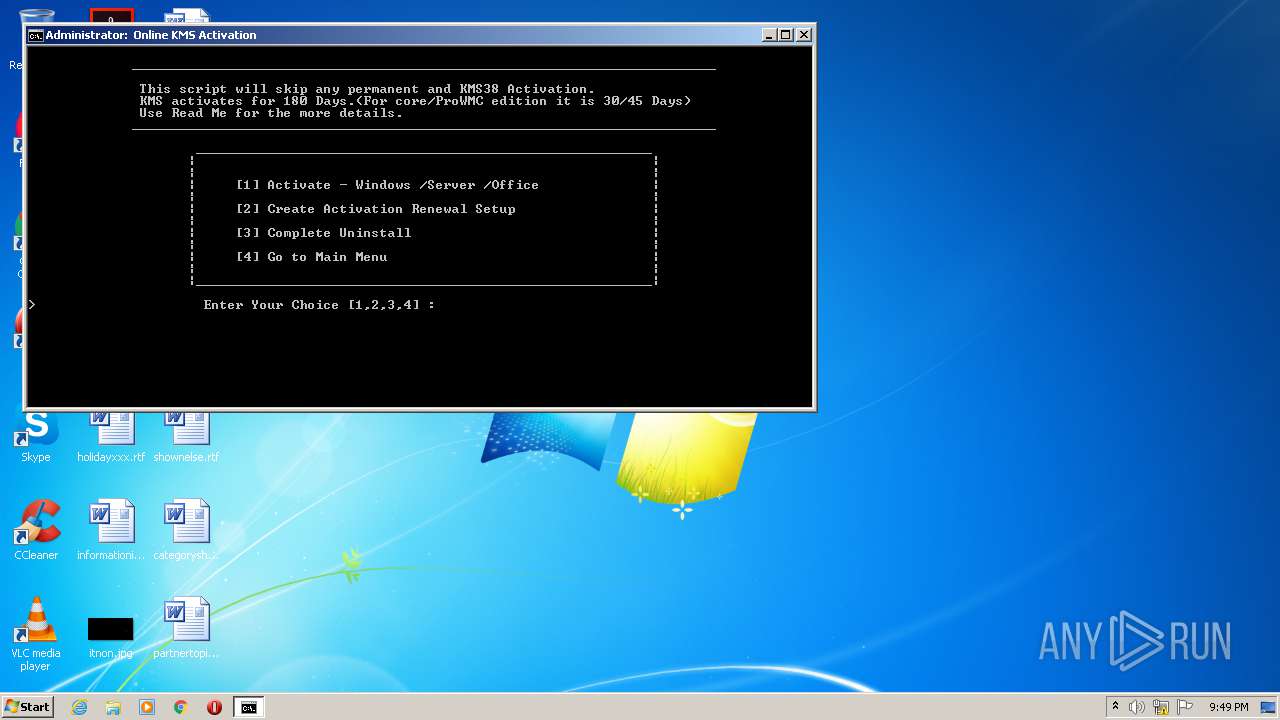
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 544)
- cmd.exe (PID: 3616)
- cmd.exe (PID: 4076)
Starts Visual C# compiler
- powershell.exe (PID: 2868)
- powershell.exe (PID: 3864)
Drops executable file immediately after starts
- csc.exe (PID: 3572)
- expand.exe (PID: 3076)
- expand.exe (PID: 2244)
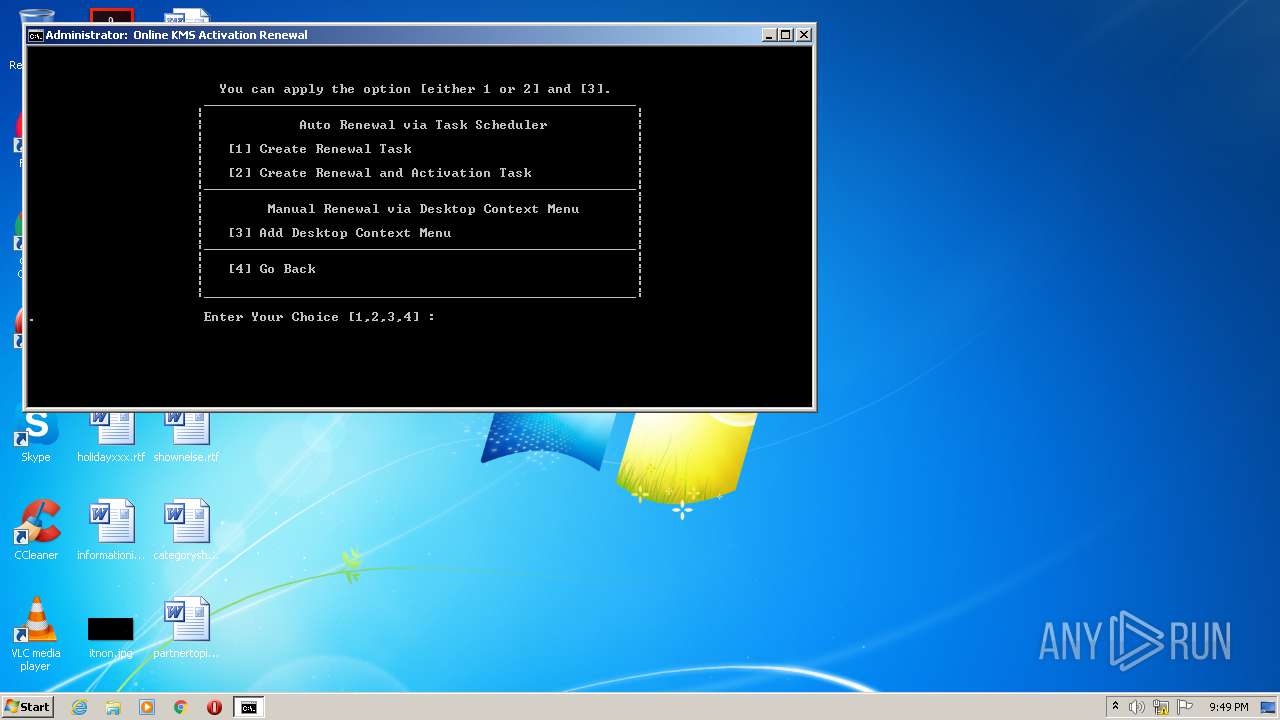
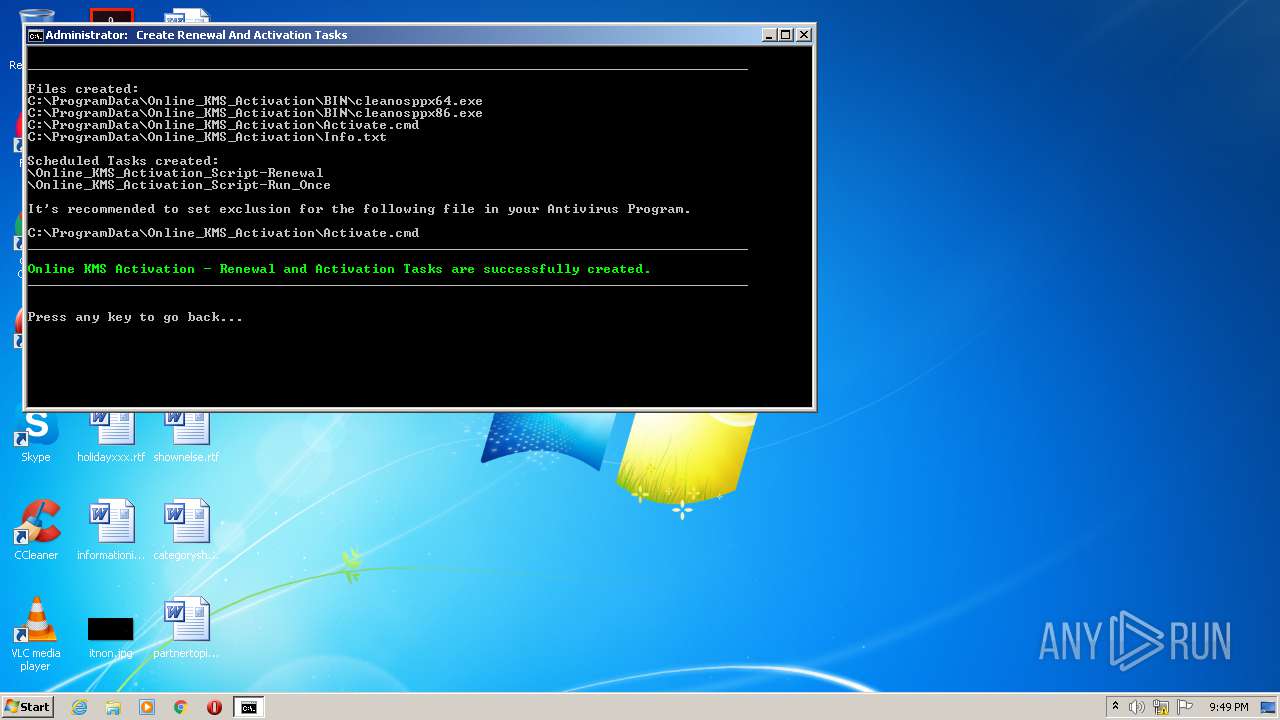
Loads the Task Scheduler COM API
- schtasks.exe (PID: 404)
- schtasks.exe (PID: 3384)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 4076)
SUSPICIOUS
Application launched itself
- cmd.exe (PID: 2844)
- cmd.exe (PID: 544)
- cmd.exe (PID: 3616)
- cmd.exe (PID: 4076)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2844)
- cscript.exe (PID: 2496)
- cmd.exe (PID: 544)
- cmd.exe (PID: 3616)
- cmd.exe (PID: 4076)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2844)
- cmd.exe (PID: 544)
- cmd.exe (PID: 3616)
- cmd.exe (PID: 2460)
- cmd.exe (PID: 4076)
Executes scripts
- cmd.exe (PID: 2844)
Uses RUNDLL32.EXE to load library
- cscript.exe (PID: 2496)
Creates files in the Windows directory
- powershell.exe (PID: 3168)
- powershell.exe (PID: 2868)
- expand.exe (PID: 3076)
- powershell.exe (PID: 2676)
- expand.exe (PID: 2244)
- powershell.exe (PID: 2364)
- powershell.exe (PID: 3060)
- powershell.exe (PID: 3864)
- powershell.exe (PID: 2428)
- powershell.exe (PID: 1252)
Creates files in the user directory
- powershell.exe (PID: 3168)
- powershell.exe (PID: 2868)
- powershell.exe (PID: 2676)
- powershell.exe (PID: 2924)
- powershell.exe (PID: 3776)
- powershell.exe (PID: 1916)
- powershell.exe (PID: 3864)
- powershell.exe (PID: 3060)
- powershell.exe (PID: 2364)
- powershell.exe (PID: 2428)
- powershell.exe (PID: 1464)
- powershell.exe (PID: 688)
- powershell.exe (PID: 1252)
Removes files from Windows directory
- cmd.exe (PID: 544)
- powershell.exe (PID: 2868)
- expand.exe (PID: 3076)
- expand.exe (PID: 2244)
- powershell.exe (PID: 3864)
- cmd.exe (PID: 4076)
Starts CHOICE.EXE (used to create a delay)
- cmd.exe (PID: 544)
- cmd.exe (PID: 4076)
Executable content was dropped or overwritten
- csc.exe (PID: 3572)
- expand.exe (PID: 3076)
- expand.exe (PID: 2244)
- cmd.exe (PID: 4076)
Drops a file that was compiled in debug mode
- csc.exe (PID: 3572)
- expand.exe (PID: 3076)
- expand.exe (PID: 2244)
- cmd.exe (PID: 4076)
Drops a file with a compile date too recent
- csc.exe (PID: 3572)
Creates files in the program directory
- cmd.exe (PID: 4076)
- powershell.exe (PID: 1464)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .bib/bibtex/txt | | | BibTeX references (100) |
|---|
Total processes
104
Monitored processes
65
Malicious processes
9
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 340 | timeout /t 2 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 404 | schtasks /create /tn "Online_KMS_Activation_Script-Run_Once" /ru "SYSTEM" /xml "C:\Windows\Temp\_KMS_Task_Work\Run_Once.xml" | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 544 | "C:\Windows\System32\cmd.exe" /c ""C:\Users\admin\AppData\Local\Temp\MAS_1.3_AIO.cmd" -el" | C:\Windows\System32\cmd.exe | cscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 680 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES7FC6.tmp" "c:\Users\admin\AppData\Local\Temp\CSC7FC5.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 688 | powershell -nop -ep bypass -c write-host -back Black -fore Green Online KMS Activation - Renewal and Activation Tasks are successfully created. | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1004 | mode con: cols=98 lines=30 | C:\Windows\system32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
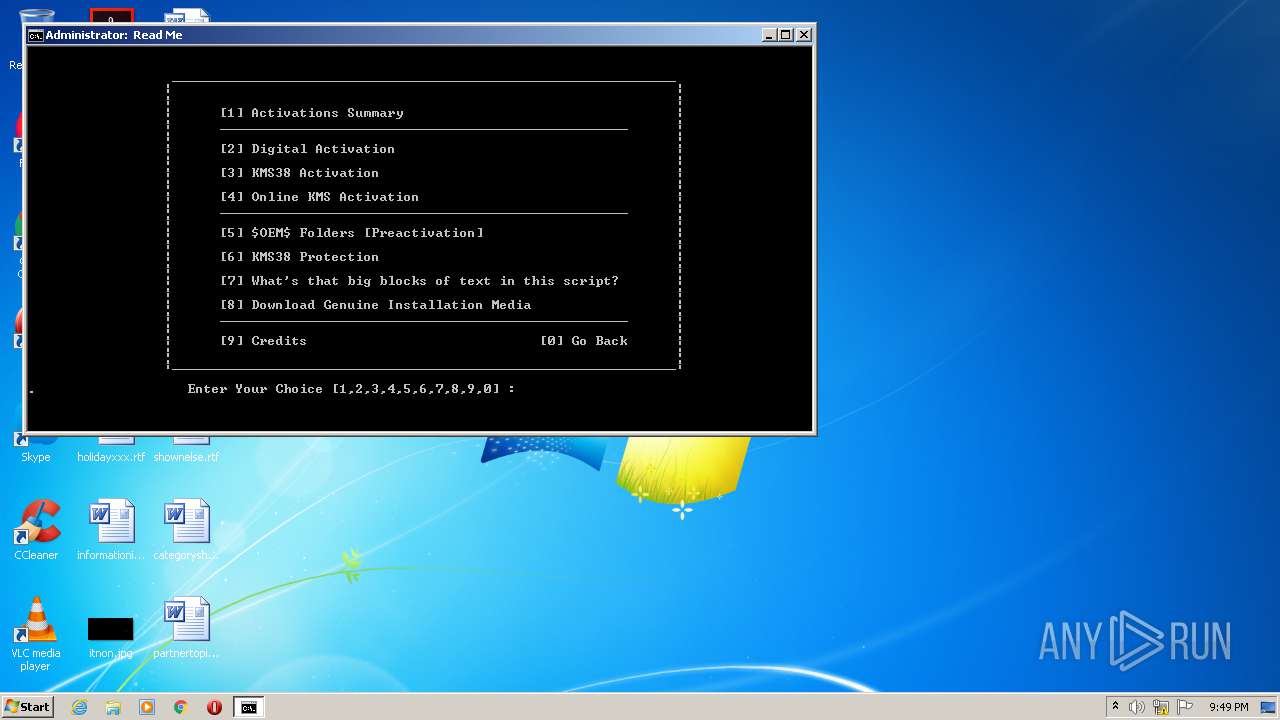
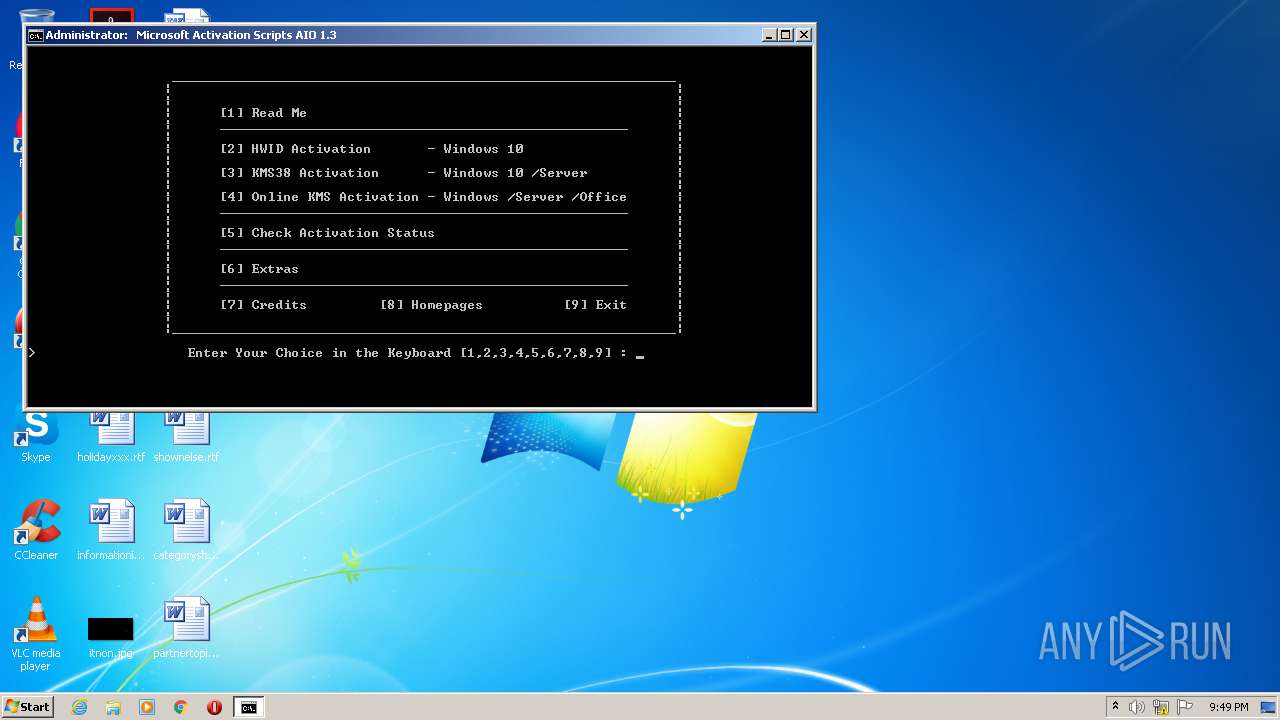
| 1068 | choice /C:1234567890 /N /M ". Enter Your Choice [1,2,3,4,5,6,7,8,9,0] : " | C:\Windows\system32\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Offers the user a choice Exit code: 10 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1252 | powershell -nop -ep bypass -c "$f=[io.file]::ReadAllText('C:\Windows\Temp\_MAS\Renewal_Setup.cmd') -split \":run_once\:.*`r`n\"; [io.file]::WriteAllText('C:\Windows\Temp\_KMS_Task_Work\Run_Once.xml',$f[1].Trim(),[System.Text.Encoding]::Unicode);" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1256 | C:\Windows\system32\cmd.exe /c ver | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1328 | reg query HKU\S-1-5-19 | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 326
Read events
2 607
Write events
719
Delete events
0
Modification events
| (PID) Process: | (2496) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2496) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3168) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2868) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2676) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3776) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2924) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1916) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3864) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3060) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
7
Suspicious files
26
Text files
15
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3168 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\I37YUK374C27ZX6YQJUP.temp | — | |
MD5:— | SHA256:— | |||
| 2868 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\6F9ZAFQSU48TW3U7FR4R.temp | — | |
MD5:— | SHA256:— | |||
| 3572 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSC571F.tmp | — | |
MD5:— | SHA256:— | |||
| 2140 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RES5720.tmp | — | |
MD5:— | SHA256:— | |||
| 3572 | csc.exe | C:\Users\admin\AppData\Local\Temp\715aawar.out | — | |
MD5:— | SHA256:— | |||
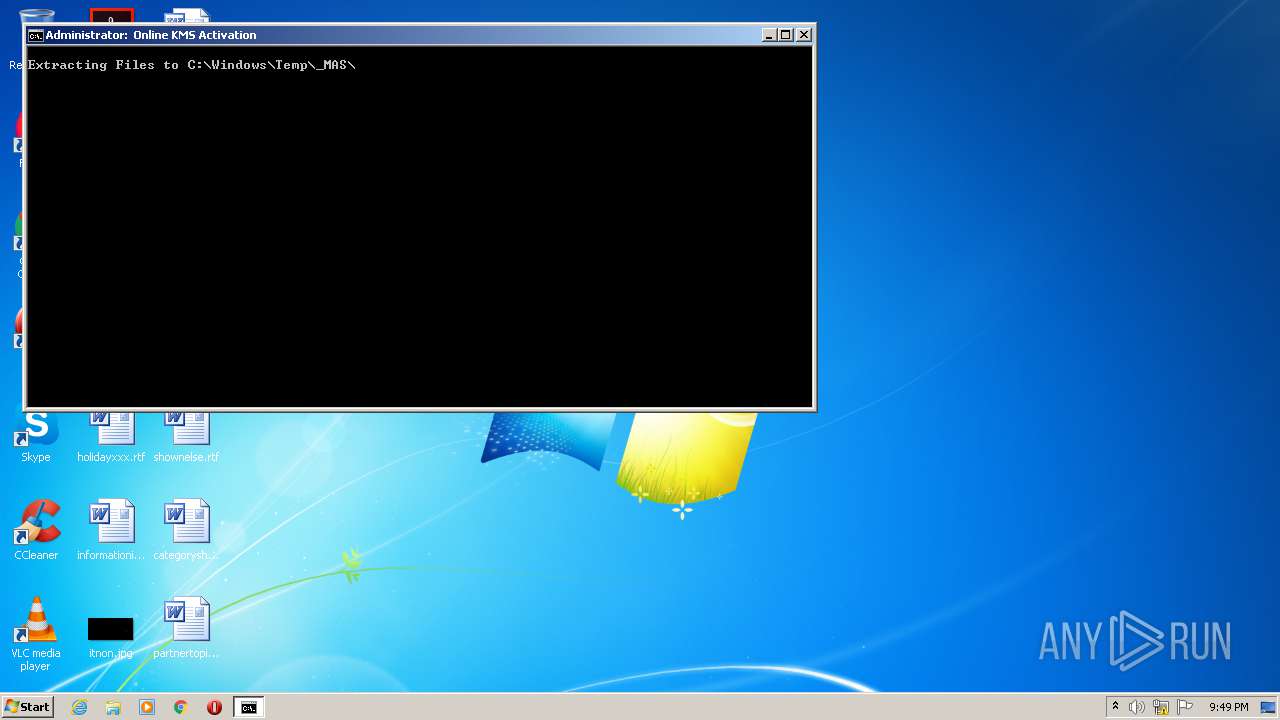
| 2868 | powershell.exe | C:\Windows\Temp\_MAS\1._ | — | |
MD5:— | SHA256:— | |||
| 3076 | expand.exe | C:\Windows\Temp\_MAS\$dpx$.tmp\9dce9678579fbf4b85c0ef1610ac9013.tmp | — | |
MD5:— | SHA256:— | |||
| 3076 | expand.exe | C:\Windows\Temp\_MAS\$dpx$.tmp\4bd28cc0d21fe745ba4032ae3f1ad0d7.tmp | — | |
MD5:— | SHA256:— | |||
| 3076 | expand.exe | C:\Windows\Temp\_MAS\$dpx$.tmp\c640a8a4a6fafb4390e2e94e712e4fc0.tmp | — | |
MD5:— | SHA256:— | |||
| 3076 | expand.exe | C:\Windows\Logs\DPX\setuperr.log | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|