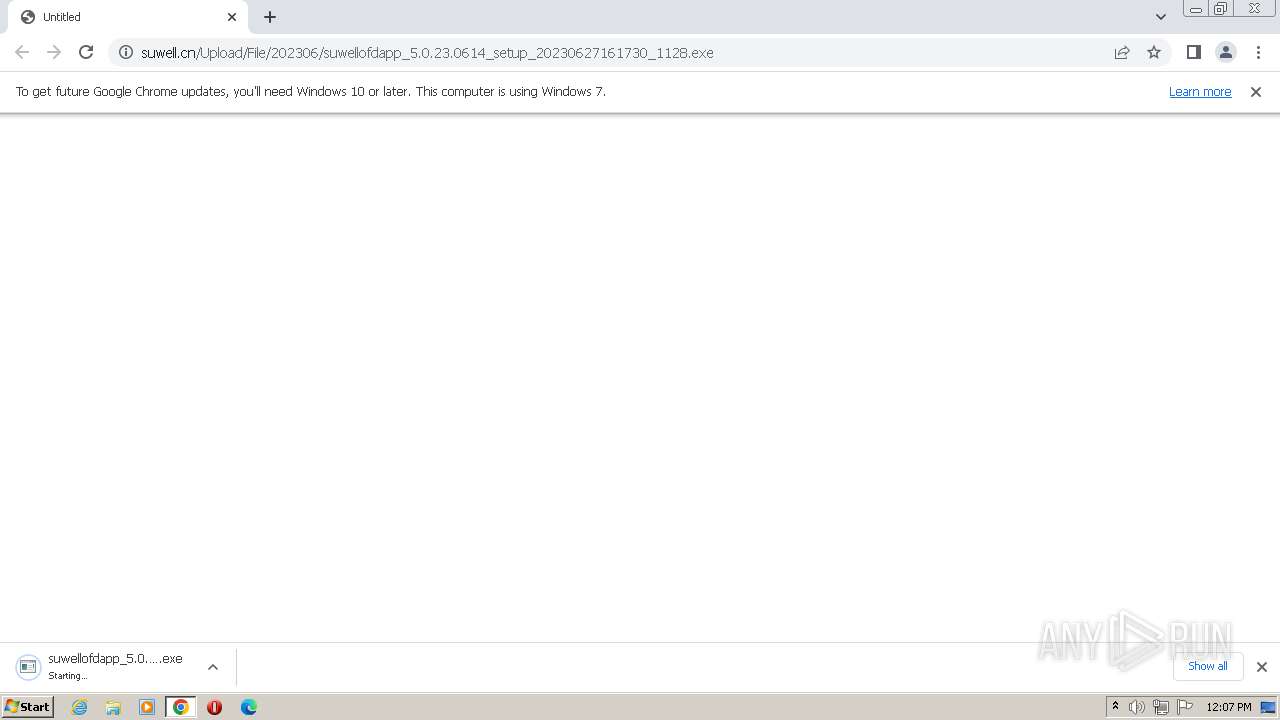
| URL: | https://www.suwell.cn/Upload/File/202306/suwellofdapp_5.0.23.0614_setup_20230627161730_1128.exe |
| Full analysis: | https://app.any.run/tasks/b536fb09-b214-42da-a247-c32215b2310e |
| Verdict: | Malicious activity |
| Analysis date: | August 01, 2023, 11:07:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 472D527C0A1BFF8197C76F52D83E094F |
| SHA1: | 140C713AB40BFEBC36AF28A268413A5FAADFC133 |
| SHA256: | A608EB8D2B3044CA13C9691068C650769C607DC1754B5C1F03678DF0493594D2 |
| SSDEEP: | 3:N8DSLjngEoK8UBMqBE/PhXWlWpQX9WcqWV6NNLACn:2OLrgjr6E5XUWo0cqWVcNJn |
MALICIOUS
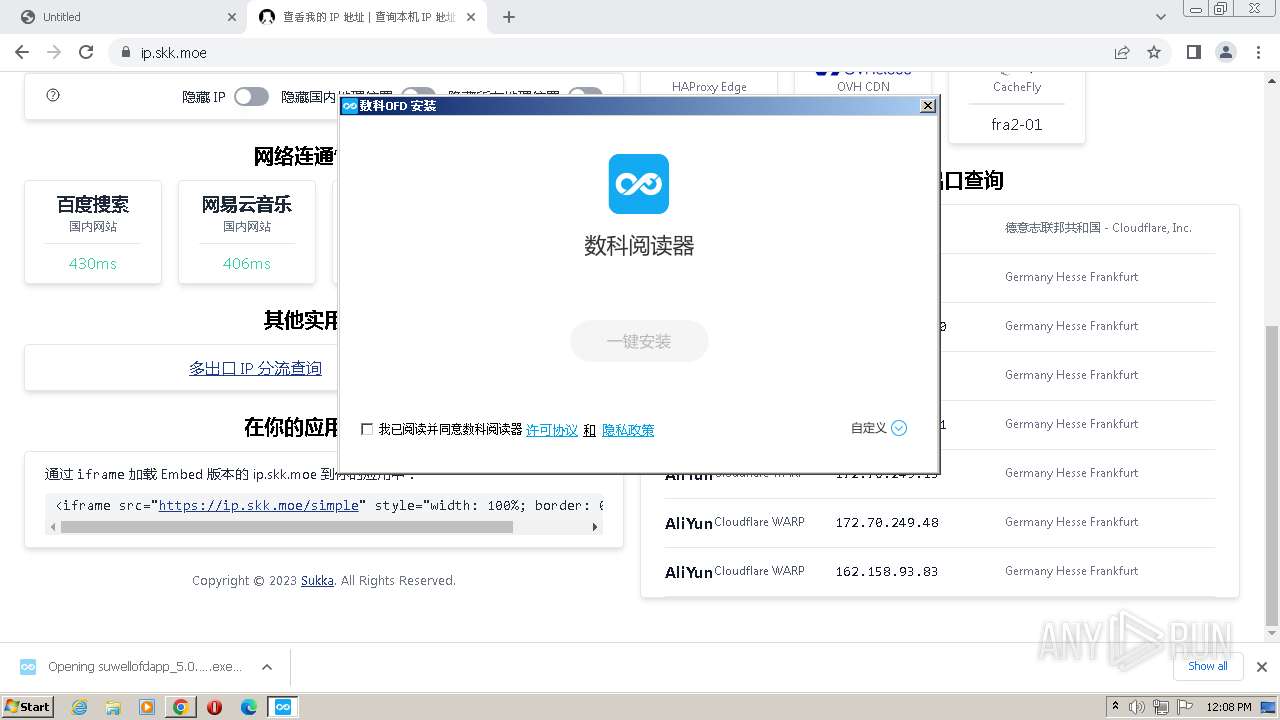
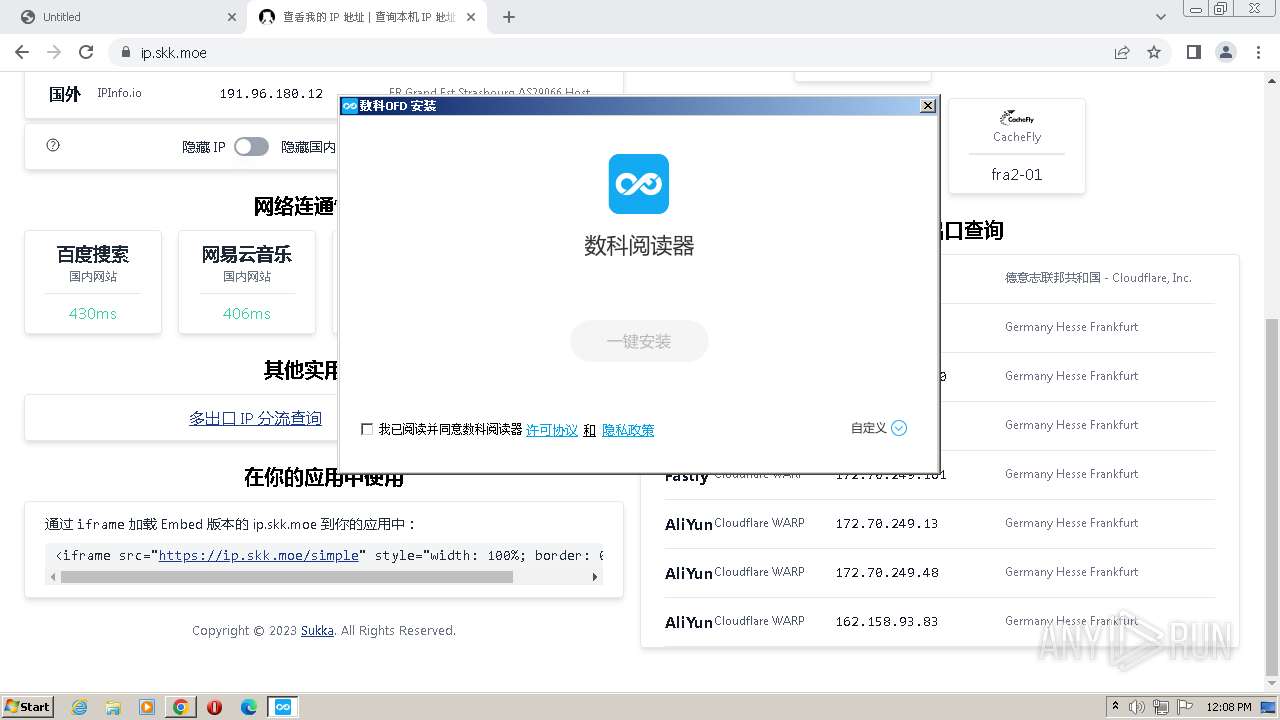
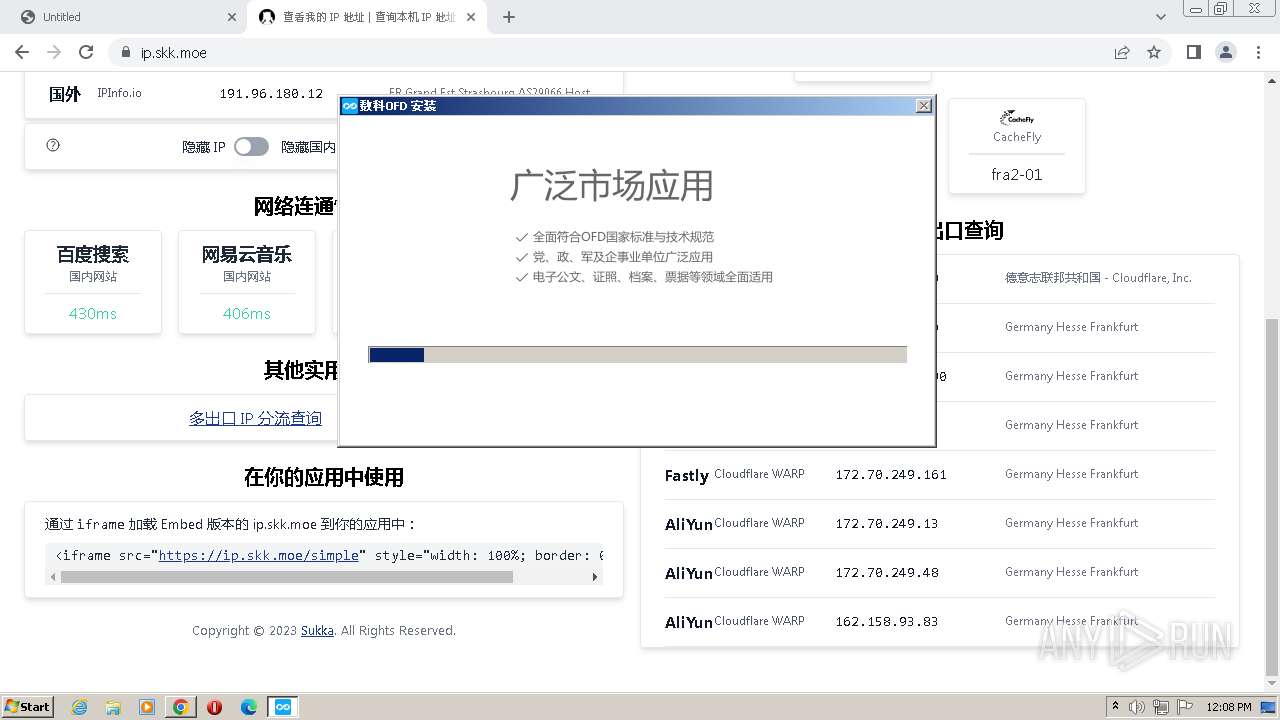
Application was dropped or rewritten from another process
- suwellofdapp_5.0.23.0614_setup_20230627161730_1128.exe (PID: 3304)
- suwellofdapp.exe (PID: 1680)
- SwOESServer.exe (PID: 1132)
- suwellofdapp_5.0.23.0614_setup_20230627161730_1128.exe (PID: 3116)
- AppUpdate.exe (PID: 680)
Loads dropped or rewritten executable
- SwOESServer.exe (PID: 1132)
- suwellofdapp.exe (PID: 1680)
- AppUpdate.exe (PID: 680)
SUSPICIOUS
The process creates files with name similar to system file names
- suwellofdapp_5.0.23.0614_setup_20230627161730_1128.exe (PID: 3304)
Uses TASKKILL.EXE to kill process
- suwellofdapp_5.0.23.0614_setup_20230627161730_1128.exe (PID: 3304)
Executable content was dropped or overwritten
- suwellofdapp_5.0.23.0614_setup_20230627161730_1128.exe (PID: 3304)
Reads the Internet Settings
- suwellofdapp_5.0.23.0614_setup_20230627161730_1128.exe (PID: 3304)
- suwellofdapp.exe (PID: 1680)
INFO
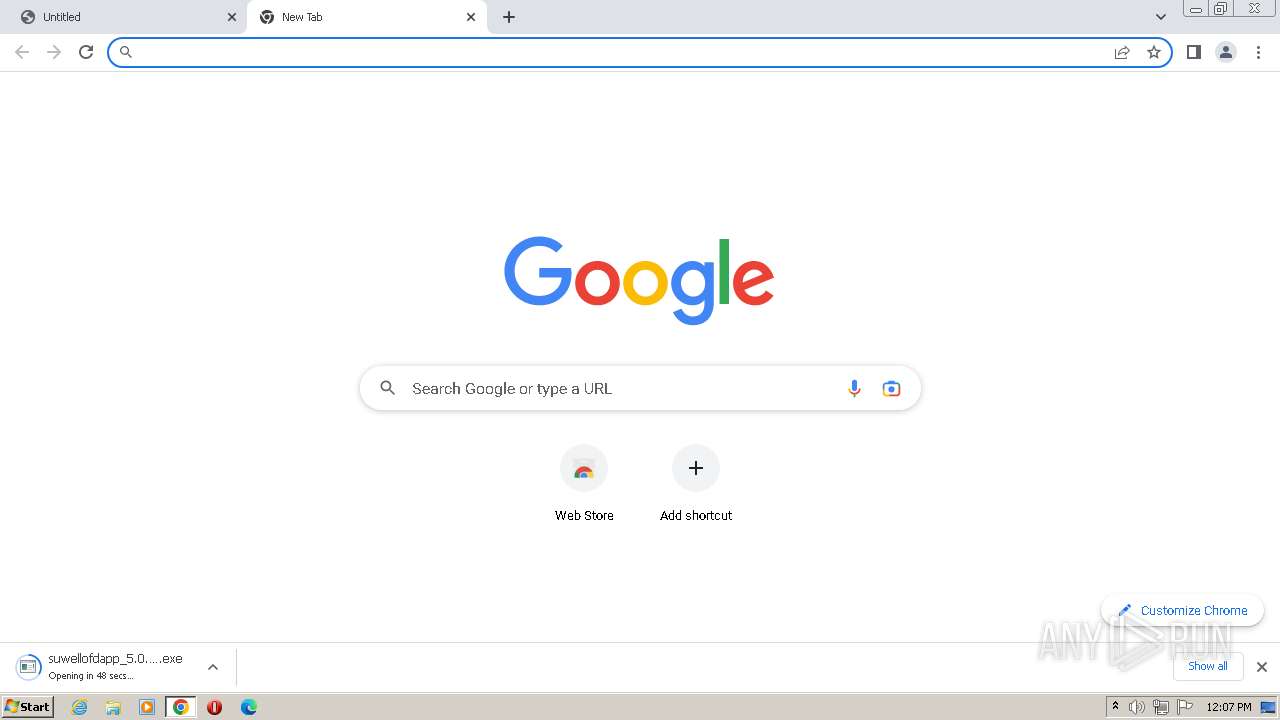
Application launched itself
- chrome.exe (PID: 1896)
The process uses the downloaded file
- chrome.exe (PID: 1896)
- chrome.exe (PID: 980)
- chrome.exe (PID: 3360)
- chrome.exe (PID: 4048)
Checks supported languages
- suwellofdapp_5.0.23.0614_setup_20230627161730_1128.exe (PID: 3304)
- suwellofdapp.exe (PID: 1680)
- SwOESServer.exe (PID: 1132)
- AppUpdate.exe (PID: 680)
Reads the computer name
- suwellofdapp_5.0.23.0614_setup_20230627161730_1128.exe (PID: 3304)
- suwellofdapp.exe (PID: 1680)
- AppUpdate.exe (PID: 680)
Create files in a temporary directory
- suwellofdapp_5.0.23.0614_setup_20230627161730_1128.exe (PID: 3304)
- suwellofdapp.exe (PID: 1680)
- SwOESServer.exe (PID: 1132)
- AppUpdate.exe (PID: 680)
The process checks LSA protection
- suwellofdapp_5.0.23.0614_setup_20230627161730_1128.exe (PID: 3304)
- taskkill.exe (PID: 2948)
- taskkill.exe (PID: 3588)
- taskkill.exe (PID: 1824)
- taskkill.exe (PID: 2256)
- taskkill.exe (PID: 3276)
- suwellofdapp.exe (PID: 1680)
- SwOESServer.exe (PID: 1132)
- AppUpdate.exe (PID: 680)
Loads dropped or rewritten executable
- suwellofdapp_5.0.23.0614_setup_20230627161730_1128.exe (PID: 3304)
Creates files in the program directory
- suwellofdapp_5.0.23.0614_setup_20230627161730_1128.exe (PID: 3304)
- suwellofdapp.exe (PID: 1680)
- SwOESServer.exe (PID: 1132)
Creates files or folders in the user directory
- suwellofdapp_5.0.23.0614_setup_20230627161730_1128.exe (PID: 3304)
- suwellofdapp.exe (PID: 1680)
Reads the machine GUID from the registry
- suwellofdapp.exe (PID: 1680)
- AppUpdate.exe (PID: 680)
Executable content was dropped or overwritten
- chrome.exe (PID: 1896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
82
Monitored processes
38
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1824 --field-trial-handle=1172,i,10844968357983232830,15715405608337681520,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=4152 --field-trial-handle=1172,i,10844968357983232830,15715405608337681520,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 680 | "C:\Program Files\Suwell\suwellofdapp\suwellofdapp_pro\AppUpdate.exe" | C:\Program Files\Suwell\suwellofdapp\suwellofdapp_pro\AppUpdate.exe | suwellofdapp.exe | ||||||||||||
User: admin Company: Suwell Integrity Level: HIGH Description: SuwellOfdappAppUpdate.exe Exit code: 0 Version: 1.0.20.0525 Modules
| |||||||||||||||
| 948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=1984 --field-trial-handle=1172,i,10844968357983232830,15715405608337681520,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3532 --field-trial-handle=1172,i,10844968357983232830,15715405608337681520,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1132 | "C:/Program Files/Suwell/suwellofdapp/suwellofdapp_pro/SwOESServer.exe" -Port=9001 -ScanOES=Enable C:\Users\admin\AppData\Local\Temp\suwell\suwellofdapp | C:\Program Files\Suwell\suwellofdapp\suwellofdapp_pro\SwOESServer.exe | — | suwellofdapp.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3792 --field-trial-handle=1172,i,10844968357983232830,15715405608337681520,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1680 | "C:\Program Files\Suwell\suwellofdapp\suwellofdapp_pro\suwellofdapp.exe" | C:\Program Files\Suwell\suwellofdapp\suwellofdapp_pro\suwellofdapp.exe | suwellofdapp_5.0.23.0614_setup_20230627161730_1128.exe | ||||||||||||
User: admin Company: Beijing Suwell Integrity Level: HIGH Description: suwellofdapp Exit code: 0 Version: 5.0.22.0627 Modules
| |||||||||||||||
| 1816 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1356 --field-trial-handle=1172,i,10844968357983232830,15715405608337681520,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1824 | taskkill /f /t /im SwOESServer.exe | C:\Windows\System32\taskkill.exe | — | suwellofdapp_5.0.23.0614_setup_20230627161730_1128.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
9 433
Read events
9 270
Write events
162
Delete events
1
Modification events
| (PID) Process: | (1896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (1896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1896) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (1896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
168
Suspicious files
106
Text files
186
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF4669d1.TMP | — | |
MD5:— | SHA256:— | |||
| 1896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 1896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 1896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:513218482935B0D388C0A990D868387A | SHA256:8E39CBAAF4AACC3A01AFA74EA8C30FB24FE69A22B8B30728AFB1614FD68809D9 | |||
| 1896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:65635E713D5CFC914717D1CC4CAC6989 | SHA256:4CB3EEB0369758290ABD7868DFD85D663C4AEF6C727FFF43BE693FDDBD0A6C28 | |||
| 1896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RF4672ba.TMP | — | |
MD5:— | SHA256:— | |||
| 1896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF4669d1.TMP | text | |
MD5:D5C9ECBD2DCA29D89266782824D7AF99 | SHA256:D22D1243ACC064A30823180D0E583C853E9395367C78C2AD9DE59A463904F702 | |||
| 1896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4c13b484-39a9-4bd1-bd75-f25abfd44c6c.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
85
DNS requests
112
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1816 | chrome.exe | GET | — | 104.18.21.226:80 | http://secure.globalsign.com/cacert/gsorganizationvalsha2g2r1.crt | US | — | — | whitelisted |
860 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/accn2h7r7qrqz4xqkrxfxappoyxq_404/lmelglejhemejginpboagddgdfbepgmp_404_all_ZZ_acqoo7fimcapp2l6txhzjzvmp5zq.crx3 | US | — | — | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/accn2h7r7qrqz4xqkrxfxappoyxq_404/lmelglejhemejginpboagddgdfbepgmp_404_all_ZZ_acqoo7fimcapp2l6txhzjzvmp5zq.crx3 | US | binary | 6.38 Kb | whitelisted |
860 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/cxpsjblnoxgjoqggdsbvujtof4_58/khaoiebndkojlmppeemjhbpbandiljpe_58_win_advr4ucepztwtigvw3fduftsvbeq.crx3 | US | binary | 940 b | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/bwz3vebv4a6glhoazexxdvgbfi_8149/hfnkpimlhhgieaddgfemjhofmfblmnib_8149_all_annfwlbl7g7xvzb23xslusnyhe.crx3 | US | binary | 16.8 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/bwz3vebv4a6glhoazexxdvgbfi_8149/hfnkpimlhhgieaddgfemjhofmfblmnib_8149_all_annfwlbl7g7xvzb23xslusnyhe.crx3 | US | binary | 8.89 Kb | whitelisted |
680 | AppUpdate.exe | GET | 200 | 47.95.198.10:80 | http://update.suwell.com/client/api/version/update?productName=suwellofdapp&version=5.0.23.0614&versionType=win | CN | binary | 159 b | unknown |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/accn2h7r7qrqz4xqkrxfxappoyxq_404/lmelglejhemejginpboagddgdfbepgmp_404_all_ZZ_acqoo7fimcapp2l6txhzjzvmp5zq.crx3 | US | binary | 940 b | whitelisted |
860 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/bwz3vebv4a6glhoazexxdvgbfi_8149/hfnkpimlhhgieaddgfemjhofmfblmnib_8149_all_annfwlbl7g7xvzb23xslusnyhe.crx3 | US | binary | 5.46 Kb | whitelisted |
860 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/cxpsjblnoxgjoqggdsbvujtof4_58/khaoiebndkojlmppeemjhbpbandiljpe_58_win_advr4ucepztwtigvw3fduftsvbeq.crx3 | US | binary | 5.46 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2640 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1896 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1816 | chrome.exe | 142.250.185.109:443 | accounts.google.com | GOOGLE | US | suspicious |
1816 | chrome.exe | 42.56.77.1:443 | www.suwell.cn | CHINA UNICOM China169 Backbone | CN | unknown |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1896 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
1816 | chrome.exe | 172.217.16.202:443 | optimizationguide-pa.googleapis.com | — | — | whitelisted |
1816 | chrome.exe | 221.195.206.1:443 | www.suwell.cn | CHINA UNICOM China169 Backbone | CN | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.suwell.cn |
| suspicious |
accounts.google.com |
| shared |
optimizationguide-pa.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
encrypted-tbn0.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
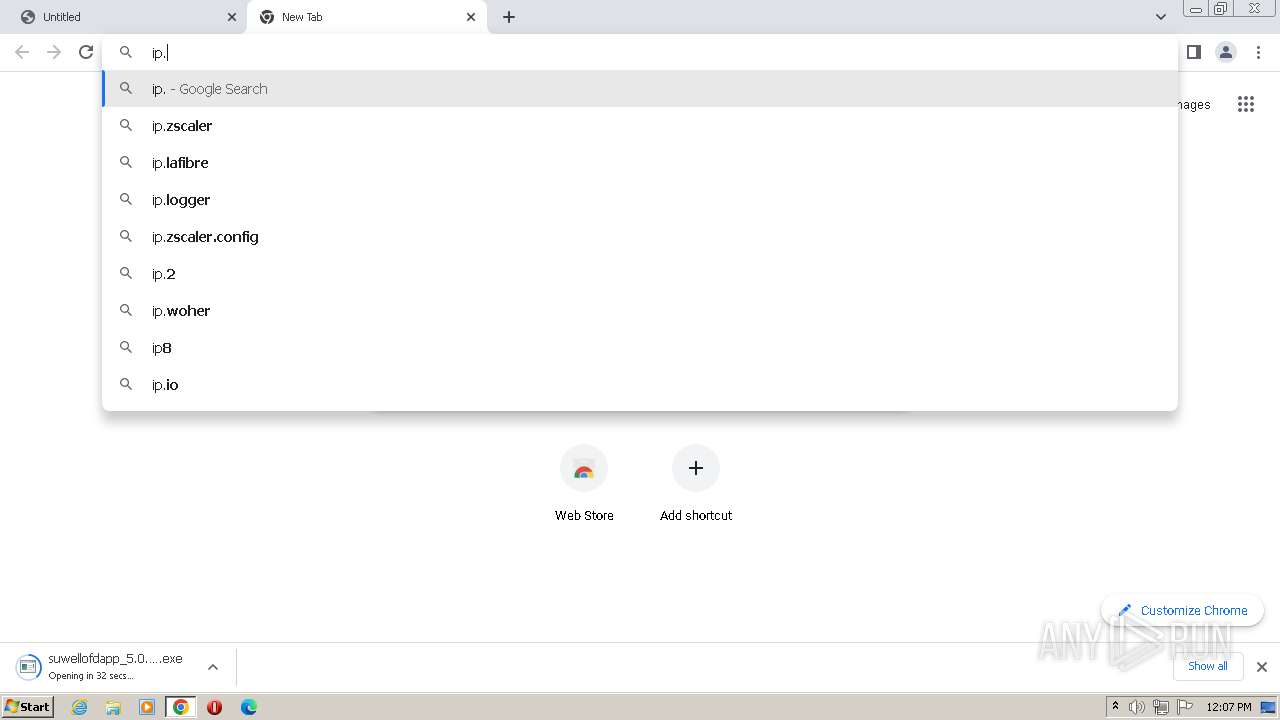
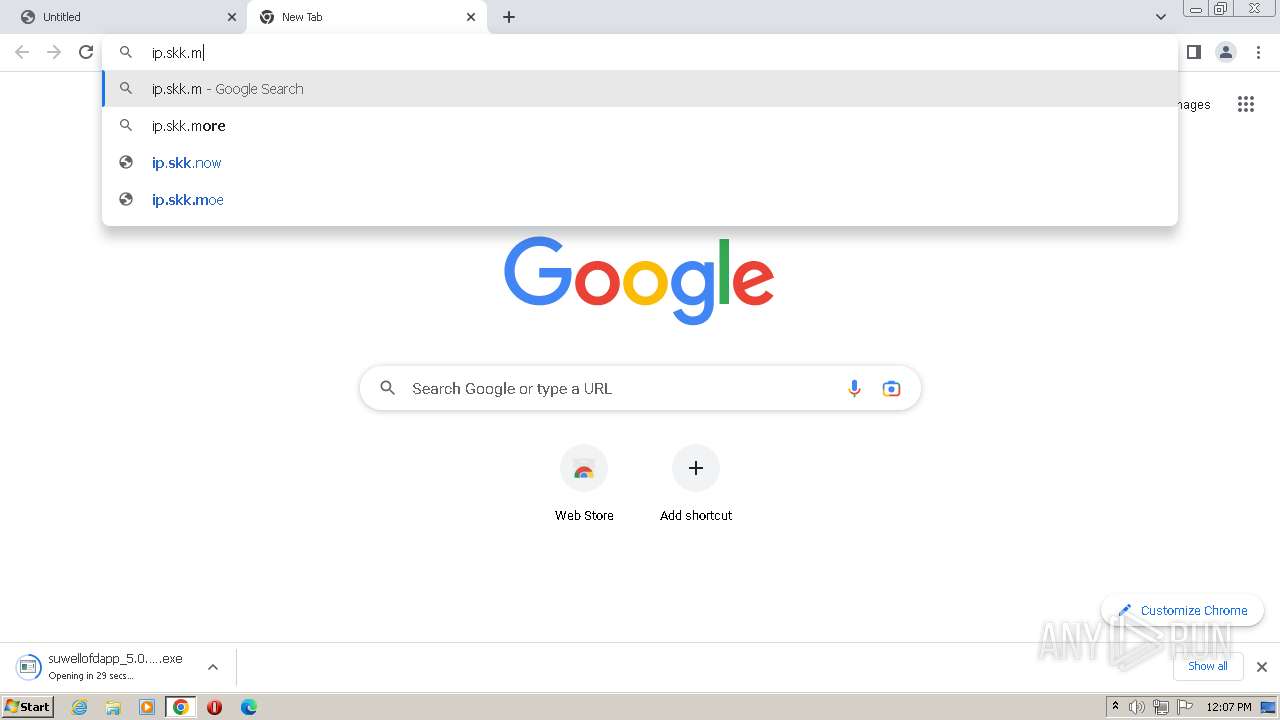
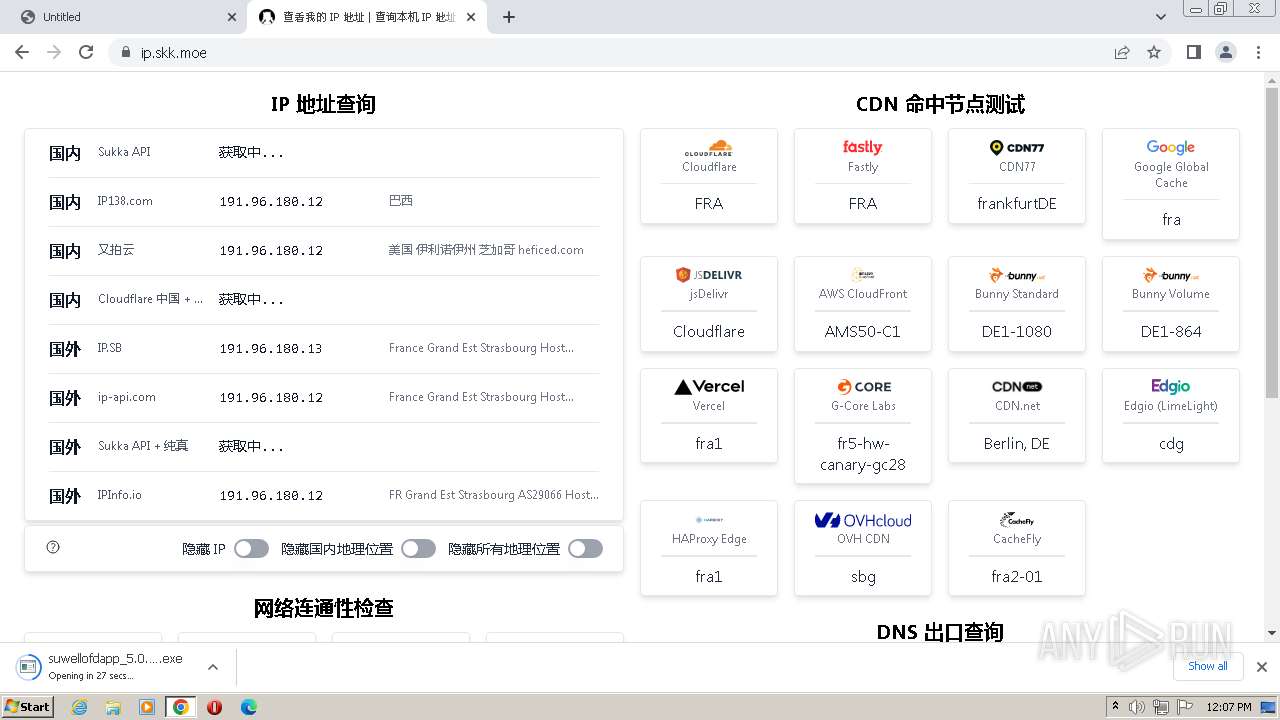
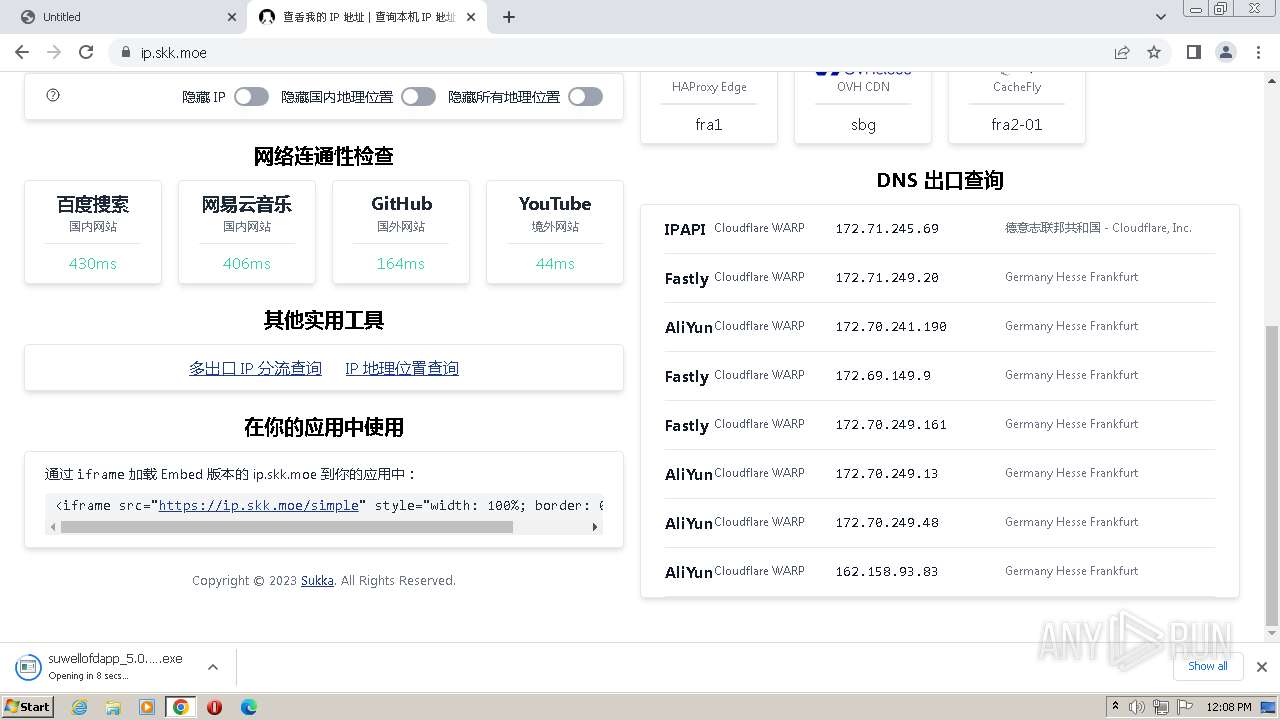
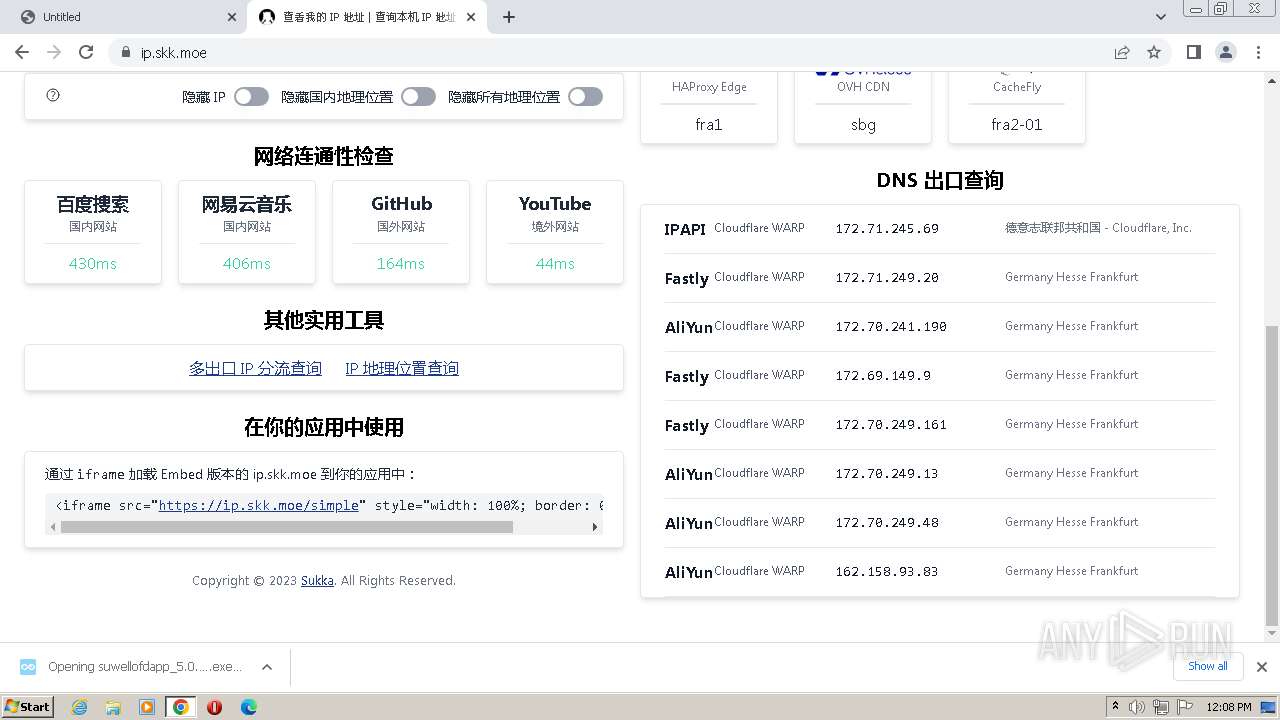
ip.skk.moe |
| unknown |
cdn.skk.moe |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1816 | chrome.exe | Device Retrieving External IP Address Detected | ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
8 ETPRO signatures available at the full report
Process | Message |
|---|---|
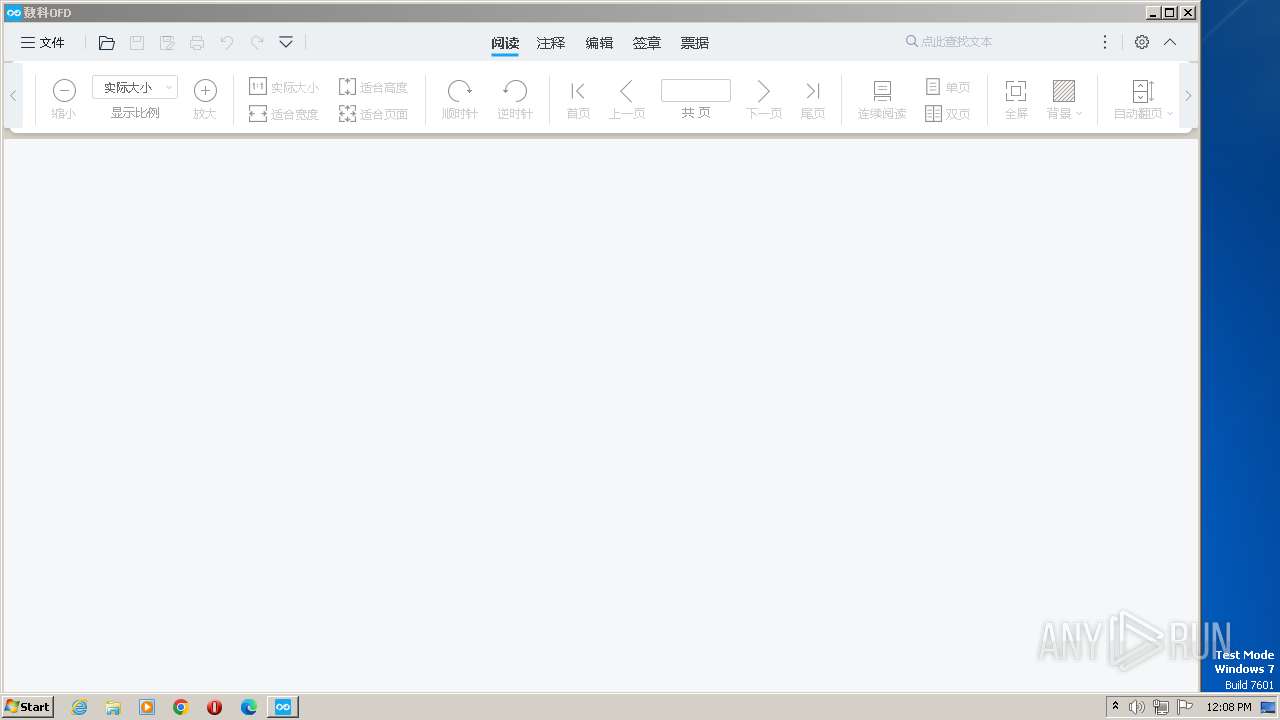
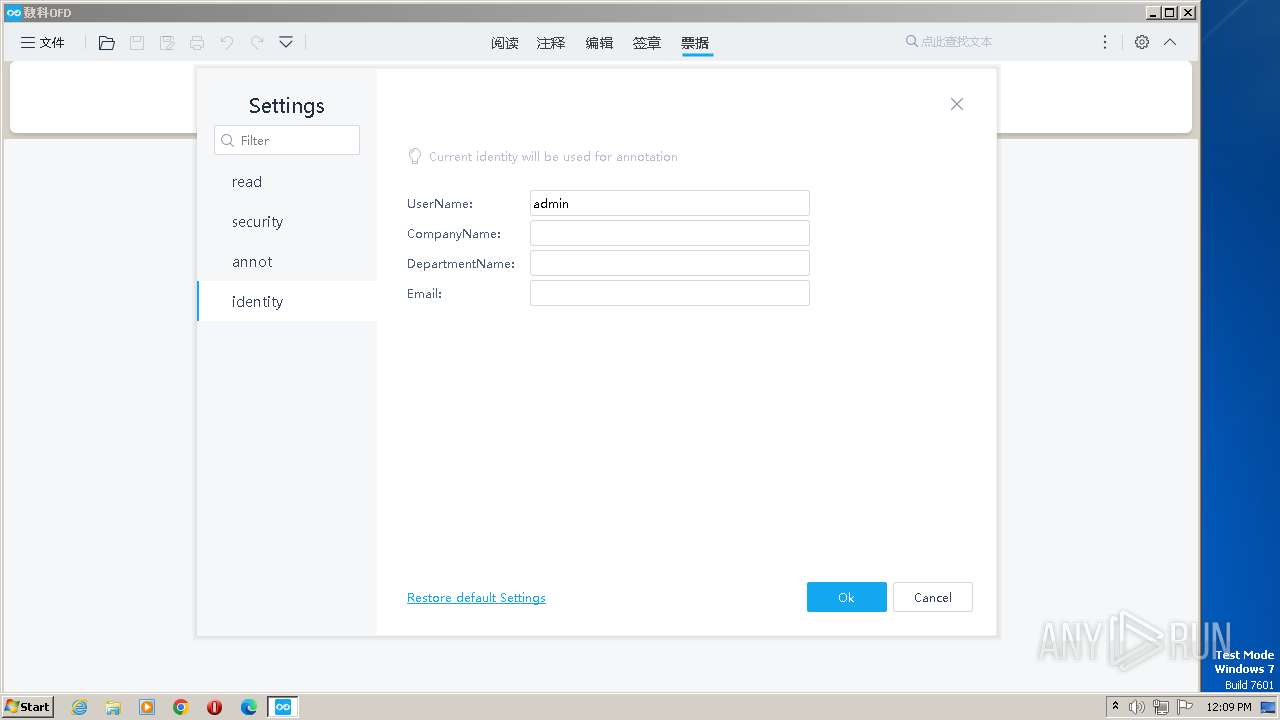
suwellofdapp.exe | load plugins: count 20
|
suwellofdapp.exe | CreateUserSettings "C:/Users/admin/AppData/Local/suwell/suwellofdapp/ofdpcapp.ini"
|
suwellofdapp.exe | InitTranslators "C:/Program Files/Suwell/suwellofdapp/suwellofdapp_pro/languages"
|
suwellofdapp.exe | InitTranslators "en_US"
|
suwellofdapp.exe | 0x1864ee0
|
suwellofdapp.exe | QLayout: Attempting to add QLayout "" to Core::Internal::SWMainWindow "", which already has a layout
|
suwellofdapp.exe | ------------------------------------222222------------------------------
|
suwellofdapp.exe | QLayout: Attempting to add QLayout "" to G_SearchDockView "SearchView", which already has a layout
|
suwellofdapp.exe | Core::Internal::SWMainWindow::resizeEvent
|
suwellofdapp.exe | Core::Internal::SWMainWindow::resizeEvent
|