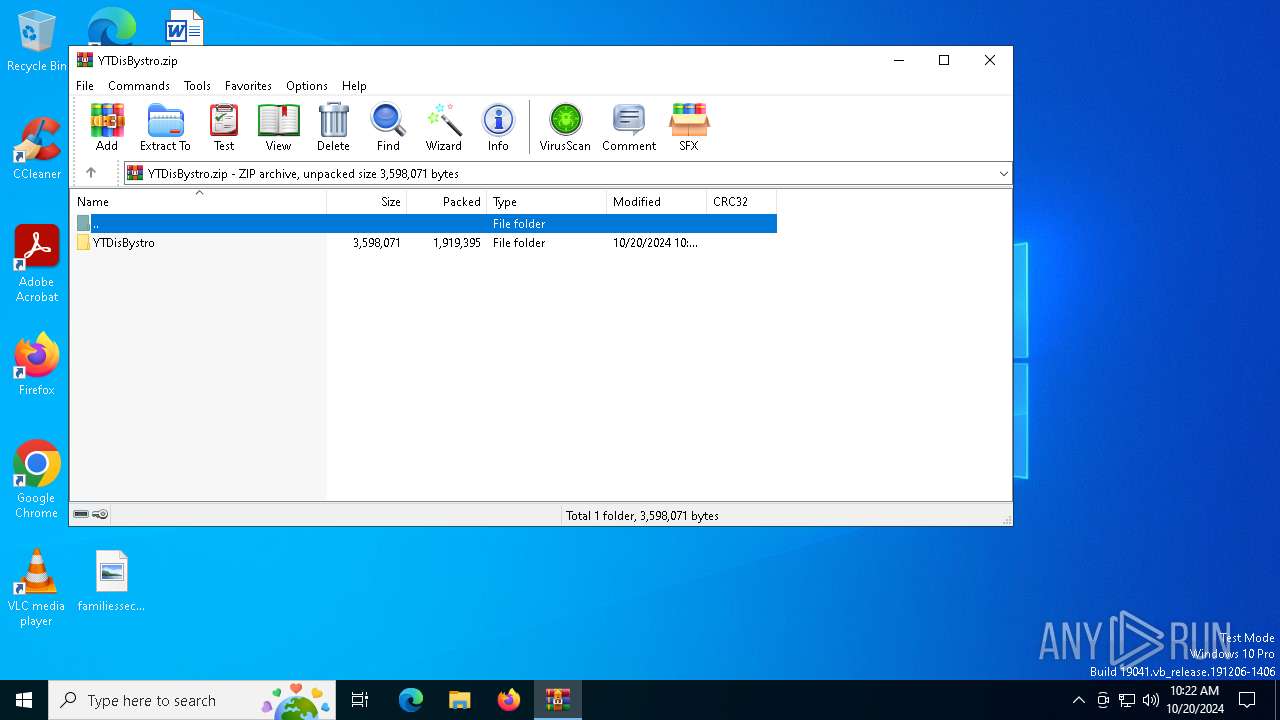
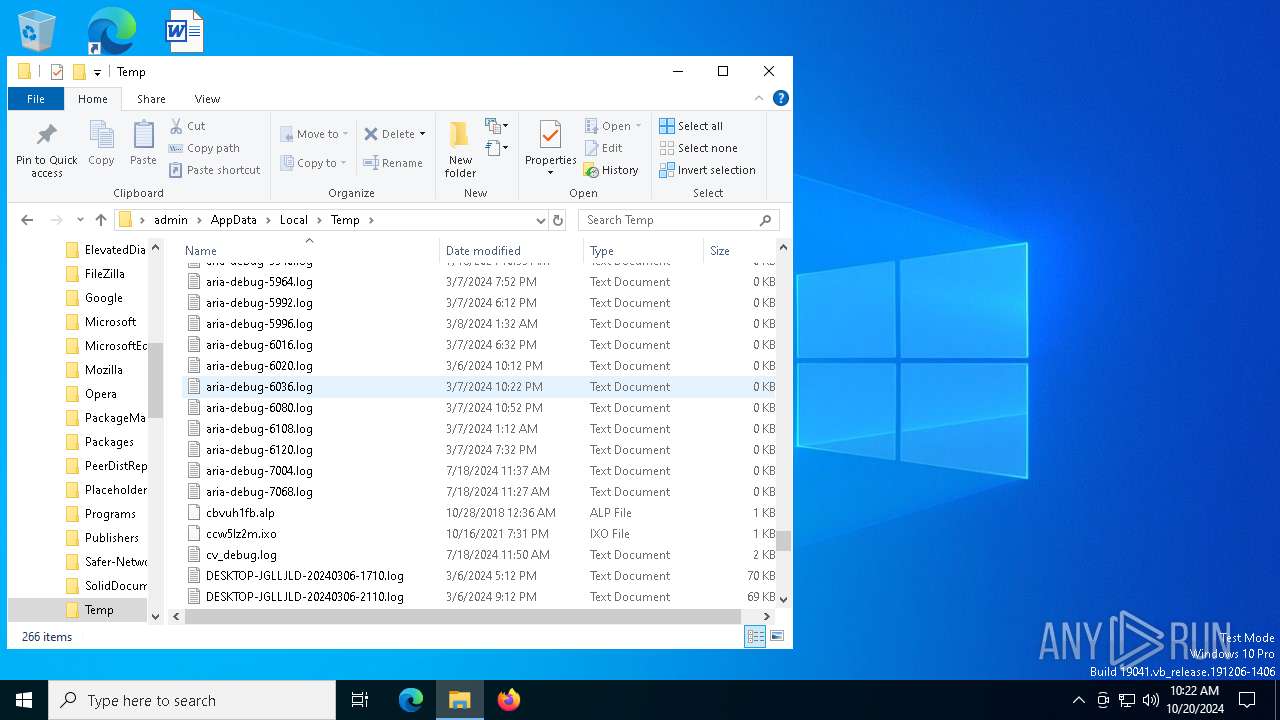
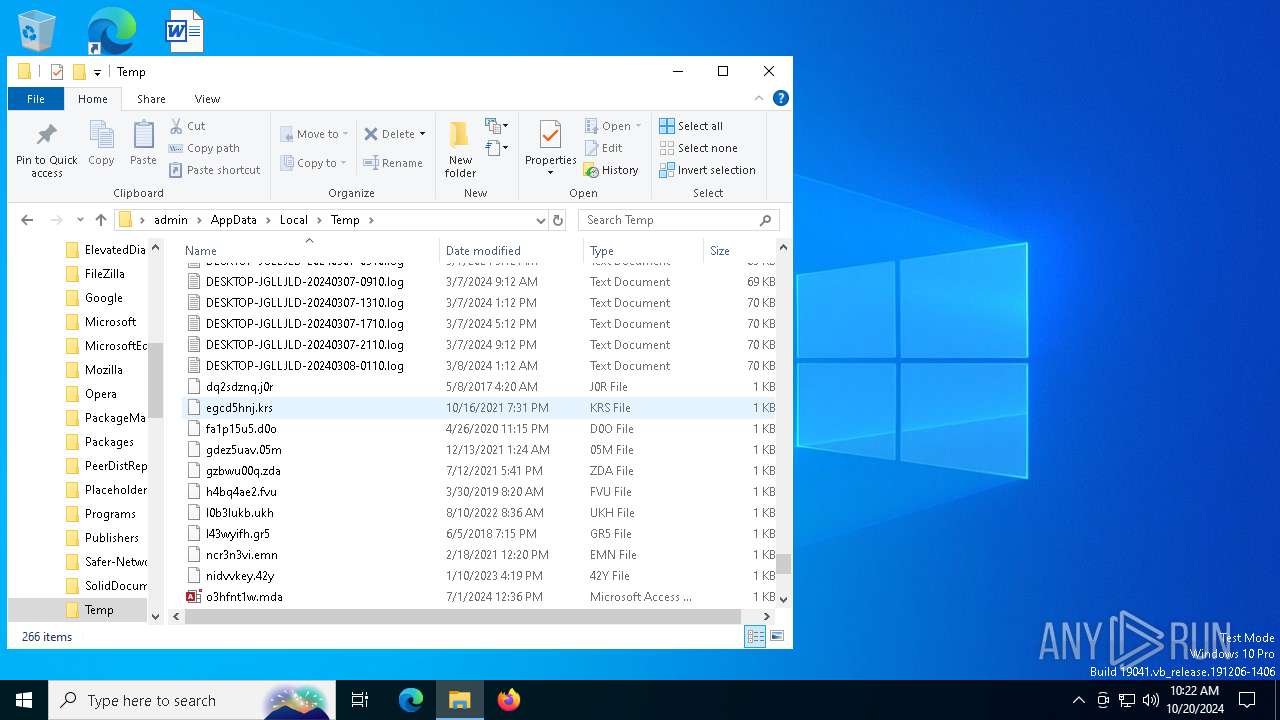
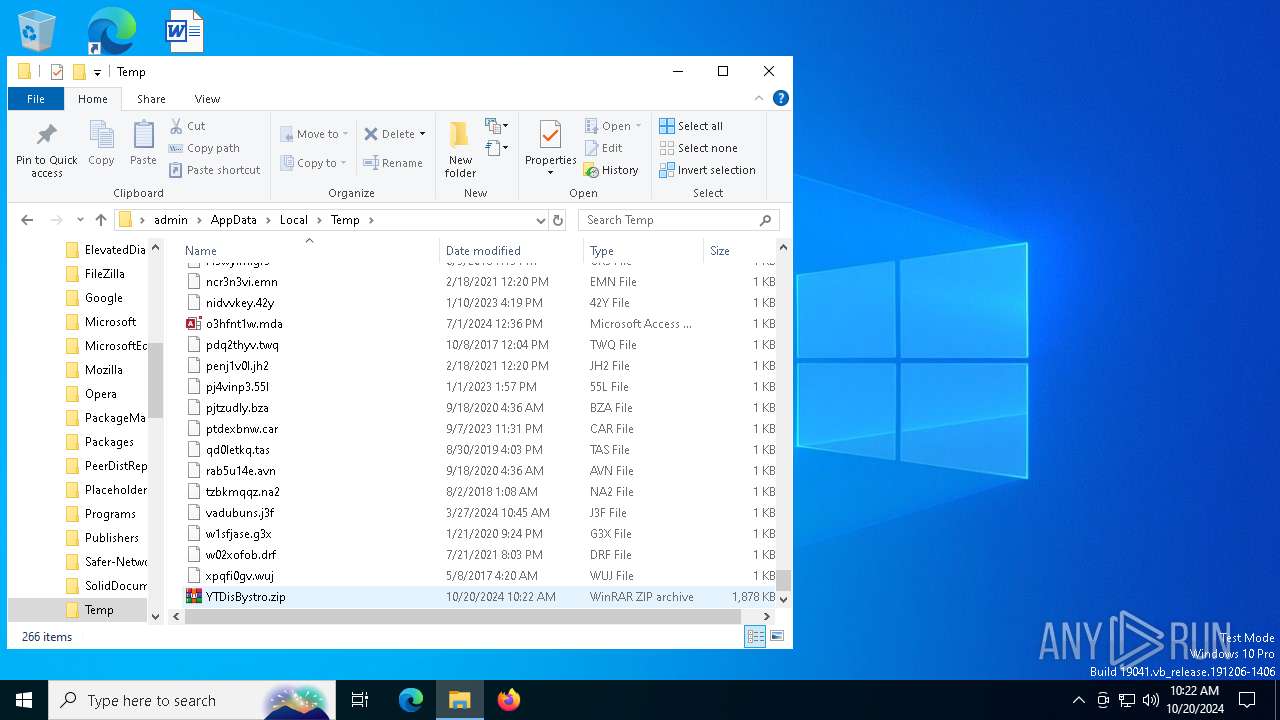
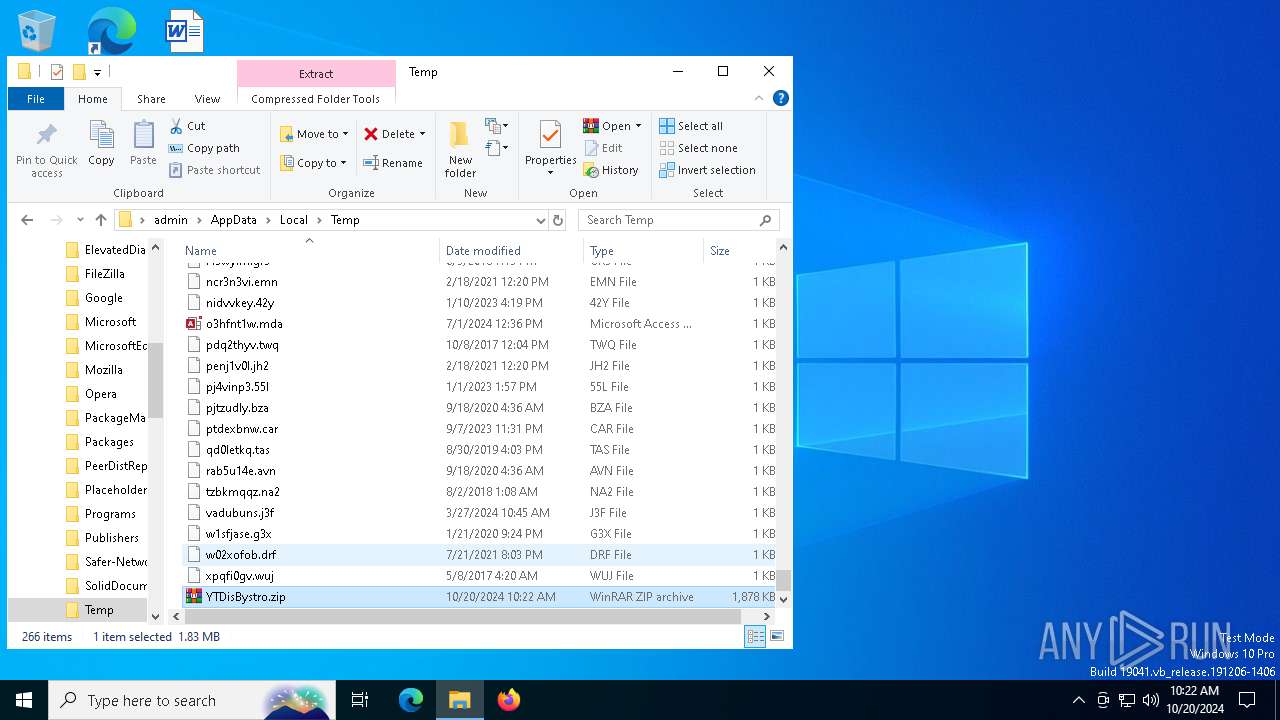
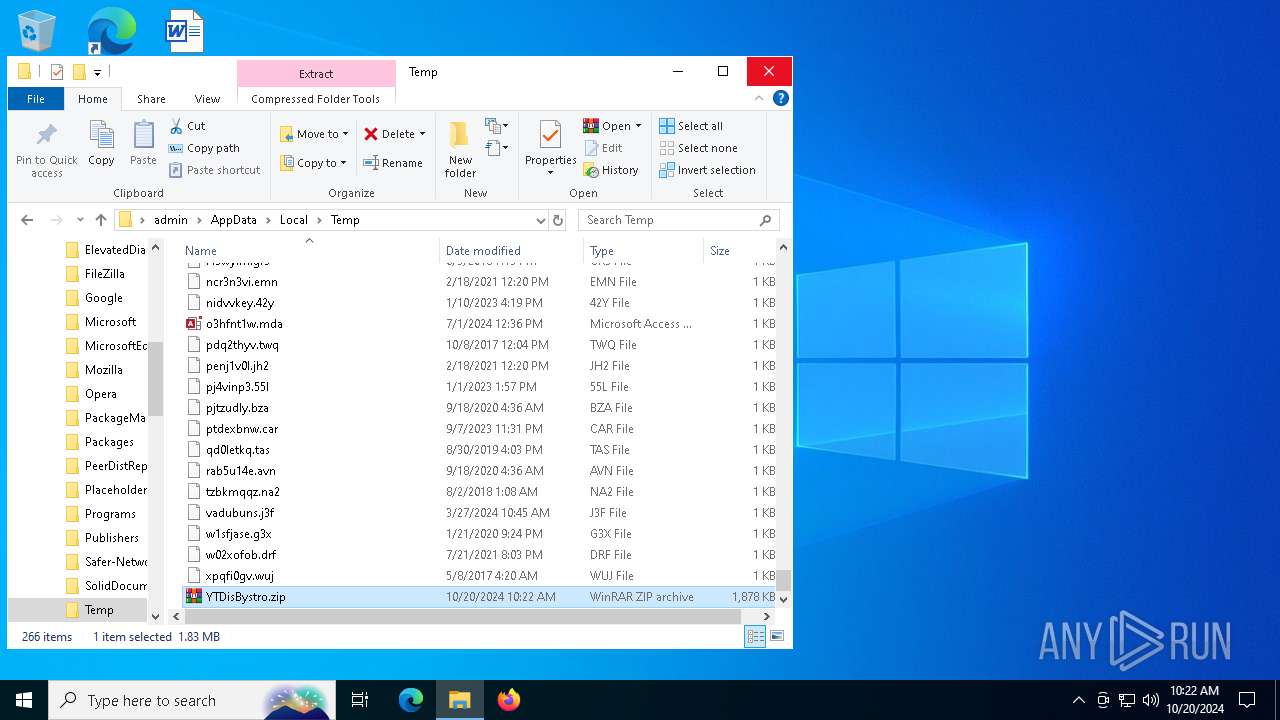
| File name: | YTDisBystro.zip |
| Full analysis: | https://app.any.run/tasks/a7a503e2-c430-4aff-ab86-f58b501b935d |
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2024, 10:22:17 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | AF087CB9A6A017A2E7540ABC7EB03D8A |
| SHA1: | CA42C5F7778C0F387B8CAAE283F7C869B8191E28 |
| SHA256: | A5F81202C37758946D2BF31F0E03A23724B18BC6964C061F1989DC3D993EF178 |
| SSDEEP: | 98304:7M8Y+USYiCJptvCJXD7EGAZUD4uxx8vHj+aBTzSJmBNAWf9G47AAgcMgVUjOC/3r:CKt |
MALICIOUS
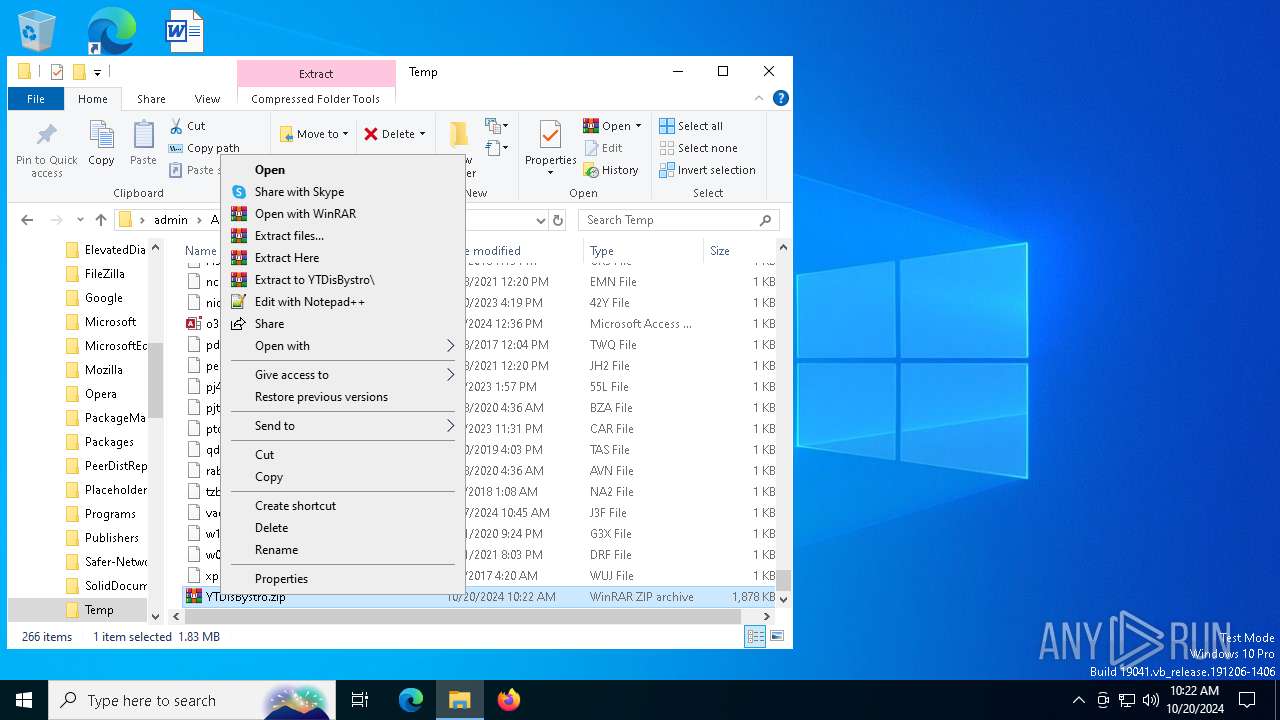
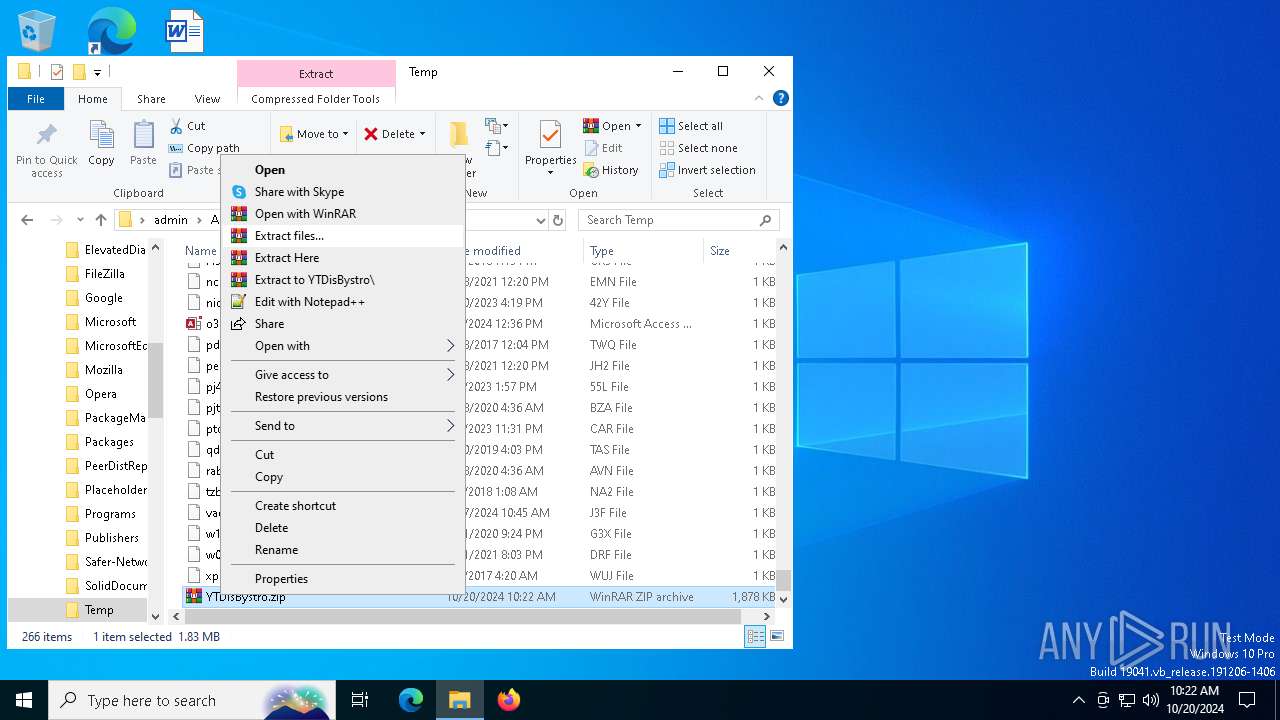
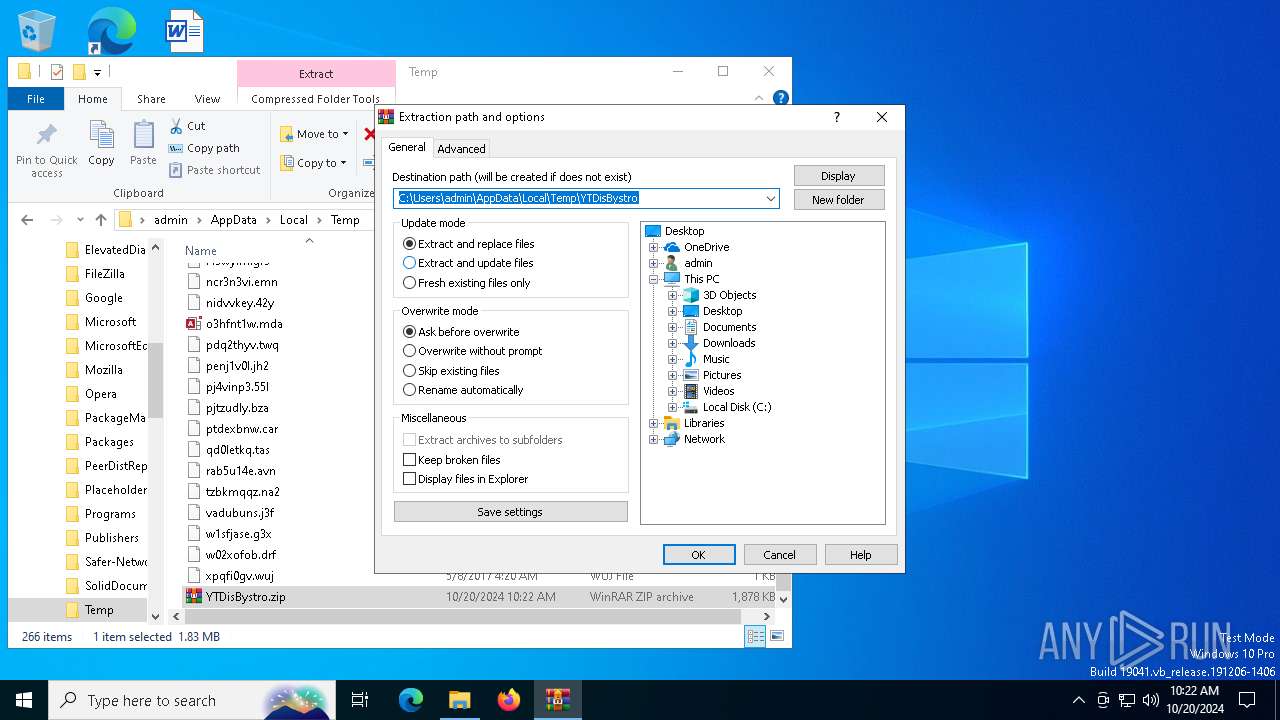
Generic archive extractor
- WinRAR.exe (PID: 1156)
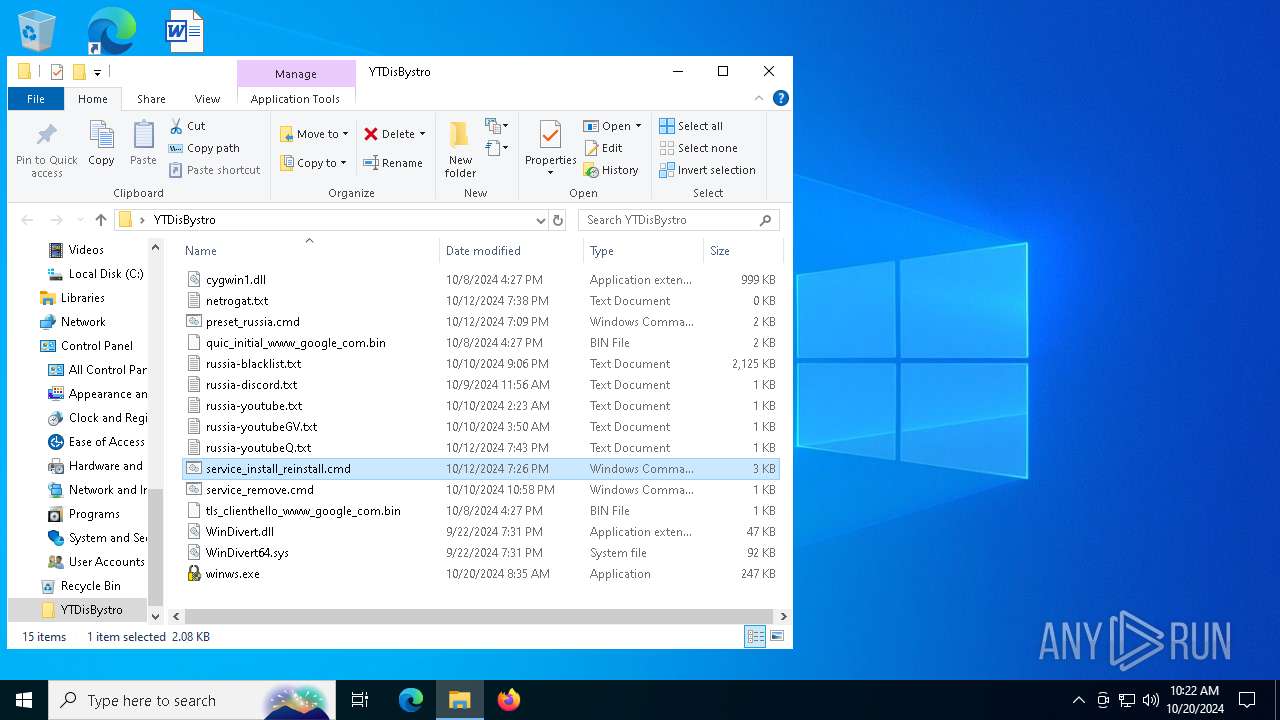
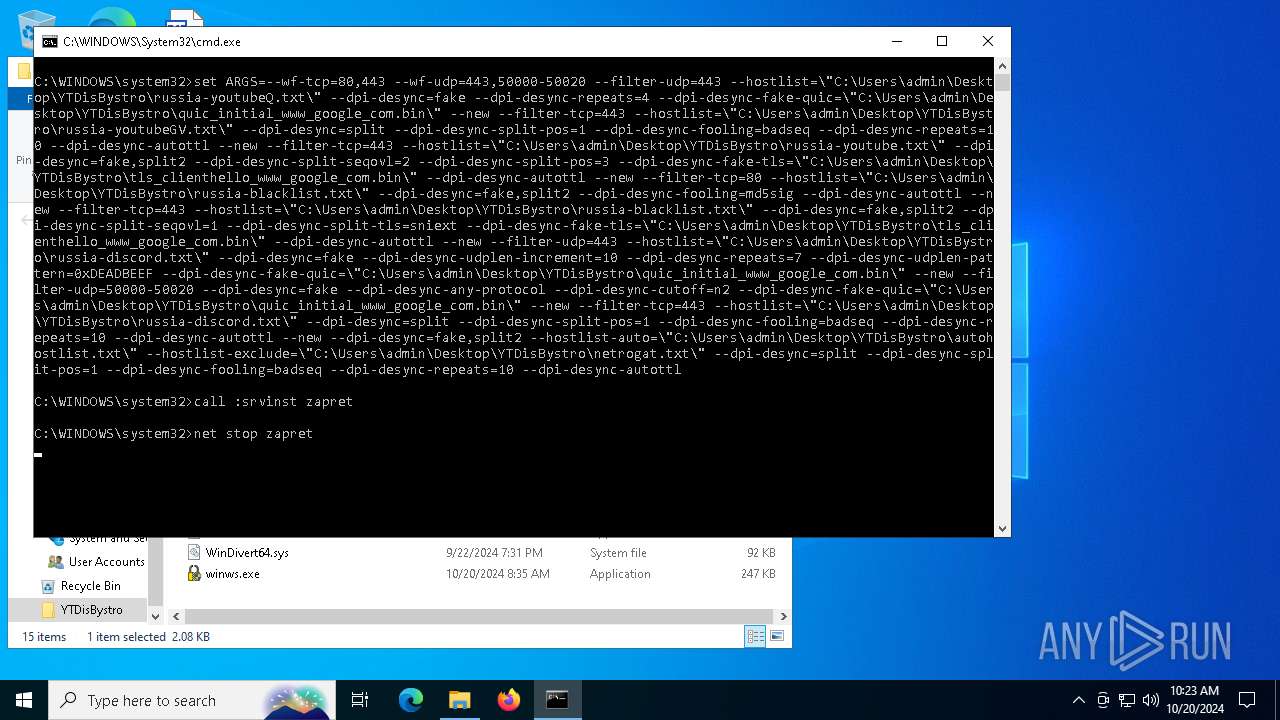
Starts NET.EXE for service management
- cmd.exe (PID: 2708)
- net.exe (PID: 1332)
SUSPICIOUS
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 6676)
Executes as Windows Service
- winws.exe (PID: 5580)
Starts SC.EXE for service management
- cmd.exe (PID: 2708)
INFO
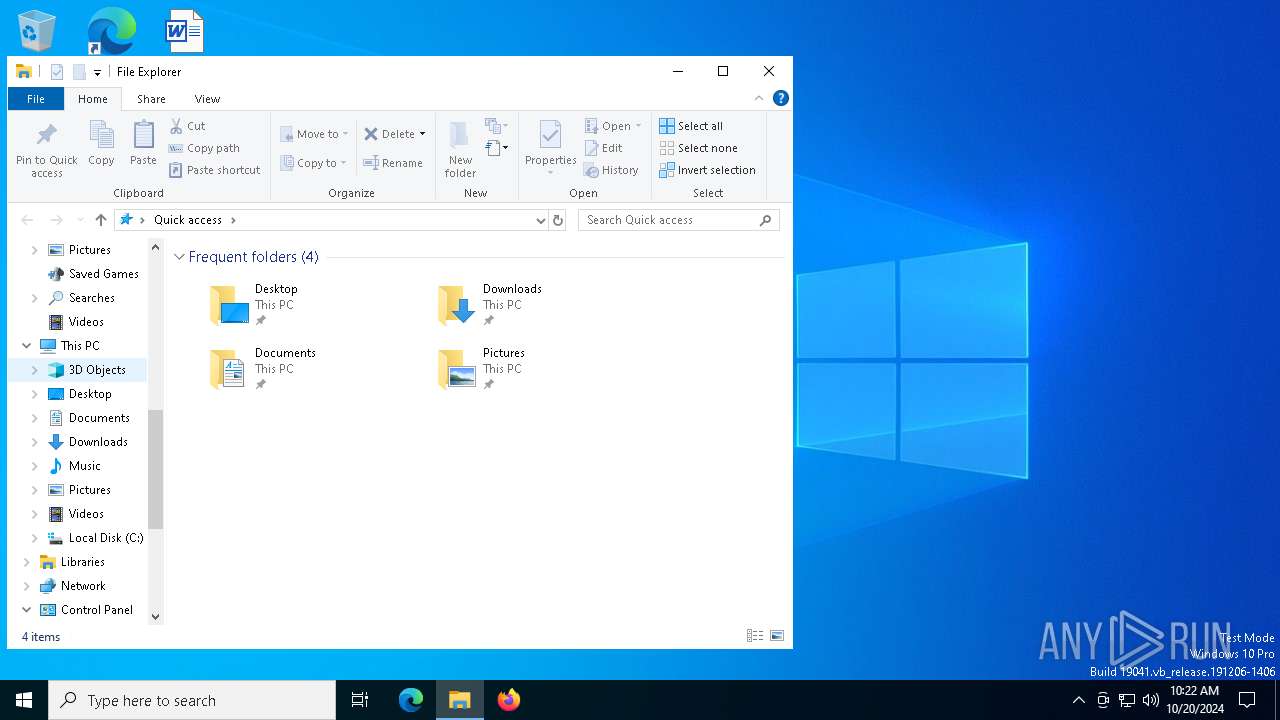
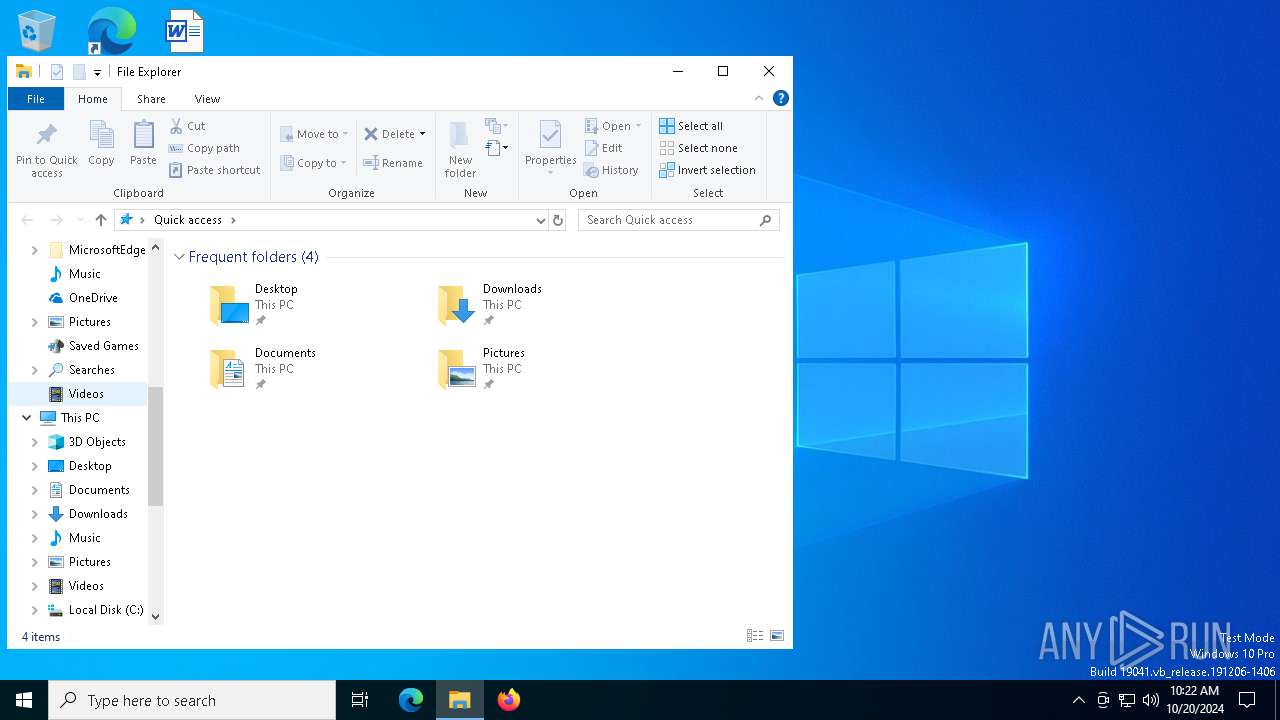
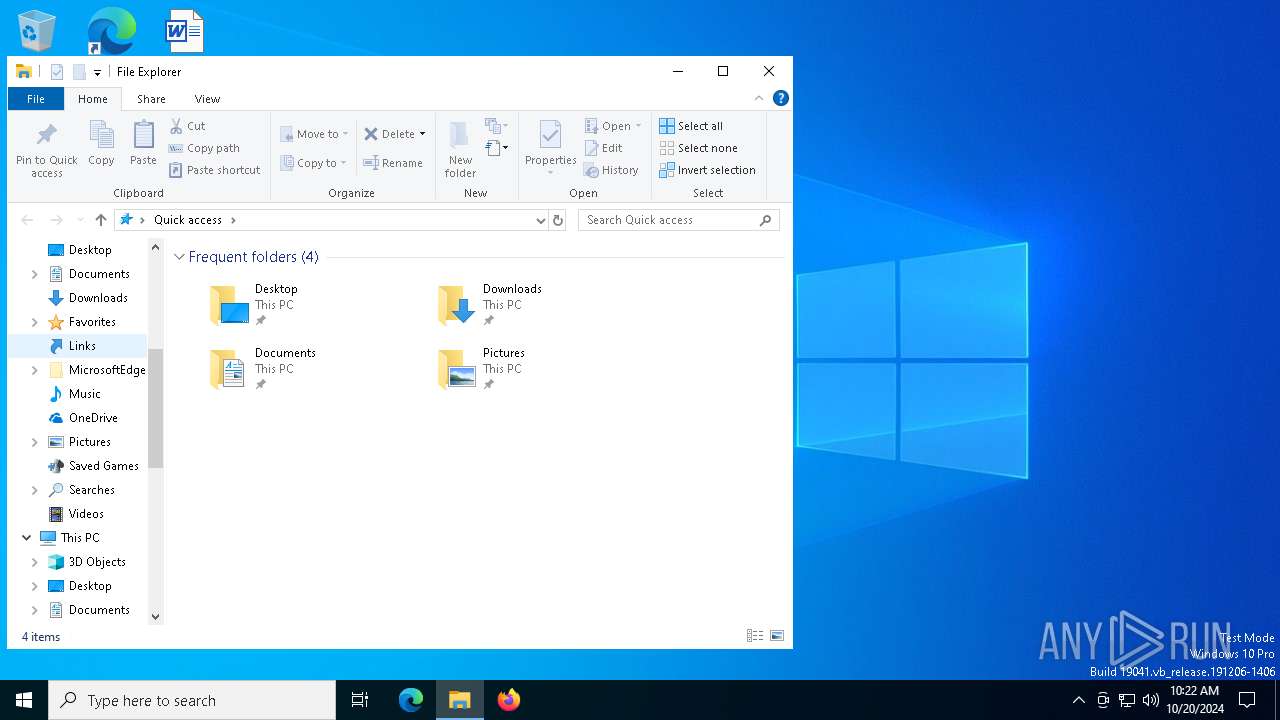
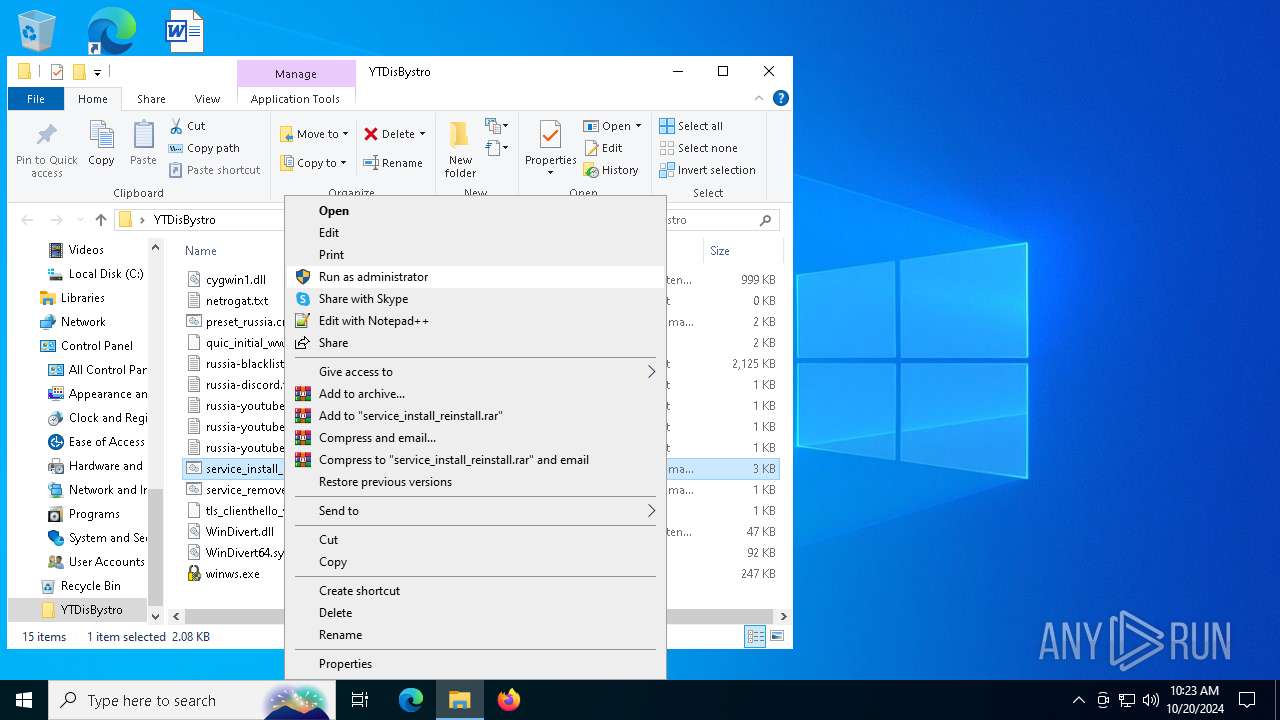
Manual execution by a user
- WinRAR.exe (PID: 6676)
- cmd.exe (PID: 2708)
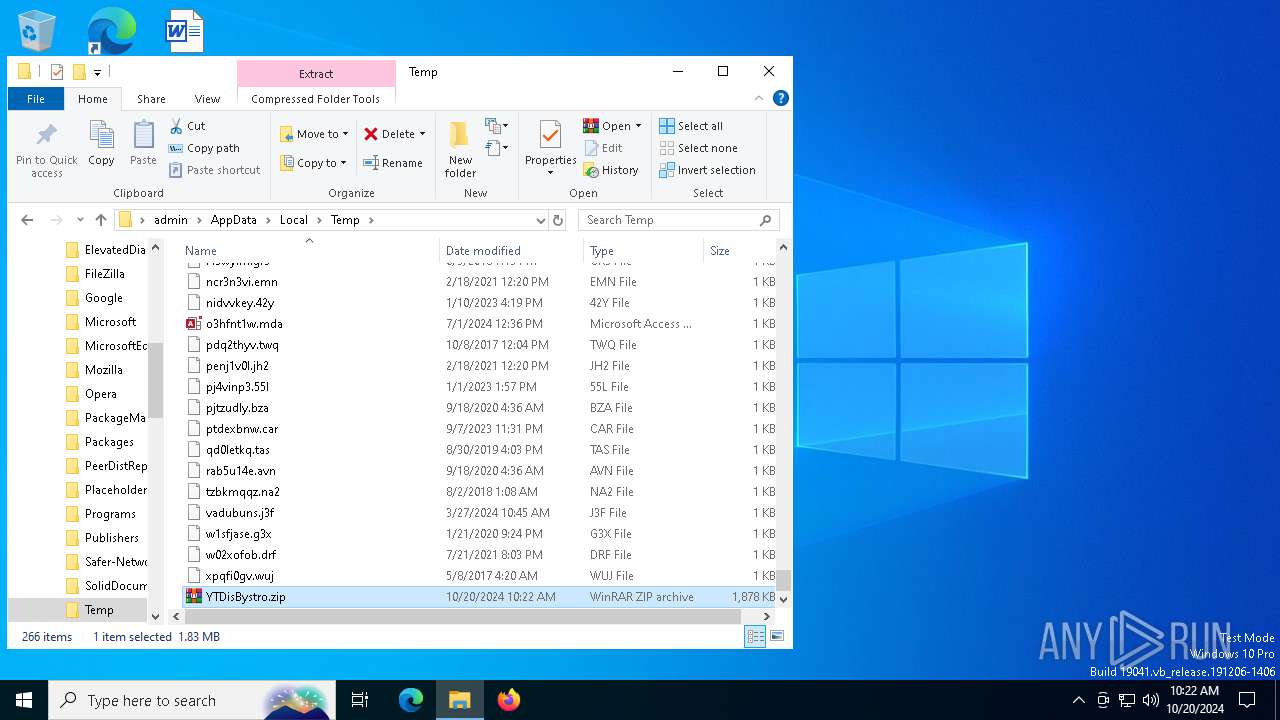
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6676)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xpi | | | Mozilla Firefox browser extension (66.6) |
|---|---|---|
| .zip | | | ZIP compressed archive (33.3) |
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:10:20 13:20:58 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | YTDisBystro/ |
Total processes
147
Monitored processes
14
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 632 | C:\WINDOWS\system32\net1 stop zapret | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
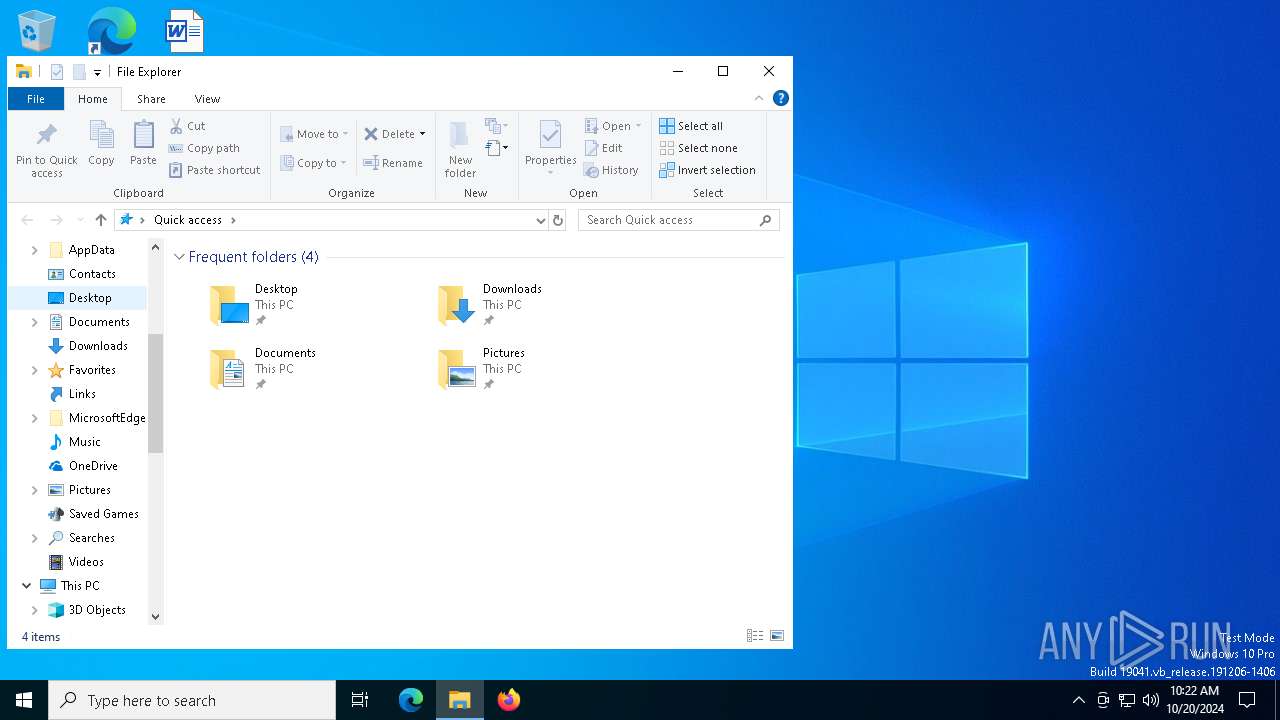
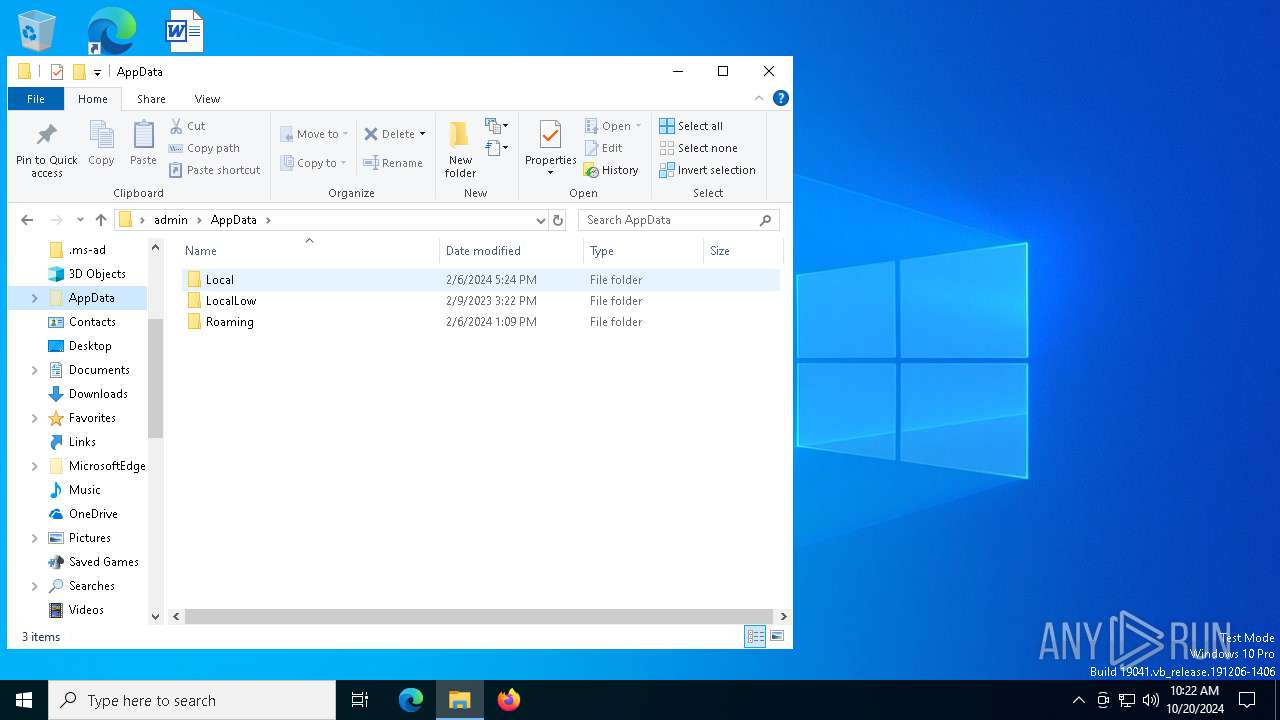
| 1156 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\YTDisBystro.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1332 | net stop zapret | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2708 | "C:\WINDOWS\System32\cmd.exe" /C "C:\Users\admin\Desktop\YTDisBystro\service_install_reinstall.cmd" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3860 | sc description zapret "Zapret DPI bypass software" | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5564 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
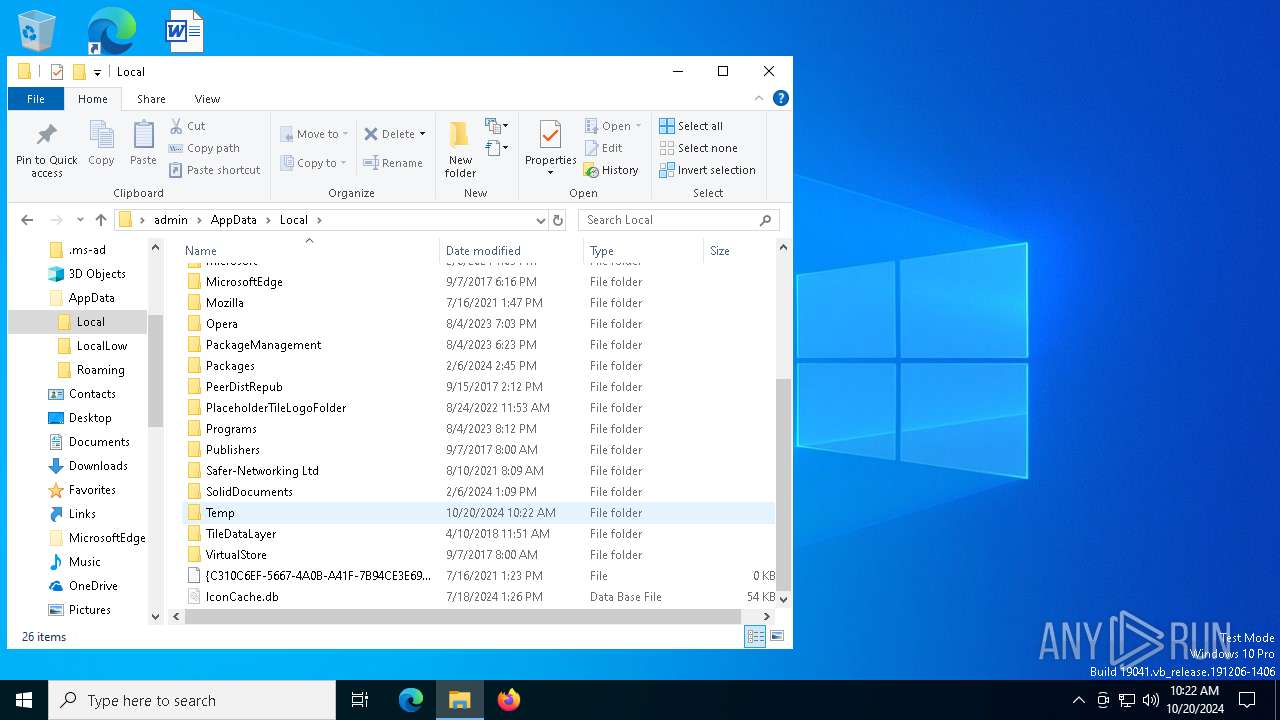
| 5580 | "C:\Users\admin\Desktop\YTDisBystro\winws.exe" --wf-tcp=80,443 --wf-udp=443,50000-50020 --filter-udp=443 --hostlist="C:\Users\admin\Desktop\YTDisBystro\russia-youtubeQ.txt" --dpi-desync=fake --dpi-desync-repeats=4 --dpi-desync-fake-quic="C:\Users\admin\Desktop\YTDisBystro\quic_initial_www_google_com.bin" --new --filter-tcp=443 --hostlist="C:\Users\admin\Desktop\YTDisBystro\russia-youtubeGV.txt" --dpi-desync=split --dpi-desync-split-pos=1 --dpi-desync-fooling=badseq --dpi-desync-repeats=10 --dpi-desync-autottl --new --filter-tcp=443 --hostlist="C:\Users\admin\Desktop\YTDisBystro\russia-youtube.txt" --dpi-desync=fake,split2 --dpi-desync-split-seqovl=2 --dpi-desync-split-pos=3 --dpi-desync-fake-tls="C:\Users\admin\Desktop\YTDisBystro\tls_clienthello_www_google_com.bin" --dpi-desync-autottl --new --filter-tcp=80 --hostlist="C:\Users\admin\Desktop\YTDisBystro\russia-blacklist.txt" --dpi-desync=fake,split2 --dpi-desync-fooling=md5sig --dpi-desync-autottl --new --filter-tcp=443 --hostlist="C:\Users\admin\Desktop\YTDisBystro\russia-blacklist.txt" --dpi-desync=fake,split2 --dpi-desync-split-seqovl=1 --dpi-desync-split-tls=sniext --dpi-desync-fake-tls="C:\Users\admin\Desktop\YTDisBystro\tls_clienthello_www_google_com.bin" --dpi-desync-autottl --new --filter-udp=443 --hostlist="C:\Users\admin\Desktop\YTDisBystro\russia-discord.txt" --dpi-desync=fake --dpi-desync-udplen-increment=10 --dpi-desync-repeats=7 --dpi-desync-udplen-pattern=0xDEADBEEF --dpi-desync-fake-quic="C:\Users\admin\Desktop\YTDisBystro\quic_initial_www_google_com.bin" --new --filter-udp=50000-50020 --dpi-desync=fake --dpi-desync-any-protocol --dpi-desync-cutoff=n2 --dpi-desync-fake-quic="C:\Users\admin\Desktop\YTDisBystro\quic_initial_www_google_com.bin" --new --filter-tcp=443 --hostlist="C:\Users\admin\Desktop\YTDisBystro\russia-discord.txt" --dpi-desync=split --dpi-desync-split-pos=1 --dpi-desync-fooling=badseq --dpi-desync-repeats=10 --dpi-desync-autottl --new --dpi-desync=fake,split2 --hostlist-auto="C:\Users\admin\Desktop\YTDisBystro\autohostlist.txt" --hostlist-exclude="C:\Users\admin\Desktop\YTDisBystro\netrogat.txt" --dpi-desync=split --dpi-desync-split-pos=1 --dpi-desync-fooling=badseq --dpi-desync-repeats=10 --dpi-desync-autottl | C:\Users\admin\Desktop\YTDisBystro\winws.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Modules
| |||||||||||||||
| 5744 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5744 | sc start zapret | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6172 | sc delete zapret | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 066
Read events
3 027
Write events
26
Delete events
13
Modification events
| (PID) Process: | (1156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (1156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\YTDisBystro.zip | |||
| (PID) Process: | (1156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (1156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
| (PID) Process: | (1156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | psize |
Value: 80 | |||
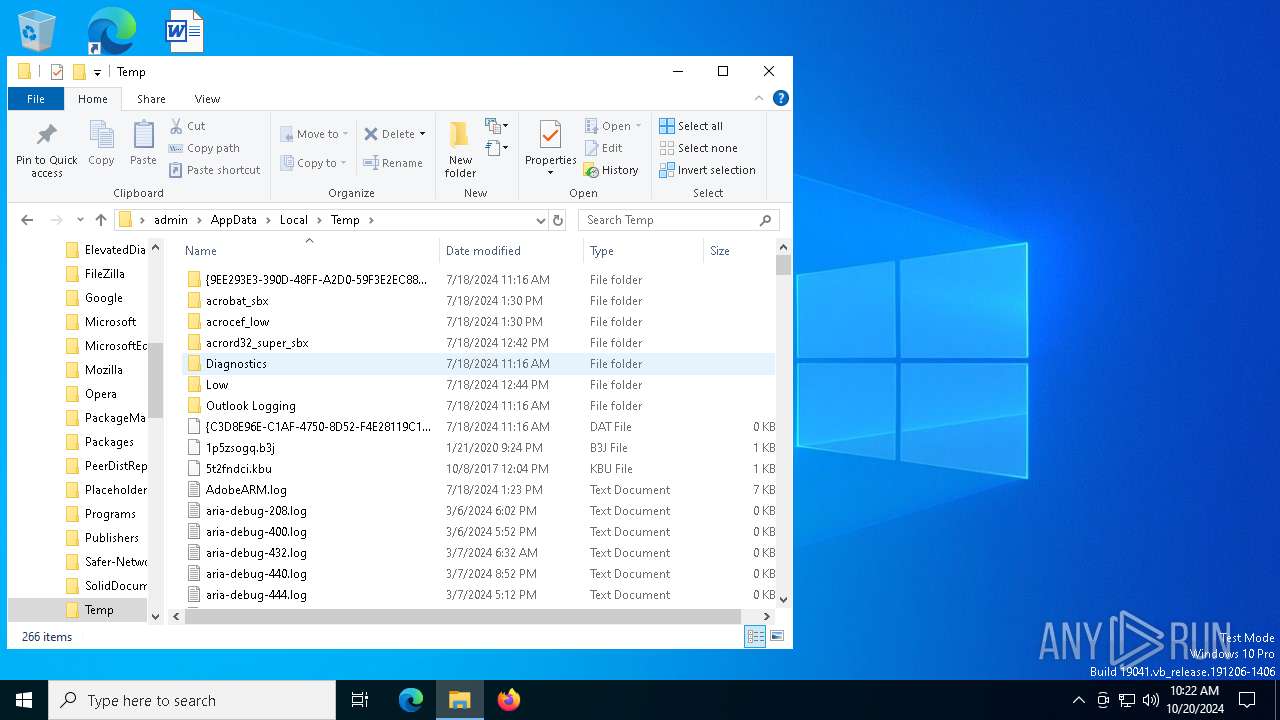
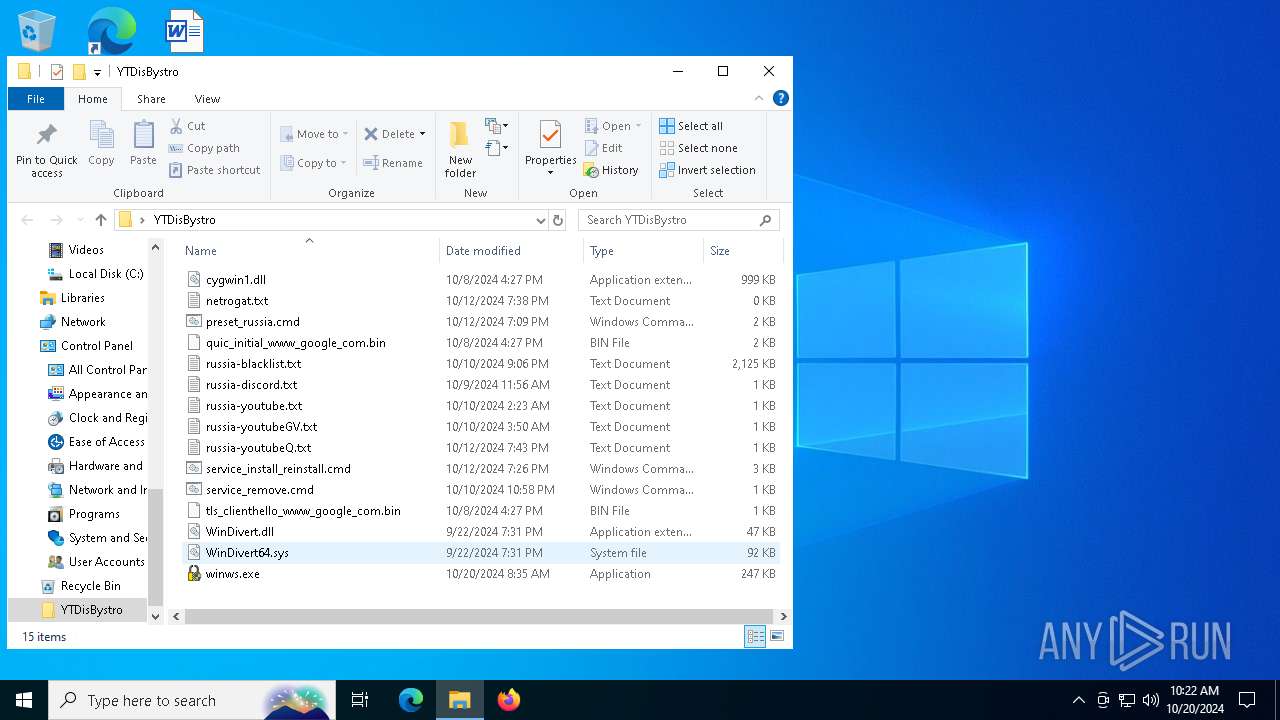
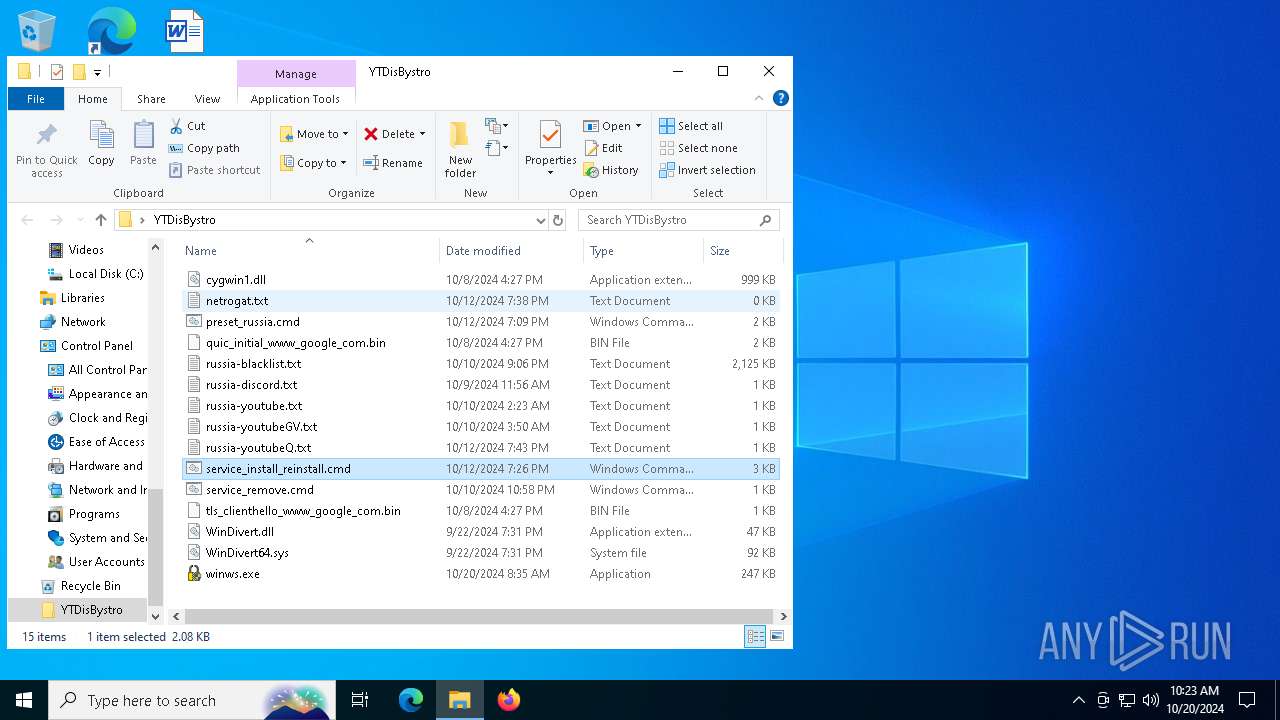
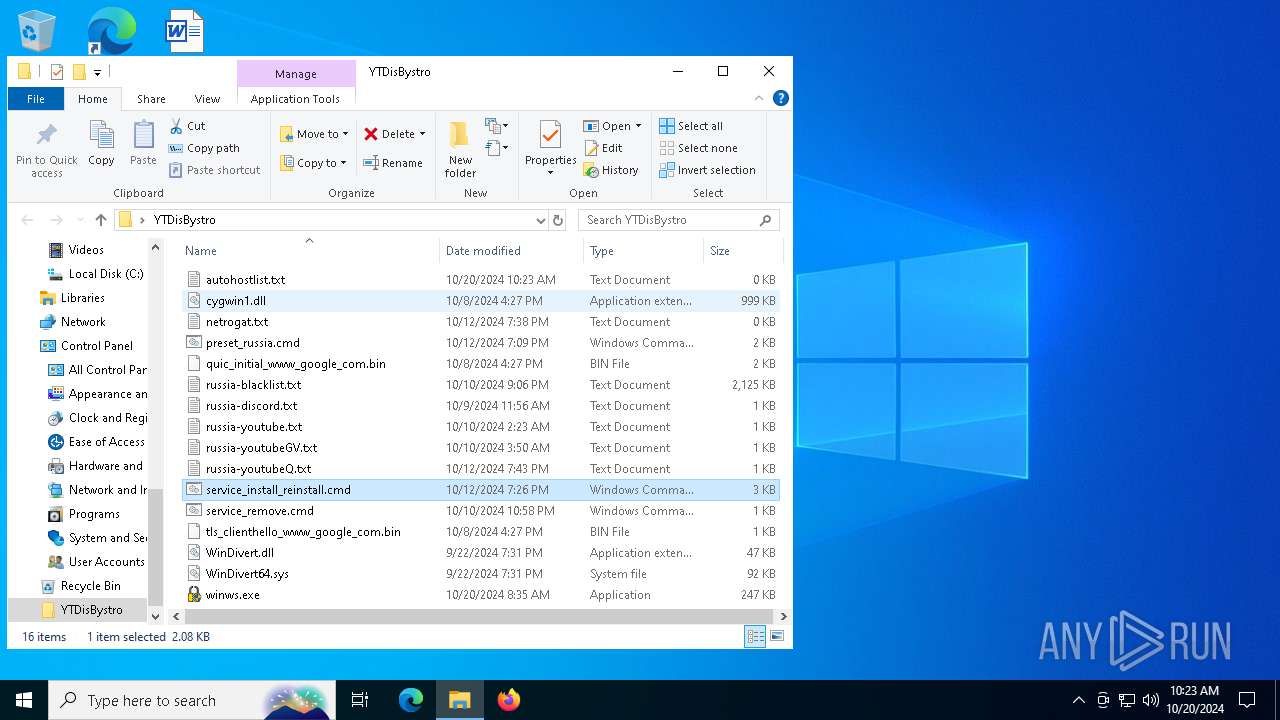
Executable files
4
Suspicious files
2
Text files
8
Unknown types
0
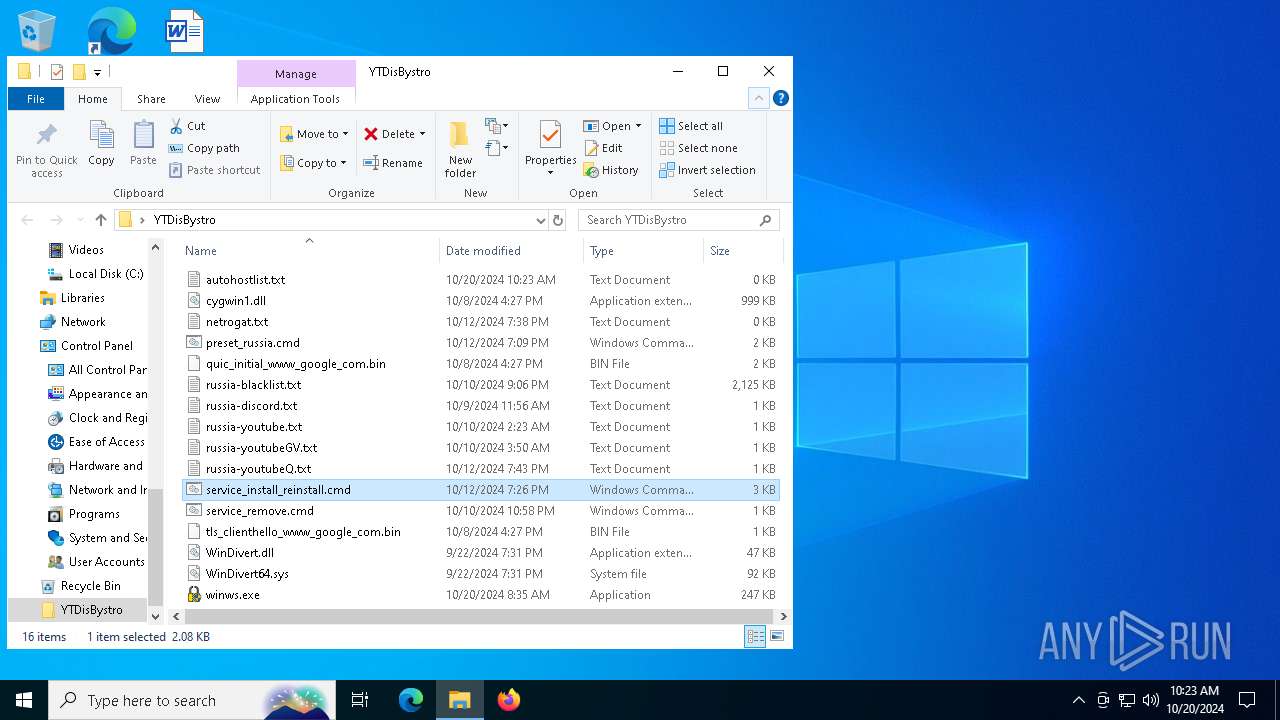
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
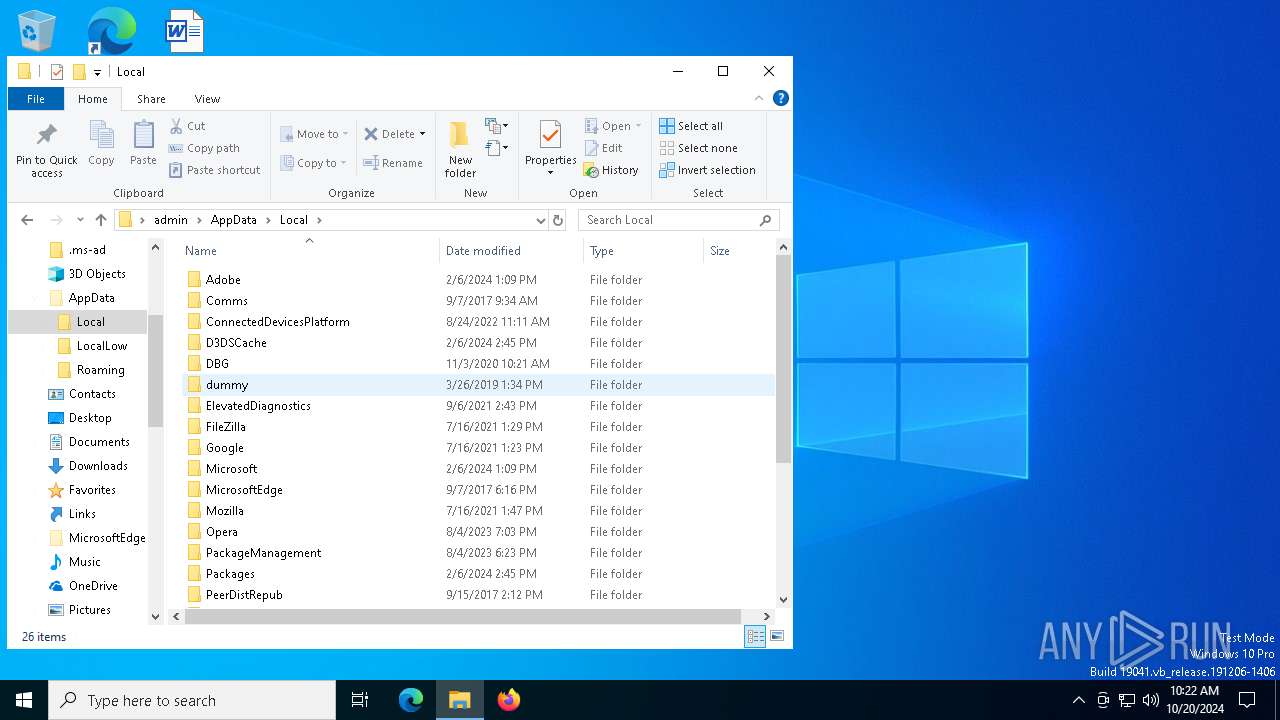
| 6676 | WinRAR.exe | C:\Users\admin\Desktop\YTDisBystro\WinDivert64.sys | executable | |
MD5:89ED5BE7EA83C01D0DE33D3519944AA5 | SHA256:8DA085332782708D8767BCACE5327A6EC7283C17CFB85E40B03CD2323A90DDC2 | |||
| 6676 | WinRAR.exe | C:\Users\admin\Desktop\YTDisBystro\tls_clienthello_www_google_com.bin | binary | |
MD5:7AB7AD857C5B8794FBDF1091B494DC94 | SHA256:E5938780152169F720383F80EABB309E9477369B83B5EC40CC137C397F862CDE | |||
| 6676 | WinRAR.exe | C:\Users\admin\Desktop\YTDisBystro\winws.exe | executable | |
MD5:B1D8A084E6D62AB1B8BF6FECF88315C6 | SHA256:153A22E7352F5F50CC773AA267CF38E8A9C4BC3CA602A754E630FEFA4337974A | |||
| 6676 | WinRAR.exe | C:\Users\admin\Desktop\YTDisBystro\russia-youtube.txt | text | |
MD5:9AD95B8203DBC5DFB25D9829477031EA | SHA256:411C1F2DC67739A36683BD8F5E4485B4E4CCF500F1D89F8BB2E1527B42141CB7 | |||
| 6676 | WinRAR.exe | C:\Users\admin\Desktop\YTDisBystro\service_remove.cmd | text | |
MD5:410D08325900864D9CF8FD7222B7F8E4 | SHA256:01D9DE489E2F589843ECF639E3B5B6DBBA8218258CBAB4A780B0FE94D5124E98 | |||
| 6676 | WinRAR.exe | C:\Users\admin\Desktop\YTDisBystro\preset_russia.cmd | text | |
MD5:007085CC6256E662E350D133465AE62C | SHA256:B5C17D2C48CCD0E8E4B88358529BE7BBE86C3DC1BAC329A30761AAB72A3FEA18 | |||
| 6676 | WinRAR.exe | C:\Users\admin\Desktop\YTDisBystro\russia-discord.txt | text | |
MD5:09F90DED3F579338996DFCB119A58408 | SHA256:F32AEE579D9499A9F5ACEA2F635F5024175FD19699BC6A9F5DAF5BF8D0650321 | |||
| 6676 | WinRAR.exe | C:\Users\admin\Desktop\YTDisBystro\quic_initial_www_google_com.bin | binary | |
MD5:312526D39958D89B1F8AB67789AB985F | SHA256:F4589C57749F956BB30538197A521D7005F8B0A8723B4707E72405E51DDAC50A | |||
| 6676 | WinRAR.exe | C:\Users\admin\Desktop\YTDisBystro\russia-youtubeQ.txt | text | |
MD5:B15E71A9DBA318FF81BB7CEFD9ED9FC6 | SHA256:0DD2A69EAB2F2E2D643A19807F336CDFFCD16ADC78A77C5A9291F231E5AFC7CB | |||
| 6676 | WinRAR.exe | C:\Users\admin\Desktop\YTDisBystro\russia-blacklist.txt | text | |
MD5:AAA4A3FA782DF525B220AC750B6D8535 | SHA256:37D88B634CEC8BCE81A41F365A620159D221B7187E73E3EEB9FC749E827F1ED7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
56
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6944 | svchost.exe | GET | 200 | 23.48.23.166:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6356 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4004 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6692 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6356 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1248 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6944 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6944 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6944 | svchost.exe | 23.48.23.166:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6944 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4360 | SearchApp.exe | 104.126.37.163:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4360 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |