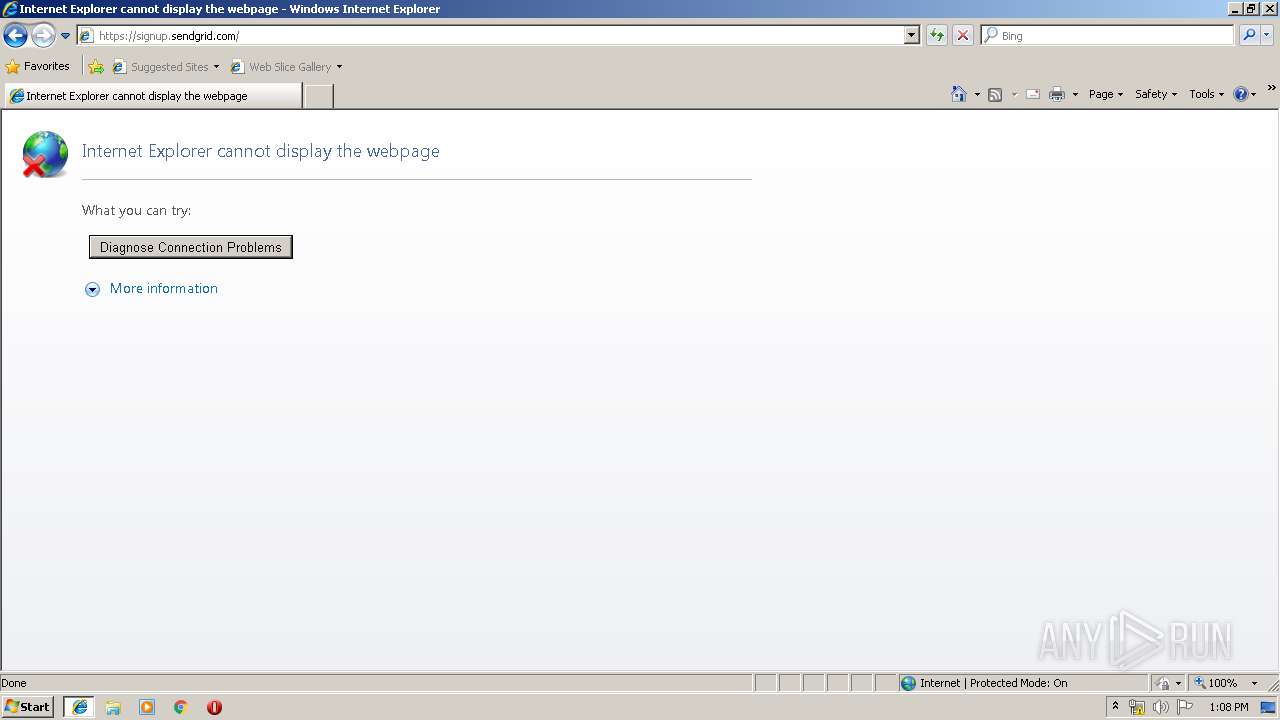
| URL: | https://u7367700.ct.sendgrid.net/wf/click?upn=sw-2BpEri5LTJKiGqpmJIs6ZqVtF51SexOhTnZ-2BWu5mI8GQa3sq18IykBiMc7QQNI2nUpgJCyYgWaVLGSanpSd1fLcZCIHCoBbtKMXG0g7g56-2B09iL9MgvldVmqQM-2Fxcgj_NOzmJHCskOif8NCnH-2BVvVRvYJ3c47-2FOFxwXWMU5cx4upLR4qPgTArrqqCNSJZ-2BYfuxhXFzgBH2ZmrrseSPaFYmYYg5E7xXf8zdPEU8sGD4qrTuR9rk-2B5tckrKZNA7AfBcULesv2WFQfmH4JTZAc5cB5sWYrYoRKTl5RAH6HzNmVkkxRwUWdl-2Bdk3-2Fd7u-2BAcQsZzp4ZeeA9jJ3BB5X7F9jRoMgQdRjoLo5b240aR1q2w-3D |
| Full analysis: | https://app.any.run/tasks/69f775d5-3441-4eeb-a0c9-a0bf919554d4 |
| Verdict: | Malicious activity |
| Analysis date: | September 19, 2019, 12:06:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 007C0AAC26103BE0DBC28C2E2CE48648 |
| SHA1: | 49F5C8F96EFCAAD48E793385DA6C38EA540C33F0 |
| SHA256: | A5F7A4F9841BBAF1ED0C7A00368B209E217E4AAD3EBF01D3C134CECCB4E42674 |
| SSDEEP: | 12:2a5DSrSLsfbo/MuMpQ0/odn/0epbAqGgS1:2+Io/Mumo187R5 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via COM
- sdiagnhost.exe (PID: 2640)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3192)
- sdiagnhost.exe (PID: 2200)
Executable content was dropped or overwritten
- msdt.exe (PID: 3028)
- msdt.exe (PID: 2500)
Uses IPCONFIG.EXE to discover IP address
- sdiagnhost.exe (PID: 2200)
- sdiagnhost.exe (PID: 2640)
INFO
Application launched itself
- iexplore.exe (PID: 3540)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 4016)
Reads internet explorer settings
- iexplore.exe (PID: 4016)
Changes settings of System certificates
- iexplore.exe (PID: 3540)
Creates files in the user directory
- iexplore.exe (PID: 4016)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3192)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3540)
Changes internet zones settings
- iexplore.exe (PID: 3540)
Reads Internet Cache Settings
- iexplore.exe (PID: 4016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
50
Monitored processes
13
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1032 | "C:\Windows\system32\makecab.exe" /f NetworkConfiguration.ddf | C:\Windows\system32\makecab.exe | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Cabinet Maker Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2200 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2212 | "C:\Windows\system32\makecab.exe" /f NetworkConfiguration.ddf | C:\Windows\system32\makecab.exe | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Cabinet Maker Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2500 | -modal 327980 -skip TRUE -path C:\Windows\diagnostics\system\networking -af C:\Users\admin\AppData\Local\Temp\NDF8CDE.tmp -ep NetworkDiagnosticsWeb | C:\Windows\system32\msdt.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2560 | "C:\Windows\system32\ipconfig.exe" /all | C:\Windows\system32\ipconfig.exe | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2640 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2868 | "C:\Windows\system32\ipconfig.exe" /all | C:\Windows\system32\ipconfig.exe | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3028 | -modal 327980 -skip TRUE -path C:\Windows\diagnostics\system\networking -af C:\Users\admin\AppData\Local\Temp\NDFD9D6.tmp -ep NetworkDiagnosticsWeb | C:\Windows\system32\msdt.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3192 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 3540 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
882
Read events
590
Write events
288
Delete events
4
Modification events
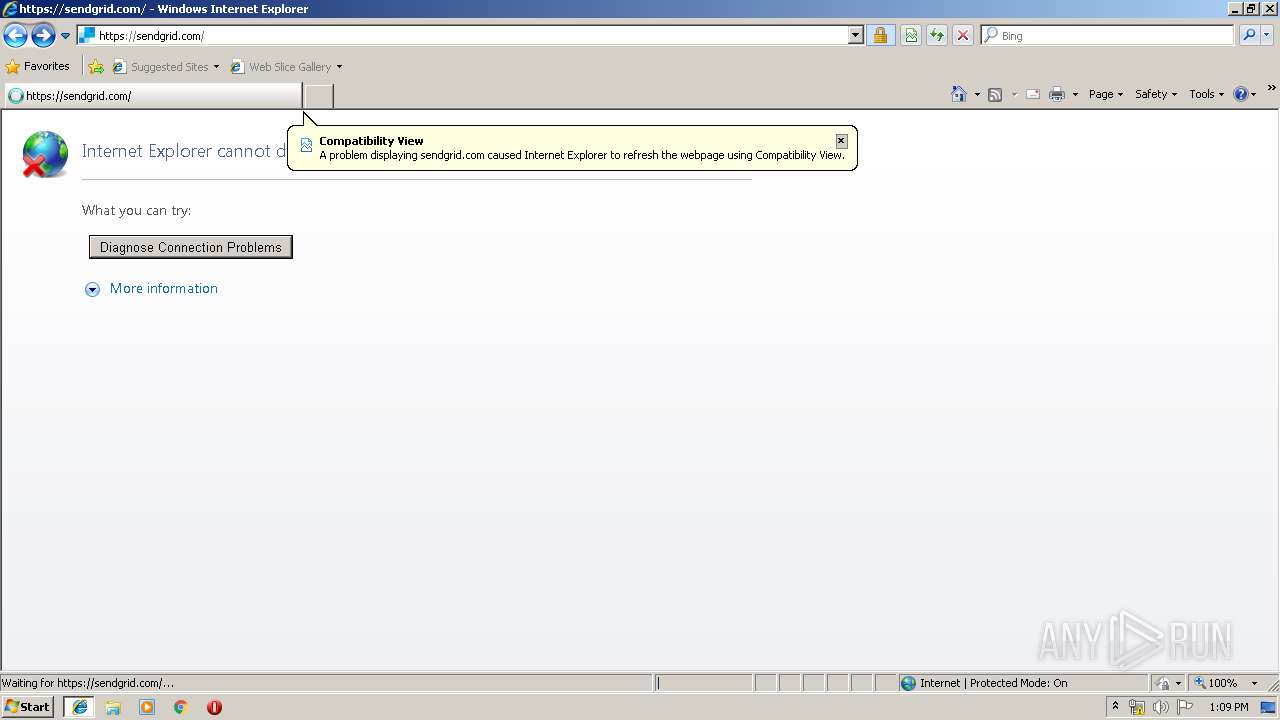
| (PID) Process: | (3540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {F95D47C3-DAD5-11E9-B86F-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (3540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070900040013000C00060039006400 | |||
Executable files
4
Suspicious files
27
Text files
245
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3540 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3540 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
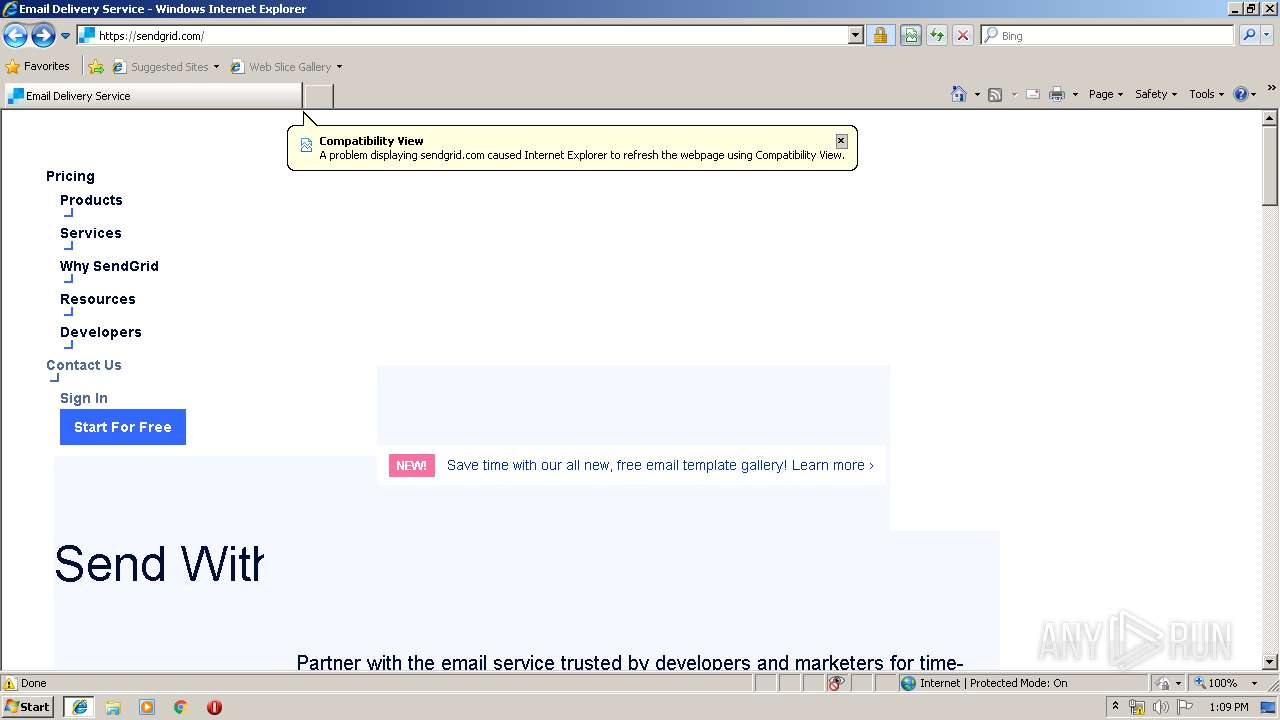
| 4016 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@go.sendgrid[1].txt | — | |
MD5:— | SHA256:— | |||
| 4016 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\DOMStore\index.dat | dat | |
MD5:— | SHA256:— | |||
| 4016 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\Z63LUP8D\style.min[1].css | text | |
MD5:— | SHA256:— | |||
| 4016 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 4016 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\RWGOAFY1\72168671[1].js | text | |
MD5:— | SHA256:— | |||
| 4016 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@sendgrid[2].txt | — | |
MD5:— | SHA256:— | |||
| 4016 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 4016 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\4T3SL64G\uwt[1].js | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
273
DNS requests
40
Threats
0
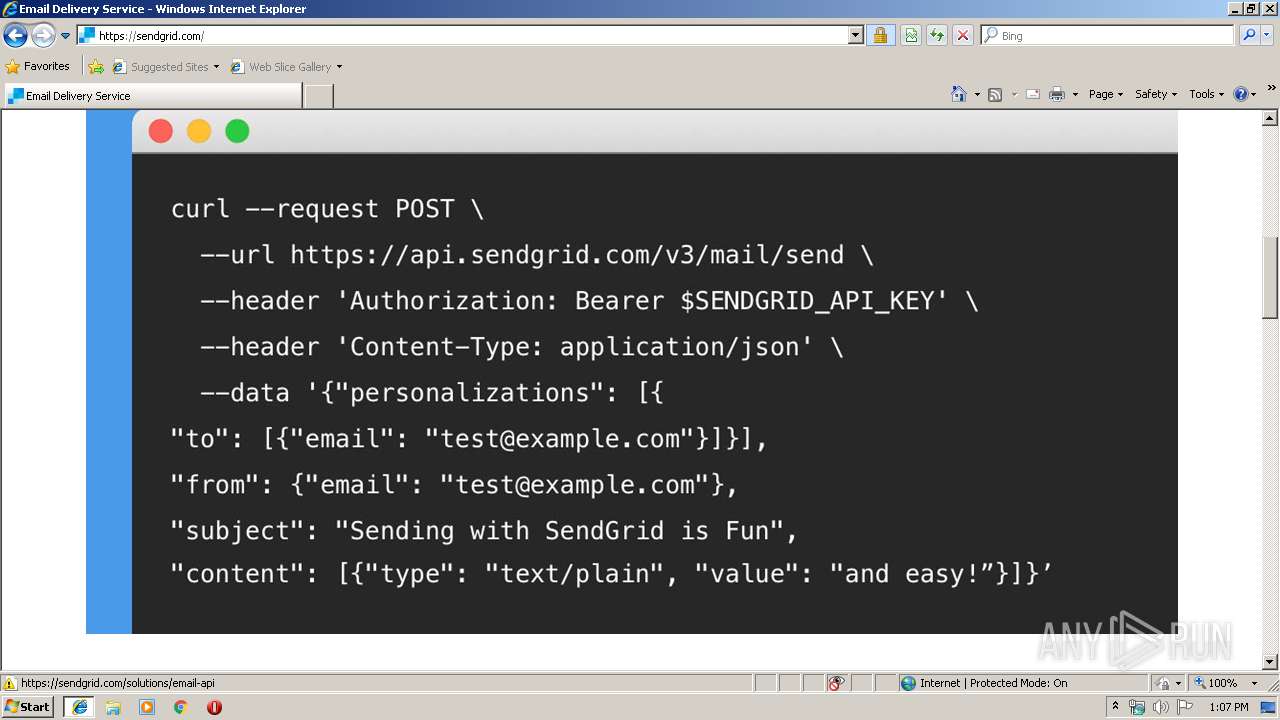
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3540 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
4016 | iexplore.exe | GET | 200 | 13.225.84.115:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
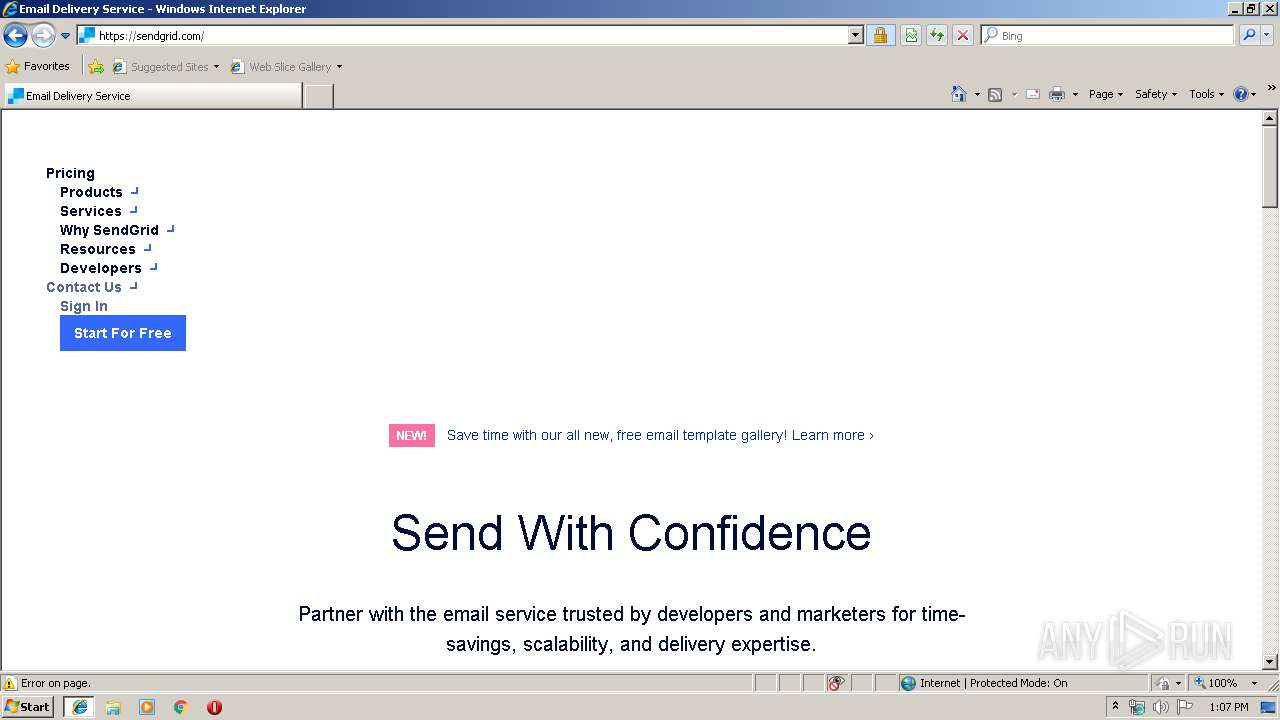
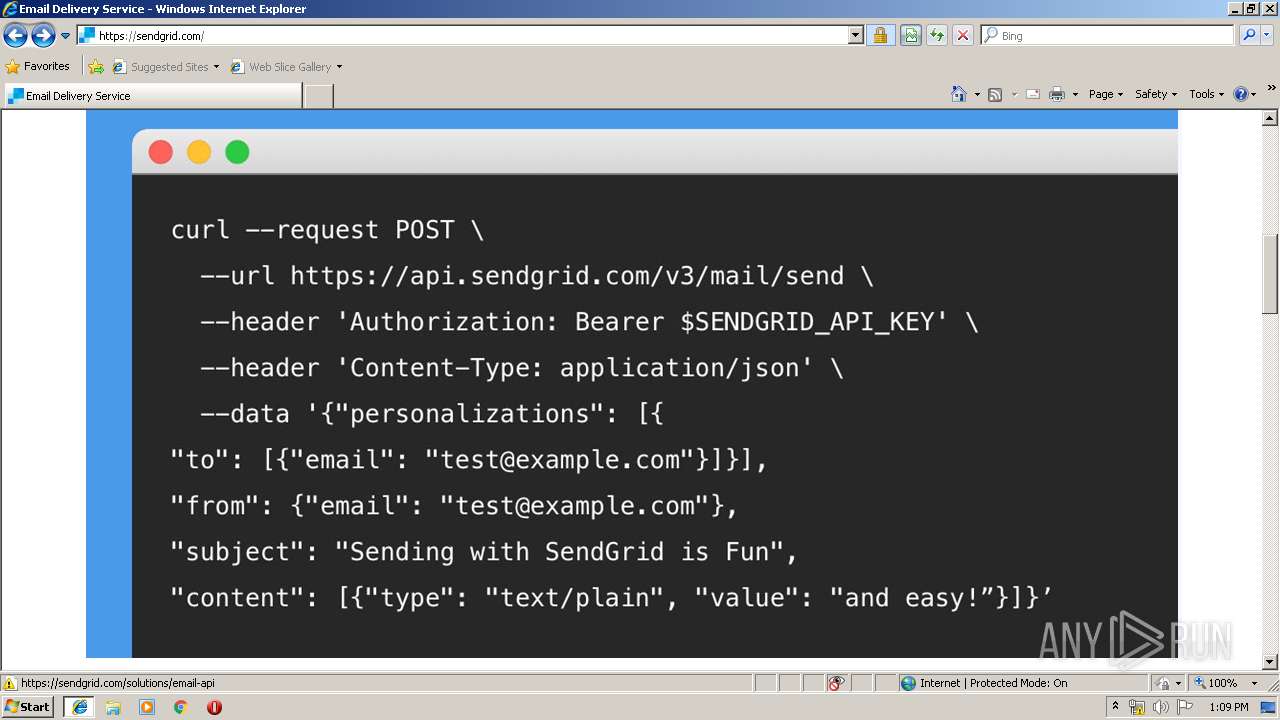
4016 | iexplore.exe | GET | 301 | 159.122.219.52:80 | http://sendgrid.com/invalidlink | US | html | 178 b | whitelisted |
4016 | iexplore.exe | GET | 200 | 205.185.216.42:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3540 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
4016 | iexplore.exe | 159.122.219.52:443 | sendgrid.com | SoftLayer Technologies Inc. | US | unknown |
4016 | iexplore.exe | 23.210.249.30:443 | cdn.optimizely.com | Akamai International B.V. | NL | whitelisted |
4016 | iexplore.exe | 172.217.18.10:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
4016 | iexplore.exe | 13.224.193.80:443 | cdn.segment.com | — | US | suspicious |
4016 | iexplore.exe | 167.89.123.16:443 | u7367700.ct.sendgrid.net | SendGrid, Inc. | US | malicious |
4016 | iexplore.exe | 159.122.219.52:80 | sendgrid.com | SoftLayer Technologies Inc. | US | unknown |
4016 | iexplore.exe | 172.217.18.104:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
4016 | iexplore.exe | 54.71.228.147:443 | api.segment.io | Amazon.com, Inc. | US | unknown |
4016 | iexplore.exe | 151.101.112.157:443 | static.ads-twitter.com | Fastly | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
u7367700.ct.sendgrid.net |
| malicious |
sendgrid.com |
| whitelisted |
cdn.optimizely.com |
| whitelisted |
go.sendgrid.com |
| suspicious |
ajax.googleapis.com |
| whitelisted |
cdn.segment.com |
| shared |
www.googletagmanager.com |
| whitelisted |
api.segment.io |
| whitelisted |
www.google-analytics.com |
| whitelisted |