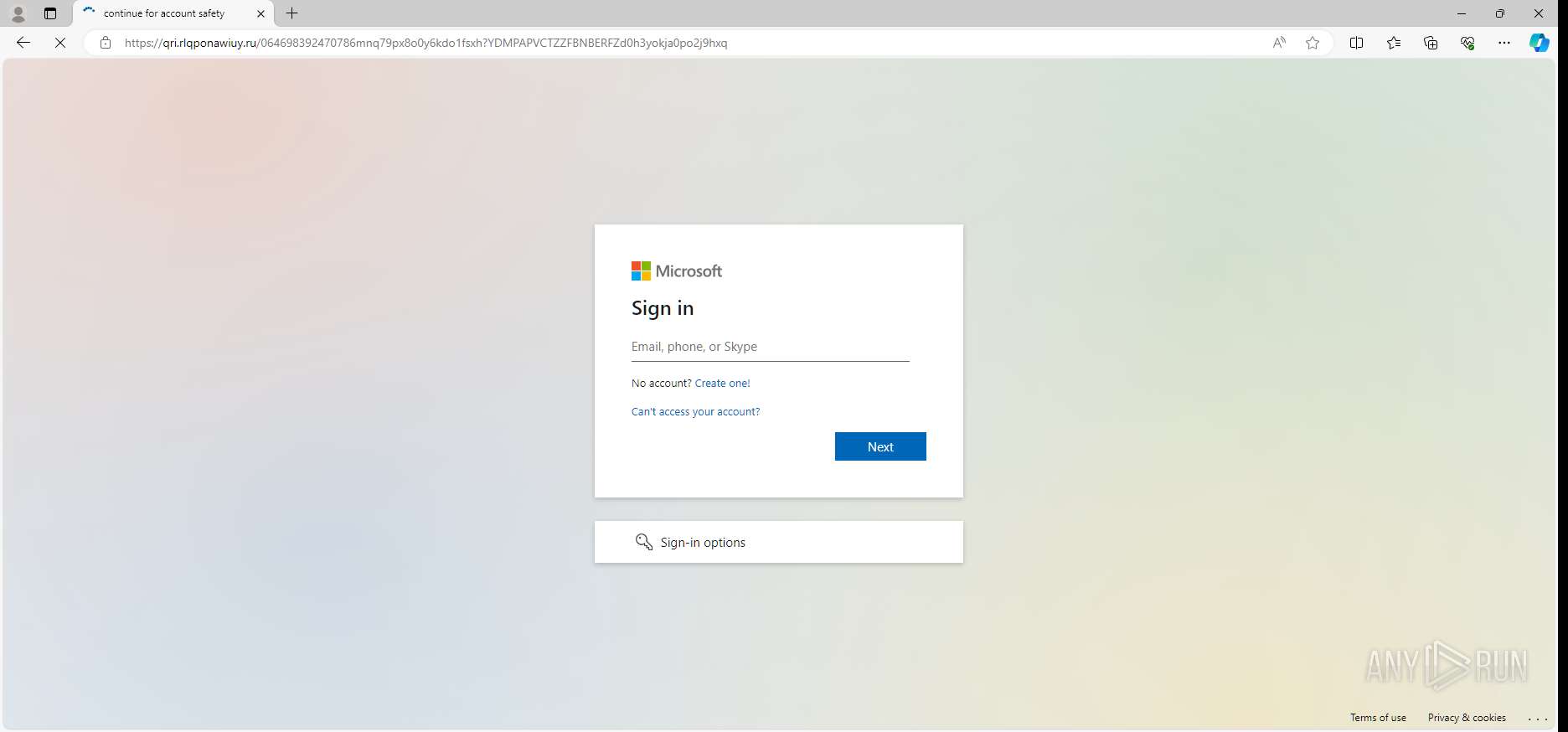
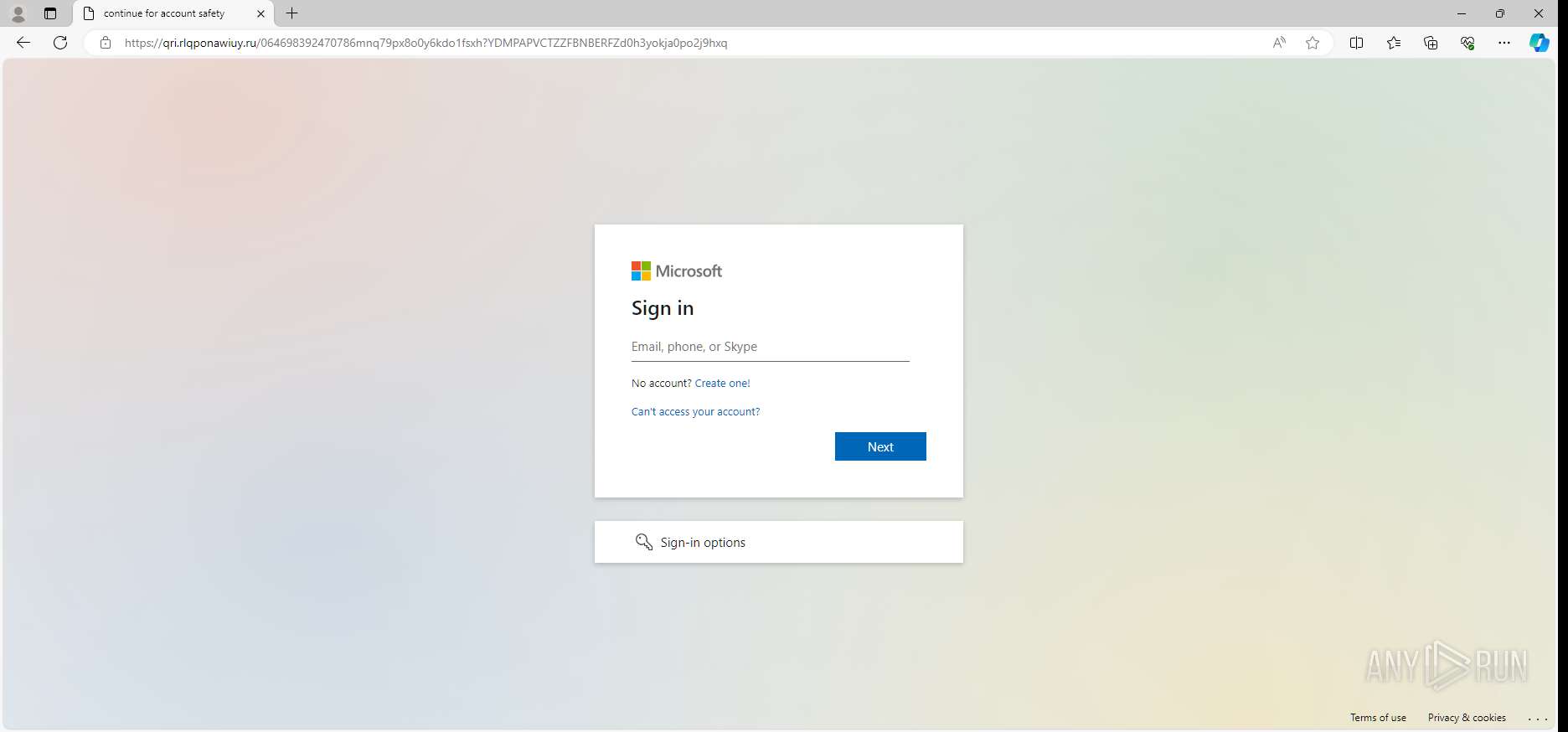
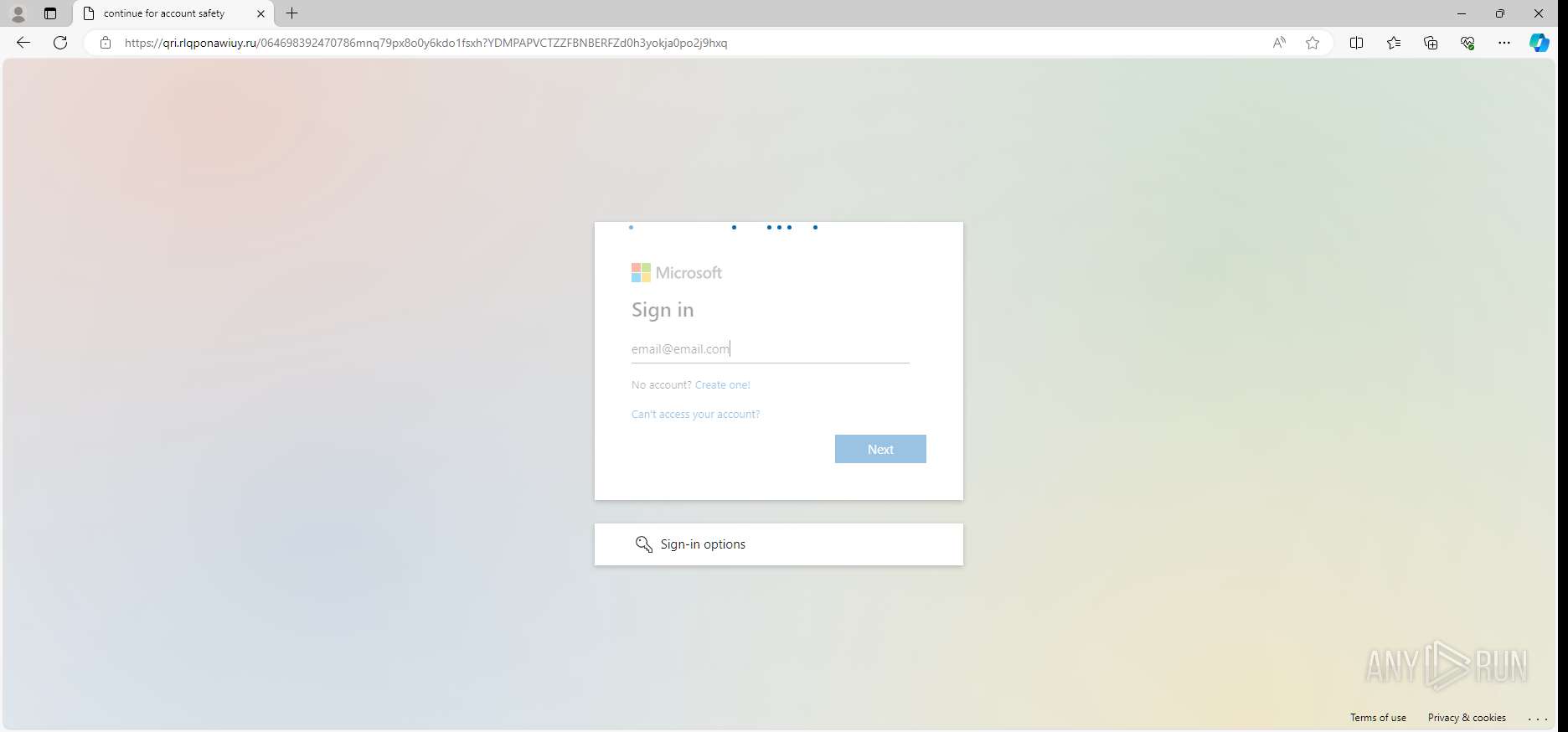
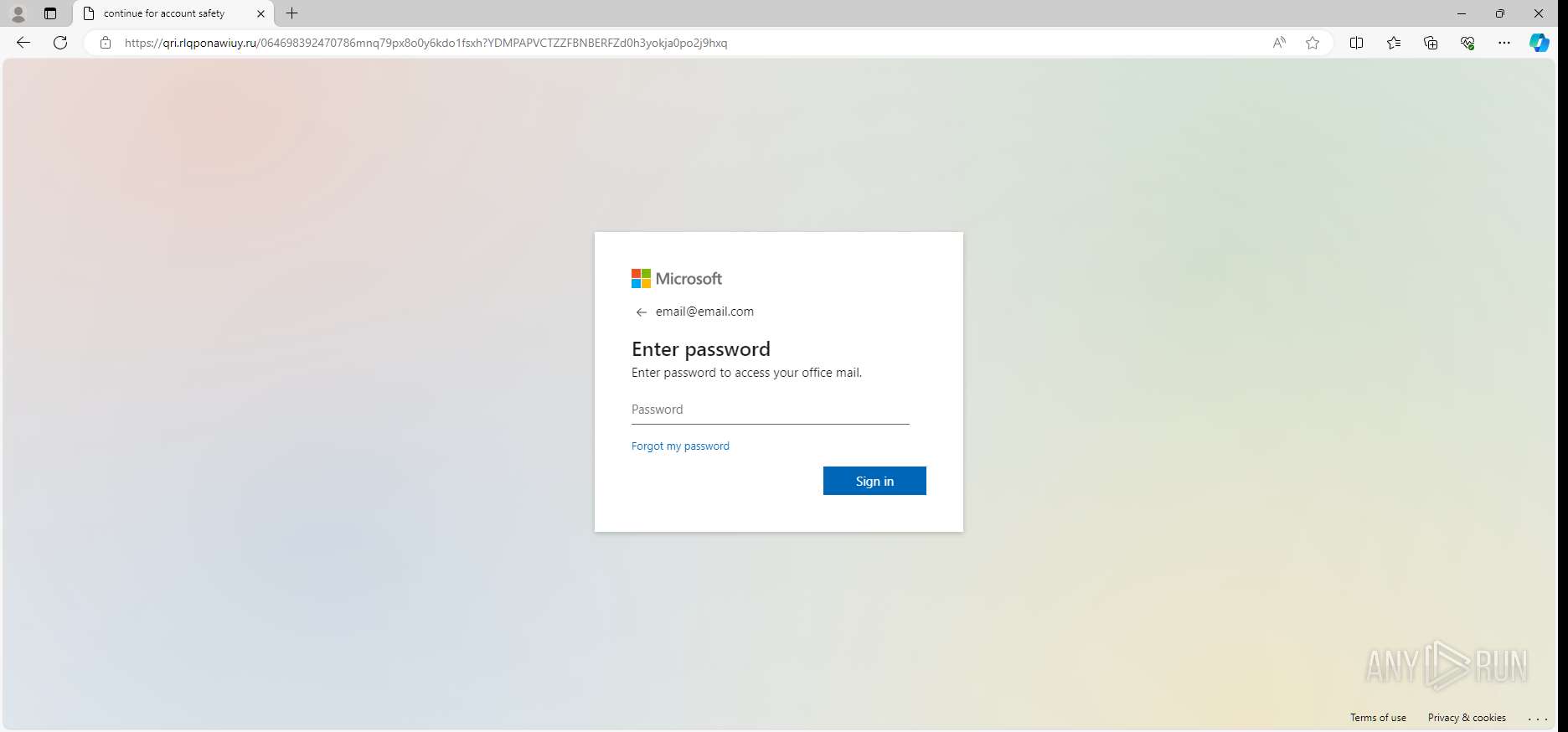
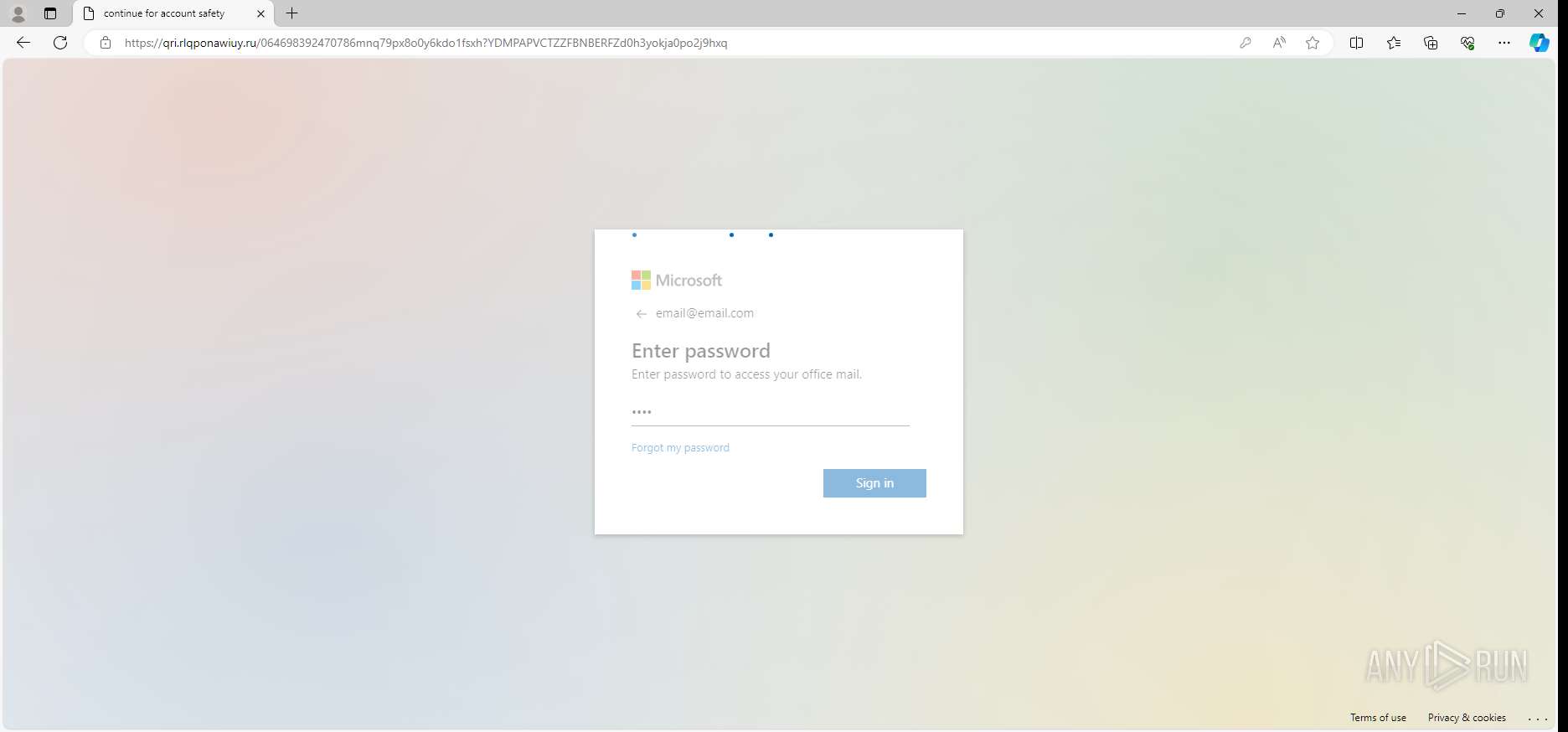
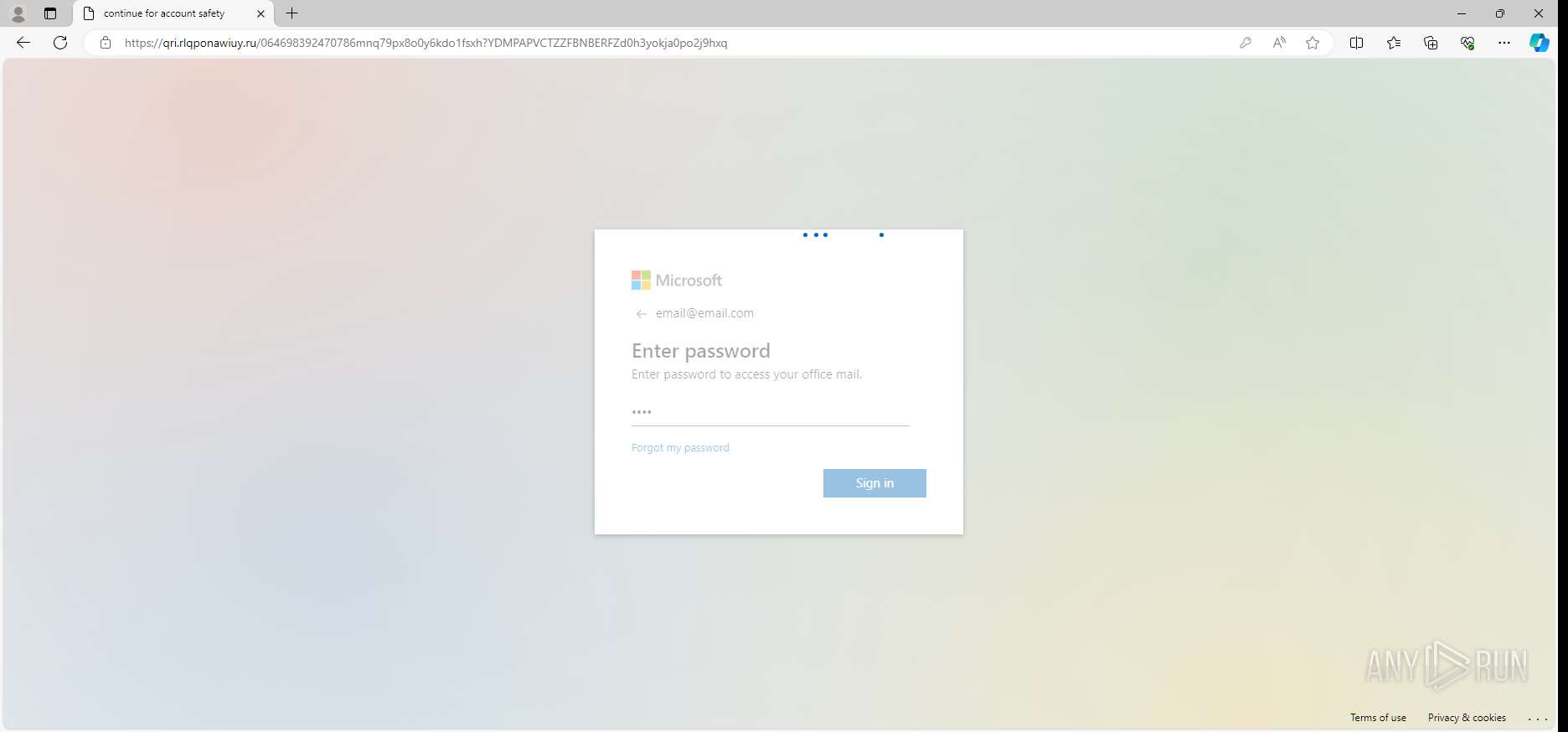
| URL: | https://projectartitude.com/res444.php?4-68747470733a2f2f7172492e726c71706f6e61776975792e72752f754a736557472f- |
| Full analysis: | https://app.any.run/tasks/306f0646-9eb2-4bbd-903a-36eaef253c18 |
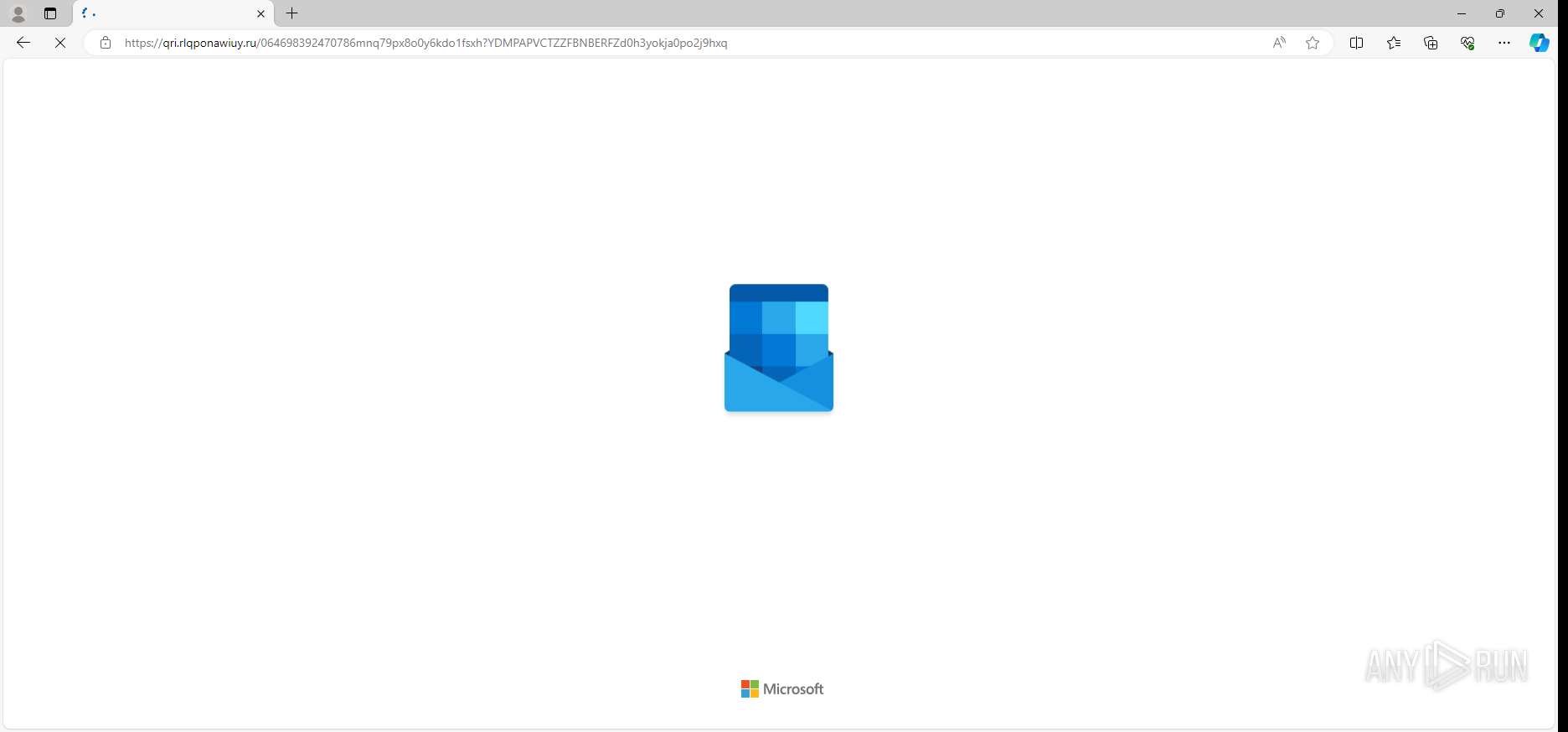
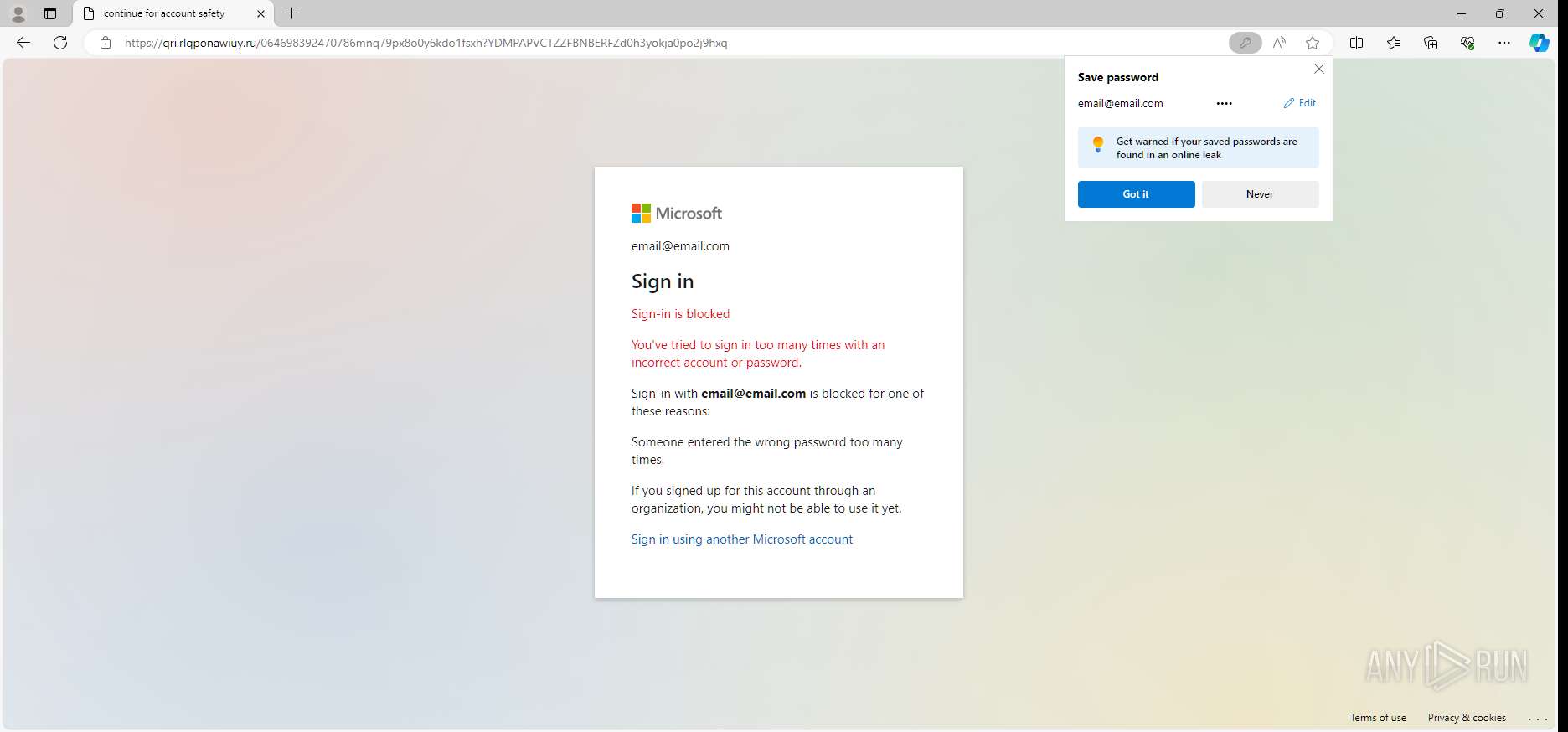
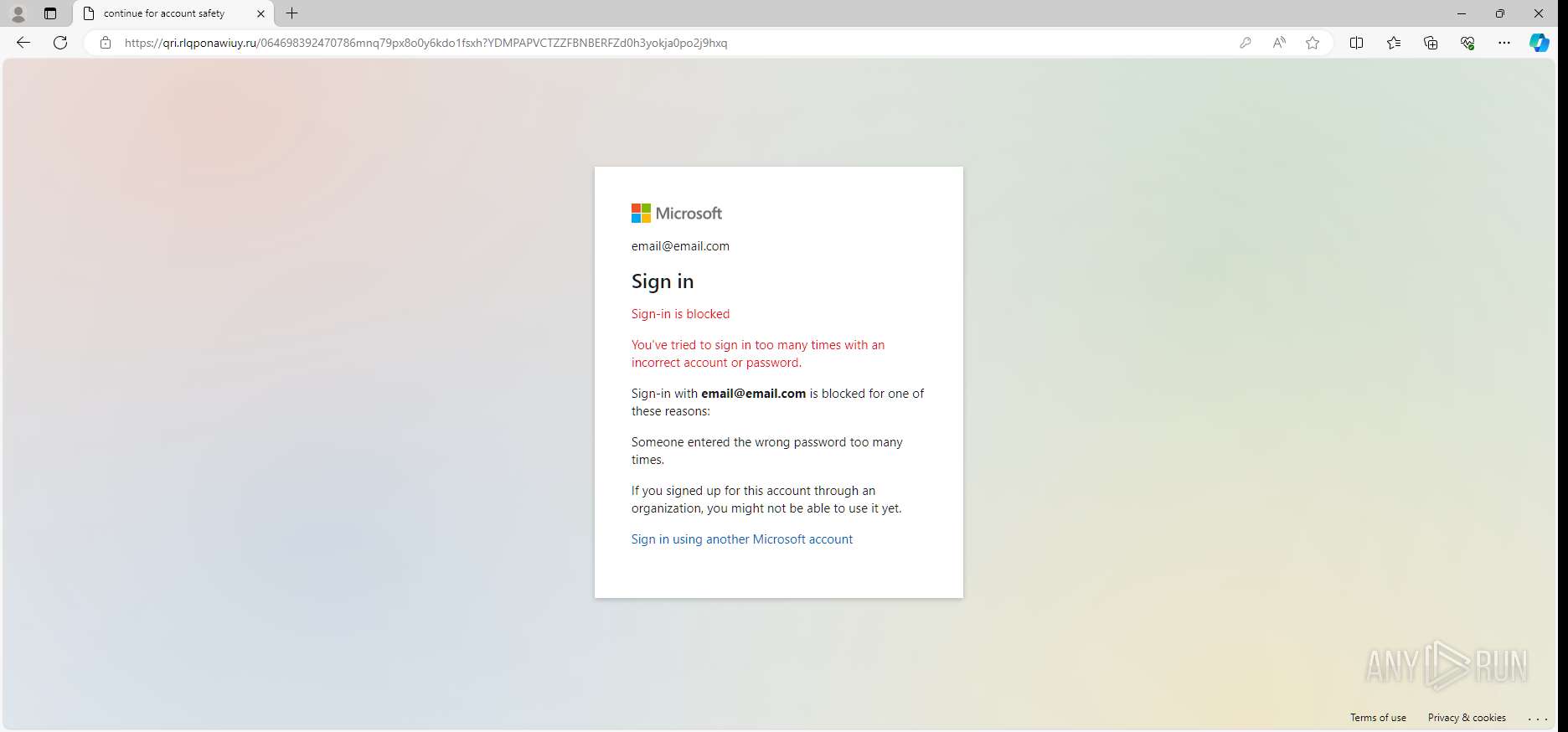
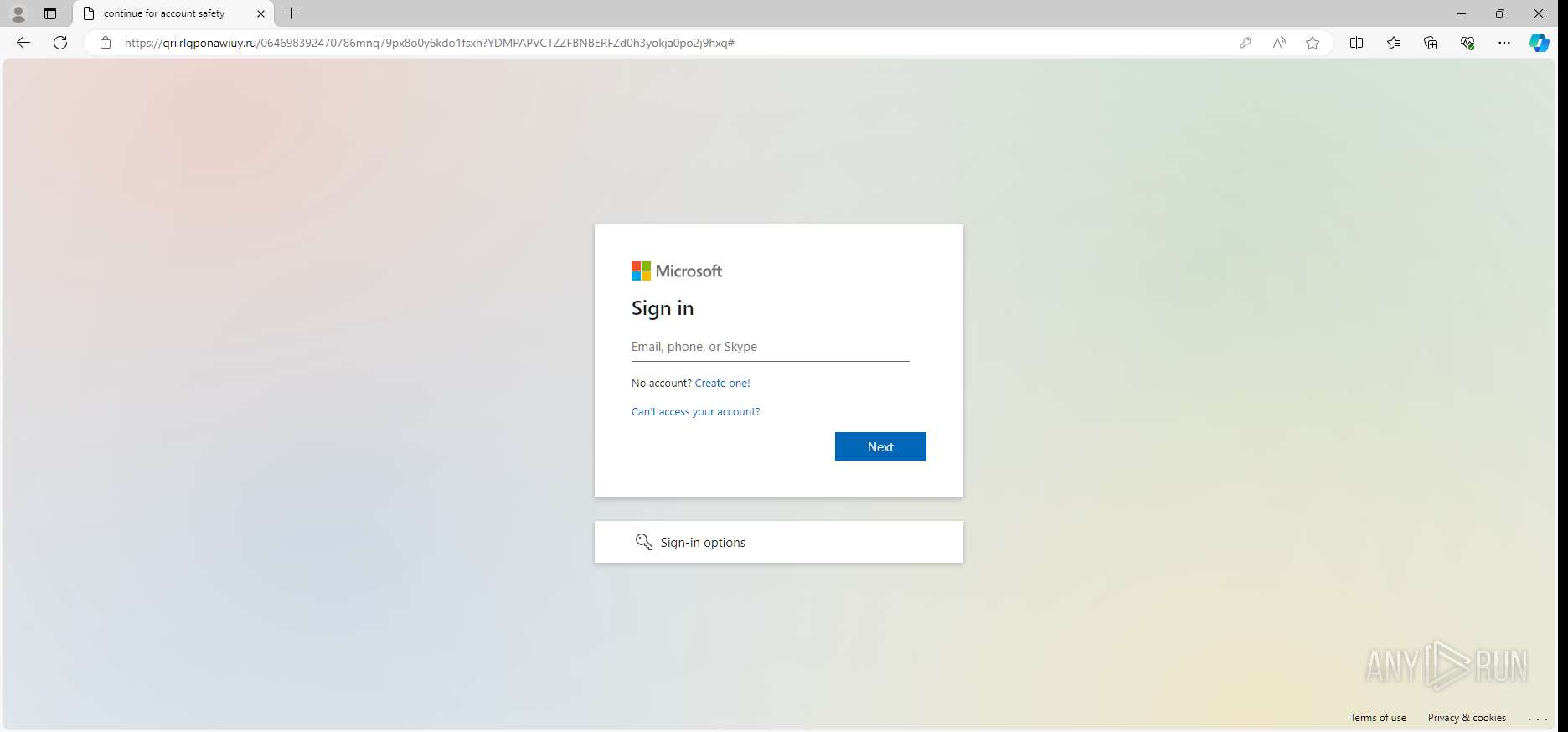
| Verdict: | Malicious activity |
| Analysis date: | December 13, 2024, 18:53:48 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | FBB653D0F34178EBD6762E806EDB9BB5 |
| SHA1: | DA3C51A94494DABEFAF09E7889C2719B97743248 |
| SHA256: | A5EE3686D0421159CDA11C85A9D3CB73AE1A51E33660D4FBBA1E39B851D5366C |
| SSDEEP: | 3:N8TKPtudKX93bwu0RSz6TSUk6HXJFLFcSQfCC/iqRT:2ouCcu0ReSxHXJRFsagnRT |
MALICIOUS
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 4792)
SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
138
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 4792 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2604 --field-trial-handle=2320,i,16194277592197507296,15814343983252007256,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
30
Text files
2
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Network\217366c1-c6d9-467d-a25b-221f3503a8f5.tmp | binary | |
MD5:ED4A66106625BA82737335748A8A0958 | SHA256:7F411856822D302C10B15EFE178CED8289ECFD6F42EECA9F6003CE39D3BBBE07 | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Network\TransportSecurity~RF2b61f5.TMP | binary | |
MD5:15D26FA4E16467BE658F42074AC0DBAA | SHA256:D287407BD901A32E3F38F4392984507184D596C3694FAA69DD0B2E68F9F3A8FE | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Network\Network Persistent State~RF2b5f35.TMP | binary | |
MD5:2A21453795942FD88CBB06714604B9FD | SHA256:5DFE0384325B556EE4B8668E502312B9BA6ADC298CD9213DDFA528CB959ADC06 | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Network\2dd1e5cc-72f8-4ce8-9573-7bbea99ea07d.tmp | binary | |
MD5:ED74D0CC3CAB53CA501F3CD6C50FAA1A | SHA256:331BB0DA5A3BE7843A14503DA9547E7309F3631916C6112882FF36D75025E7EE | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000bb | compressed | |
MD5:CA6E0DCAF6FE11E3B4D4D299ECBAB7A6 | SHA256:F4A93CF3834C5F3BBBAB2BA619425FB1415050A847F5BC12CD6B0BAB5E68074E | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000c6 | image | |
MD5:F9A795E2270664A7A169C73B6D84A575 | SHA256:D00203B2EEA6E418C31BAAFA949ADA5349A9F9B7E99FA003AEC7406822693740 | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Network\Network Persistent State | binary | |
MD5:ED74D0CC3CAB53CA501F3CD6C50FAA1A | SHA256:331BB0DA5A3BE7843A14503DA9547E7309F3631916C6112882FF36D75025E7EE | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000bd | binary | |
MD5:DCD74E4268B9E5C10D2A8E460107F670 | SHA256:C4D82C305DA85F0F04018AF6314DD3488DC09D04C50BC671DCBC4176DD1C03A9 | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000c4 | compressed | |
MD5:65C8E946B531157A11540468B5AC0047 | SHA256:4E8970B4FDC306A25683625031983483FDB8EF809F7F2539C64120D13772EA18 | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000bc | binary | |
MD5:D17B5A55EC9D8608C1D2B531CCB6DE88 | SHA256:DC2A3600C7CDFAEA40DB03757D6915D67518215DB51397C8A5BB3F132AE89A49 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
45
TCP/UDP connections
69
DNS requests
69
Threats
30
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6900 | svchost.exe | GET | 200 | 2.16.164.90:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | HEAD | 200 | 23.213.164.137:443 | https://fs.microsoft.com/fs/windows/config.json | unknown | — | — | — |
1792 | RUXIMICS.exe | GET | 200 | 2.16.164.90:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6900 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4304 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.90:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4304 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
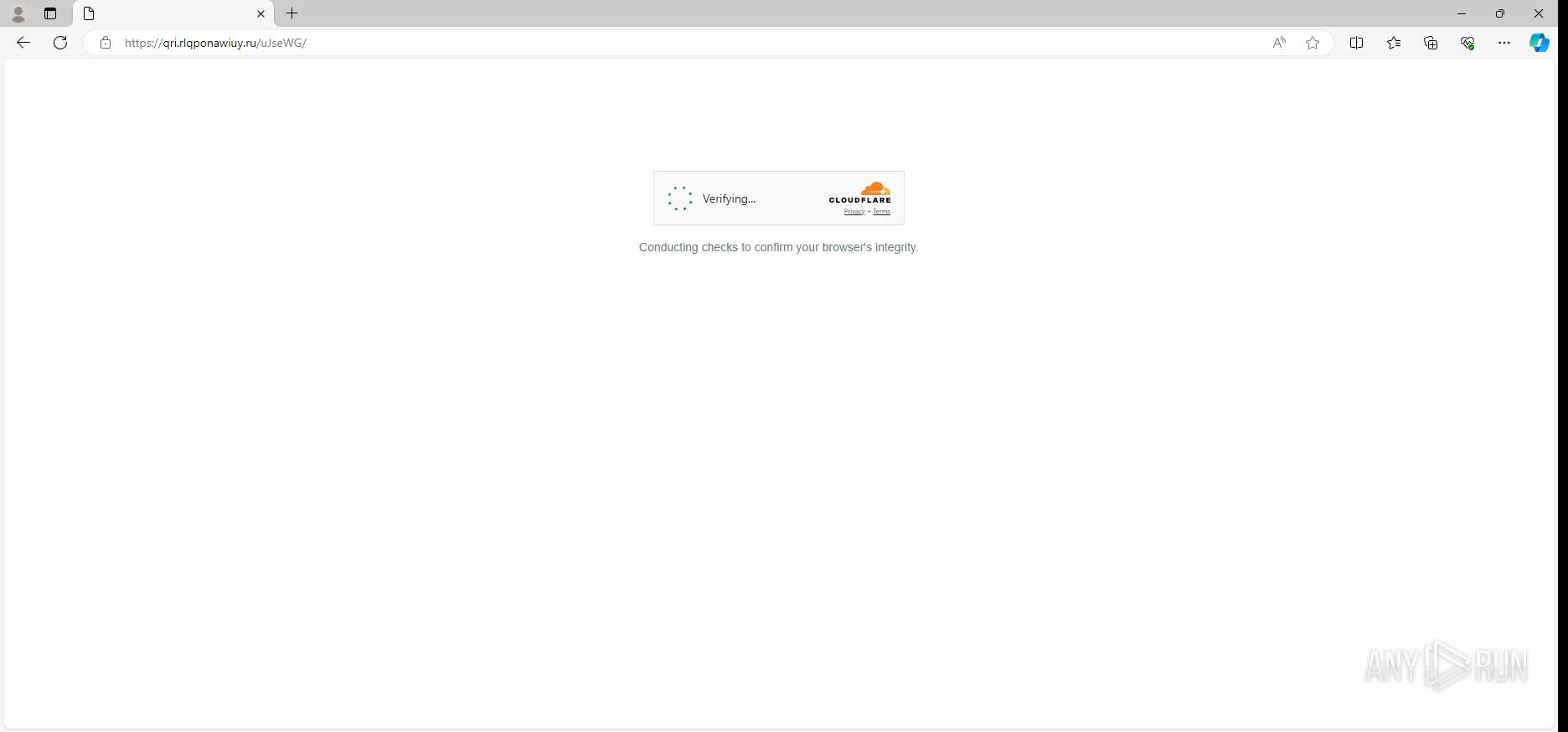
— | — | GET | 302 | 104.18.94.41:443 | https://challenges.cloudflare.com/turnstile/v0/api.js?render=explicit | unknown | — | — | — |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 302 | 140.82.121.3:443 | https://github.com/fent/randexp.js/releases/download/v0.4.3/randexp.min.js | unknown | — | — | — |
— | — | OPTIONS | 200 | 35.190.80.1:443 | https://a.nel.cloudflare.com/report/v4?s=mSsANpeGM71Xke7qNqJOItueNyASzkVXjdHyox%2FPBjLV6%2BIagcBU6pbE6benwEG2R%2BzUMg%2BDe2BJIMvTvIp%2BQBaj%2F0%2FfMb24HCu8E7Fjfwd%2FWG6tnmqdARyIee%2BQwg%3D%3D | unknown | — | — | — |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1792 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 224.0.0.251:5353 | — | — | — | unknown |
4792 | msedge.exe | 13.89.179.11:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
4304 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6900 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5988 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
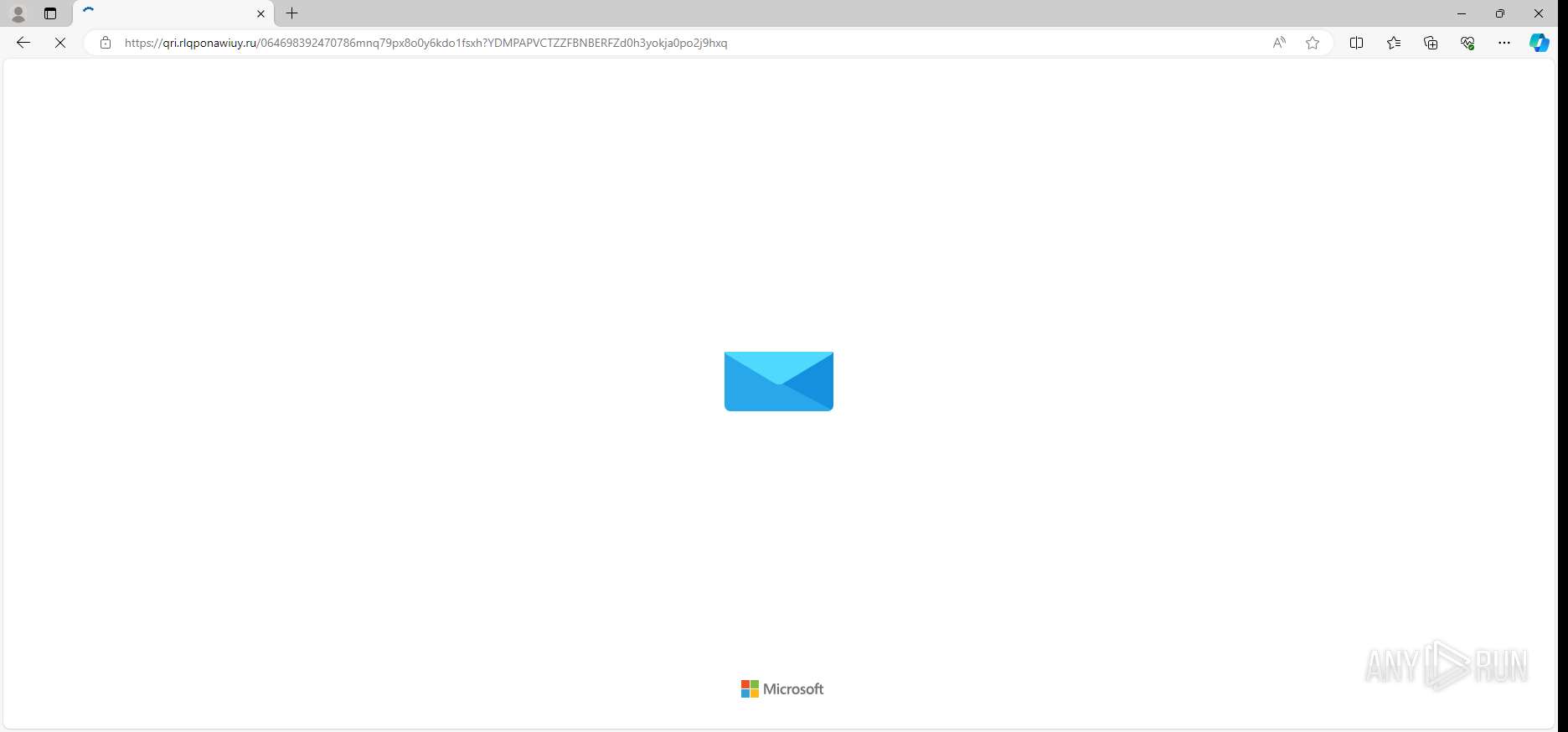
4792 | msedge.exe | 69.49.245.172:443 | projectartitude.com | UNIFIEDLAYER-AS-1 | US | unknown |
3900 | svchost.exe | 184.28.90.27:443 | fs.microsoft.com | AKAMAI-AS | US | whitelisted |
4792 | msedge.exe | 104.17.25.14:443 | cdnjs.cloudflare.com | — | — | whitelisted |
4792 | msedge.exe | 2.23.209.189:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
projectartitude.com |
| unknown |
fs.microsoft.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
qri.rlqponawiuy.ru |
| unknown |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
code.jquery.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Domain identified as part of Tycoon phishing service [Storm-1747] (projectartitude .com) |
— | — | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Domain identified as part of Tycoon phishing service [Storm-1747] (projectartitude .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
— | — | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Storms-1747`s Phishing domain by CrossDomain ( .rlqponawiuy .ru) |
— | — | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Storms-1747`s Phishing domain by CrossDomain ( .rlqponawiuy .ru) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |