| File name: | myscrapnook.2e46c764e10b400194a90bdd9fdea621.exe |
| Full analysis: | https://app.any.run/tasks/b74e2d42-cf66-4848-bdd0-5725a98e8233 |
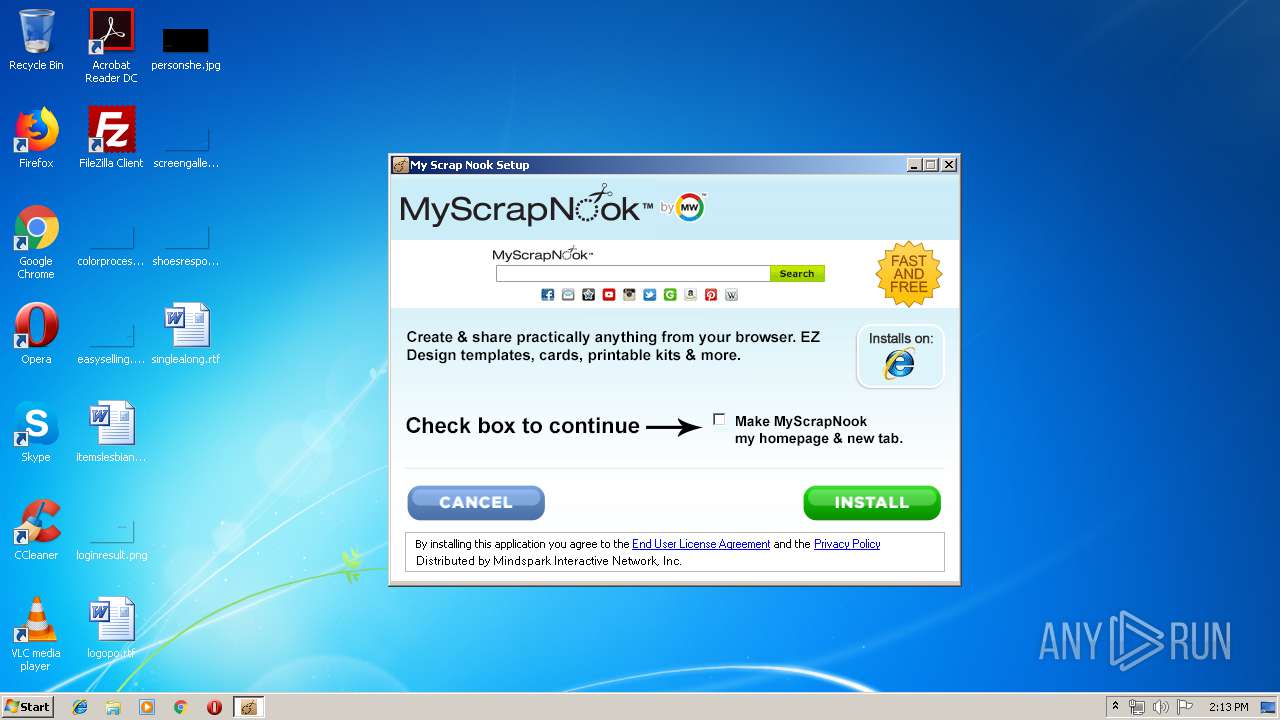
| Verdict: | Malicious activity |
| Analysis date: | May 23, 2019, 13:13:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | B5AF25DF9697AAEAAACD983860B0720B |
| SHA1: | 2D6866768301770D0D7FB071908936D598D08C66 |
| SHA256: | A5E3A99BF5B606E41C8EDD21100B53FF4E309AB7552CE619270B1EF43C1DFB1C |
| SSDEEP: | 6144:fbUTp1rg0uRgM+zsT8qEJEbrPBj3AGQvCdWYDbHIae+0U/aM4tp5iFw2E9:fIbgbwJ2arasspeuSLp5ief9 |
MALICIOUS
Changes settings of System certificates
- myscrapnook.2e46c764e10b400194a90bdd9fdea621.exe (PID: 3548)
Loads dropped or rewritten executable
- myscrapnook.2e46c764e10b400194a90bdd9fdea621.exe (PID: 3548)
SUSPICIOUS
Executable content was dropped or overwritten
- myscrapnook.2e46c764e10b400194a90bdd9fdea621.exe (PID: 3548)
Creates files in the user directory
- myscrapnook.2e46c764e10b400194a90bdd9fdea621.exe (PID: 3548)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:12:25 06:01:44+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 186368 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x3229 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.7.1.3000 |
| ProductVersionNumber: | 2.7.1.3000 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
| Comments: | http://www.mindspark.com |
| CompanyName: | Mindspark Interactive Network, Inc. |
| FileDescription: | My Scrap Nook Setup |
| FileVersion: | 2.7.1.3000 |
| InternalName: | My Scrap Nook |
| LegalCopyright: | © 2015 Mindspark Interactive Network, Inc. An IAC Company. All rights reserved. |
| LegalTrademarks: | ® & ™ Mindspark Interactive Network, Inc. An IAC Company. All rights reserved. |
| ProductName: | My Scrap Nook |
| ProductVersion: | 2.7.1.3000 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Dec-2013 05:01:44 |
| Detected languages: |
|
| Comments: | http://www.mindspark.com |
| CompanyName: | Mindspark Interactive Network, Inc. |
| FileDescription: | My Scrap Nook Setup |
| FileVersion: | 2.7.1.3000 |
| InternalName: | My Scrap Nook |
| LegalCopyright: | © 2015 Mindspark Interactive Network, Inc. An IAC Company. All rights reserved. |
| LegalTrademarks: | ® & ™ Mindspark Interactive Network, Inc. An IAC Company. All rights reserved. |
| ProductName: | My Scrap Nook |
| ProductVersion: | 2.7.1.3000 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 25-Dec-2013 05:01:44 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000606C | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45707 |
.rdata | 0x00008000 | 0x00001460 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.94596 |
.data | 0x0000A000 | 0x0002AF98 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.79535 |
.ndata | 0x00035000 | 0x00055000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0008A000 | 0x00003440 | 0x00003600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.04648 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.31253 | 1118 | UNKNOWN | English - United States | RT_MANIFEST |
103 | 1.91924 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.89384 | 248 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.89887 | 238 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
32
Monitored processes
1
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3548 | "C:\Users\admin\AppData\Local\Temp\myscrapnook.2e46c764e10b400194a90bdd9fdea621.exe" | C:\Users\admin\AppData\Local\Temp\myscrapnook.2e46c764e10b400194a90bdd9fdea621.exe | explorer.exe | ||||||||||||
User: admin Company: Mindspark Interactive Network, Inc. Integrity Level: MEDIUM Description: My Scrap Nook Setup Exit code: 0 Version: 2.7.1.3000 Modules
| |||||||||||||||
Total events
391
Read events
362
Write events
29
Delete events
0
Modification events
| (PID) Process: | (3548) myscrapnook.2e46c764e10b400194a90bdd9fdea621.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\myscrapnook_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3548) myscrapnook.2e46c764e10b400194a90bdd9fdea621.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\myscrapnook_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3548) myscrapnook.2e46c764e10b400194a90bdd9fdea621.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\myscrapnook_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3548) myscrapnook.2e46c764e10b400194a90bdd9fdea621.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\myscrapnook_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3548) myscrapnook.2e46c764e10b400194a90bdd9fdea621.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\myscrapnook_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3548) myscrapnook.2e46c764e10b400194a90bdd9fdea621.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\myscrapnook_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3548) myscrapnook.2e46c764e10b400194a90bdd9fdea621.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\myscrapnook_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3548) myscrapnook.2e46c764e10b400194a90bdd9fdea621.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\myscrapnook_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3548) myscrapnook.2e46c764e10b400194a90bdd9fdea621.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\myscrapnook_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3548) myscrapnook.2e46c764e10b400194a90bdd9fdea621.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\myscrapnook_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
4
Suspicious files
1
Text files
9
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3548 | myscrapnook.2e46c764e10b400194a90bdd9fdea621.exe | C:\Users\admin\AppData\Local\Temp\nsg41DF.tmp\secondary_bg.png | image | |
MD5:— | SHA256:— | |||
| 3548 | myscrapnook.2e46c764e10b400194a90bdd9fdea621.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\A2ECA083537A02B6158458FF1752C63F | binary | |
MD5:— | SHA256:— | |||
| 3548 | myscrapnook.2e46c764e10b400194a90bdd9fdea621.exe | C:\Users\admin\AppData\Local\Temp\nsg41DF.tmp\System.dll | executable | |
MD5:7399323923E3946FE9140132AC388132 | SHA256:5A1C20A3E2E2EB182976977669F2C5D9F3104477E98F74D69D2434E79B92FDC3 | |||
| 3548 | myscrapnook.2e46c764e10b400194a90bdd9fdea621.exe | C:\Users\admin\AppData\Local\Temp\nsg41DF.tmp\Install_ENG_1435268357767.bmp | image | |
MD5:7078777F775A58435028C19515955085 | SHA256:DF2BD2E2781DAA4D3270FF3BAC2CFAE49FCB42E2A331D10F4F0CBDA2E3B1DDDC | |||
| 3548 | myscrapnook.2e46c764e10b400194a90bdd9fdea621.exe | C:\Users\admin\AppData\Local\Temp\nsg41DF.tmp\secondary_accept.png | image | |
MD5:— | SHA256:— | |||
| 3548 | myscrapnook.2e46c764e10b400194a90bdd9fdea621.exe | C:\Users\admin\AppData\Local\Temp\nsg41DF.tmp\installerParams | text | |
MD5:— | SHA256:— | |||
| 3548 | myscrapnook.2e46c764e10b400194a90bdd9fdea621.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\installerParams[1].jhtml | text | |
MD5:— | SHA256:— | |||
| 3548 | myscrapnook.2e46c764e10b400194a90bdd9fdea621.exe | C:\Users\admin\AppData\Local\Temp\nsg41DF.tmp\secondary_decline.png | image | |
MD5:— | SHA256:— | |||
| 3548 | myscrapnook.2e46c764e10b400194a90bdd9fdea621.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\DriverUpdate-Downloader[1].exe | executable | |
MD5:— | SHA256:— | |||
| 3548 | myscrapnook.2e46c764e10b400194a90bdd9fdea621.exe | C:\Users\admin\AppData\Local\Temp\nsg41DF.tmp\SlimCleanerPlus.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
7
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3548 | myscrapnook.2e46c764e10b400194a90bdd9fdea621.exe | GET | 200 | 104.111.245.93:80 | http://cert.int-x3.letsencrypt.org/ | NL | der | 1.15 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3548 | myscrapnook.2e46c764e10b400194a90bdd9fdea621.exe | 74.113.237.192:443 | anx.mindspark.com | Mindspark Interactive Network, Inc. | US | malicious |
3548 | myscrapnook.2e46c764e10b400194a90bdd9fdea621.exe | 35.244.218.203:443 | dp.tb.ask.com | — | US | whitelisted |
3548 | myscrapnook.2e46c764e10b400194a90bdd9fdea621.exe | 104.111.245.93:80 | cert.int-x3.letsencrypt.org | Akamai International B.V. | NL | whitelisted |
3548 | myscrapnook.2e46c764e10b400194a90bdd9fdea621.exe | 2.18.232.251:443 | ak.ssl.imgfarm.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
anx.mindspark.com |
| whitelisted |
dp.tb.ask.com |
| whitelisted |
cert.int-x3.letsencrypt.org |
| whitelisted |
ak.ssl.imgfarm.com |
| whitelisted |