| File name: | winhelp.wll |
| Full analysis: | https://app.any.run/tasks/faf63c89-180d-4894-8927-9d99af0b8e14 |
| Verdict: | Malicious activity |
| Analysis date: | February 22, 2019, 10:36:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows |
| MD5: | 3F57B0B235A0E3669DEACA39468E1E30 |
| SHA1: | CB3D32ED72000A403A4136DD16A0BE385E215083 |
| SHA256: | A5D8CAE9DE9EDF81D4898879B09C16D6AFD12F1BDC320ACDBC5C8A430831E55B |
| SSDEEP: | 6144:GODt/l2jddF/b6h2n5oHuF/8r2Ni+wYHF3LFU+1JSVQJ+01VuC8kE/tlA:zDt/Mdm2nKHuV8rcrPHFbFU+KX4Ste |
MALICIOUS
Loads dropped or rewritten executable
- explorer.exe (PID: 116)
- svchost.exe (PID: 844)
- cfgwiz.exe (PID: 3472)
Application was dropped or rewritten from another process
- cfgwiz.exe (PID: 3472)
- cfgwiz.exe (PID: 2140)
Uses SVCHOST.EXE for hidden code execution
- cfgwiz.exe (PID: 2140)
- svchost.exe (PID: 3320)
- svchost.exe (PID: 3752)
- svchost.exe (PID: 2496)
- svchost.exe (PID: 2816)
Changes the autorun value in the registry
- svchost.exe (PID: 3320)
SUSPICIOUS
Executable content was dropped or overwritten
- rundll32.exe (PID: 2936)
- cfgwiz.exe (PID: 3472)
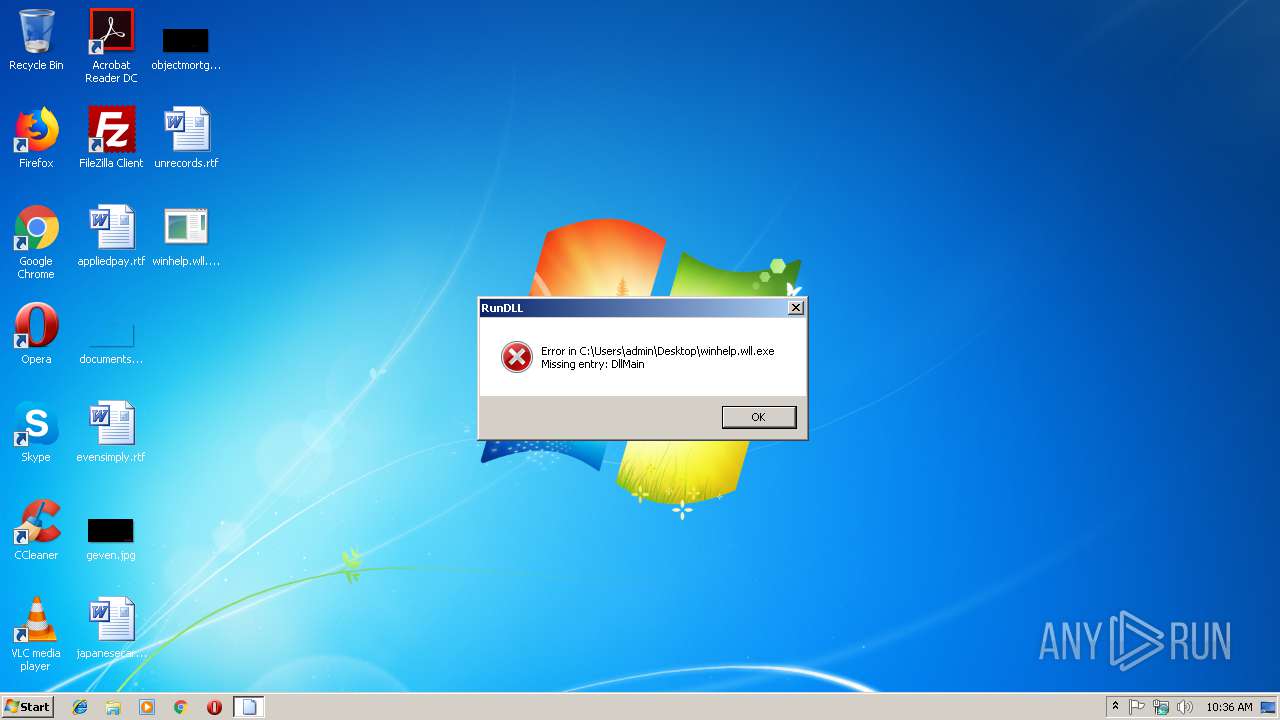
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 116)
Creates files in the program directory
- rundll32.exe (PID: 2936)
Application launched itself
- svchost.exe (PID: 3752)
- svchost.exe (PID: 2816)
INFO
Loads main object executable
- rundll32.exe (PID: 2936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:02:21 10:55:58+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 43008 |
| InitializedDataSize: | 26624 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3374 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-Feb-2019 09:55:58 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 21-Feb-2019 09:55:58 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000A7EB | 0x0000A800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.53539 |
.rdata | 0x0000C000 | 0x00003B1E | 0x00003C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.80153 |
.data | 0x00010000 | 0x00002EE8 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.4881 |
.rsrc | 0x00013000 | 0x000001B4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.10724 |
.reloc | 0x00014000 | 0x00001690 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 3.85347 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
2 | 4.79597 | 346 | Latin 1 / Western European | English - United States | RT_MANIFEST |
Imports
KERNEL32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
Total processes
38
Monitored processes
10
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 844 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2140 | C:\ProgramData\cfgwiz\cfgwiz.exe | C:\ProgramData\cfgwiz\cfgwiz.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft SharePoint and FrontPage Server Administrator Snapin Exit code: 0 Version: 10.0.5012 Modules
| |||||||||||||||
| 2496 | 1 | C:\Windows\system32\svchost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2816 | 1 2 3 | C:\Windows\system32\svchost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2936 | "C:\Windows\System32\rundll32.exe" "C:\Users\admin\Desktop\winhelp.wll.exe", DllMain | C:\Windows\System32\rundll32.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3320 | 1 2 | C:\Windows\system32\svchost.exe | cfgwiz.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3472 | C:\ProgramData\xsada\cfgwiz.exe USER-PC | C:\ProgramData\xsada\cfgwiz.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft SharePoint and FrontPage Server Administrator Snapin Exit code: 0 Version: 10.0.5012 Modules
| |||||||||||||||
| 3752 | 1 2 3 | C:\Windows\system32\svchost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3844 | 1 | C:\Windows\system32\svchost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
885
Read events
871
Write events
14
Delete events
0
Modification events
| (PID) Process: | (3752) svchost.exe | Key: | HKEY_CLASSES_ROOT\x86 Family 6 Model 94 Stepping 3-ll37389743nxshkhjhgee |
| Operation: | write | Name: | 1 |
Value: F7461515C3B20A65ABD9890A3E859E12 | |||
| (PID) Process: | (3752) svchost.exe | Key: | HKEY_CLASSES_ROOT\x86 Family 6 Model 94 Stepping 3-ll37389743nxshkhjhgee |
| Operation: | write | Name: | 2 |
Value: DA6D328B1B33F23F2615451F76F9C4D2 | |||
| (PID) Process: | (3752) svchost.exe | Key: | HKEY_CLASSES_ROOT\x86 Family 6 Model 94 Stepping 3-ll37389743nxshkhjhgee |
| Operation: | write | Name: | 3 |
Value: 06C6BF3D0C4F20EA4065BC60A4CD761EF44D58F149D51A69 | |||
| (PID) Process: | (3752) svchost.exe | Key: | HKEY_CLASSES_ROOT\x86 Family 6 Model 94 Stepping 3-ll37389743nxshkhjhgee |
| Operation: | write | Name: | 4 |
Value: BAC81B51CFA10E43117F9125AC8FA1437F224B6A034C99B5 | |||
| (PID) Process: | (3752) svchost.exe | Key: | HKEY_CLASSES_ROOT\x86 Family 6 Model 94 Stepping 3-ll37389743nxshkhjhgee |
| Operation: | write | Name: | 5 |
Value: CB738C49A5402E44D4CAAB3424ECD8FE | |||
| (PID) Process: | (3752) svchost.exe | Key: | HKEY_CLASSES_ROOT\x86 Family 6 Model 94 Stepping 3-ll37389743nxshkhjhgee |
| Operation: | write | Name: | 6 |
Value: BE67FDE236F0A6E63844D02891EE091CA7A2866A58A890F6 | |||
| (PID) Process: | (3752) svchost.exe | Key: | HKEY_CLASSES_ROOT\x86 Family 6 Model 94 Stepping 3-ll37389743nxshkhjhgee |
| Operation: | write | Name: | 7 |
Value: BE67FDE236F0A6E63844D02891EE091CA7A2866A58A890F6 | |||
| (PID) Process: | (3752) svchost.exe | Key: | HKEY_CLASSES_ROOT\x86 Family 6 Model 94 Stepping 3-ll37389743nxshkhjhgee |
| Operation: | write | Name: | 8 |
Value: E30B4874BE396F1DBF1CD851CC199184190308B072C2B1B5 | |||
| (PID) Process: | (3752) svchost.exe | Key: | HKEY_CLASSES_ROOT\x86 Family 6 Model 94 Stepping 3-ll37389743nxshkhjhgee |
| Operation: | write | Name: | 10 |
Value: 6FBDC113AB7A9D15 | |||
| (PID) Process: | (3752) svchost.exe | Key: | HKEY_CLASSES_ROOT\x86 Family 6 Model 94 Stepping 3-ll37389743nxshkhjhgee |
| Operation: | write | Name: | 12 |
Value: FF961FE48EF1FA80B8C38139EEDDAE8B | |||
Executable files
4
Suspicious files
2
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3472 | cfgwiz.exe | \Device\HarddiskVolume2\ProgramData\cfgwiz\GvG36a467C6Hkea | — | |
MD5:— | SHA256:— | |||
| 844 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
| 3752 | svchost.exe | C:\ProgramData\cfgwiz\GvG36a467C6Hkea | binary | |
MD5:— | SHA256:— | |||
| 2936 | rundll32.exe | C:\ProgramData\xsada\cfgwiz.exe | executable | |
MD5:F0747A5FCBE6873AD74B073E3AA70E8F | SHA256:D1B7093EB66D103DACE02B27F7E137873FDBFC1C9661E9850CD2A36A7807D92C | |||
| 2936 | rundll32.exe | C:\ProgramData\xsada\GvG36a467C6Hkea | binary | |
MD5:6A9A4DA3F7B2075984F79F67E4EB2F28 | SHA256:AB6998352FC0D745AF94F02E42F8C3F061A99179FCE2C890760F293F9744D1E8 | |||
| 3472 | cfgwiz.exe | C:\ProgramData\cfgwiz\cfgwiz.exe | executable | |
MD5:F0747A5FCBE6873AD74B073E3AA70E8F | SHA256:D1B7093EB66D103DACE02B27F7E137873FDBFC1C9661E9850CD2A36A7807D92C | |||
| 2936 | rundll32.exe | C:\ProgramData\xsada\FPMMC.dll | executable | |
MD5:113044788A356AAB6C693A3E80189141 | SHA256:1AC0BE7D289F2BBD00979069B9D3BF6AC76C0828C0CA7674EC791CDB463B8FF0 | |||
| 3472 | cfgwiz.exe | C:\ProgramData\cfgwiz\FPMMC.DLL | executable | |
MD5:113044788A356AAB6C693A3E80189141 | SHA256:1AC0BE7D289F2BBD00979069B9D3BF6AC76C0828C0CA7674EC791CDB463B8FF0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3752 | svchost.exe | 139.59.81.253:443 | — | Digital Ocean, Inc. | IN | unknown |
3844 | svchost.exe | 139.59.81.253:443 | — | Digital Ocean, Inc. | IN | unknown |
2816 | svchost.exe | 139.59.81.253:443 | — | Digital Ocean, Inc. | IN | unknown |
DNS requests
Threats
Process | Message |
|---|---|
rundll32.exe | [test] C:\ProgramData\xsada\cfgwiz.exe USER-PC |
svchost.exe | [Defender]System Start |
svchost.exe | [Defender]Start |
svchost.exe | mydebugview::FireConnect -26880 |