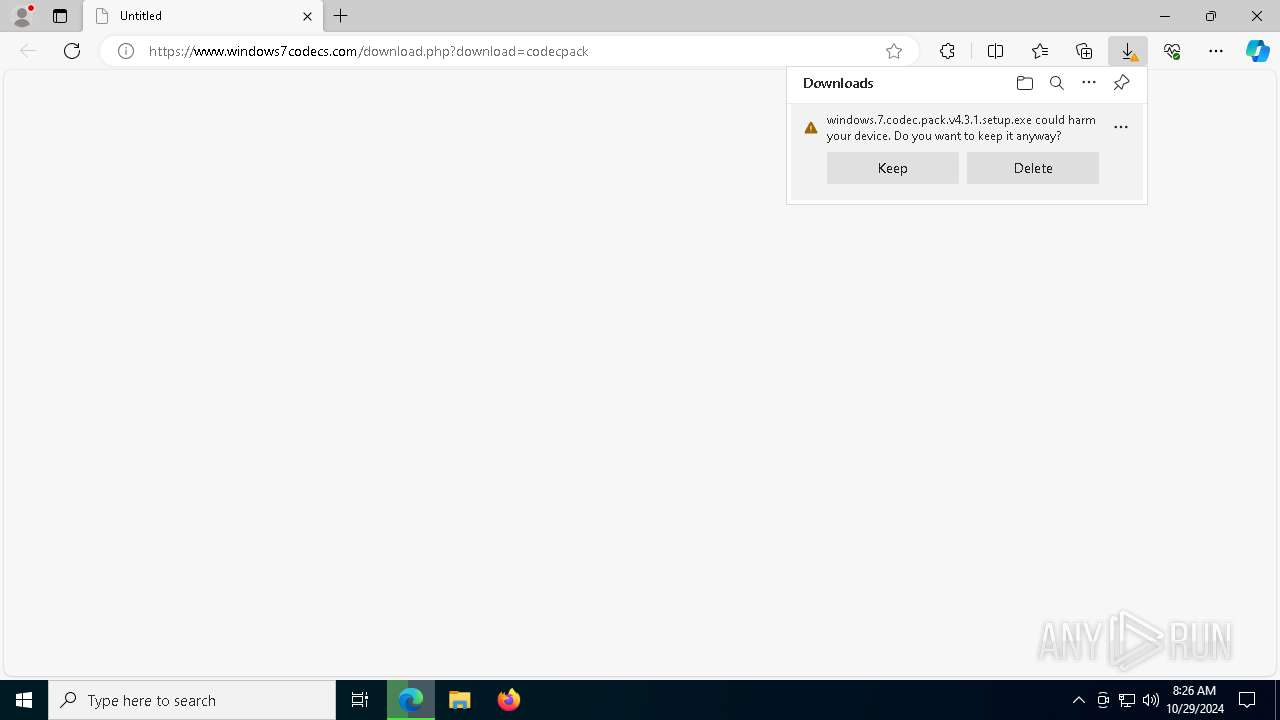
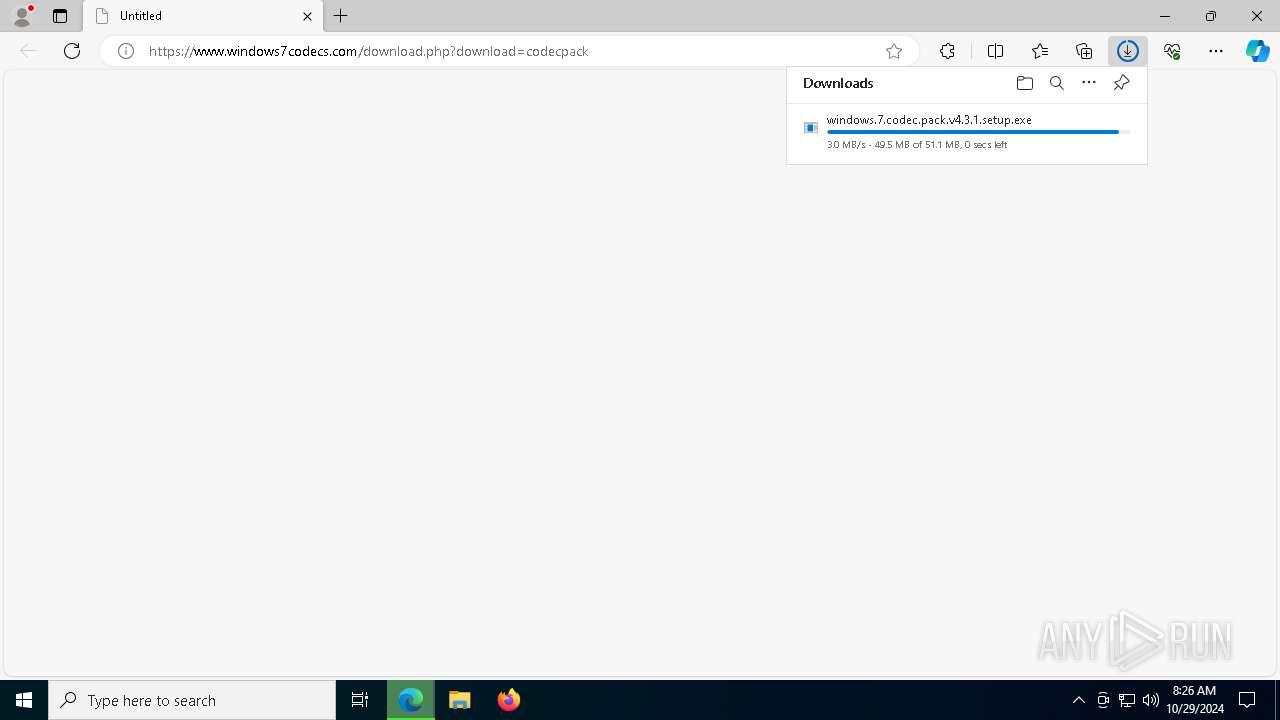
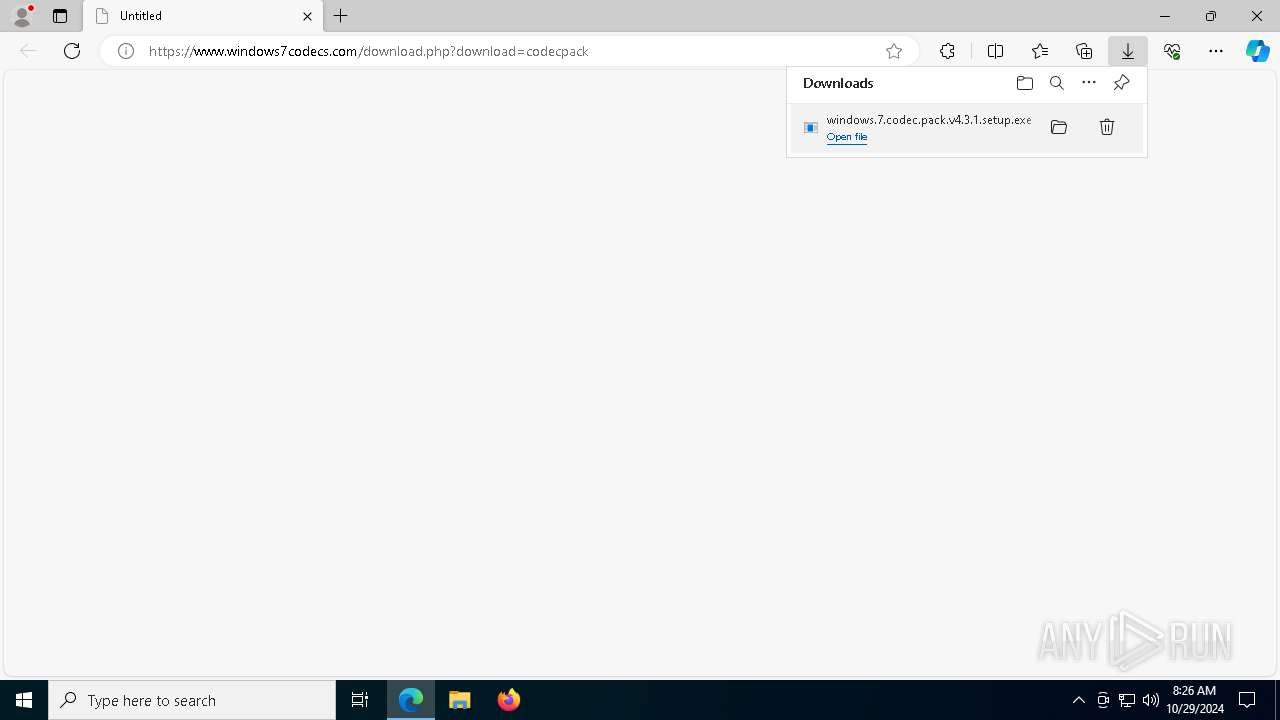
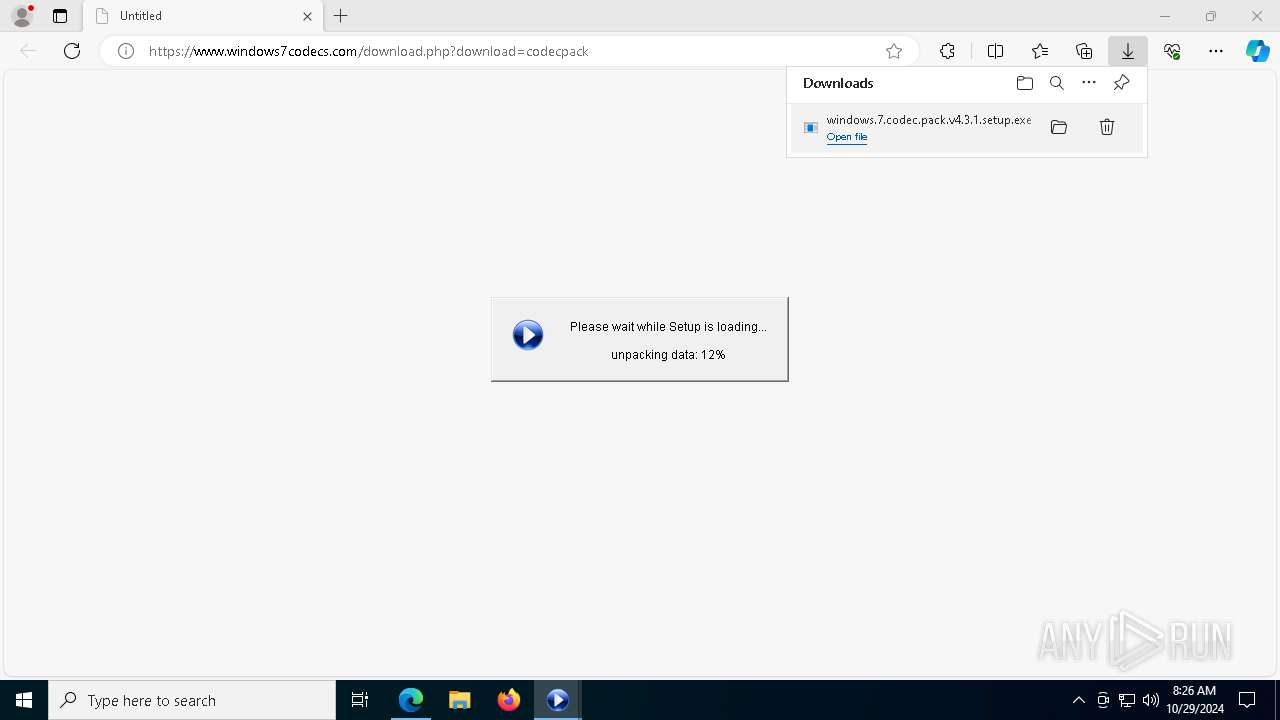
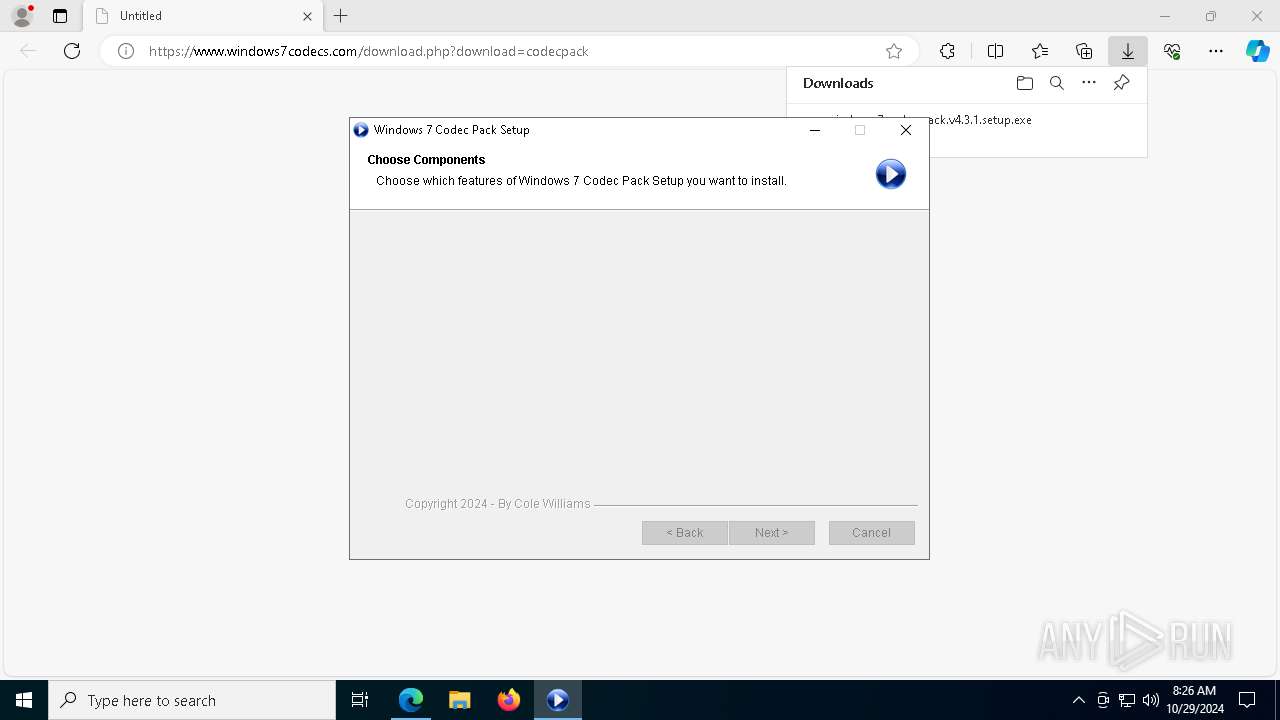
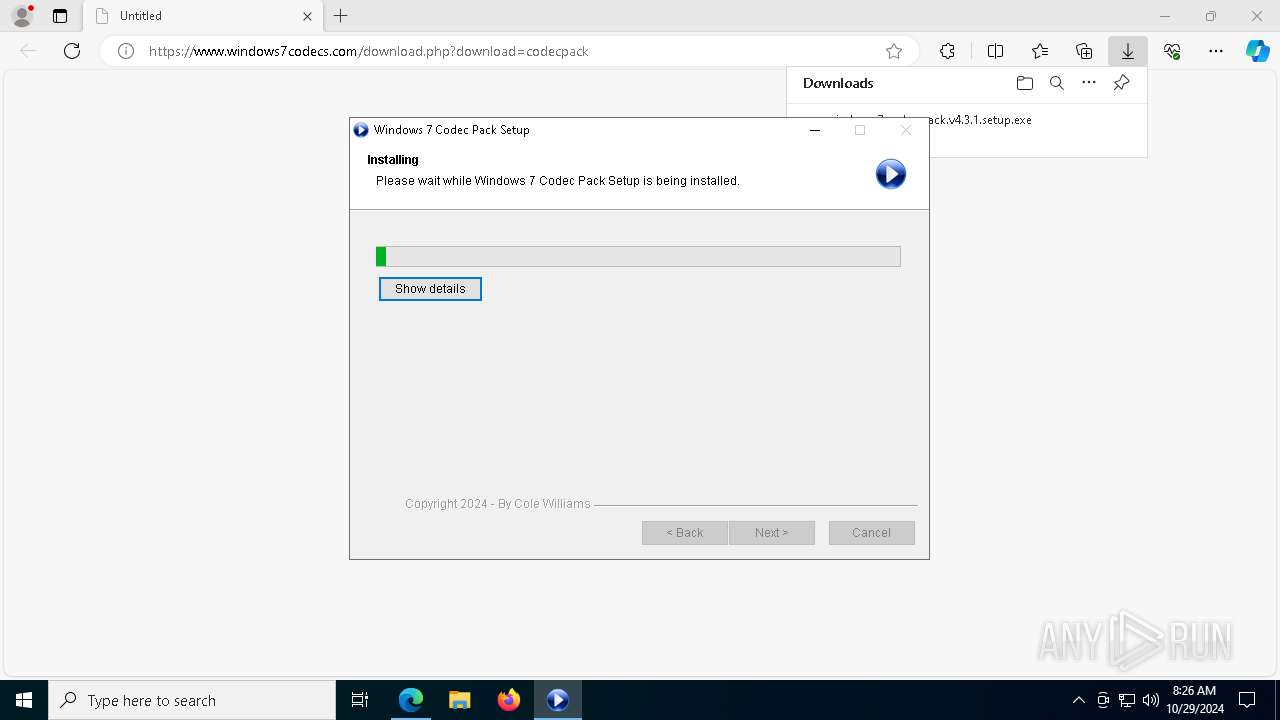
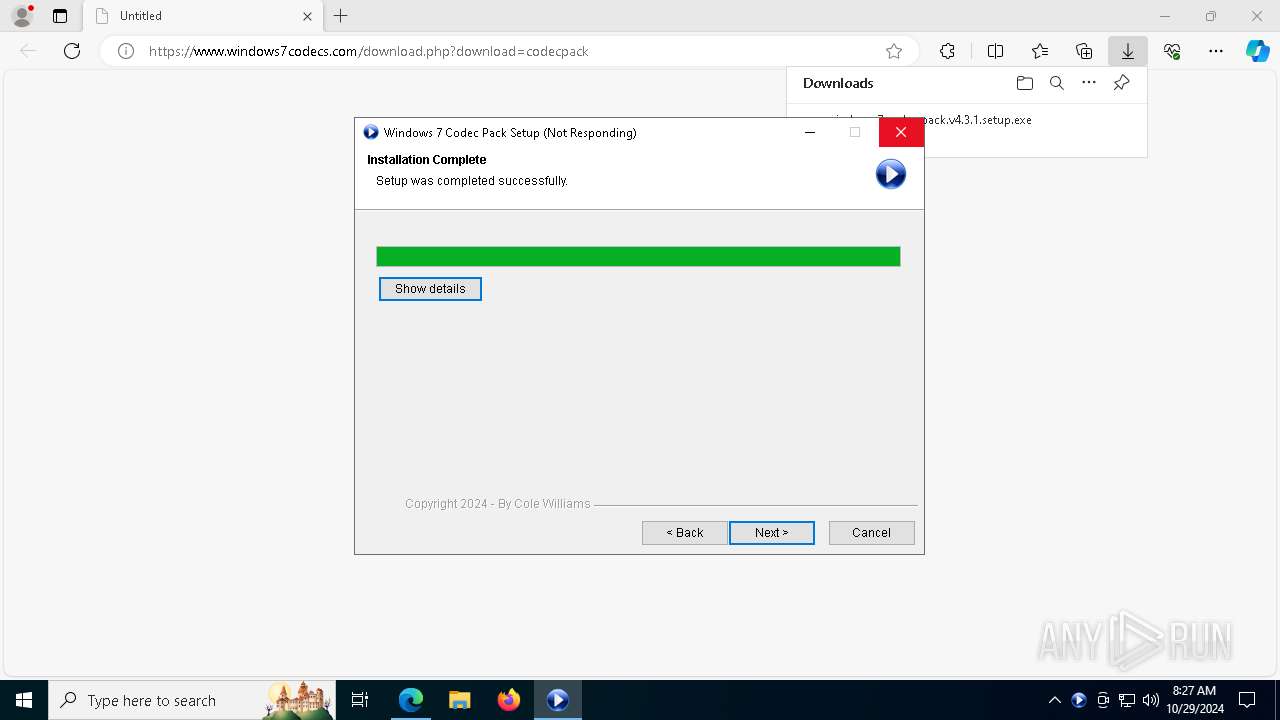
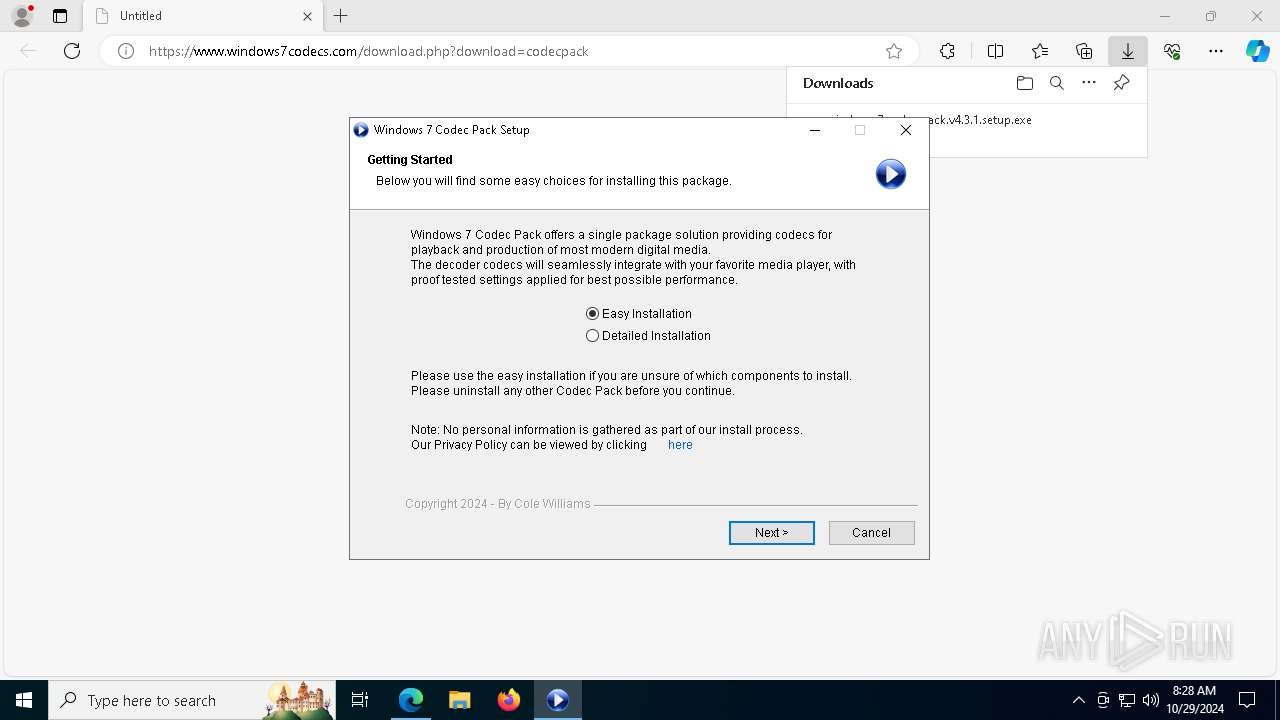
| URL: | https://www.windows7codecs.com/download.php?download=codecpack |
| Full analysis: | https://app.any.run/tasks/90178c4f-a807-4b3b-908b-b979a62d4b7a |
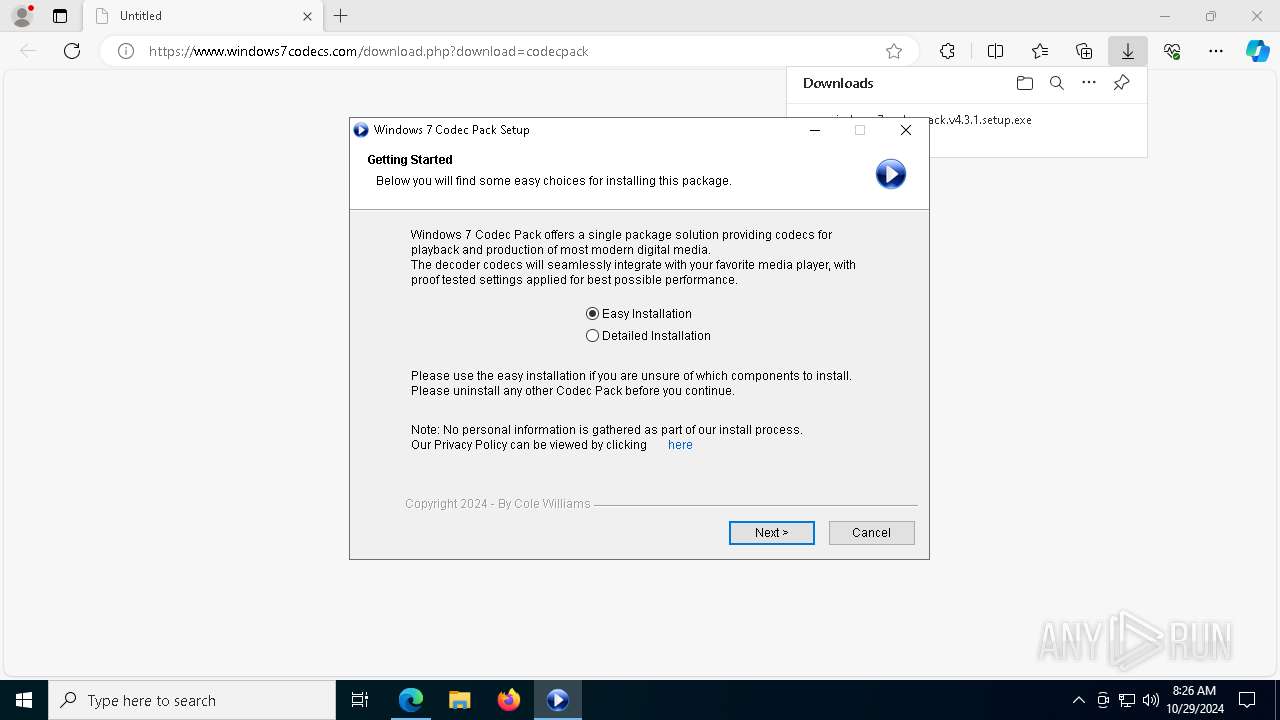
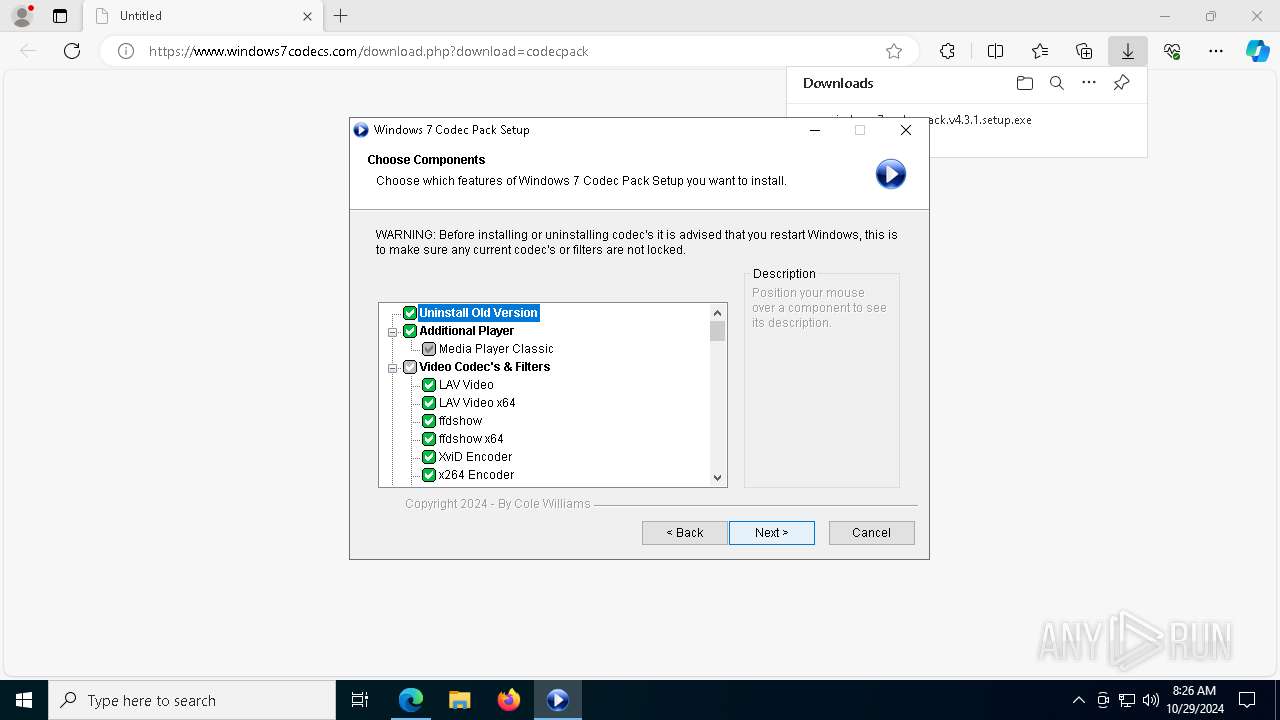
| Verdict: | Malicious activity |
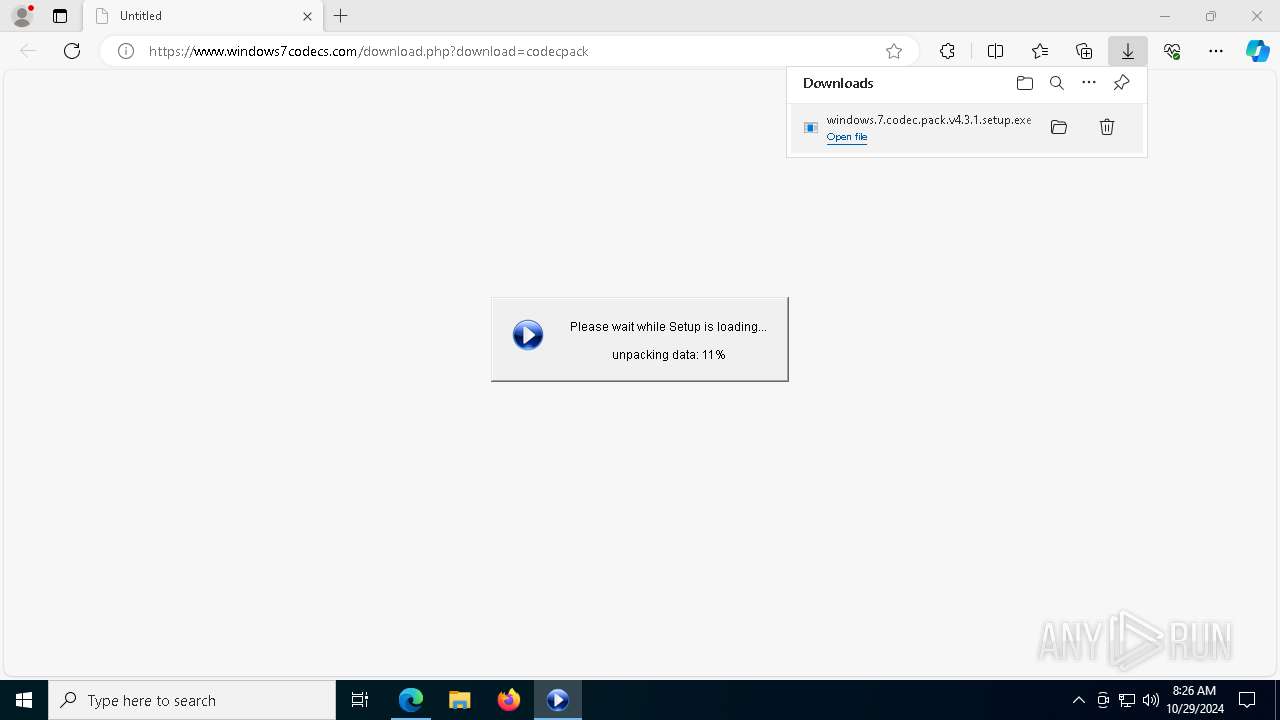
| Analysis date: | October 29, 2024, 08:26:09 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | B54F630C773221C83684DEDCCFE4F6C5 |
| SHA1: | D3ADC85B65065BA9E024EA2B84DD8926CA4B88F3 |
| SHA256: | A5D1F97422CE278E6D0F9A6B8F0FE5AC7A37DE970A83E4FD33CD5C479C55EF6B |
| SSDEEP: | 3:N8DSLkajMdIaKK/FGGWn:2OLkawKBKkVn |
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- windows.7.codec.pack.v4.3.1.setup.exe (PID: 7420)
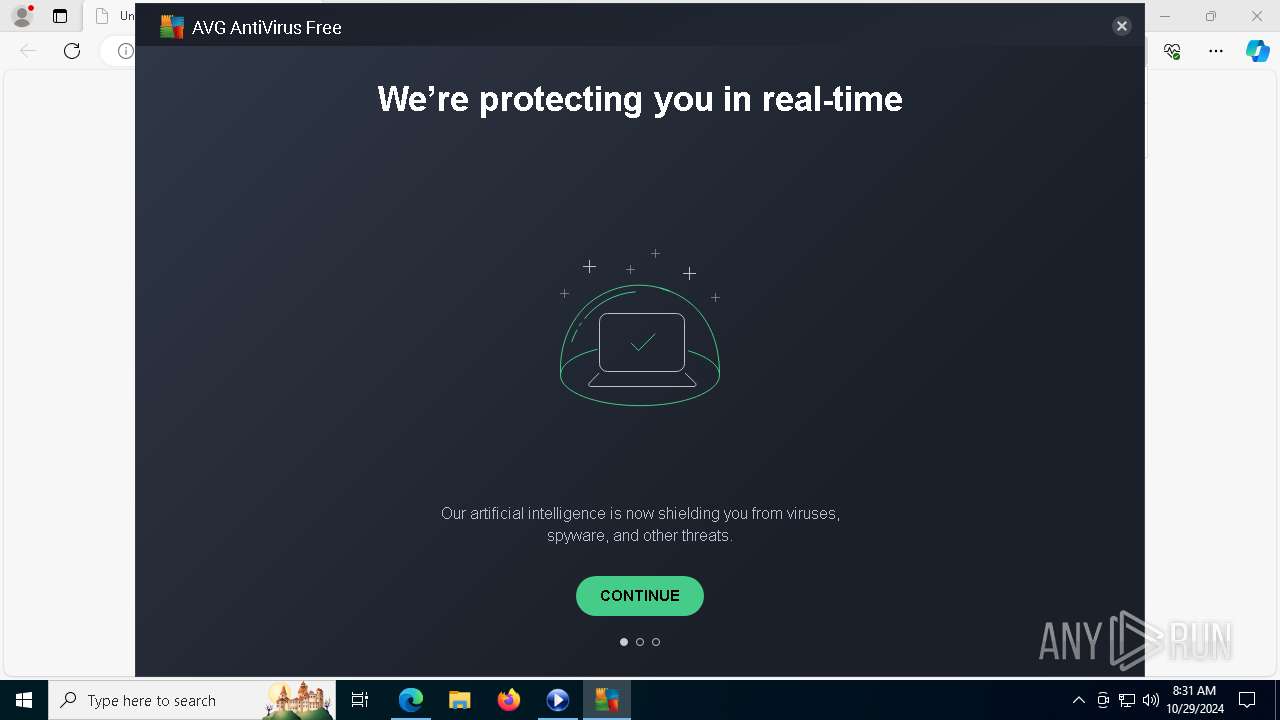
Antivirus name has been found in the command line (generic signature)
- AVGUI.exe (PID: 7888)
- AVGUI.exe (PID: 9628)
- AVGUI.exe (PID: 3532)
- AVGUI.exe (PID: 7684)
- AVGUI.exe (PID: 9132)
- AVGUI.exe (PID: 5476)
SUSPICIOUS
Executable content was dropped or overwritten
- windows.7.codec.pack.v4.3.1.setup.exe (PID: 7848)
- avg_antivirus_free_setup.exe (PID: 5184)
- icarus.exe (PID: 6308)
- icarus.exe (PID: 7096)
- saBSI.exe (PID: 2576)
- installer.exe (PID: 7228)
- installer.exe (PID: 948)
- avg_antivirus_free_online_setup.exe (PID: 6320)
- windows.7.codec.pack.v4.3.1.setup.exe (PID: 8596)
- windows.7.codec.pack.v4.3.1.setup.exe (PID: 9012)
- windows.7.codec.pack.v4.3.1.setup.exe (PID: 7420)
- AvEmUpdate.exe (PID: 6344)
- icarus.exe (PID: 7388)
- AVGSvc.exe (PID: 7532)
- aswOfferTool.exe (PID: 9836)
- engsup.exe (PID: 8560)
Malware-specific behavior (creating "System.dll" in Temp)
- windows.7.codec.pack.v4.3.1.setup.exe (PID: 7420)
- windows.7.codec.pack.v4.3.1.setup.exe (PID: 7848)
- windows.7.codec.pack.v4.3.1.setup.exe (PID: 9012)
- windows.7.codec.pack.v4.3.1.setup.exe (PID: 8596)
Process drops legitimate windows executable
- windows.7.codec.pack.v4.3.1.setup.exe (PID: 7420)
- installer.exe (PID: 7228)
- icarus.exe (PID: 7096)
The process drops C-runtime libraries
- windows.7.codec.pack.v4.3.1.setup.exe (PID: 7420)
- icarus.exe (PID: 7096)
Starts itself from another location
- icarus.exe (PID: 6308)
Executes as Windows Service
- servicehost.exe (PID: 7444)
- AVGSvc.exe (PID: 7532)
- avgToolsSvc.exe (PID: 8500)
- aswidsagent.exe (PID: 6236)
- wsc_proxy.exe (PID: 7488)
- afwServ.exe (PID: 5932)
Starts CMD.EXE for commands execution
- servicehost.exe (PID: 7444)
- updater.exe (PID: 8716)
Hides command output
- cmd.exe (PID: 8760)
Drops a system driver (possible attempt to evade defenses)
- icarus.exe (PID: 7096)
- engsup.exe (PID: 8560)
Application launched itself
- AVGUI.exe (PID: 9132)
INFO
Application launched itself
- msedge.exe (PID: 4032)
Executable content was dropped or overwritten
- msedge.exe (PID: 2100)
- msedge.exe (PID: 4032)
Manual execution by a user
- AVGUI.exe (PID: 9132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
556
Monitored processes
415
Malicious processes
4
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 512 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2812 --field-trial-handle=2436,i,6798690452234944823,14176291115615664308,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 540 | C:\WINDOWS\system32\Codecs\SetACL.exe -on HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\DirectShow\Preferred -ot reg -actn ace -ace n:S-1-5-32-544;s:y;p:full -silent | C:\Windows\SysWOW64\Codecs\SetACL.exe | — | windows.7.codec.pack.v4.3.1.setup.exe | |||||||||||
User: admin Company: Helge Klein Integrity Level: HIGH Description: SetACL 3 Exit code: 0 Version: 3.0.6.0 Modules
| |||||||||||||||
| 540 | C:\WINDOWS\system32\Codecs\SetACL.exe -on HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Wow6432Node\MediaFoundation\MediaSources\Preferred -ot reg -actn setowner -ownr n:S-1-5-80-956008885-3418522649-1831038044-1853292631-2271478464;s:y -silent | C:\Windows\SysWOW64\Codecs\SetACL.exe | — | windows.7.codec.pack.v4.3.1.setup.exe | |||||||||||
User: admin Company: Helge Klein Integrity Level: HIGH Description: SetACL 3 Exit code: 0 Version: 3.0.6.0 Modules
| |||||||||||||||
| 540 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SetACL.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 712 | C:\WINDOWS\system32\Codecs\SetACL.exe -on HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\DirectShow\Preferred -ot reg -actn setowner -ownr n:S-1-5-32-544;s:y -silent | C:\Windows\SysWOW64\Codecs\SetACL.exe | — | windows.7.codec.pack.v4.3.1.setup.exe | |||||||||||
User: admin Company: Helge Klein Integrity Level: HIGH Description: SetACL 3 Exit code: 0 Version: 3.0.6.0 Modules
| |||||||||||||||
| 712 | C:\WINDOWS\system32\Codecs\SetACL.exe -on HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Wow6432Node\MediaFoundation\MediaSources\Preferred -ot reg -actn ace -ace n:S-1-5-32-544;s:y;p:full -silent | C:\Windows\SysWOW64\Codecs\SetACL.exe | — | windows.7.codec.pack.v4.3.1.setup.exe | |||||||||||
User: admin Company: Helge Klein Integrity Level: HIGH Description: SetACL 3 Exit code: 0 Version: 3.0.6.0 Modules
| |||||||||||||||
| 712 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SetACL.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 712 | C:\WINDOWS\system32\Codecs\SetACL.exe -on "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Foundation\ByteStreamHandlers\.mp4" -ot reg -actn ace -ace n:S-1-5-32-544;s:y;p:read -silent | C:\Windows\SysWOW64\Codecs\SetACL.exe | — | windows.7.codec.pack.v4.3.1.setup.exe | |||||||||||
User: admin Company: Helge Klein Integrity Level: HIGH Description: SetACL 3 Exit code: 25 Version: 3.0.6.0 | |||||||||||||||
| 948 | "C:\Users\admin\AppData\Local\Temp\MPCP_FS_files\\installer.exe" /setOem:Affid=91082 /s /thirdparty /upgrade | C:\Users\admin\AppData\Local\Temp\MPCP_FS_files\installer.exe | saBSI.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1172 | C:\WINDOWS\system32\Codecs\SetACL.exe -on HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Wow6432Node\MediaFoundation\MediaSources\DoNotUse -ot reg -actn ace -ace n:S-1-5-32-544;s:y;p:read -silent | C:\Windows\SysWOW64\Codecs\SetACL.exe | — | windows.7.codec.pack.v4.3.1.setup.exe | |||||||||||
User: admin Company: Helge Klein Integrity Level: HIGH Description: SetACL 3 Exit code: 25 Version: 3.0.6.0 Modules
| |||||||||||||||
Total events
31 698
Read events
23 510
Write events
8 142
Delete events
46
Modification events
| (PID) Process: | (4032) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4032) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4032) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4032) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4032) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 79622E9F2F842F00 | |||
| (PID) Process: | (4032) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: B1F8369F2F842F00 | |||
| (PID) Process: | (4032) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459414 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {3F8B846D-DD49-4823-9195-3B2DB54FC7A1} | |||
| (PID) Process: | (4032) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459414 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {94A52BCA-190E-4078-9BE4-0271C2213FFF} | |||
| (PID) Process: | (4032) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 08EE529F2F842F00 | |||
| (PID) Process: | (4032) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
1 129
Suspicious files
2 276
Text files
1 249
Unknown types
43
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF8b5bc.TMP | — | |
MD5:— | SHA256:— | |||
| 4032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF8b5bc.TMP | — | |
MD5:— | SHA256:— | |||
| 4032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF8b5bc.TMP | — | |
MD5:— | SHA256:— | |||
| 4032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF8b5cc.TMP | — | |
MD5:— | SHA256:— | |||
| 4032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF8b5cc.TMP | — | |
MD5:— | SHA256:— | |||
| 4032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
88
TCP/UDP connections
395
DNS requests
320
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2776 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7476 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8016 | svchost.exe | HEAD | 200 | 23.50.131.71:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/181d62d0-8e71-4ab0-b6f0-62f746749689?P1=1730374005&P2=404&P3=2&P4=id0fnqSvMQkHpzSwKZKKp2fJejFjychMPucY1tsqUol53RMqT3X9S87GMTa%2bliTILnkEX2tmI6M5AwG5vu8YIg%3d%3d | unknown | — | — | whitelisted |
7868 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5184 | avg_antivirus_free_setup.exe | POST | 200 | 172.217.16.206:80 | http://www.google-analytics.com/collect | unknown | — | — | whitelisted |
8016 | svchost.exe | GET | 206 | 23.50.131.71:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/181d62d0-8e71-4ab0-b6f0-62f746749689?P1=1730374005&P2=404&P3=2&P4=id0fnqSvMQkHpzSwKZKKp2fJejFjychMPucY1tsqUol53RMqT3X9S87GMTa%2bliTILnkEX2tmI6M5AwG5vu8YIg%3d%3d | unknown | — | — | whitelisted |
8016 | svchost.exe | HEAD | 200 | 23.50.131.71:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1730370402&P2=404&P3=2&P4=R2fM1i3whZ5KxNPtEt%2fT9NP4VpPgyRSzP4TWMnbpUZgwFc01RTVxc5cLYTnLDrNCSnC8x5zCzNs2C%2bGbP2QL3w%3d%3d | unknown | — | — | whitelisted |
5184 | avg_antivirus_free_setup.exe | POST | 200 | 172.217.16.206:80 | http://www.google-analytics.com/collect | unknown | — | — | whitelisted |
8016 | svchost.exe | GET | 206 | 23.50.131.71:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/181d62d0-8e71-4ab0-b6f0-62f746749689?P1=1730374005&P2=404&P3=2&P4=id0fnqSvMQkHpzSwKZKKp2fJejFjychMPucY1tsqUol53RMqT3X9S87GMTa%2bliTILnkEX2tmI6M5AwG5vu8YIg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1588 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5284 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4032 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5284 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5284 | msedge.exe | 13.107.253.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5284 | msedge.exe | 170.187.143.246:443 | www.windows7codecs.com | Linode, LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
www.windows7codecs.com |
| unknown |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgeservices.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO External IP Lookup Service in DNS Query (ip-info .ff .avast .com) |
— | — | Misc activity | ET INFO External IP Lookup Service in DNS Query (ip-info .ff .avast .com) |
— | — | Misc activity | ET INFO Observed External IP Lookup Domain (ip-info .ff .avast .com) in TLS SNI |
— | — | Misc activity | ET INFO External IP Lookup Service in DNS Query (ip-info .ff .avast .com) |
— | — | Misc activity | ET INFO Observed External IP Lookup Domain (ip-info .ff .avast .com) in TLS SNI |
— | — | Misc activity | ET INFO External IP Lookup Service in DNS Query (ip-info .ff .avast .com) |
— | — | Misc activity | ET INFO Observed External IP Lookup Domain (ip-info .ff .avast .com) in TLS SNI |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
— | — | Potential Corporate Privacy Violation | ET POLICY External IP Lookup (avast .com) |
Process | Message |
|---|---|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in current directory
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in EXE directory
|
saBSI.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\MPCP_FS_files\saBSI.exe loading C:\Users\admin\AppData\Local\Temp\MPCP_FS_files\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in EXE directory
|
saBSI.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\MPCP_FS_files\saBSI.exe loading C:\Users\admin\AppData\Local\Temp\MPCP_FS_files\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in current directory
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in current directory
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in EXE directory
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in current directory
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in EXE directory
|