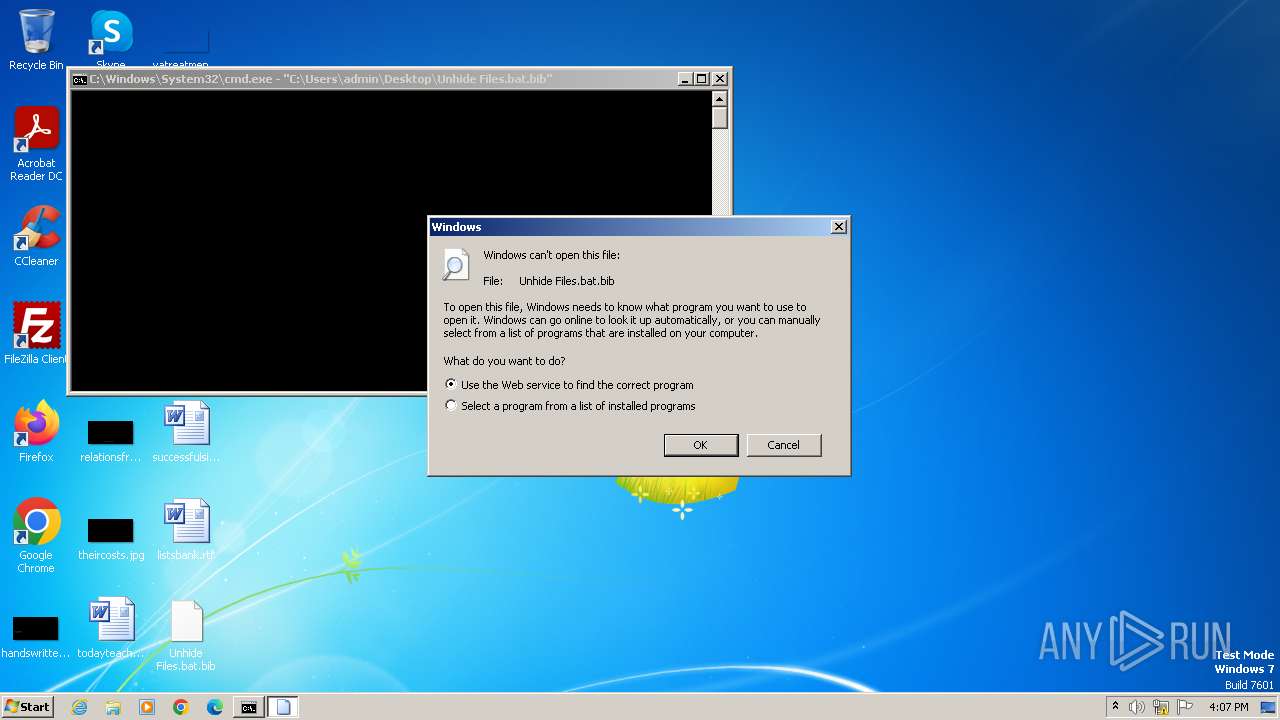
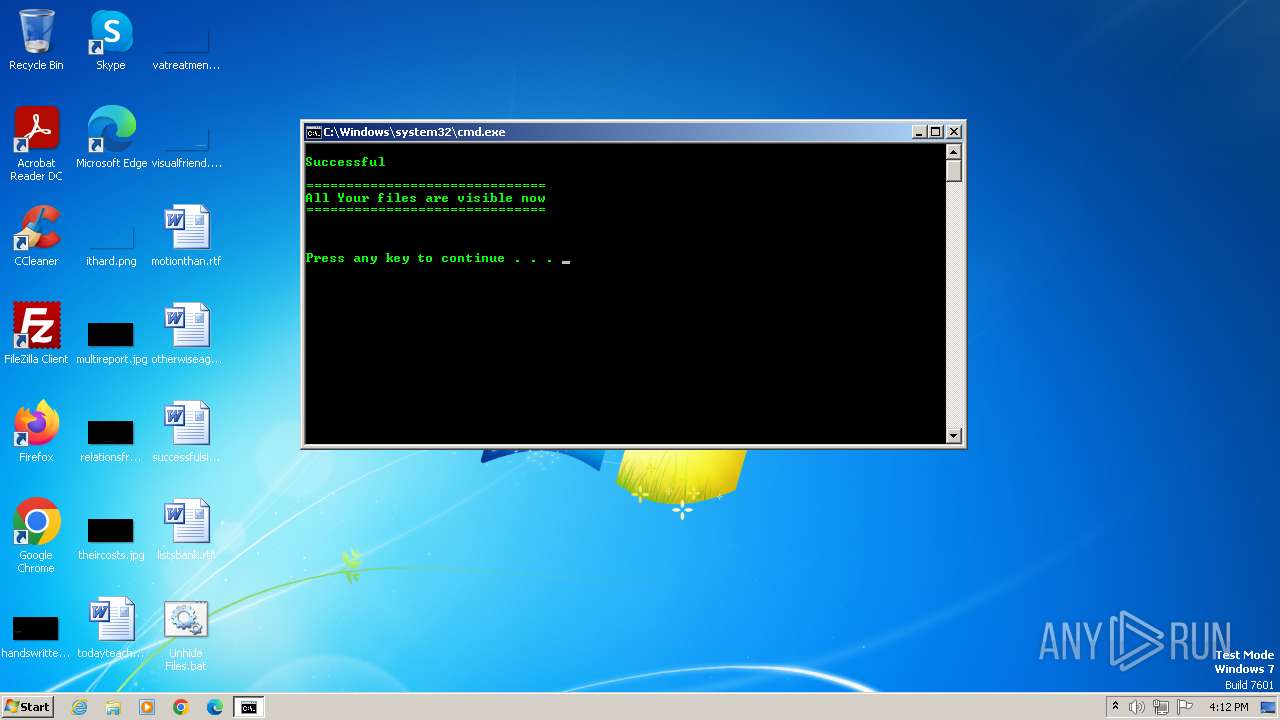
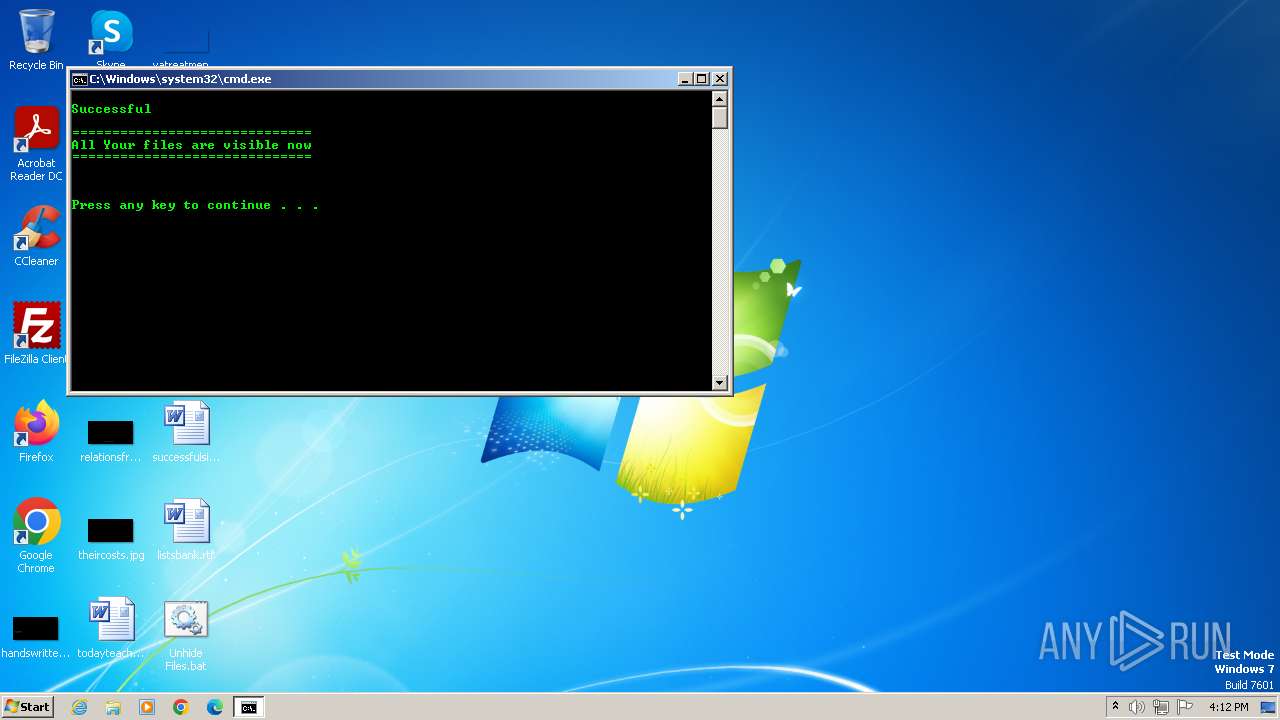
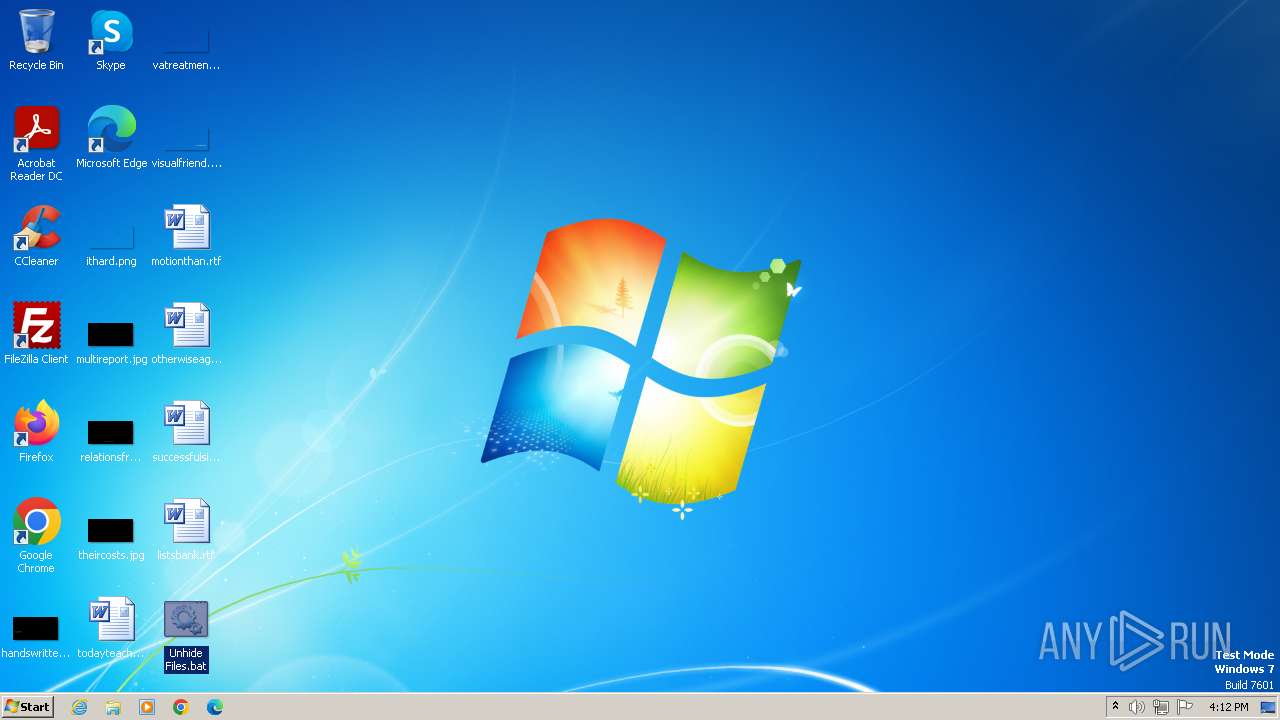
| File name: | Unhide Files.bat |
| Full analysis: | https://app.any.run/tasks/80306066-74f8-4d9e-8165-3599640788db |
| Verdict: | Malicious activity |
| Analysis date: | December 12, 2023, 16:07:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | data |
| MD5: | EB0E0C123D2EA9AF6487B8D695EB402F |
| SHA1: | 6730F38A2CC3AF5580532DE53EA1D08E89E88E48 |
| SHA256: | A5C4046BE14907415076E391BAFFCFBAFF7464C234359CEE3CA0A0C0B1C8F25A |
| SSDEEP: | 12288:toCUCQOeTiqKunM9RFm6D5jKMW5tkox9P1MptUek2T1qKe6hjjZtzQ41OyR5cyEW:toCU1OeTiRunsLBD5jK1Llx9P1itxk2n |
MALICIOUS
Drops the executable file immediately after the start
- cmd.exe (PID: 3892)
- eng.exe (PID: 3924)
- rf.exe (PID: 1016)
- cmd.exe (PID: 3804)
- cmd.exe (PID: 952)
- eng.exe (PID: 3796)
- cmd.exe (PID: 2640)
- eng.exe (PID: 1248)
- eng.exe (PID: 948)
SUSPICIOUS
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 280)
Process drops legitimate windows executable
- cmd.exe (PID: 3892)
- eng.exe (PID: 3924)
- rf.exe (PID: 1016)
- eng.exe (PID: 3796)
- cmd.exe (PID: 3804)
- cmd.exe (PID: 952)
- cmd.exe (PID: 2640)
- eng.exe (PID: 1248)
- eng.exe (PID: 948)
Reads security settings of Internet Explorer
- eng.exe (PID: 3924)
- eng.exe (PID: 3796)
- eng.exe (PID: 1248)
- eng.exe (PID: 948)
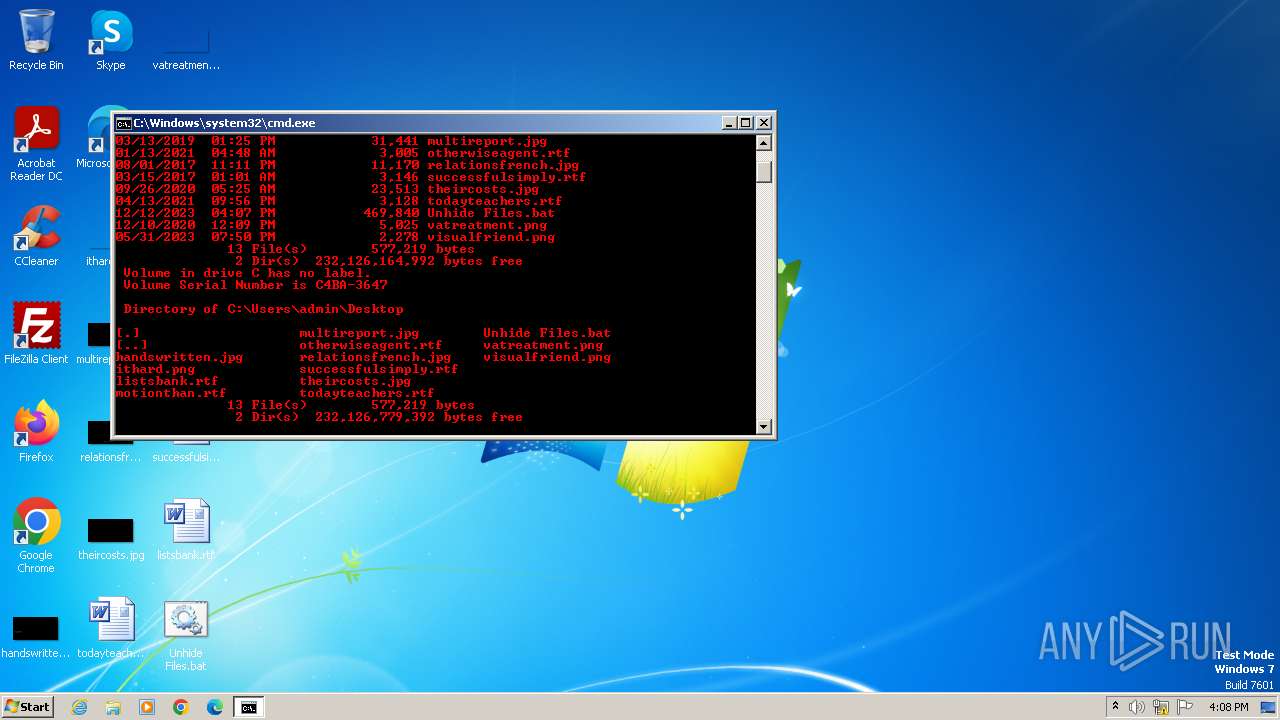
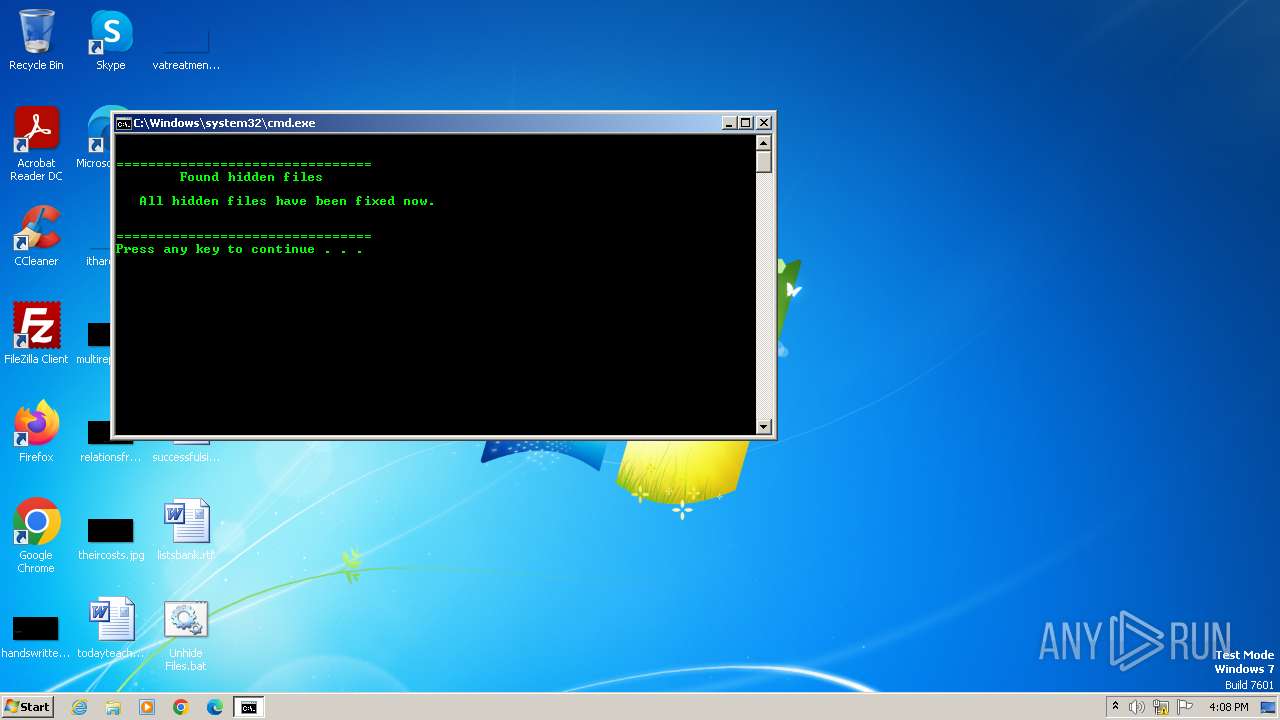
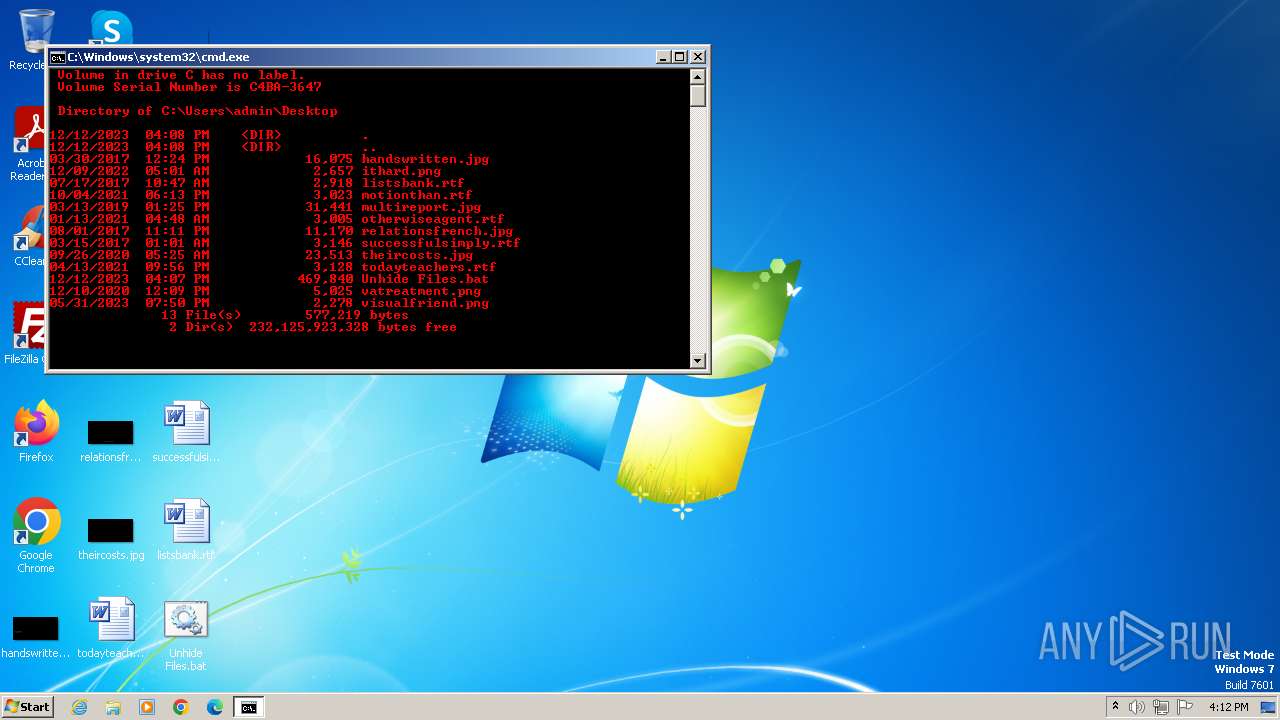
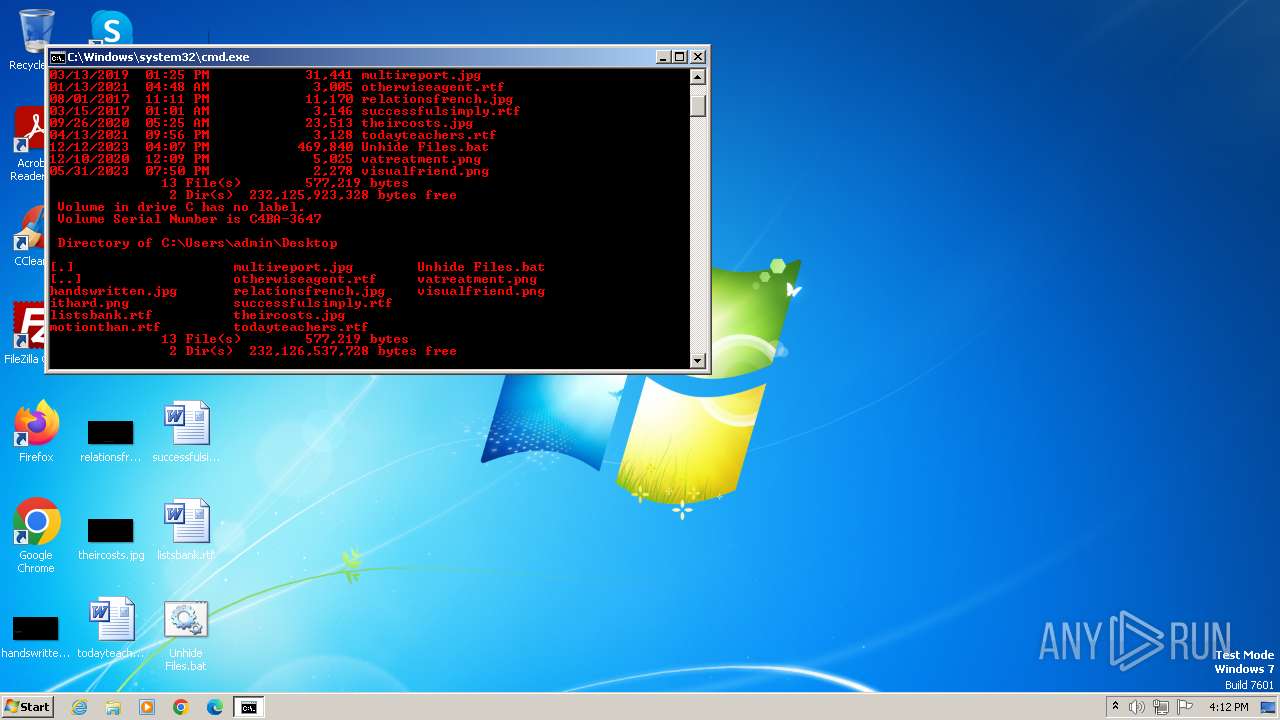
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 3892)
- cmd.exe (PID: 3460)
- cmd.exe (PID: 3540)
- cmd.exe (PID: 4076)
- cmd.exe (PID: 2368)
- cmd.exe (PID: 3020)
- cmd.exe (PID: 3804)
- cmd.exe (PID: 952)
- cmd.exe (PID: 2640)
Checks Windows Trust Settings
- eng.exe (PID: 3924)
- eng.exe (PID: 3796)
- eng.exe (PID: 1248)
- eng.exe (PID: 948)
Application launched itself
- cmd.exe (PID: 3892)
- cmd.exe (PID: 3804)
- cmd.exe (PID: 952)
- cmd.exe (PID: 2640)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3892)
- rf.exe (PID: 1016)
- cmd.exe (PID: 3804)
- cmd.exe (PID: 952)
- cmd.exe (PID: 2640)
Creates FileSystem object to access computer's file system (SCRIPT)
- eng.exe (PID: 3924)
- eng.exe (PID: 3796)
- eng.exe (PID: 1248)
- eng.exe (PID: 948)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- eng.exe (PID: 3924)
- eng.exe (PID: 3796)
- eng.exe (PID: 1248)
- eng.exe (PID: 948)
Reads data from a file (SCRIPT)
- eng.exe (PID: 3924)
- eng.exe (PID: 3796)
- eng.exe (PID: 1248)
- eng.exe (PID: 948)
Checks whether a specific file exists (SCRIPT)
- eng.exe (PID: 3924)
- eng.exe (PID: 3796)
- eng.exe (PID: 1248)
- eng.exe (PID: 948)
Writes binary data to a Stream object (SCRIPT)
- eng.exe (PID: 3924)
- eng.exe (PID: 3796)
- eng.exe (PID: 1248)
- eng.exe (PID: 948)
Reads data from a binary Stream object (SCRIPT)
- eng.exe (PID: 3924)
- eng.exe (PID: 3796)
- eng.exe (PID: 1248)
- eng.exe (PID: 948)
Saves data to a binary file (SCRIPT)
- eng.exe (PID: 3924)
- eng.exe (PID: 3796)
- eng.exe (PID: 1248)
- eng.exe (PID: 948)
Reads the Internet Settings
- eng.exe (PID: 3924)
- rf.exe (PID: 1016)
- svcnosts.exe (PID: 1900)
- svcnost.exe (PID: 1128)
- eng.exe (PID: 3796)
- eng.exe (PID: 1248)
- eng.exe (PID: 948)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 3892)
- cmd.exe (PID: 952)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 3728)
- cmd.exe (PID: 3600)
- cmd.exe (PID: 3448)
- cmd.exe (PID: 3340)
- cmd.exe (PID: 3928)
- cmd.exe (PID: 3584)
- cmd.exe (PID: 3456)
- cmd.exe (PID: 2116)
- cmd.exe (PID: 3292)
- cmd.exe (PID: 2296)
- cmd.exe (PID: 3152)
- cmd.exe (PID: 2312)
- cmd.exe (PID: 3732)
- cmd.exe (PID: 1496)
Runs shell command (SCRIPT)
- eng.exe (PID: 3924)
- eng.exe (PID: 3796)
- eng.exe (PID: 1248)
- eng.exe (PID: 948)
The process creates files with name similar to system file names
- rf.exe (PID: 1016)
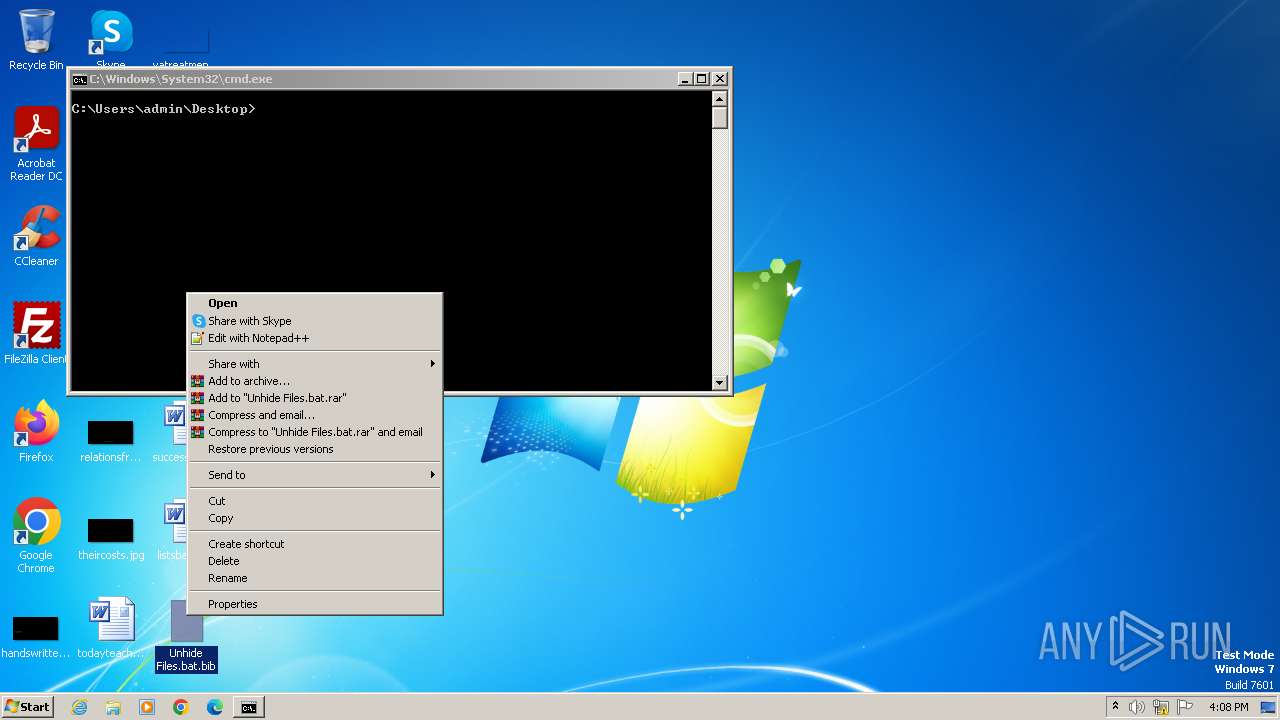
Write to the desktop.ini file (may be used to cloak folders)
- rf.exe (PID: 1016)
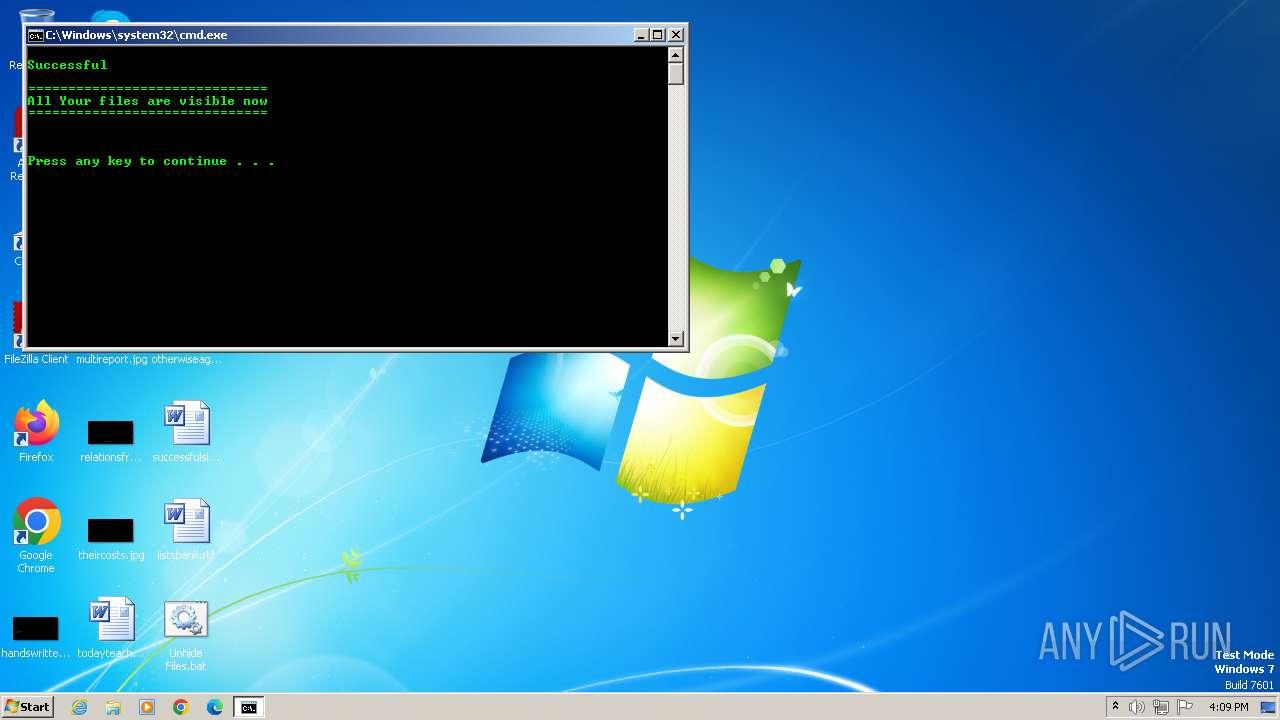
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 3892)
- cmd.exe (PID: 3804)
- cmd.exe (PID: 952)
- cmd.exe (PID: 2640)
Starts itself from another location
- svcnosts.exe (PID: 1900)
Reads settings of System Certificates
- svcnost.exe (PID: 1128)
INFO
Checks supported languages
- eng.exe (PID: 3924)
- rf.exe (PID: 1016)
- svcnosts.exe (PID: 1900)
- svcnost.exe (PID: 1128)
- wmpnscfg.exe (PID: 2828)
- eng.exe (PID: 3796)
- rf.exe (PID: 3176)
- eng.exe (PID: 1248)
- rf.exe (PID: 3744)
- eng.exe (PID: 948)
- rf.exe (PID: 2988)
Reads the computer name
- eng.exe (PID: 3924)
- rf.exe (PID: 1016)
- svcnost.exe (PID: 1128)
- wmpnscfg.exe (PID: 2828)
- svcnosts.exe (PID: 1900)
- eng.exe (PID: 3796)
- rf.exe (PID: 3176)
- eng.exe (PID: 1248)
- rf.exe (PID: 3744)
- eng.exe (PID: 948)
- rf.exe (PID: 2988)
Reads Environment values
- eng.exe (PID: 3924)
- svcnost.exe (PID: 1128)
- eng.exe (PID: 3796)
- eng.exe (PID: 1248)
- eng.exe (PID: 948)
Reads the machine GUID from the registry
- eng.exe (PID: 3924)
- rf.exe (PID: 1016)
- svcnost.exe (PID: 1128)
- svcnosts.exe (PID: 1900)
- eng.exe (PID: 3796)
- rf.exe (PID: 3176)
- eng.exe (PID: 1248)
- rf.exe (PID: 3744)
- eng.exe (PID: 948)
- rf.exe (PID: 2988)
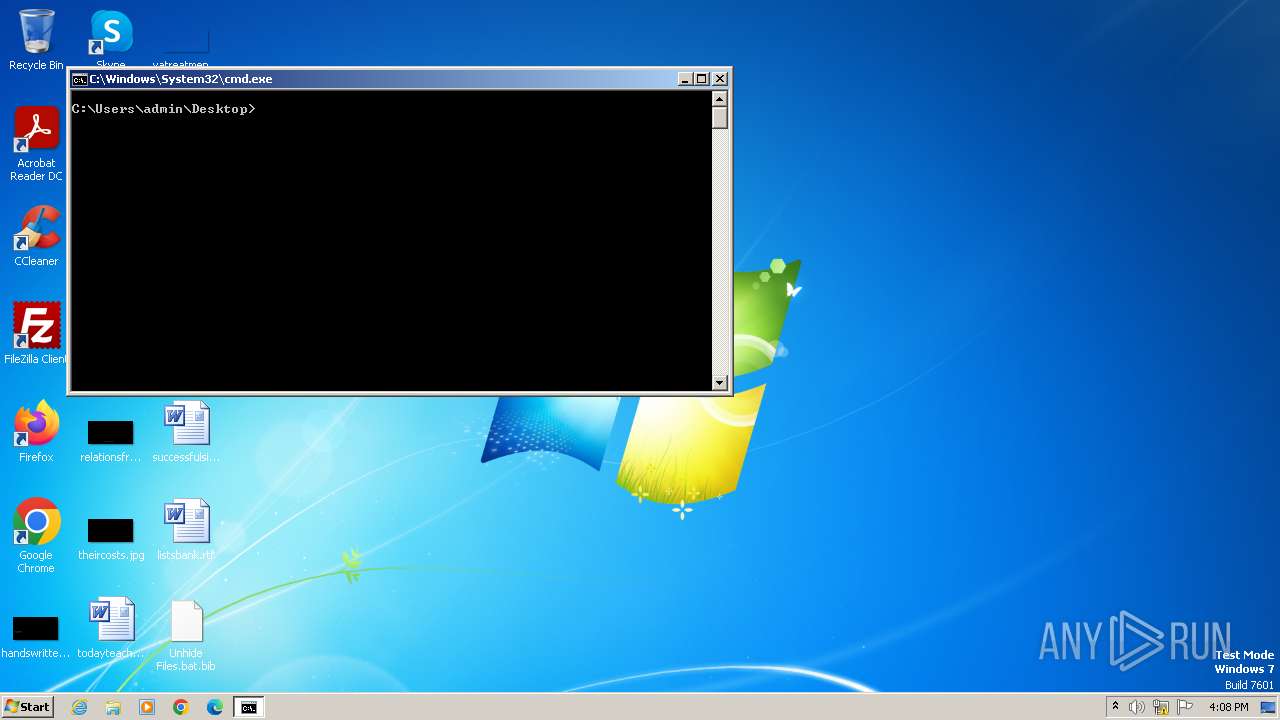
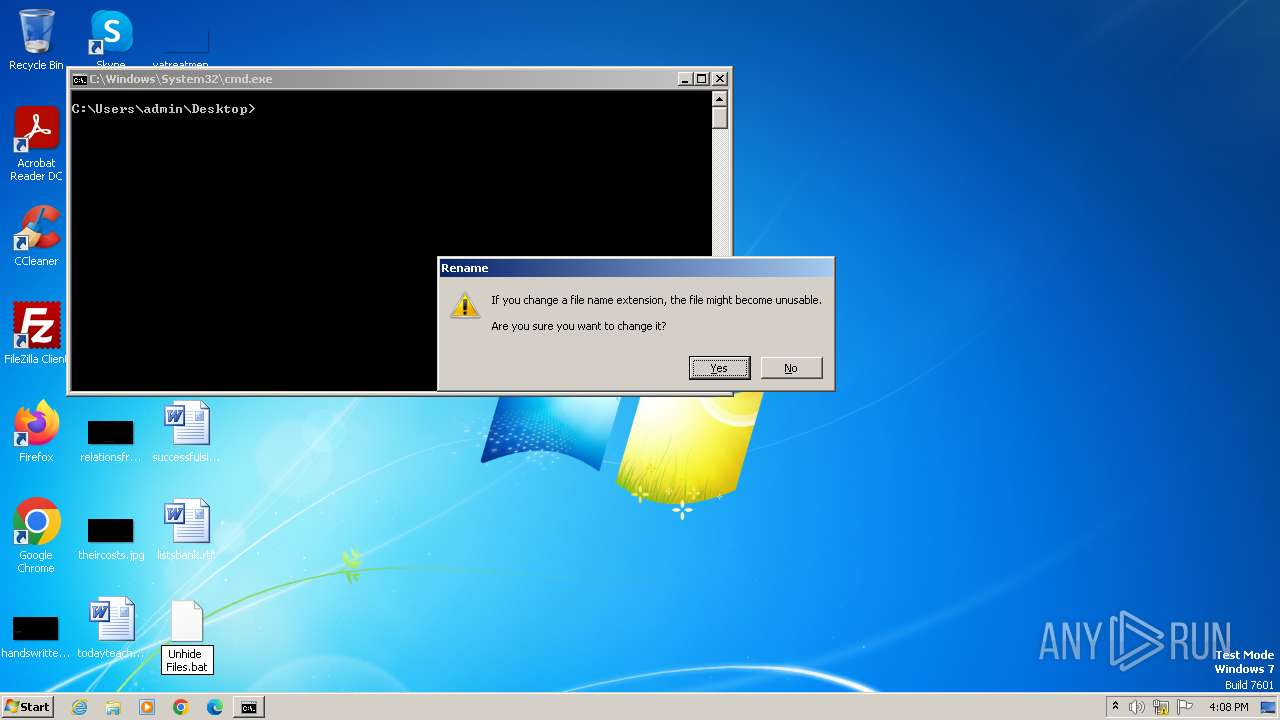
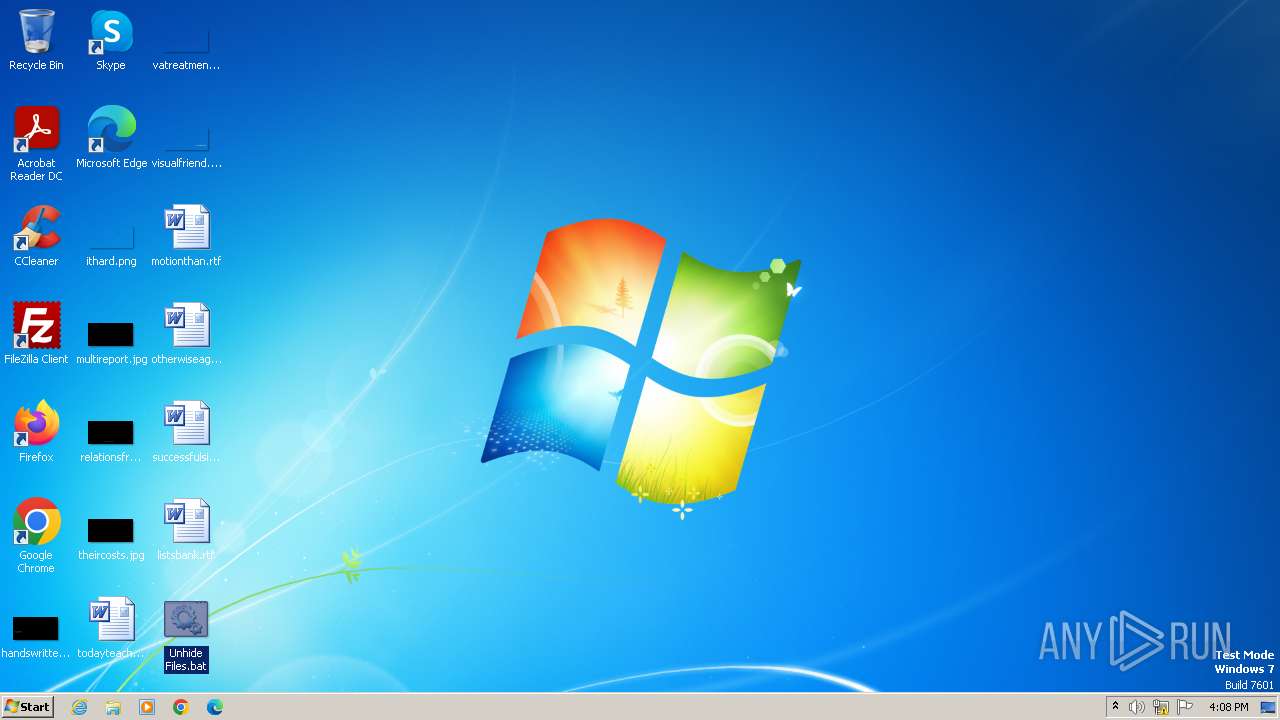
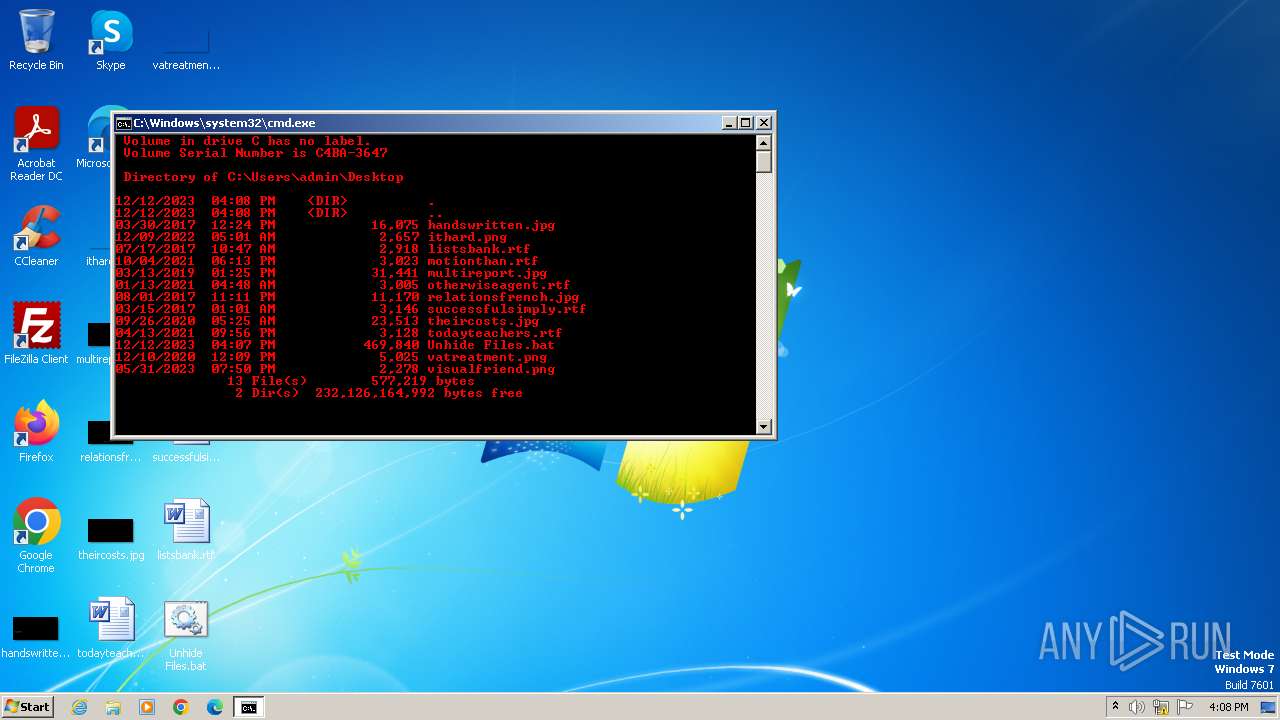
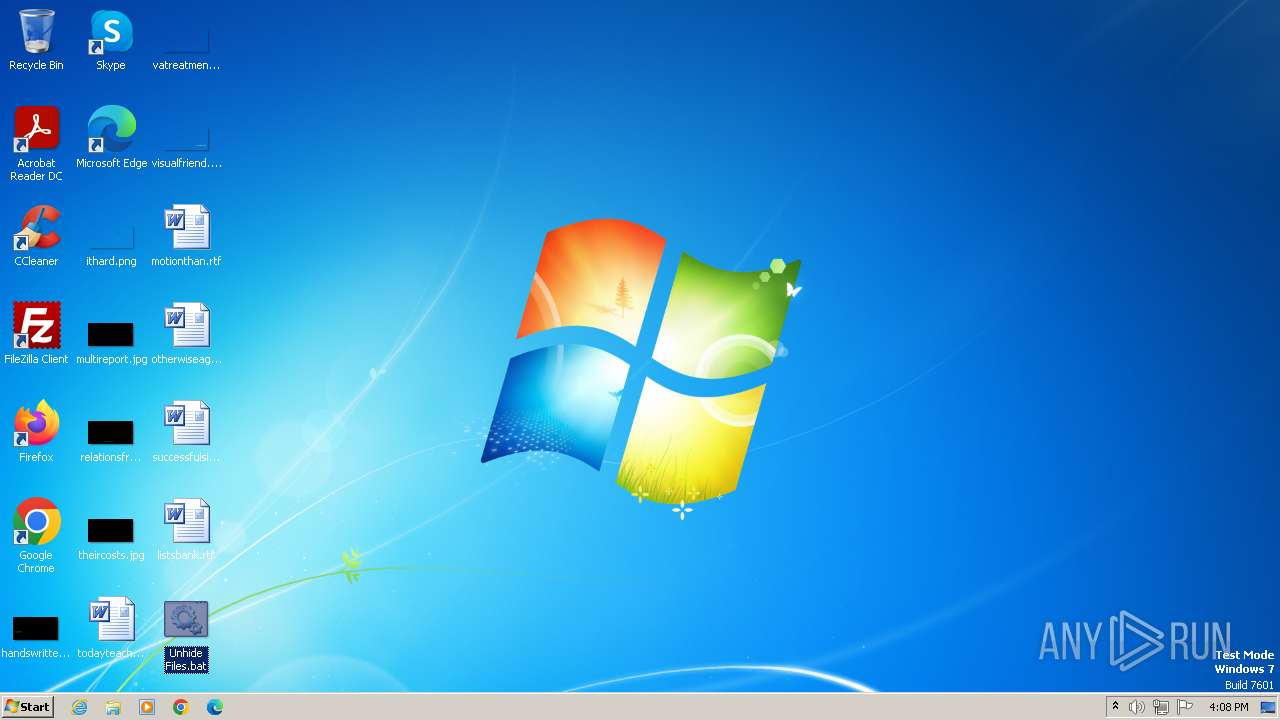
Manual execution by a user
- cmd.exe (PID: 3892)
- wmpnscfg.exe (PID: 2828)
- cmd.exe (PID: 3804)
- cmd.exe (PID: 952)
- cmd.exe (PID: 2640)
Create files in a temporary directory
- eng.exe (PID: 3924)
- eng.exe (PID: 3796)
- eng.exe (PID: 1248)
- eng.exe (PID: 948)
Reads product name
- svcnost.exe (PID: 1128)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .bib/bibtex/txt | | | BibTeX references (100) |
|---|
Total processes
145
Monitored processes
83
Malicious processes
11
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | reg add "HKCU\SOFTWARE\bt" /v gp /t REG_SZ /d 16:0 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 280 | "C:\Windows\System32\cmd.exe" /k "C:\Users\admin\Desktop\Unhide Files.bat.bib" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 476 | cacls C:\System_VoIume_lnformation\Jnt\yeuyvy\..\.. /d administrators /e | C:\Windows\System32\cacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Control ACLs Program Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 556 | attrib C:\sefera\Jnt\qocece\..\..\desktop.ini +s +h | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 600 | attrib * -h -s /d | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 788 | attrib * -h /d | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 900 | cacls n:\sefera\Jnt\null\..\.. /g everyone:f /e /t | C:\Windows\System32\cacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Control ACLs Program Exit code: 3 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 948 | "C:\Users\admin\AppData\Local\Temp\rlgms26316\eng.exe" "C:\Users\admin\AppData\Local\Temp\rlgms26316\sk.js" | C:\Users\admin\AppData\Local\Temp\rlgms26316\eng.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7601.24288 Modules
| |||||||||||||||
| 952 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\Desktop\Unhide Files.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1016 | "C:\Users\admin\AppData\Local\Temp\rlgms25506\rf.exe" rlc | C:\Users\admin\AppData\Local\Temp\rlgms25506\rf.exe | — | eng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
8 799
Read events
8 736
Write events
63
Delete events
0
Modification events
| (PID) Process: | (3924) eng.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3924) eng.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3924) eng.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3924) eng.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1016) rf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1016) rf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1016) rf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1016) rf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1900) svcnosts.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1900) svcnosts.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
14
Suspicious files
6
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3892 | cmd.exe | C:\Users\admin\AppData\Local\Temp\rlgms25506\unrf.dll | binary | |
MD5:EB0E0C123D2EA9AF6487B8D695EB402F | SHA256:A5C4046BE14907415076E391BAFFCFBAFF7464C234359CEE3CA0A0C0B1C8F25A | |||
| 3804 | cmd.exe | C:\Users\admin\AppData\Local\Temp\rlgms25666\sk.js | text | |
MD5:3ABAFFE780DACFD3C83A6D79D3456CD1 | SHA256:1D16BCFDCC3ACBD37D4E39E07DF2FA6F496FB4B9998D6F1D83C5E076860AFC6B | |||
| 3804 | cmd.exe | C:\Users\admin\AppData\Local\Temp\rlgms25666\unrf.dll | bib | |
MD5:EB0E0C123D2EA9AF6487B8D695EB402F | SHA256:A5C4046BE14907415076E391BAFFCFBAFF7464C234359CEE3CA0A0C0B1C8F25A | |||
| 1016 | rf.exe | C:\sefera\Jnt\qocece\gotera.bmp | binary | |
MD5:F1A2D63899B87CEF381F57BB4D195F7C | SHA256:C0F305F40A1CCCCE836A9DC9F44368ABC4173D4A697709D3EC8C71AFDC30FCEA | |||
| 1016 | rf.exe | C:\System_VoIume_lnformation\Jnt\yeuyvy\gotera.bmp | binary | |
MD5:F1A2D63899B87CEF381F57BB4D195F7C | SHA256:C0F305F40A1CCCCE836A9DC9F44368ABC4173D4A697709D3EC8C71AFDC30FCEA | |||
| 1016 | rf.exe | C:\System_VoIume_lnformation\Jnt\yeuyvy\bmz\explorer.exe | executable | |
MD5:AD7B9C14083B52BC532FBA5948342B98 | SHA256:17F746D82695FA9B35493B41859D39D786D32B23A9D2E00F4011DEC7A02402AE | |||
| 1016 | rf.exe | C:\sefera\Jnt\qocece\desktop.ini | text | |
MD5:ADC4B5D4444D26293DC782B6238CA6F0 | SHA256:ABE8A5933FF450A89B8E9A736F08874B43B7355D17FFE6540C4A6EAD0F0995D3 | |||
| 3804 | cmd.exe | C:\Users\admin\AppData\Local\Temp\rlgms25666\eng.exe | executable | |
MD5:BA7AC4381D685354FF87E0553E950A4E | SHA256:BED1028BADEE2ADE8A8A8EDD25AA4C3E70A6BEEFAFBDFFD6426E5E467F24EB01 | |||
| 1016 | rf.exe | C:\sefera\Jnt\qocece\svcnost.exe | executable | |
MD5:E1C8E6FA5477FC3C6459B70EC2C362E0 | SHA256:33AEDB26DBCAC8C27AD724A2583C93CDD5E2F1C8535444AB0DBAF0ECCAABD360 | |||
| 3796 | eng.exe | C:\Users\admin\AppData\Local\Temp\rlgms25666\rf.exe | executable | |
MD5:A6C776F57B289B97DDF353C32776A4AE | SHA256:686467F75A5C0A056ABA4614AA42E404FE9535D3DE98806AD8C059C582F55716 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1128 | svcnost.exe | 199.36.158.100:443 | clear-march.firebaseapp.com | FASTLY | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clear-march.firebaseapp.com |
| malicious |