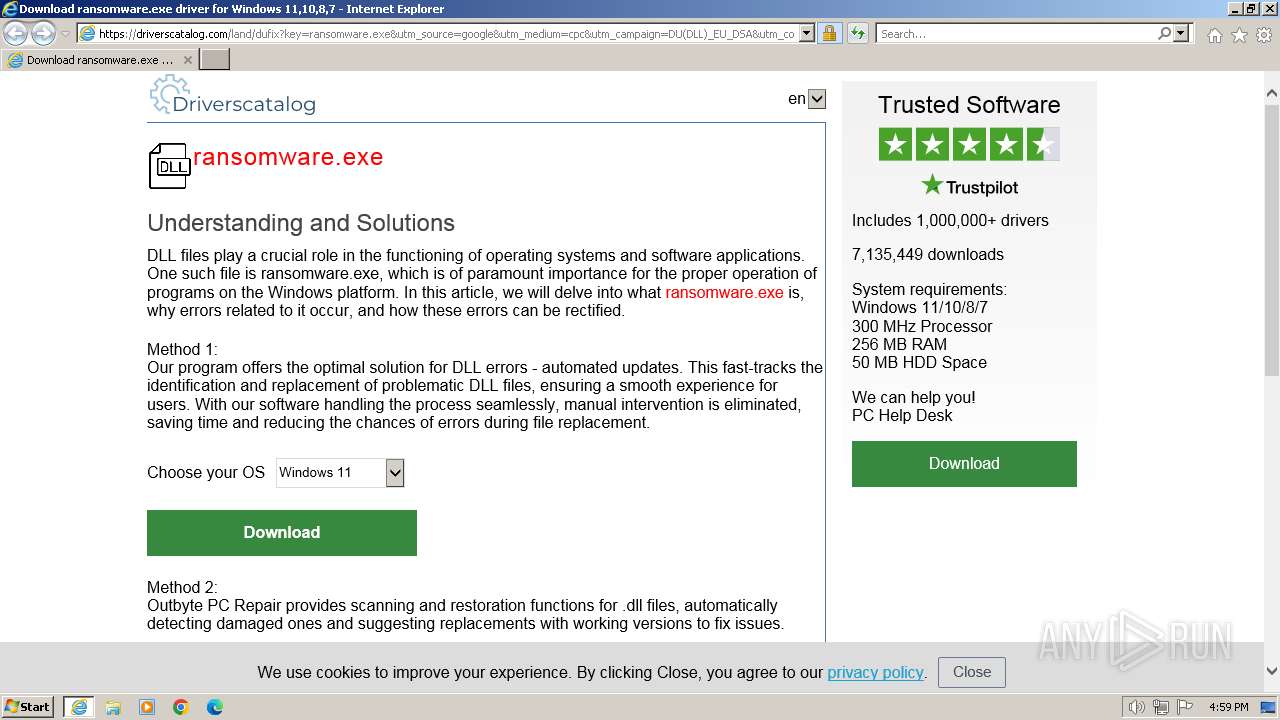
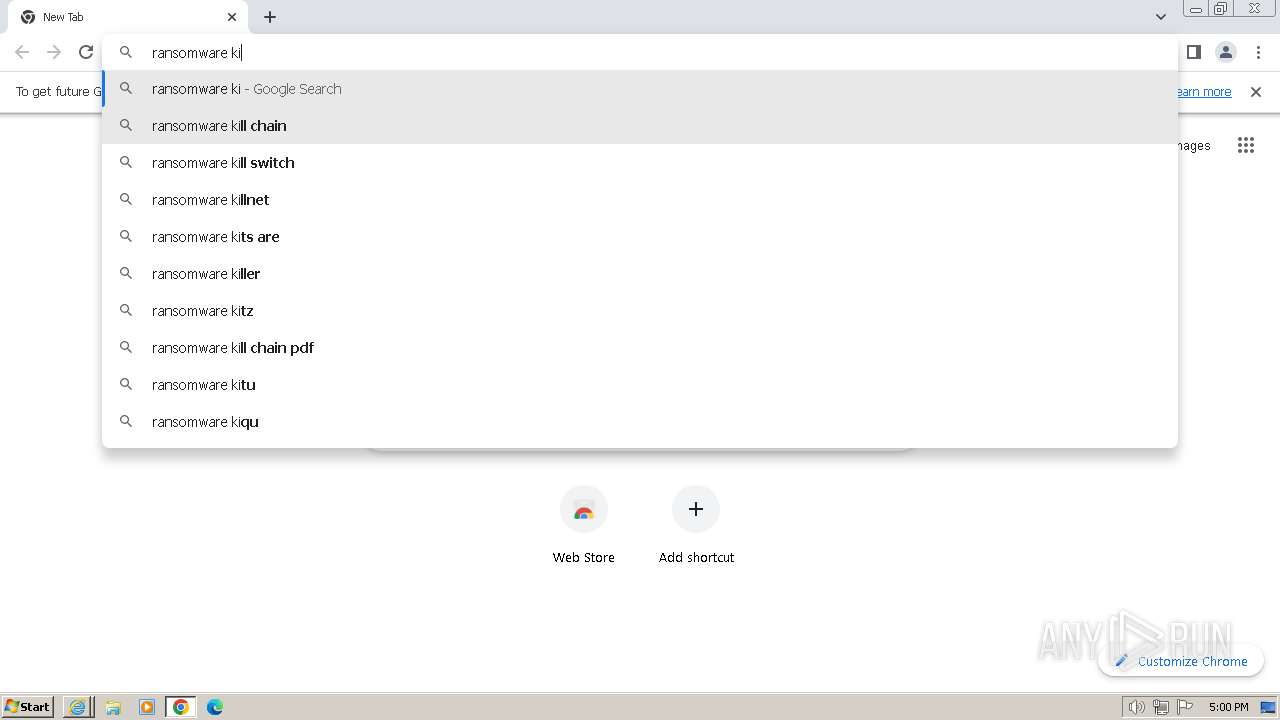
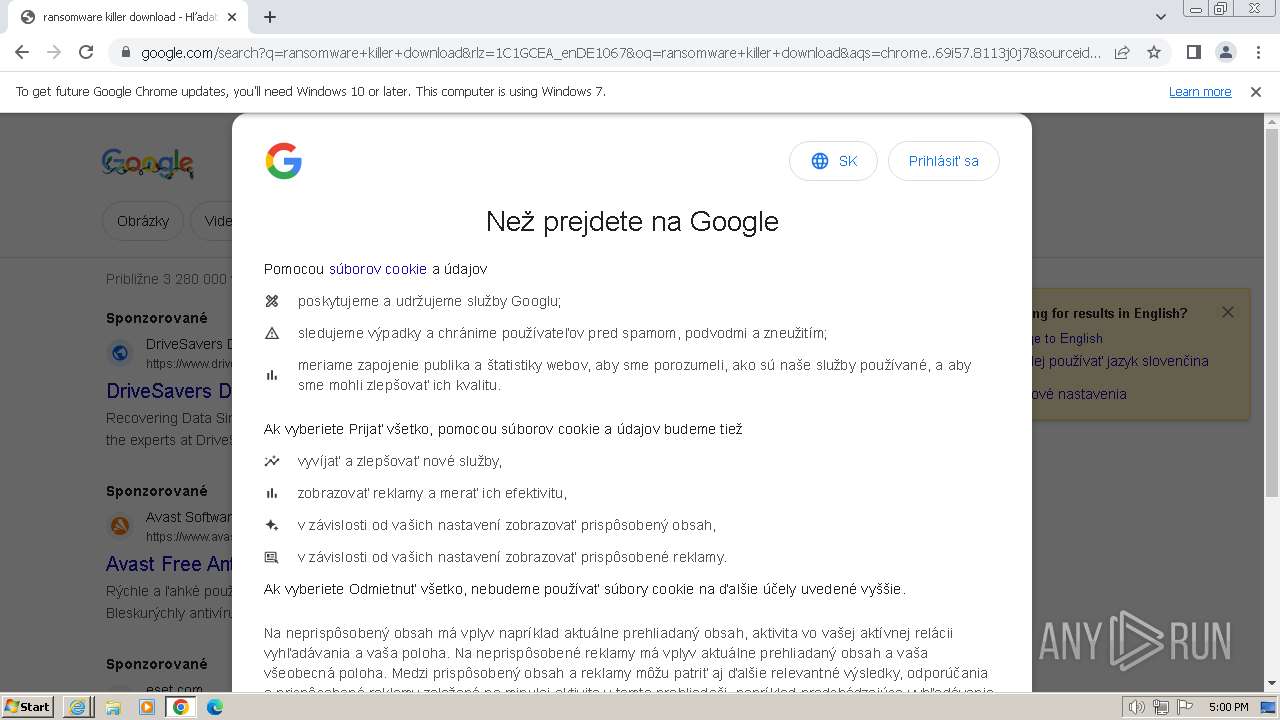
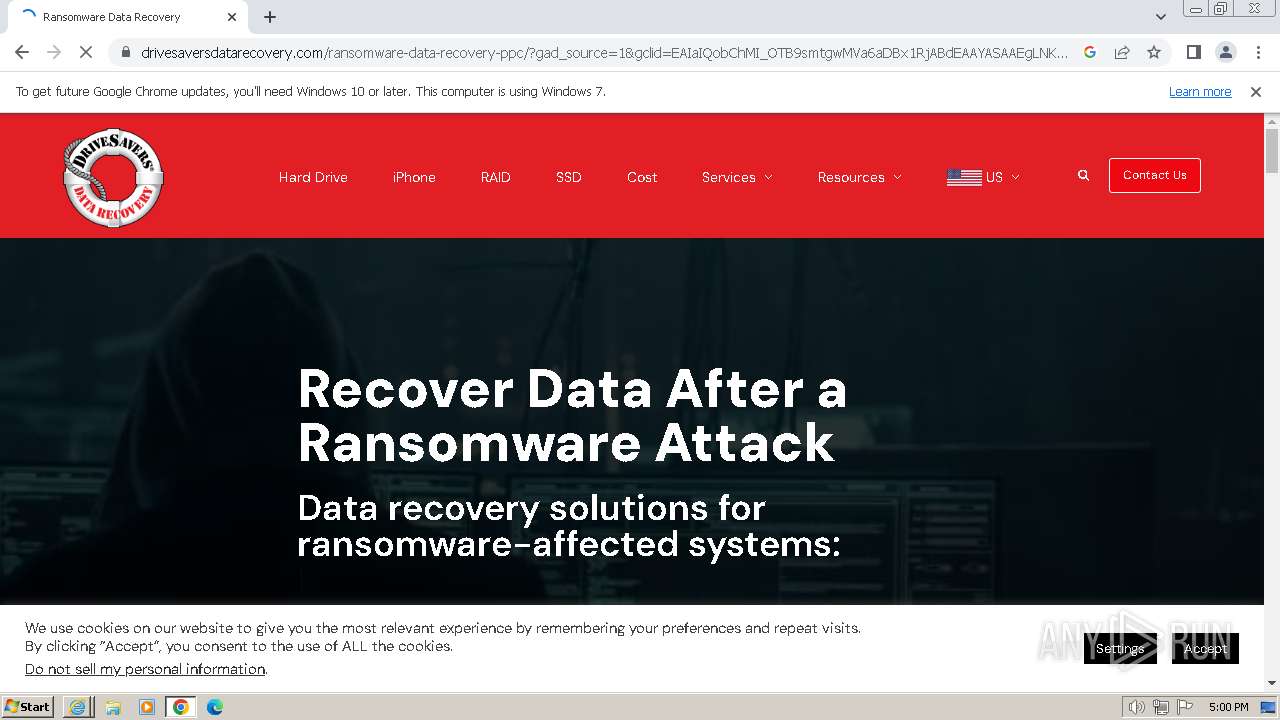
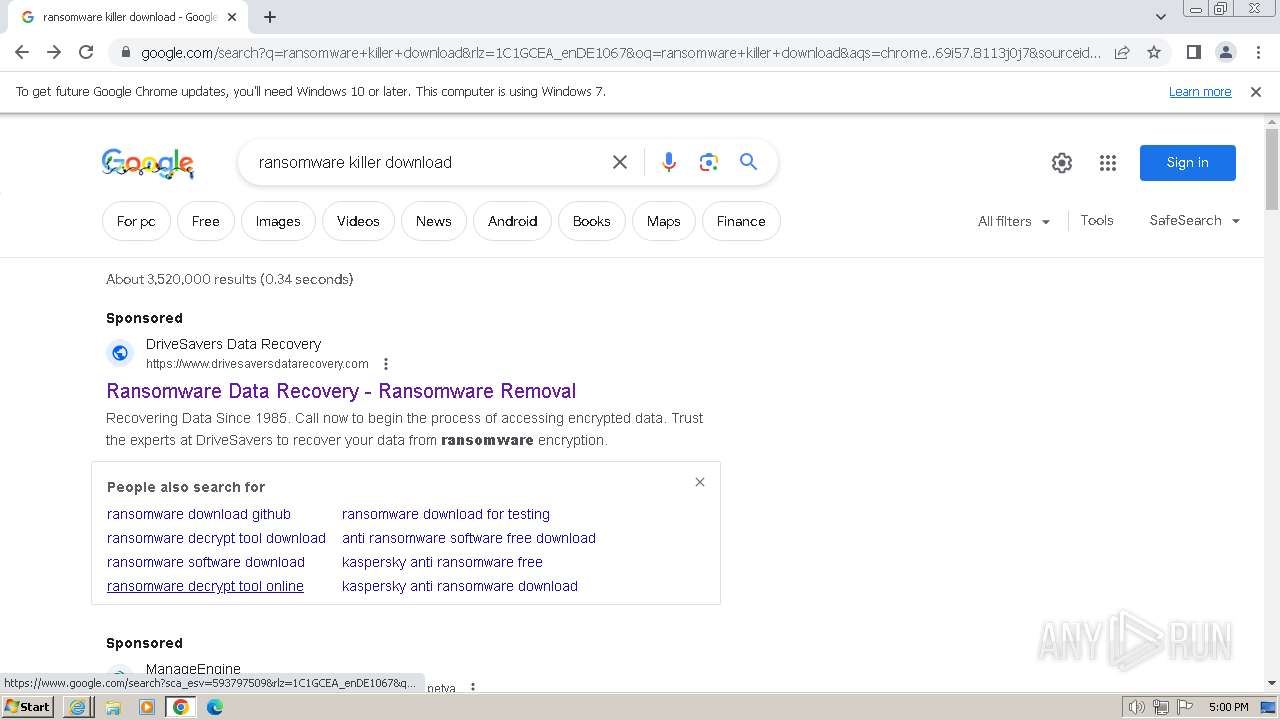
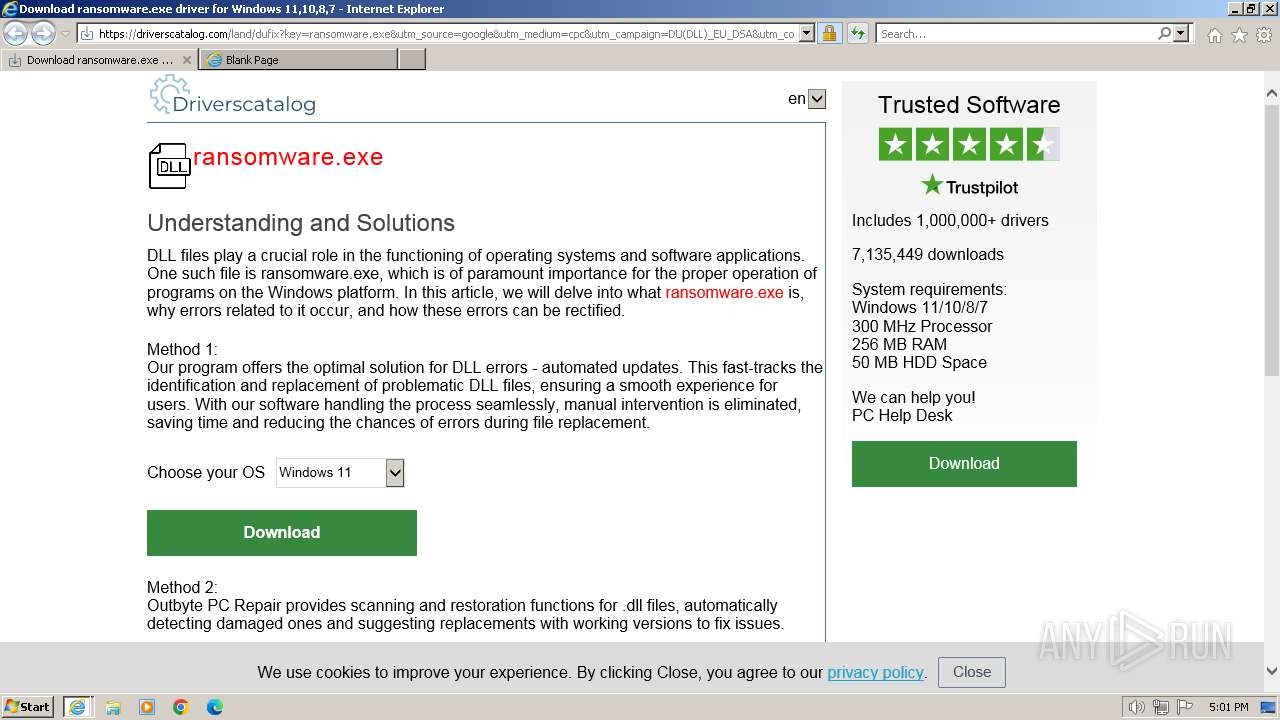
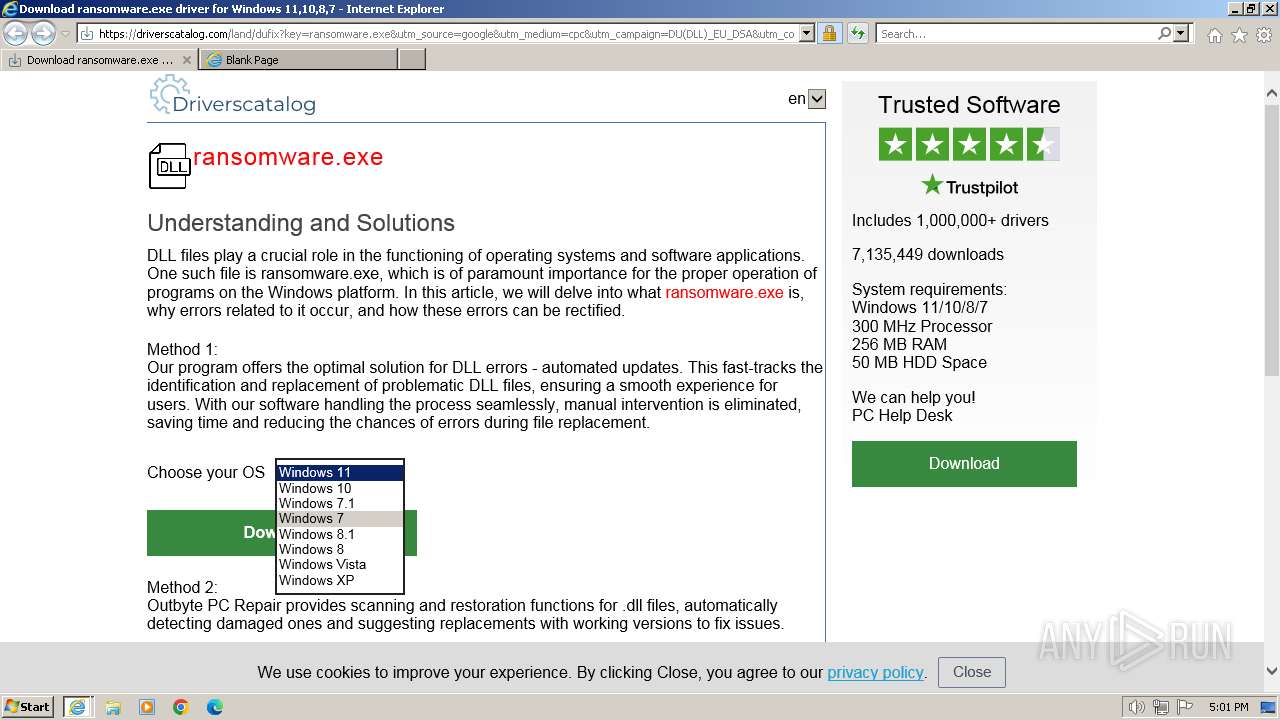
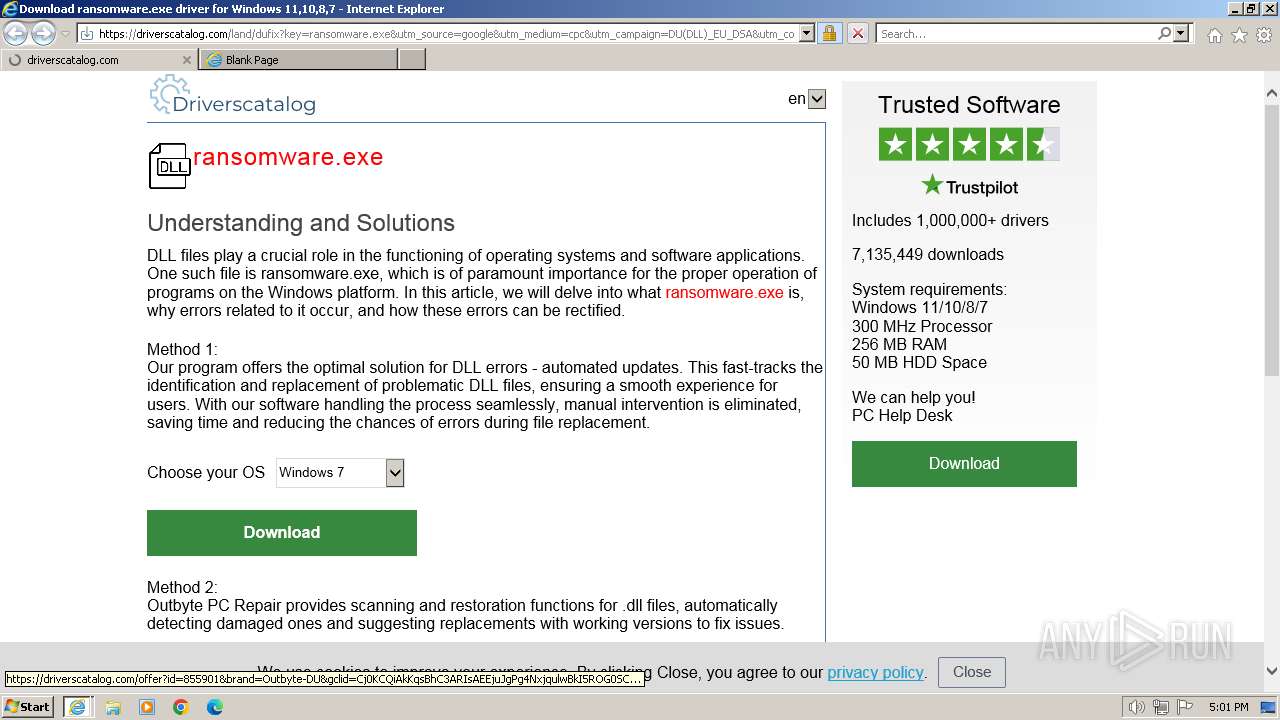
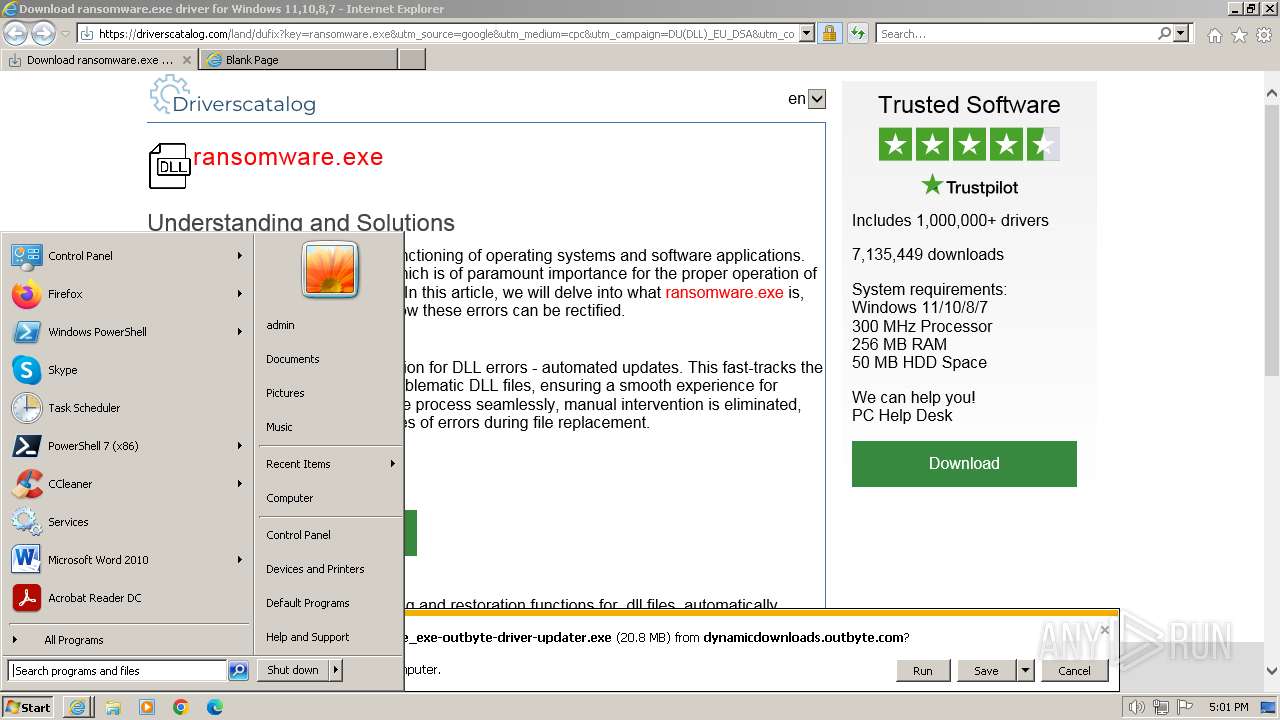
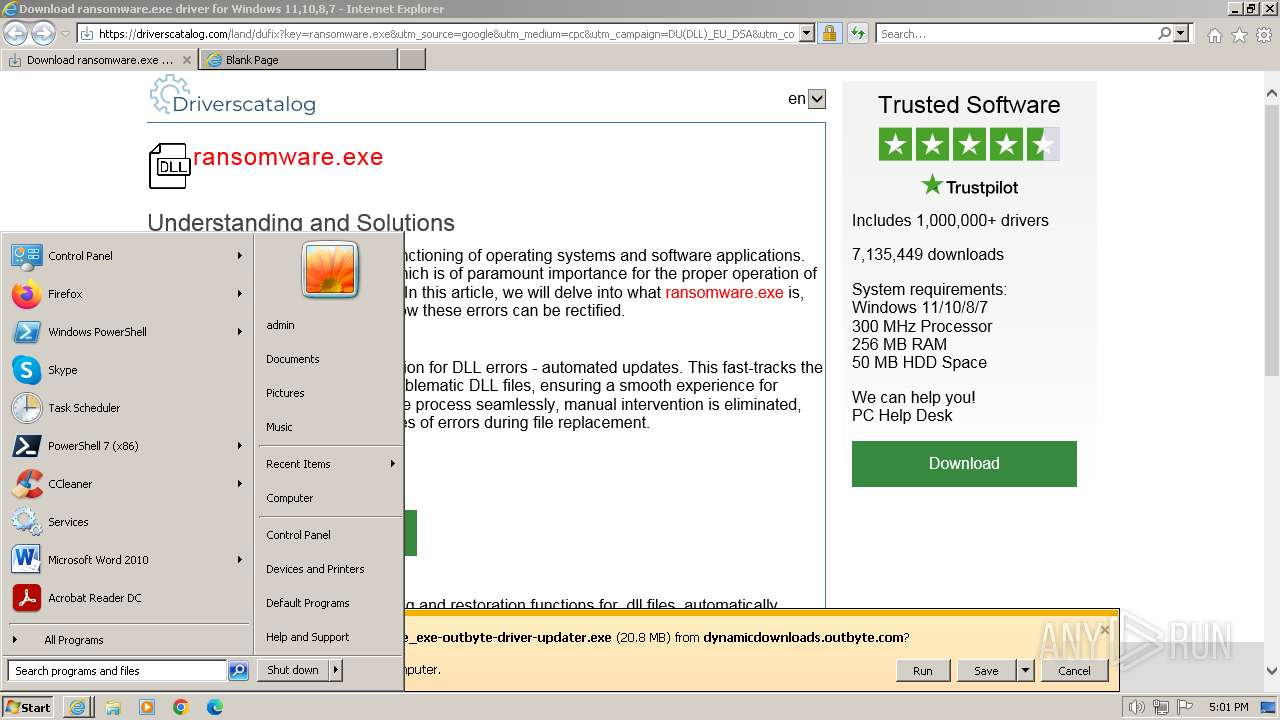
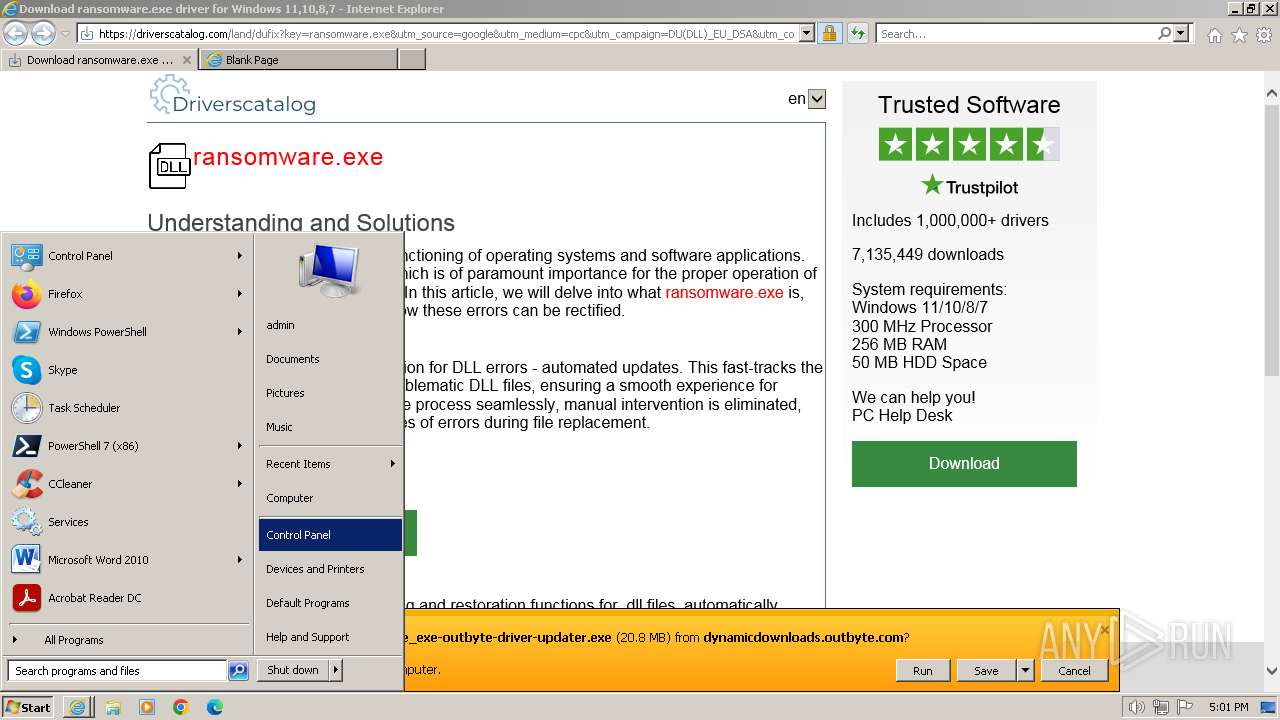
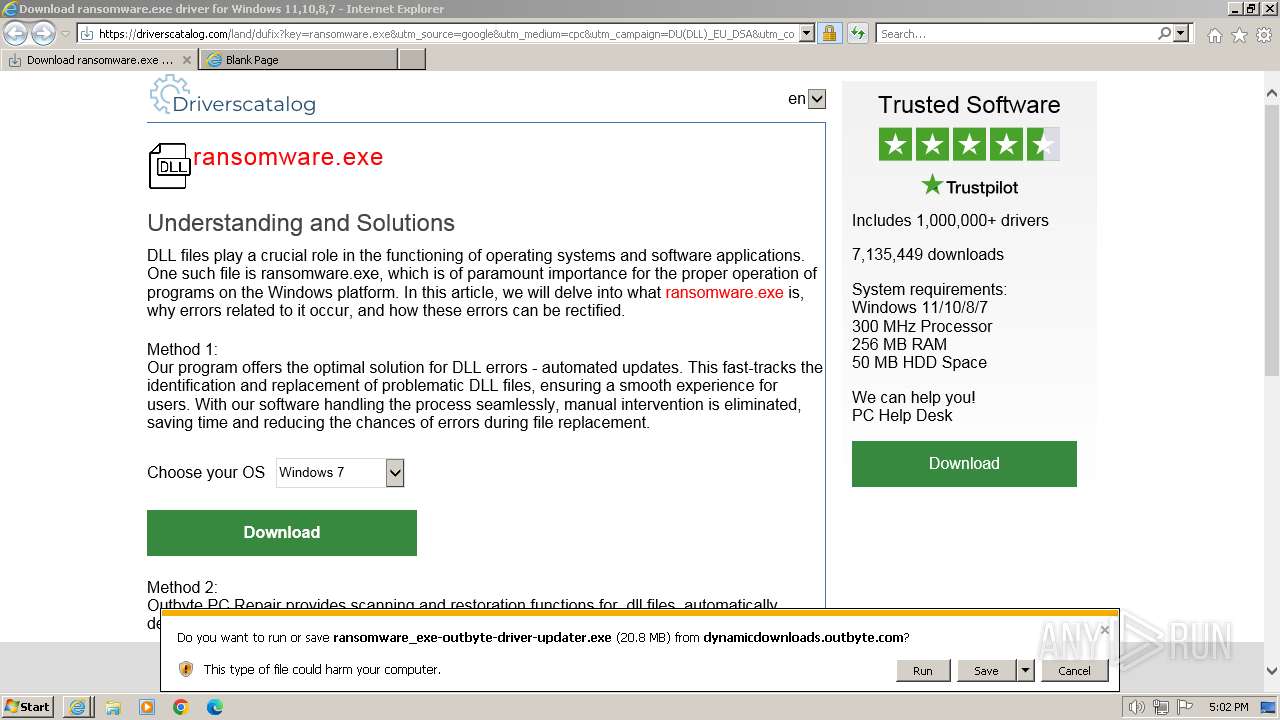
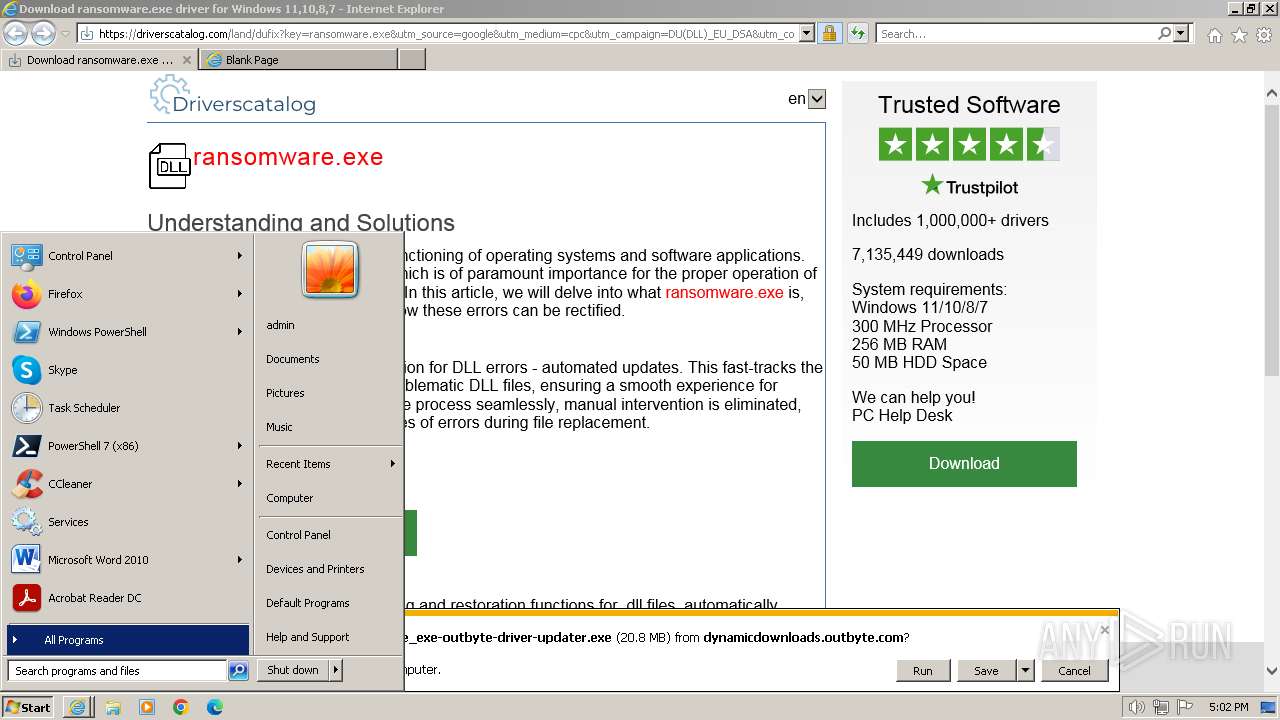
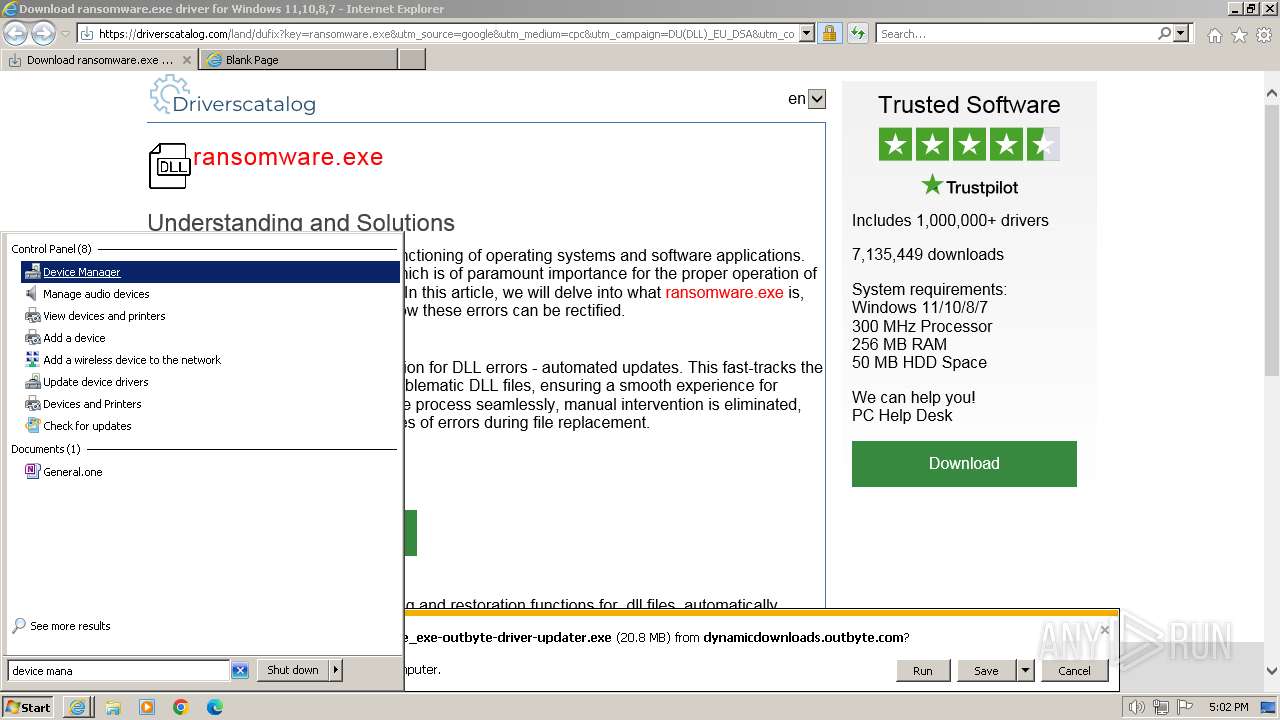
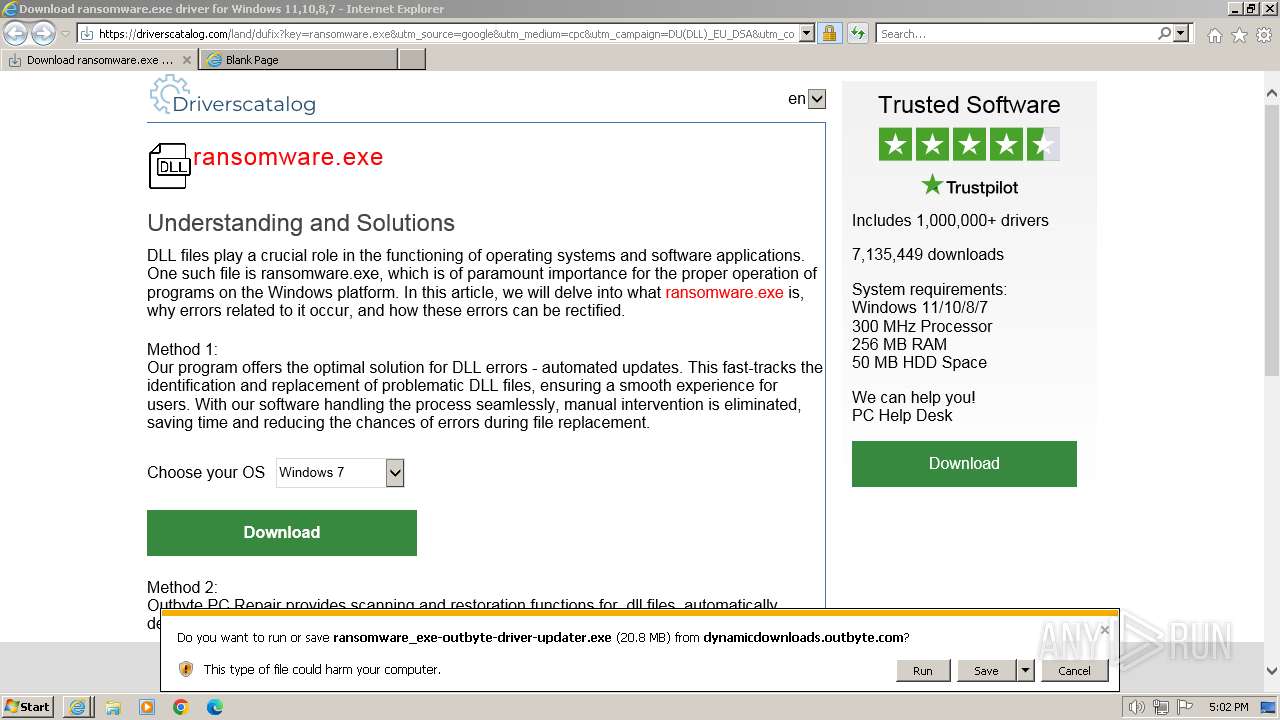
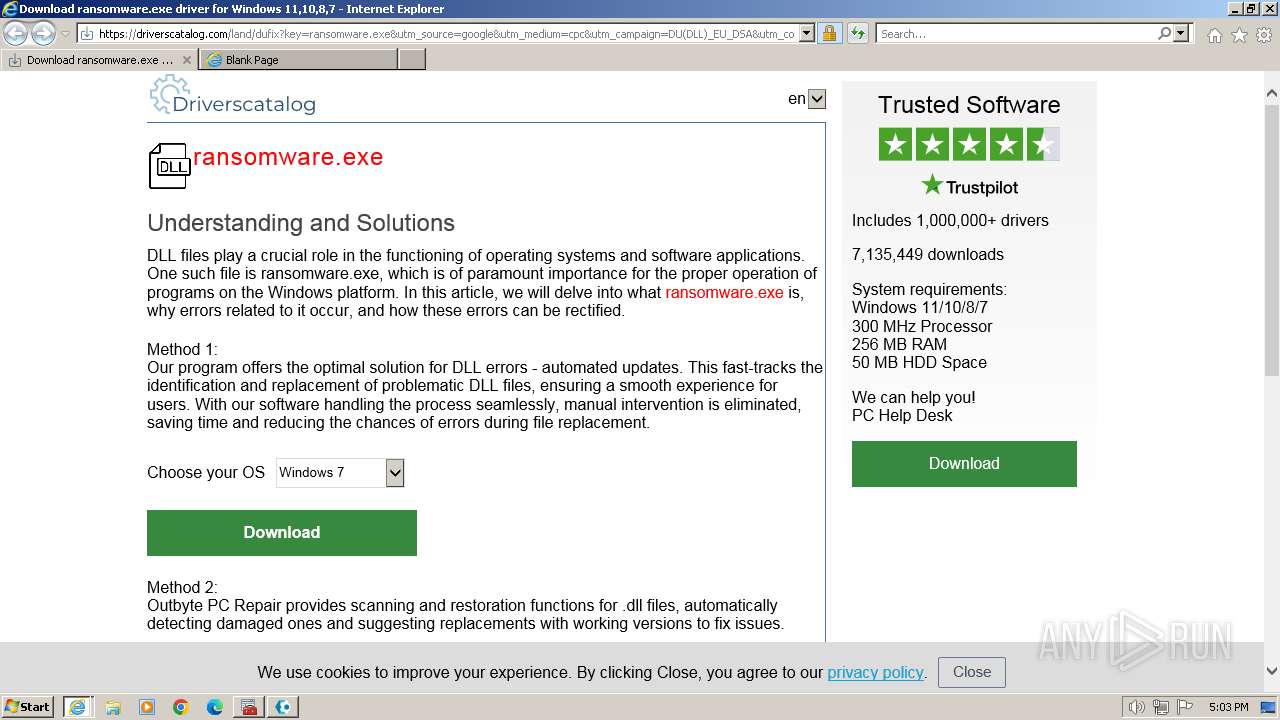
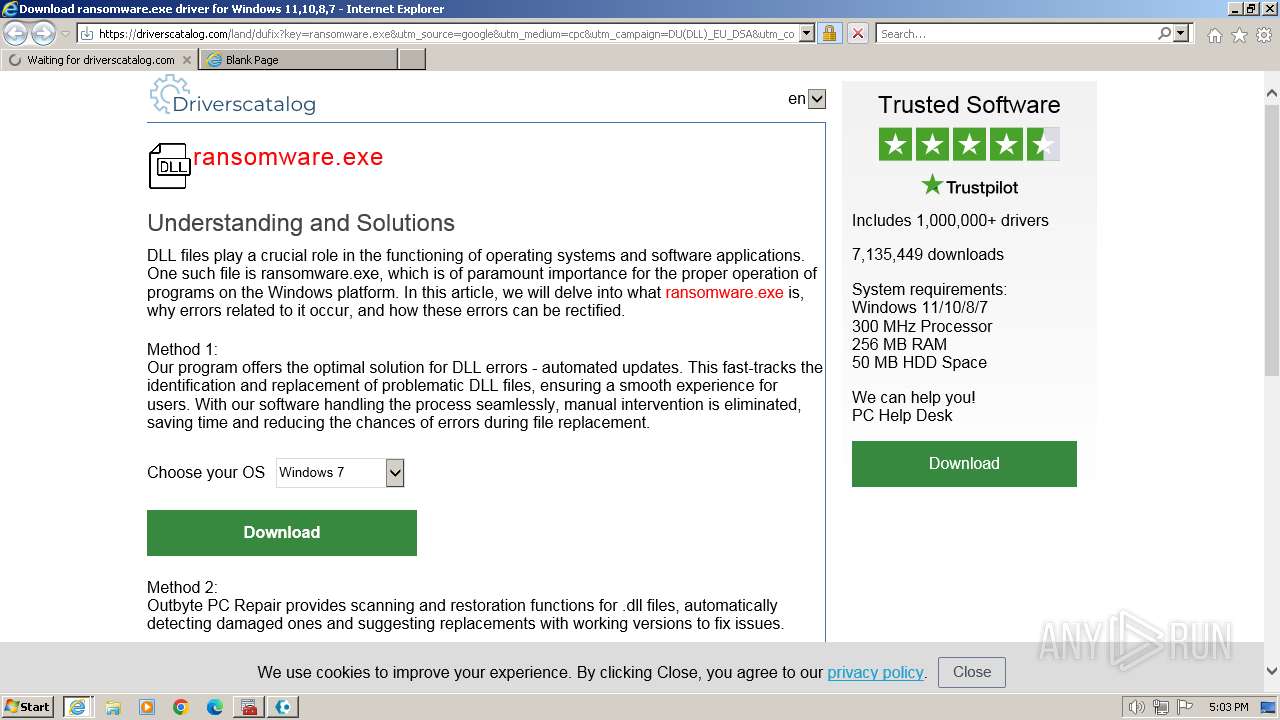
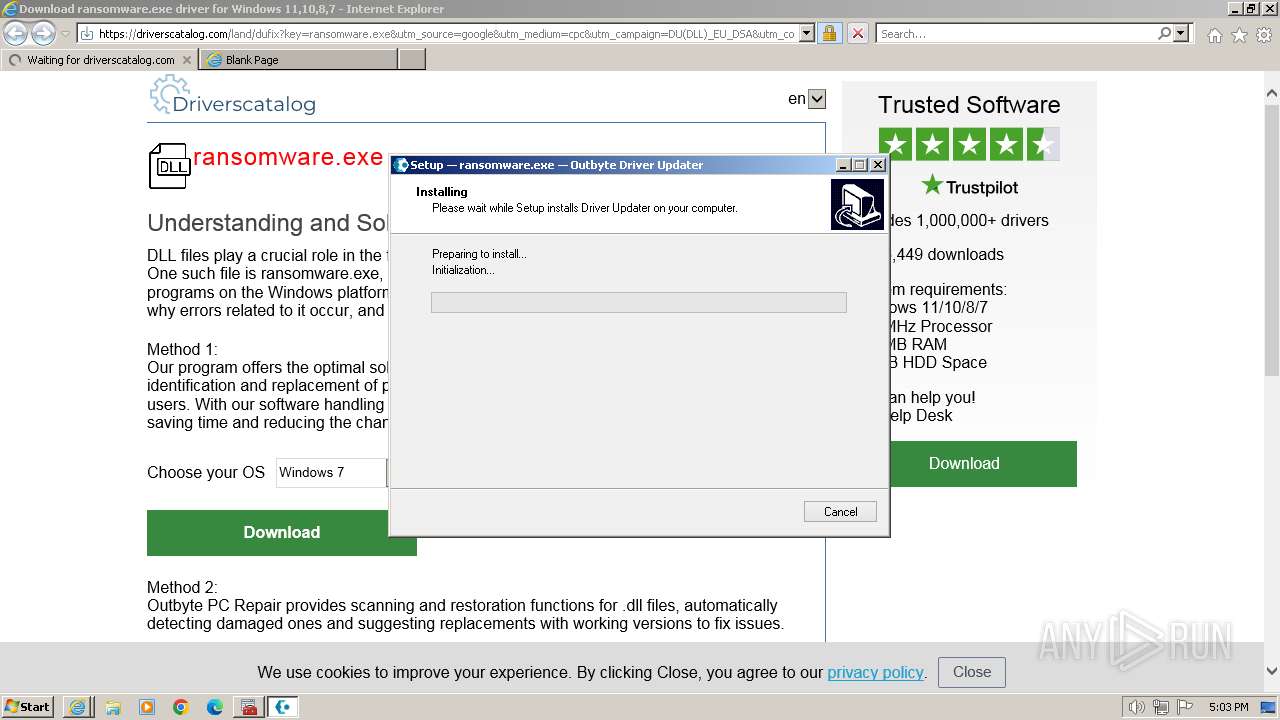
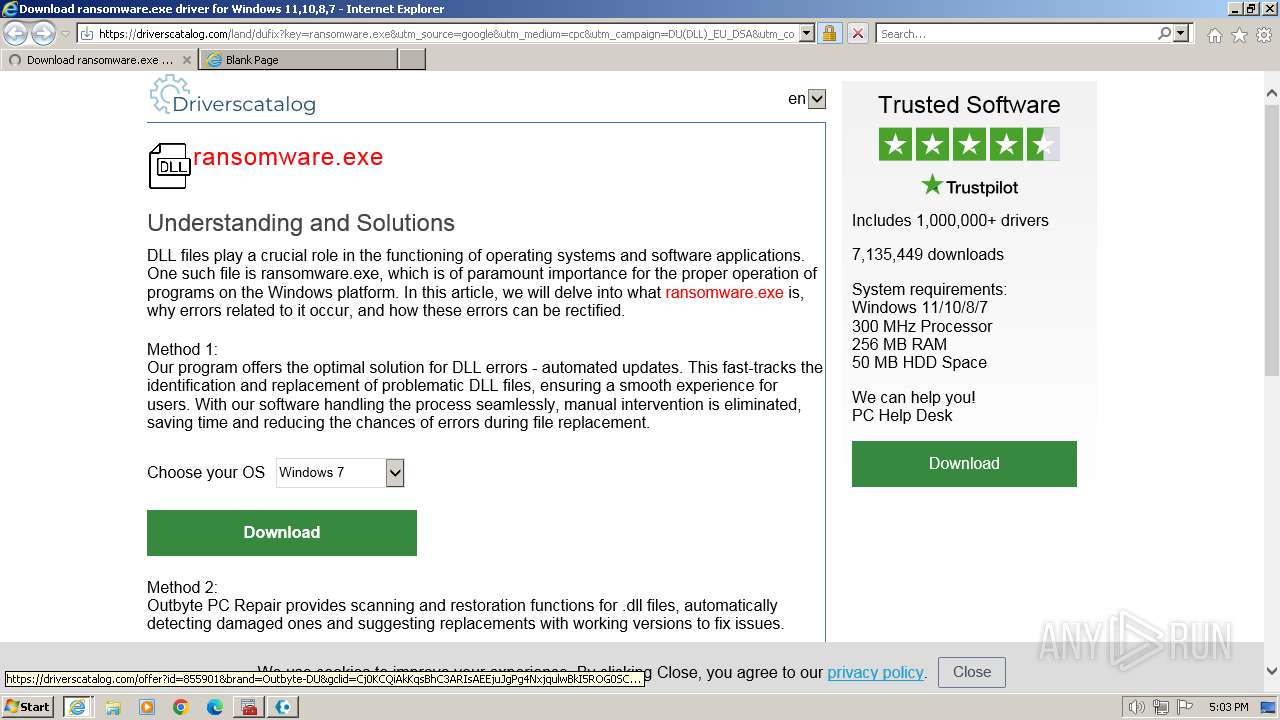
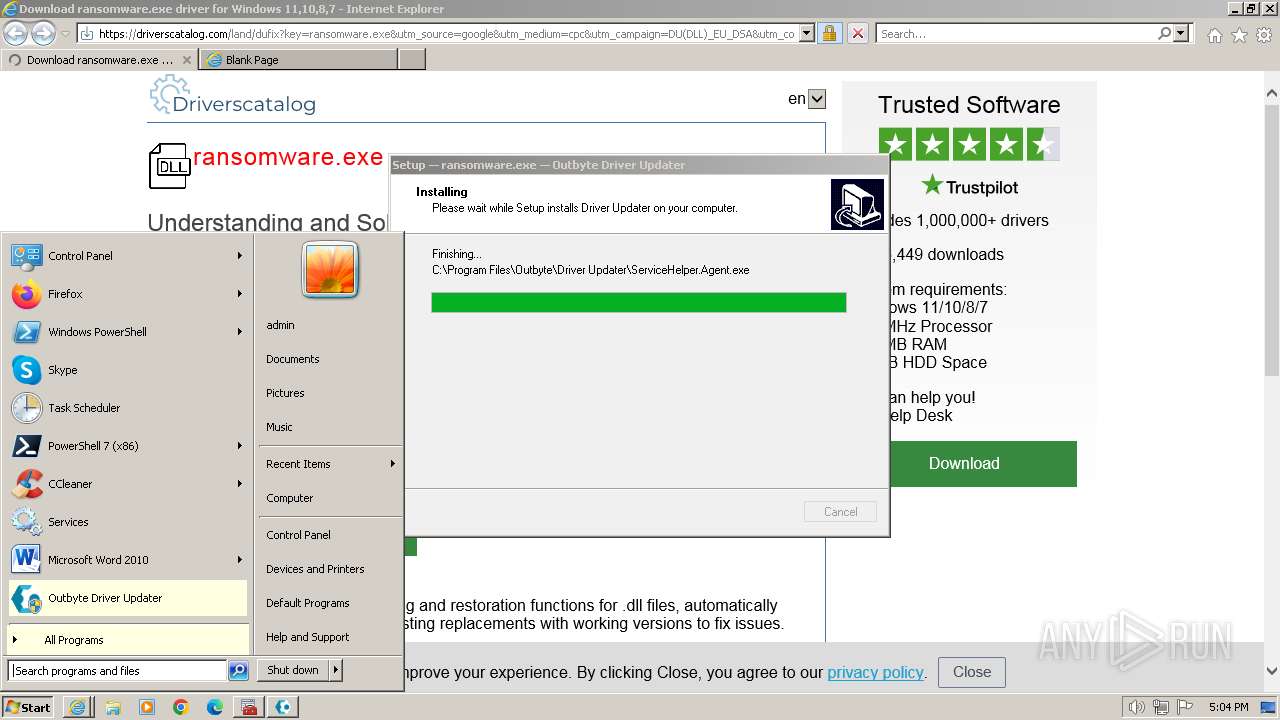
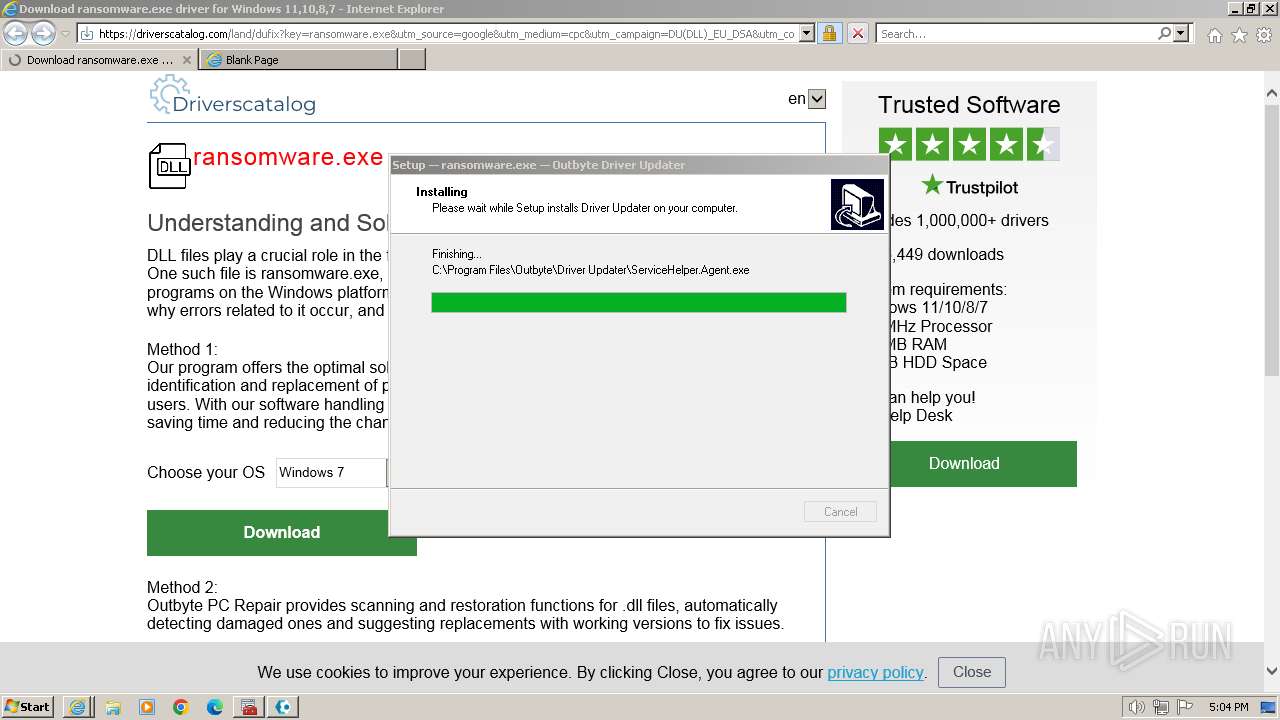
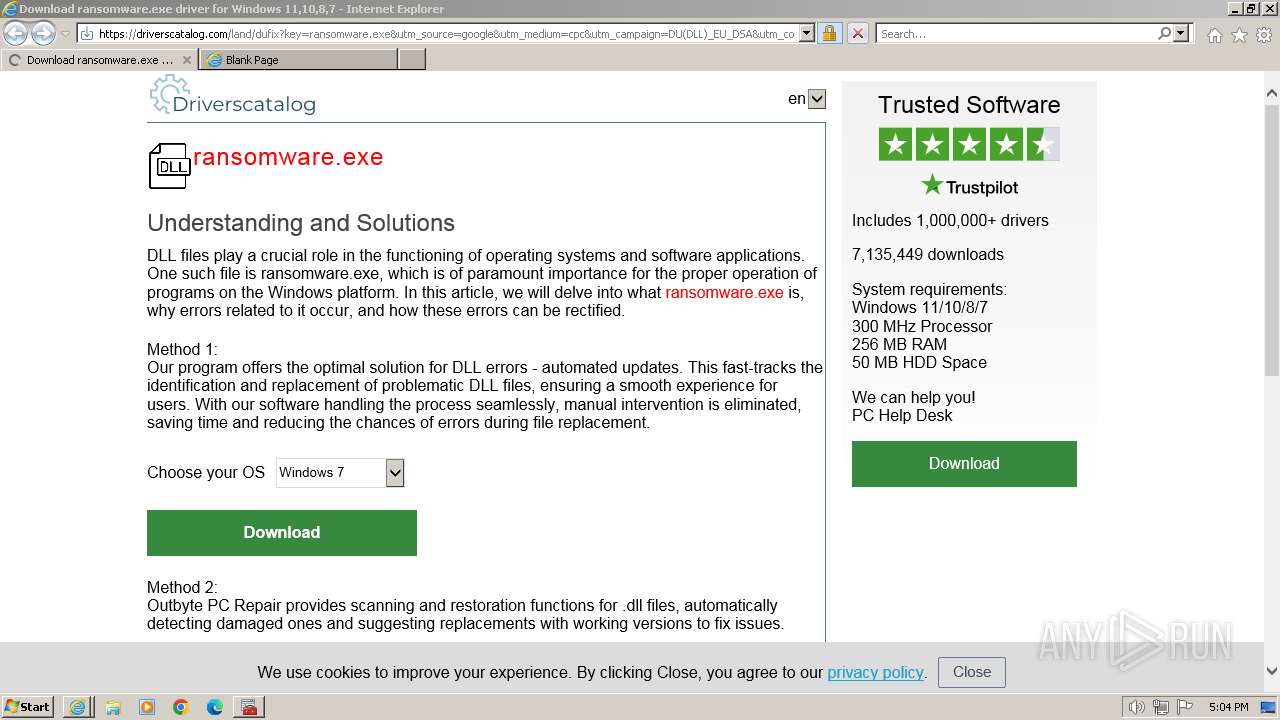
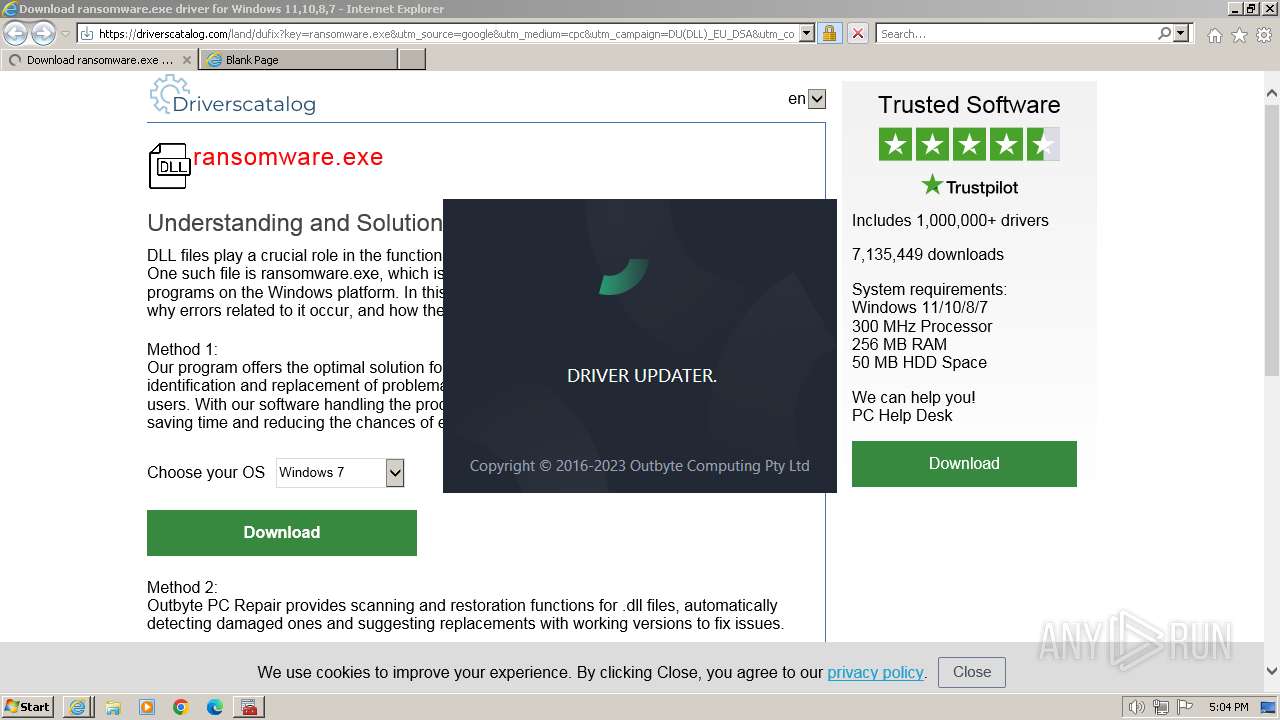
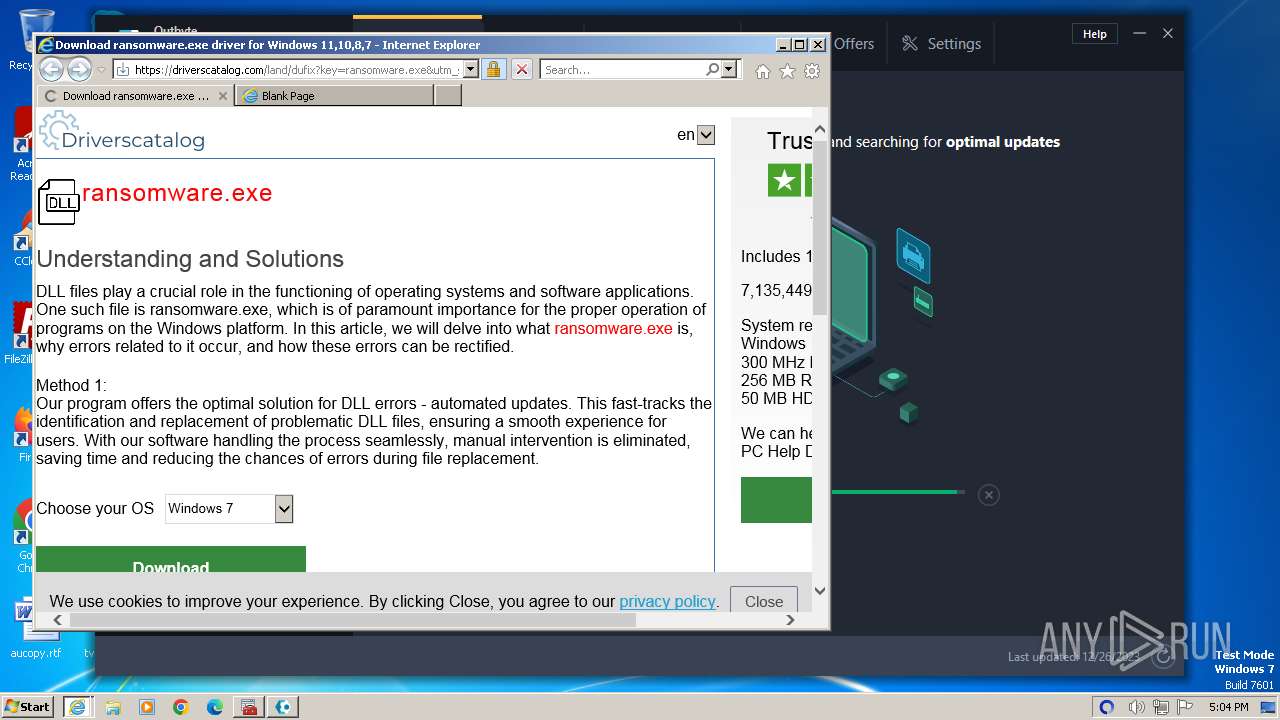
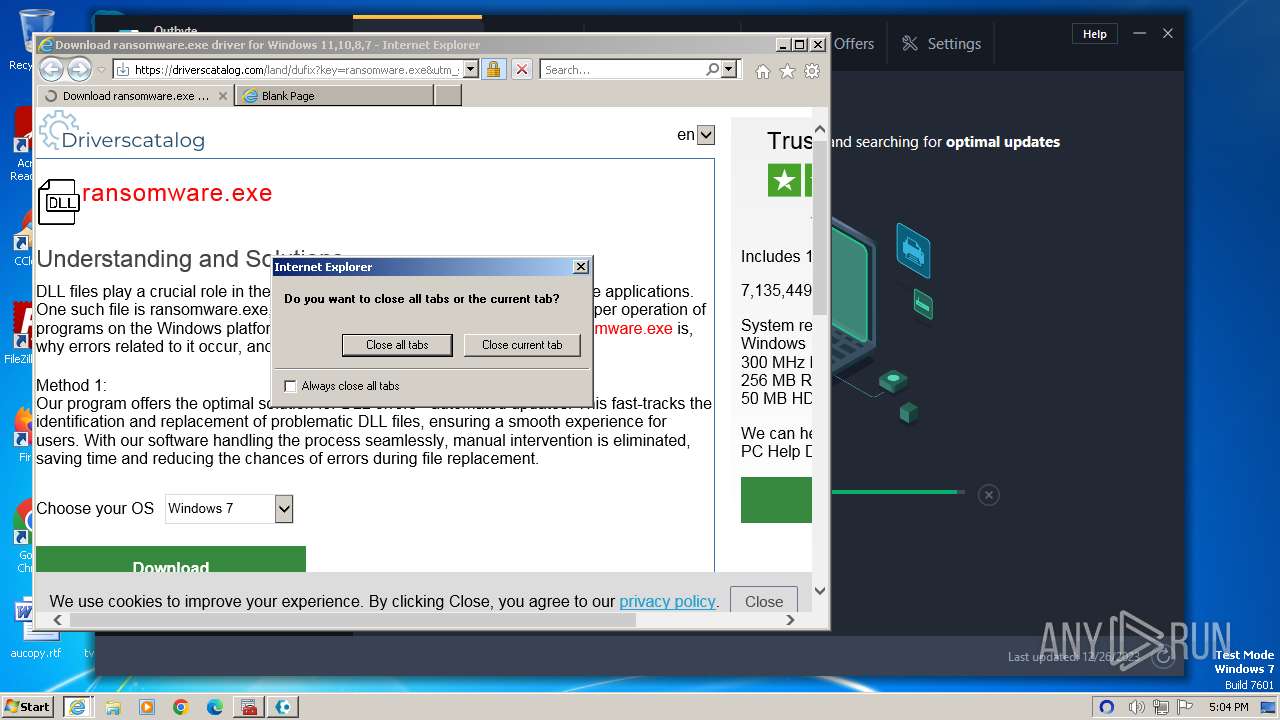
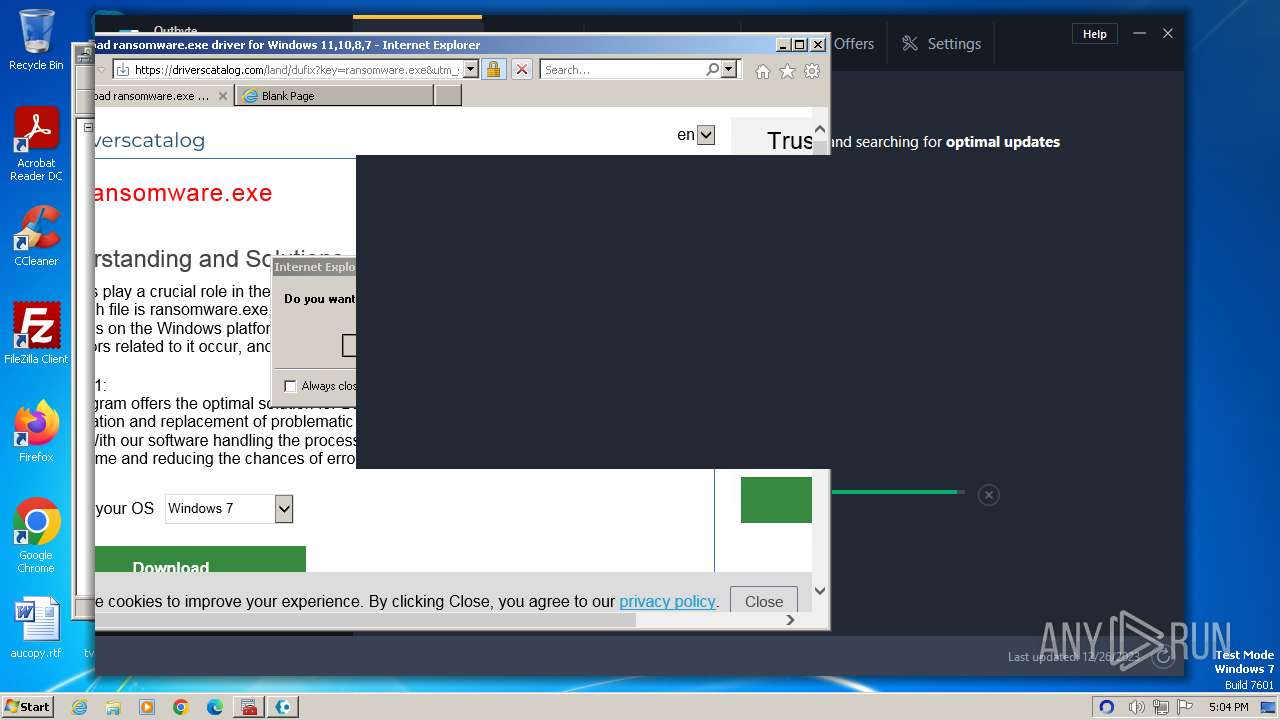
| URL: | https://driverscatalog.com/land/dufix?key=ransomware.exe&utm_source=google&utm_medium=cpc&utm_campaign=DU(DLL)_EU_DSA&utm_content=high&utm_term=ransomware.exe&gclid=Cj0KCQiAkKqsBhC3ARIsAEEjuJgPg4NxjqulwBkI5ROG0SCIQyz1susR_3NAH5BaF1TvVecAYY9MUYYaAtVjEALw_wcB |
| Full analysis: | https://app.any.run/tasks/220fc161-8147-401f-bc6d-5f0400f09339 |
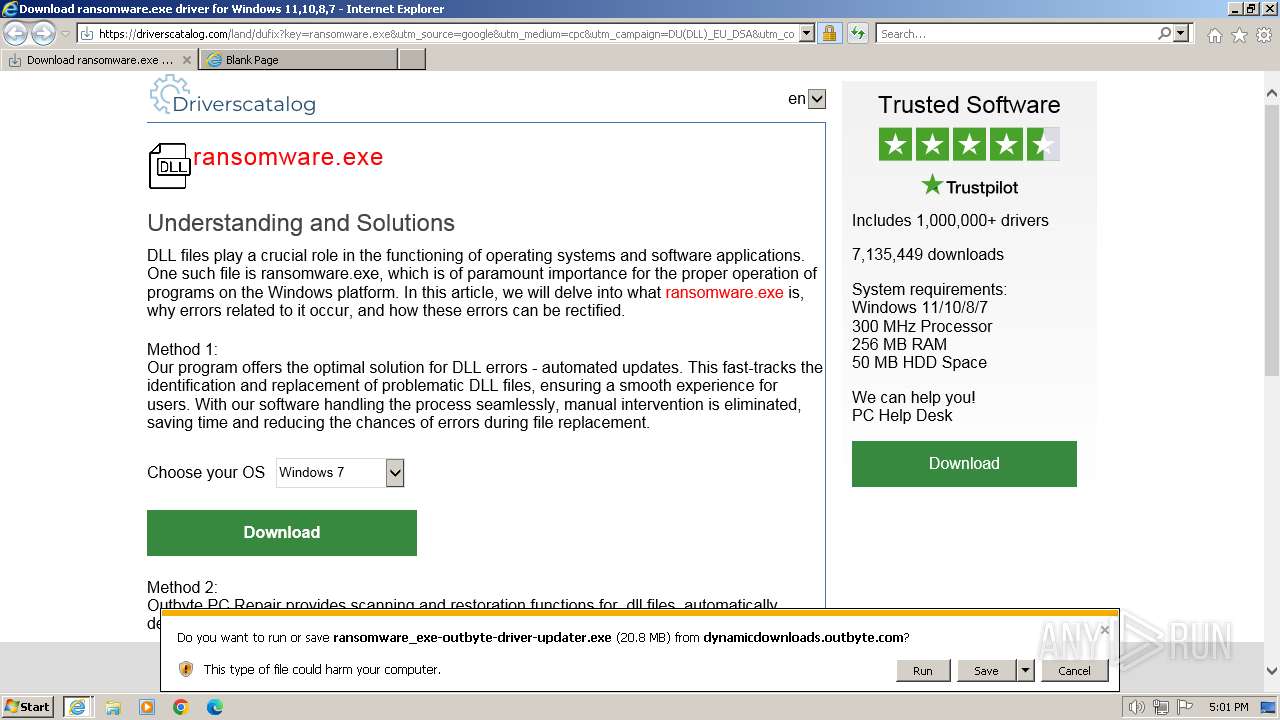
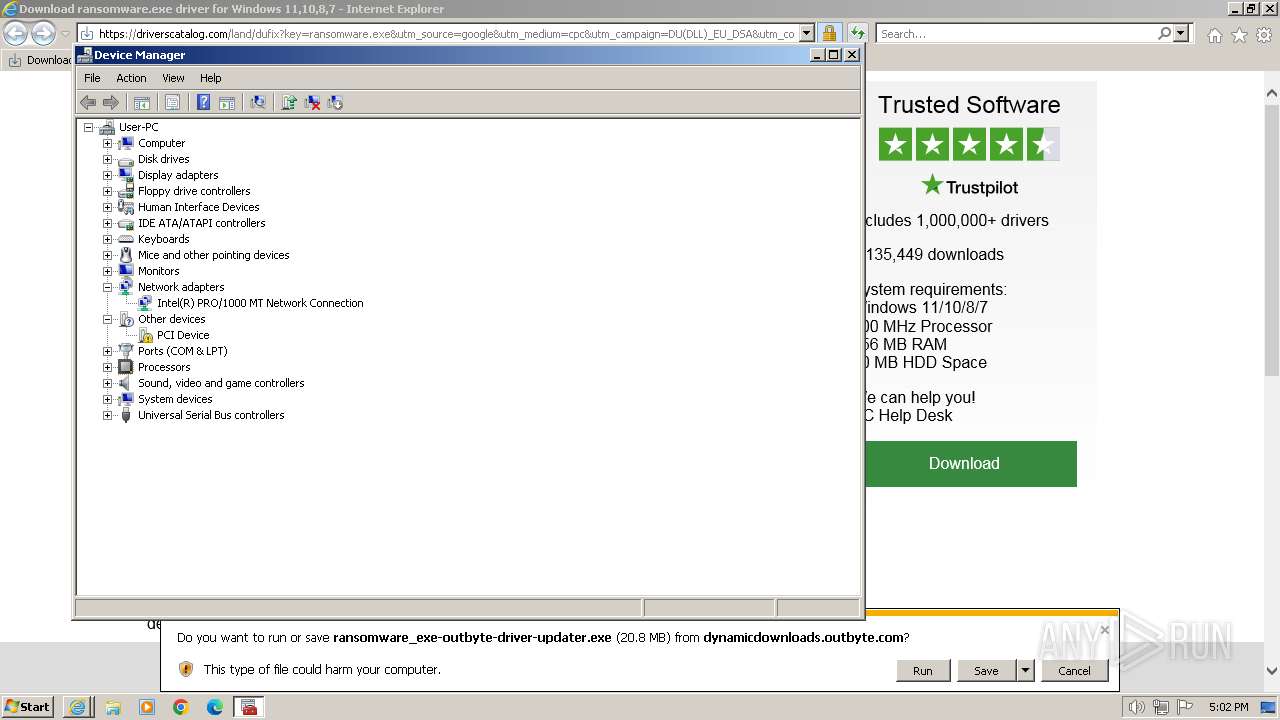
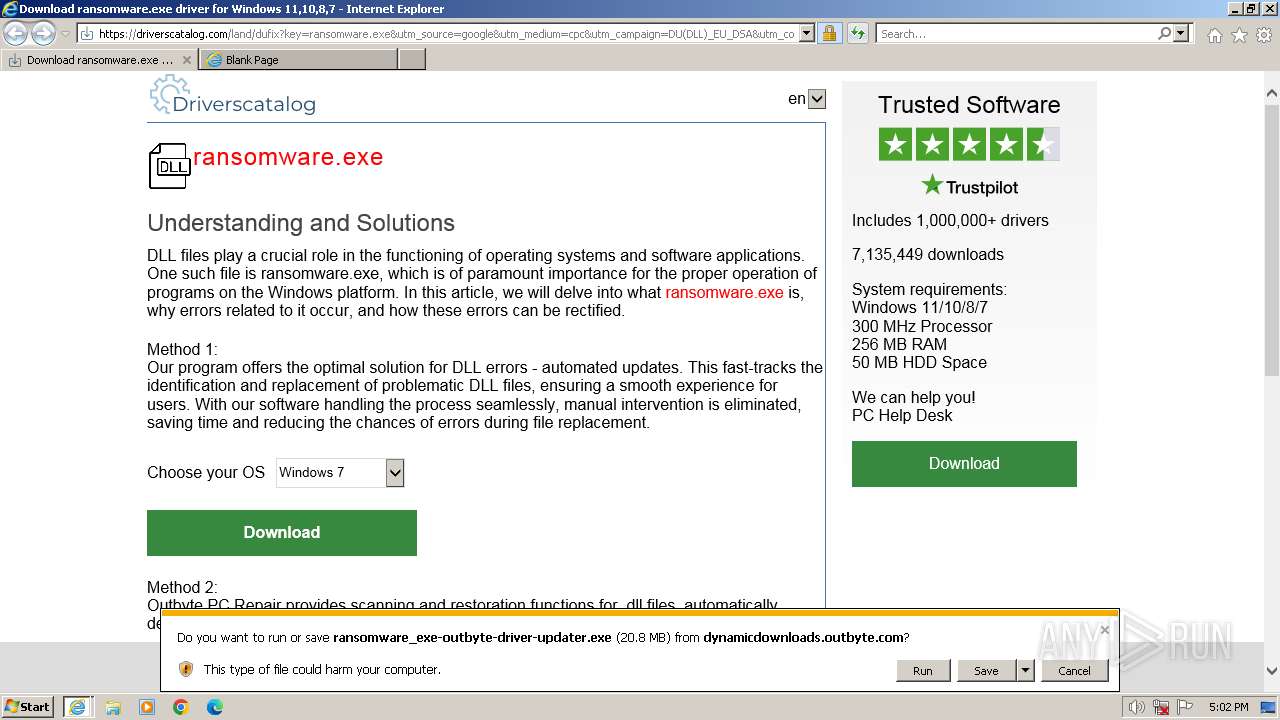
| Verdict: | Malicious activity |
| Analysis date: | December 26, 2023, 16:59:40 |
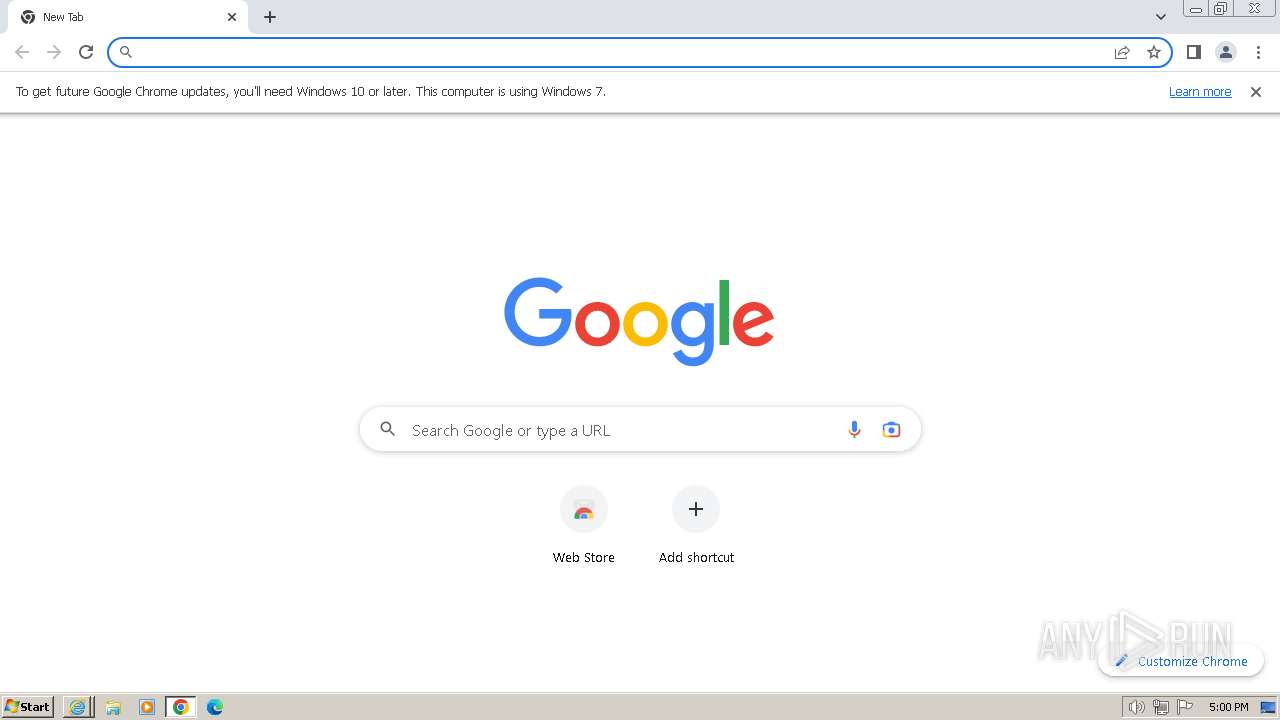
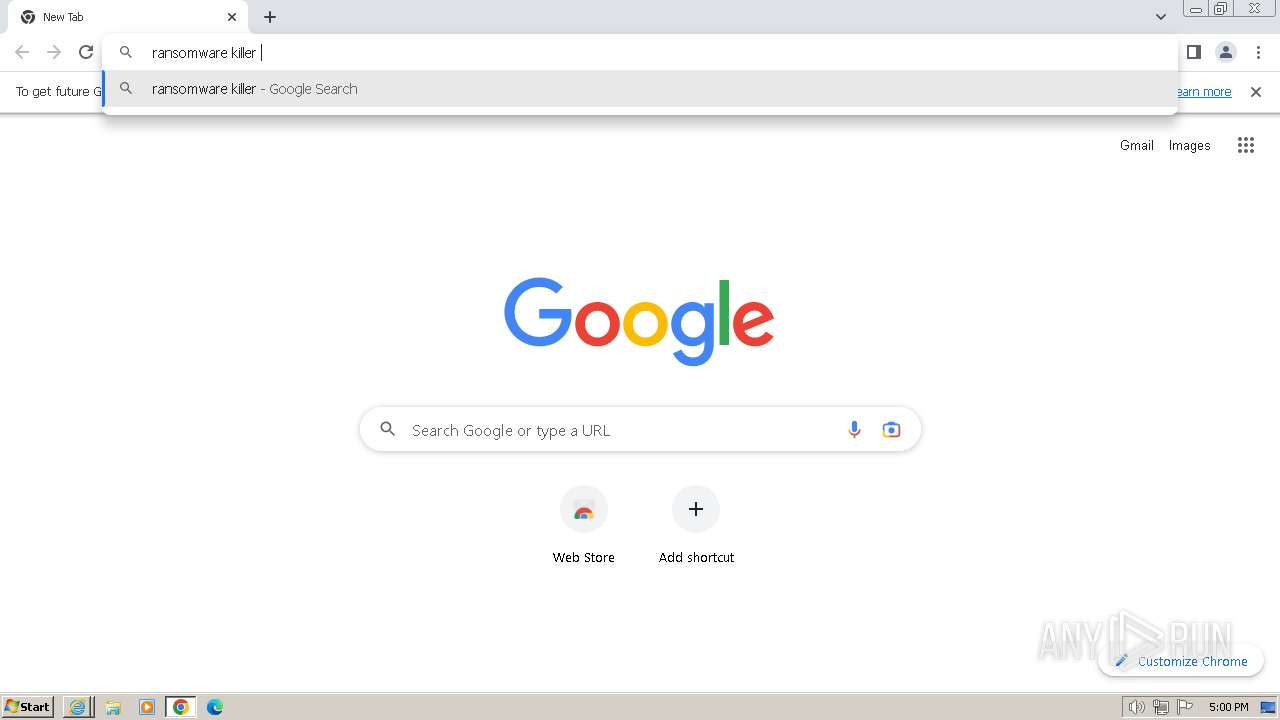
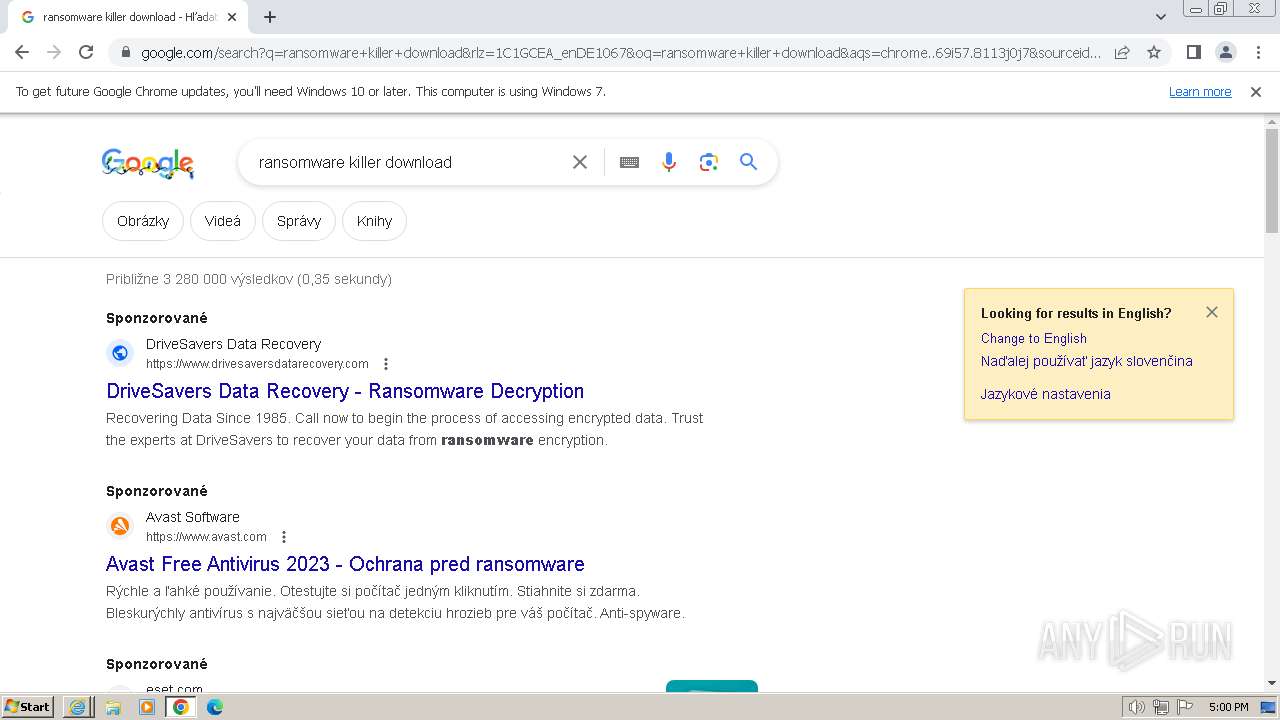
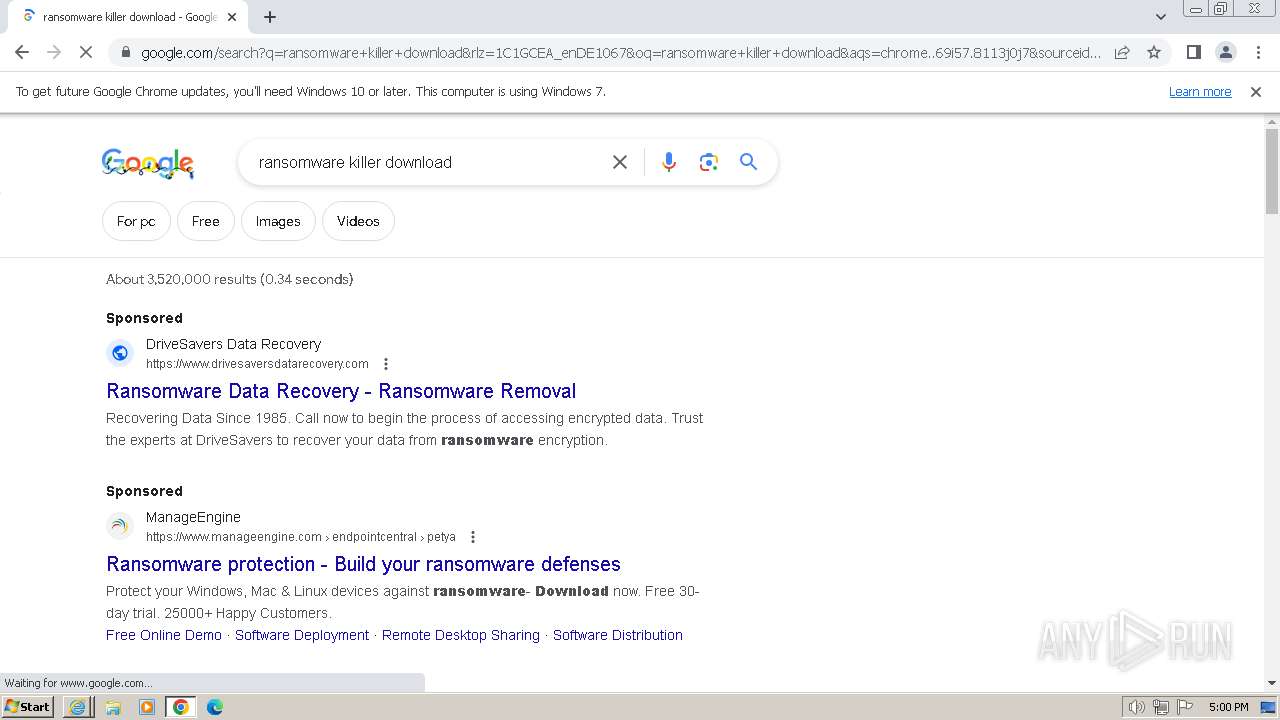
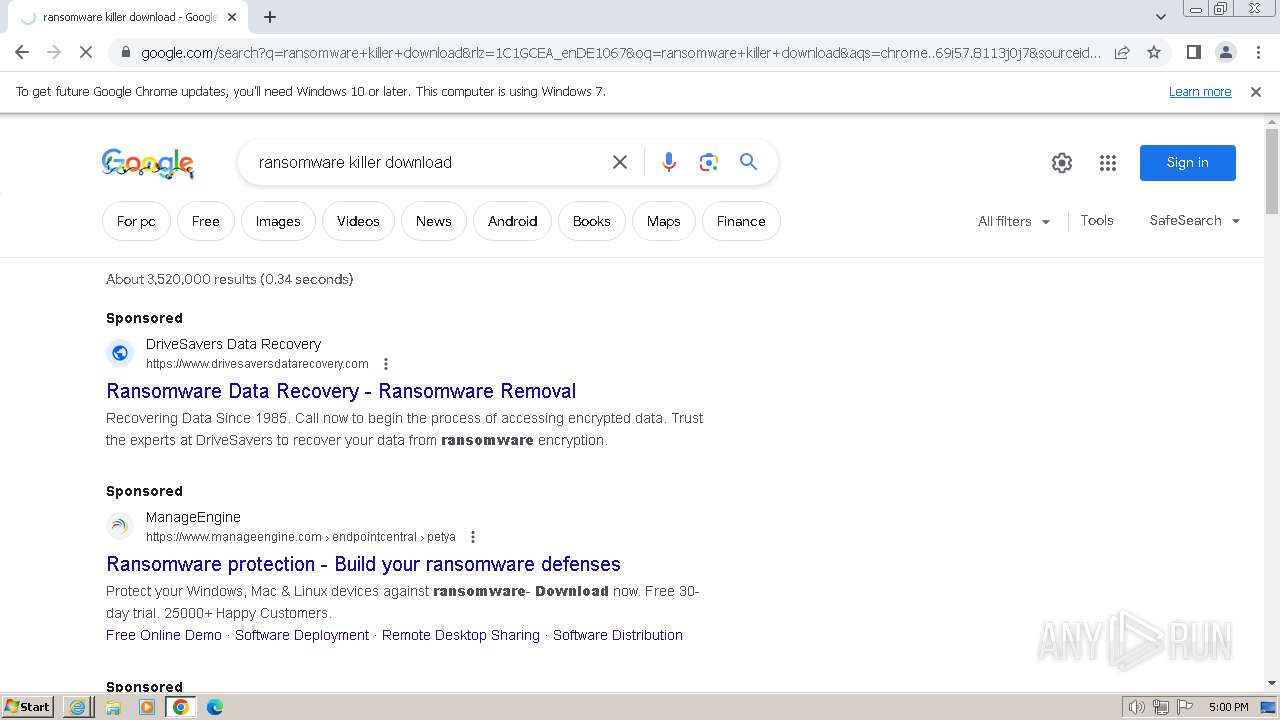
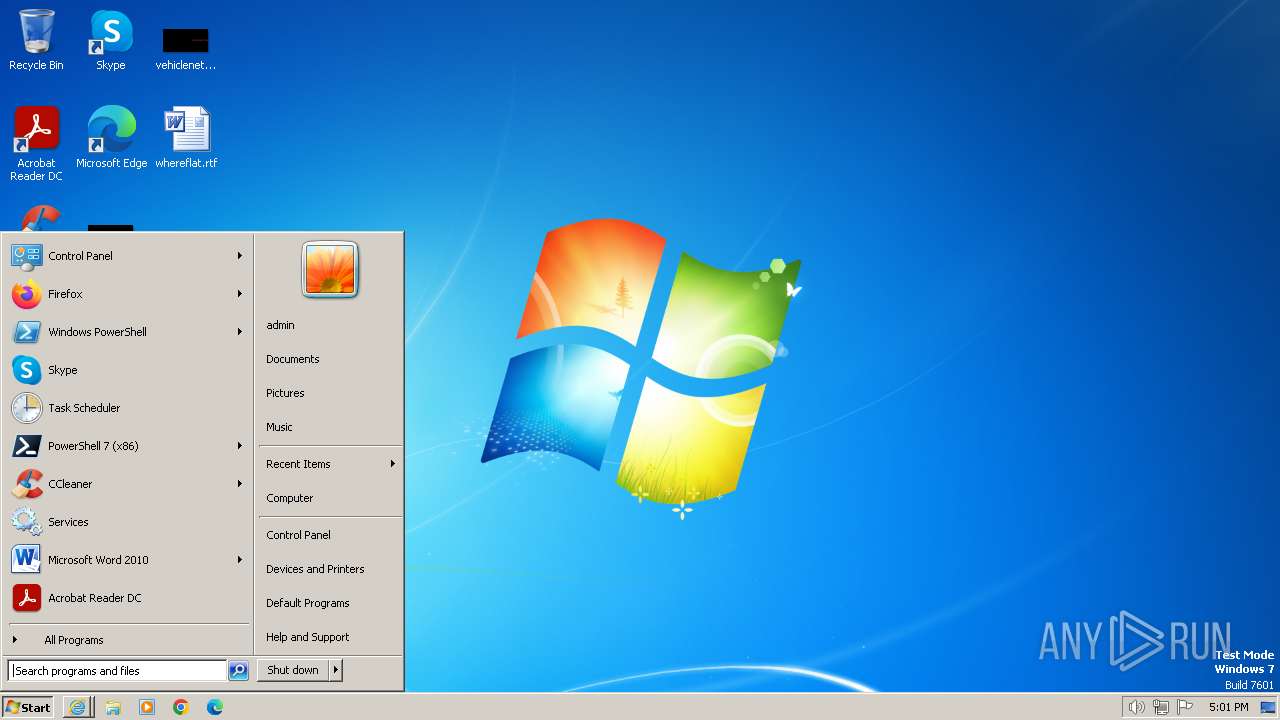
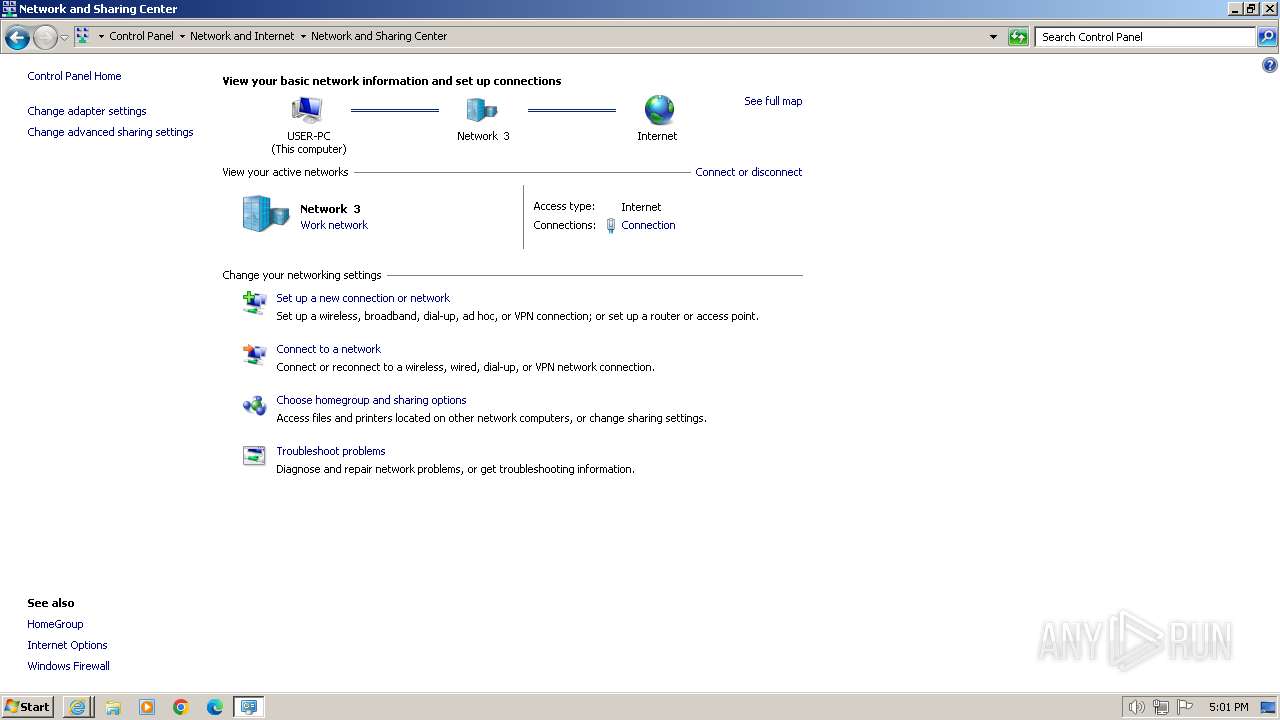
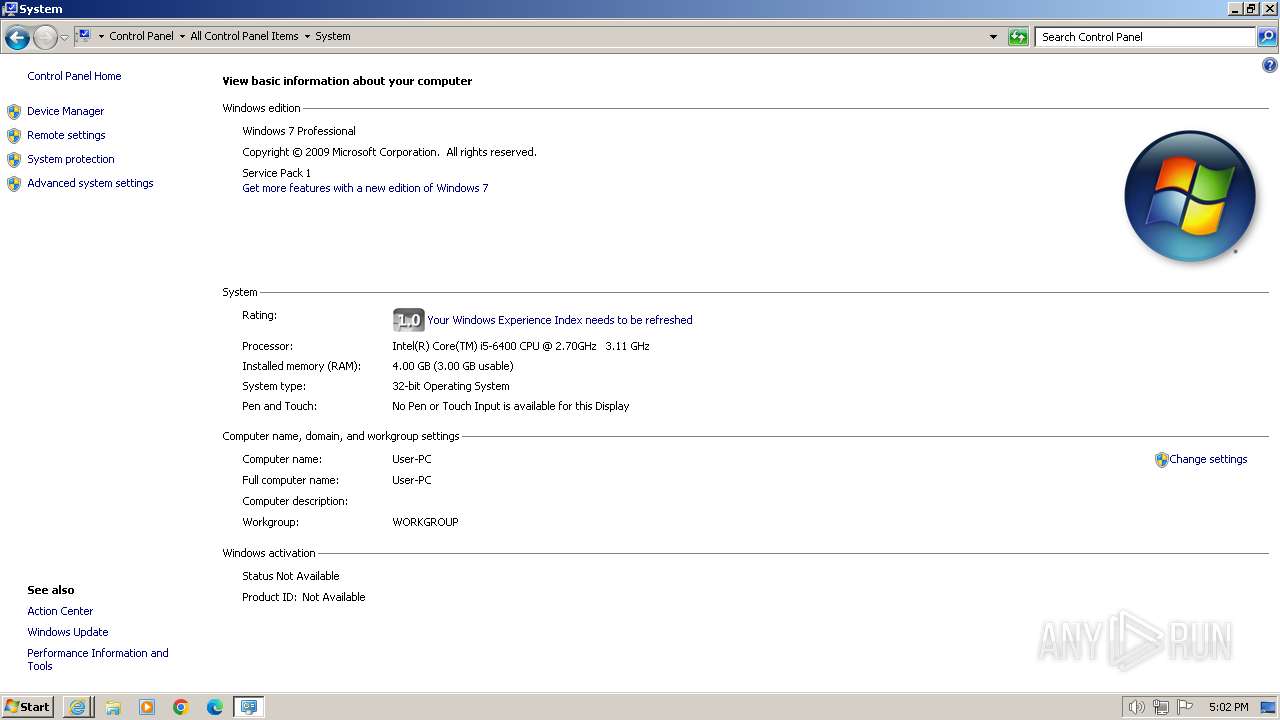
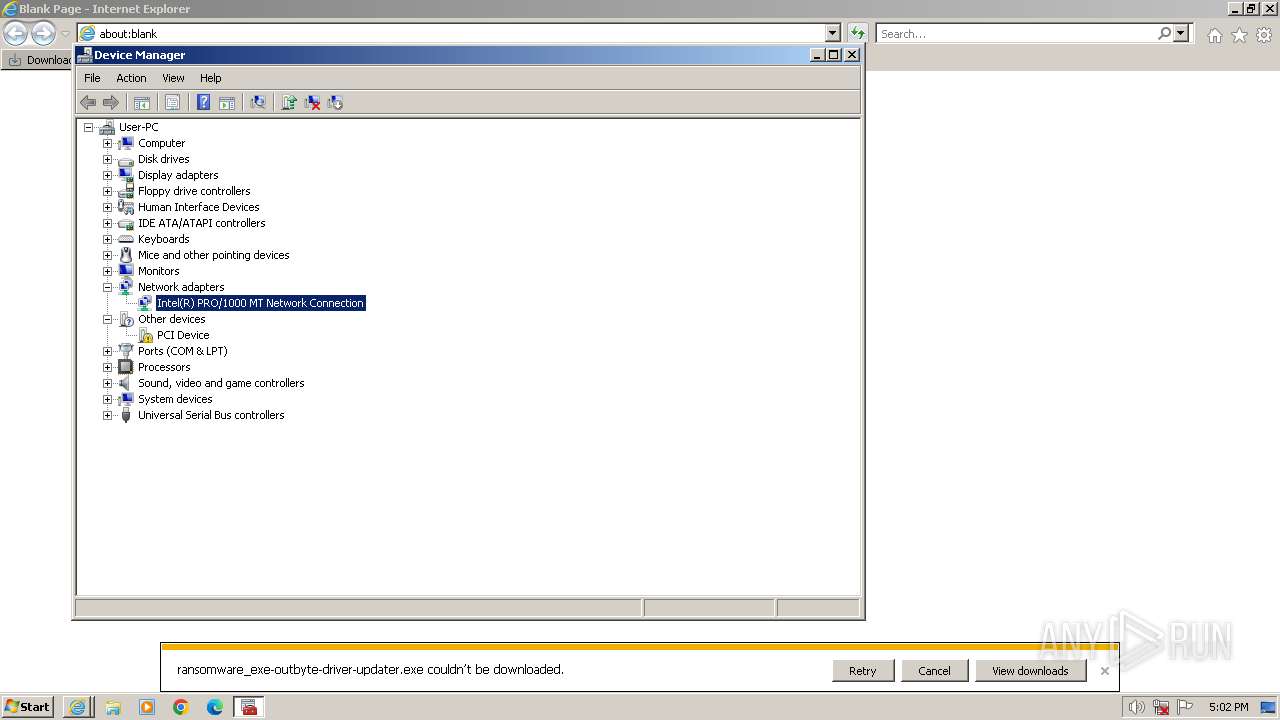
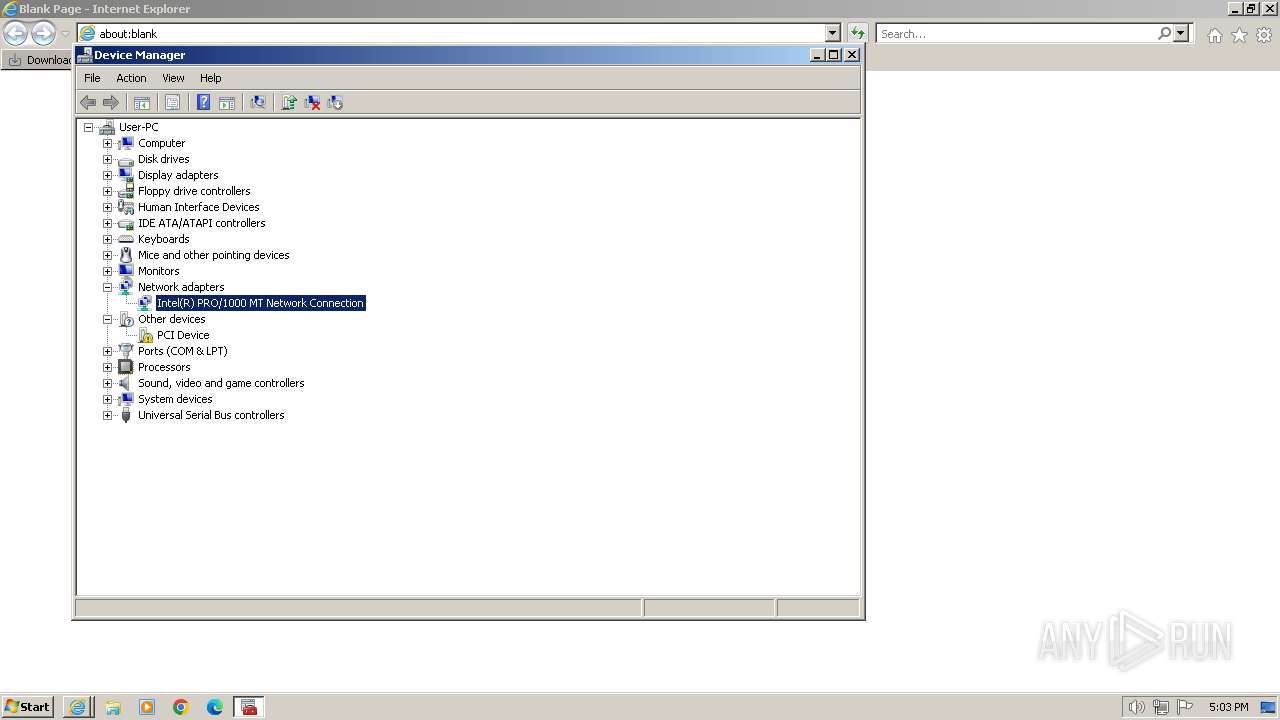
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 64DB14DE280A79690D6D7BAC2CE37C7C |
| SHA1: | E049568DA9213D5209CEDD4660C2907FDDF804D7 |
| SHA256: | A5BACF50CFA8FD60BA11B723BC1DB97A296EEFE771D7637C14868D802F92CAF3 |
| SSDEEP: | 6:2WDT31aLdj8I7WuhHhcmD6hRazIQak4m6xIGv:2WPqBhHWmD6hRaXraIGv |
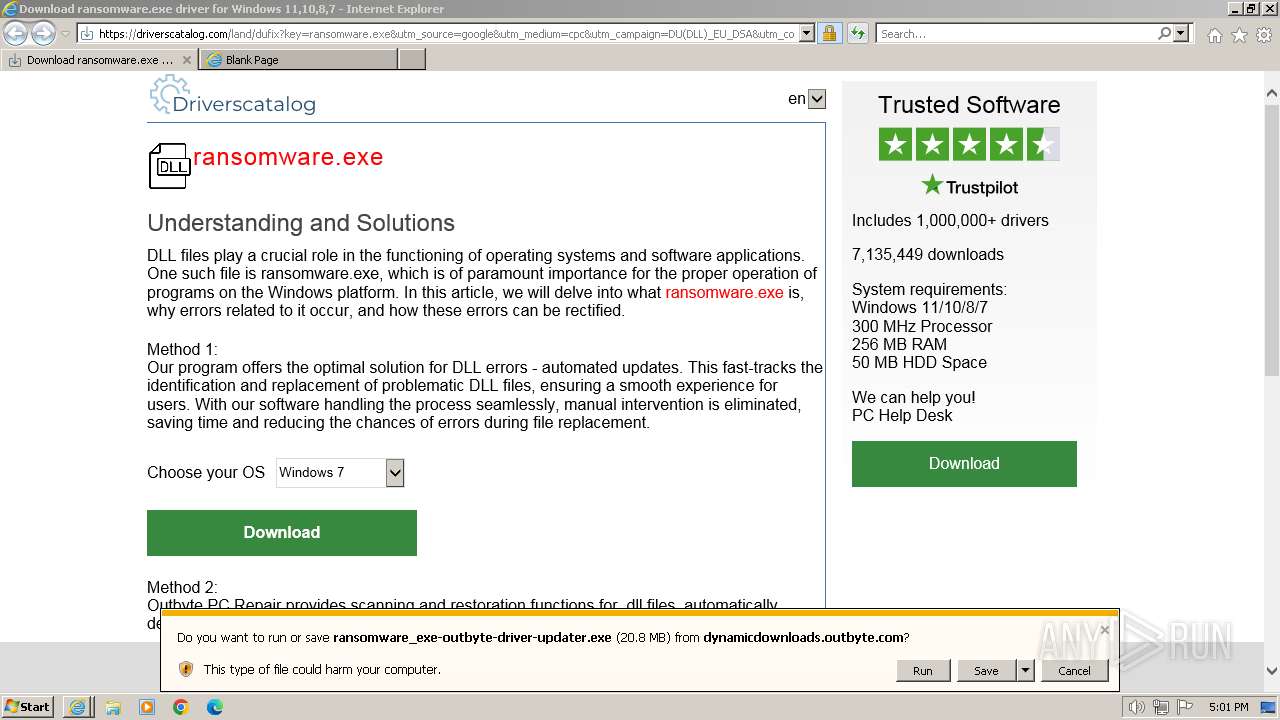
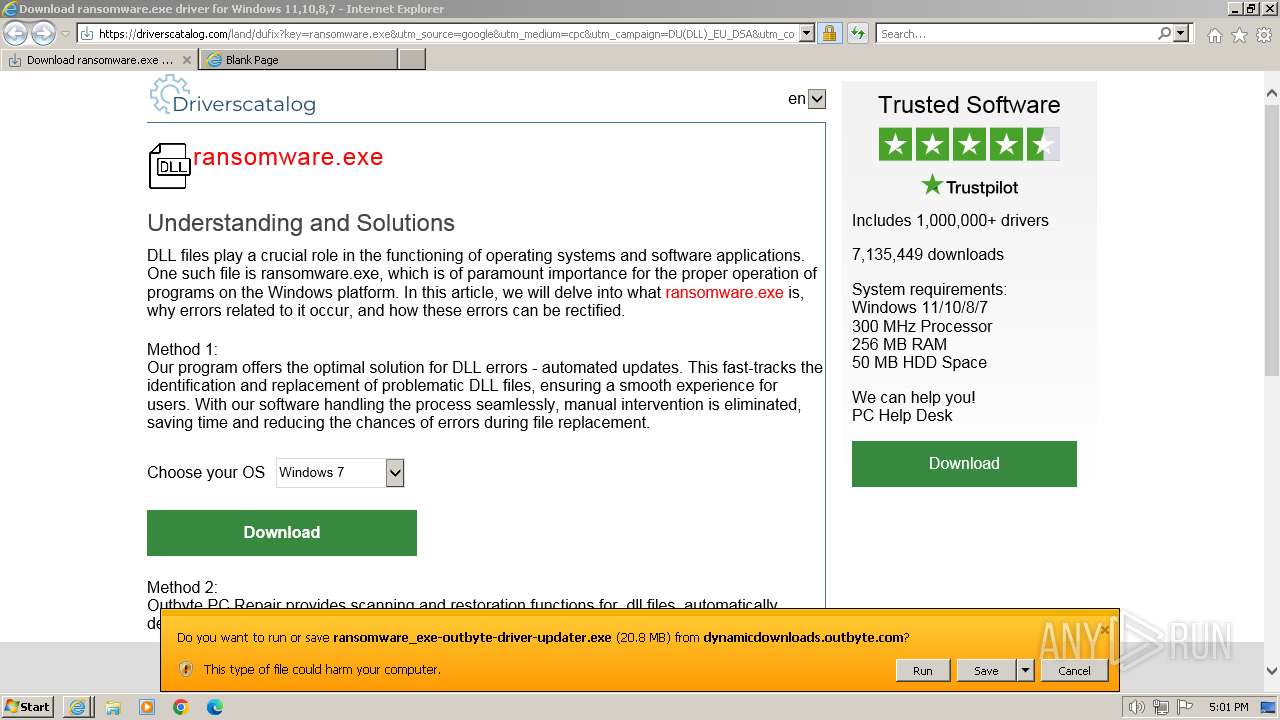
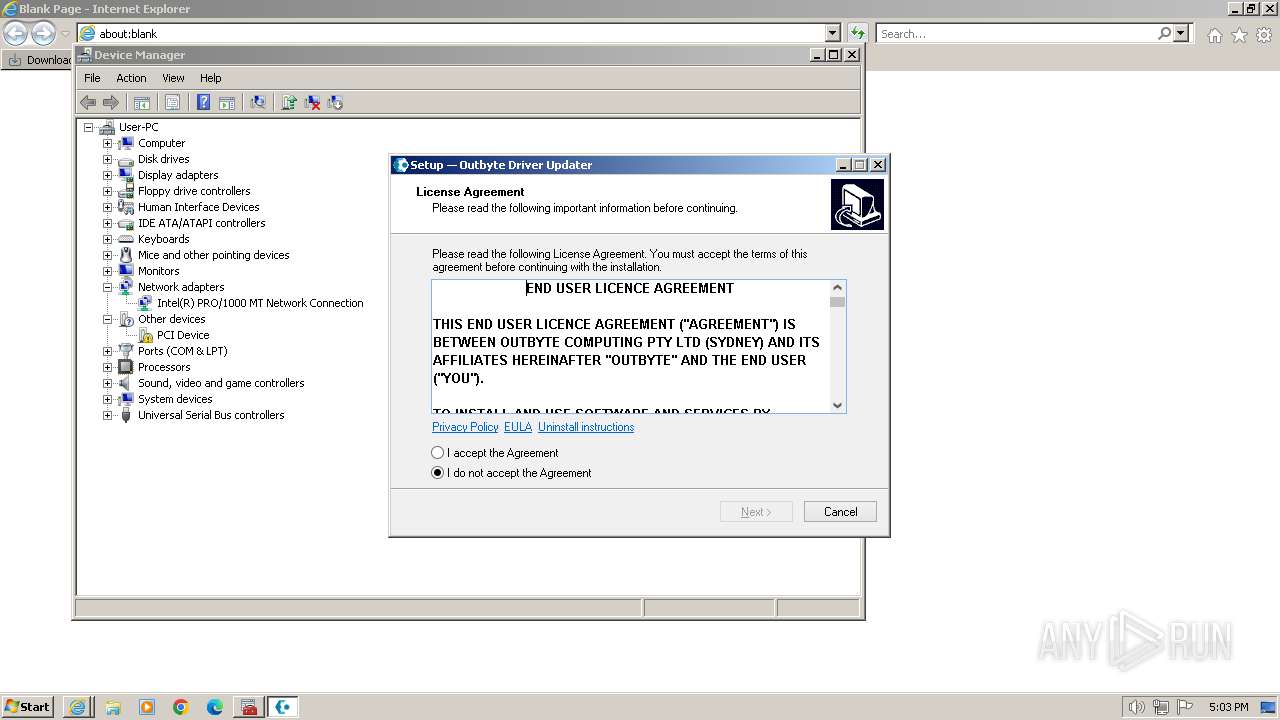
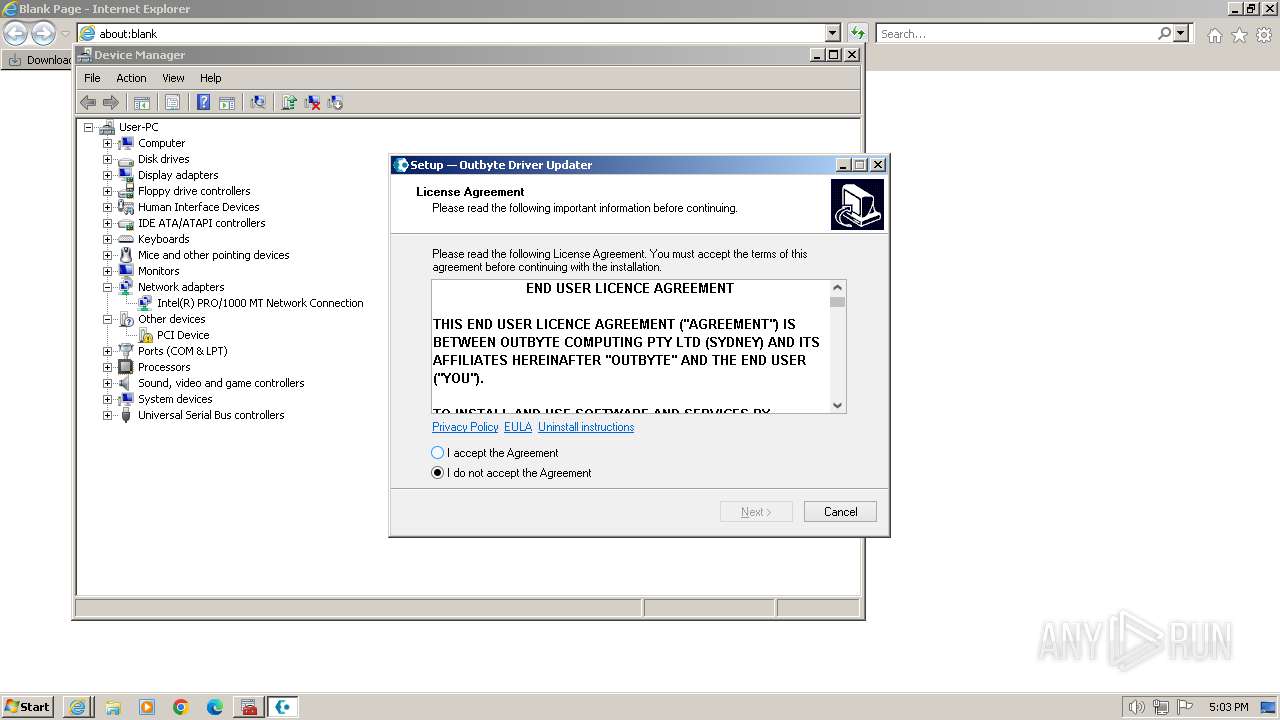
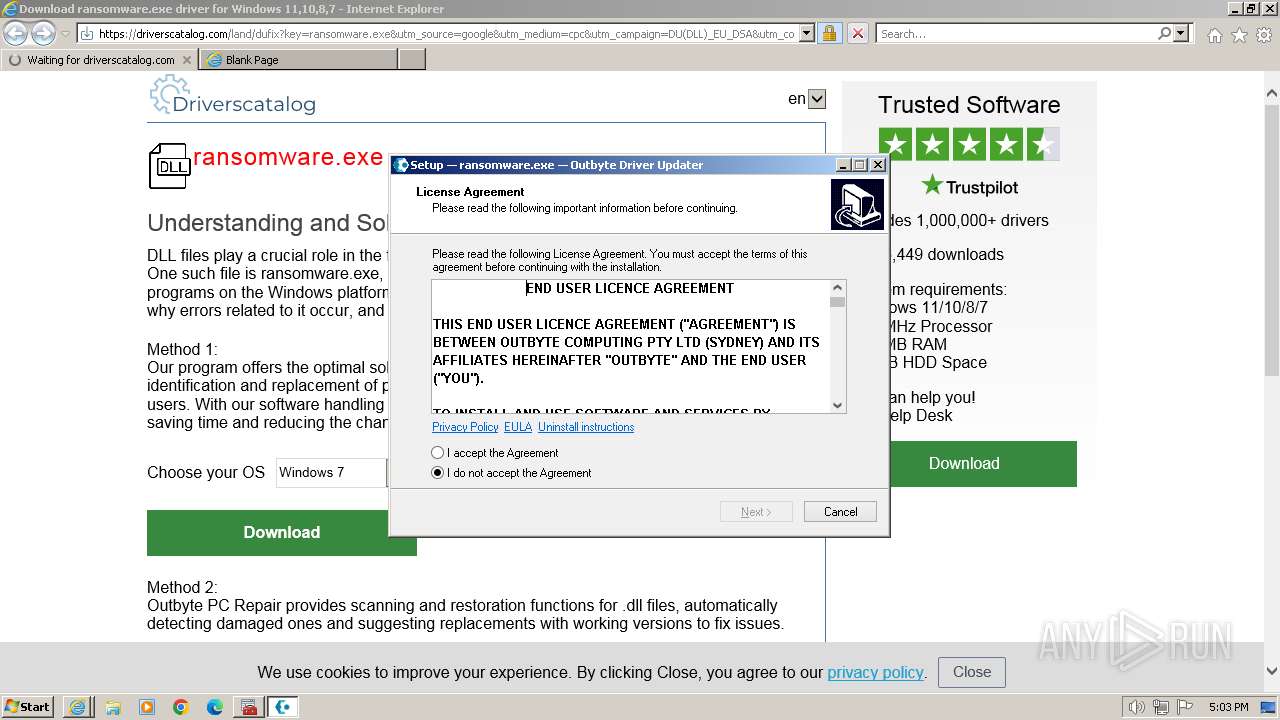
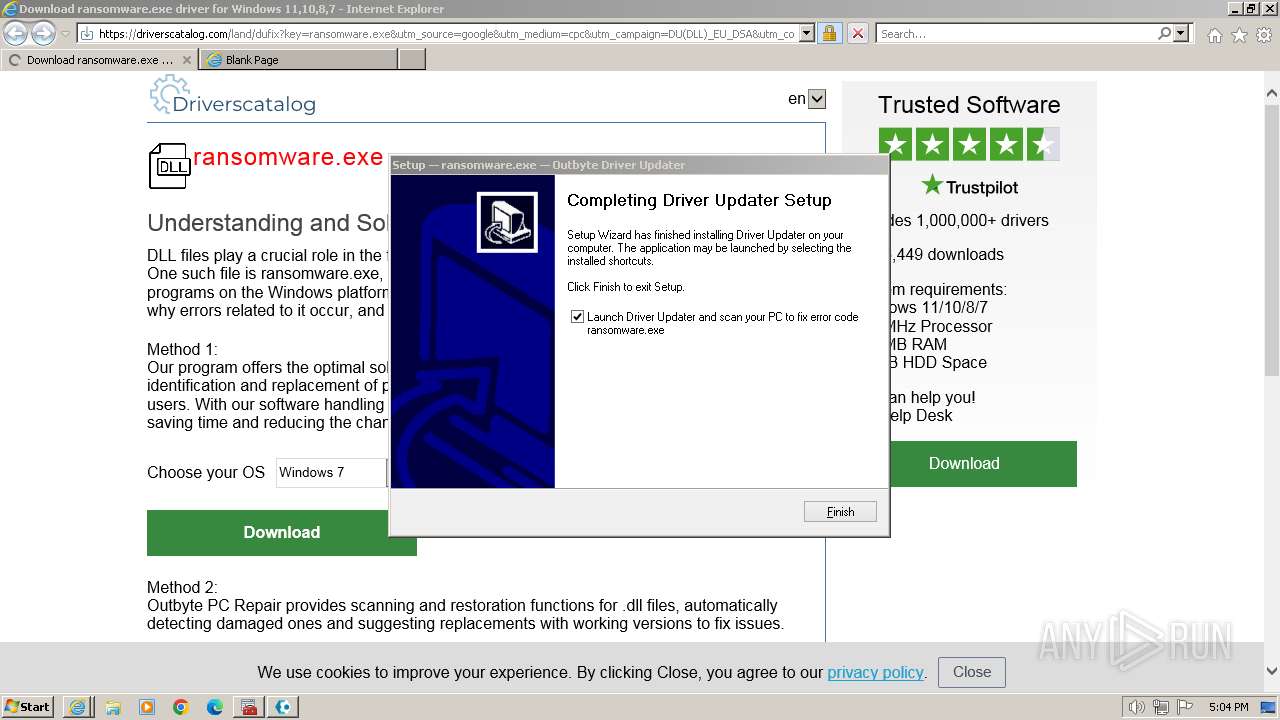
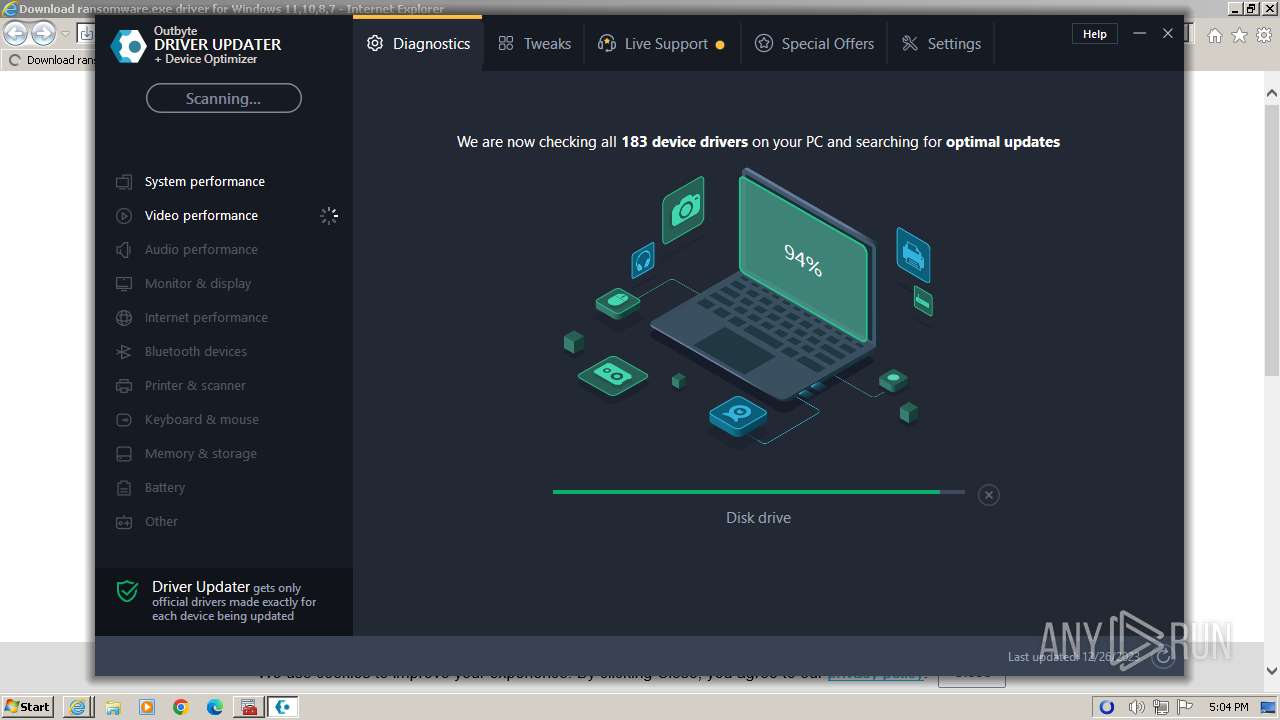
MALICIOUS
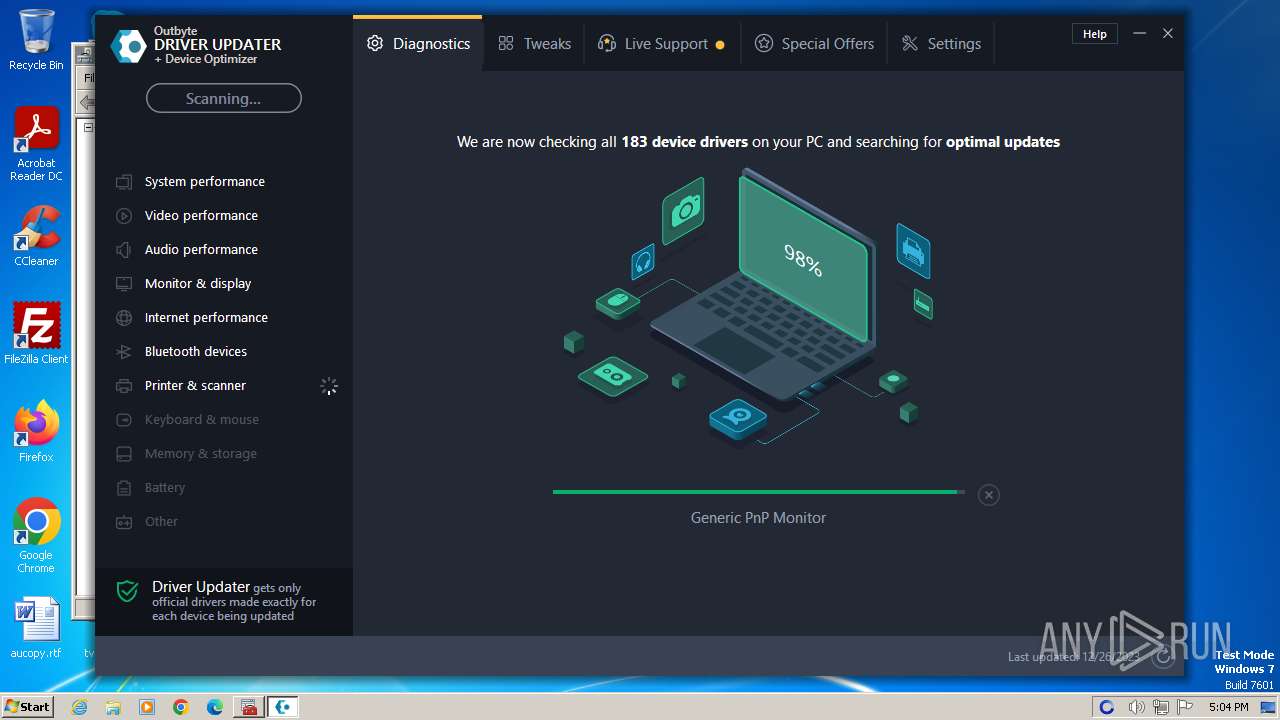
Steals credentials from Web Browsers
- DriverUpdater.exe (PID: 3652)
Actions looks like stealing of personal data
- DriverUpdater.exe (PID: 3652)
- CustomDllSurrogate.x32.exe (PID: 1820)
- DriverUpdater.exe (PID: 2808)
Registers / Runs the DLL via REGSVR32.EXE
- DriverUpdater.exe (PID: 2808)
SUSPICIOUS
Checks Windows Trust Settings
- Installer.exe (PID: 2988)
- DriverUpdater.exe (PID: 3652)
- DriverUpdater.exe (PID: 2808)
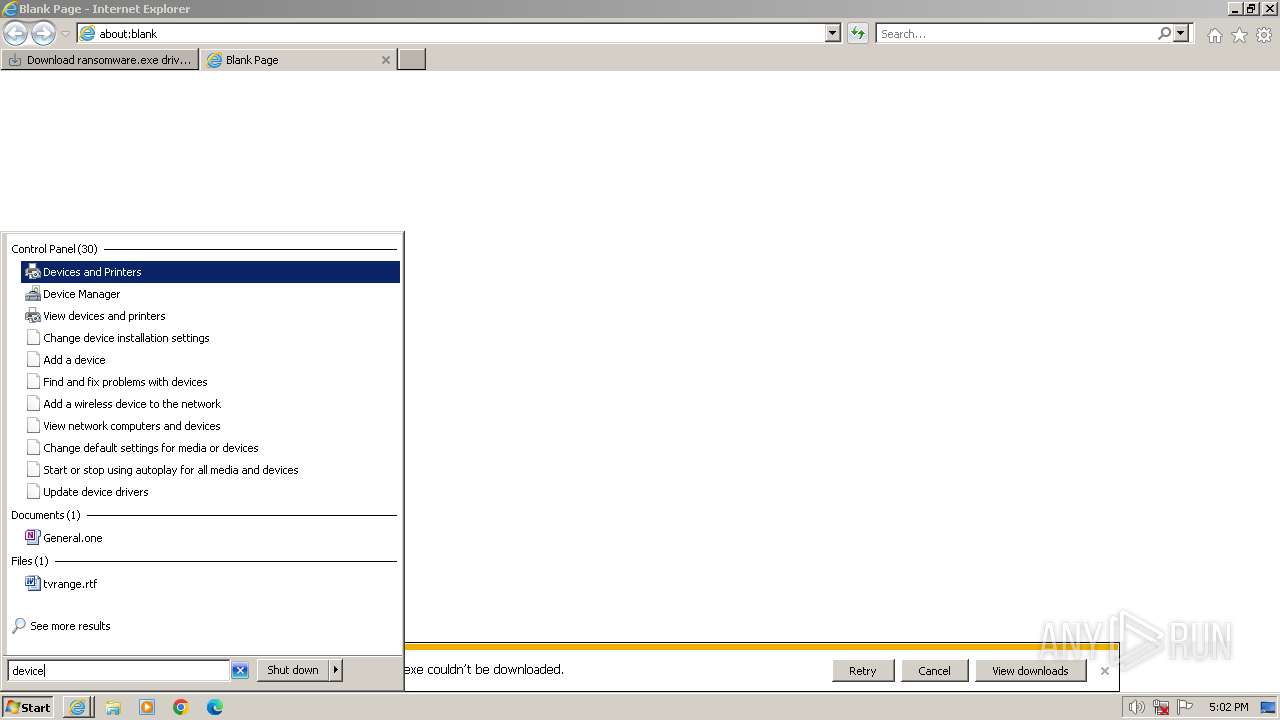
Reads the BIOS version
- Installer.exe (PID: 2988)
- DriverUpdater.exe (PID: 3652)
- DriverUpdater.exe (PID: 2808)
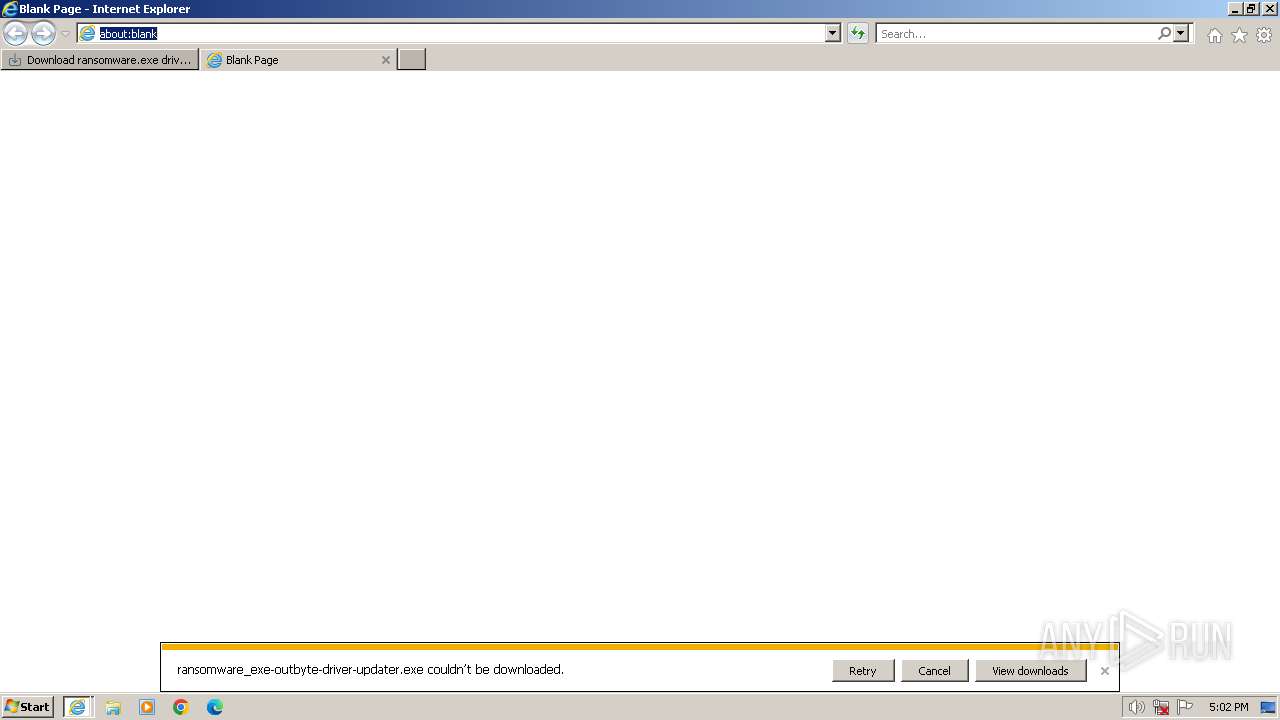
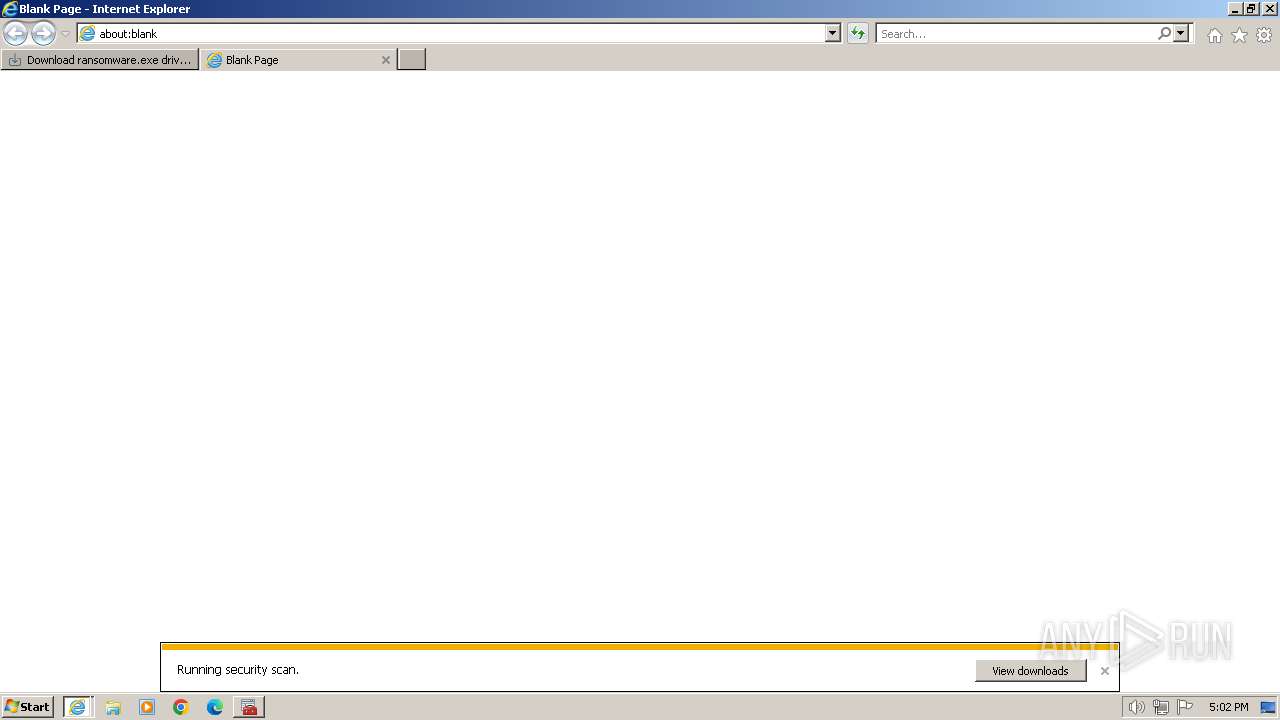
Reads the Internet Settings
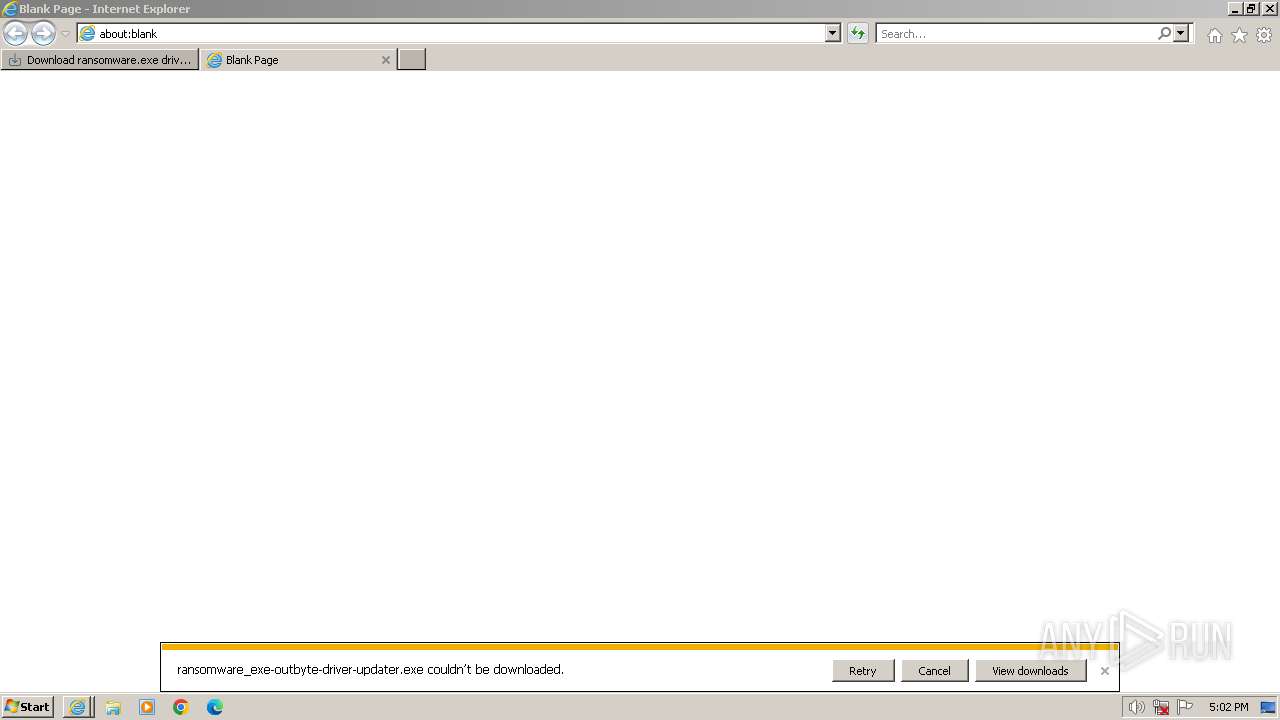
- ransomware_exe-outbyte-driver-updater.exe (PID: 2944)
- Installer.exe (PID: 2988)
- DriverUpdater.exe (PID: 2808)
Reads security settings of Internet Explorer
- Installer.exe (PID: 2988)
- DriverUpdater.exe (PID: 3652)
- DriverUpdater.exe (PID: 2808)
Reads settings of System Certificates
- Installer.exe (PID: 2988)
- DriverUpdater.exe (PID: 3652)
- DriverUpdater.exe (PID: 2808)
Adds/modifies Windows certificates
- DriverUpdater.exe (PID: 3652)
- DriverUpdater.exe (PID: 2808)
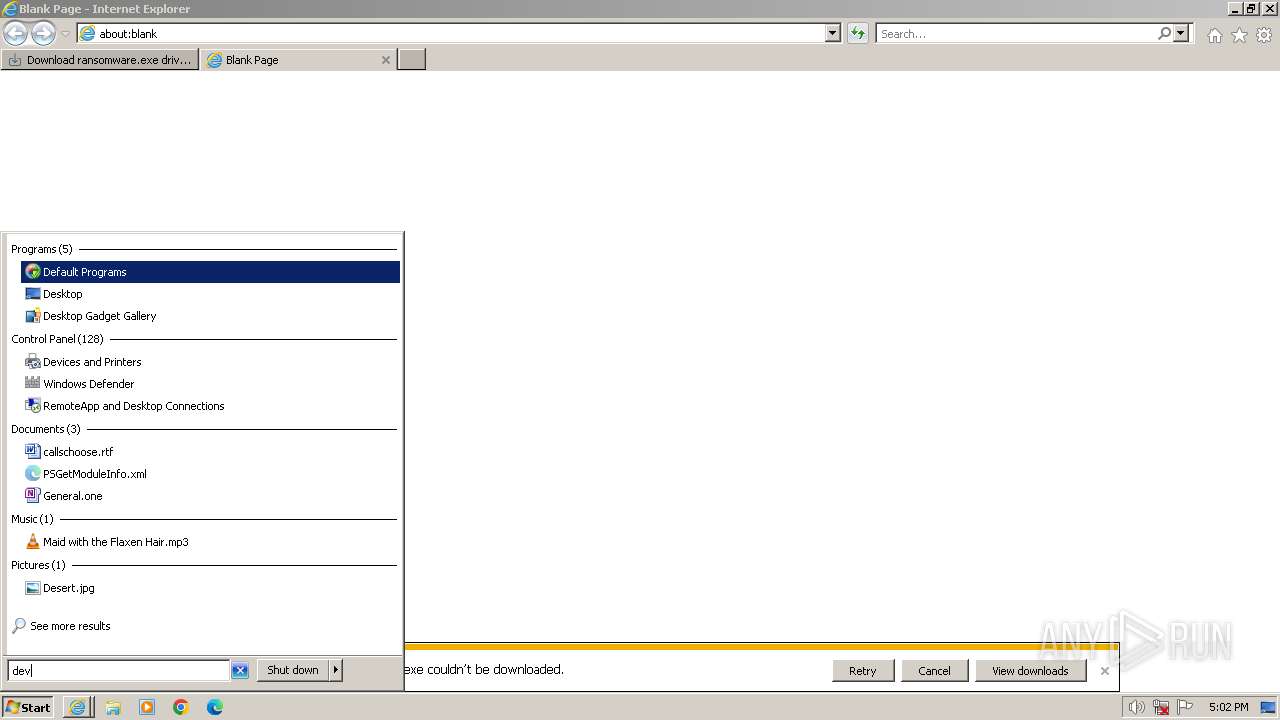
Searches for installed software
- dllhost.exe (PID: 3916)
- DriverUpdater.exe (PID: 3652)
- DriverUpdater.exe (PID: 2808)
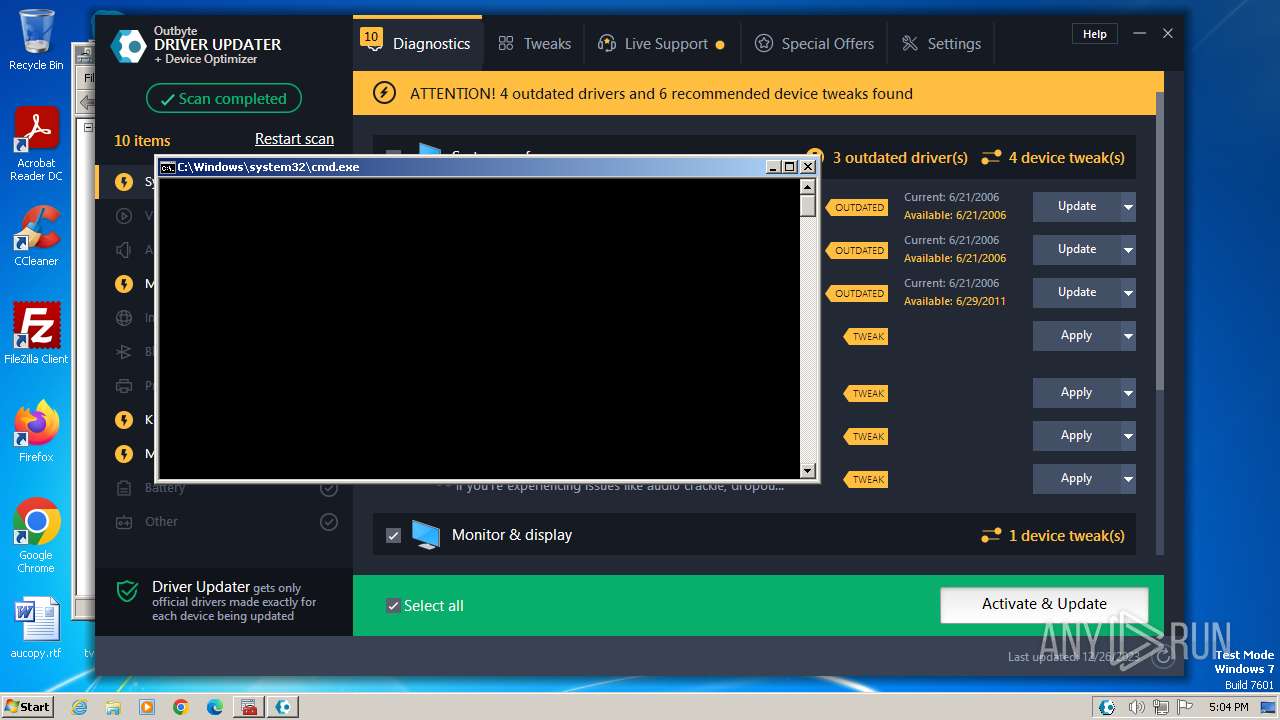
Starts CMD.EXE for commands execution
- DriverUpdater.exe (PID: 2808)
INFO
Application launched itself
- iexplore.exe (PID: 2044)
- chrome.exe (PID: 2640)
- msedge.exe (PID: 3988)
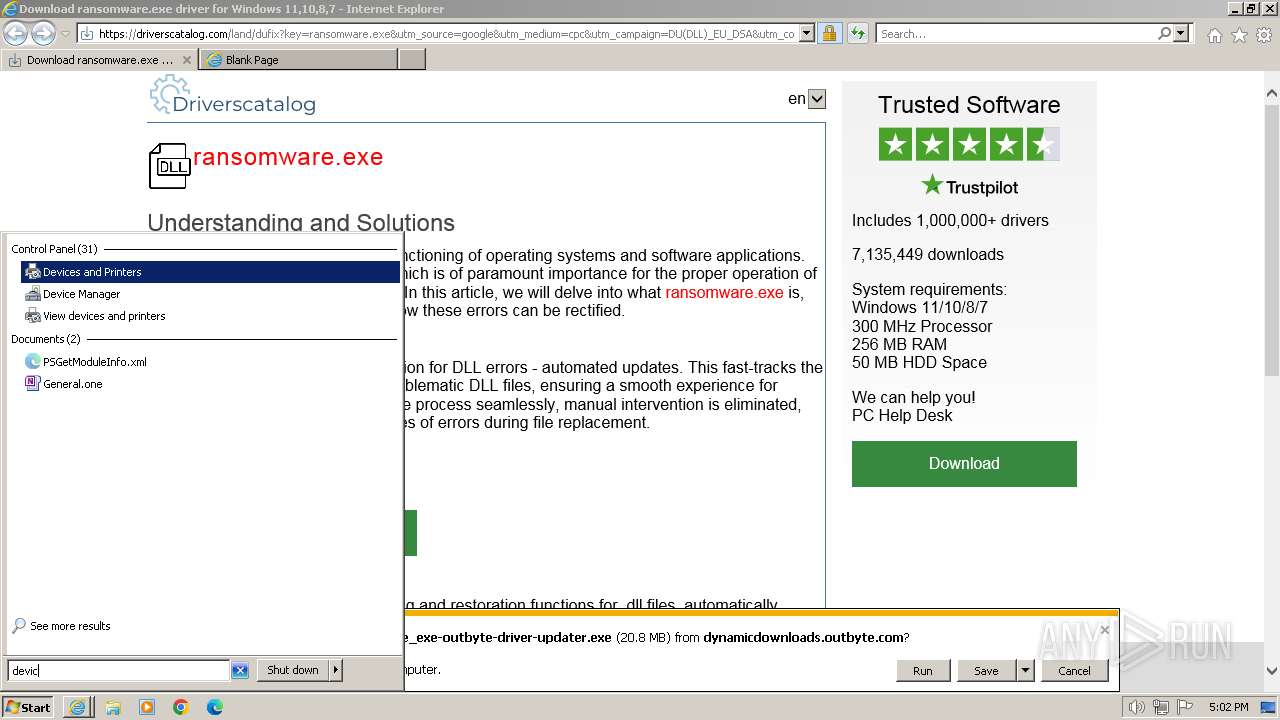
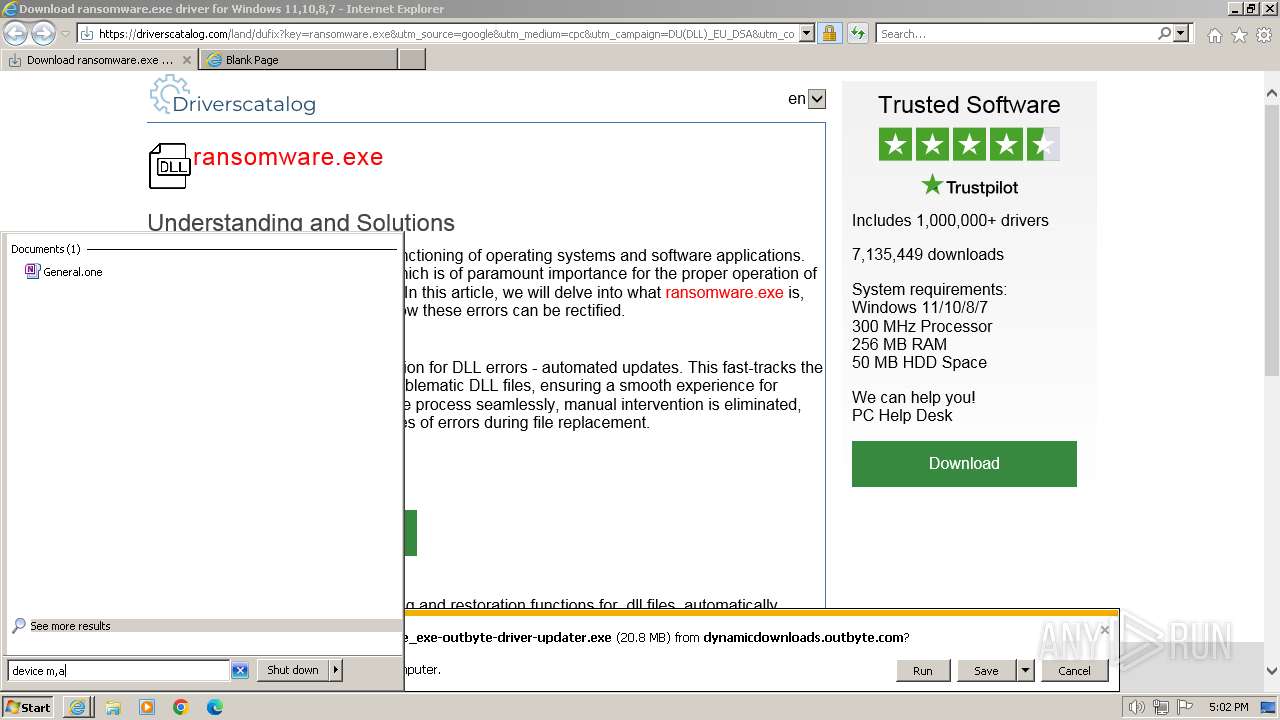
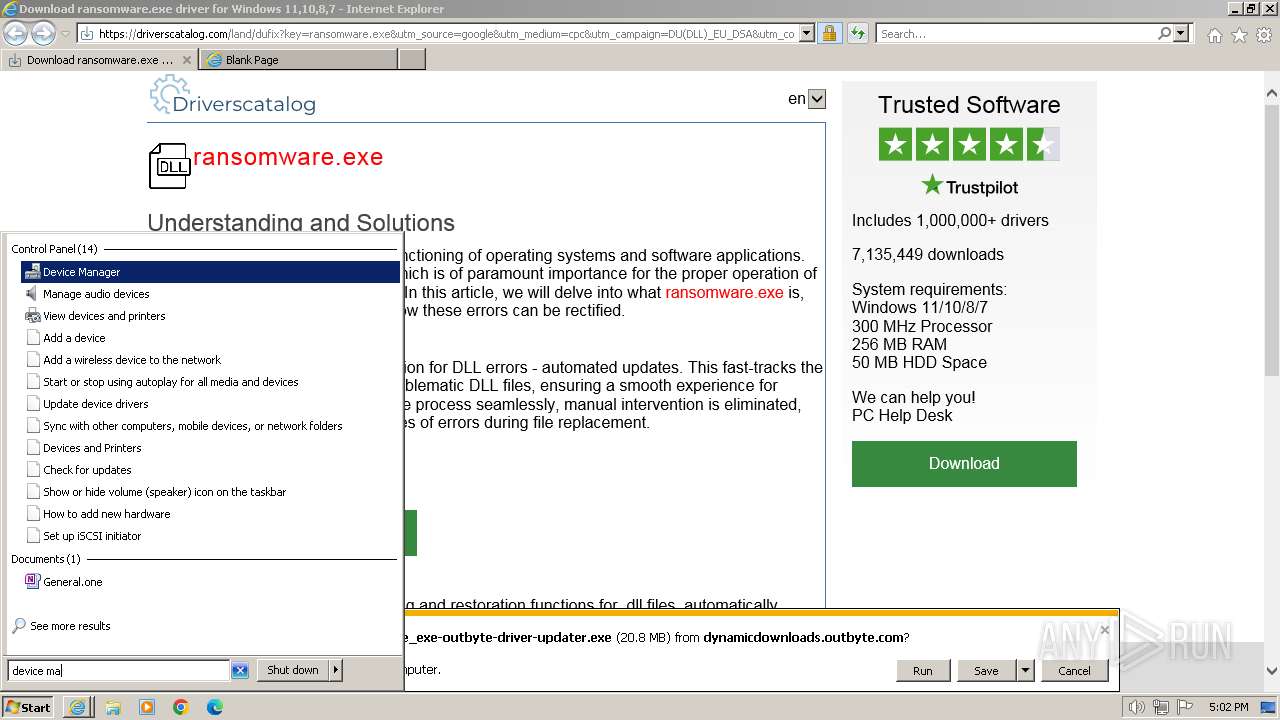
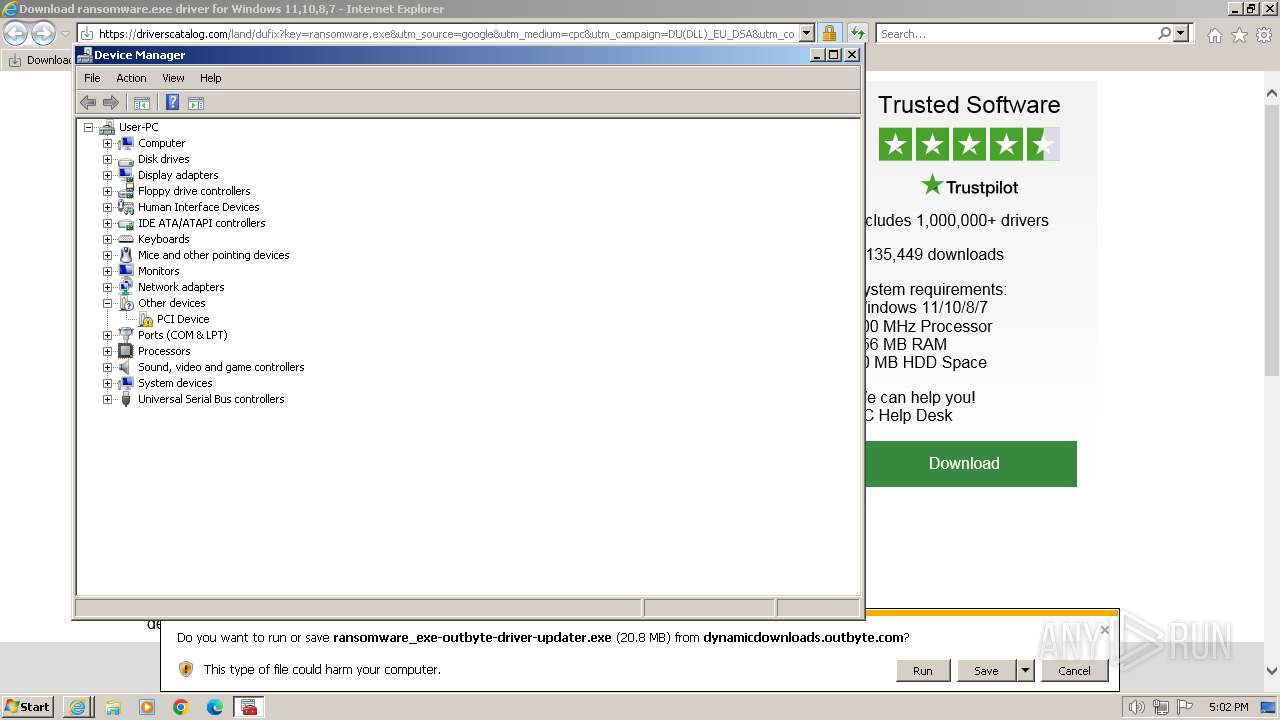
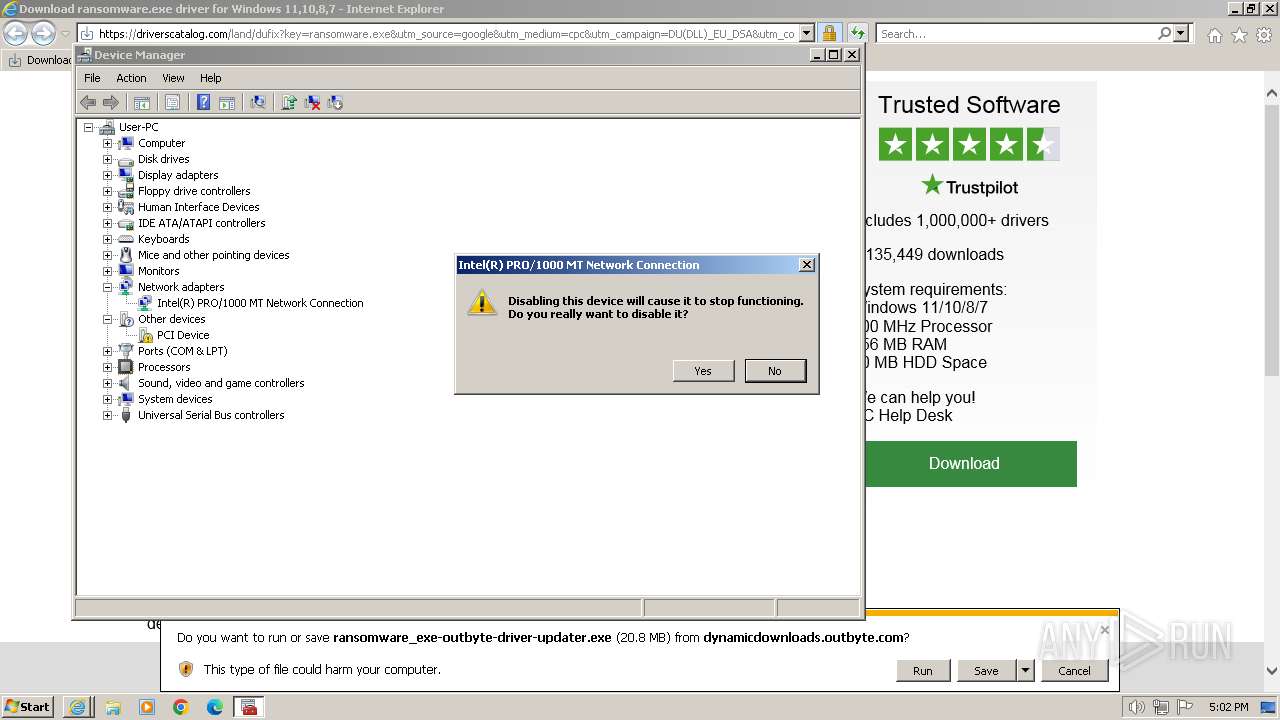
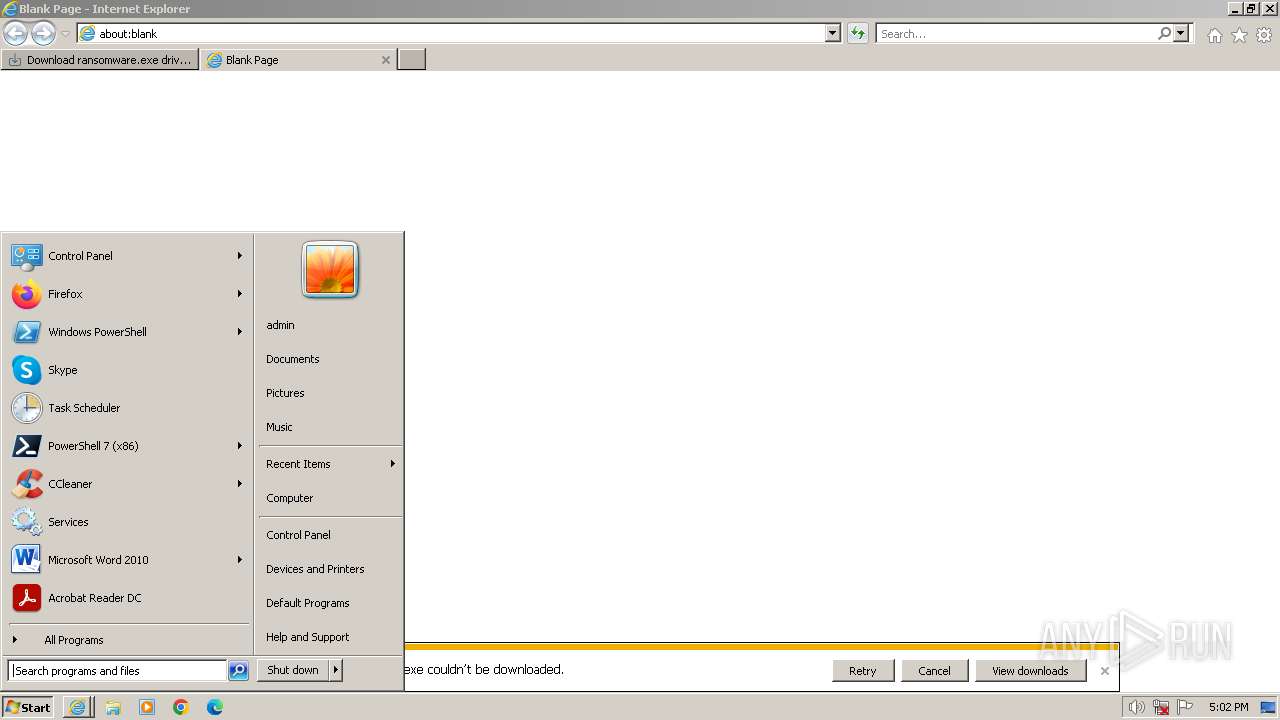
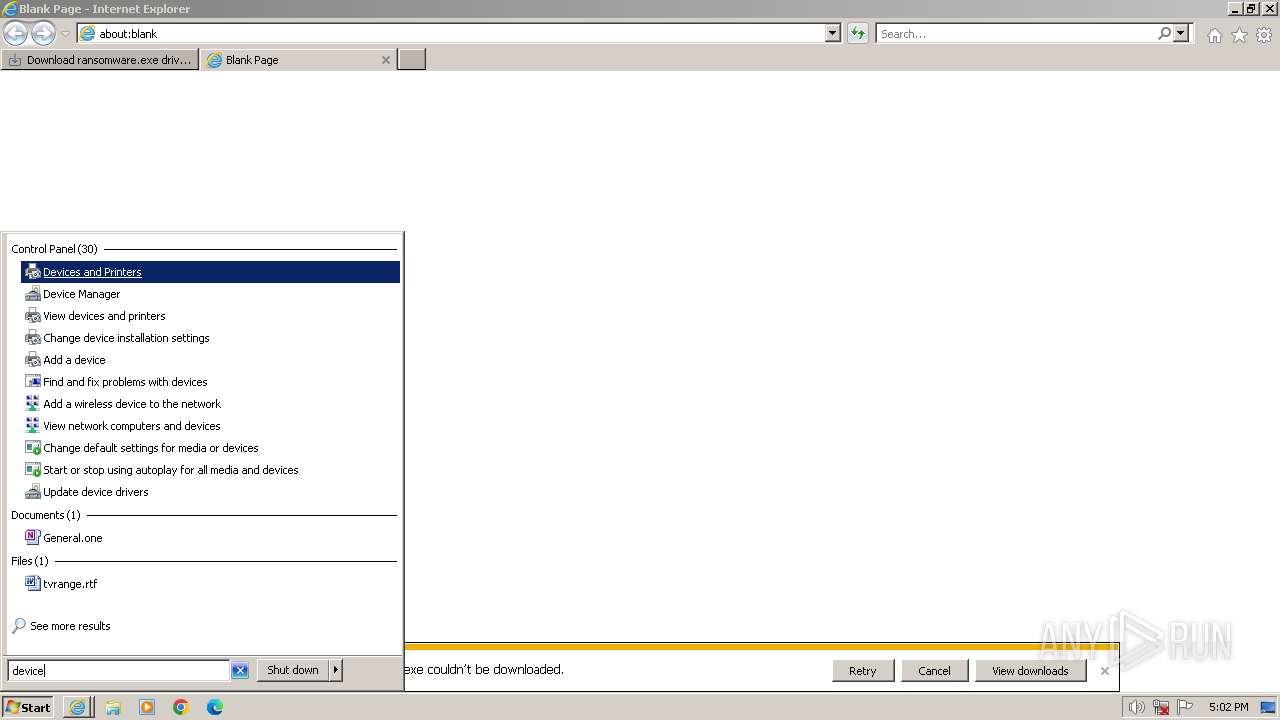
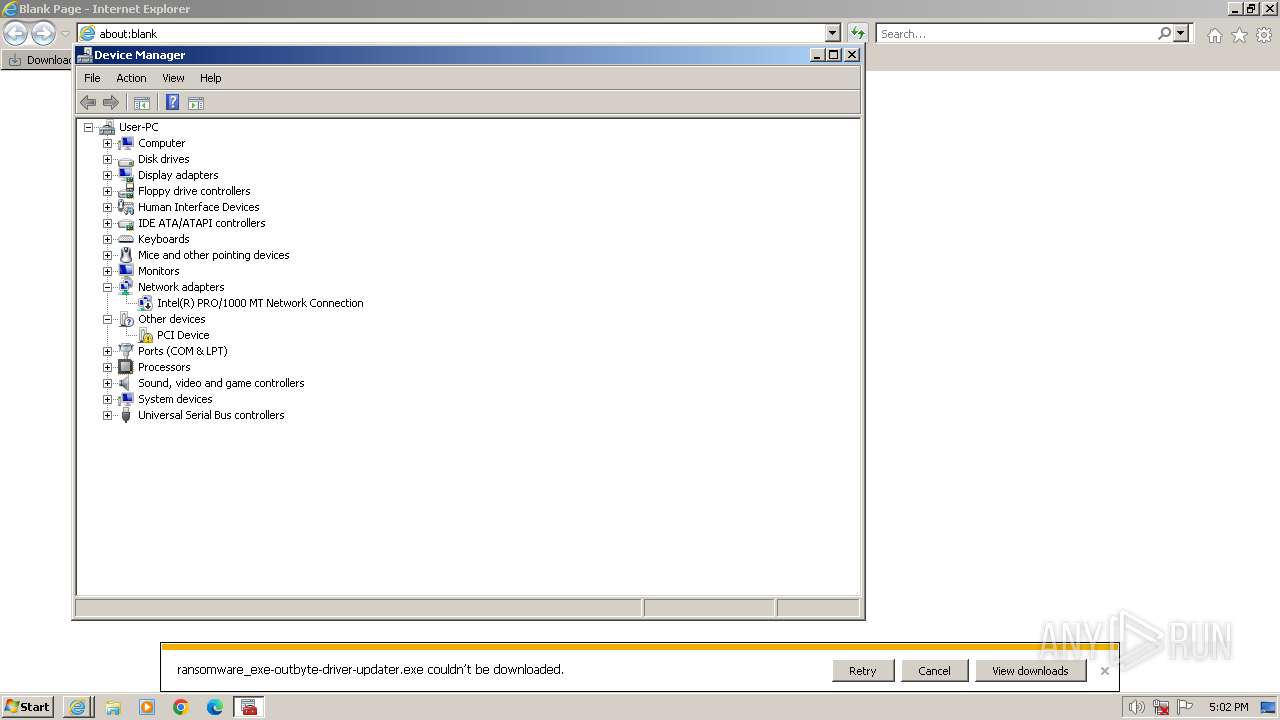
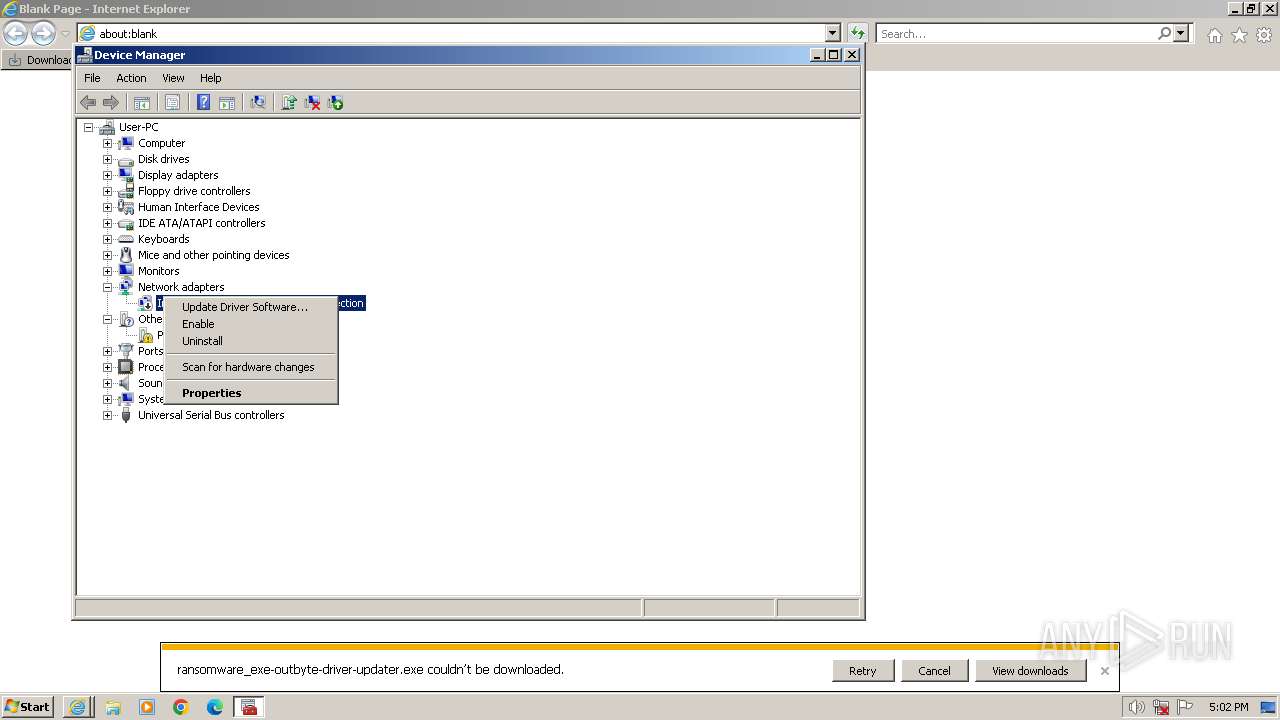
Manual execution by a user
- mmc.exe (PID: 844)
- wmpnscfg.exe (PID: 3740)
- mmc.exe (PID: 1632)
- mmc.exe (PID: 316)
- wmpnscfg.exe (PID: 3060)
- chrome.exe (PID: 2640)
- mmc.exe (PID: 3860)
Reads the computer name
- wmpnscfg.exe (PID: 3740)
- wmpnscfg.exe (PID: 3060)
- Installer.exe (PID: 2988)
- ServiceHelper.Agent.exe (PID: 1540)
- ServiceHelper.Agent.exe (PID: 2108)
- ransomware_exe-outbyte-driver-updater.exe (PID: 2944)
- DriverUpdater.exe (PID: 2808)
- CustomDllSurrogate.x32.exe (PID: 1820)
- DriverUpdater.exe (PID: 3652)
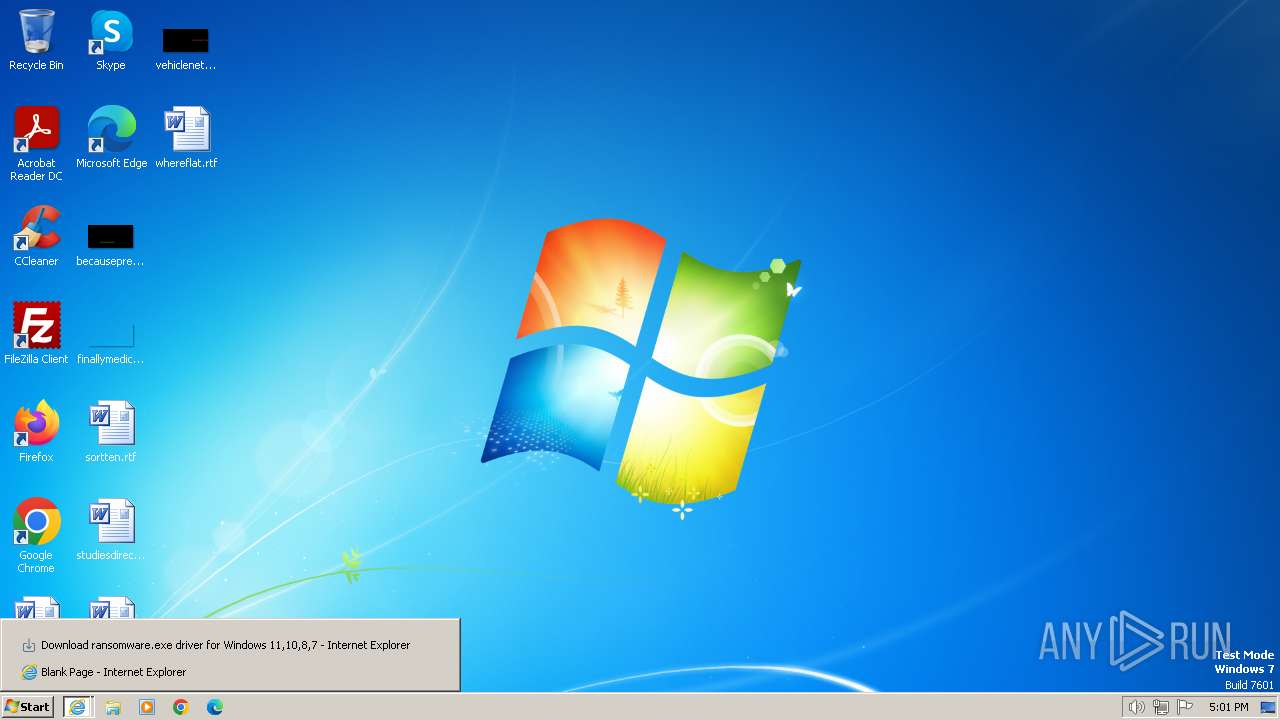
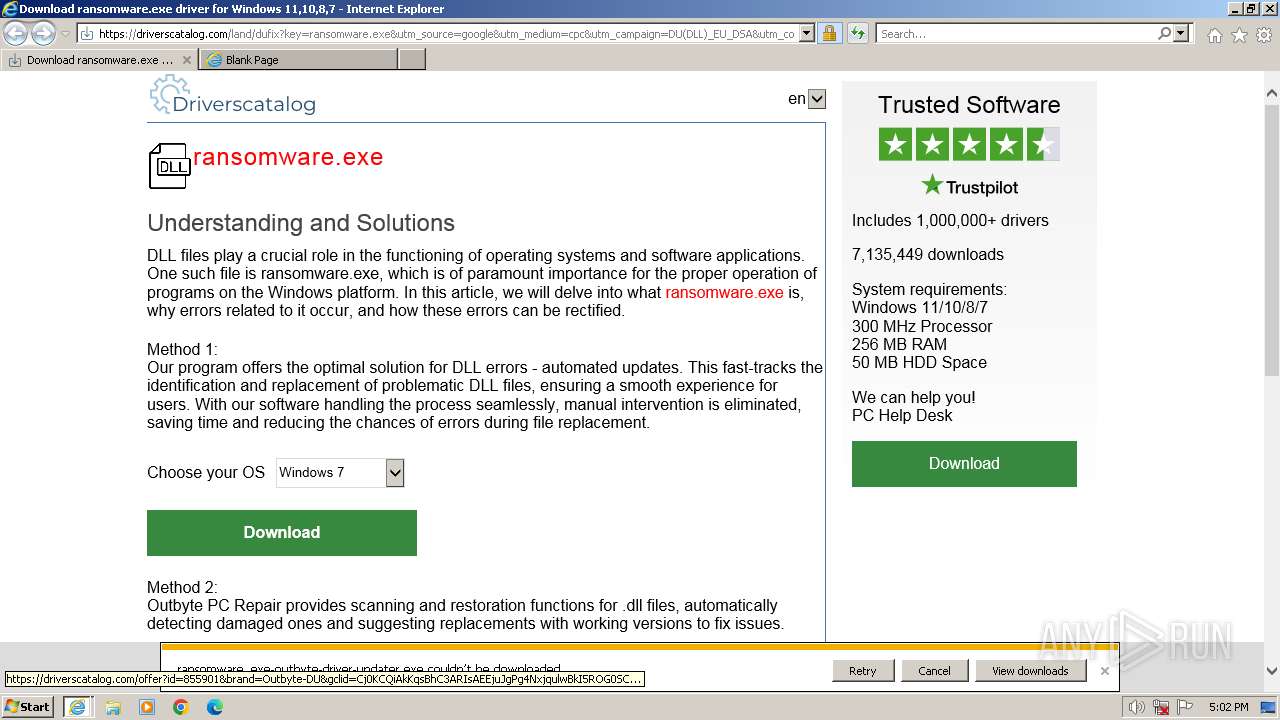
Drops the executable file immediately after the start
- iexplore.exe (PID: 324)
- iexplore.exe (PID: 2044)
- ransomware_exe-outbyte-driver-updater.exe (PID: 2944)
- Installer.exe (PID: 2988)
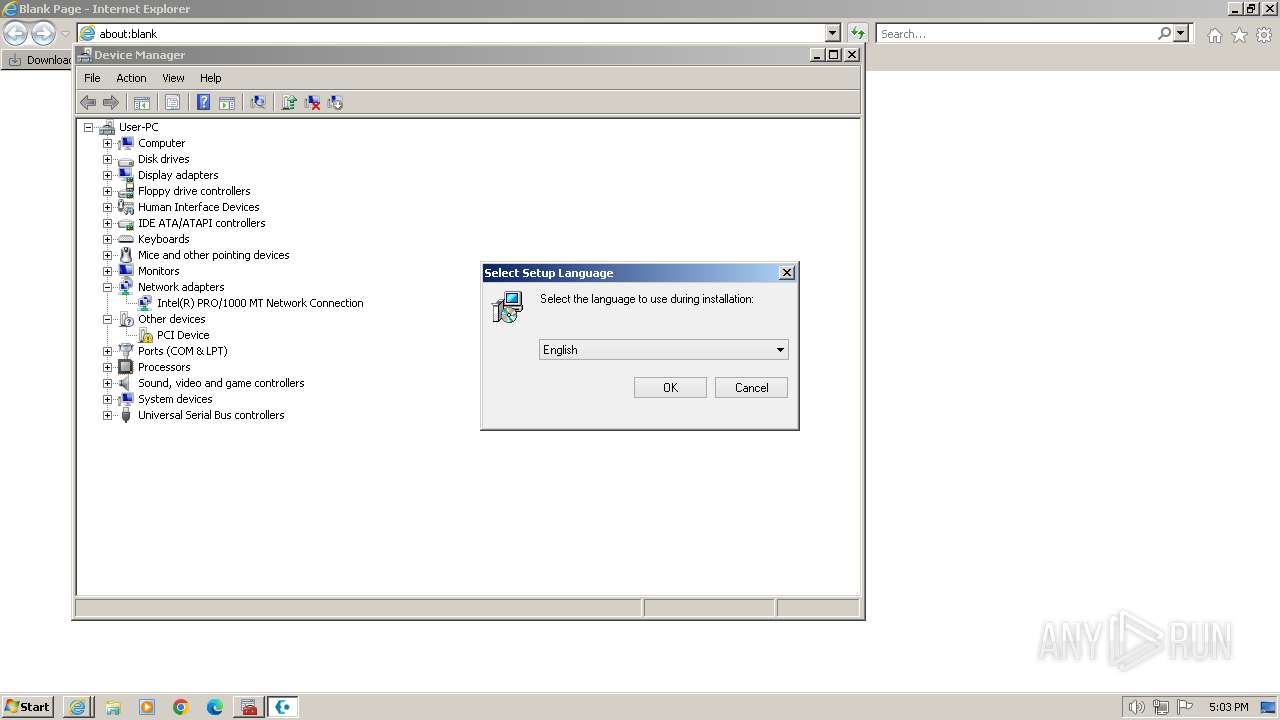
Checks supported languages
- wmpnscfg.exe (PID: 3060)
- ransomware_exe-outbyte-driver-updater.exe (PID: 2944)
- ServiceHelper.Agent.exe (PID: 1540)
- wmpnscfg.exe (PID: 3740)
- DriverUpdater.exe (PID: 3652)
- Installer.exe (PID: 2988)
- DriverUpdater.exe (PID: 2808)
- CustomDllSurrogate.x32.exe (PID: 1820)
- ServiceHelper.Agent.exe (PID: 2108)
Process checks computer location settings
- ransomware_exe-outbyte-driver-updater.exe (PID: 2944)
- Installer.exe (PID: 2988)
- DriverUpdater.exe (PID: 2808)
Create files in a temporary directory
- ransomware_exe-outbyte-driver-updater.exe (PID: 2944)
- Installer.exe (PID: 2988)
The process uses the downloaded file
- iexplore.exe (PID: 2044)
Reads the machine GUID from the registry
- Installer.exe (PID: 2988)
- DriverUpdater.exe (PID: 3652)
- DriverUpdater.exe (PID: 2808)
- CustomDllSurrogate.x32.exe (PID: 1820)
Reads Windows Product ID
- Installer.exe (PID: 2988)
- DriverUpdater.exe (PID: 3652)
- DriverUpdater.exe (PID: 2808)
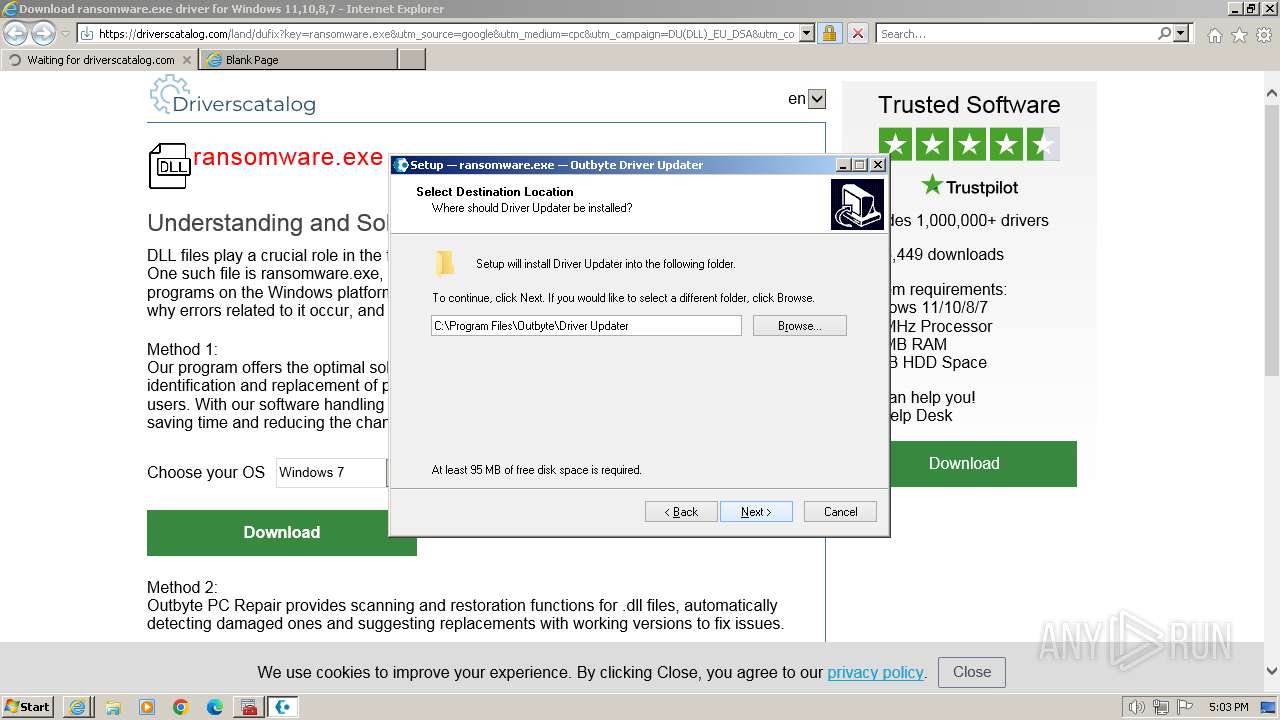
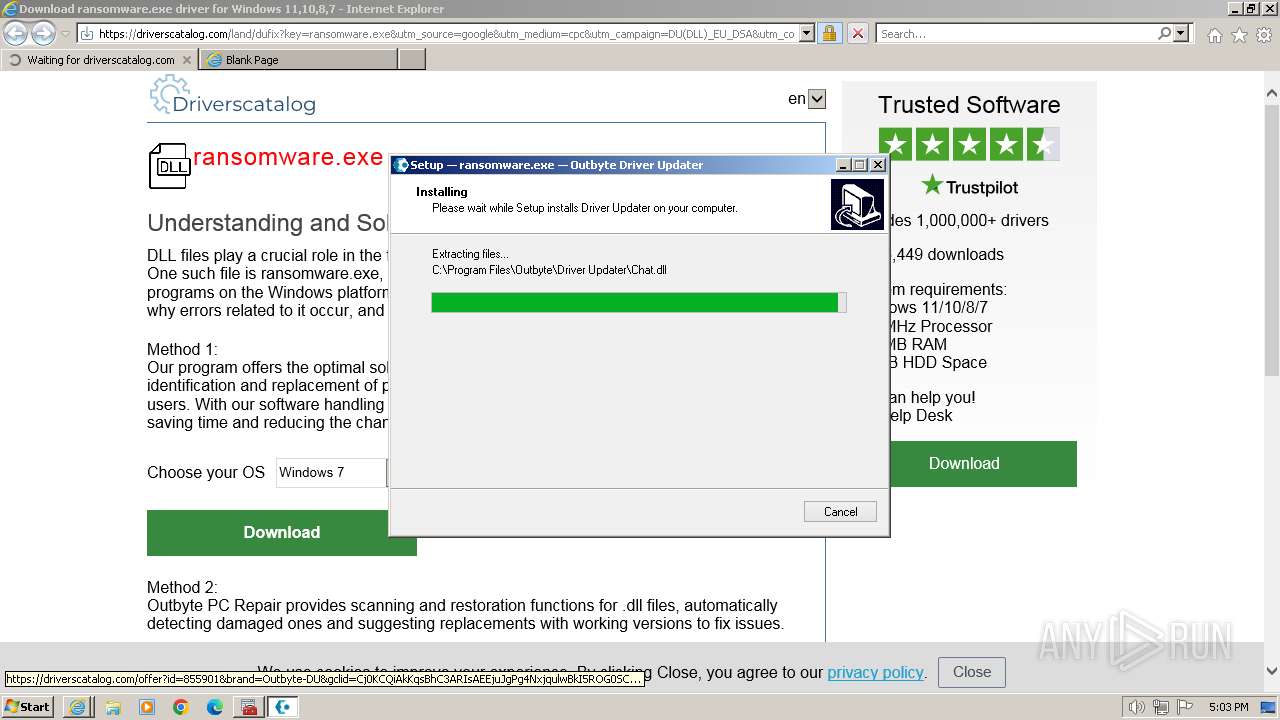
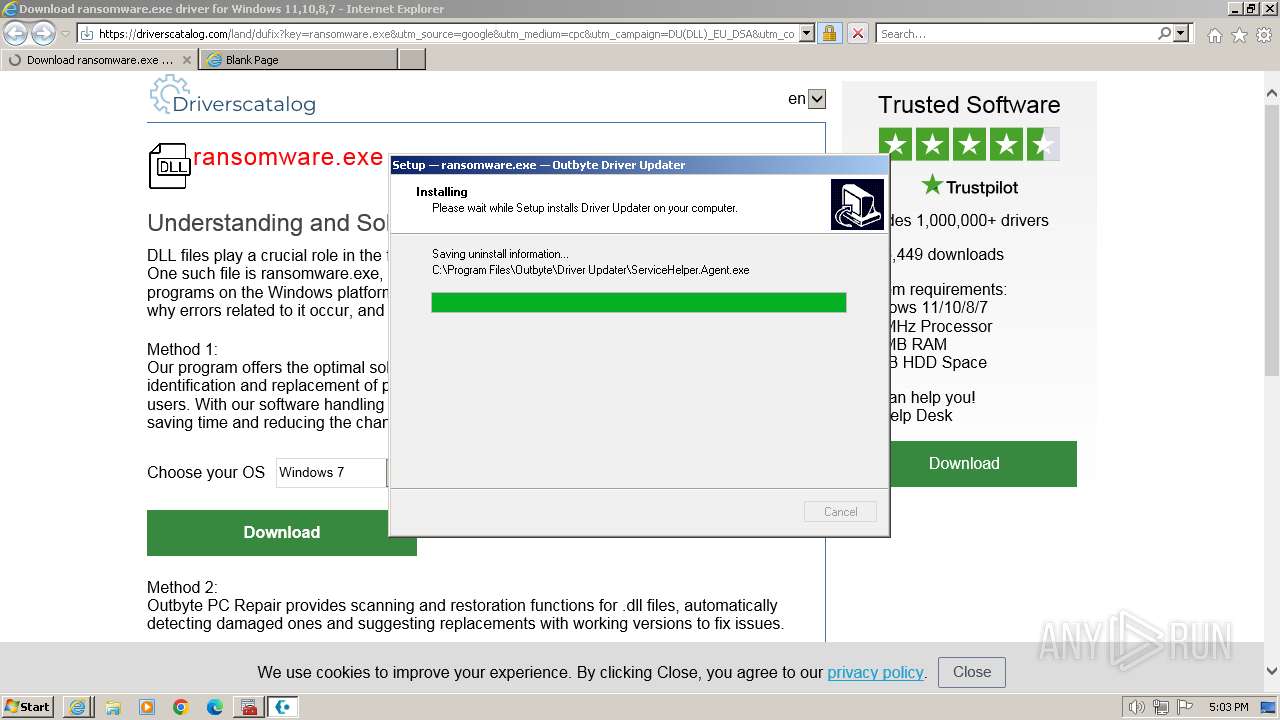
Creates files in the program directory
- Installer.exe (PID: 2988)
- DriverUpdater.exe (PID: 3652)
- CustomDllSurrogate.x32.exe (PID: 1820)
- DriverUpdater.exe (PID: 2808)
Checks proxy server information
- ransomware_exe-outbyte-driver-updater.exe (PID: 2944)
- Installer.exe (PID: 2988)
- DriverUpdater.exe (PID: 2808)
Process drops legitimate windows executable
- Installer.exe (PID: 2988)
Executes as Windows Service
- ServiceHelper.Agent.exe (PID: 2108)
- VSSVC.exe (PID: 296)
Creates files or folders in the user directory
- DriverUpdater.exe (PID: 2808)
Reads Microsoft Office registry keys
- DriverUpdater.exe (PID: 2808)
Process drops SQLite DLL files
- Installer.exe (PID: 2988)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
112
Monitored processes
51
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 296 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 316 | "C:\Windows\system32\mmc.exe" C:\Windows\system32\devmgmt.msc | C:\Windows\System32\mmc.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 324 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2044 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 844 | "C:\Windows\system32\mmc.exe" C:\Windows\system32\devmgmt.msc | C:\Windows\System32\mmc.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=2256 --field-trial-handle=1156,i,1655380398019357620,12772927602284063403,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1220 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1516 --field-trial-handle=1324,i,325024030959331664,2963251784440215188,131072 /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3736 --field-trial-handle=1156,i,1655380398019357620,12772927602284063403,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1540 | "C:\Program Files\Outbyte\Driver Updater\ServiceHelper.Agent.exe" /install /silent | C:\Program Files\Outbyte\Driver Updater\ServiceHelper.Agent.exe | — | Installer.exe | |||||||||||
User: admin Company: Outbyte Integrity Level: HIGH Description: DU Helper Exit code: 0 Version: 2.3.1.25150 Modules
| |||||||||||||||
| 1632 | "C:\Windows\system32\mmc.exe" C:\Windows\system32\devmgmt.msc | C:\Windows\System32\mmc.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1820 | "C:\Program Files\Outbyte\Driver Updater\CustomDllSurrogate.x32.exe" {67EABA29-89CD-450E-A9CC-8EC44CCFCED1} -Embedding | C:\Program Files\Outbyte\Driver Updater\CustomDllSurrogate.x32.exe | svchost.exe | ||||||||||||
User: admin Company: Outbyte Integrity Level: HIGH Description: Custom Dll Surrogate x32 Exit code: 0 Version: 2.0.0.25077 Modules
| |||||||||||||||
Total events
67 173
Read events
66 813
Write events
352
Delete events
8
Modification events
| (PID) Process: | (2044) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2044) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2044) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2044) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2044) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2044) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2044) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2044) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2044) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2044) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
106
Suspicious files
374
Text files
141
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 324 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 324 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\186FBED197980E591B5D0985849DAF91 | binary | |
MD5:54136729245E34EBB3F615ACF0614248 | SHA256:F16C97B8E845C4E7A4D6BE43B02784EF07CEAB8062F2C9E2609AD546A7843954 | |||
| 324 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:26298D96CC9E2CEF6BEB09F62AE1D32C | SHA256:08CE770358C6EF32DEDF0E24CC770055B341108CB04129C16E1F906736A4392C | |||
| 324 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:81095C453FAA7A9610AD74F2D17C1286 | SHA256:4E8E0A82720A2CCDF2336DF86124307D37AE1DF9063B53EF0D142789EE8ADFEC | |||
| 324 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 324 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\dufix[1].htm | html | |
MD5:7DF3EEE4004FC497B11A90E47045D5C6 | SHA256:0D7B971091D100A8470953D8D27F4FF4B664CEFDCE7BC091487EC10AA853700F | |||
| 324 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\F2DDCD2B5F37625B82E81F4976CEE400_BB0E5383BB6E3CF78C8AC8388DB6A7BF | binary | |
MD5:CB64B956E763BDAB7B0271AA42480435 | SHA256:48C334B600F8DE36C411C5DE28B8CB22731F93F908D0DAE3594798D596E728EC | |||
| 324 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarFA9E.tmp | binary | |
MD5:9C0C641C06238516F27941AA1166D427 | SHA256:4276AF3669A141A59388BC56A87F6614D9A9BDDDF560636C264219A7EB11256F | |||
| 324 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabFA9F.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 324 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:F5F9F5C9531AF7EFA4002F465FFB8586 | SHA256:32443A23413724DDF840C149BB3284AB682BB6533FEB70D8B2CC9EAF39953BFE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
199
DNS requests
203
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
324 | iexplore.exe | GET | 200 | 23.192.153.142:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
324 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCZXmpIP%2Bo%2BHhJmodADfw%2Fc | unknown | binary | 472 b | unknown |
324 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?2fa7828491fdb1d6 | unknown | compressed | 65.2 Kb | unknown |
324 | iexplore.exe | GET | 200 | 23.53.40.161:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgTS2PKAbi%2Foer%2F9WuAjbi4dzg%3D%3D | unknown | binary | 503 b | unknown |
324 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?7a9d8baceff24343 | unknown | compressed | 4.66 Kb | unknown |
324 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?16e53a13f7f2d96f | unknown | compressed | 4.66 Kb | unknown |
2044 | iexplore.exe | GET | — | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
324 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/rootr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHUeP1PjGFkz6V8I7O6tApc%3D | unknown | binary | 1.41 Kb | unknown |
324 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?608cb4ab6d3f68d3 | unknown | compressed | 65.2 Kb | unknown |
324 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | unknown | binary | 724 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
324 | iexplore.exe | 157.230.15.209:443 | driverscatalog.com | DIGITALOCEAN-ASN | US | unknown |
324 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
324 | iexplore.exe | 23.192.153.142:80 | x1.c.lencr.org | AKAMAI-AS | GB | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
324 | iexplore.exe | 23.53.40.161:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
324 | iexplore.exe | 142.250.181.232:443 | www.googletagmanager.com | GOOGLE | US | unknown |
324 | iexplore.exe | 142.250.185.99:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
324 | iexplore.exe | 87.250.250.119:443 | mc.yandex.ru | YANDEX LLC | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
driverscatalog.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
www.googletagmanager.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
mc.yandex.ru |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |
region1.analytics.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2404 | chrome.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
2404 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Global content delivery network (unpkg .com) |