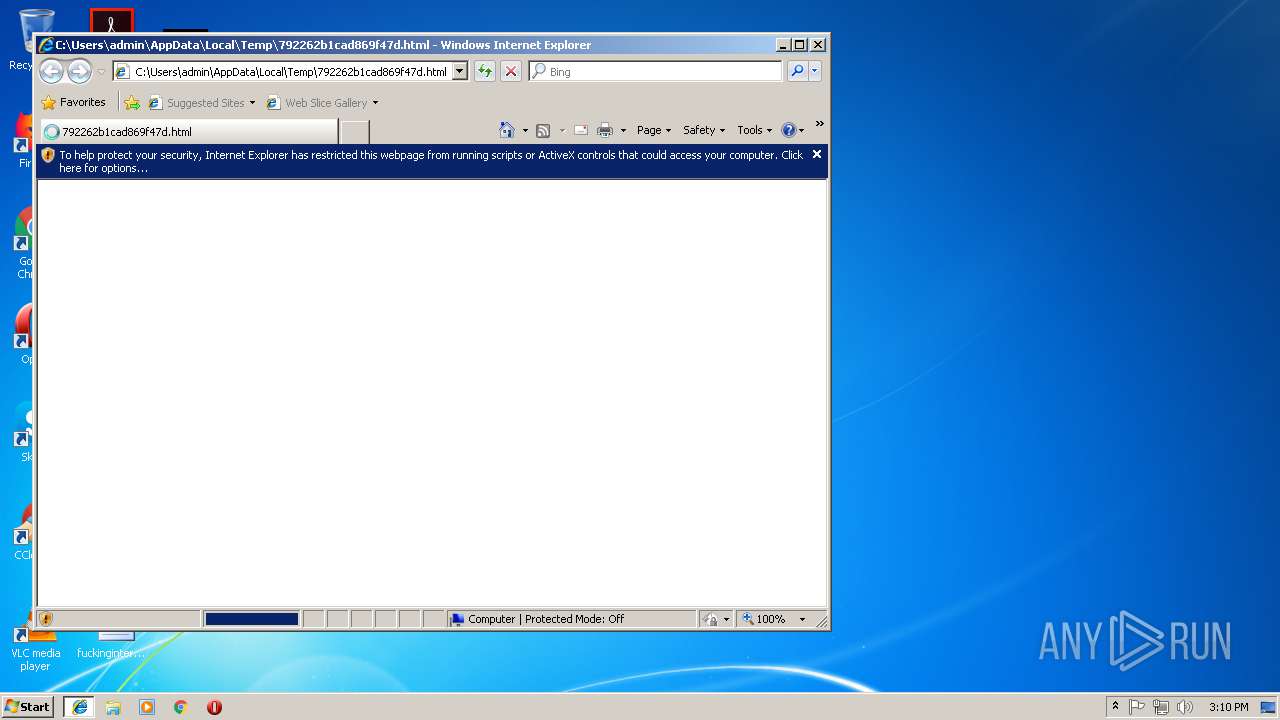
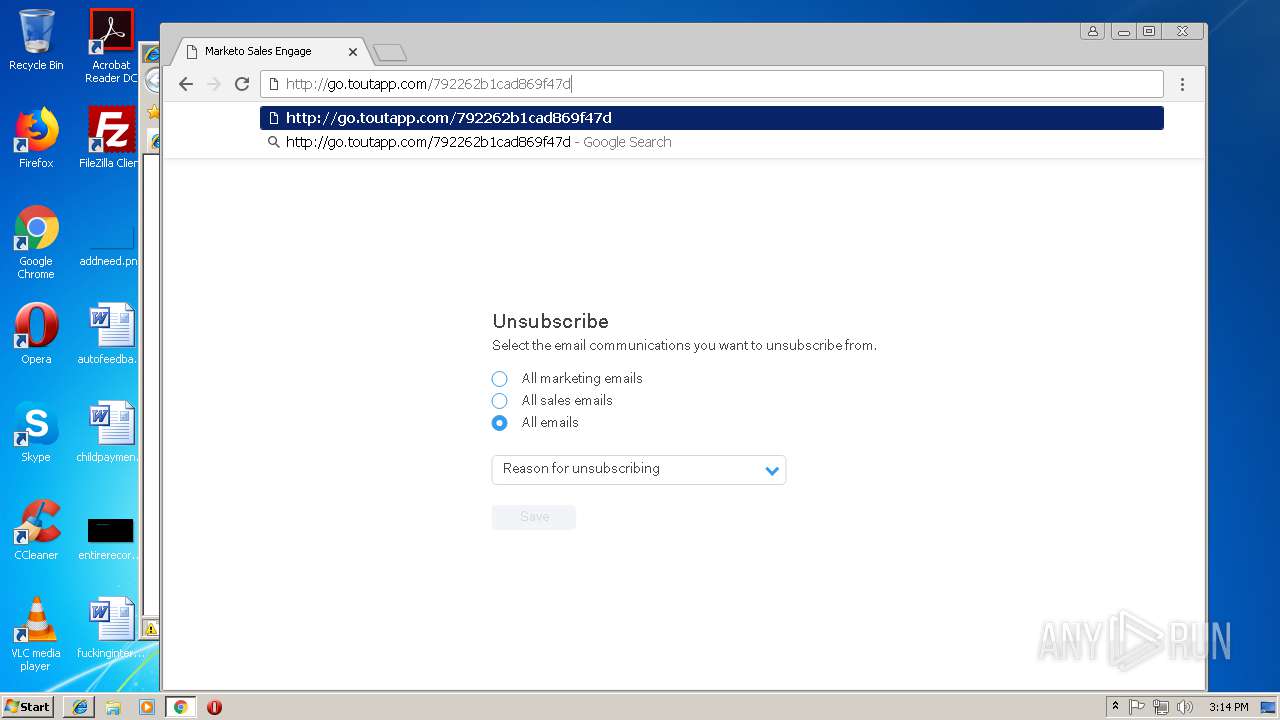
| download: | 792262b1cad869f47d |
| Full analysis: | https://app.any.run/tasks/df8e4aba-c238-4a58-8626-6ab13b2471db |
| Verdict: | Malicious activity |
| Analysis date: | November 14, 2018, 15:09:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
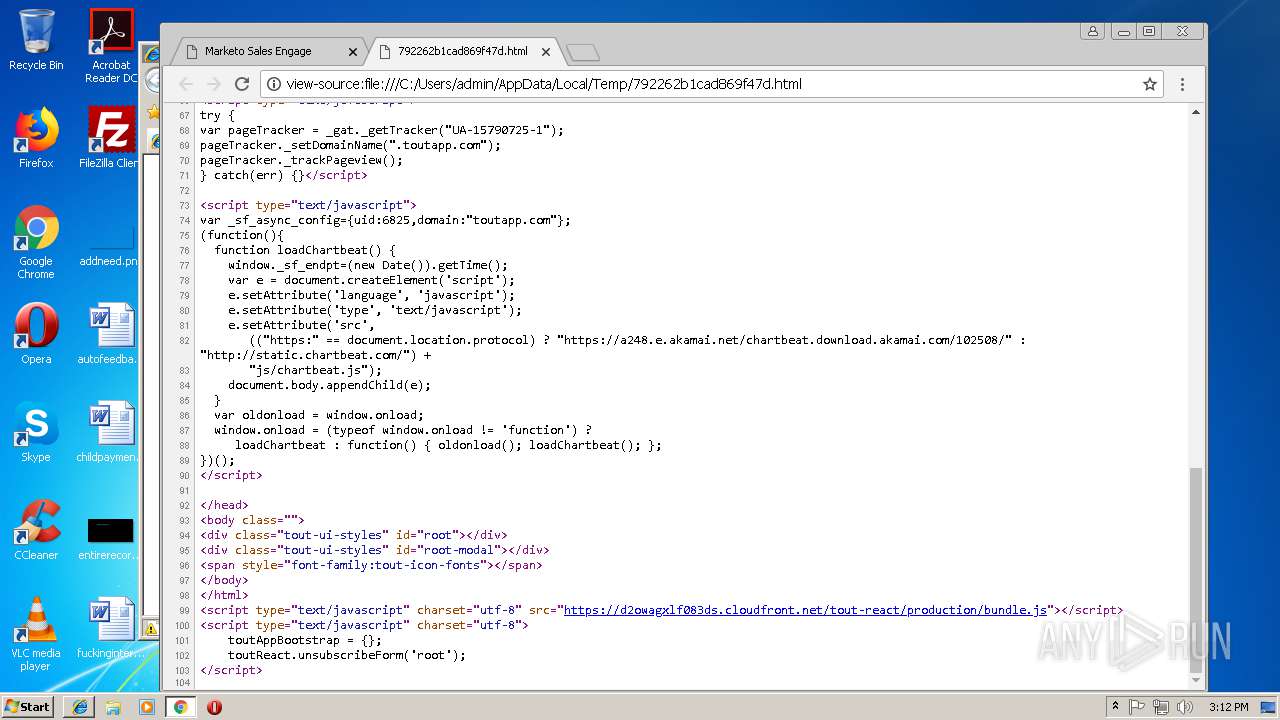
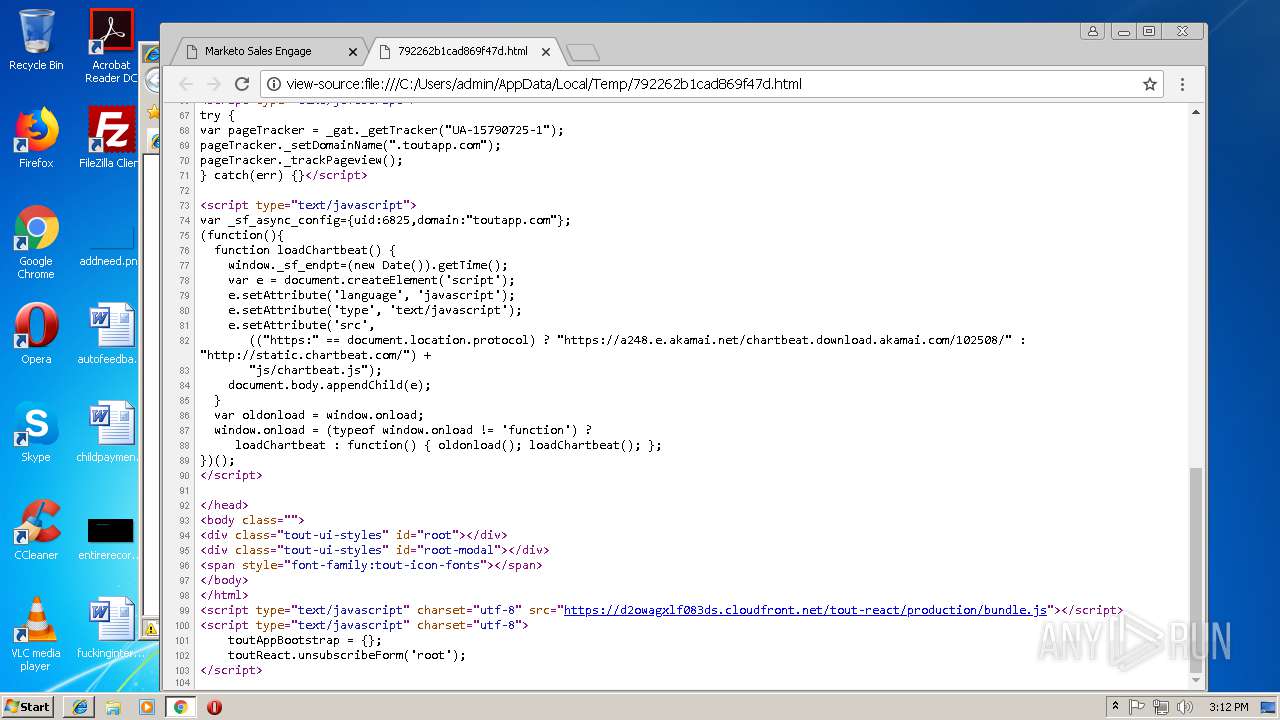
| MIME: | text/html |
| File info: | HTML document, ASCII text |
| MD5: | D7A1B81749963C17BC3D77AC5DE1BB16 |
| SHA1: | C777BD18A856CB0191072F432CE97D12EBA83D57 |
| SHA256: | A5ADAF87003682211A5313DDE06EC6B6F25C50AE4546F6E4F4862D35D91E2B22 |
| SSDEEP: | 96:SIroeie28eB4BZKJPESJXSnasa81pNMpuXNpwsbl3pyb:BrfiTOBZKJPpaasaYQ4osRZyb |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
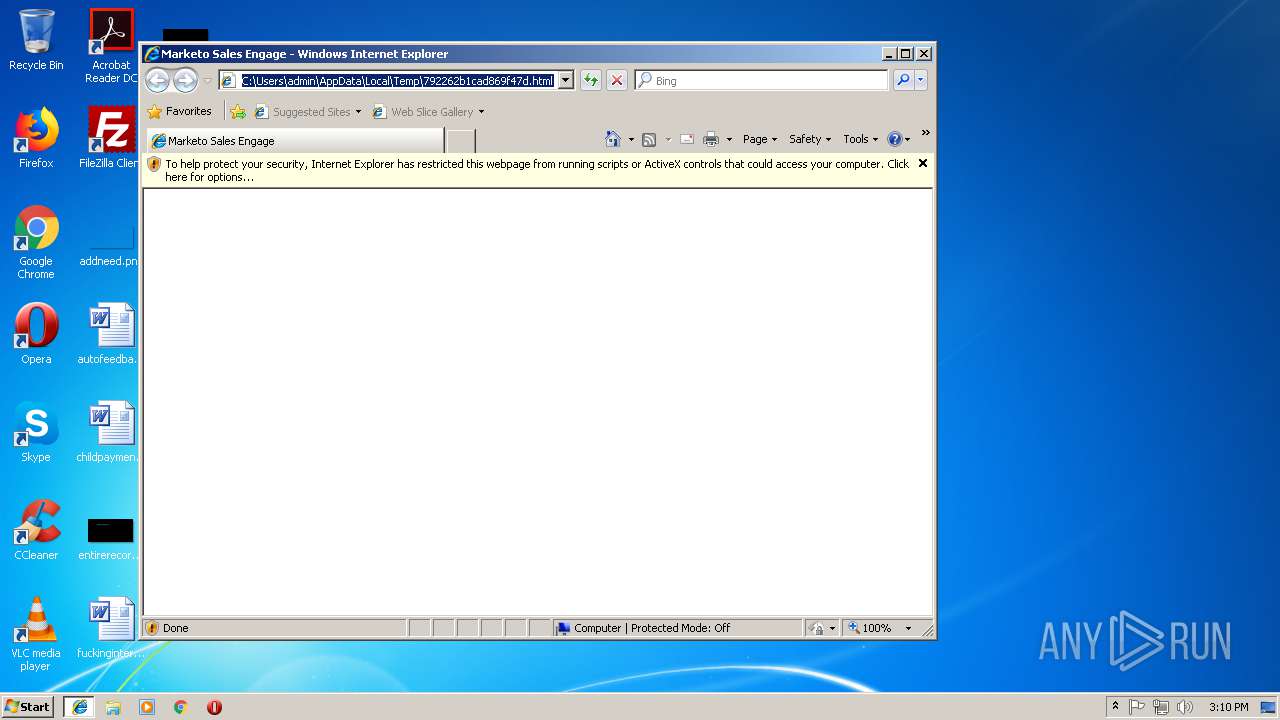
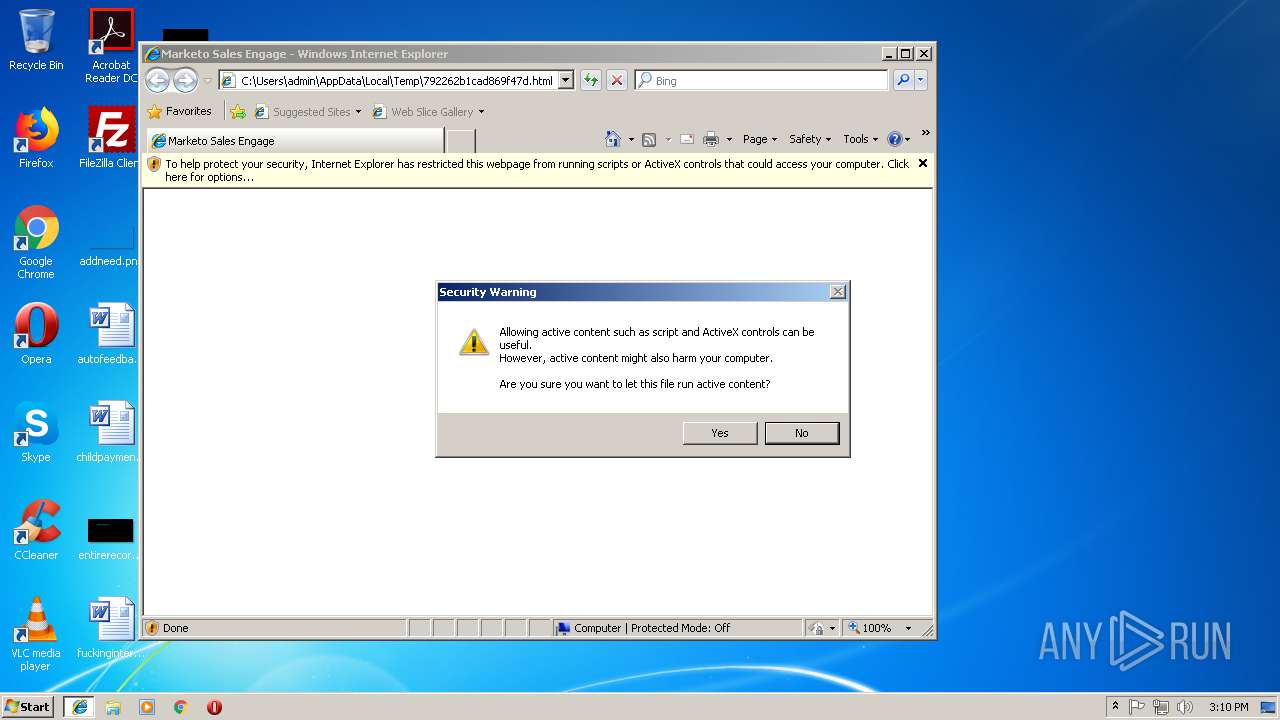
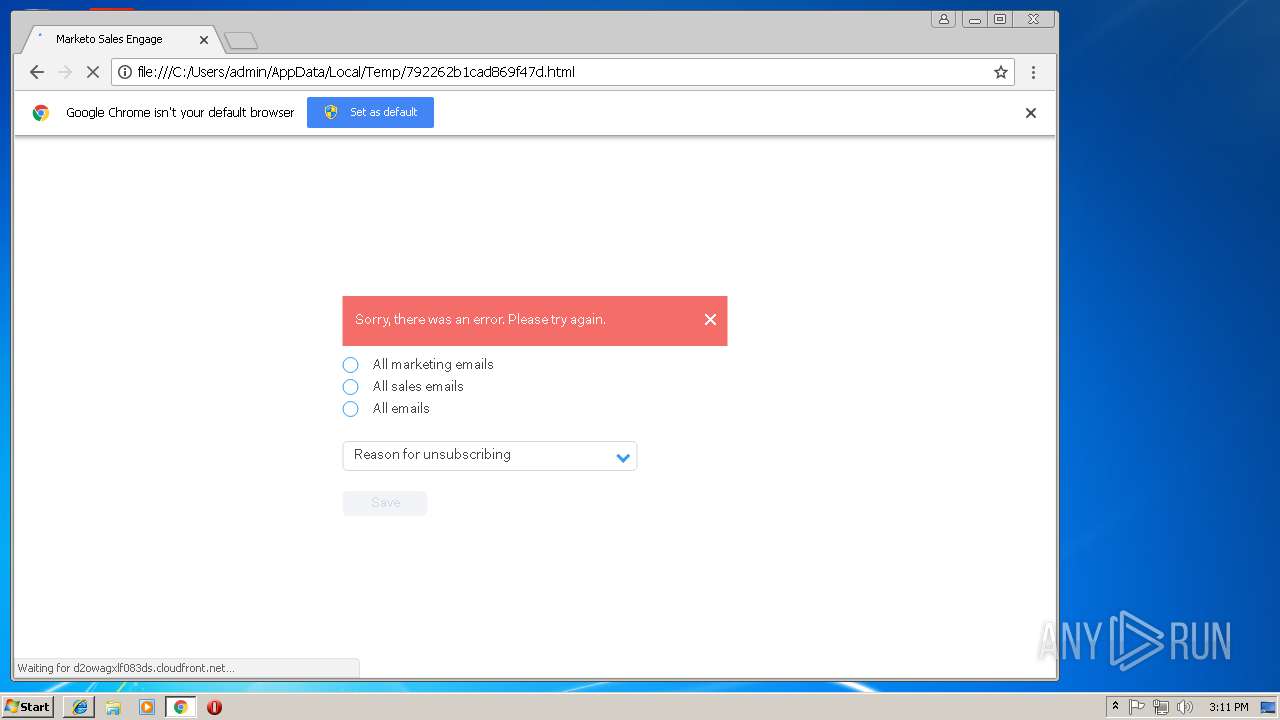
Changes internet zones settings
- iexplore.exe (PID: 3544)
Application launched itself
- chrome.exe (PID: 2372)
- iexplore.exe (PID: 3544)
Creates files in the user directory
- iexplore.exe (PID: 3232)
- chrome.exe (PID: 2372)
Reads internet explorer settings
- iexplore.exe (PID: 3232)
Reads Internet Cache Settings
- iexplore.exe (PID: 3232)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
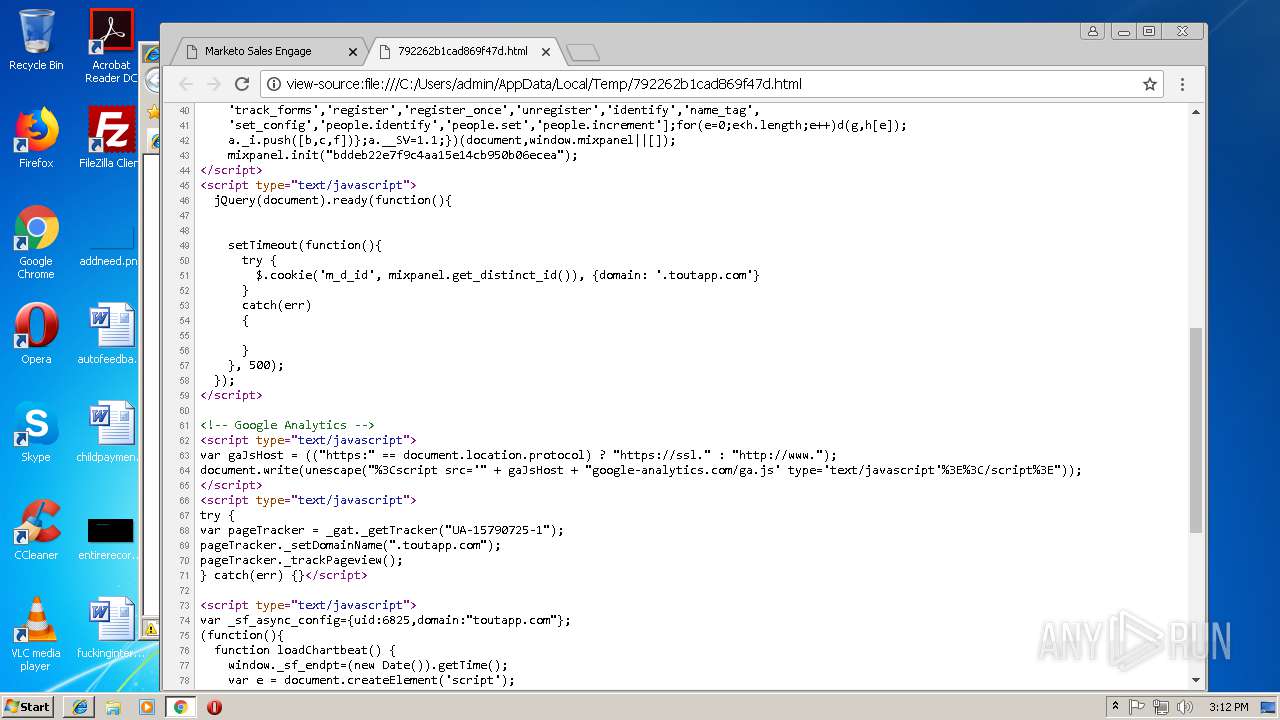
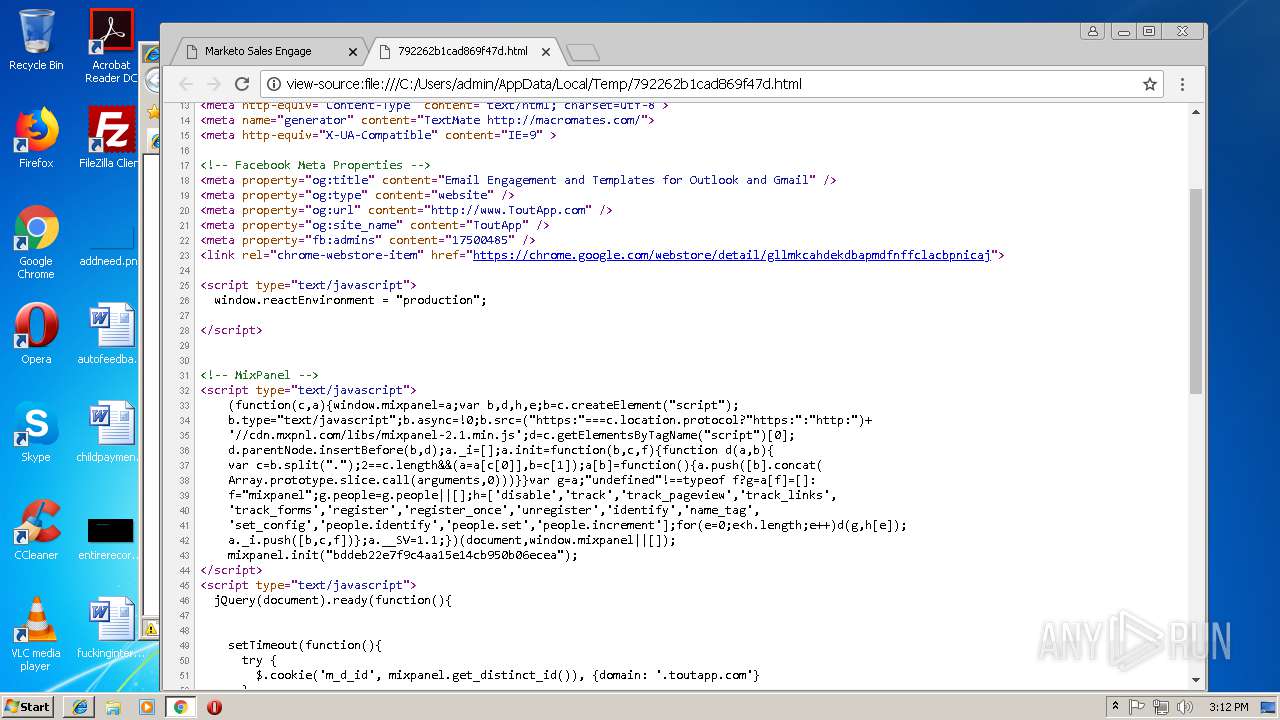
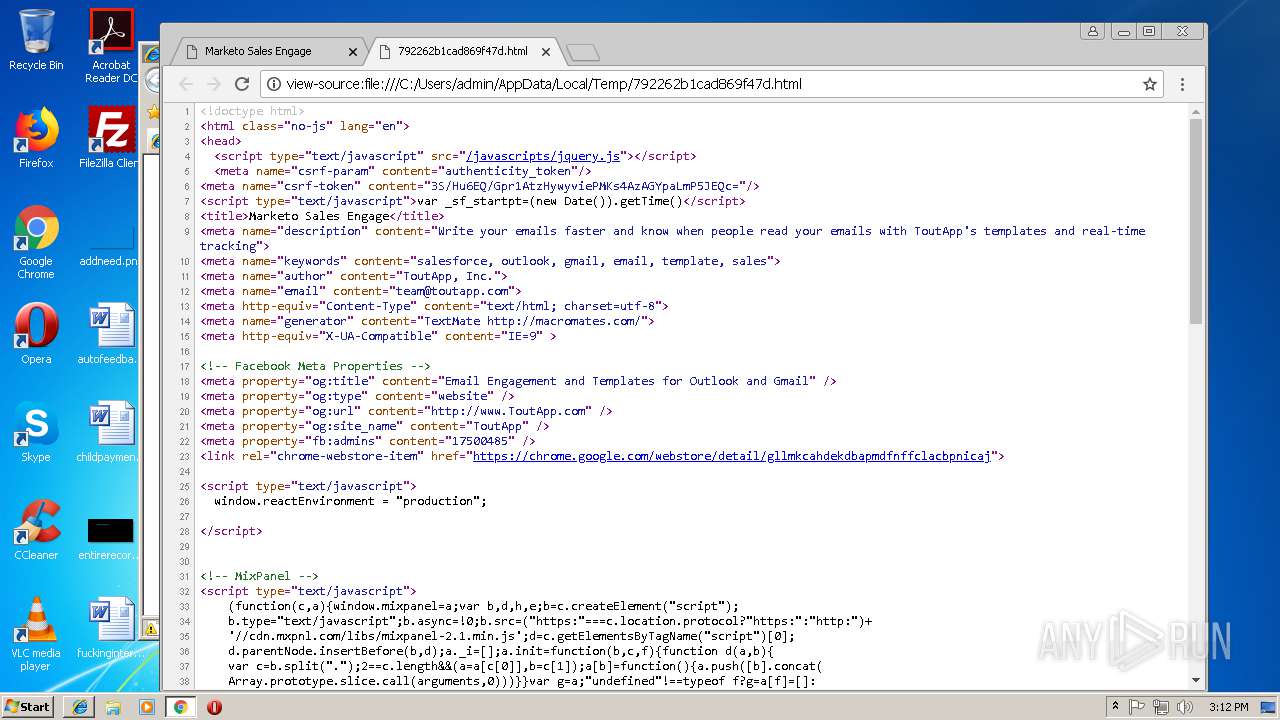
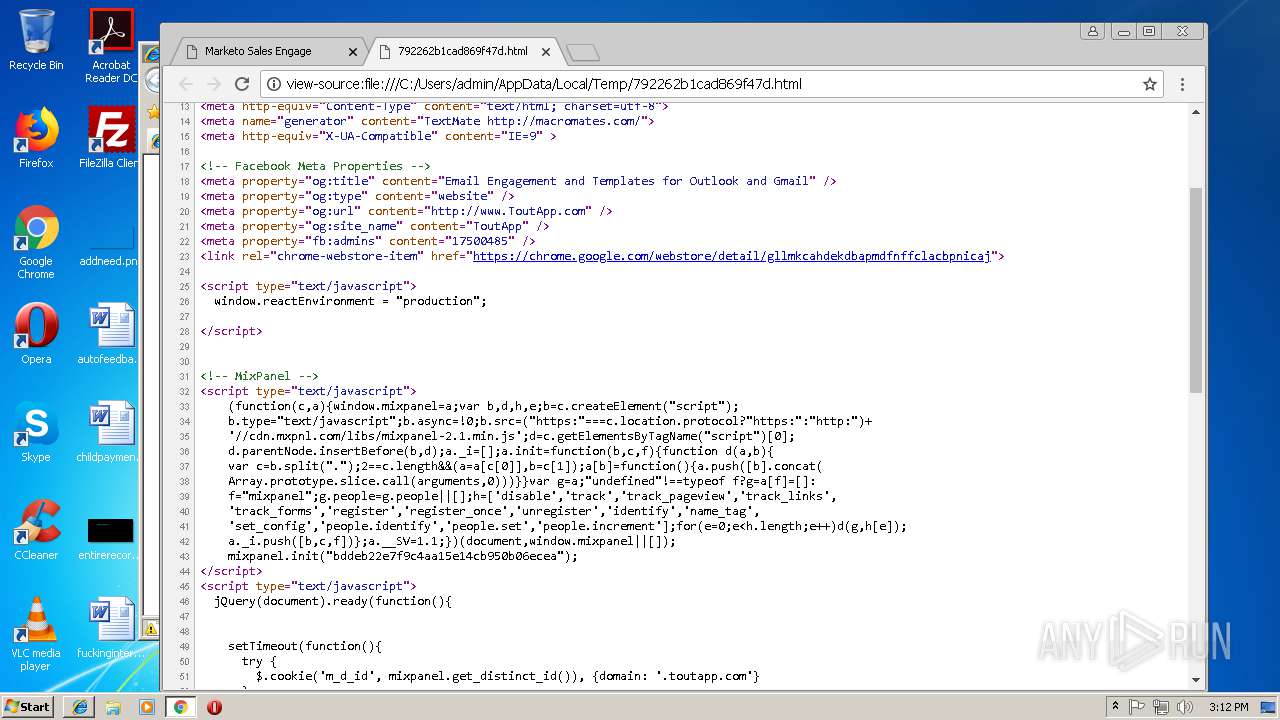
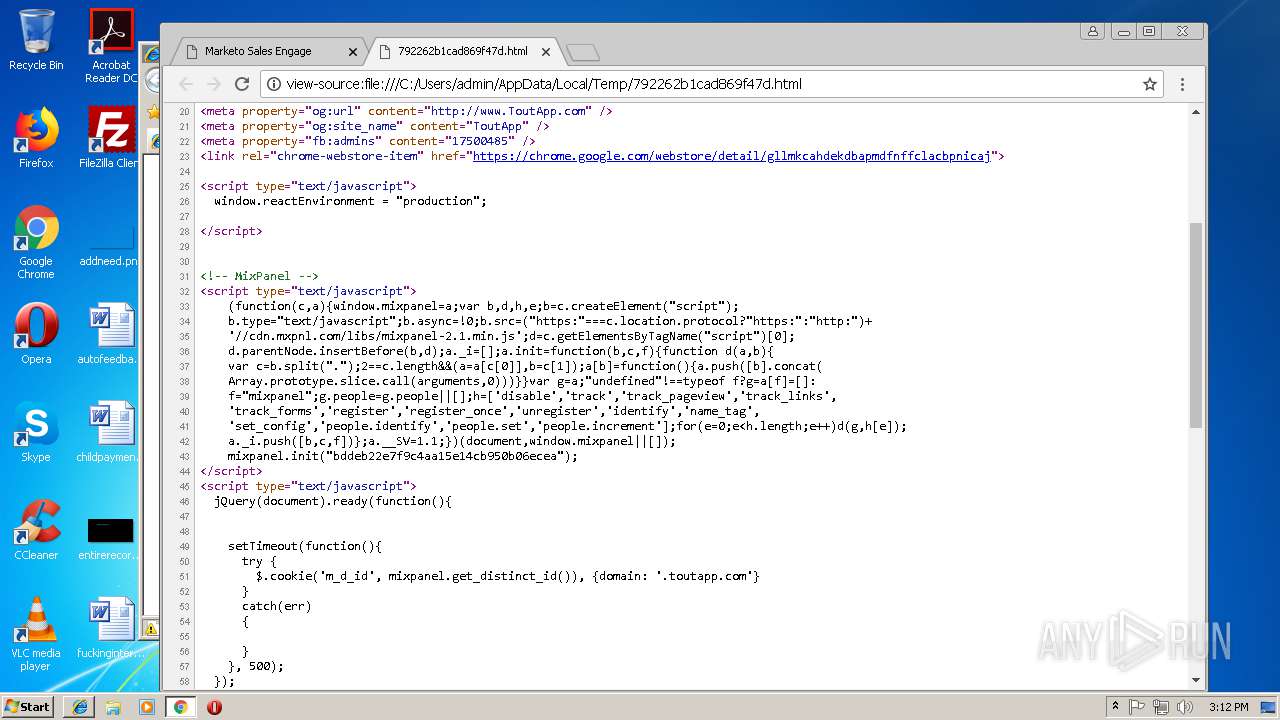
HTML
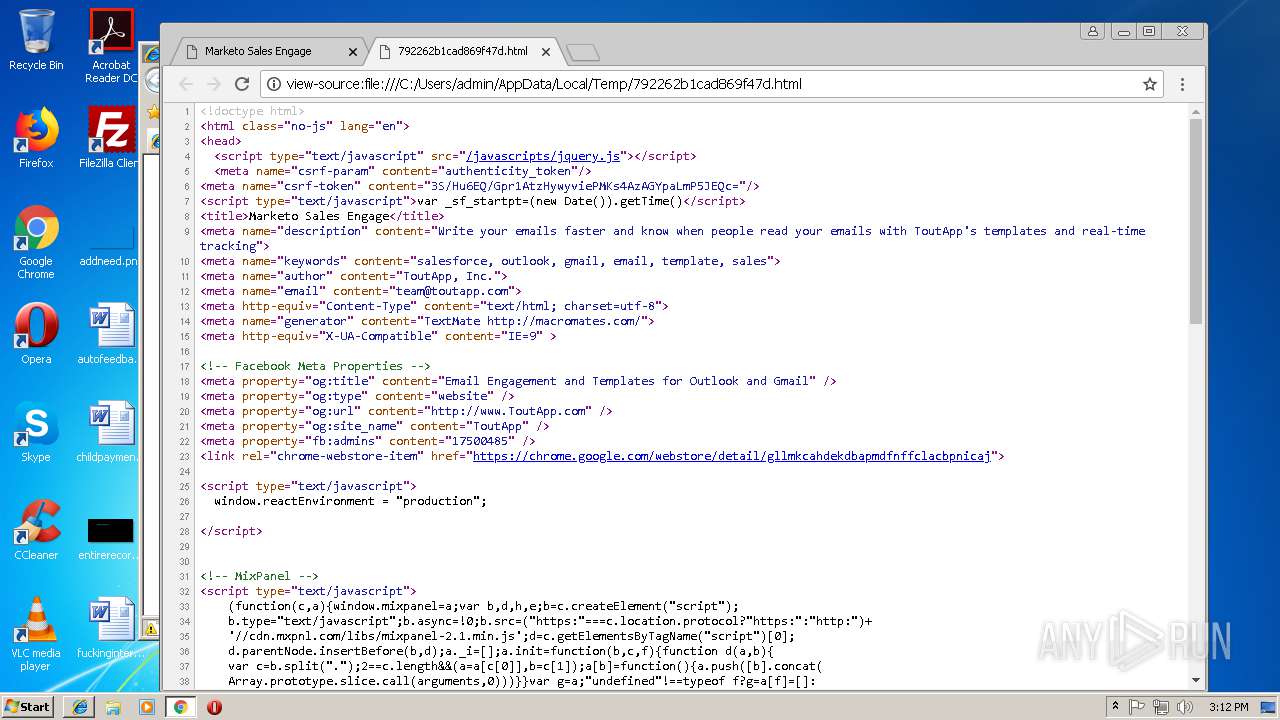
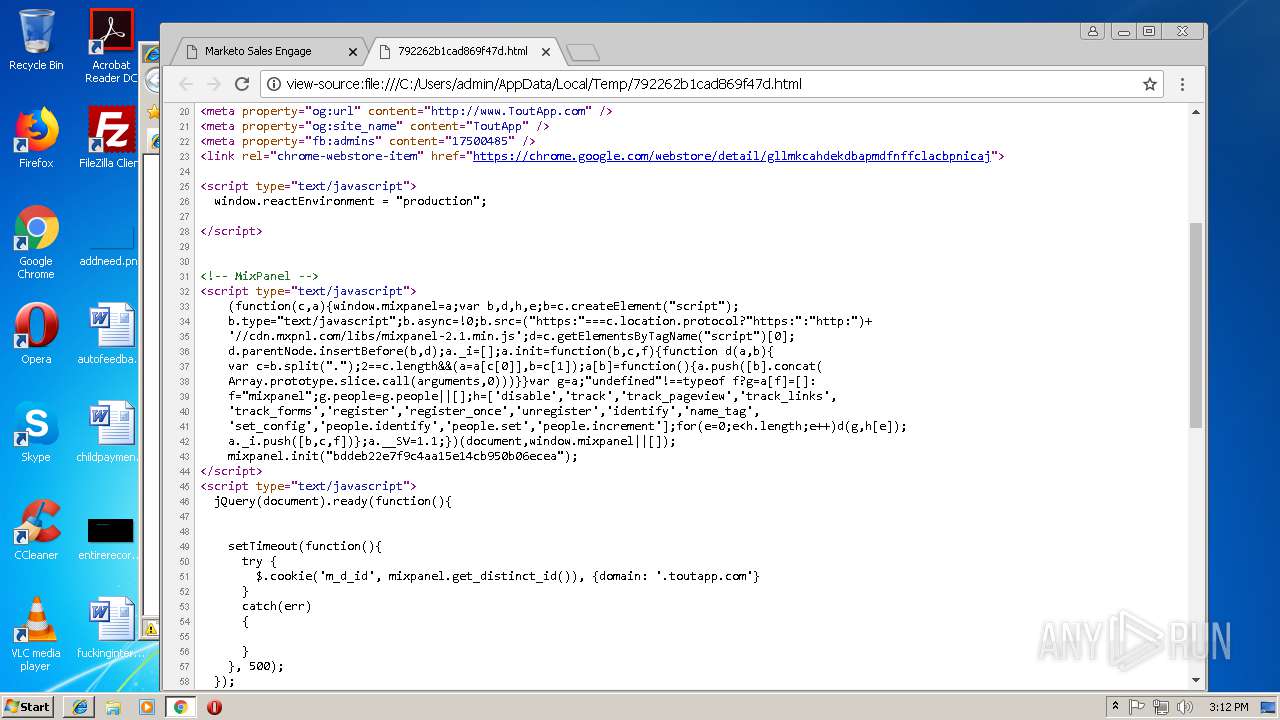
| csrfParam: | authenticity_token |
|---|---|
| csrfToken: | 3S/Hu6EQ/Gpr1AtzHywyviePMKs4AzAGYpaLmP5JEQc= |
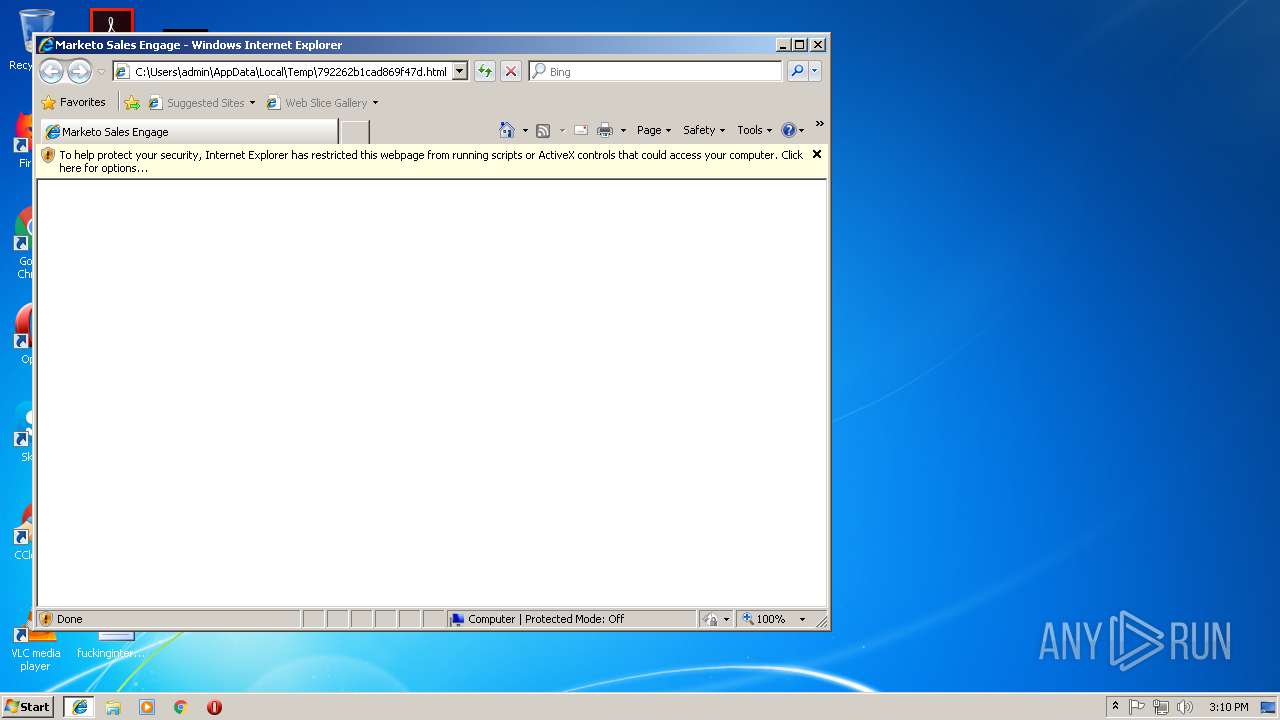
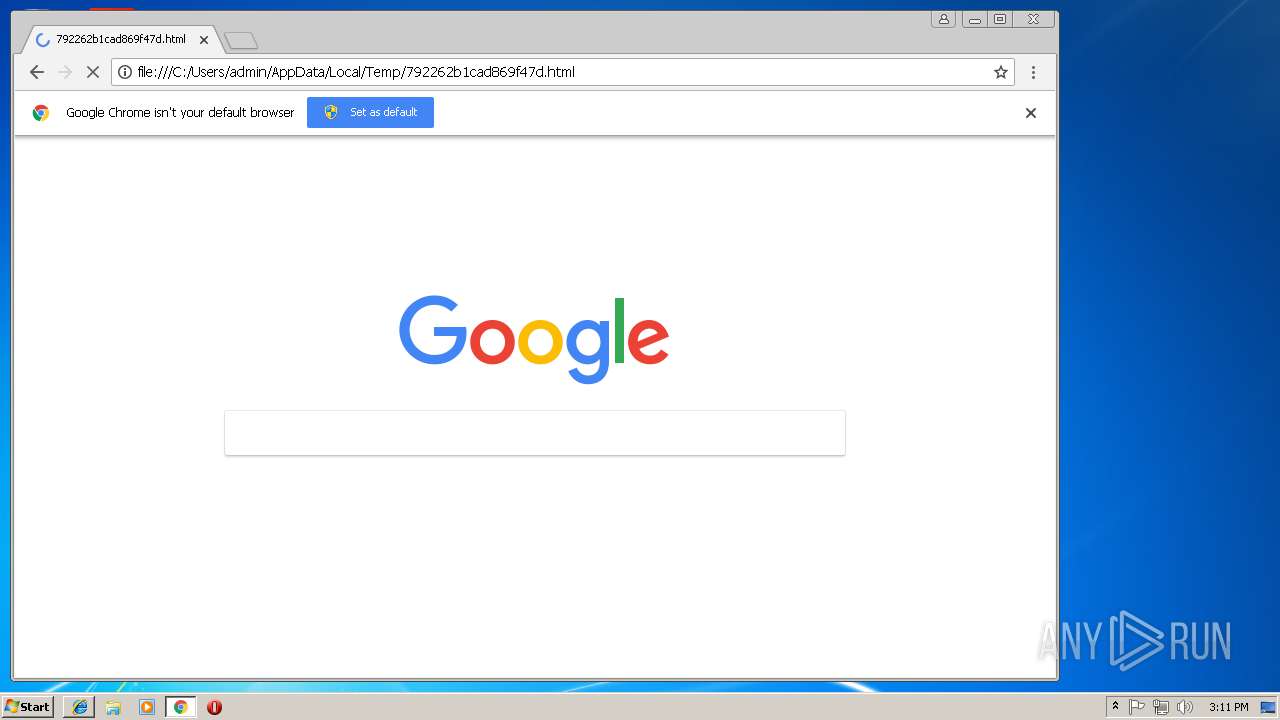
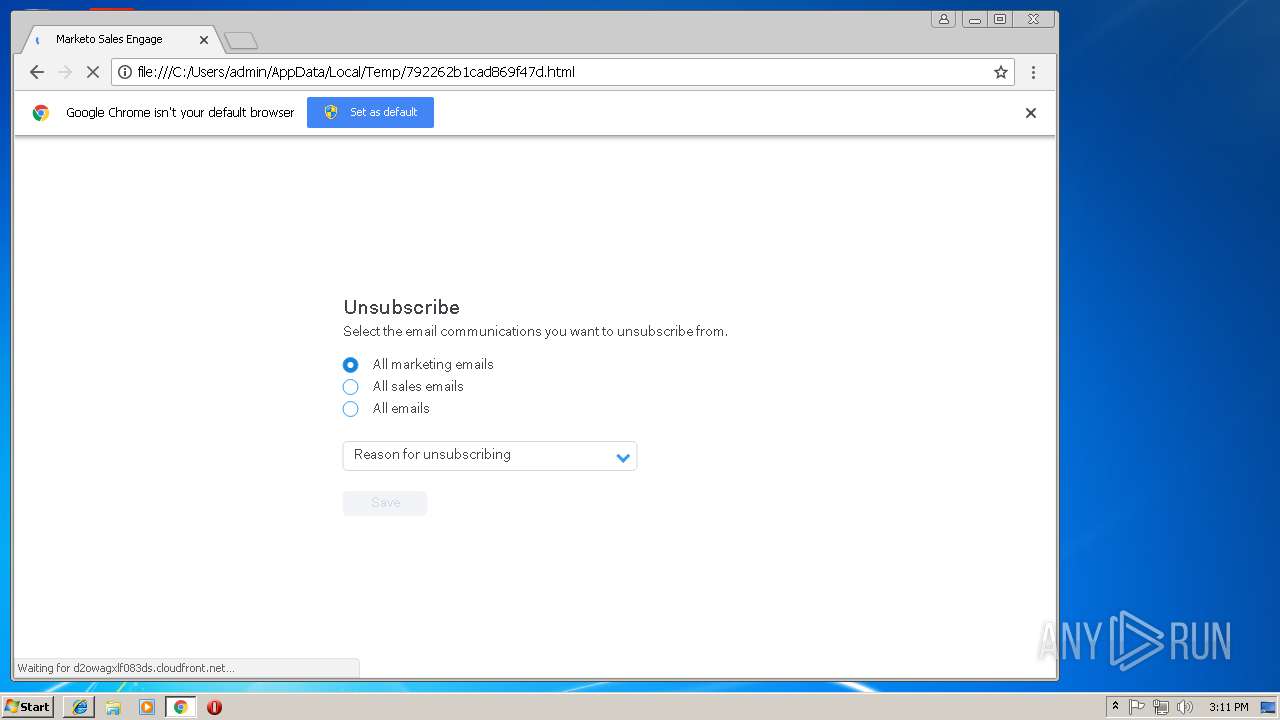
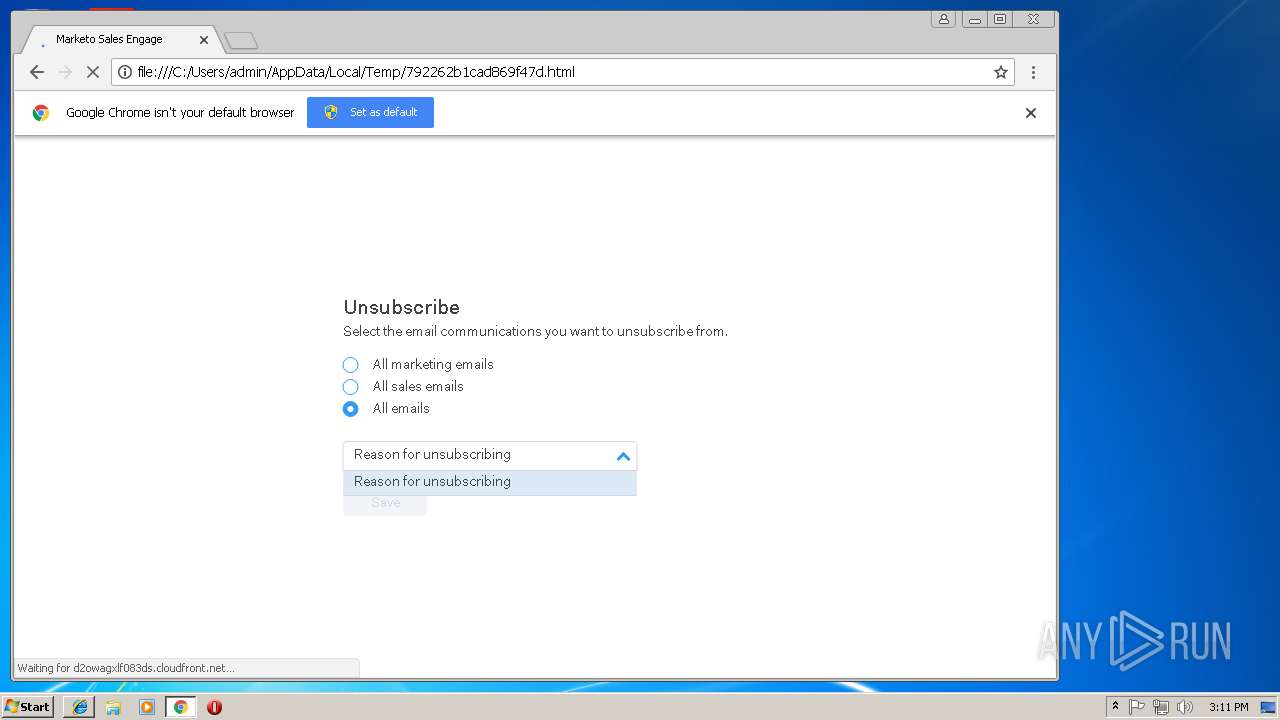
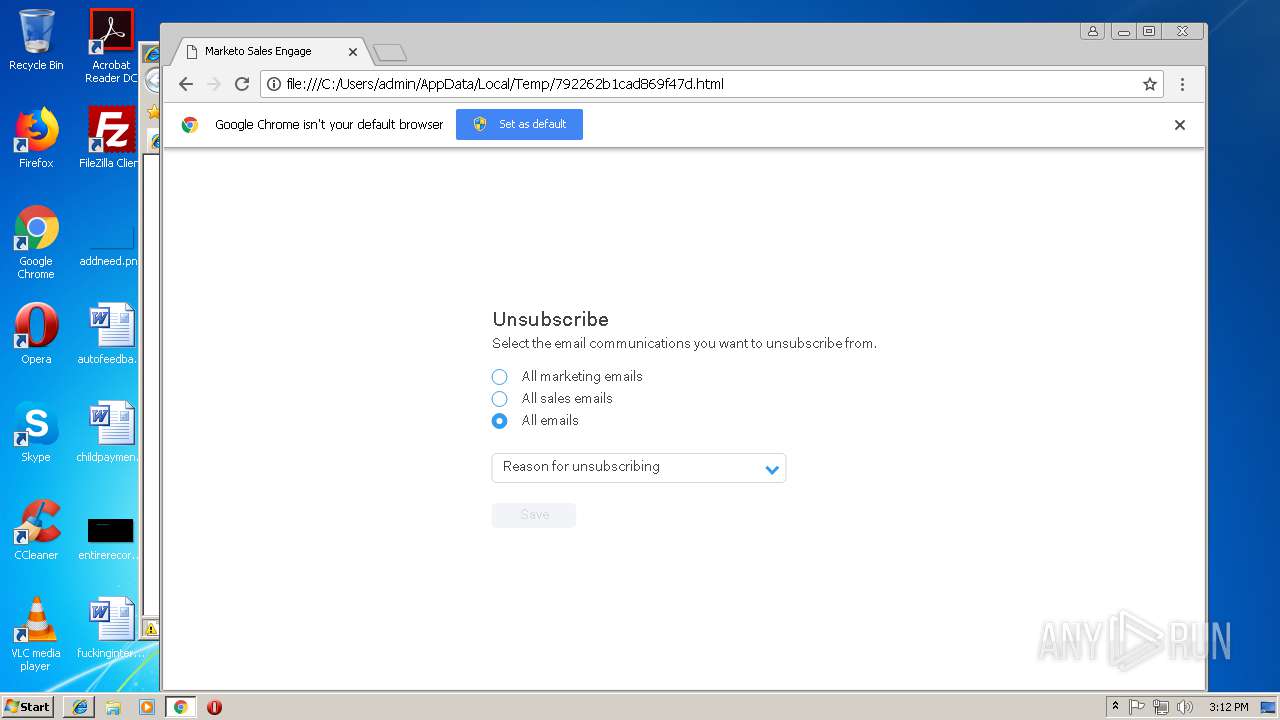
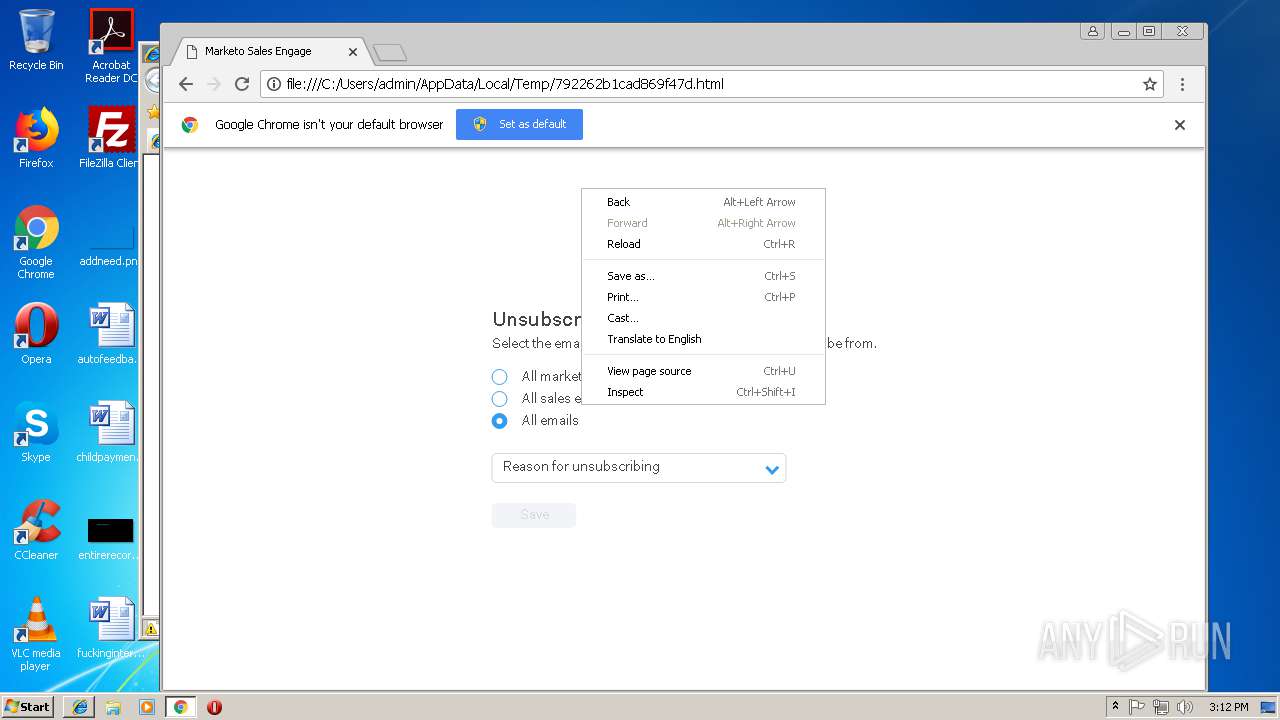
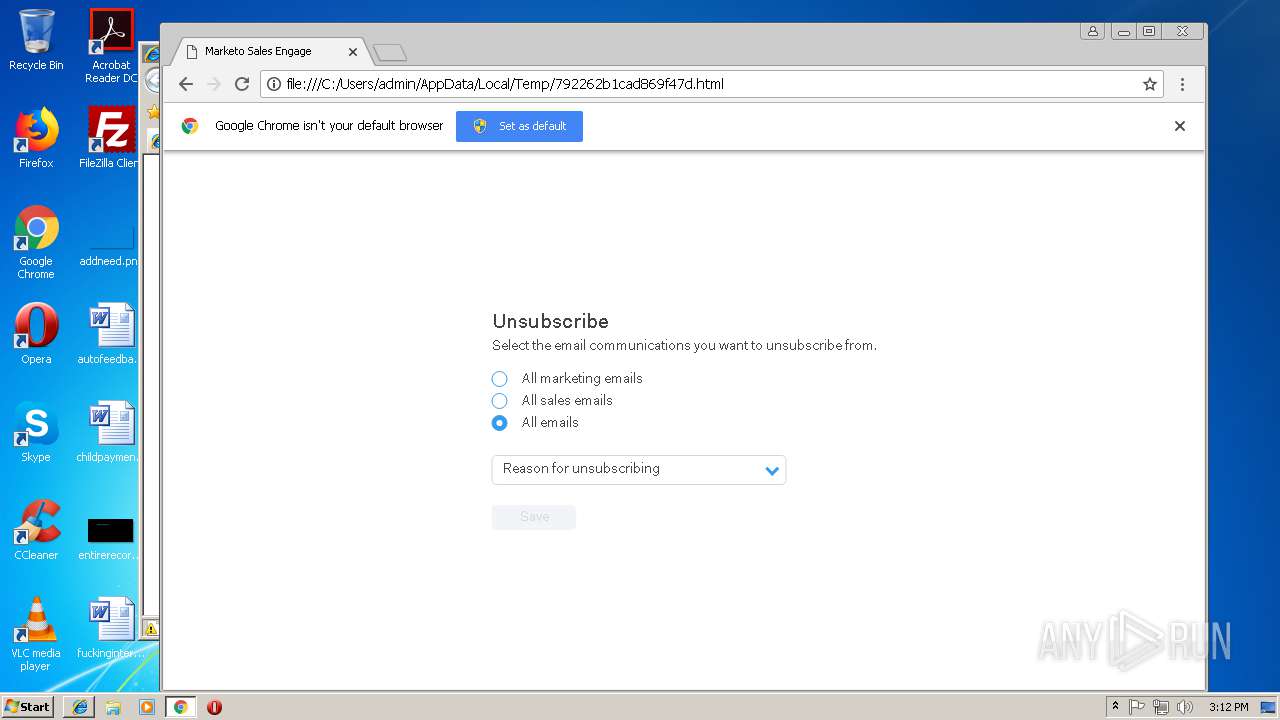
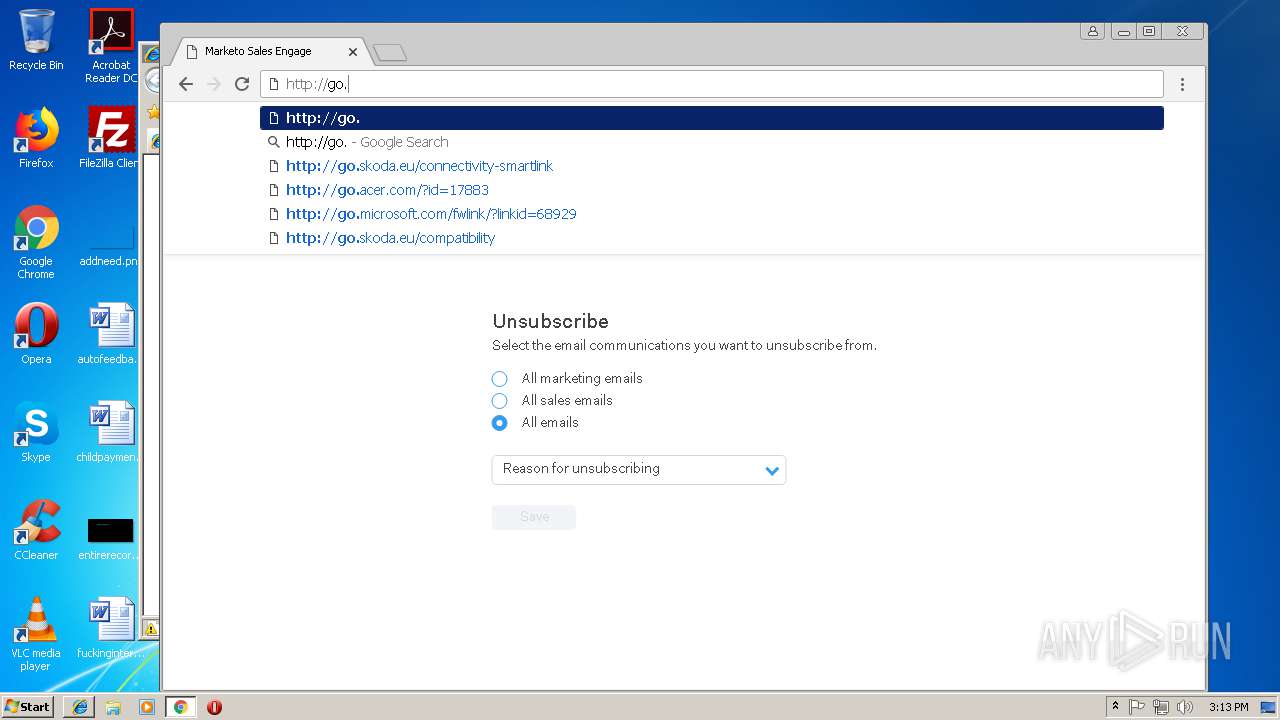
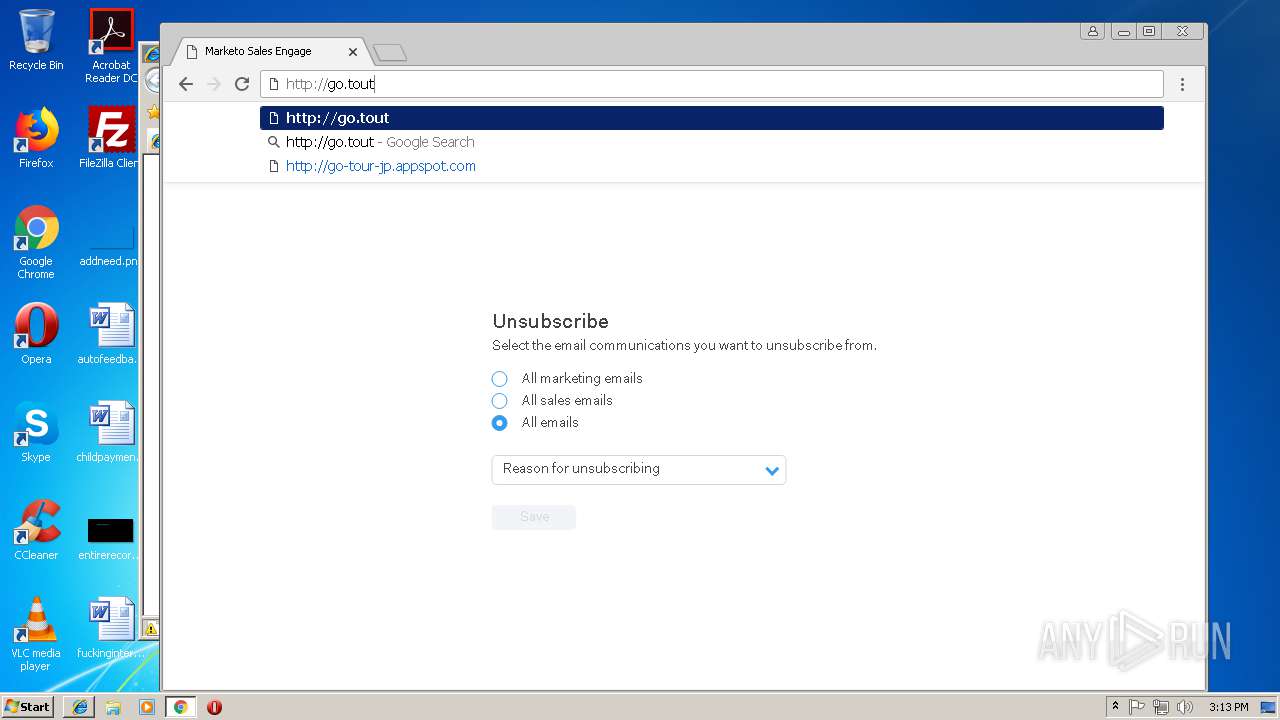
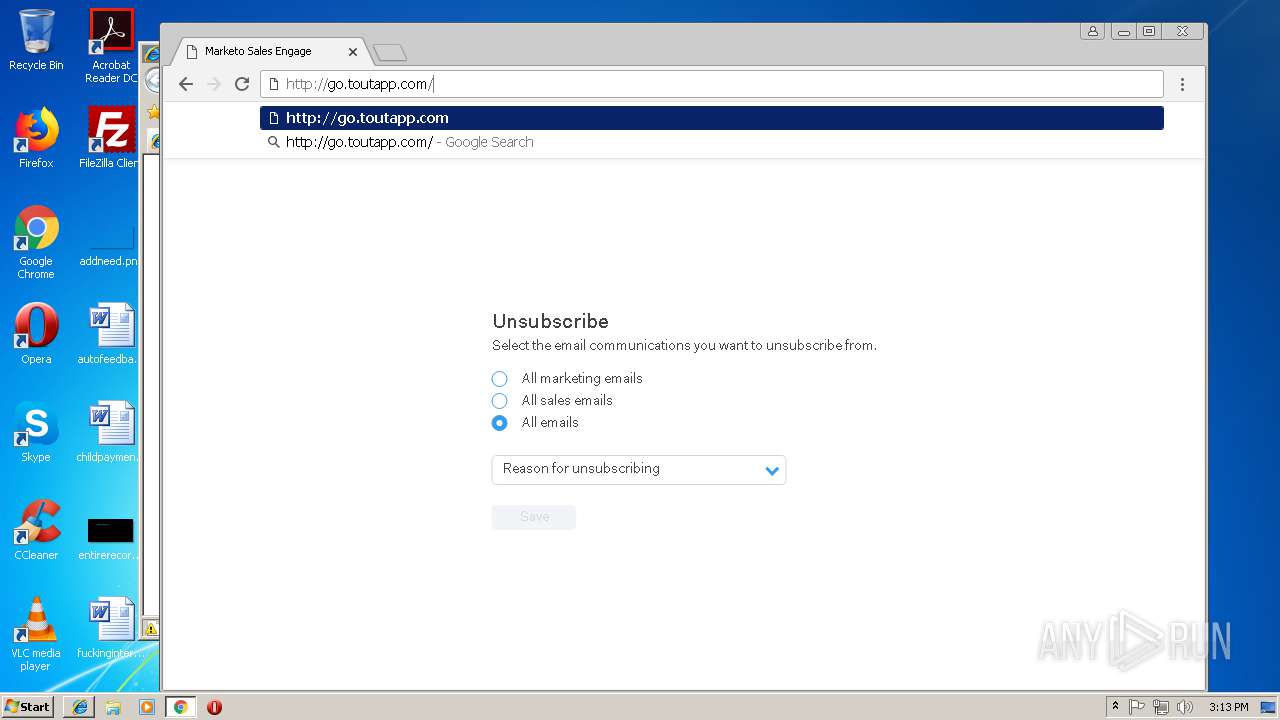
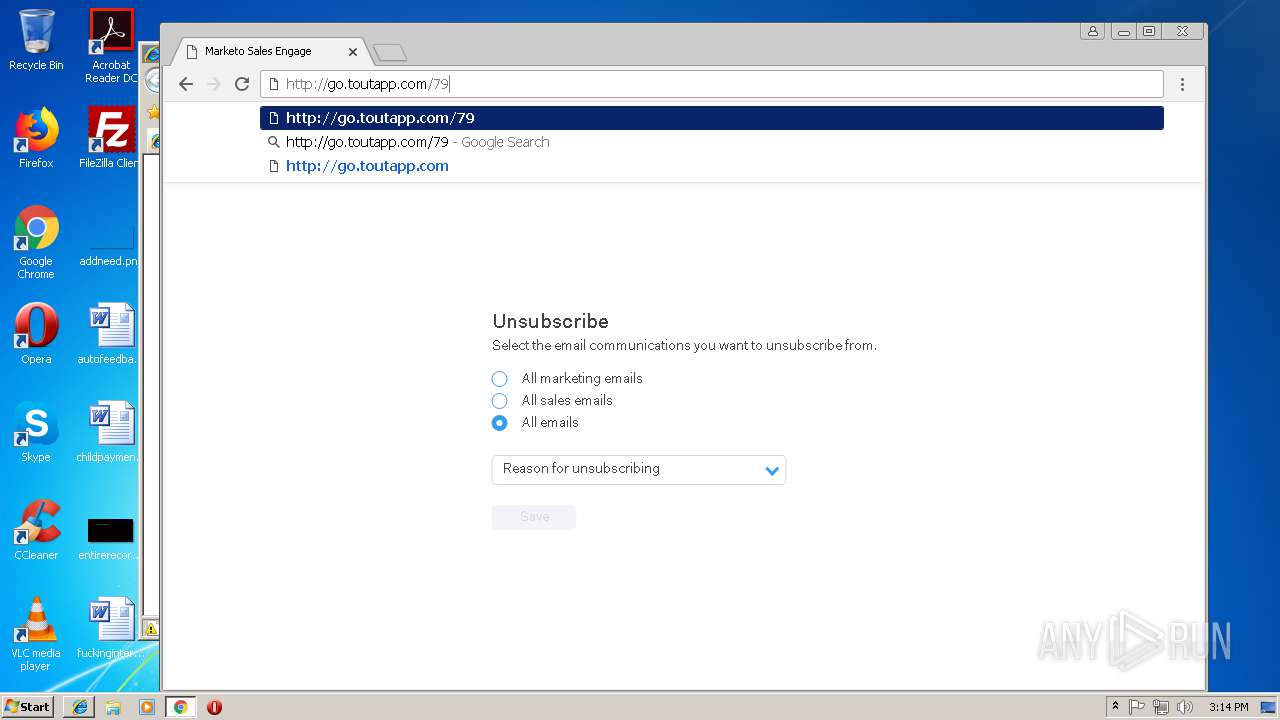
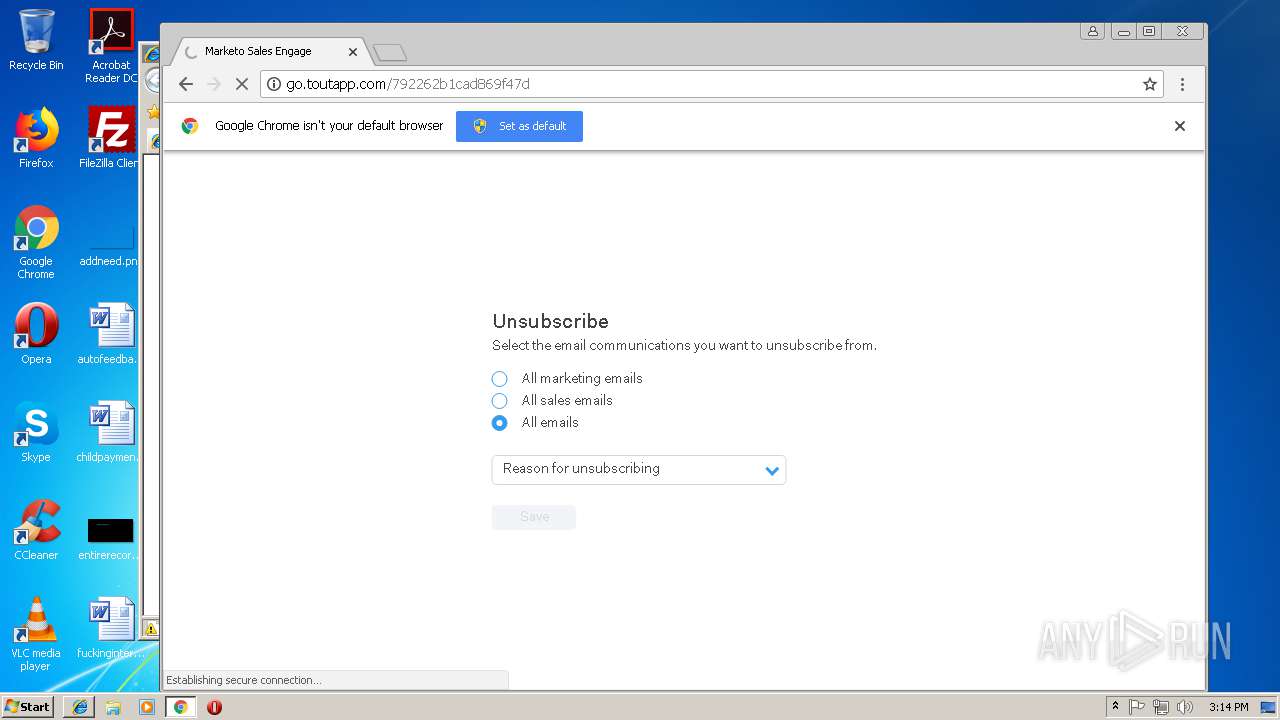
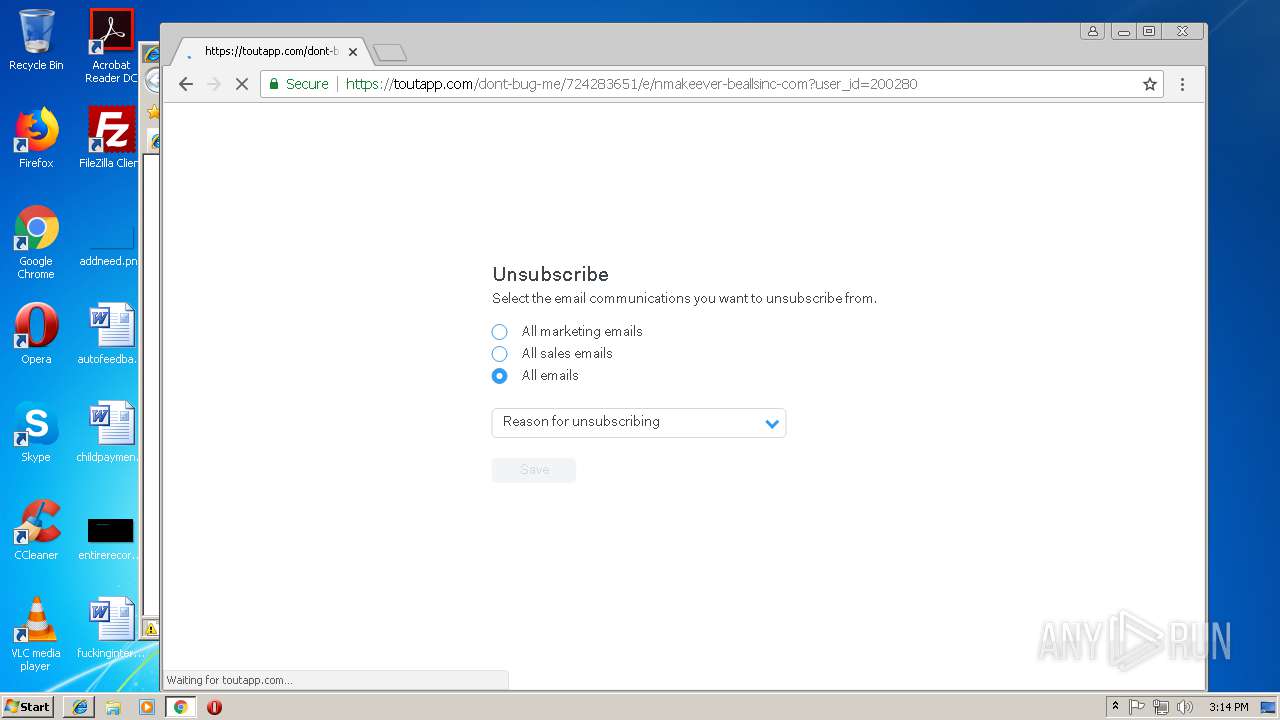
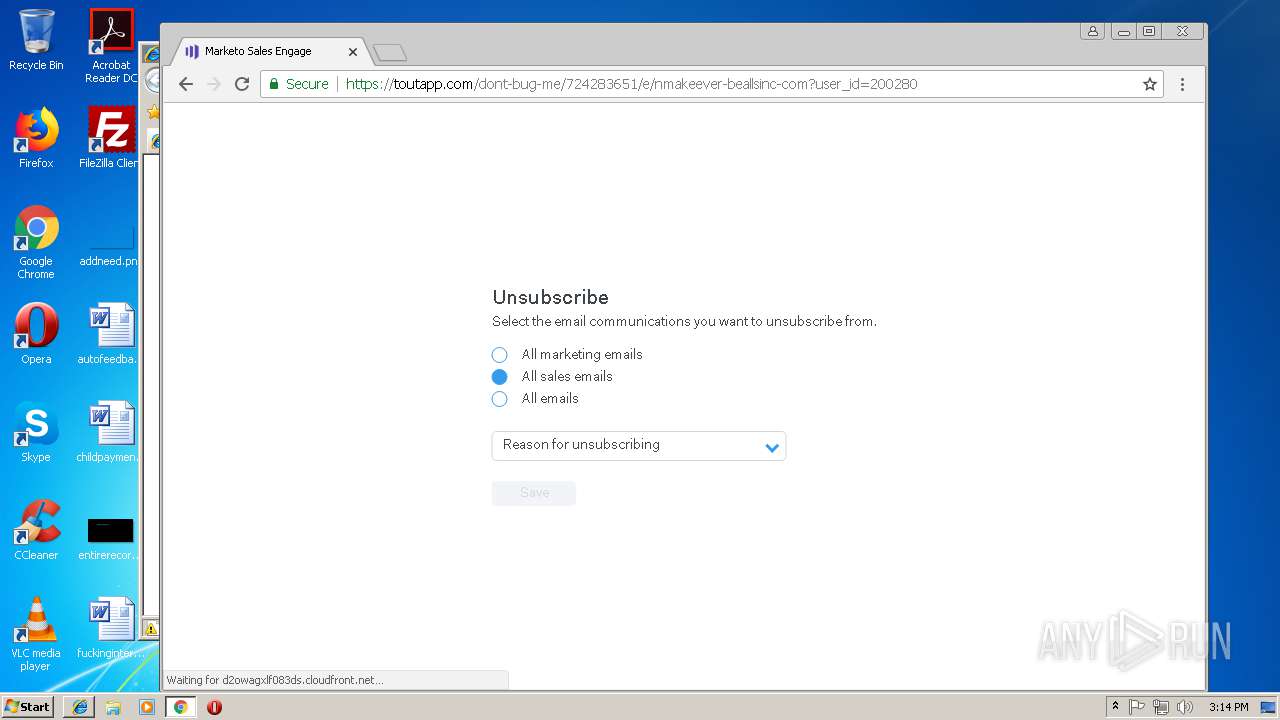
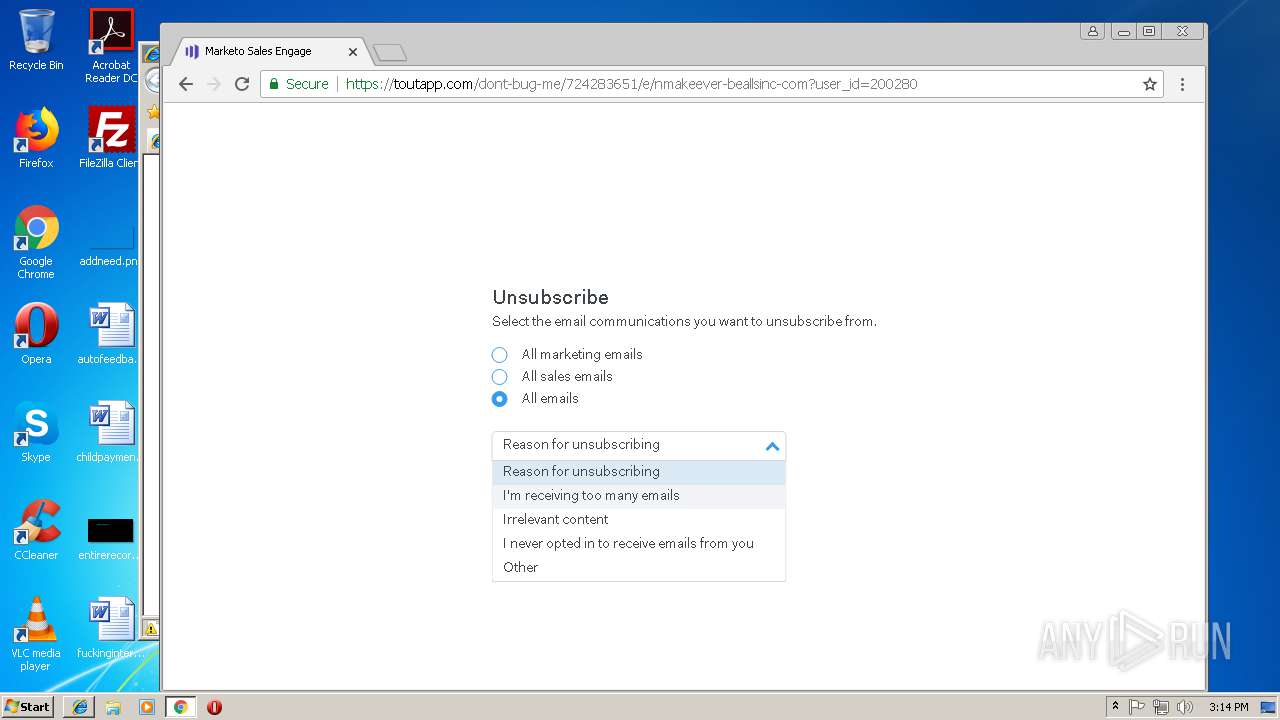
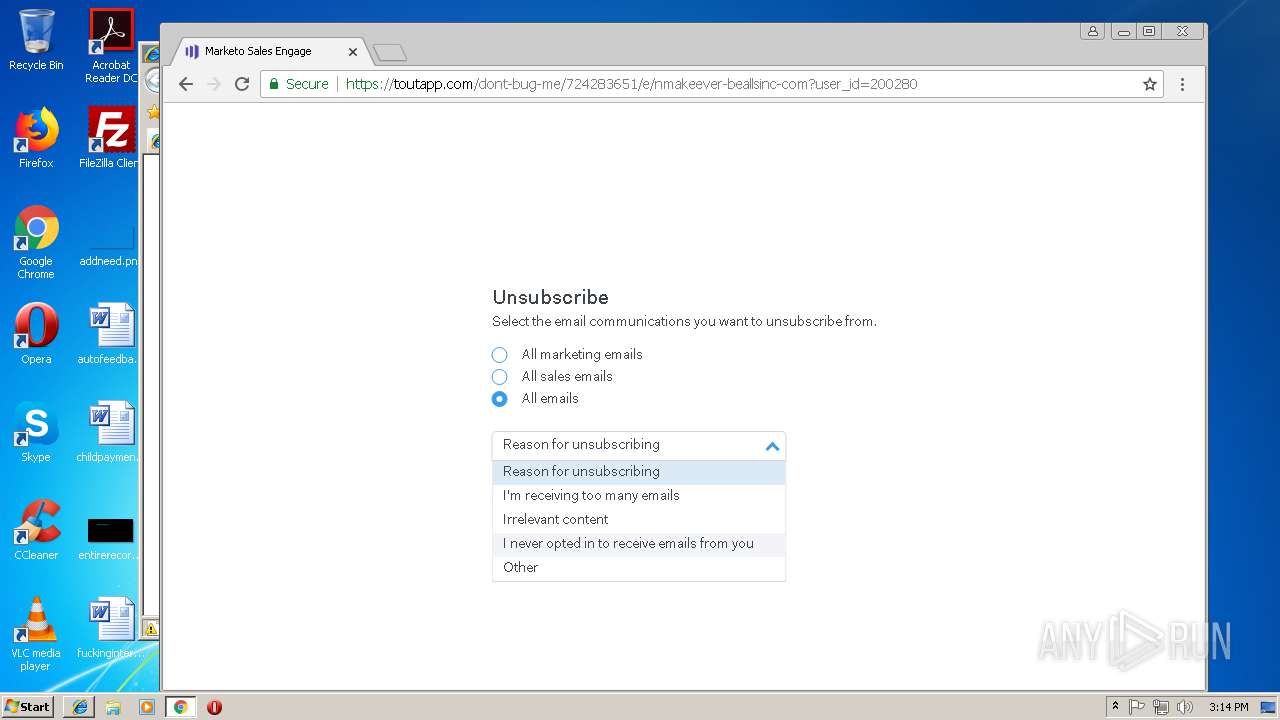
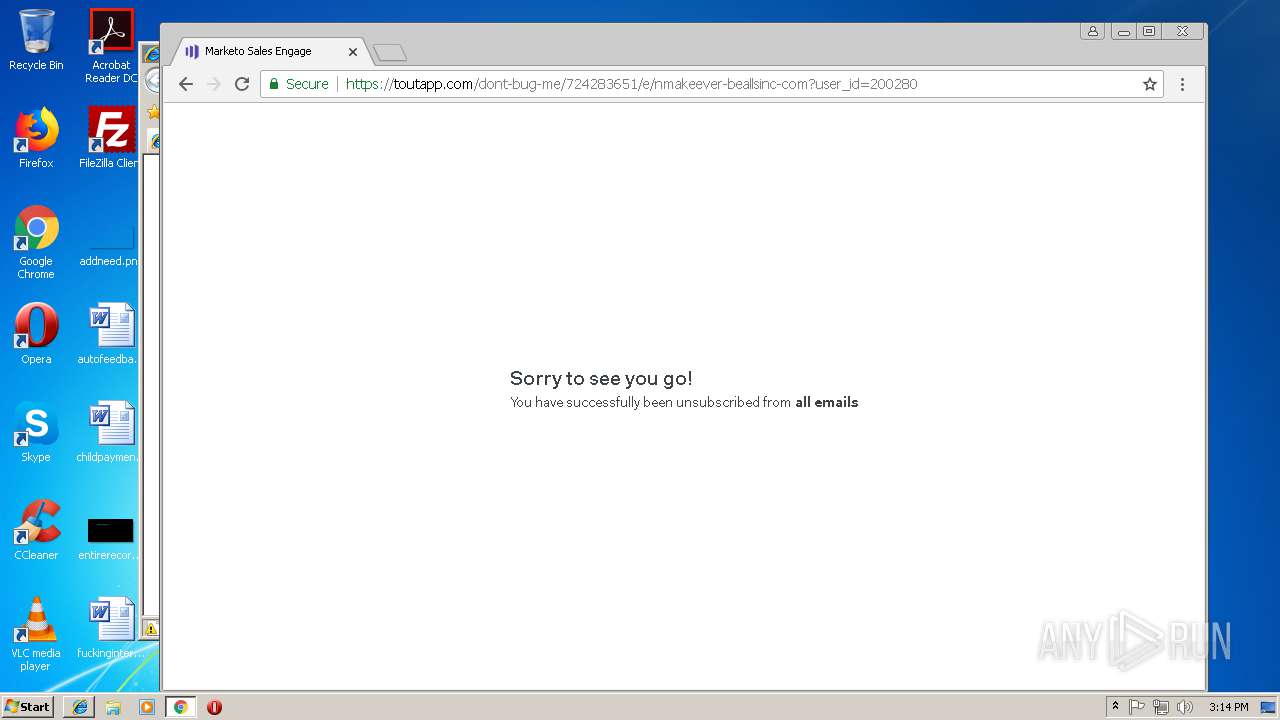
| Title: | Marketo Sales Engage |
| Description: | Write your emails faster and know when people read your emails with ToutApp's templates and real-time tracking |
| Keywords: | salesforce, outlook, gmail, email, template, sales |
| Author: | ToutApp, Inc. |
| email: | team@toutapp.com |
| ContentType: | text/html; charset=utf-8 |
| Generator: | TextMate http://macromates.com/ |
| HTTPEquivXUACompatible: | IE=9 |
Total processes
49
Monitored processes
17
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=880,6667324470227671217,1032423671413057018,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=818606AB0A1A4C798B74FBE8EE75A5F5 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=818606AB0A1A4C798B74FBE8EE75A5F5 --renderer-client-id=13 --mojo-platform-channel-handle=3812 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=880,6667324470227671217,1032423671413057018,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=B4B65F477B6D00D86C022A69B124BE7B --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=B4B65F477B6D00D86C022A69B124BE7B --renderer-client-id=15 --mojo-platform-channel-handle=3360 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6df100b0,0x6df100c0,0x6df100cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2224 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=880,6667324470227671217,1032423671413057018,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=B7652F1B20621C50C3E34A52467EEC88 --mojo-platform-channel-handle=908 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=880,6667324470227671217,1032423671413057018,131072 --enable-features=PasswordImport --service-pipe-token=F7CF56CD5EE1CF706A9408A24B6DC3F4 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=F7CF56CD5EE1CF706A9408A24B6DC3F4 --renderer-client-id=3 --mojo-platform-channel-handle=1932 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=880,6667324470227671217,1032423671413057018,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=F35DB8B1FC3A593DDB9648423420169C --mojo-platform-channel-handle=608 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2812 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=780 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=880,6667324470227671217,1032423671413057018,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=925324BDC2D2B509159C8812517B86A4 --mojo-platform-channel-handle=2380 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=880,6667324470227671217,1032423671413057018,131072 --enable-features=PasswordImport --service-pipe-token=9134D52166310513354F21894084FAF7 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9134D52166310513354F21894084FAF7 --renderer-client-id=5 --mojo-platform-channel-handle=1928 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
926
Read events
792
Write events
129
Delete events
5
Modification events
| (PID) Process: | (3544) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3544) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3544) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3544) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3544) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3544) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3544) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {65B731DB-E81F-11E8-BFAB-5254004AAD11} |
Value: 0 | |||
| (PID) Process: | (3544) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3544) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (3544) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E2070B0003000E000F000A0013008C02 | |||
Executable files
0
Suspicious files
72
Text files
137
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3544 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3544 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3232 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@~~local~~[2].txt | — | |
MD5:— | SHA256:— | |||
| 3232 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\bundle[1].js | — | |
MD5:— | SHA256:— | |||
| 3232 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@~~local~~[3].txt | — | |
MD5:— | SHA256:— | |||
| 2372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\010460e8-b51d-450c-bbc5-41d9078777f1.tmp | — | |
MD5:— | SHA256:— | |||
| 2372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3232 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@~~local~~[1].txt | text | |
MD5:— | SHA256:— | |||
| 3232 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012018111420181115\index.dat | dat | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
43
DNS requests
28
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
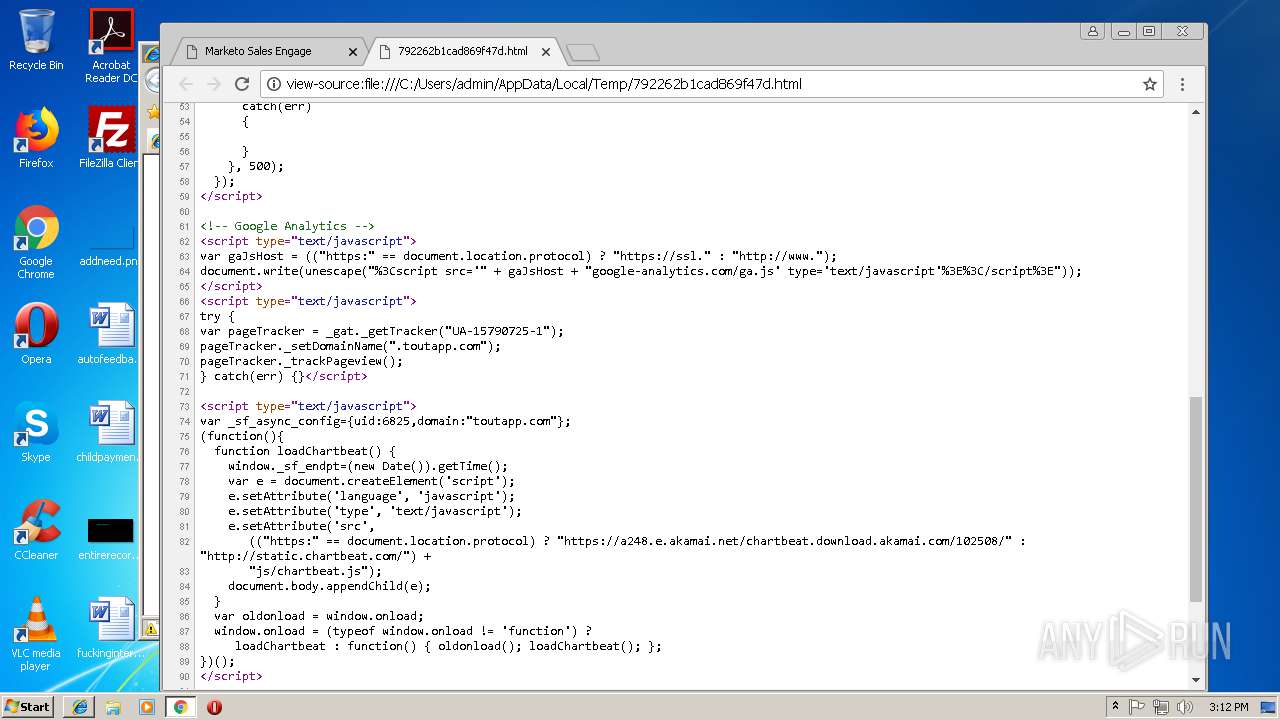
3232 | iexplore.exe | GET | 304 | 54.192.8.15:80 | http://static.chartbeat.com/js/chartbeat.js | US | — | — | whitelisted |
3232 | iexplore.exe | GET | 304 | 35.186.235.23:80 | http://cdn.mxpnl.com/libs/mixpanel-2.1.min.js | US | — | — | whitelisted |
3232 | iexplore.exe | GET | 304 | 35.186.235.23:80 | http://cdn.mxpnl.com/libs/mixpanel-2.1.min.js | US | — | — | whitelisted |
3232 | iexplore.exe | GET | 304 | 216.58.215.238:80 | http://www.google-analytics.com/ga.js | US | — | — | whitelisted |
3232 | iexplore.exe | GET | 304 | 216.58.215.238:80 | http://www.google-analytics.com/ga.js | US | — | — | whitelisted |
2372 | chrome.exe | GET | 302 | 34.236.1.30:80 | http://go.toutapp.com/792262b1cad869f47d | US | — | — | whitelisted |
3232 | iexplore.exe | GET | 200 | 54.192.8.15:80 | http://static.chartbeat.com/js/chartbeat.js | US | text | 13.6 Kb | whitelisted |
2372 | chrome.exe | GET | 200 | 54.192.8.15:80 | http://static.chartbeat.com/js/chartbeat.js | US | text | 13.6 Kb | whitelisted |
3232 | iexplore.exe | GET | 200 | 35.186.235.23:80 | http://cdn.mxpnl.com/libs/mixpanel-2.1.min.js | US | text | 9.22 Kb | whitelisted |
3232 | iexplore.exe | GET | 200 | 35.186.241.51:80 | http://api.mixpanel.com/track/?data=eyJldmVudCI6ICJtcF9wYWdlX3ZpZXciLCJwcm9wZXJ0aWVzIjogeyIkb3MiOiAiV2luZG93cyIsIiRicm93c2VyIjogIkludGVybmV0IEV4cGxvcmVyIiwiJHNjcmVlbl9oZWlnaHQiOiA3MjAsIiRzY3JlZW5fd2lkdGgiOiAxMjgwLCJtcF9saWIiOiAid2ViIiwiZGlzdGluY3RfaWQiOiAiMTY3MTJjNjI2ODdhMDgtMDJlNDEyNjI5NzkxNjljLTQ0NzAzNDE4LWUxMDAwLTE2NzEyYzYyNjk2MTY0MyIsIiRpbml0aWFsX3JlZmVycmVyIjogIiRkaXJlY3QiLCIkaW5pdGlhbF9yZWZlcnJpbmdfZG9tYWluIjogIiRkaXJlY3QiLCJtcF9wYWdlIjogImZpbGU6Ly8vQzovVXNlcnMvYWRtaW4vQXBwRGF0YS9Mb2NhbC9UZW1wLzc5MjI2MmIxY2FkODY5ZjQ3ZC5odG1sIiwibXBfYnJvd3NlciI6ICJJbnRlcm5ldCBFeHBsb3JlciIsIm1wX3BsYXRmb3JtIjogIldpbmRvd3MiLCJ0b2tlbiI6ICJiZGRlYjIyZTdmOWM0YWExNWUxNGNiOTUwYjA2ZWNlYSJ9fQ%3D%3D&ip=1&_=1542208324231 | US | binary | 1 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
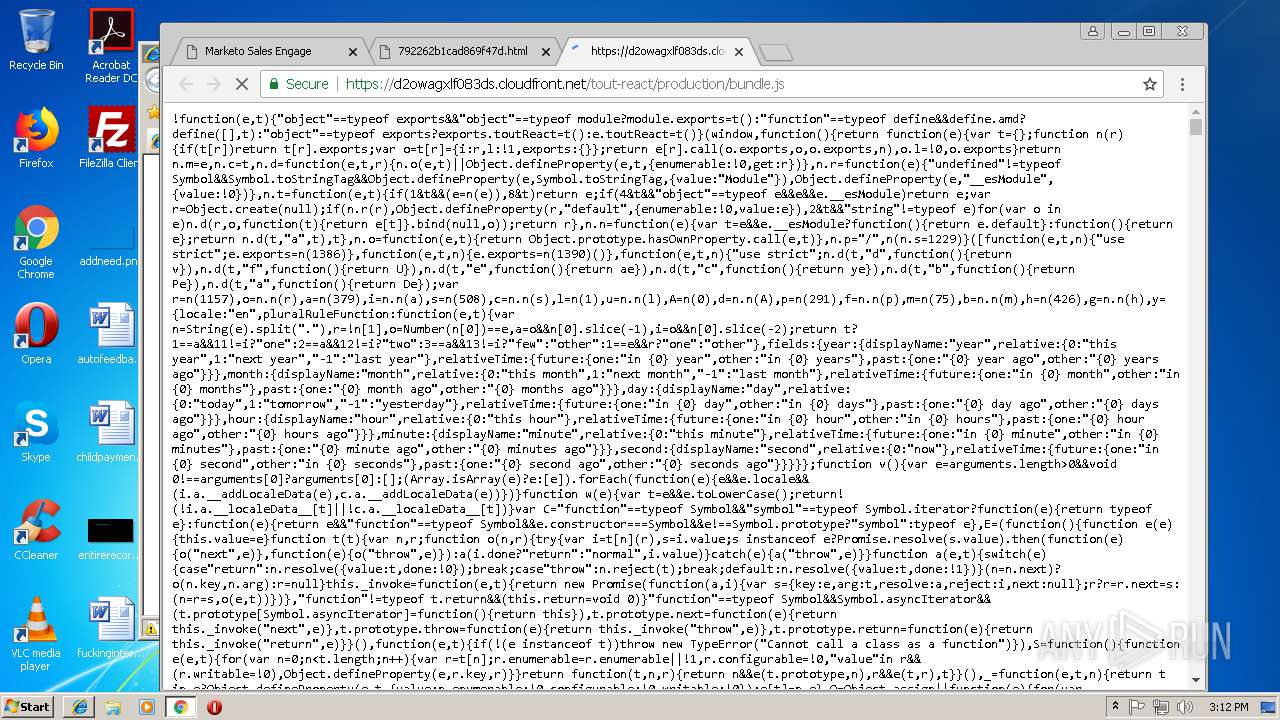
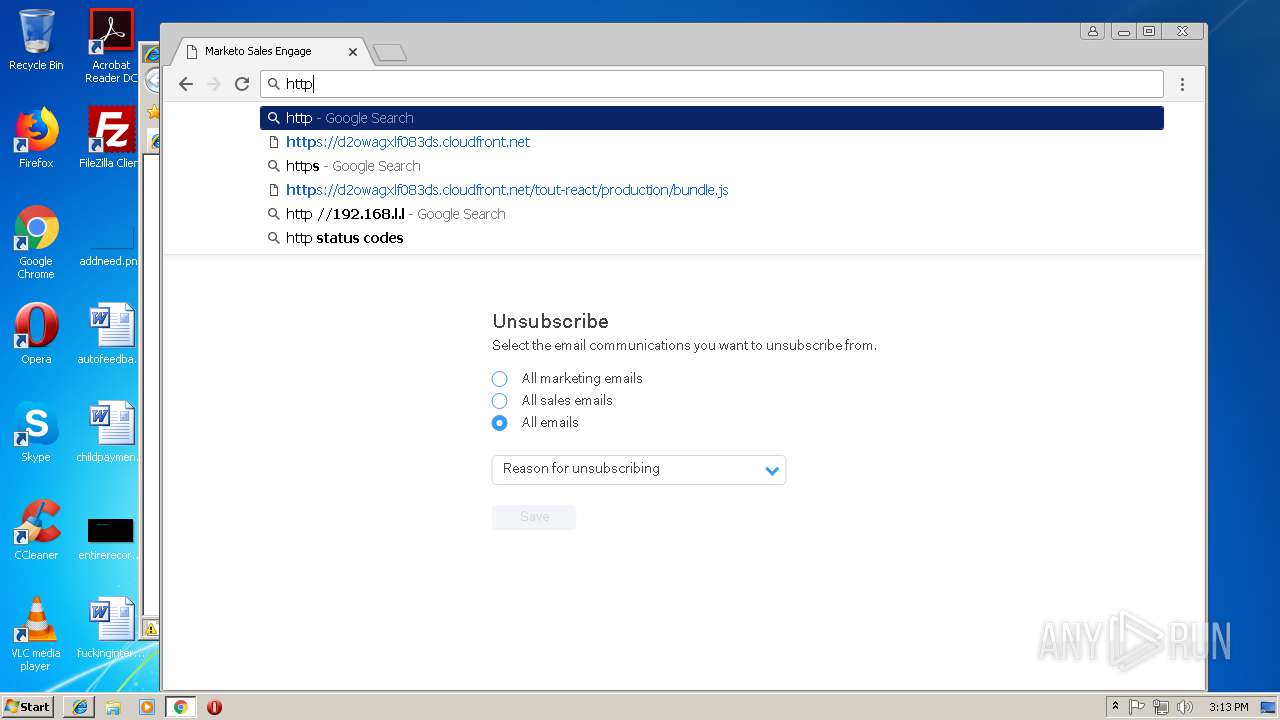
3232 | iexplore.exe | 52.85.182.73:443 | d2owagxlf083ds.cloudfront.net | Amazon.com, Inc. | US | suspicious |
3232 | iexplore.exe | 35.186.235.23:80 | cdn.mxpnl.com | Google Inc. | US | whitelisted |
— | — | 52.85.182.73:443 | d2owagxlf083ds.cloudfront.net | Amazon.com, Inc. | US | suspicious |
3232 | iexplore.exe | 216.58.215.238:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
3232 | iexplore.exe | 35.186.241.51:80 | api.mixpanel.com | Google Inc. | US | whitelisted |
3232 | iexplore.exe | 54.192.8.15:80 | static.chartbeat.com | Amazon.com, Inc. | US | unknown |
3232 | iexplore.exe | 54.164.229.237:443 | ping.chartbeat.net | Amazon.com, Inc. | US | unknown |
2372 | chrome.exe | 172.217.168.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2372 | chrome.exe | 172.217.168.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2372 | chrome.exe | 216.58.215.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
d2owagxlf083ds.cloudfront.net |
| whitelisted |
www.bing.com |
| whitelisted |
cdn.mxpnl.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
api.mixpanel.com |
| whitelisted |
static.chartbeat.com |
| whitelisted |
ping.chartbeat.net |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.de |
| whitelisted |