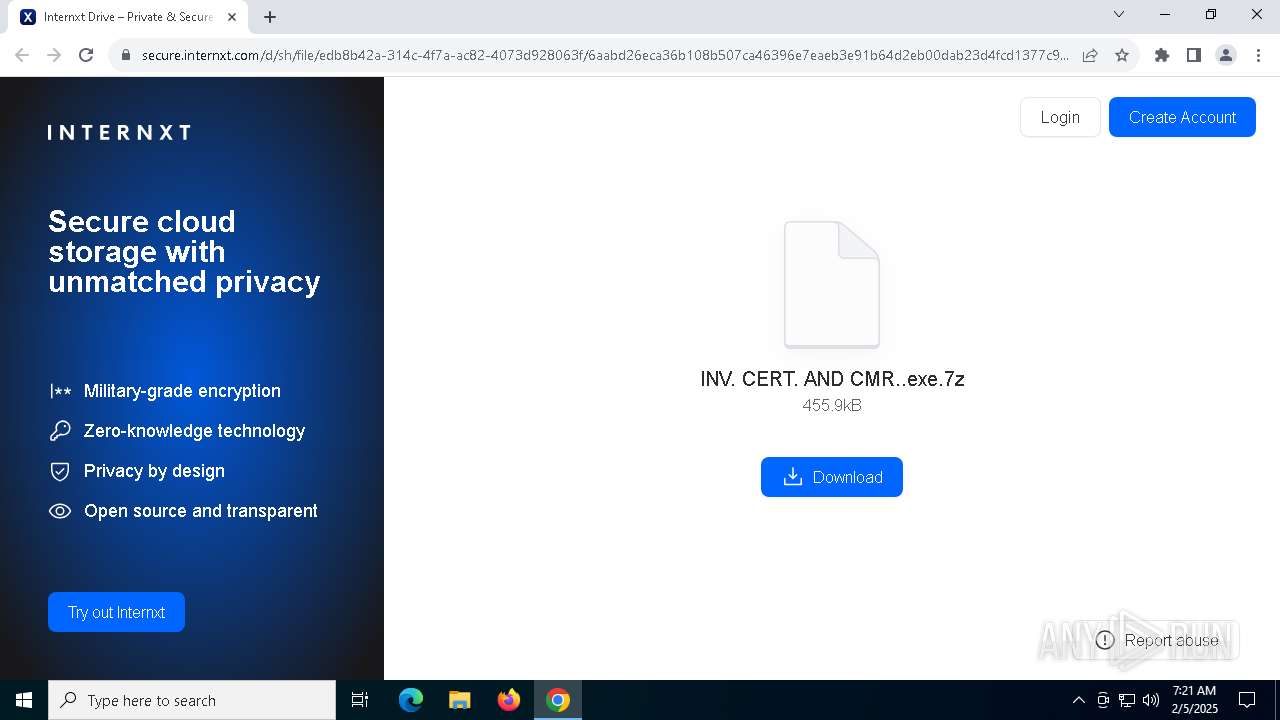
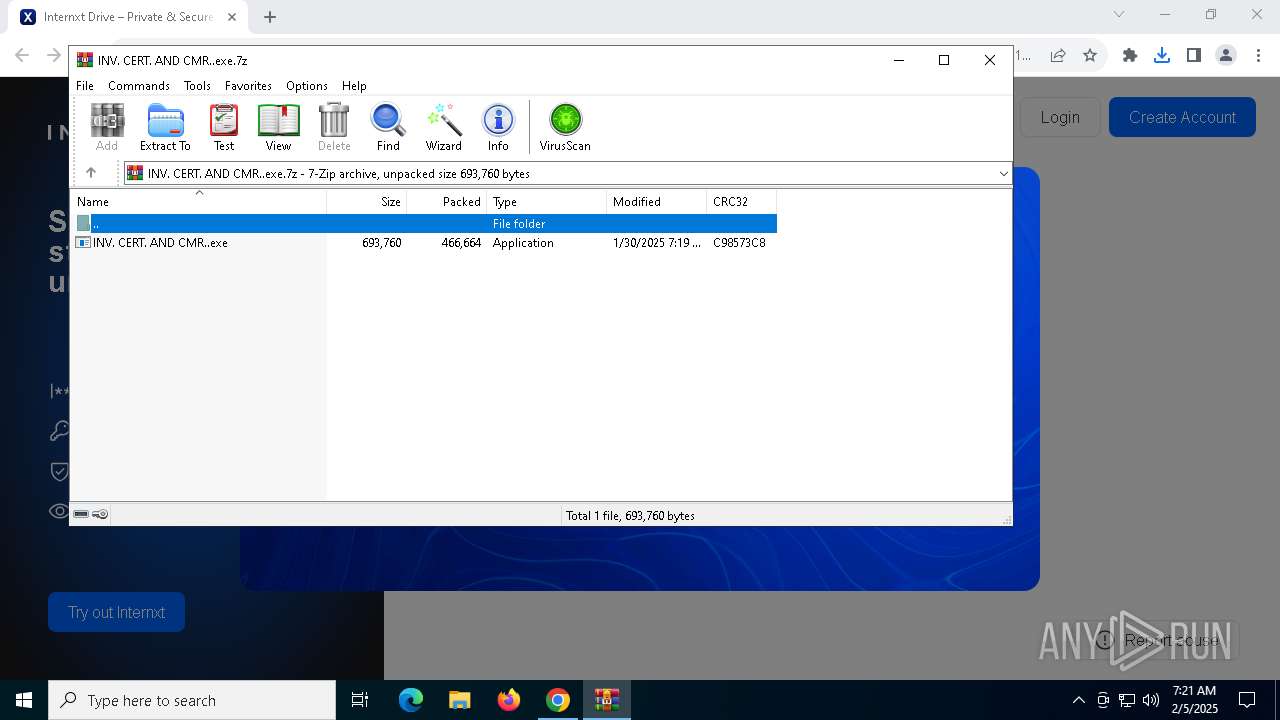
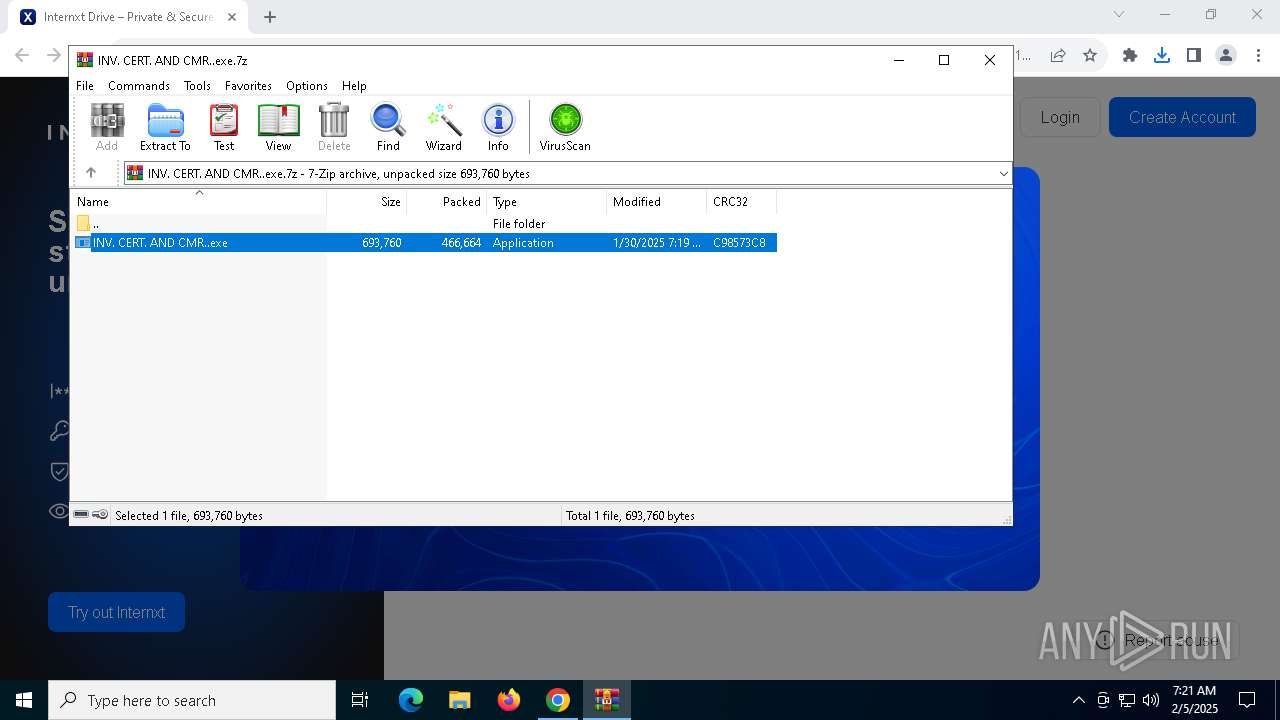
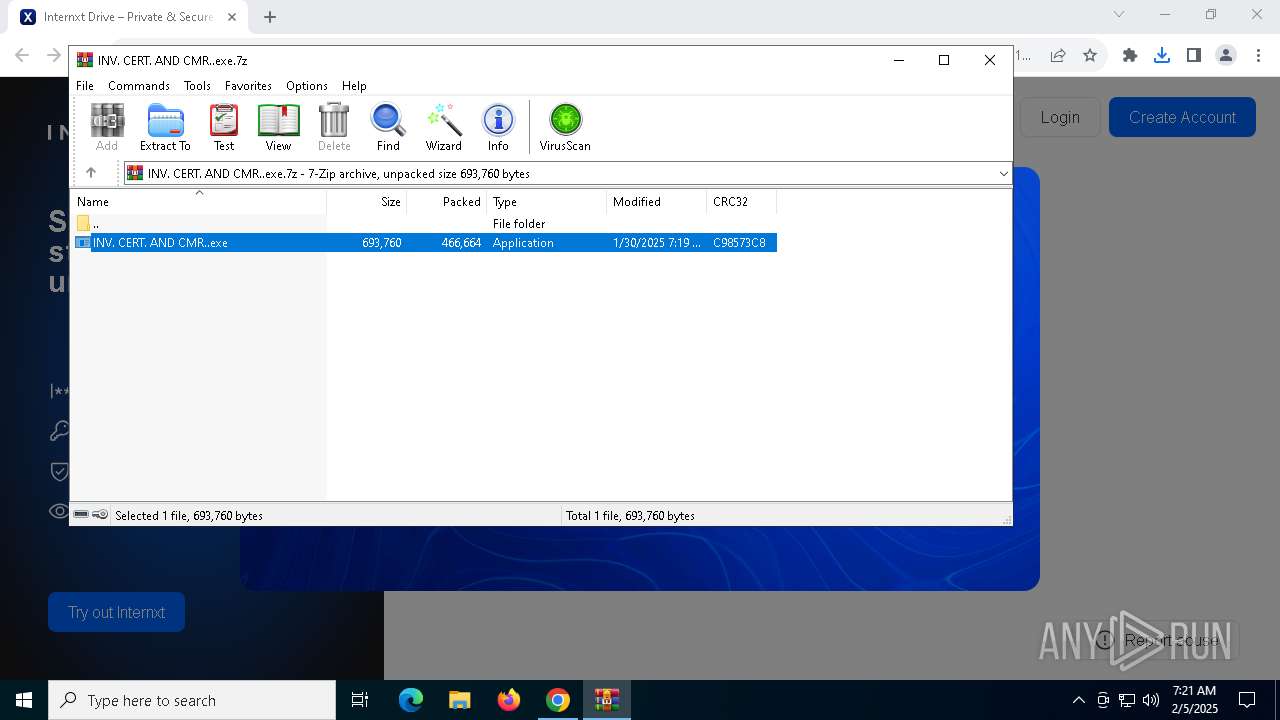
| URL: | https://secure.internxt.com/d/sh/file/edb8b42a-314c-4f7a-ac82-4073d928063f/6aabd26eca36b108b507ca46396e7eaeb3e91b64d2eb00dab23d4fcd1377c9d3 |
| Full analysis: | https://app.any.run/tasks/02a960d2-179c-4ad9-a00e-53524632e84e |
| Verdict: | Malicious activity |
| Analysis date: | February 05, 2025, 07:21:11 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 0636AC4ACEE9359BB4FF2F6E0433E835 |
| SHA1: | D28028DB6C7AF73E4A7D036B5AF9B58C56C28BFC |
| SHA256: | A5AD8D935FDD13C7AF27E86CD72443A3DB61E755860EDC8951C5A4D67D441C50 |
| SSDEEP: | 3:N8N3ubXL9IBKXk4rUgsct/v/Mt6HHdLApGUVB:2ZubXLqt4AgLVq6HxARn |
MALICIOUS
Uses Task Scheduler to run other applications
- INV. CERT. AND CMR..exe (PID: 3884)
- INV. CERT. AND CMR..exe (PID: 4672)
- INV. CERT. AND CMR..exe (PID: 432)
- INV. CERT. AND CMR..exe (PID: 2148)
- INV. CERT. AND CMR..exe (PID: 3696)
- INV. CERT. AND CMR..exe (PID: 1356)
- INV. CERT. AND CMR..exe (PID: 7000)
- INV. CERT. AND CMR..exe (PID: 5876)
- INV. CERT. AND CMR..exe (PID: 1172)
- INV. CERT. AND CMR..exe (PID: 6432)
- INV. CERT. AND CMR..exe (PID: 7040)
Create files in the Startup directory
- INV. CERT. AND CMR..exe (PID: 4052)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 1144)
- INV. CERT. AND CMR..exe (PID: 3884)
- INV. CERT. AND CMR..exe (PID: 4672)
- INV. CERT. AND CMR..exe (PID: 432)
- INV. CERT. AND CMR..exe (PID: 2148)
- INV. CERT. AND CMR..exe (PID: 3696)
- INV. CERT. AND CMR..exe (PID: 7000)
- INV. CERT. AND CMR..exe (PID: 1356)
- INV. CERT. AND CMR..exe (PID: 5876)
- INV. CERT. AND CMR..exe (PID: 1172)
- INV. CERT. AND CMR..exe (PID: 6432)
- INV. CERT. AND CMR..exe (PID: 7040)
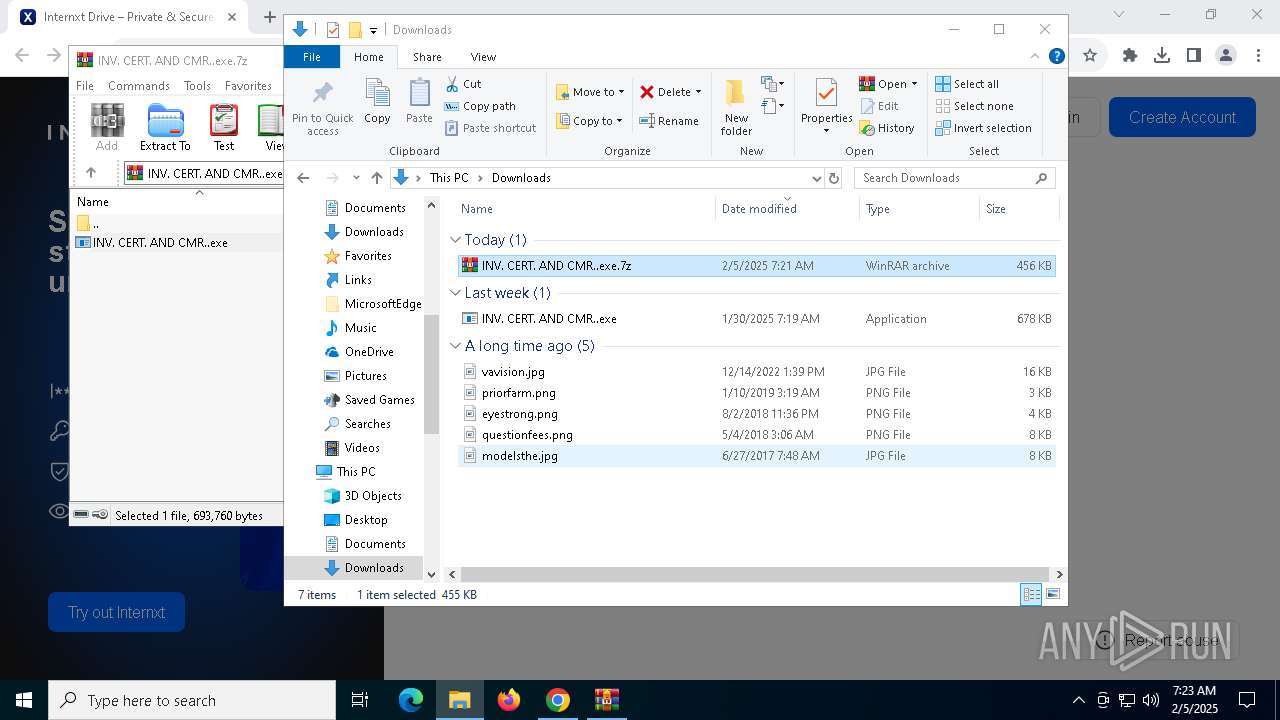
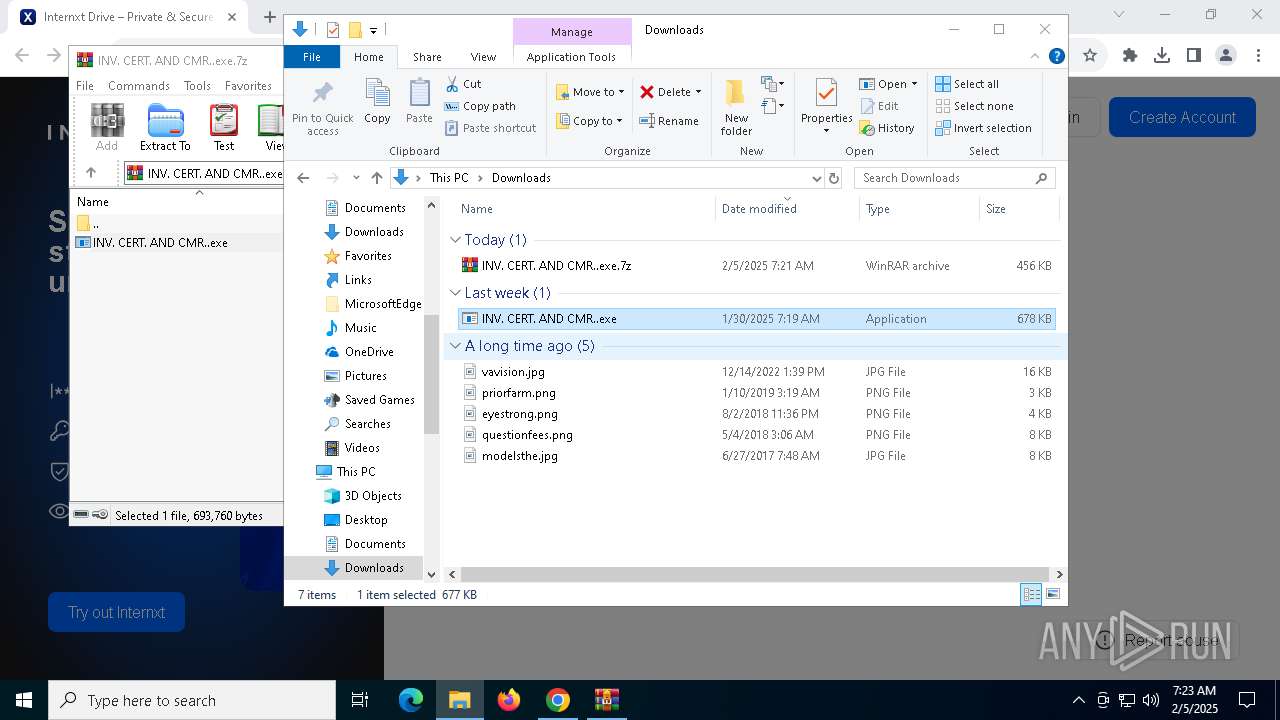
Executable content was dropped or overwritten
- INV. CERT. AND CMR..exe (PID: 3884)
- INV. CERT. AND CMR..exe (PID: 4052)
Application launched itself
- INV. CERT. AND CMR..exe (PID: 3884)
- INV. CERT. AND CMR..exe (PID: 4672)
- INV. CERT. AND CMR..exe (PID: 432)
- INV. CERT. AND CMR..exe (PID: 2148)
- INV. CERT. AND CMR..exe (PID: 3696)
- INV. CERT. AND CMR..exe (PID: 7000)
- INV. CERT. AND CMR..exe (PID: 1356)
- INV. CERT. AND CMR..exe (PID: 5876)
- INV. CERT. AND CMR..exe (PID: 1172)
- INV. CERT. AND CMR..exe (PID: 6432)
- INV. CERT. AND CMR..exe (PID: 7040)
Connects to unusual port
- INV. CERT. AND CMR..exe (PID: 4052)
INFO
Reads Microsoft Office registry keys
- chrome.exe (PID: 6076)
Reads the computer name
- INV. CERT. AND CMR..exe (PID: 4672)
- INV. CERT. AND CMR..exe (PID: 3884)
- INV. CERT. AND CMR..exe (PID: 432)
- INV. CERT. AND CMR..exe (PID: 2148)
- INV. CERT. AND CMR..exe (PID: 4052)
- INV. CERT. AND CMR..exe (PID: 1488)
- INV. CERT. AND CMR..exe (PID: 520)
- INV. CERT. AND CMR..exe (PID: 3696)
- INV. CERT. AND CMR..exe (PID: 5936)
- INV. CERT. AND CMR..exe (PID: 5876)
- INV. CERT. AND CMR..exe (PID: 1200)
- INV. CERT. AND CMR..exe (PID: 7000)
- INV. CERT. AND CMR..exe (PID: 1356)
- INV. CERT. AND CMR..exe (PID: 3080)
- INV. CERT. AND CMR..exe (PID: 7104)
- INV. CERT. AND CMR..exe (PID: 1172)
- INV. CERT. AND CMR..exe (PID: 3828)
- INV. CERT. AND CMR..exe (PID: 1300)
- INV. CERT. AND CMR..exe (PID: 6432)
- INV. CERT. AND CMR..exe (PID: 7040)
- INV. CERT. AND CMR..exe (PID: 3864)
- INV. CERT. AND CMR..exe (PID: 848)
Reads the machine GUID from the registry
- INV. CERT. AND CMR..exe (PID: 3884)
- INV. CERT. AND CMR..exe (PID: 4672)
- INV. CERT. AND CMR..exe (PID: 2148)
- INV. CERT. AND CMR..exe (PID: 432)
- INV. CERT. AND CMR..exe (PID: 4052)
- INV. CERT. AND CMR..exe (PID: 1488)
- INV. CERT. AND CMR..exe (PID: 520)
- INV. CERT. AND CMR..exe (PID: 3696)
- INV. CERT. AND CMR..exe (PID: 5936)
- INV. CERT. AND CMR..exe (PID: 5876)
- INV. CERT. AND CMR..exe (PID: 1200)
- INV. CERT. AND CMR..exe (PID: 7000)
- INV. CERT. AND CMR..exe (PID: 1356)
- INV. CERT. AND CMR..exe (PID: 1172)
- INV. CERT. AND CMR..exe (PID: 3080)
- INV. CERT. AND CMR..exe (PID: 7104)
- INV. CERT. AND CMR..exe (PID: 3828)
- INV. CERT. AND CMR..exe (PID: 1300)
- INV. CERT. AND CMR..exe (PID: 7040)
- INV. CERT. AND CMR..exe (PID: 6432)
- INV. CERT. AND CMR..exe (PID: 3864)
- INV. CERT. AND CMR..exe (PID: 848)
Checks supported languages
- INV. CERT. AND CMR..exe (PID: 4672)
- INV. CERT. AND CMR..exe (PID: 432)
- INV. CERT. AND CMR..exe (PID: 2148)
- INV. CERT. AND CMR..exe (PID: 1488)
- INV. CERT. AND CMR..exe (PID: 4052)
- INV. CERT. AND CMR..exe (PID: 520)
- INV. CERT. AND CMR..exe (PID: 3696)
- INV. CERT. AND CMR..exe (PID: 5936)
- INV. CERT. AND CMR..exe (PID: 1356)
- INV. CERT. AND CMR..exe (PID: 1200)
- INV. CERT. AND CMR..exe (PID: 7000)
- INV. CERT. AND CMR..exe (PID: 5876)
- INV. CERT. AND CMR..exe (PID: 1172)
- INV. CERT. AND CMR..exe (PID: 7104)
- INV. CERT. AND CMR..exe (PID: 3080)
- INV. CERT. AND CMR..exe (PID: 3828)
- INV. CERT. AND CMR..exe (PID: 1300)
- INV. CERT. AND CMR..exe (PID: 7040)
- INV. CERT. AND CMR..exe (PID: 3884)
- INV. CERT. AND CMR..exe (PID: 6432)
- INV. CERT. AND CMR..exe (PID: 3864)
- INV. CERT. AND CMR..exe (PID: 848)
Creates files or folders in the user directory
- INV. CERT. AND CMR..exe (PID: 3884)
- INV. CERT. AND CMR..exe (PID: 4052)
Create files in a temporary directory
- INV. CERT. AND CMR..exe (PID: 3884)
- INV. CERT. AND CMR..exe (PID: 4672)
- INV. CERT. AND CMR..exe (PID: 432)
- INV. CERT. AND CMR..exe (PID: 2148)
- INV. CERT. AND CMR..exe (PID: 3696)
- INV. CERT. AND CMR..exe (PID: 7000)
- INV. CERT. AND CMR..exe (PID: 1356)
- INV. CERT. AND CMR..exe (PID: 5876)
- INV. CERT. AND CMR..exe (PID: 1172)
- INV. CERT. AND CMR..exe (PID: 6432)
- INV. CERT. AND CMR..exe (PID: 7040)
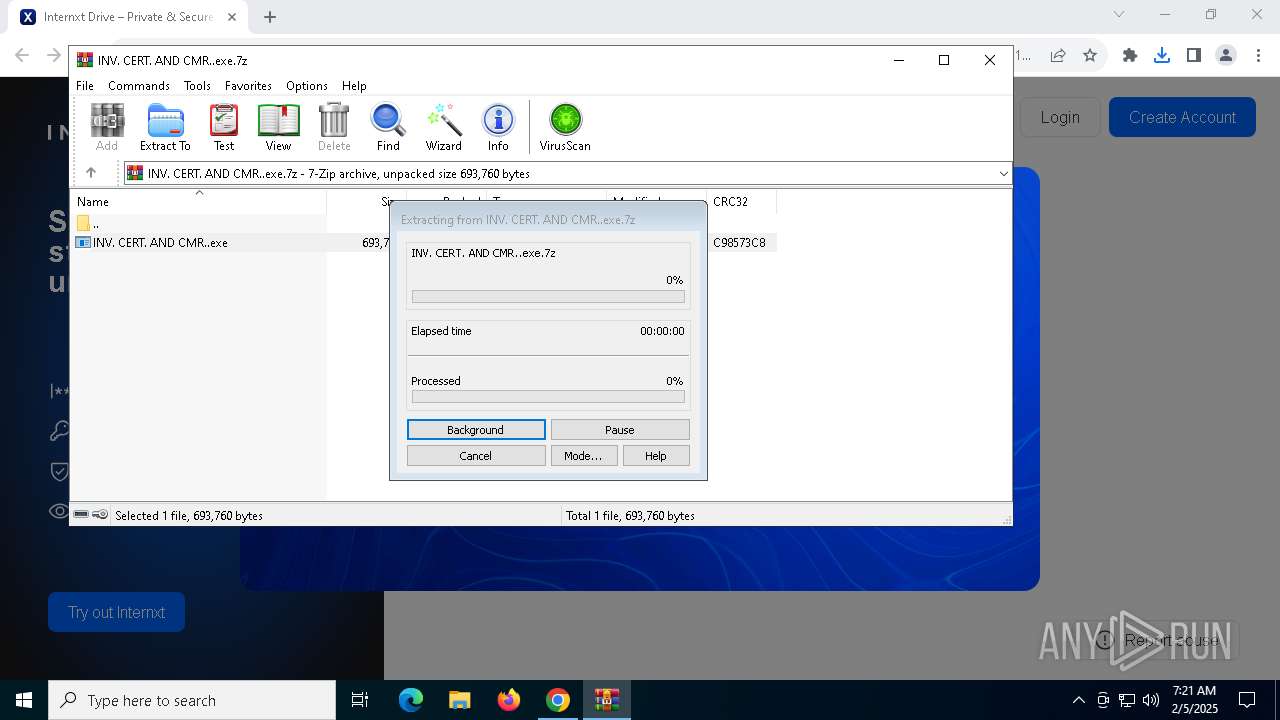
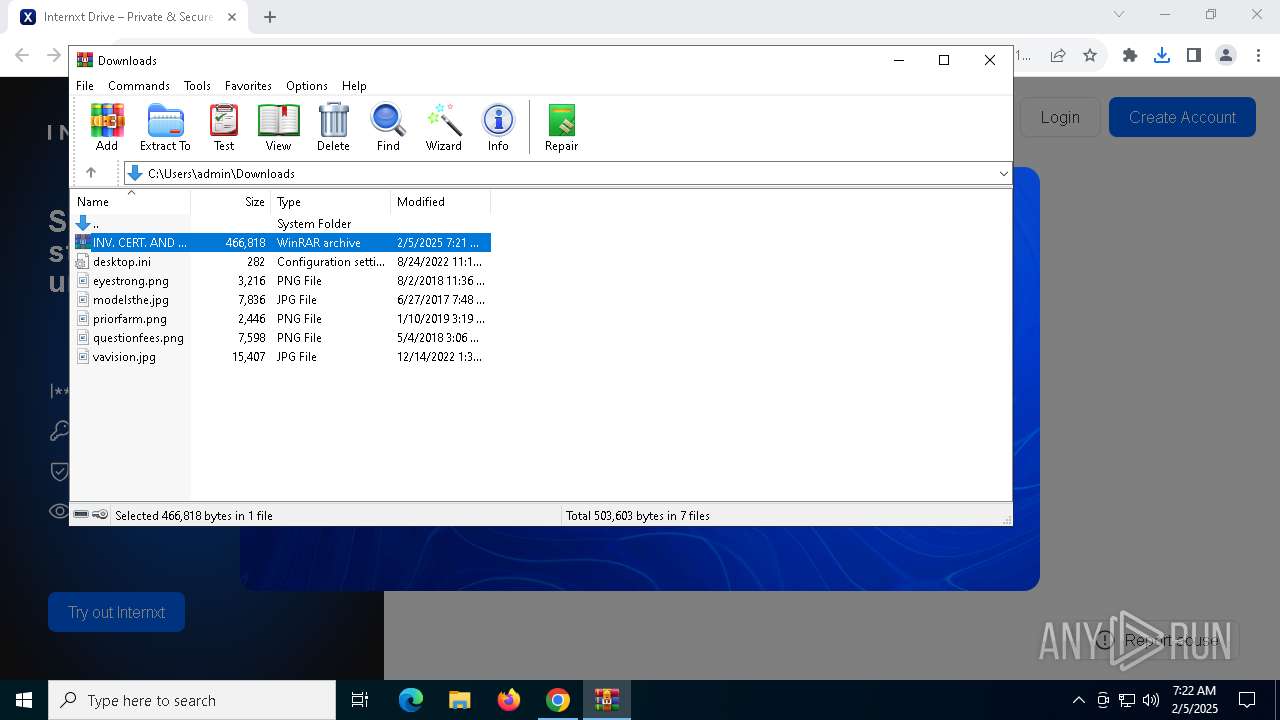
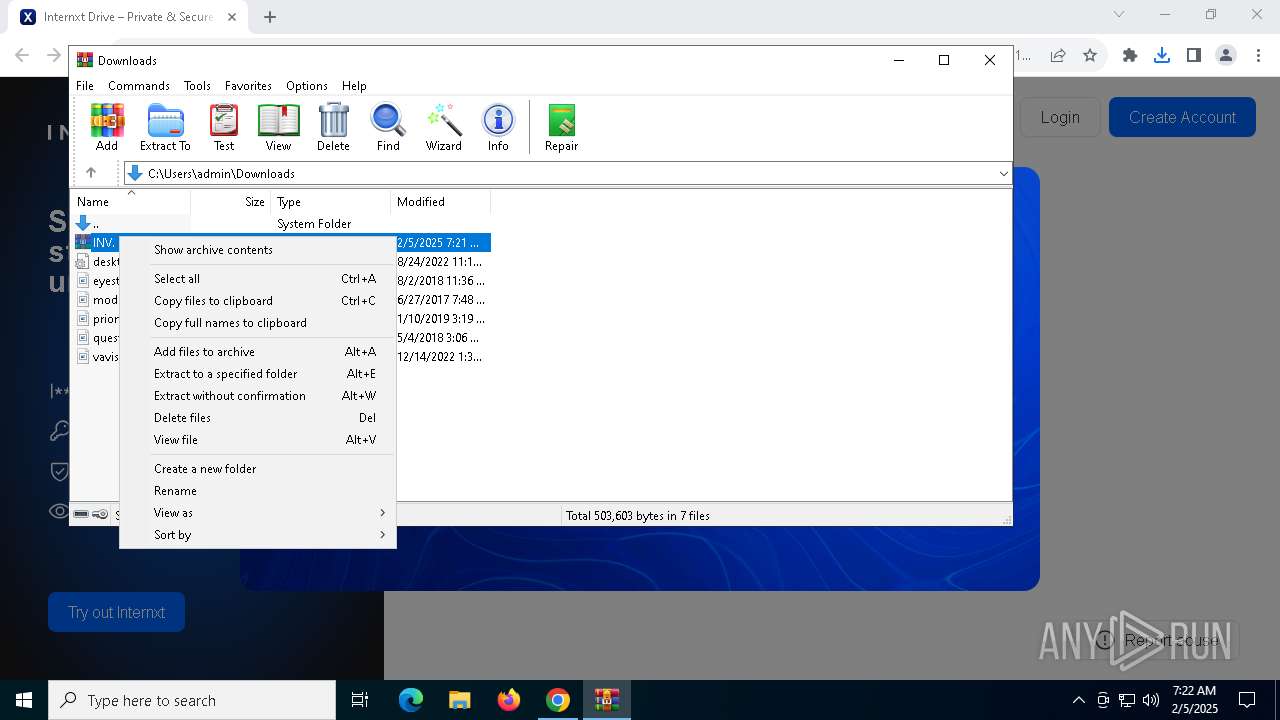
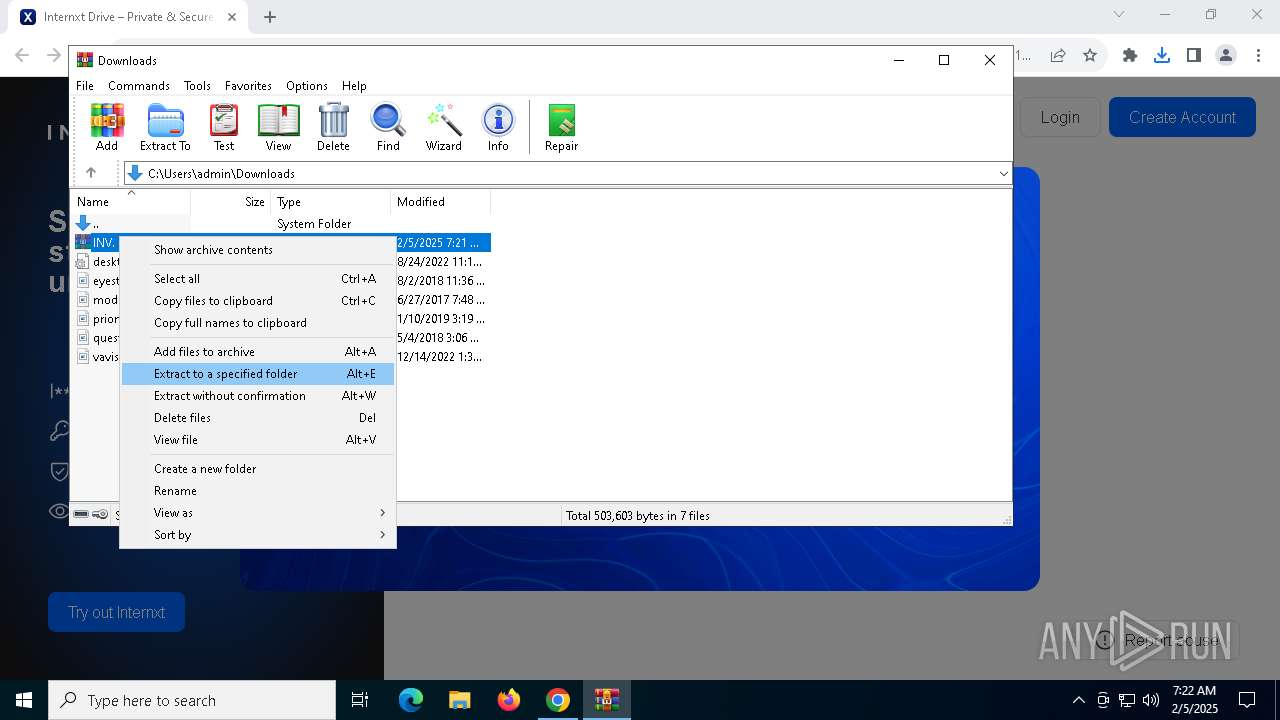
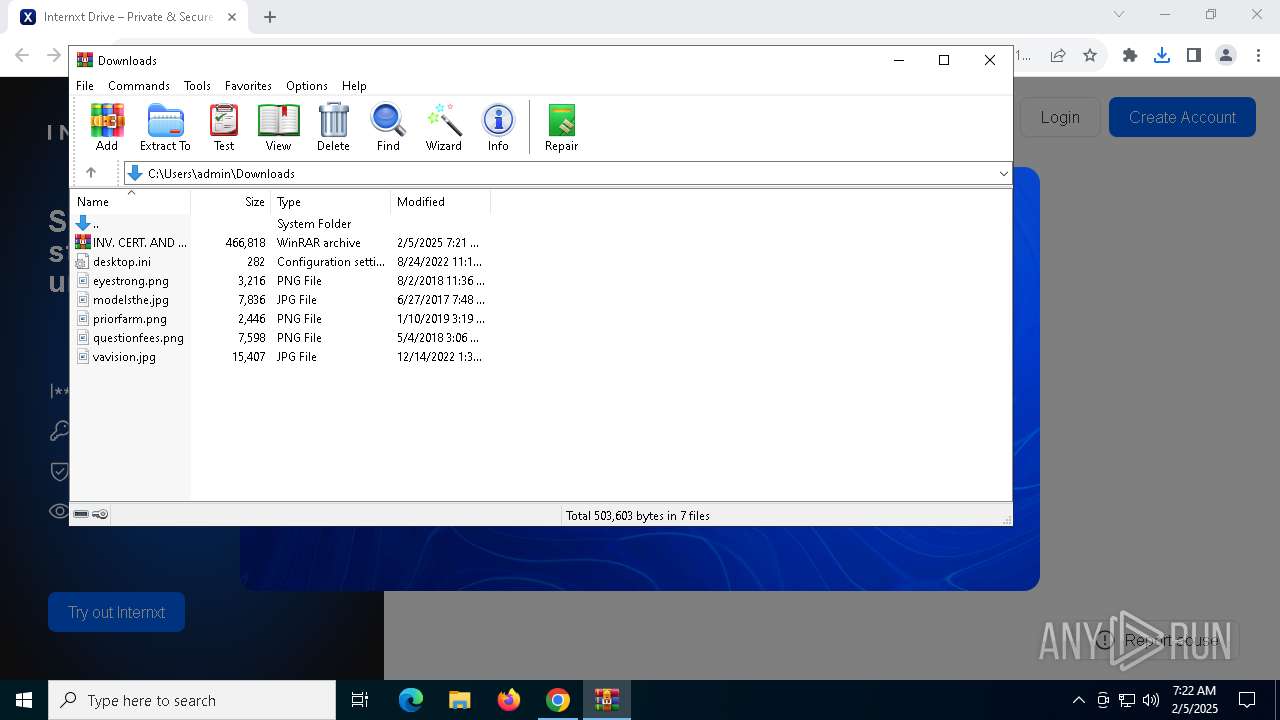
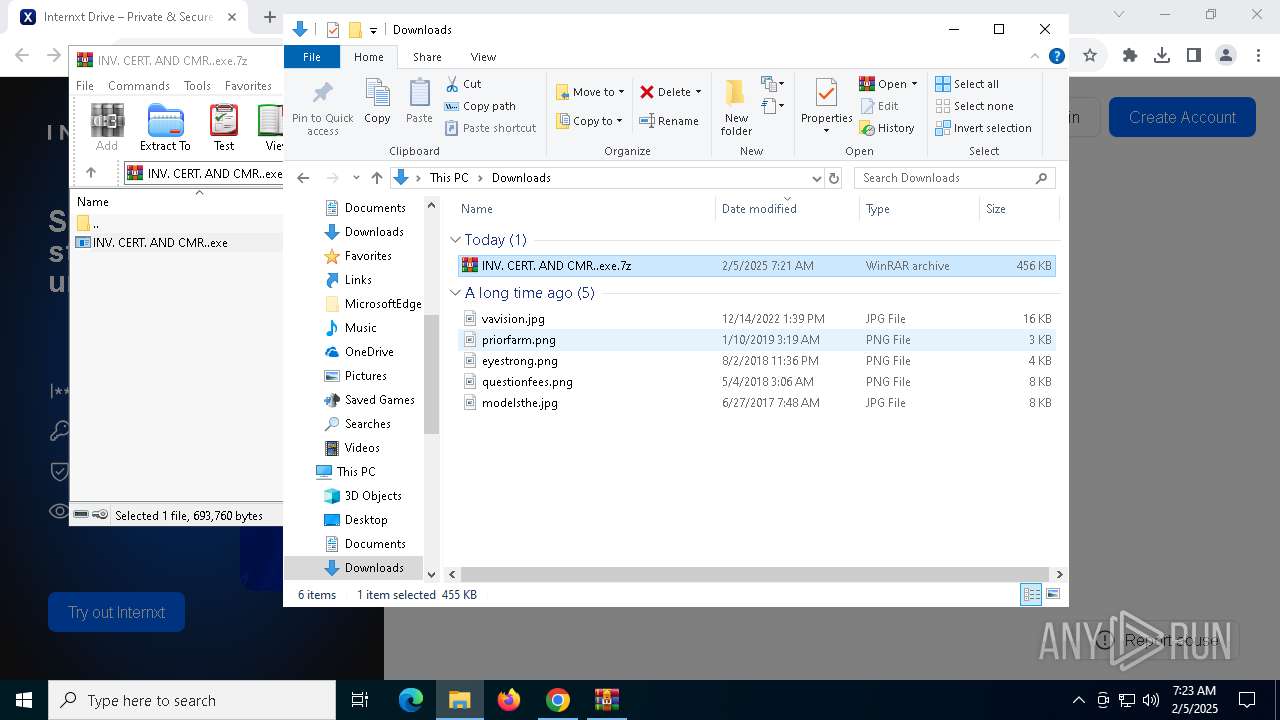
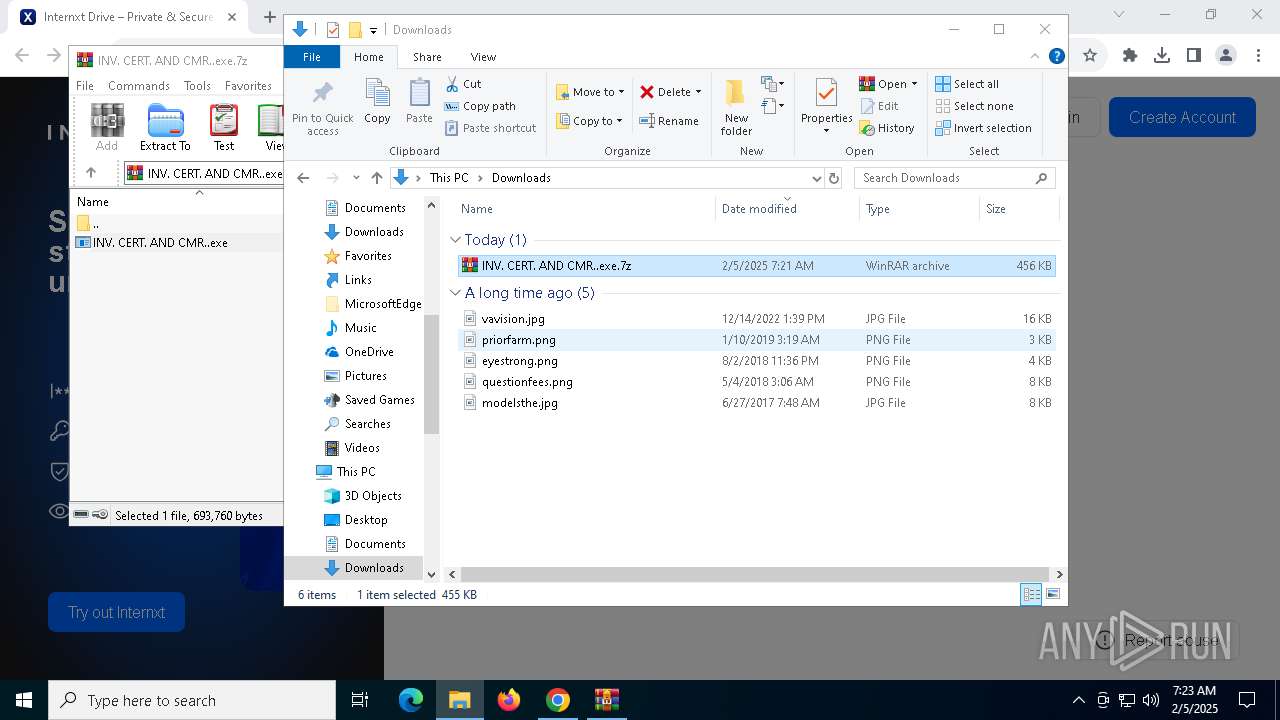
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1144)
- WinRAR.exe (PID: 6404)
Process checks computer location settings
- INV. CERT. AND CMR..exe (PID: 3884)
- INV. CERT. AND CMR..exe (PID: 4672)
- INV. CERT. AND CMR..exe (PID: 432)
- INV. CERT. AND CMR..exe (PID: 2148)
- INV. CERT. AND CMR..exe (PID: 3696)
- INV. CERT. AND CMR..exe (PID: 7000)
- INV. CERT. AND CMR..exe (PID: 1356)
- INV. CERT. AND CMR..exe (PID: 5876)
- INV. CERT. AND CMR..exe (PID: 1172)
- INV. CERT. AND CMR..exe (PID: 6432)
- INV. CERT. AND CMR..exe (PID: 7040)
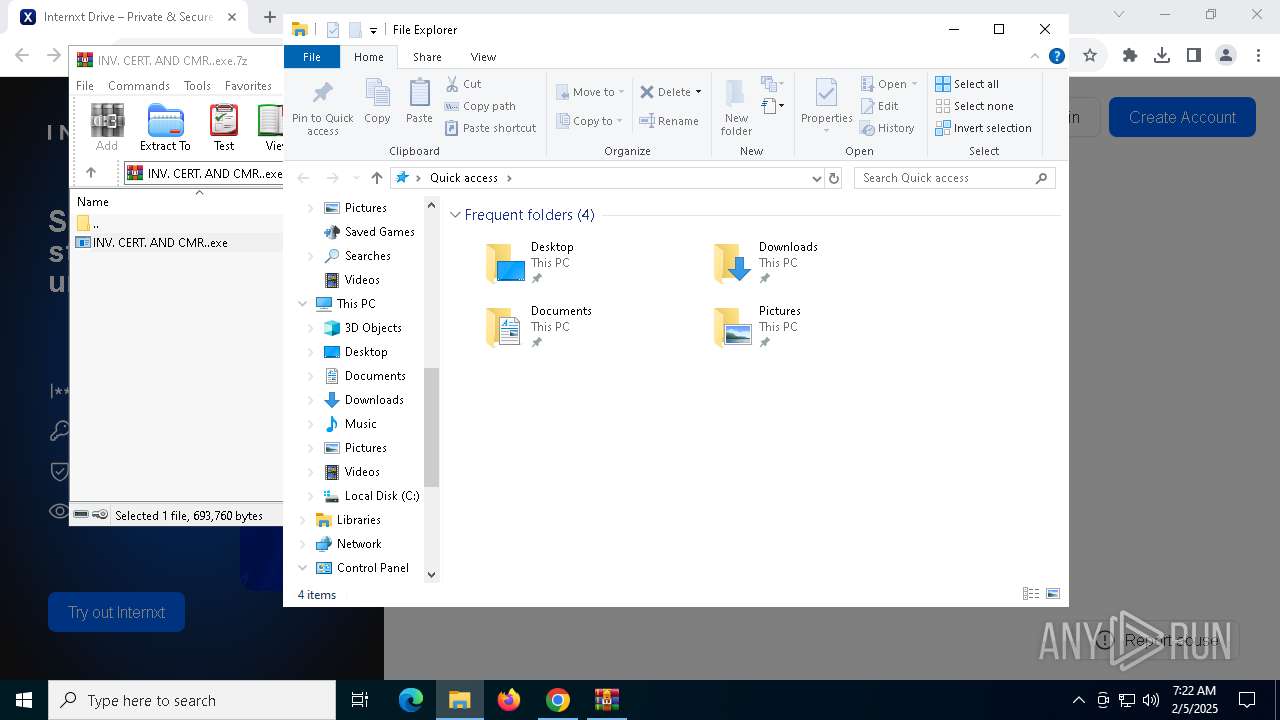
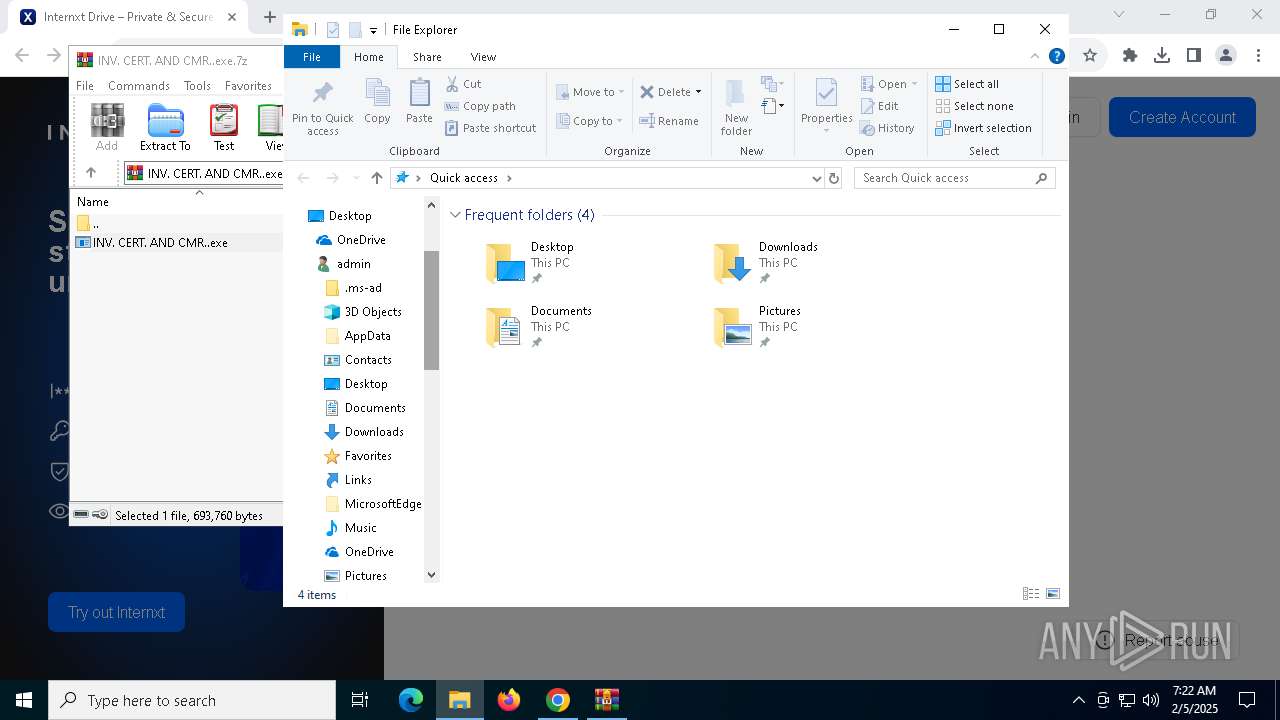
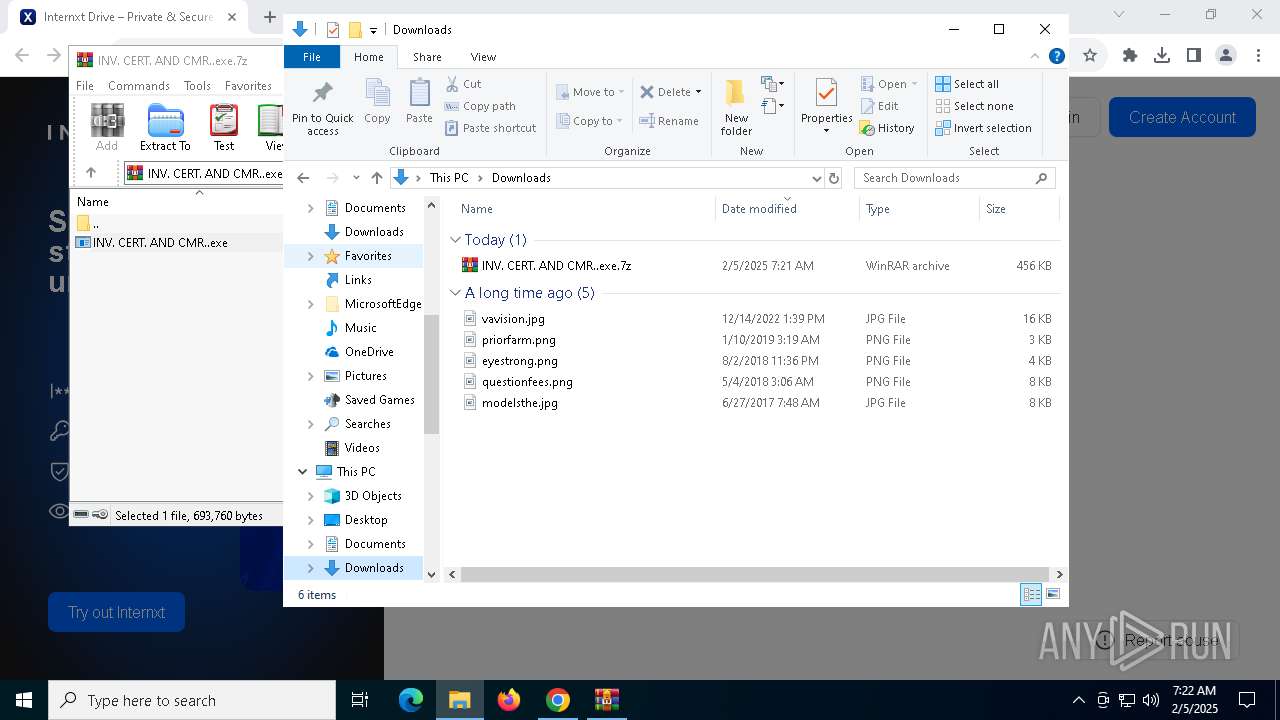
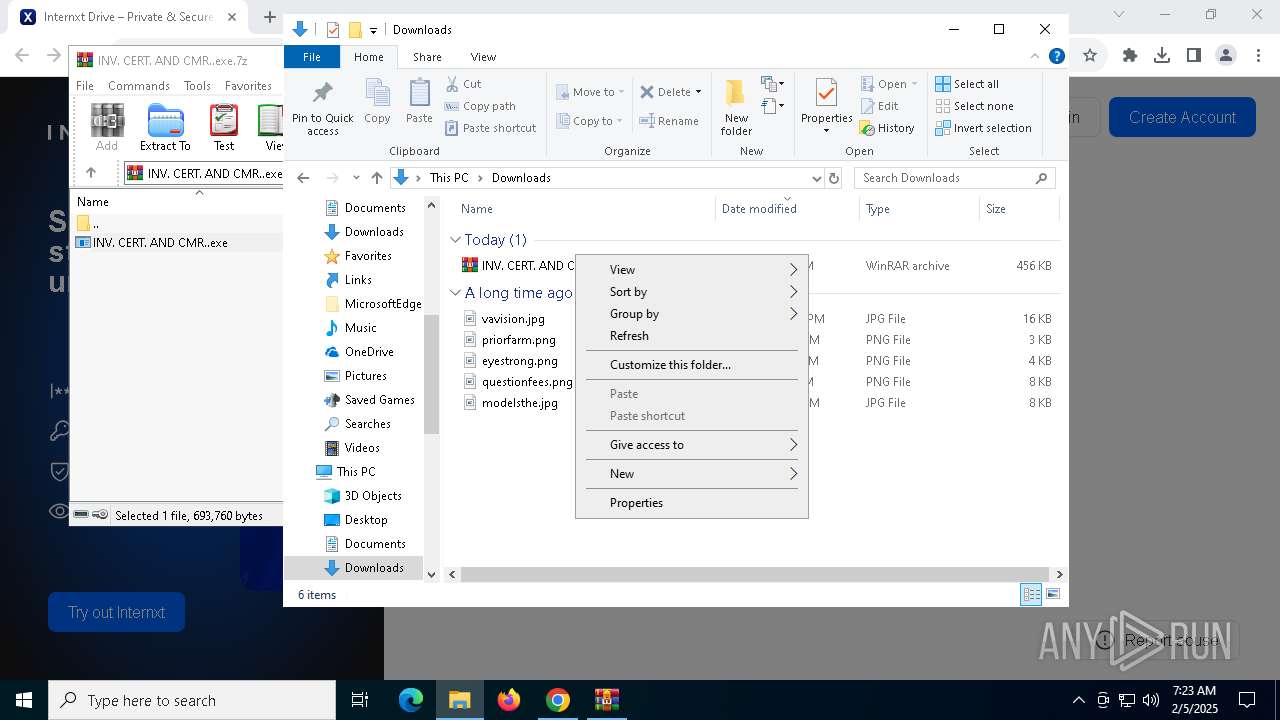
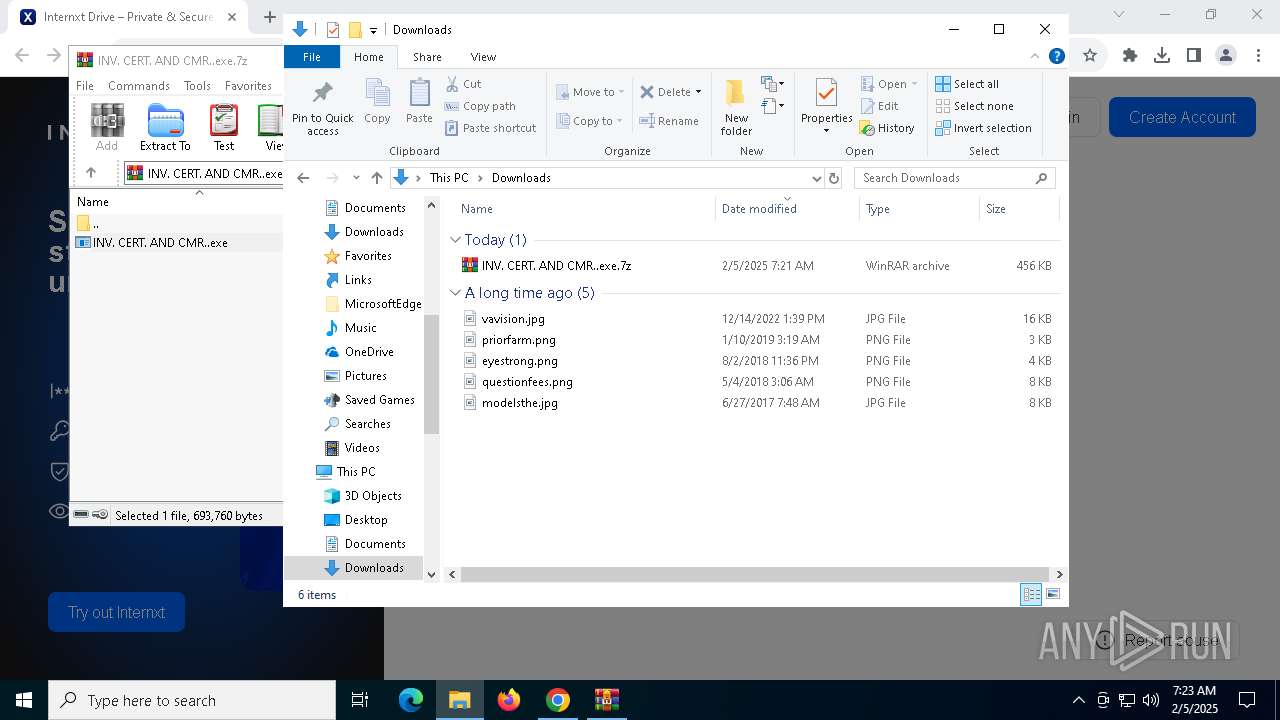
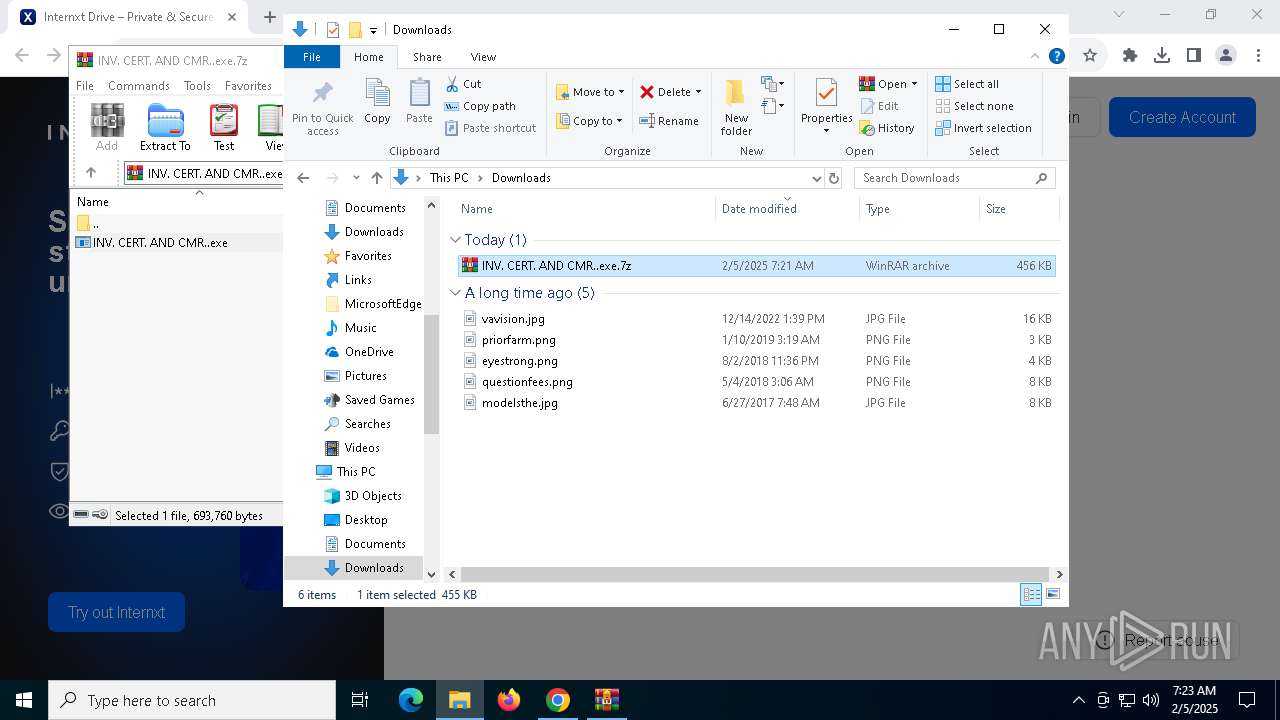
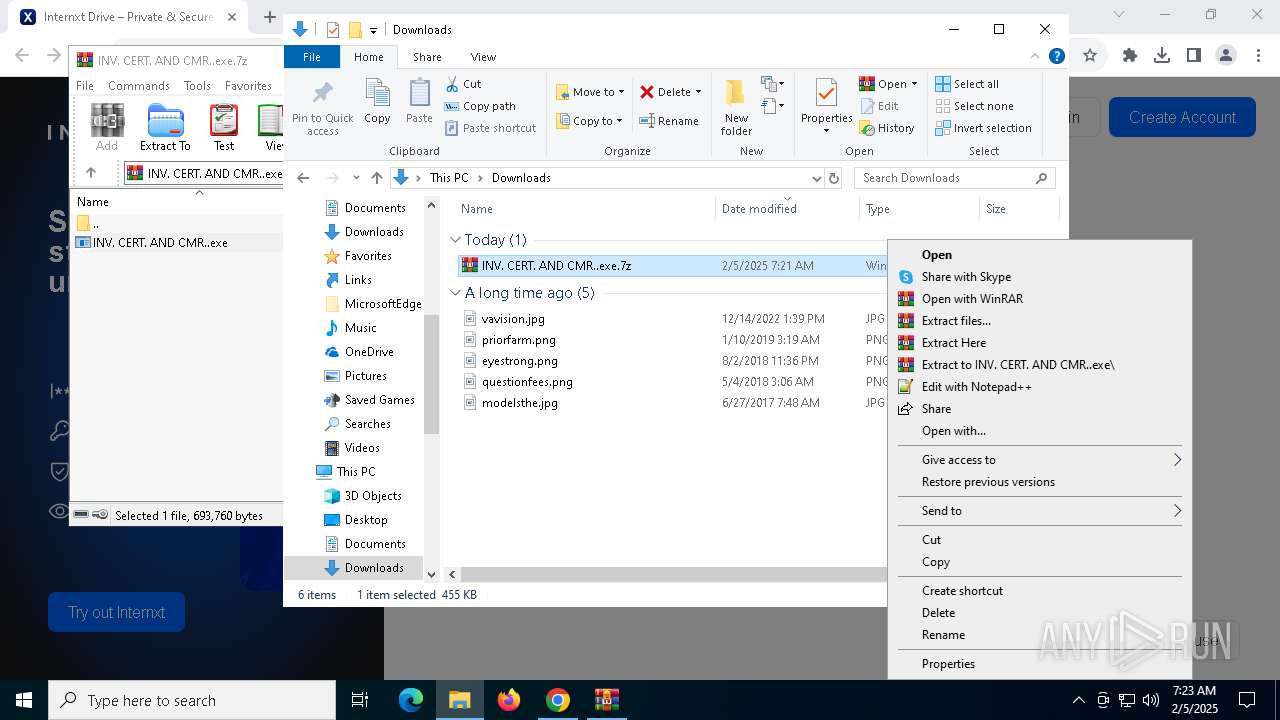
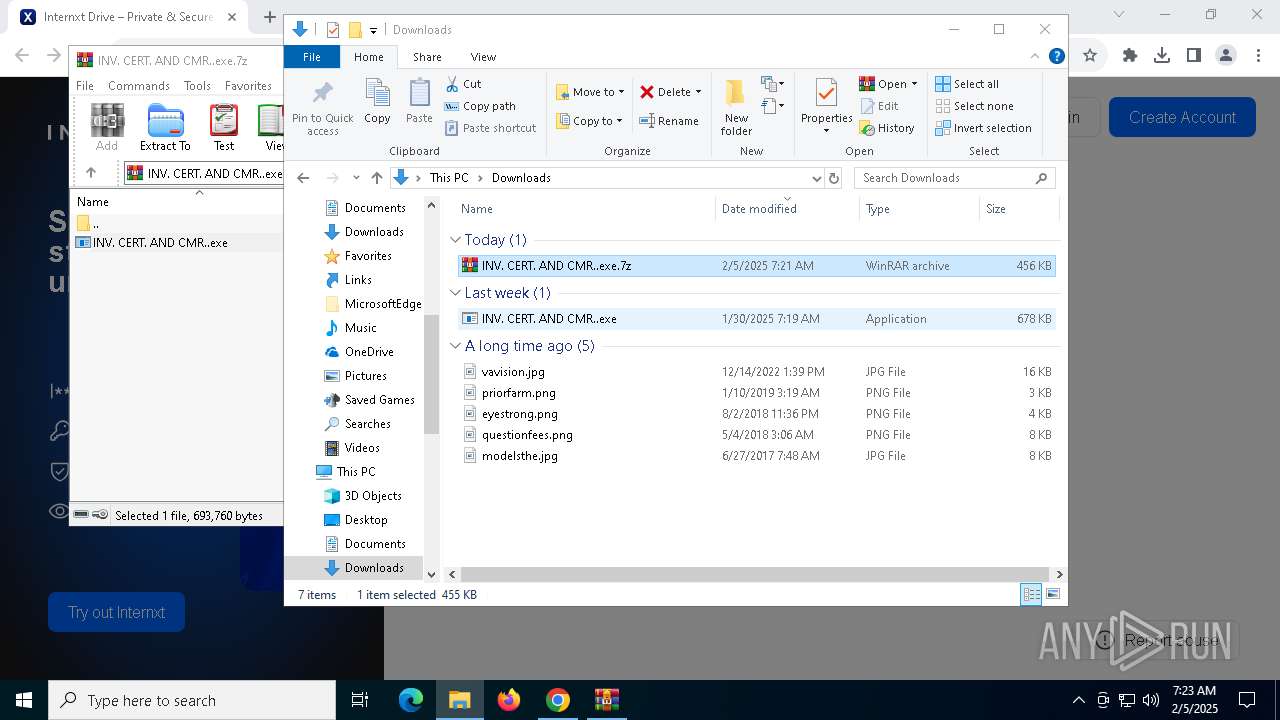
Manual execution by a user
- INV. CERT. AND CMR..exe (PID: 6432)
- INV. CERT. AND CMR..exe (PID: 7040)
- WinRAR.exe (PID: 6404)
Application launched itself
- chrome.exe (PID: 6076)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
205
Monitored processes
73
Malicious processes
4
Suspicious processes
10
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 188 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
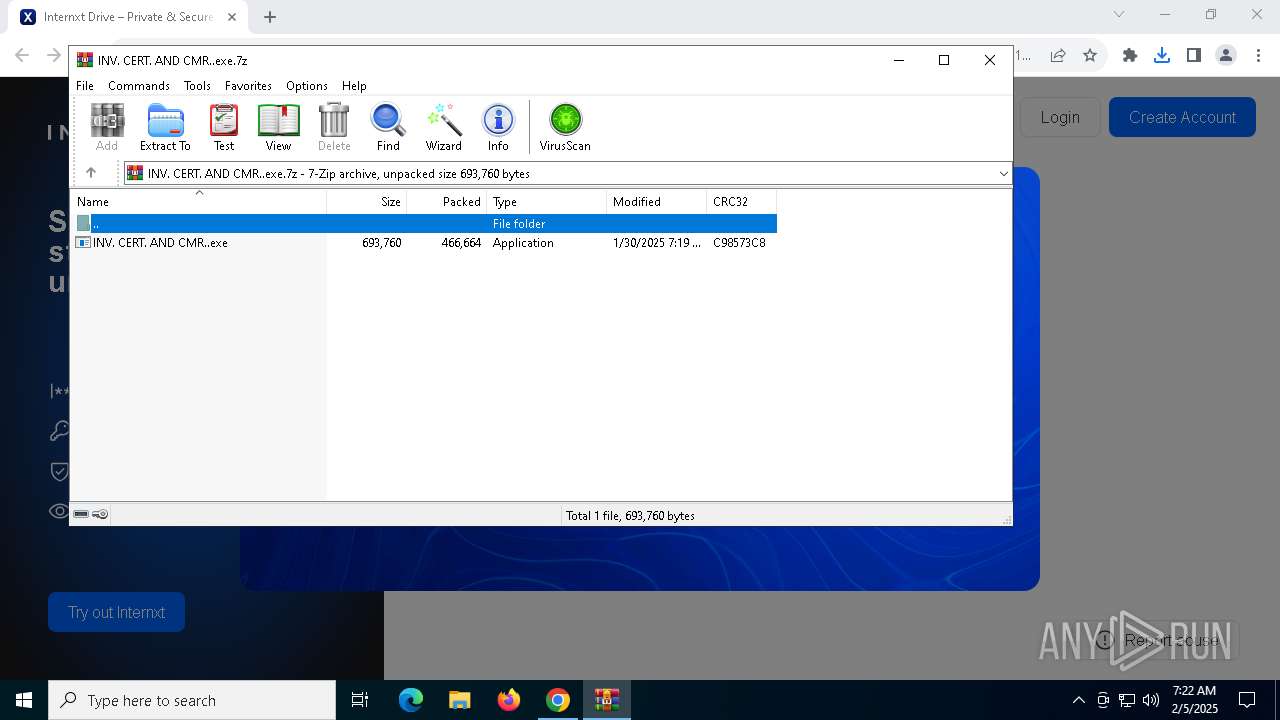
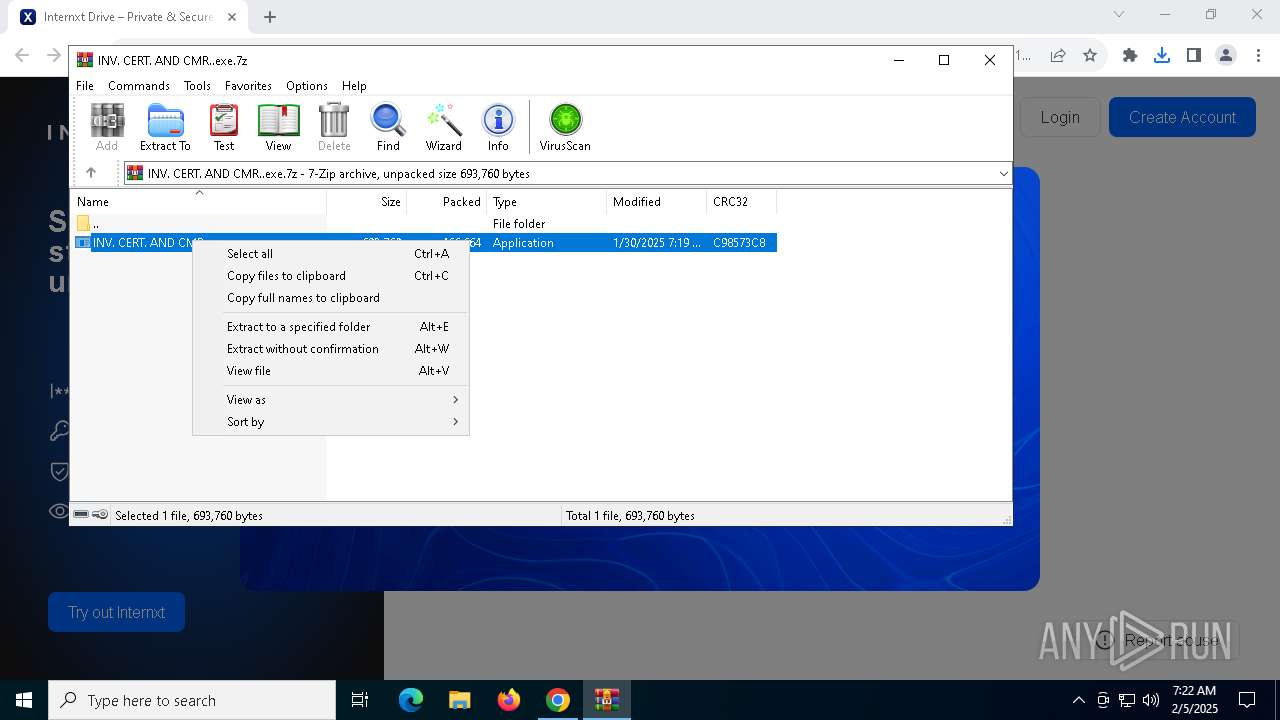
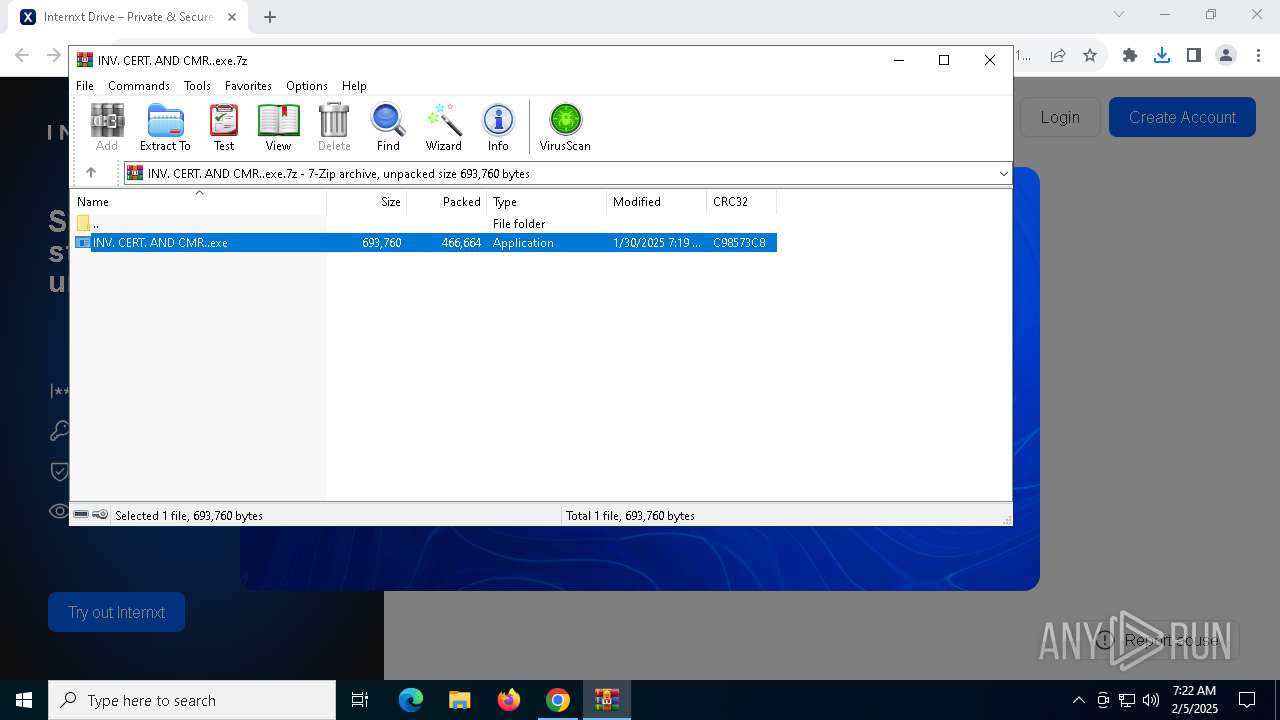
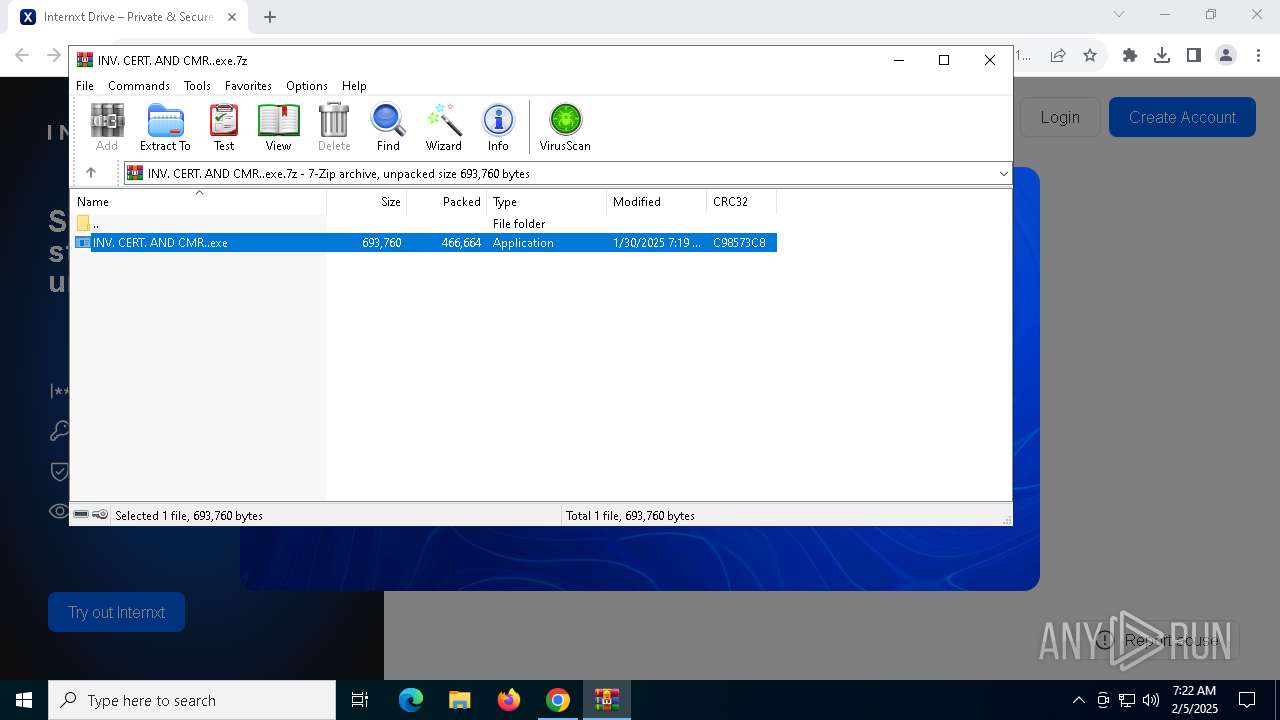
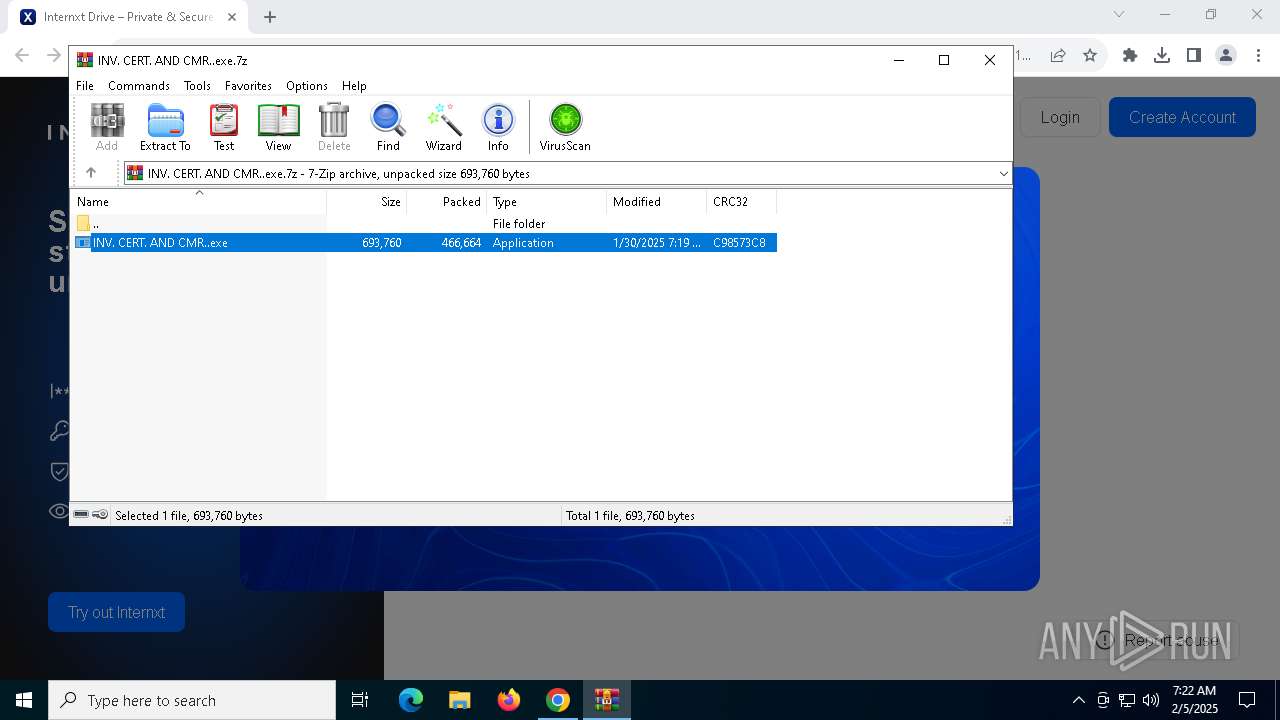
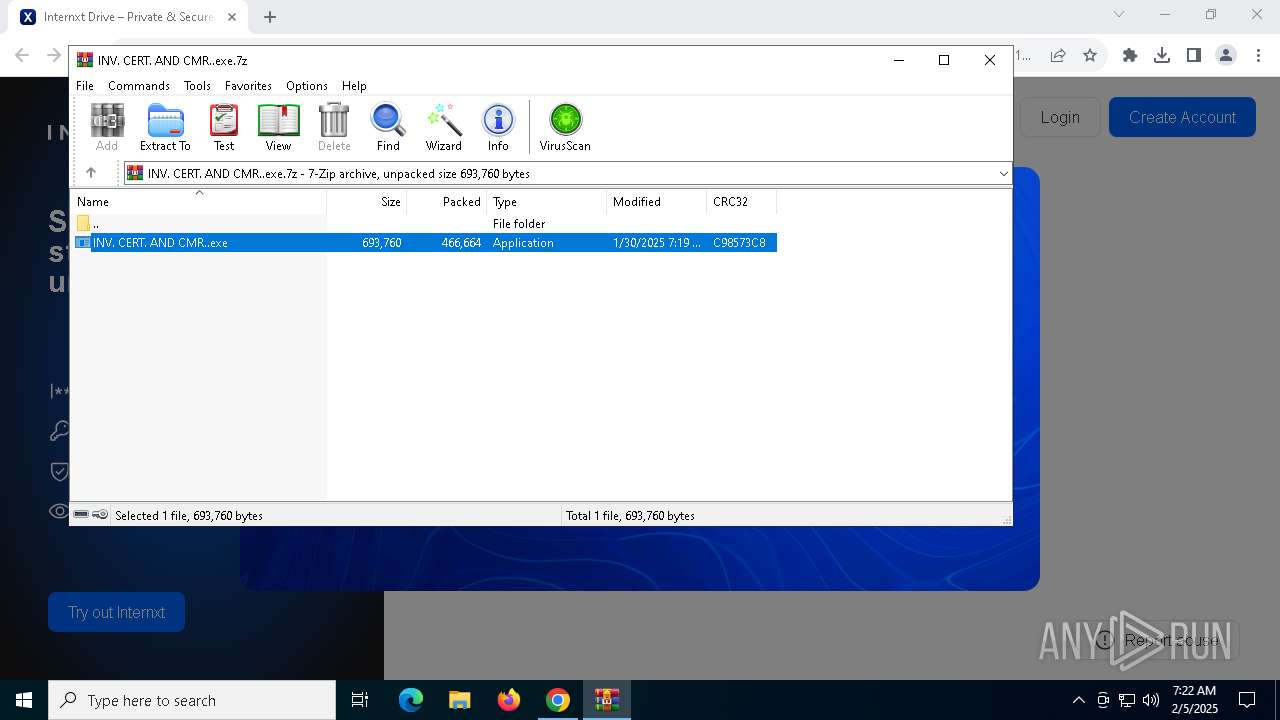
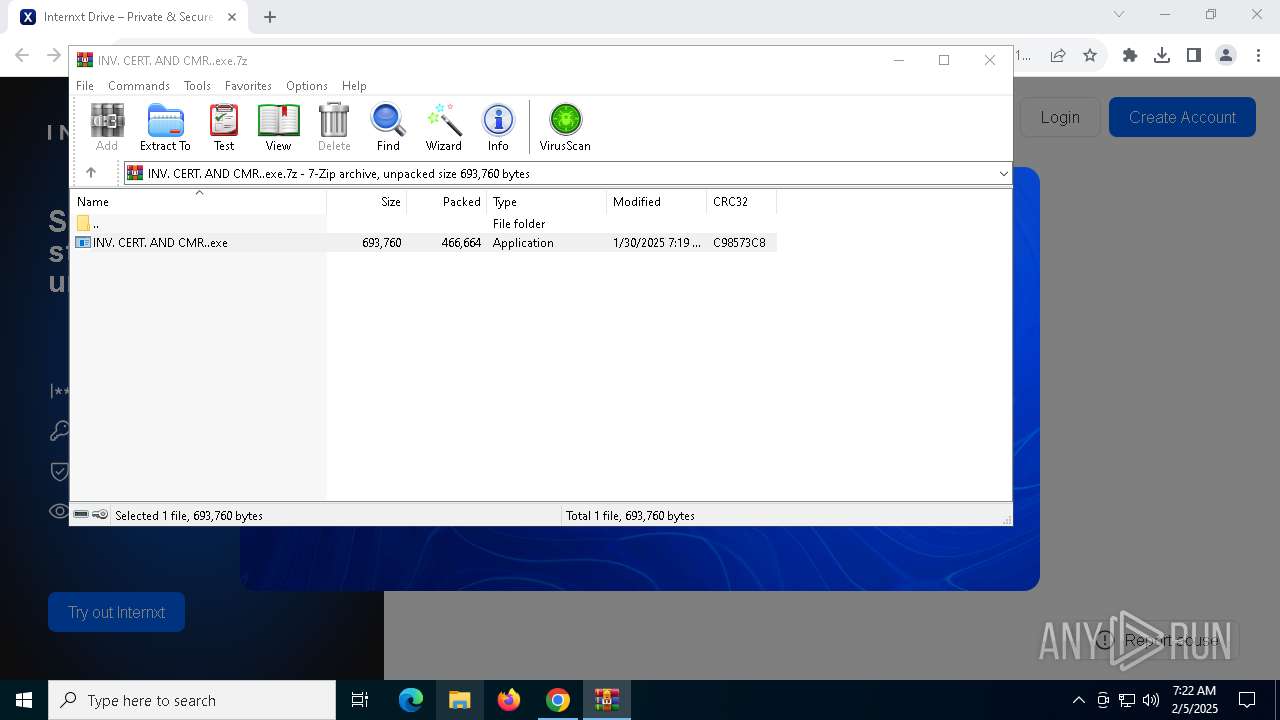
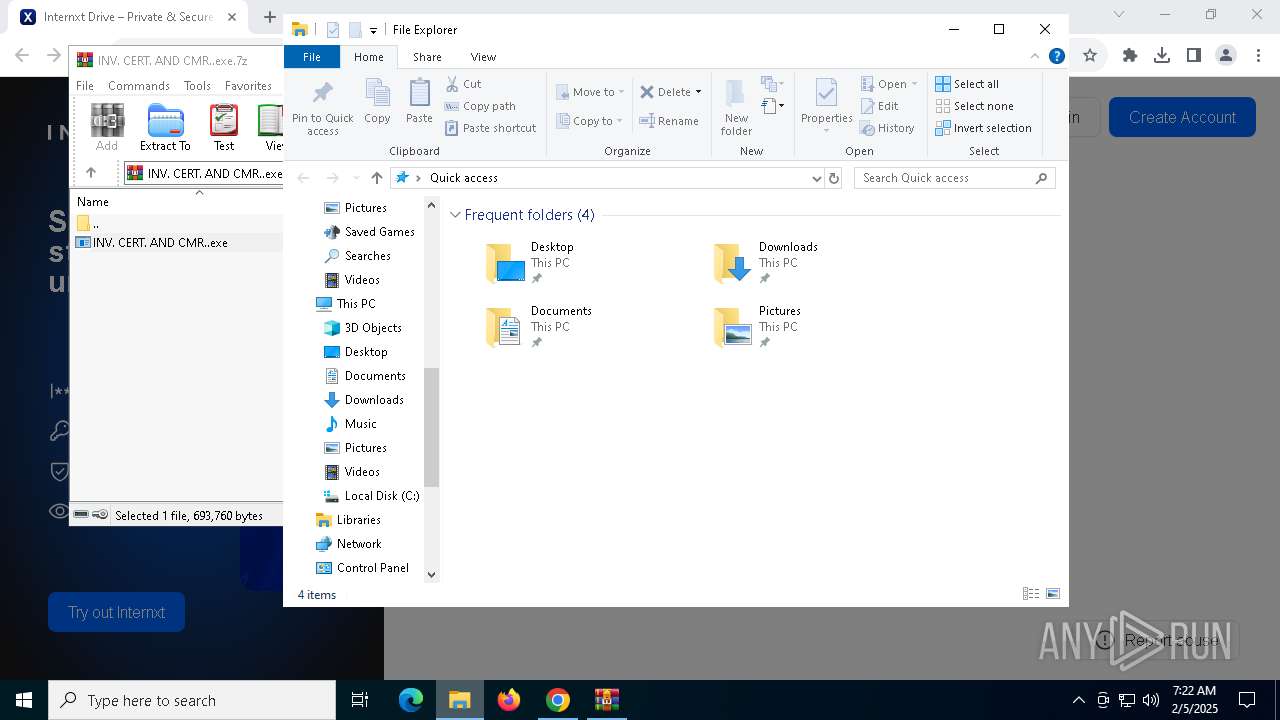
| 432 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1144.41950\INV. CERT. AND CMR..exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1144.41950\INV. CERT. AND CMR..exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: RDP Plugin Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 520 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1144.41950\INV. CERT. AND CMR..exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1144.41950\INV. CERT. AND CMR..exe | — | INV. CERT. AND CMR..exe | |||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: RDP Plugin Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
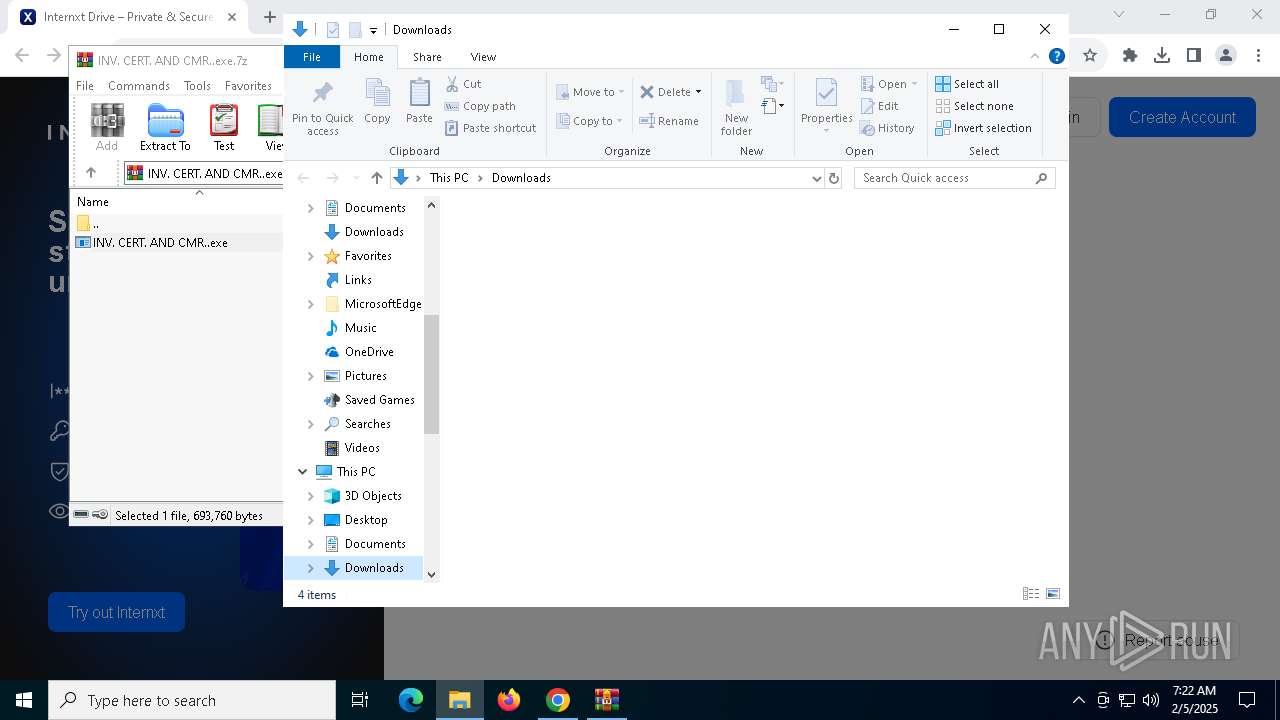
| 848 | "C:\Users\admin\Downloads\INV. CERT. AND CMR..exe" | C:\Users\admin\Downloads\INV. CERT. AND CMR..exe | — | INV. CERT. AND CMR..exe | |||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: RDP Plugin Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1144 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\INV. CERT. AND CMR..exe.7z" | C:\Program Files\WinRAR\WinRAR.exe | chrome.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 1172 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1144.46985\INV. CERT. AND CMR..exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1144.46985\INV. CERT. AND CMR..exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: RDP Plugin Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1200 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1144.43556\INV. CERT. AND CMR..exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1144.43556\INV. CERT. AND CMR..exe | — | INV. CERT. AND CMR..exe | |||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: RDP Plugin Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1228 | "C:\Windows\System32\schtasks.exe" /Create /TN "Updates\PCJPqggsIb" /XML "C:\Users\admin\AppData\Local\Temp\tmp17BC.tmp" | C:\Windows\SysWOW64\schtasks.exe | — | INV. CERT. AND CMR..exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1300 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1144.46985\INV. CERT. AND CMR..exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1144.46985\INV. CERT. AND CMR..exe | — | INV. CERT. AND CMR..exe | |||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: RDP Plugin Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
17 231
Read events
17 174
Write events
50
Delete events
7
Modification events
| (PID) Process: | (6076) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6076) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6076) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6076) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6076) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2084) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000267ABA939E77DB01 | |||
| (PID) Process: | (6076) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.7z\OpenWithProgids |
| Operation: | write | Name: | WinRAR |
Value: | |||
| (PID) Process: | (1144) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (1144) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (1144) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
Executable files
13
Suspicious files
133
Text files
35
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF137199.TMP | — | |
MD5:— | SHA256:— | |||
| 6076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF137199.TMP | — | |
MD5:— | SHA256:— | |||
| 6076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF1371a9.TMP | — | |
MD5:— | SHA256:— | |||
| 6076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF1371b8.TMP | — | |
MD5:— | SHA256:— | |||
| 6076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF137199.TMP | — | |
MD5:— | SHA256:— | |||
| 6076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF137199.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
98
DNS requests
98
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 95.101.78.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 1.01 Kb | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 973 b | whitelisted |
440 | svchost.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 973 b | whitelisted |
3364 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
3364 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
5064 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 313 b | whitelisted |
4628 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | — | — | whitelisted |
4628 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | binary | 349 b | whitelisted |
4628 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | compressed | 1.64 Kb | whitelisted |
4628 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | binary | 1.09 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.78.42:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
440 | svchost.exe | 95.101.78.42:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.19.217.218:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
440 | svchost.exe | 2.19.217.218:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 20.190.160.65:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
5064 | SearchApp.exe | 2.16.204.149:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
secure.internxt.com |
| unknown |
accounts.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6692 | chrome.exe | Misc activity | ET FILE_SHARING Commonly Abused File Sharing Domain (wasabisys .com) in DNS Lookup |
6692 | chrome.exe | Misc activity | ET FILE_SHARING Commonly Abused File Sharing Domain (wasabisys .com) in DNS Lookup |
6692 | chrome.exe | Misc activity | ET FILE_SHARING Commonly Abused File Sharing Domain (wasabisys .com) in TLS SNI |
6692 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to newrelic .com |
6692 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to newrelic .com |
6692 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Domain in DNS Lookup (drive .internxt .com) |
6692 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Domain in DNS Lookup (drive .internxt .com) |
6692 | chrome.exe | Misc activity | ET FILE_SHARING Commonly Abused File Sharing Domain (wasabisys .com) in DNS Lookup |
6692 | chrome.exe | Misc activity | ET FILE_SHARING Commonly Abused File Sharing Domain (wasabisys .com) in DNS Lookup |
6692 | chrome.exe | Misc activity | ET FILE_SHARING Observed File Sharing Domain (drive .internxt .com in TLS SNI) |