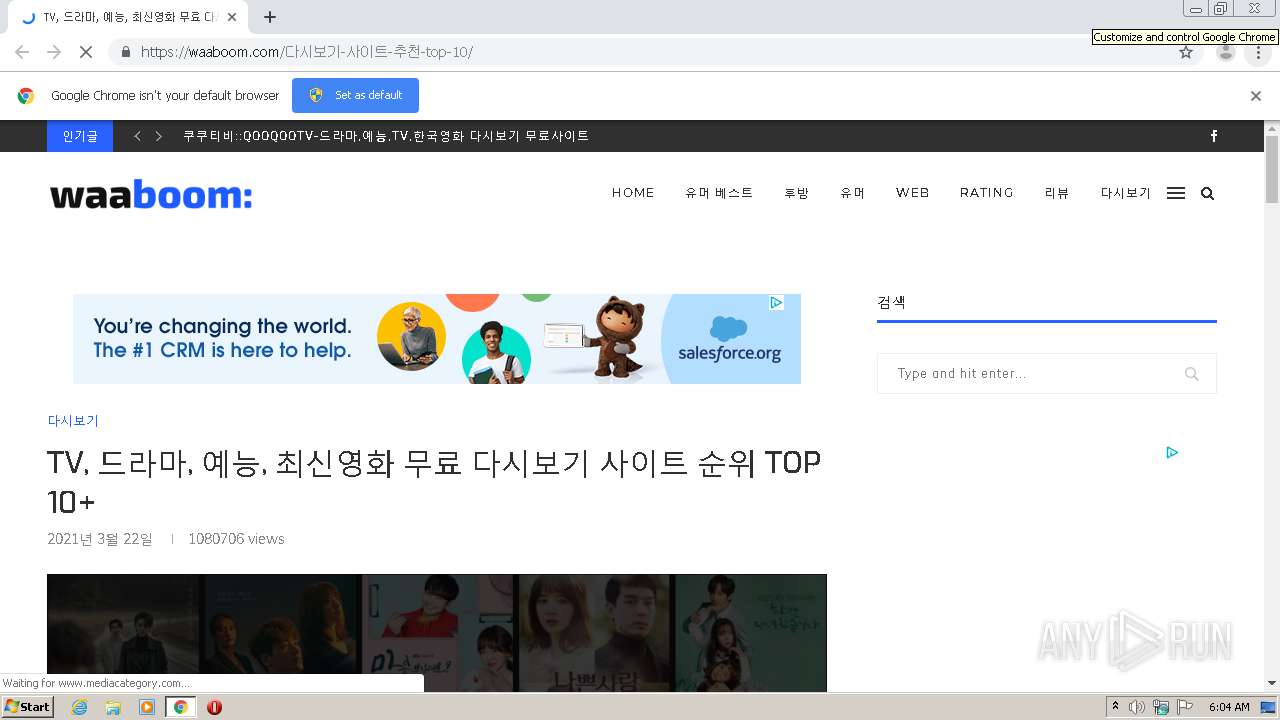
| URL: | https://waaboom.com/%EB%8B%A4%EC%8B%9C%EB%B3%B4%EA%B8%B0-%EC%82%AC%EC%9D%B4%ED%8A%B8-%EC%B6%94%EC%B2%9C-top-10/ |
| Full analysis: | https://app.any.run/tasks/a644f963-3fba-458a-90d8-27c863b08310 |
| Verdict: | Malicious activity |
| Analysis date: | March 23, 2021, 06:03:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 993C5CA350EE0845E63C3D7D4D6DAD83 |
| SHA1: | 74596DBB30FE146DAB84680A25DD4E9FC362909F |
| SHA256: | A57C96361EC8397F5B61ABFA791CA73ED10D3BF09EECE7C53B69C0795F83C3D8 |
| SSDEEP: | 3:N8VuuZIbi4ASmAdAyGhAkVIbQvAgBhpAdIFDt3nX50VIL:2Iu2bi4ASm7yUAcWQvAgDxZ0VO |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 2136)
Reads the hosts file
- chrome.exe (PID: 2820)
- chrome.exe (PID: 2136)
Reads settings of System Certificates
- chrome.exe (PID: 2820)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
68
Monitored processes
27
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,7842055567091953346,4318333465968341054,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10194128538511837567 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2548 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,7842055567091953346,4318333465968341054,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14274826663788212743 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4296 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1016,7842055567091953346,4318333465968341054,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=4192571501840225481 --mojo-platform-channel-handle=1008 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,7842055567091953346,4318333465968341054,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3556115628621303084 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3980 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,7842055567091953346,4318333465968341054,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=3806387589708557720 --mojo-platform-channel-handle=1900 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,7842055567091953346,4318333465968341054,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14776974689639454171 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3488 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,7842055567091953346,4318333465968341054,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7674059110315413546 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3808 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2136 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://waaboom.com/%EB%8B%A4%EC%8B%9C%EB%B3%B4%EA%B8%B0-%EC%82%AC%EC%9D%B4%ED%8A%B8-%EC%B6%94%EC%B2%9C-top-10/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,7842055567091953346,4318333465968341054,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8341312970568778191 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4276 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,7842055567091953346,4318333465968341054,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15144674816352506413 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2724 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 089
Read events
999
Write events
87
Delete events
3
Modification events
| (PID) Process: | (2304) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2136-13260953036273375 |
Value: 259 | |||
| (PID) Process: | (2136) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2136) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2136) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2136) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2136) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2136) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2136) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2136) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2136) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2136-13260953036273375 |
Value: 259 | |||
Executable files
0
Suspicious files
184
Text files
105
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2136 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-605984CC-858.pma | — | |
MD5:— | SHA256:— | |||
| 2136 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2136 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2136 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFcfc57.TMP | — | |
MD5:— | SHA256:— | |||
| 2136 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\99f45e29-44dc-4f65-921e-1a04d07606c2.tmp | — | |
MD5:— | SHA256:— | |||
| 2136 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2136 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFcfc57.TMP | text | |
MD5:— | SHA256:— | |||
| 2136 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2136 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2136 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFcfff1.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
208
DNS requests
116
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2820 | chrome.exe | GET | 200 | 205.185.216.42:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.2 Kb | whitelisted |
2820 | chrome.exe | GET | 304 | 205.185.216.42:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2820 | chrome.exe | 172.217.20.2:443 | pagead2.googlesyndication.com | Google Inc. | US | unknown |
2820 | chrome.exe | 172.67.208.150:443 | waaboom.com | — | US | malicious |
2820 | chrome.exe | 142.250.185.205:443 | accounts.google.com | Google Inc. | US | suspicious |
2820 | chrome.exe | 172.217.19.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2820 | chrome.exe | 172.64.134.12:443 | rawcdn.githack.com | Cloudflare Inc | US | unknown |
2820 | chrome.exe | 211.249.221.246:443 | developers.kakao.com | DREAMLINE CO. | KR | suspicious |
2820 | chrome.exe | 104.75.88.18:443 | ads-partners.coupang.com | Akamai Technologies, Inc. | NL | unknown |
2820 | chrome.exe | 172.217.18.67:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2820 | chrome.exe | 49.254.250.66:443 | ad.aceplanet.co.kr | Korea Telecom | KR | unknown |
2820 | chrome.exe | 65.9.58.55:443 | partners.coupangcdn.com | AT&T Services, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
waaboom.com |
| malicious |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
developers.kakao.com |
| suspicious |
rawcdn.githack.com |
| whitelisted |
ads-partners.coupang.com |
| unknown |
fonts.gstatic.com |
| whitelisted |
ad.aceplanet.co.kr |
| unknown |
partners.coupangcdn.com |
| suspicious |
secure.gravatar.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1040 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1040 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1040 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1040 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |