| URL: | http://the.bestoffersonline.stream/?utm_term=6760043211252564762&clickverify=1&utm_content=e7cacbe0c0dbc9c1a2a391959297a49c8a8bb888becabcc8b2b381858287b48dbbb988babebf8cbcb38380b086878485a89bd9e9eef3f9bdd1fcfde1e3e3f1e7c6cba1878dc1ecdfd6e3d2d5e6e7e491888e9df9fecefcccc6c7c0f1cfc7c4f5cacba6 |
| Full analysis: | https://app.any.run/tasks/b863d04e-0692-4616-b060-3fe2ec6b0505 |
| Verdict: | Malicious activity |
| Analysis date: | November 17, 2019, 03:15:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 7F235033063327CFDEF63B887D606B9E |
| SHA1: | 3980283215866259571829553F57048F2A8A120E |
| SHA256: | A55C434E20ED956729E5A792035BB8E54E812DEA518B79CDDE2E3EECC2992B49 |
| SSDEEP: | 6:CKNaJhI4P0nKUIqQwtOS2VUfSiFm6WkdscA2kaA9/xMT3AtriQRMZ:aI4P0nKUIIV5k9k+caRp+yOQKZ |
MALICIOUS
No malicious indicators.SUSPICIOUS
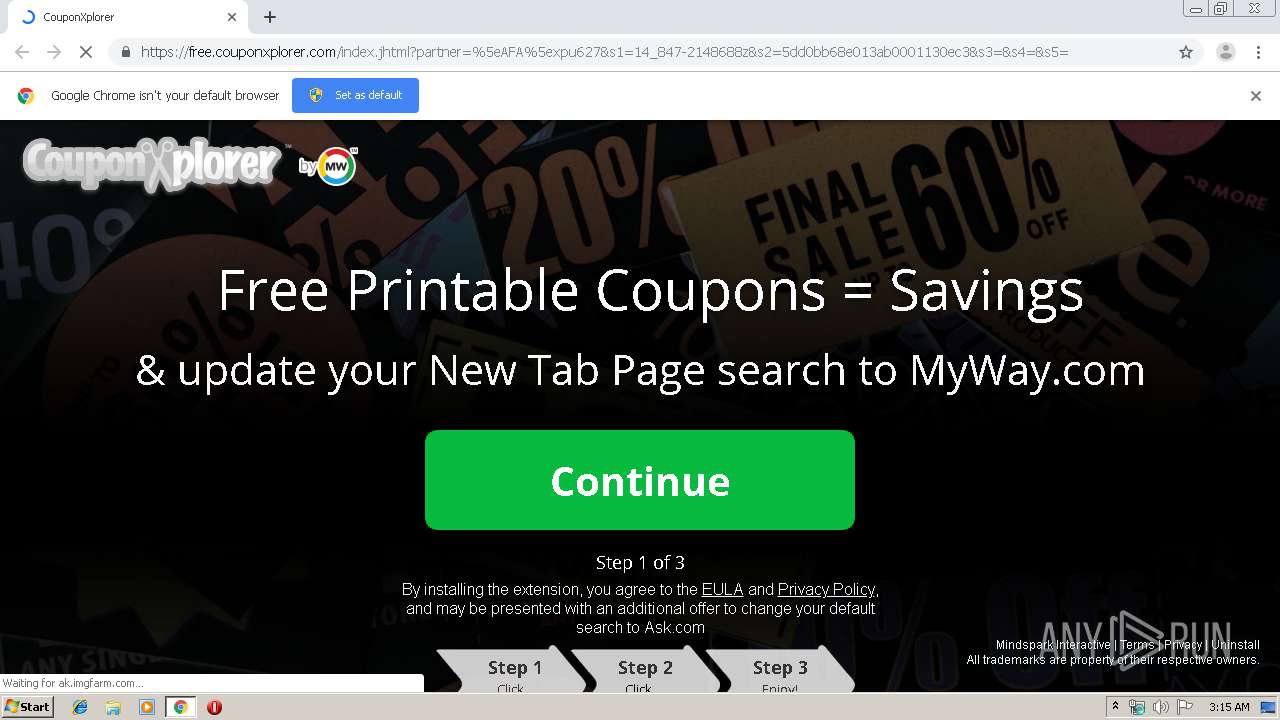
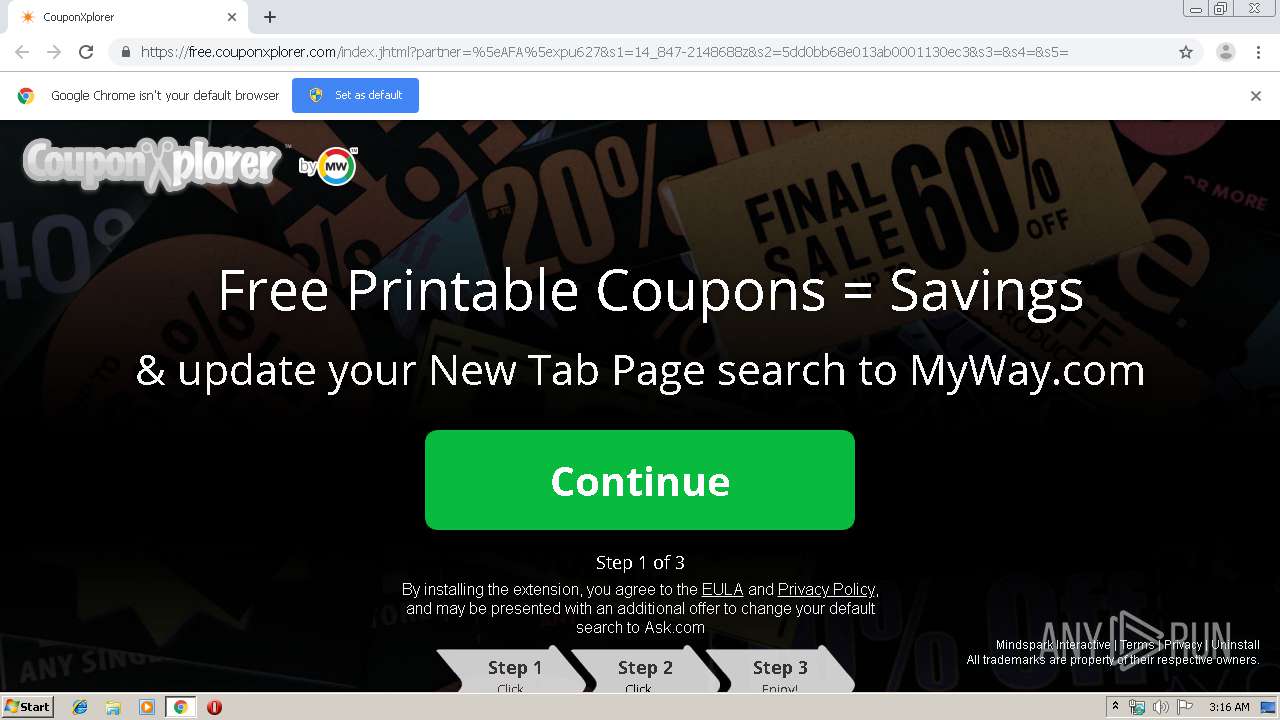
Modifies files in Chrome extension folder
- chrome.exe (PID: 2572)
INFO
Application launched itself
- chrome.exe (PID: 2572)
Reads the hosts file
- chrome.exe (PID: 2572)
- chrome.exe (PID: 4016)
Reads settings of System Certificates
- chrome.exe (PID: 4016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
65
Monitored processes
30
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,7147081294062879578,14128116837692931282,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17838661179519497479 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2200 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,7147081294062879578,14128116837692931282,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12775944091715095981 --mojo-platform-channel-handle=4596 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,7147081294062879578,14128116837692931282,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10240729148874649406 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3144 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,7147081294062879578,14128116837692931282,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13206824218731471435 --mojo-platform-channel-handle=4648 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,7147081294062879578,14128116837692931282,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8288017391074165248 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3604 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,7147081294062879578,14128116837692931282,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5525934047777997511 --mojo-platform-channel-handle=5080 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,7147081294062879578,14128116837692931282,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14338115067830616871 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3100 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,7147081294062879578,14128116837692931282,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15156665584129069292 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2508 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,7147081294062879578,14128116837692931282,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7008742299351054156 --mojo-platform-channel-handle=4412 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,7147081294062879578,14128116837692931282,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10920597585843614746 --mojo-platform-channel-handle=4616 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
625
Read events
526
Write events
94
Delete events
5
Modification events
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2452) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2572-13218434148698375 |
Value: 259 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2572) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
27
Text files
239
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\163f3fb4-3144-442f-ab5b-05dd607bee19.tmp | — | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF39a66c.TMP | text | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RF39a737.TMP | text | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF39a69b.TMP | text | |
MD5:— | SHA256:— | |||
| 2572 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
32
DNS requests
27
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4016 | chrome.exe | GET | 302 | 35.244.218.203:80 | http://free.couponxplorer.com/index.jhtml?partner=^AFA^xpu627&s1=14_847-2148688z&s2=5dd0bb68e013ab0001130ec3&s3=&s4=&s5= | US | — | — | whitelisted |
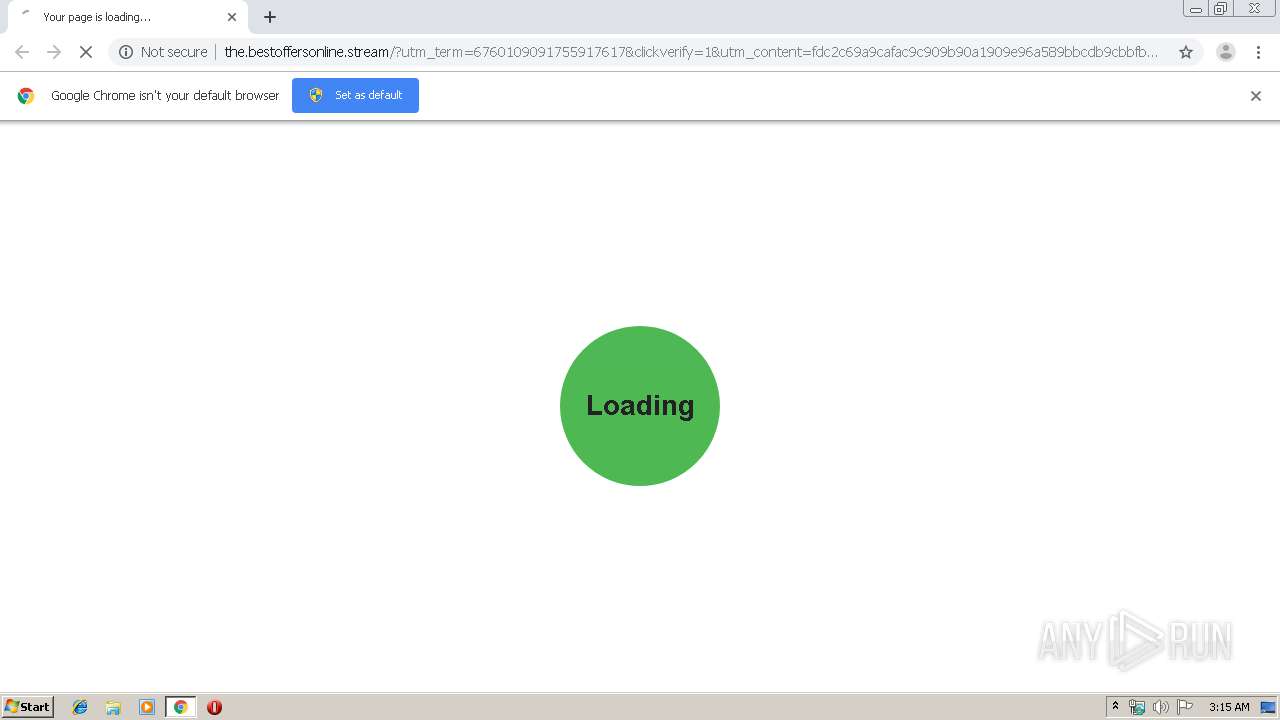
4016 | chrome.exe | GET | 200 | 99.198.108.194:80 | http://the.bestoffersonline.stream/?utm_term=6760109091755917617&clickverify=1&utm_content=fdc2c69a9cafac9c909b90a1909e96a589bbcdb9cbbfbc8c828782b1838f83b5ba8bb9b88e8fbd8d8283ece0e8e3f7e6fbebfdb4eeedf5f0f3e1e991a797d3fa858c848ccea6828ecce3d2d5e6d5d0e5fafb9e98928c99fdf2c2f0c0c4cfc4f5fdf9f8c9cecfb6 | US | html | 2.43 Kb | malicious |
4016 | chrome.exe | GET | 200 | 99.198.108.194:80 | http://the.bestoffersonline.stream/?utm_term=6760043211252564762&clickverify=1&utm_content=e7cacbe0c0dbc9c1a2a391959297a49c8a8bb888becabcc8b2b381858287b48dbbb988babebf8cbcb38380b086878485a89bd9e9eef3f9bdd1fcfde1e3e3f1e7c6cba1878dc1ecdfd6e3d2d5e6e7e491888e9df9fecefcccc6c7c0f1cfc7c4f5cacba6 | US | html | 1.25 Kb | malicious |
4016 | chrome.exe | GET | 302 | 172.217.22.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 509 b | whitelisted |
4016 | chrome.exe | GET | 200 | 103.2.116.76:80 | http://r1---sn-f5p5-hxae.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=85.203.20.5&mm=28&mn=sn-f5p5-hxae&ms=nvh&mt=1573959942&mv=u&mvi=0&pl=24&shardbypass=yes | AU | crx | 293 Kb | whitelisted |
4016 | chrome.exe | GET | 302 | 172.217.22.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
4016 | chrome.exe | GET | 200 | 103.2.116.78:80 | http://r3---sn-f5p5-hxae.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=85.203.20.5&mm=28&mn=sn-f5p5-hxae&ms=nvh&mt=1573959942&mv=u&mvi=2&pl=24&shardbypass=yes | AU | crx | 862 Kb | whitelisted |
4016 | chrome.exe | GET | 302 | 99.198.108.194:80 | http://the.bestoffersonline.stream/proc.php?5faa040b5f885f4dc4614e7b948fb3d4b4a487a6 | US | compressed | 2.43 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4016 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
4016 | chrome.exe | 216.58.208.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
4016 | chrome.exe | 212.32.252.92:443 | track.wbamedia.com | LeaseWeb Netherlands B.V. | NL | unknown |
4016 | chrome.exe | 99.198.108.194:80 | the.bestoffersonline.stream | SingleHop, Inc. | US | suspicious |
4016 | chrome.exe | 35.244.218.203:443 | free.couponxplorer.com | — | US | whitelisted |
4016 | chrome.exe | 35.244.218.203:80 | free.couponxplorer.com | — | US | whitelisted |
4016 | chrome.exe | 172.217.22.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
4016 | chrome.exe | 104.111.214.175:443 | ak.staticimgfarm.com | Akamai International B.V. | NL | whitelisted |
4016 | chrome.exe | 172.217.16.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
4016 | chrome.exe | 104.109.89.65:443 | akz.imgfarm.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
the.bestoffersonline.stream |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
track.wbamedia.com |
| unknown |
free.couponxplorer.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
ak.staticimgfarm.com |
| whitelisted |
ak.imgfarm.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
akz.imgfarm.com |
| whitelisted |