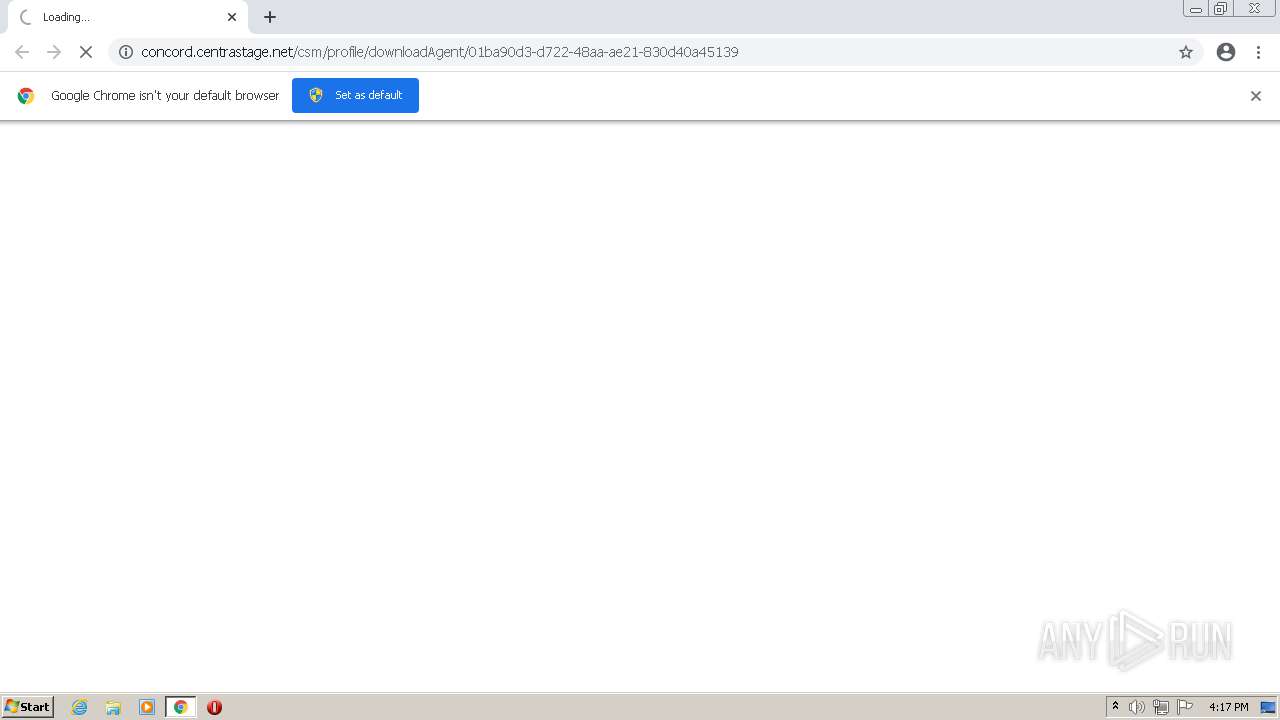
| URL: | https://concord.centrastage.net/csm/profile/downloadAgent/01ba90d3-d722-48aa-ae21-830d40a45139 |
| Full analysis: | https://app.any.run/tasks/940276ed-307d-432d-a54b-904b65701c06 |
| Verdict: | Malicious activity |
| Analysis date: | May 19, 2021, 15:17:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | E8B51D4013120464295B0FB7BBB984D5 |
| SHA1: | 00B7FAD36627D56CE929EB55E8C9F59B8934B99A |
| SHA256: | A554DF8B82594879273E86DE6CE14AA10AACEB9E6D0A3E86ACDCE93F220C7B53 |
| SSDEEP: | 3:N8XKeUf/tIKVXoaFIC/bIWLXV7RdyzE6cn:25e/hV4aFjHZ2m |
MALICIOUS
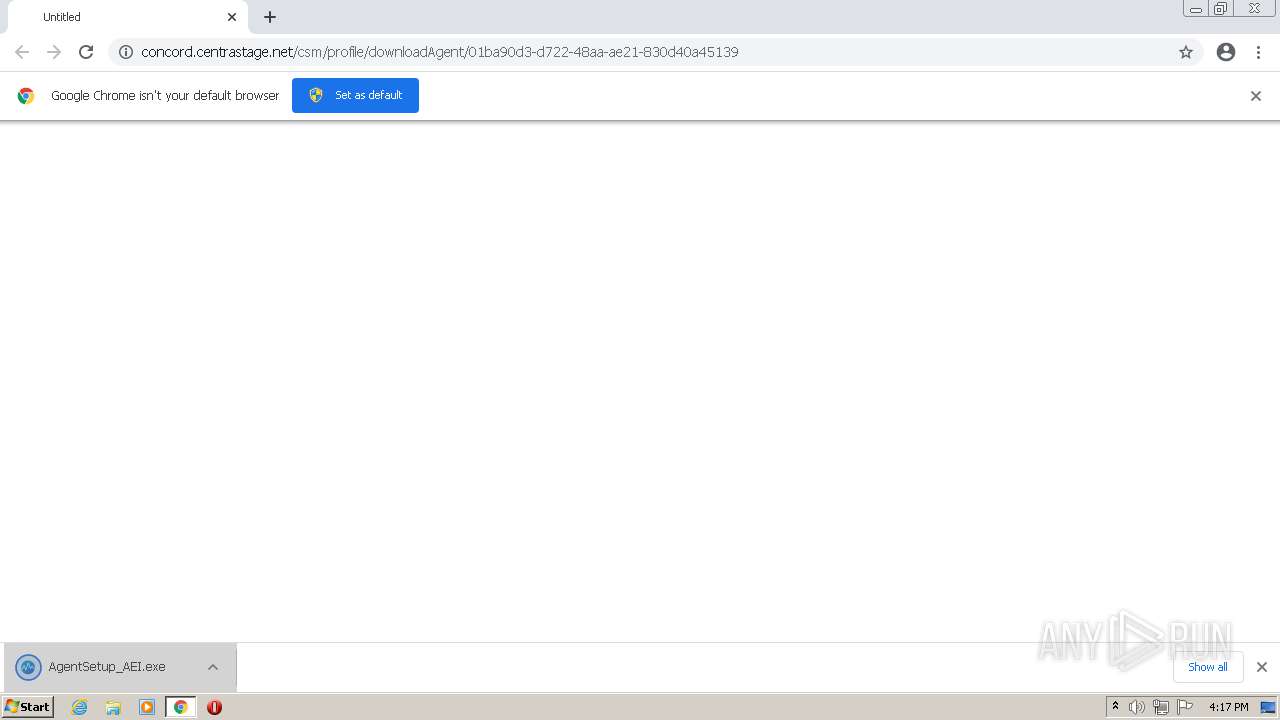
Drops executable file immediately after starts
- AgentSetup_AEI.exe (PID: 2940)
- chrome.exe (PID: 3172)
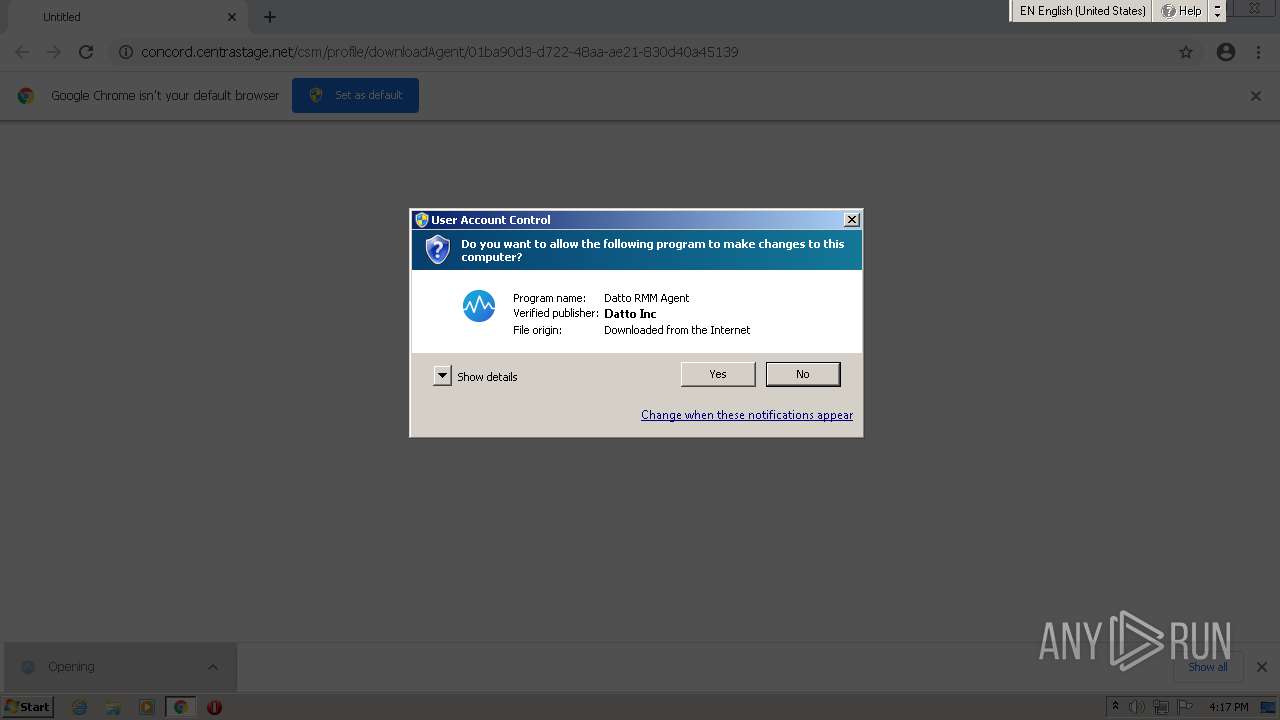
Application was dropped or rewritten from another process
- AgentSetup_AEI.exe (PID: 1872)
- AgentSetup_AEI.exe (PID: 2940)
- CagService.exe (PID: 3036)
- AEMAgent.exe (PID: 3720)
- AEMAgent.exe (PID: 3668)
- aria2c.exe (PID: 3980)
- Gui.exe (PID: 3120)
- RMM.WebRemote.exe (PID: 3484)
Loads dropped or rewritten executable
- AgentSetup_AEI.exe (PID: 2940)
- CagService.exe (PID: 3036)
- Gui.exe (PID: 3120)
- regsvr32.exe (PID: 304)
- AEMAgent.exe (PID: 3720)
- AEMAgent.exe (PID: 3668)
- RMM.WebRemote.exe (PID: 3484)
Changes the autorun value in the registry
- AgentSetup_AEI.exe (PID: 2940)
Registers / Runs the DLL via REGSVR32.EXE
- CagService.exe (PID: 3036)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3728)
- AgentSetup_AEI.exe (PID: 2940)
- CagService.exe (PID: 3036)
- AEMAgent.exe (PID: 3668)
- RMM.WebRemote.exe (PID: 3484)
- chrome.exe (PID: 3172)
Reads the computer name
- AgentSetup_AEI.exe (PID: 2940)
- CagService.exe (PID: 3036)
- AEMAgent.exe (PID: 3668)
- aria2c.exe (PID: 3980)
- Gui.exe (PID: 3120)
- RMM.WebRemote.exe (PID: 3484)
Creates a directory in Program Files
- AgentSetup_AEI.exe (PID: 2940)
- CagService.exe (PID: 3036)
Drops a file with too old compile date
- AgentSetup_AEI.exe (PID: 2940)
- CagService.exe (PID: 3036)
- AEMAgent.exe (PID: 3668)
- RMM.WebRemote.exe (PID: 3484)
Creates files in the program directory
- AgentSetup_AEI.exe (PID: 2940)
- AEMAgent.exe (PID: 3720)
- aria2c.exe (PID: 3980)
- AEMAgent.exe (PID: 3668)
- CagService.exe (PID: 3036)
- RMM.WebRemote.exe (PID: 3484)
Checks supported languages
- AgentSetup_AEI.exe (PID: 2940)
- CagService.exe (PID: 3036)
- Gui.exe (PID: 3120)
- AEMAgent.exe (PID: 3720)
- AEMAgent.exe (PID: 3668)
- aria2c.exe (PID: 3980)
- RMM.WebRemote.exe (PID: 3484)
- cmd.exe (PID: 2936)
Reads Environment values
- AgentSetup_AEI.exe (PID: 2940)
- CagService.exe (PID: 3036)
- netsh.exe (PID: 2404)
- netsh.exe (PID: 3960)
- netsh.exe (PID: 2408)
- netsh.exe (PID: 3720)
- netsh.exe (PID: 4072)
- netsh.exe (PID: 3696)
- netsh.exe (PID: 908)
- netsh.exe (PID: 2548)
- netsh.exe (PID: 3044)
- netsh.exe (PID: 756)
- netsh.exe (PID: 2036)
- netsh.exe (PID: 908)
- netsh.exe (PID: 2264)
- netsh.exe (PID: 1208)
- netsh.exe (PID: 1456)
- netsh.exe (PID: 2404)
- netsh.exe (PID: 2444)
- netsh.exe (PID: 4036)
Drops a file that was compiled in debug mode
- AgentSetup_AEI.exe (PID: 2940)
- CagService.exe (PID: 3036)
- AEMAgent.exe (PID: 3668)
- RMM.WebRemote.exe (PID: 3484)
- chrome.exe (PID: 3172)
Creates a software uninstall entry
- AgentSetup_AEI.exe (PID: 2940)
- CagService.exe (PID: 3036)
Executed as Windows Service
- CagService.exe (PID: 3036)
Removes files from Windows directory
- CagService.exe (PID: 3036)
Changes default file association
- CagService.exe (PID: 3036)
Creates files in the Windows directory
- CagService.exe (PID: 3036)
- AEMAgent.exe (PID: 3668)
- RMM.WebRemote.exe (PID: 3484)
Creates or modifies windows services
- CagService.exe (PID: 3036)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 304)
Drops a file with a compile date too recent
- CagService.exe (PID: 3036)
Uses NETSH.EXE for network configuration
- AEMAgent.exe (PID: 3668)
- RMM.WebRemote.exe (PID: 3484)
- CagService.exe (PID: 3036)
Searches for installed software
- CagService.exe (PID: 3036)
Uses TASKLIST.EXE to query information about running processes
- cmd.exe (PID: 2936)
Starts CMD.EXE for commands execution
- CagService.exe (PID: 3036)
Starts SC.EXE for service management
- cmd.exe (PID: 2936)
INFO
Checks supported languages
- chrome.exe (PID: 2284)
- chrome.exe (PID: 1556)
- chrome.exe (PID: 2632)
- chrome.exe (PID: 3728)
- chrome.exe (PID: 2568)
- chrome.exe (PID: 3272)
- chrome.exe (PID: 3204)
- chrome.exe (PID: 1940)
- chrome.exe (PID: 1896)
- chrome.exe (PID: 1840)
- chrome.exe (PID: 1692)
- chrome.exe (PID: 2992)
- chrome.exe (PID: 1796)
- chrome.exe (PID: 2644)
- regsvr32.exe (PID: 304)
- chrome.exe (PID: 3440)
- chrome.exe (PID: 1588)
- chrome.exe (PID: 1284)
- netsh.exe (PID: 3960)
- netsh.exe (PID: 2404)
- netsh.exe (PID: 2408)
- netsh.exe (PID: 3720)
- netsh.exe (PID: 3696)
- netsh.exe (PID: 908)
- netsh.exe (PID: 2548)
- netsh.exe (PID: 4072)
- netsh.exe (PID: 756)
- netsh.exe (PID: 2036)
- netsh.exe (PID: 908)
- netsh.exe (PID: 3044)
- netsh.exe (PID: 2404)
- netsh.exe (PID: 1456)
- netsh.exe (PID: 2264)
- netsh.exe (PID: 1208)
- chrome.exe (PID: 3500)
- netsh.exe (PID: 4036)
- find.exe (PID: 1380)
- sc.exe (PID: 2332)
- netsh.exe (PID: 2444)
- tasklist.exe (PID: 3988)
- chrome.exe (PID: 3172)
- chrome.exe (PID: 3916)
- chrome.exe (PID: 3784)
- chrome.exe (PID: 3544)
Reads the hosts file
- chrome.exe (PID: 3728)
- chrome.exe (PID: 3204)
Reads the computer name
- chrome.exe (PID: 3204)
- chrome.exe (PID: 3728)
- chrome.exe (PID: 2568)
- chrome.exe (PID: 1896)
- chrome.exe (PID: 1840)
- chrome.exe (PID: 1796)
- chrome.exe (PID: 3440)
- chrome.exe (PID: 1588)
- chrome.exe (PID: 1284)
- netsh.exe (PID: 2404)
- netsh.exe (PID: 3960)
- netsh.exe (PID: 2408)
- netsh.exe (PID: 4072)
- netsh.exe (PID: 3720)
- netsh.exe (PID: 908)
- netsh.exe (PID: 2548)
- netsh.exe (PID: 3696)
- netsh.exe (PID: 3044)
- netsh.exe (PID: 756)
- netsh.exe (PID: 2036)
- netsh.exe (PID: 908)
- netsh.exe (PID: 2404)
- netsh.exe (PID: 2264)
- netsh.exe (PID: 1208)
- netsh.exe (PID: 1456)
- netsh.exe (PID: 2444)
- netsh.exe (PID: 4036)
- sc.exe (PID: 2332)
- tasklist.exe (PID: 3988)
Application launched itself
- chrome.exe (PID: 3728)
Reads settings of System Certificates
- chrome.exe (PID: 3204)
- chrome.exe (PID: 3728)
- Gui.exe (PID: 3120)
- CagService.exe (PID: 3036)
- AEMAgent.exe (PID: 3668)
Checks Windows Trust Settings
- chrome.exe (PID: 3728)
- Gui.exe (PID: 3120)
Reads the date of Windows installation
- chrome.exe (PID: 1588)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
111
Monitored processes
53
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\CentraStage\scvncctrl.dll" | C:\Windows\system32\regsvr32.exe | — | CagService.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 756 | "netsh" advfirewall firewall add rule name="RMM.WebRemote 9.4.0.14" dir=out action=allow program="C:\ProgramData\CentraStage\AEMAgent\RMM.WebRemote\9.4.0.14\RMM.WebRemote.exe" enable=yes | C:\Windows\system32\netsh.exe | — | AEMAgent.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 908 | "netsh" advfirewall firewall add rule name="AEMAgent" dir=in action=allow program="C:\ProgramData\CentraStage\AEMAgent\AEMAgent.exe" enable=yes | C:\Windows\system32\netsh.exe | — | AEMAgent.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 908 | "netsh" advfirewall firewall add rule name="RMM RTC Proxy" dir=in action=allow program="C:\ProgramData\CentraStage\AEMAgent\RMM.WebRemote\9.4.0.14\RMM.RTC.Proxy\RMM.RTC.Proxy.exe" enable=yes | C:\Windows\system32\netsh.exe | — | RMM.WebRemote.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1208 | "netsh" advfirewall firewall add rule name="RMM RTO Proxy" dir=in action=allow program="C:\ProgramData\CentraStage\AEMAgent\RMM.WebRemote\9.4.0.14\RMM.RTO.Proxy\RMM.RTO.Proxy.exe" enable=yes | C:\Windows\system32\netsh.exe | — | RMM.WebRemote.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1060,7972399855345835874,12846055955575685889,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1780 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1380 | find ":" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Find String (grep) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1456 | "netsh" advfirewall firewall add rule name="RMM RTO Proxy" dir=out action=allow program="C:\ProgramData\CentraStage\AEMAgent\RMM.WebRemote\9.4.0.14\RMM.RTO.Proxy\RMM.RTO.Proxy.exe" enable=yes | C:\Windows\system32\netsh.exe | — | RMM.WebRemote.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,7972399855345835874,12846055955575685889,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2172 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1060,7972399855345835874,12846055955575685889,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1396 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
37 619
Read events
36 535
Write events
1 079
Delete events
5
Modification events
| (PID) Process: | (3728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3728) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
442
Suspicious files
56
Text files
214
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-60A52C00-E90.pma | — | |
MD5:— | SHA256:— | |||
| 3728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c0943702-43a9-4f9f-9f3f-35a28f699810.tmp | text | |
MD5:— | SHA256:— | |||
| 3728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 3728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF193b0b.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 3728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF193a6f.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 3728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF193a6f.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 3728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old~RF194106.TMP | text | |
MD5:D097F8EB2230B3F32C41C5D75790508C | SHA256:ADDF87D20CD455CFB4AACB6B76719629C0277A4CF70B496343047BB73ABBAEF5 | |||
| 2284 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 3728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old | text | |
MD5:5202CA4D6AF0C37DAEC0D528CC7F2986 | SHA256:8F5B8FF94B14C36EA0CBE8FA0A4D165A632B45F834BBB7239E1A6CF6685F256C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
36
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | — | — | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | binary | 7.10 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | binary | 21.1 Kb | whitelisted |
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODNjQUFXN0xyYnNNZ1UyTjZEQjNiZzhuQQ/4.10.2209.0_oimompecagnajdejgnnjijobebaeigek.crx | US | binary | 364 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | binary | 43.6 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | gpg | 719 Kb | whitelisted |
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/TZdDvov1bHrXSAB3xrtQbA_2021.5.9.1142/AldQIKB0SuIgdbye2Jfxww | US | crx | 384 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | binary | 88.7 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | binary | 358 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODNjQUFXN0xyYnNNZ1UyTjZEQjNiZzhuQQ/4.10.2209.0_oimompecagnajdejgnnjijobebaeigek.crx | US | binary | 2.81 Mb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3204 | chrome.exe | 142.250.185.173:443 | accounts.google.com | Google Inc. | US | suspicious |
3204 | chrome.exe | 142.250.186.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
3204 | chrome.exe | 13.224.193.36:443 | concord.centrastage.net | — | US | suspicious |
3204 | chrome.exe | 142.250.186.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3204 | chrome.exe | 142.250.185.78:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
3036 | CagService.exe | 54.164.96.143:443 | concordcc.centrastage.net | Amazon.com, Inc. | US | unknown |
3036 | CagService.exe | 34.195.169.6:443 | concord-agent.centrastage.net | Amazon.com, Inc. | US | unknown |
3036 | CagService.exe | 13.224.193.68:443 | update-concord.centrastage.net | — | US | suspicious |
3036 | CagService.exe | 68.232.34.200:443 | download.visualstudio.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3668 | AEMAgent.exe | 34.224.132.33:443 | concord-agent-notifications.centrastage.net | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
concord.centrastage.net |
| malicious |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
concordcc.centrastage.net |
| unknown |
concord-agent.centrastage.net |
| unknown |
update-concord.centrastage.net |
| malicious |
download.visualstudio.microsoft.com |
| whitelisted |
update.googleapis.com |
| whitelisted |