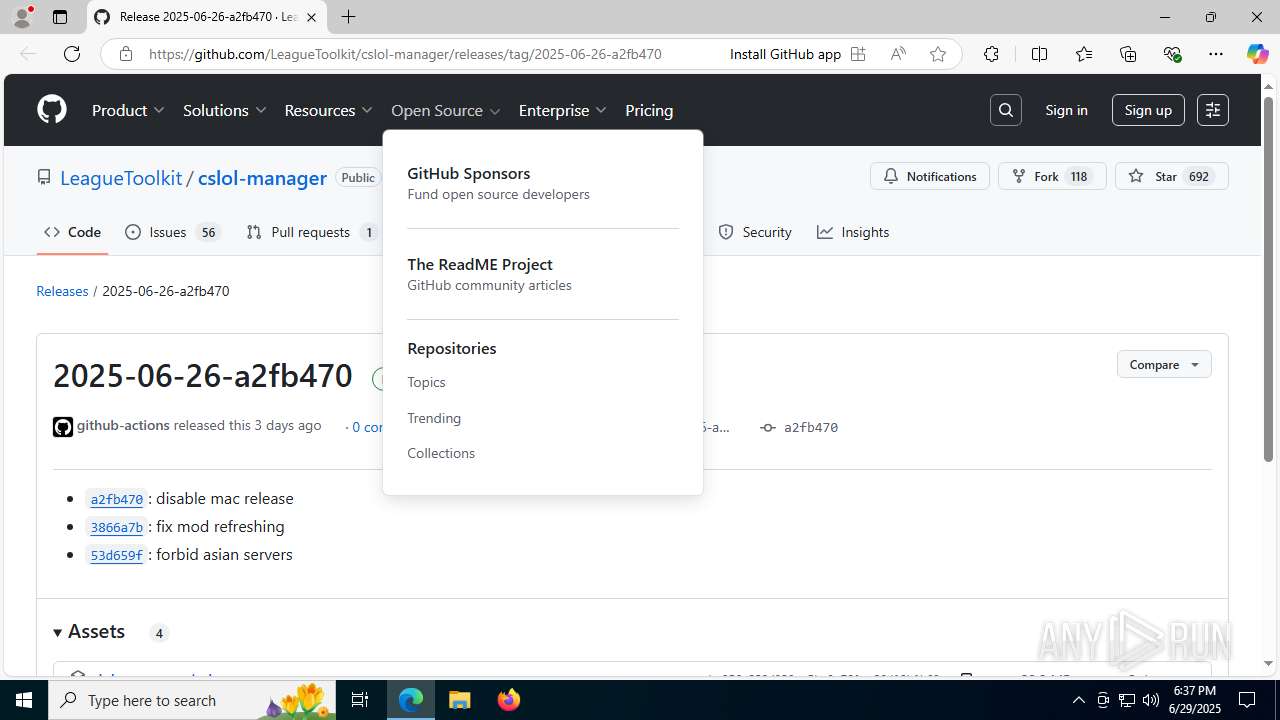
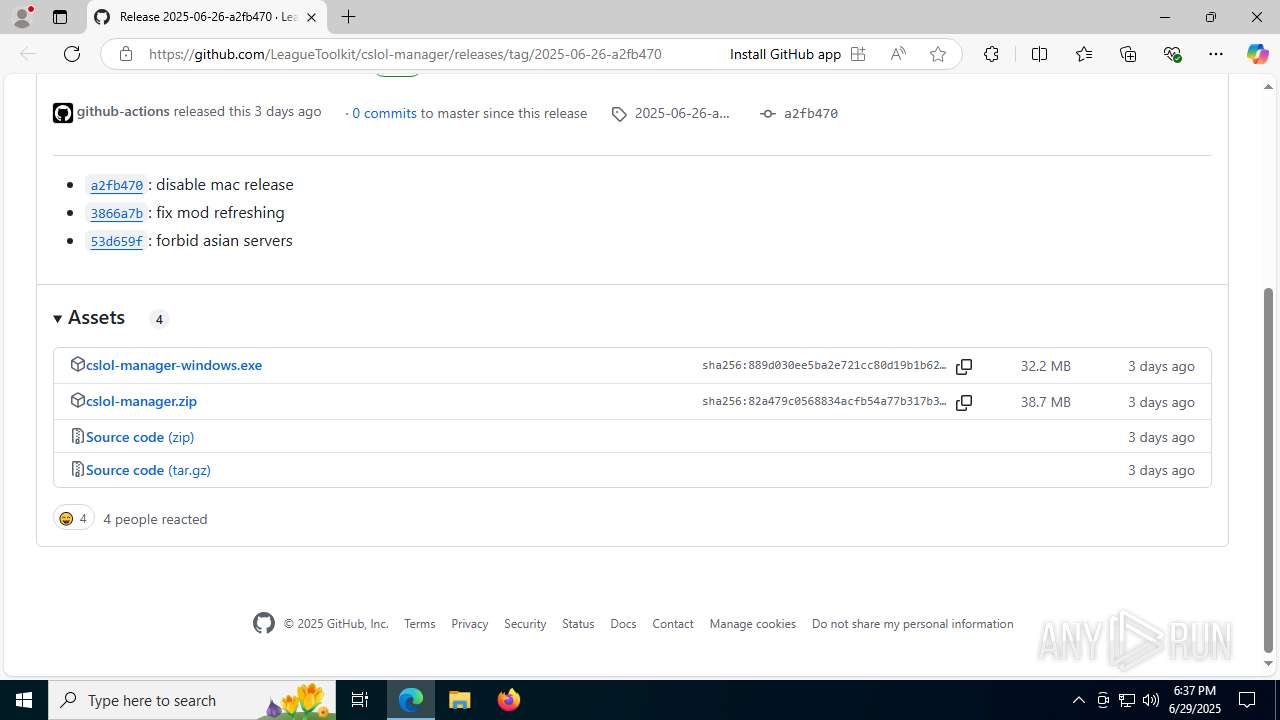
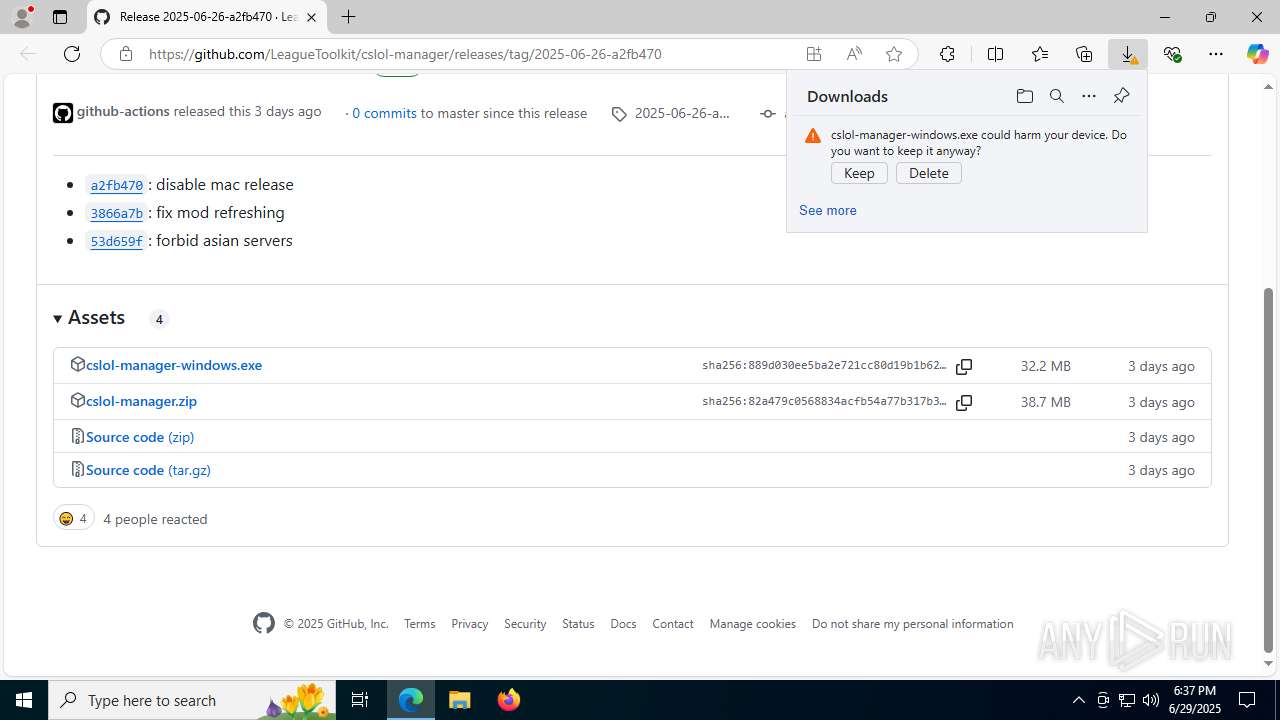
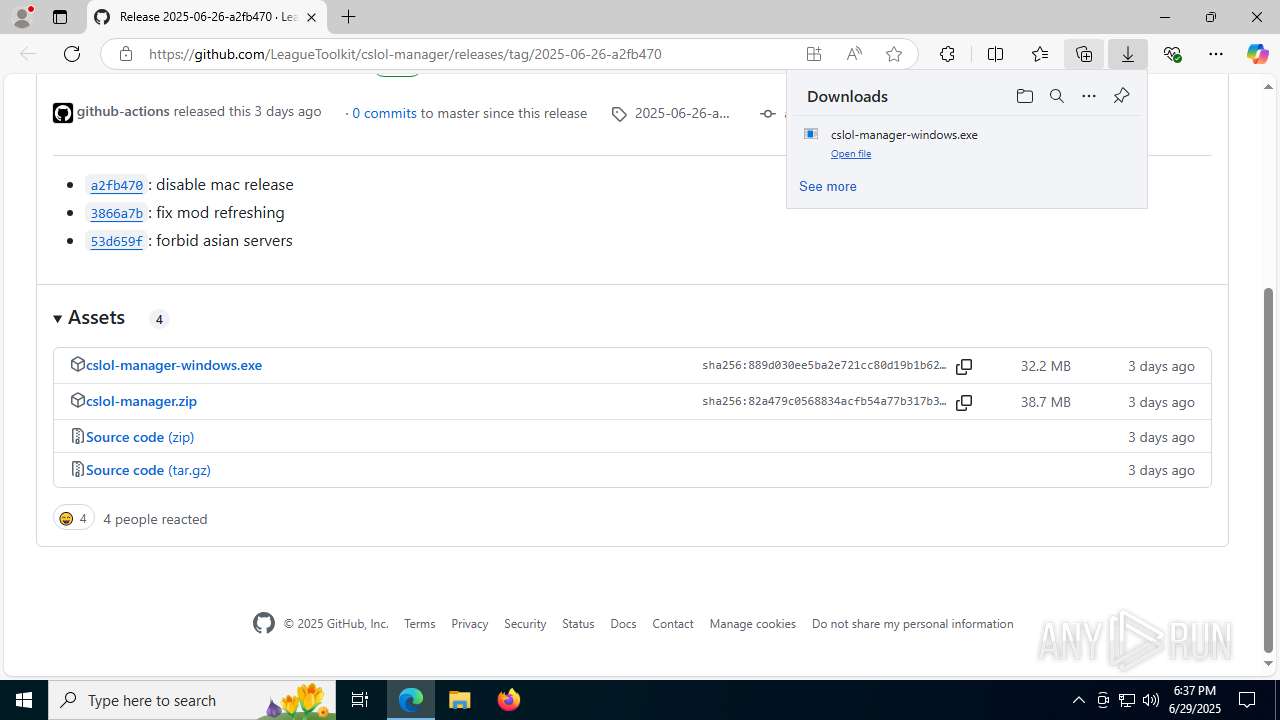
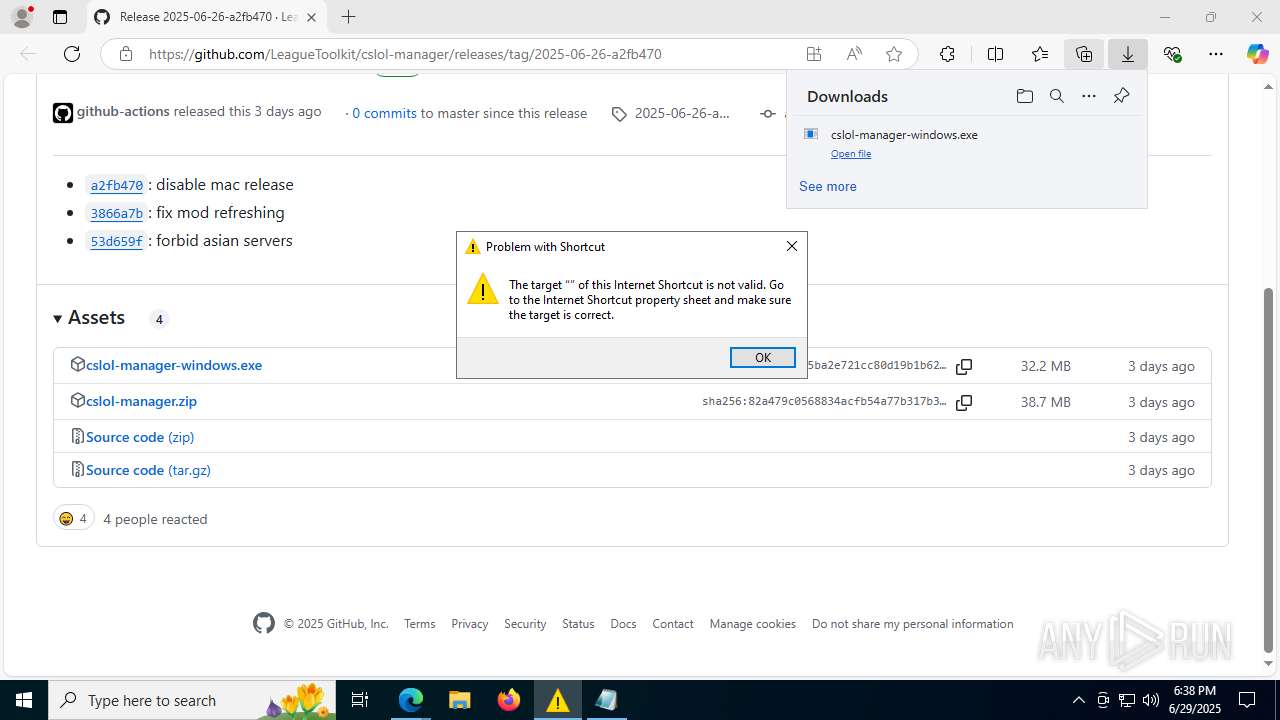
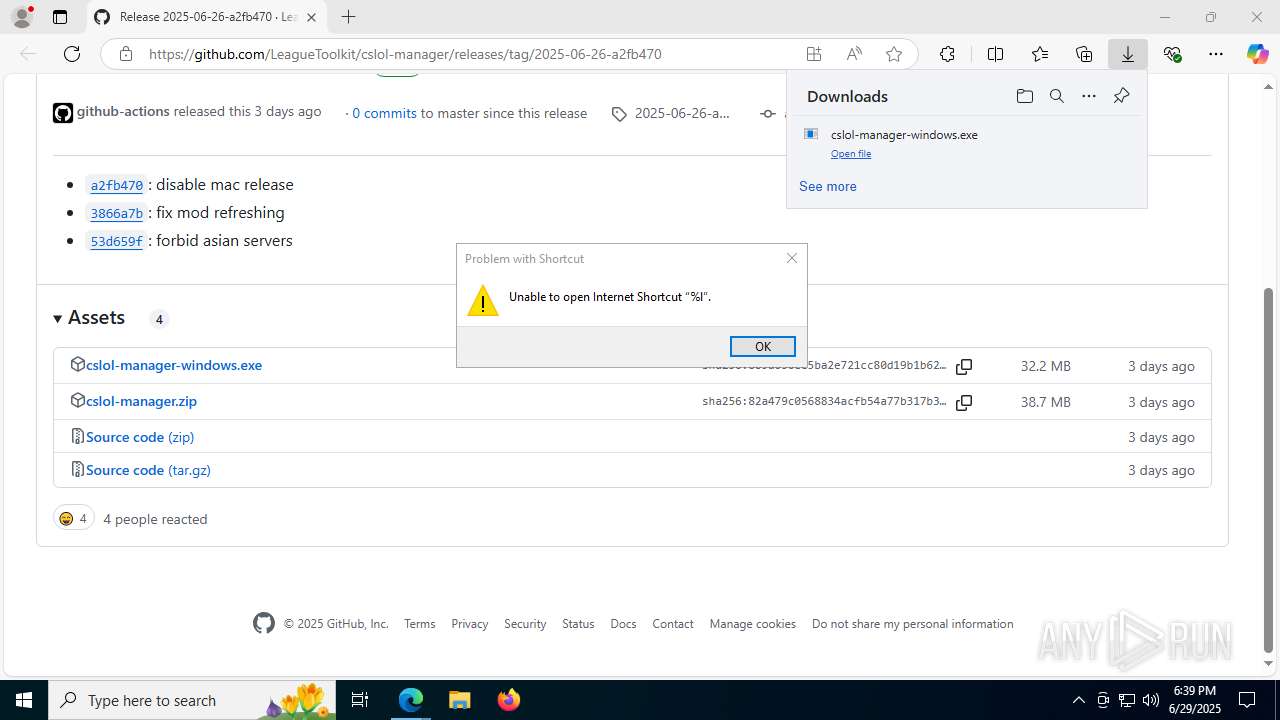
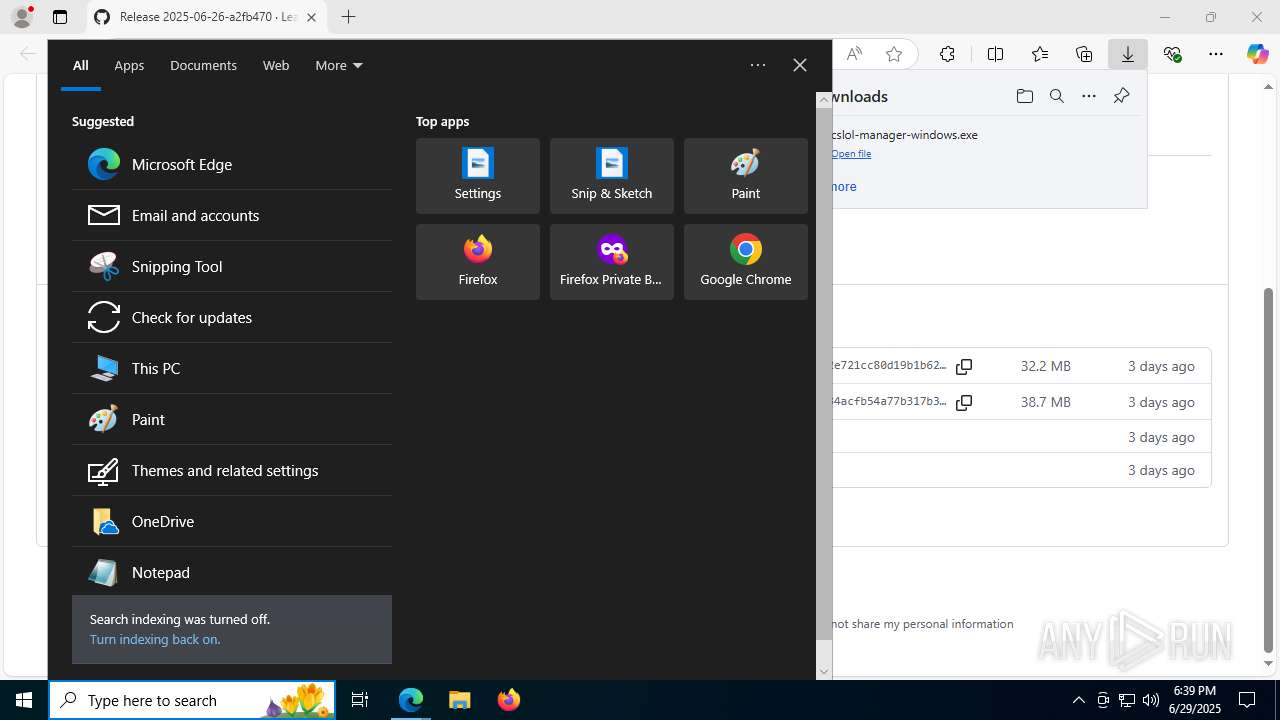
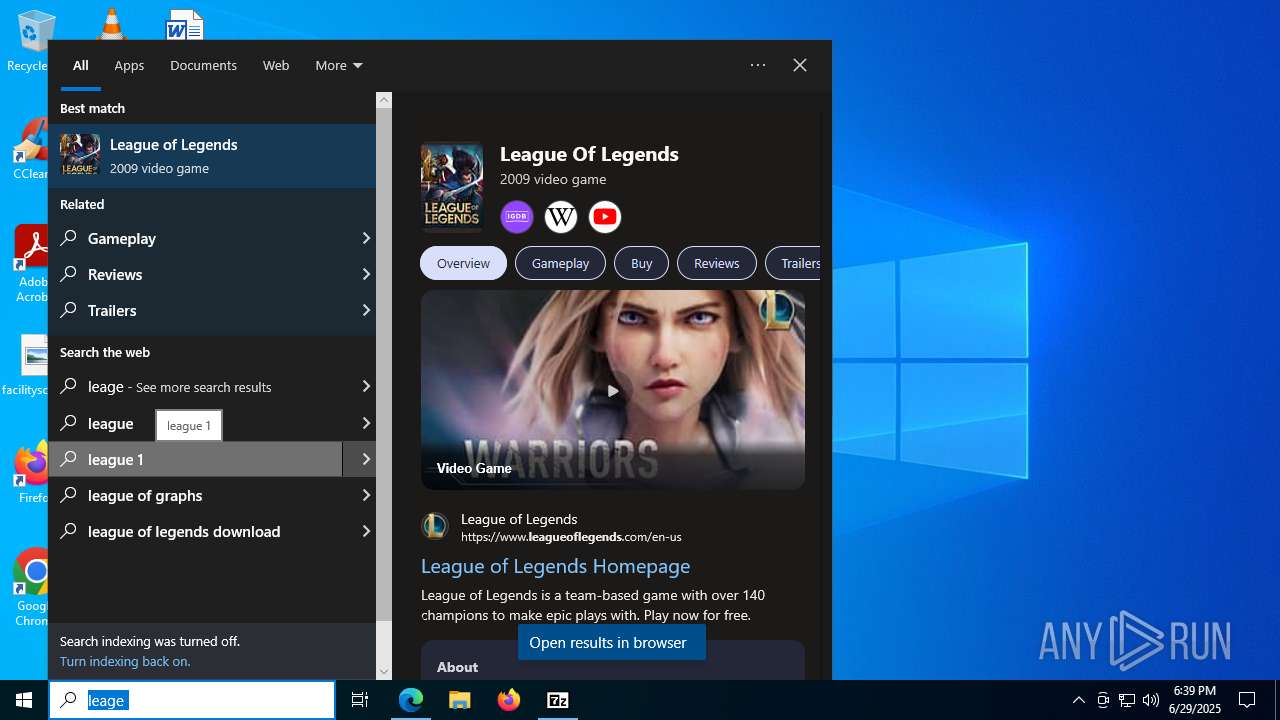
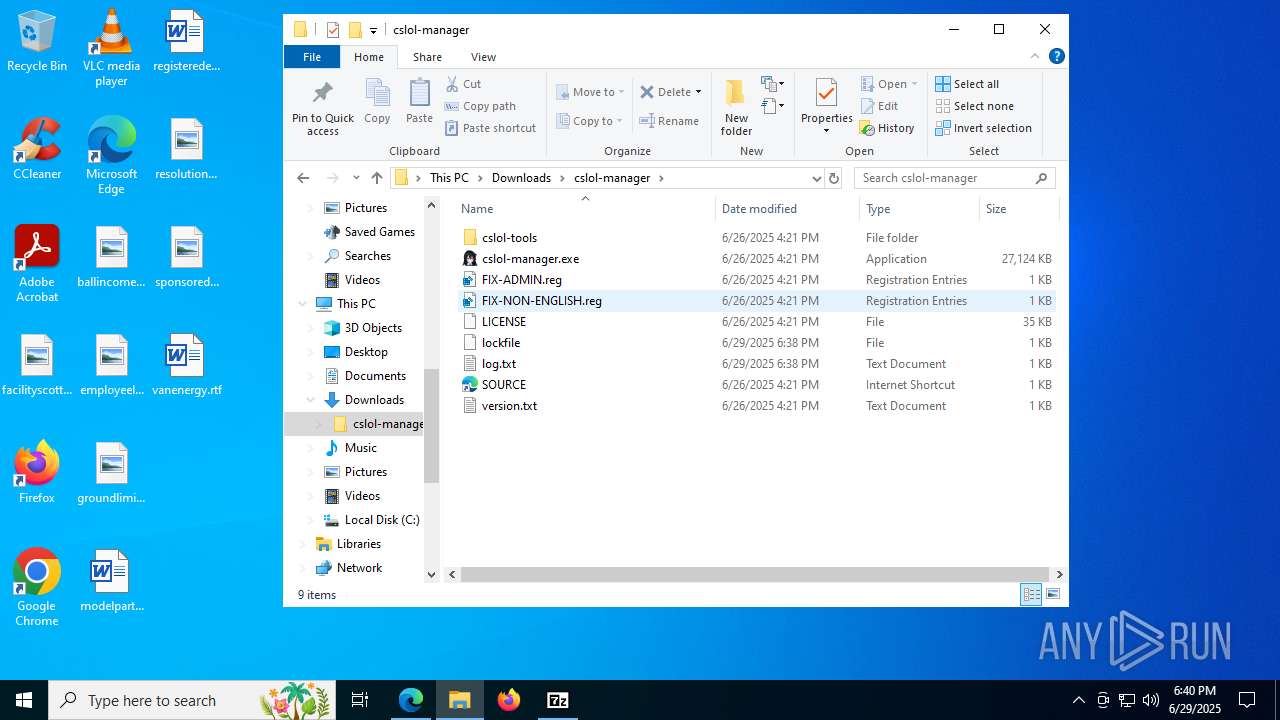
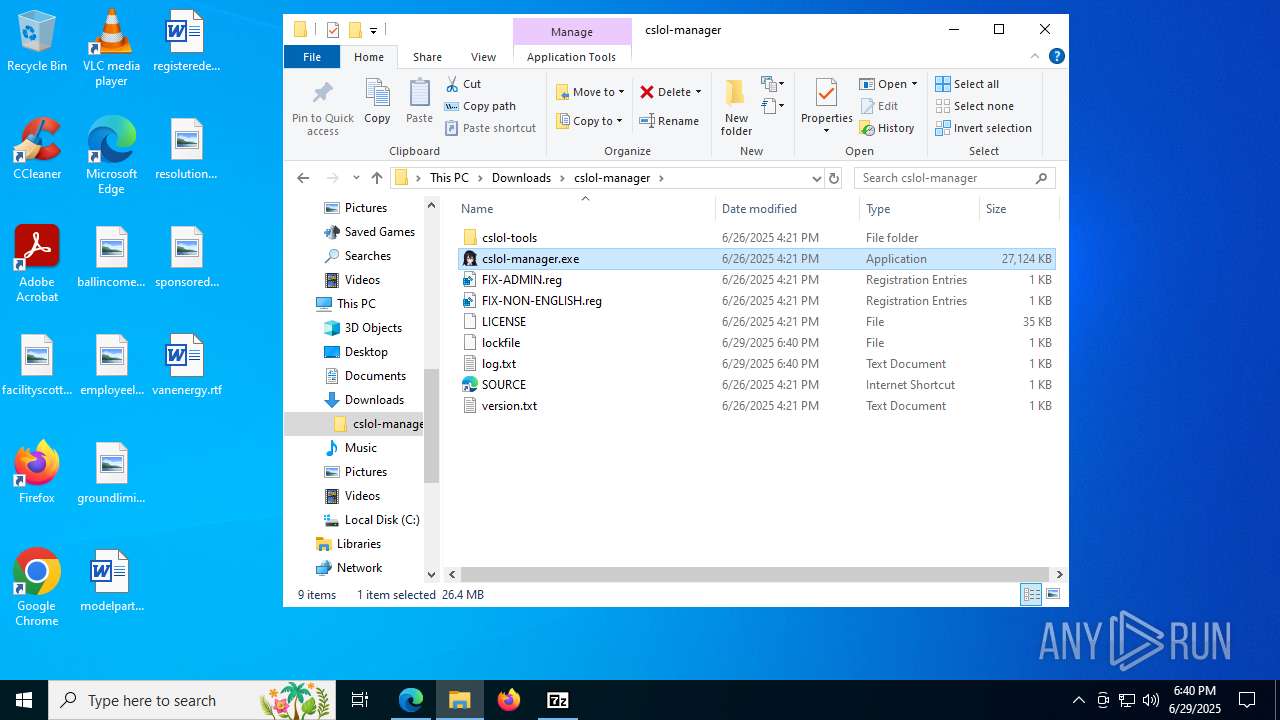
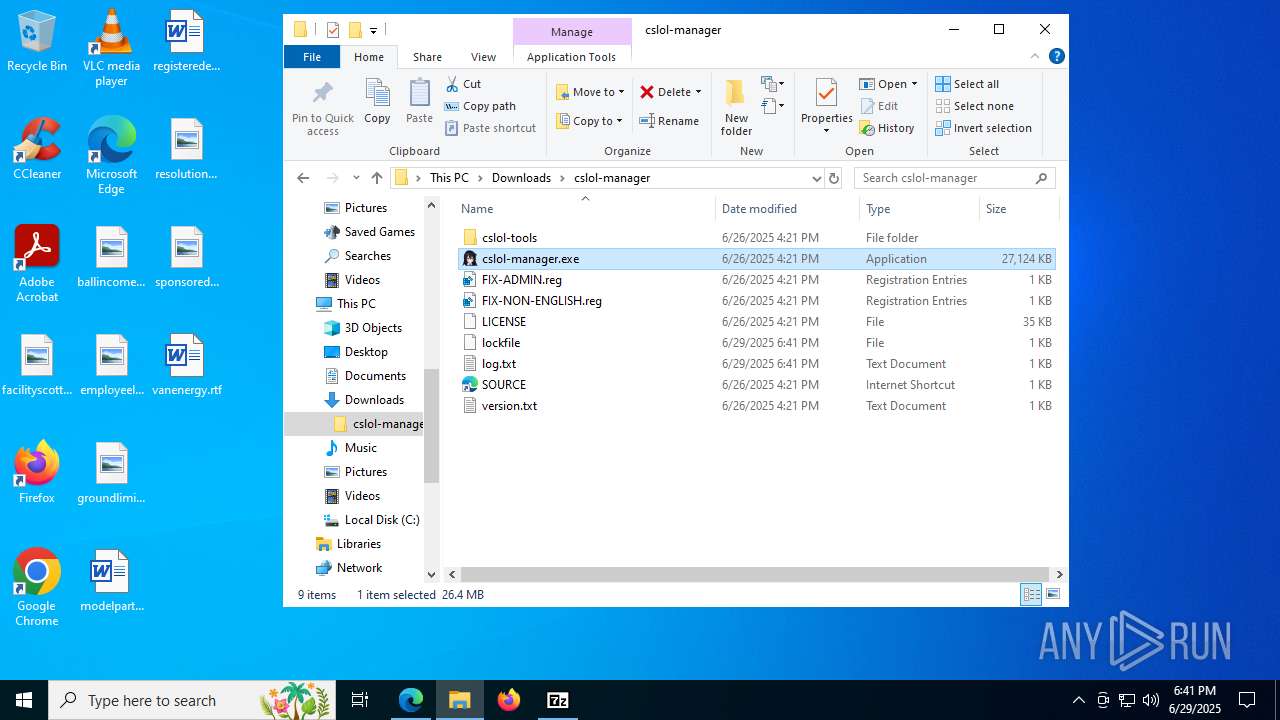
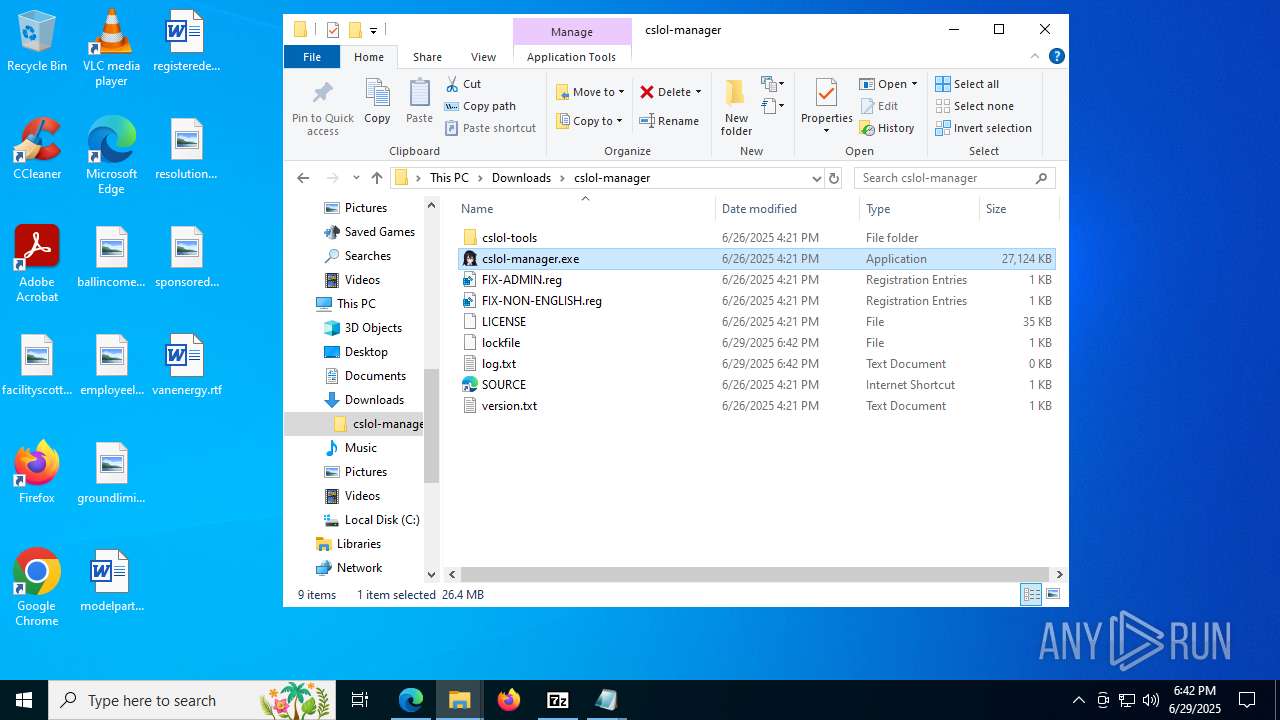
| URL: | https://github.com/LeagueToolkit/cslol-manager/releases/tag/2025-06-26-a2fb470 |
| Full analysis: | https://app.any.run/tasks/51b07047-1a87-4a7c-9344-16b574f7e52b |
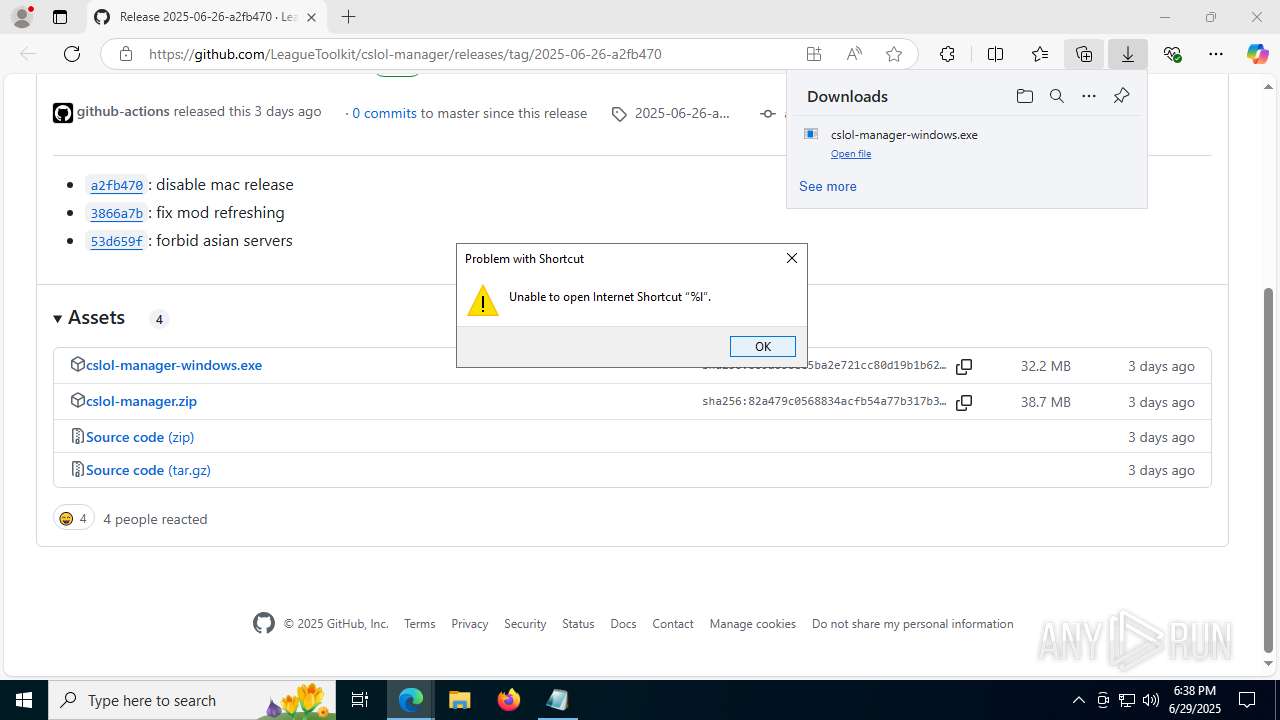
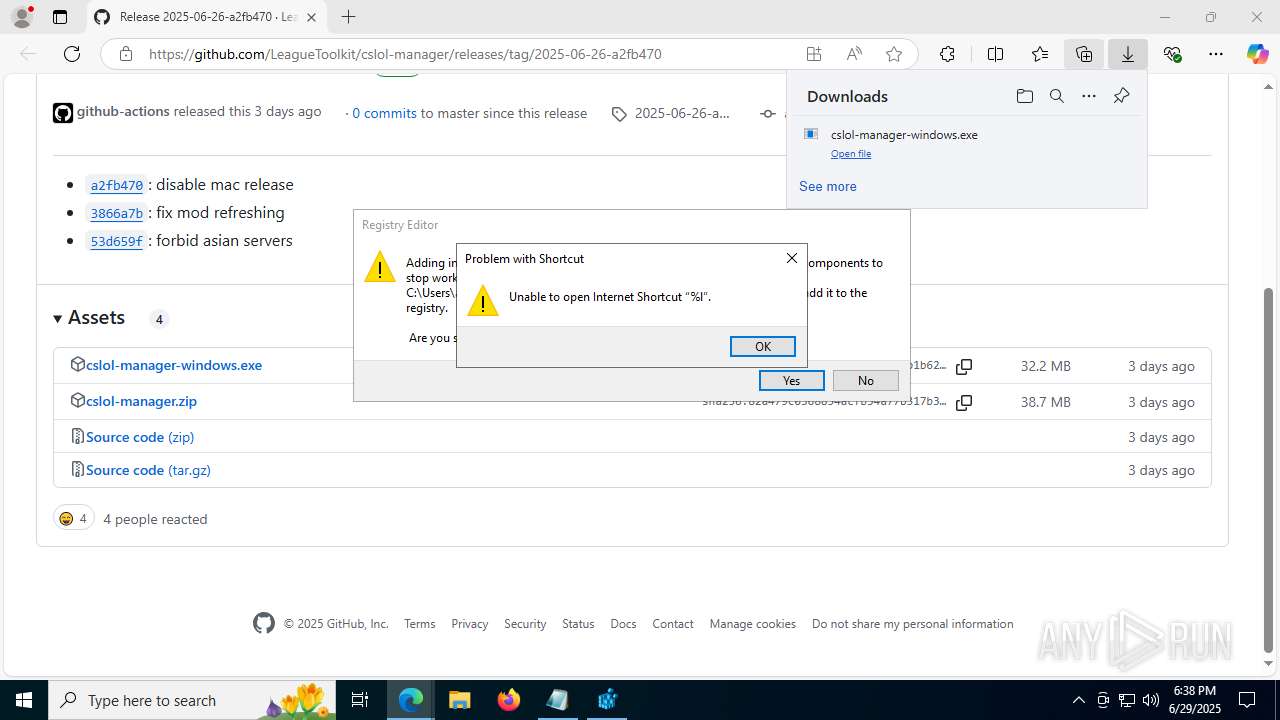
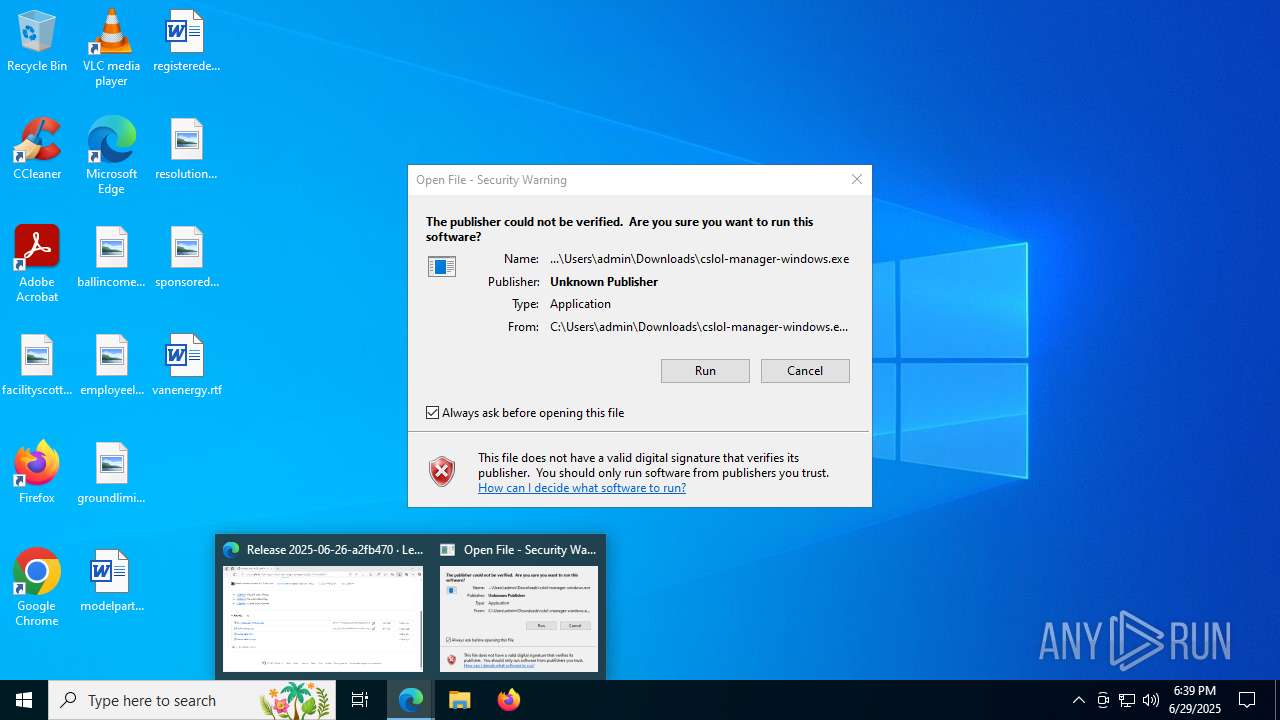
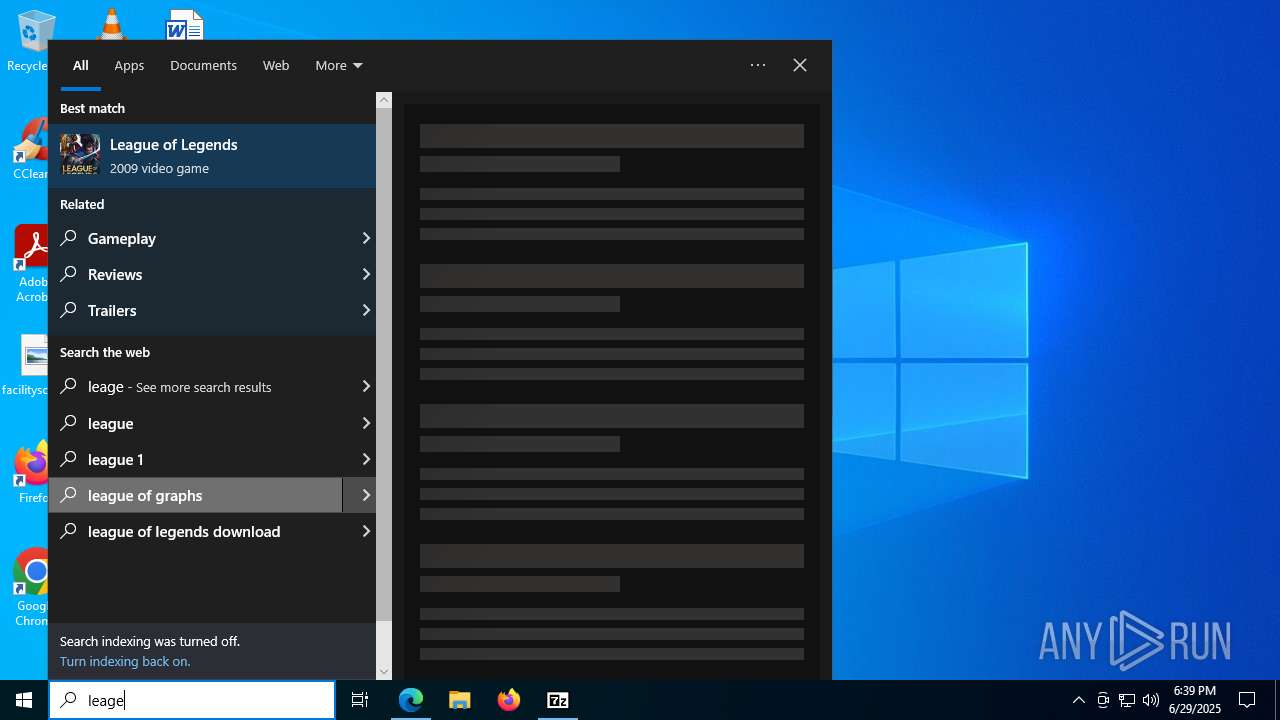
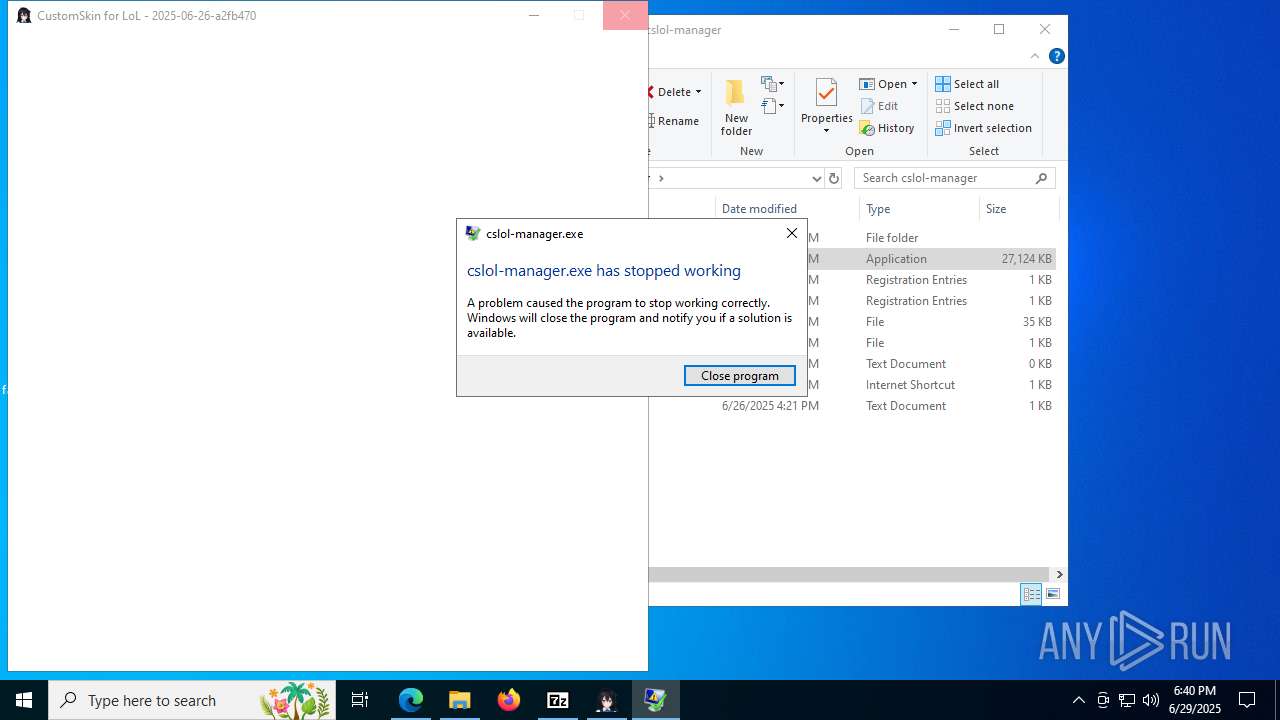
| Verdict: | Malicious activity |
| Analysis date: | June 29, 2025, 18:37:23 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | AB155CFF9FD345172B578612B52A71C3 |
| SHA1: | 3B138C2C8D09CEE06E5FEA290189163A22300EE4 |
| SHA256: | A551C75D4CA049B4CC3FA6A6A4C151649AF45660481C7B4F105651C9803B9EA1 |
| SSDEEP: | 3:N8tEdHejnls3AXBJAE2qKFXdWdXDM:2u8nBX/ArxFtkM |
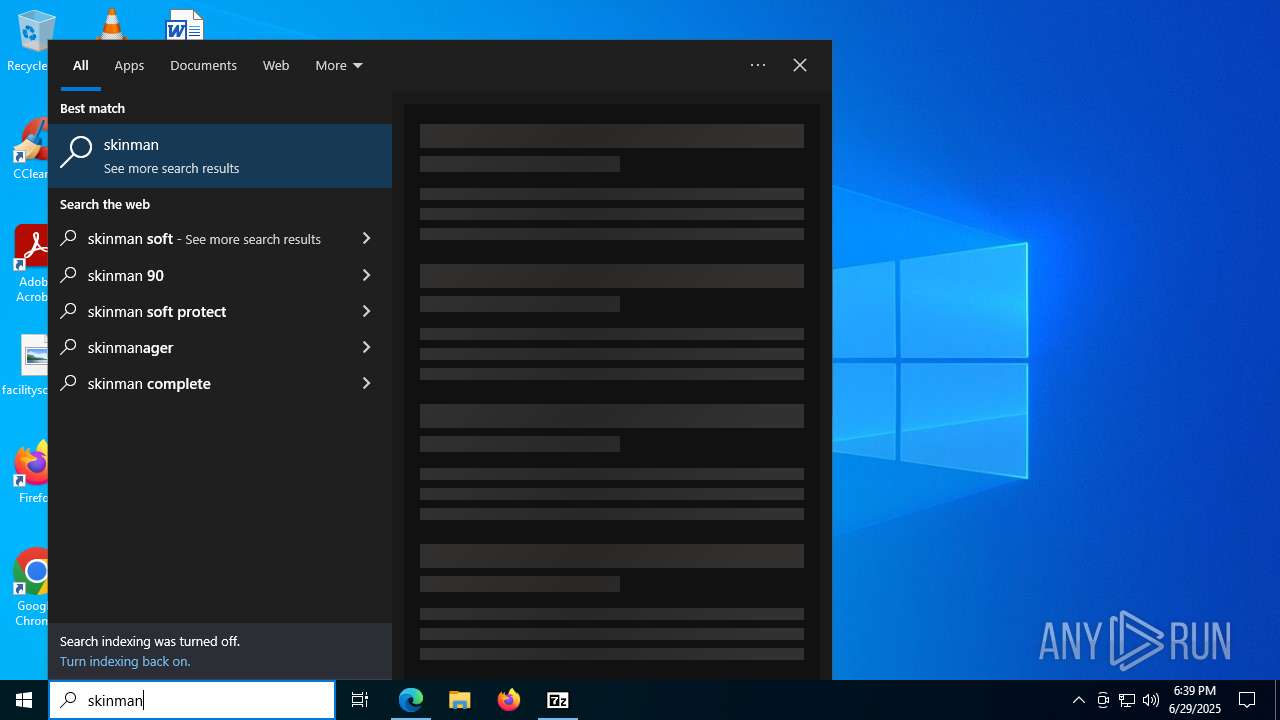
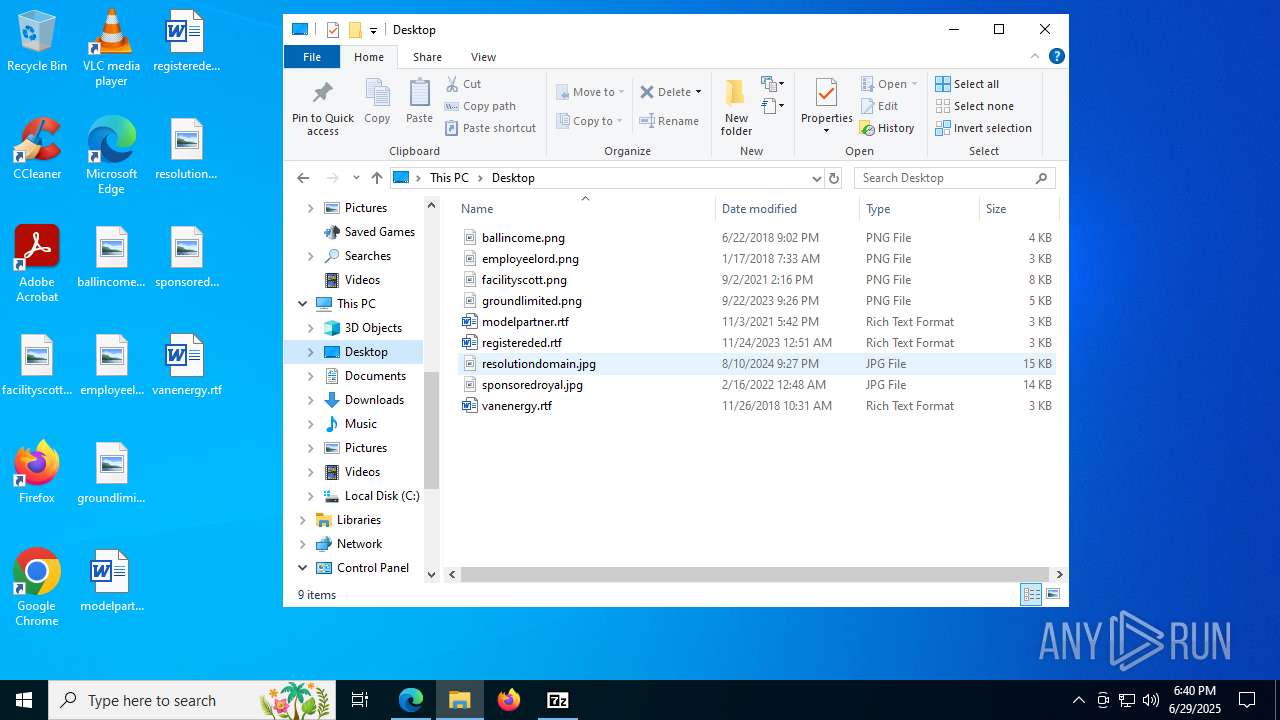
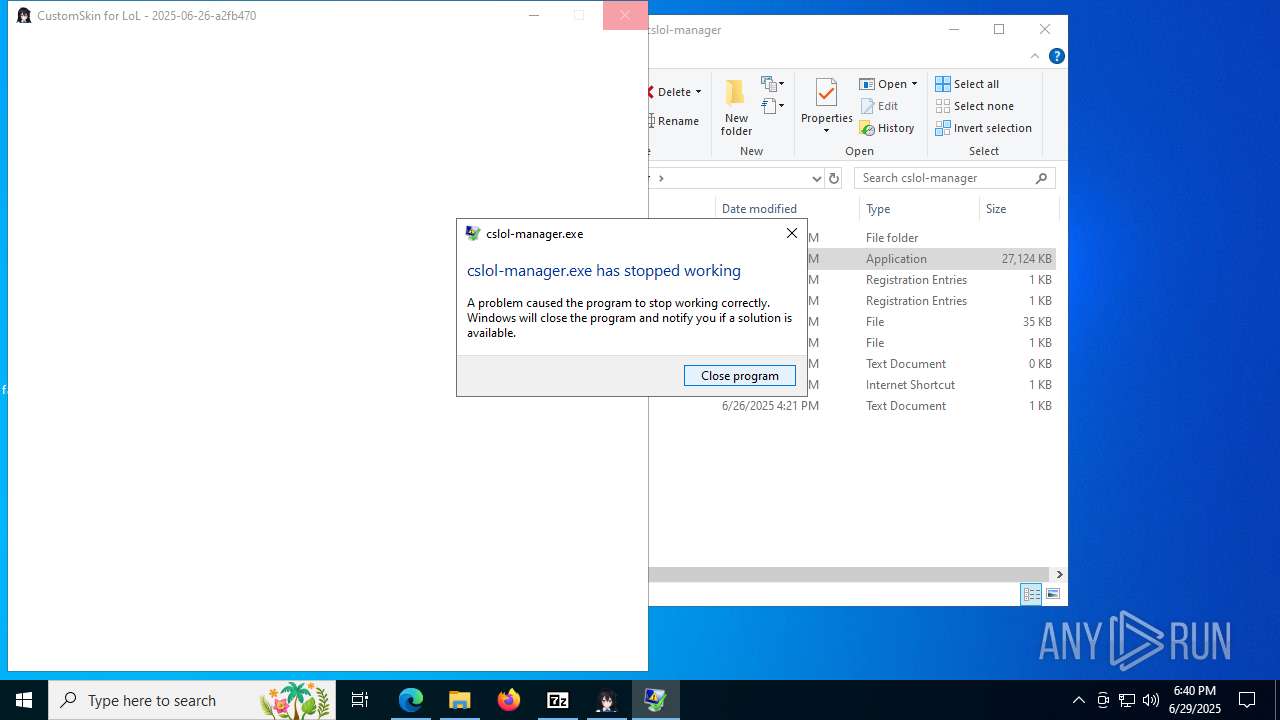
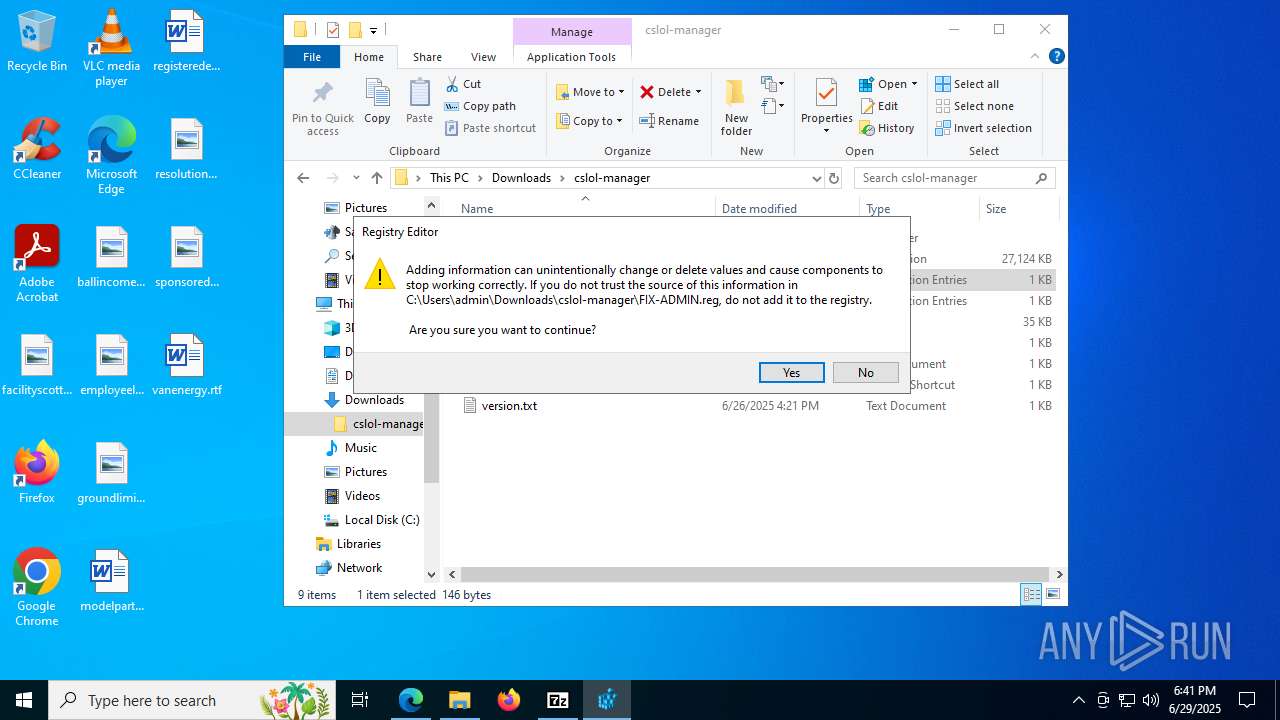
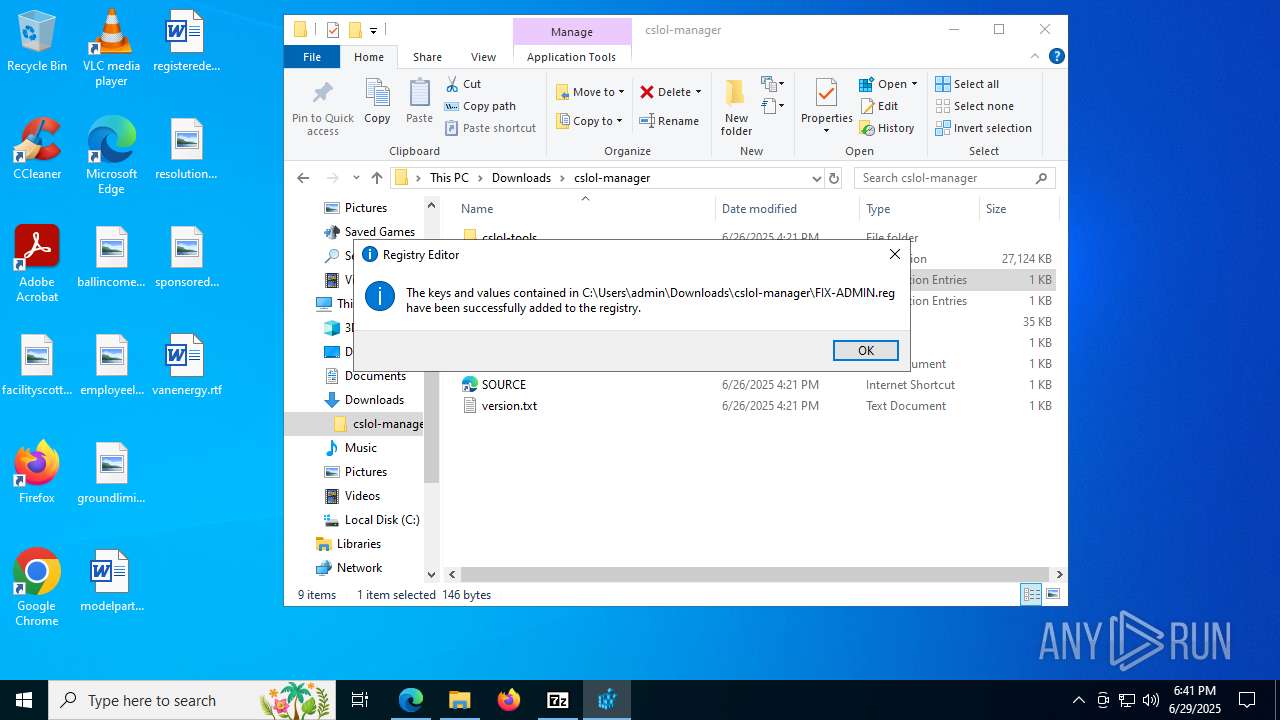
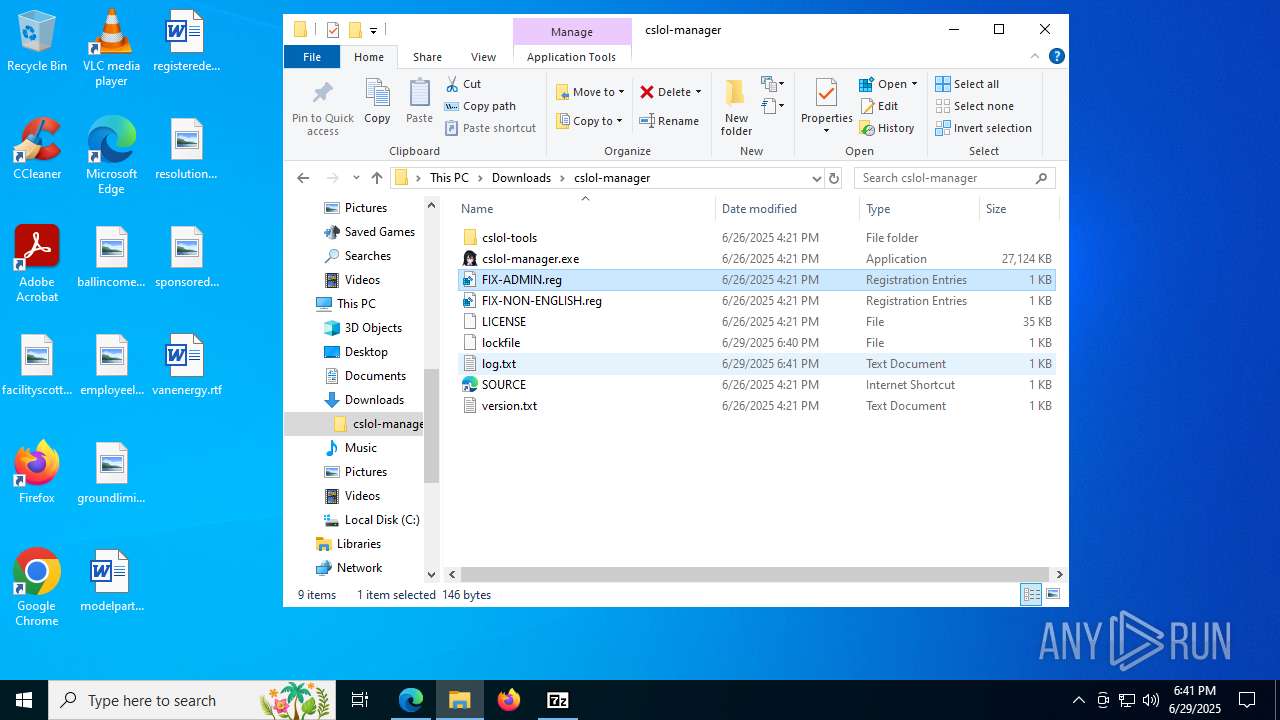
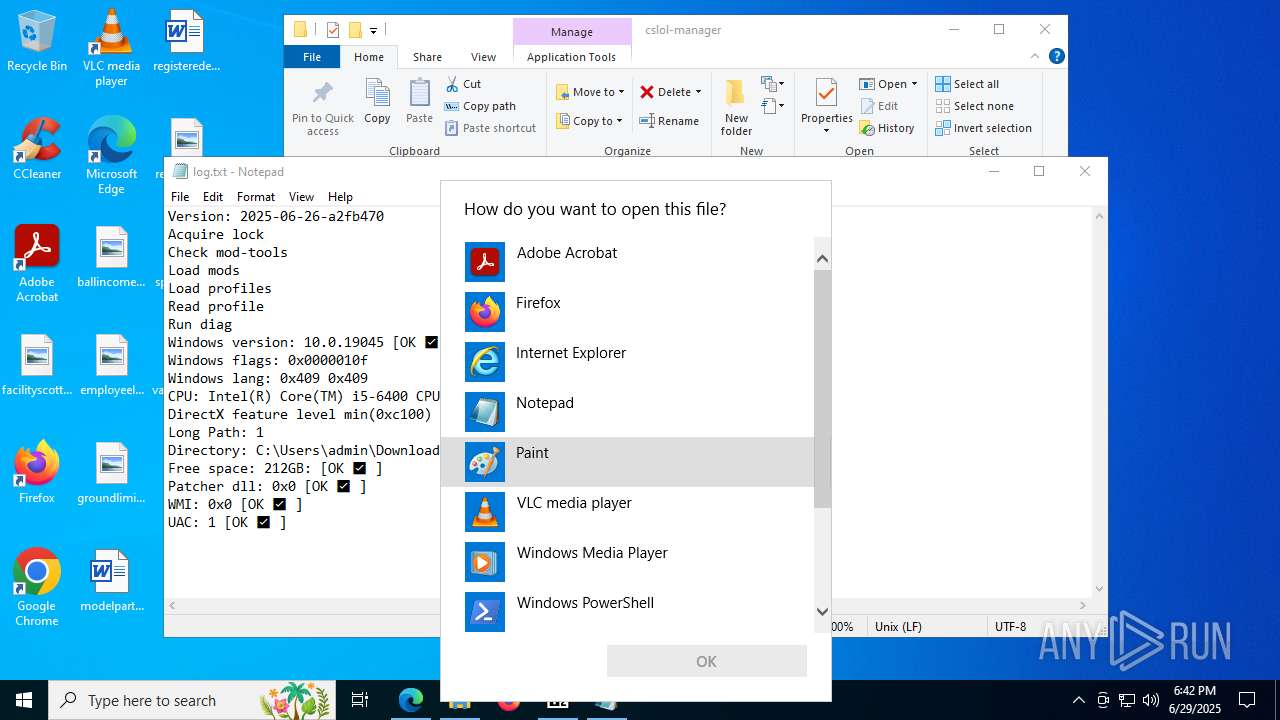
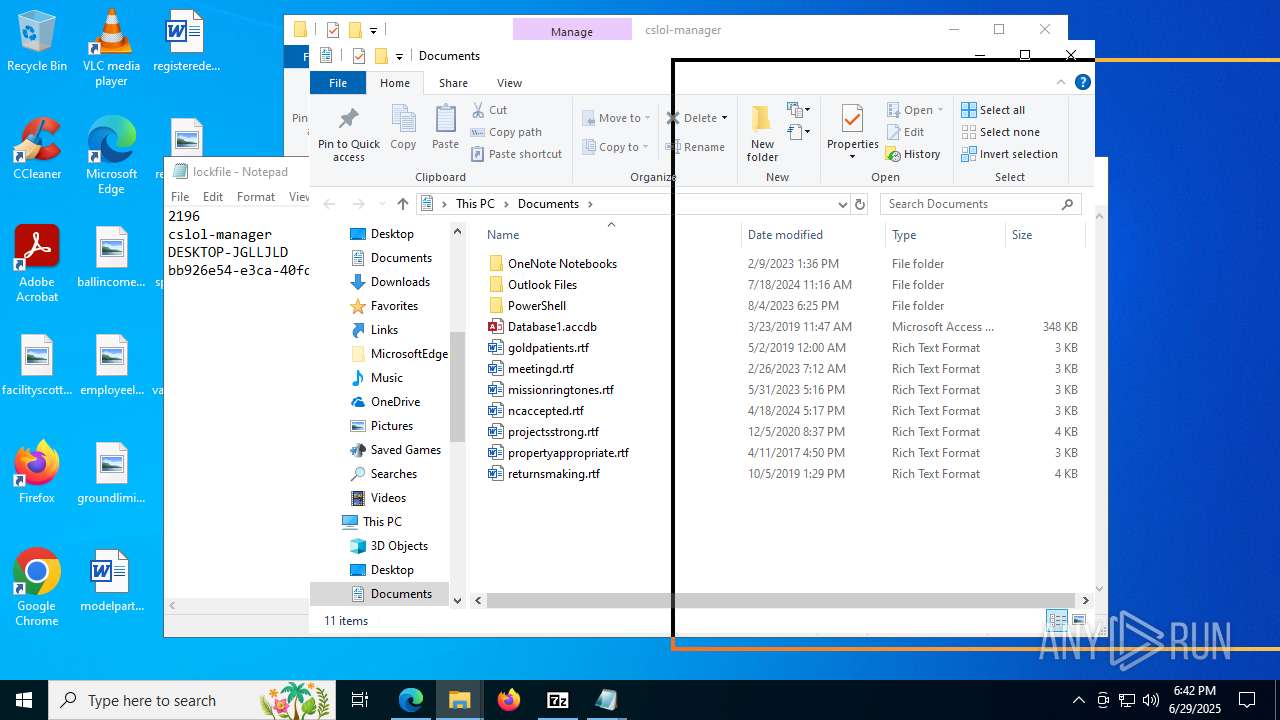
MALICIOUS
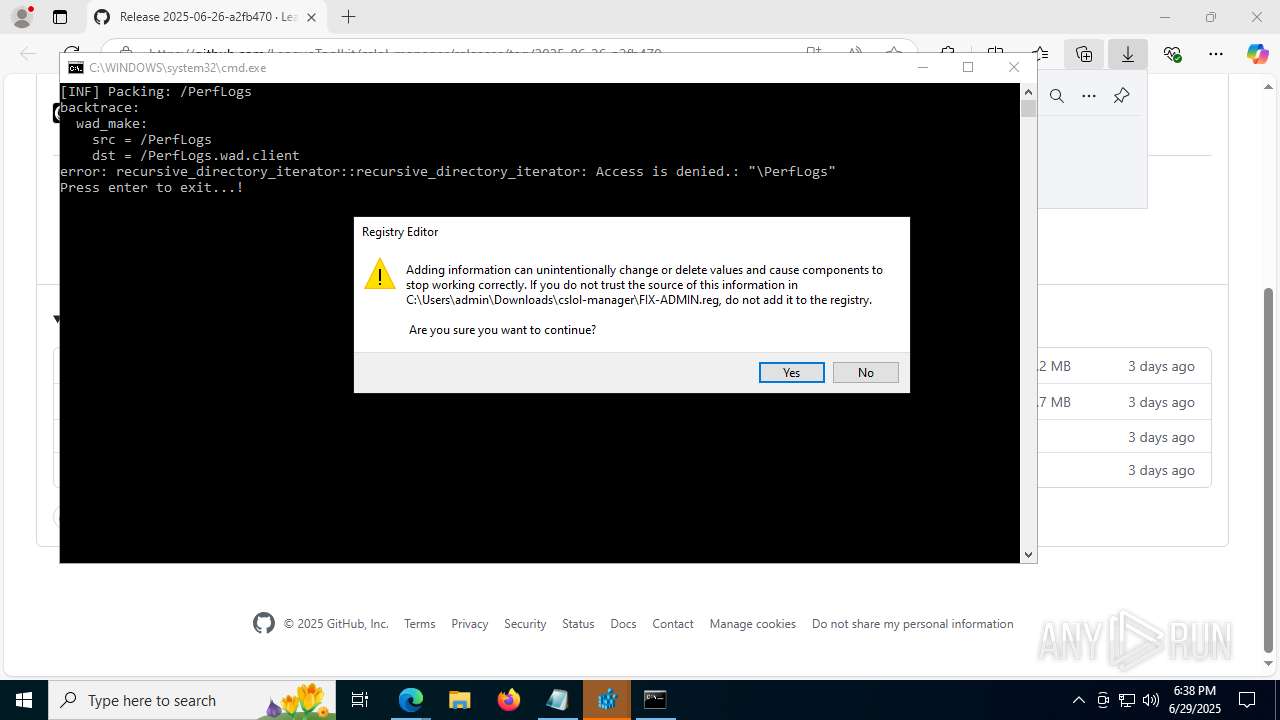
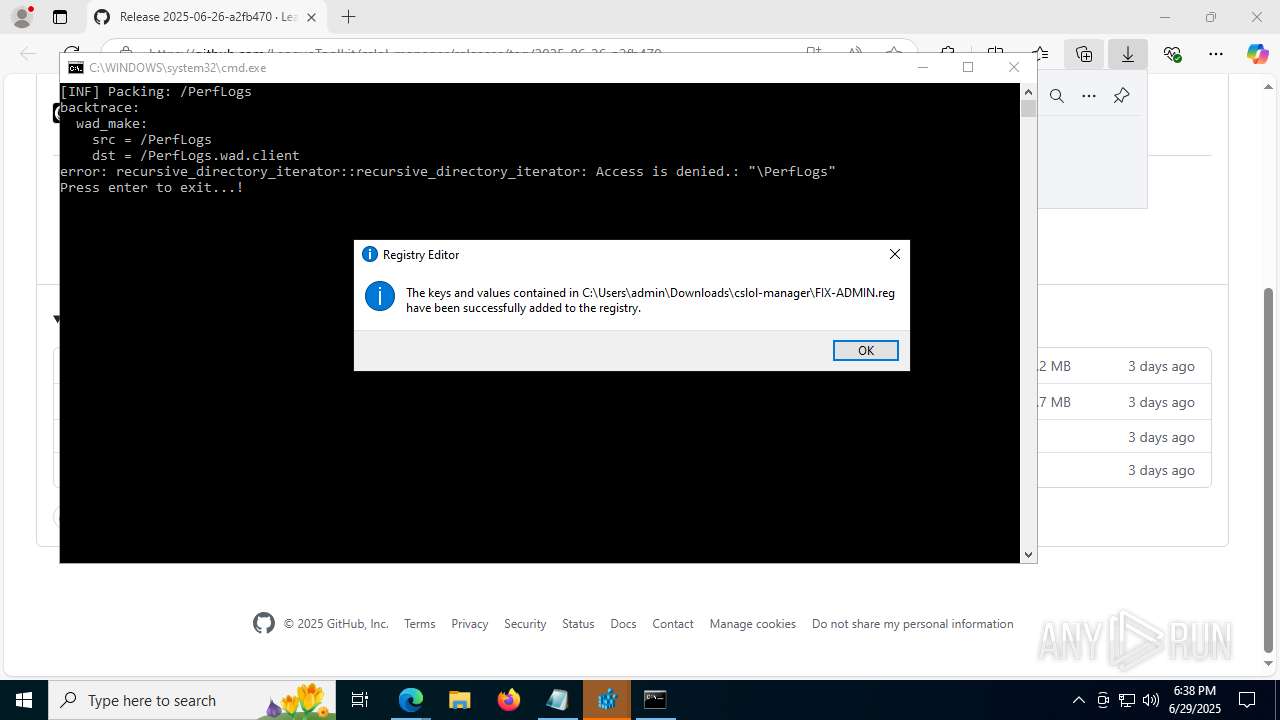
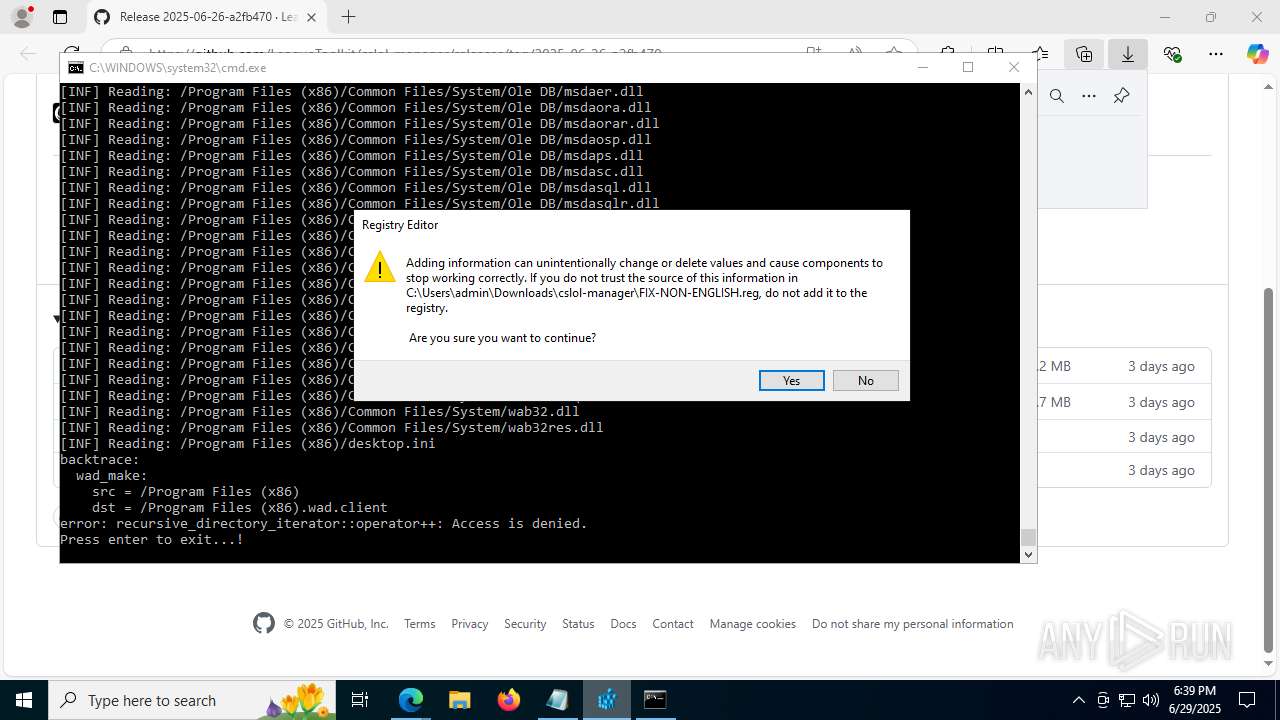
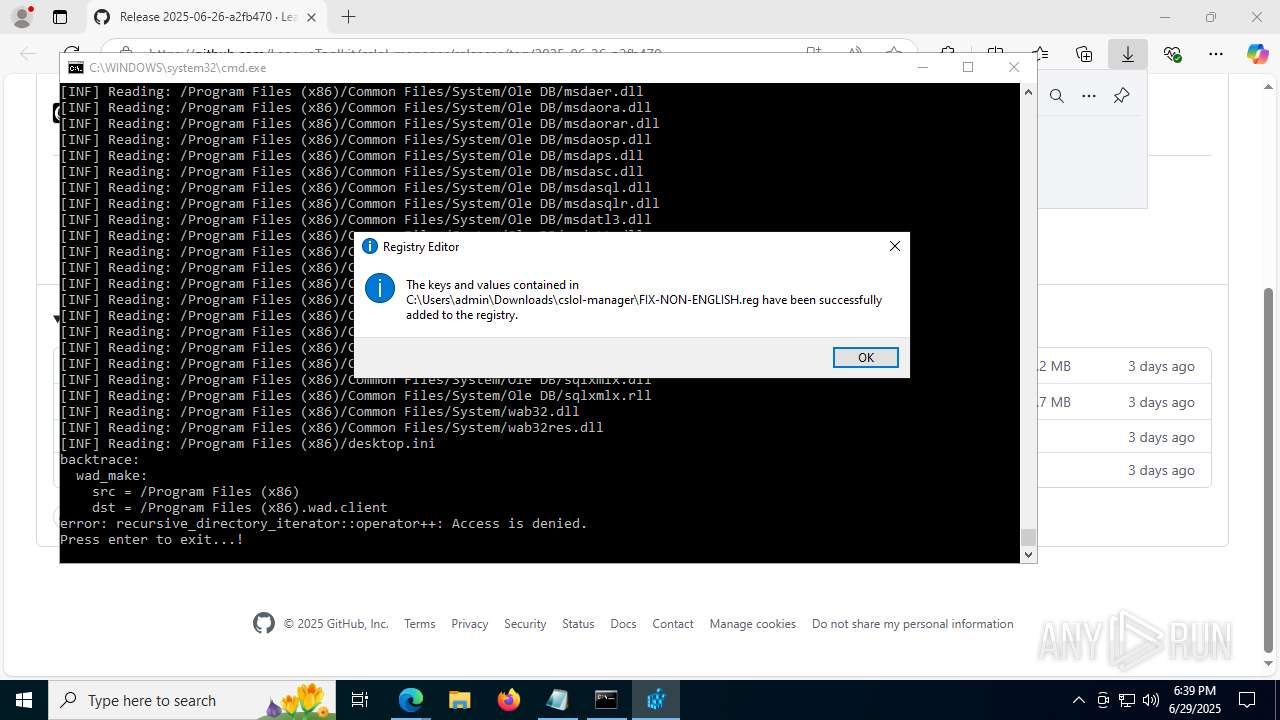
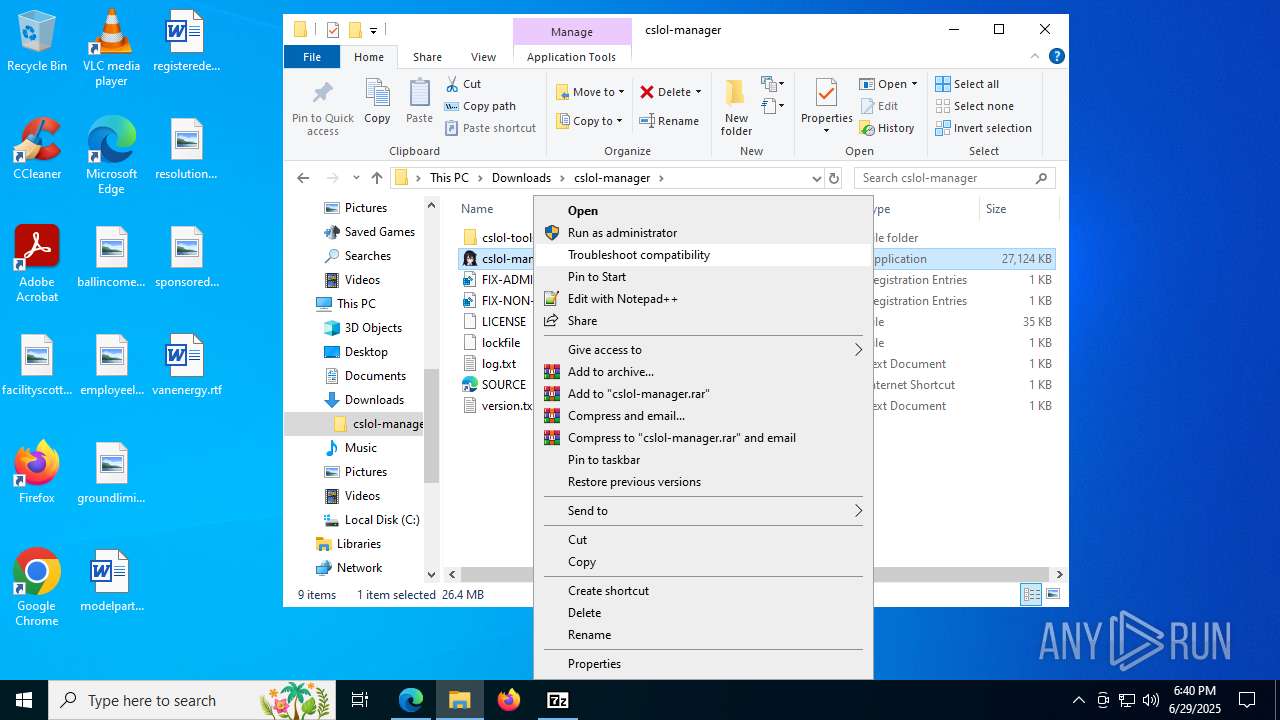
UAC/LUA settings modification
- regedit.exe (PID: 6516)
- regedit.exe (PID: 7132)
SUSPICIOUS
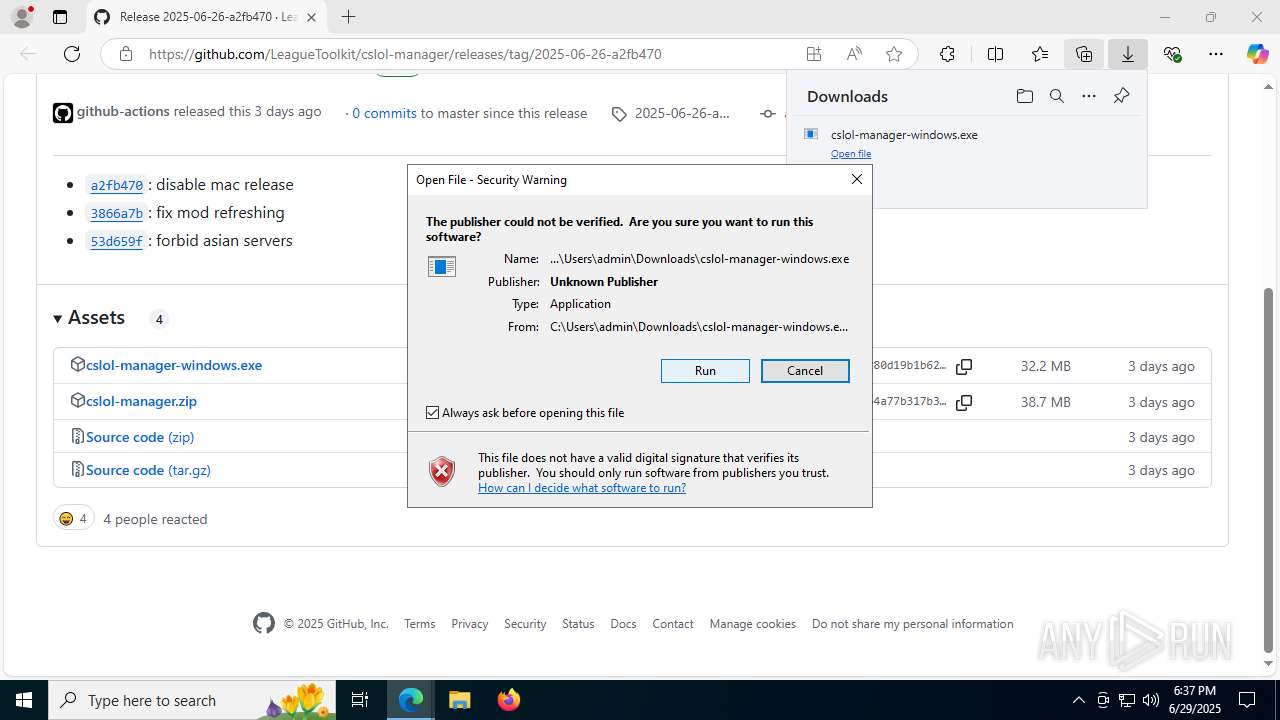
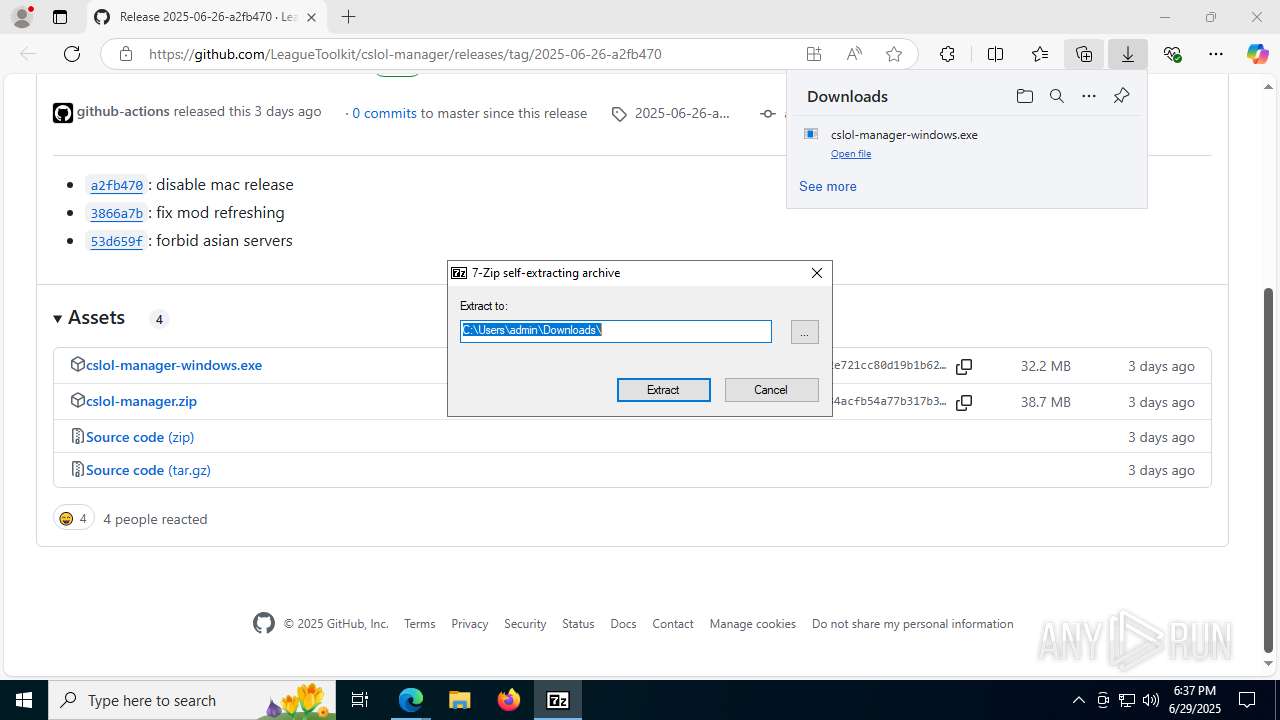
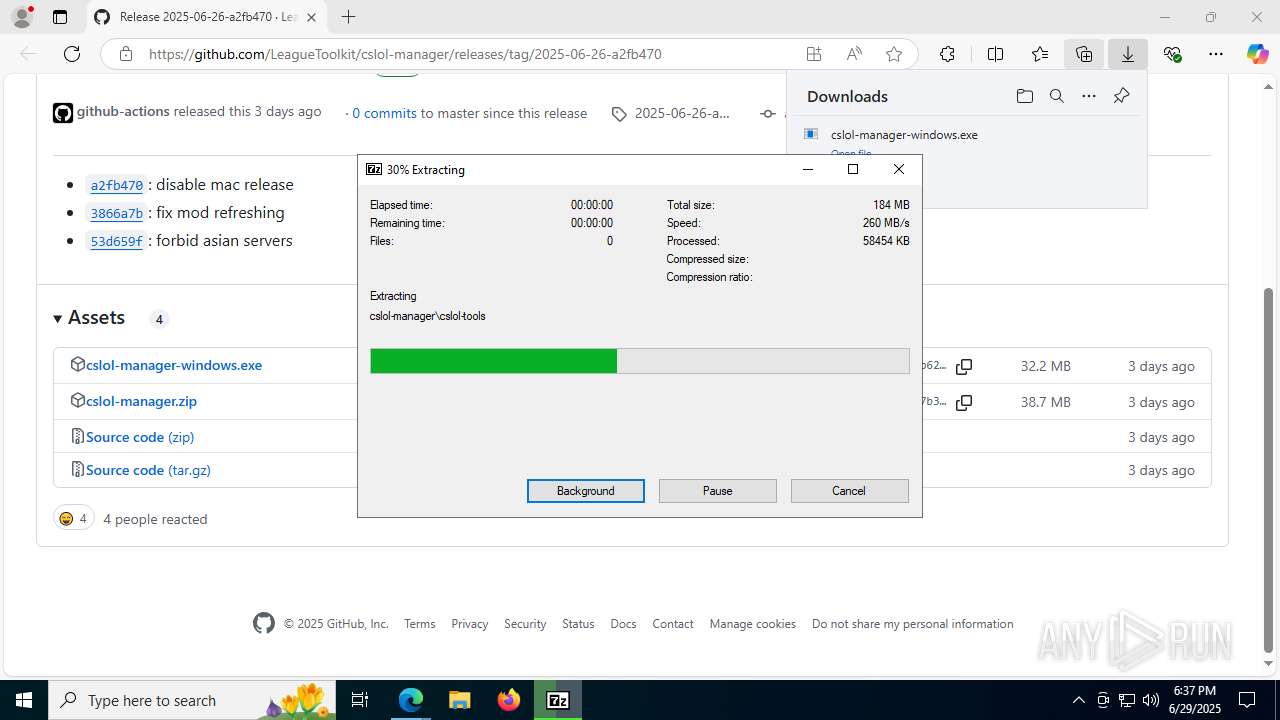
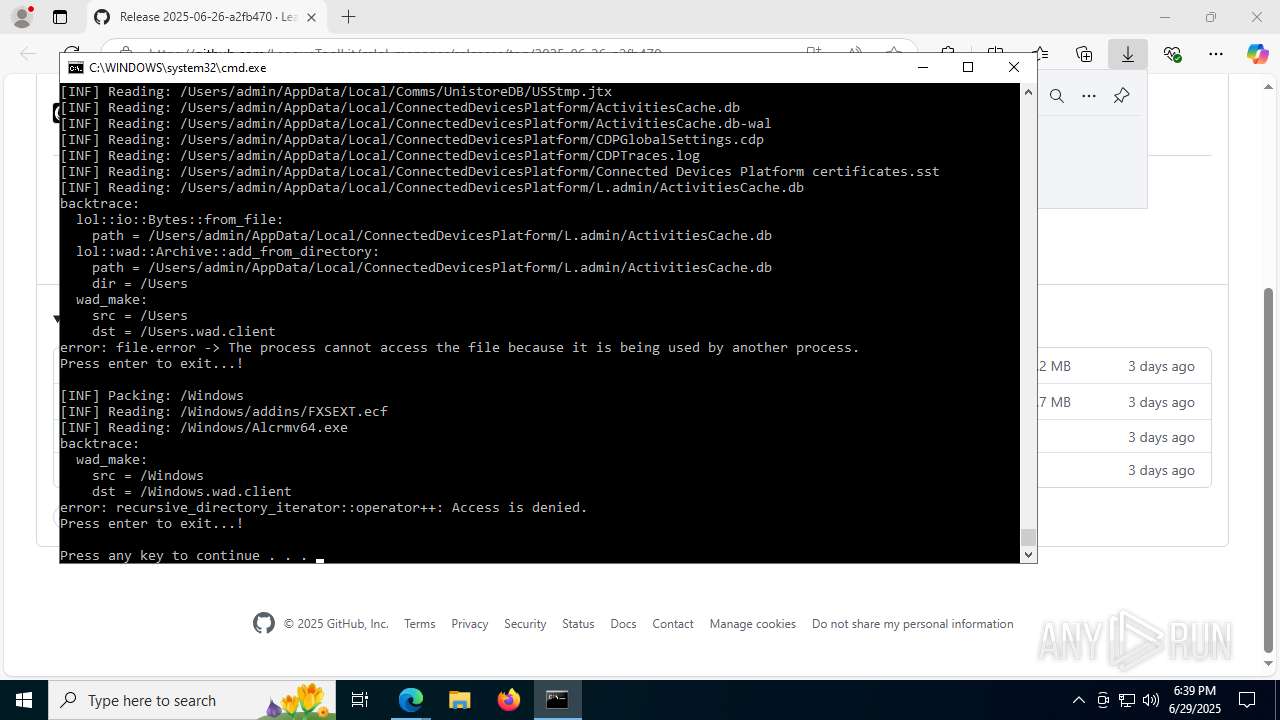
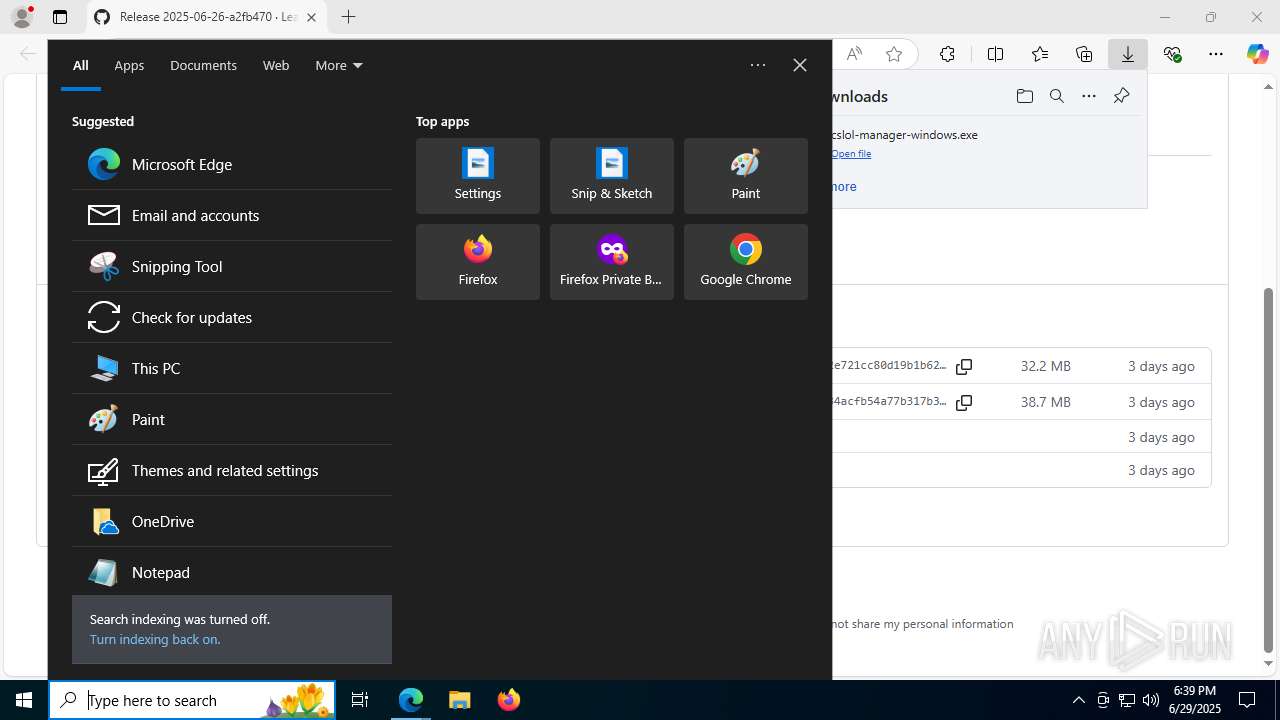
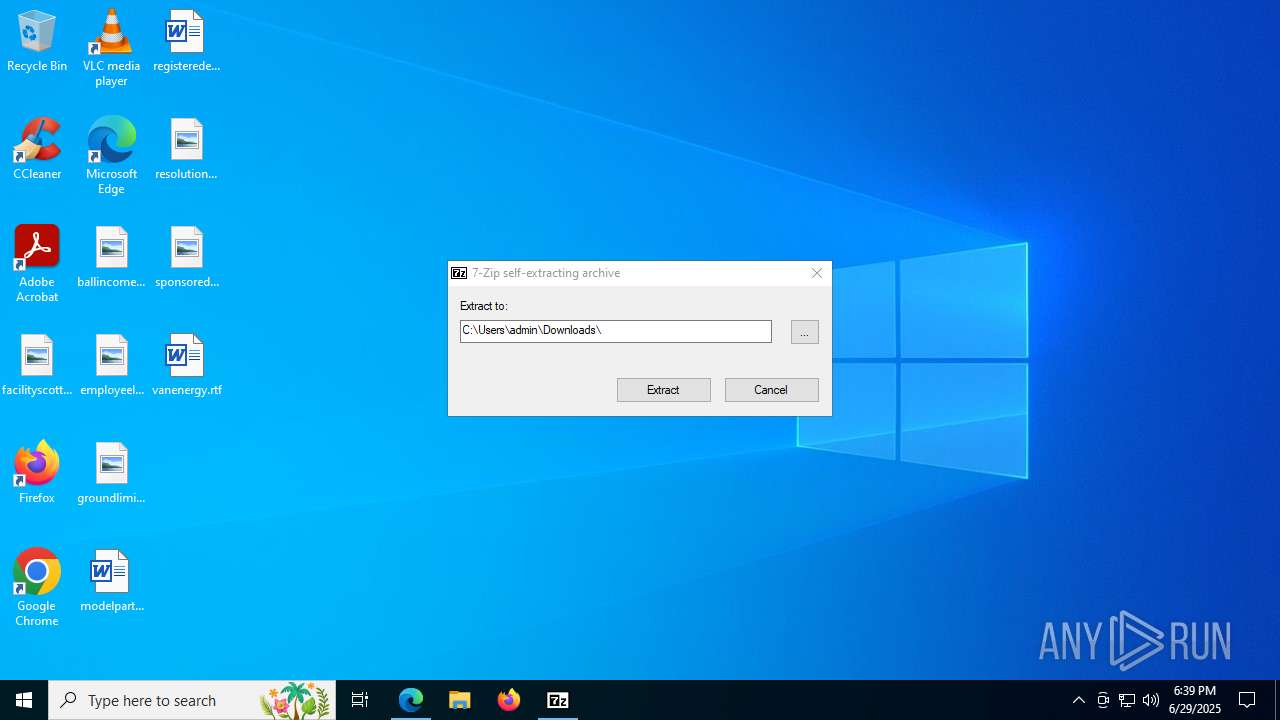
Drops 7-zip archiver for unpacking
- msedge.exe (PID: 5368)
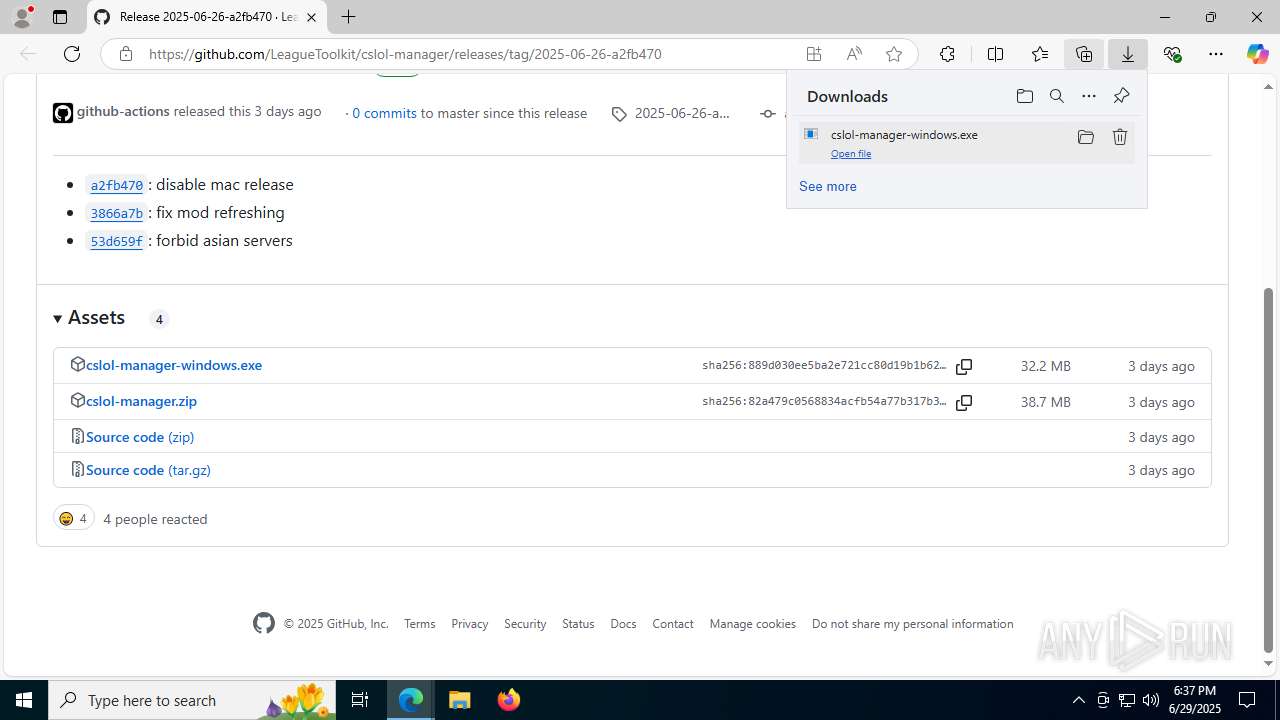
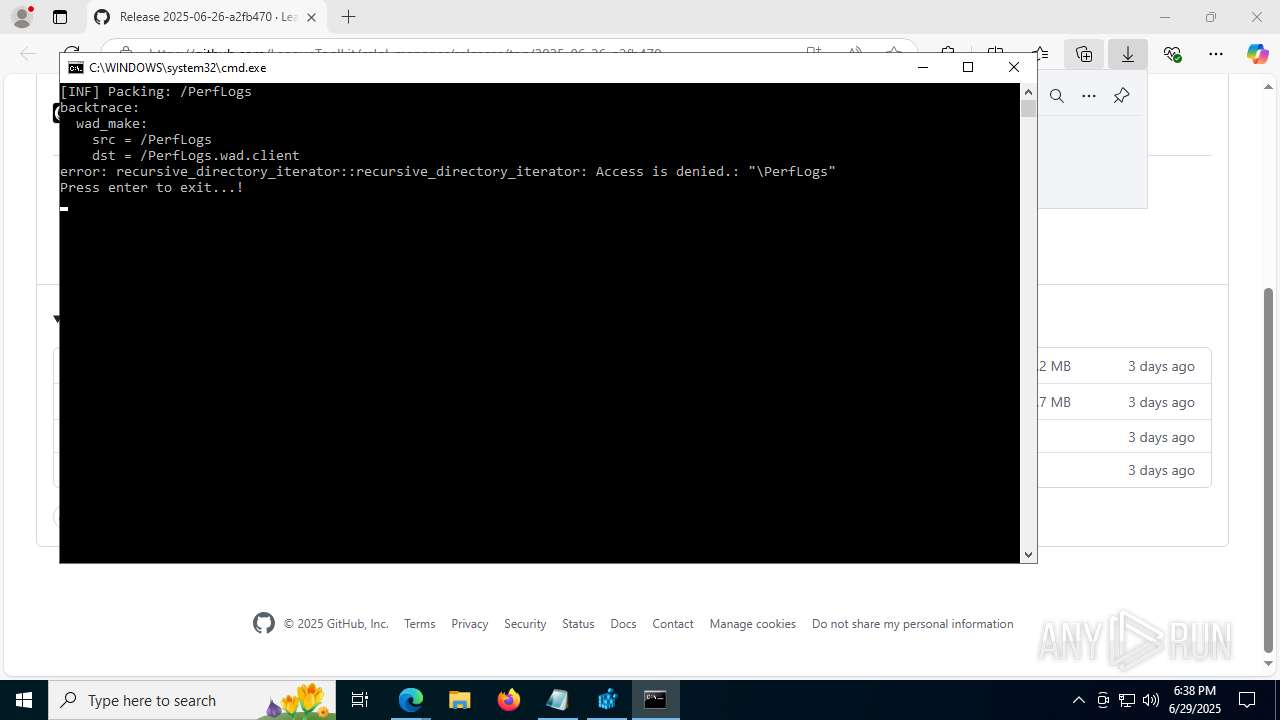
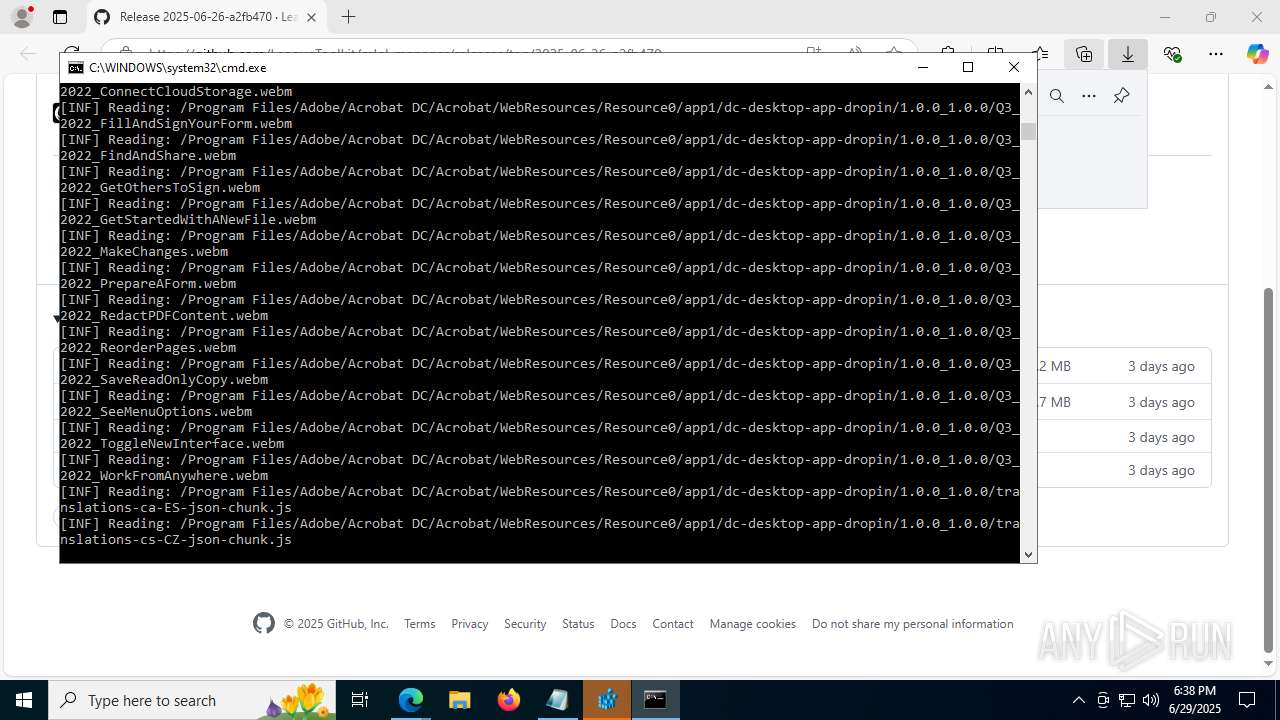
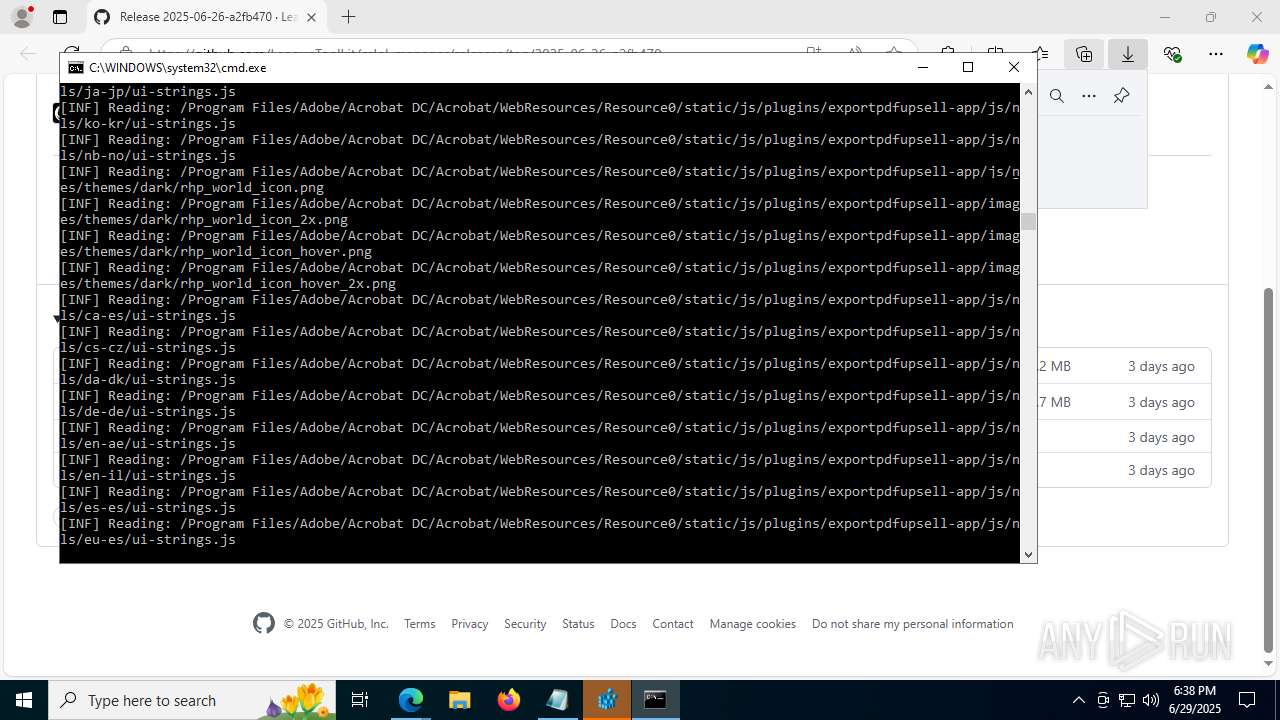
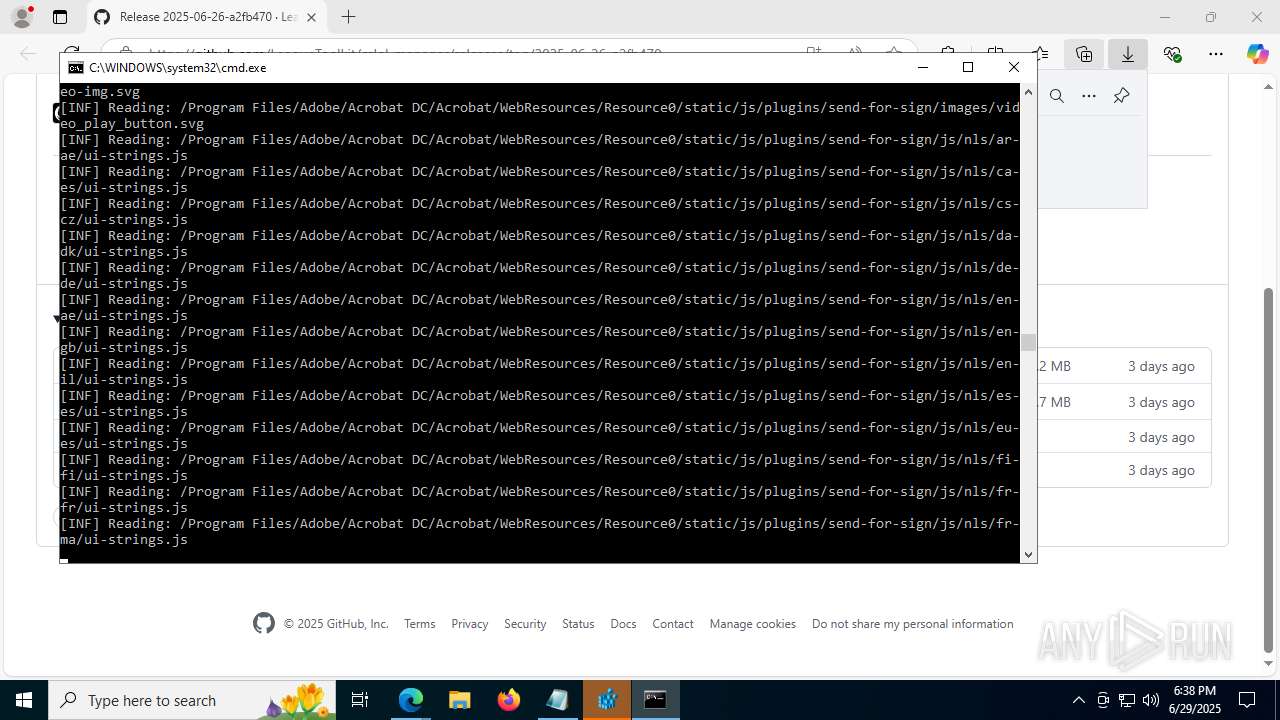
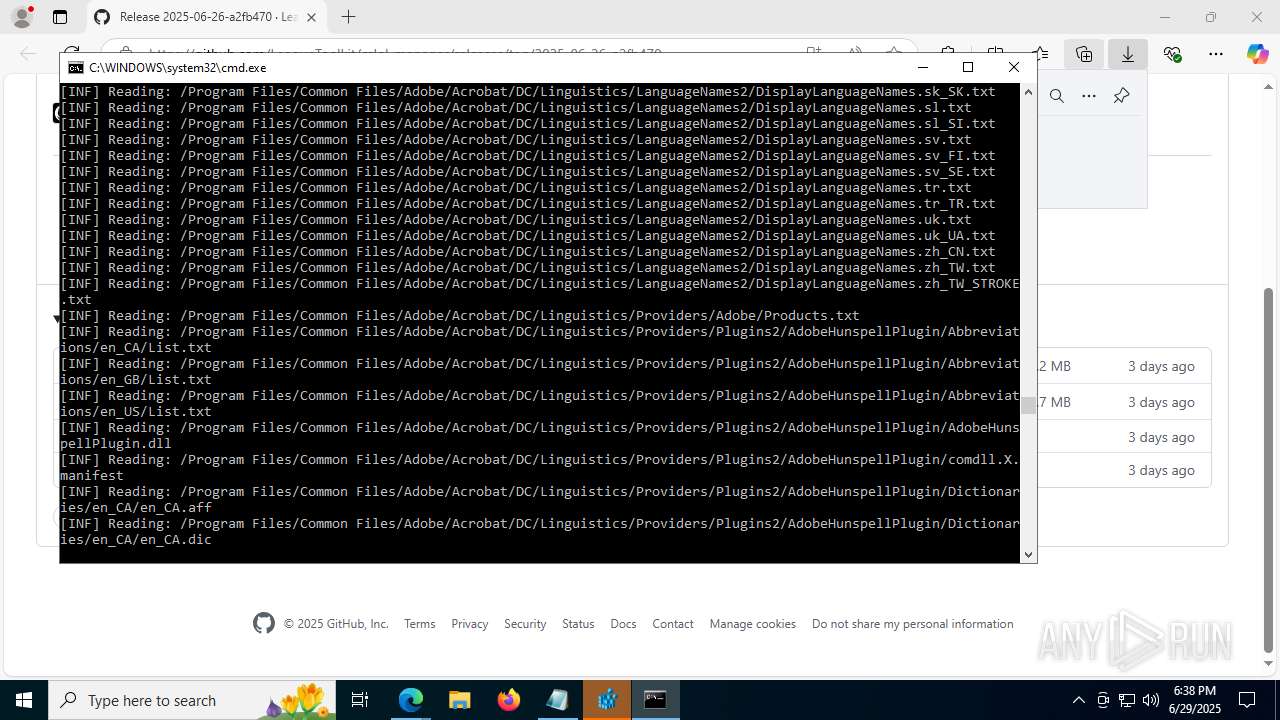
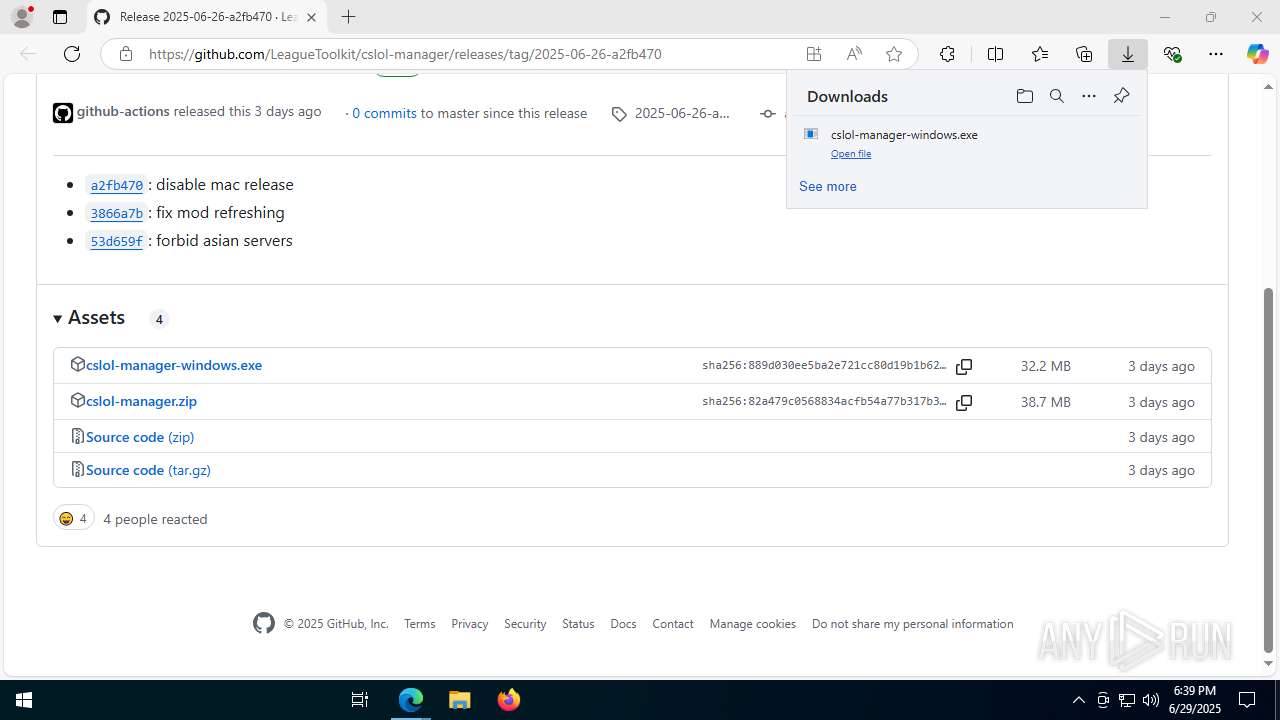
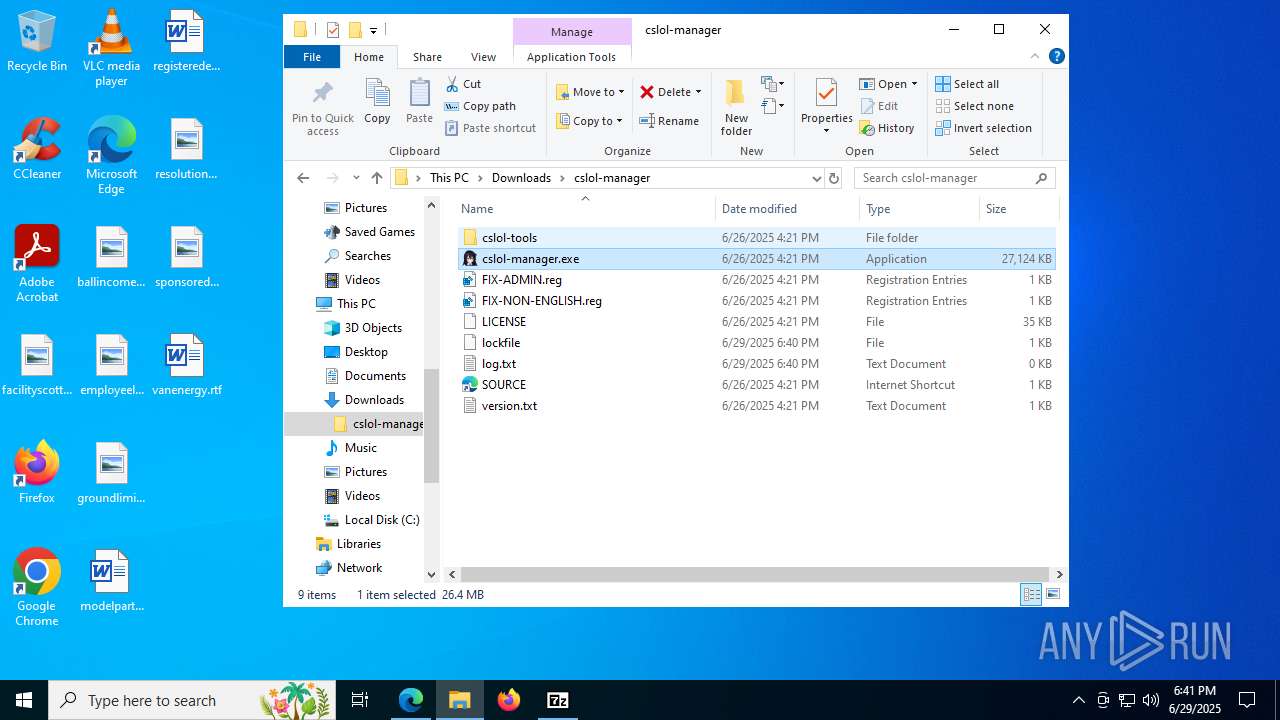
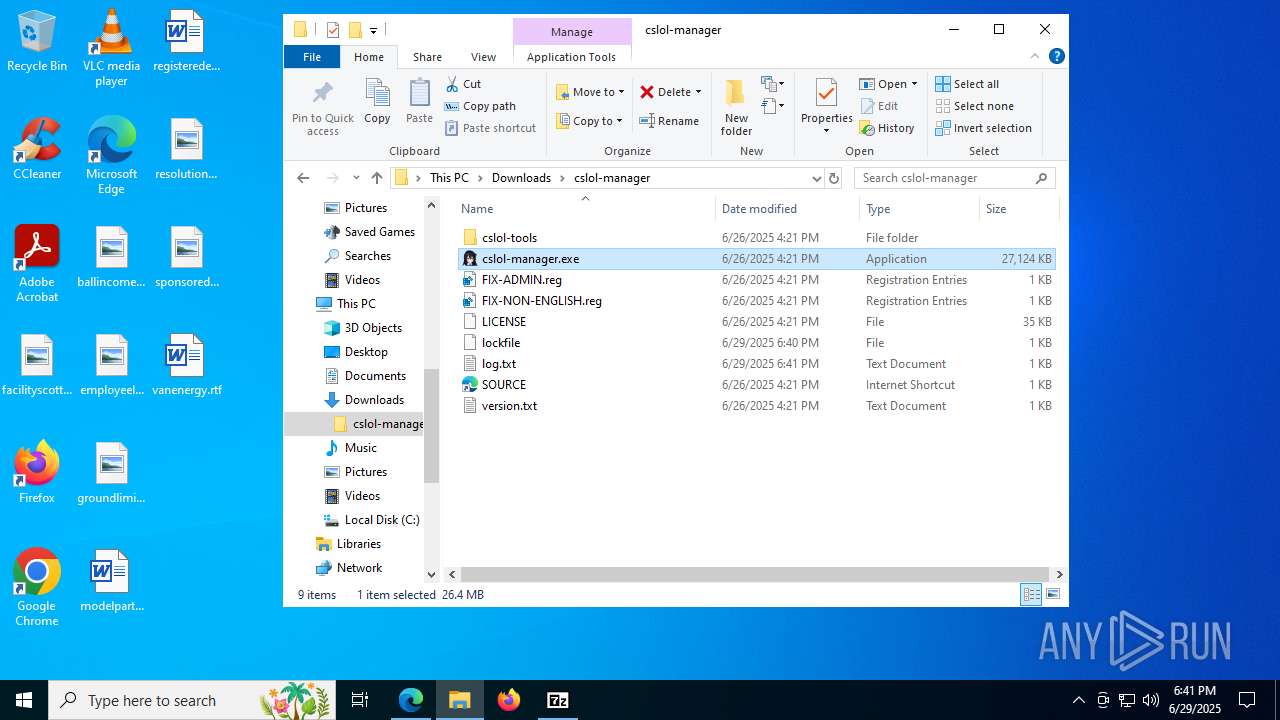
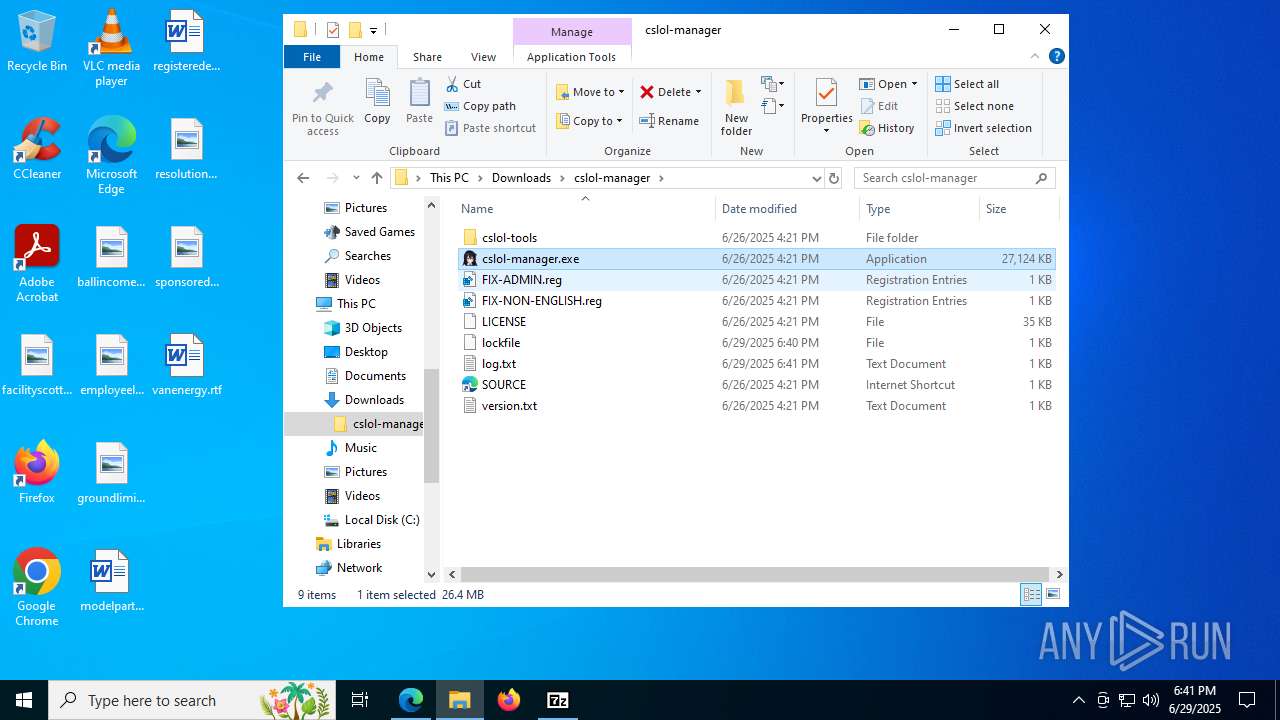
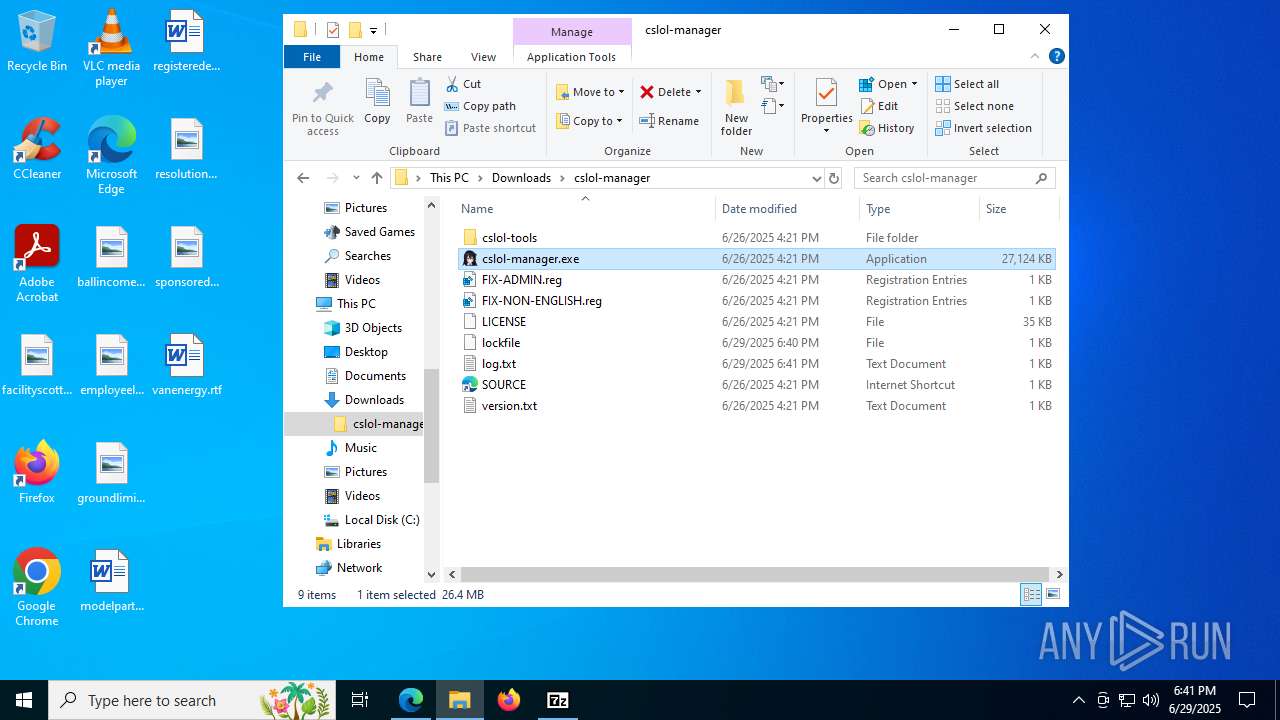
Executable content was dropped or overwritten
- cslol-manager-windows.exe (PID: 7868)
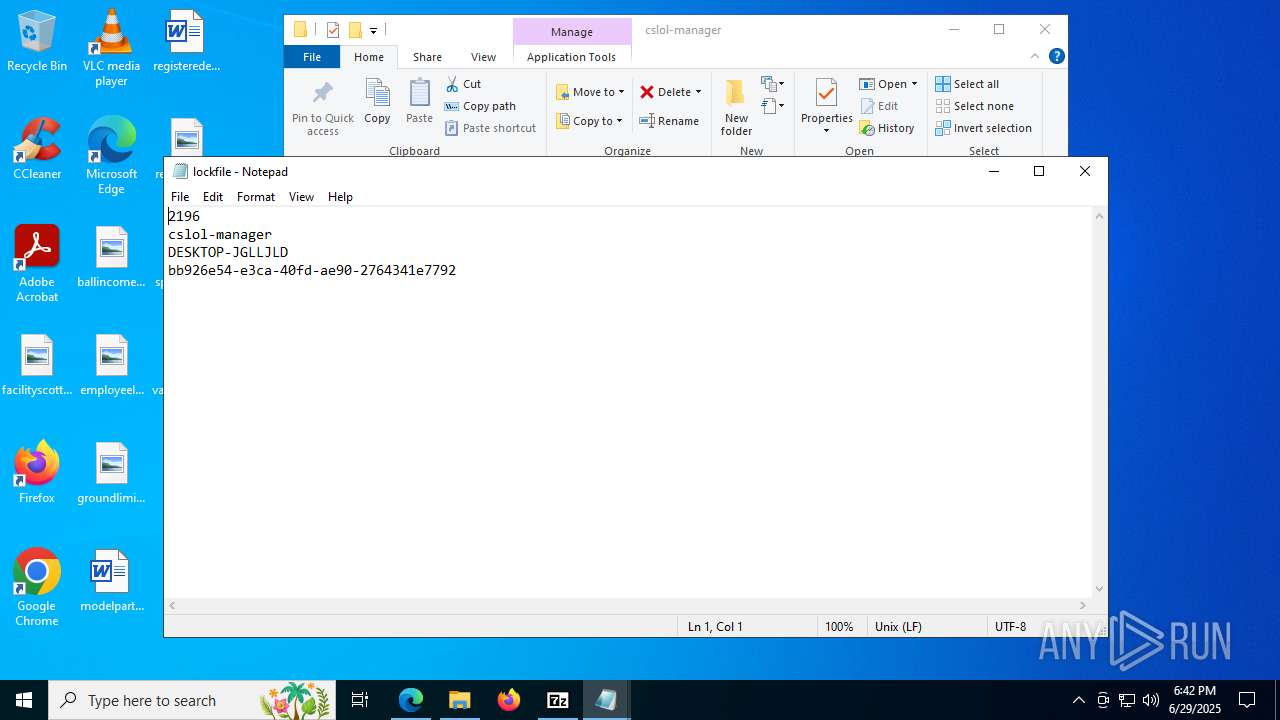
Detected use of alternative data streams (AltDS)
- cslol-manager.exe (PID: 6348)
- cslol-manager.exe (PID: 7616)
- cslol-manager.exe (PID: 7428)
- cslol-manager.exe (PID: 2196)
- cslol-manager.exe (PID: 1752)
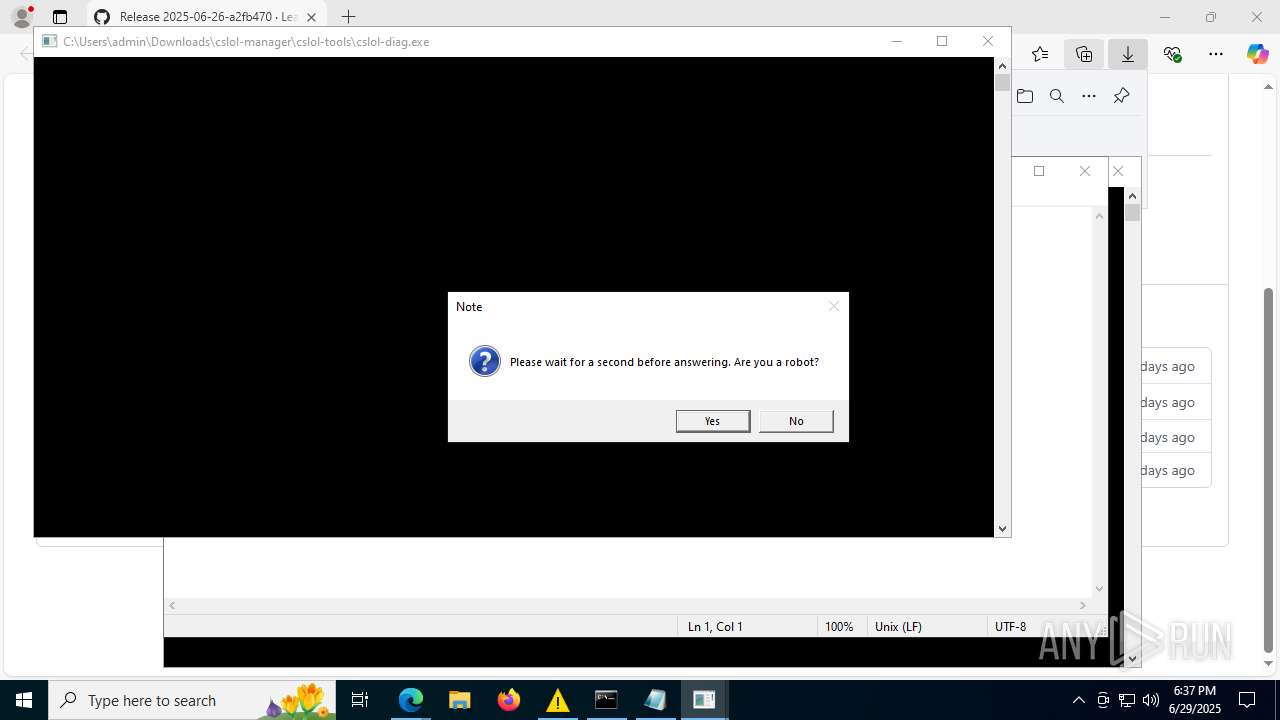
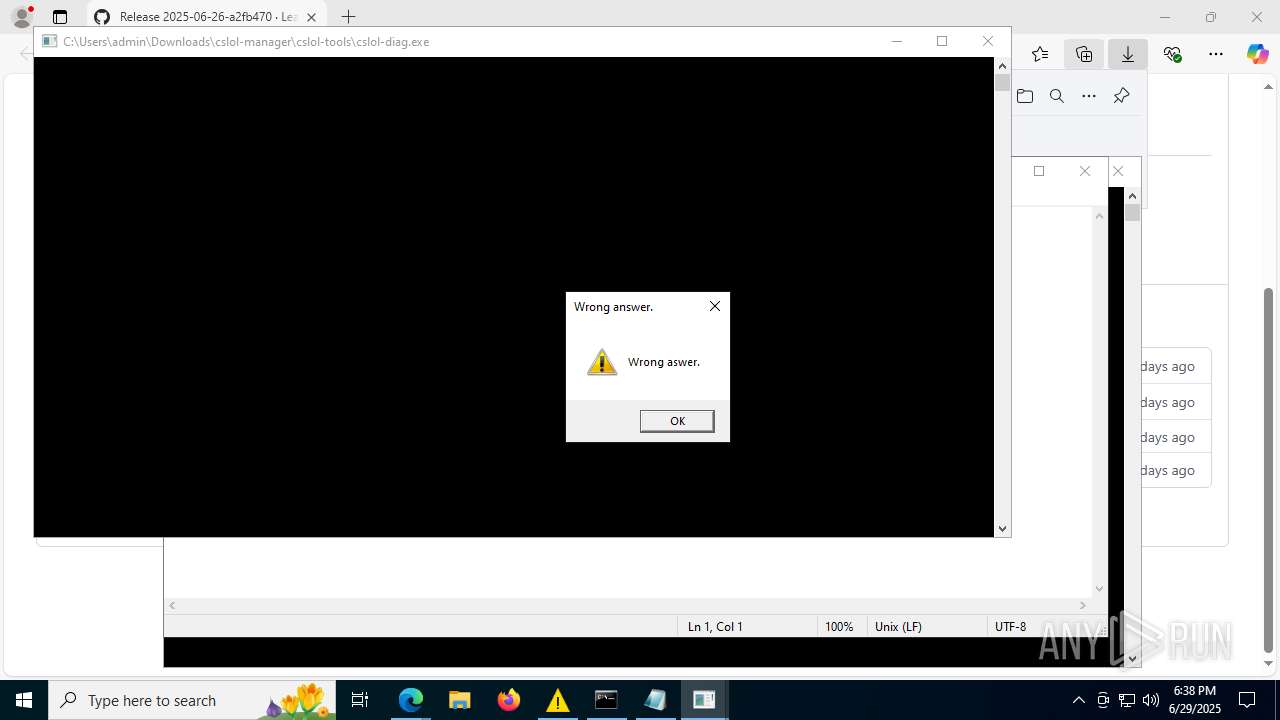
Reads security settings of Internet Explorer
- cslol-diag.exe (PID: 7796)
- ShellExperienceHost.exe (PID: 6352)
- cslol-diag.exe (PID: 8176)
- cslol-diag.exe (PID: 7528)
- cslol-diag.exe (PID: 7472)
- cslol-diag.exe (PID: 5652)
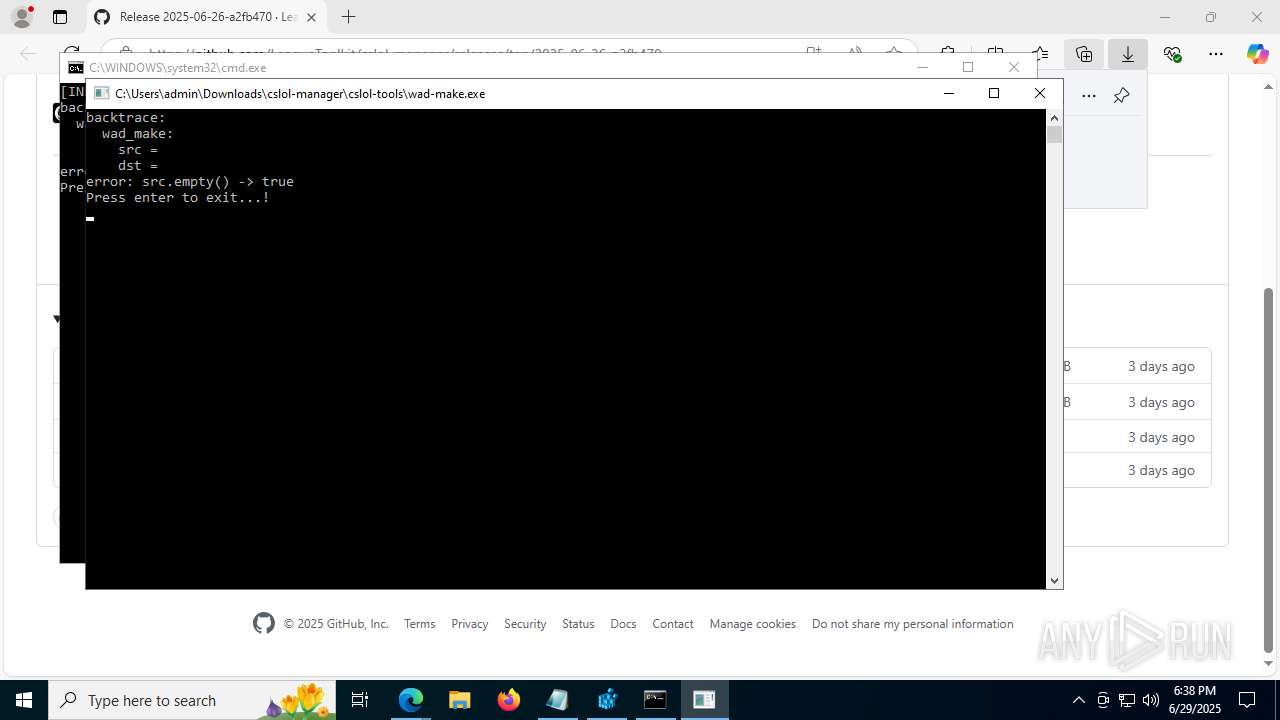
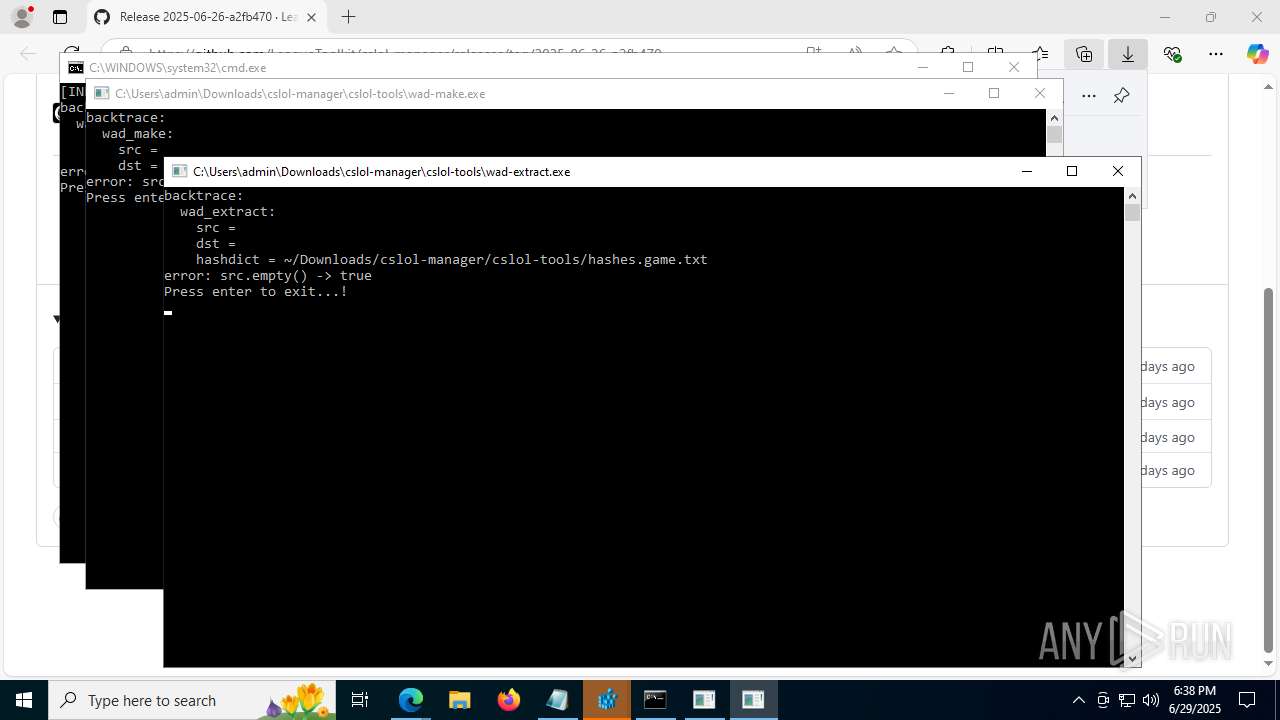
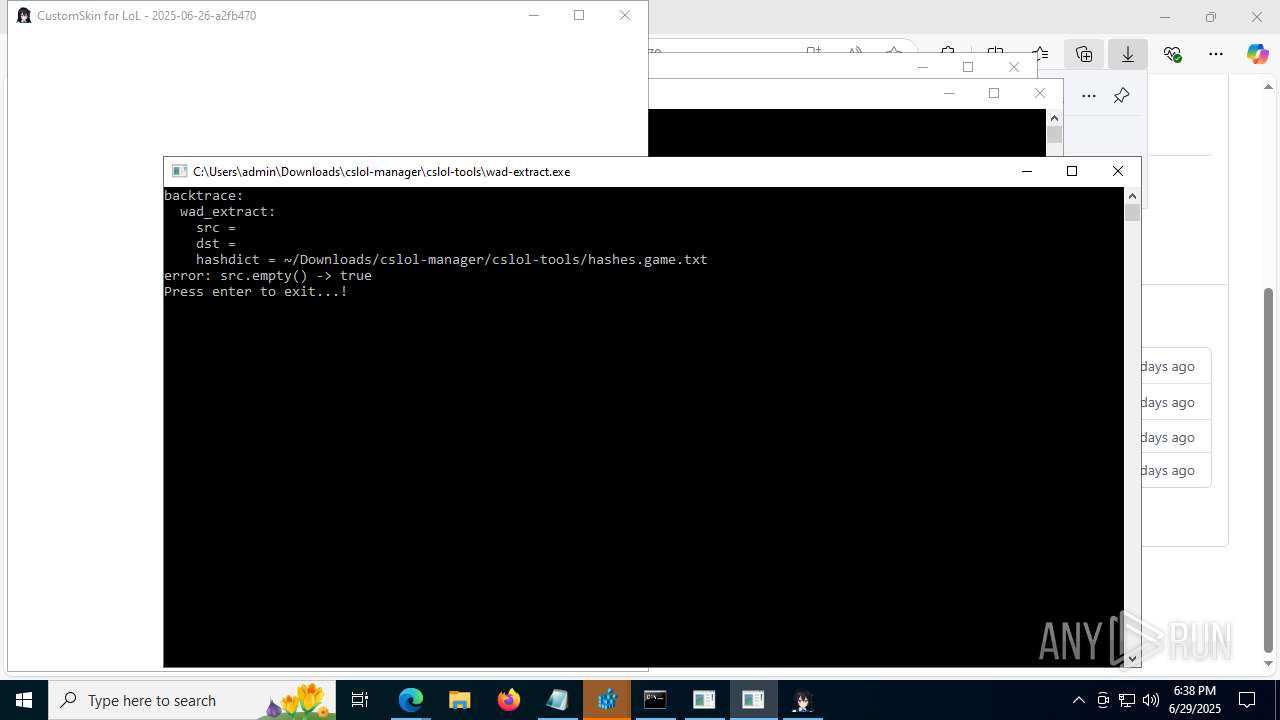
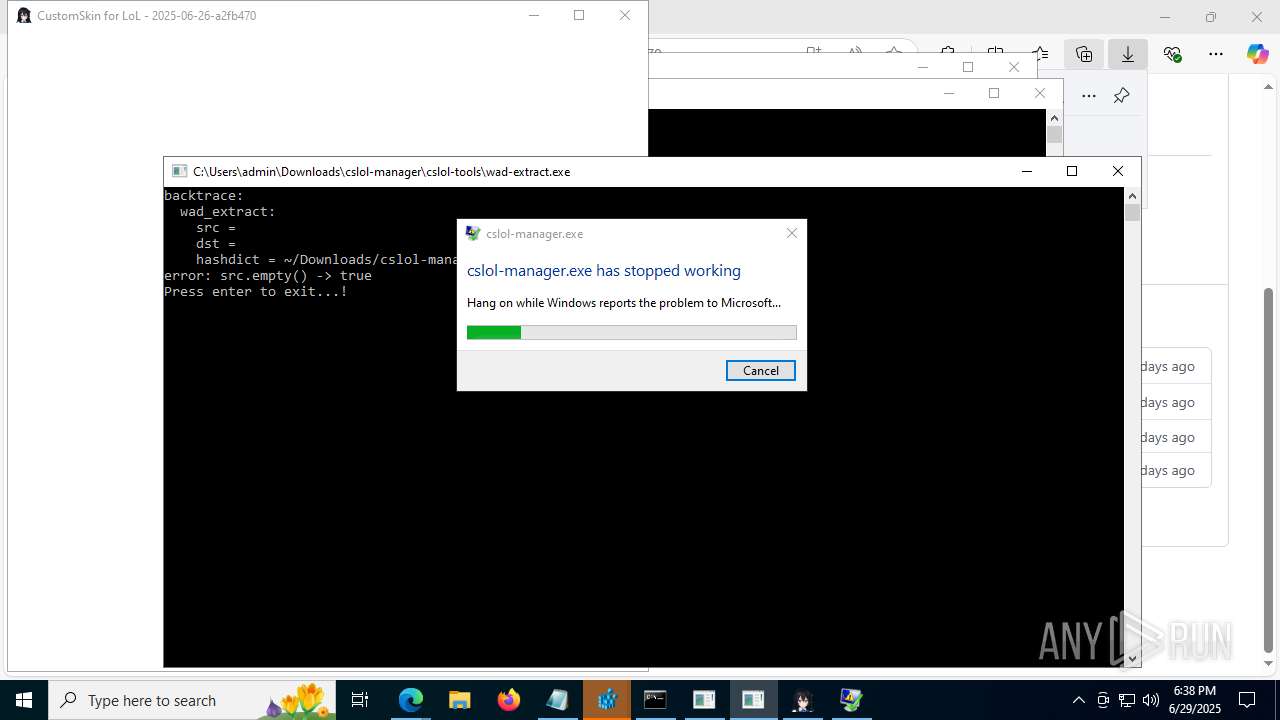
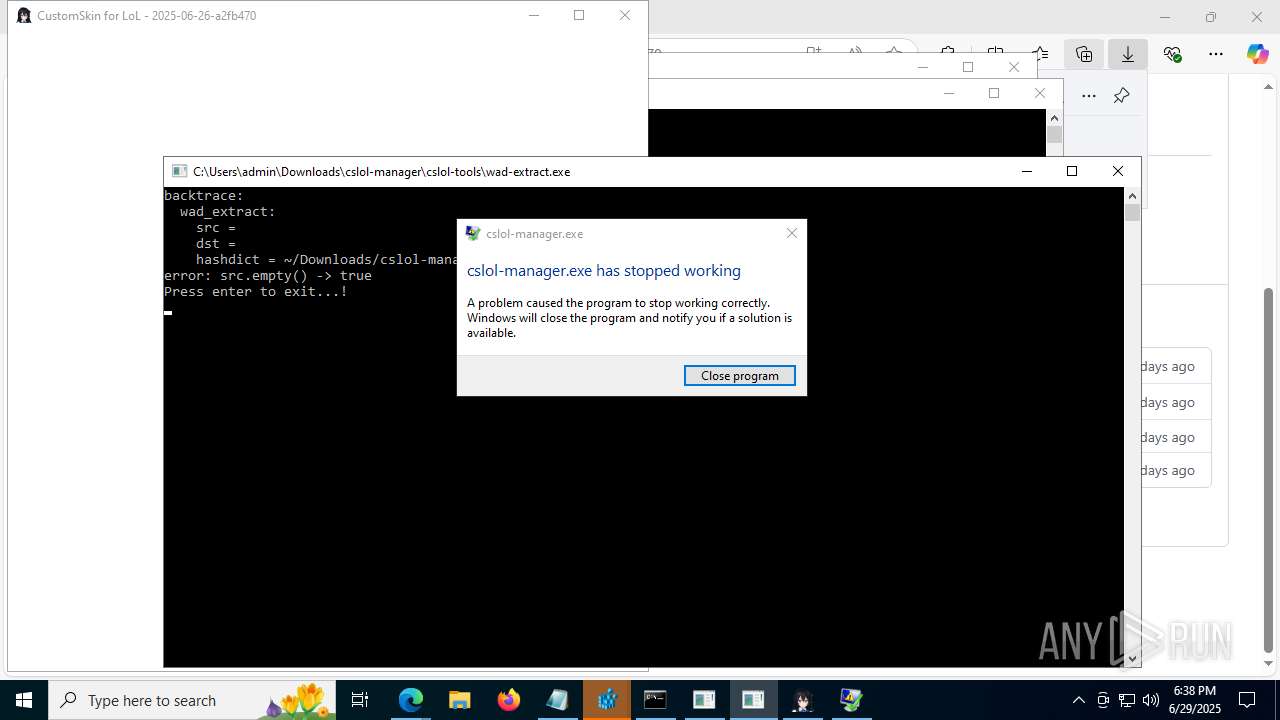
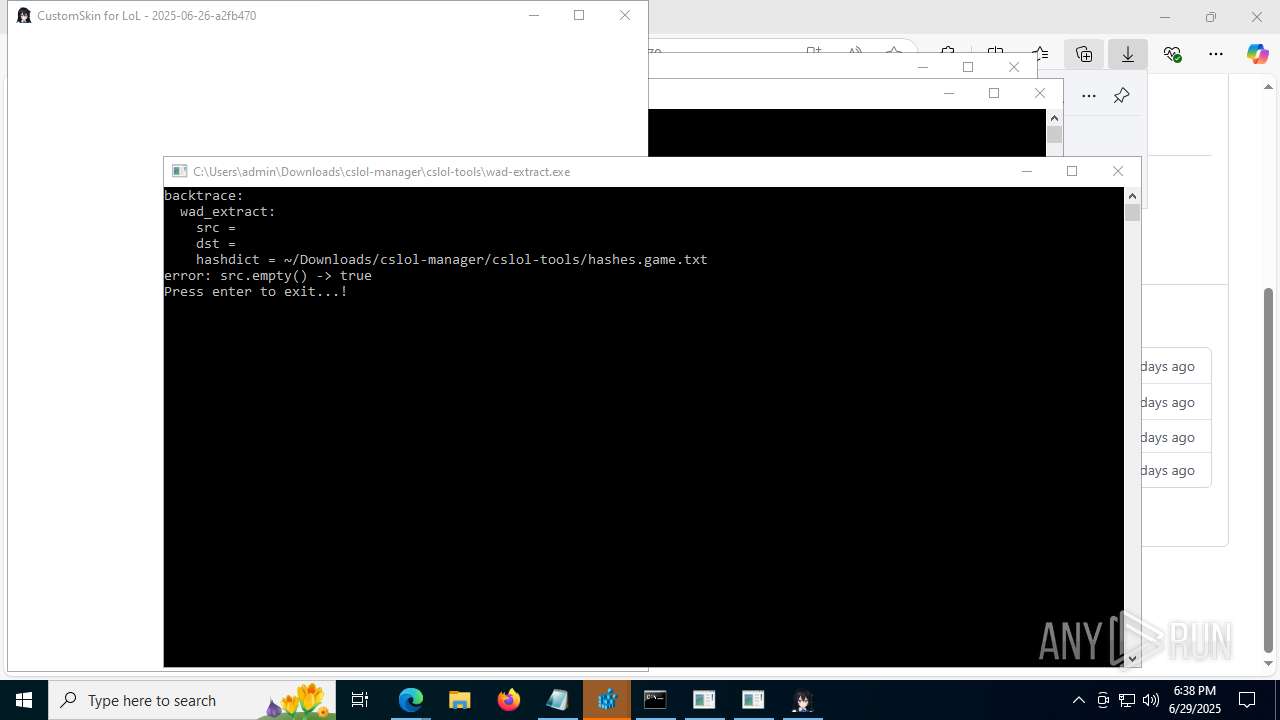
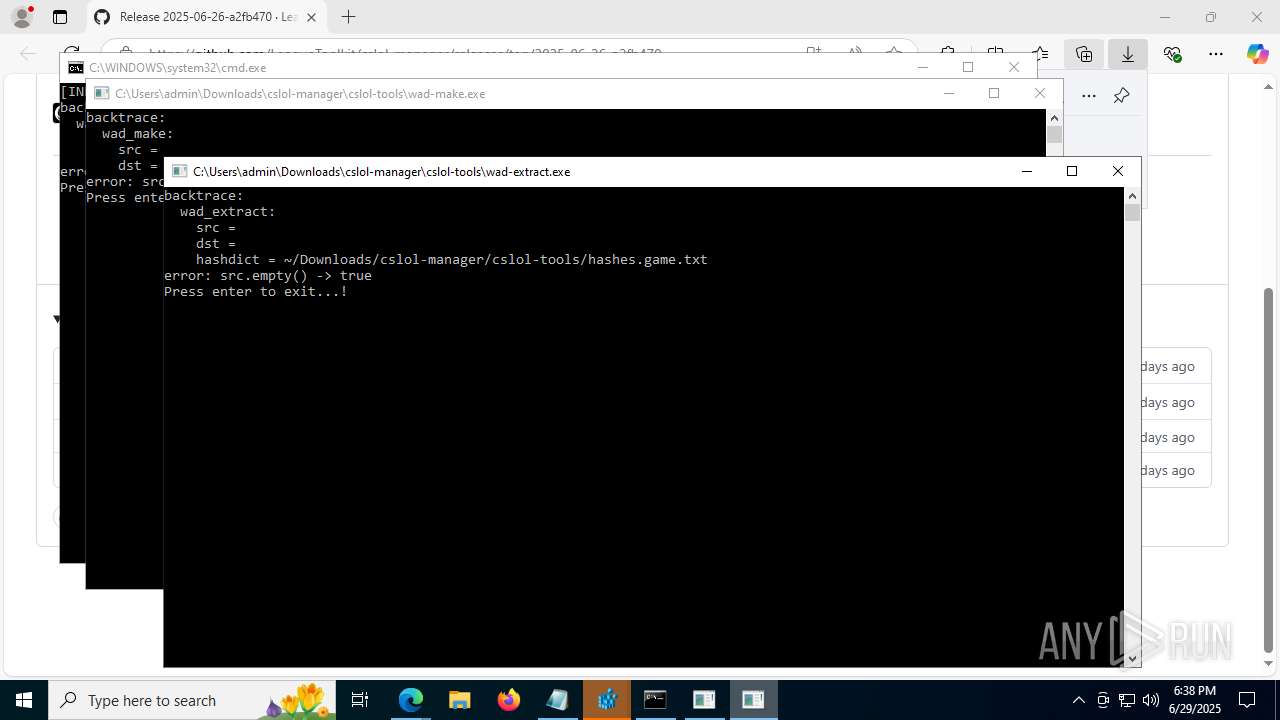
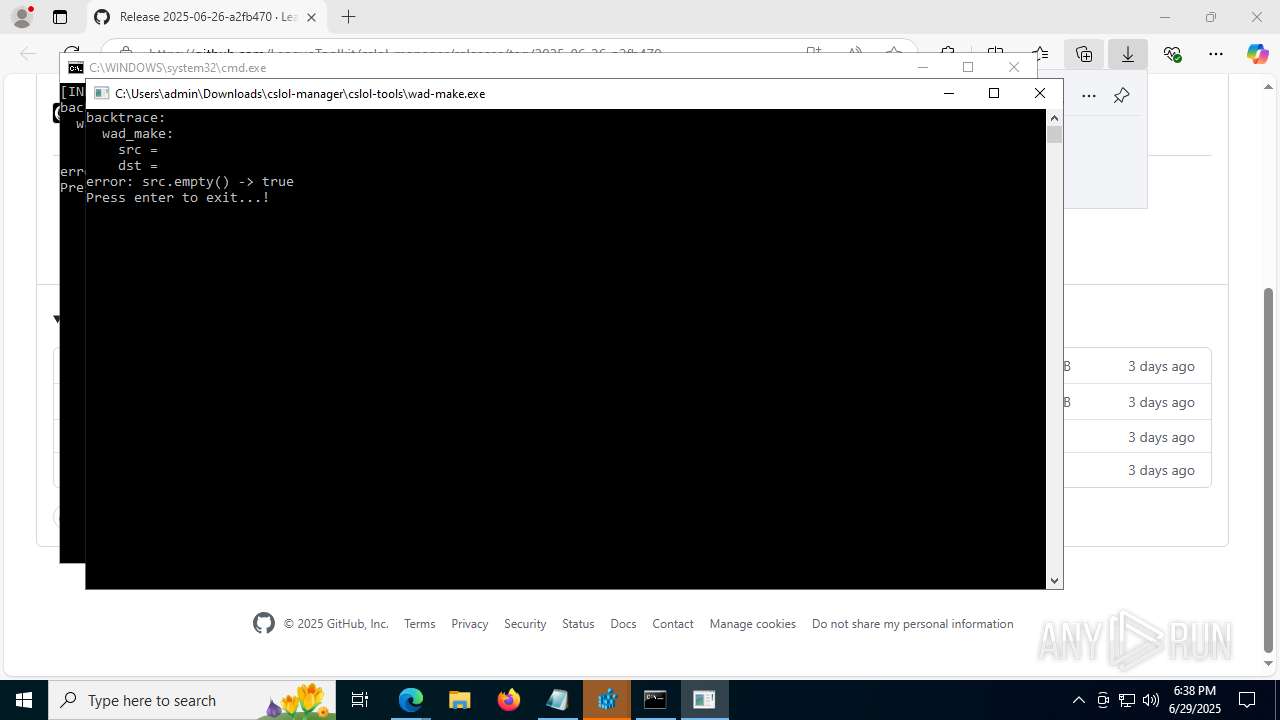
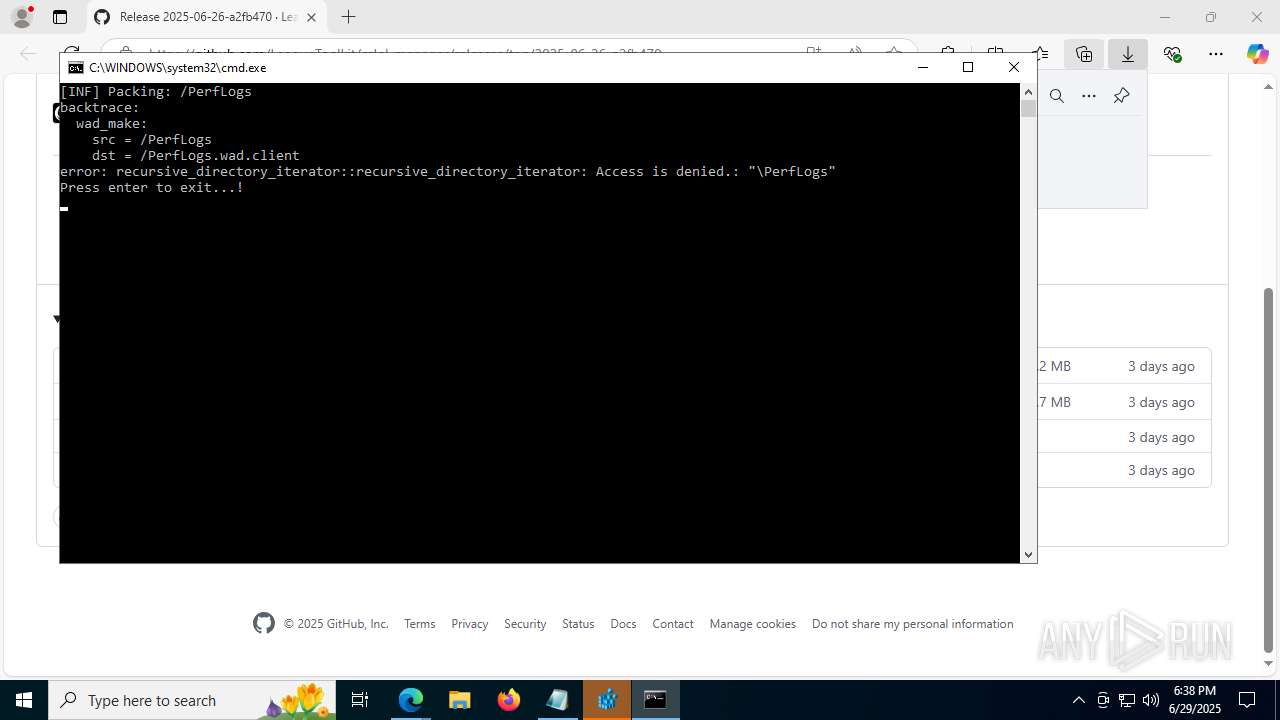
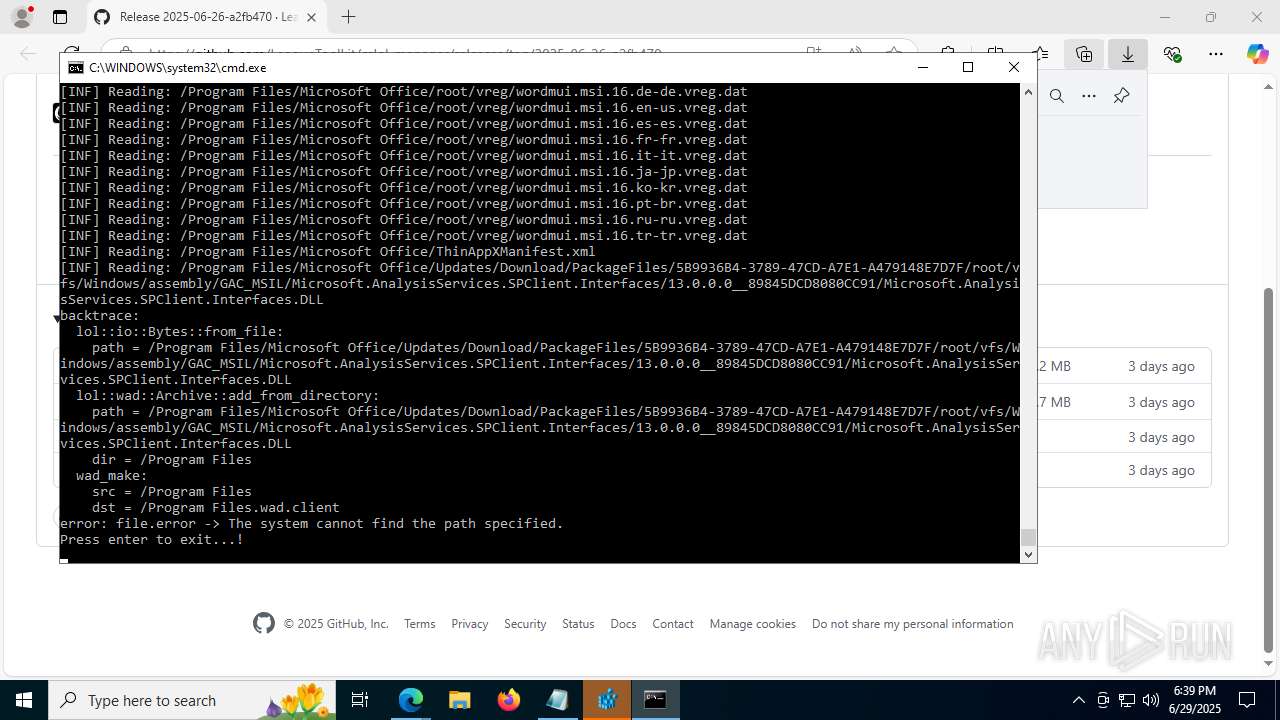
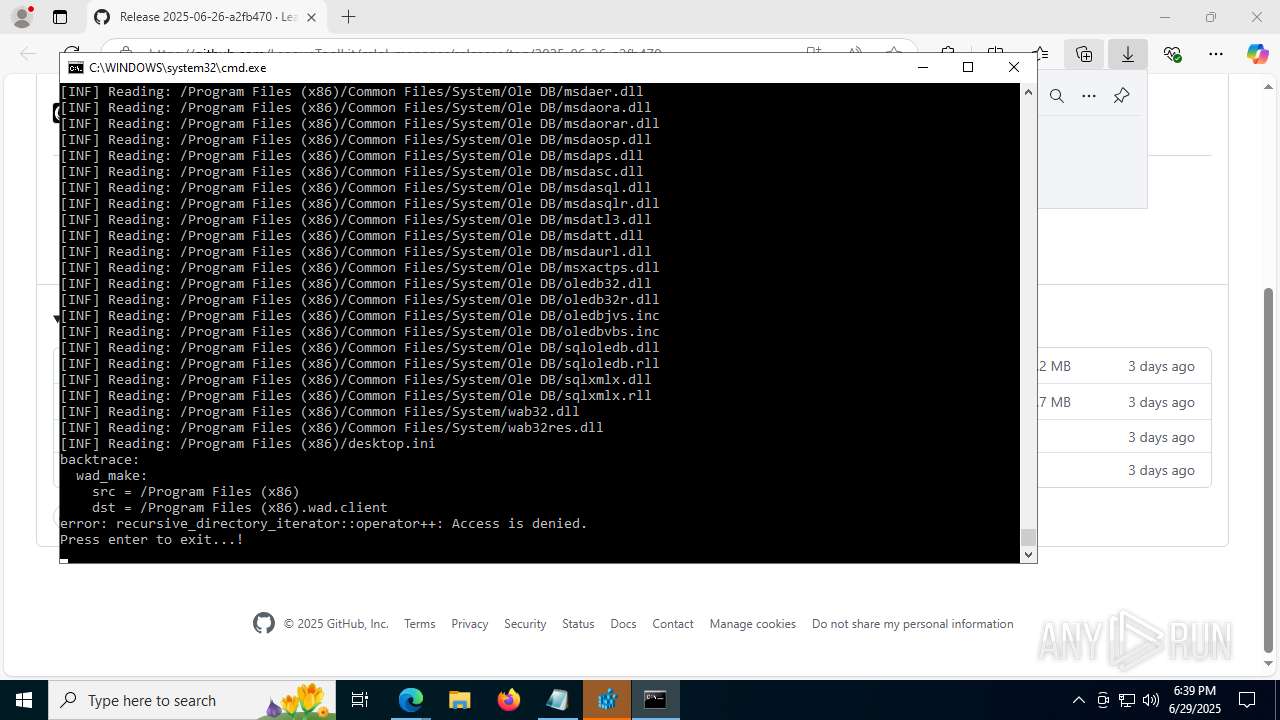
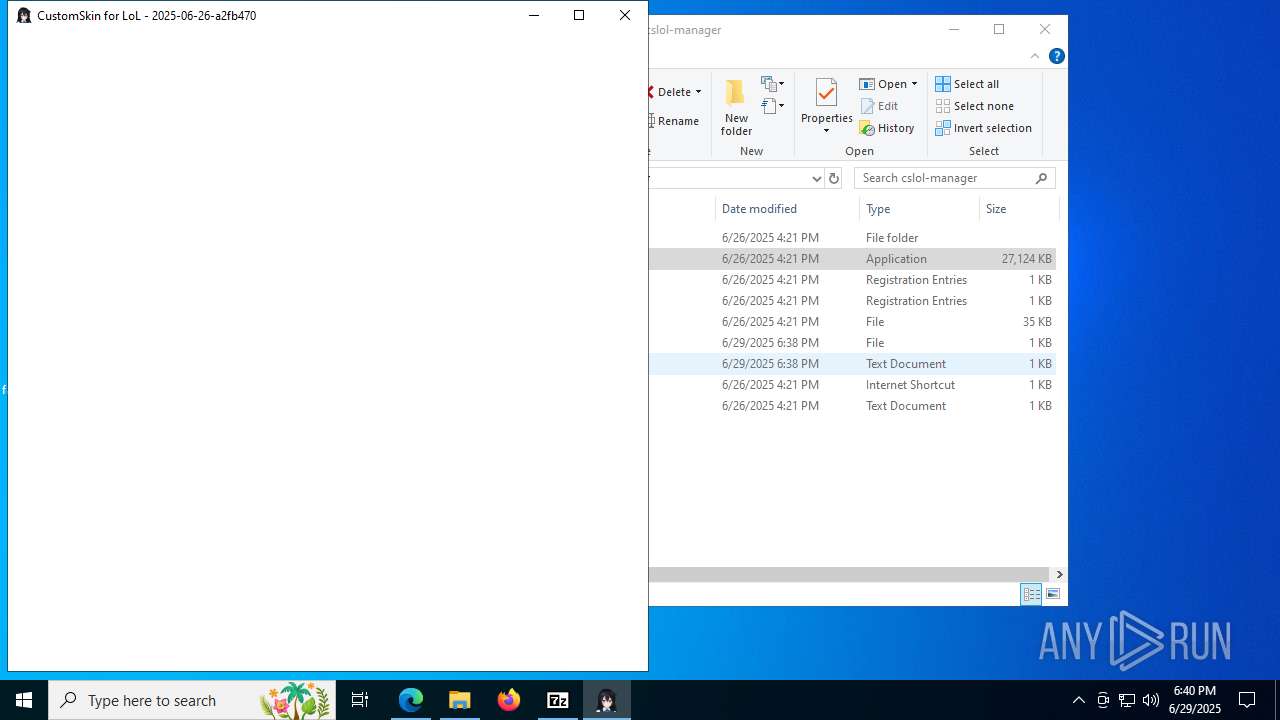
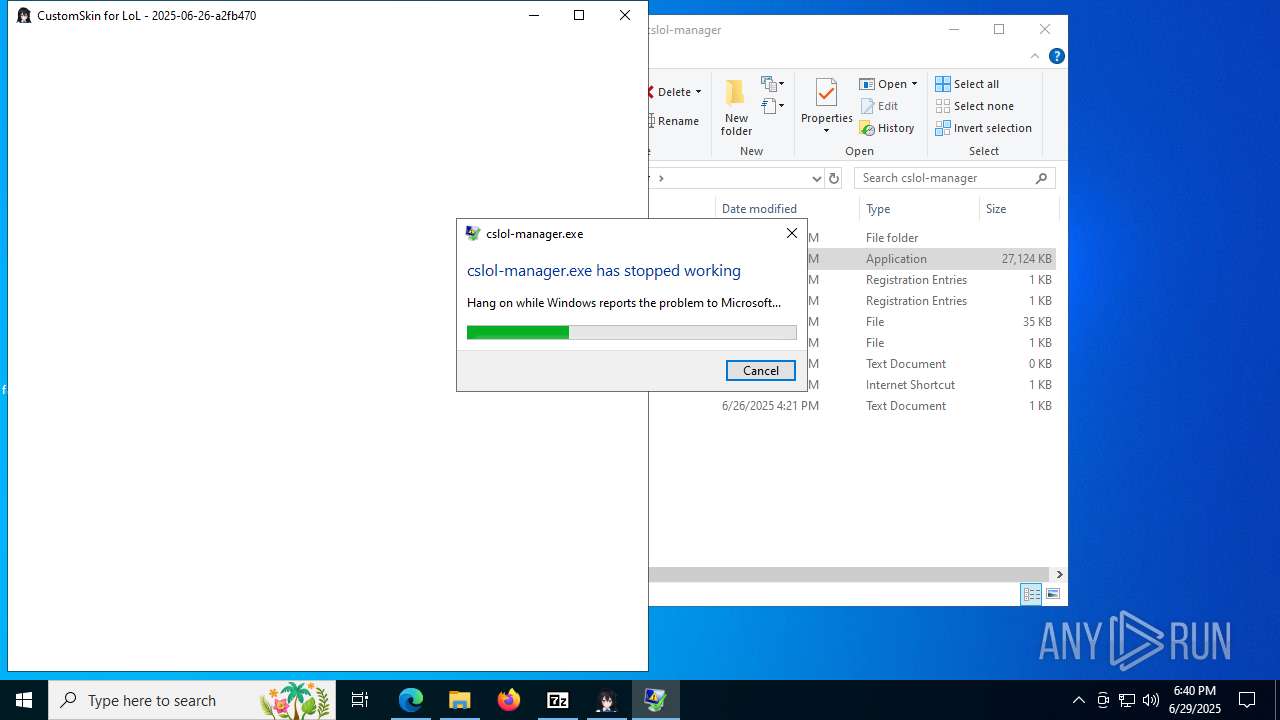
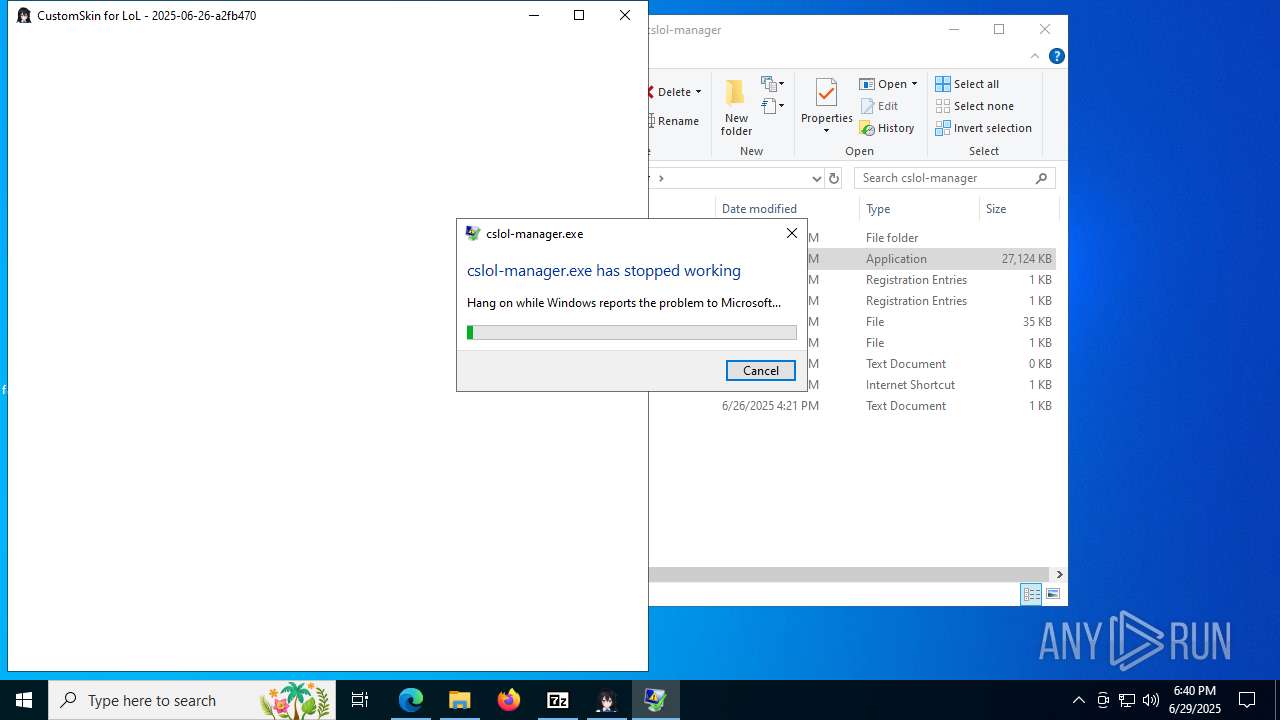
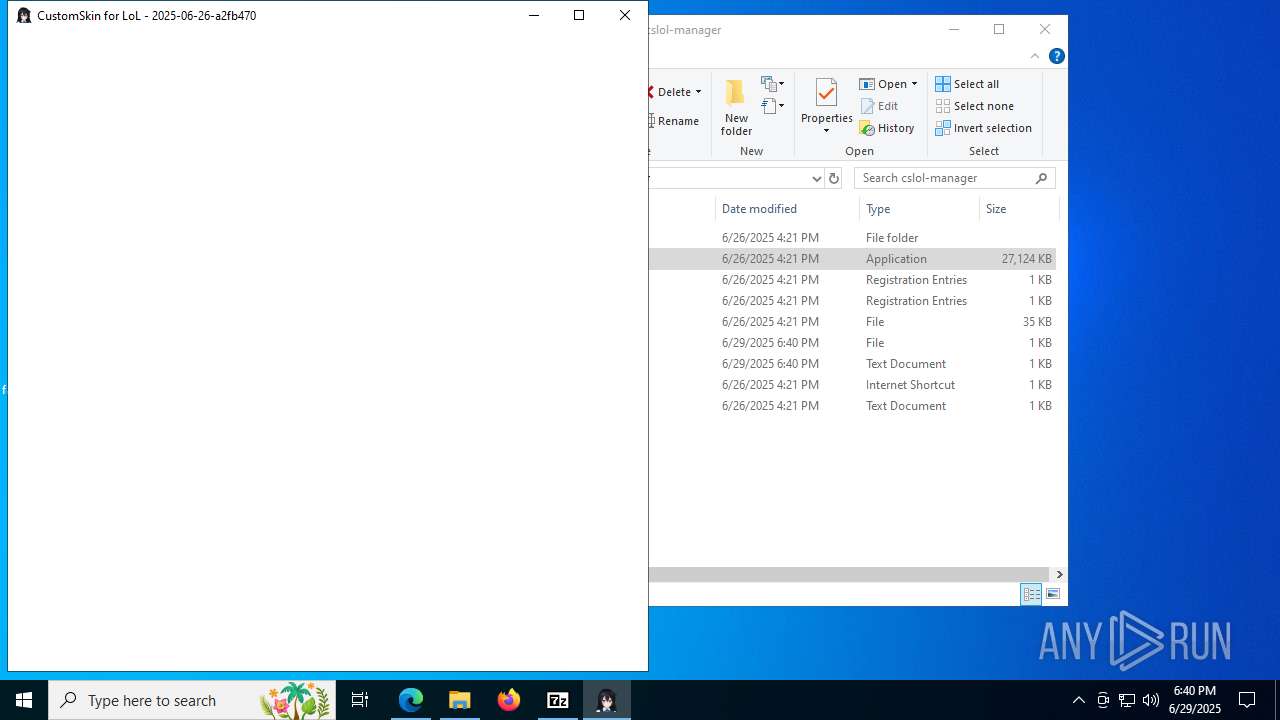
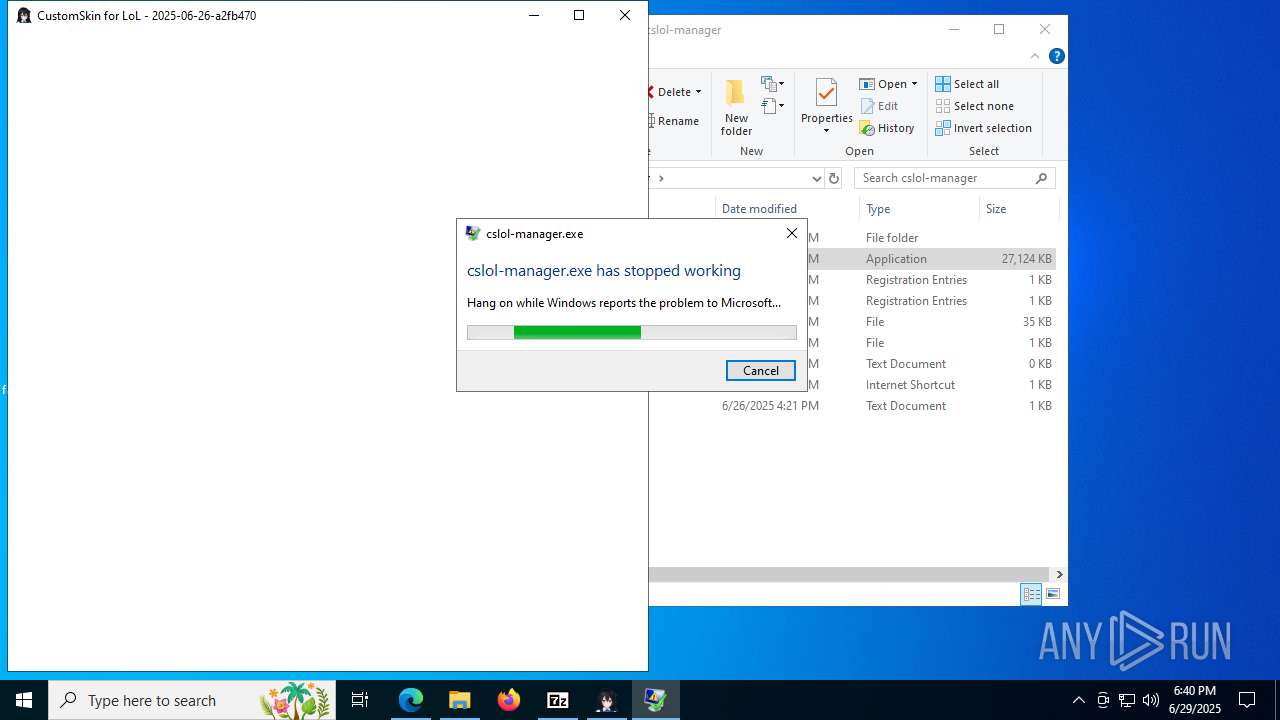
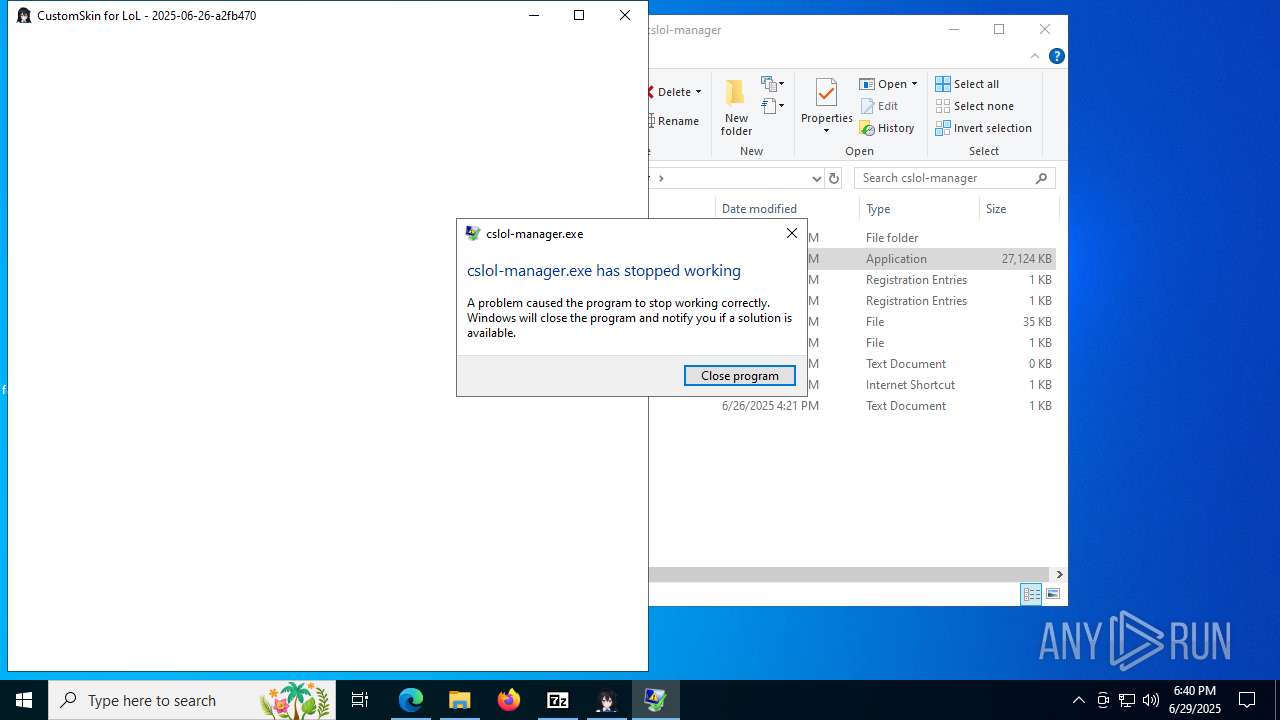
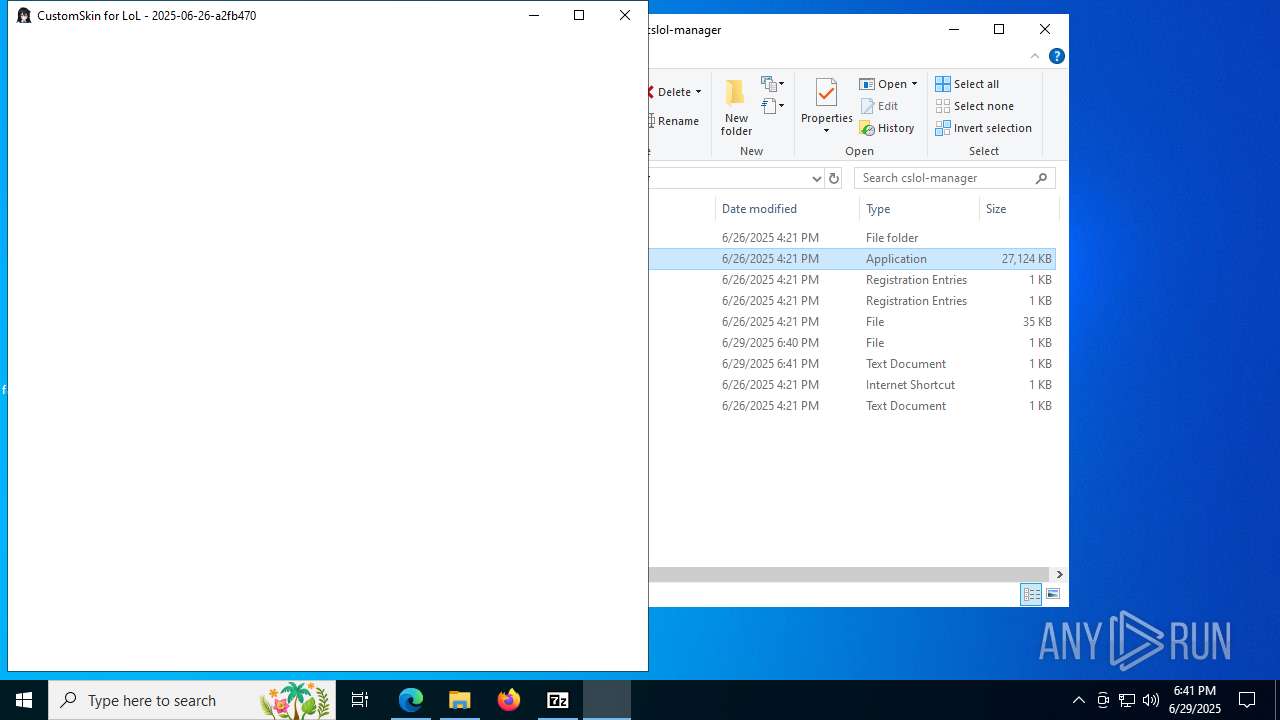
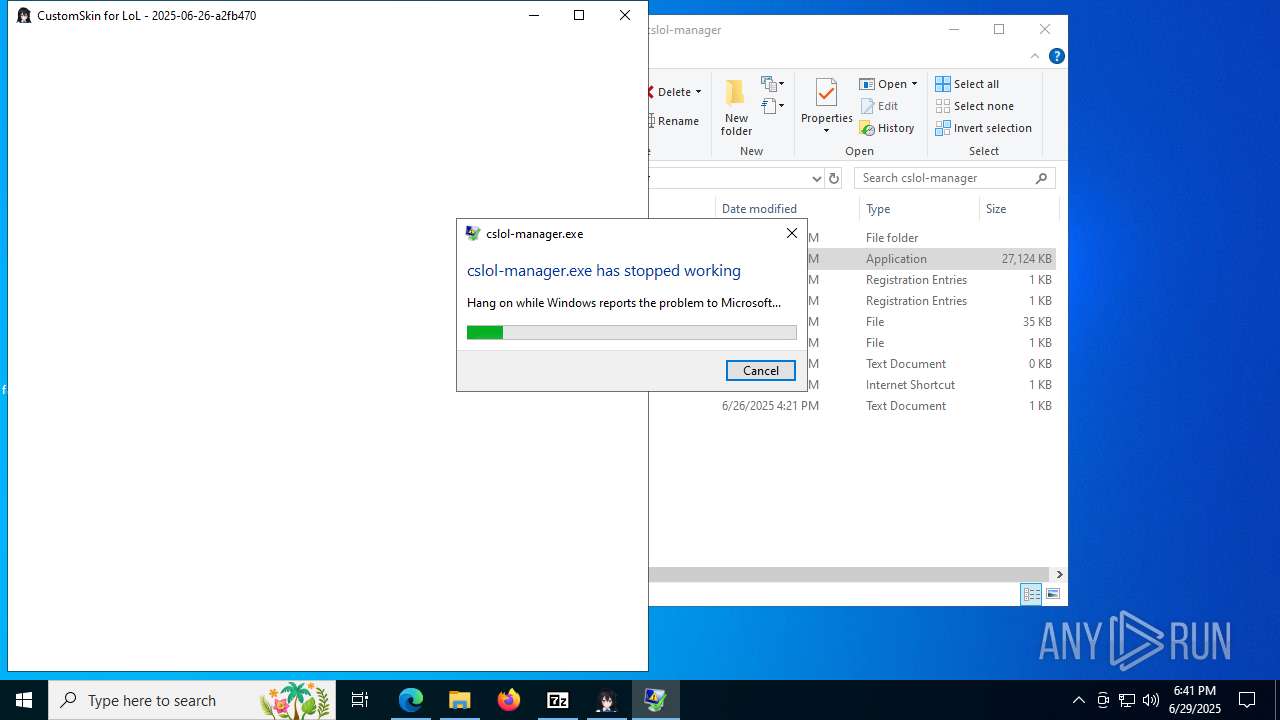
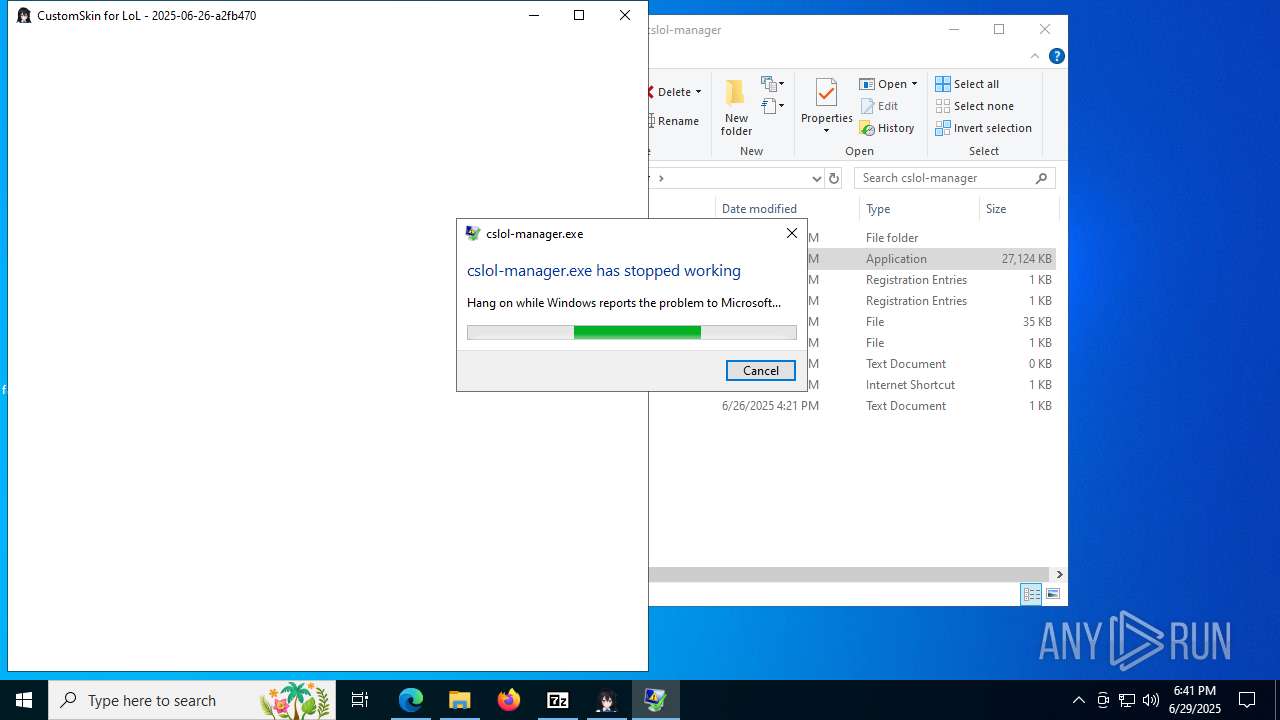
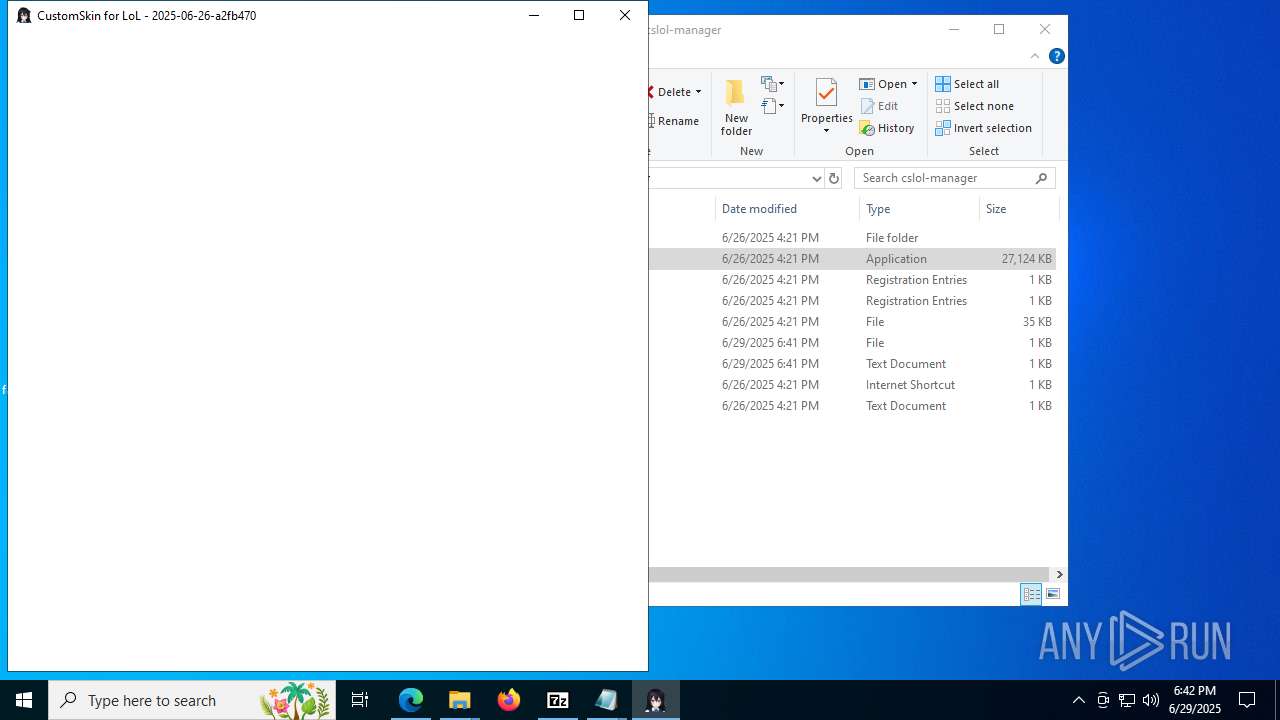
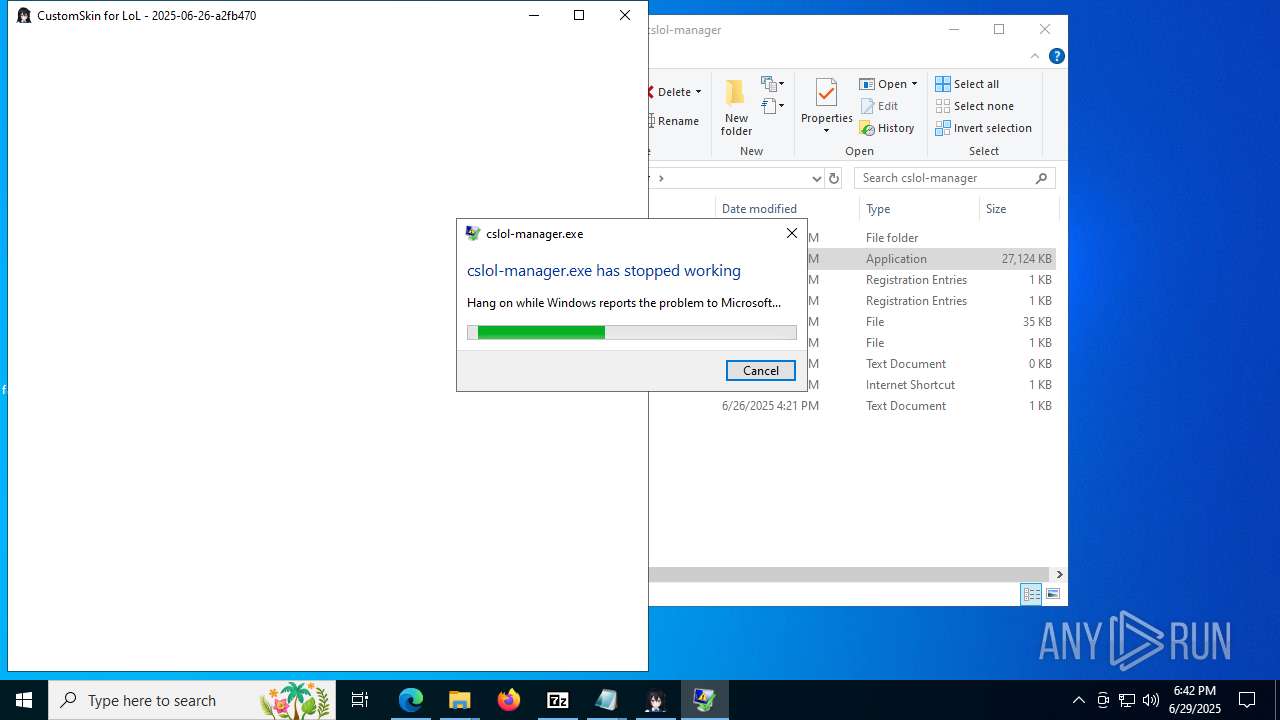
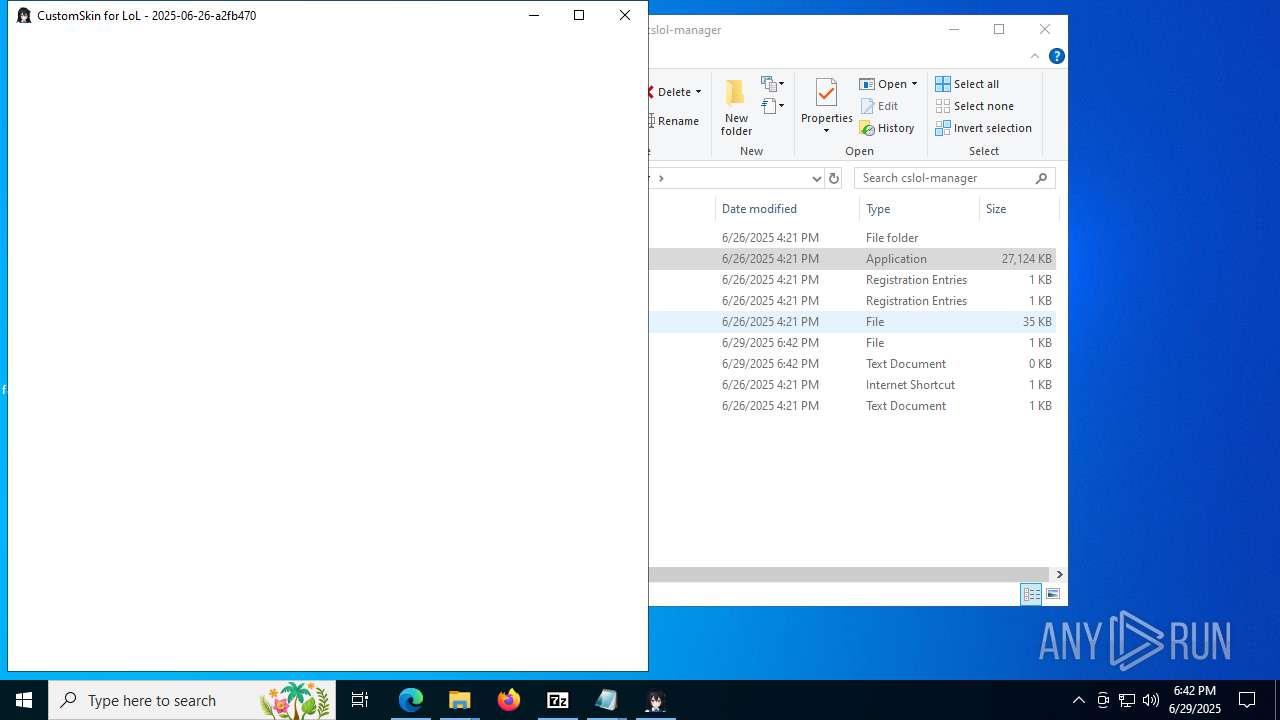
Executes application which crashes
- cslol-manager.exe (PID: 6348)
- cslol-manager.exe (PID: 7616)
- cslol-manager.exe (PID: 7428)
- cslol-manager.exe (PID: 2196)
- cslol-manager.exe (PID: 1752)
There is functionality for taking screenshot (YARA)
- wad-make.exe (PID: 856)
Adds/modifies Windows certificates
- cslol-diag.exe (PID: 7528)
INFO
Checks supported languages
- identity_helper.exe (PID: 7404)
- cslol-manager-windows.exe (PID: 7868)
- cslol-diag.exe (PID: 3476)
- wad-make.exe (PID: 7896)
- wad-make.exe (PID: 8032)
- mod-tools.exe (PID: 2148)
- wad-extract.exe (PID: 4084)
- cslol-manager.exe (PID: 6348)
- cslol-diag.exe (PID: 7796)
- wad-make.exe (PID: 856)
- wad-make.exe (PID: 2380)
- wad-make.exe (PID: 5284)
- wad-make.exe (PID: 7292)
- ShellExperienceHost.exe (PID: 6352)
- cslol-diag.exe (PID: 8176)
- cslol-manager.exe (PID: 7616)
- cslol-manager-windows.exe (PID: 4796)
- cslol-manager.exe (PID: 7428)
- cslol-diag.exe (PID: 7528)
- cslol-diag.exe (PID: 7472)
- cslol-manager.exe (PID: 2196)
- cslol-manager.exe (PID: 1752)
- cslol-diag.exe (PID: 5652)
Application launched itself
- msedge.exe (PID: 5368)
The sample compiled with english language support
- msedge.exe (PID: 5368)
Reads the computer name
- identity_helper.exe (PID: 7404)
- cslol-manager-windows.exe (PID: 7868)
- cslol-diag.exe (PID: 3476)
- cslol-manager.exe (PID: 6348)
- cslol-diag.exe (PID: 7796)
- ShellExperienceHost.exe (PID: 6352)
- cslol-diag.exe (PID: 8176)
- cslol-manager-windows.exe (PID: 4796)
- cslol-manager.exe (PID: 7616)
- cslol-manager.exe (PID: 7428)
- cslol-diag.exe (PID: 7528)
- cslol-manager.exe (PID: 2196)
- cslol-diag.exe (PID: 7472)
- cslol-manager.exe (PID: 1752)
- cslol-diag.exe (PID: 5652)
Reads Environment values
- identity_helper.exe (PID: 7404)
Executable content was dropped or overwritten
- msedge.exe (PID: 5368)
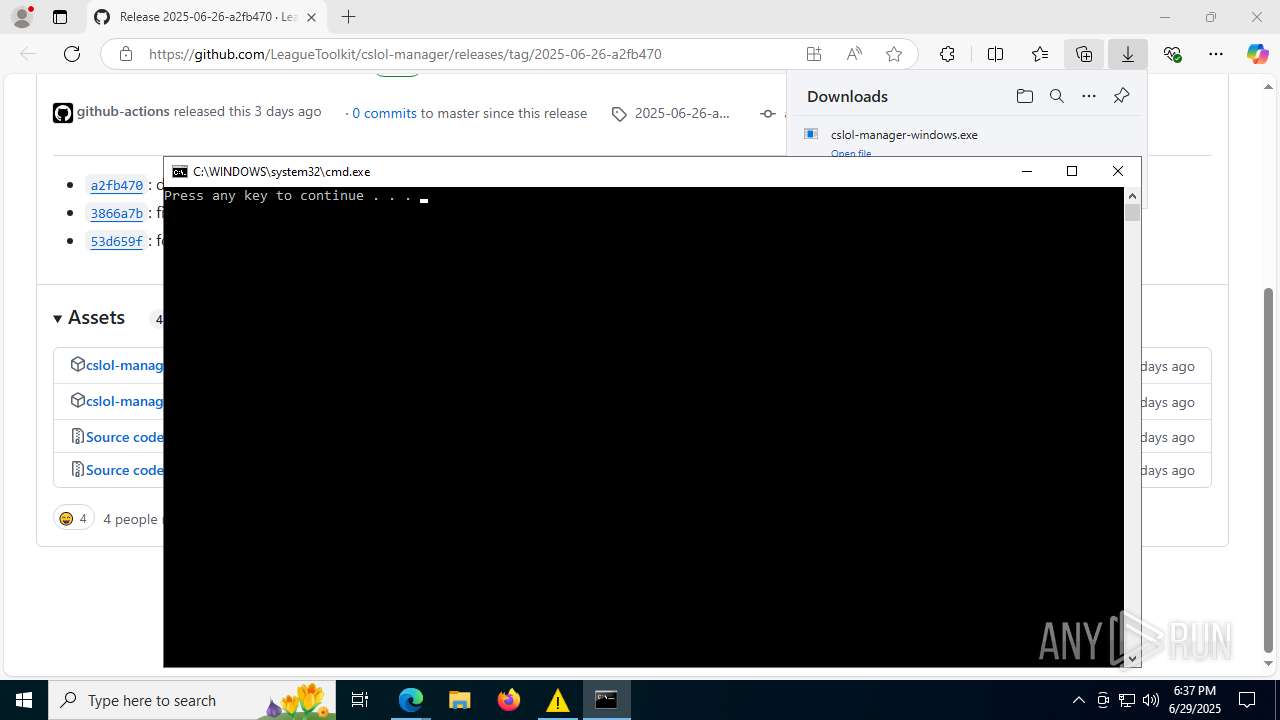
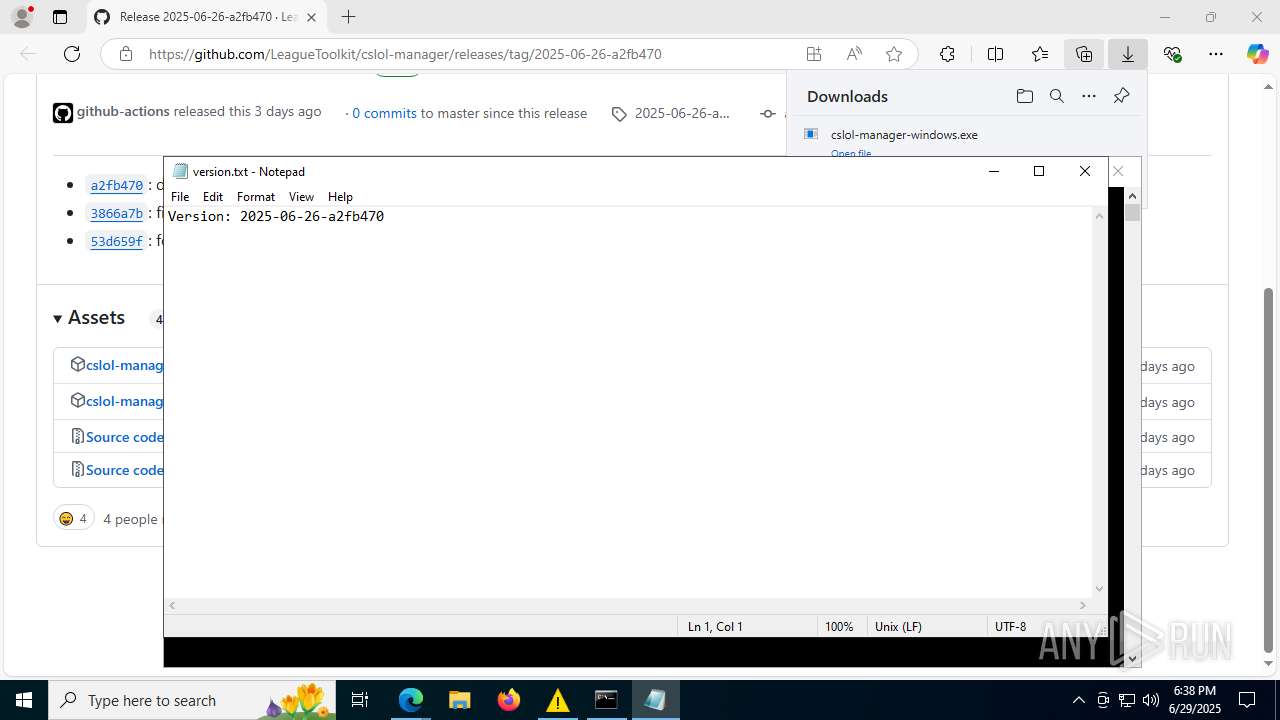
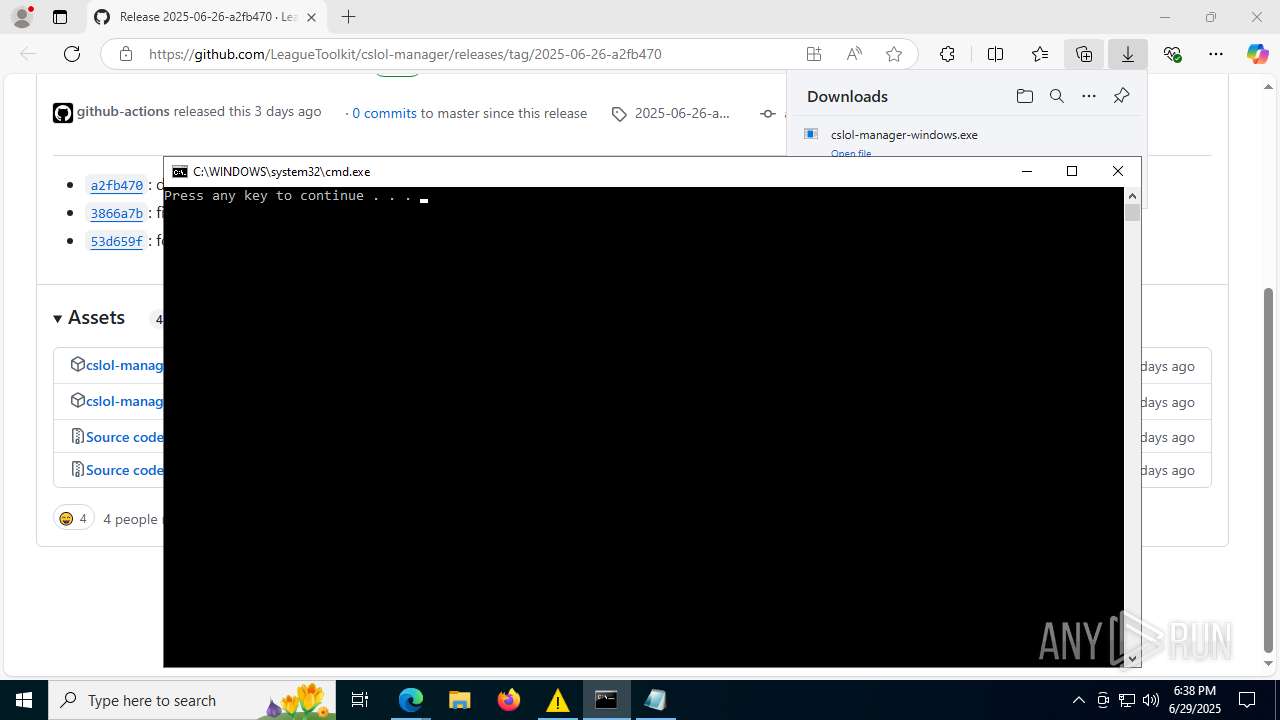
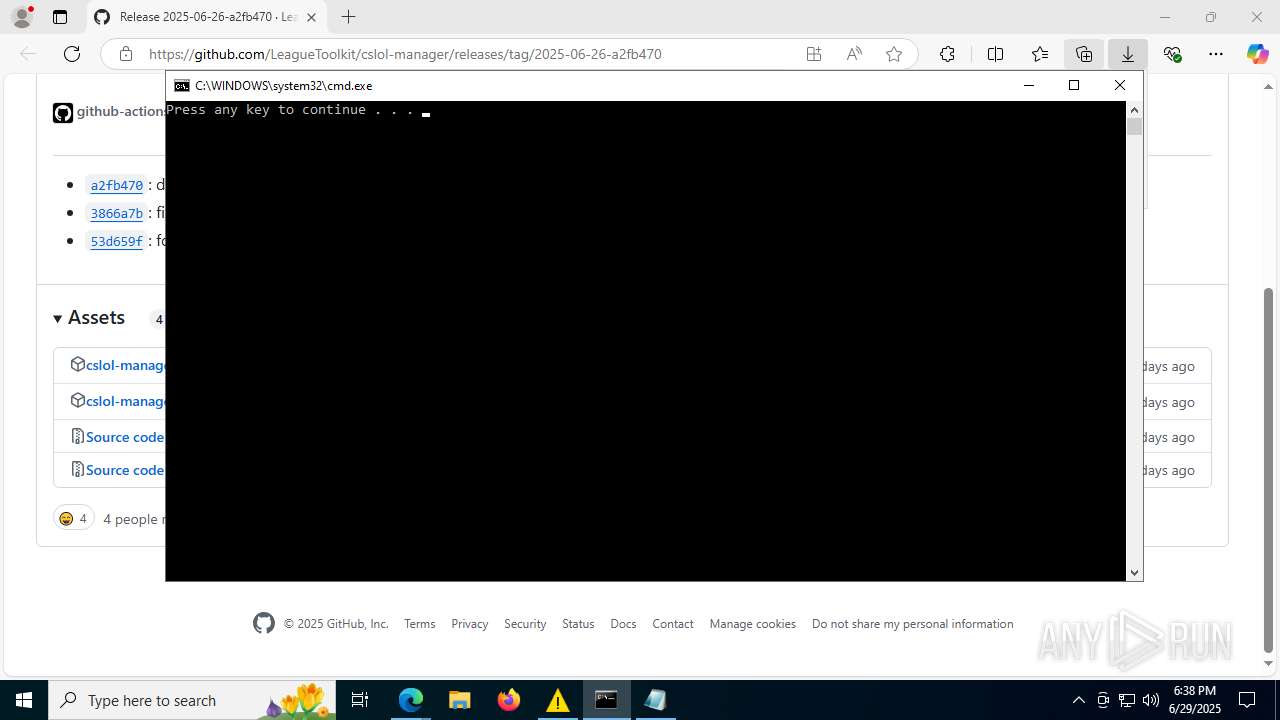
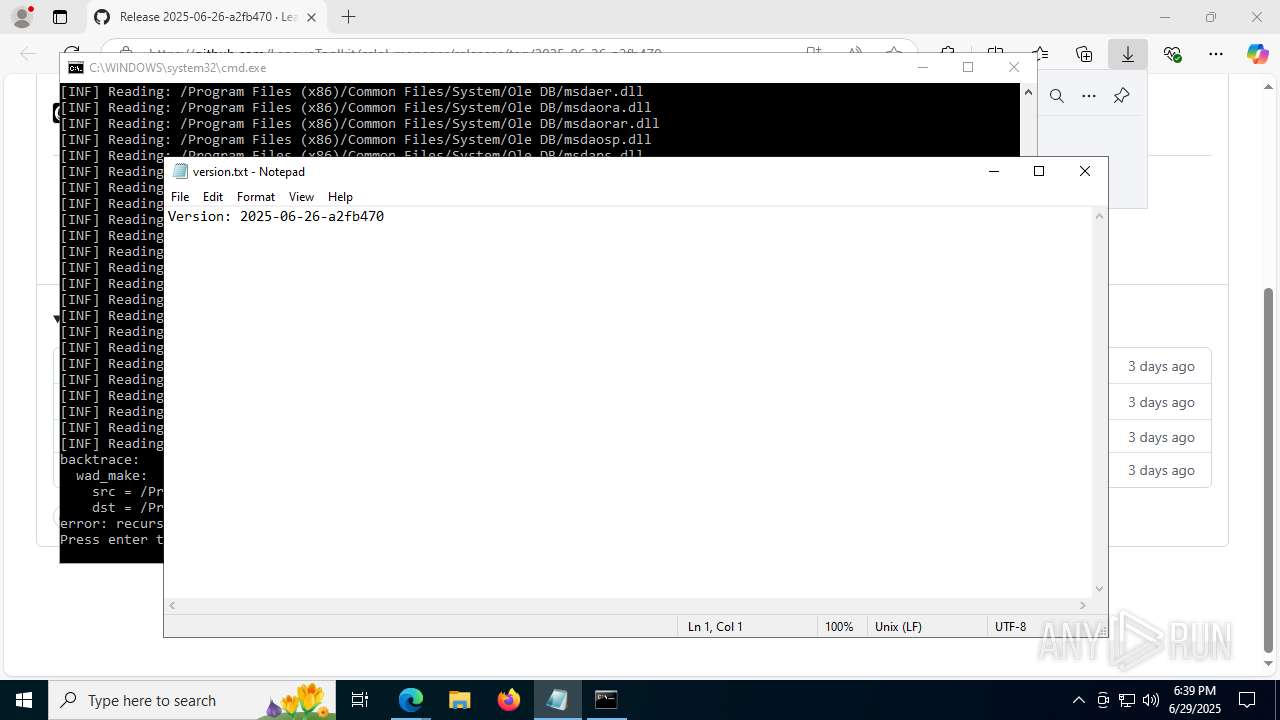
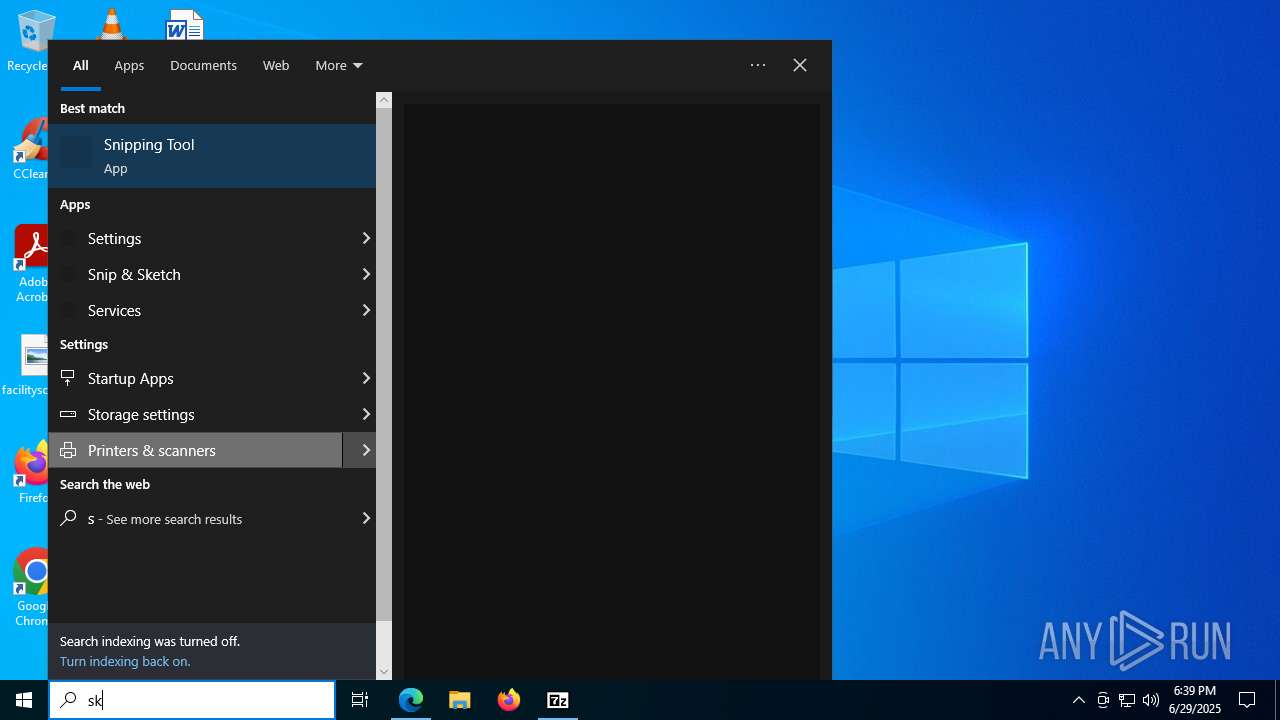
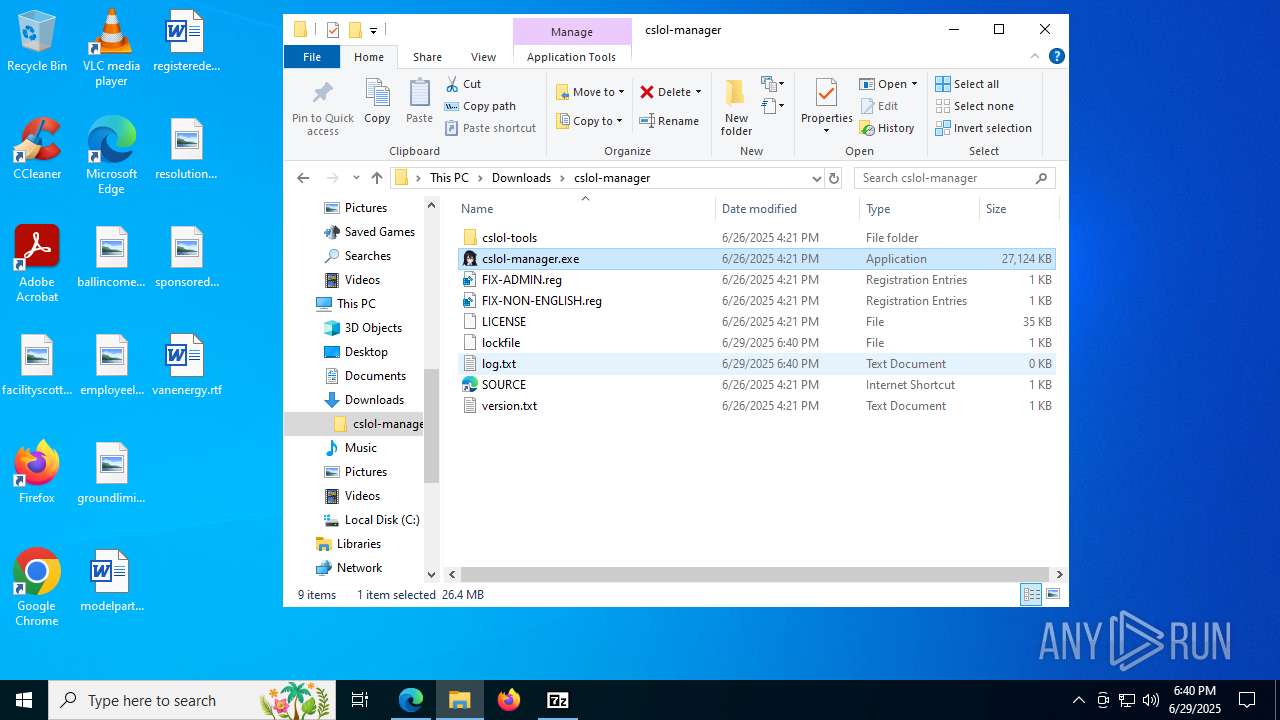
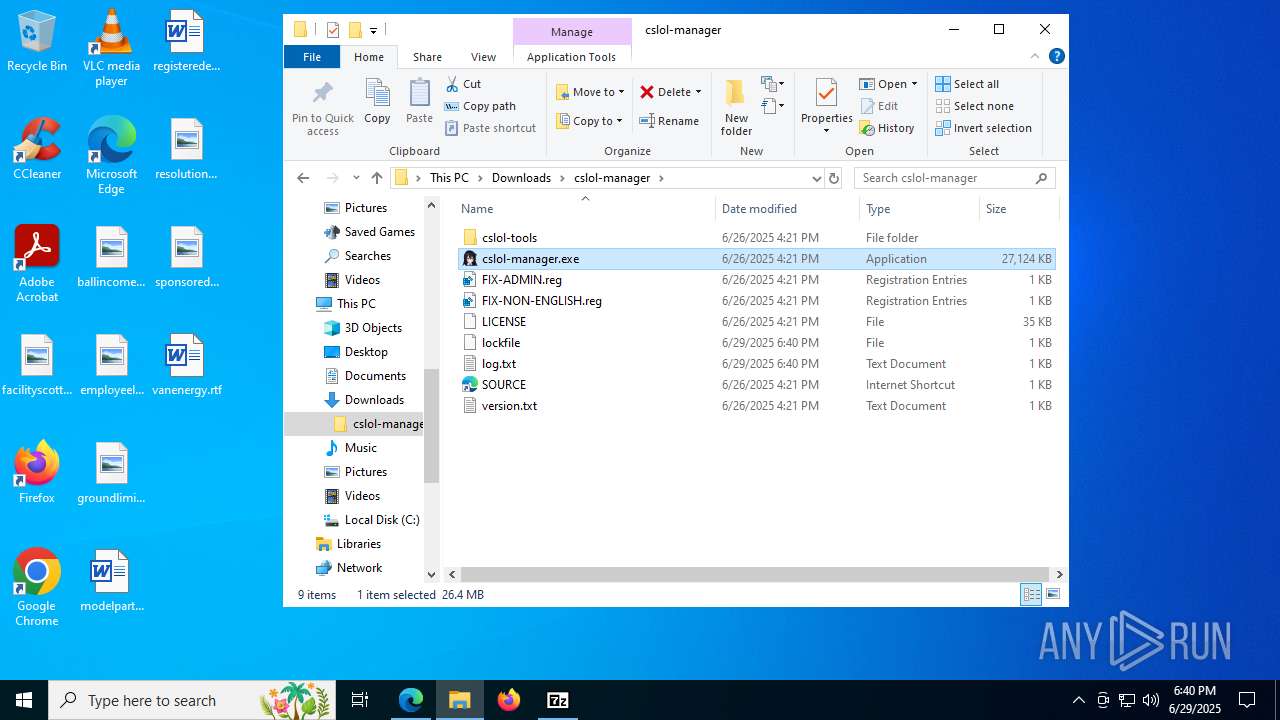
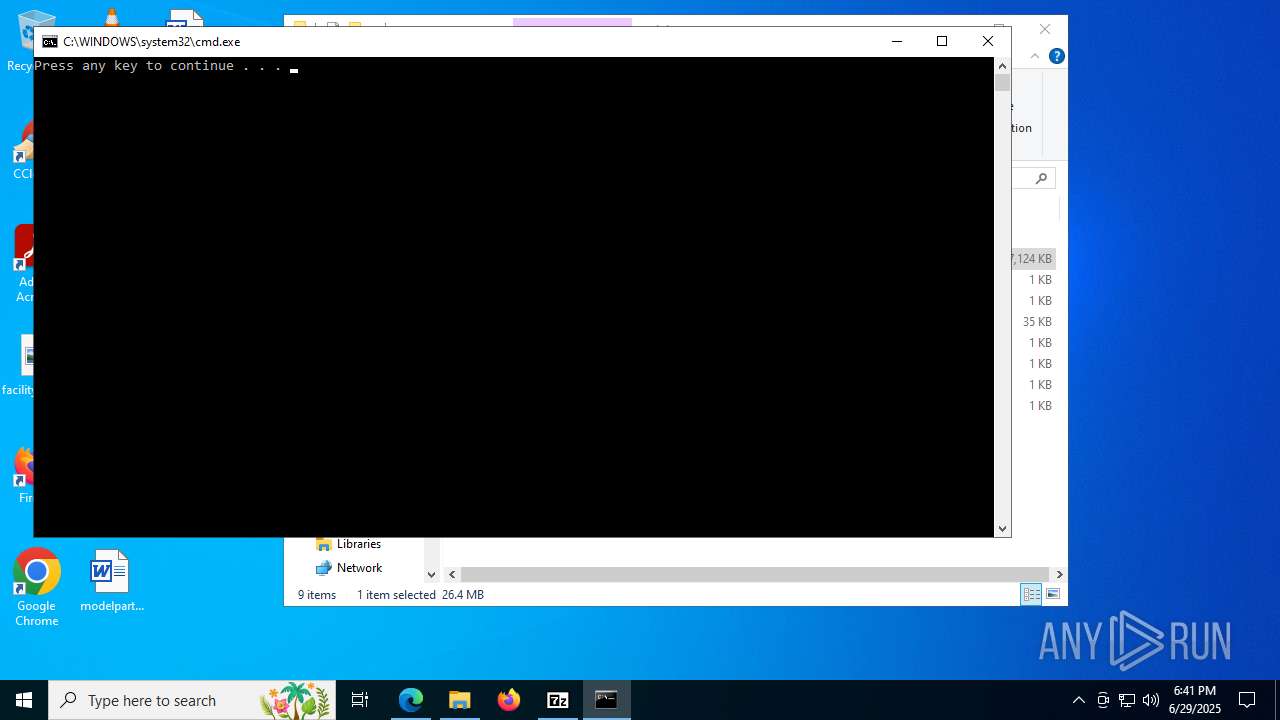
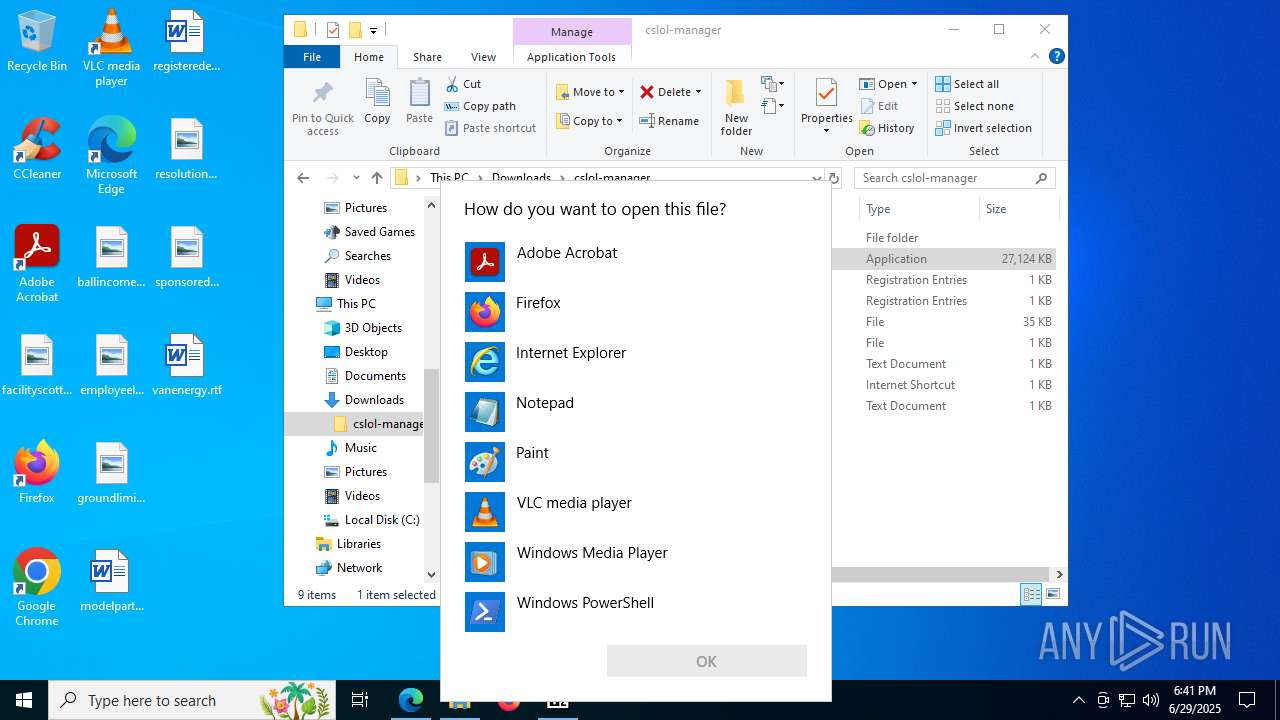
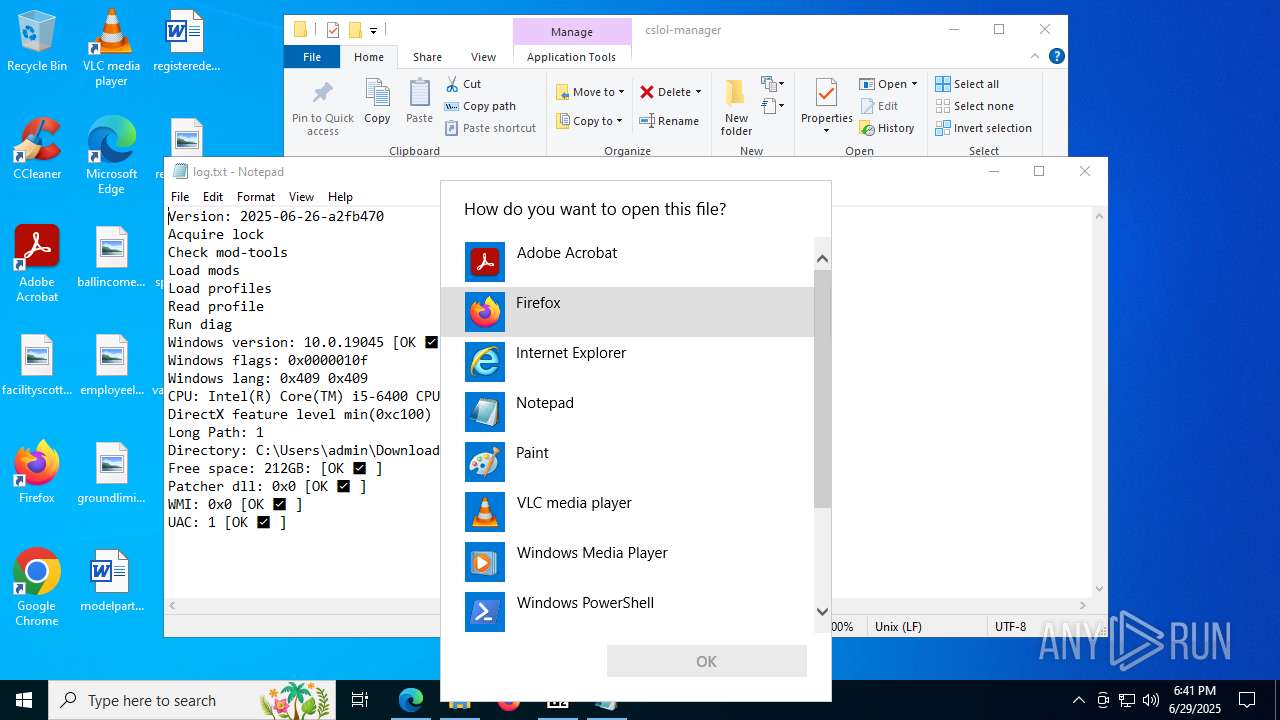
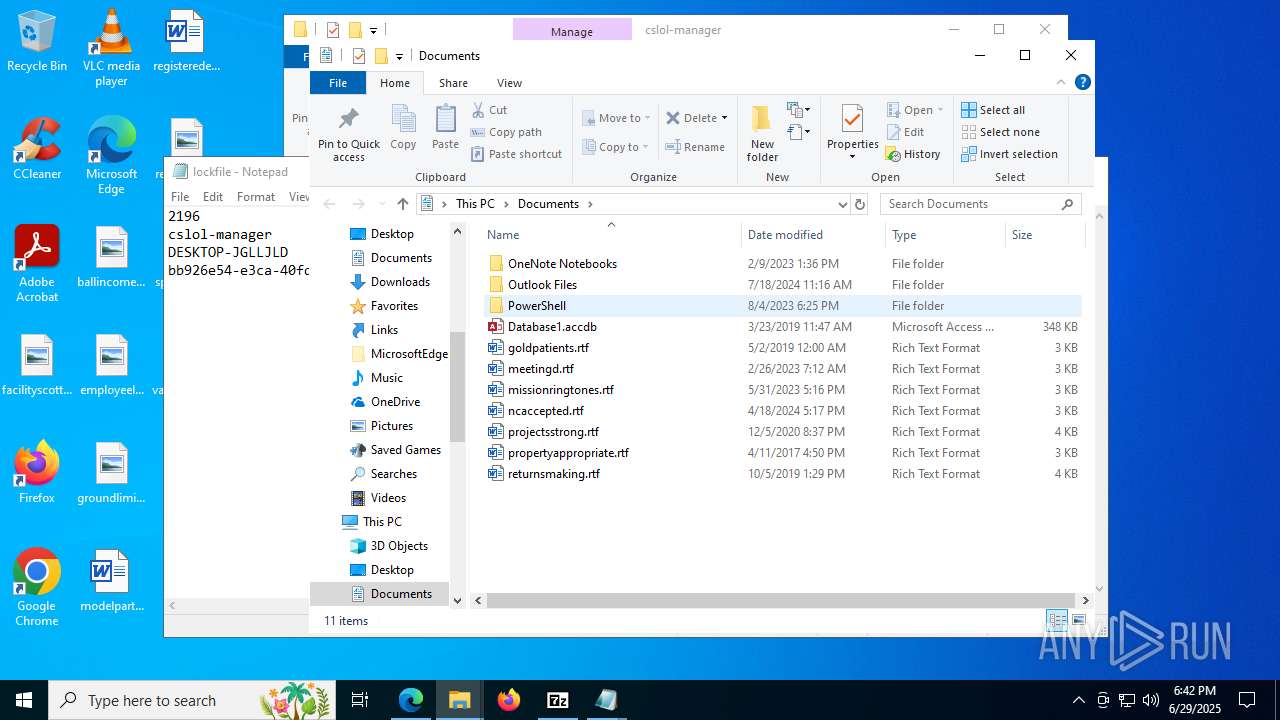
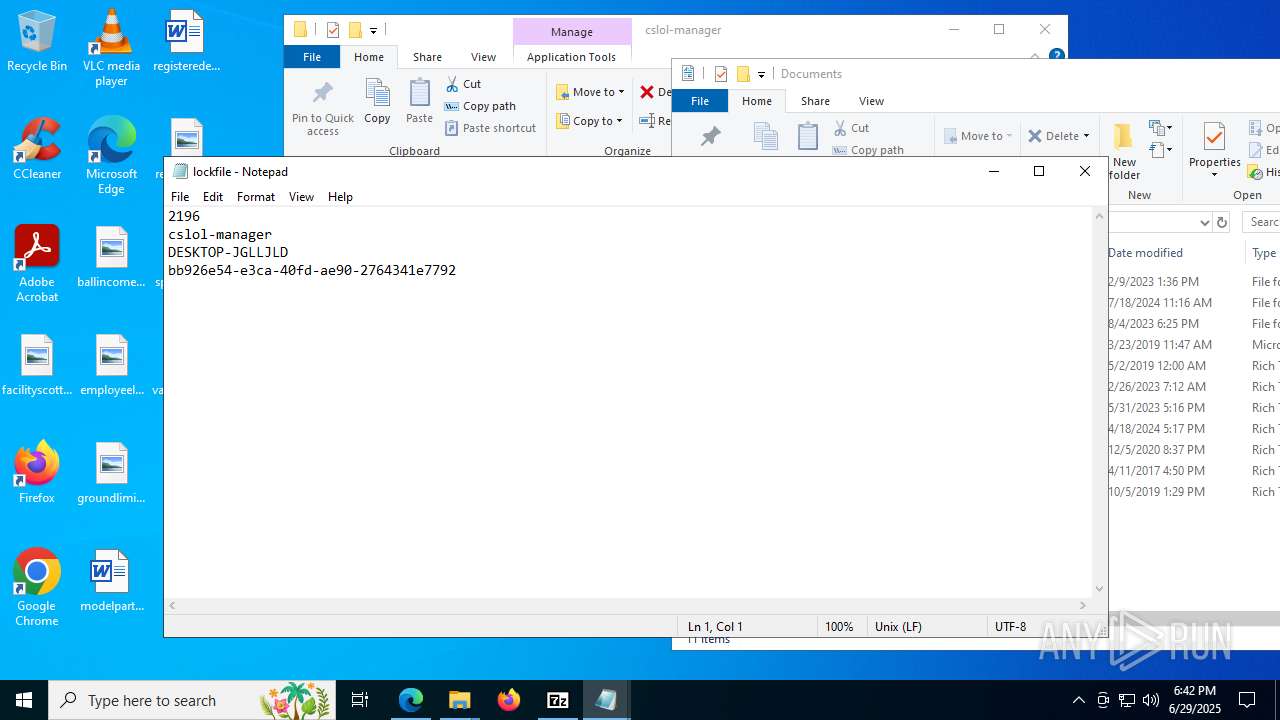
Manual execution by a user
- rundll32.exe (PID: 7228)
- cmd.exe (PID: 7208)
- notepad.exe (PID: 7360)
- cslol-diag.exe (PID: 3476)
- regedit.exe (PID: 7920)
- regedit.exe (PID: 7424)
- cmd.exe (PID: 7456)
- wad-extract.exe (PID: 4084)
- wad-make.exe (PID: 7896)
- regedit.exe (PID: 6772)
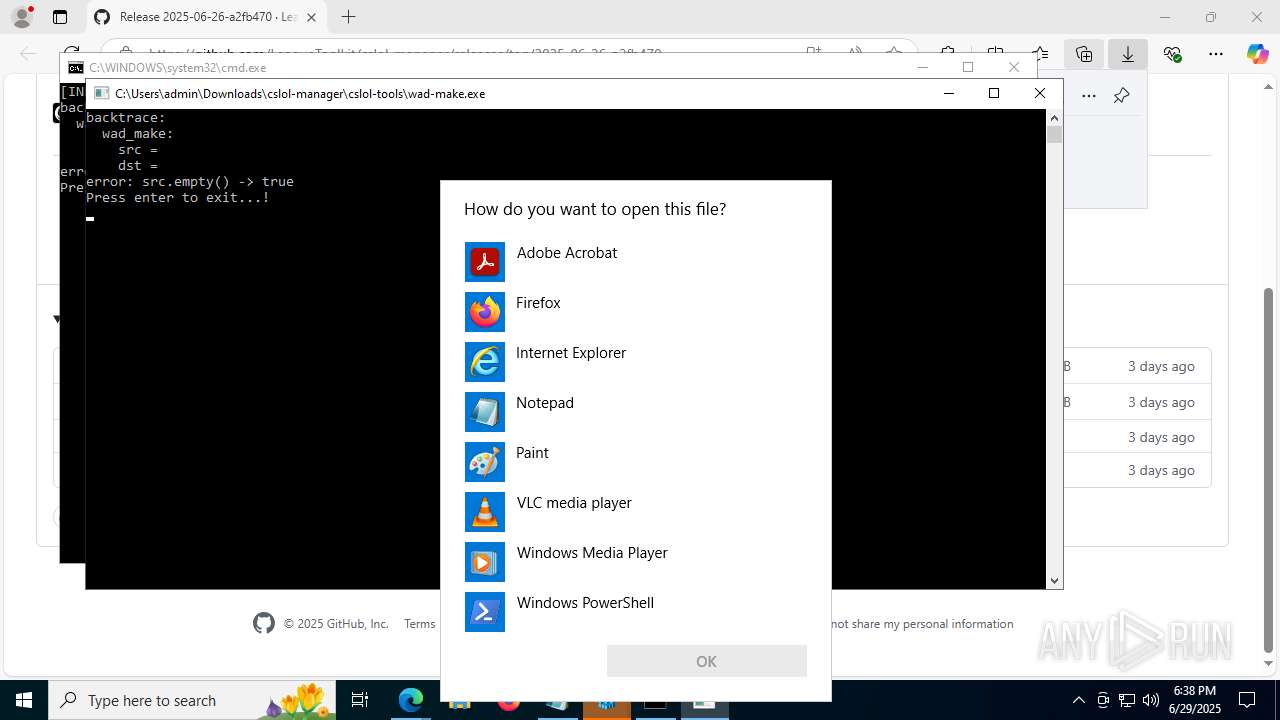
- OpenWith.exe (PID: 8100)
- regedit.exe (PID: 6516)
- mod-tools.exe (PID: 2148)
- cslol-manager.exe (PID: 6348)
- cslol-manager.exe (PID: 7616)
- cslol-manager.exe (PID: 7428)
- regedit.exe (PID: 6412)
- cslol-manager.exe (PID: 2196)
- regedit.exe (PID: 7132)
- cmd.exe (PID: 7284)
- OpenWith.exe (PID: 7308)
- notepad.exe (PID: 6768)
- cslol-manager.exe (PID: 1752)
Reads security settings of Internet Explorer
- rundll32.exe (PID: 7228)
- notepad.exe (PID: 7360)
- OpenWith.exe (PID: 7308)
- notepad.exe (PID: 7980)
- notepad.exe (PID: 6768)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 8100)
- OpenWith.exe (PID: 7308)
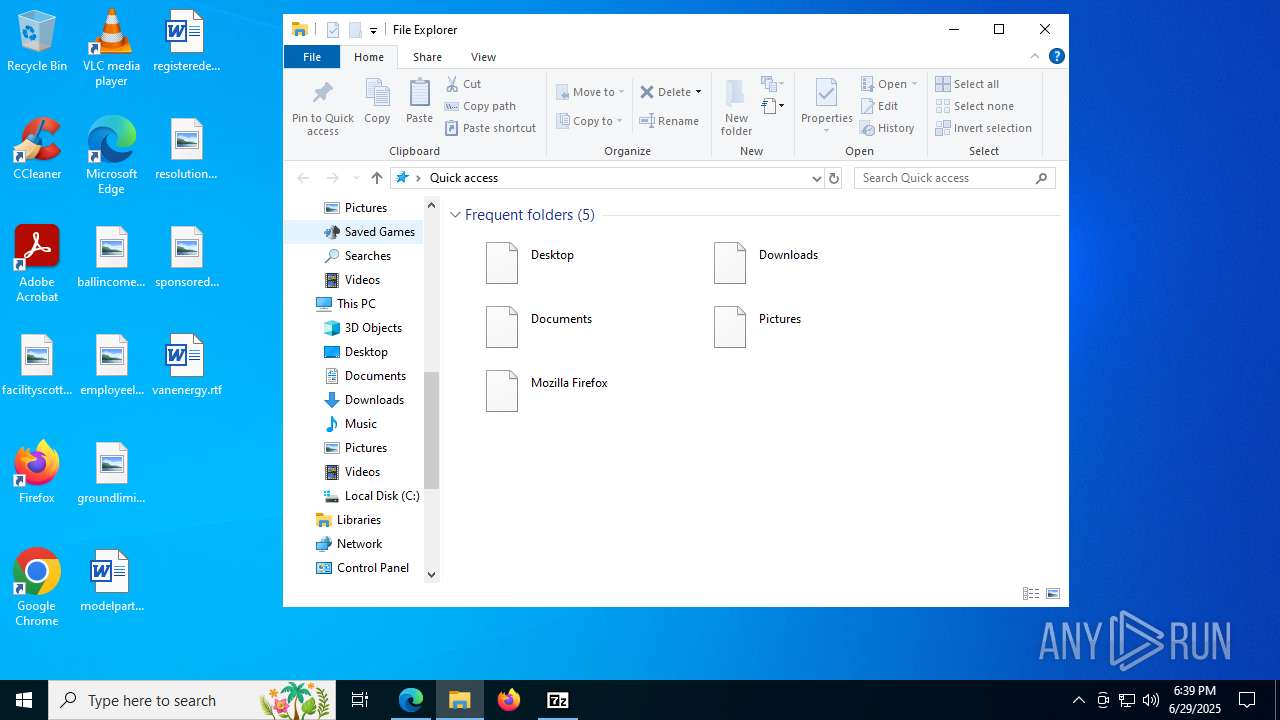
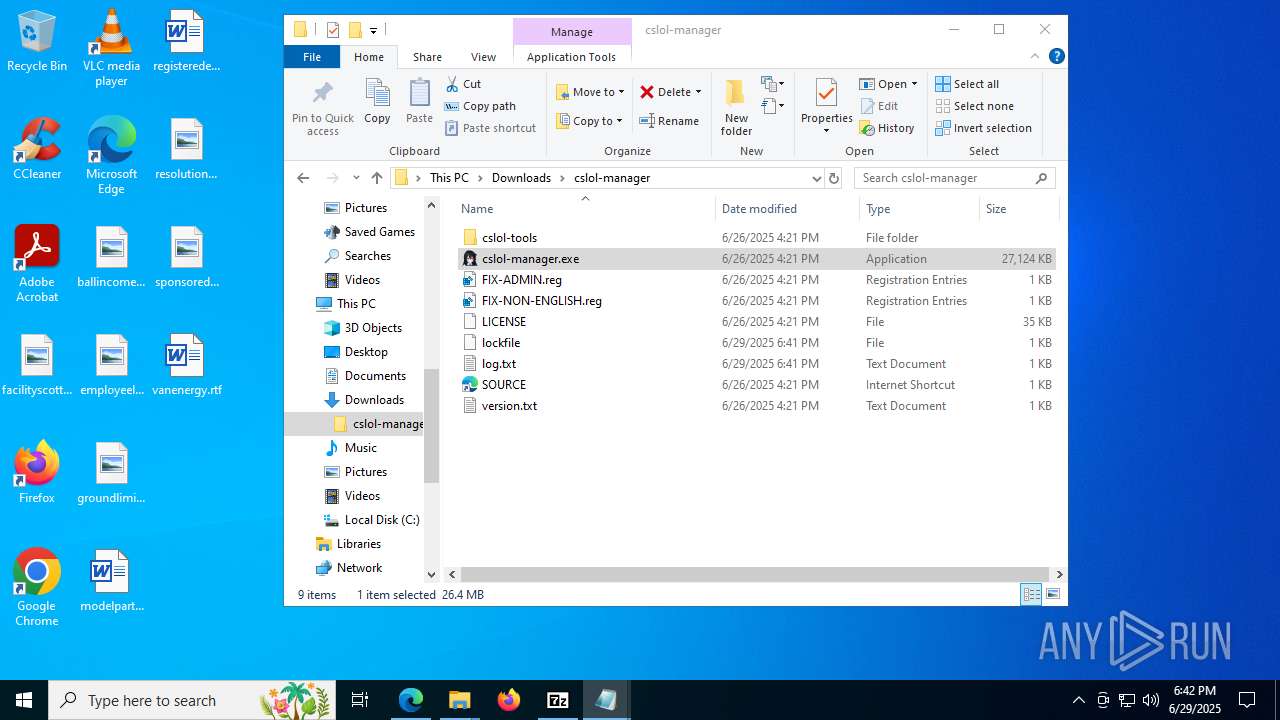
Creates files or folders in the user directory
- cslol-manager.exe (PID: 6348)
- cslol-diag.exe (PID: 7796)
- WerFault.exe (PID: 7512)
- WerFault.exe (PID: 7940)
- WerFault.exe (PID: 7624)
- WerFault.exe (PID: 7484)
- WerFault.exe (PID: 8032)
Reads the machine GUID from the registry
- cslol-manager.exe (PID: 6348)
- cslol-diag.exe (PID: 7796)
- cslol-manager.exe (PID: 7616)
- cslol-diag.exe (PID: 8176)
- cslol-manager.exe (PID: 7428)
- cslol-diag.exe (PID: 7528)
- cslol-manager.exe (PID: 2196)
- cslol-diag.exe (PID: 7472)
- cslol-diag.exe (PID: 5652)
- cslol-manager.exe (PID: 1752)
Reads the software policy settings
- cslol-diag.exe (PID: 7796)
- WerFault.exe (PID: 7512)
- slui.exe (PID: 6140)
- cslol-diag.exe (PID: 8176)
- WerFault.exe (PID: 7940)
- cslol-diag.exe (PID: 7528)
- WerFault.exe (PID: 7624)
- cslol-diag.exe (PID: 7472)
- WerFault.exe (PID: 7484)
- cslol-diag.exe (PID: 5652)
- WerFault.exe (PID: 8032)
Checks proxy server information
- cslol-diag.exe (PID: 7796)
- WerFault.exe (PID: 7512)
- slui.exe (PID: 6140)
- WerFault.exe (PID: 7940)
- WerFault.exe (PID: 7624)
- WerFault.exe (PID: 7484)
- WerFault.exe (PID: 8032)
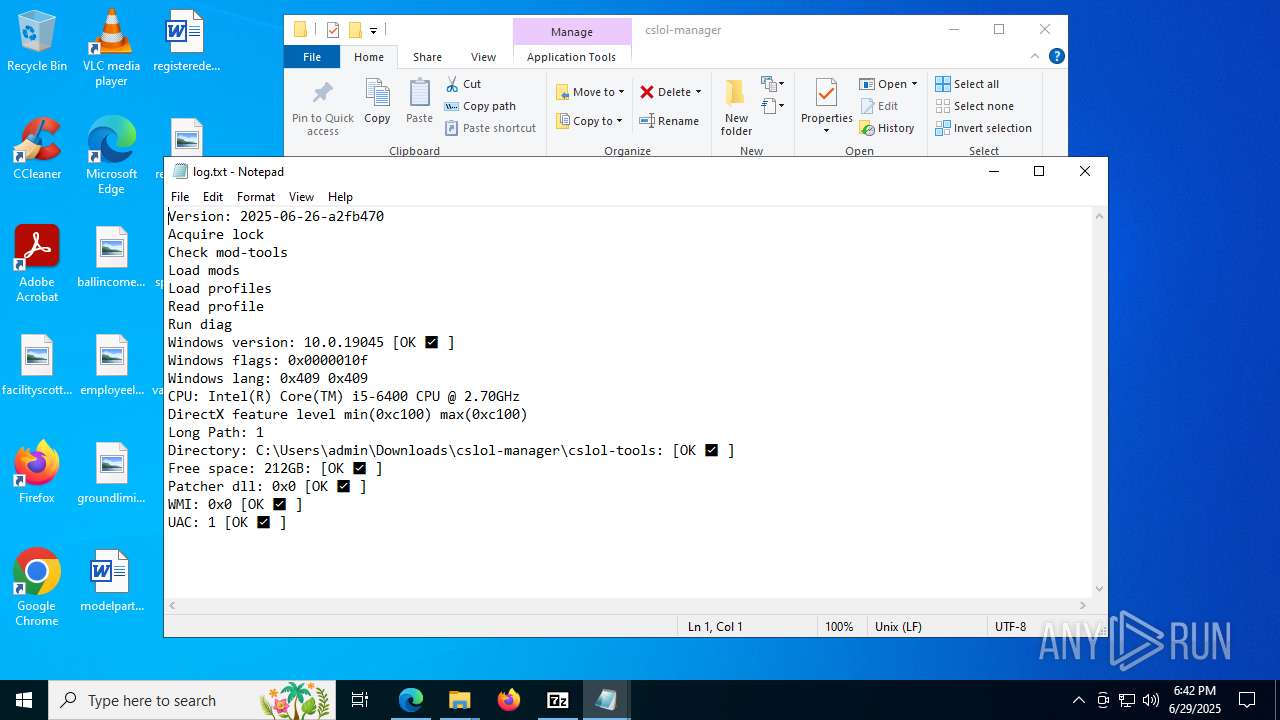
Process checks whether UAC notifications are on
- cslol-diag.exe (PID: 7796)
- cslol-diag.exe (PID: 8176)
- cslol-diag.exe (PID: 7528)
- cslol-diag.exe (PID: 7472)
- cslol-diag.exe (PID: 5652)
Reads CPU info
- cslol-diag.exe (PID: 7796)
- cslol-diag.exe (PID: 8176)
- cslol-diag.exe (PID: 7528)
- cslol-diag.exe (PID: 7472)
- cslol-diag.exe (PID: 5652)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
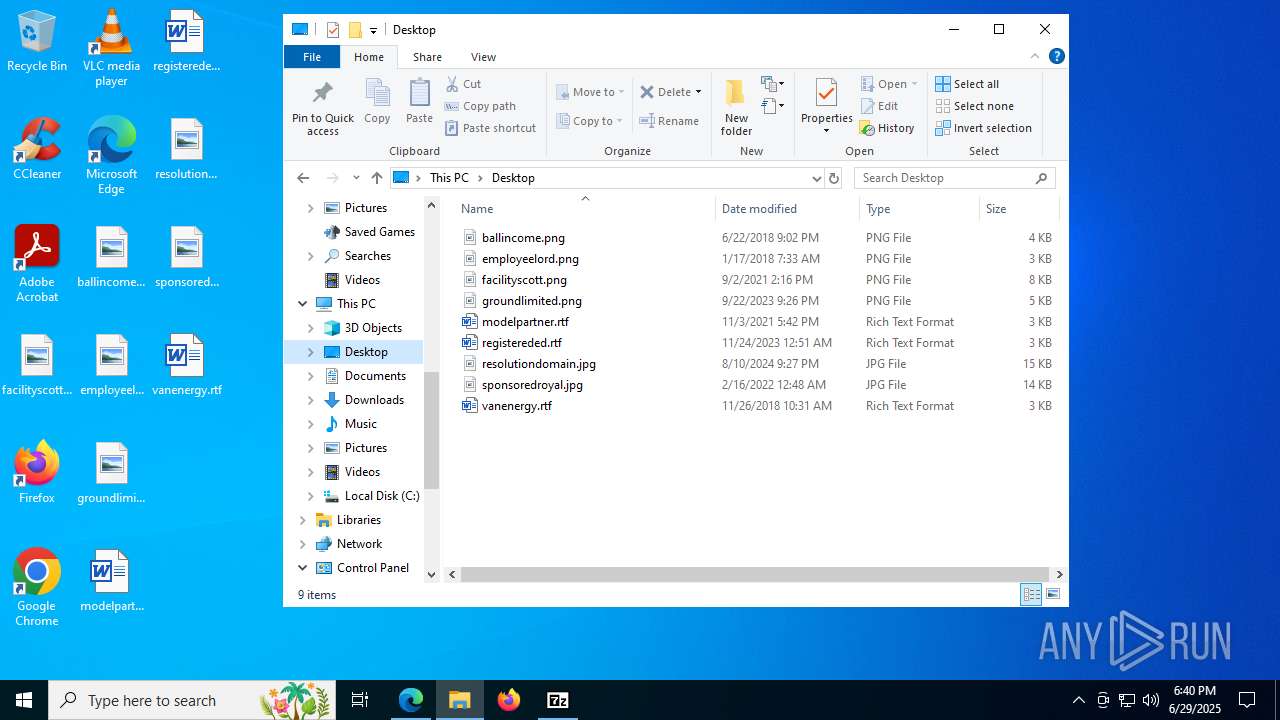
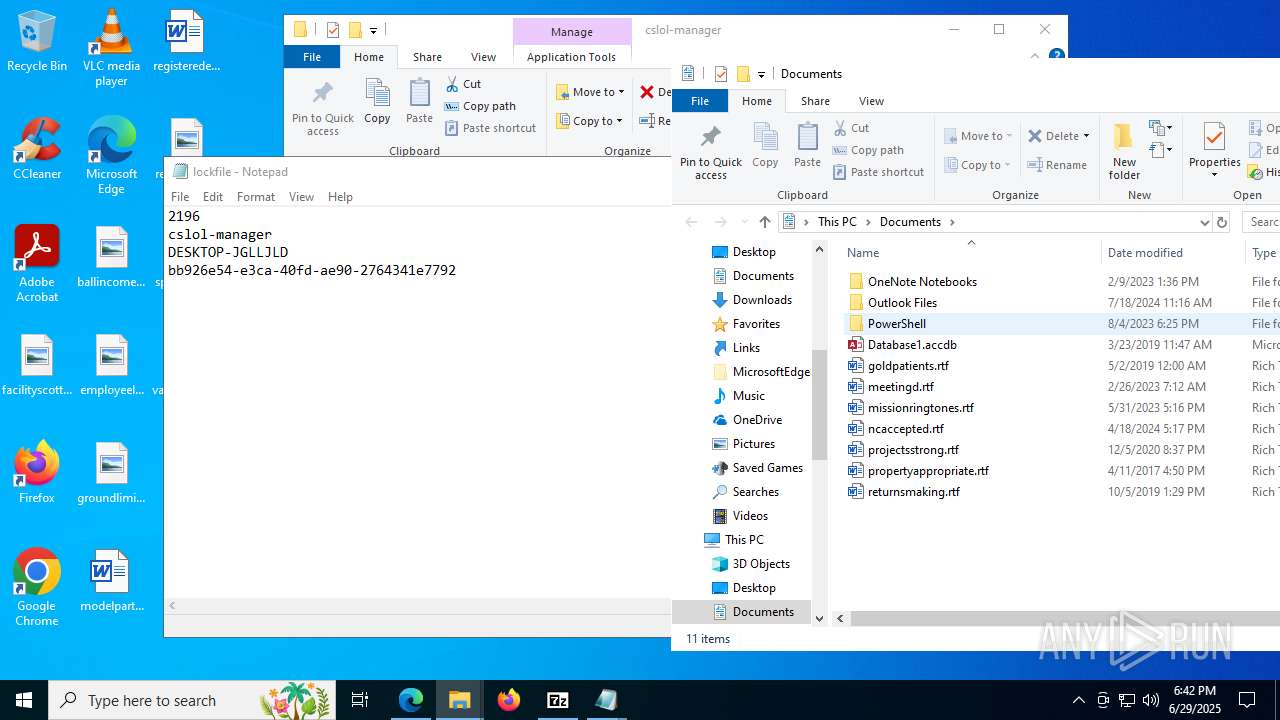
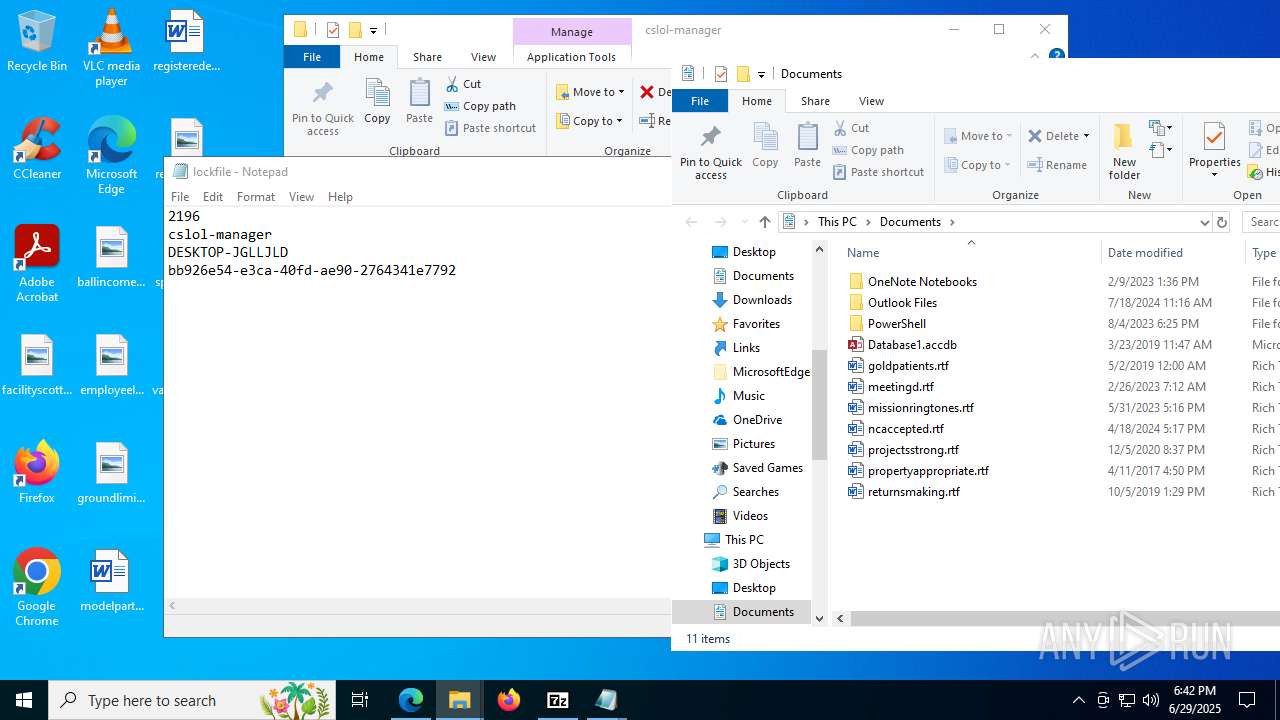
Total processes
251
Monitored processes
91
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 420 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | mod-tools.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
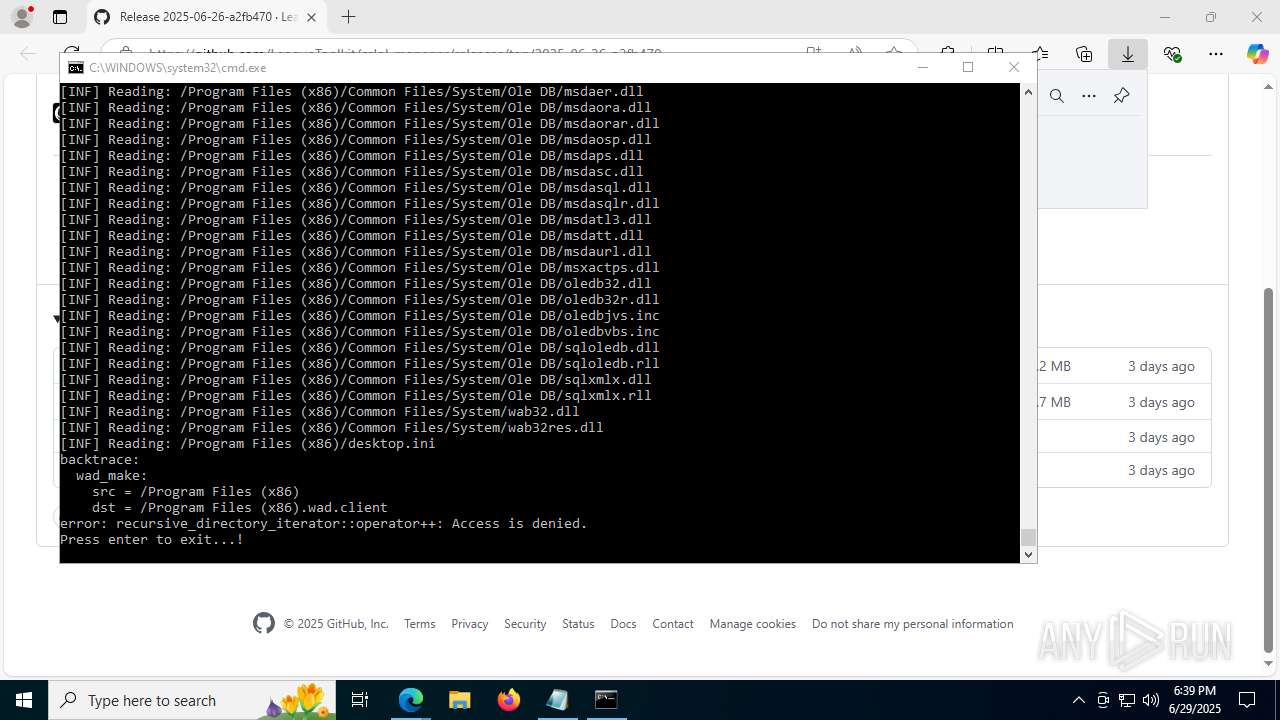
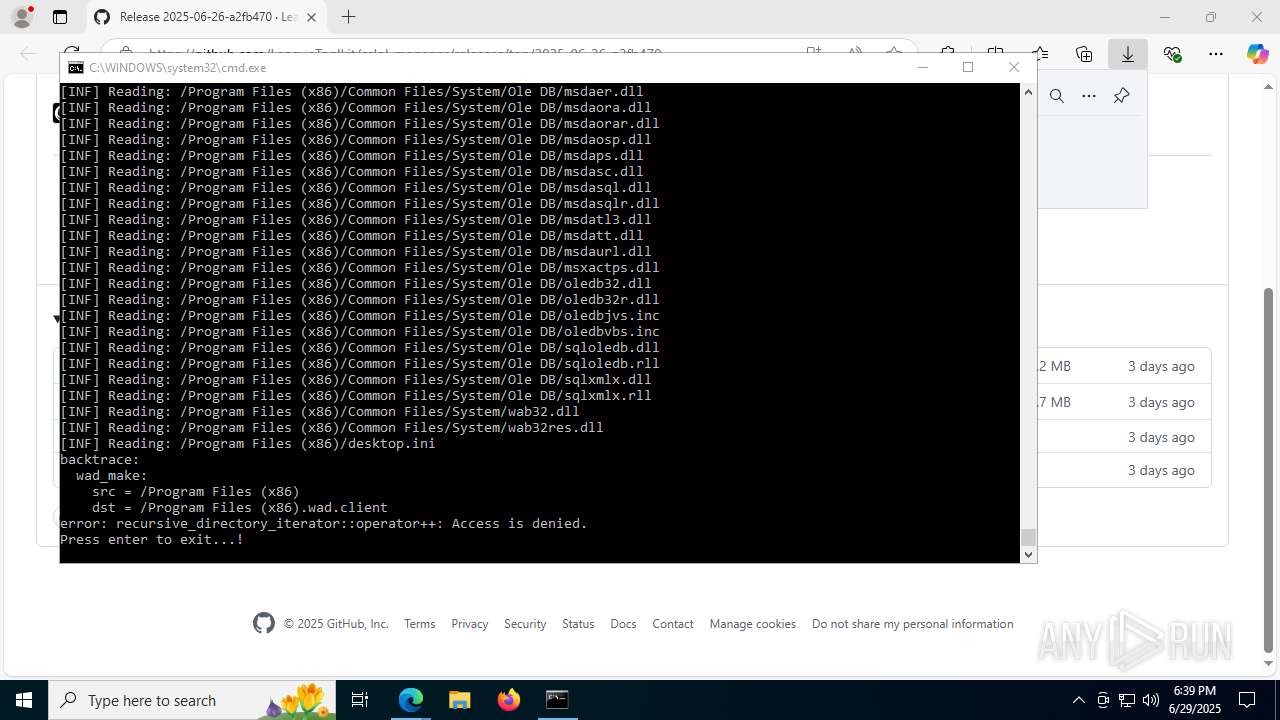
| 856 | "C:\Users\admin\Downloads\cslol-manager\cslol-tools\\wad-make.exe" "\Program Files" | C:\Users\admin\Downloads\cslol-manager\cslol-tools\wad-make.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 1128 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4364,i,10680964623644662341,9452146206351205281,262144 --variations-seed-version --mojo-platform-channel-handle=5008 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1632 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2728,i,10680964623644662341,9452146206351205281,262144 --variations-seed-version --mojo-platform-channel-handle=2716 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1752 | "C:\Users\admin\Downloads\cslol-manager\cslol-manager.exe" | C:\Users\admin\Downloads\cslol-manager\cslol-manager.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
| 1944 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2192,i,10680964623644662341,9452146206351205281,262144 --variations-seed-version --mojo-platform-channel-handle=2436 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2148 | "C:\Users\admin\Downloads\cslol-manager\cslol-tools\mod-tools.exe" | C:\Users\admin\Downloads\cslol-manager\cslol-tools\mod-tools.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
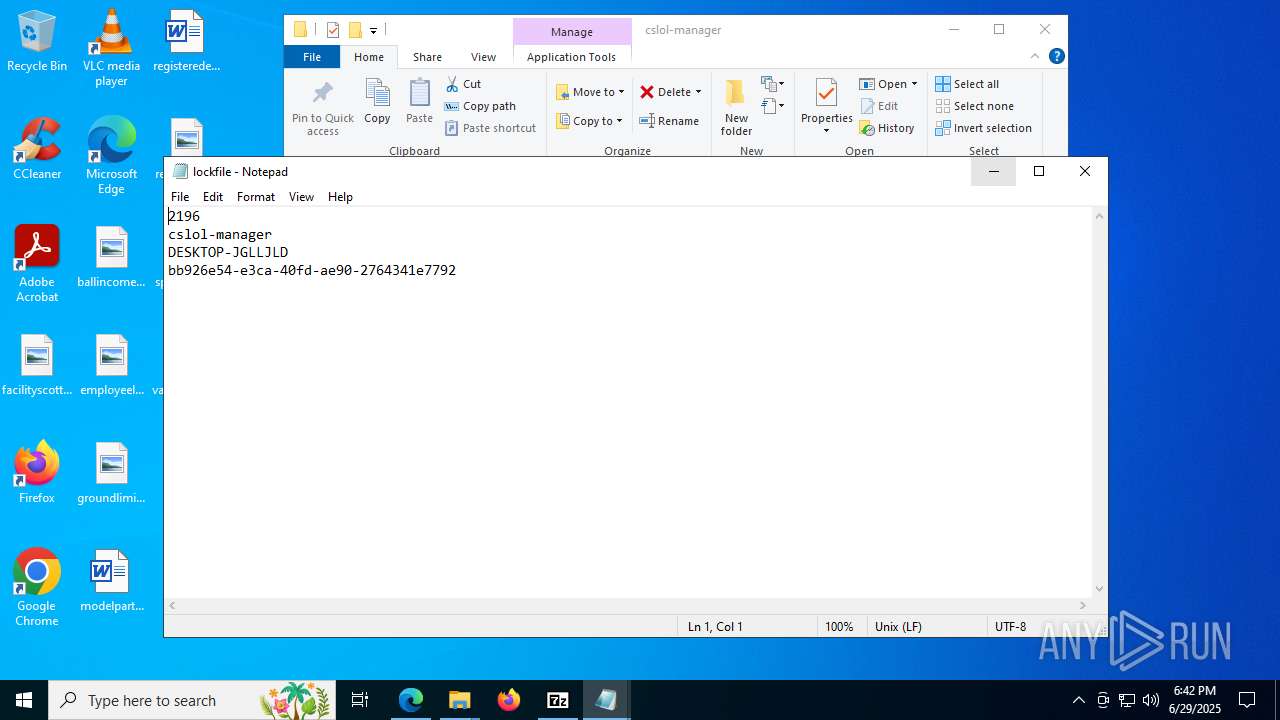
| 2196 | "C:\Users\admin\Downloads\cslol-manager\cslol-manager.exe" | C:\Users\admin\Downloads\cslol-manager\cslol-manager.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
| 2380 | "C:\Users\admin\Downloads\cslol-manager\cslol-tools\\wad-make.exe" "\Program Files (x86)" | C:\Users\admin\Downloads\cslol-manager\cslol-tools\wad-make.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 2380 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6836,i,10680964623644662341,9452146206351205281,262144 --variations-seed-version --mojo-platform-channel-handle=4984 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
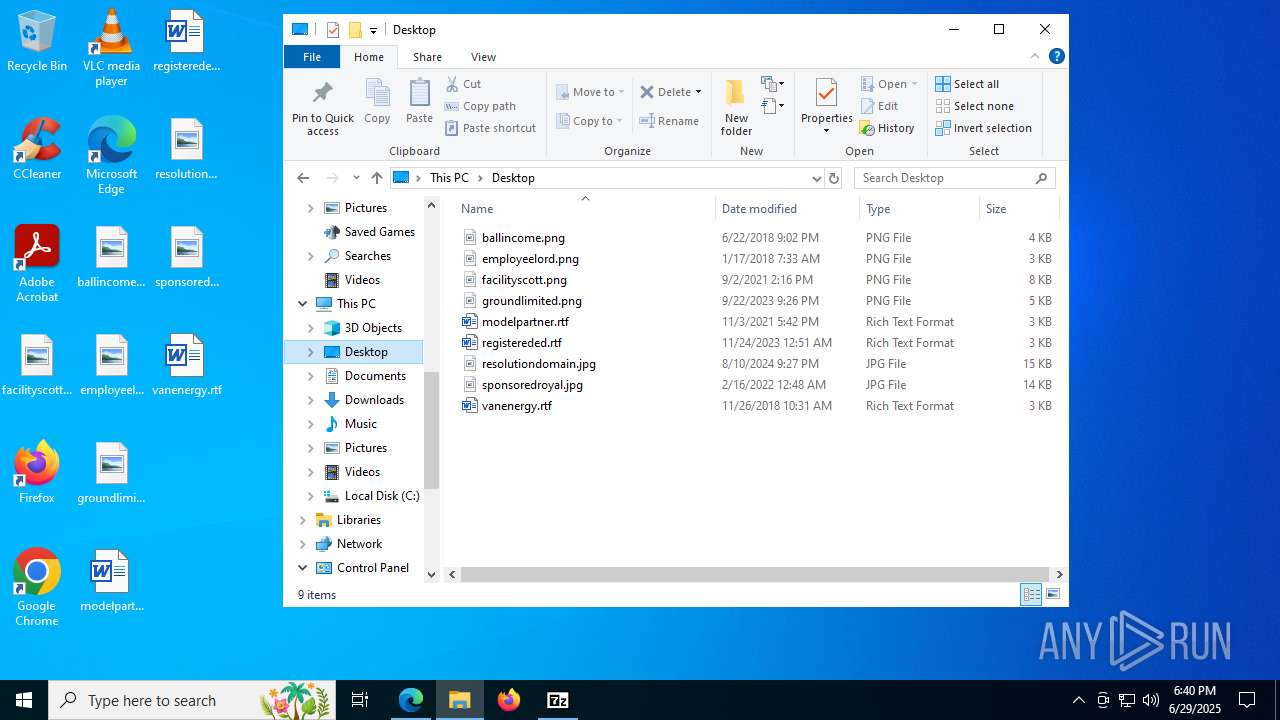
Total events
46 594
Read events
46 555
Write events
34
Delete events
5
Modification events
| (PID) Process: | (5368) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5368) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5368) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (5368) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (5368) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5368) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 5BE0C67C50972F00 | |||
| (PID) Process: | (5368) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5368) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\721710 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {5332E494-0151-498B-A6EF-84AD874F5204} | |||
| (PID) Process: | (5368) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\721710 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {CEC92BC0-3FE1-4F29-B945-A989B672A6E3} | |||
| (PID) Process: | (5368) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\721710 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {1FD1B0E6-ED37-4421-9AA2-8BBEB51F23AD} | |||
Executable files
15
Suspicious files
340
Text files
81
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5368 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF175da0.TMP | — | |
MD5:— | SHA256:— | |||
| 5368 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5368 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF175da0.TMP | — | |
MD5:— | SHA256:— | |||
| 5368 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5368 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF175ddf.TMP | — | |
MD5:— | SHA256:— | |||
| 5368 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5368 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF175ddf.TMP | — | |
MD5:— | SHA256:— | |||
| 5368 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5368 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF175ddf.TMP | — | |
MD5:— | SHA256:— | |||
| 5368 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
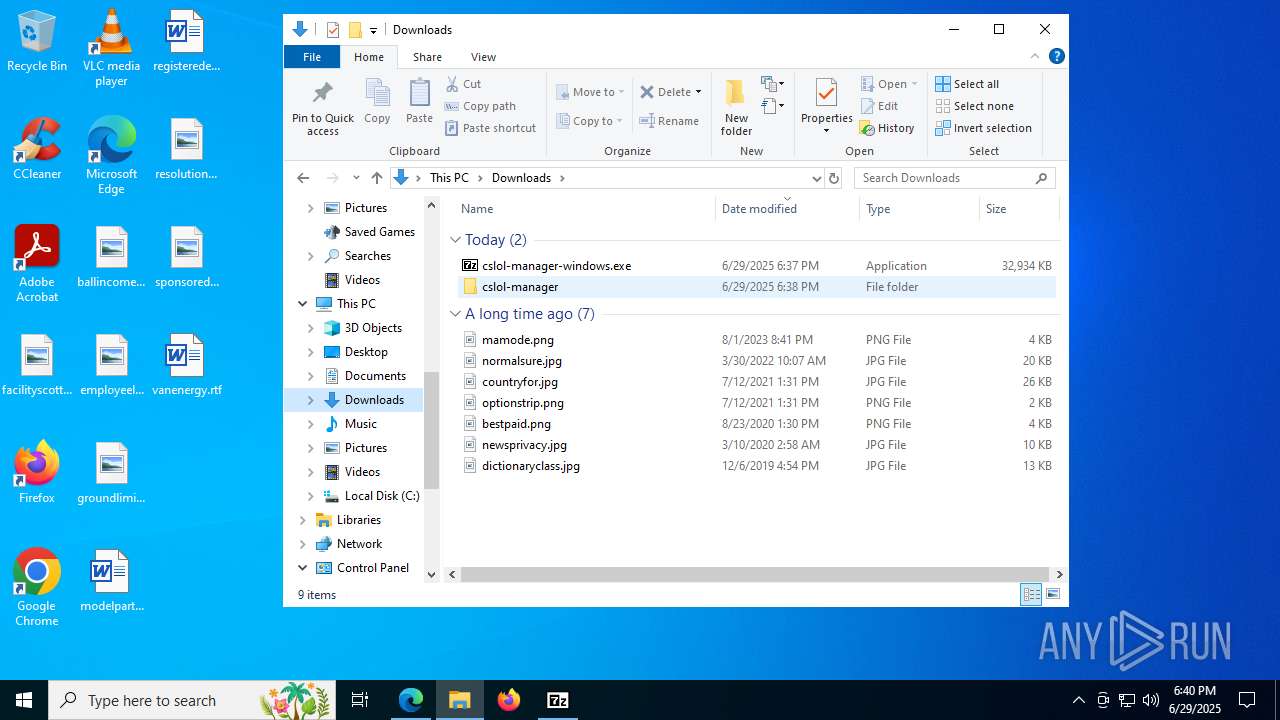
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
117
DNS requests
106
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1944 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:48OwTWC7BcZlWh48ddGaBNORUNRg9LVDOv-tQp1OOOA&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5240 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8092 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8092 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7796 | cslol-diag.exe | GET | 200 | 2.18.244.84:80 | http://ccsca2021.ocsp-certum.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRxypYNH69rICCzQBIRXN0YAFa3AAQU3XRdTADbe5%2BgdMqxbvc8wDLAcM0CEE%2FwT6OwCfLpZW2krGNArb0%3D | unknown | — | — | unknown |
7796 | cslol-diag.exe | GET | 200 | 2.18.244.88:80 | http://subca.ocsp-certum.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRIH1V64SBkA%2BzJQVQ6VFBAcvLB3wQUtqFUOQLDoD%2BOirz61PgcptE6Dv0CEQCZo4AKJlU7ZavcboSms%2Bo5 | unknown | — | — | whitelisted |
7512 | WerFault.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7512 | WerFault.exe | GET | 200 | 173.223.117.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4916 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1944 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1944 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1944 | msedge.exe | 185.199.109.133:443 | avatars.githubusercontent.com | FASTLY | US | whitelisted |
1944 | msedge.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
1944 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
github.githubassets.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
www.bing.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
— | — | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
— | — | Misc activity | ET INFO EXE - Served Attached HTTP |
5328 | SearchApp.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |