| File name: | Rubly4.exe |
| Full analysis: | https://app.any.run/tasks/cd1d6eb9-3823-4ad9-8a6e-ec2f9324a6dd |
| Verdict: | Malicious activity |
| Analysis date: | February 19, 2025, 17:49:52 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | CACE46A66ADD9416A9657AF4819556F0 |
| SHA1: | C847BD2A4657BE55CE0FF7069AE8E16D5878F09E |
| SHA256: | A54EF676ED88E1B7A5C61F7CB652EF0BFD59CFF076E7C45E535C19F742A3216C |
| SSDEEP: | 24576:X9Yra6GvJtZvy91Om9IPhAbRDy8asBRj6LbzN1Sc6zX46jIcKRPgpYsNwct0sX+d:X9YGNvJtZvy91Om9IPhAbRDy8acl6Lb3 |
MALICIOUS
Create files in the Startup directory
- mtrmbr.exe (PID: 6520)
Changes the autorun value in the registry
- mtr.exe (PID: 6720)
SUSPICIOUS
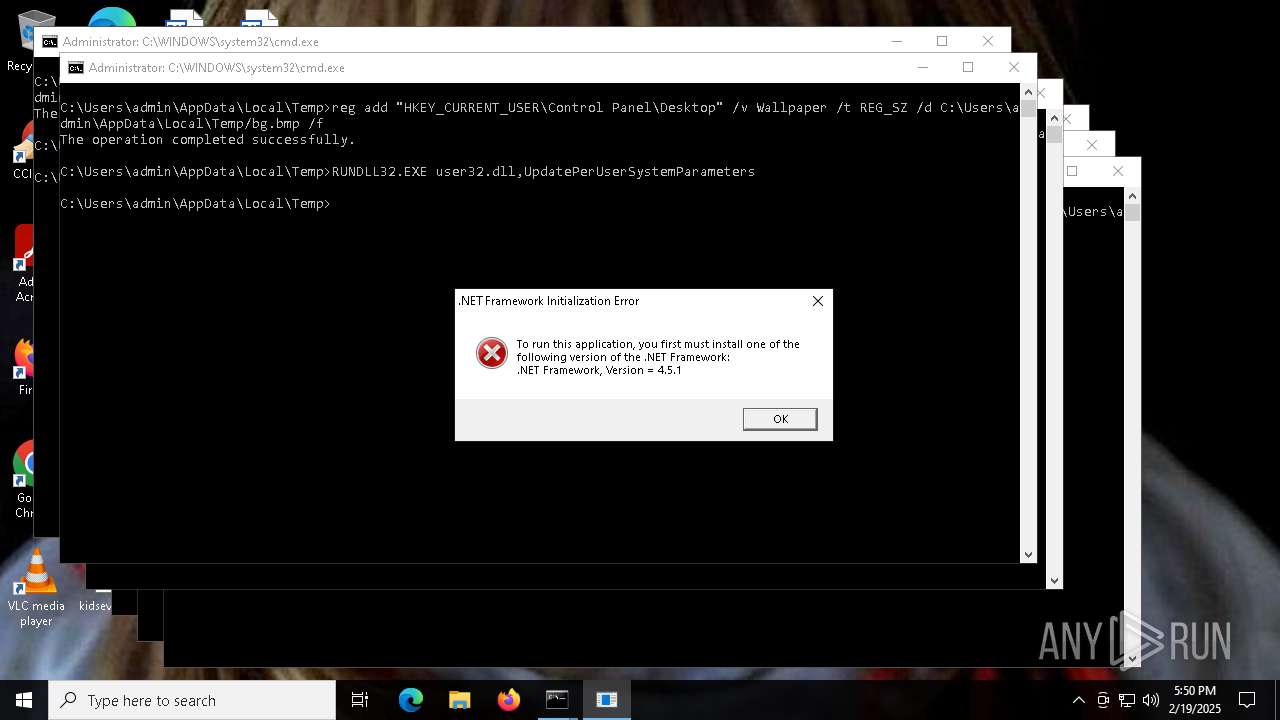
Executable content was dropped or overwritten
- Rubly4.exe (PID: 6440)
- mtrmbr.exe (PID: 6520)
- dt.exe (PID: 6540)
- mtr.exe (PID: 6720)
Reads security settings of Internet Explorer
- Rubly4.exe (PID: 6440)
- mtrmbr.exe (PID: 6520)
- dt.exe (PID: 6540)
- bg.exe (PID: 6564)
- mtr.exe (PID: 6720)
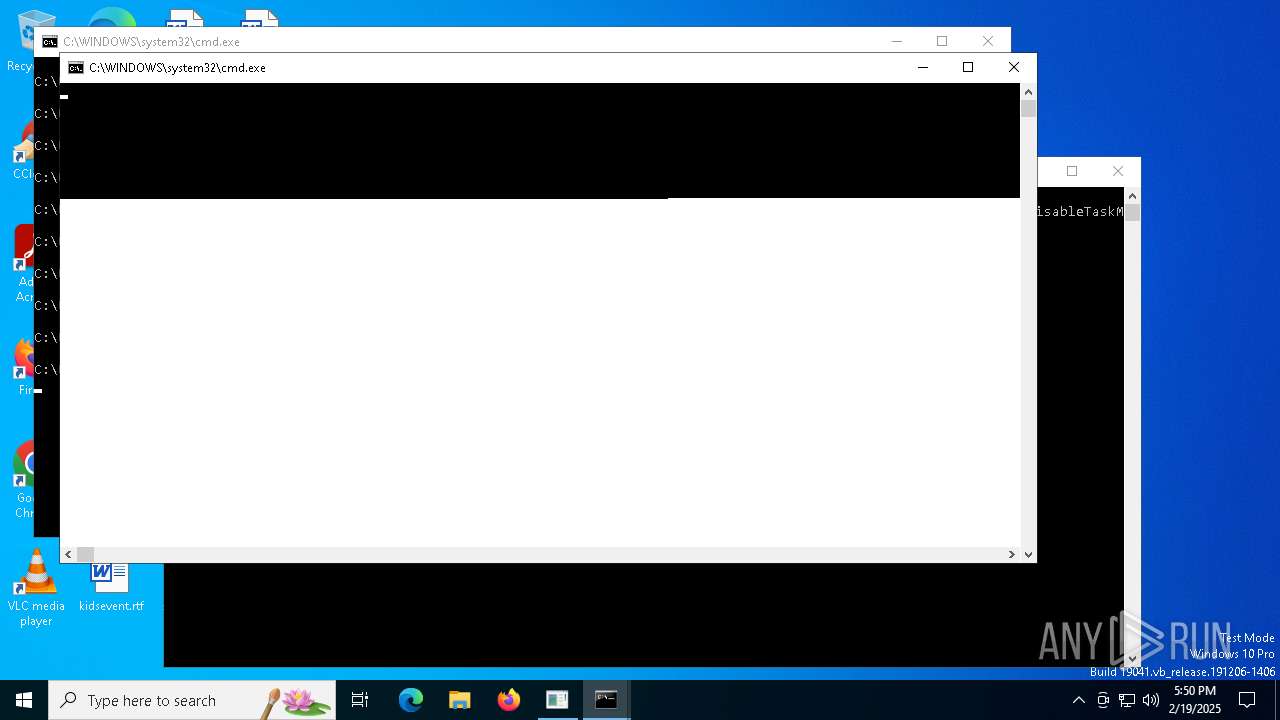
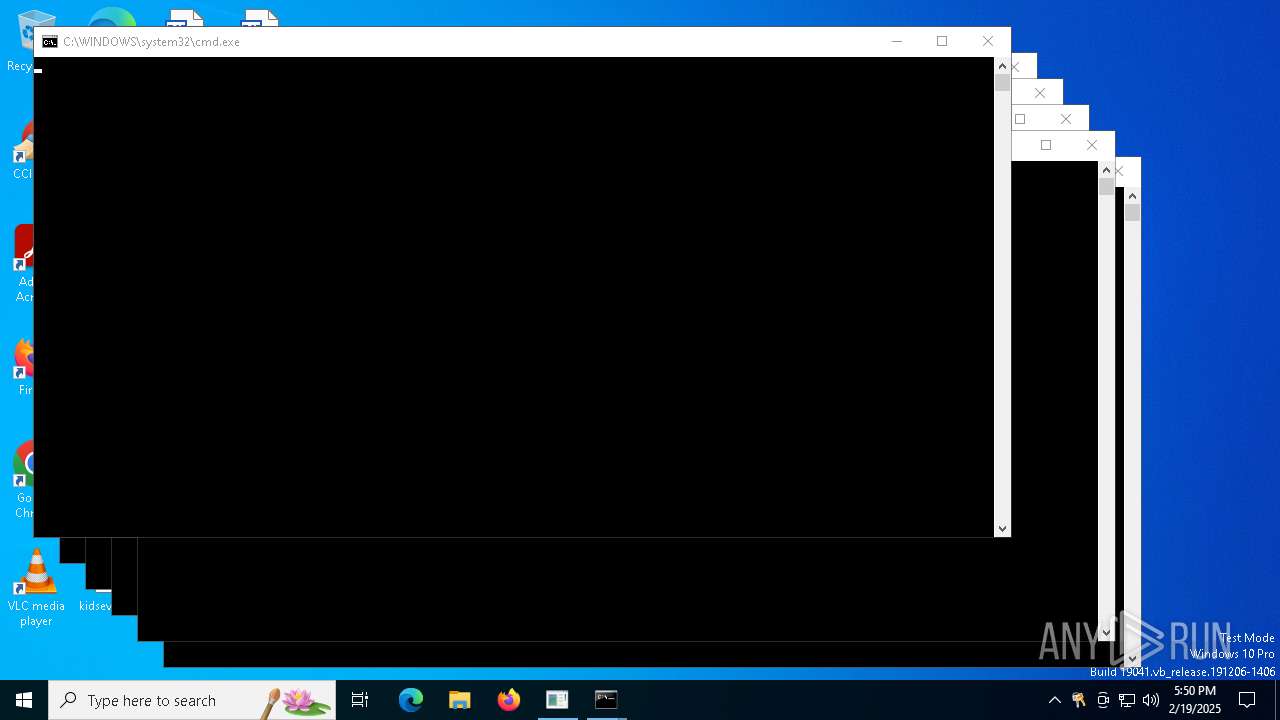
Executing commands from a ".bat" file
- Rubly4.exe (PID: 6440)
- bg.exe (PID: 6564)
- cmd.exe (PID: 6852)
- dt.exe (PID: 6744)
Starts CMD.EXE for commands execution
- Rubly4.exe (PID: 6440)
- bg.exe (PID: 6564)
- cmd.exe (PID: 6852)
- dt.exe (PID: 6744)
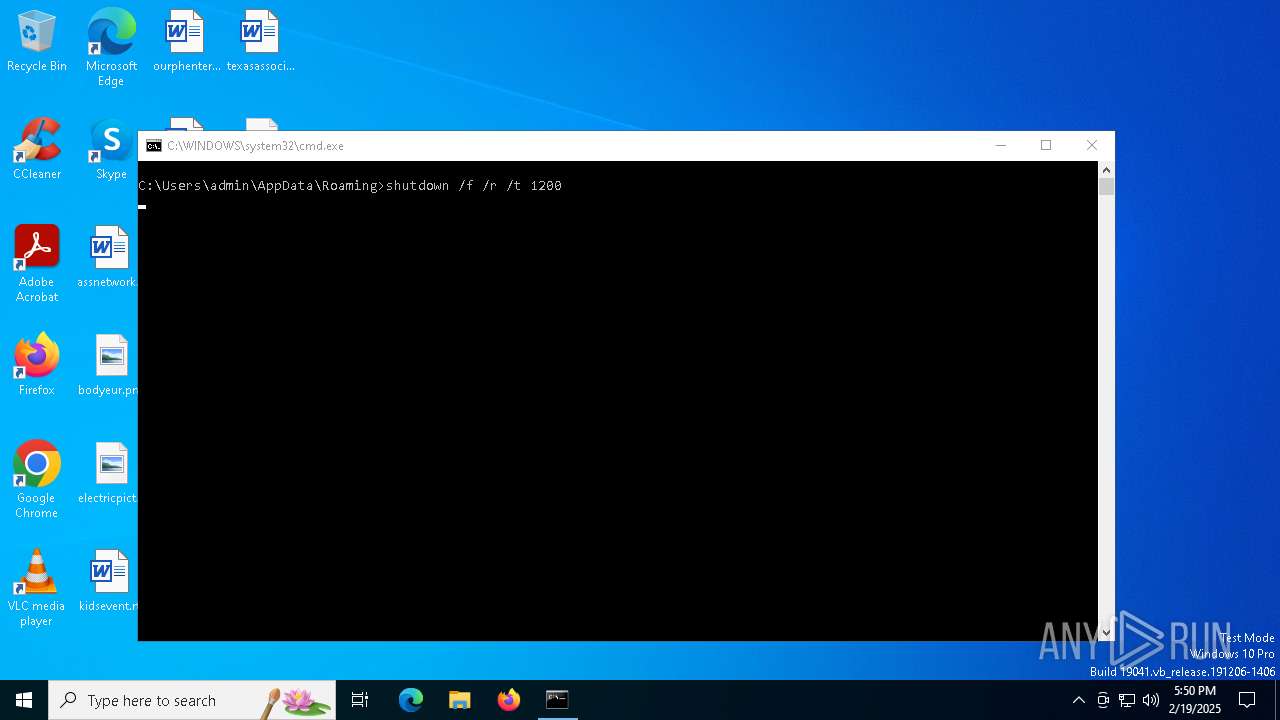
The system shut down or reboot
- cmd.exe (PID: 6588)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7004)
- cmd.exe (PID: 1556)
- cmd.exe (PID: 7036)
- cmd.exe (PID: 7000)
- cmd.exe (PID: 6976)
- cmd.exe (PID: 6984)
- cmd.exe (PID: 1412)
- cmd.exe (PID: 7124)
- cmd.exe (PID: 7144)
- cmd.exe (PID: 3840)
- cmd.exe (PID: 6188)
- cmd.exe (PID: 6212)
- cmd.exe (PID: 6704)
- cmd.exe (PID: 6192)
- cmd.exe (PID: 6860)
- cmd.exe (PID: 6584)
- cmd.exe (PID: 6524)
- cmd.exe (PID: 6712)
- cmd.exe (PID: 6804)
- cmd.exe (PID: 7320)
- cmd.exe (PID: 6676)
Application launched itself
- cmd.exe (PID: 6852)
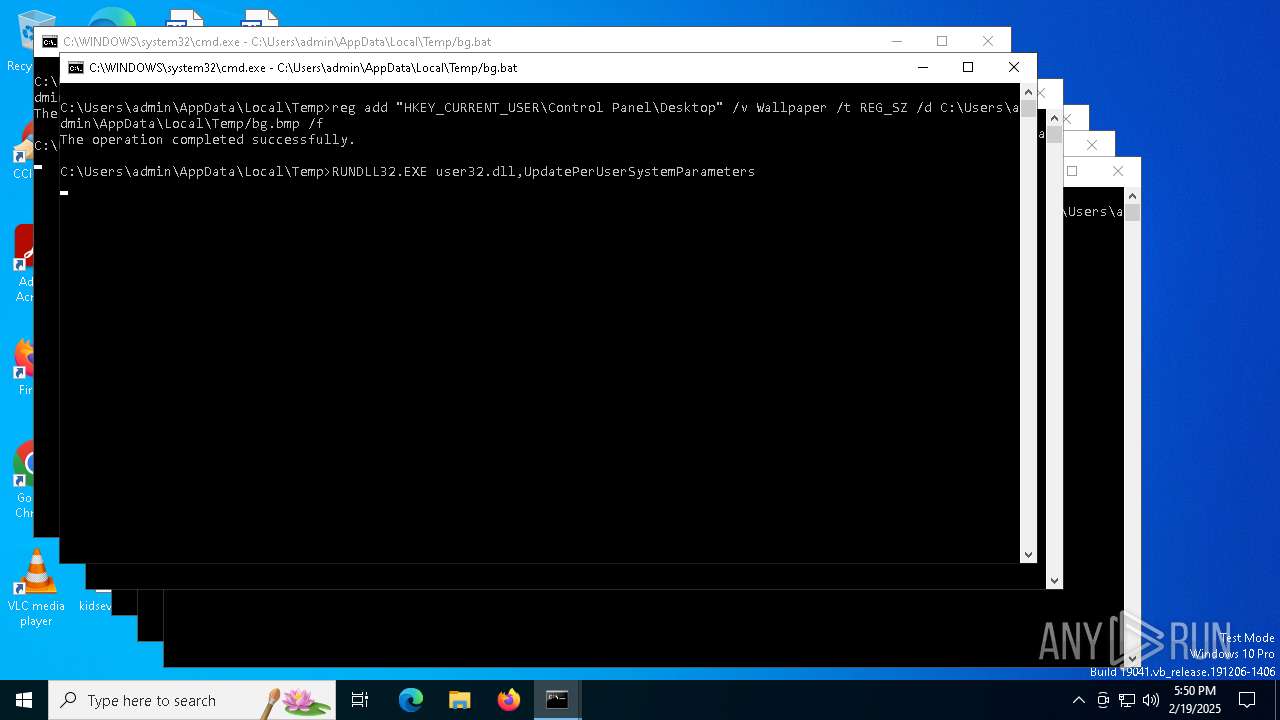
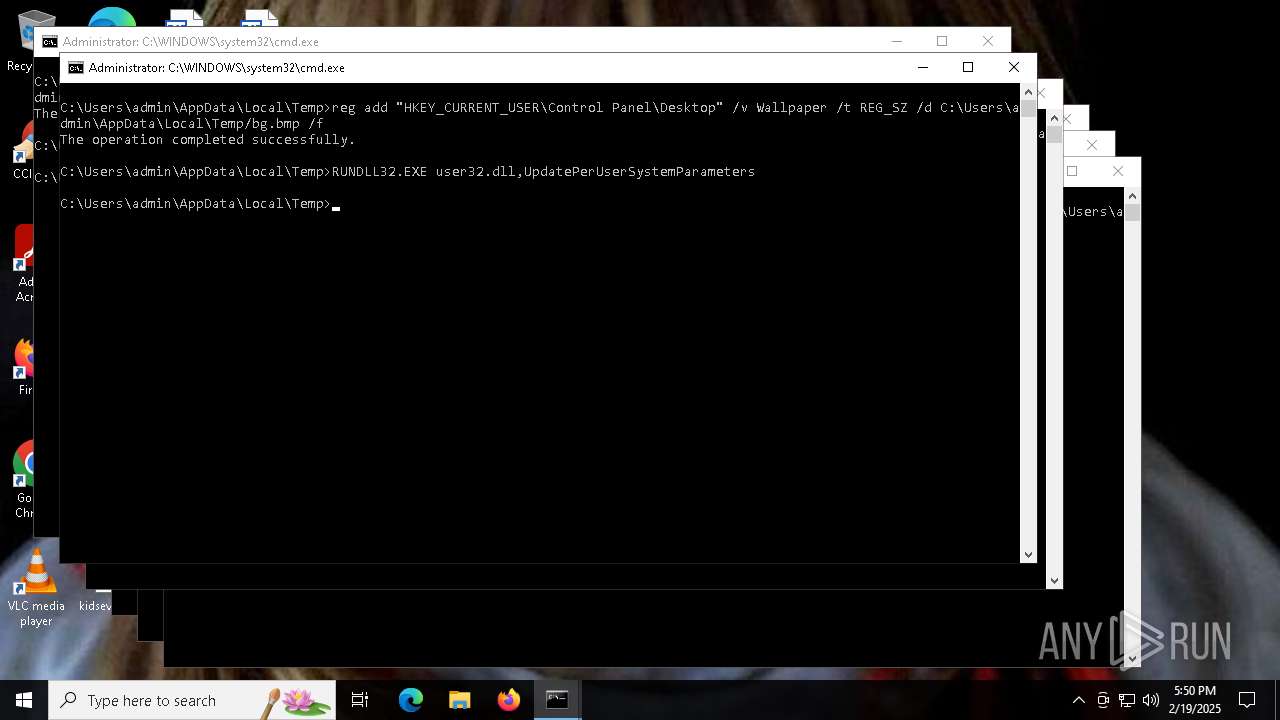
Changes the desktop background image
- reg.exe (PID: 6204)
- reg.exe (PID: 6672)
- reg.exe (PID: 6736)
- reg.exe (PID: 7052)
- reg.exe (PID: 6468)
- reg.exe (PID: 7100)
- reg.exe (PID: 6600)
- reg.exe (PID: 6560)
- reg.exe (PID: 7404)
- reg.exe (PID: 7208)
- reg.exe (PID: 7252)
- reg.exe (PID: 7192)
- reg.exe (PID: 7388)
- reg.exe (PID: 7476)
- reg.exe (PID: 7496)
- reg.exe (PID: 7536)
- reg.exe (PID: 7576)
- reg.exe (PID: 7508)
- reg.exe (PID: 7724)
- reg.exe (PID: 7732)
Reads the date of Windows installation
- mtr.exe (PID: 6720)
Starts itself from another location
- mtr.exe (PID: 6720)
INFO
Checks supported languages
- Rubly4.exe (PID: 6440)
- mtrmbr.exe (PID: 6520)
- dt.exe (PID: 6540)
- bg.exe (PID: 6564)
- dt.exe (PID: 6744)
- mbr.exe (PID: 6816)
- drpbx.exe (PID: 7228)
- mtr.exe (PID: 6720)
Creates files or folders in the user directory
- Rubly4.exe (PID: 6440)
- mtr.exe (PID: 6720)
Reads the computer name
- Rubly4.exe (PID: 6440)
- dt.exe (PID: 6540)
- mtrmbr.exe (PID: 6520)
- bg.exe (PID: 6564)
- mtr.exe (PID: 6720)
- drpbx.exe (PID: 7228)
Process checks computer location settings
- Rubly4.exe (PID: 6440)
- dt.exe (PID: 6540)
- mtrmbr.exe (PID: 6520)
- bg.exe (PID: 6564)
- mtr.exe (PID: 6720)
Creates files in the program directory
- mtrmbr.exe (PID: 6520)
Create files in a temporary directory
- dt.exe (PID: 6540)
- bg.exe (PID: 6564)
- dt.exe (PID: 6744)
Reads the machine GUID from the registry
- mtr.exe (PID: 6720)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:12:05 07:37:23+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 198656 |
| InitializedDataSize: | 227328 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1e239 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
226
Monitored processes
97
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1412 | C:\WINDOWS\system32\cmd.exe /K C:\Users\admin\AppData\Local\Temp/bg.bat | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1544 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1556 | C:\WINDOWS\system32\cmd.exe /K C:\Users\admin\AppData\Local\Temp/bg.bat | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3640 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3840 | C:\WINDOWS\system32\cmd.exe /K C:\Users\admin\AppData\Local\Temp/bg.bat | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5568 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6168 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6172 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6188 | C:\WINDOWS\system32\cmd.exe /K C:\Users\admin\AppData\Local\Temp/bg.bat | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6192 | C:\WINDOWS\system32\cmd.exe /K C:\Users\admin\AppData\Local\Temp/bg.bat | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 076
Read events
5 054
Write events
22
Delete events
0
Modification events
| (PID) Process: | (6720) mtr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | firefox.exe |
Value: C:\Users\admin\AppData\Roaming\Frfx\firefox.exe | |||
| (PID) Process: | (6560) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | Wallpaper |
Value: C:\Users\admin\AppData\Local\Temp/bg.bmp | |||
| (PID) Process: | (6468) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | Wallpaper |
Value: C:\Users\admin\AppData\Local\Temp/bg.bmp | |||
| (PID) Process: | (6204) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | Wallpaper |
Value: C:\Users\admin\AppData\Local\Temp/bg.bmp | |||
| (PID) Process: | (7192) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | Wallpaper |
Value: C:\Users\admin\AppData\Local\Temp/bg.bmp | |||
| (PID) Process: | (7252) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | Wallpaper |
Value: C:\Users\admin\AppData\Local\Temp/bg.bmp | |||
| (PID) Process: | (7404) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | Wallpaper |
Value: C:\Users\admin\AppData\Local\Temp/bg.bmp | |||
| (PID) Process: | (7496) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | Wallpaper |
Value: C:\Users\admin\AppData\Local\Temp/bg.bmp | |||
| (PID) Process: | (7536) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | Wallpaper |
Value: C:\Users\admin\AppData\Local\Temp/bg.bmp | |||
| (PID) Process: | (7576) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | Wallpaper |
Value: C:\Users\admin\AppData\Local\Temp/bg.bmp | |||
Executable files
8
Suspicious files
1
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6816 | mbr.exe | \Device\Harddisk0\DR0 | — | |
MD5:— | SHA256:— | |||
| 6440 | Rubly4.exe | C:\Users\admin\AppData\Roaming\bg.exe | executable | |
MD5:19ED87E5BF49F790025490E8368B1EC5 | SHA256:0AE484AB8AAE75267C541ABD0BD95CAFAE840BD9A9F67AEB1473682CF9B99D30 | |||
| 6440 | Rubly4.exe | C:\Users\admin\AppData\Roaming\restart.bat | text | |
MD5:B1E5726BD11A59CF5AB2F3A655108569 | SHA256:77A9C6AA0DC9979F56DDAAC475E1EF31462EDC559B542763CF94E658BE9DE8AC | |||
| 6564 | bg.exe | C:\Users\admin\AppData\Local\Temp\run.bat | text | |
MD5:BE7966CBF9D04A6300FEBEBC0802FD36 | SHA256:F7BDF62E1E46336CBE0F25681A5AC643D59E6FB4CD69BF55C0B2D5DA746CA59A | |||
| 6520 | mtrmbr.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\StartUp\mbr.exe | executable | |
MD5:E5717D5AA01C544162C615E3F2C41453 | SHA256:4902850B09C940537CBAAAFD83CCBE906ECB735ED58963093B718827FFB8D8EE | |||
| 6440 | Rubly4.exe | C:\Users\admin\AppData\Roaming\dt.exe | executable | |
MD5:79466F9BB9E981220A43897D33E57D1E | SHA256:08F2977CB8EDB77EB870878088EB64C23395C67BDD071D303FF10532D72C754A | |||
| 6540 | dt.exe | C:\Users\admin\AppData\Local\Temp\dt.exe | executable | |
MD5:5E46FFAB95250291C5410237340B9439 | SHA256:5FC8D9B02BE1321863CC46BCDE6E9A77EF2B6A24FF8F15F5F4F7E36C62D9DE34 | |||
| 6564 | bg.exe | C:\Users\admin\AppData\Local\Temp\bg.bat | text | |
MD5:308060FF726CB2BE6EE2023C1B2A401D | SHA256:0C0760682D75388A03CC7BA621D338871FC66E17F6D82C8B5147371CB7CE9A47 | |||
| 6564 | bg.exe | C:\Users\admin\AppData\Local\Temp\bg.bmp | binary | |
MD5:889074311BF2B2985E461C4AA4971ED2 | SHA256:DD9C56A65E28CB73BDBEF0CA97608A564465E736483CEF06EAE378EA6F2DB836 | |||
| 6720 | mtr.exe | C:\Users\admin\AppData\Local\Drpbx\drpbx.exe | executable | |
MD5:D124BB6A1419C81A887317E08745147C | SHA256:17772E58ABA8A700B98C5422A94667C49330DF0DB1EEF631B740485350A7C408 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
34
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.173:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
8156 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
1356 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1356 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5340 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 92.123.104.32:443 | — | Akamai International B.V. | DE | unknown |
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.173:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 104.79.89.142:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 92.123.104.34:443 | — | Akamai International B.V. | DE | unknown |
1176 | svchost.exe | 40.126.31.0:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |