| File name: | Rubly4.exe |
| Full analysis: | https://app.any.run/tasks/0155df8b-1bff-4c06-9e26-86477c1915d3 |
| Verdict: | Malicious activity |
| Analysis date: | February 11, 2022, 09:58:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | CACE46A66ADD9416A9657AF4819556F0 |
| SHA1: | C847BD2A4657BE55CE0FF7069AE8E16D5878F09E |
| SHA256: | A54EF676ED88E1B7A5C61F7CB652EF0BFD59CFF076E7C45E535C19F742A3216C |
| SSDEEP: | 12288:7GqN/XdctpVtkMtsyDqBQ0tA3nyF0Fh0zJmViYV5yvQX05oWI:lNcBtkUqBQ0tknx5yIXgoWI |
MALICIOUS
Drops executable file immediately after starts
- Rubly4.exe (PID: 3508)
- mtrmbr.exe (PID: 3920)
- dt.exe (PID: 2520)
Writes to a start menu file
- mtrmbr.exe (PID: 3920)
Task Manager has been disabled (taskmgr)
- reg.exe (PID: 2976)
Changes the autorun value in the registry
- mtr.exe (PID: 2516)
Application was dropped or rewritten from another process
- dt.exe (PID: 2520)
- mtrmbr.exe (PID: 3920)
- bg.exe (PID: 3044)
- dt.exe (PID: 1972)
- mtr.exe (PID: 2516)
- drpbx.exe (PID: 3608)
- mbr.exe (PID: 3496)
Actions looks like stealing of personal data
- drpbx.exe (PID: 3608)
Steals credentials from Web Browsers
- drpbx.exe (PID: 3608)
Modifies files in Chrome extension folder
- drpbx.exe (PID: 3608)
SUSPICIOUS
Creates files in the user directory
- Rubly4.exe (PID: 3508)
- mtr.exe (PID: 2516)
- drpbx.exe (PID: 3608)
Checks supported languages
- Rubly4.exe (PID: 3508)
- mtrmbr.exe (PID: 3920)
- mtr.exe (PID: 2516)
- mbr.exe (PID: 3496)
- cmd.exe (PID: 3344)
- dt.exe (PID: 2520)
- bg.exe (PID: 3044)
- cmd.exe (PID: 2668)
- cmd.exe (PID: 3188)
- cmd.exe (PID: 3036)
- dt.exe (PID: 1972)
- cmd.exe (PID: 1300)
- cmd.exe (PID: 300)
- cmd.exe (PID: 3924)
- cmd.exe (PID: 3096)
- cmd.exe (PID: 3224)
- cmd.exe (PID: 2084)
- cmd.exe (PID: 3588)
- cmd.exe (PID: 3784)
- cmd.exe (PID: 560)
- cmd.exe (PID: 3628)
- cmd.exe (PID: 1164)
- cmd.exe (PID: 3856)
- drpbx.exe (PID: 3608)
- cmd.exe (PID: 864)
- cmd.exe (PID: 2952)
- cmd.exe (PID: 3632)
- cmd.exe (PID: 3404)
- cmd.exe (PID: 3916)
- cmd.exe (PID: 3952)
- cmd.exe (PID: 3196)
Reads the computer name
- Rubly4.exe (PID: 3508)
- mtrmbr.exe (PID: 3920)
- dt.exe (PID: 2520)
- bg.exe (PID: 3044)
- mtr.exe (PID: 2516)
Executable content was dropped or overwritten
- Rubly4.exe (PID: 3508)
- mtrmbr.exe (PID: 3920)
- dt.exe (PID: 2520)
- mtr.exe (PID: 2516)
Drops a file that was compiled in debug mode
- Rubly4.exe (PID: 3508)
- mtrmbr.exe (PID: 3920)
- mtr.exe (PID: 2516)
Creates files in the program directory
- mtrmbr.exe (PID: 3920)
- drpbx.exe (PID: 3608)
Drops a file with too old compile date
- mtrmbr.exe (PID: 3920)
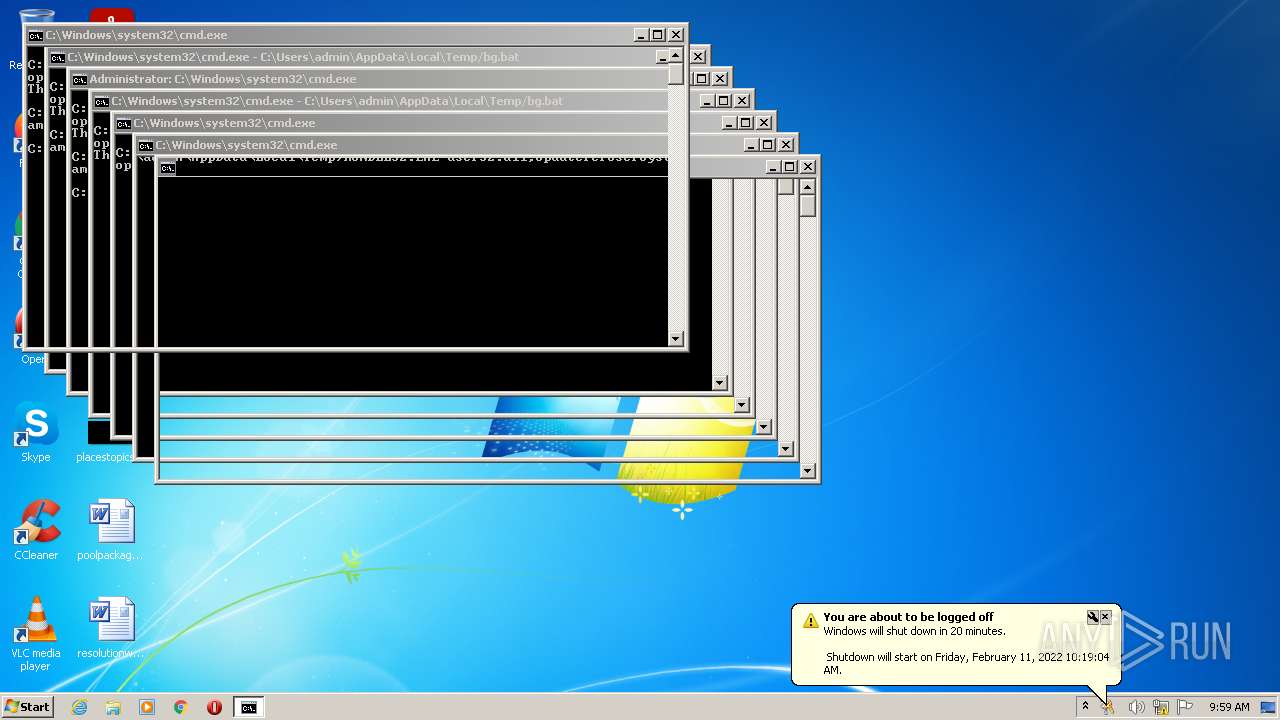
Starts CMD.EXE for commands execution
- Rubly4.exe (PID: 3508)
- dt.exe (PID: 1972)
- bg.exe (PID: 3044)
- cmd.exe (PID: 3188)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2668)
- cmd.exe (PID: 3036)
- cmd.exe (PID: 1300)
- cmd.exe (PID: 300)
- cmd.exe (PID: 3224)
- cmd.exe (PID: 3924)
- cmd.exe (PID: 3096)
- cmd.exe (PID: 3588)
- cmd.exe (PID: 3784)
- cmd.exe (PID: 3856)
- cmd.exe (PID: 560)
- cmd.exe (PID: 3628)
- cmd.exe (PID: 2084)
- cmd.exe (PID: 1164)
- cmd.exe (PID: 2952)
- cmd.exe (PID: 864)
- cmd.exe (PID: 3632)
- cmd.exe (PID: 3952)
- cmd.exe (PID: 3404)
- cmd.exe (PID: 3916)
- cmd.exe (PID: 3196)
Application launched itself
- cmd.exe (PID: 3188)
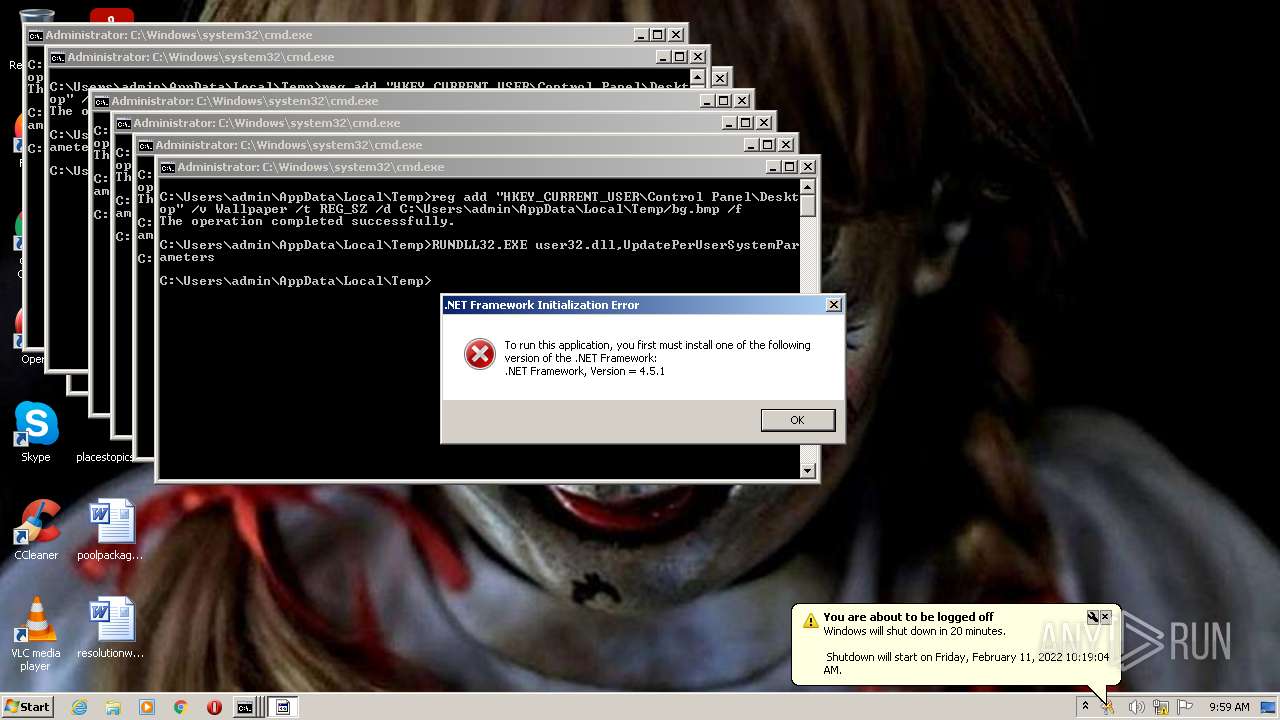
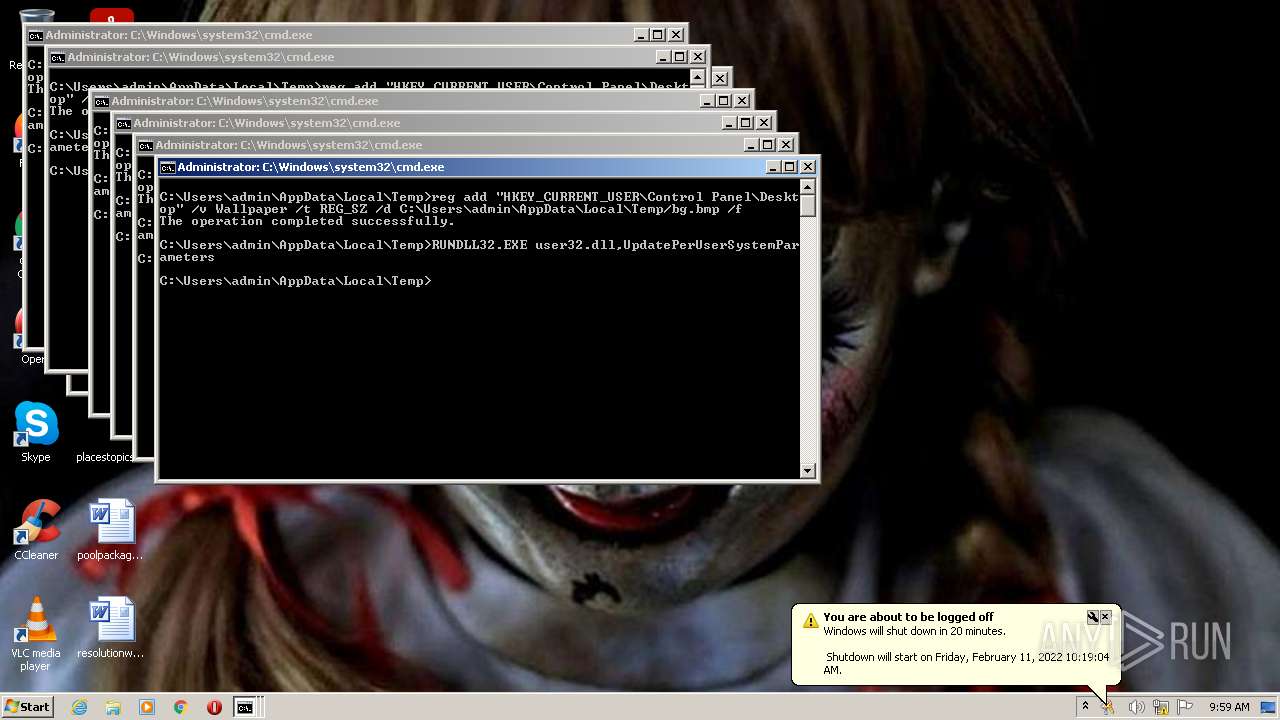
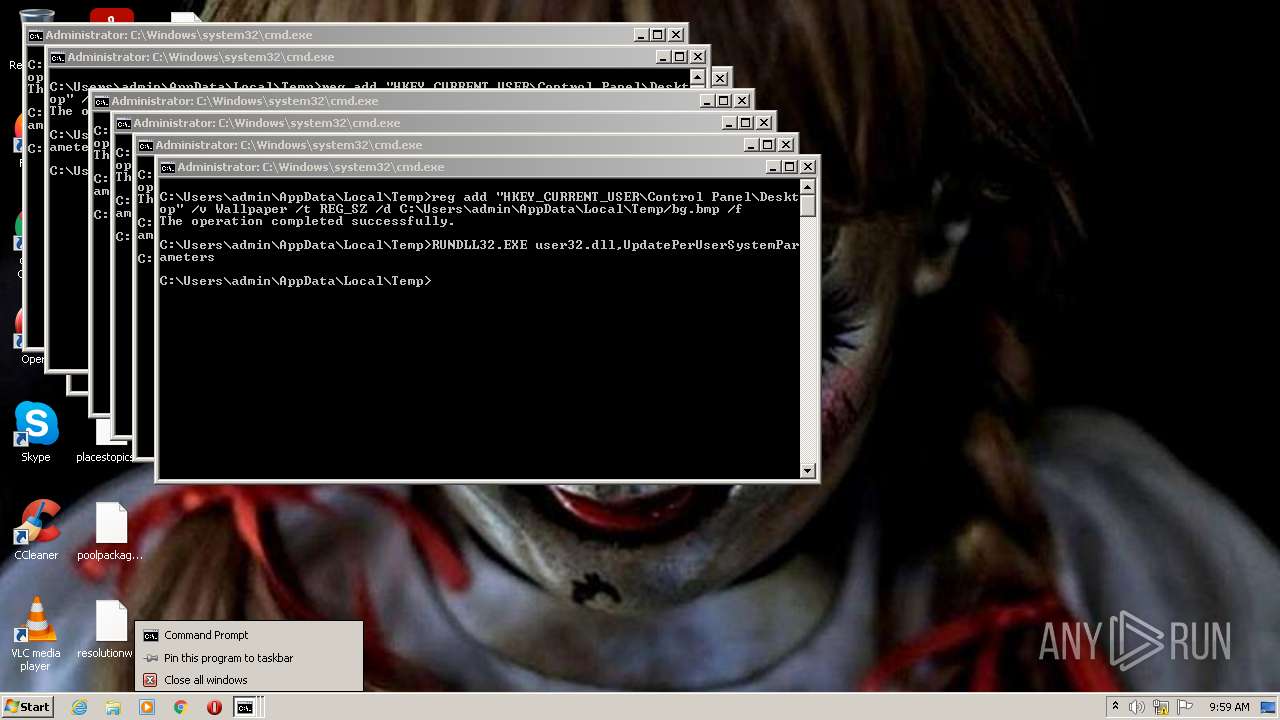
Changes the desktop background image
- reg.exe (PID: 3692)
- reg.exe (PID: 900)
- reg.exe (PID: 2948)
- reg.exe (PID: 776)
- reg.exe (PID: 664)
- reg.exe (PID: 3668)
- reg.exe (PID: 2216)
- reg.exe (PID: 2916)
- reg.exe (PID: 4068)
- reg.exe (PID: 2432)
- reg.exe (PID: 3260)
- reg.exe (PID: 1512)
- reg.exe (PID: 3872)
- reg.exe (PID: 2696)
- reg.exe (PID: 524)
- reg.exe (PID: 3068)
- reg.exe (PID: 2432)
- reg.exe (PID: 344)
- reg.exe (PID: 3700)
- reg.exe (PID: 2008)
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 300)
- cmd.exe (PID: 1300)
- cmd.exe (PID: 3036)
- cmd.exe (PID: 3096)
- cmd.exe (PID: 3224)
- cmd.exe (PID: 3924)
- cmd.exe (PID: 3588)
- cmd.exe (PID: 3784)
- cmd.exe (PID: 2084)
- cmd.exe (PID: 560)
- cmd.exe (PID: 1164)
- cmd.exe (PID: 864)
- cmd.exe (PID: 3628)
- cmd.exe (PID: 3856)
- cmd.exe (PID: 2952)
- cmd.exe (PID: 3952)
- cmd.exe (PID: 3632)
- cmd.exe (PID: 3196)
- cmd.exe (PID: 3404)
- cmd.exe (PID: 3916)
Starts itself from another location
- mtr.exe (PID: 2516)
Drops a file with a compile date too recent
- drpbx.exe (PID: 3608)
INFO
Checks supported languages
- reg.exe (PID: 2976)
- reg.exe (PID: 3692)
- shutdown.exe (PID: 3884)
- reg.exe (PID: 900)
- rundll32.exe (PID: 4092)
- rundll32.exe (PID: 1188)
- rundll32.exe (PID: 984)
- reg.exe (PID: 2948)
- reg.exe (PID: 664)
- rundll32.exe (PID: 1864)
- reg.exe (PID: 776)
- rundll32.exe (PID: 3772)
- reg.exe (PID: 2916)
- reg.exe (PID: 3668)
- reg.exe (PID: 2216)
- rundll32.exe (PID: 2788)
- rundll32.exe (PID: 2284)
- reg.exe (PID: 4068)
- reg.exe (PID: 2432)
- reg.exe (PID: 1512)
- rundll32.exe (PID: 888)
- reg.exe (PID: 3260)
- reg.exe (PID: 3872)
- rundll32.exe (PID: 3888)
- rundll32.exe (PID: 388)
- reg.exe (PID: 524)
- rundll32.exe (PID: 980)
- rundll32.exe (PID: 2760)
- reg.exe (PID: 2696)
- rundll32.exe (PID: 2976)
- rundll32.exe (PID: 3476)
- rundll32.exe (PID: 2332)
- rundll32.exe (PID: 1156)
- reg.exe (PID: 2008)
- reg.exe (PID: 2432)
- reg.exe (PID: 344)
- reg.exe (PID: 3068)
- reg.exe (PID: 3700)
- rundll32.exe (PID: 2912)
- rundll32.exe (PID: 476)
- rundll32.exe (PID: 3136)
- rundll32.exe (PID: 2512)
Reads the computer name
- shutdown.exe (PID: 3884)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x1e239 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 227328 |
| CodeSize: | 198656 |
| LinkerVersion: | 14 |
| PEType: | PE32 |
| TimeStamp: | 2019:12:05 08:37:23+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2019 07:37:23 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 05-Dec-2019 07:37:23 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0003060F | 0x00030800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.69302 |
.rdata | 0x00032000 | 0x0000A402 | 0x0000A600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.20298 |
.data | 0x0003D000 | 0x000238B0 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.83802 |
.gfids | 0x00061000 | 0x000000E8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.11817 |
.rsrc | 0x00062000 | 0x00029B68 | 0x00029C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.31308 |
.reloc | 0x0008C000 | 0x0000212C | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.62179 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.26192 | 1875 | Latin 1 / Western European | English - United States | RT_MANIFEST |
7 | 3.1586 | 482 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 3.11685 | 460 | Latin 1 / Western European | English - United States | RT_STRING |
9 | 3.11236 | 440 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 2.99727 | 326 | Latin 1 / Western European | English - United States | RT_STRING |
11 | 3.2036 | 1094 | Latin 1 / Western European | English - United States | RT_STRING |
12 | 3.12889 | 358 | Latin 1 / Western European | English - United States | RT_STRING |
13 | 3.01704 | 338 | Latin 1 / Western European | English - United States | RT_STRING |
14 | 2.94627 | 266 | Latin 1 / Western European | English - United States | RT_STRING |
15 | 2.83619 | 188 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
KERNEL32.dll |
USER32.dll (delay-loaded) |
gdiplus.dll |
Total processes
136
Monitored processes
74
Malicious processes
5
Suspicious processes
22
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | C:\Windows\system32\cmd.exe /K C:\Users\admin\AppData\Local\Temp/bg.bat | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 344 | reg add "HKEY_CURRENT_USER\Control Panel\Desktop" /v Wallpaper /t REG_SZ /d C:\Users\admin\AppData\Local\Temp/bg.bmp /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 388 | RUNDLL32.EXE user32.dll,UpdatePerUserSystemParameters | C:\Windows\system32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 476 | RUNDLL32.EXE user32.dll,UpdatePerUserSystemParameters | C:\Windows\system32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 524 | reg add "HKEY_CURRENT_USER\Control Panel\Desktop" /v Wallpaper /t REG_SZ /d C:\Users\admin\AppData\Local\Temp/bg.bmp /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 560 | C:\Windows\system32\cmd.exe /K C:\Users\admin\AppData\Local\Temp/bg.bat | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 664 | reg add "HKEY_CURRENT_USER\Control Panel\Desktop" /v Wallpaper /t REG_SZ /d C:\Users\admin\AppData\Local\Temp/bg.bmp /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 776 | reg add "HKEY_CURRENT_USER\Control Panel\Desktop" /v Wallpaper /t REG_SZ /d C:\Users\admin\AppData\Local\Temp/bg.bmp /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 864 | C:\Windows\system32\cmd.exe /K C:\Users\admin\AppData\Local\Temp/bg.bat | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 888 | RUNDLL32.EXE user32.dll,UpdatePerUserSystemParameters | C:\Windows\system32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
56 890
Read events
56 828
Write events
62
Delete events
0
Modification events
| (PID) Process: | (3508) Rubly4.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3508) Rubly4.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3508) Rubly4.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3508) Rubly4.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3920) mtrmbr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3920) mtrmbr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3920) mtrmbr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3920) mtrmbr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3044) bg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3044) bg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
8
Suspicious files
4 628
Text files
66
Unknown types
47
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3920 | mtrmbr.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\StartUp\mbr.exe | executable | |
MD5:E5717D5AA01C544162C615E3F2C41453 | SHA256:4902850B09C940537CBAAAFD83CCBE906ECB735ED58963093B718827FFB8D8EE | |||
| 3508 | Rubly4.exe | C:\Users\admin\AppData\Roaming\bg.exe | executable | |
MD5:19ED87E5BF49F790025490E8368B1EC5 | SHA256:0AE484AB8AAE75267C541ABD0BD95CAFAE840BD9A9F67AEB1473682CF9B99D30 | |||
| 3508 | Rubly4.exe | C:\Users\admin\AppData\Roaming\restart.bat | text | |
MD5:B1E5726BD11A59CF5AB2F3A655108569 | SHA256:77A9C6AA0DC9979F56DDAAC475E1EF31462EDC559B542763CF94E658BE9DE8AC | |||
| 2520 | dt.exe | C:\Users\admin\AppData\Local\Temp\dt.exe | executable | |
MD5:5E46FFAB95250291C5410237340B9439 | SHA256:5FC8D9B02BE1321863CC46BCDE6E9A77EF2B6A24FF8F15F5F4F7E36C62D9DE34 | |||
| 1972 | dt.exe | C:\Users\admin\AppData\Local\Temp\CC51.tmp\disable_taskmgr.bat | text | |
MD5:3FC537B642D3756646715325299C6367 | SHA256:708511C356493E41CA103DB51B8DF3FB57898DDB2BB7CF4F11560FACDE9425ED | |||
| 3608 | drpbx.exe | C:\Program Files\Mozilla Firefox\firefox.VisualElementsManifest.xml.rubly | binary | |
MD5:A637BE9E9DE520314E46CD5674127E31 | SHA256:B45E9F96D5A59DE1D8C8F963DB51CCE1168B0FC885D822375C0BB31745E56EFB | |||
| 3608 | drpbx.exe | C:\Program Files\Notepad++\contextMenu.xml.rubly | binary | |
MD5:BE71D95C47DFAD9533F15D52CF2566D5 | SHA256:2501FE92DDBF8D2AE4B05D348504D090268C0E7397188856F38E4E72C5D4E918 | |||
| 3608 | drpbx.exe | C:\Program Files\Notepad++\stylers.model.xml.rubly | binary | |
MD5:D08290B0A29A17B244E72FBDDBE7A8CB | SHA256:1CF956464D997A8FBE1DC5BA8C0A293F84CCA9CA6B17E081E0A76B8E509599B6 | |||
| 3508 | Rubly4.exe | C:\Users\admin\AppData\Roaming\dt.exe | executable | |
MD5:79466F9BB9E981220A43897D33E57D1E | SHA256:08F2977CB8EDB77EB870878088EB64C23395C67BDD071D303FF10532D72C754A | |||
| 3044 | bg.exe | C:\Users\admin\AppData\Local\Temp\bg.bat | text | |
MD5:308060FF726CB2BE6EE2023C1B2A401D | SHA256:0C0760682D75388A03CC7BA621D338871FC66E17F6D82C8B5147371CB7CE9A47 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report