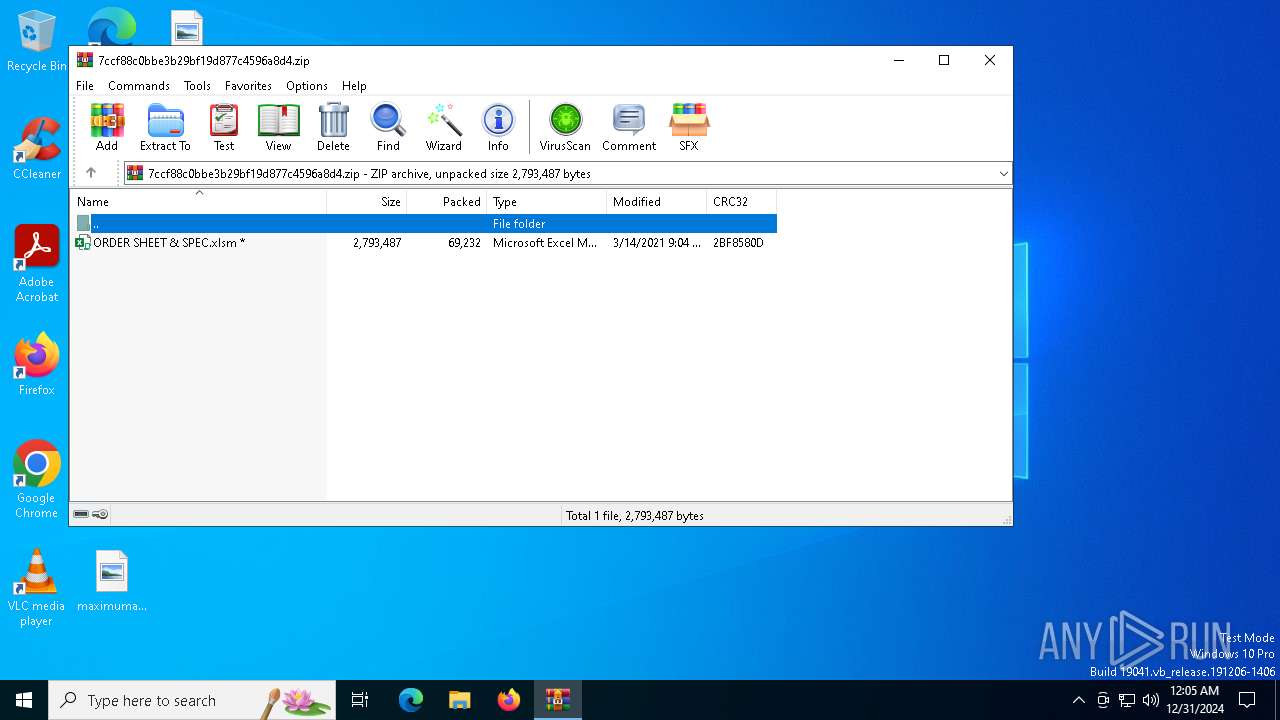
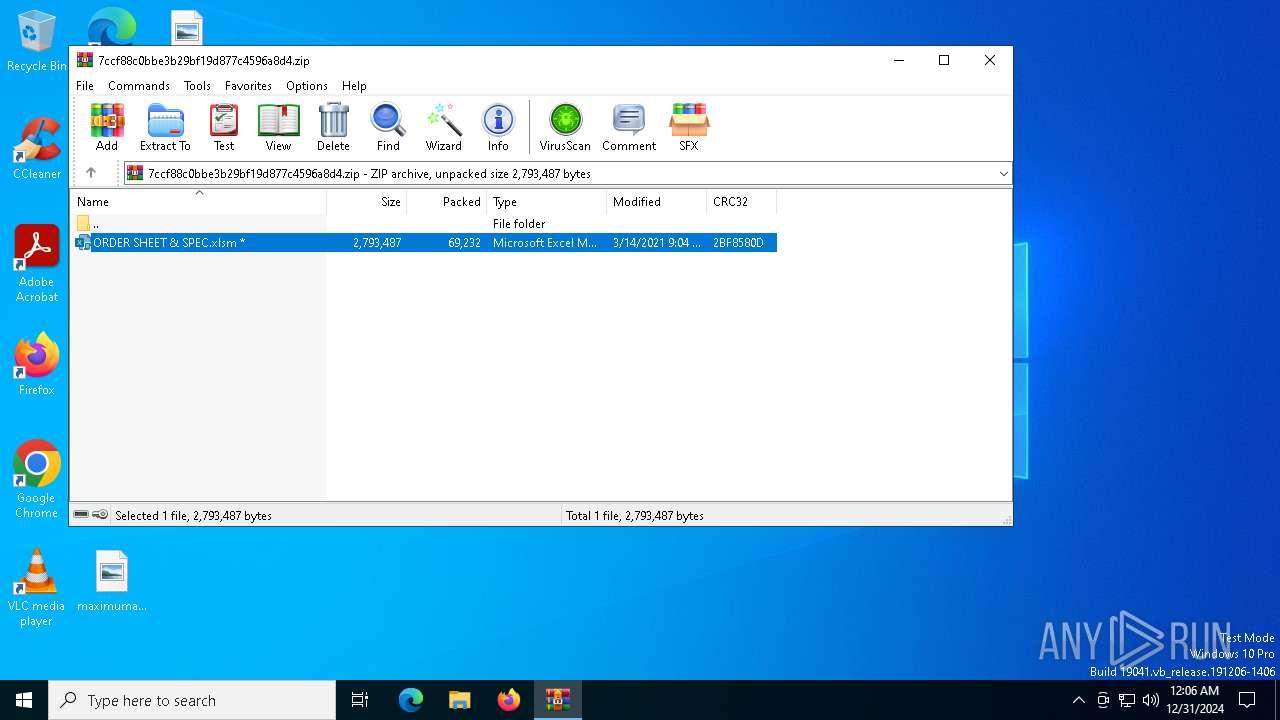
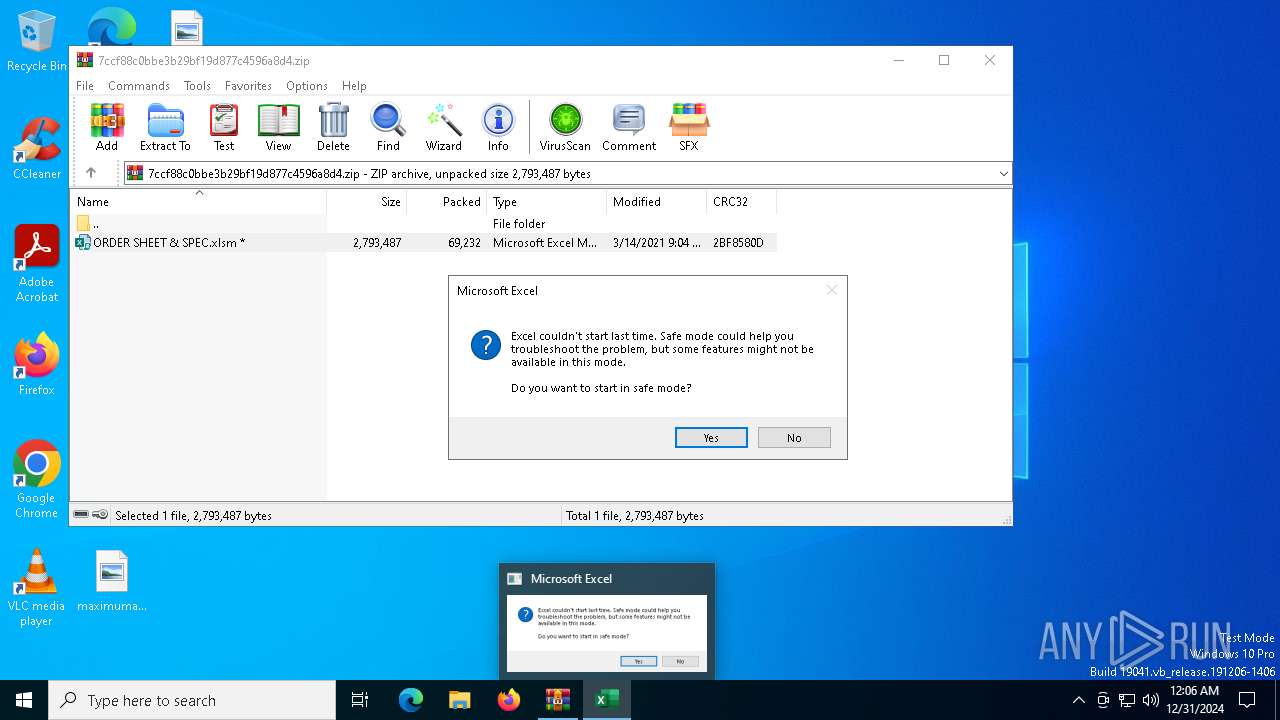
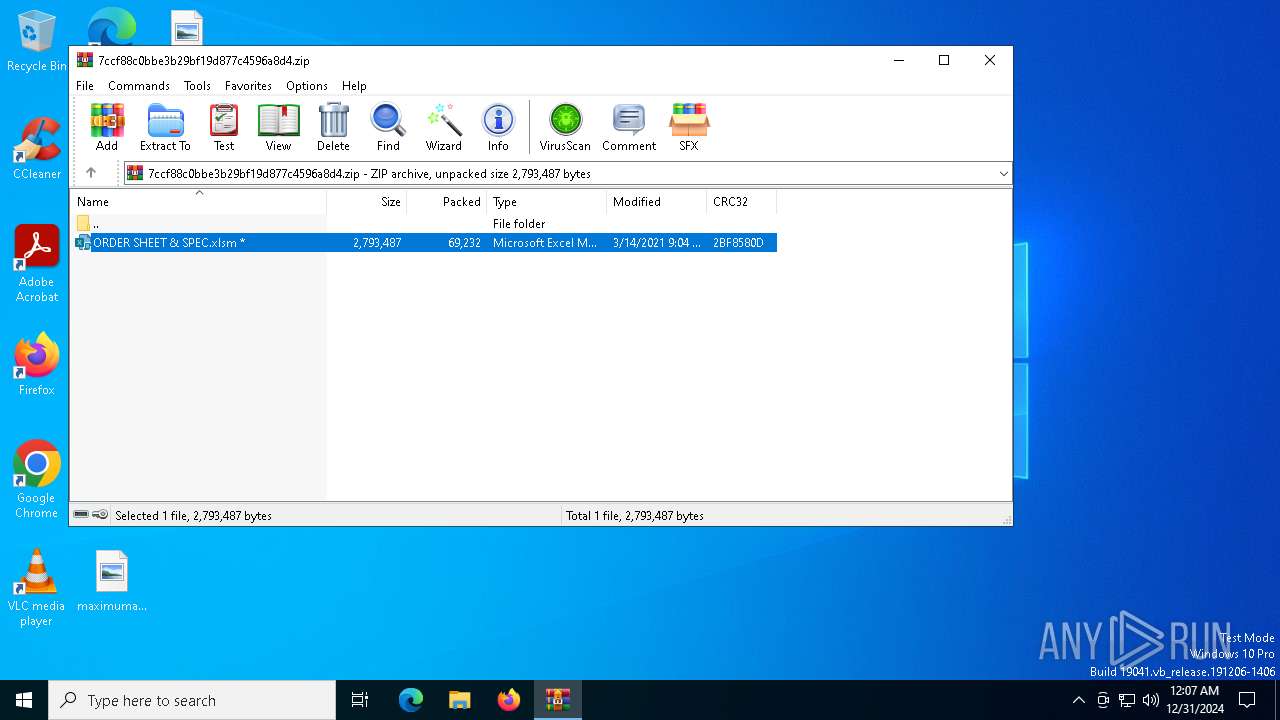
| File name: | 7ccf88c0bbe3b29bf19d877c4596a8d4.zip |
| Full analysis: | https://app.any.run/tasks/be12faf1-35ff-4752-bd00-c16c4c0f85bf |
| Verdict: | Malicious activity |
| Analysis date: | December 31, 2024, 00:04:43 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
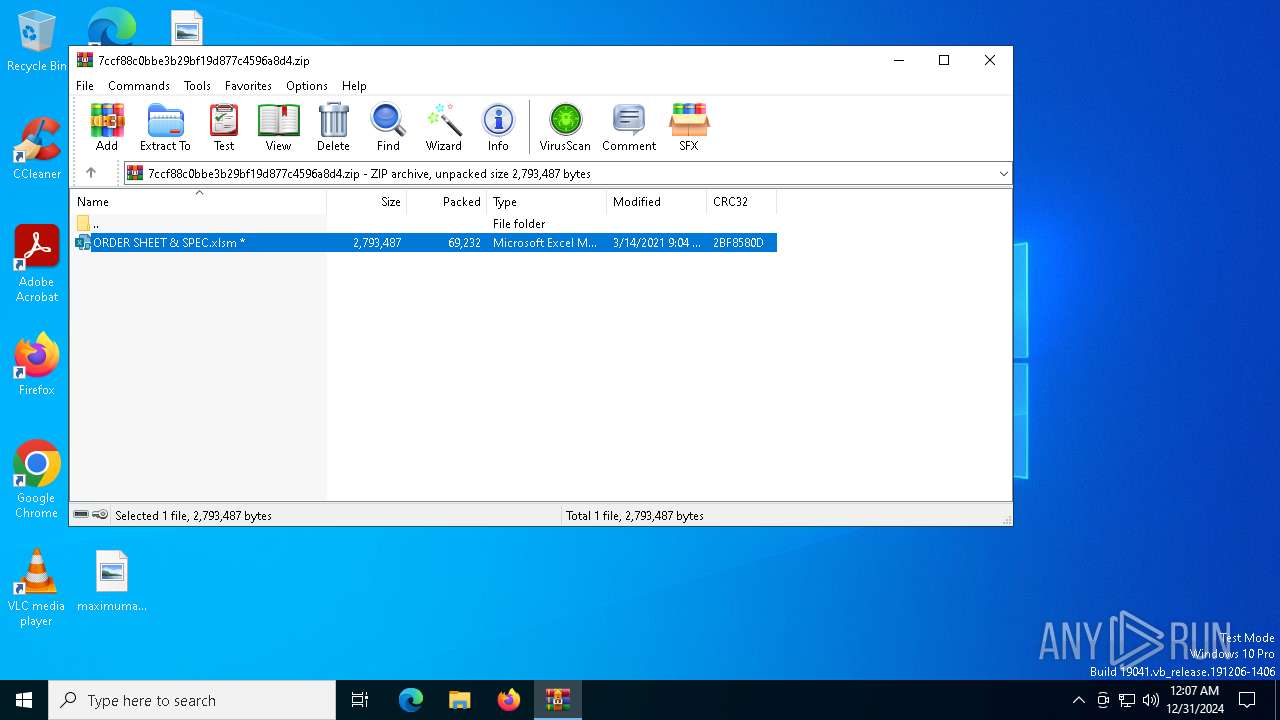
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | ADEE407A5D9F4425707FE5BD4C25AA14 |
| SHA1: | 5A99F6B3B106DAF23BA2C29F2FF94CB118703414 |
| SHA256: | A53DB45F1D4A2F36EBC0B0E268D2073BABA89CA6C1D05FE9A06EF395E8658A51 |
| SSDEEP: | 1536:jjaEudvK51sOagtBDPihqGGJRvbB8lmAqQap28rxmQ3wIUG7ChXtZlYGdf:jejdvK17JKhqNjv3p2oxzw67CVtZlYi |
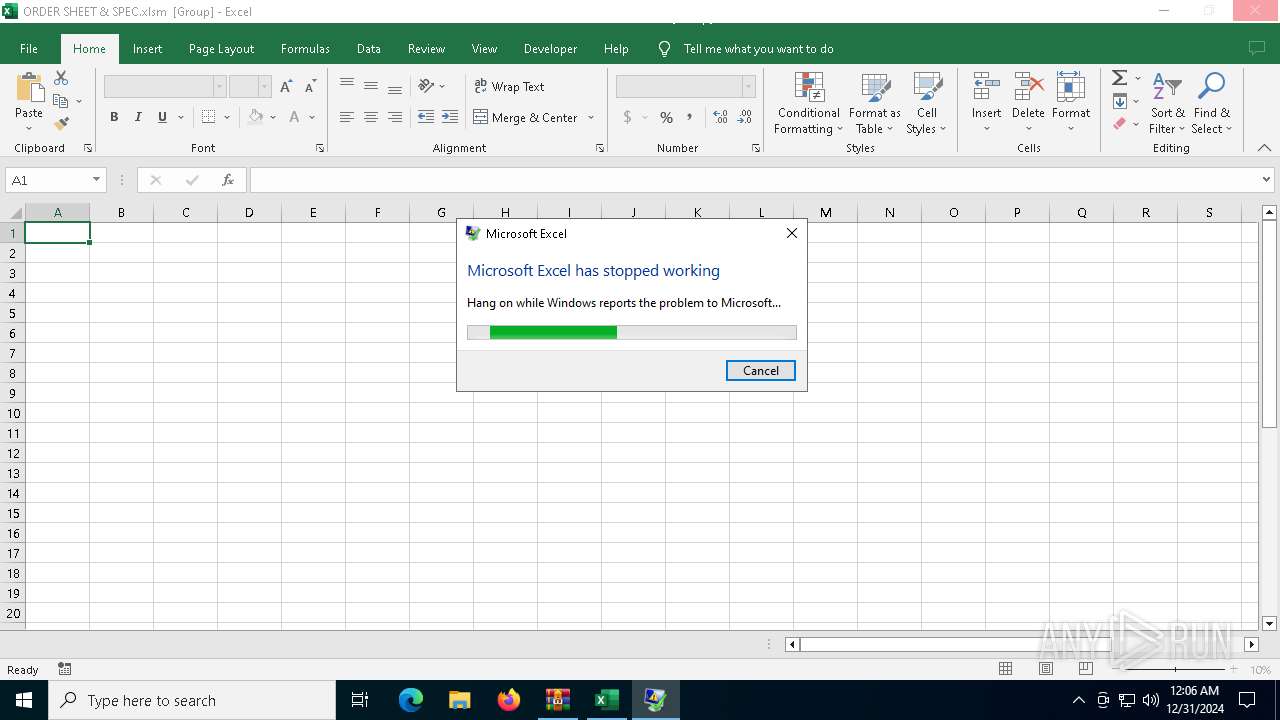
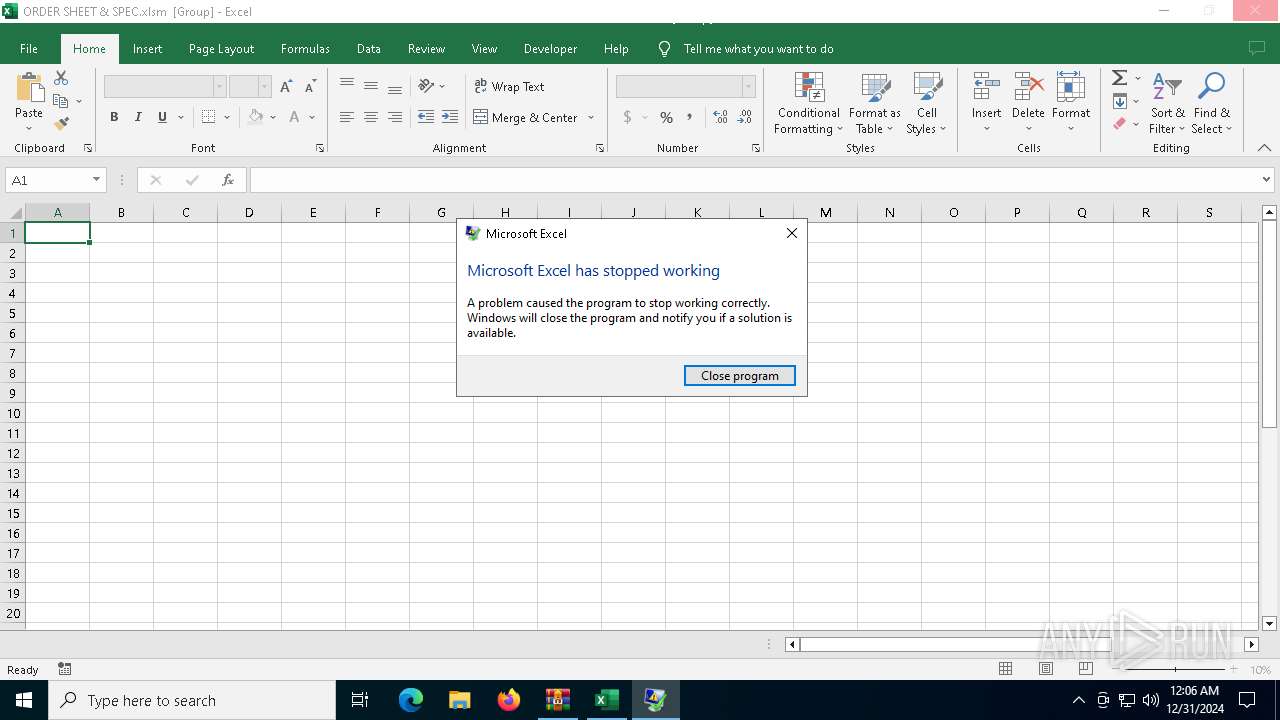
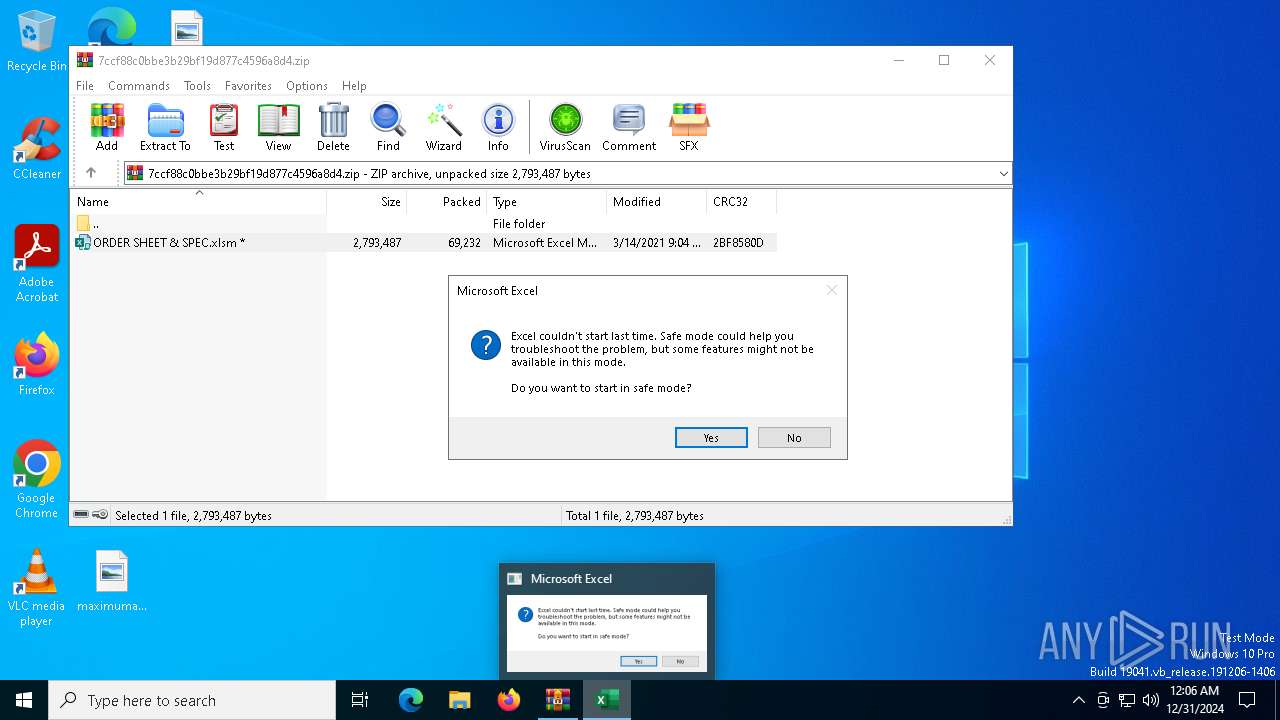
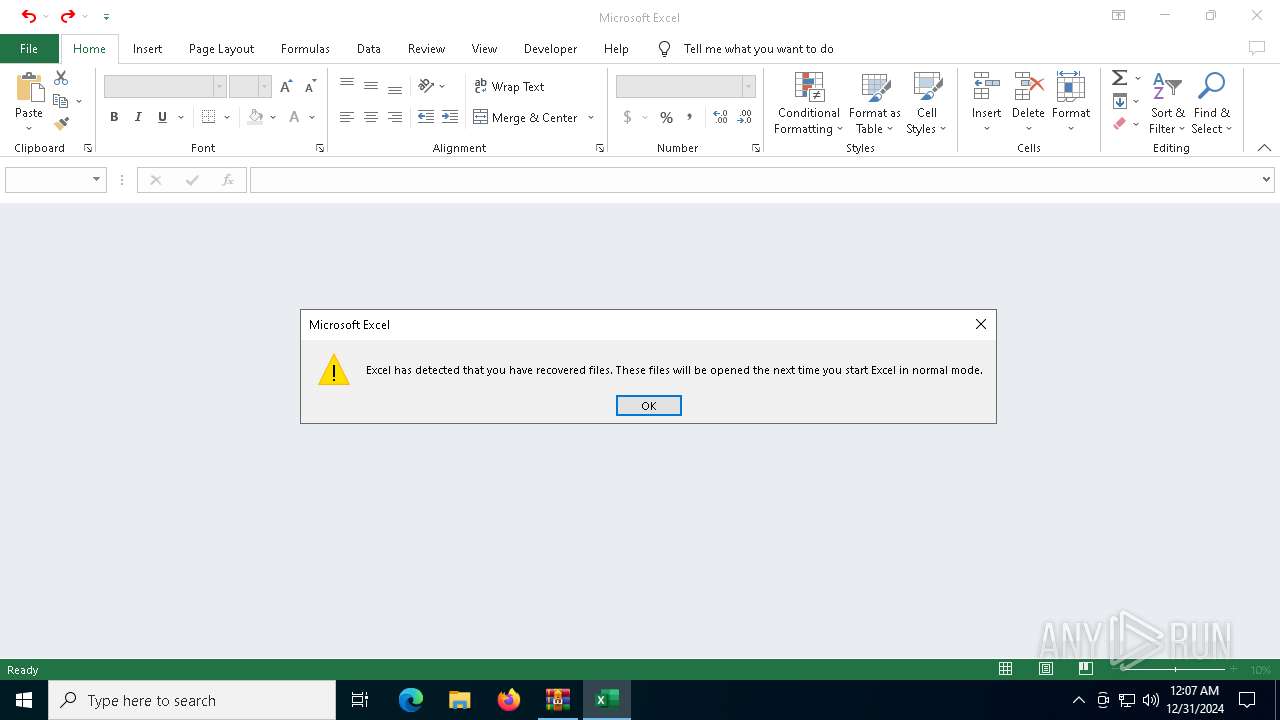
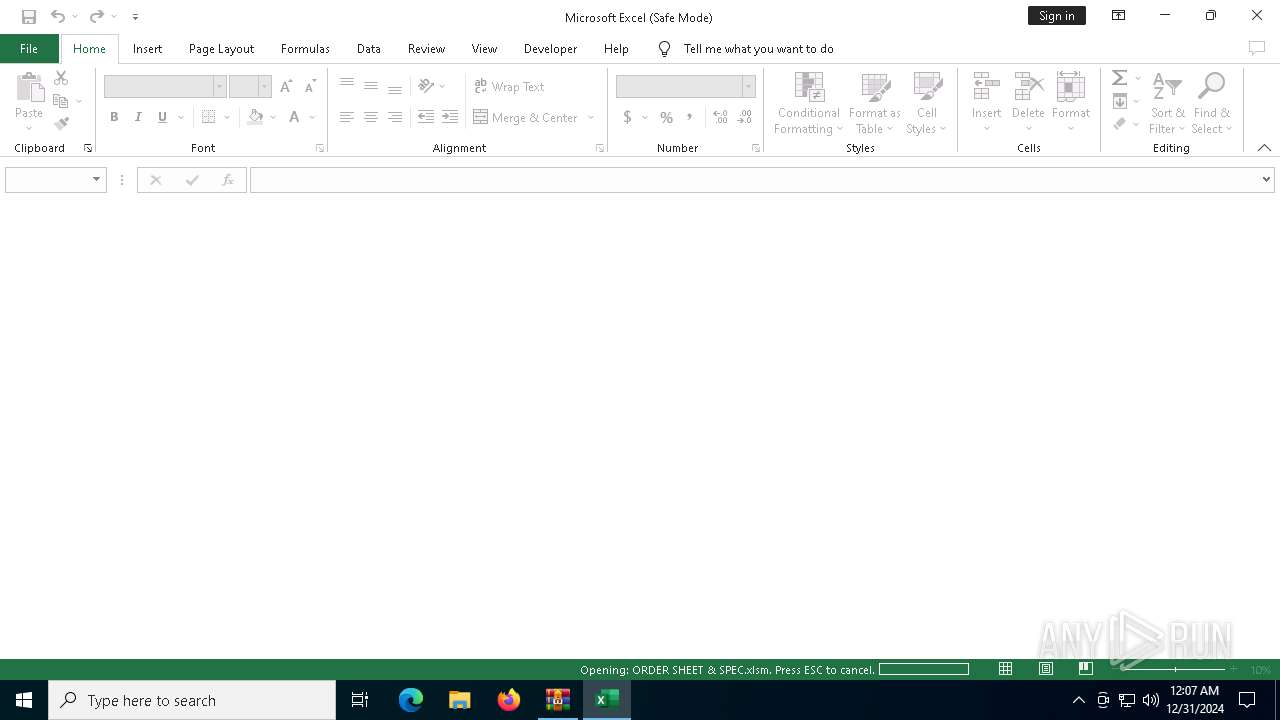
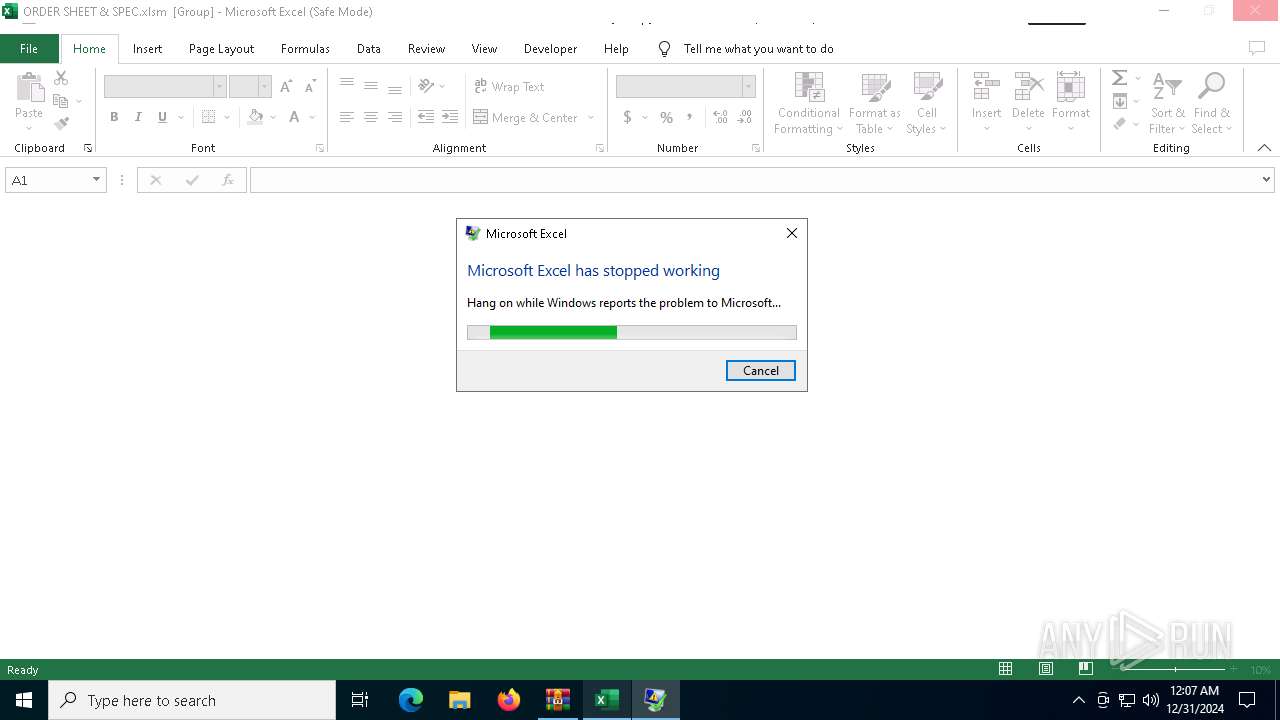
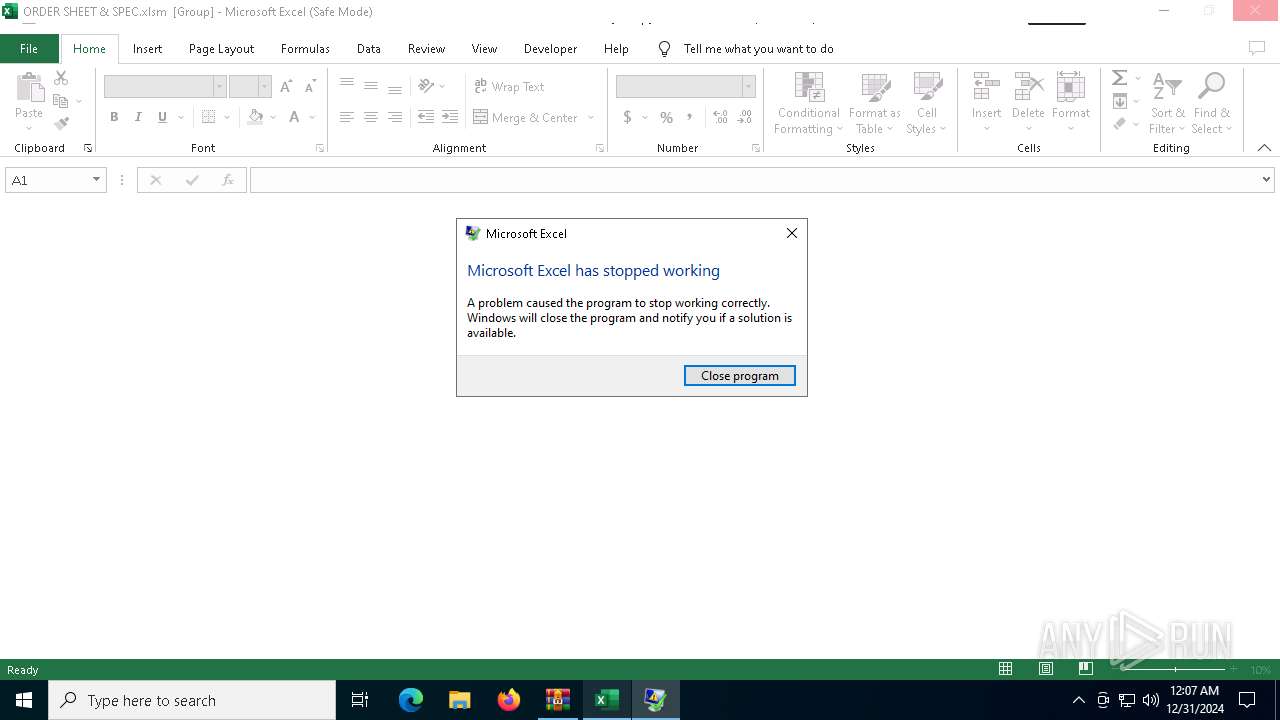
MALICIOUS
Phishing document has been detected
- WinRAR.exe (PID: 4392)
- EXCEL.EXE (PID: 6916)
- EXCEL.EXE (PID: 6416)
Unusual execution from MS Office
- EXCEL.EXE (PID: 6916)
- EXCEL.EXE (PID: 6416)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 4392)
Detected use of alternative data streams (AltDS)
- EXCEL.EXE (PID: 6916)
- EXCEL.EXE (PID: 6416)
INFO
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 4392)
- DWWIN.EXE (PID: 6236)
- DWWIN.EXE (PID: 3836)
Creates files in the program directory
- EXCEL.EXE (PID: 6916)
- DWWIN.EXE (PID: 6236)
- DWWIN.EXE (PID: 3836)
The process uses the downloaded file
- EXCEL.EXE (PID: 6916)
- WinRAR.exe (PID: 4392)
- EXCEL.EXE (PID: 6416)
Checks proxy server information
- DWWIN.EXE (PID: 6236)
- DWWIN.EXE (PID: 3836)
Reads the software policy settings
- DWWIN.EXE (PID: 6236)
- DWWIN.EXE (PID: 3836)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2021:03:14 21:04:16 |
| ZipCRC: | 0x2bf8580d |
| ZipCompressedSize: | 69232 |
| ZipUncompressedSize: | 2793487 |
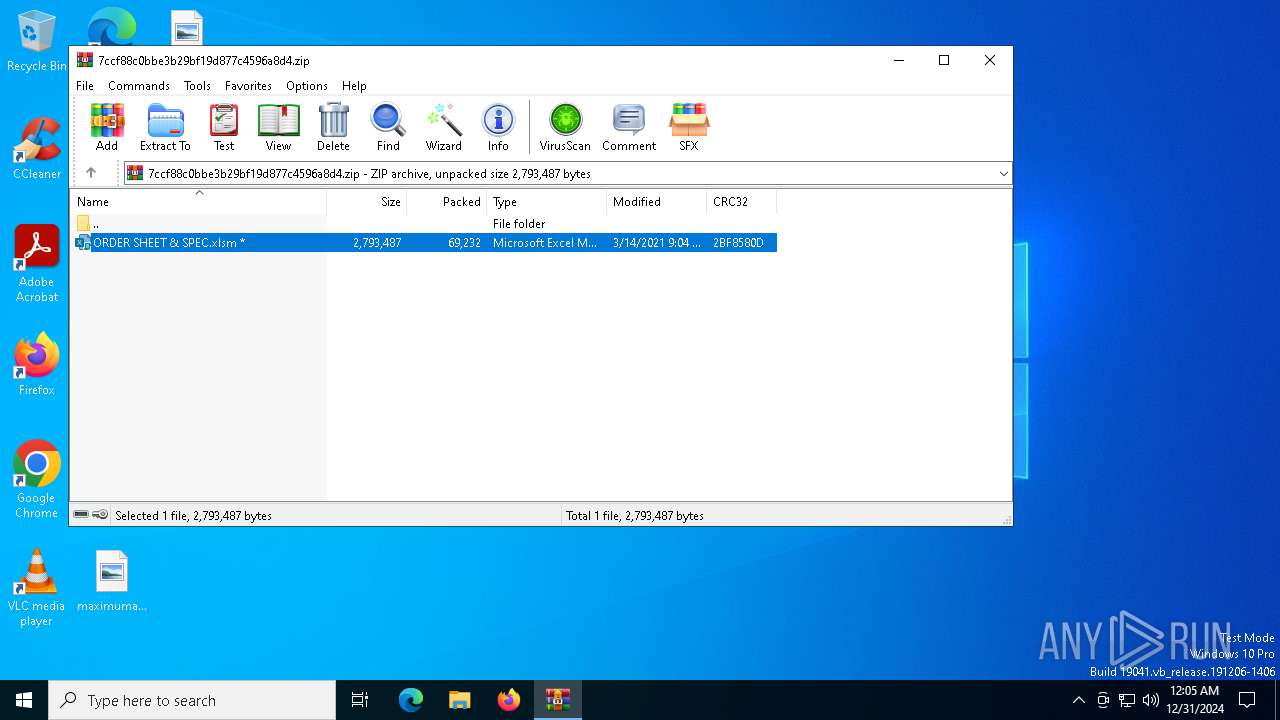
| ZipFileName: | ORDER SHEET & SPEC.xlsm |
Total processes
140
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3836 | C:\WINDOWS\system32\dwwin.exe -x -s 5044 | C:\Windows\System32\DWWIN.EXE | EXCEL.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Error Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
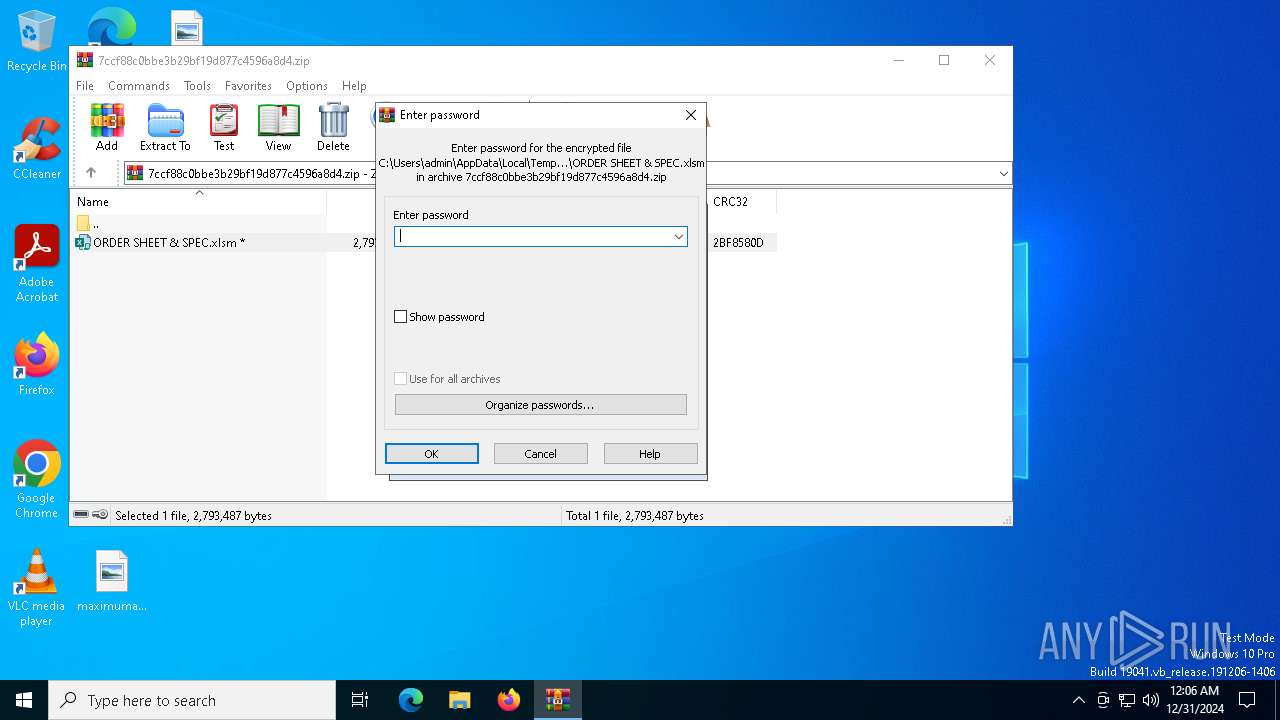
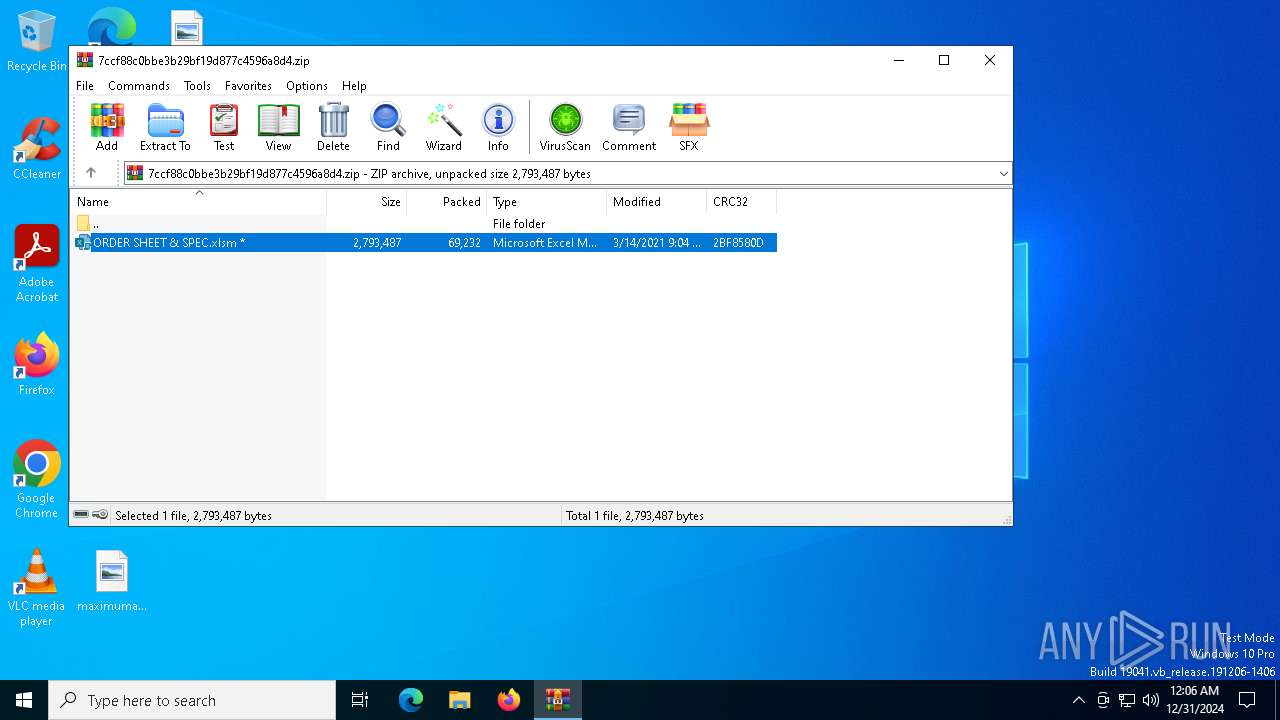
| 4392 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\7ccf88c0bbe3b29bf19d877c4596a8d4.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6236 | C:\WINDOWS\system32\dwwin.exe -x -s 4724 | C:\Windows\System32\DWWIN.EXE | EXCEL.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Error Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6416 | "C:\Program Files\Microsoft Office\Root\Office16\EXCEL.EXE" "C:\Users\admin\AppData\Local\Temp\Rar$DIb4392.41150\ORDER SHEET & SPEC.xlsm" | C:\Program Files\Microsoft Office\root\Office16\EXCEL.EXE | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 4 Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 6916 | "C:\Program Files\Microsoft Office\Root\Office16\EXCEL.EXE" "C:\Users\admin\AppData\Local\Temp\Rar$DIb4392.33685\ORDER SHEET & SPEC.xlsm" | C:\Program Files\Microsoft Office\root\Office16\EXCEL.EXE | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 4 Version: 16.0.16026.20146 Modules
| |||||||||||||||
Total events
17 381
Read events
16 930
Write events
422
Delete events
29
Modification events
| (PID) Process: | (4392) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4392) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4392) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4392) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\7ccf88c0bbe3b29bf19d877c4596a8d4.zip | |||
| (PID) Process: | (4392) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4392) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4392) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4392) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
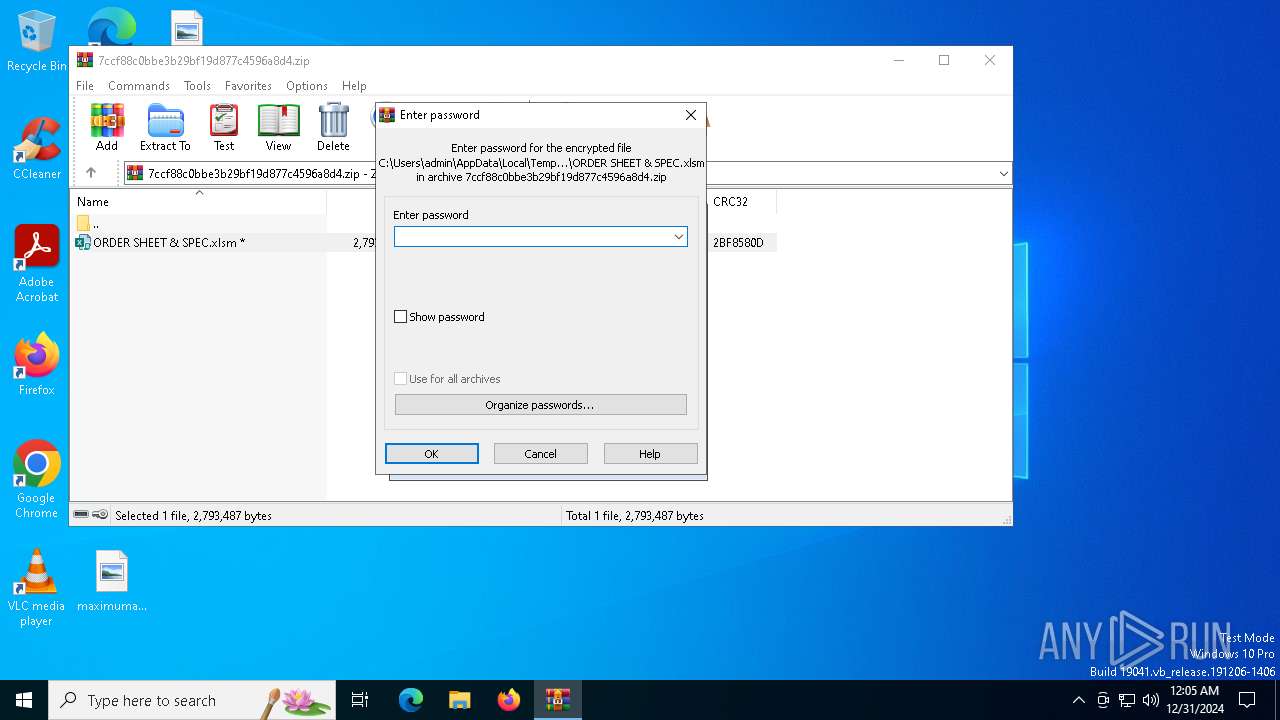
| (PID) Process: | (4392) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (4392) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.xlsm\OpenWithProgids |
| Operation: | write | Name: | Excel.SheetMacroEnabled.12 |
Value: | |||
Executable files
0
Suspicious files
29
Text files
9
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6236 | DWWIN.EXE | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_EXCEL.EXE_9888f89a1bac96f533a345418c59838875502c_00000000_4691efa6-ba44-479a-b22b-aafdcb6fefa2\Report.wer | — | |
MD5:— | SHA256:— | |||
| 6916 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.MSO\msoD9C9.tmp | — | |
MD5:— | SHA256:— | |||
| 6916 | EXCEL.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_CBDCCBFE4F7A916411C1E69BDD97BB04 | binary | |
MD5:6B2A4A7DD01445580F626F11F834A77D | SHA256:FEB0C589A3FD7EFDCC6F93E6871AA244615542820D0D47C41323B7E375B6E162 | |||
| 6916 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\56a61aeb75d8f5be186c26607f4bb213abe7c5ec.tbres | binary | |
MD5:D2CC9E3124E865BD72A98B7F0B44024F | SHA256:7CE761F4AFE9836C574BCCCF3569887D8E2CA634CFECFB51A145E36B2DC41220 | |||
| 6916 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.MSO\A80291EF.emf | emf | |
MD5:1DA917FE3A7E876F3F711FE30E1F46DB | SHA256:4D4D1E7B04C99DCB8E885915068AD6F74CC2333E91580CDAE5CCAA00C427247F | |||
| 6916 | EXCEL.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_CBDCCBFE4F7A916411C1E69BDD97BB04 | binary | |
MD5:E8BA069C45C25E190F968CFE7A31FF28 | SHA256:7818AA1C62F8BF378A0F6A624E48E06663B596C3AB0072BA1AB224A47E86E639 | |||
| 6236 | DWWIN.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\21253908F3CB05D51B1C2DA8B681A785 | der | |
MD5:F6F53CD09A41E968C363419B279D3112 | SHA256:6D2BB01CC7A9BADE2113B219CAC1BDA86B2733196B7E1BD0C807CE1E396B1892 | |||
| 6236 | DWWIN.EXE | C:\ProgramData\Microsoft\Windows\WER\Temp\WER3FB8.tmp.xml | xml | |
MD5:C79D1FCA96166C45B561B57F8532ACC5 | SHA256:E56698E88D648454AB8228BA5D3F9C9977E16FB0E7F3E7C066628CBA7A254577 | |||
| 6916 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.MSO\641C26.emf | emf | |
MD5:B59DD20DE3FDC50CD6B3C4BAF9C12DE8 | SHA256:979DDE2AED02F077C16AE53546C6DF9EED40E8386D6DB6FC36AEE9F966D2CB82 | |||
| 6236 | DWWIN.EXE | C:\ProgramData\Microsoft\Windows\WER\Temp\WER3F98.tmp.WERInternalMetadata.xml | binary | |
MD5:B0777B45FB8456242D0340E71E36ECF8 | SHA256:E98A3E8DD9B59A564B078D2EE25FCFAF562DDDAB986F0D2B9CD951BED6104622 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
47
DNS requests
35
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1596 | svchost.exe | GET | 200 | 2.20.245.138:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1596 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7004 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7004 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6916 | EXCEL.EXE | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
6236 | DWWIN.EXE | GET | 200 | 2.20.245.137:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6528 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6236 | DWWIN.EXE | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1596 | svchost.exe | 2.20.245.138:80 | crl.microsoft.com | Akamai International B.V. | SE | unknown |
1596 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1448 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1596 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5064 | SearchApp.exe | 104.126.37.162:443 | www.bing.com | Akamai International B.V. | DE | unknown |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |