| File name: | SManager.exe |
| Full analysis: | https://app.any.run/tasks/e656ddb0-5d76-42ef-9070-642c60f6c484 |
| Verdict: | Malicious activity |
| Analysis date: | November 19, 2024, 17:06:07 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 8 sections |
| MD5: | E3E044B227852E36DA9E97894A73C6B3 |
| SHA1: | 3AF4783C386A852882D51C9F3D57298DEBD668CB |
| SHA256: | A52C8C0EBA5E0C5B0CF1AC34E3D6D49EFE537ABE96EC34C99E257ADBBE1B0B21 |
| SSDEEP: | 98304:+jAyadLvu5RQM00gs/8DN0Xd8ymRMuakZl8DH+fxB14qZr8jY7WJqXhoXyd3trBP:FgWHL3dbEjGCtCykm5iMnFl+b |
MALICIOUS
No malicious indicators.SUSPICIOUS
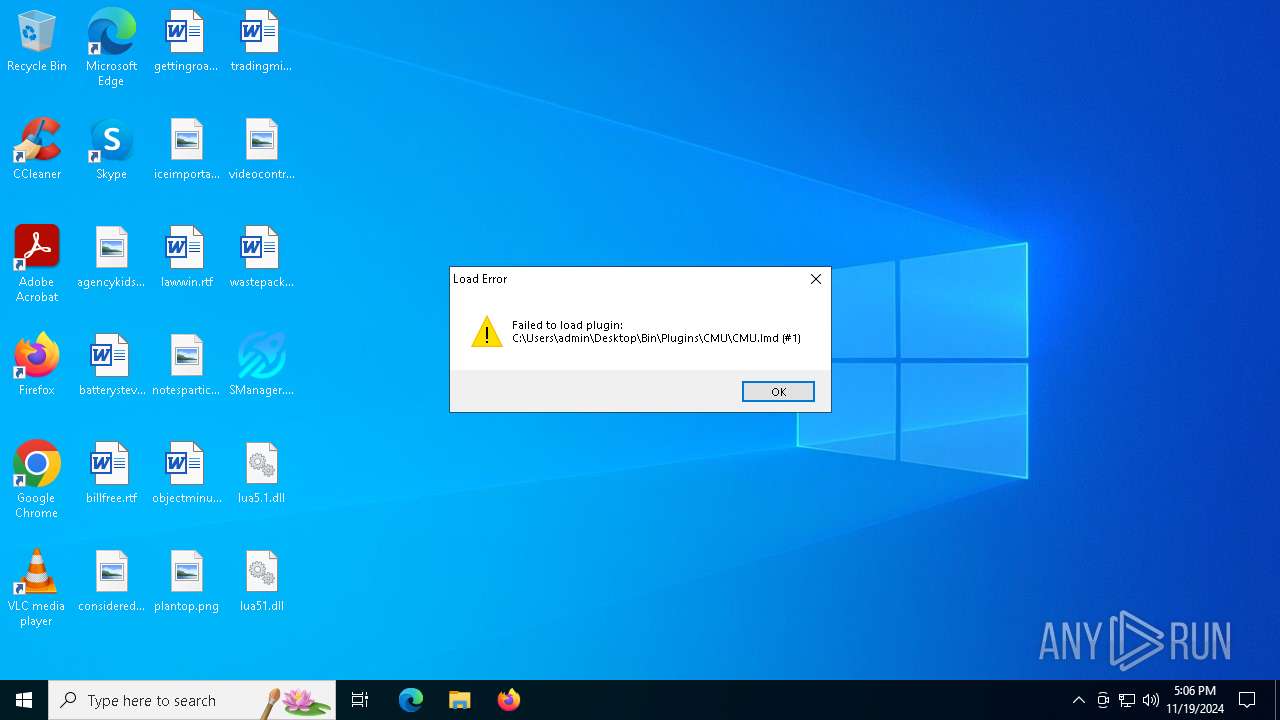
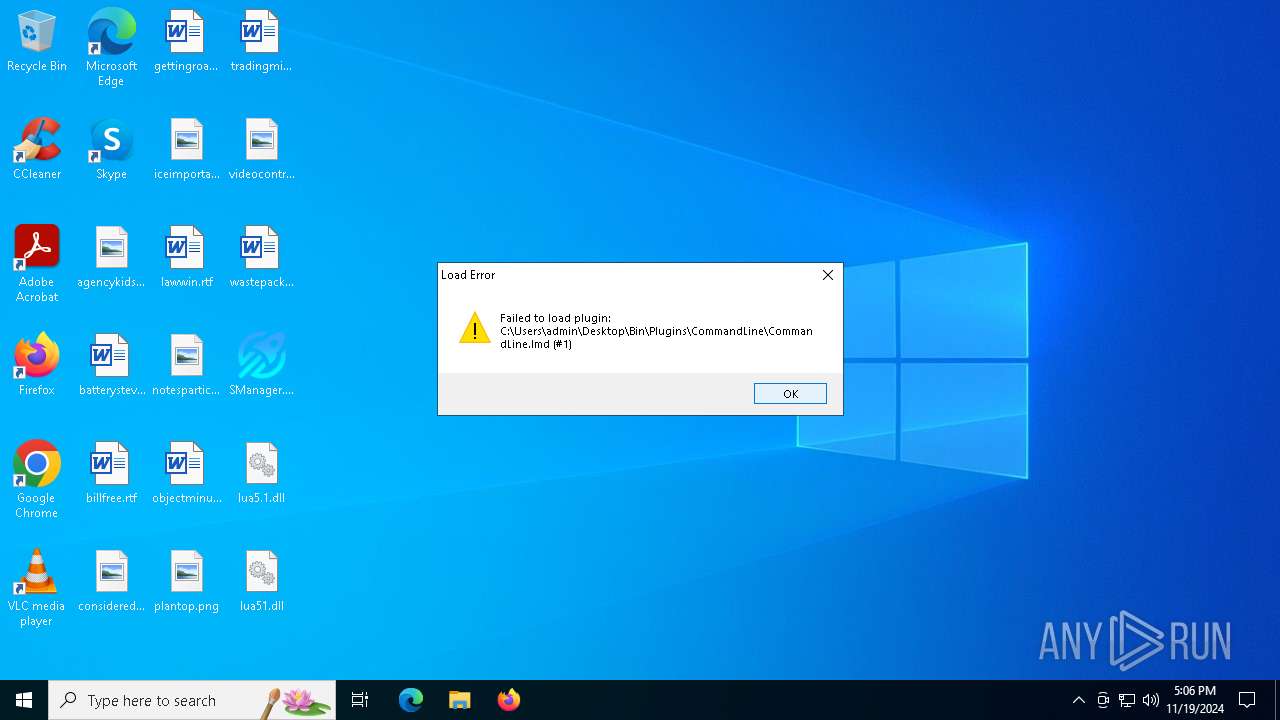
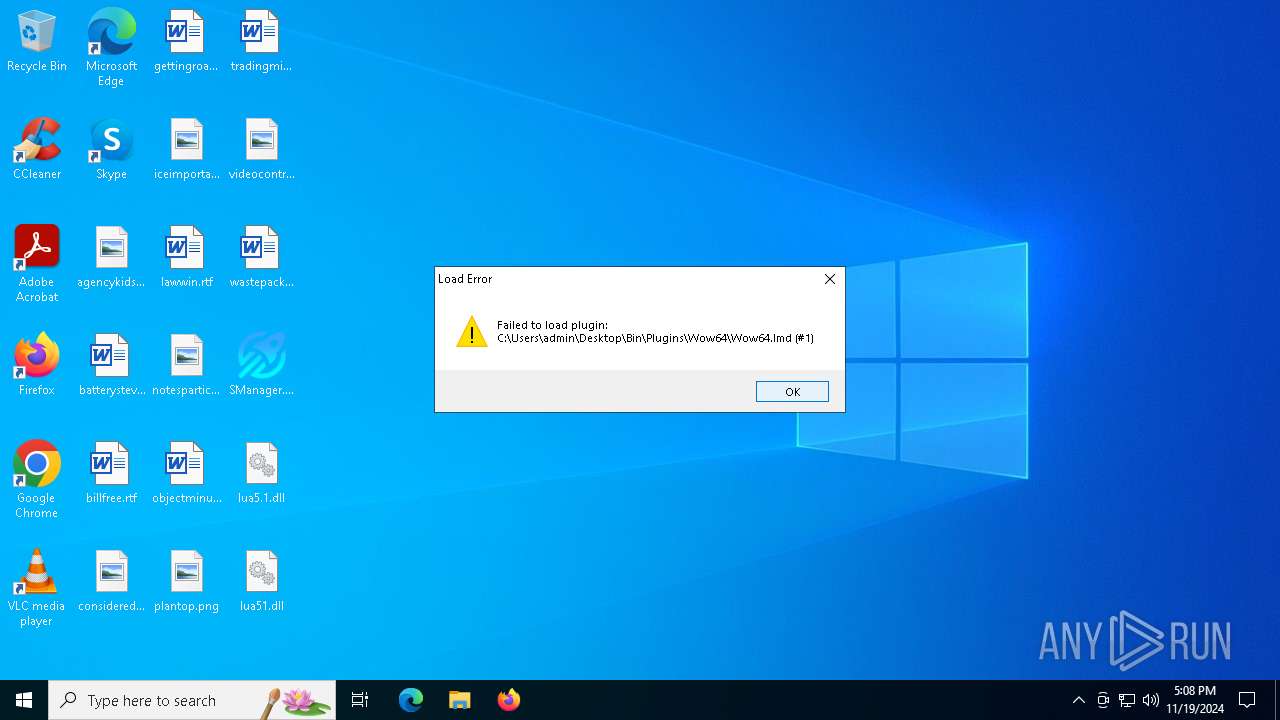
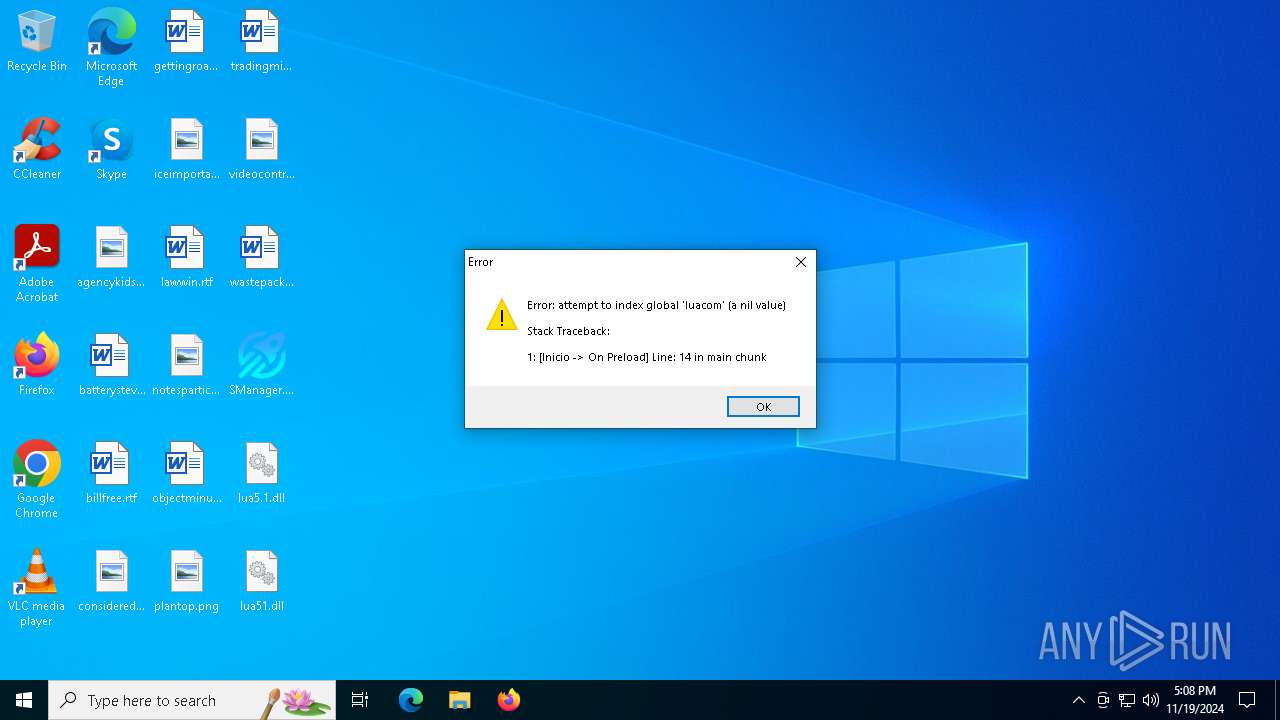
Executable content was dropped or overwritten
- SManager.exe (PID: 304)
Reads the BIOS version
- SManager.exe (PID: 304)
INFO
Checks supported languages
- SManager.exe (PID: 304)
Creates files in the program directory
- SManager.exe (PID: 304)
Reads the computer name
- SManager.exe (PID: 304)
Themida protector has been detected
- SManager.exe (PID: 304)
The process uses Lua
- SManager.exe (PID: 304)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:02:10 21:03:05+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 4030976 |
| InitializedDataSize: | 2319872 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xfa1058 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.2.0.0 |
| ProductVersionNumber: | 1.2.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
| Comments: | Created with AutoPlay Media Studio (www.indigorose.com) |
| CompanyName: | Doofy's Projects |
| FileDescription: | Herramienta que te aydua en la administracion de tu ordenador |
| FileVersion: | 1.2.0.0 |
| InternalName: | ams_runtime |
| LegalCopyright: | Copyright © 2024 Daniel Rodriguez |
| OriginalFileName: | SManager.exe |
| ProductName: | System Manager |
| ProductVersion: | 1.2.0.0 |
Total processes
116
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "C:\Users\admin\Desktop\SManager.exe" | C:\Users\admin\Desktop\SManager.exe | explorer.exe | ||||||||||||
User: admin Company: Doofy's Projects Integrity Level: MEDIUM Description: Herramienta que te aydua en la administracion de tu ordenador Version: 1.2.0.0 Modules
| |||||||||||||||
Total events
296
Read events
296
Write events
0
Delete events
0
Modification events
Executable files
2
Suspicious files
4
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 304 | SManager.exe | C:\Users\admin\Desktop\lua51.dll | executable | |
MD5:7FA818F532EFFD80CF7C1C54676E5A0D | SHA256:1C2D1BA8425139D45DE89192D2AE4982E9581F8AE0F22B8497AA0055080237CA | |||
| 304 | SManager.exe | C:\Users\admin\AppData\Local\Temp\_ir_tmpfnt_1\Segoe UI Semibold_1.TFT | odttf | |
MD5:7020A5C06453AB2574F9C46A2E43BADD | SHA256:60CD474595D07BBDFA9D87DE1A1E24C876E218D117C4A3098E0AC937157A1B9D | |||
| 304 | SManager.exe | C:\Users\admin\AppData\Local\Temp\_ir_tmpfnt_1\.TFT | binary | |
MD5:5438DCAD3AA57A3C56EB61E2F1955EFC | SHA256:090B89742910172C69E1FD3B1814AD4E482A1C712B87D24E96B377BEAAC3A6D1 | |||
| 304 | SManager.exe | C:\ProgramData\mntemp | binary | |
MD5:FBB17B3984C10F94042906AA326CE9FA | SHA256:4F9B5376A96BE818E85B38C2B226F40B1723C9CEB1AD1D33B376512BA3C2EA07 | |||
| 304 | SManager.exe | C:\Users\admin\Desktop\lua5.1.dll | executable | |
MD5:C3256800DCE47C14ACC83CCCA4C3E2AC | SHA256:F26F4F66022ACC96D0319C09814EBEDA60F4AB96B63B6262045DC786DC7C5866 | |||
| 304 | SManager.exe | C:\Users\admin\AppData\Local\Temp\_ir_tmpfnt_1\Segoe UI_1.TFT | ttf | |
MD5:2E28C110F34FD143428DB0FBEEA7306D | SHA256:74F2B3D0C20CF7380EB121A09FD7CDFDC1CCDD12A00DB83CAEC0FEB48B4DB9F7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
21
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4932 | svchost.exe | GET | 200 | 2.16.164.112:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 1.01 Kb | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.112:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 1.01 Kb | whitelisted |
3992 | RUXIMICS.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
4932 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
3992 | RUXIMICS.exe | GET | 200 | 2.16.164.112:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 1.01 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4932 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.23.209.135:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3992 | RUXIMICS.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4932 | svchost.exe | 2.16.164.112:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.164.112:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
3992 | RUXIMICS.exe | 2.16.164.112:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4932 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |