| File name: | a5238e60cbe814a8021050ddeb4c9569eea12cf8379d689e0cd84bb83a9b8266.exe |
| Full analysis: | https://app.any.run/tasks/a407736c-26e3-4b4b-b459-767045d5598d |
| Verdict: | Malicious activity |
| Analysis date: | July 13, 2024, 15:36:51 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | AEFAEBE48F578958C832F359D62406C1 |
| SHA1: | DA6313C09DDBC2BB7EC5E0ACC8A0C9D49D5D0051 |
| SHA256: | A5238E60CBE814A8021050DDEB4C9569EEA12CF8379D689E0CD84BB83A9B8266 |
| SSDEEP: | 393216:13+j4AZh6SYujeDsw3wBgZBVfR4TGcqMULE7Xo8In5w4pFtki614ywHrIlP:13+j7ZhRYujsbPVnc5UL+Inq43ykjcR |
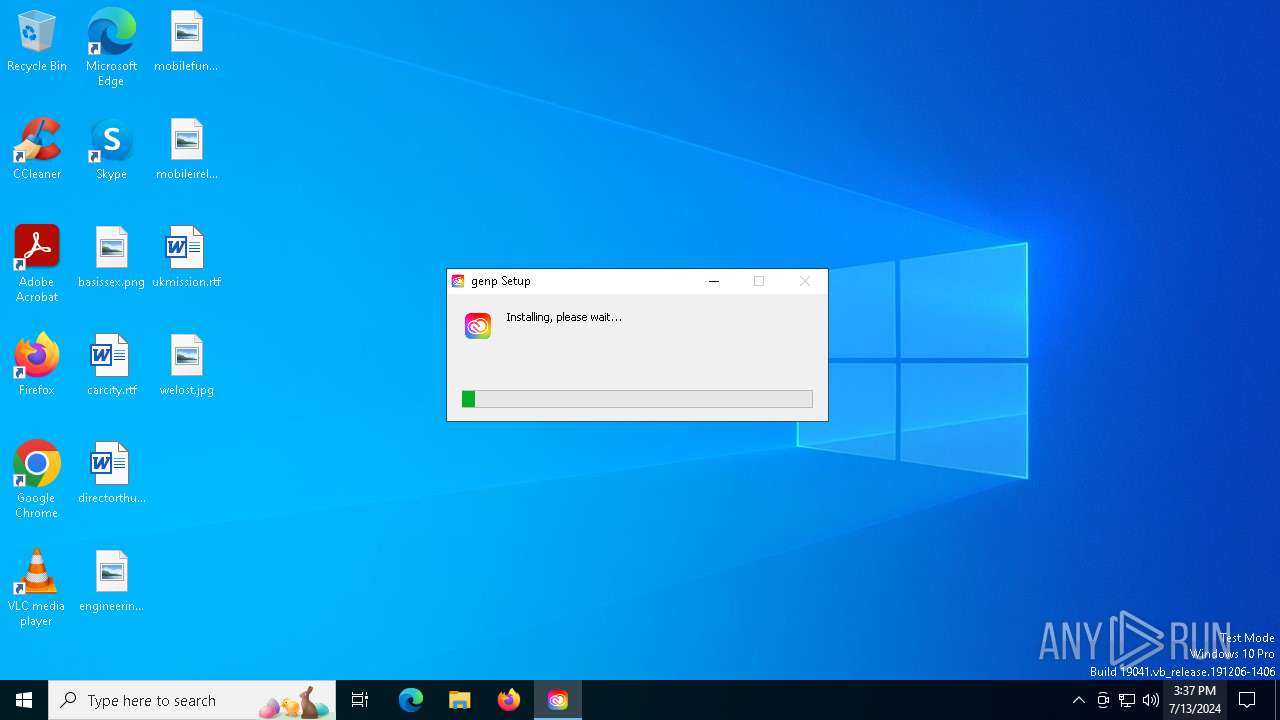
MALICIOUS
Drops the executable file immediately after the start
- a5238e60cbe814a8021050ddeb4c9569eea12cf8379d689e0cd84bb83a9b8266.exe (PID: 2128)
- genp.exe (PID: 3808)
Actions looks like stealing of personal data
- cmd.exe (PID: 3152)
SUSPICIOUS
Application launched itself
- genp.exe (PID: 3808)
Malware-specific behavior (creating "System.dll" in Temp)
- a5238e60cbe814a8021050ddeb4c9569eea12cf8379d689e0cd84bb83a9b8266.exe (PID: 2128)
Executable content was dropped or overwritten
- a5238e60cbe814a8021050ddeb4c9569eea12cf8379d689e0cd84bb83a9b8266.exe (PID: 2128)
- genp.exe (PID: 3808)
The process creates files with name similar to system file names
- a5238e60cbe814a8021050ddeb4c9569eea12cf8379d689e0cd84bb83a9b8266.exe (PID: 2128)
Reads security settings of Internet Explorer
- a5238e60cbe814a8021050ddeb4c9569eea12cf8379d689e0cd84bb83a9b8266.exe (PID: 2128)
Starts CMD.EXE for commands execution
- genp.exe (PID: 3808)
The process drops C-runtime libraries
- genp.exe (PID: 3808)
Process drops python dynamic module
- genp.exe (PID: 3808)
Process drops legitimate windows executable
- genp.exe (PID: 3808)
- a5238e60cbe814a8021050ddeb4c9569eea12cf8379d689e0cd84bb83a9b8266.exe (PID: 2128)
Drops 7-zip archiver for unpacking
- a5238e60cbe814a8021050ddeb4c9569eea12cf8379d689e0cd84bb83a9b8266.exe (PID: 2128)
Creates a software uninstall entry
- a5238e60cbe814a8021050ddeb4c9569eea12cf8379d689e0cd84bb83a9b8266.exe (PID: 2128)
INFO
Reads the computer name
- a5238e60cbe814a8021050ddeb4c9569eea12cf8379d689e0cd84bb83a9b8266.exe (PID: 2128)
- genp.exe (PID: 2992)
- genp.exe (PID: 6216)
- genp.exe (PID: 3808)
Reads Environment values
- genp.exe (PID: 3808)
Reads product name
- genp.exe (PID: 3808)
Checks supported languages
- genp.exe (PID: 2992)
- a5238e60cbe814a8021050ddeb4c9569eea12cf8379d689e0cd84bb83a9b8266.exe (PID: 2128)
- genp.exe (PID: 6216)
- genp.exe (PID: 3808)
Creates files or folders in the user directory
- a5238e60cbe814a8021050ddeb4c9569eea12cf8379d689e0cd84bb83a9b8266.exe (PID: 2128)
- genp.exe (PID: 3808)
Create files in a temporary directory
- a5238e60cbe814a8021050ddeb4c9569eea12cf8379d689e0cd84bb83a9b8266.exe (PID: 2128)
- genp.exe (PID: 3808)
Checks proxy server information
- genp.exe (PID: 3808)
Process checks computer location settings
- genp.exe (PID: 3808)
Reads the software policy settings
- slui.exe (PID: 7152)
Manual execution by a user
- genp.exe (PID: 3808)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:01:30 03:58:52+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 473088 |
| UninitializedDataSize: | 16384 |
| EntryPoint: | 0x338f |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| FileDescription: | Adobe-GenP |
| FileVersion: | 1.0.0 |
| LegalCopyright: | Copyright © 2024 genp |
| ProductName: | genp |
| ProductVersion: | 1.0.0 |
Total processes
145
Monitored processes
10
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2128 | "C:\Users\admin\AppData\Local\Temp\a5238e60cbe814a8021050ddeb4c9569eea12cf8379d689e0cd84bb83a9b8266.exe" | C:\Users\admin\AppData\Local\Temp\a5238e60cbe814a8021050ddeb4c9569eea12cf8379d689e0cd84bb83a9b8266.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Adobe-GenP Exit code: 0 Version: 1.0.0 Modules
| |||||||||||||||
| 2556 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2992 | "C:\Users\admin\AppData\Local\Programs\genp\genp.exe" --type=gpu-process --field-trial-handle=1564,821718500632672469,12559025279710570603,131072 --enable-features=WebComponentsV0Enabled --disable-features=CookiesWithoutSameSiteMustBeSecure,SameSiteByDefaultCookies,SpareRendererForSitePerProcess --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1276 /prefetch:2 | C:\Users\admin\AppData\Local\Programs\genp\genp.exe | — | genp.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: LOW Description: genp Version: 1.0.0 Modules
| |||||||||||||||
| 3152 | C:\WINDOWS\system32\cmd.exe /d /s /c ""C:\Users\admin\AppData\Local\Discord\Update.exe" --processStart Discord.exe" | C:\Windows\System32\cmd.exe | genp.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3808 | "C:\Users\admin\AppData\Local\Programs\genp\genp.exe" | C:\Users\admin\AppData\Local\Programs\genp\genp.exe | explorer.exe | ||||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: genp Version: 1.0.0 Modules
| |||||||||||||||
| 6216 | "C:\Users\admin\AppData\Local\Programs\genp\genp.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1564,821718500632672469,12559025279710570603,131072 --enable-features=WebComponentsV0Enabled --disable-features=CookiesWithoutSameSiteMustBeSecure,SameSiteByDefaultCookies,SpareRendererForSitePerProcess --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=2172 /prefetch:8 | C:\Users\admin\AppData\Local\Programs\genp\genp.exe | — | genp.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: genp Version: 1.0.0 Modules
| |||||||||||||||
| 6292 | C:\Windows\System32\CompPkgSrv.exe -Embedding | C:\Windows\System32\CompPkgSrv.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Component Package Support Server Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6892 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7120 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7152 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 449
Read events
5 437
Write events
12
Delete events
0
Modification events
| (PID) Process: | (2128) a5238e60cbe814a8021050ddeb4c9569eea12cf8379d689e0cd84bb83a9b8266.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\7b478d44-4f6e-56a1-a650-4cd9601cd76e |
| Operation: | write | Name: | InstallLocation |
Value: C:\Users\admin\AppData\Local\Programs\genp | |||
| (PID) Process: | (2128) a5238e60cbe814a8021050ddeb4c9569eea12cf8379d689e0cd84bb83a9b8266.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\7b478d44-4f6e-56a1-a650-4cd9601cd76e |
| Operation: | write | Name: | KeepShortcuts |
Value: true | |||
| (PID) Process: | (2128) a5238e60cbe814a8021050ddeb4c9569eea12cf8379d689e0cd84bb83a9b8266.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\7b478d44-4f6e-56a1-a650-4cd9601cd76e |
| Operation: | write | Name: | ShortcutName |
Value: genp | |||
| (PID) Process: | (2128) a5238e60cbe814a8021050ddeb4c9569eea12cf8379d689e0cd84bb83a9b8266.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\7b478d44-4f6e-56a1-a650-4cd9601cd76e |
| Operation: | write | Name: | DisplayName |
Value: uninstaller | |||
| (PID) Process: | (2128) a5238e60cbe814a8021050ddeb4c9569eea12cf8379d689e0cd84bb83a9b8266.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\7b478d44-4f6e-56a1-a650-4cd9601cd76e |
| Operation: | write | Name: | UninstallString |
Value: "C:\Users\admin\AppData\Local\Programs\genp\Uninstall genp.exe" /currentuser | |||
| (PID) Process: | (2128) a5238e60cbe814a8021050ddeb4c9569eea12cf8379d689e0cd84bb83a9b8266.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\7b478d44-4f6e-56a1-a650-4cd9601cd76e |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\Users\admin\AppData\Local\Programs\genp\Uninstall genp.exe" /currentuser /S | |||
| (PID) Process: | (2128) a5238e60cbe814a8021050ddeb4c9569eea12cf8379d689e0cd84bb83a9b8266.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\7b478d44-4f6e-56a1-a650-4cd9601cd76e |
| Operation: | write | Name: | DisplayVersion |
Value: 1.0.0 | |||
| (PID) Process: | (2128) a5238e60cbe814a8021050ddeb4c9569eea12cf8379d689e0cd84bb83a9b8266.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\7b478d44-4f6e-56a1-a650-4cd9601cd76e |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Users\admin\AppData\Local\Programs\genp\uninstallerIcon.ico | |||
| (PID) Process: | (2128) a5238e60cbe814a8021050ddeb4c9569eea12cf8379d689e0cd84bb83a9b8266.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\7b478d44-4f6e-56a1-a650-4cd9601cd76e |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
| (PID) Process: | (2128) a5238e60cbe814a8021050ddeb4c9569eea12cf8379d689e0cd84bb83a9b8266.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\7b478d44-4f6e-56a1-a650-4cd9601cd76e |
| Operation: | write | Name: | NoRepair |
Value: 1 | |||
Executable files
137
Suspicious files
838
Text files
1 062
Unknown types
42
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2128 | a5238e60cbe814a8021050ddeb4c9569eea12cf8379d689e0cd84bb83a9b8266.exe | C:\Users\admin\AppData\Local\Temp\nsv1CA4.tmp\app-64.7z | — | |
MD5:— | SHA256:— | |||
| 2128 | a5238e60cbe814a8021050ddeb4c9569eea12cf8379d689e0cd84bb83a9b8266.exe | C:\Users\admin\AppData\Local\Programs\genp\icudtl.dat | — | |
MD5:— | SHA256:— | |||
| 2128 | a5238e60cbe814a8021050ddeb4c9569eea12cf8379d689e0cd84bb83a9b8266.exe | C:\Users\admin\AppData\Local\Programs\genp\LICENSES.chromium.html | — | |
MD5:— | SHA256:— | |||
| 2128 | a5238e60cbe814a8021050ddeb4c9569eea12cf8379d689e0cd84bb83a9b8266.exe | C:\Users\admin\AppData\Local\Programs\genp\locales\bg.pak | pgc | |
MD5:26A0431FF9F22716C55F68F7E164C595 | SHA256:1BB8C5CE9215D42BA9CEEC52F86FBFF46DF668CE48FF56BD1CBE96ADADF4922C | |||
| 2128 | a5238e60cbe814a8021050ddeb4c9569eea12cf8379d689e0cd84bb83a9b8266.exe | C:\Users\admin\AppData\Local\Programs\genp\locales\cs.pak | pgc | |
MD5:B7ED7DD838C0C0980D7C011A3CEF03B5 | SHA256:9651B8F3304C70D96DCCA76CFFFAD90CE8AFCAB6231FFD8E4E9BEADE3D510841 | |||
| 2128 | a5238e60cbe814a8021050ddeb4c9569eea12cf8379d689e0cd84bb83a9b8266.exe | C:\Users\admin\AppData\Local\Programs\genp\locales\bn.pak | pgc | |
MD5:5D7894BC1947927ACAC8491E1036D44E | SHA256:F7D704207CB3340F1ACE2F2E5AF031E816BB86E4BF3F665907D837D094BBA37A | |||
| 2128 | a5238e60cbe814a8021050ddeb4c9569eea12cf8379d689e0cd84bb83a9b8266.exe | C:\Users\admin\AppData\Local\Programs\genp\locales\de.pak | pgc | |
MD5:9B1F23B3E07D947C0227F640560BC0A6 | SHA256:E71F4320553F65CFD0356A4B30F3AEC2EEC7B4FD327866D528917B9909CFA761 | |||
| 2128 | a5238e60cbe814a8021050ddeb4c9569eea12cf8379d689e0cd84bb83a9b8266.exe | C:\Users\admin\AppData\Local\Programs\genp\locales\el.pak | pgc | |
MD5:5949036E7E364F5C97FEC60C80A4740C | SHA256:A3431D3AC720F871C33D7E522CF506B2FA8EA1872BAC02A4B4B427A6D063AF38 | |||
| 2128 | a5238e60cbe814a8021050ddeb4c9569eea12cf8379d689e0cd84bb83a9b8266.exe | C:\Users\admin\AppData\Local\Programs\genp\locales\en-GB.pak | mmw | |
MD5:32F8D0492B73CE67DF70C2F6B65A9DB6 | SHA256:C4FDFA9C6F30AD657BF12CCB95F70542A0FADE45D8490259A4507629F4B33299 | |||
| 2128 | a5238e60cbe814a8021050ddeb4c9569eea12cf8379d689e0cd84bb83a9b8266.exe | C:\Users\admin\AppData\Local\Programs\genp\locales\en-US.pak | mmw | |
MD5:BD8F7B719110342B7CEFB16DDD05EC55 | SHA256:D1D3F892BE16329C79F9A8EE8C5FA1C9FB46D17EDFEB56A3D9407F9D7587A0DE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
77
DNS requests
23
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2340 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2340 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4656 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2568 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6552 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3228 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6552 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5236 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
3040 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2088 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2340 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
2340 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
4656 | SearchApp.exe | 2.23.209.162:443 | www.bing.com | Akamai International B.V. | GB | unknown |
2088 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
rentry.co |
| unknown |
cosmoplwnets.xyz |
| unknown |
go.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3808 | genp.exe | Misc activity | ET INFO Observed Pastebin Service Domain (rentry .co in TLS SNI) |
2168 | svchost.exe | Misc activity | ET INFO Pastebin Service Domain in DNS Lookup (rentry .co) |