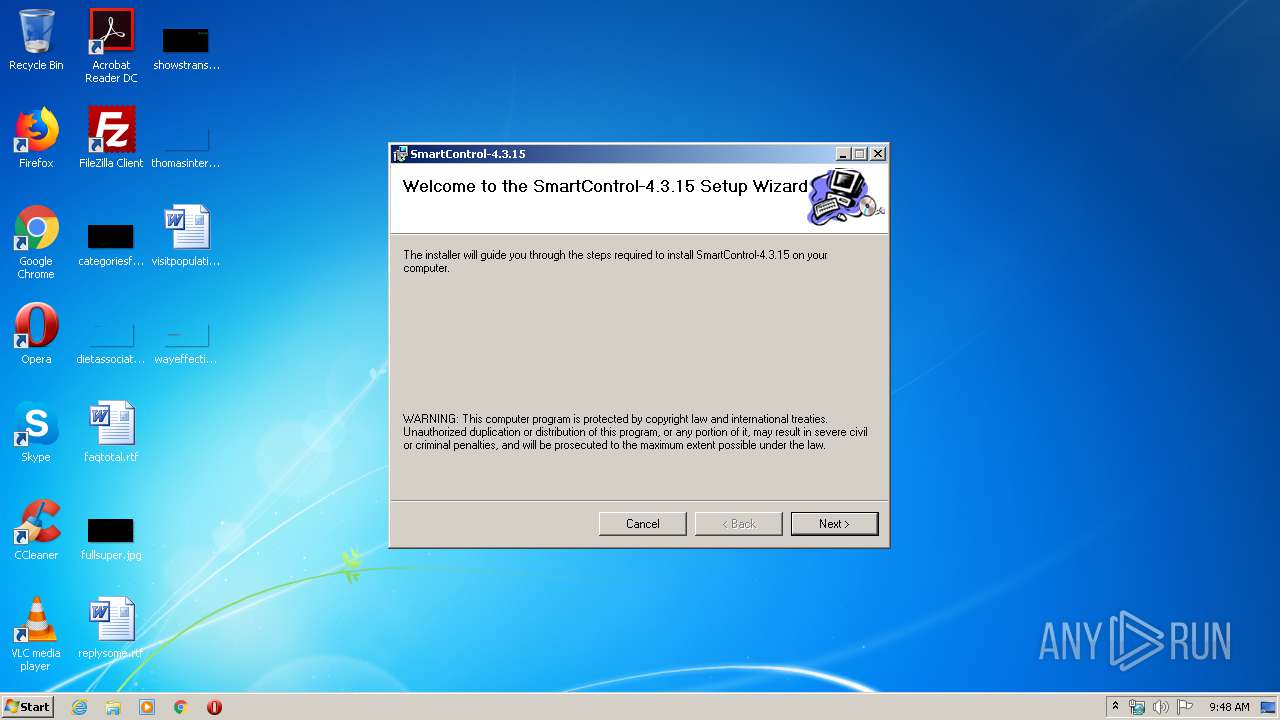
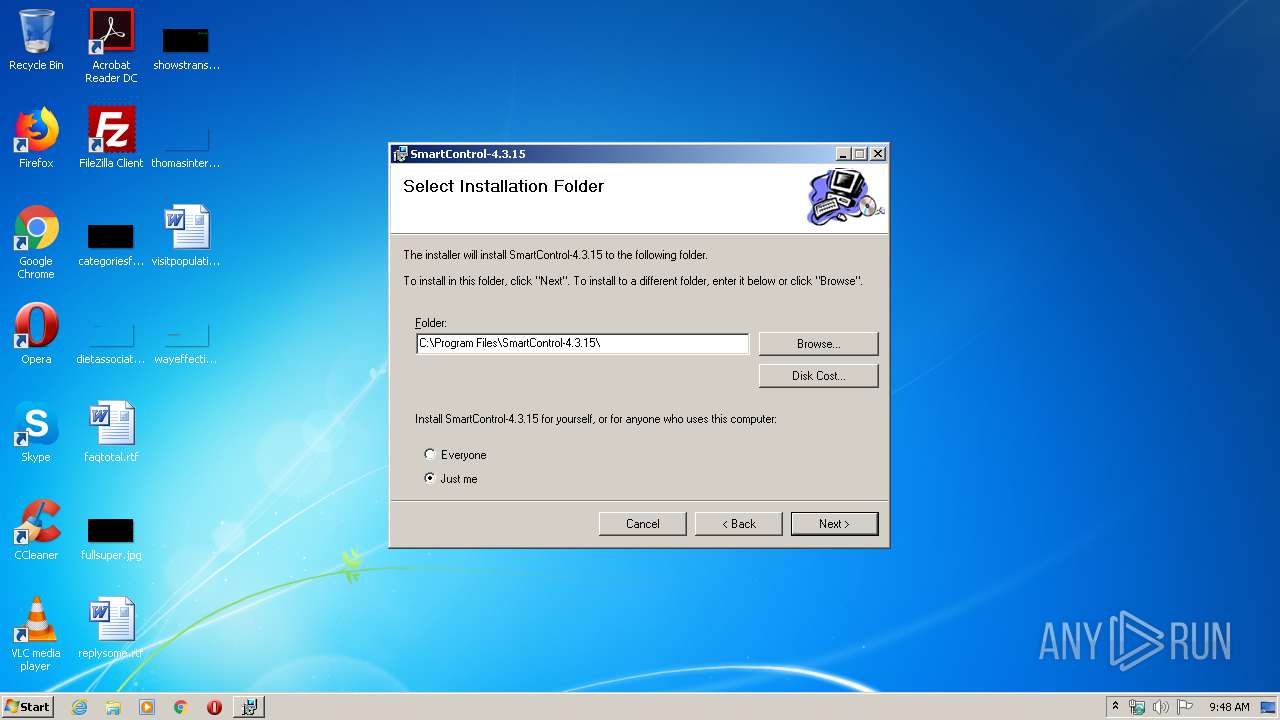
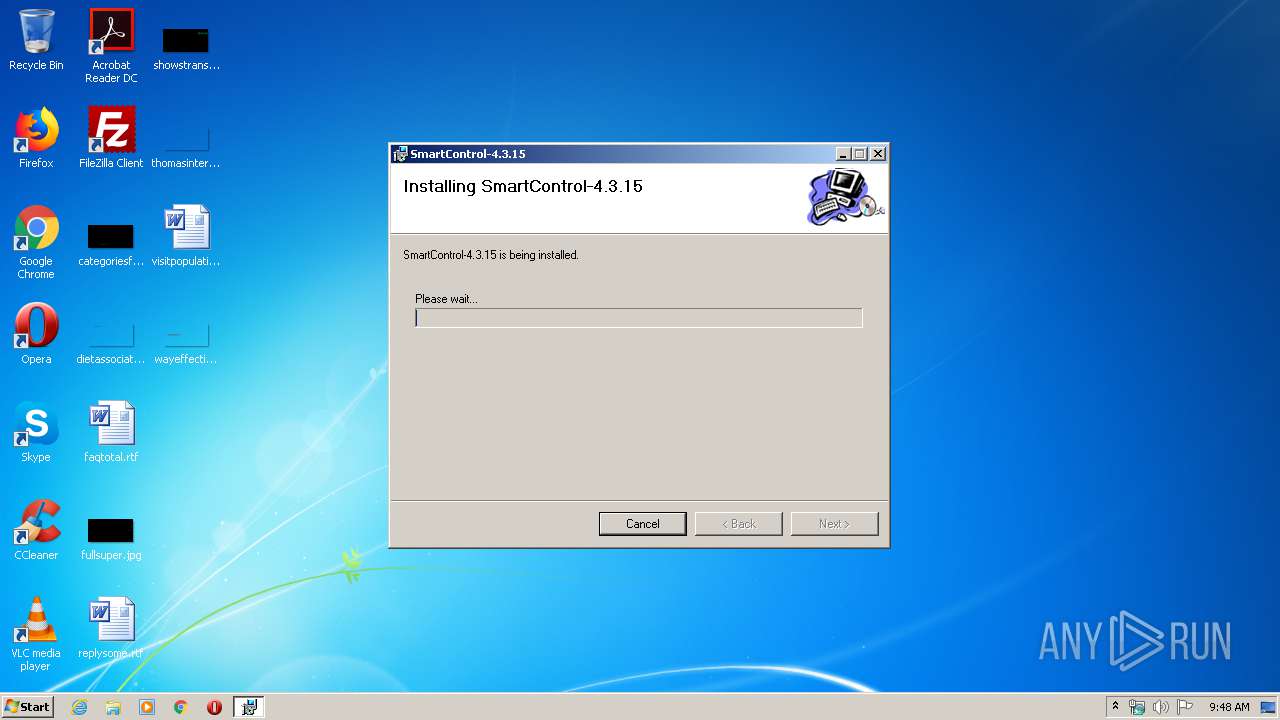
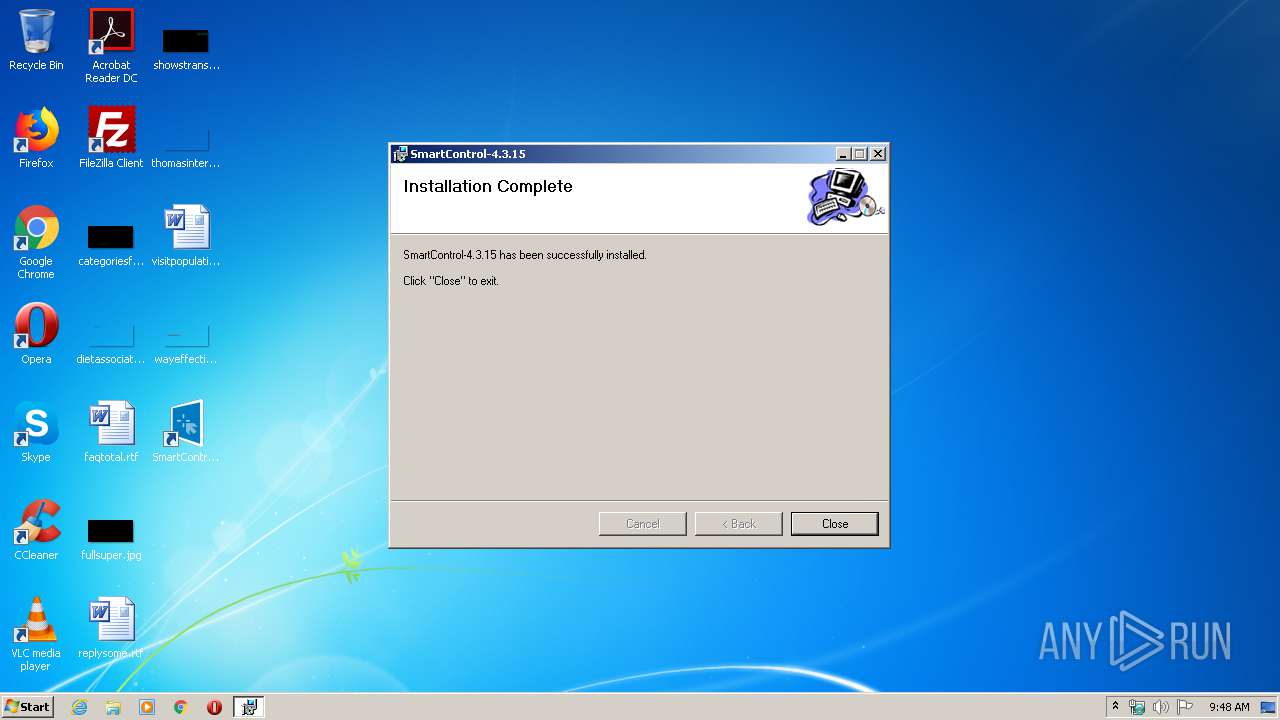
| File name: | SmartControl-4.3.15-Setup.msi |
| Full analysis: | https://app.any.run/tasks/784a7296-31cc-46b2-b0e8-b823e8772367 |
| Verdict: | Malicious activity |
| Analysis date: | January 28, 2020, 09:47:53 |
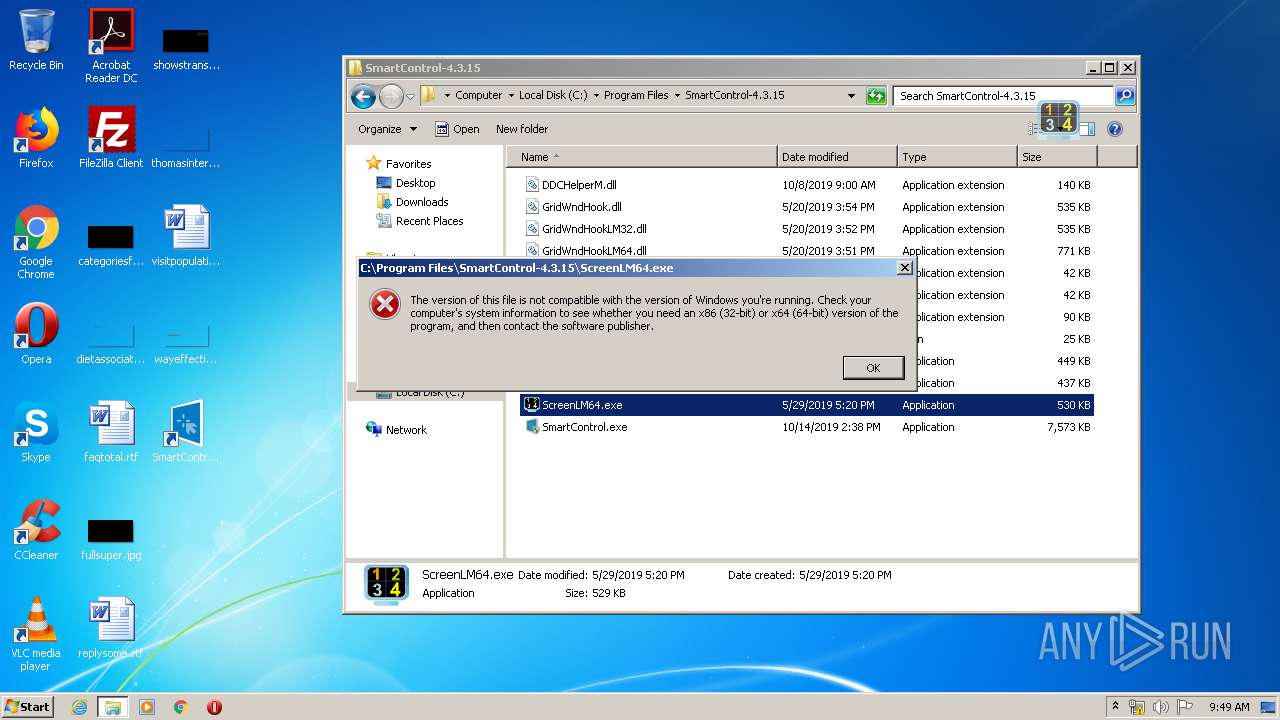
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, MSI Installer, Create Time/Date: Mon Jun 21 08:00:00 1999, Name of Creating Application: Windows Installer, Security: 1, Code page: 1252, Template: Intel;1033, Number of Pages: 200, Revision Number: {A687F3A8-3929-4330-94FD-62F0FD0E381D}, Title: SmartControl-4.3.15, Author: PHL, Comments: PHL, Number of Words: 2, Last Saved Time/Date: Mon Oct 14 06:48:07 2019, Last Printed: Mon Oct 14 06:48:07 2019 |
| MD5: | 3D475829B600E71131B2C77B3F73A9B3 |
| SHA1: | C714215C7C39CD969CBA387C115FA4281D2776AA |
| SHA256: | A51B4A910BDA29F827BF47DFD175936291AB65E619B058091BA4A6152F174AF7 |
| SSDEEP: | 98304:qU+TAkke16O/iLzLGye76ZzV+TM+hTXPn48Vsrg:qU+0Ro6O/uLGye7iuM+hTXfl |
MALICIOUS
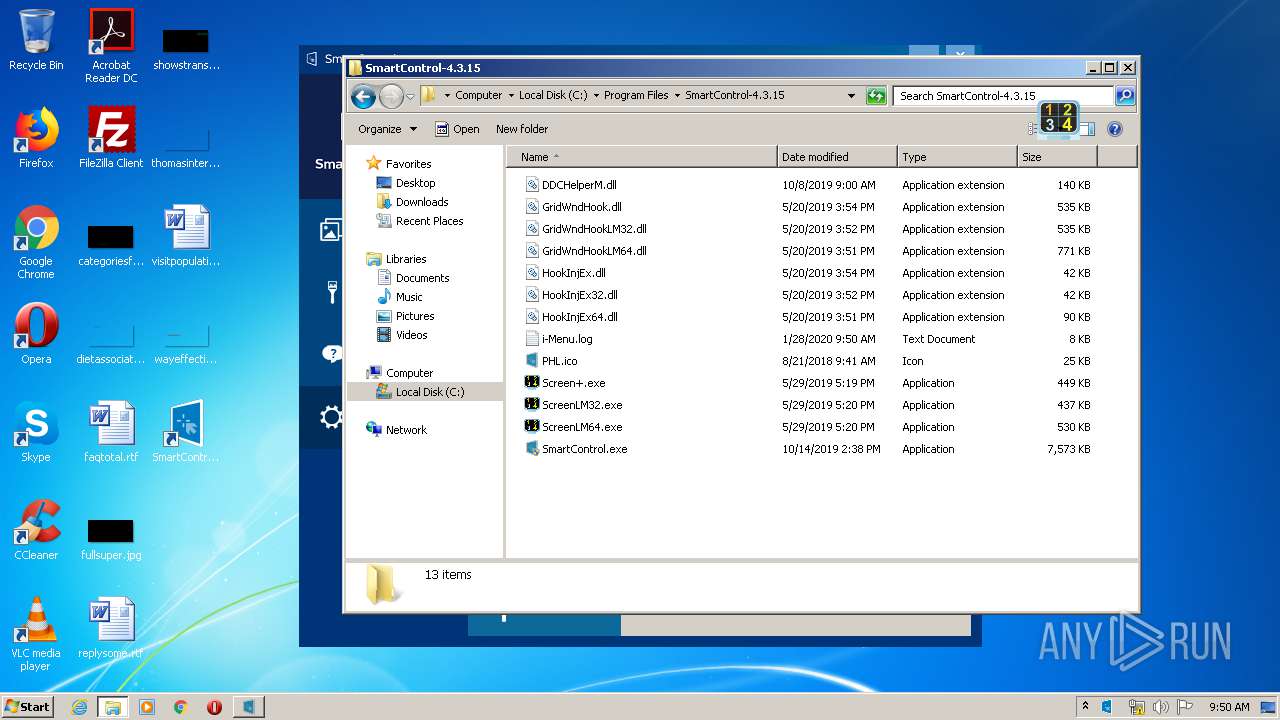
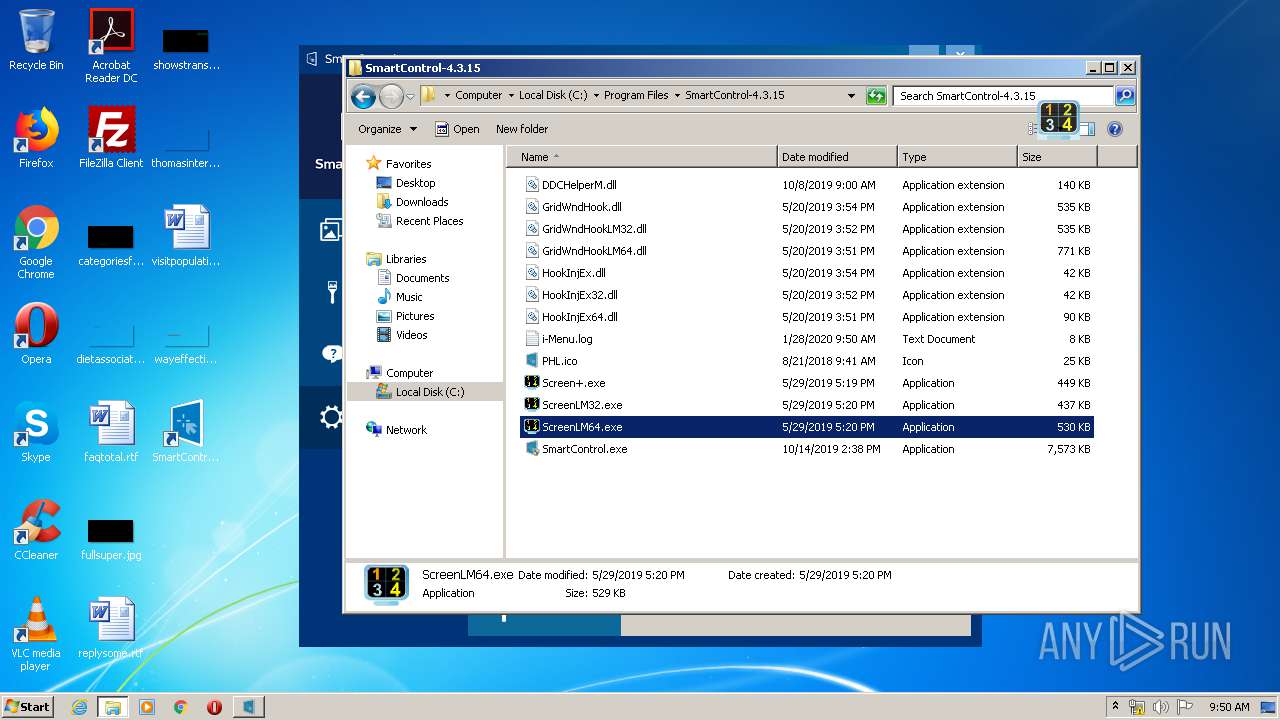
Loads dropped or rewritten executable
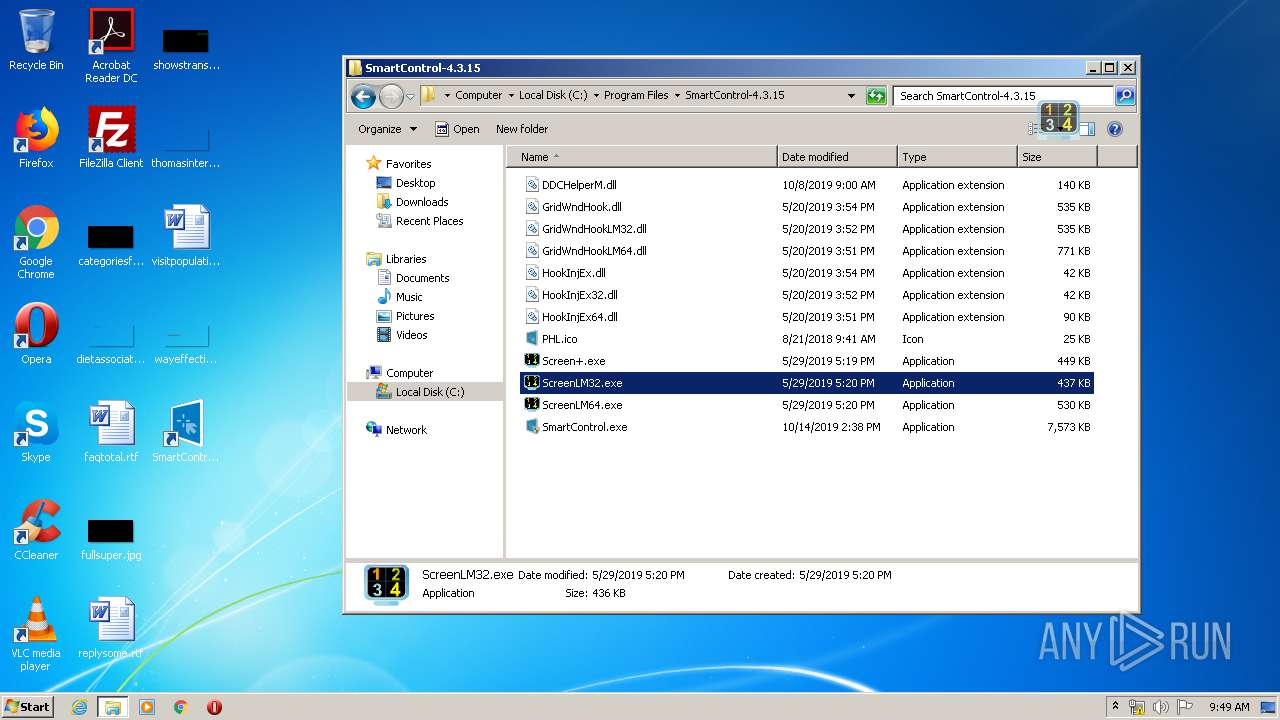
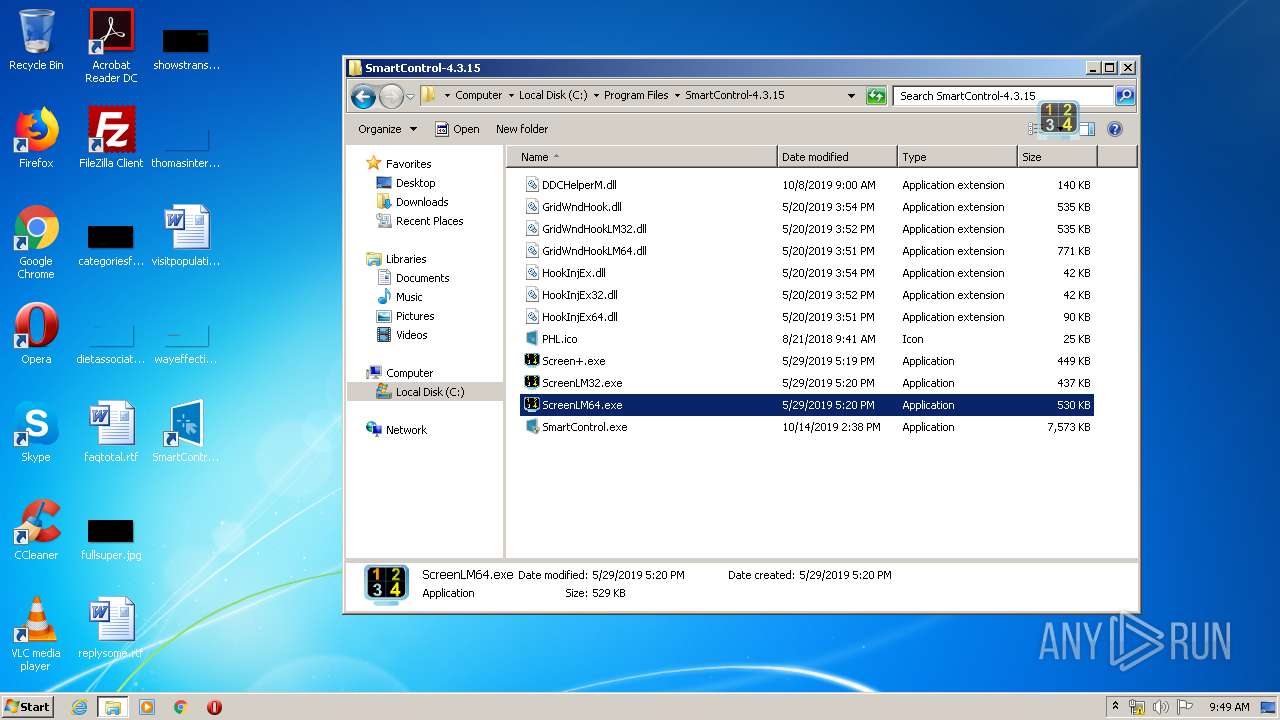
- ScreenLM32.exe (PID: 792)
- Screen+.exe (PID: 3292)
- explorer.exe (PID: 372)
- DllHost.exe (PID: 3664)
- SmartControl.exe (PID: 1136)
- DllHost.exe (PID: 3404)
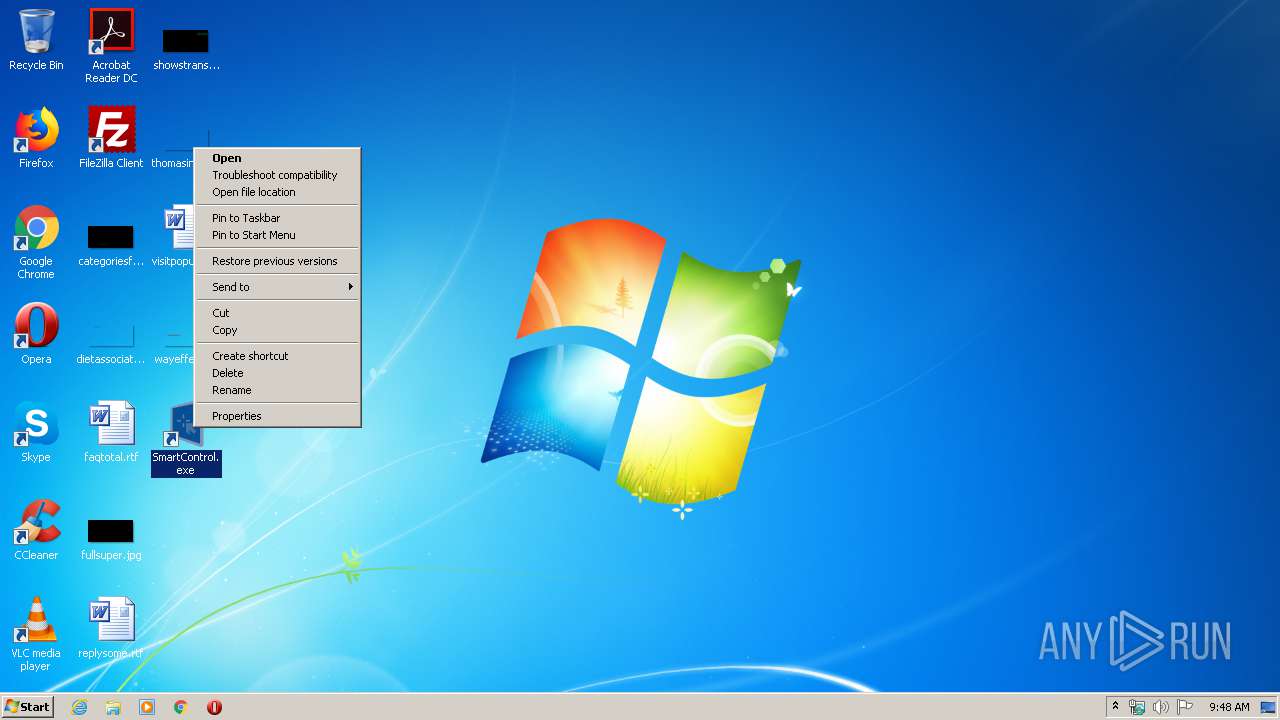
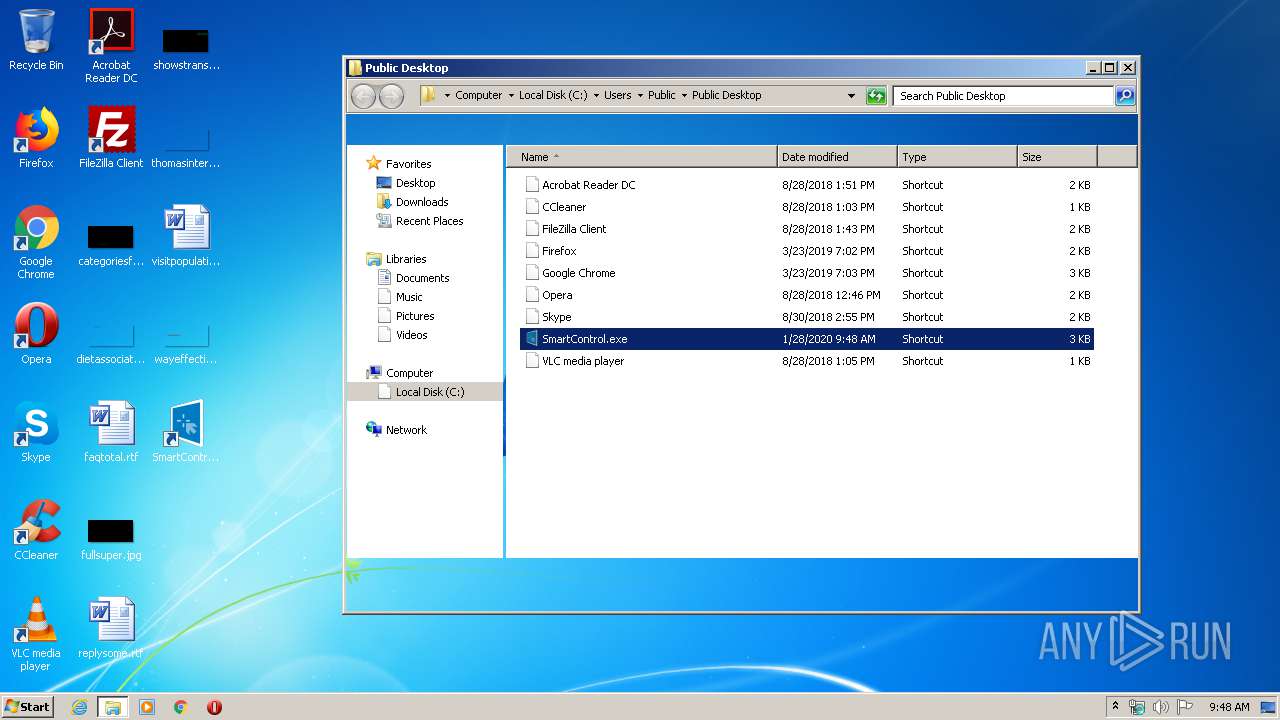
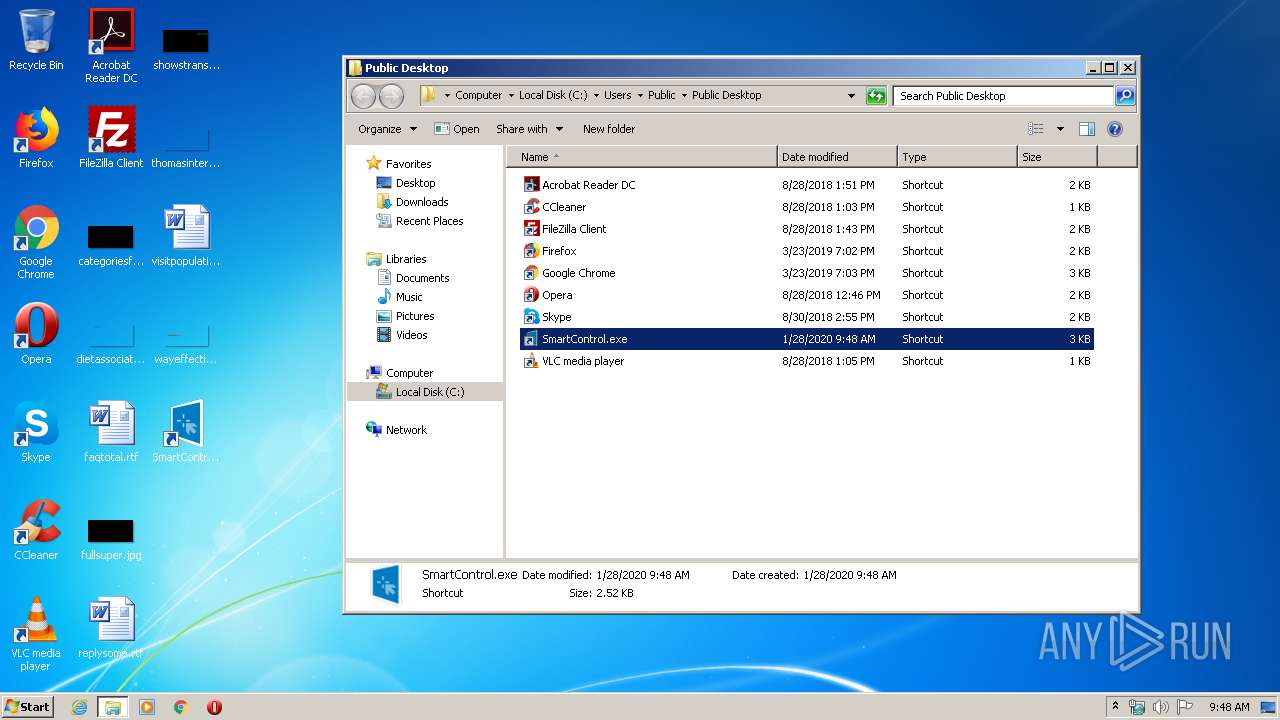
Application was dropped or rewritten from another process
- SmartControl.exe (PID: 1000)
- SmartControl.exe (PID: 1136)
- ScreenLM32.exe (PID: 792)
- Screen+.exe (PID: 3292)
SUSPICIOUS
Executed as Windows Service
- vssvc.exe (PID: 3352)
Starts Microsoft Installer
- explorer.exe (PID: 372)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3556)
- SmartControl.exe (PID: 1136)
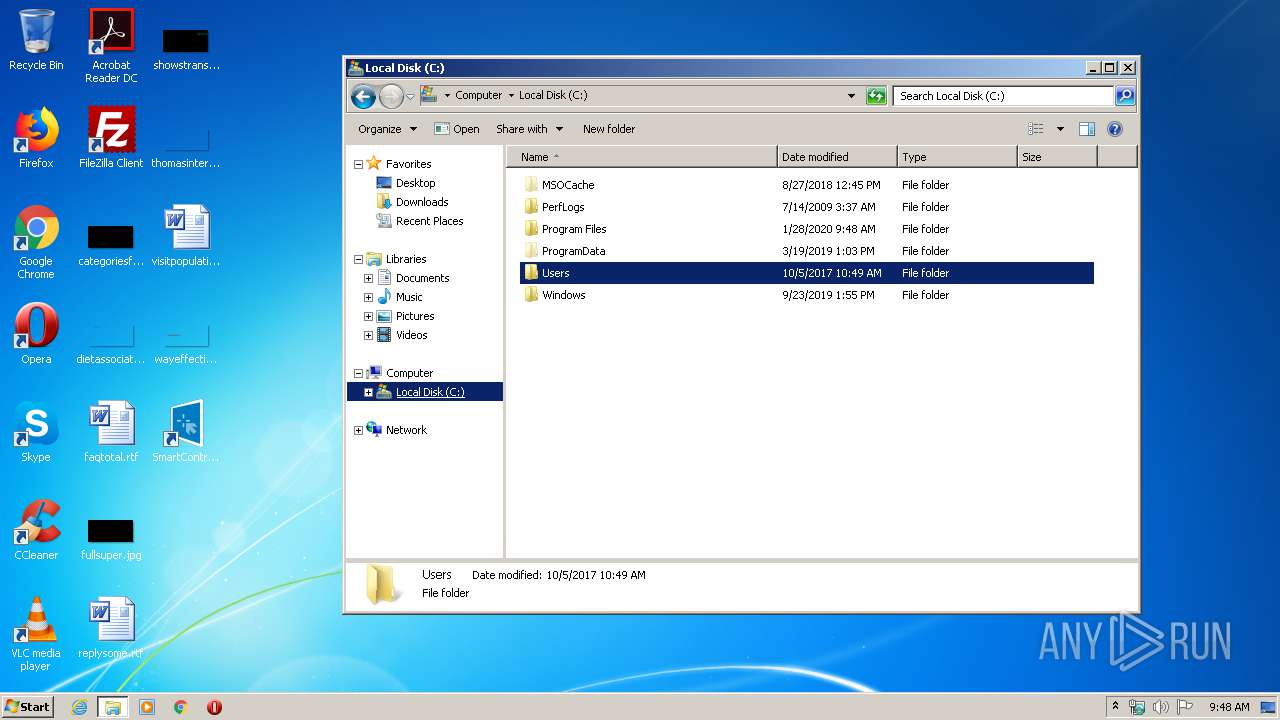
Creates files in the driver directory
- SmartControl.exe (PID: 1136)
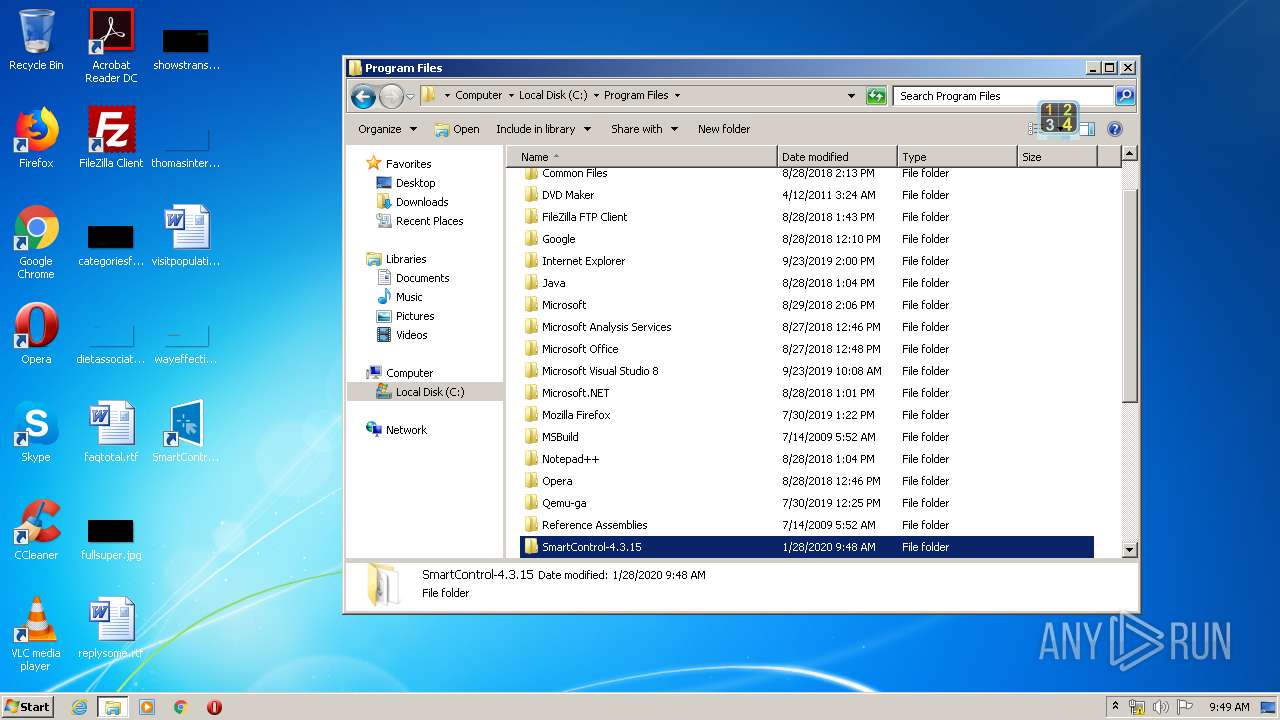
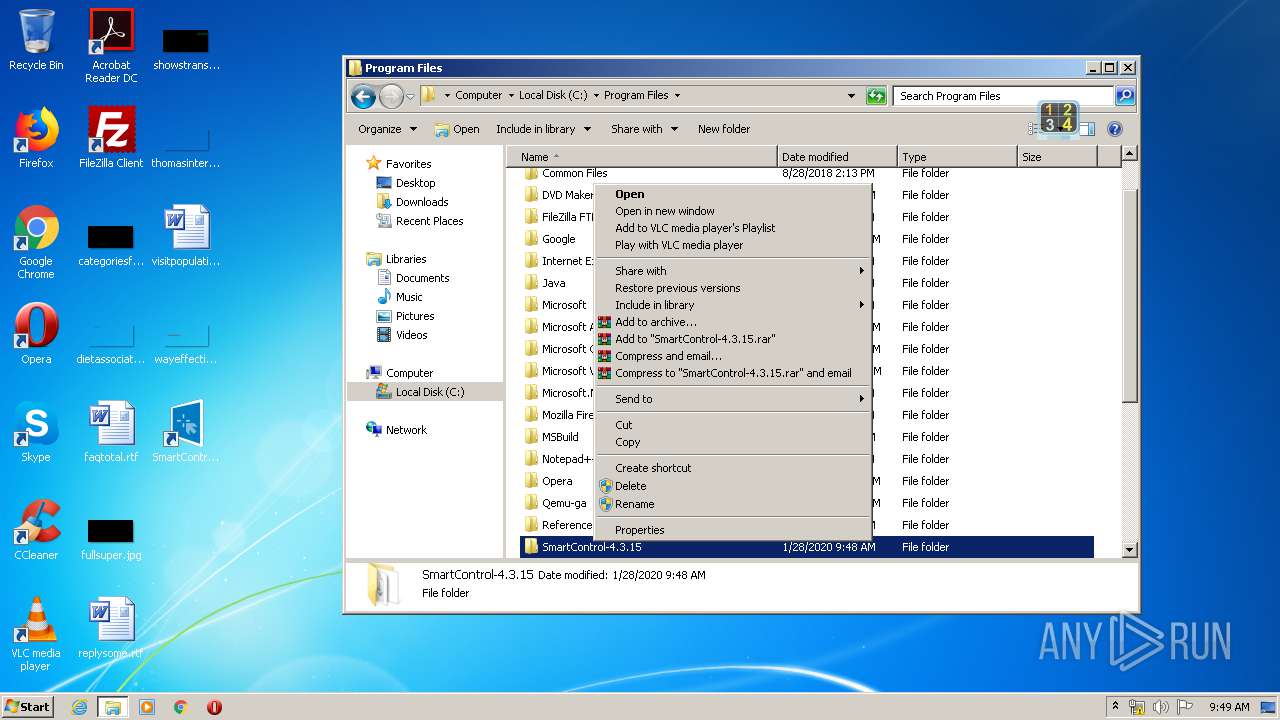
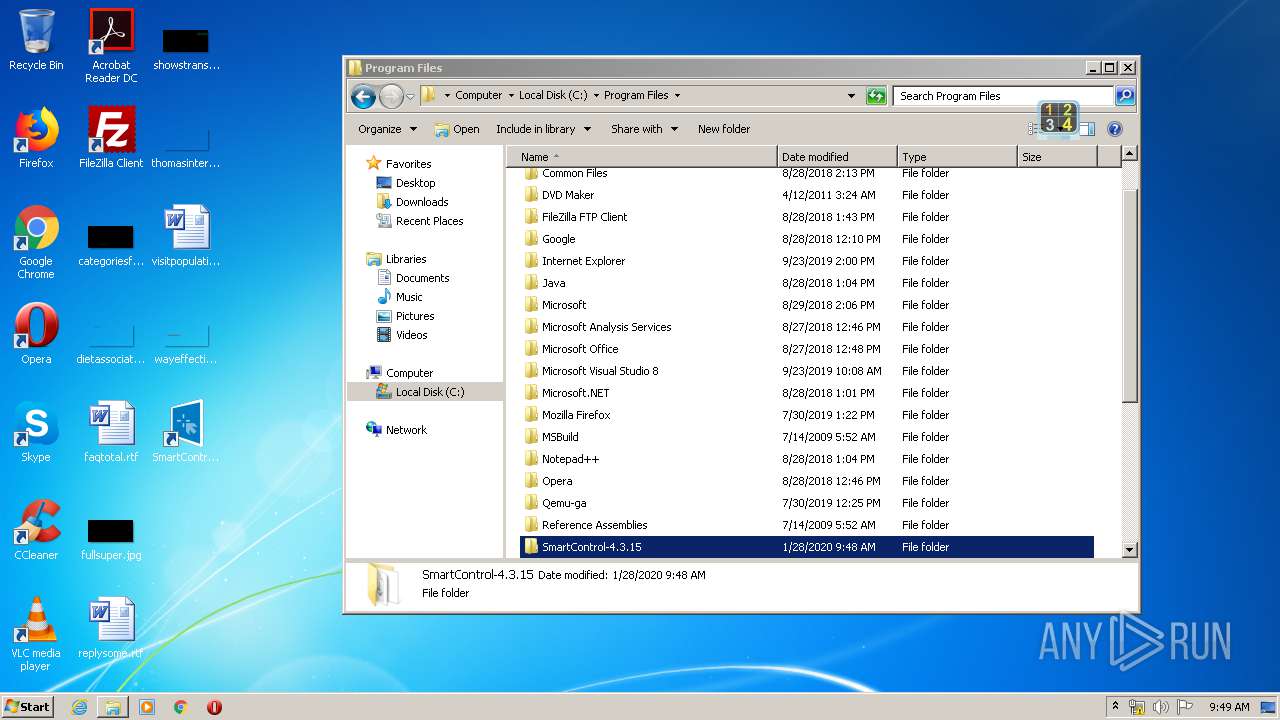
Creates files in the program directory
- SmartControl.exe (PID: 1136)
Creates files in the Windows directory
- SmartControl.exe (PID: 1136)
INFO
Creates a software uninstall entry
- msiexec.exe (PID: 3556)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3352)
Creates files in the program directory
- msiexec.exe (PID: 3556)
Manual execution by user
- Screen+.exe (PID: 3292)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CreateDate: | 1999:06:21 07:00:00 |
|---|---|
| Software: | Windows Installer |
| Security: | Password protected |
| CodePage: | Windows Latin 1 (Western European) |
| Template: | Intel;1033 |
| Pages: | 200 |
| RevisionNumber: | {A687F3A8-3929-4330-94FD-62F0FD0E381D} |
| Title: | SmartControl-4.3.15 |
| Subject: | - |
| Author: | PHL |
| Keywords: | - |
| Comments: | PHL |
| Words: | 2 |
| ModifyDate: | 2019:10:14 05:48:07 |
| LastPrinted: | 2019:10:14 05:48:07 |
Total processes
52
Monitored processes
10
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
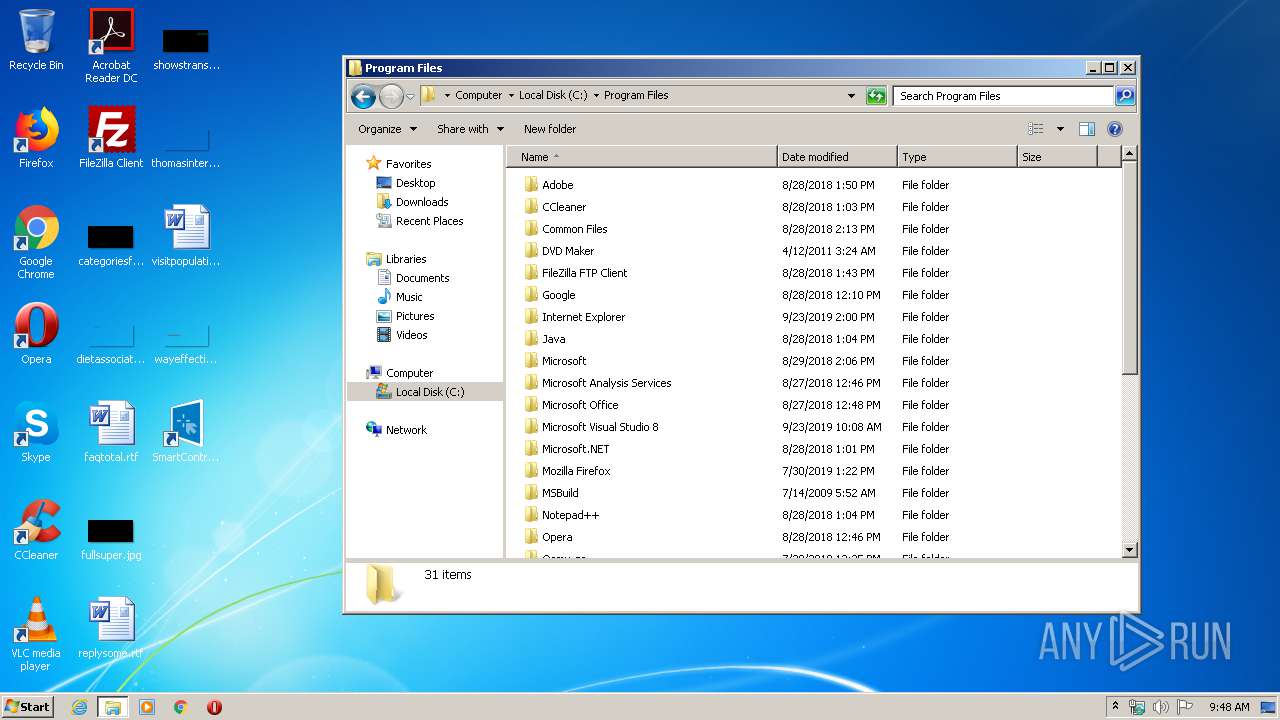
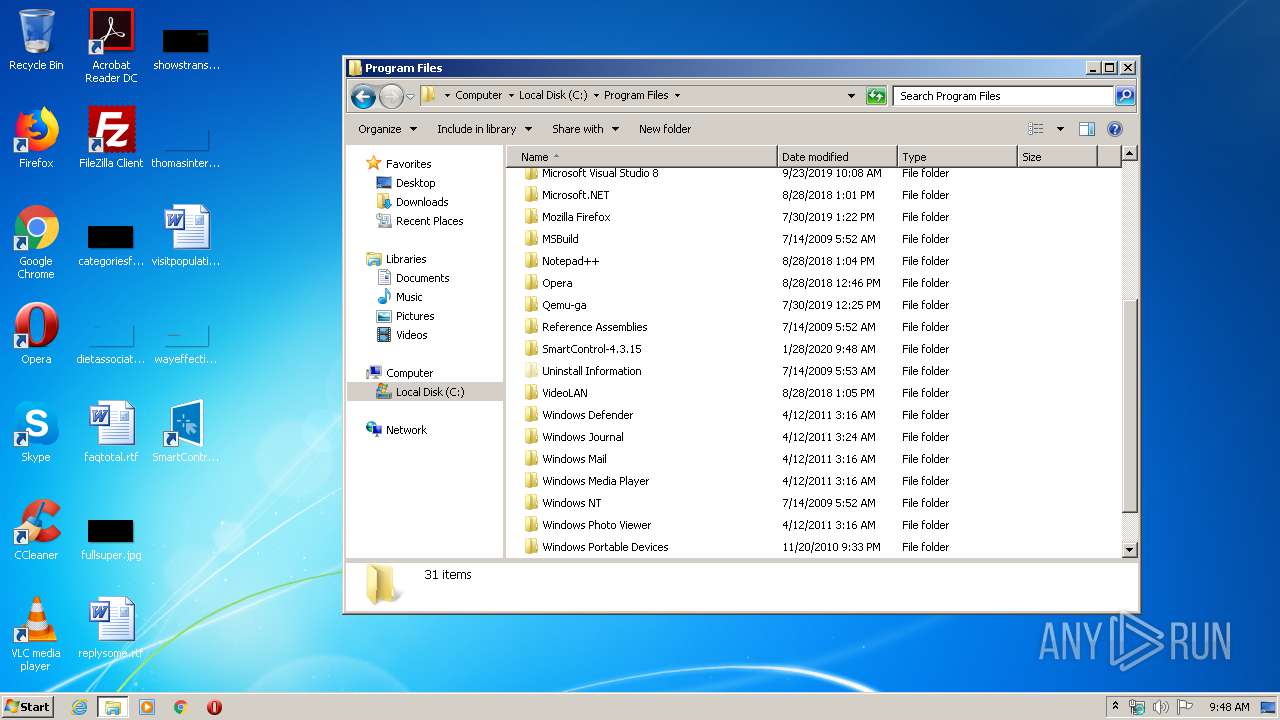
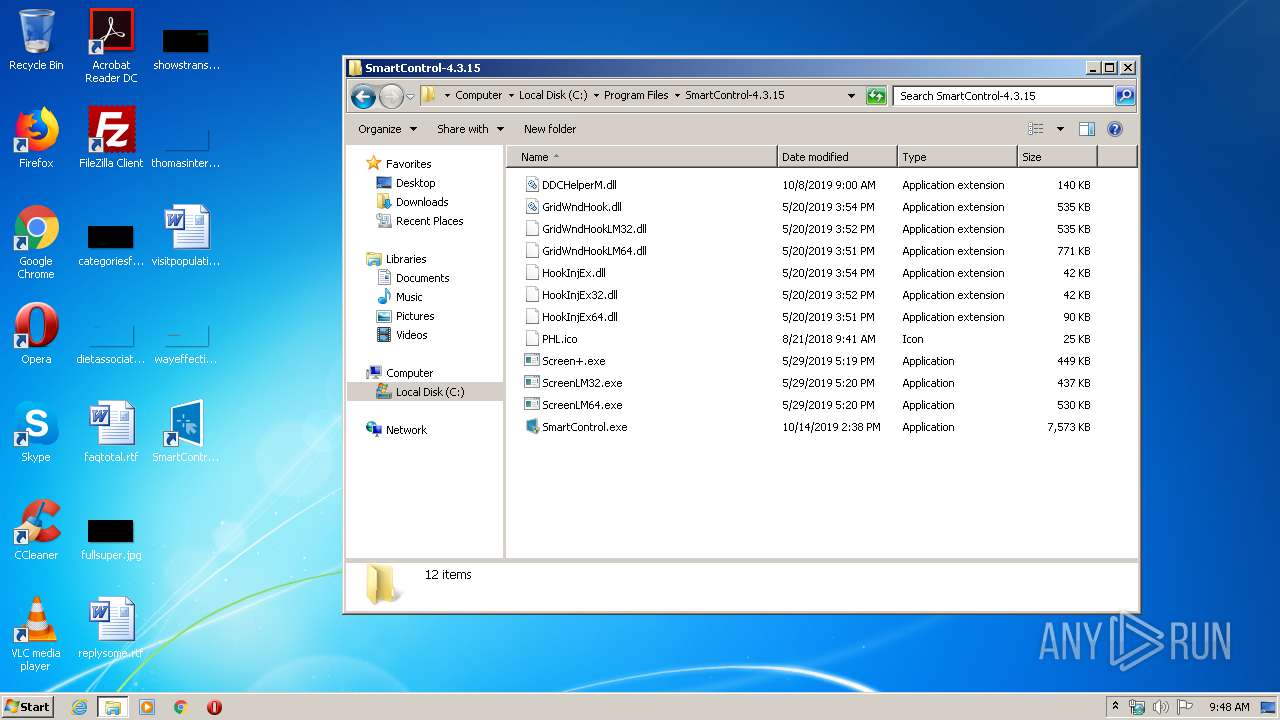
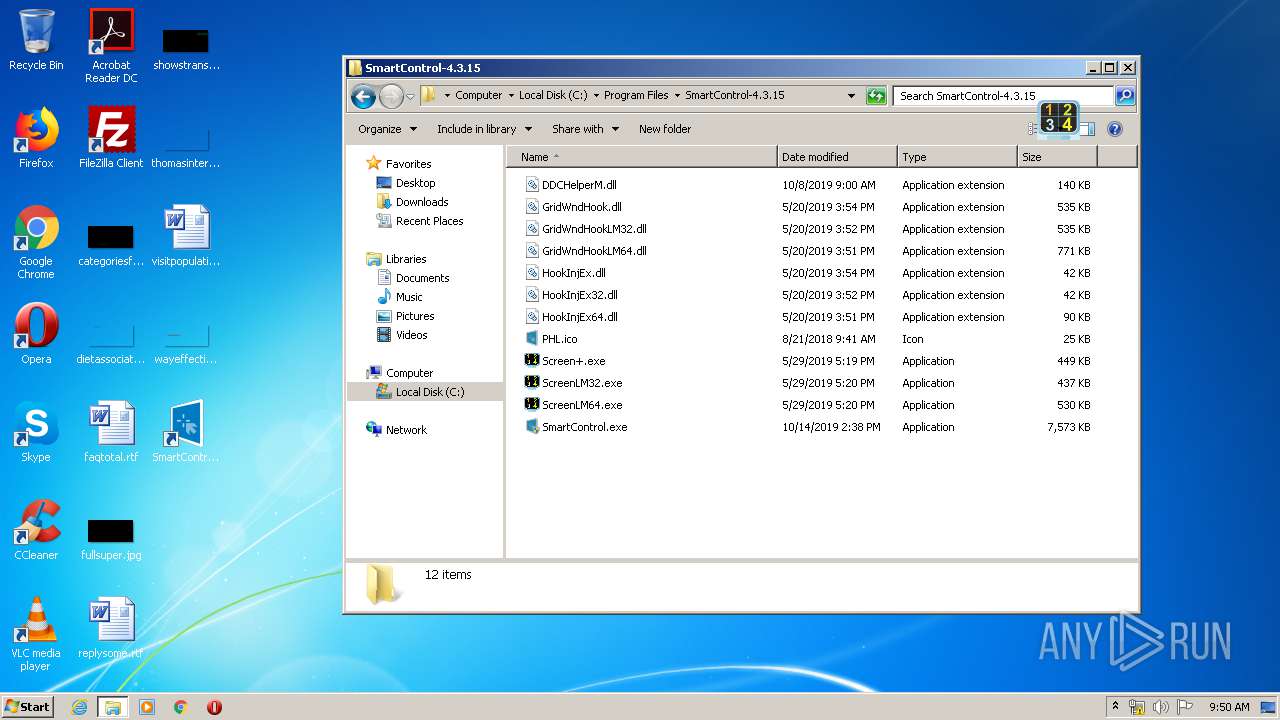
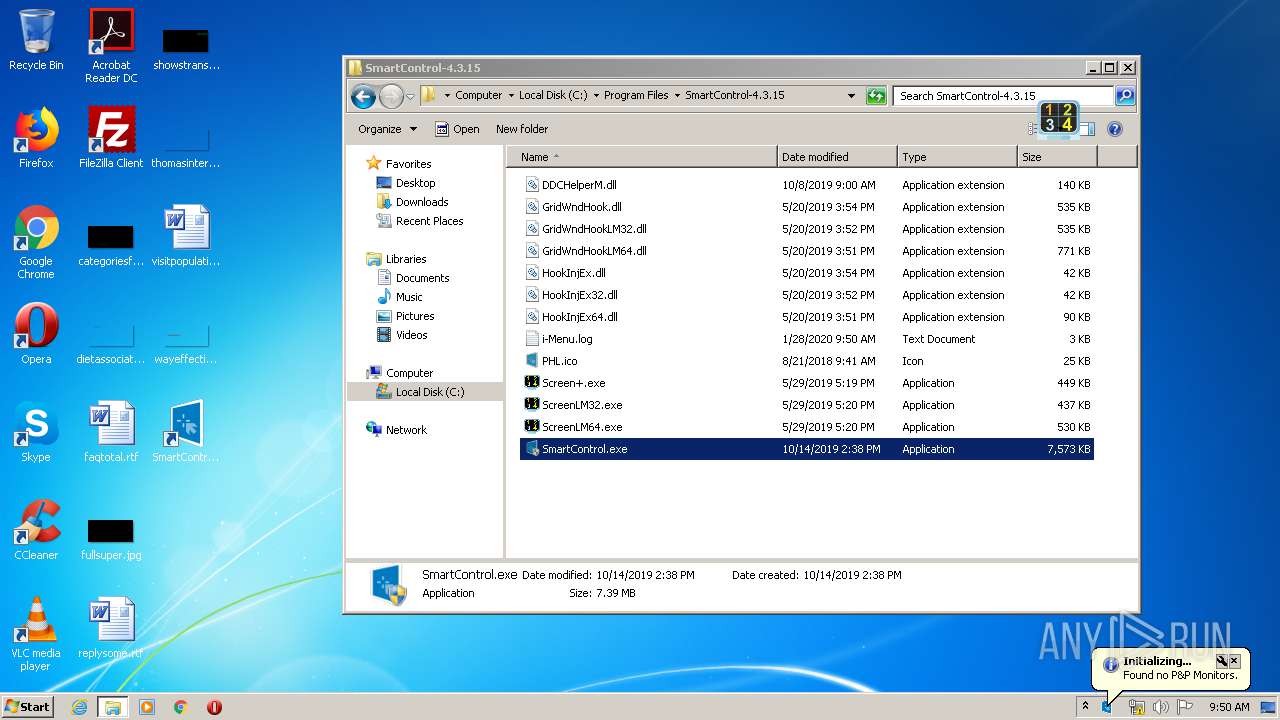
| 792 | "C:\Program Files\SmartControl-4.3.15\ScreenLM32.exe" | C:\Program Files\SmartControl-4.3.15\ScreenLM32.exe | explorer.exe | ||||||||||||
User: admin Company: AOC Corps Integrity Level: MEDIUM Description: Grid screen executable file Exit code: 0 Version: 1.1.1 Modules
| |||||||||||||||
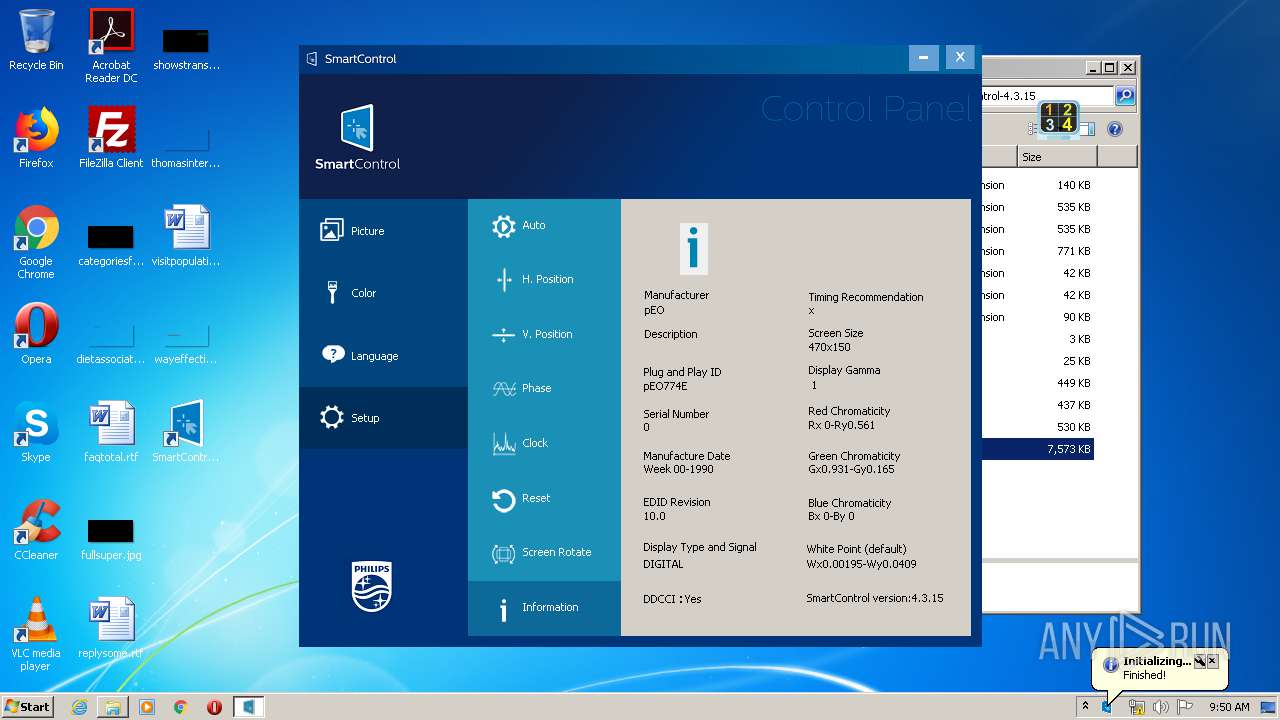
| 1000 | "C:\Program Files\SmartControl-4.3.15\SmartControl.exe" | C:\Program Files\SmartControl-4.3.15\SmartControl.exe | — | explorer.exe | |||||||||||
User: admin Company: PHL Monitors. Integrity Level: MEDIUM Description: SmartControl Exit code: 3221226540 Version: 4, 3, 10, 0 Modules
| |||||||||||||||
| 1136 | "C:\Program Files\SmartControl-4.3.15\SmartControl.exe" | C:\Program Files\SmartControl-4.3.15\SmartControl.exe | explorer.exe | ||||||||||||
User: admin Company: PHL Monitors. Integrity Level: HIGH Description: SmartControl Exit code: 0 Version: 4, 3, 10, 0 Modules
| |||||||||||||||
| 1232 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\SmartControl-4.3.15-Setup.msi" | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
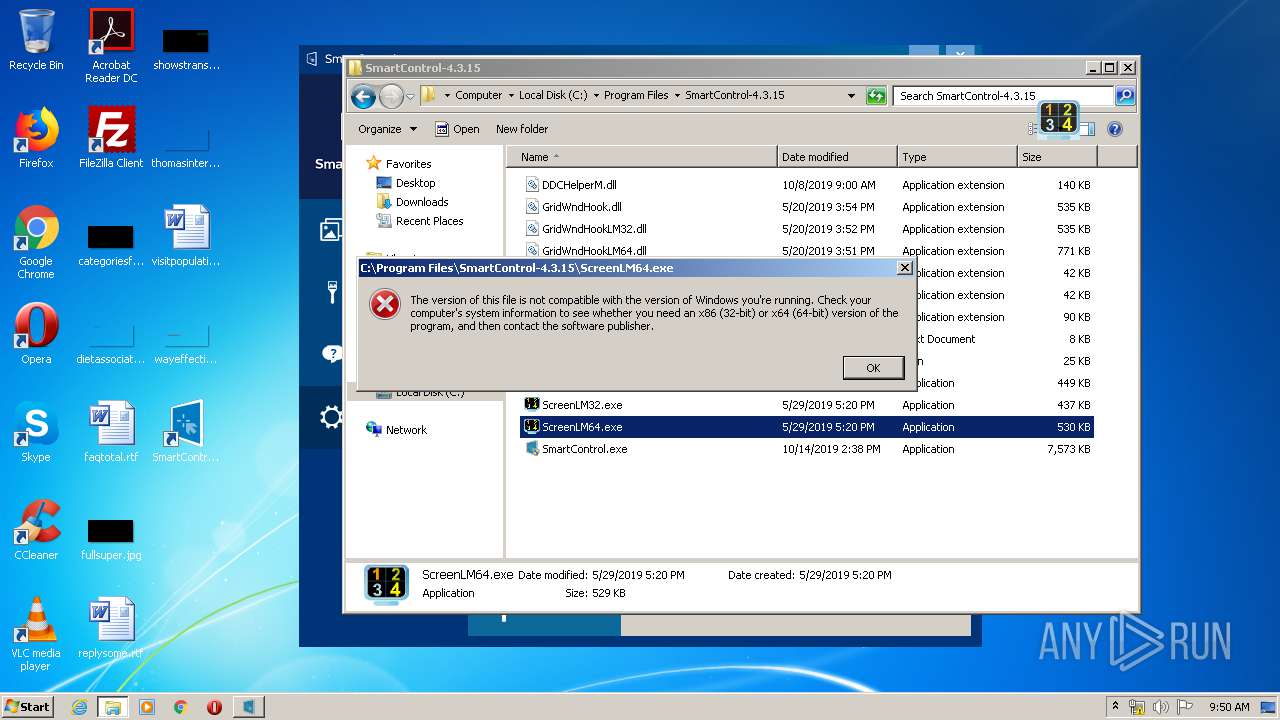
| 3292 | "C:\Program Files\SmartControl-4.3.15\Screen+.exe" | C:\Program Files\SmartControl-4.3.15\Screen+.exe | explorer.exe | ||||||||||||
User: admin Company: AOC Corps Integrity Level: MEDIUM Description: Grid screen executable file Exit code: 0 Version: 1.1.1 Modules
| |||||||||||||||
| 3352 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3404 | C:\Windows\system32\DllHost.exe /Processid:{AB8902B4-09CA-4BB6-B78D-A8F59079A8D5} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3556 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3664 | C:\Windows\system32\DllHost.exe /Processid:{AB8902B4-09CA-4BB6-B78D-A8F59079A8D5} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 819
Read events
2 247
Write events
554
Delete events
18
Modification events
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1232) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | Zvpebfbsg.Jvaqbjf.JvaqbjfVafgnyyre |
Value: 000000000000000000000000A6010000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000003F0000004F00000032B025000A00000018000000868F0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000005CE9ED0100000000000000000000000000000000480B20020000000005000000D80B200200000000340C200270E9ED01C0E9ED010000000000000000C0DB2002050000002000000000000000000000000100000064666C7464666C7400000000400000000459A377AD0501A70000000000000000010000000000000000000000B02D0C08A82C0C08A4E9ED013DA9D27600000000FBFFFF7FC8E9ED01987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000371054065310540637105406000000000000000000000000080000002E006C006E006B0000006E006400200011000000483D3200403D32002E006C006E006B0000002F0080EA0000C85704AB34EAED018291D27680EAED01EC430000E45704AB48EAED01B69CD276F04311024C06000060EAED01603F11026CEAED0111000000483D3200403D320060EAED01803F1102D0EA0000BC5704AB80EAED018291D276D0EAED0184EAED012795D27600000000EC431102ACEAED01CD94D276EC43110258EBED01603F1102E194D27600000000603F110258EBED01B4EAED010A00000018000000868F0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000005CE9ED0100000000000000000000000000000000480B20020000000005000000D80B200200000000340C200270E9ED01C0E9ED010000000000000000C0DB2002050000002000000000000000000000000100000064666C7464666C7400000000400000000459A377AD0501A70000000000000000010000000000000000000000B02D0C08A82C0C08A4E9ED013DA9D27600000000FBFFFF7FC8E9ED01987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000371054065310540637105406000000000000000000000000080000002E006C006E006B0000006E006400200011000000483D3200403D32002E006C006E006B0000002F0080EA0000C85704AB34EAED018291D27680EAED01EC430000E45704AB48EAED01B69CD276F04311024C06000060EAED01603F11026CEAED0111000000483D3200403D320060EAED01803F1102D0EA0000BC5704AB80EAED018291D276D0EAED0184EAED012795D27600000000EC431102ACEAED01CD94D276EC43110258EBED01603F1102E194D27600000000603F110258EBED01B4EAED010A00000018000000868F0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000005CE9ED0100000000000000000000000000000000480B20020000000005000000D80B200200000000340C200270E9ED01C0E9ED010000000000000000C0DB2002050000002000000000000000000000000100000064666C7464666C7400000000400000000459A377AD0501A70000000000000000010000000000000000000000B02D0C08A82C0C08A4E9ED013DA9D27600000000FBFFFF7FC8E9ED01987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000371054065310540637105406000000000000000000000000080000002E006C006E006B0000006E006400200011000000483D3200403D32002E006C006E006B0000002F0080EA0000C85704AB34EAED018291D27680EAED01EC430000E45704AB48EAED01B69CD276F04311024C06000060EAED01603F11026CEAED0111000000483D3200403D320060EAED01803F1102D0EA0000BC5704AB80EAED018291D276D0EAED0184EAED012795D27600000000EC431102ACEAED01CD94D276EC43110258EBED01603F1102E194D27600000000603F110258EBED01B4EAED01 | |||
| (PID) Process: | (3556) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 40000000000000008C7F6814C0D5D501E40D000030030000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3556) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 40000000000000008C7F6814C0D5D501E40D000030030000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3556) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 34 | |||
| (PID) Process: | (3556) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4000000000000000262DB714C0D5D501E40D000030030000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3556) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000262DB714C0D5D501E40D0000E4080000E8030000010000000000000000000000DCAD6DEF728B5A4DB030C8F2E3FE129F0000000000000000 | |||
| (PID) Process: | (3352) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000427BC514C0D5D501180D00008C0C0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
14
Suspicious files
5
Text files
132
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3556 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3556 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFDC14538350DBBCE4.TMP | — | |
MD5:— | SHA256:— | |||
| 3556 | msiexec.exe | C:\Program Files\SmartControl-4.3.15\GridWndHook.dll | executable | |
MD5:— | SHA256:— | |||
| 3556 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:— | SHA256:— | |||
| 3556 | msiexec.exe | C:\Windows\Installer\a6d3e3.ipi | binary | |
MD5:— | SHA256:— | |||
| 3352 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 3556 | msiexec.exe | C:\Config.Msi\a6d3e4.rbs | — | |
MD5:— | SHA256:— | |||
| 3556 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFFCE960C6A0BEC694.TMP | — | |
MD5:— | SHA256:— | |||
| 3556 | msiexec.exe | C:\Windows\Installer\a6d3e2.msi | executable | |
MD5:— | SHA256:— | |||
| 3556 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{ef6daddc-8b72-4d5a-b030-c8f2e3fe129f}_OnDiskSnapshotProp | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
Screen+.exe | Find Window failed! |
Screen+.exe | That is Inj message!
|
Screen+.exe | Installed hook successfully!
|
ScreenLM32.exe | That is Inj message!
|
ScreenLM32.exe | Find Window failed! |
Screen+.exe | Window created!
|
ScreenLM32.exe | Installed hook successfully!
|
ScreenLM32.exe | WM_DESTROY!
|
ScreenLM32.exe | WM_DESTROY!
|
ScreenLM32.exe | WM_DESTROY!
|