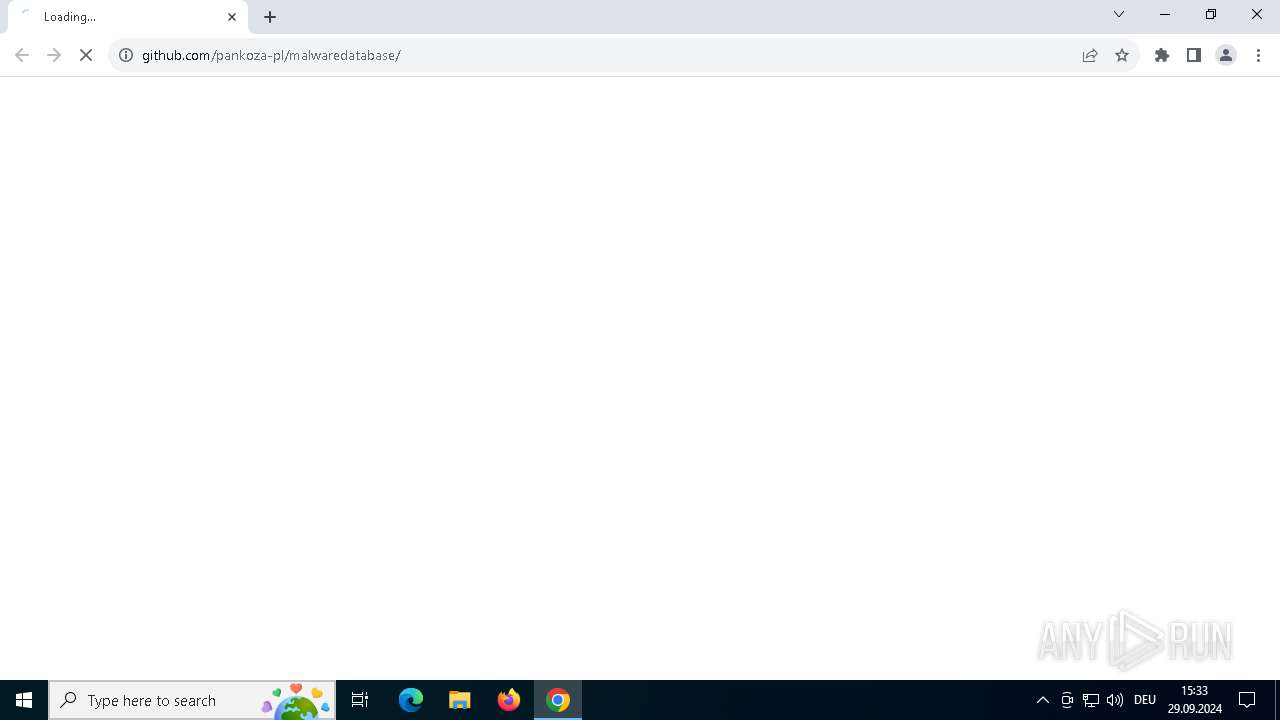
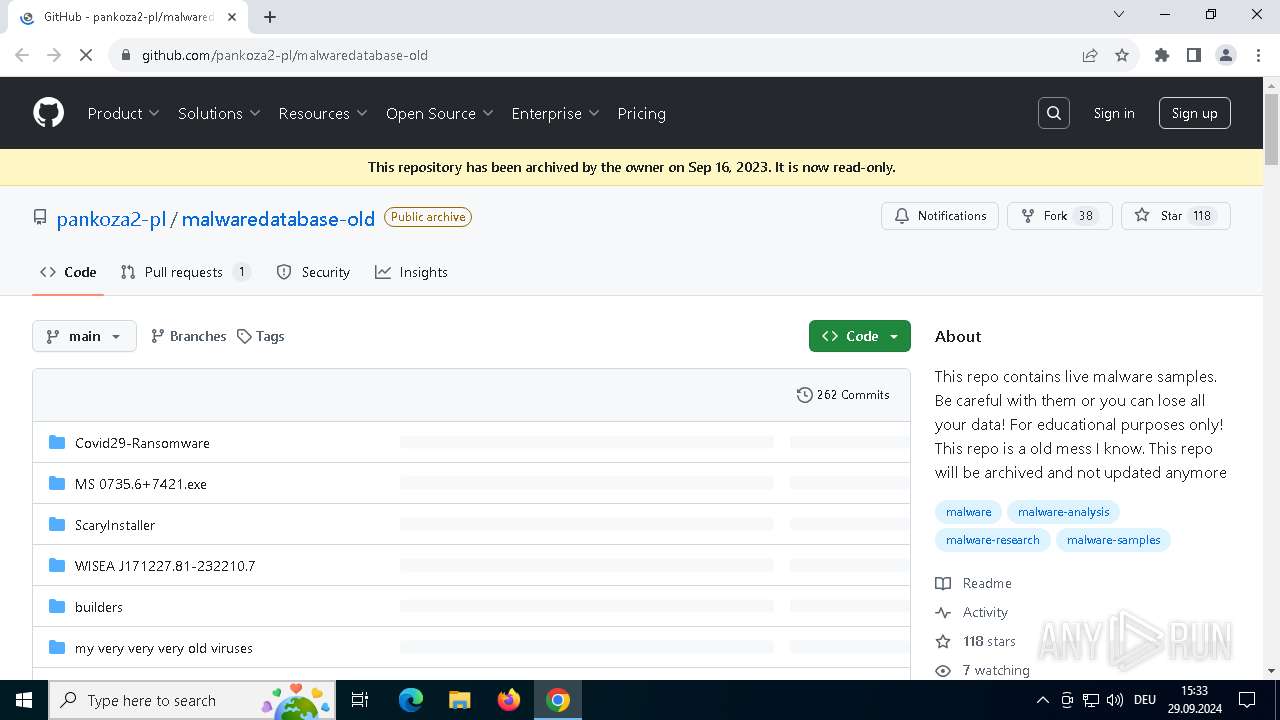
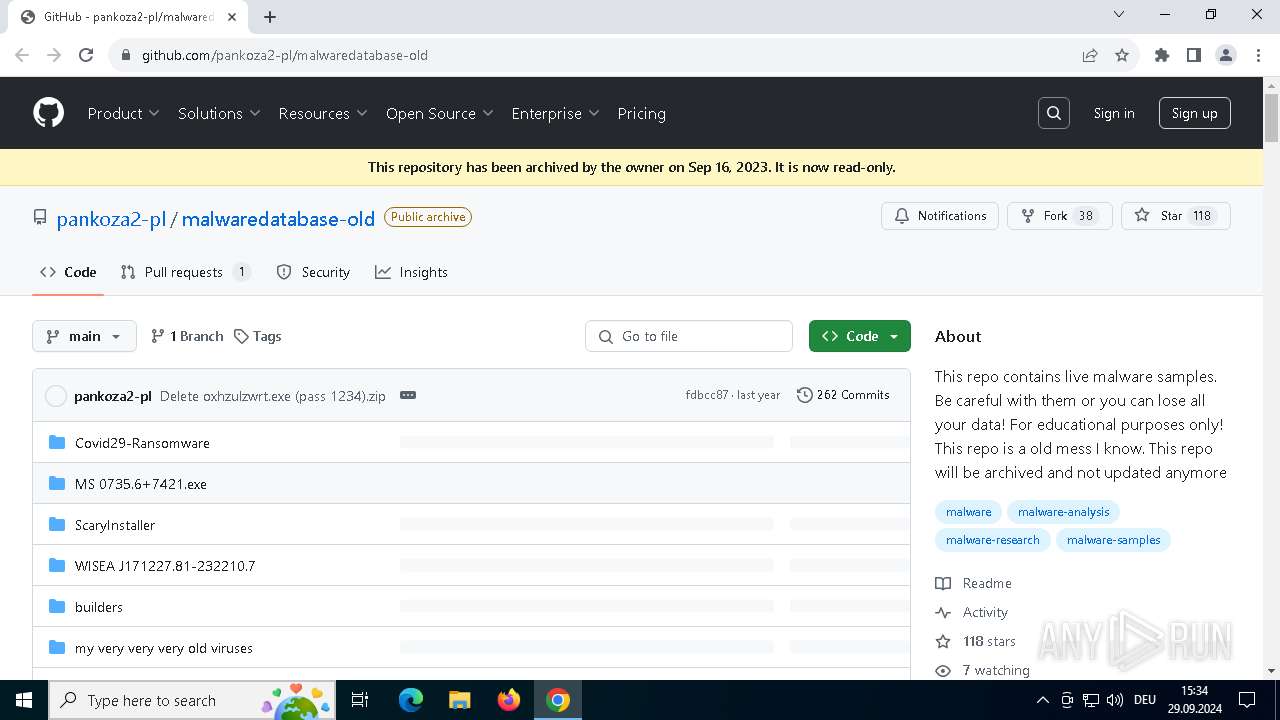
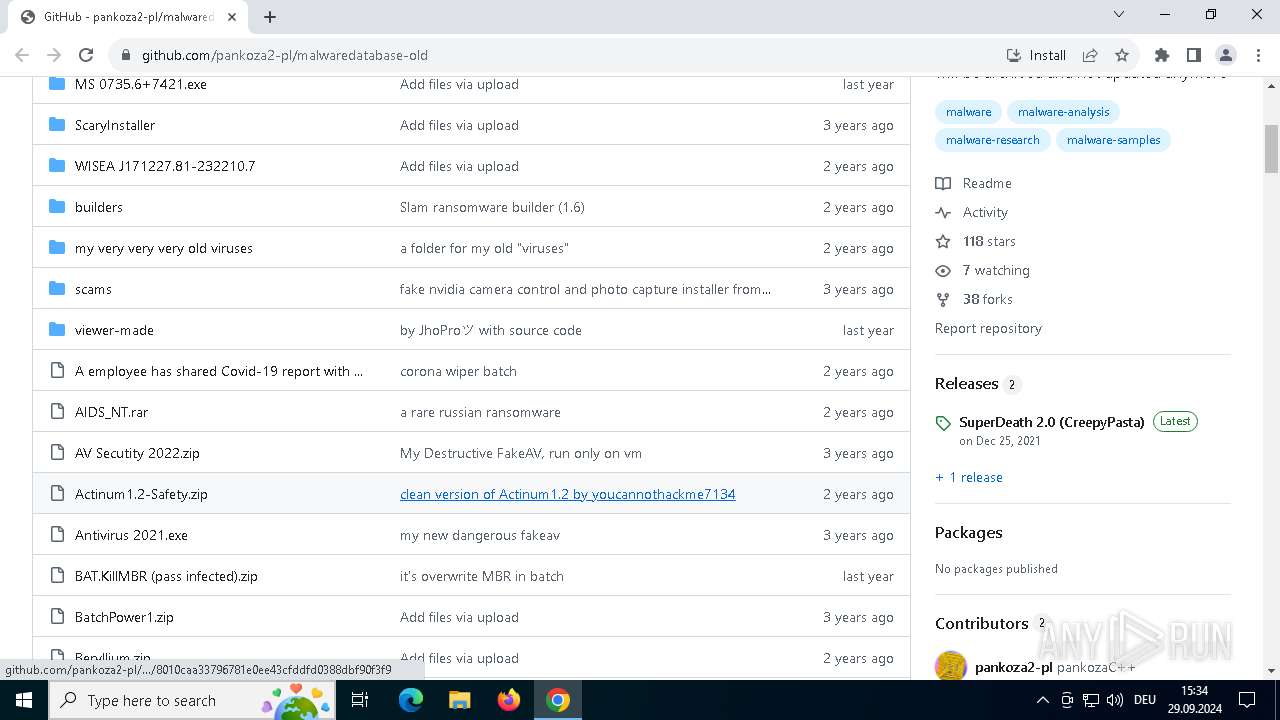
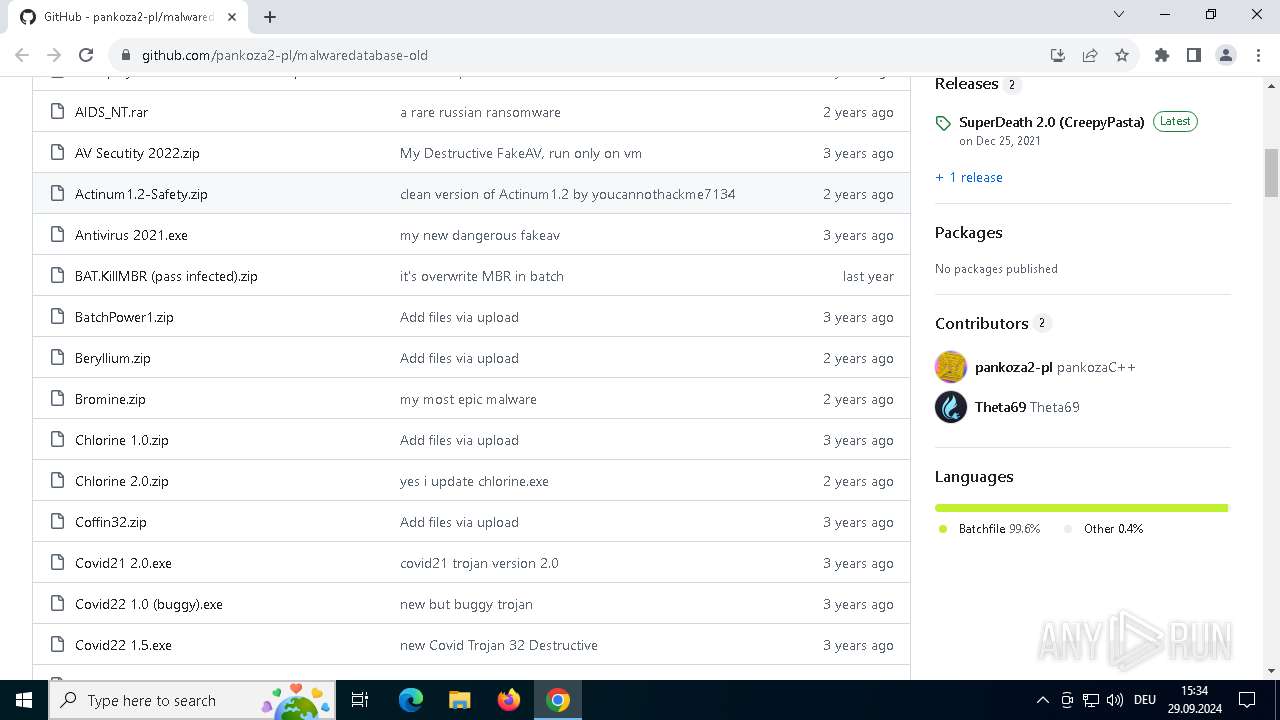
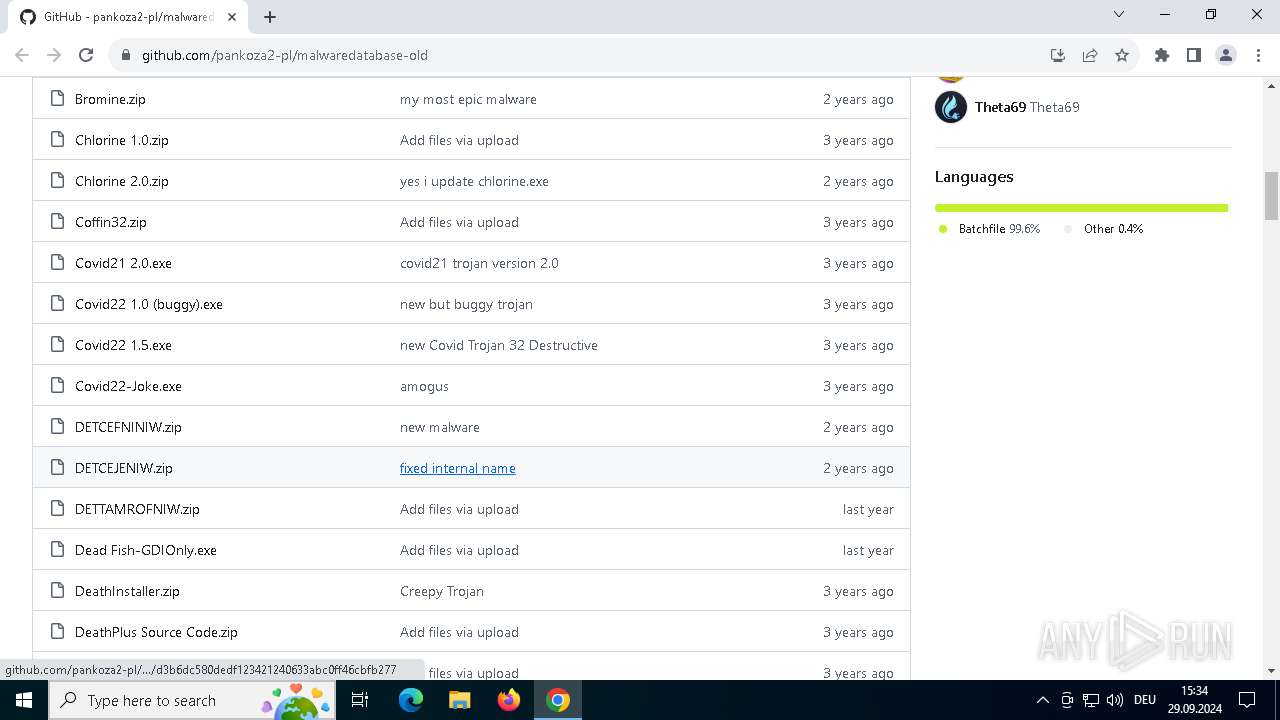
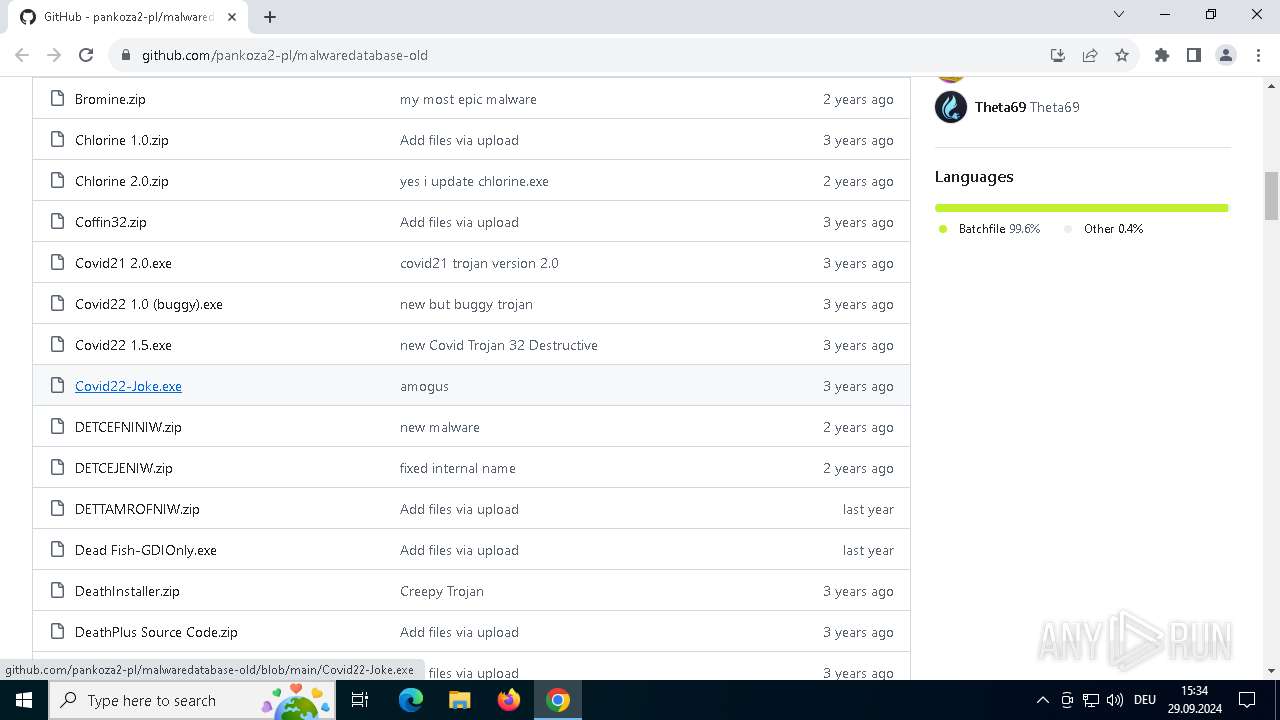
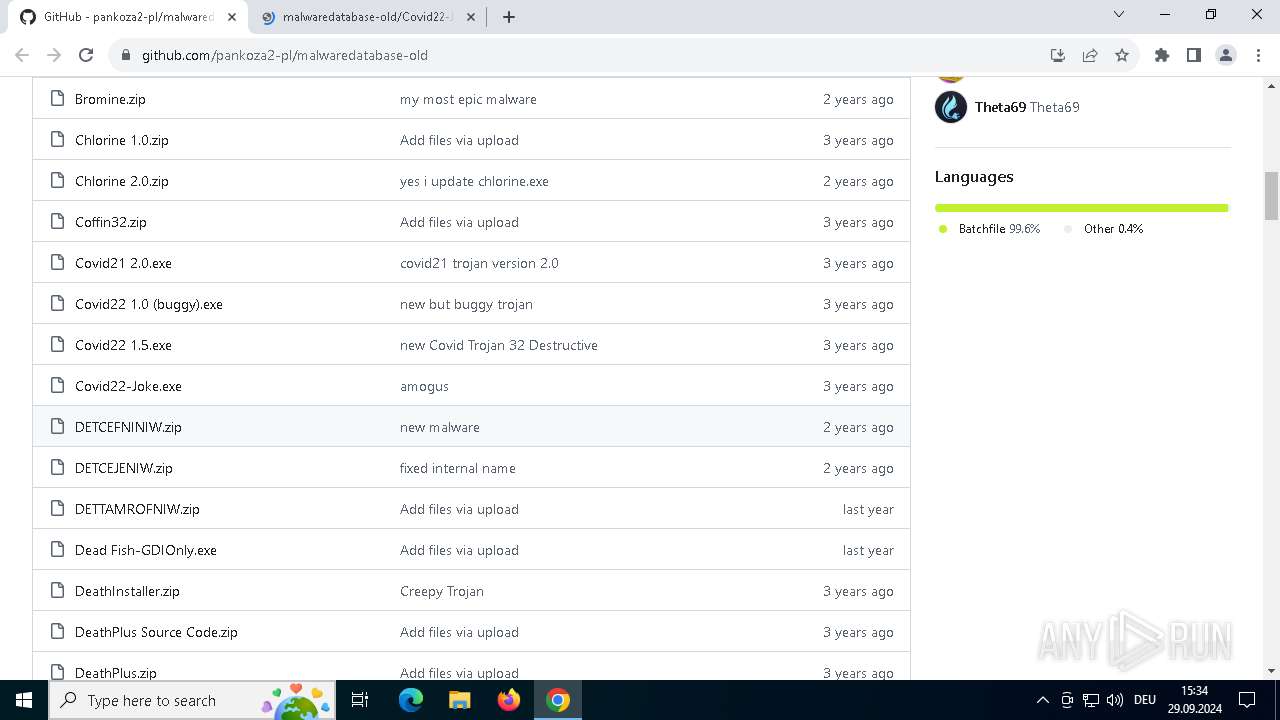
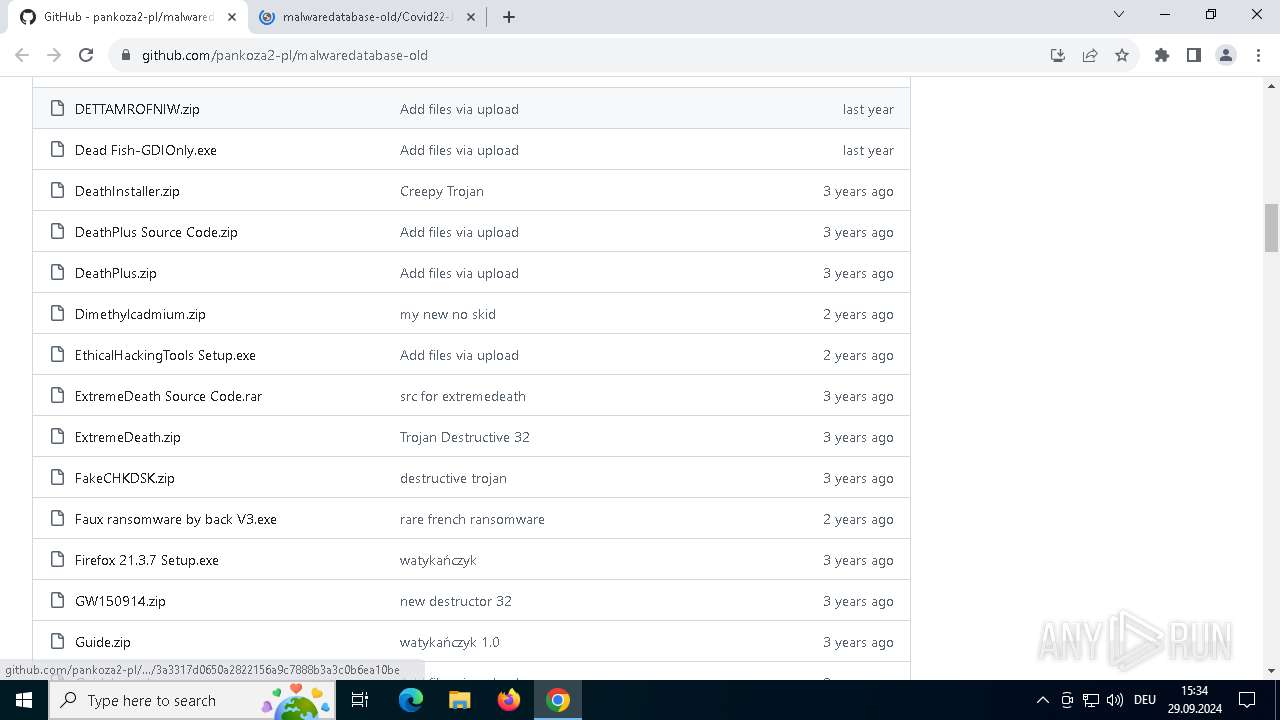
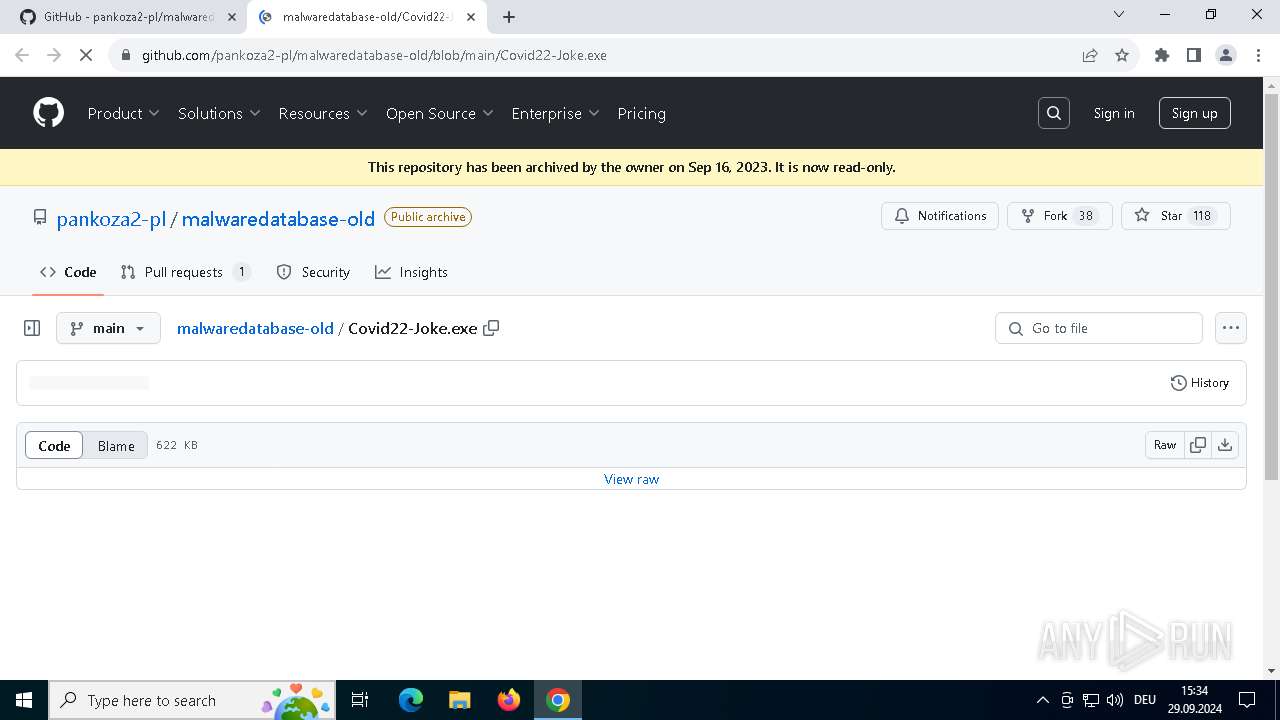
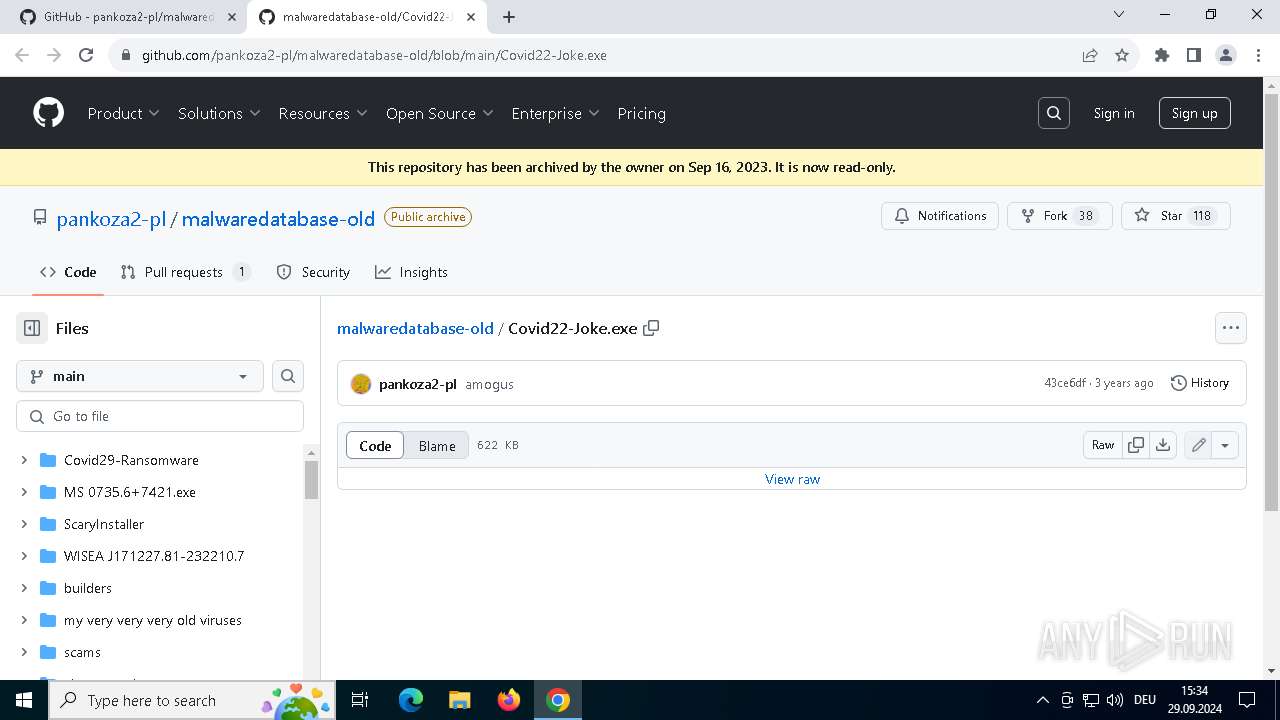
| URL: | https://github.com/pankoza-pl/malwaredatabase/ |
| Full analysis: | https://app.any.run/tasks/189c2f1e-be13-434c-a52d-3d5f4a9dd99c |
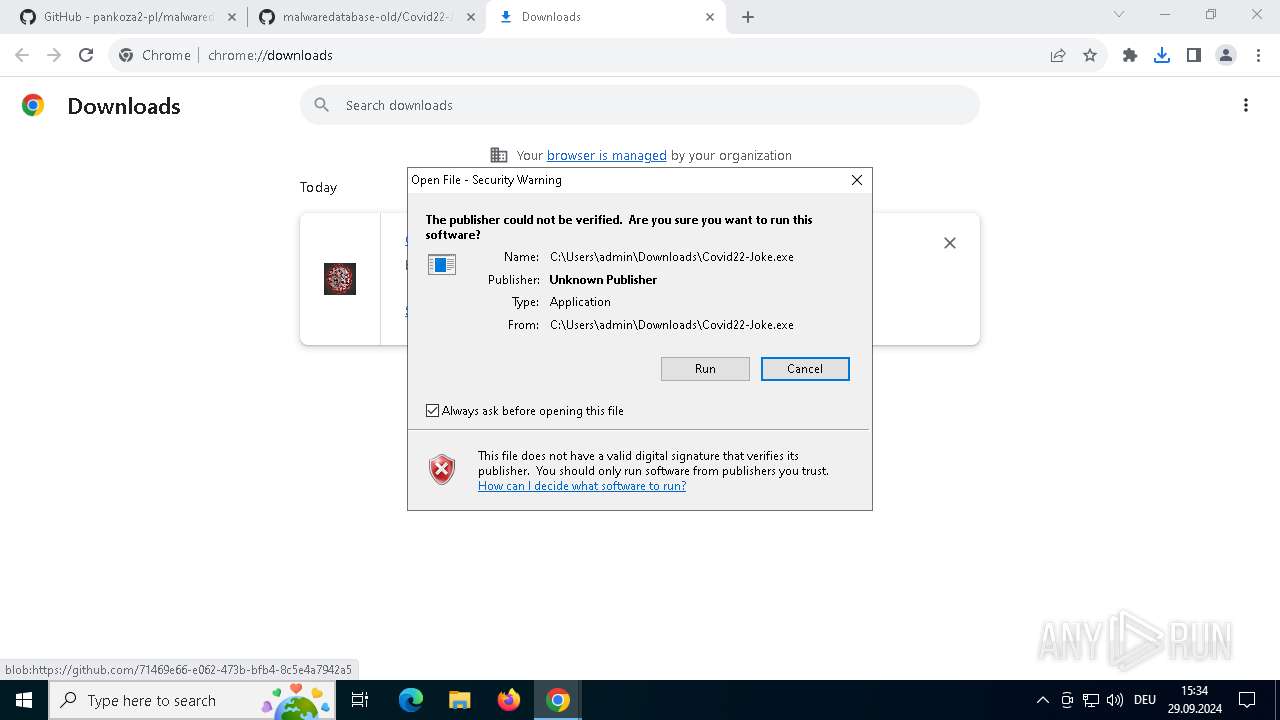
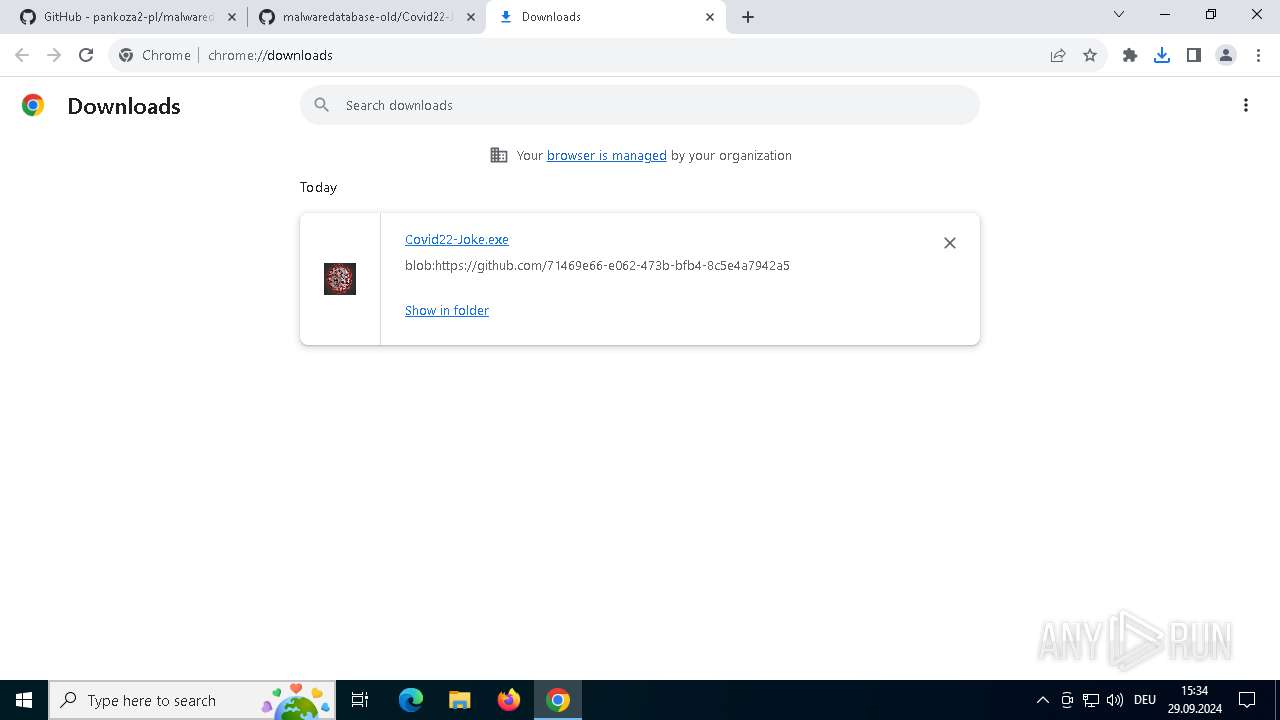
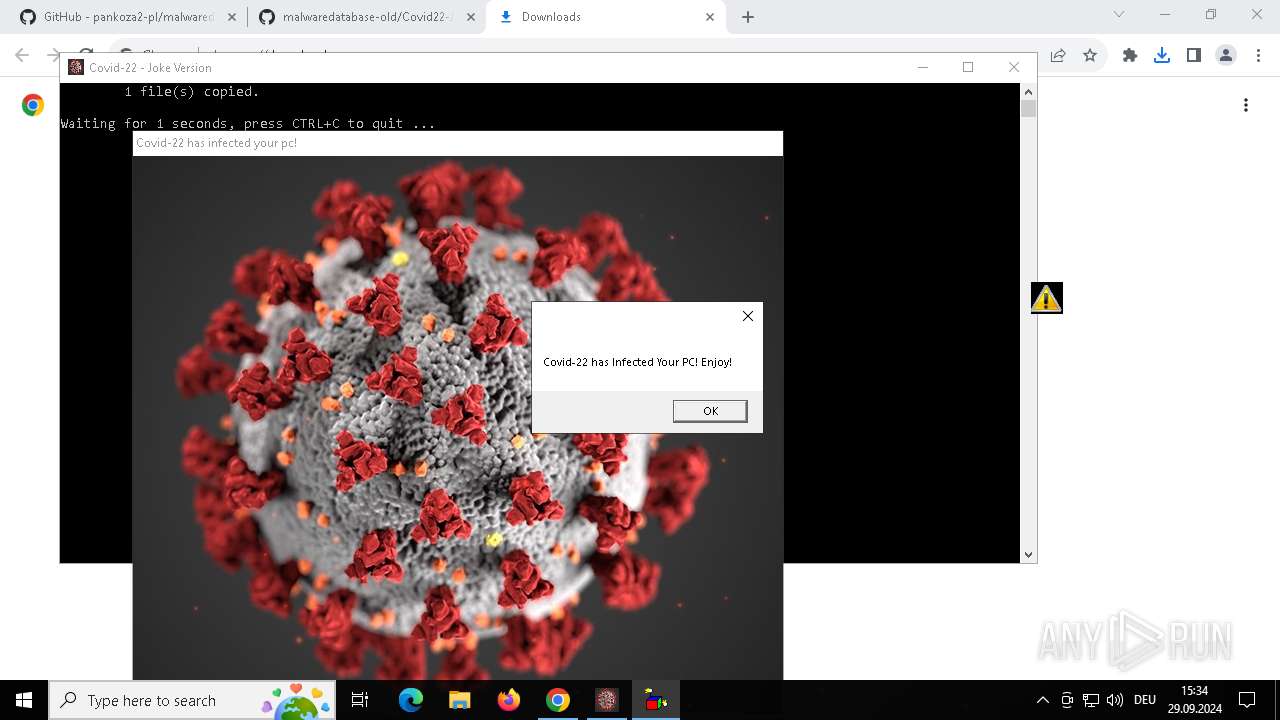
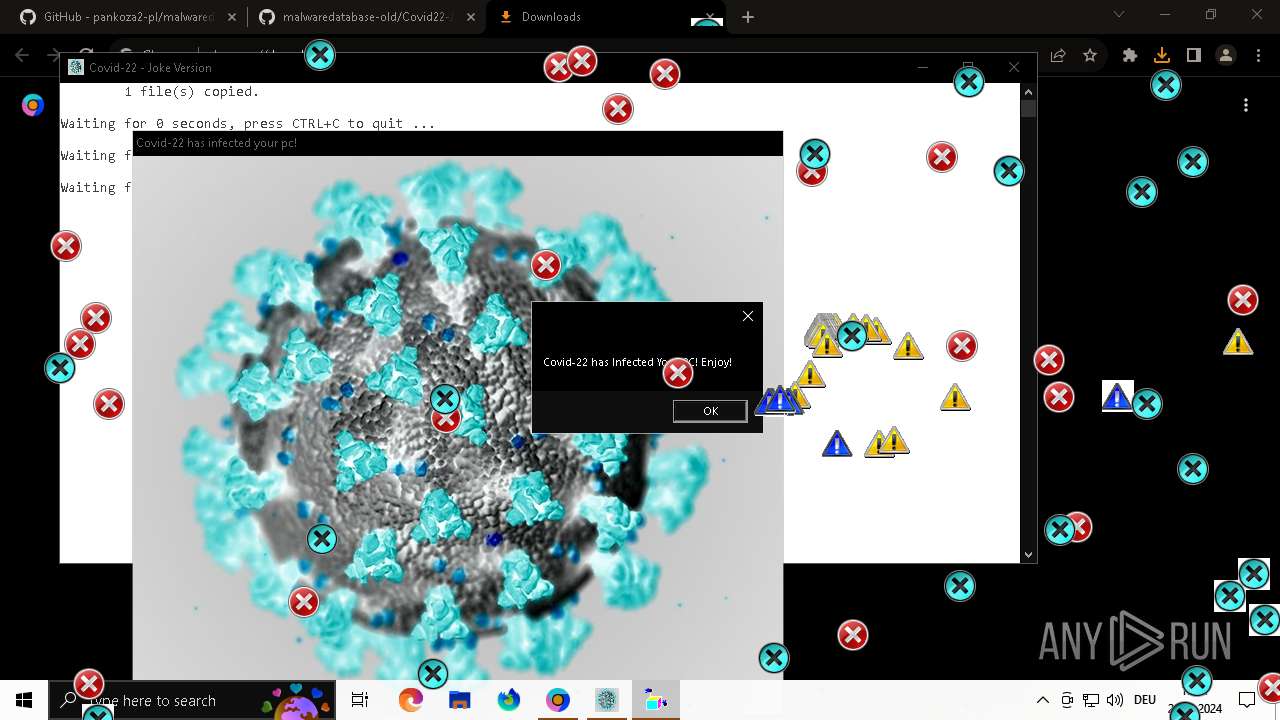
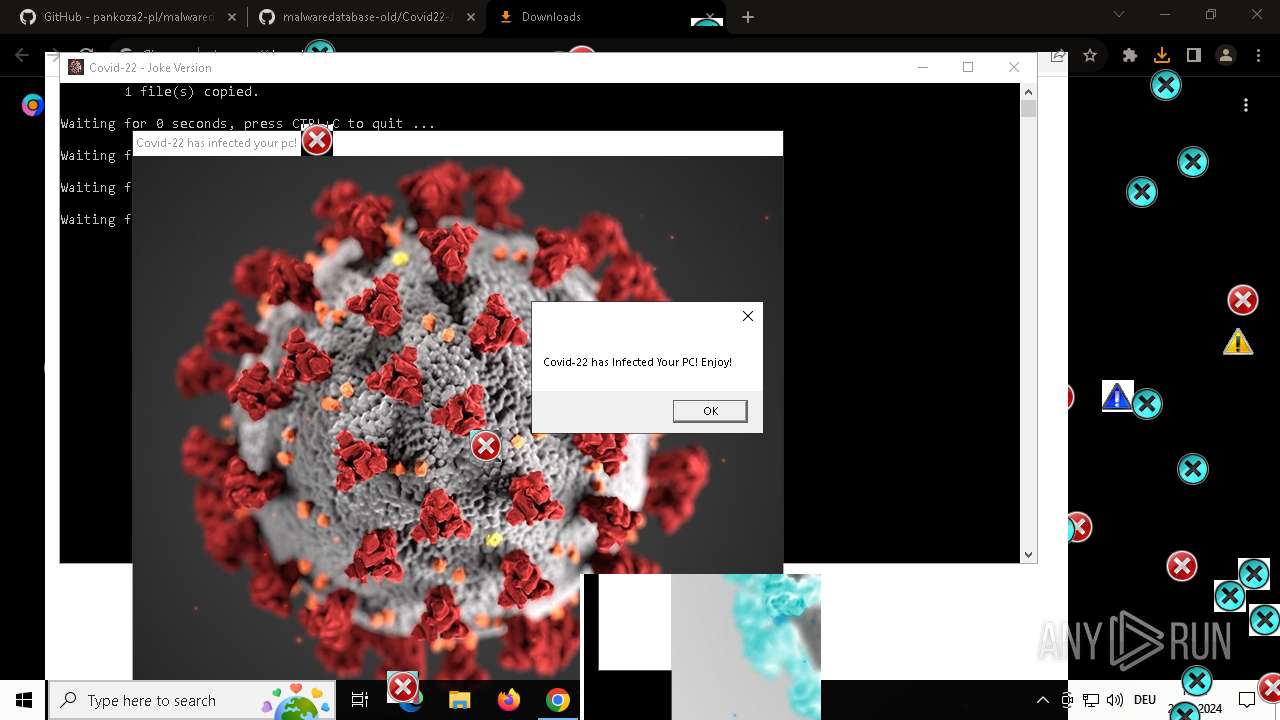
| Verdict: | Malicious activity |
| Analysis date: | September 29, 2024, 13:33:43 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 61ACCD74C9D0795DD5843EAE08B476C5 |
| SHA1: | 0DF16A760AAD9D5BB17F6878739B5C15D0D6FC21 |
| SHA256: | A51A84F762EF1CAC8FBE67F4220BCA858C406FD9CDC991572E9EA8DC80E5BFB9 |
| SSDEEP: | 3:N8tEdlELlfVKIXKR2n:2uoLFN62 |
MALICIOUS
No malicious indicators.SUSPICIOUS
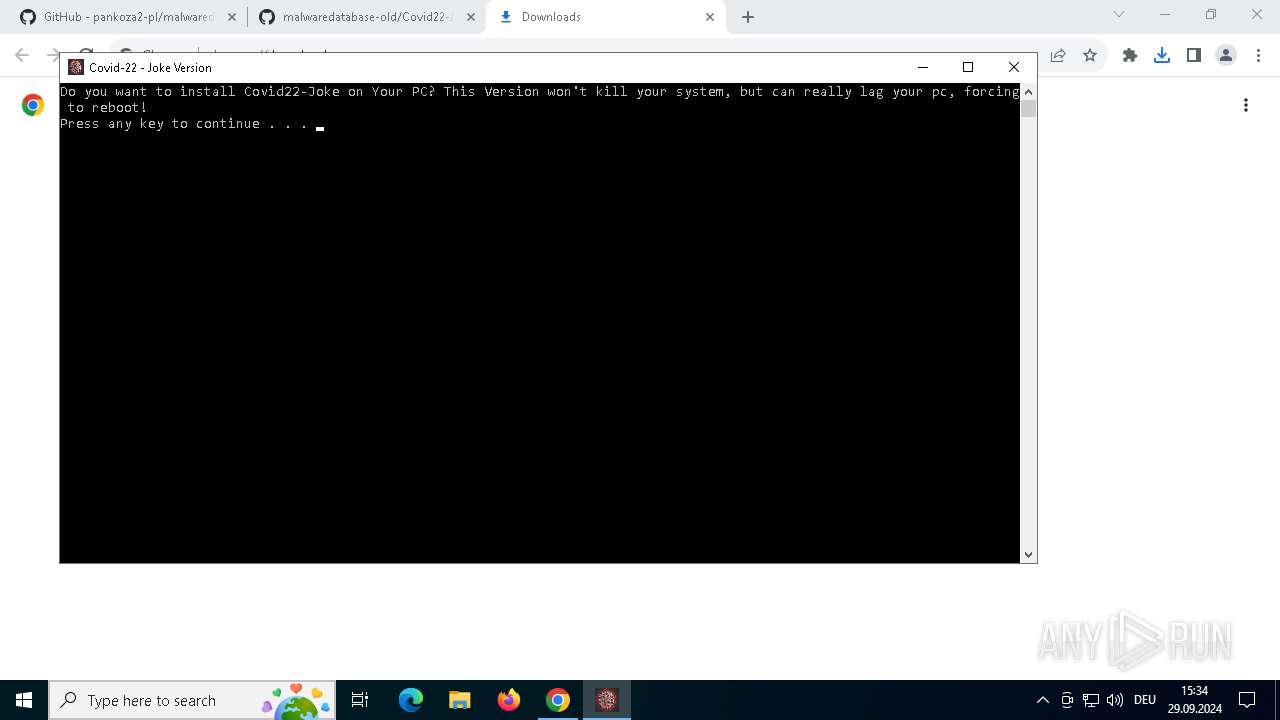
Starts CMD.EXE for commands execution
- Covid22-Joke.exe (PID: 6056)
Executing commands from ".cmd" file
- Covid22-Joke.exe (PID: 6056)
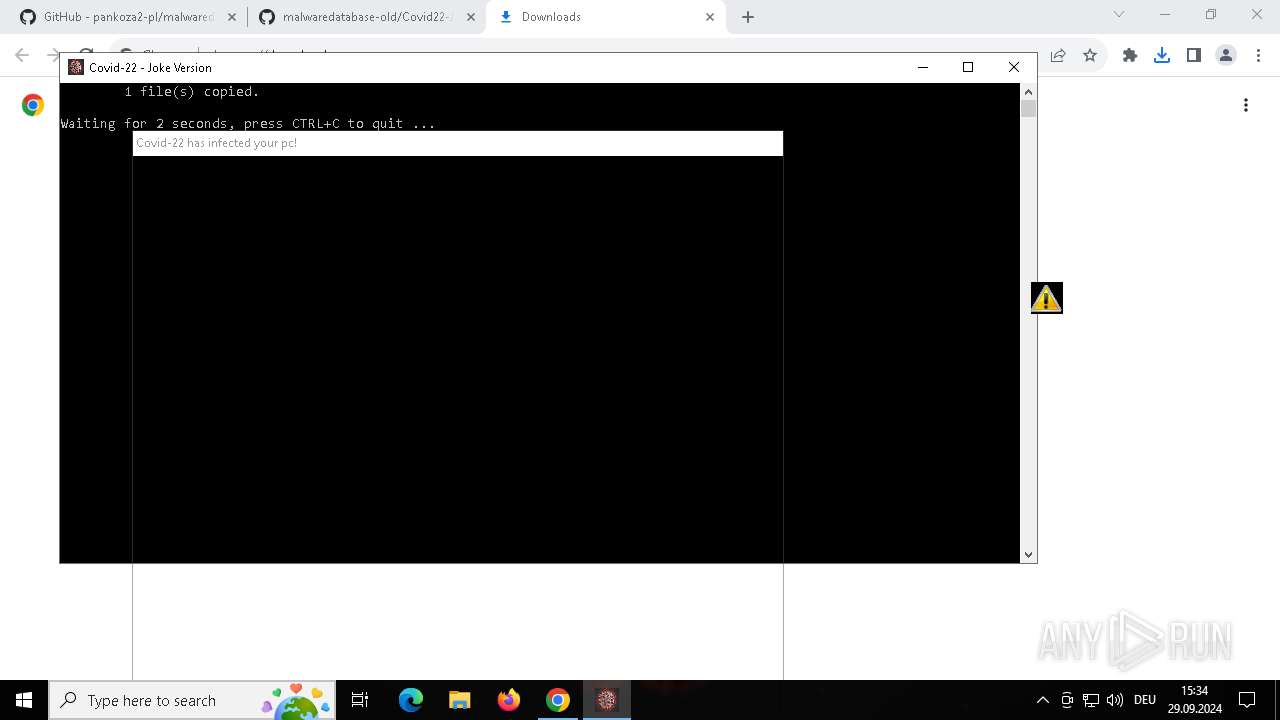
Executable content was dropped or overwritten
- Covid22-Joke.exe (PID: 6056)
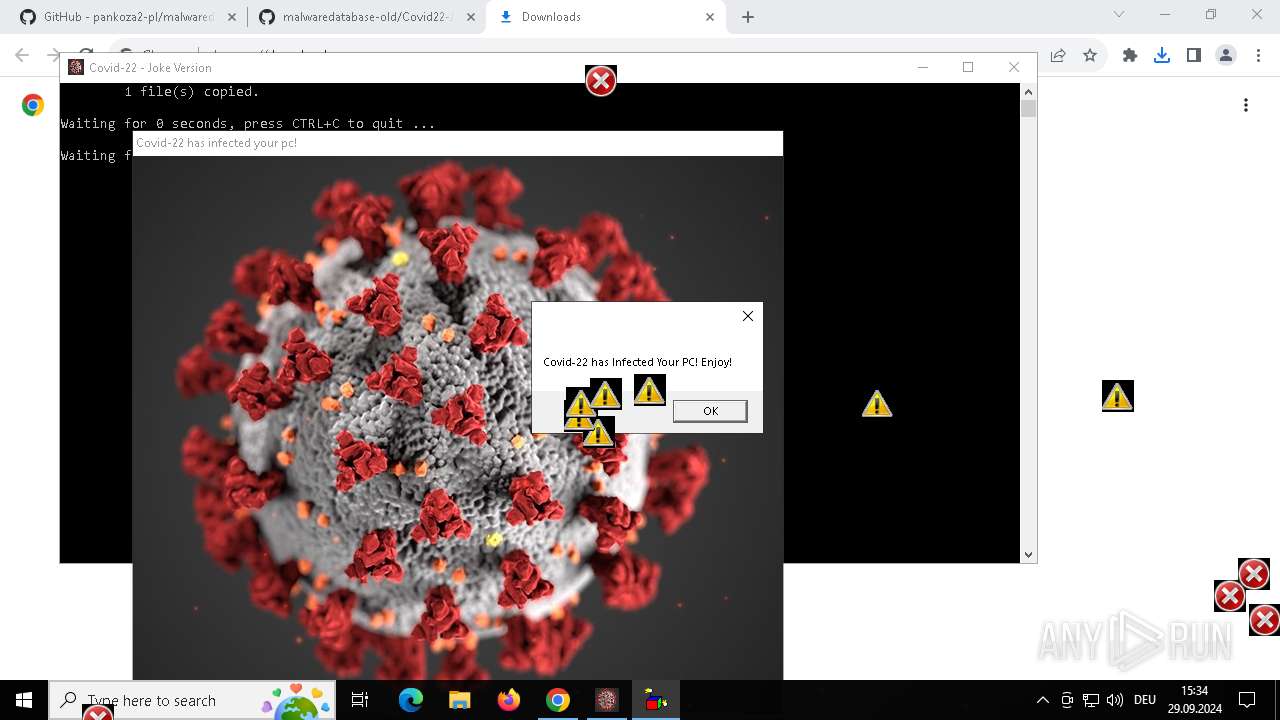
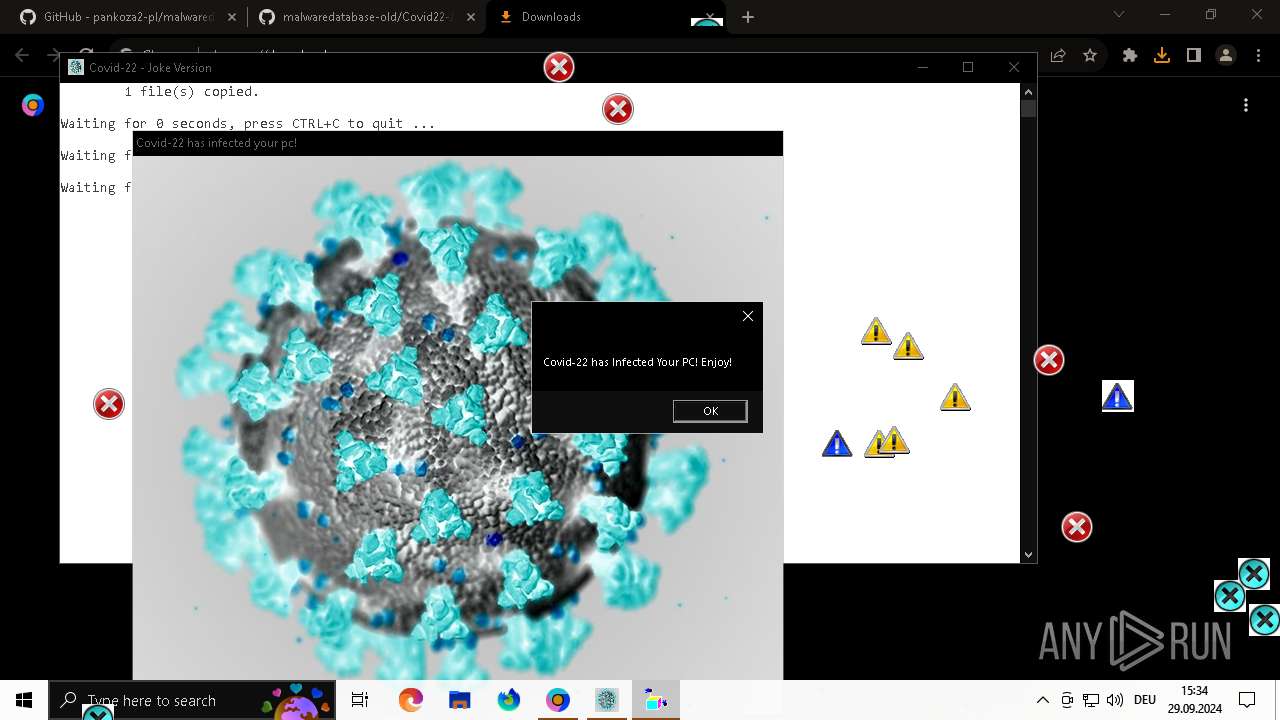
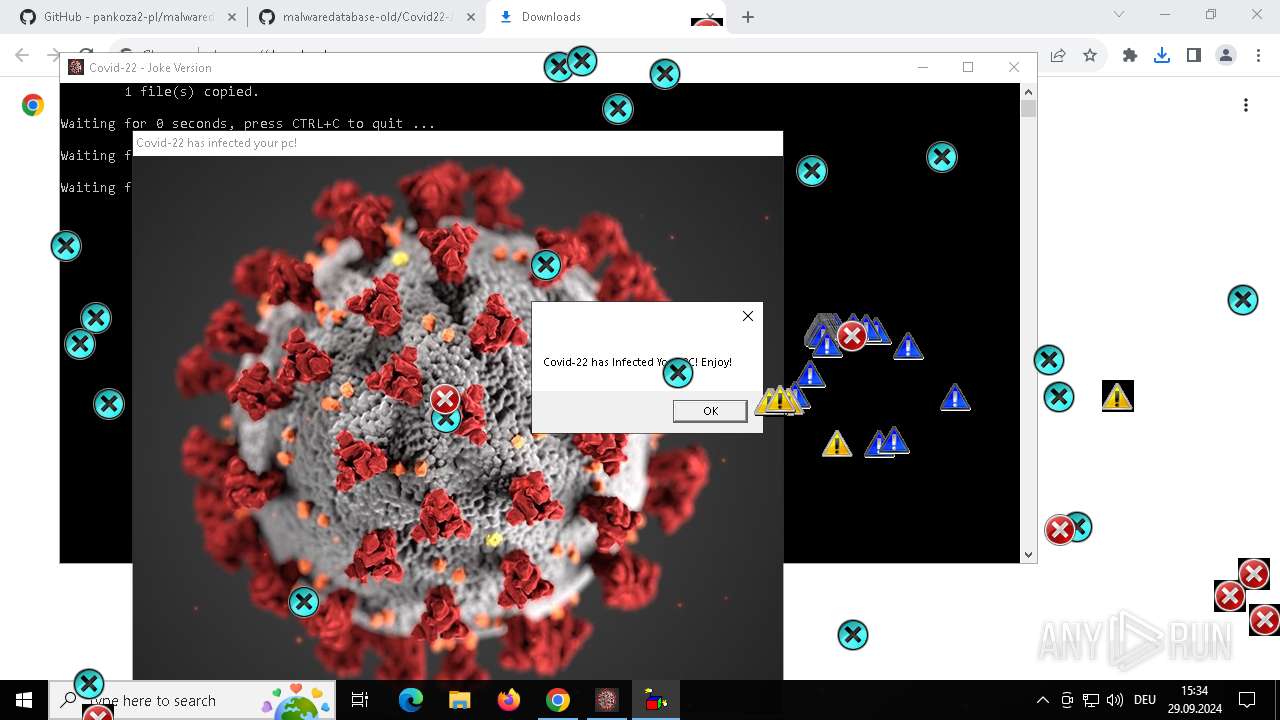
The executable file from the user directory is run by the CMD process
- IconSpam.exe (PID: 5940)
- CoronaPopup.exe (PID: 6972)
- CLWCP.exe (PID: 1944)
- inv.exe (PID: 1072)
- ClutterScreen.exe (PID: 2636)
- MouseDraw.exe (PID: 3116)
The process executes VB scripts
- cmd.exe (PID: 5288)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 5288)
INFO
Executable content was dropped or overwritten
- chrome.exe (PID: 832)
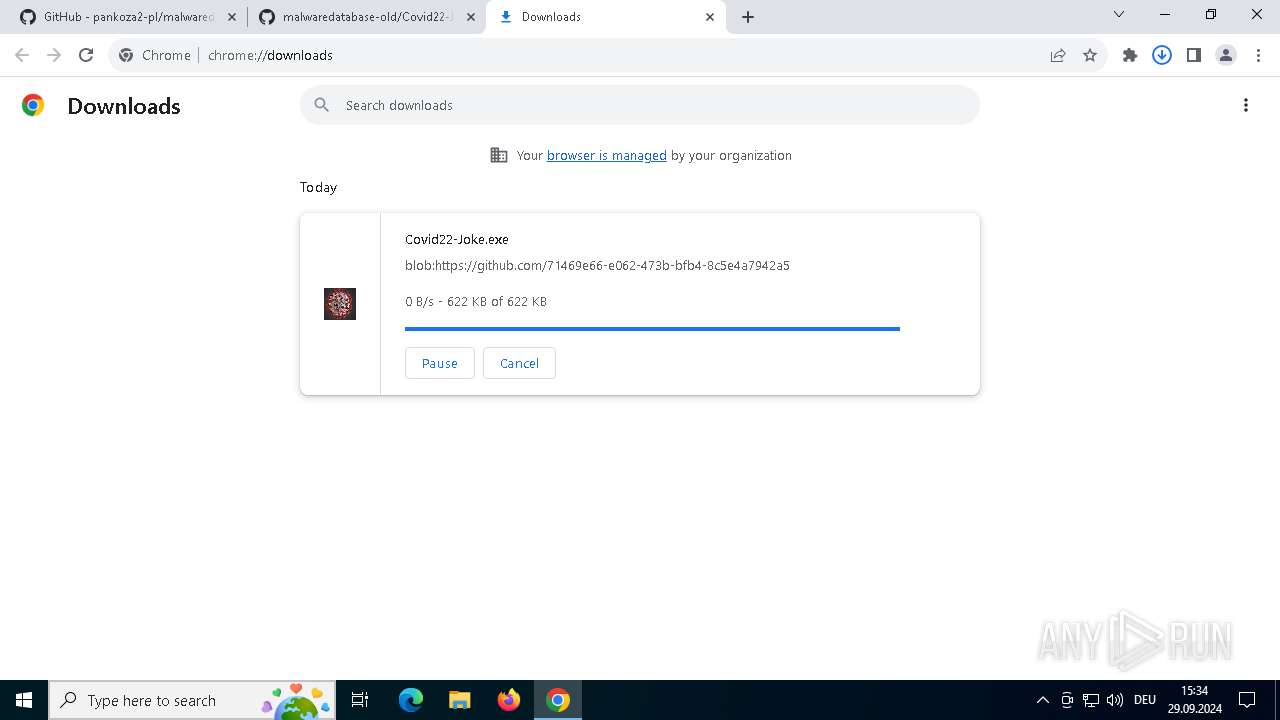
Drops a (possible) Coronavirus decoy
- Covid22-Joke.exe (PID: 6056)
- chrome.exe (PID: 832)
- cmd.exe (PID: 5288)
Application launched itself
- chrome.exe (PID: 832)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
145
Monitored processes
33
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=1816 --field-trial-handle=1852,i,5293028682152489788,18420359686507707971,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 492 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\EBA5.tmp\lole.vbs" | C:\Windows\SysWOW64\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 832 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://github.com/pankoza-pl/malwaredatabase/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --extension-process --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=3428 --field-trial-handle=1852,i,5293028682152489788,18420359686507707971,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 908 | timeout 5 /nobreak | C:\Windows\SysWOW64\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1072 | Inv.exe | C:\Users\admin\AppData\Local\Temp\EBA5.tmp\inv.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 1076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --mojo-platform-channel-handle=5236 --field-trial-handle=1852,i,5293028682152489788,18420359686507707971,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1184 | timeout 2 /nobreak | C:\Windows\SysWOW64\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1308 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | IconSpam.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1944 | clwcp c:\c22joke\covid.jpg | C:\Users\admin\AppData\Local\Temp\EBA5.tmp\CLWCP.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
4 829
Read events
4 822
Write events
7
Delete events
0
Modification events
| (PID) Process: | (832) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (832) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (832) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (832) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (832) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (5728) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 01000000000000002F75914B7412DB01 | |||
| (PID) Process: | (5288) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.vbs\OpenWithProgids |
| Operation: | write | Name: | VBSFile |
Value: | |||
Executable files
10
Suspicious files
42
Text files
24
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF3f7452.TMP | — | |
MD5:— | SHA256:— | |||
| 832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF3f7481.TMP | — | |
MD5:— | SHA256:— | |||
| 832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF3f7481.TMP | — | |
MD5:— | SHA256:— | |||
| 832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF3f7481.TMP | — | |
MD5:— | SHA256:— | |||
| 832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF3f7481.TMP | — | |
MD5:— | SHA256:— | |||
| 832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
280
TCP/UDP connections
68
DNS requests
34
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 301 | 140.82.121.4:443 | https://github.com/pankoza-pl/malwaredatabase/ | unknown | — | — | unknown |
3916 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 142.250.110.84:443 | https://accounts.google.com/ListAccounts?gpsia=1&source=ChromiumBrowser&json=standard | unknown | — | — | whitelisted |
— | — | GET | 200 | 185.199.108.154:443 | https://github.githubassets.com/assets/vendors-node_modules_oddbird_popover-polyfill_dist_popover_js-56729c905fe2.js | unknown | text | 9.38 Kb | whitelisted |
— | — | GET | 200 | 140.82.121.4:443 | https://github.com/pankoza2-pl/malwaredatabase-old | unknown | html | 493 Kb | shared |
— | — | GET | 200 | 185.199.108.154:443 | https://github.githubassets.com/assets/light-3e154969b9f9.css | unknown | text | 48.9 Kb | whitelisted |
— | — | GET | 200 | 185.199.108.154:443 | https://github.githubassets.com/assets/dark-9c5b7a476542.css | unknown | text | 48.9 Kb | whitelisted |
— | — | GET | 200 | 185.199.108.154:443 | https://github.githubassets.com/assets/github-6da540aa3f84.css | unknown | text | 125 Kb | whitelisted |
— | — | GET | 200 | 185.199.111.154:443 | https://github.githubassets.com/assets/primer-react-css.8879c83c1311e6328466.module.css | unknown | text | 29.7 Kb | whitelisted |
— | — | GET | 200 | 185.199.109.154:443 | https://github.githubassets.com/assets/primer-fefb1a332c28.css | unknown | text | 332 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3916 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
832 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
132 | chrome.exe | 140.82.121.4:443 | github.com | GITHUB | US | shared |
132 | chrome.exe | 142.250.110.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
132 | chrome.exe | 185.199.111.154:443 | github.githubassets.com | FASTLY | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
github.com |
| shared |
accounts.google.com |
| whitelisted |
github.githubassets.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| shared |
user-images.githubusercontent.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET HUNTING Suspicious GET Request with Possible COVID-19 URI M1 |
— | — | Potentially Bad Traffic | ET HUNTING Suspicious GET Request with Possible COVID-19 URI M1 |
— | — | Potentially Bad Traffic | ET HUNTING Suspicious GET Request with Possible COVID-19 URI M1 |
132 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
132 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
— | — | Potentially Bad Traffic | ET HUNTING Suspicious GET Request with Possible COVID-19 URI M1 |
— | — | Potentially Bad Traffic | ET HUNTING Suspicious GET Request with Possible COVID-19 URI M1 |
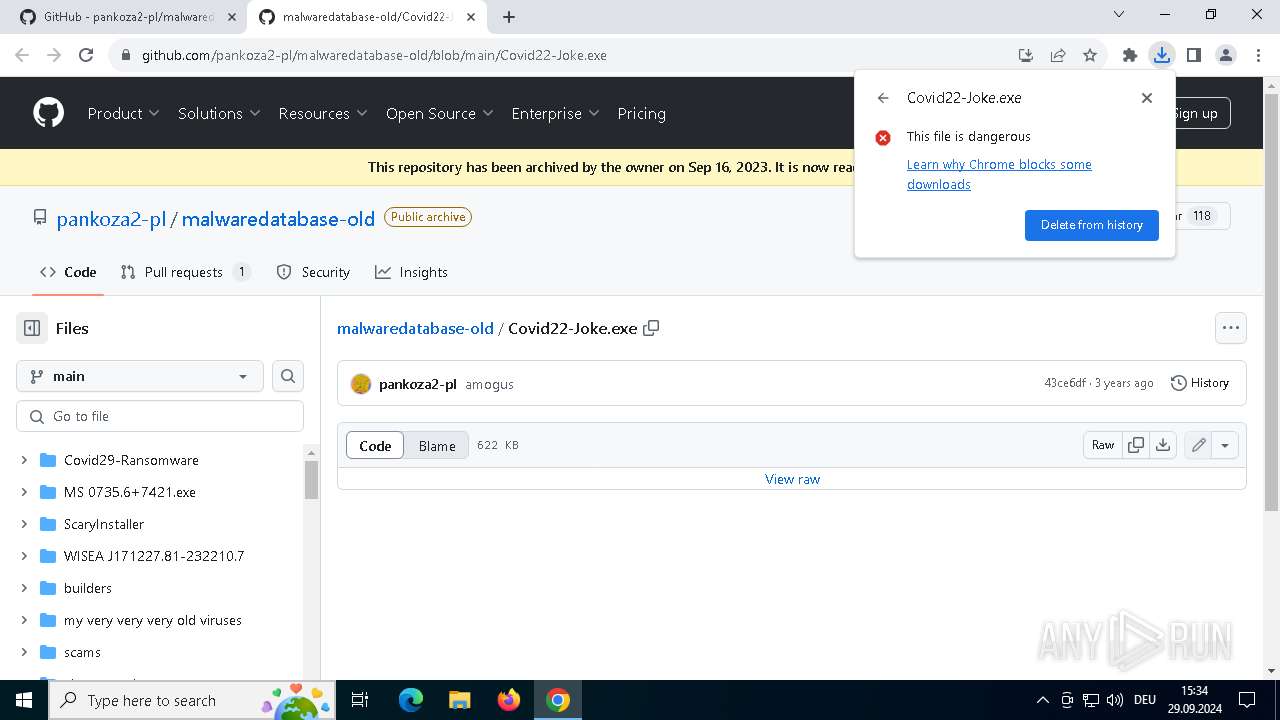
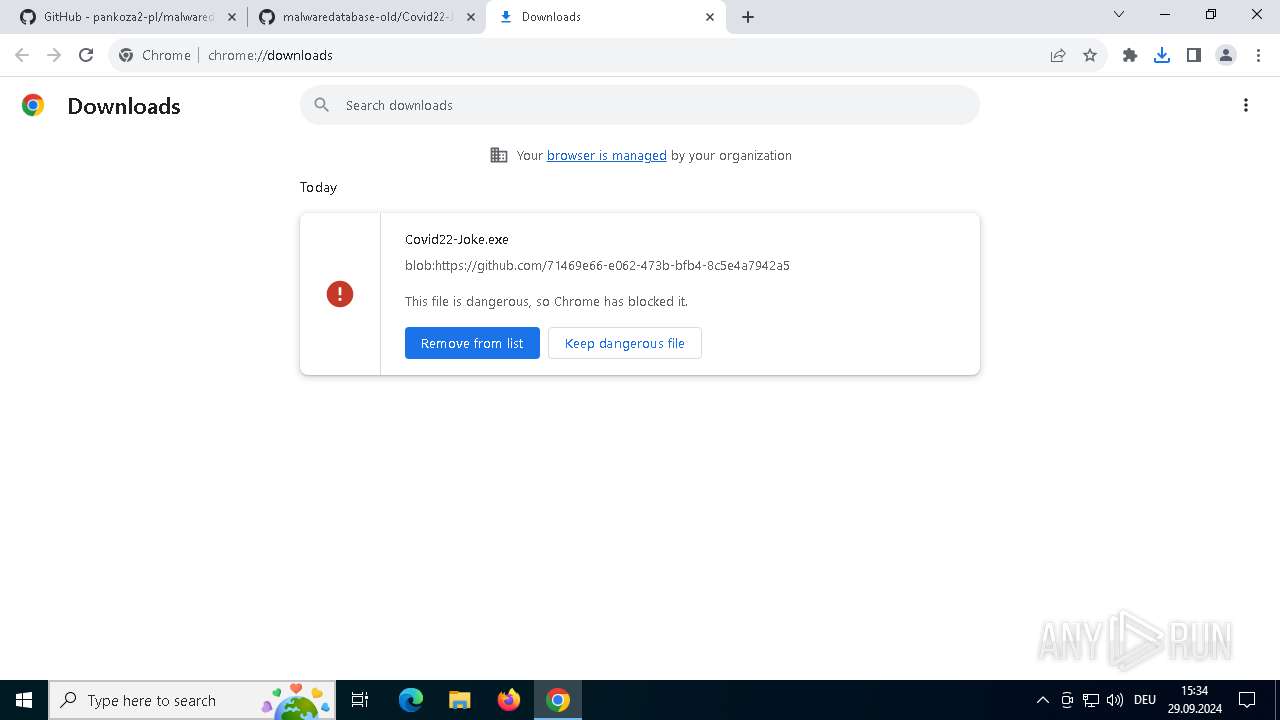
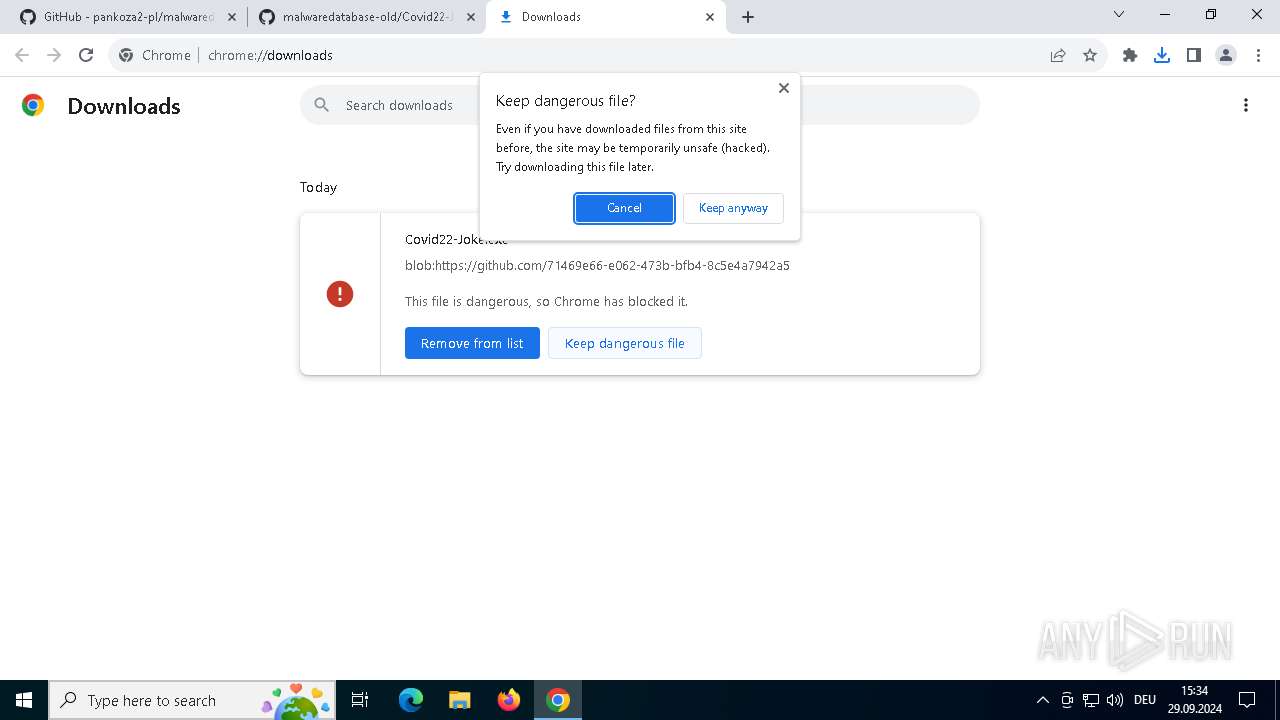
— | — | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
— | — | Misc activity | ET HUNTING EXE Downloaded from Github |