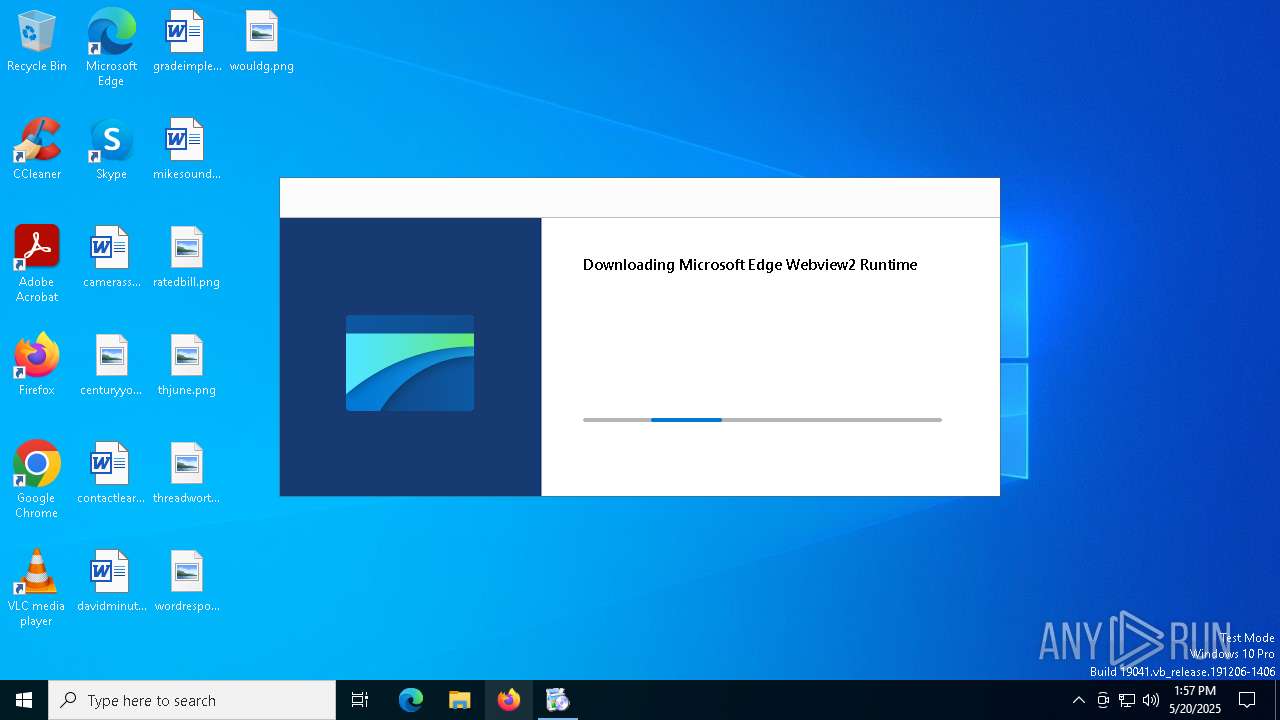
| File name: | Client++ Pico.exe |
| Full analysis: | https://app.any.run/tasks/c021dbab-f305-41ae-9a4a-9585b1454d62 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2025, 13:56:43 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 2374A67E47146212459246AF223419FF |
| SHA1: | D13835A0F493184FB08545F76FF266116F8F89DF |
| SHA256: | A4FE40CEFFD45CEFA9683445DE0C752742A7796CD8A2A1202AFA0FF2AC574CB0 |
| SSDEEP: | 98304:2FgYm6EsS0IQWf17VXXj79wp0zL5f+KWKg/x9myYJDzmCfaIsXtNj73qN6V1hfDo:zvHre+gB3wUCP |
MALICIOUS
Changes the autorun value in the registry
- MicrosoftEdgeUpdate.exe (PID: 3020)
SUSPICIOUS
Reads security settings of Internet Explorer
- Client++ Pico.exe (PID: 2568)
- MicrosoftEdgeUpdate.exe (PID: 3020)
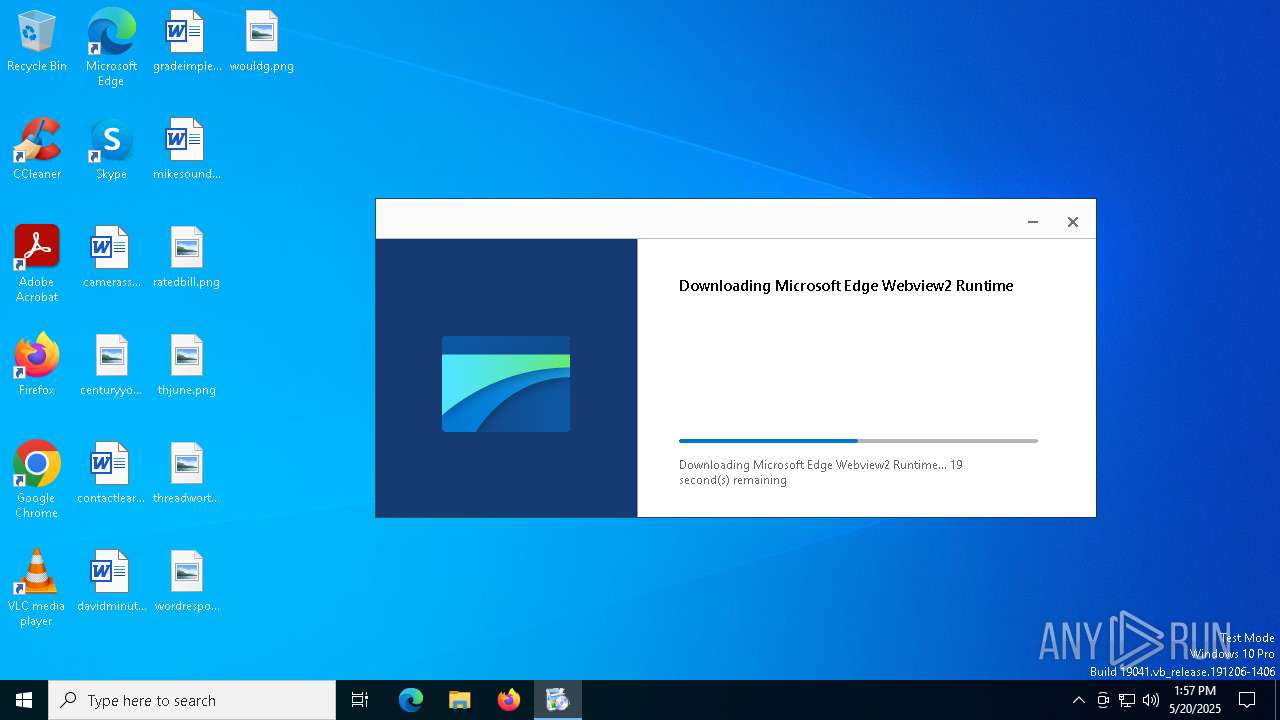
Executable content was dropped or overwritten
- Client++ Pico.exe (PID: 2568)
- MicrosoftEdgeWebview2Setup.exe (PID: 5428)
- MicrosoftEdgeUpdate.exe (PID: 3020)
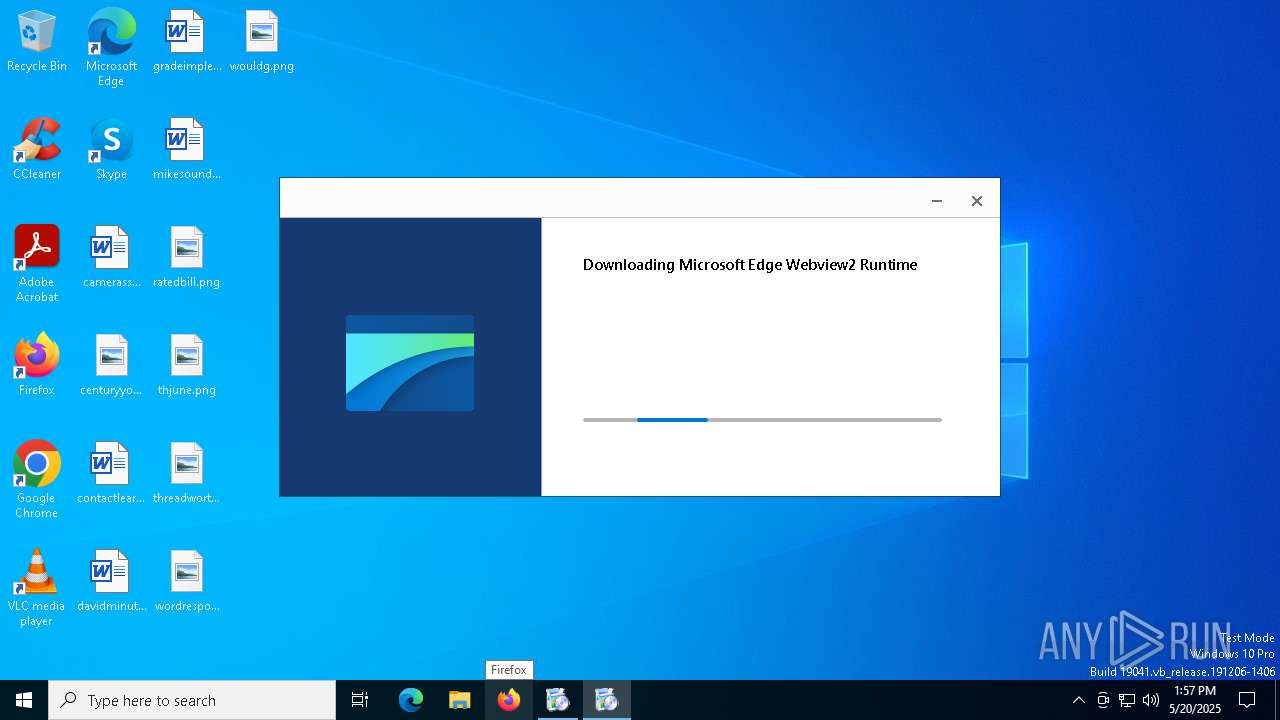
Starts a Microsoft application from unusual location
- MicrosoftEdgeWebview2Setup.exe (PID: 5428)
- MicrosoftEdgeUpdate.exe (PID: 3020)
Process drops legitimate windows executable
- MicrosoftEdgeWebview2Setup.exe (PID: 5428)
- Client++ Pico.exe (PID: 2568)
- MicrosoftEdgeUpdate.exe (PID: 3020)
Creates/Modifies COM task schedule object
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 5512)
- MicrosoftEdgeUpdate.exe (PID: 4488)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 1628)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 2108)
Starts itself from another location
- MicrosoftEdgeUpdate.exe (PID: 3020)
INFO
Checks supported languages
- Client++ Pico.exe (PID: 2568)
- MicrosoftEdgeWebview2Setup.exe (PID: 5428)
- MicrosoftEdgeUpdate.exe (PID: 3020)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 5512)
- MicrosoftEdgeUpdate.exe (PID: 4488)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 2108)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 1628)
- MicrosoftEdgeUpdate.exe (PID: 6816)
- MicrosoftEdgeUpdate.exe (PID: 3332)
- MicrosoftEdgeUpdate.exe (PID: 6676)
Reads the machine GUID from the registry
- Client++ Pico.exe (PID: 2568)
Reads the software policy settings
- Client++ Pico.exe (PID: 2568)
- MicrosoftEdgeUpdate.exe (PID: 6816)
- MicrosoftEdgeUpdate.exe (PID: 6676)
Reads the computer name
- Client++ Pico.exe (PID: 2568)
- MicrosoftEdgeUpdate.exe (PID: 3020)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 2108)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 5512)
- MicrosoftEdgeUpdate.exe (PID: 4488)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 1628)
- MicrosoftEdgeUpdate.exe (PID: 6816)
- MicrosoftEdgeUpdate.exe (PID: 3332)
- MicrosoftEdgeUpdate.exe (PID: 6676)
Application based on Rust
- Client++ Pico.exe (PID: 2568)
The sample compiled with english language support
- MicrosoftEdgeWebview2Setup.exe (PID: 5428)
- Client++ Pico.exe (PID: 2568)
- MicrosoftEdgeUpdate.exe (PID: 3020)
Create files in a temporary directory
- MicrosoftEdgeWebview2Setup.exe (PID: 5428)
- Client++ Pico.exe (PID: 2568)
- MicrosoftEdgeUpdate.exe (PID: 3020)
Creates files or folders in the user directory
- MicrosoftEdgeUpdate.exe (PID: 3020)
- MicrosoftEdgeUpdate.exe (PID: 6676)
Checks proxy server information
- MicrosoftEdgeUpdate.exe (PID: 6816)
- MicrosoftEdgeUpdate.exe (PID: 6676)
- Client++ Pico.exe (PID: 2568)
Process checks computer location settings
- MicrosoftEdgeUpdate.exe (PID: 3020)
Reads Environment values
- MicrosoftEdgeUpdate.exe (PID: 6816)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
139
Monitored processes
12
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 896 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1616 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1628 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.185.21\MicrosoftEdgeUpdateComRegisterShell64.exe" /user | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.185.21\MicrosoftEdgeUpdateComRegisterShell64.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update COM Registration Helper Exit code: 0 Version: 1.3.185.21 Modules
| |||||||||||||||
| 2108 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.185.21\MicrosoftEdgeUpdateComRegisterShell64.exe" /user | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.185.21\MicrosoftEdgeUpdateComRegisterShell64.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update COM Registration Helper Exit code: 0 Version: 1.3.185.21 Modules
| |||||||||||||||
| 2568 | "C:\Users\admin\AppData\Local\Temp\Client++ Pico.exe" | C:\Users\admin\AppData\Local\Temp\Client++ Pico.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
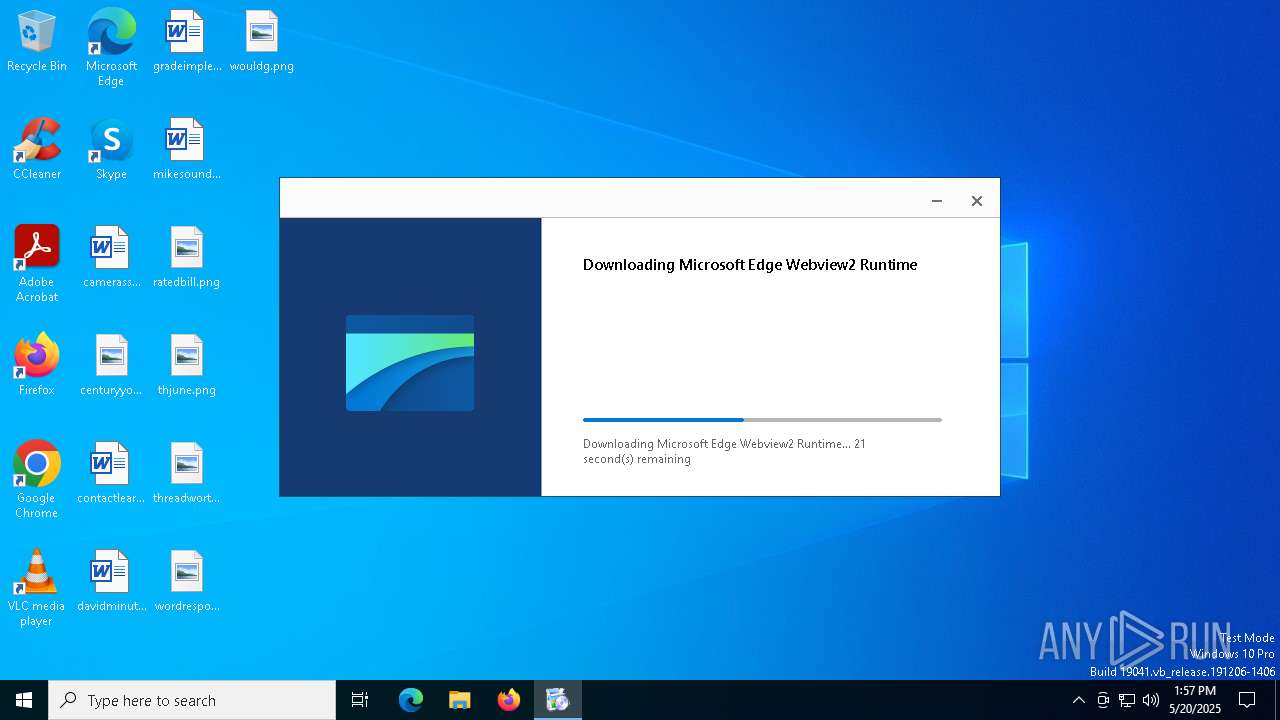
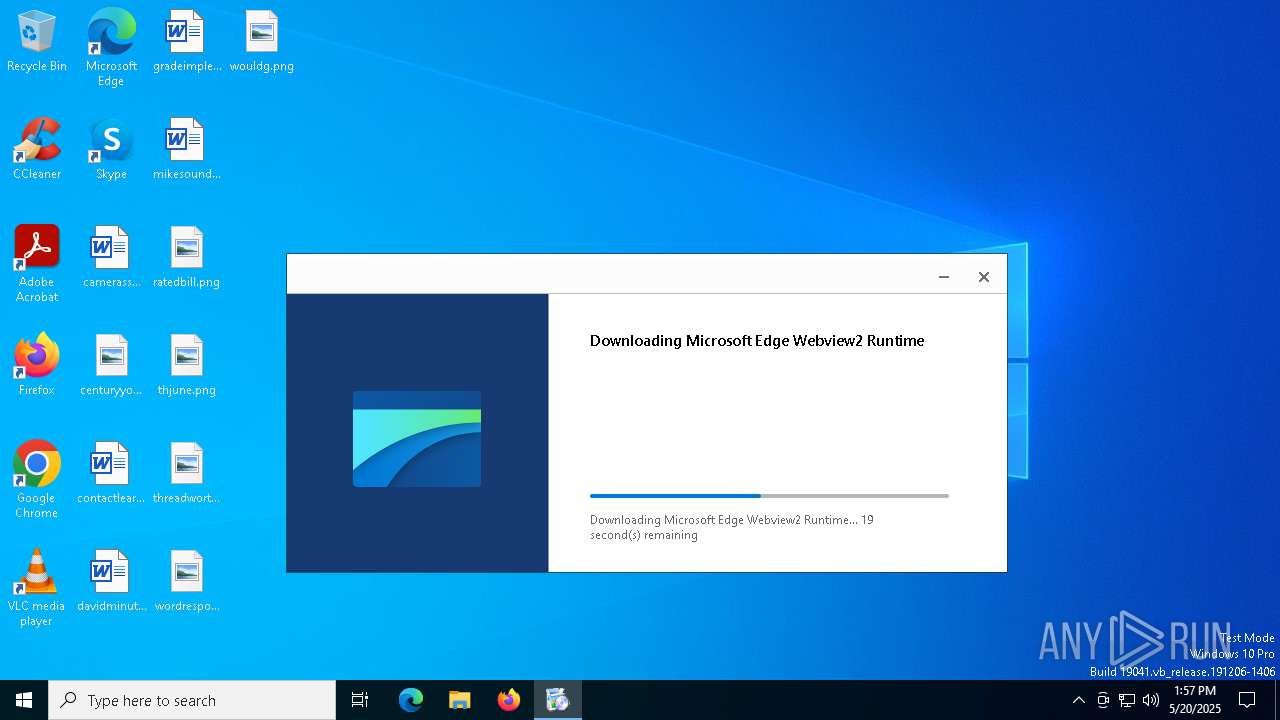
| 3020 | C:\Users\admin\AppData\Local\Temp\EUF222.tmp\MicrosoftEdgeUpdate.exe /installsource taggedmi /install "appguid={F3017226-FE2A-4295-8BDF-00C3A9A7E4C5}&appname=Microsoft%20Edge%20Webview2%20Runtime&needsadmin=prefers" | C:\Users\admin\AppData\Local\Temp\EUF222.tmp\MicrosoftEdgeUpdate.exe | MicrosoftEdgeWebview2Setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Version: 1.3.185.21 Modules
| |||||||||||||||
| 3332 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /handoff "appguid={F3017226-FE2A-4295-8BDF-00C3A9A7E4C5}&appname=Microsoft%20Edge%20Webview2%20Runtime&needsadmin=false" /installsource taggedmi /sessionid "{27EF111A-2271-4270-B74B-23DBA1764A0A}" | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Version: 1.3.185.21 Modules
| |||||||||||||||
| 4488 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /regserver | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Exit code: 0 Version: 1.3.185.21 Modules
| |||||||||||||||
| 5428 | C:\Users\admin\AppData\Local\Temp\\MicrosoftEdgeWebview2Setup.exe | C:\Users\admin\AppData\Local\Temp\MicrosoftEdgeWebview2Setup.exe | Client++ Pico.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Setup Version: 1.3.185.21 Modules
| |||||||||||||||
| 5512 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.185.21\MicrosoftEdgeUpdateComRegisterShell64.exe" /user | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.185.21\MicrosoftEdgeUpdateComRegisterShell64.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update COM Registration Helper Exit code: 0 Version: 1.3.185.21 Modules
| |||||||||||||||
Total events
6 976
Read events
5 749
Write events
1 193
Delete events
34
Modification events
| (PID) Process: | (3020) MicrosoftEdgeUpdate.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate |
| Operation: | delete value | Name: | eulaaccepted |
Value: | |||
| (PID) Process: | (3020) MicrosoftEdgeUpdate.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate |
| Operation: | write | Name: | path |
Value: C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | |||
| (PID) Process: | (3020) MicrosoftEdgeUpdate.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate |
| Operation: | write | Name: | UninstallCmdLine |
Value: "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /uninstall | |||
| (PID) Process: | (3020) MicrosoftEdgeUpdate.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{F3C4FE00-EFD5-403B-9569-398A20F1BA4A} |
| Operation: | write | Name: | pv |
Value: 1.3.185.21 | |||
| (PID) Process: | (3020) MicrosoftEdgeUpdate.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{F3C4FE00-EFD5-403B-9569-398A20F1BA4A} |
| Operation: | write | Name: | name |
Value: Microsoft Edge Update | |||
| (PID) Process: | (3020) MicrosoftEdgeUpdate.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{F3C4FE00-EFD5-403B-9569-398A20F1BA4A} |
| Operation: | write | Name: | pv |
Value: 1.3.185.21 | |||
| (PID) Process: | (3020) MicrosoftEdgeUpdate.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Microsoft Edge Update |
Value: "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.185.21\MicrosoftEdgeUpdateCore.exe" | |||
| (PID) Process: | (5512) MicrosoftEdgeUpdateComRegisterShell64.exe | Key: | HKEY_CLASSES_ROOT\CLSID\{81093D63-7825-417B-BFC8-ADC63FA4E53D}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (5512) MicrosoftEdgeUpdateComRegisterShell64.exe | Key: | HKEY_CLASSES_ROOT\CLSID\{5EA43877-C6D8-4885-B77A-C0BB27E94372}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (5512) MicrosoftEdgeUpdateComRegisterShell64.exe | Key: | HKEY_CLASSES_ROOT\CLSID\{AF41D186-598E-49DD-A801-1B87D2F8941A}\InprocHandler32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
Executable files
202
Suspicious files
2
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5428 | MicrosoftEdgeWebview2Setup.exe | C:\Users\admin\AppData\Local\Temp\EUF222.tmp\MicrosoftEdgeUpdate.exe | executable | |
MD5:31F9E08922765BA2913632F758BC7423 | SHA256:C2988C13F66CE033FEF65F3AF20A00FAF555047E710DC6C282C124C848C1EB88 | |||
| 5428 | MicrosoftEdgeWebview2Setup.exe | C:\Users\admin\AppData\Local\Temp\EUF222.tmp\msedgeupdate.dll | executable | |
MD5:9CB2B82FBDDE7133369F0D8618DBA139 | SHA256:0AA838B27DA61C7BD94E073B35CB5CF1CF0762D74CCC0214D052F7327D52AE06 | |||
| 5428 | MicrosoftEdgeWebview2Setup.exe | C:\Users\admin\AppData\Local\Temp\EUF222.tmp\psmachine.dll | executable | |
MD5:E454864035FEBE2CDD04685BDE98228E | SHA256:D441F6E6862E2AF4799AD29960F7D952FF73FED68AC579D314199C076D8B7D0B | |||
| 5428 | MicrosoftEdgeWebview2Setup.exe | C:\Users\admin\AppData\Local\Temp\EUF222.tmp\psuser_arm64.dll | executable | |
MD5:C396428DC5A13FC440A5A87FDC8DD795 | SHA256:7FFD4F9B5E8060A08BEC64316462271CC9F5FC88D715140EF9946BA1C7AAE845 | |||
| 5428 | MicrosoftEdgeWebview2Setup.exe | C:\Users\admin\AppData\Local\Temp\EUF222.tmp\MicrosoftEdgeComRegisterShellARM64.exe | executable | |
MD5:433681CA511D96F96479AC2CCA102522 | SHA256:DA5F97895EFB9698657EA213E6D0CAB53FFE6BEE32933CA2341406FAF64DFCBC | |||
| 5428 | MicrosoftEdgeWebview2Setup.exe | C:\Users\admin\AppData\Local\Temp\EUF222.tmp\MicrosoftEdgeUpdateBroker.exe | executable | |
MD5:0ED41F5910128213C23EDC35DB3D46D3 | SHA256:EF7E0E4E9CBD804356C897156436EF50C5F3F7C3D223E412CC1F66315CC36D6A | |||
| 5428 | MicrosoftEdgeWebview2Setup.exe | C:\Users\admin\AppData\Local\Temp\EUF222.tmp\psmachine_64.dll | executable | |
MD5:988956F643A289B4C49B8896C890630F | SHA256:09289D824808C218E23D12AD9519FFE388F4660EC96CB50DAF233FAA0D1BA12A | |||
| 5428 | MicrosoftEdgeWebview2Setup.exe | C:\Users\admin\AppData\Local\Temp\EUF222.tmp\psuser.dll | executable | |
MD5:CBEE286B03D265CEFB8426990DB933C6 | SHA256:0430814EB5CCEF382A92CE99F1DEA7B5C3A4E7B7476A6198FD4F764B609F7131 | |||
| 5428 | MicrosoftEdgeWebview2Setup.exe | C:\Users\admin\AppData\Local\Temp\EUF222.tmp\EdgeUpdate.dat | binary | |
MD5:369BBC37CFF290ADB8963DC5E518B9B8 | SHA256:3D7EC761BEF1B1AF418B909F1C81CE577C769722957713FDAFBC8131B0A0C7D3 | |||
| 5428 | MicrosoftEdgeWebview2Setup.exe | C:\Users\admin\AppData\Local\Temp\EUF222.tmp\MicrosoftEdgeUpdateCore.exe | executable | |
MD5:F5E9477194D0D7C18A7C3529A10F917C | SHA256:F5C45634EFA29ACB9DBD1F16880737797171630C3F81FE23AEA26F4DFB094323 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
24
DNS requests
16
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5964 | svchost.exe | GET | — | 23.48.23.66:80 | http://msedge.f.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/6eb5dca7-2768-4016-8dbe-9762e2b79397?P1=1748354228&P2=404&P3=2&P4=NvNrDZJAZFh6NRJvmhPK36IGHQoWtpe0SqPwJiQOpjKJURHOACRaLn%2fjs2xuqVO7RPzyM53fIVJFFjv3K5VOPg%3d%3d | unknown | — | — | whitelisted |
5964 | svchost.exe | HEAD | 200 | 23.48.23.66:80 | http://msedge.f.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/6eb5dca7-2768-4016-8dbe-9762e2b79397?P1=1748354228&P2=404&P3=2&P4=NvNrDZJAZFh6NRJvmhPK36IGHQoWtpe0SqPwJiQOpjKJURHOACRaLn%2fjs2xuqVO7RPzyM53fIVJFFjv3K5VOPg%3d%3d | unknown | — | — | whitelisted |
1272 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1272 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2568 | Client++ Pico.exe | 144.6.249.106:443 | files.cuffuffles.dev | The University of Tasmania | AU | unknown |
6544 | svchost.exe | 40.126.32.136:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
files.cuffuffles.dev |
| unknown |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
msedge.api.cdp.microsoft.com |
| whitelisted |
msedge.f.tlu.dl.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5964 | svchost.exe | Misc activity | ET INFO Packed Executable Download |