| File name: | newactive.exe |
| Full analysis: | https://app.any.run/tasks/eee3d900-de19-4bae-b879-9aad5d5ed312 |
| Verdict: | Malicious activity |
| Analysis date: | May 24, 2019, 06:57:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 448891A1FB179982E4A1CFF20F6EDF9F |
| SHA1: | D046849D7139E2CFA4B6A08B96B644BF8F29E8AC |
| SHA256: | A4F45C61130575E558842EAB6B4E20B81DFA2CC155E07E9B7DD165D57F644F52 |
| SSDEEP: | 98304:O06FOznLo0+Dd6uxcm7Sk6RSYZhukINBipO2iERUKDJB:O3F6n80W6uGmv6j2+sERU0 |
MALICIOUS
Application was dropped or rewritten from another process
- irsetup.exe (PID: 968)
- uninstall.exe (PID: 3680)
- uninstall.exe (PID: 2772)
Registers / Runs the DLL via REGSVR32.EXE
- irsetup.exe (PID: 968)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 284)
- uninstall.exe (PID: 3680)
- irsetup.exe (PID: 968)
SUSPICIOUS
Executable content was dropped or overwritten
- irsetup.exe (PID: 968)
- newactive.exe (PID: 2660)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3388)
Removes files from Windows directory
- uninstall.exe (PID: 3680)
- irsetup.exe (PID: 968)
Starts CMD.EXE for commands execution
- irsetup.exe (PID: 968)
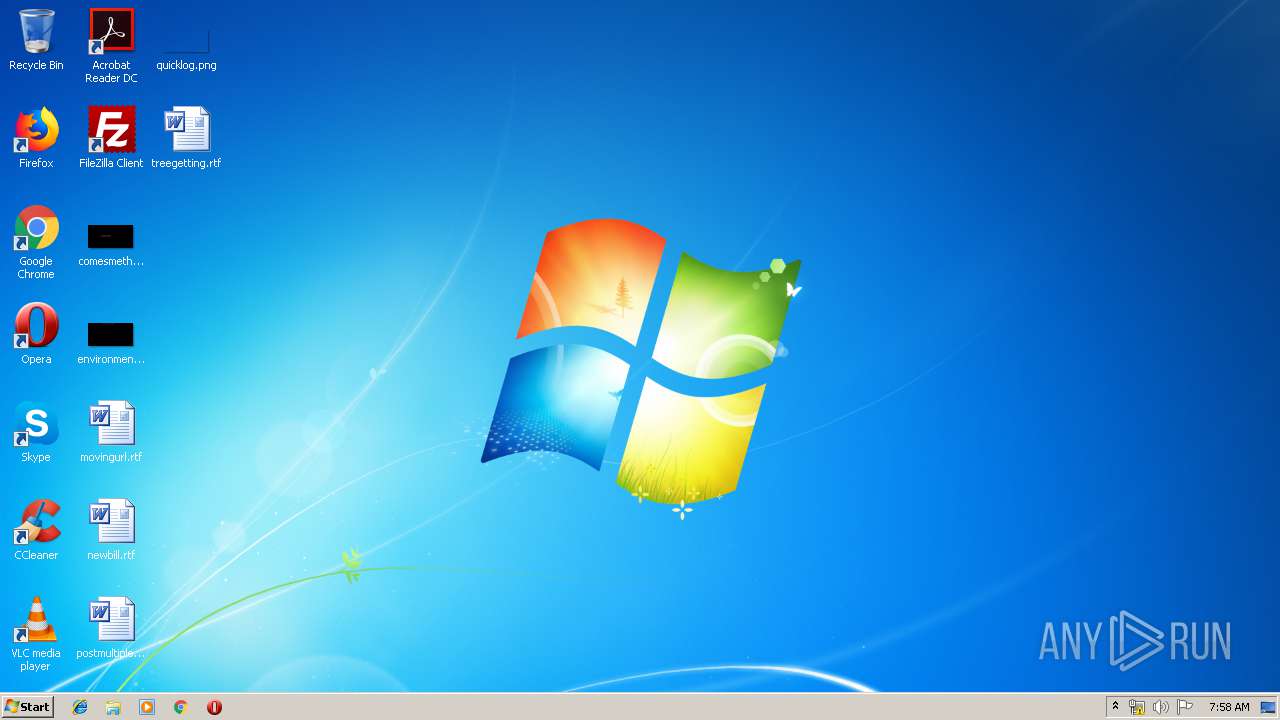
Creates files in the program directory
- irsetup.exe (PID: 968)
Creates files in the Windows directory
- irsetup.exe (PID: 968)
Creates files in the user directory
- irsetup.exe (PID: 968)
Creates a software uninstall entry
- irsetup.exe (PID: 968)
INFO
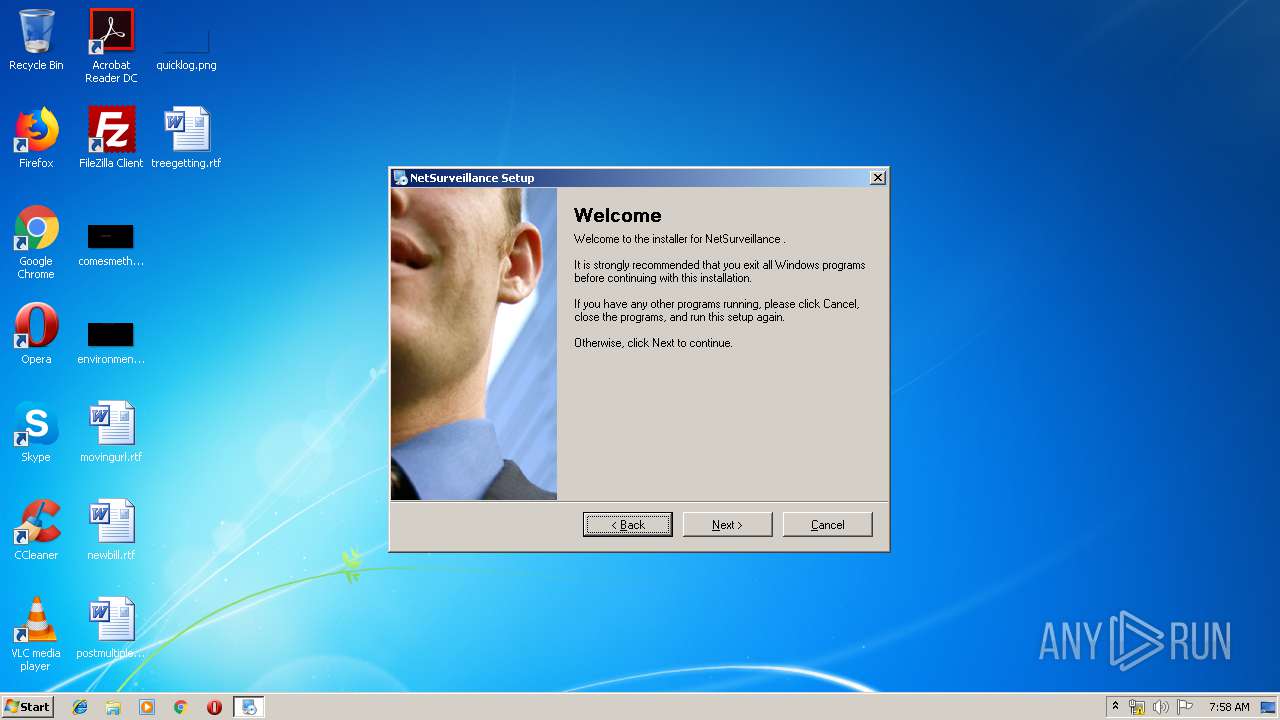
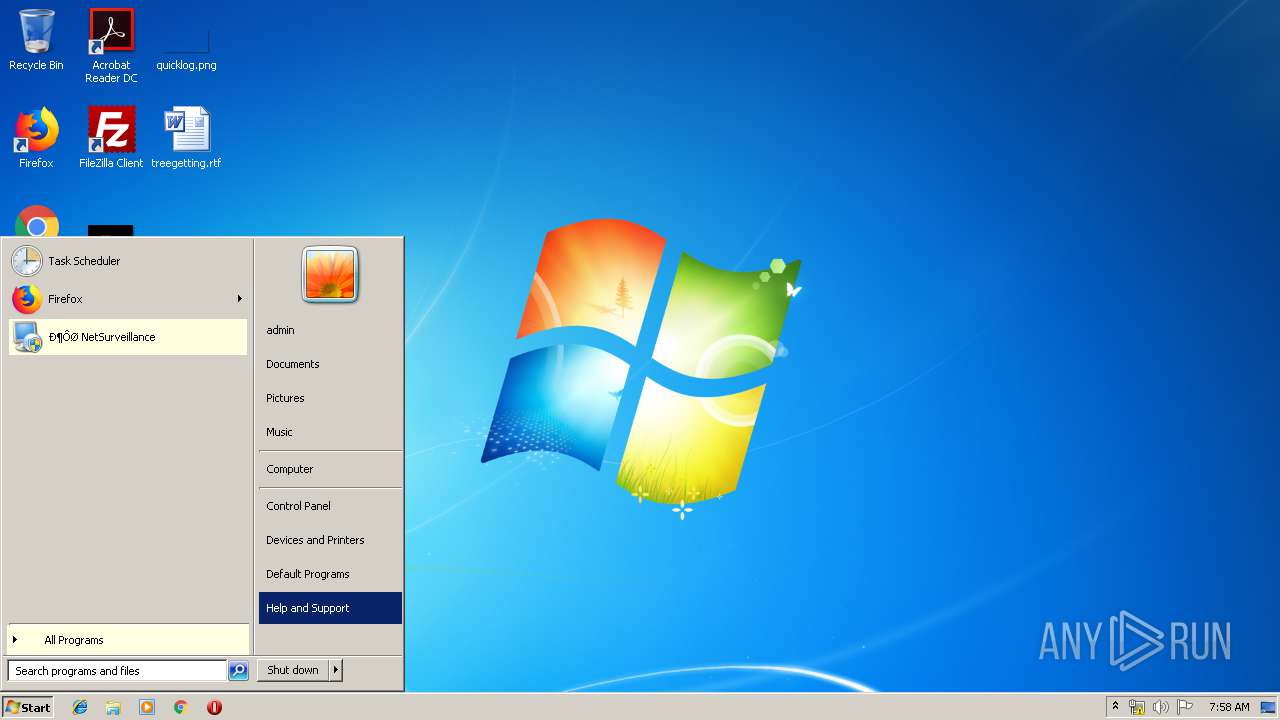
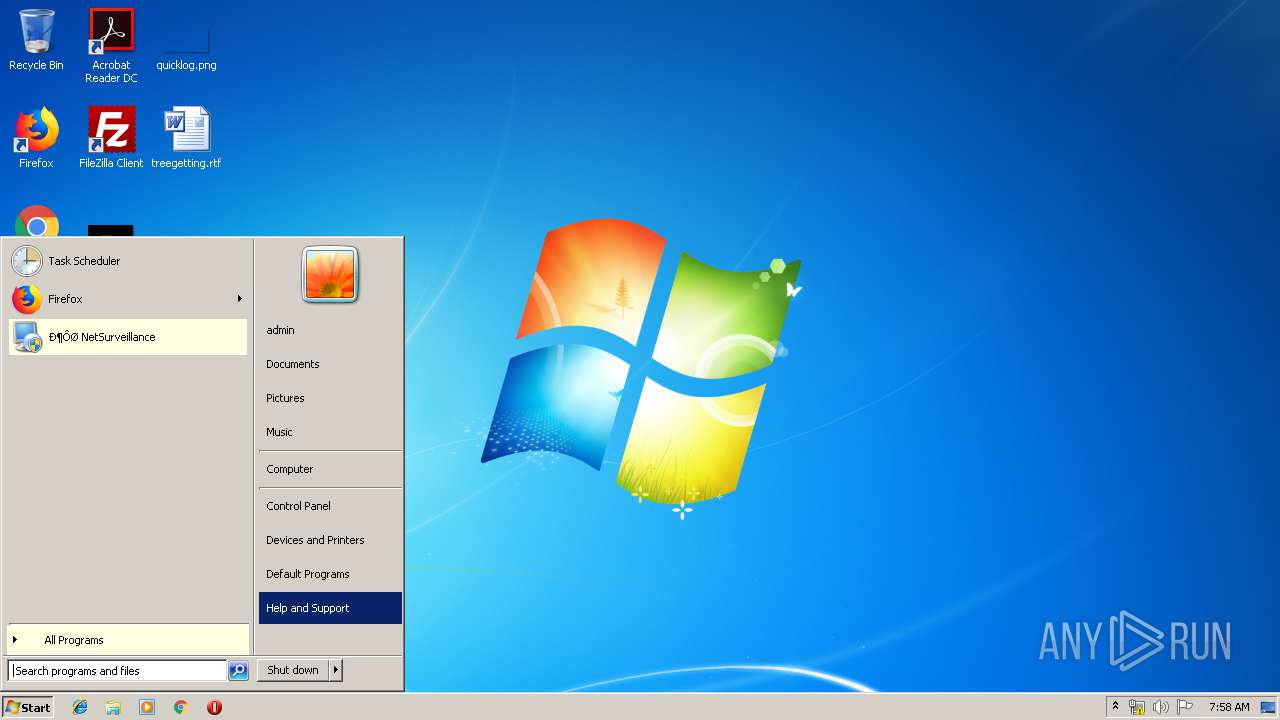
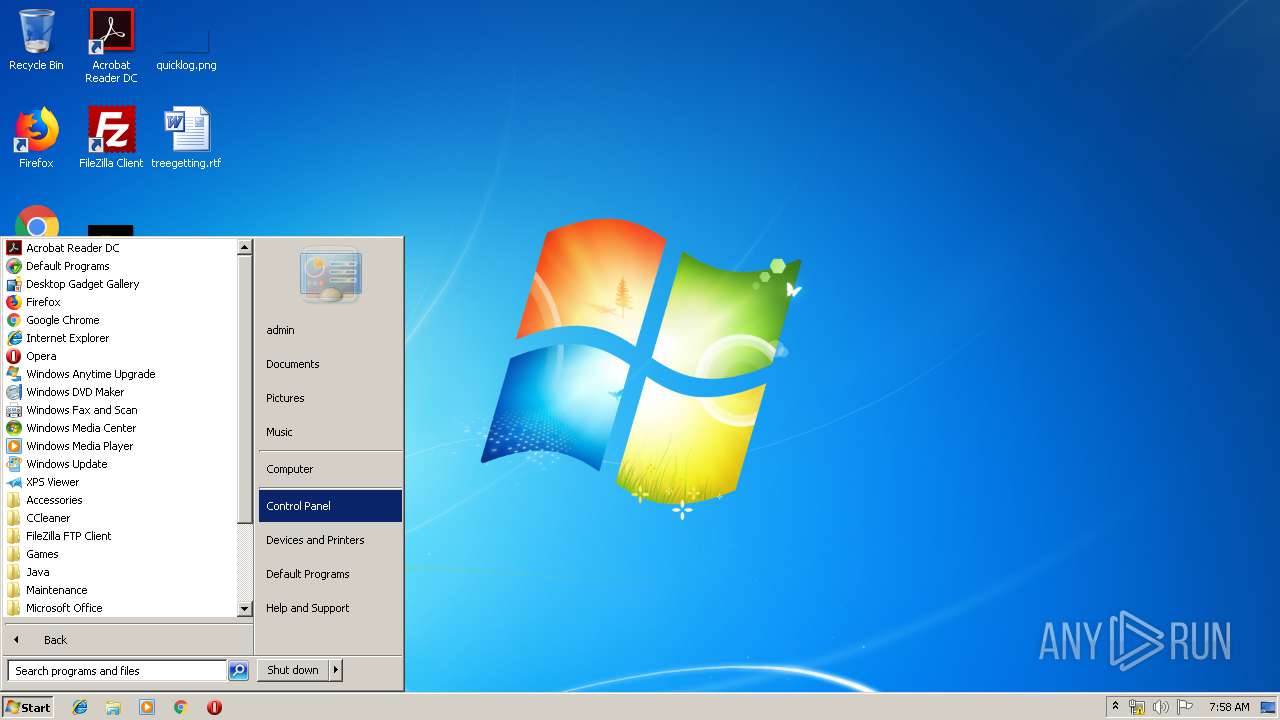
Manual execution by user
- uninstall.exe (PID: 3680)
- uninstall.exe (PID: 2772)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.8) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (36.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (9) |
| .exe | | | Win32 Executable (generic) (6.1) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:06:14 18:16:10+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 22528 |
| InitializedDataSize: | 48128 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x29e1 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 9.1.0.0 |
| ProductVersionNumber: | 9.1.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Private build |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | Created with Setup Factory |
| FileDescription: | Setup Application |
| FileVersion: | 9.1.0.0 |
| InternalName: | suf_launch |
| LegalCopyright: | Setup Engine Copyright © 2004-2012 Indigo Rose Corporation |
| LegalTrademarks: | Setup Factory is a trademark of Indigo Rose Corporation. |
| OriginalFileName: | suf_launch.exe |
| ProductName: | Setup Factory Runtime |
| ProductVersion: | 9.1.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Jun-2012 16:16:10 |
| Detected languages: |
|
| Comments: | Created with Setup Factory |
| FileDescription: | Setup Application |
| FileVersion: | 9.1.0.0 |
| InternalName: | suf_launch |
| LegalCopyright: | Setup Engine Copyright © 2004-2012 Indigo Rose Corporation |
| LegalTrademarks: | Setup Factory is a trademark of Indigo Rose Corporation. |
| OriginalFilename: | suf_launch.exe |
| ProductName: | Setup Factory Runtime |
| ProductVersion: | 9.1.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 14-Jun-2012 16:16:10 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005718 | 0x00005800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45945 |
.rdata | 0x00007000 | 0x00002E82 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.97533 |
.data | 0x0000A000 | 0x00001968 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.58663 |
.rsrc | 0x0000C000 | 0x00006DCC | 0x00006E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.82004 |
.reloc | 0x00013000 | 0x00001092 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 3.7122 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.31872 | 1232 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.31421 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.9477 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.78233 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 6.14953 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.83714 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 3.64397 | 1640 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 5.84115 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 5.41049 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
101 | 2.89097 | 132 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
Total processes
48
Monitored processes
11
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
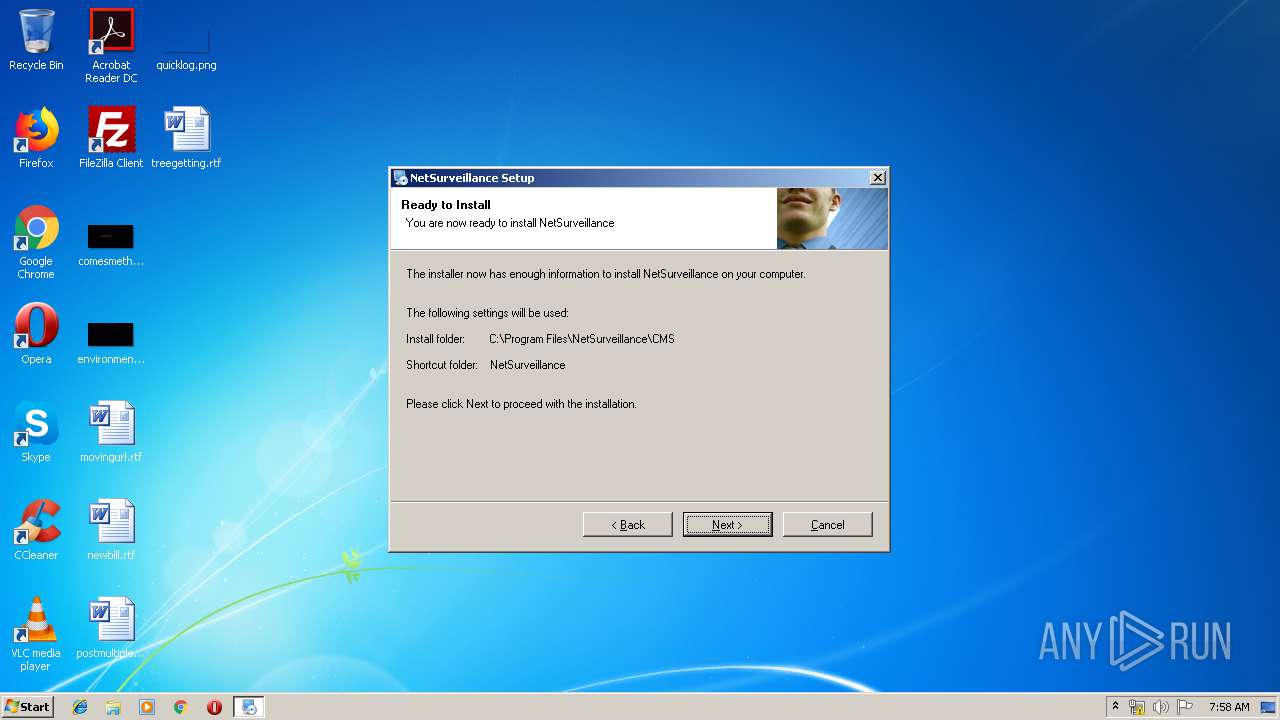
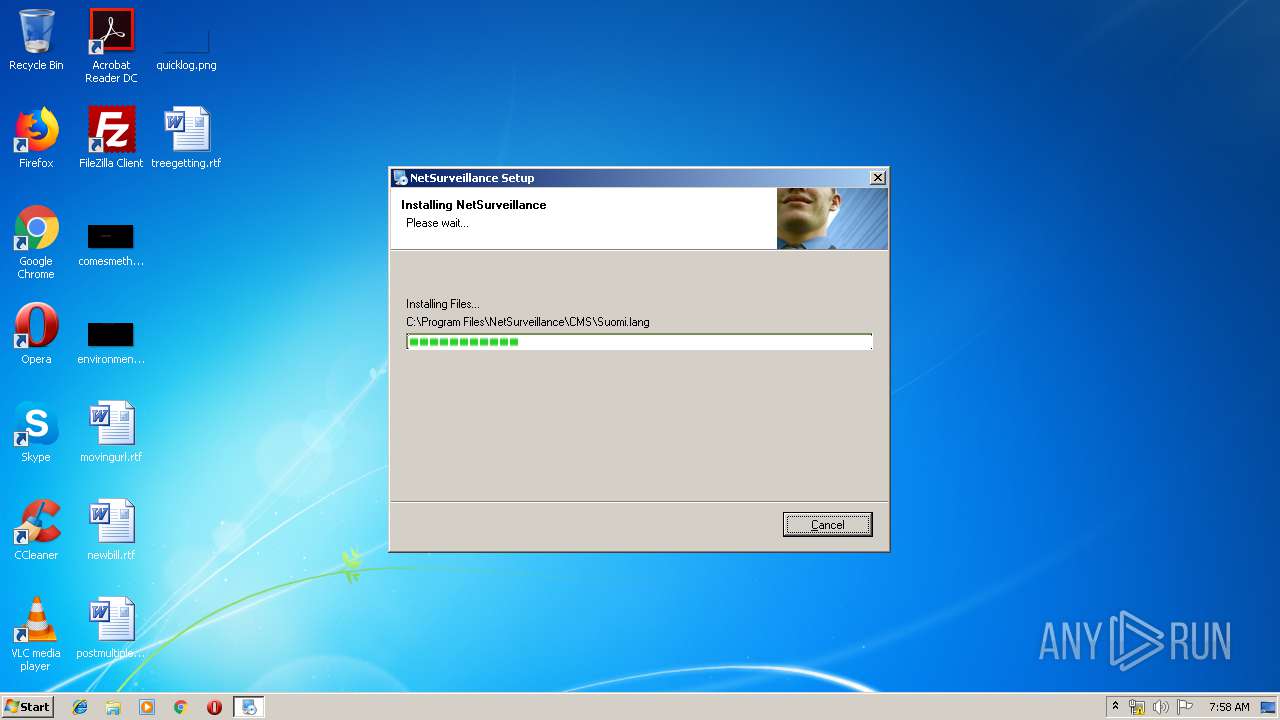
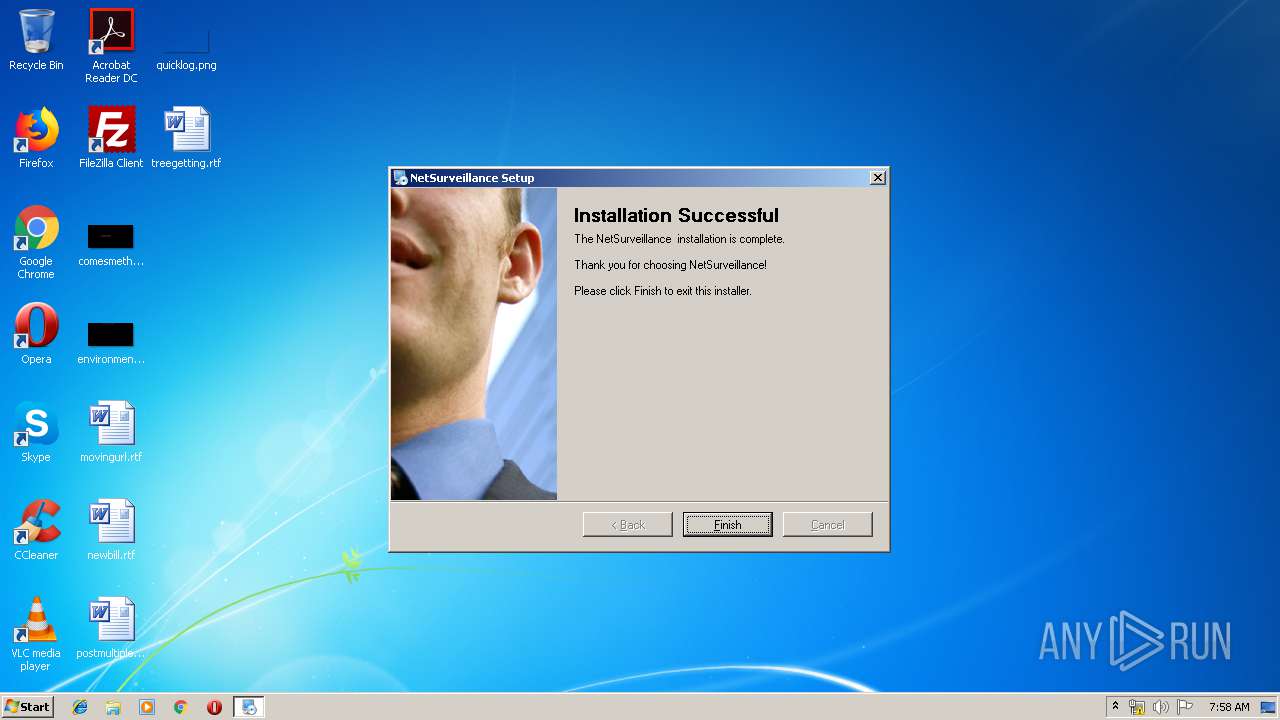
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | "C:\Windows\System32\regsvr32.exe" /s "C:\Program Files\NetSurveillance\CMS\web.ocx" | C:\Windows\System32\regsvr32.exe | — | irsetup.exe | |||||||||||
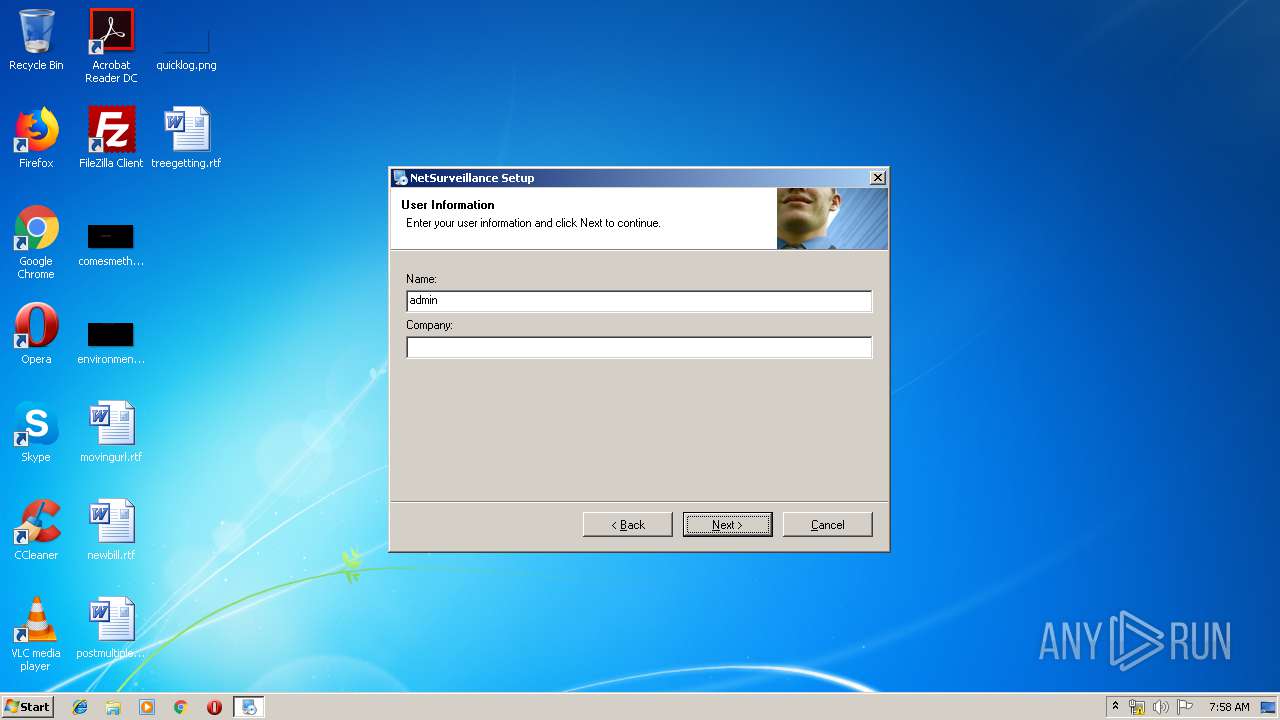
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 728 | "C:\Users\admin\AppData\Local\Temp\newactive.exe" | C:\Users\admin\AppData\Local\Temp\newactive.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup Application Exit code: 3221226540 Version: 9.1.0.0 Modules
| |||||||||||||||
| 968 | "C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\irsetup.exe" __IRAOFF:1742194 "__IRAFN:C:\Users\admin\AppData\Local\Temp\newactive.exe" "__IRCT:0" "__IRTSS:0" "__IRSID:S-1-5-21-1302019708-1500728564-335382590-1000" | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\irsetup.exe | newactive.exe | ||||||||||||
User: admin Company: Indigo Rose Corporation Integrity Level: HIGH Description: Setup Application Exit code: 0 Version: 9.1.0.0 Modules
| |||||||||||||||
| 1240 | reg add "HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\MozillaPlugins\JFWeb" /v Path /t REG_SZ /d "C:\Program Files\NetSurveillance\CMS\npWebPlugin.dll" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1904 | reg add "HKEY_LOCAL_MACHINE\SOFTWARE\MozillaPlugins\JFWeb" /v Path /t REG_SZ /d "C:\Program Files\NetSurveillance\CMS\npWebPlugin.dll" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2084 | reg add "HKEY_LOCAL_MACHINE\SOFTWARE\MozillaPlugins\JFGuide" /v Path /t REG_SZ /d "C:\Program Files\NetSurveillance\CMS\npGuide.dll" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2660 | "C:\Users\admin\AppData\Local\Temp\newactive.exe" | C:\Users\admin\AppData\Local\Temp\newactive.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup Application Exit code: 0 Version: 9.1.0.0 Modules
| |||||||||||||||
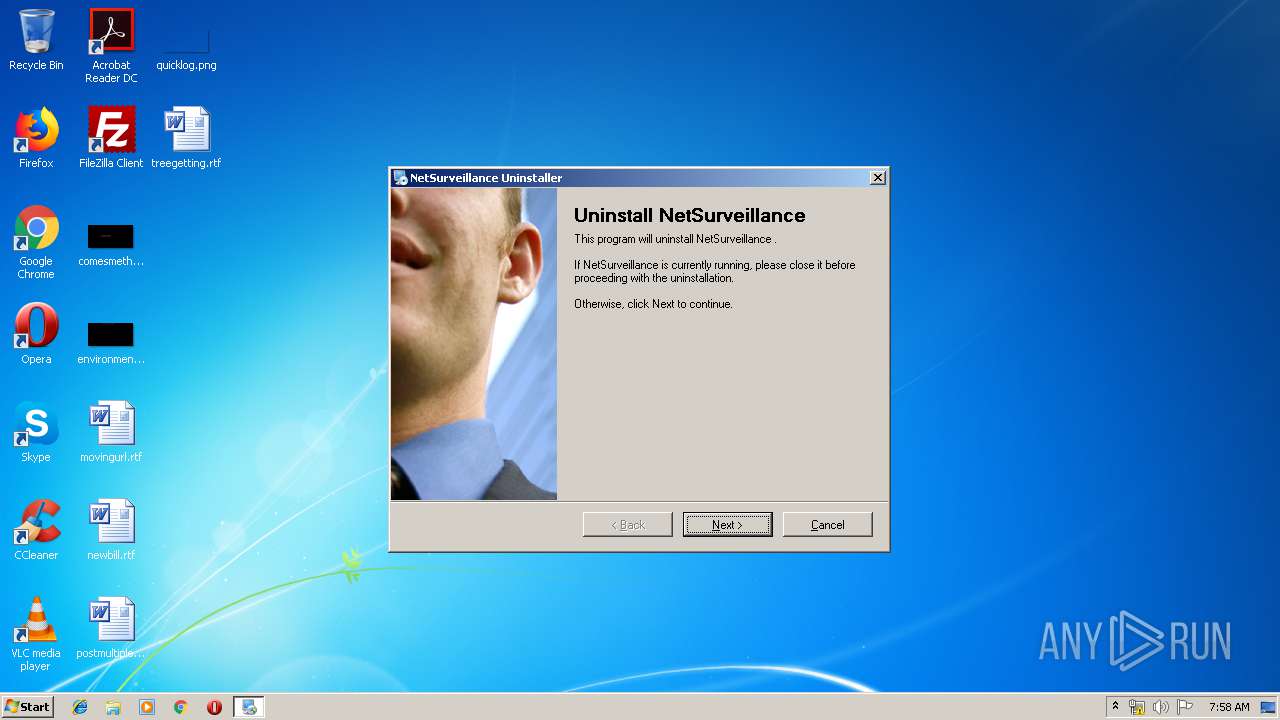
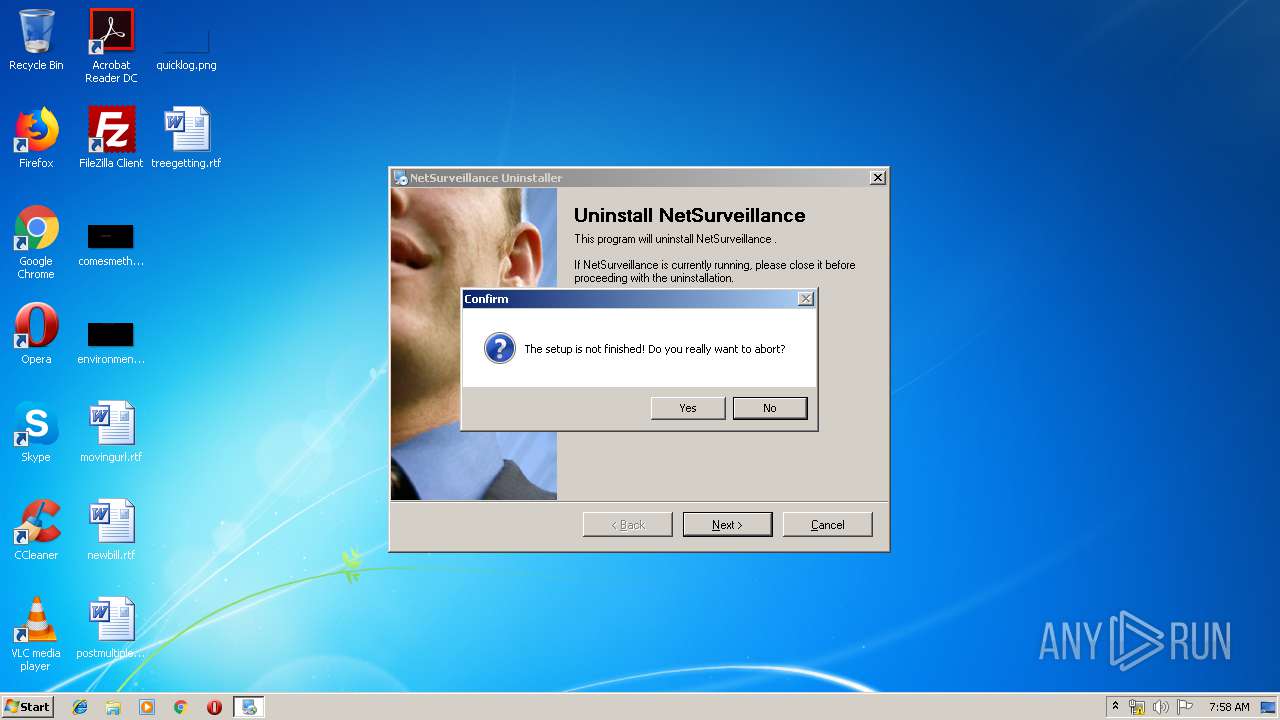
| 2772 | "C:\Windows\NetSurveillance\uninstall.exe" "/U:C:\Windows\NetSurveillance\Uninstall\uninstall.xml" | C:\Windows\NetSurveillance\uninstall.exe | — | explorer.exe | |||||||||||
User: admin Company: Indigo Rose Corporation Integrity Level: MEDIUM Description: Setup Application Exit code: 3221226540 Version: 9.1.0.0 Modules
| |||||||||||||||
| 2960 | reg add "HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\MozillaPlugins\JFGuide" /v Path /t REG_SZ /d "C:\Program Files\NetSurveillance\CMS\npGuide.dll" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3388 | cmd /c ""C:\Program Files\NetSurveillance\CMS\reg.bat" " | C:\Windows\system32\cmd.exe | — | irsetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
673
Read events
624
Write events
49
Delete events
0
Modification events
| (PID) Process: | (2660) newactive.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2660) newactive.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
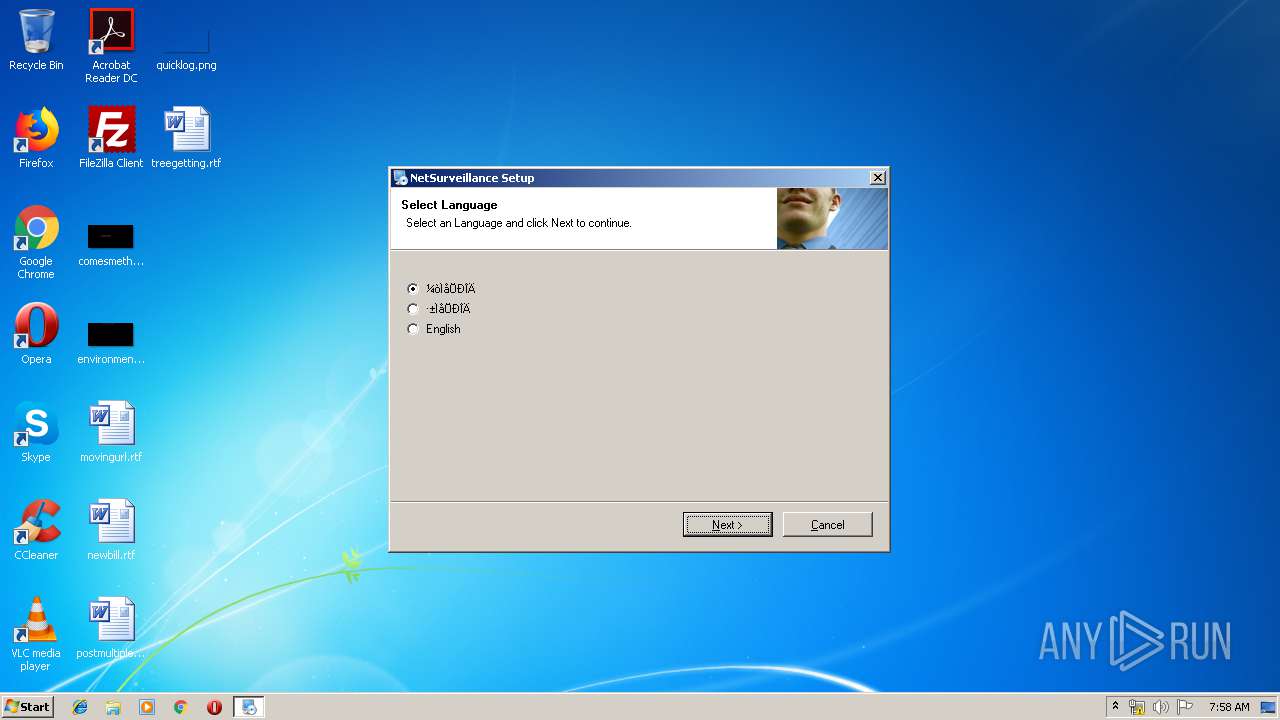
| (PID) Process: | (968) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NetSurveillance |
| Operation: | write | Name: | DisplayName |
Value: NetSurveillance | |||
| (PID) Process: | (968) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NetSurveillance |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
| (PID) Process: | (968) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NetSurveillance |
| Operation: | write | Name: | NoRepair |
Value: 1 | |||
| (PID) Process: | (968) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NetSurveillance |
| Operation: | write | Name: | UninstallString |
Value: "C:\Windows\NetSurveillance\uninstall.exe" "/U:C:\Windows\NetSurveillance\Uninstall\uninstall.xml" | |||
| (PID) Process: | (968) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NetSurveillance |
| Operation: | write | Name: | Contact |
Value: Ö§³Ö²¿ÃÅ | |||
| (PID) Process: | (968) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NetSurveillance |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\NetSurveillance\CMS | |||
| (PID) Process: | (968) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NetSurveillance |
| Operation: | write | Name: | DisplayIcon |
Value: "C:\Windows\NetSurveillance\uninstall.exe" | |||
| (PID) Process: | (968) irsetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
14
Suspicious files
2
Text files
54
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 968 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\irsetup.dat | — | |
MD5:— | SHA256:— | |||
| 968 | irsetup.exe | C:\Windows\NetSurveillance\Uninstall\uni2013.tmp | — | |
MD5:— | SHA256:— | |||
| 2660 | newactive.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\irsetup.exe | executable | |
MD5:DEC931E86140139380EA0DF57CD132B6 | SHA256:5FFD4B20DCCFB84C8890ABDB780184A7651E760AEFBA4AB0C6FBA5B2A81F97D9 | |||
| 2660 | newactive.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\lua5.1.dll | executable | |
MD5:B5FC476C1BF08D5161346CC7DD4CB0BA | SHA256:12CB9B8F59C00EF40EA8F28BFC59A29F12DC28332BF44B1A5D8D6A8823365650 | |||
| 968 | irsetup.exe | C:\Program Files\NetSurveillance\CMS\ConfigModule.dll | executable | |
MD5:— | SHA256:— | |||
| 968 | irsetup.exe | C:\Windows\NetSurveillance\Uninstall\uninstall.dat | binary | |
MD5:— | SHA256:— | |||
| 968 | irsetup.exe | C:\Program Files\NetSurveillance\CMS\ConfigModule.ini | text | |
MD5:EC6FE0F6A8248FA4593A401165DB9E9B | SHA256:AF33E017E71A7F5C91E8F2294077192235C6C9D5381DD9AE0831FA4550E239C4 | |||
| 968 | irsetup.exe | C:\Program Files\NetSurveillance\CMS\H264Play.dll | executable | |
MD5:A13E14CBF39F59B10C8C298C2DA0FAF8 | SHA256:614F8BB649D1078901FD60E17C2EA954CEDB20FACE7B49978F9BB908EE684CE5 | |||
| 968 | irsetup.exe | C:\Program Files\NetSurveillance\CMS\mp_channel.JPG | image | |
MD5:0C47ED6CD47314B14314E876DC08DE0A | SHA256:2F6ED1882504D41908EF5E4106A392257010F24D2094D534457E5FA4C3A967D5 | |||
| 968 | irsetup.exe | C:\Program Files\NetSurveillance\CMS\mp_thumb.JPG | image | |
MD5:019B6EF1743DD24A6D9A970979B65255 | SHA256:5079C33ACED132997F65C49BB70ADCA663C565B2A6653E29705720D1AD265192 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report