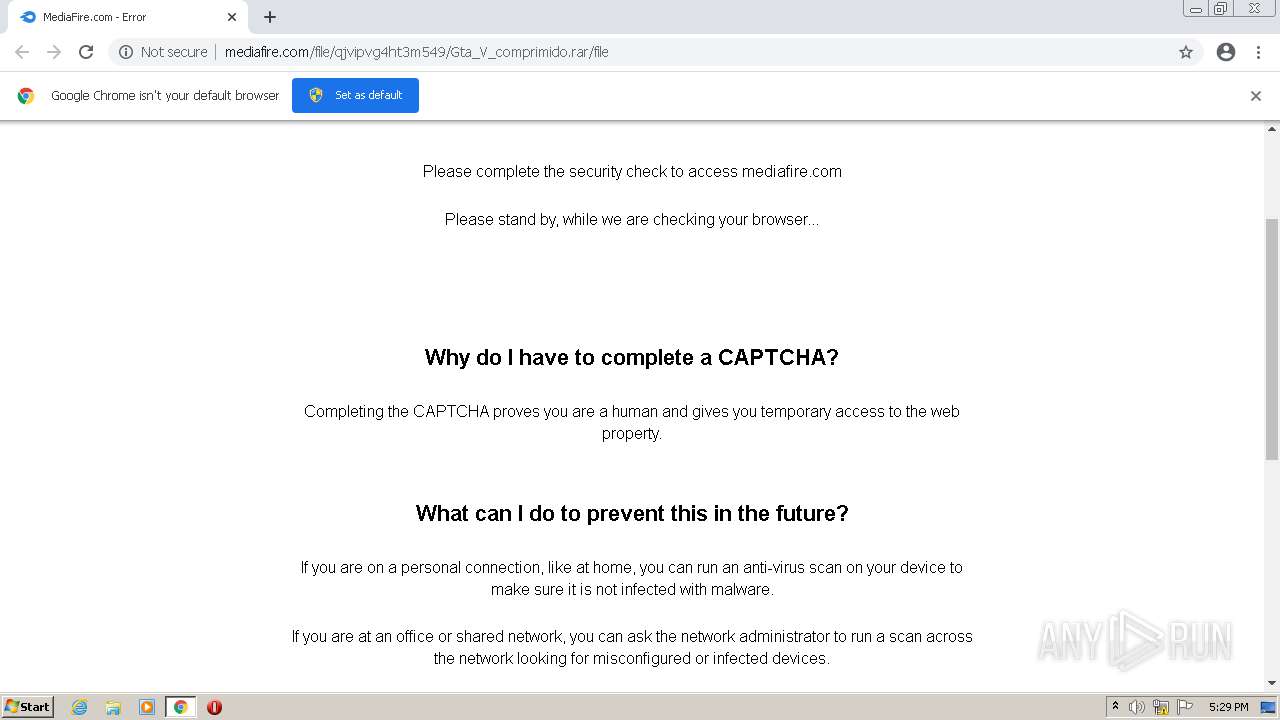
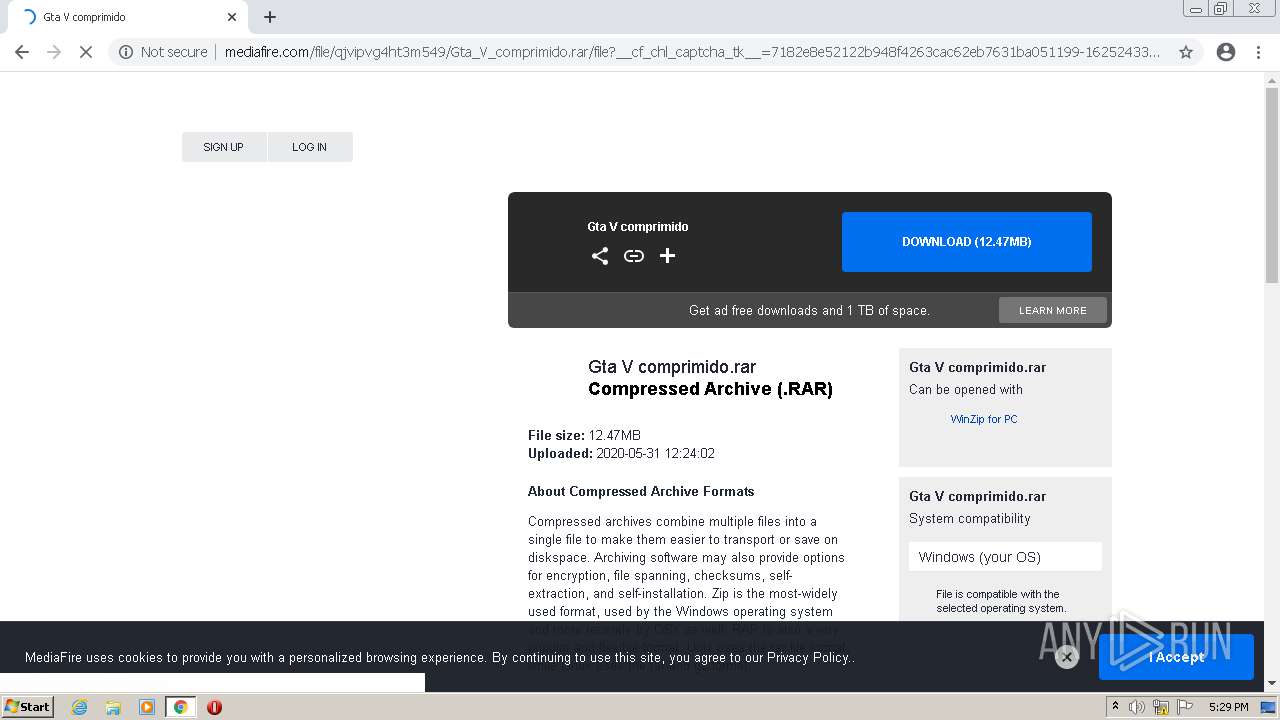
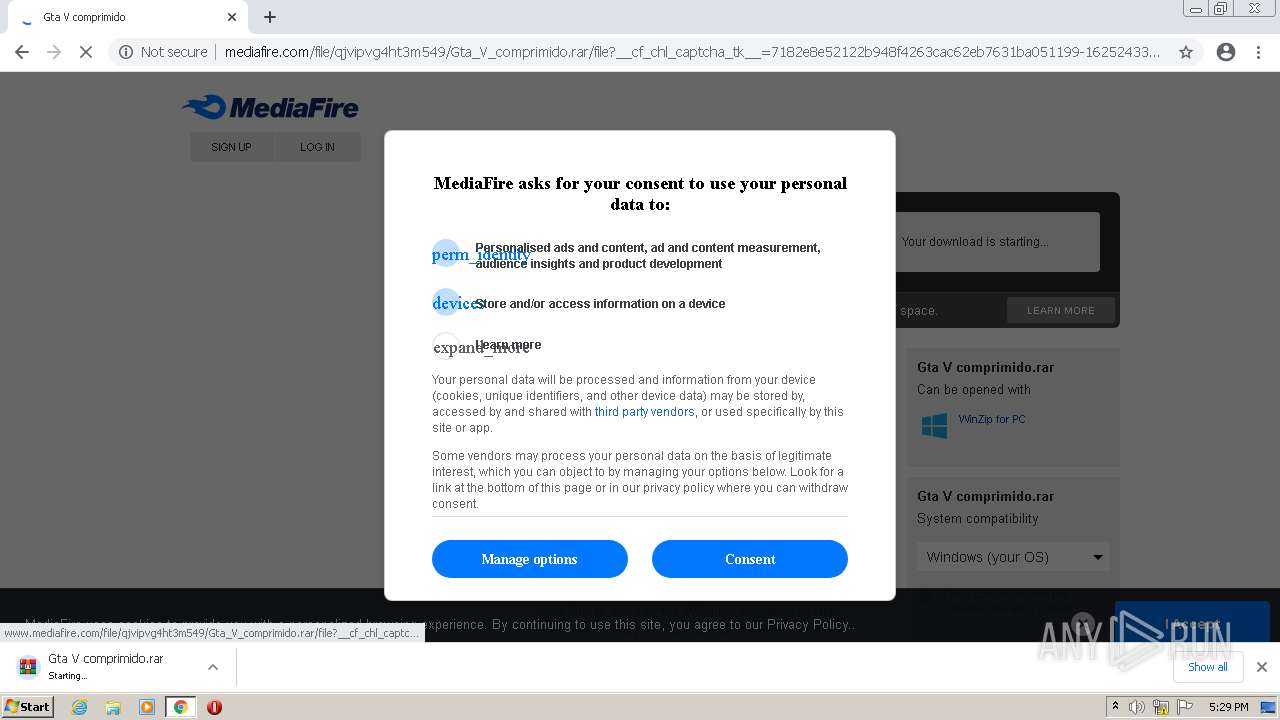
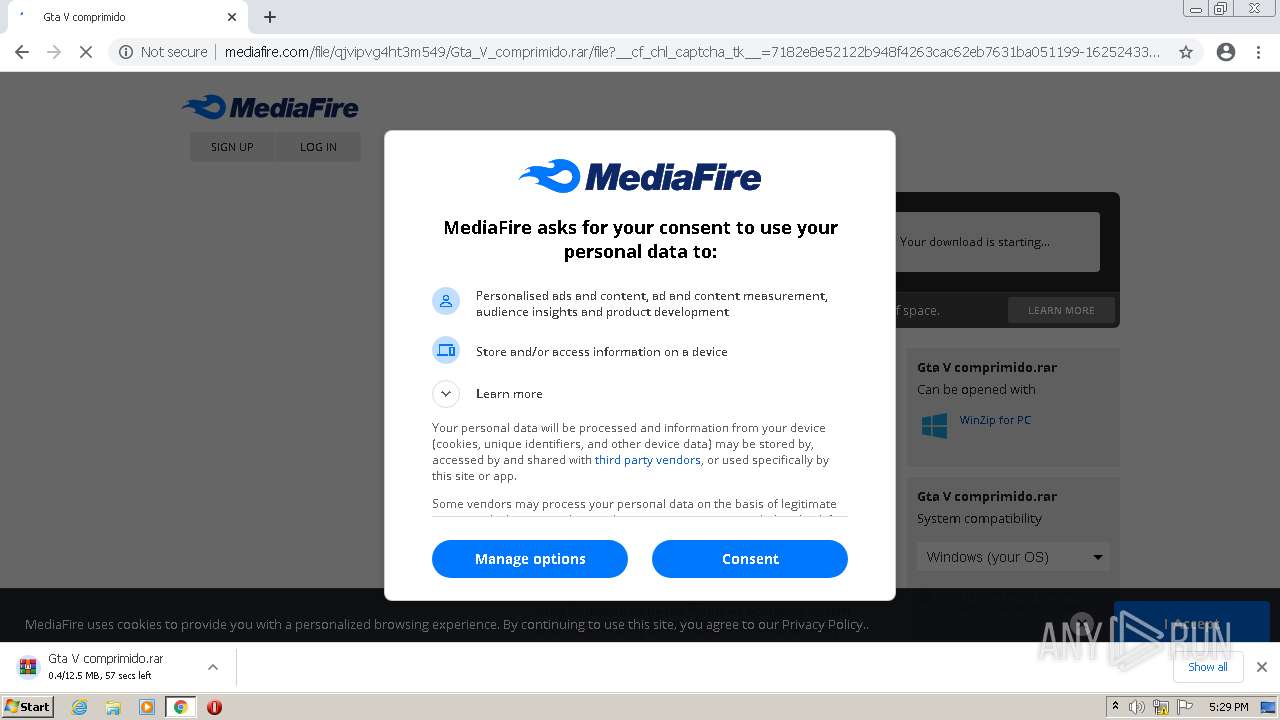
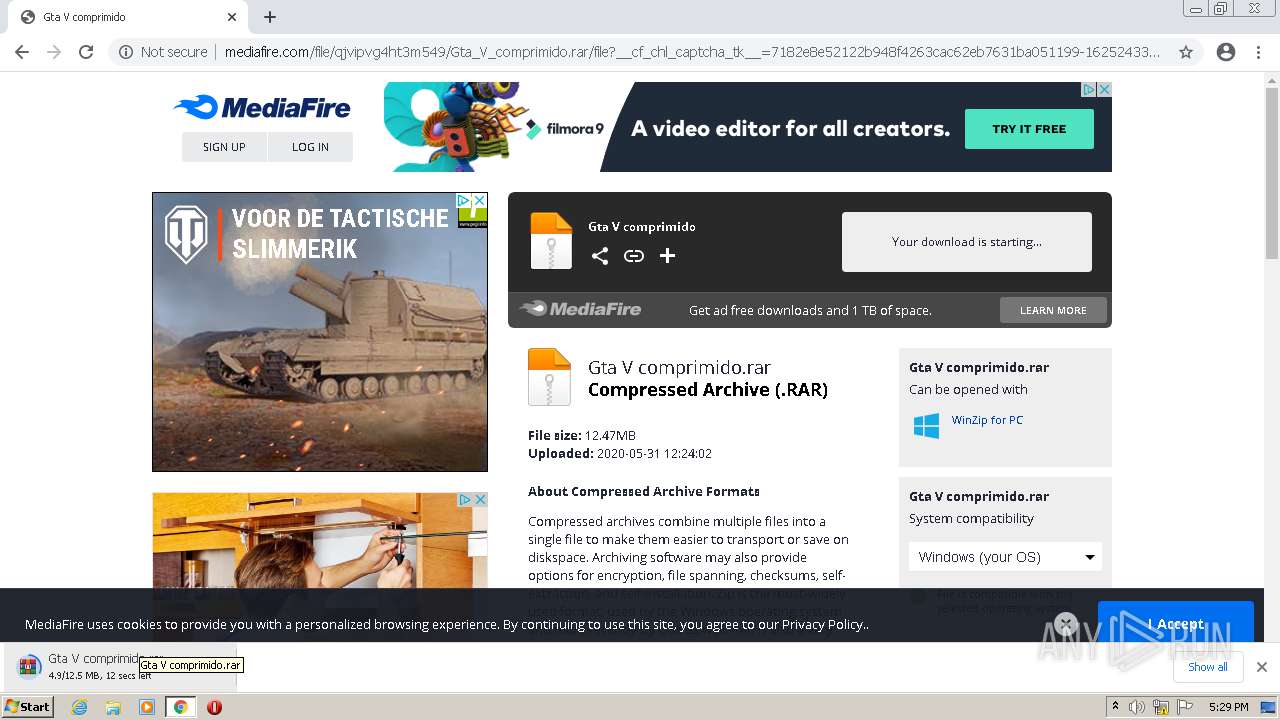
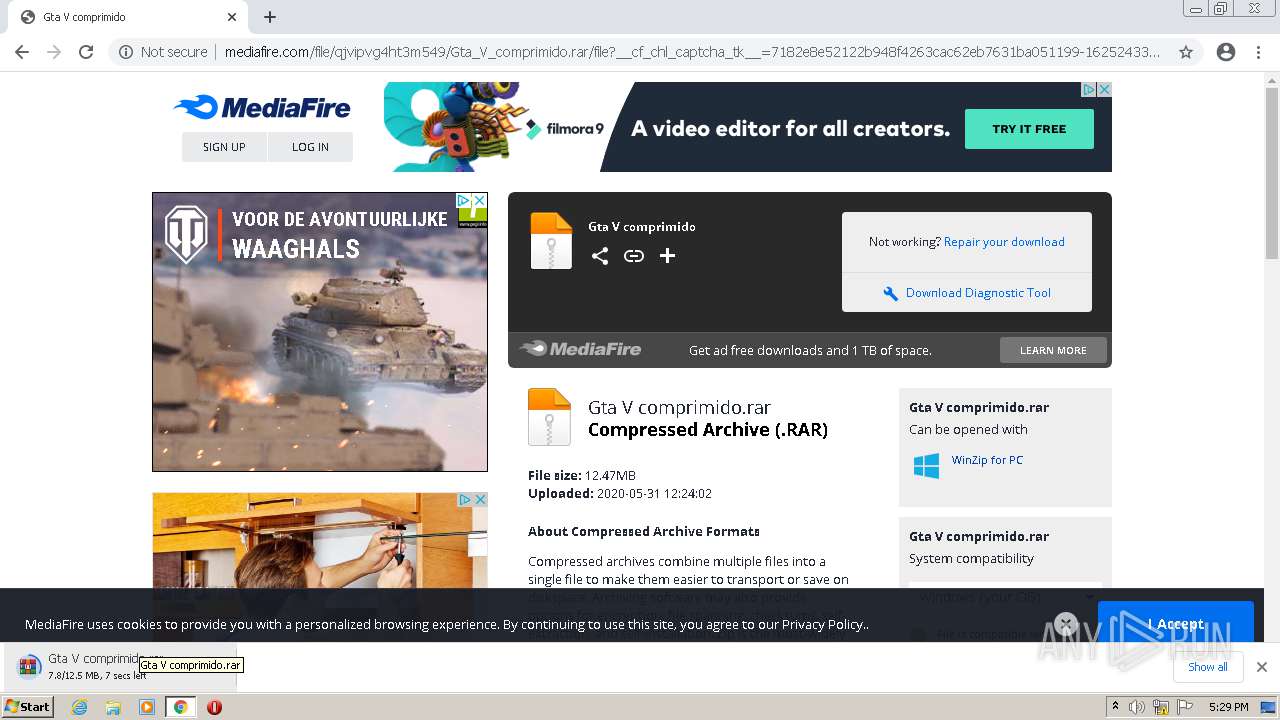
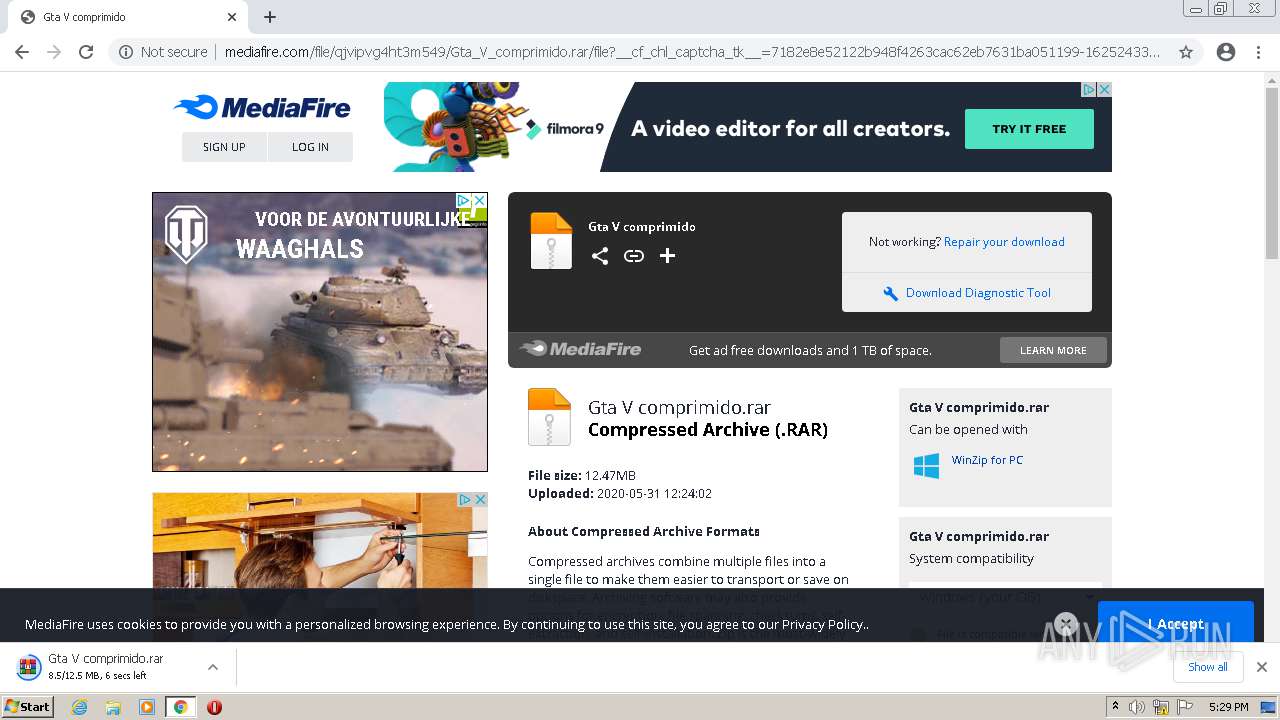
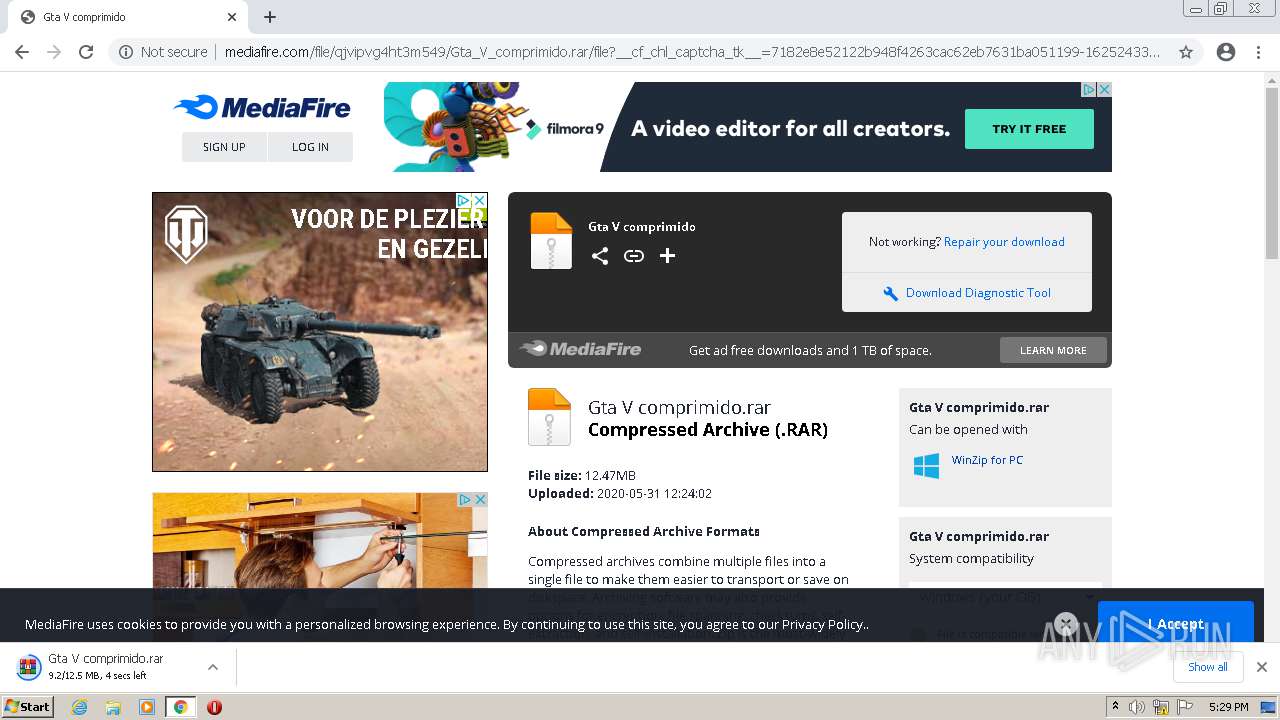
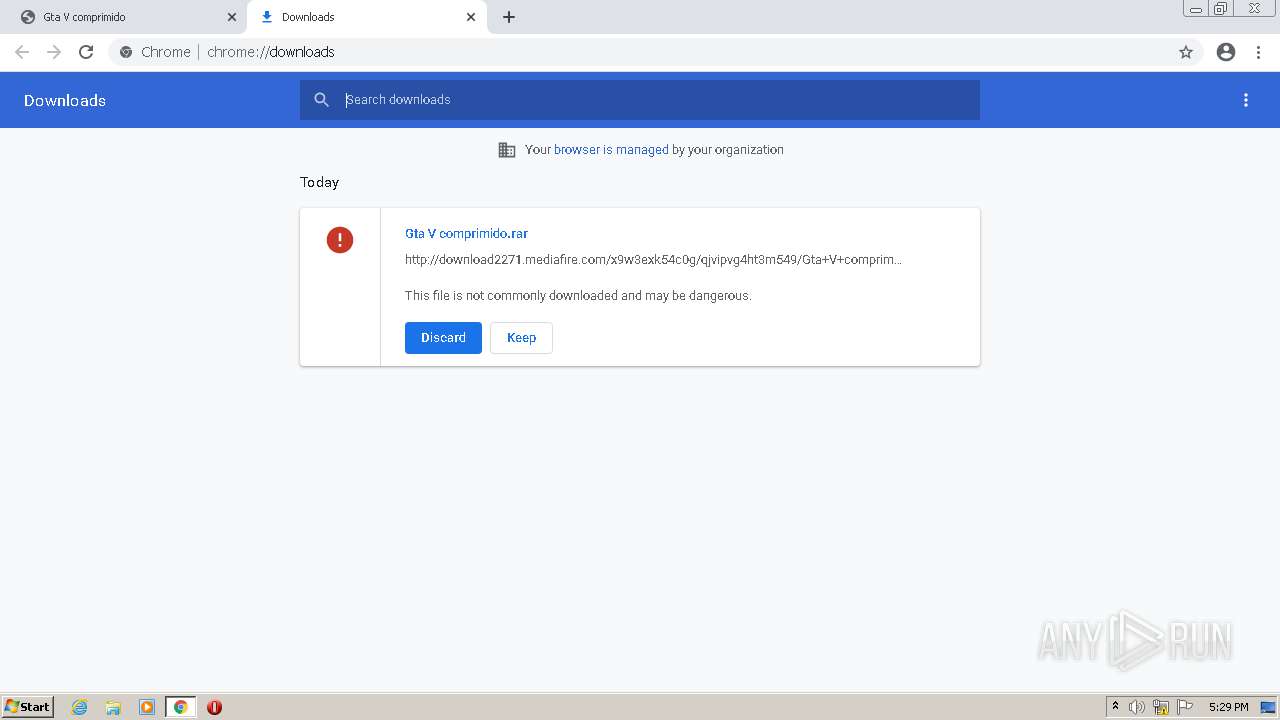
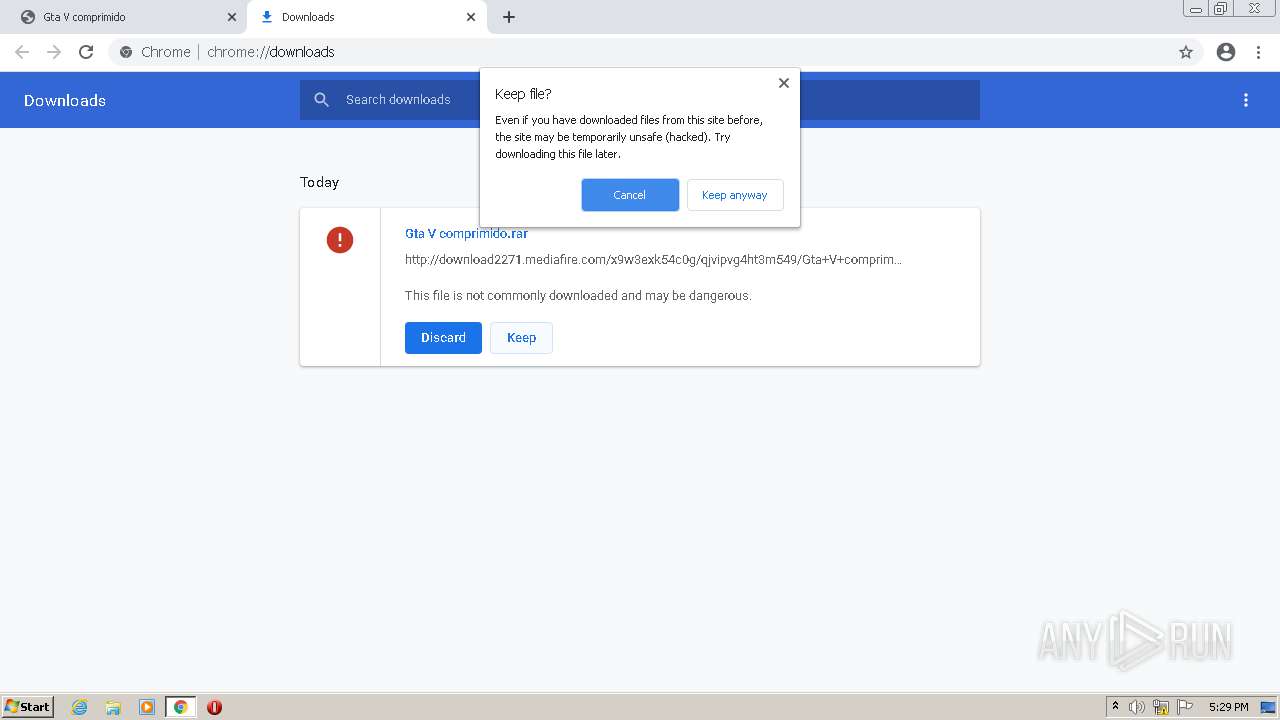
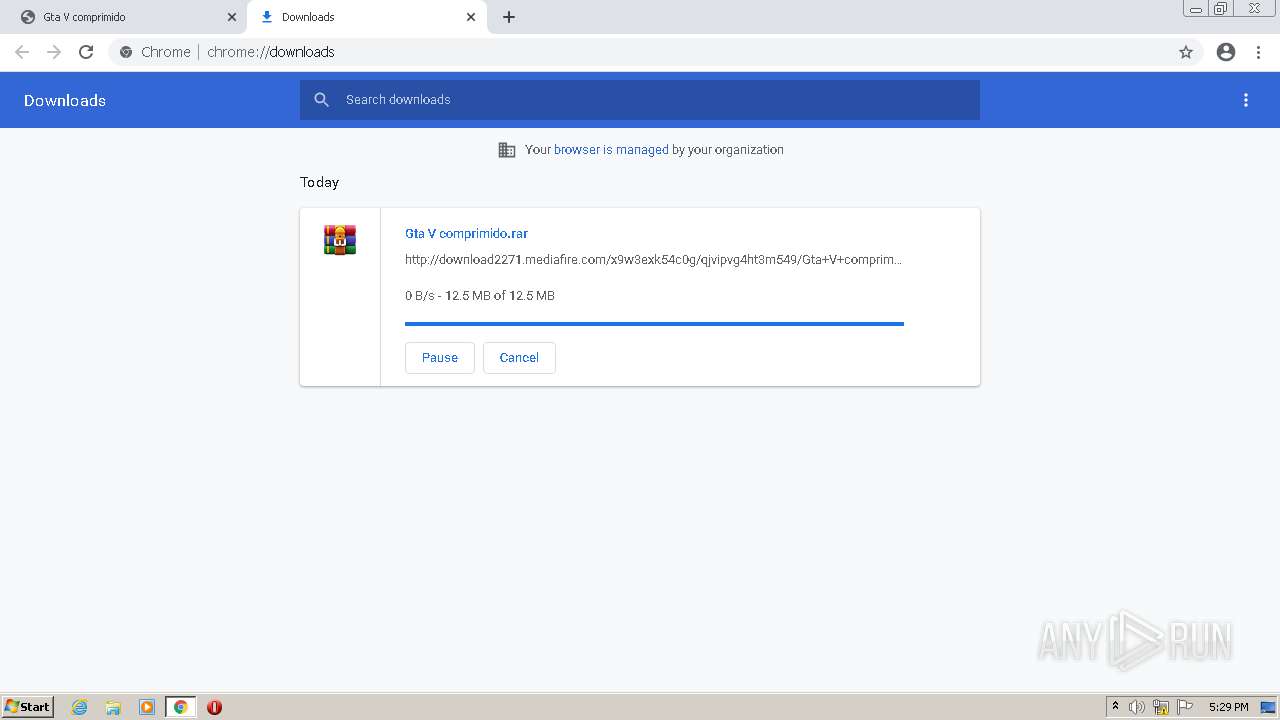
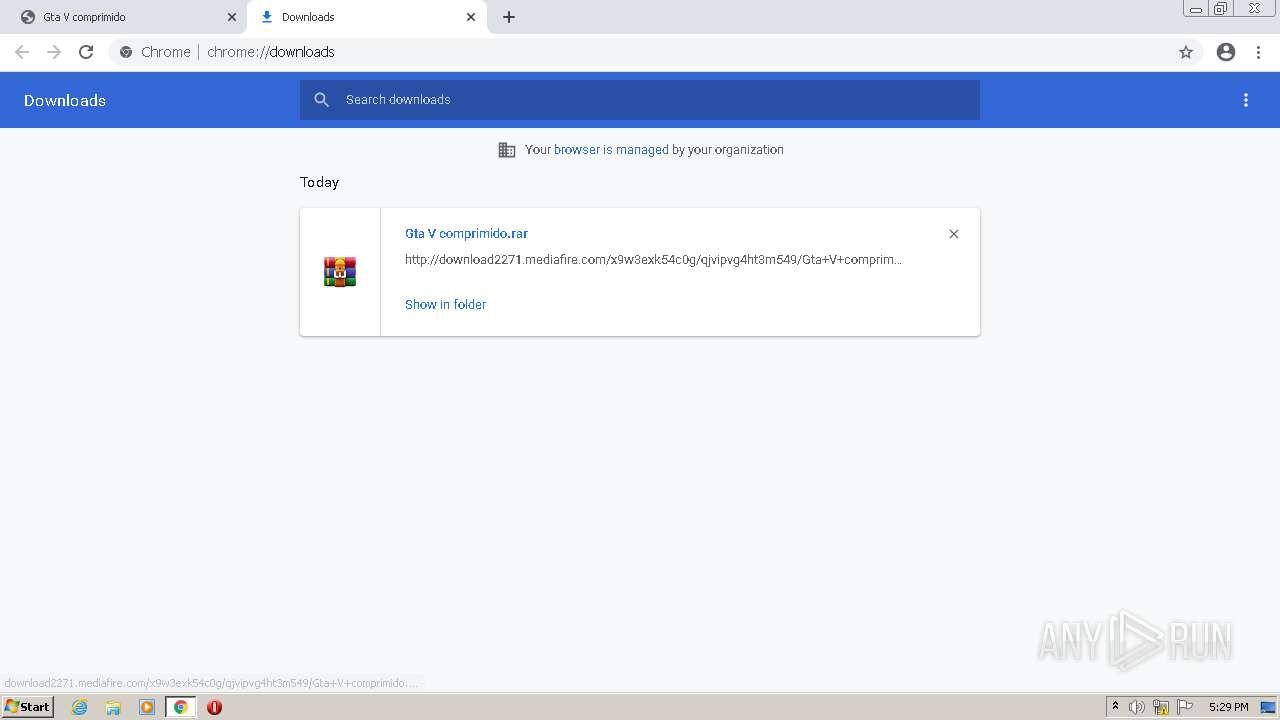
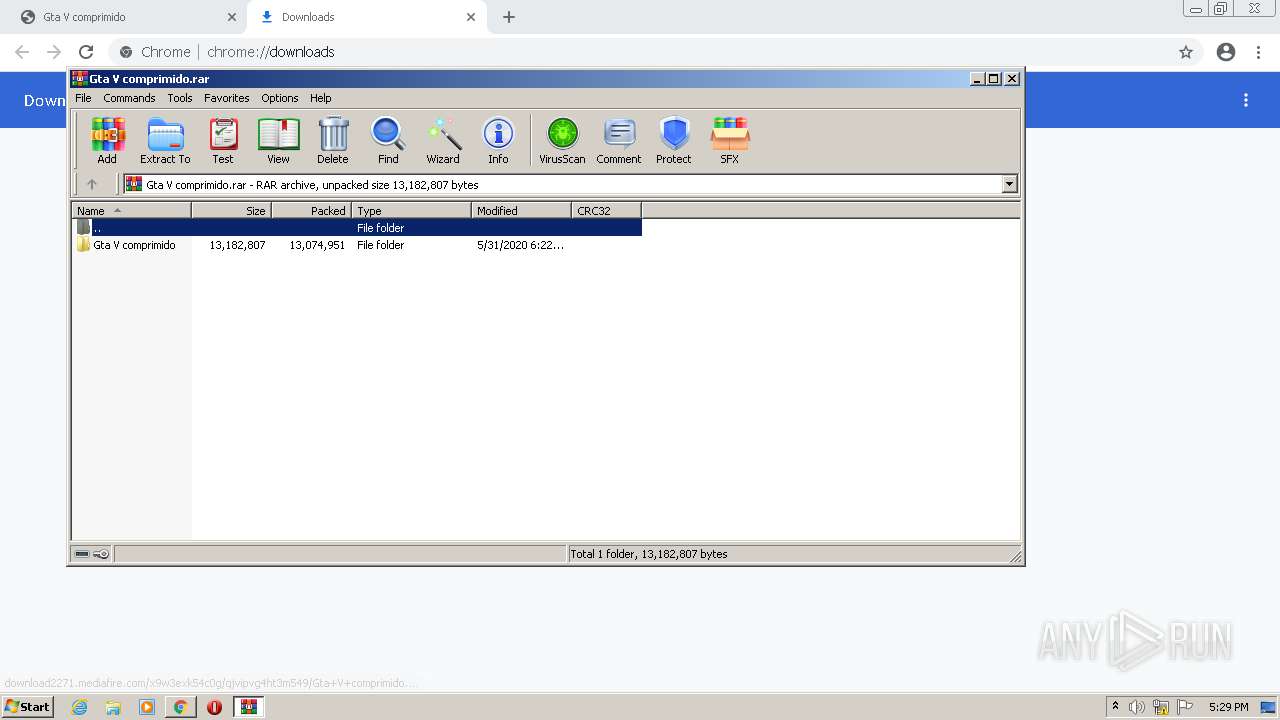
| URL: | http://www.mediafire.com/file/qjvipvg4ht3m549/Gta_V_comprimido.rar/file |
| Full analysis: | https://app.any.run/tasks/3135f406-9939-4145-a587-715740c0c469 |
| Verdict: | Malicious activity |
| Analysis date: | July 02, 2021, 16:28:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 317188E3A71B45845116AA9E51B90BA7 |
| SHA1: | D99E6A2FFF83DAC9457DB1715F3C1DDCC10FE065 |
| SHA256: | A4EE62D5E7A1AB036D236D15E56E78F1B561331F5FCCCBDEC0F63A4E87D4496D |
| SSDEEP: | 3:N1KJS4w3eGUoWmCrwjcKX6WGKoXJAKLUXKcA:Cc4w3eG6m+wPGKYTUXfA |
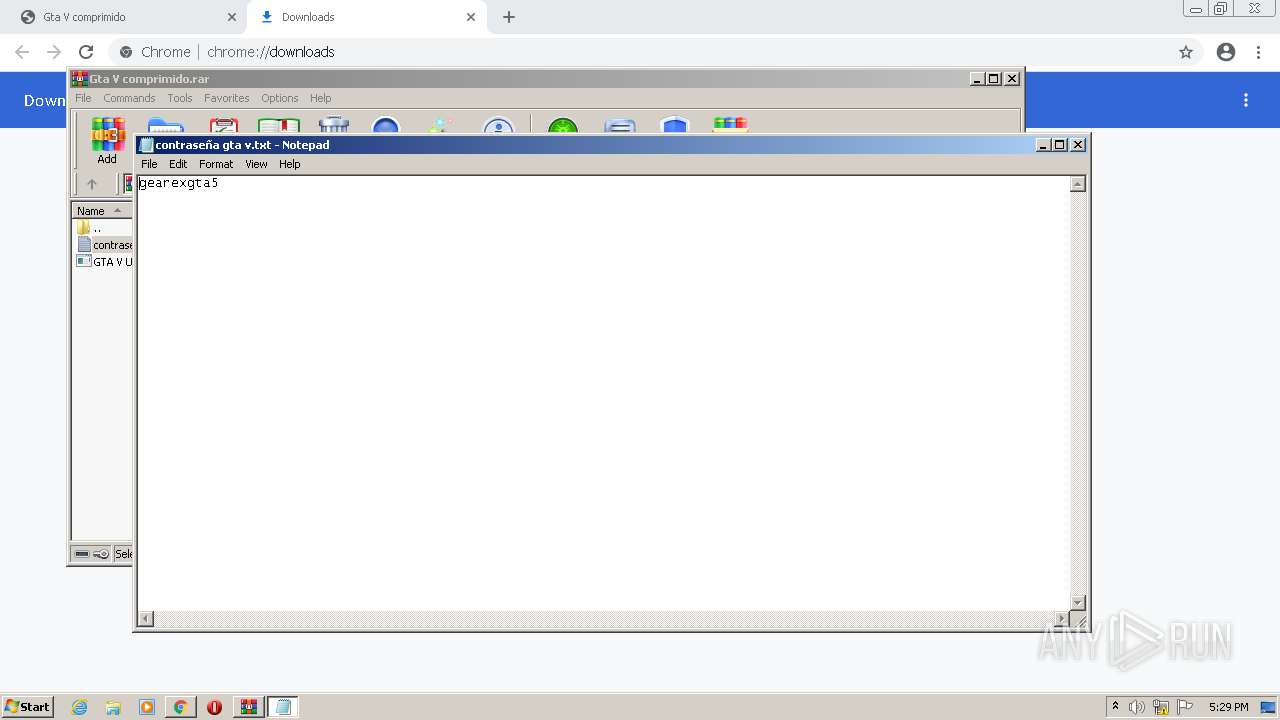
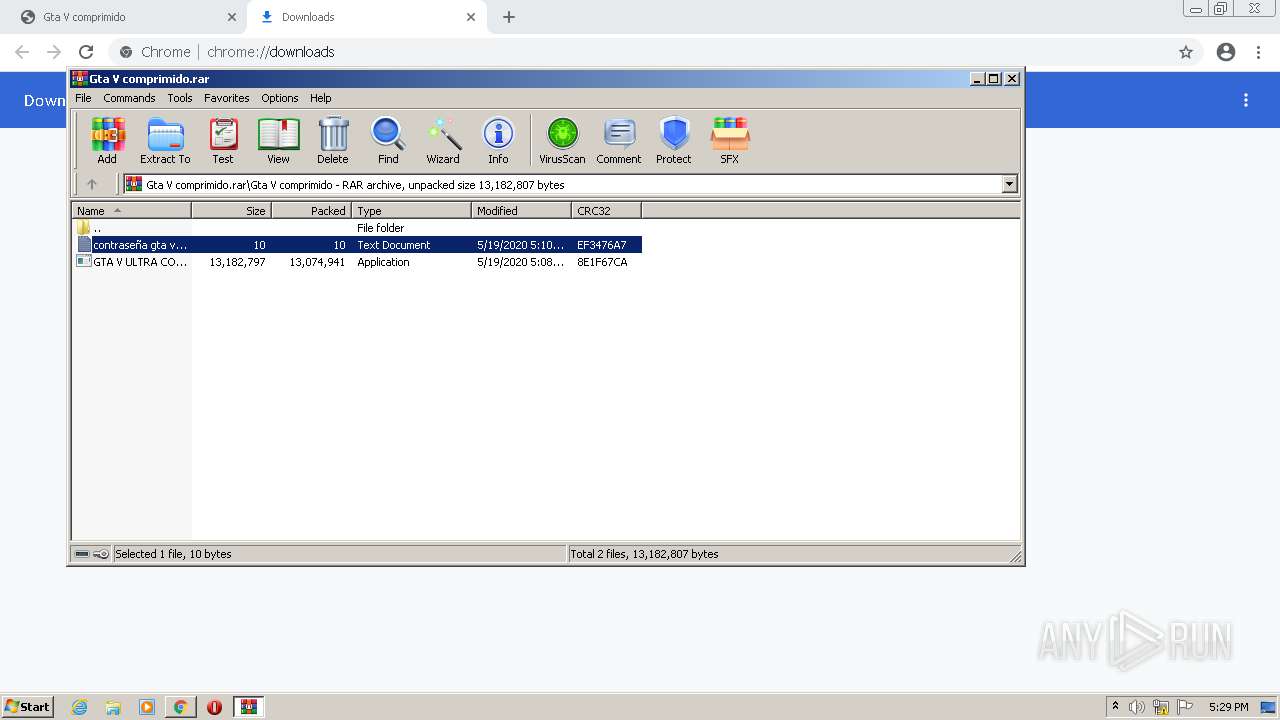
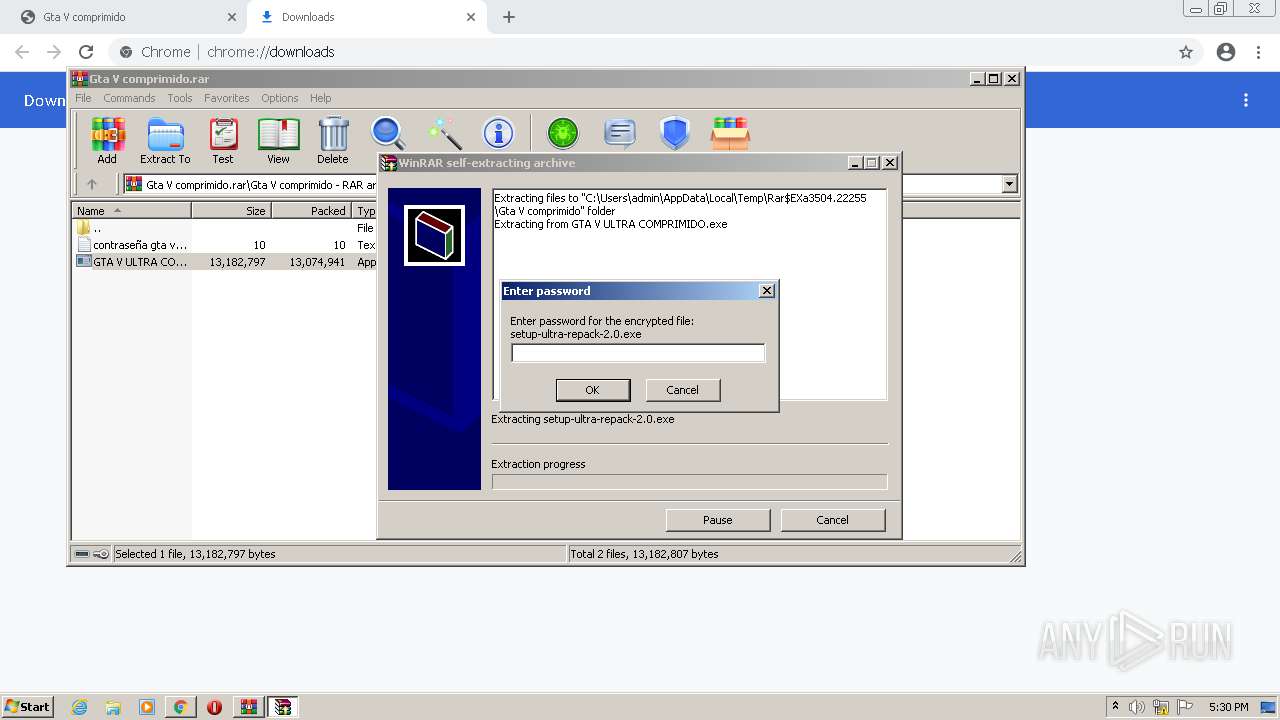
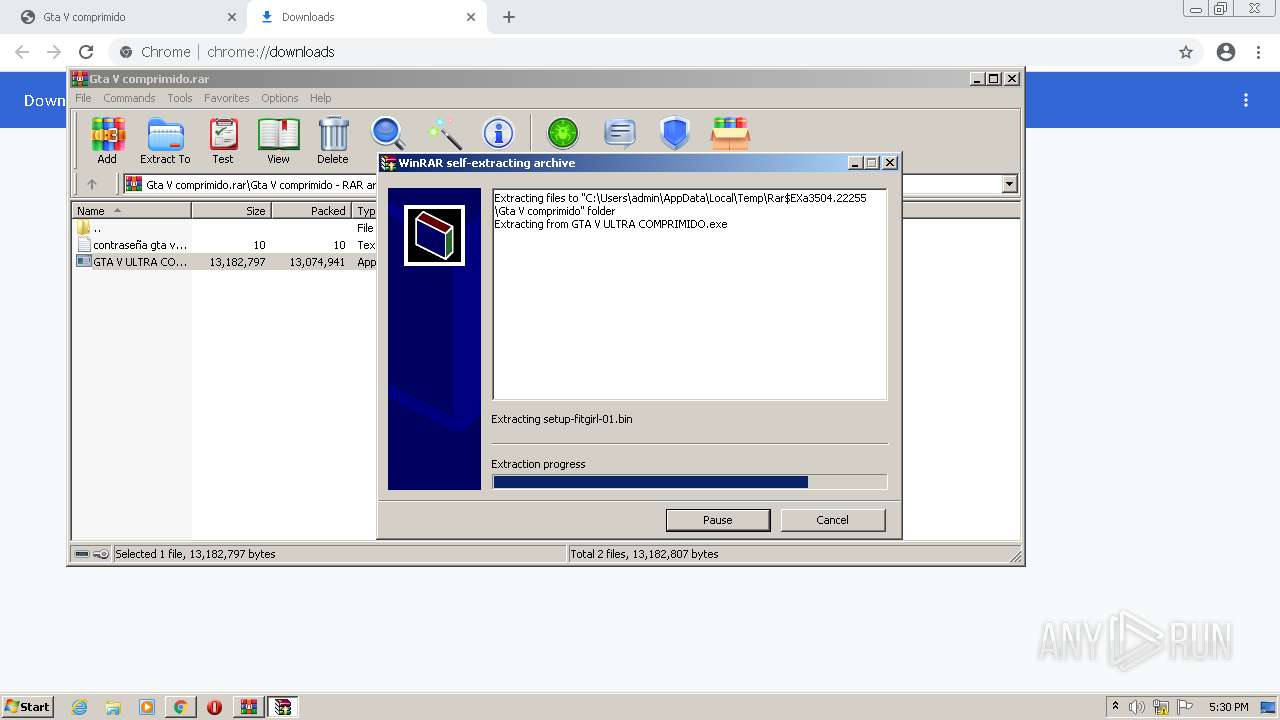
MALICIOUS
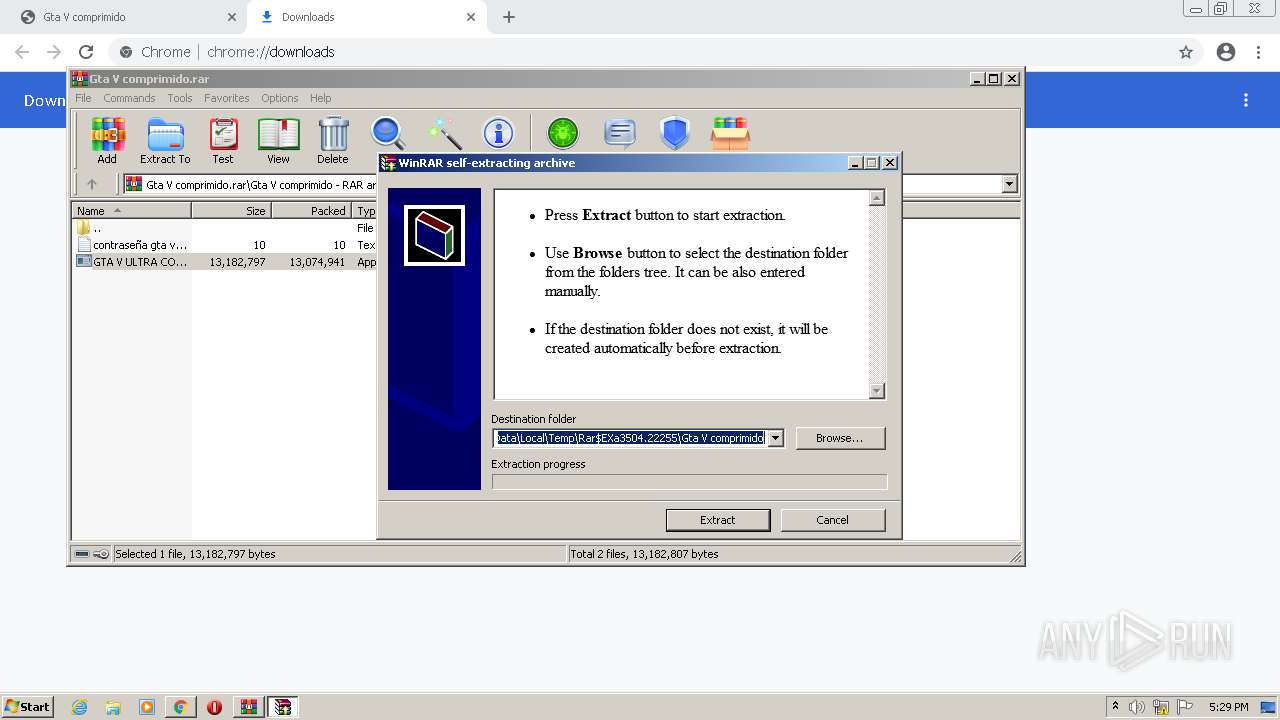
Application was dropped or rewritten from another process
- GTA V ULTRA COMPRIMIDO.exe (PID: 1860)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 3504)
- GTA V ULTRA COMPRIMIDO.exe (PID: 1860)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3504)
- GTA V ULTRA COMPRIMIDO.exe (PID: 1860)
Reads the computer name
- WinRAR.exe (PID: 3504)
- GTA V ULTRA COMPRIMIDO.exe (PID: 1860)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 3504)
Reads Microsoft Outlook installation path
- GTA V ULTRA COMPRIMIDO.exe (PID: 1860)
Reads internet explorer settings
- GTA V ULTRA COMPRIMIDO.exe (PID: 1860)
INFO
Checks supported languages
- chrome.exe (PID: 3556)
- chrome.exe (PID: 1692)
- chrome.exe (PID: 3724)
- chrome.exe (PID: 2260)
- chrome.exe (PID: 3676)
- chrome.exe (PID: 3380)
- chrome.exe (PID: 2080)
- chrome.exe (PID: 3216)
- chrome.exe (PID: 3172)
- chrome.exe (PID: 292)
- chrome.exe (PID: 3052)
- chrome.exe (PID: 4048)
- chrome.exe (PID: 1452)
- chrome.exe (PID: 2180)
- chrome.exe (PID: 912)
- chrome.exe (PID: 2688)
- chrome.exe (PID: 2988)
- chrome.exe (PID: 3236)
- chrome.exe (PID: 1380)
- chrome.exe (PID: 4068)
- chrome.exe (PID: 2472)
- chrome.exe (PID: 428)
- chrome.exe (PID: 1448)
- chrome.exe (PID: 2628)
- chrome.exe (PID: 2864)
- chrome.exe (PID: 3656)
- chrome.exe (PID: 3896)
- chrome.exe (PID: 424)
- chrome.exe (PID: 904)
- NOTEPAD.EXE (PID: 3812)
- chrome.exe (PID: 584)
- chrome.exe (PID: 2384)
- chrome.exe (PID: 272)
- chrome.exe (PID: 3168)
- chrome.exe (PID: 1480)
- chrome.exe (PID: 1152)
- chrome.exe (PID: 1684)
- chrome.exe (PID: 904)
- chrome.exe (PID: 2788)
- chrome.exe (PID: 3636)
- chrome.exe (PID: 2944)
- chrome.exe (PID: 3880)
- chrome.exe (PID: 3540)
- chrome.exe (PID: 532)
Reads the hosts file
- chrome.exe (PID: 3556)
- chrome.exe (PID: 3216)
Reads the computer name
- chrome.exe (PID: 3556)
- chrome.exe (PID: 3676)
- chrome.exe (PID: 3216)
- chrome.exe (PID: 292)
- chrome.exe (PID: 3172)
- chrome.exe (PID: 3380)
- chrome.exe (PID: 4048)
- chrome.exe (PID: 2180)
- chrome.exe (PID: 2472)
- chrome.exe (PID: 424)
Application launched itself
- chrome.exe (PID: 3556)
Reads settings of System Certificates
- chrome.exe (PID: 3216)
Reads the date of Windows installation
- chrome.exe (PID: 2180)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
82
Monitored processes
46
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1036,17188520439176275277,1573488837539348581,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1816 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1036,17188520439176275277,1573488837539348581,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1052 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 424 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1036,17188520439176275277,1573488837539348581,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4764 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,17188520439176275277,1573488837539348581,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3888 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,17188520439176275277,1573488837539348581,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=39 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5272 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,17188520439176275277,1573488837539348581,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5000 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1036,17188520439176275277,1573488837539348581,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=4732 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,17188520439176275277,1573488837539348581,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=29 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1176 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,17188520439176275277,1573488837539348581,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2916 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1036,17188520439176275277,1573488837539348581,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3644 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
16 814
Read events
16 631
Write events
178
Delete events
5
Modification events
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
2
Suspicious files
35
Text files
134
Unknown types
1
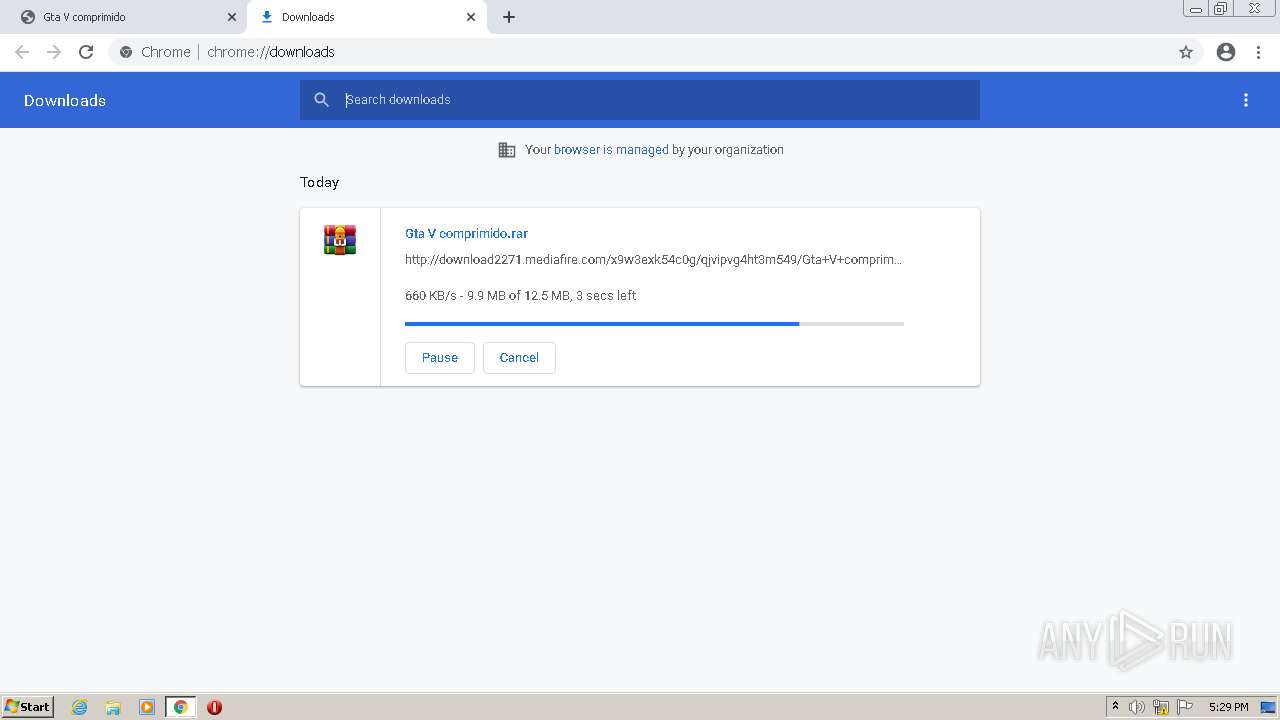
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-60DF3EA6-DE4.pma | — | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFd6765.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old~RFd6a82.TMP | text | |
MD5:D0BA19096D6C8F8DE58312E8D938E893 | SHA256:AADE90A7B0984F3C719D528E4E6FAE3854E28B30363BDD4DF65037E69784A078 | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RFd685f.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:EF1D5606A483BB6C72C81A3F649BEB18 | SHA256:BA083E7585ADA9936944FE56BC0141A544F18A01C3424E5C9F02375B34FE3D45 | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences~RFd68dc.TMP | text | |
MD5:8304B8F42465198890090F52D3F80A4C | SHA256:80C32AC2585E7E81200104B1630F19560A156C4ABF51B5888B0FBF07323FAB34 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
52
TCP/UDP connections
143
DNS requests
117
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3216 | chrome.exe | GET | 403 | 104.16.203.237:80 | http://www.mediafire.com/file/qjvipvg4ht3m549/Gta_V_comprimido.rar/file | US | html | 7.72 Kb | shared |
3216 | chrome.exe | GET | 200 | 104.16.203.237:80 | http://www.mediafire.com/cdn-cgi/challenge-platform/h/g/orchestrate/captcha/v1?ray=66893f3ee9bbedd7 | US | text | 13.7 Kb | shared |
3216 | chrome.exe | GET | 200 | 104.16.203.237:80 | http://static.mediafire.com/images/backgrounds/download/apps_list_sprite-v4.png | US | image | 6.78 Kb | shared |
3216 | chrome.exe | GET | 200 | 104.16.203.237:80 | http://www.mediafire.com/js/prebid2.44.1.js | US | text | 52.9 Kb | shared |
3216 | chrome.exe | POST | 200 | 104.16.203.237:80 | http://www.mediafire.com/cdn-cgi/challenge-platform/h/g/flow/ov1/0.5393242622915511:1625242063:a337fccef1e38386e0c5f3db3f0d970136fc0c0872aa0214bb9d918cc5b576c4/66893f3ee9bbedd7/92e0e112978862b | US | text | 3.26 Kb | shared |
3216 | chrome.exe | POST | 200 | 104.16.203.237:80 | http://www.mediafire.com/cdn-cgi/challenge-platform/h/g/flow/ov1/0.5393242622915511:1625242063:a337fccef1e38386e0c5f3db3f0d970136fc0c0872aa0214bb9d918cc5b576c4/66893f3ee9bbedd7/92e0e112978862b | US | text | 4.27 Kb | shared |
3216 | chrome.exe | GET | 200 | 104.16.203.237:80 | http://www.mediafire.com/images/icons/svg_light/icons_sprite.svg | US | image | 8.17 Kb | shared |
3216 | chrome.exe | GET | 200 | 104.16.203.237:80 | http://www.mediafire.com/cdn-cgi/images/trace/captcha/nojs/h/transparent.gif?ray=66893f3ee9bbedd7 | US | image | 42 b | shared |
3216 | chrome.exe | POST | 200 | 185.33.220.240:80 | http://ib.adnxs.com/ut/v3/prebid | unknown | text | 239 b | whitelisted |
3216 | chrome.exe | GET | 200 | 104.16.203.237:80 | http://www.mediafire.com/images/icons/svg_dark/arrow_dropdown.svg | US | image | 250 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3216 | chrome.exe | 172.217.168.238:443 | clients2.google.com | Google Inc. | US | whitelisted |
3216 | chrome.exe | 104.16.203.237:80 | www.mediafire.com | Cloudflare Inc | US | unknown |
3216 | chrome.exe | 142.251.36.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3216 | chrome.exe | 172.217.20.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
3216 | chrome.exe | 104.16.168.131:443 | newassets.hcaptcha.com | Cloudflare Inc | US | unknown |
3216 | chrome.exe | 172.217.168.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3216 | chrome.exe | 185.64.189.112:443 | hbopenbid.pubmatic.com | PubMatic, Inc. | GB | unknown |
3216 | chrome.exe | 142.250.179.136:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
3216 | chrome.exe | 172.217.168.206:443 | fundingchoicesmessages.google.com | Google Inc. | US | whitelisted |
3216 | chrome.exe | 142.250.179.202:443 | content-autofill.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
www.mediafire.com |
| shared |
accounts.google.com |
| shared |
mediafire.zendesk.com |
| whitelisted |
hcaptcha.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
newassets.hcaptcha.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
imgs.hcaptcha.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3216 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3216 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3216 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |