| File name: | wsetup.exe |
| Full analysis: | https://app.any.run/tasks/13906f3d-b362-4486-a6d4-ce697b18478a |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 11:43:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D621F450D24942018C1C25C267DCD9AC |
| SHA1: | 788E529B512FDF729F3B75941DDCEBA8B626CD3C |
| SHA256: | A4E5DB28A8508DF1CA9CC8839B0D409D450B07DE8FD253A9CCDD2C0914B70A0D |
| SSDEEP: | 98304:GfK3k0cYf1T/xNWgkB42q6Te+MTXjTqmUrqfGoPp8PMWRa3LF/eEoUwoD:t3k0l7wgkO2q6TzMTzcrqeoPeP147FGc |
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- wsetup.exe (PID: 3436)
Loads dropped or rewritten executable
- Regsvr32.exe (PID: 3648)
- Regsvr32.exe (PID: 3288)
Application was dropped or rewritten from another process
- P_Sips_Client_CA.exe (PID: 3948)
SUSPICIOUS
Executable content was dropped or overwritten
- wsetup.exe (PID: 3436)
Creates files in the program directory
- wsetup.exe (PID: 3436)
Creates files in the Windows directory
- wsetup.exe (PID: 3436)
Creates a software uninstall entry
- wsetup.exe (PID: 3436)
Modifies the open verb of a shell class
- wsetup.exe (PID: 3436)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (36.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (26.6) |
| .exe | | | Win64 Executable (generic) (23.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:02:14 03:23:32+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 442368 |
| InitializedDataSize: | 159232 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4ebbf |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 5.8.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | 青岛锐普信息科技有限公司 |
| FileDescription: | 统计网上直报 |
| FileVersion: | 5.8.0.0 |
| LegalCopyright: | 青岛锐普信息科技有限公司 |
| ProductVersion: | 5, 8, 0, 0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Feb-2009 02:23:32 |
| Detected languages: |
|
| CompanyName: | 青岛锐普信息科技有限公司 |
| ___________________________________________________________________________________________________________________________________________________________________________________________________________________________________________________________________________________________: | - |
| FileDescription: | 统计网上直报 |
| _________________________________________________________________________________________________________________________________________________________________________________________________________________________________________________________________________________________________: | - |
| FileVersion: | 5.8.0.0 |
| LegalCopyright: | 青岛锐普信息科技有限公司 |
| ProductVersion: | 5, 8, 0, 0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 14-Feb-2009 02:23:32 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0006BEB9 | 0x0006C000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.56344 |
.rdata | 0x0006D000 | 0x0001C328 | 0x0001C400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.30347 |
.data | 0x0008A000 | 0x000084FC | 0x00003400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.43697 |
.rsrc | 0x00093000 | 0x00007450 | 0x00007600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.35658 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.79597 | 346 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.02695 | 308 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
3 | 2.74274 | 180 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
4 | 2.34038 | 308 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
5 | 2.34004 | 308 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
6 | 2.51649 | 308 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
7 | 2.45401 | 308 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
8 | 2.34864 | 308 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
9 | 2.82349 | 352 | Latin 1 / Western European | UNKNOWN | RT_DIALOG |
10 | 2.34864 | 308 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
OLEACC.dll (delay-loaded) |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
Total processes
43
Monitored processes
6
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2848 | C:\Windows\system32\Regsvr32.exe "C:\Windows\msscript.ocx" /s | C:\Windows\system32\Regsvr32.exe | — | wsetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3096 | "C:\wsetup.exe" | C:\wsetup.exe | — | explorer.exe | |||||||||||
User: admin Company: 青岛锐普信息科技有限公司 Integrity Level: MEDIUM Description: 统计网上直报 Exit code: 3221226540 Version: 5.8.0.0 Modules
| |||||||||||||||
| 3288 | C:\Windows\system32\Regsvr32.exe "C:\Windows\JITSecurityTool.ocx" /s | C:\Windows\system32\Regsvr32.exe | — | wsetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 3 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3436 | "C:\wsetup.exe" | C:\wsetup.exe | explorer.exe | ||||||||||||
User: admin Company: 青岛锐普信息科技有限公司 Integrity Level: HIGH Description: 统计网上直报 Exit code: 0 Version: 5.8.0.0 Modules
| |||||||||||||||
| 3648 | C:\Windows\system32\Regsvr32.exe "C:\Windows\SdcaTsa.ocx" /s | C:\Windows\system32\Regsvr32.exe | — | wsetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
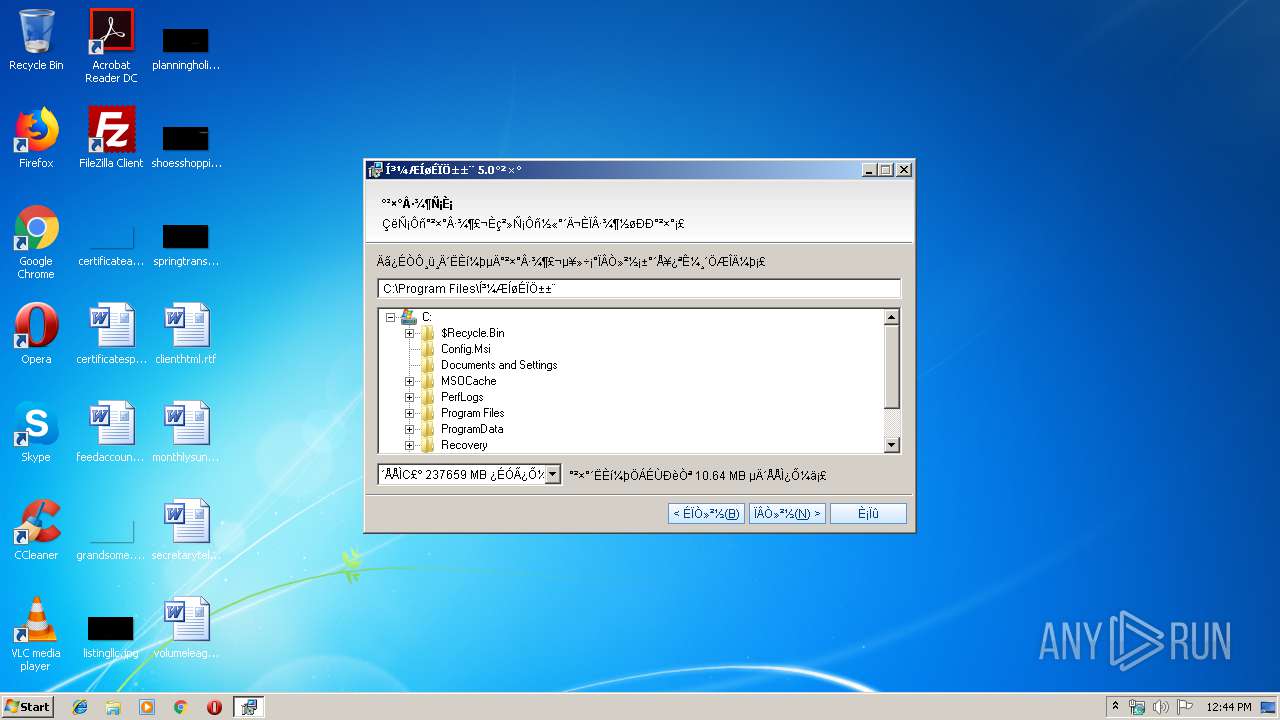
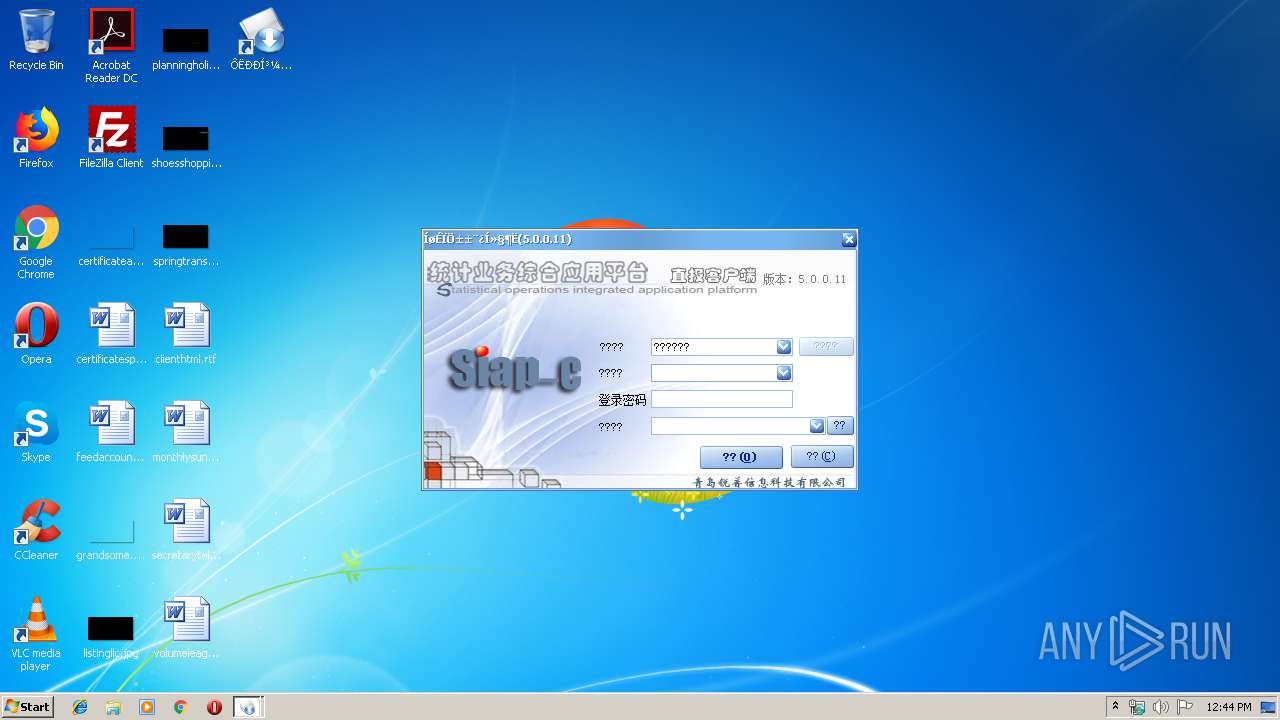
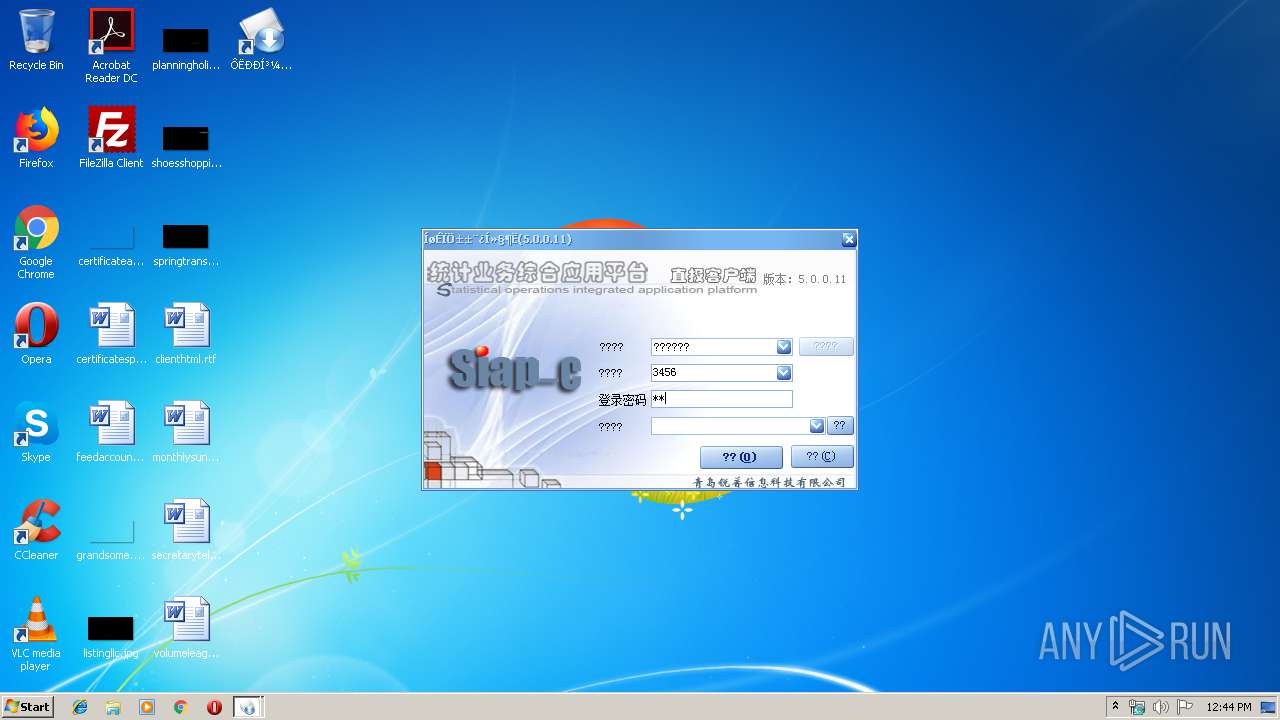
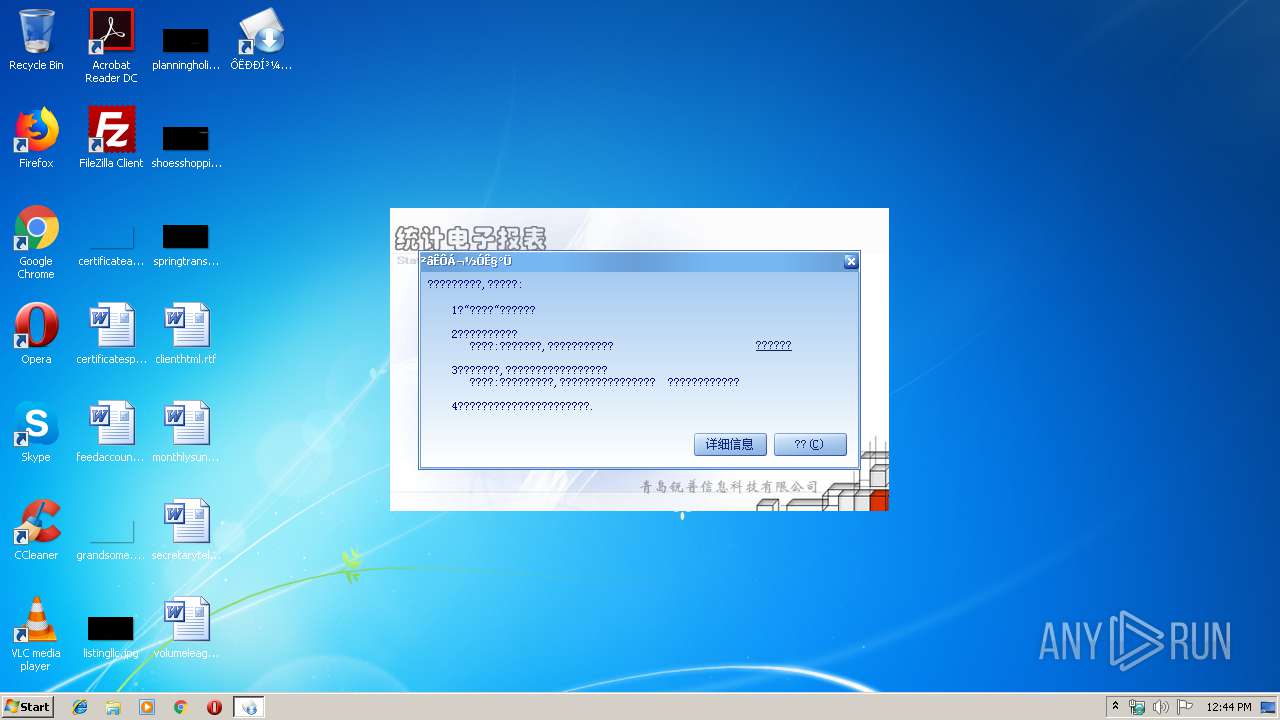
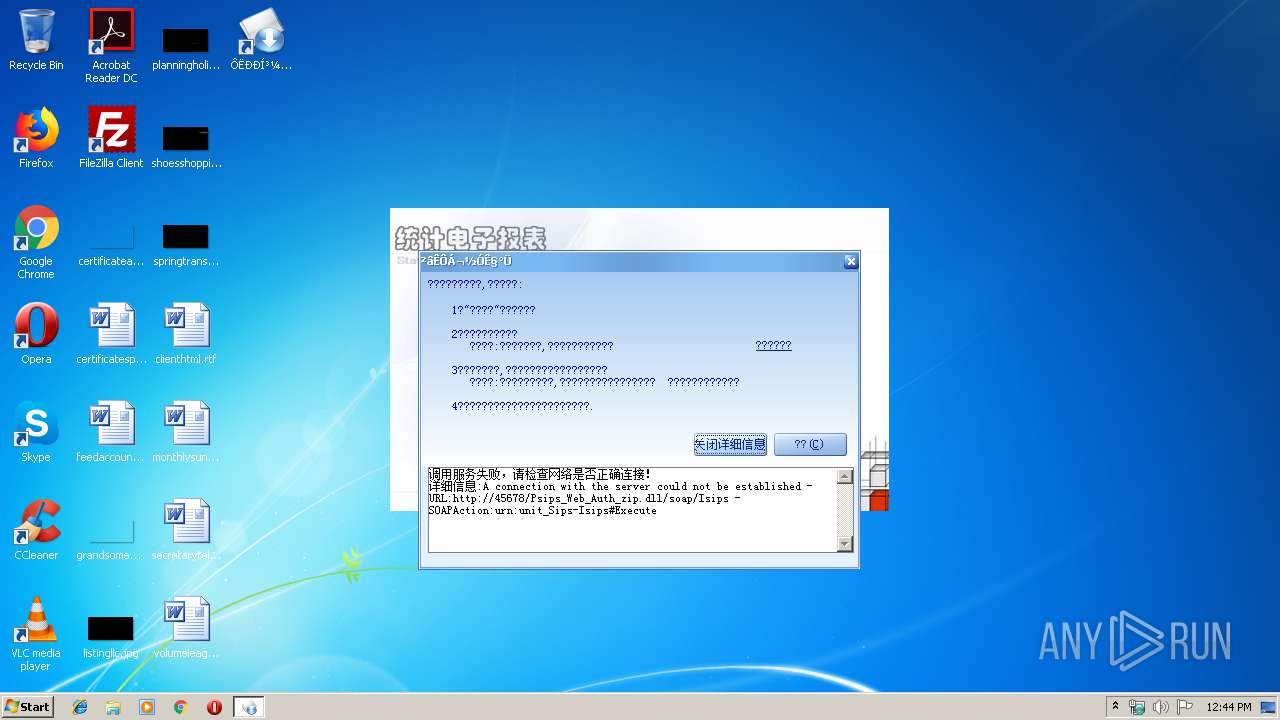
| 3948 | "C:\Program Files\ͳ¼ÆÍøÉÏÖ±±¨\P_Sips_Client_CA.exe" | C:\Program Files\ͳ¼ÆÍøÉÏÖ±±¨\P_Sips_Client_CA.exe | wsetup.exe | ||||||||||||
User: admin Company: 青岛锐普信息科技 Integrity Level: HIGH Exit code: 0 Version: 5.0.0.10 Modules
| |||||||||||||||
Total events
472
Read events
409
Write events
63
Delete events
0
Modification events
| (PID) Process: | (3436) wsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\YingSoft\YingInstall |
| Operation: | write | Name: | LastVersion |
Value: 5.81 | |||
| (PID) Process: | (3648) Regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{539A09D9-2C56-4EC8-91C5-7C394B14FA95}\1.0 |
| Operation: | write | Name: | |
Value: SdcaTsa ActiveX Control module | |||
| (PID) Process: | (3648) Regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{539A09D9-2C56-4EC8-91C5-7C394B14FA95}\1.0\FLAGS |
| Operation: | write | Name: | |
Value: 2 | |||
| (PID) Process: | (3648) Regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{539A09D9-2C56-4EC8-91C5-7C394B14FA95}\1.0\0\win32 |
| Operation: | write | Name: | |
Value: C:\Windows\SdcaTsa.ocx | |||
| (PID) Process: | (3648) Regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{539A09D9-2C56-4EC8-91C5-7C394B14FA95}\1.0\HELPDIR |
| Operation: | write | Name: | |
Value: C:\Windows | |||
| (PID) Process: | (3648) Regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{48C3834F-FE7A-4A56-B5AF-1A4EC5371546} |
| Operation: | write | Name: | |
Value: _DSdcaTsa | |||
| (PID) Process: | (3648) Regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{48C3834F-FE7A-4A56-B5AF-1A4EC5371546}\ProxyStubClsid |
| Operation: | write | Name: | |
Value: {00020420-0000-0000-C000-000000000046} | |||
| (PID) Process: | (3648) Regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{48C3834F-FE7A-4A56-B5AF-1A4EC5371546}\ProxyStubClsid32 |
| Operation: | write | Name: | |
Value: {00020420-0000-0000-C000-000000000046} | |||
| (PID) Process: | (3648) Regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{48C3834F-FE7A-4A56-B5AF-1A4EC5371546}\TypeLib |
| Operation: | write | Name: | |
Value: {539A09D9-2C56-4EC8-91C5-7C394B14FA95} | |||
| (PID) Process: | (3648) Regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{48C3834F-FE7A-4A56-B5AF-1A4EC5371546}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.0 | |||
Executable files
10
Suspicious files
0
Text files
6
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3436 | wsetup.exe | C:\Windows\system32\YingInstall\409.ini | text | |
MD5:— | SHA256:— | |||
| 3436 | wsetup.exe | C:\Users\admin\AppData\Local\Temp\YingInstall20190718124404647.xml | xml | |
MD5:— | SHA256:— | |||
| 3436 | wsetup.exe | C:\Users\admin\AppData\Local\Temp\20190718124404647~YingInstall-TopFramePicture.bmp | image | |
MD5:3484D86629E1919532FFC79725C9CAA2 | SHA256:51AC8618CE8C51B73FE0439C1997BCA3F6CAF7D9BF50AD2F2330A8C10E37ECFC | |||
| 3436 | wsetup.exe | C:\Windows\Ying-UnInstall.exe | executable | |
MD5:— | SHA256:— | |||
| 3436 | wsetup.exe | C:\Windows\sdcatsaclient.dll | executable | |
MD5:— | SHA256:— | |||
| 3436 | wsetup.exe | C:\Users\admin\AppData\Local\Temp\20190718124404647~YingInstall-WelcomeWndPicture.bmp | image | |
MD5:890E7011519B59C41ECB2C94035C2179 | SHA256:3B1A1E3D46F1AE4F81ADFC4E93F929F26537983CF245B45CB92E3B9444B2E056 | |||
| 3436 | wsetup.exe | C:\Windows\jca30api.dll | executable | |
MD5:— | SHA256:— | |||
| 3436 | wsetup.exe | C:\Windows\SdcaTsa.ocx | executable | |
MD5:— | SHA256:— | |||
| 3436 | wsetup.exe | C:\Windows\JITSecurityTool.ocx | executable | |
MD5:— | SHA256:— | |||
| 3436 | wsetup.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\ͳ¼ÆÍøÉÏÖ±±¨\ÔËÐÐͳ¼ÆÍøÉÏÖ±±¨.Lnk | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report