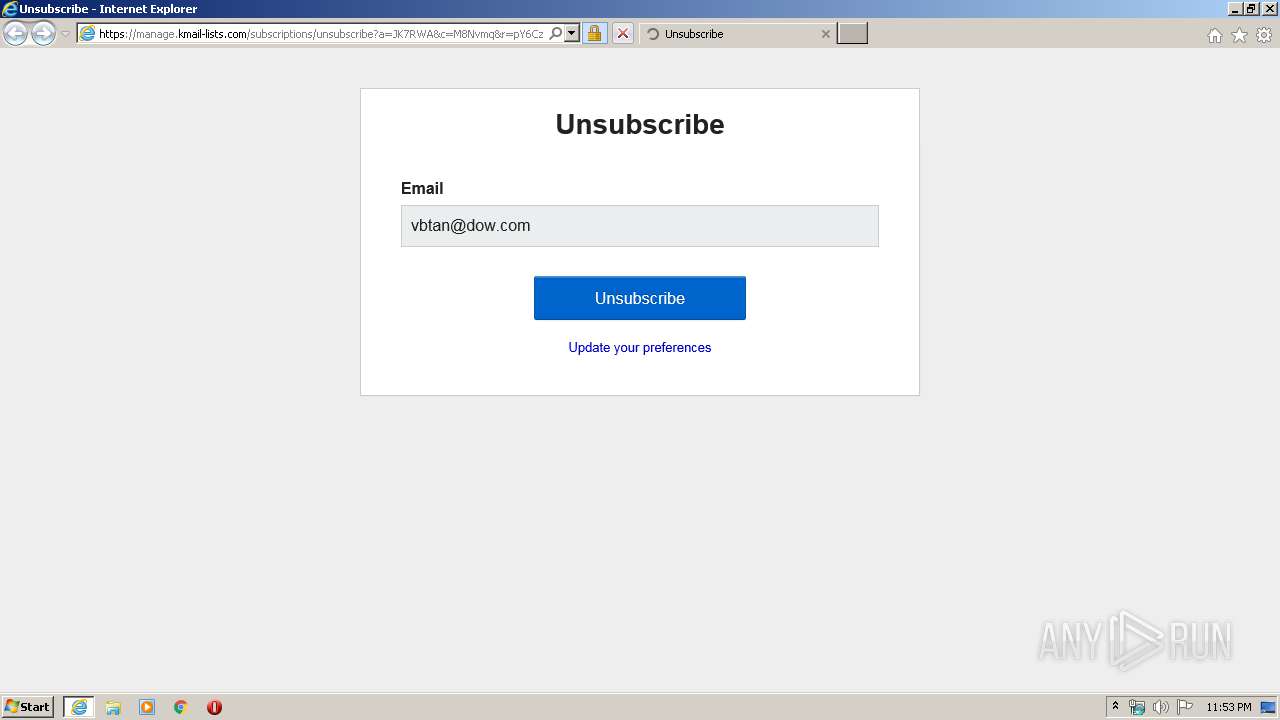
| URL: | https://manage.kmail-lists.com/subscriptions/unsubscribe?a=JK7RWA&c=M8Nvmq&r=pY6Czh2&m=J6CHhv&k=1f4fba13cb66579d2f93f79f383096d9 |
| Full analysis: | https://app.any.run/tasks/0de1aaf5-2785-4e2e-9009-e82238578dcc |
| Verdict: | Malicious activity |
| Analysis date: | March 22, 2020, 23:53:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 079952C5E54B6B82EA96EF07B5425486 |
| SHA1: | E5A36945023B357CC055B4C7C418D59C92575955 |
| SHA256: | A4CD2A97F1F06DEE59B50779BE1EA150F2B7D02B0EB56CAF460F528BFD779AD8 |
| SSDEEP: | 3:N8EXO5IISLdIKWQHWAKWLrlC1zxCoNTI7TS5DlH/YXvvDdVic:2EXE1SkSWwGqT+/6vvj/ |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Changes internet zones settings
- iexplore.exe (PID: 3376)
Reads Internet Cache Settings
- iexplore.exe (PID: 3376)
- iexplore.exe (PID: 2824)
Creates files in the user directory
- iexplore.exe (PID: 2824)
Reads internet explorer settings
- iexplore.exe (PID: 2824)
Reads settings of System Certificates
- iexplore.exe (PID: 2824)
- iexplore.exe (PID: 3376)
Changes settings of System certificates
- iexplore.exe (PID: 3376)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3376)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2824 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3376 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3376 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://manage.kmail-lists.com/subscriptions/unsubscribe?a=JK7RWA&c=M8Nvmq&r=pY6Czh2&m=J6CHhv&k=1f4fba13cb66579d2f93f79f383096d9" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
6 132
Read events
922
Write events
3 491
Delete events
1 719
Modification events
| (PID) Process: | (3376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 724867840 | |||
| (PID) Process: | (3376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30802085 | |||
| (PID) Process: | (3376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3376) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
132
Text files
90
Unknown types
82
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2824 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab6308.tmp | — | |
MD5:— | SHA256:— | |||
| 2824 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar6309.tmp | — | |
MD5:— | SHA256:— | |||
| 2824 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\5457A8CE4B2A7499F8299A013B6E1C7C_CE50F893881D43DC0C815E4D80FAF2B4 | der | |
MD5:6F902BC0A5ABB6957A6C2B4360CD2884 | SHA256:E4918B66F842D94BD2C1D022EEE41E9D3518F0F412EBE25AB6BFD5B3AF7AFF52 | |||
| 2824 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\5457A8CE4B2A7499F8299A013B6E1C7C_CE50F893881D43DC0C815E4D80FAF2B4 | binary | |
MD5:1469D98C57DB720CA55CFAFDCB40A09B | SHA256:9706C34D05404BFB44E51F52CC138CD372B0D76AC6D48D7C1C42D3D8E9CA46E1 | |||
| 2824 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\unsubscribe[1].htm | html | |
MD5:BF75621C206FDCD8C63BACD82EAF7D54 | SHA256:1422BCF3FA62F7451ED519ABF853310259BE75E22D9EDD6605139E9F444B0F2B | |||
| 2824 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\1BB09BEEC155258835C193A7AA85AA5B_1B18E262D1AECEAF06A52D9CE6C43BBF | binary | |
MD5:B89F952E5E33C388E5320D49FDABC6E1 | SHA256:0195E0E2CF7B2843E34134C875B21A2575EA744BD01091A8A90997003021D762 | |||
| 2824 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\straps[1].css | text | |
MD5:1D0B4BB2A82A40DBD5D90E13F555F87E | SHA256:ABF983ECE33265DA6036FDAF85EB2967BB4CB0912050A348CE414FDAD67126FC | |||
| 2824 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\5080DC7A65DB6A5960ECD874088F3328_6CBA2C06D5985DD95AE59AF8FC7C6220 | binary | |
MD5:5979112ECFCFD950669DCC8EFDFD9146 | SHA256:CD24A866CAA026F88D52A6F130F7CA300F970DA6918D94B1DBF658E3D9AB2947 | |||
| 2824 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\5080DC7A65DB6A5960ECD874088F3328_6CBA2C06D5985DD95AE59AF8FC7C6220 | der | |
MD5:B57F51BF1A6B9DFA0C9069818DD93EB5 | SHA256:19DB09298B176432EE1549AB735694984147DA32FABB2C48193E4D01D47AB59A | |||
| 2824 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\1BB09BEEC155258835C193A7AA85AA5B_1B18E262D1AECEAF06A52D9CE6C43BBF | der | |
MD5:8350CA32AC3191B7CC7062D4513A05E4 | SHA256:FF34FFE933A12E18635287CC639F120A82B20198A93A1FB92C08E76247C78F02 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
71
TCP/UDP connections
125
DNS requests
53
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2824 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCECsuburZdTZsFIpu26N8jAc%3D | US | der | 727 b | whitelisted |
2824 | iexplore.exe | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2824 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCECdm7lbrSfOOq9dwovyE3iI%3D | US | der | 471 b | whitelisted |
2824 | iexplore.exe | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2824 | iexplore.exe | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEFeh1L3VO0beCAAAAAAyCgc%3D | US | der | 471 b | whitelisted |
2824 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBR64T7ooMQqLLQoy%2BemBUYZQOKh6QQUkK9qOpRaC9iQ6hJWc99DtDoo2ucCEQC1lybgGoEJ83O6kzpkcbRs | US | der | 472 b | whitelisted |
2824 | iexplore.exe | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2824 | iexplore.exe | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDL%2FQslYWVuogIAAAAAXGdc | US | der | 472 b | whitelisted |
2824 | iexplore.exe | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDL%2FQslYWVuogIAAAAAXGdc | US | der | 472 b | whitelisted |
2824 | iexplore.exe | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDL%2FQslYWVuogIAAAAAXGdc | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2824 | iexplore.exe | 3.221.115.252:443 | manage.kmail-lists.com | — | US | unknown |
2824 | iexplore.exe | 216.58.206.8:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
2824 | iexplore.exe | 151.139.128.14:80 | ocsp.usertrust.com | Highwinds Network Group, Inc. | US | suspicious |
2824 | iexplore.exe | 172.217.22.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2824 | iexplore.exe | 216.58.205.227:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3376 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3376 | iexplore.exe | 3.221.115.252:443 | manage.kmail-lists.com | — | US | unknown |
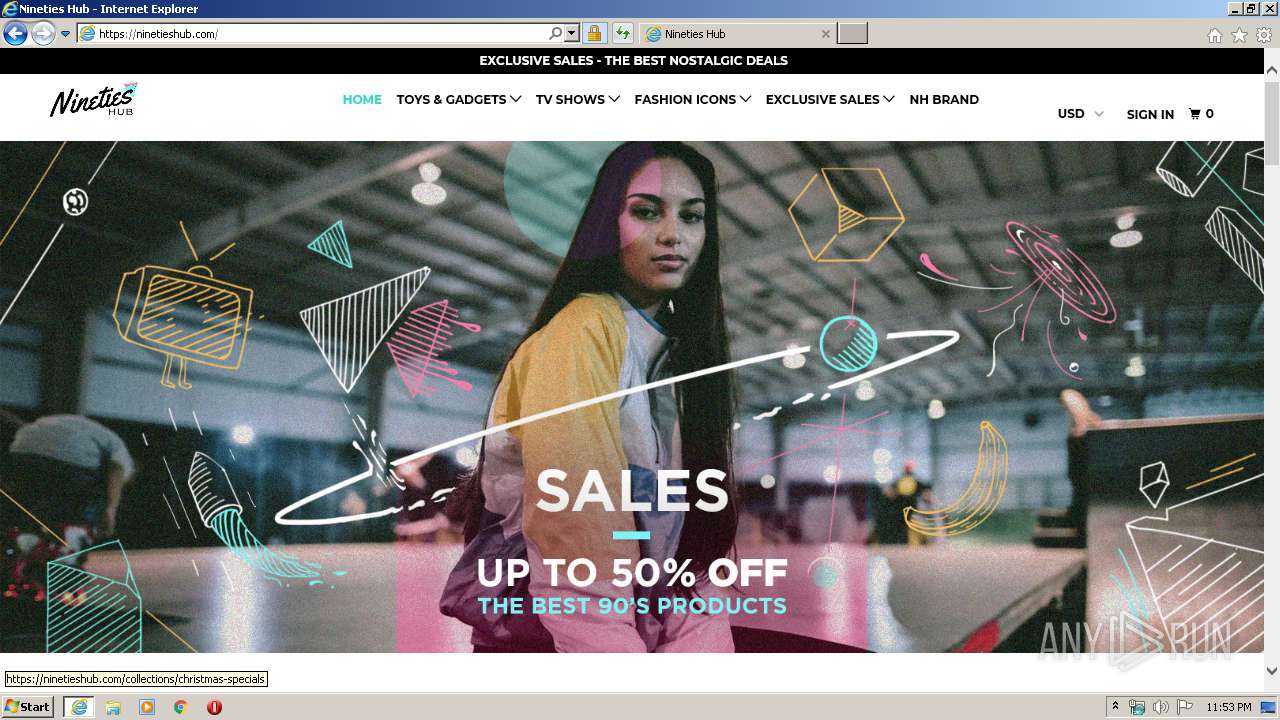
2824 | iexplore.exe | 23.227.38.64:443 | www.ninetieshub.com | Shopify, Inc. | CA | malicious |
2824 | iexplore.exe | 23.227.38.32:443 | ninetieshub.com | Shopify, Inc. | CA | malicious |
2824 | iexplore.exe | 172.217.22.74:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
manage.kmail-lists.com |
| suspicious |
ocsp.usertrust.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.ninetieshub.com |
| malicious |
isrg.trustid.ocsp.identrust.com |
| whitelisted |