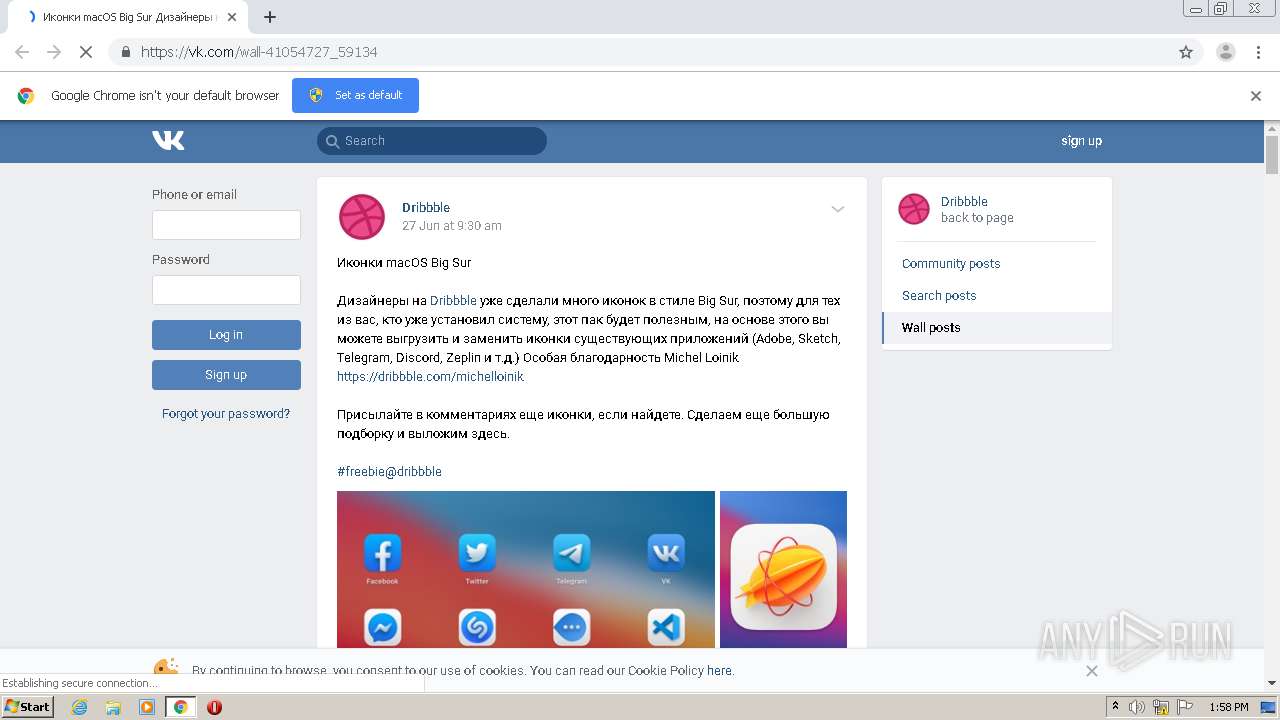
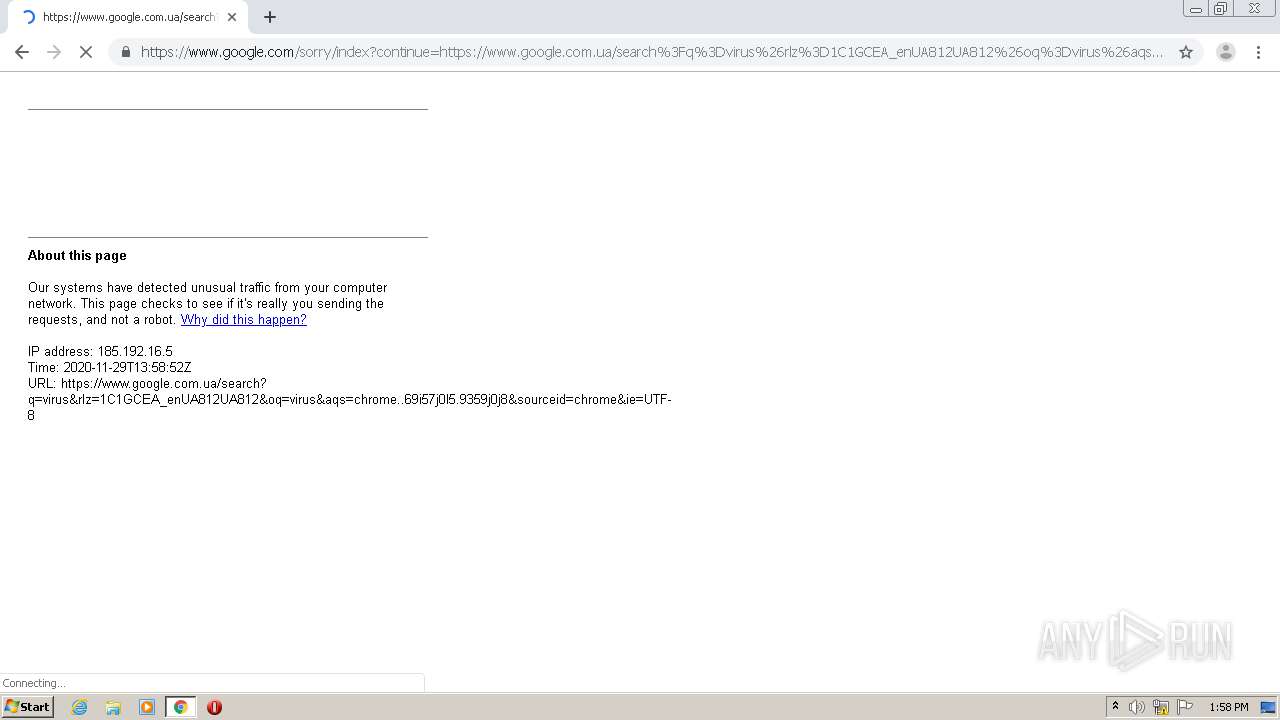
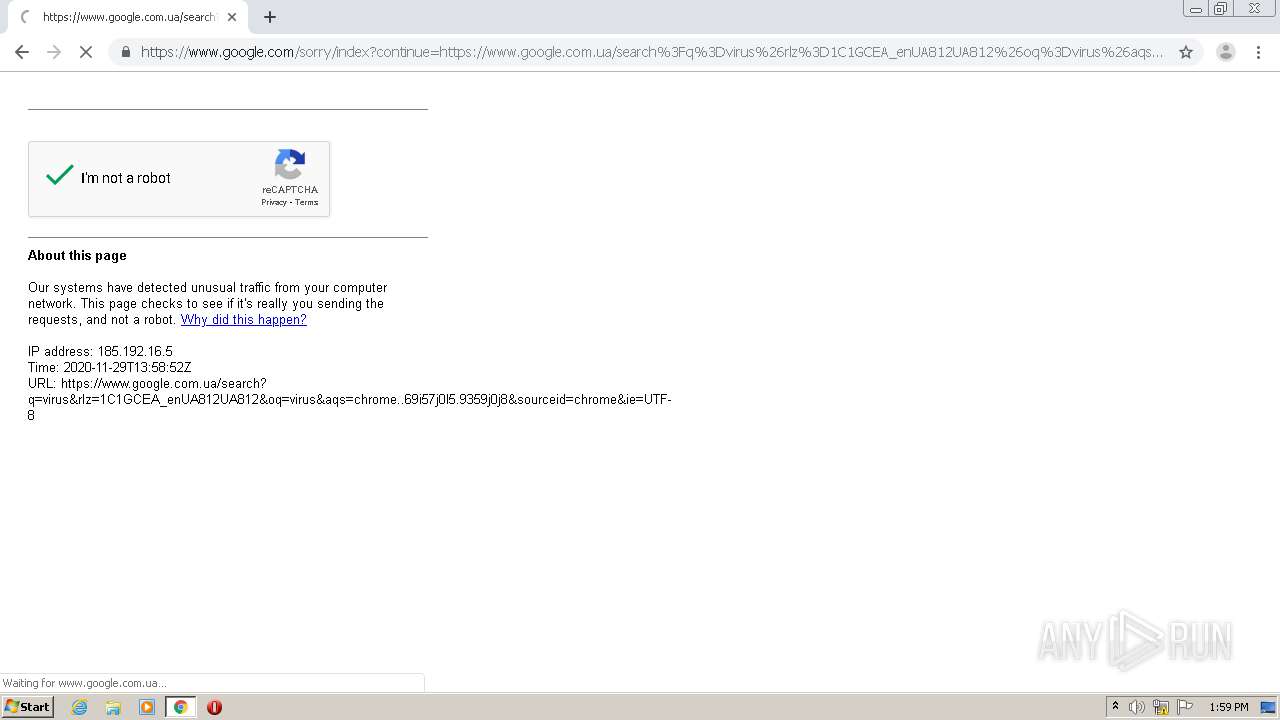
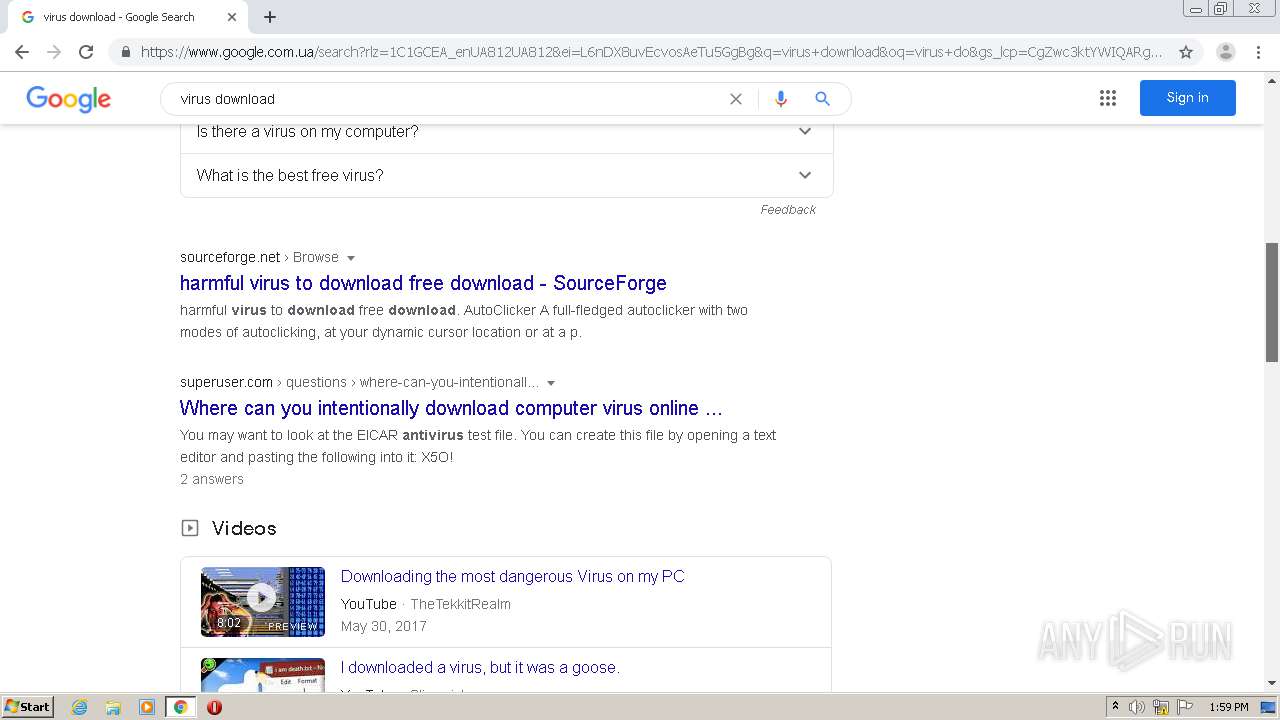
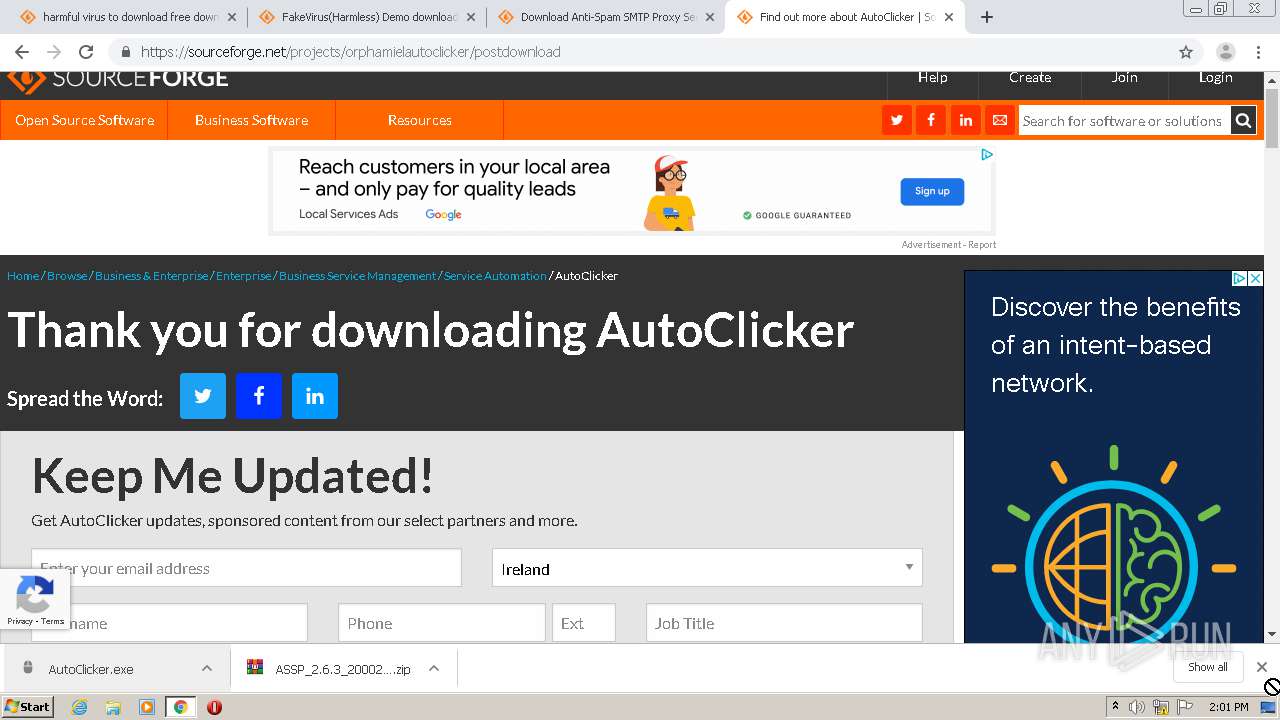
| URL: | https://vk.com/wall-41054727_59134 |
| Full analysis: | https://app.any.run/tasks/fe98dd5e-3189-403b-be1f-45880bd5b347 |
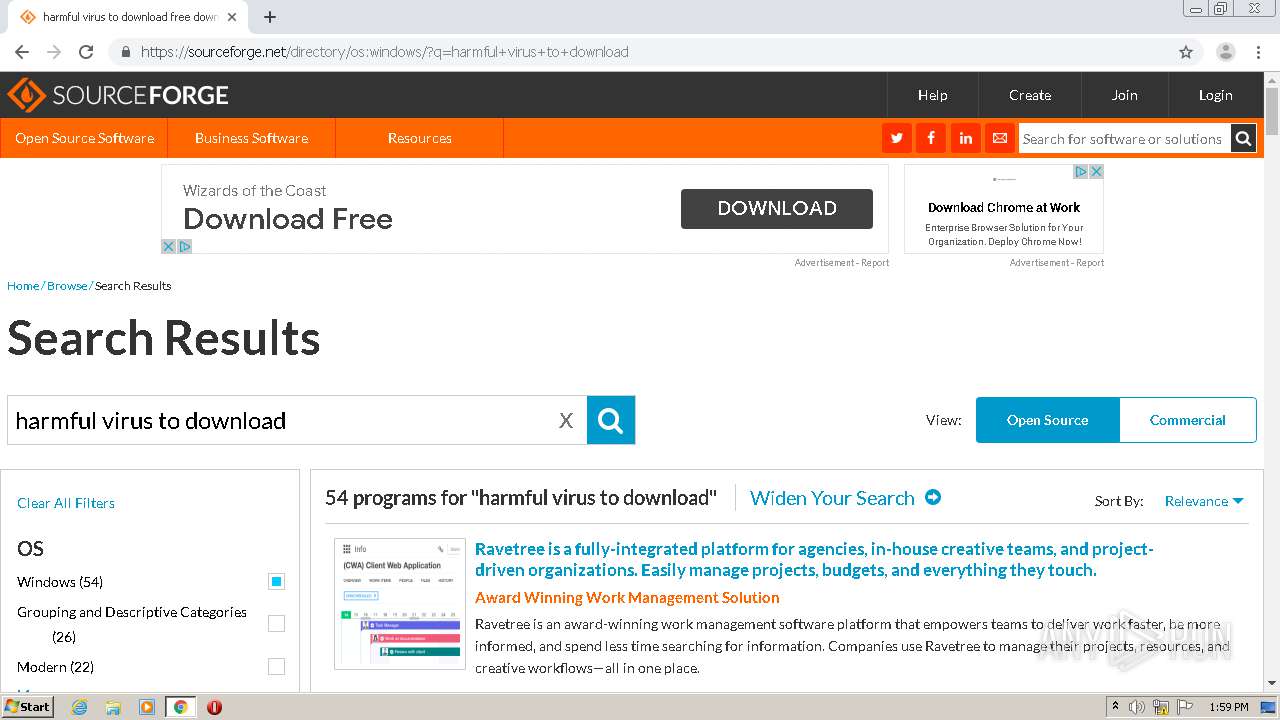
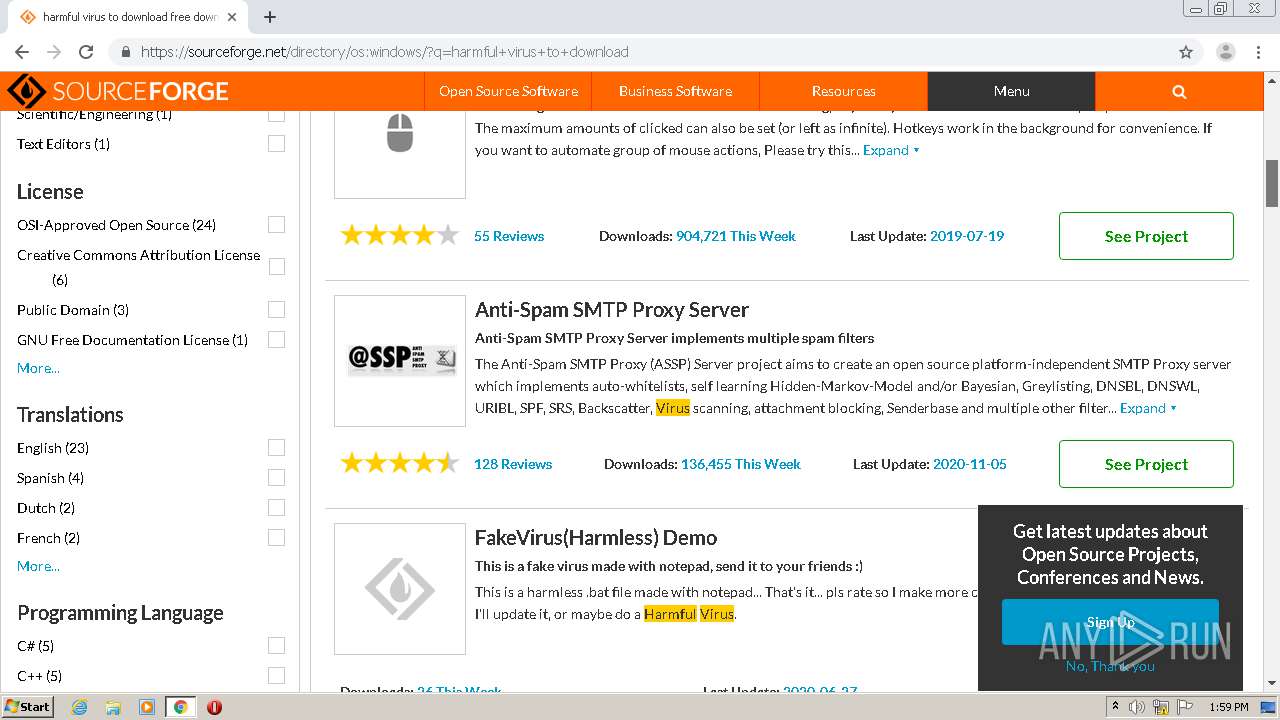
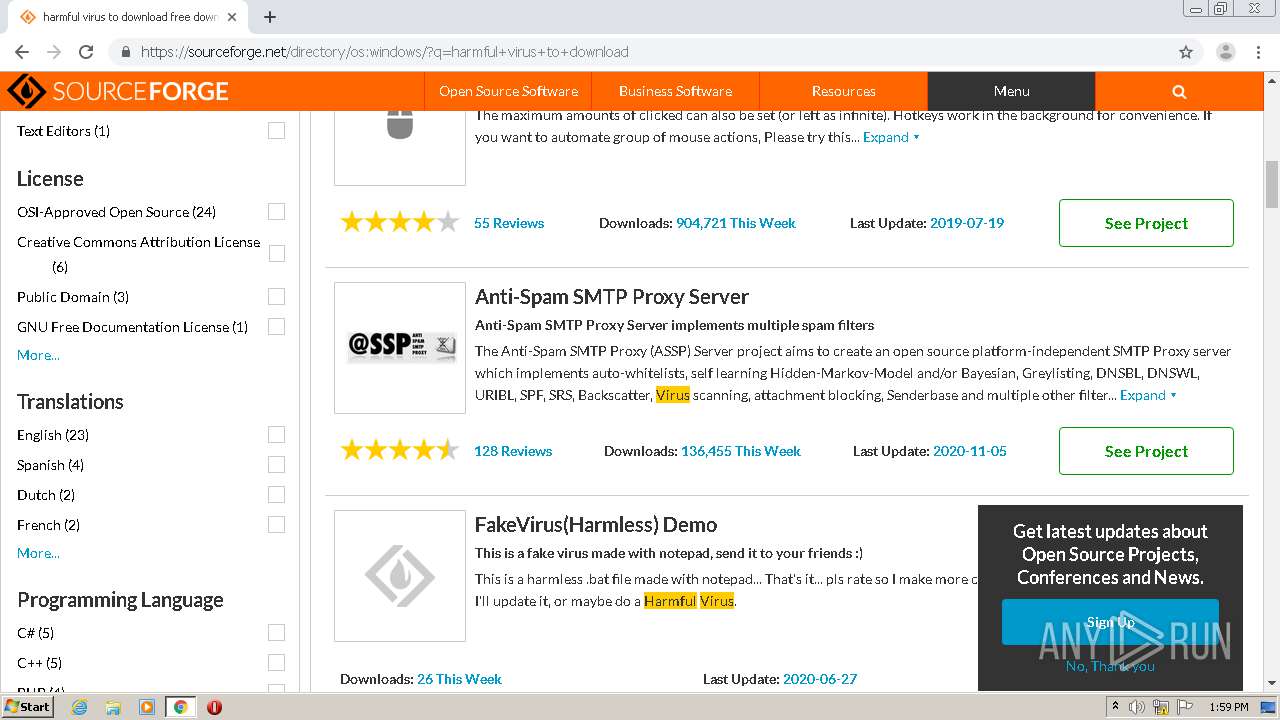
| Verdict: | Malicious activity |
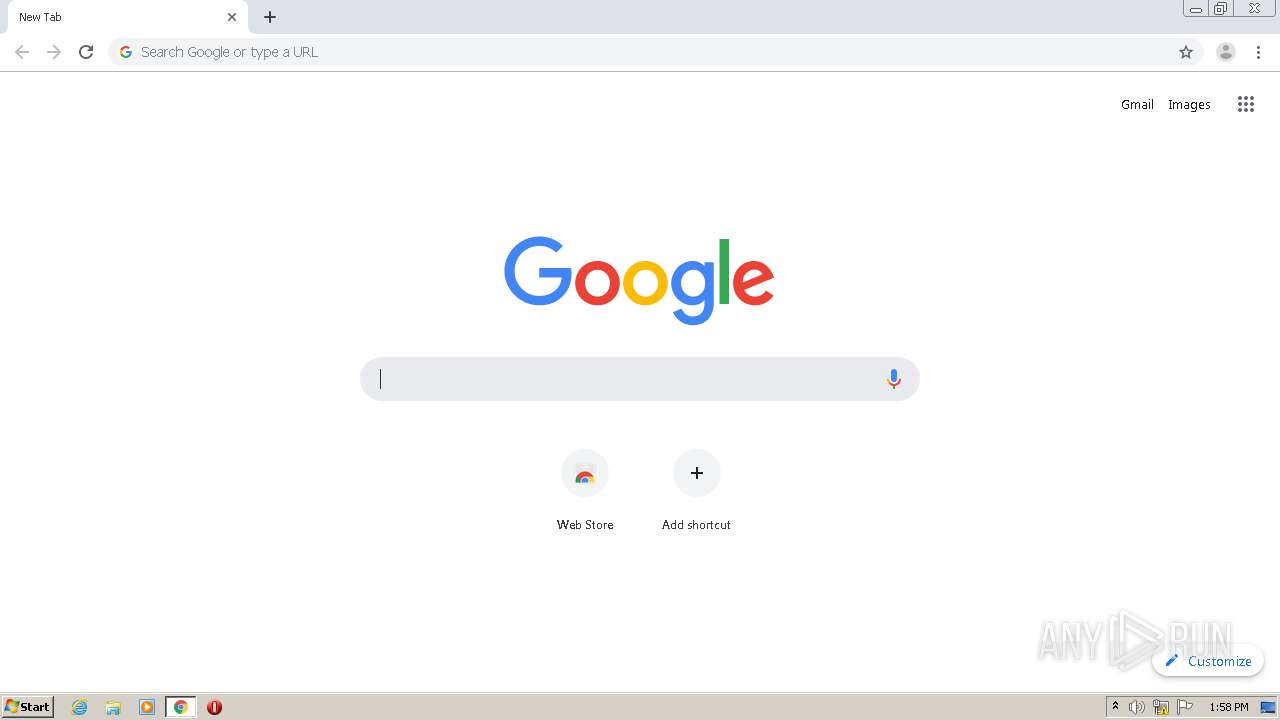
| Analysis date: | November 29, 2020, 13:58:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
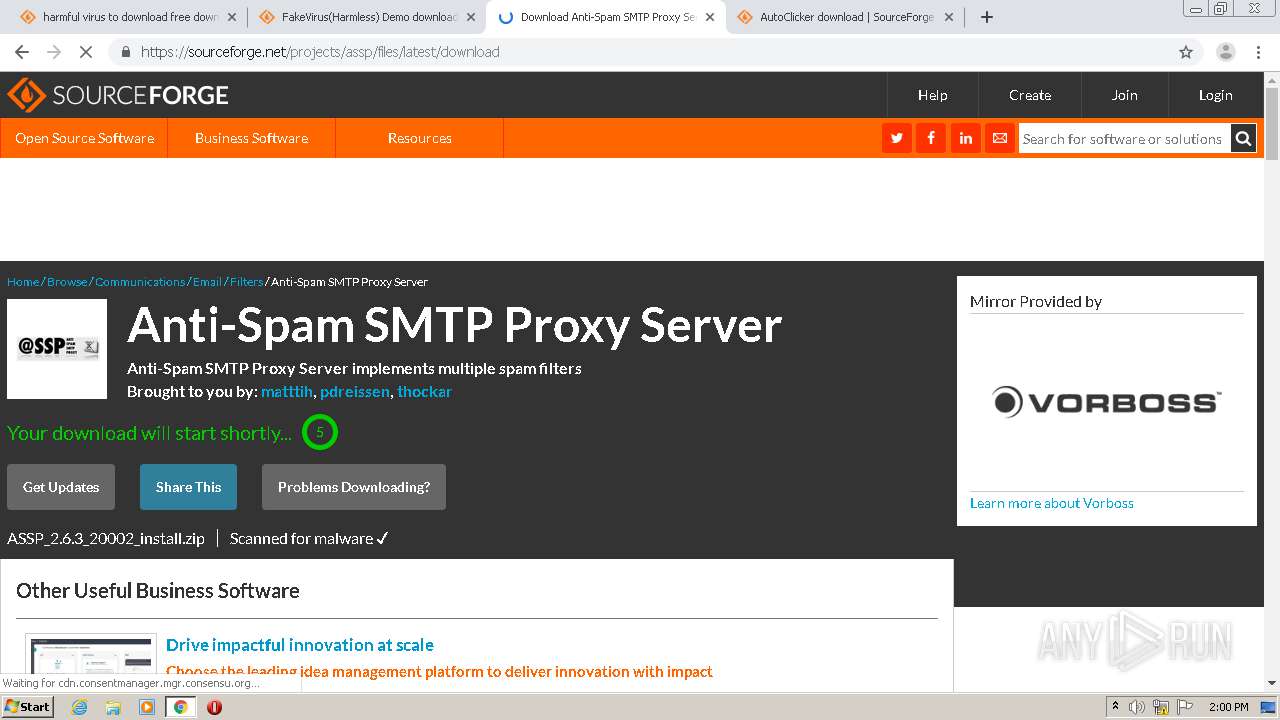
| MD5: | 7A25E61897A444CD5FBB43D7963FB18F |
| SHA1: | 0ED95D6FF01FD8750CF97AA2F9B4BC8E0CBB49E8 |
| SHA256: | A4C3320E6BC9609584A2761C91995175E5080533F59CCF508FC89901925CFF1F |
| SSDEEP: | 3:N8qGKIKNJUW:2FW |
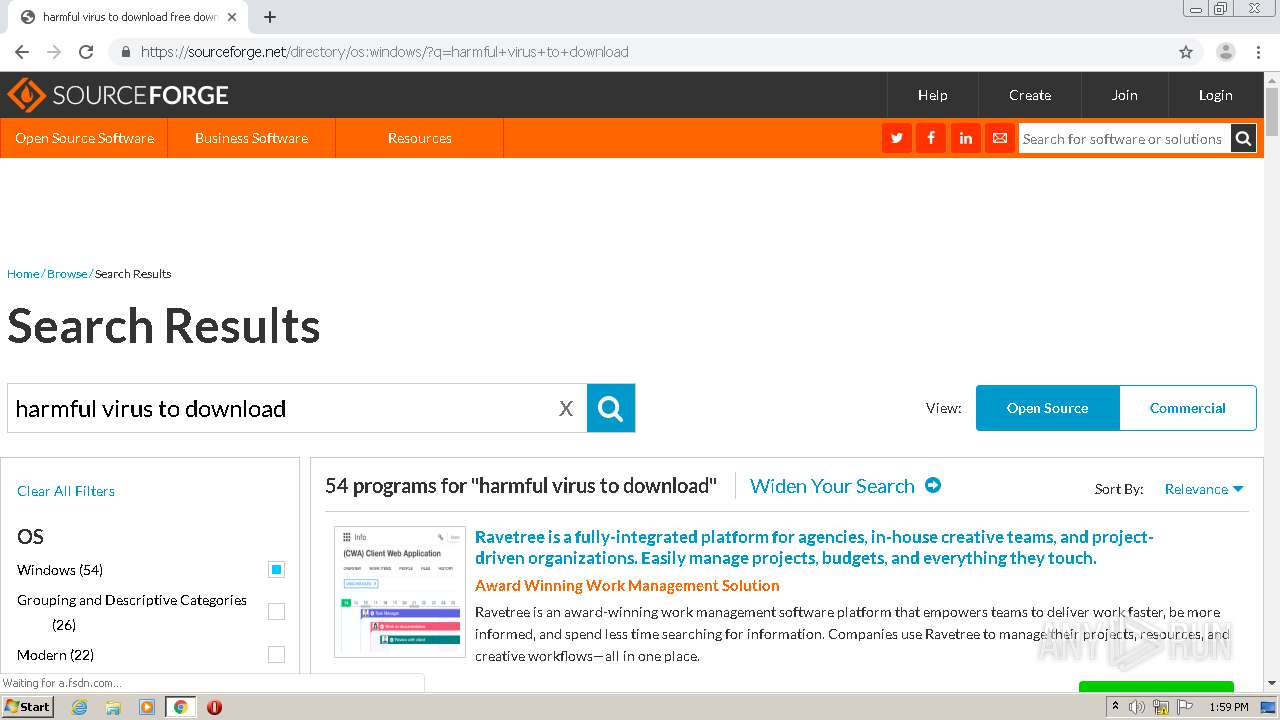
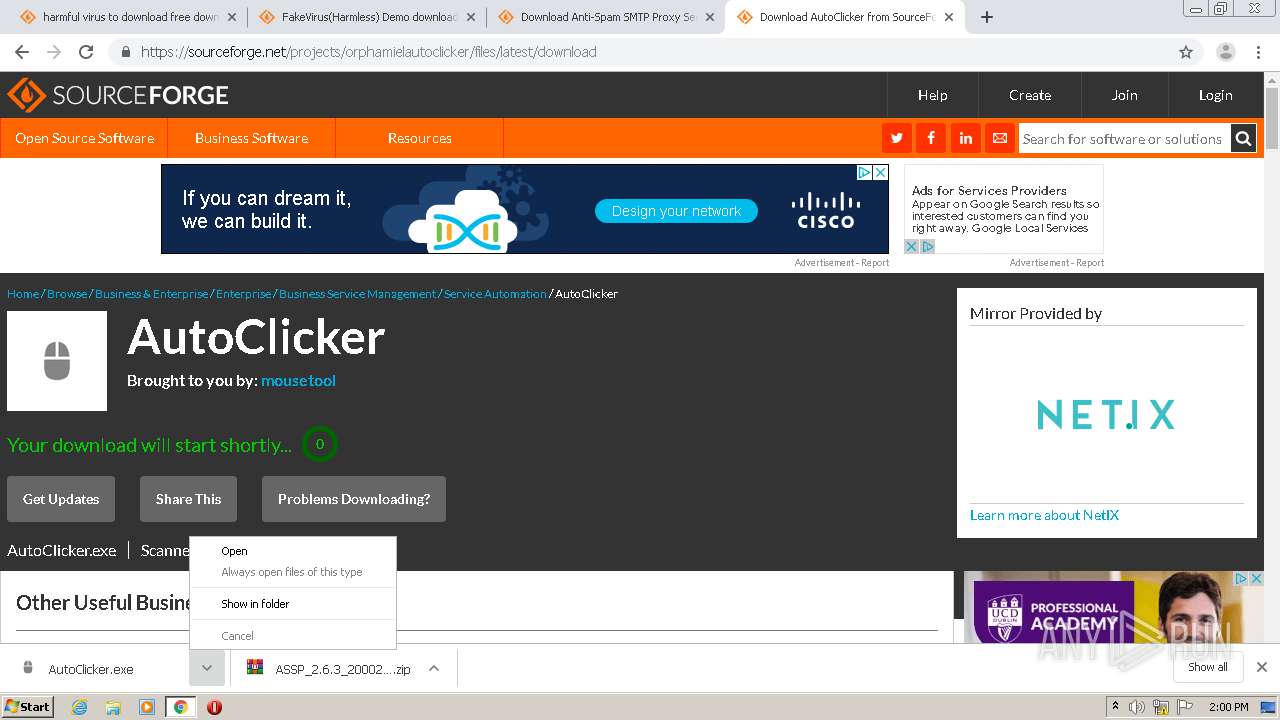
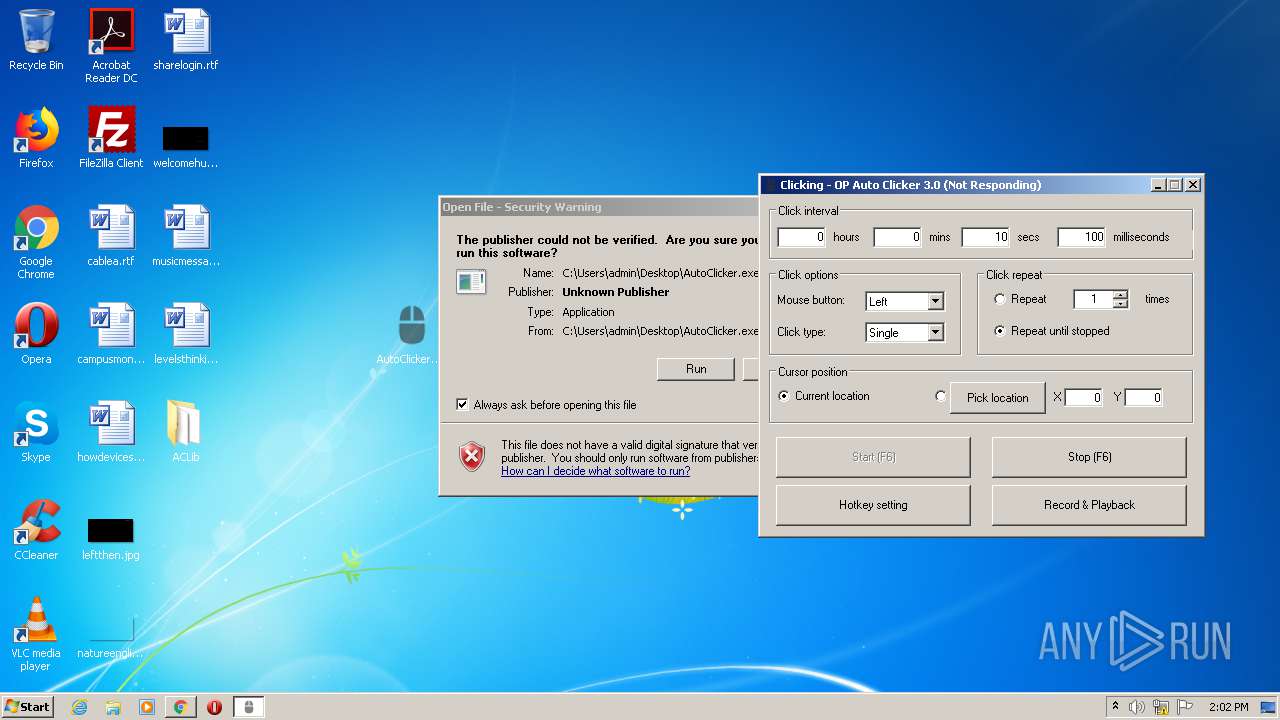
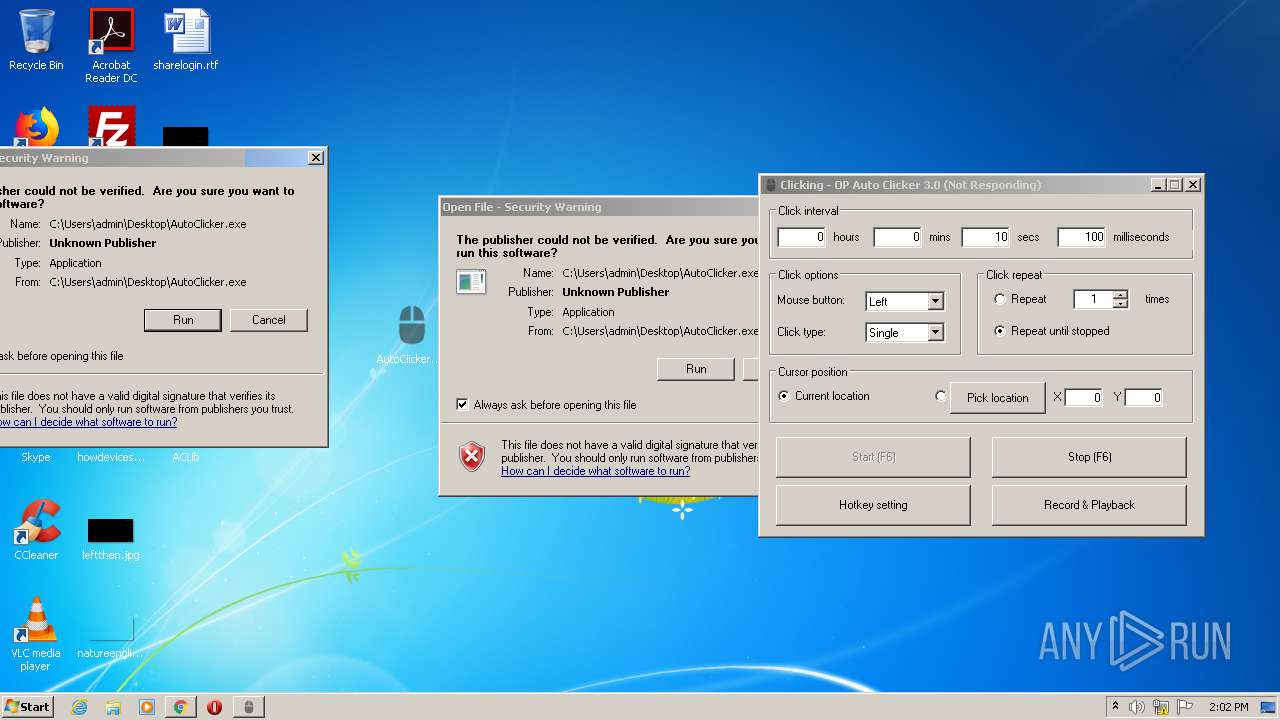
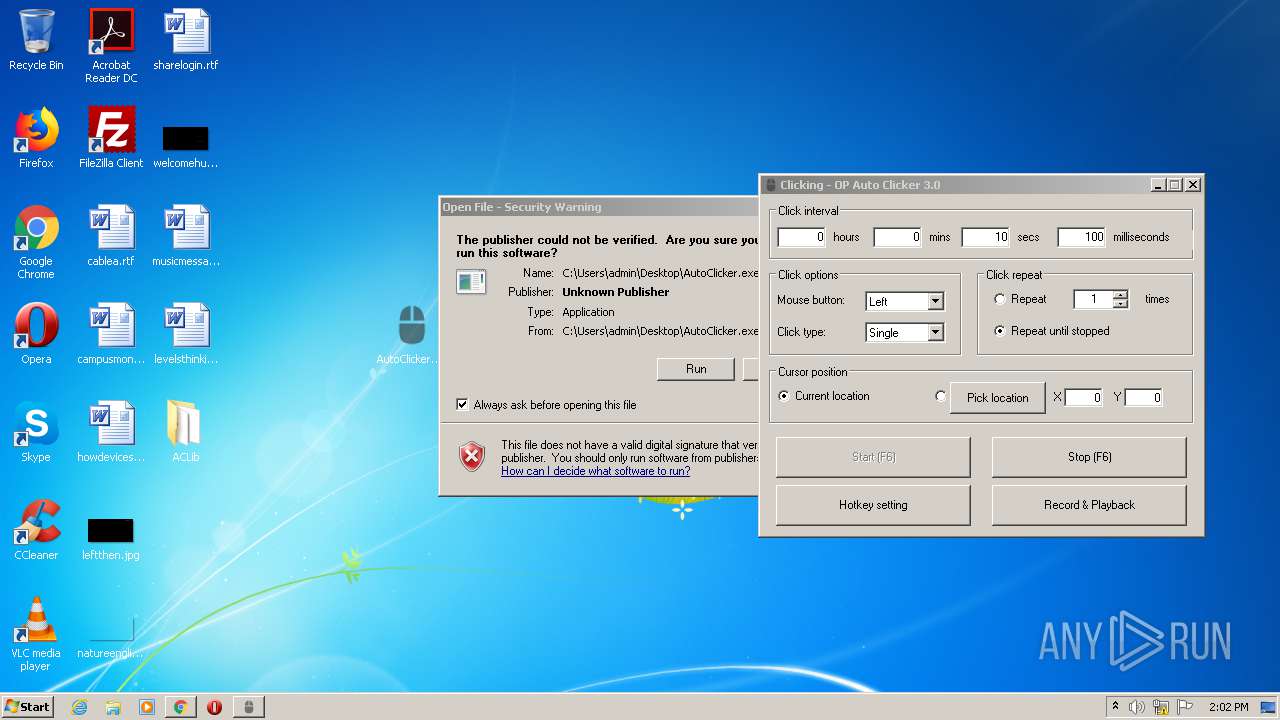
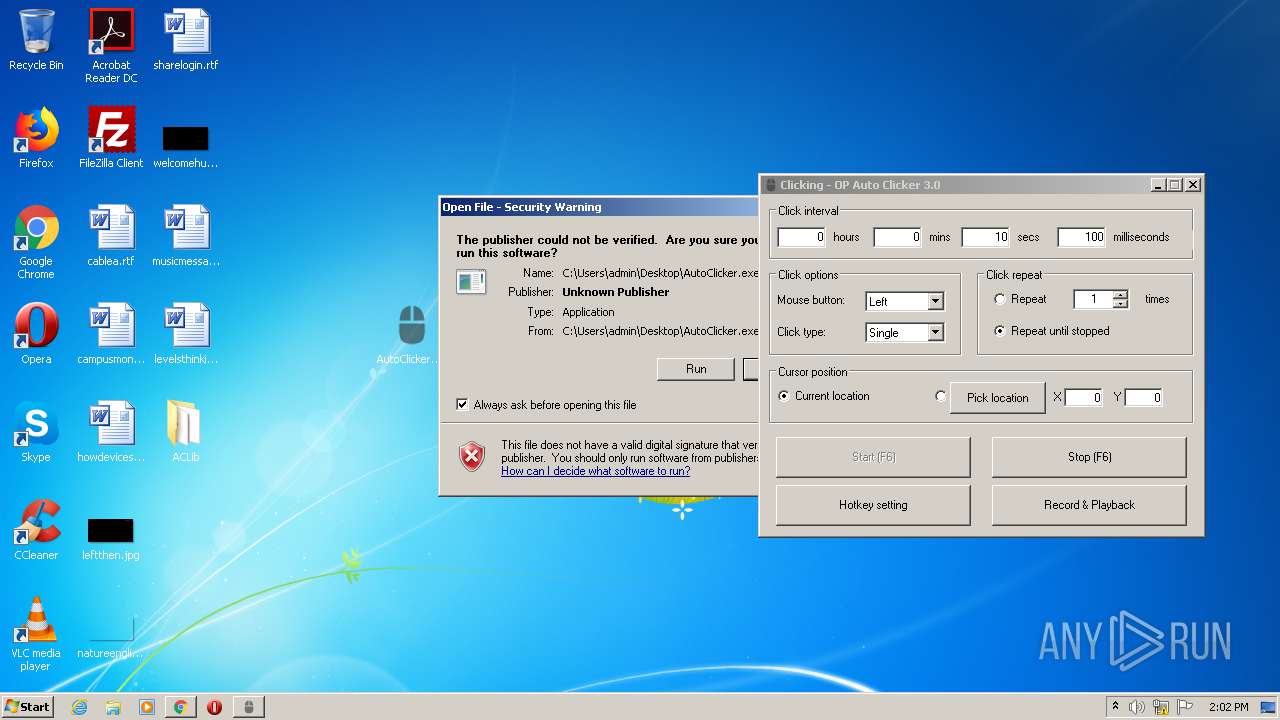
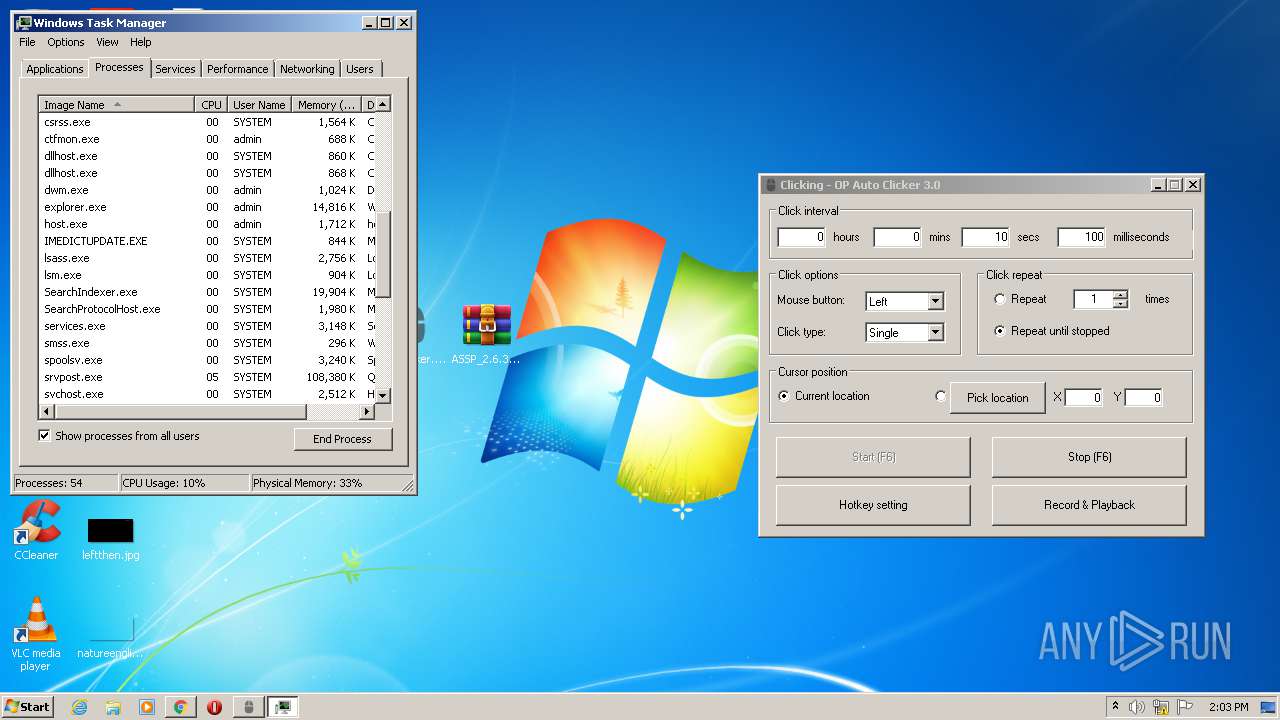
MALICIOUS
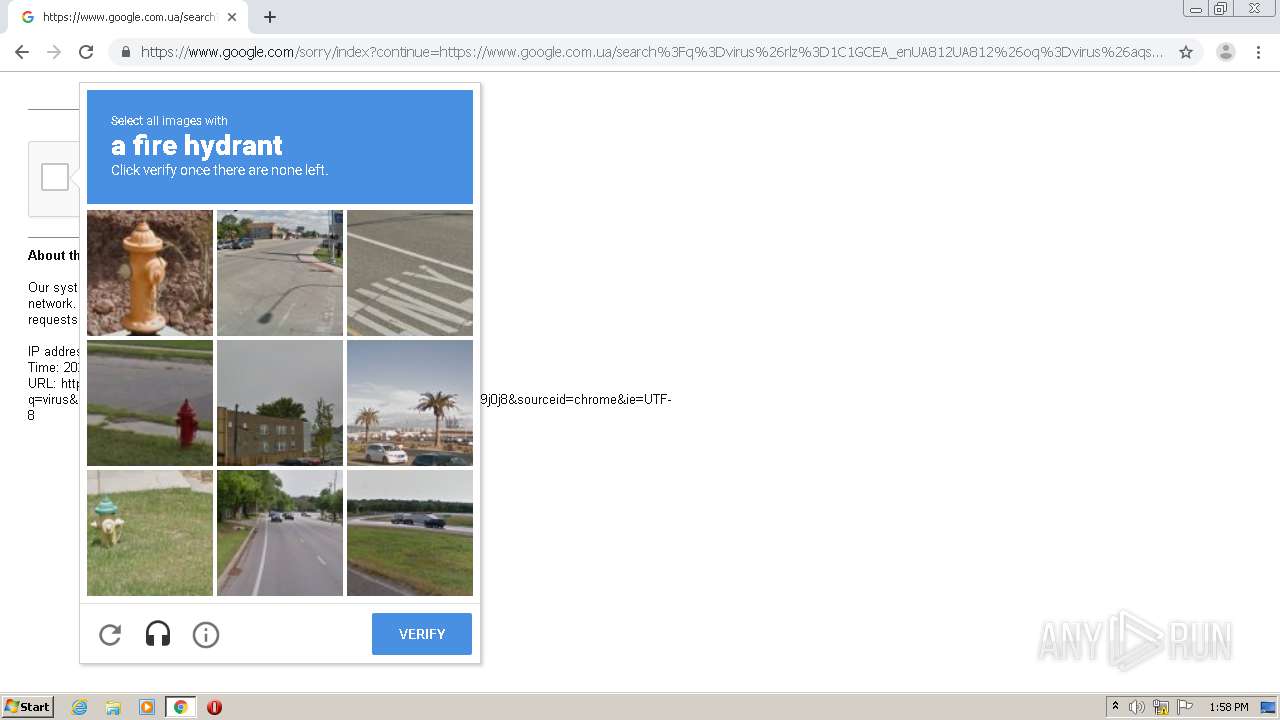
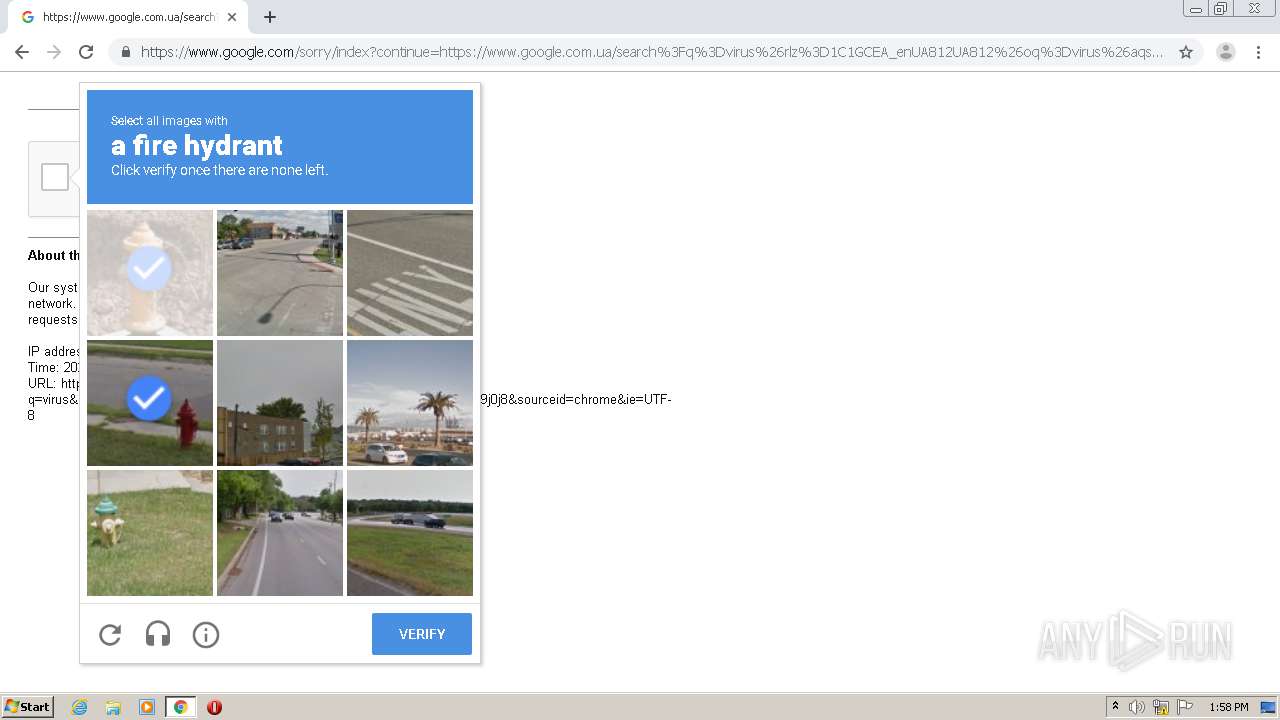
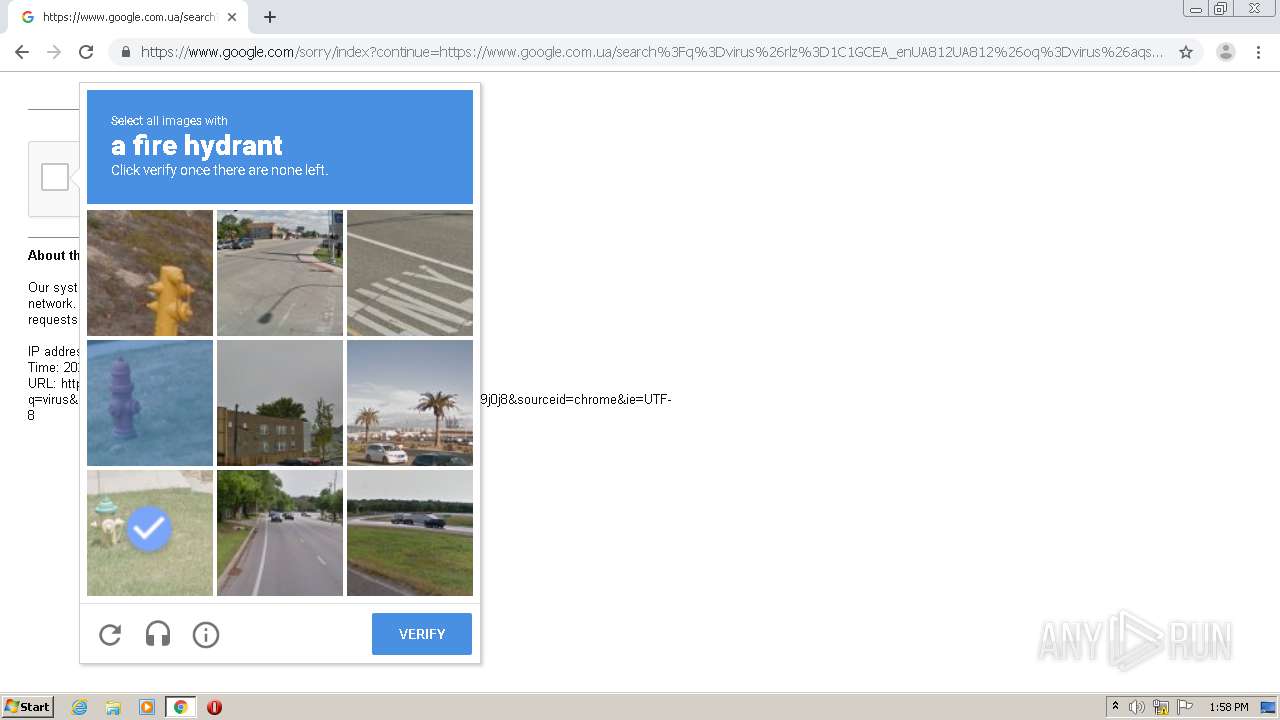
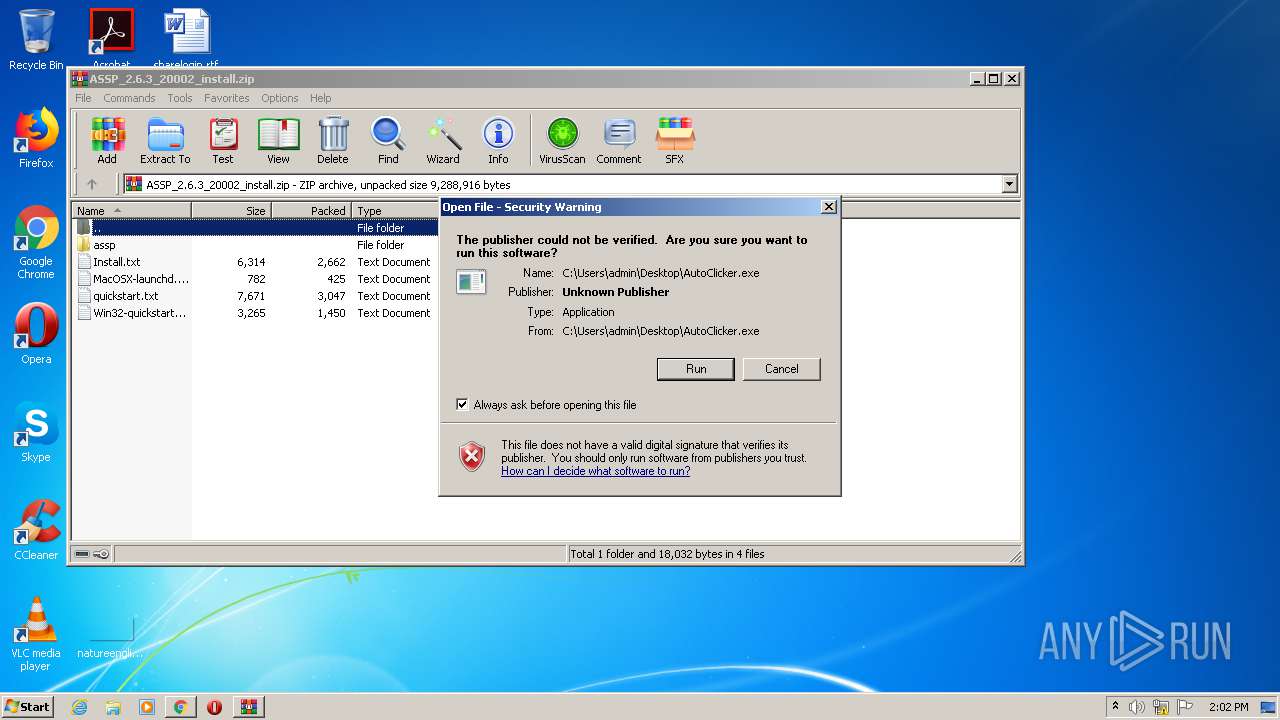
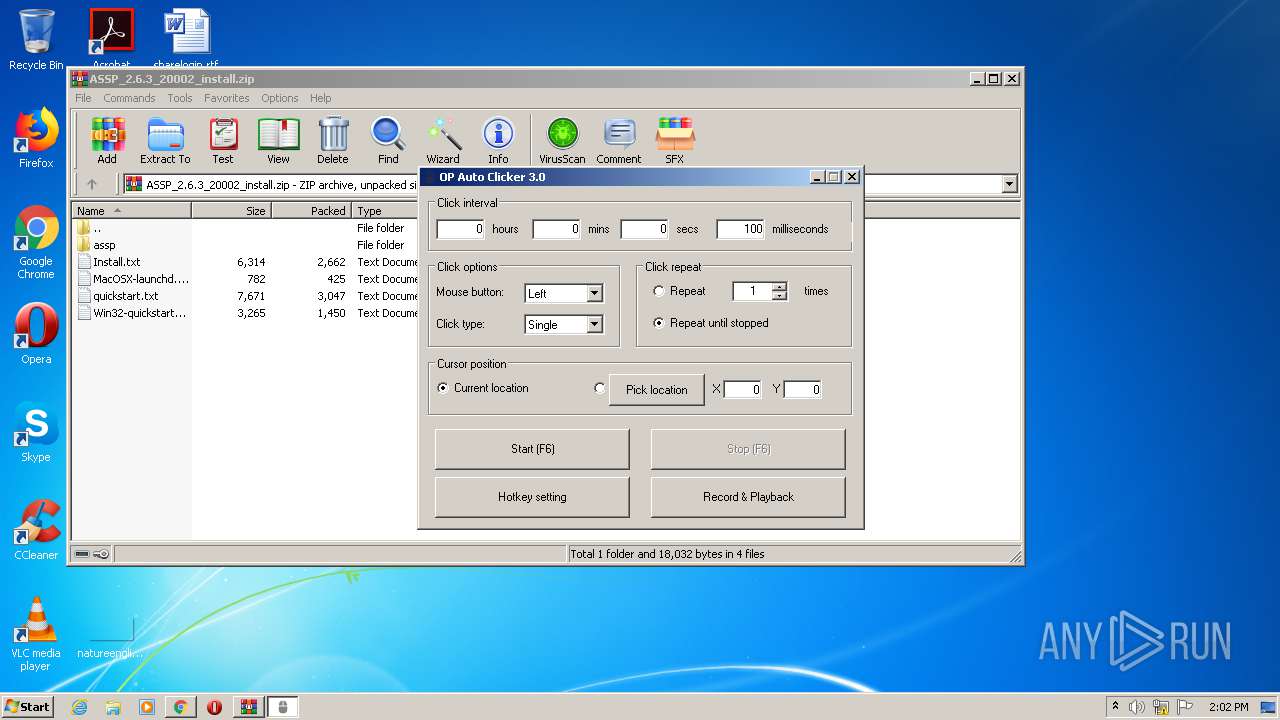
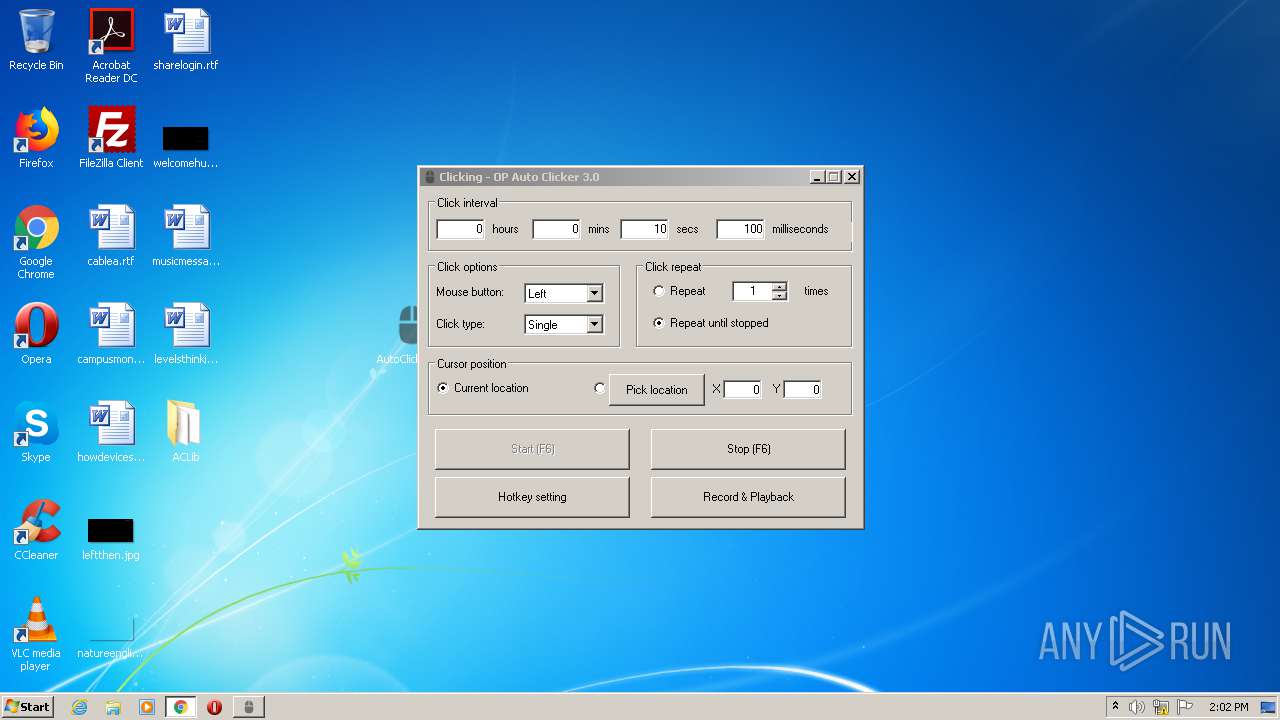
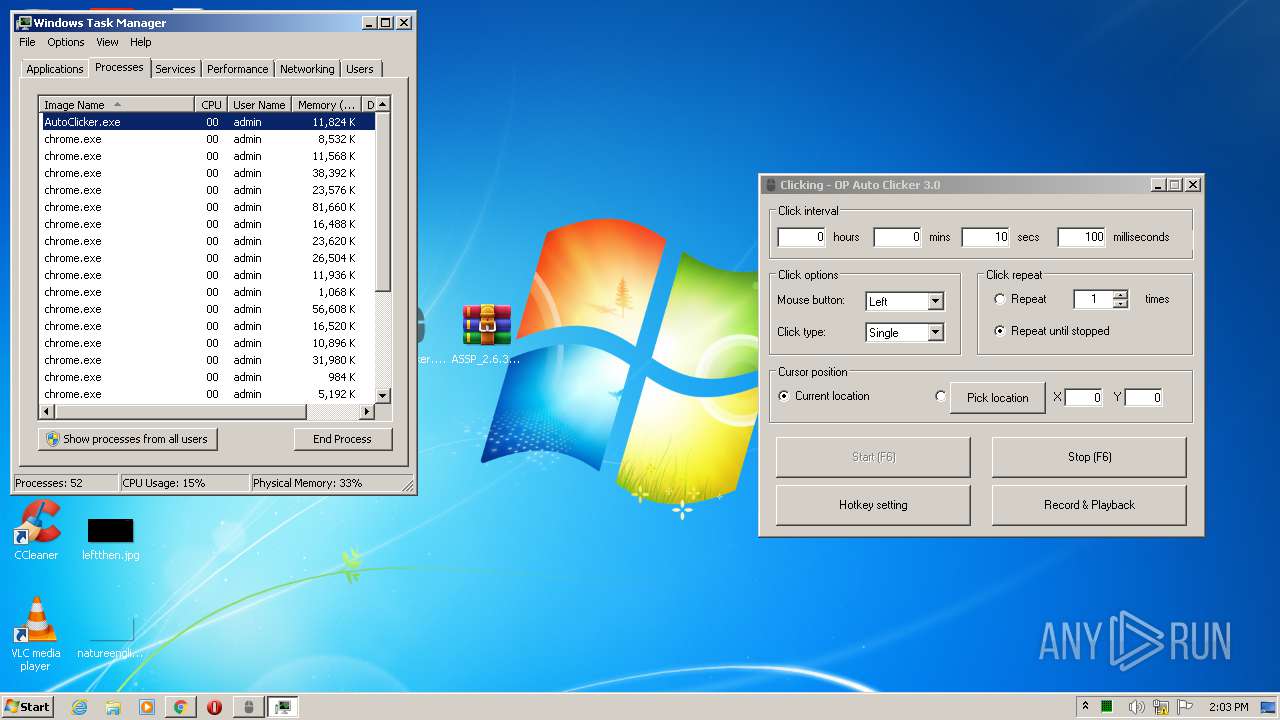
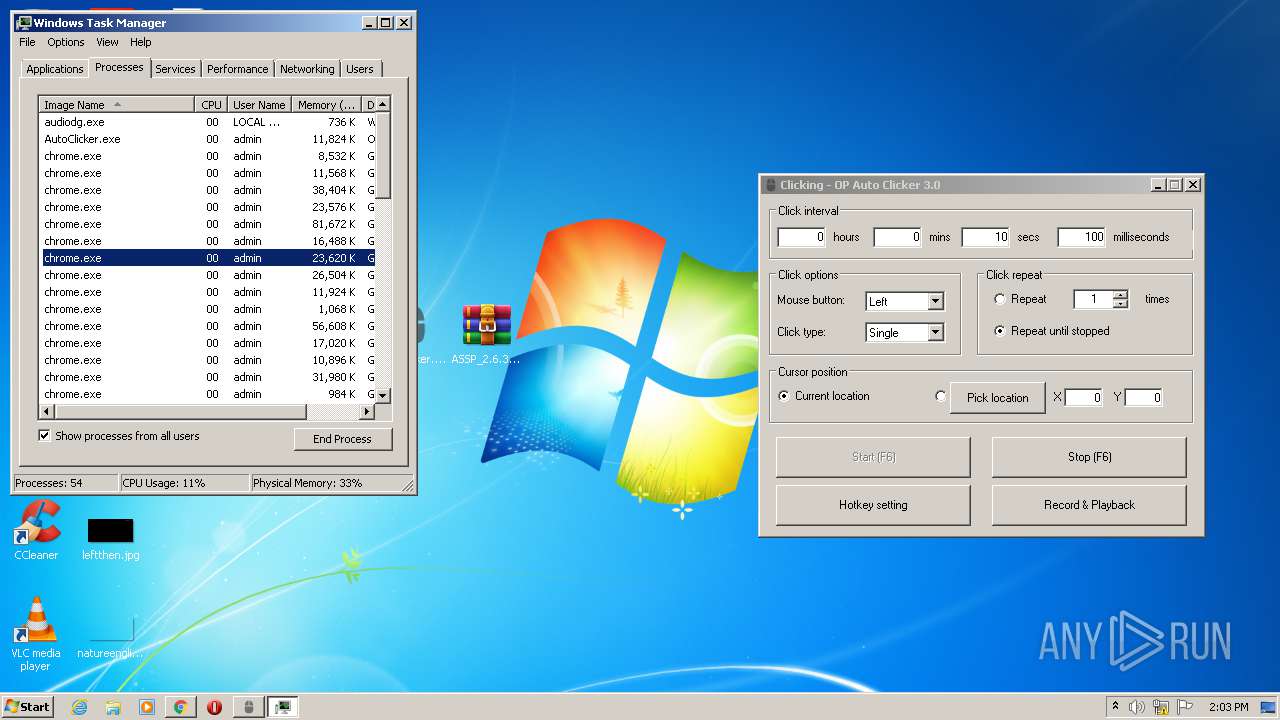
Application was dropped or rewritten from another process
- AutoClicker.exe (PID: 3152)
- AutoClicker.exe (PID: 3328)
- AutoClicker.exe (PID: 2104)
- AutoClicker.exe (PID: 2244)
- AutoClicker.exe (PID: 2364)
- AutoClicker.exe (PID: 3964)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2696)
Drops a file with a compile date too recent
- chrome.exe (PID: 2696)
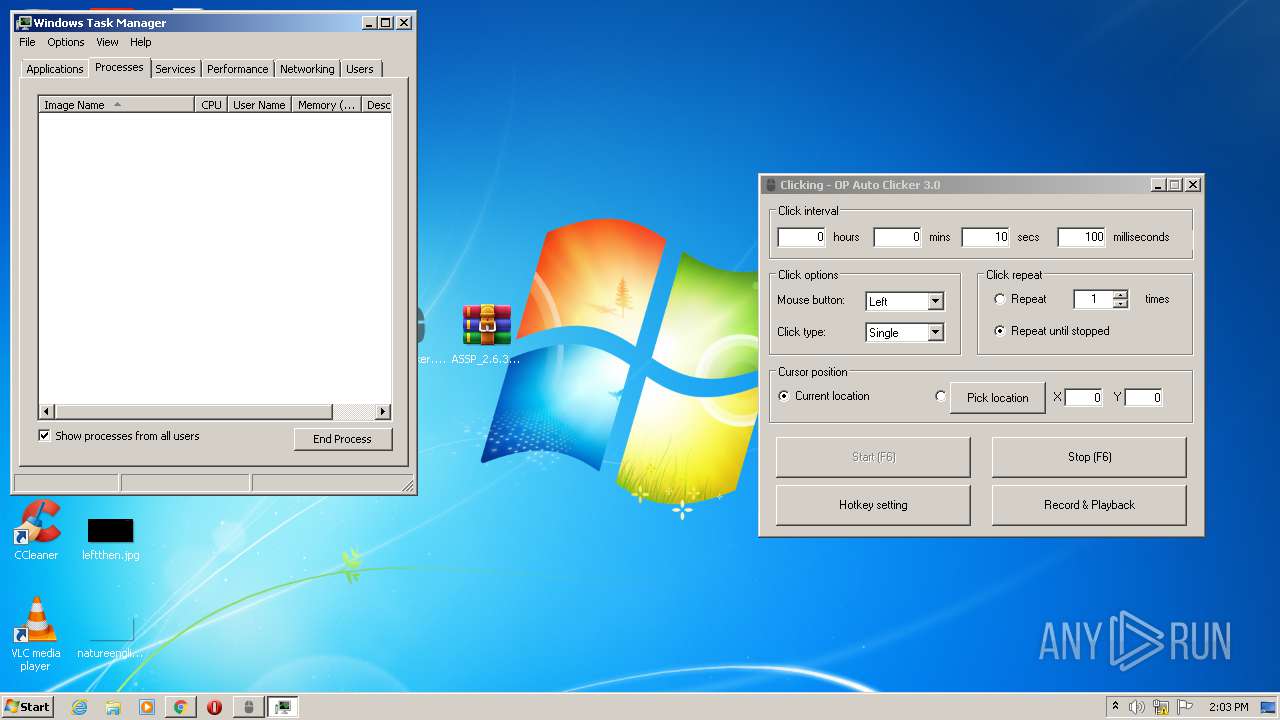
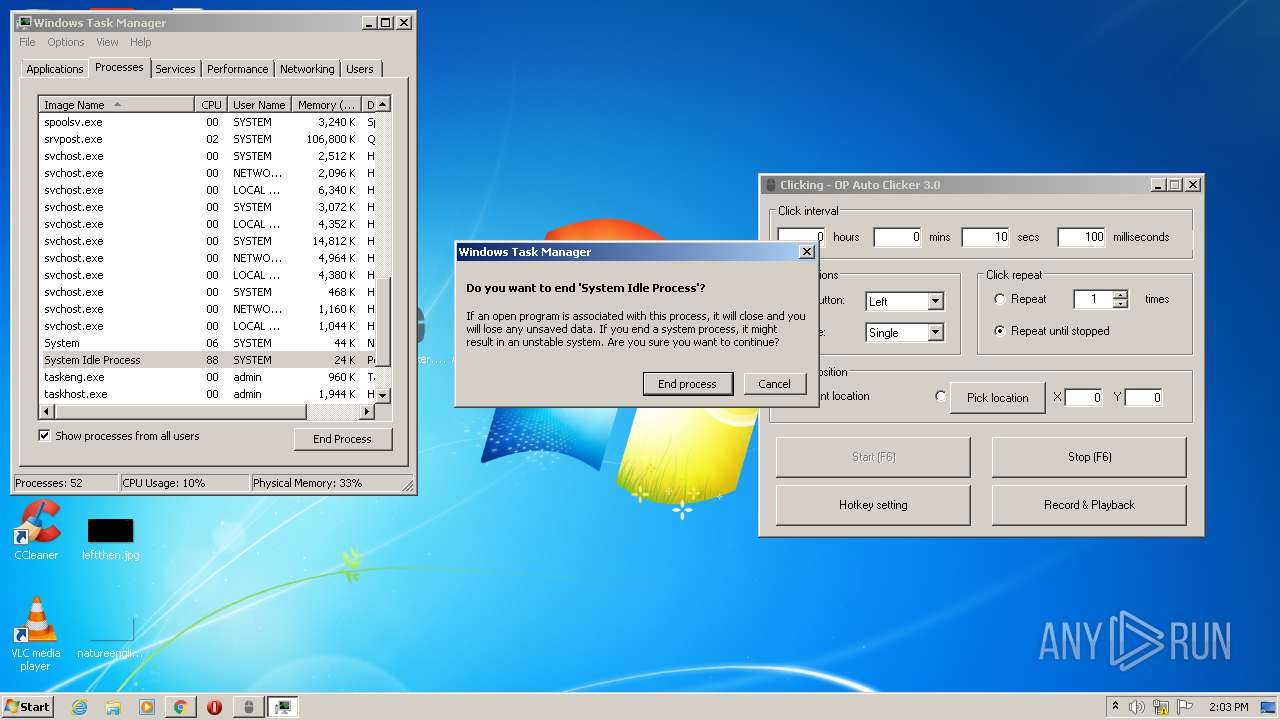
Application launched itself
- taskmgr.exe (PID: 3972)
INFO
Application launched itself
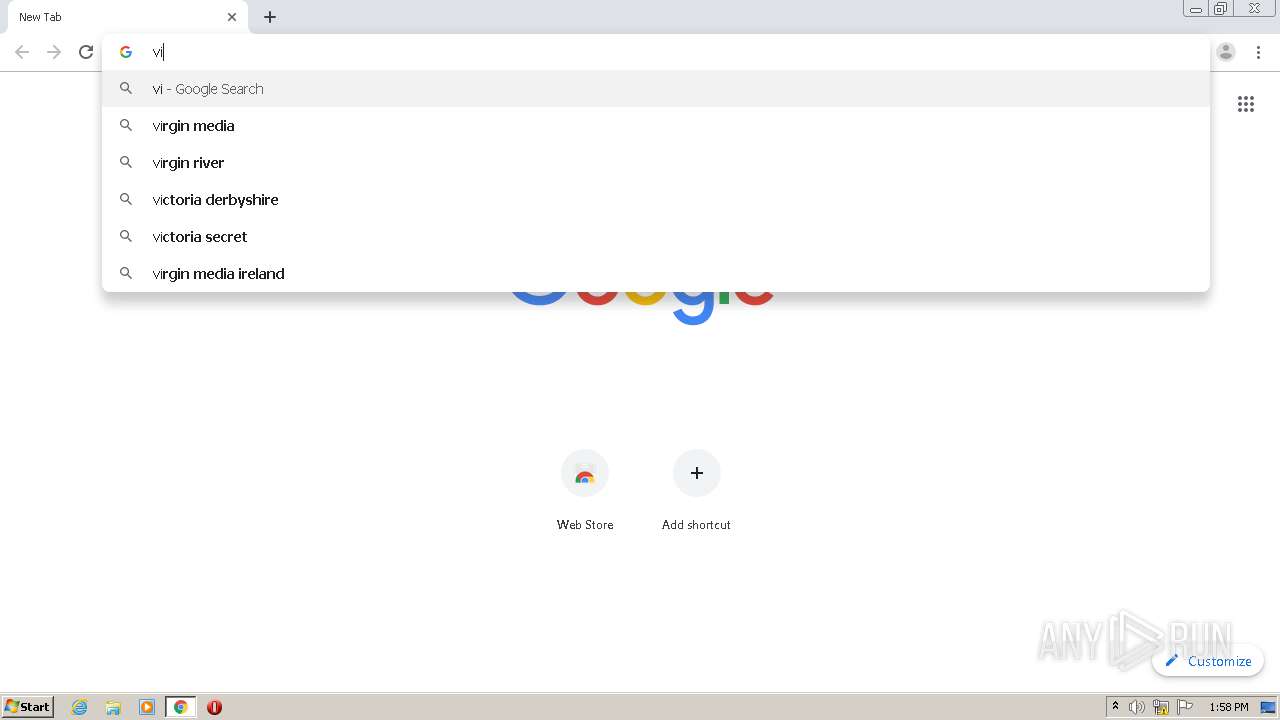
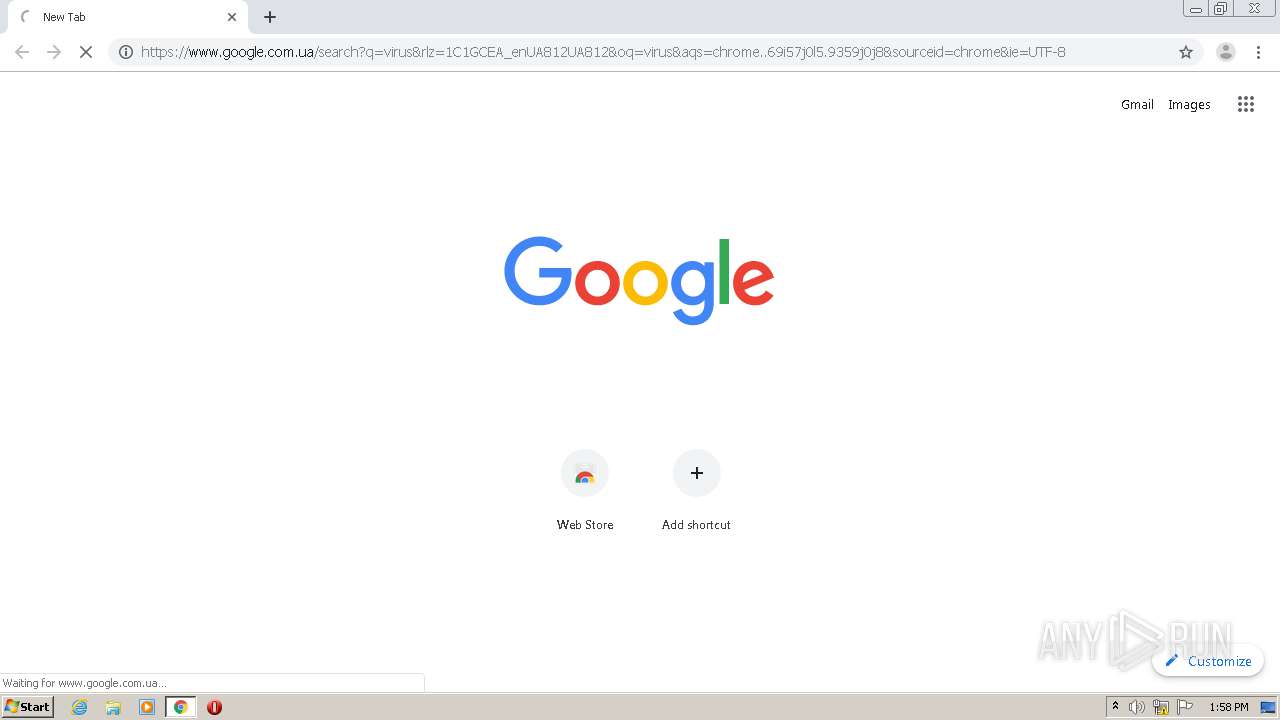
- chrome.exe (PID: 2696)
Reads the hosts file
- chrome.exe (PID: 1792)
- chrome.exe (PID: 2696)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2696)
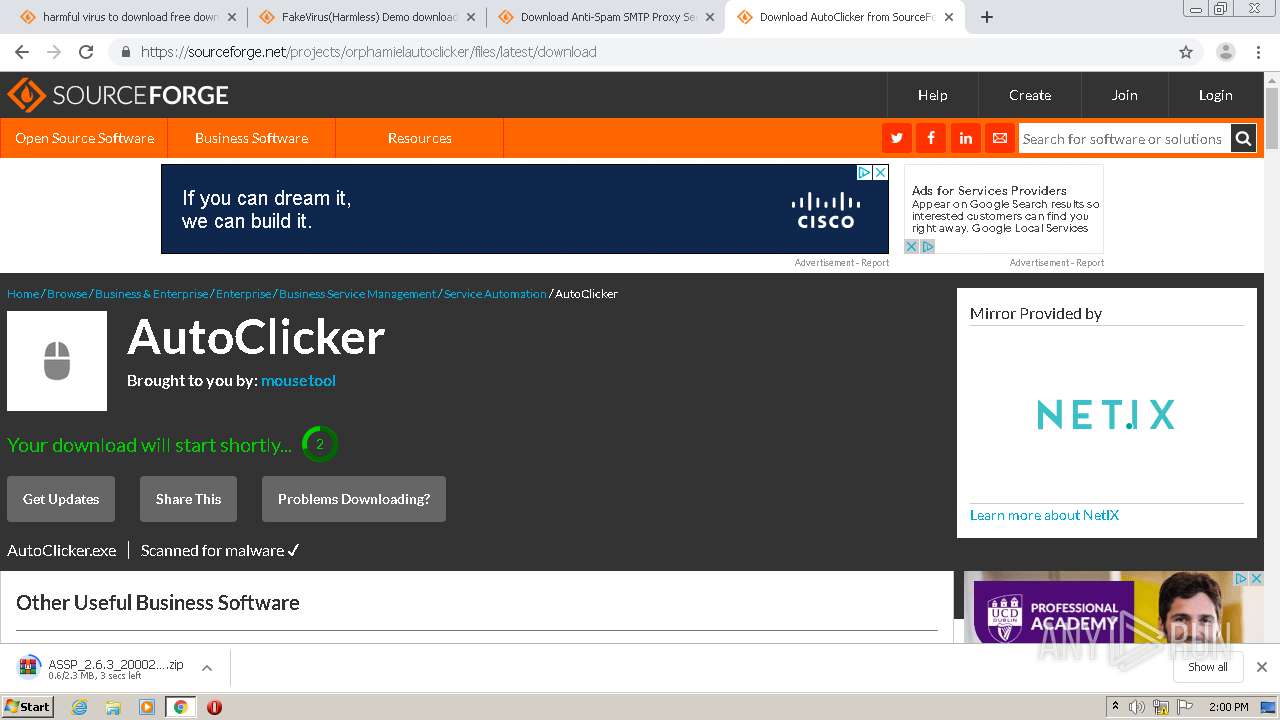
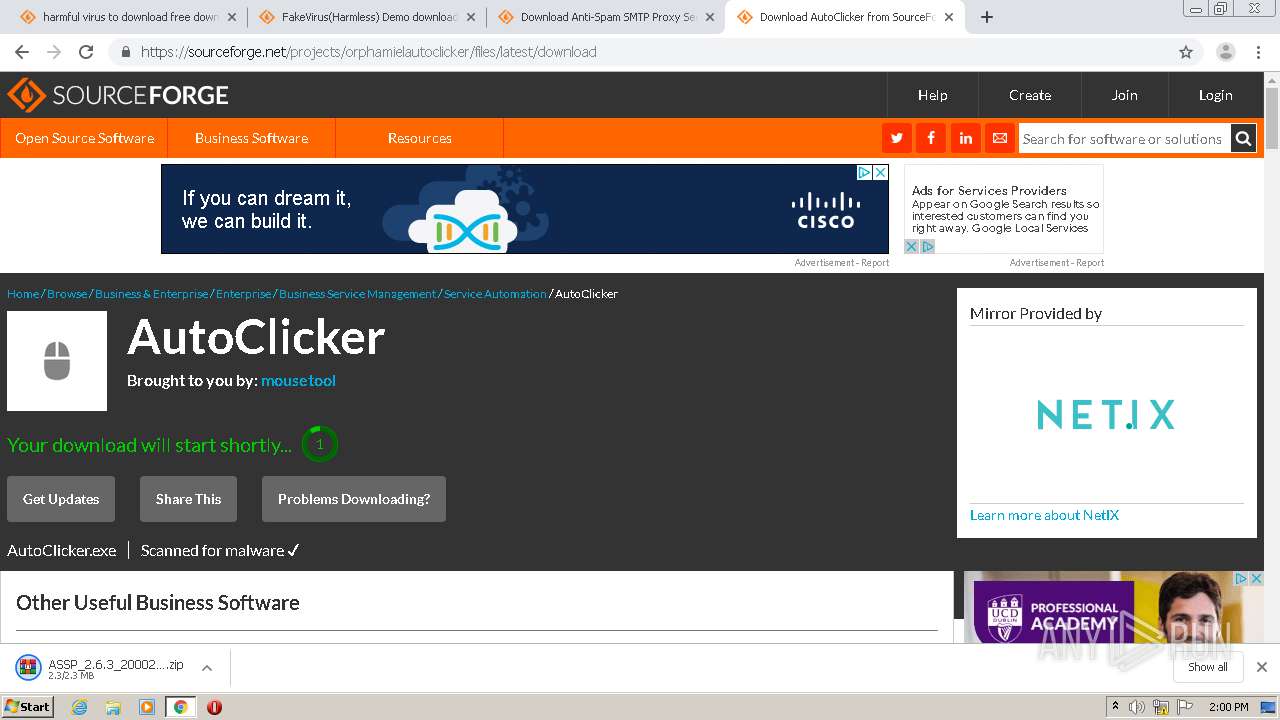
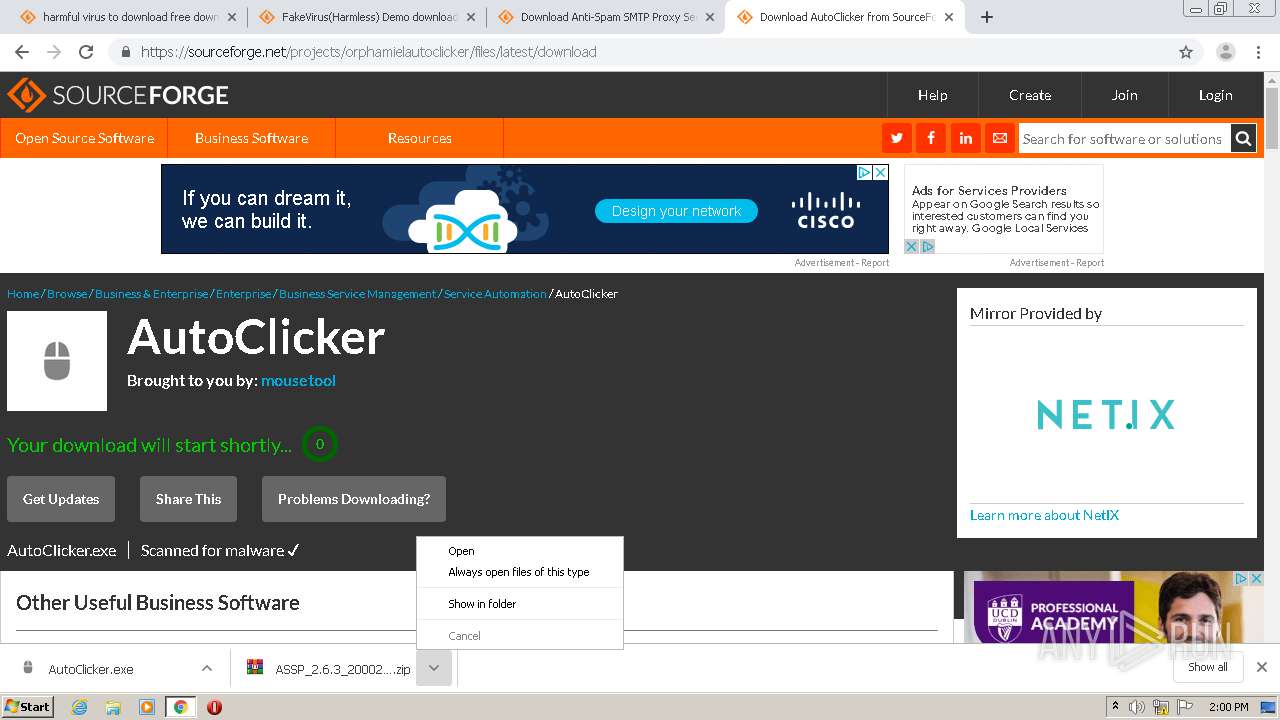
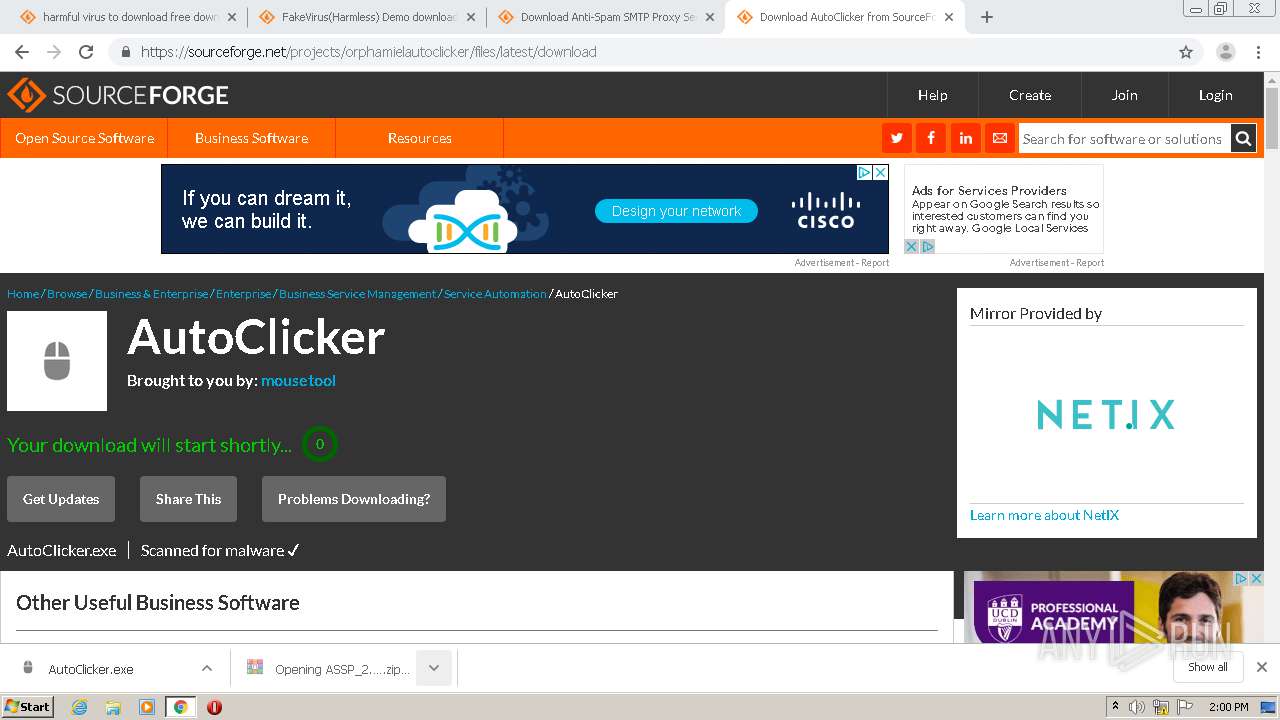
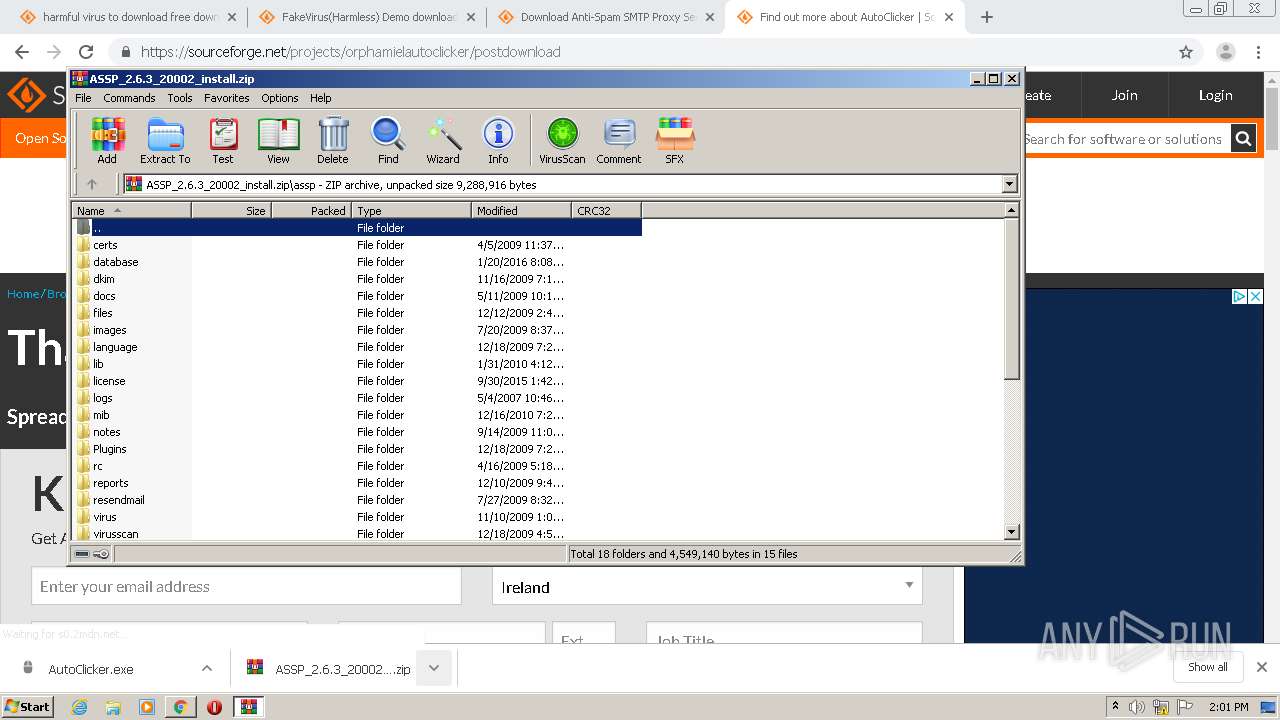
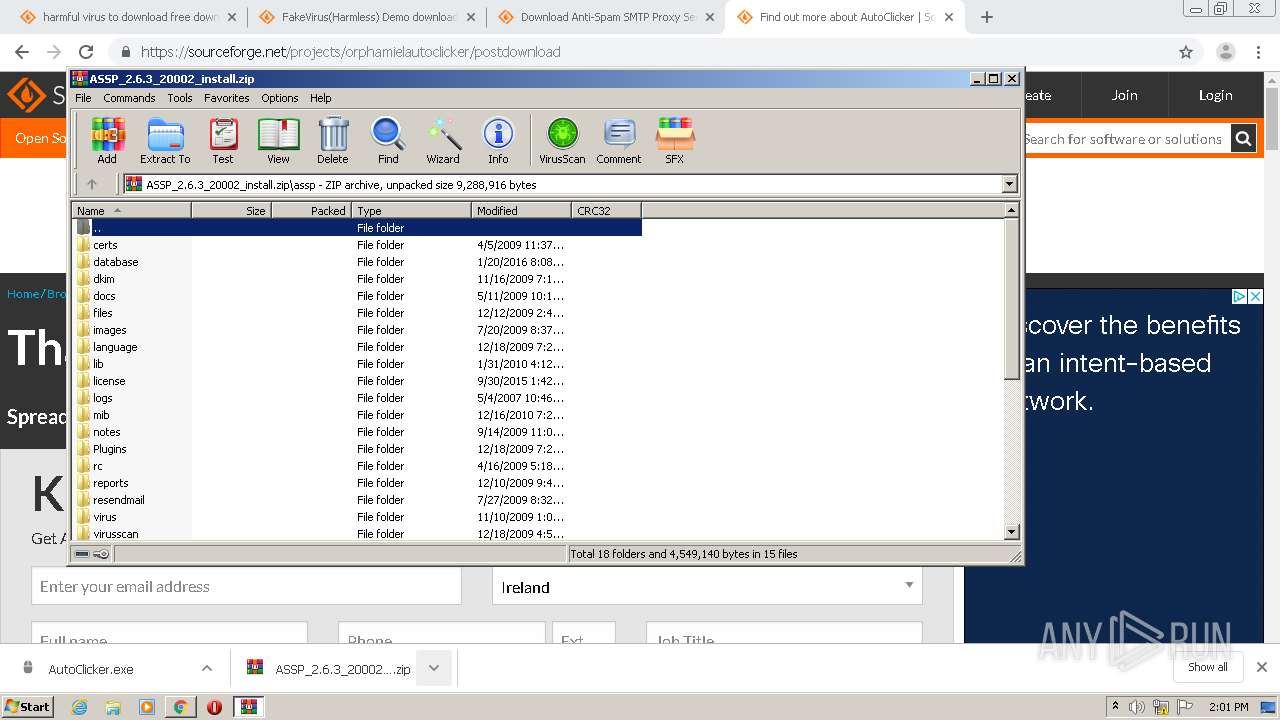
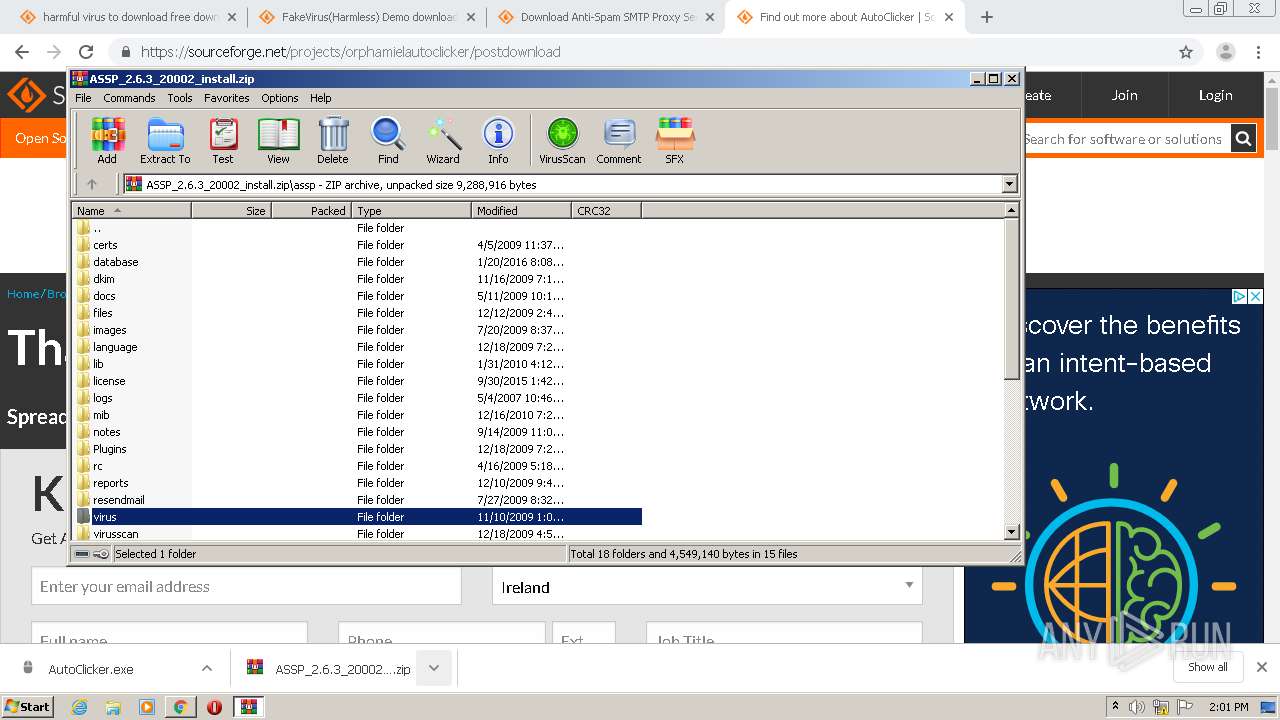
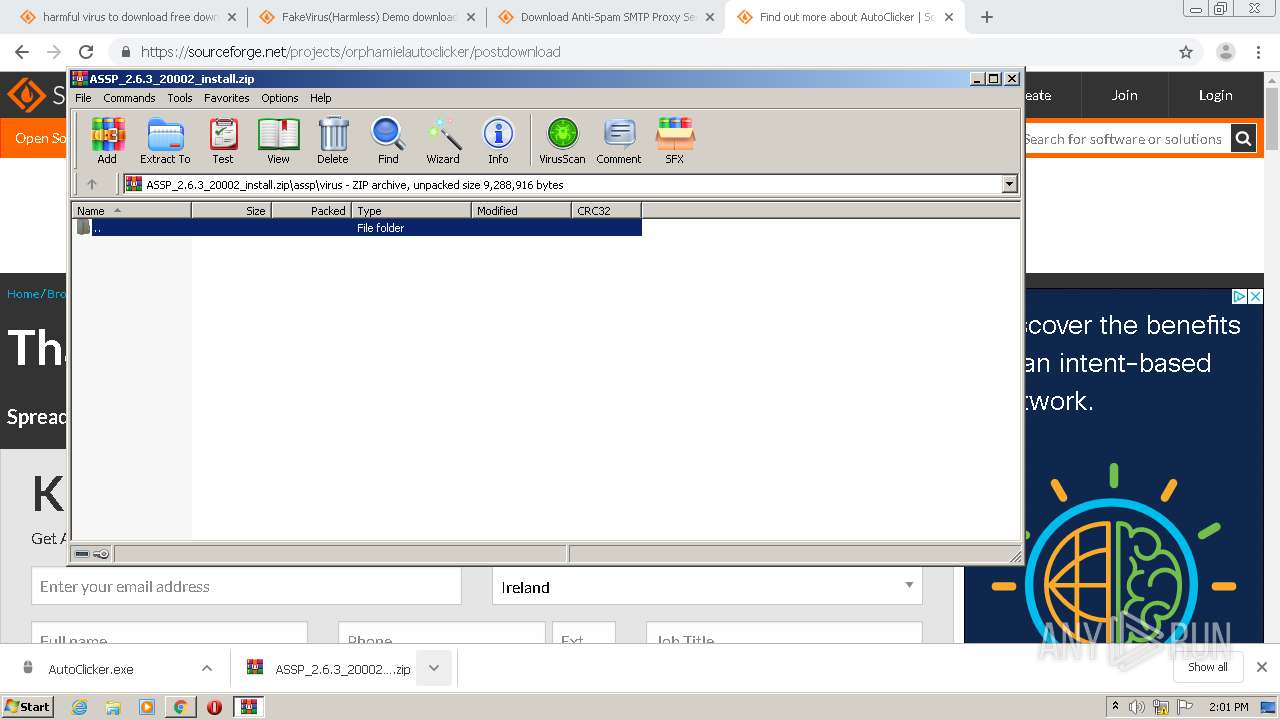
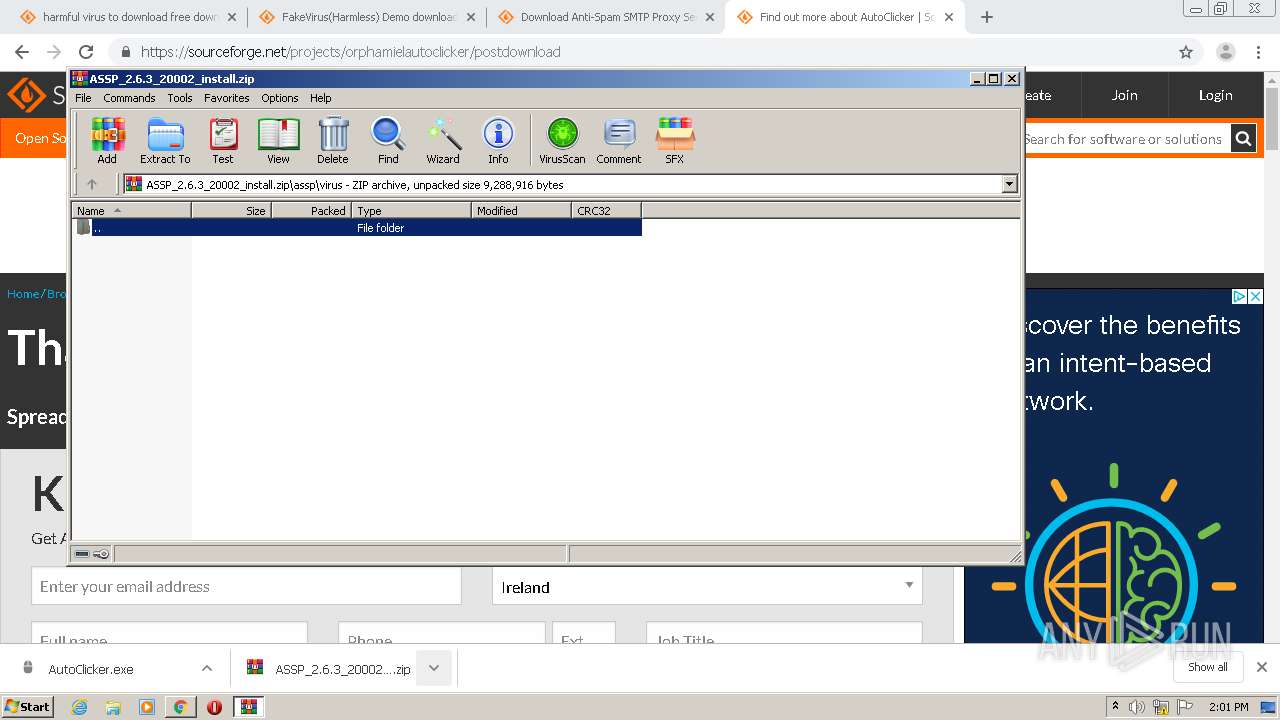
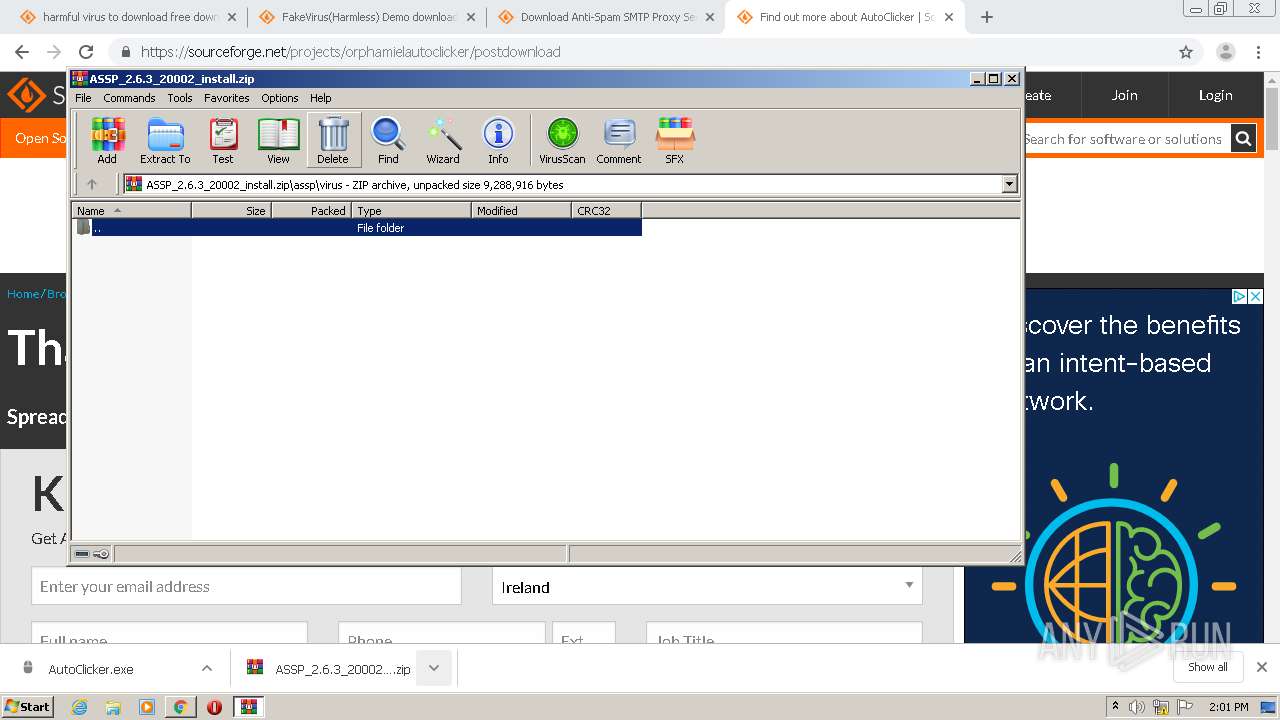
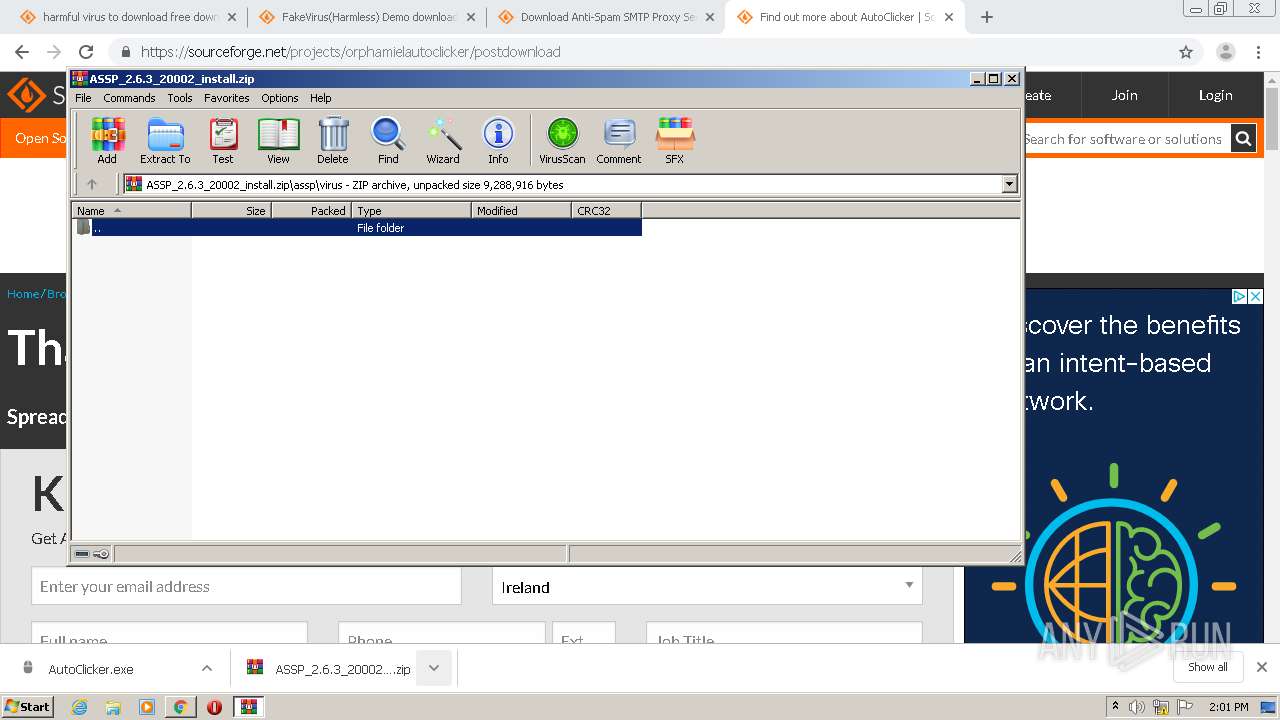
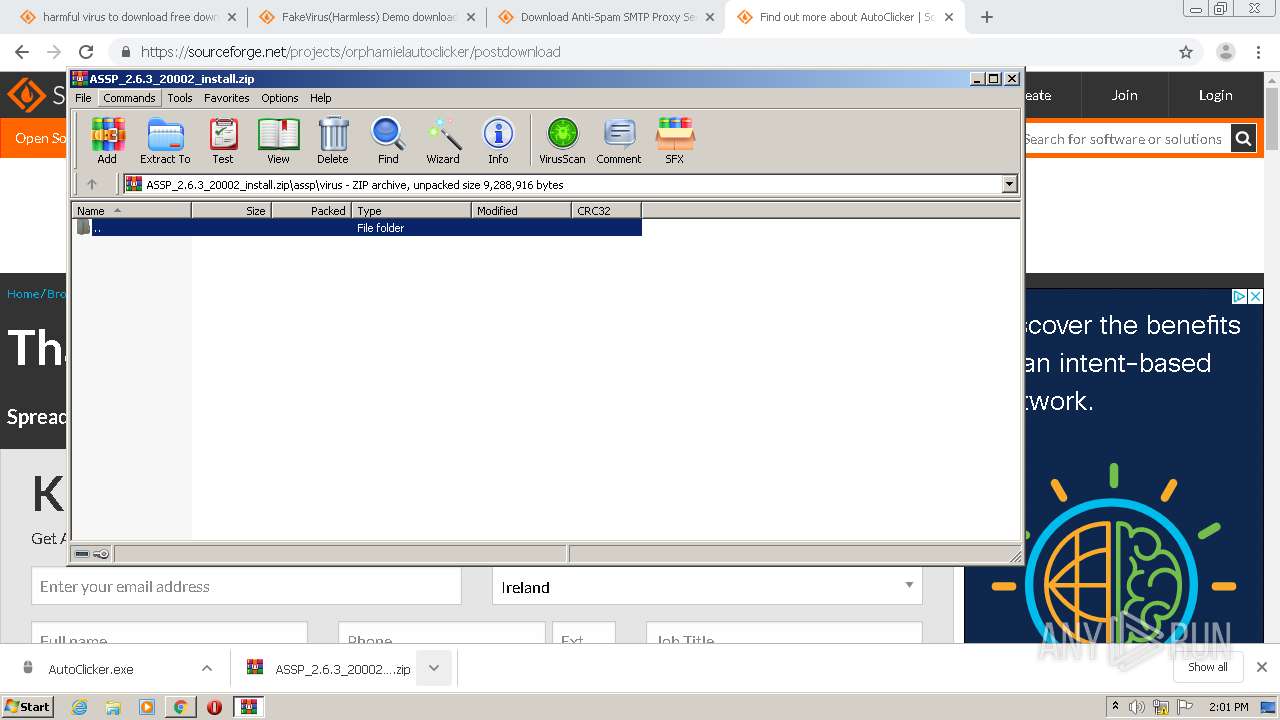
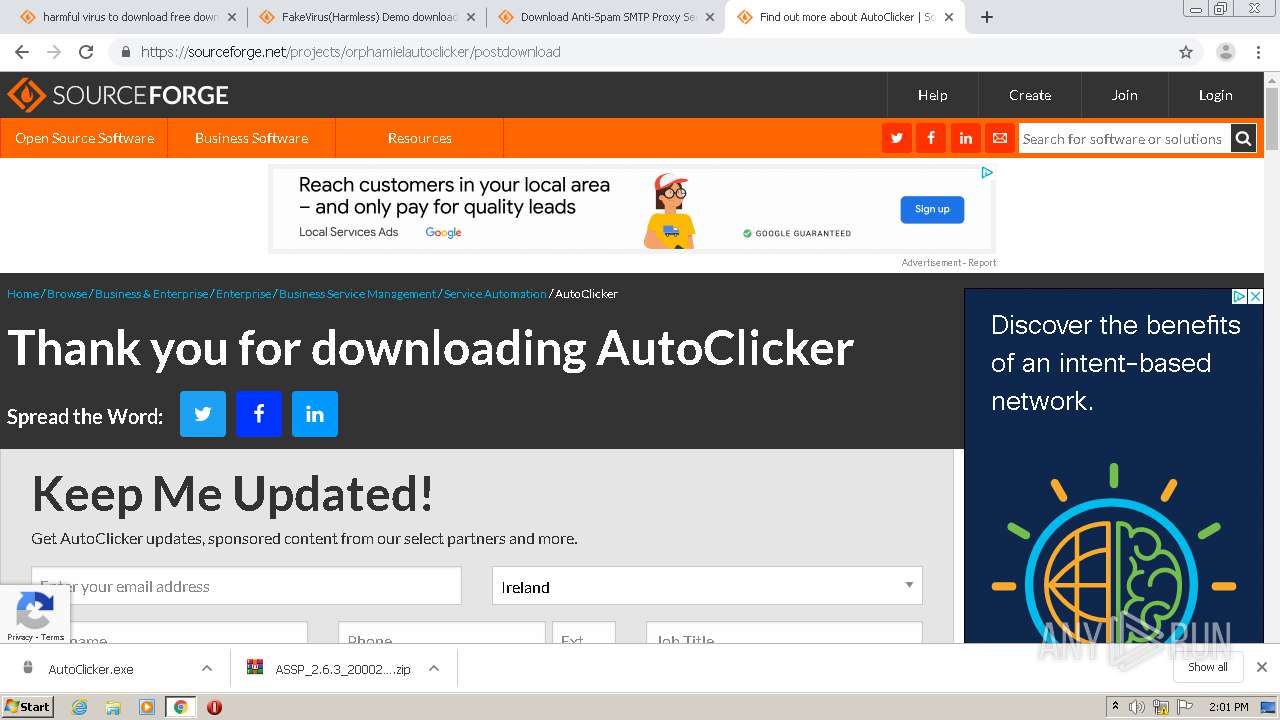
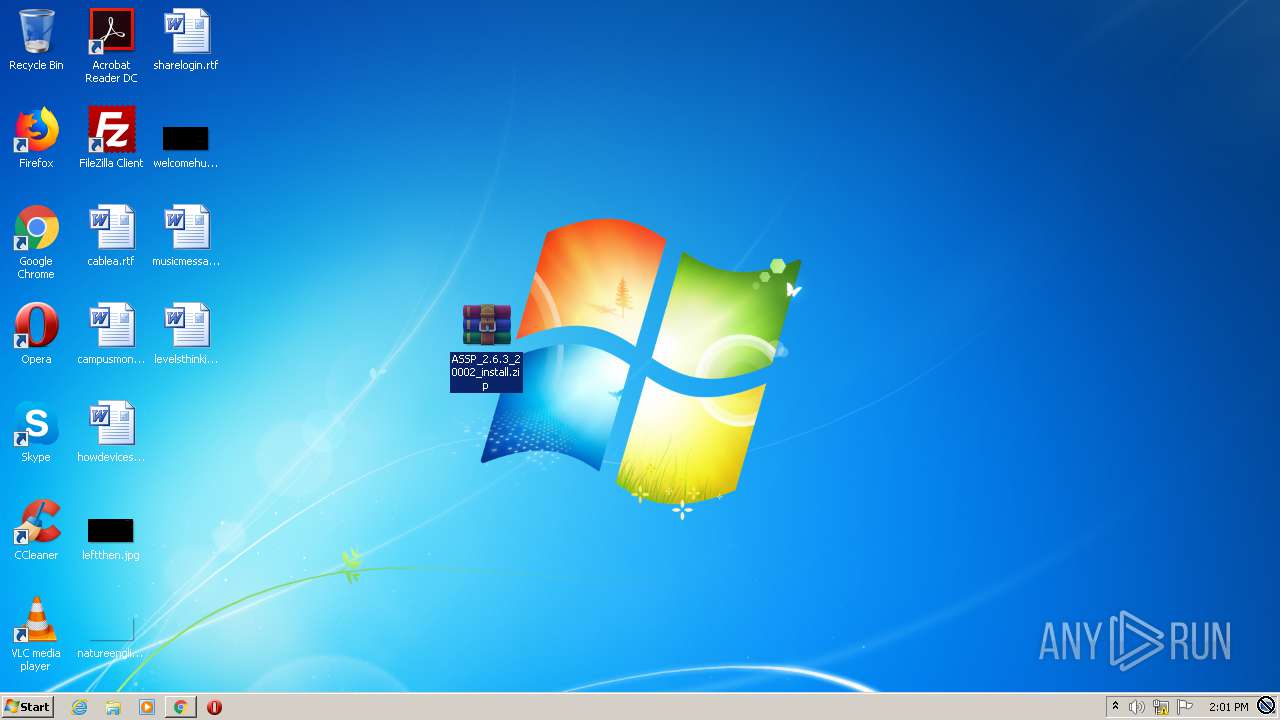
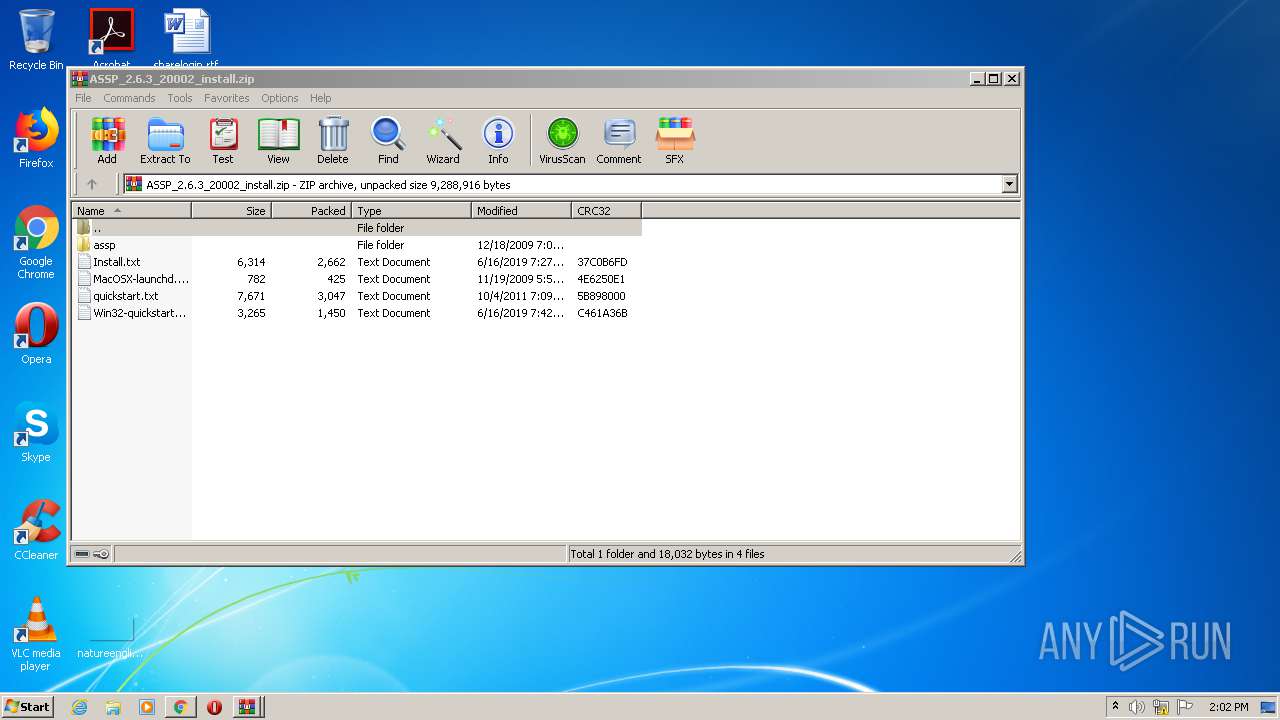
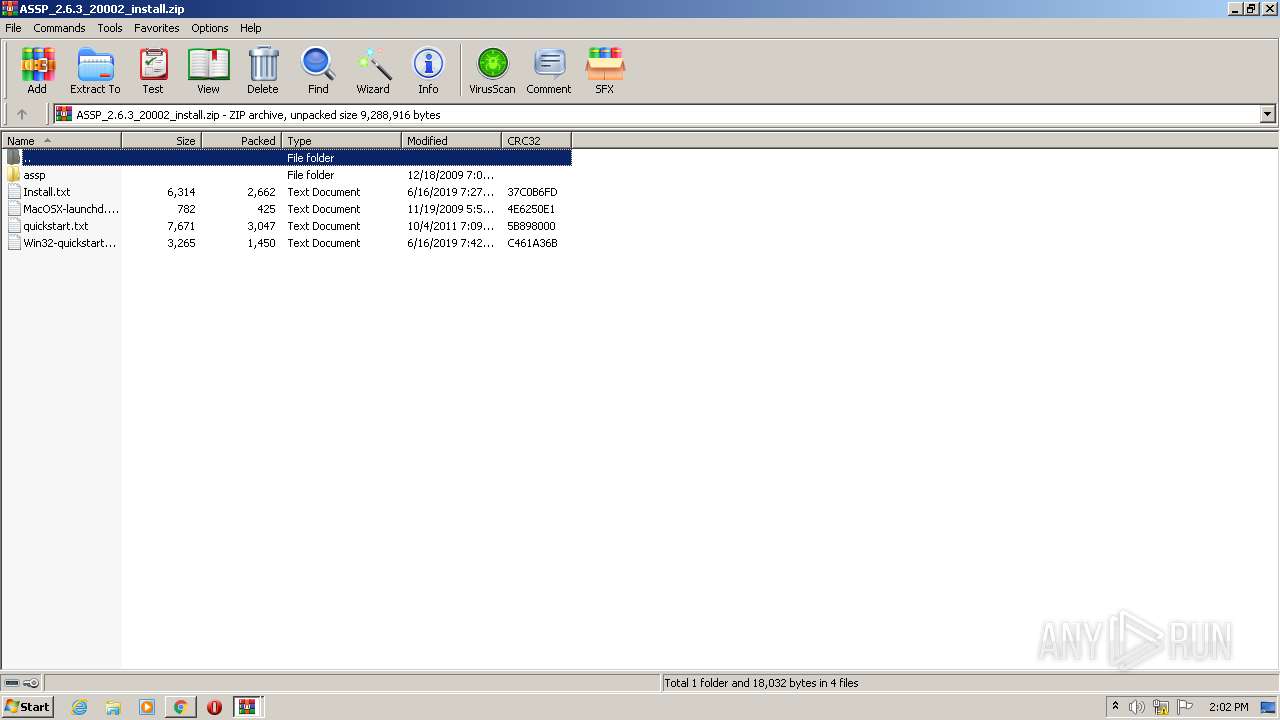
Manual execution by user
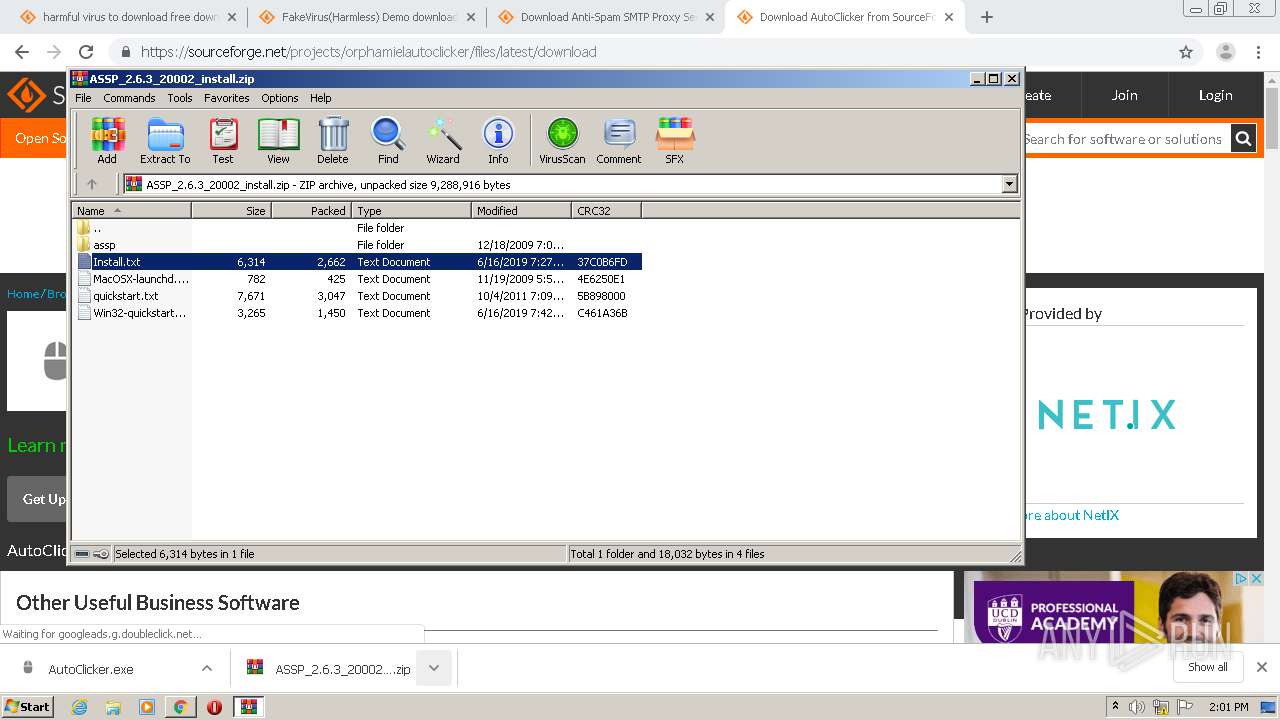
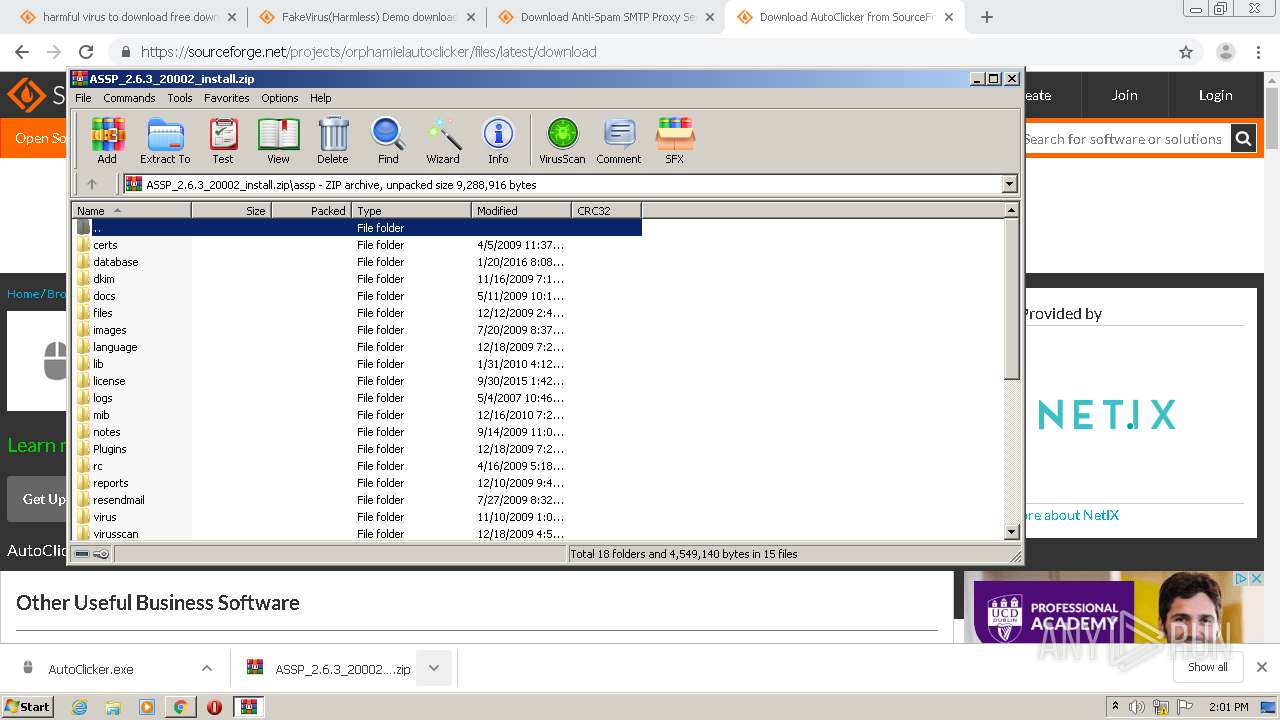
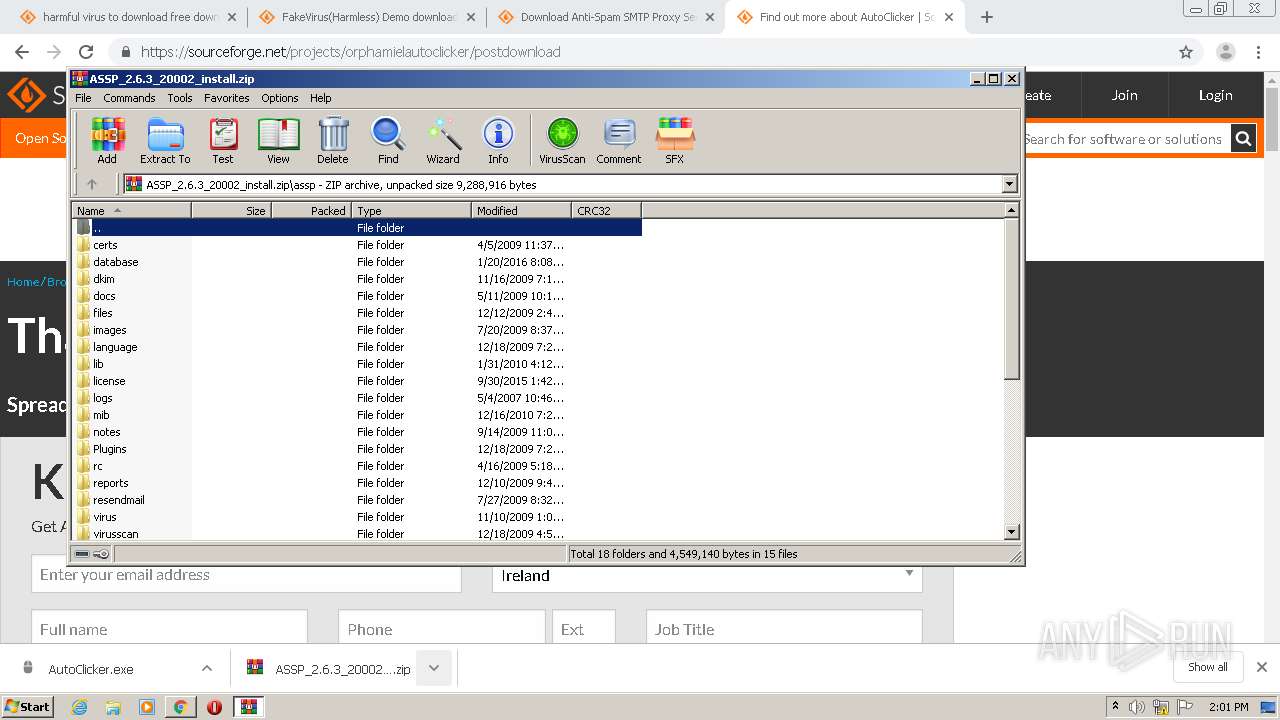
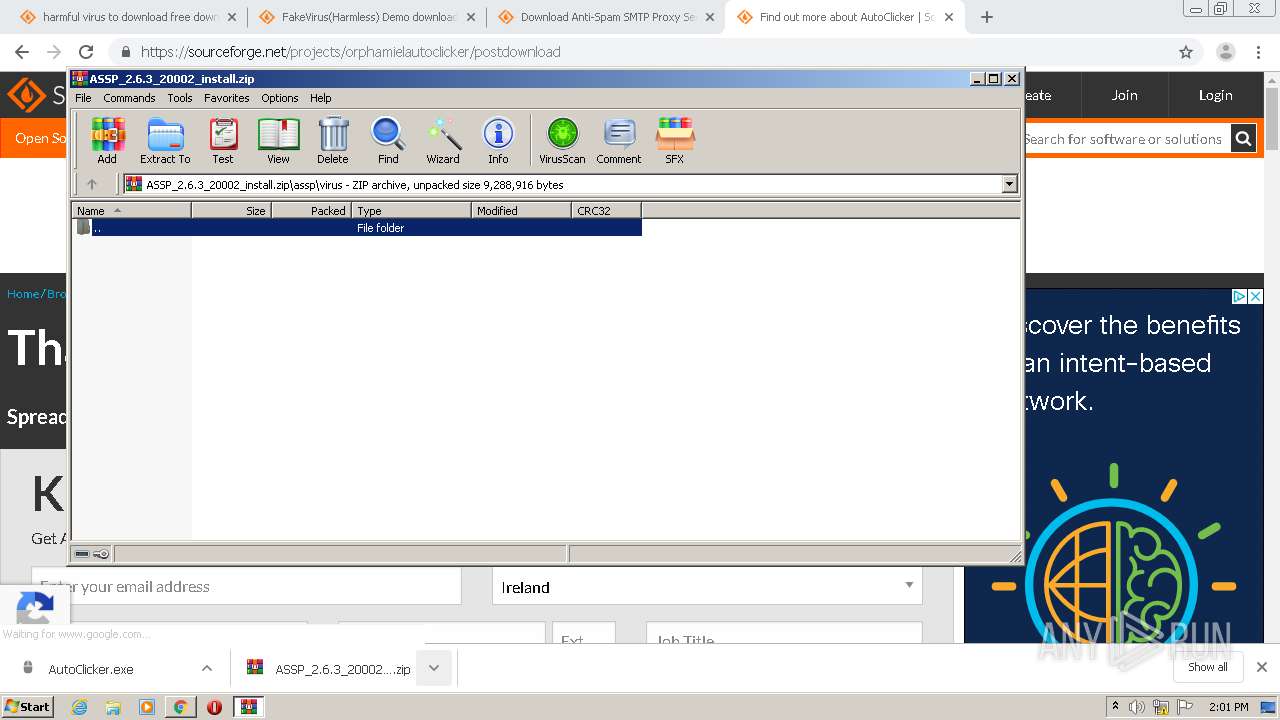
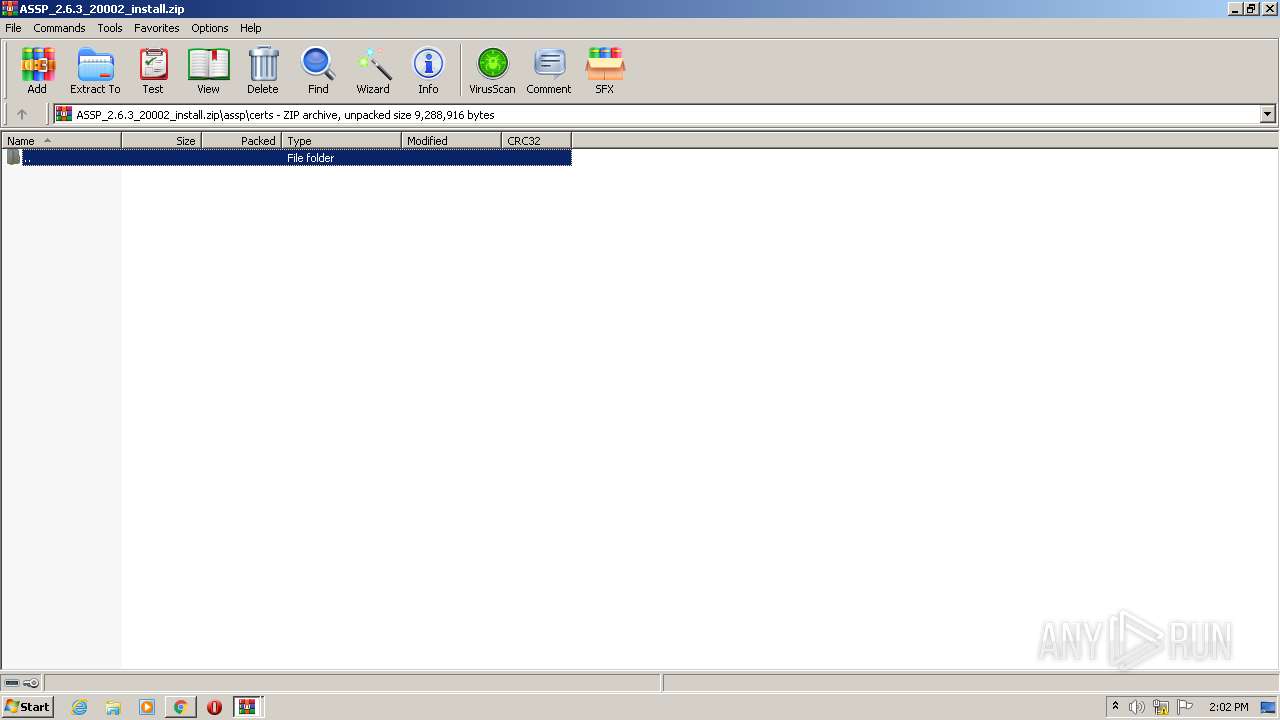
- WinRAR.exe (PID: 1188)
- AutoClicker.exe (PID: 3152)
- WinRAR.exe (PID: 2288)
- AutoClicker.exe (PID: 3328)
- AutoClicker.exe (PID: 2104)
- AutoClicker.exe (PID: 2244)
- AutoClicker.exe (PID: 2364)
- taskmgr.exe (PID: 3972)
- AutoClicker.exe (PID: 3964)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
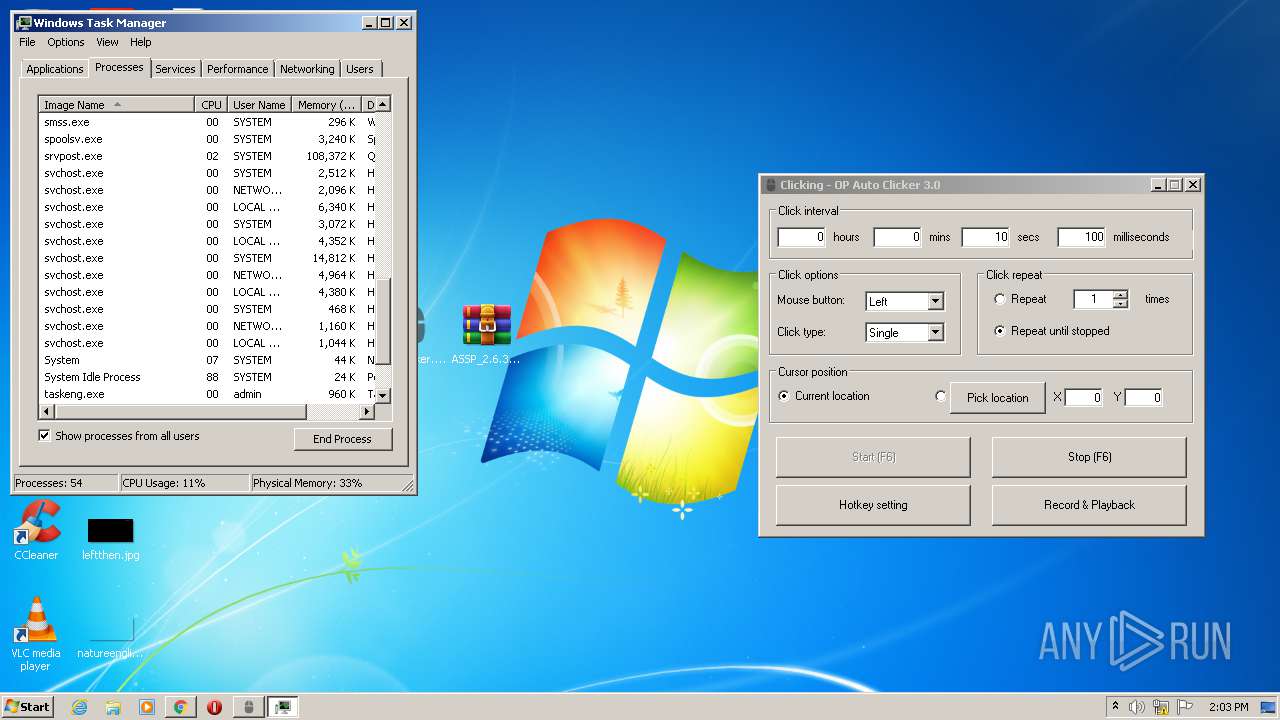
Total processes
89
Monitored processes
44
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,18278771730369731740,13124697746291414453,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16207380353051075497 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3140 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,18278771730369731740,13124697746291414453,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8568218761884505755 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1844 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
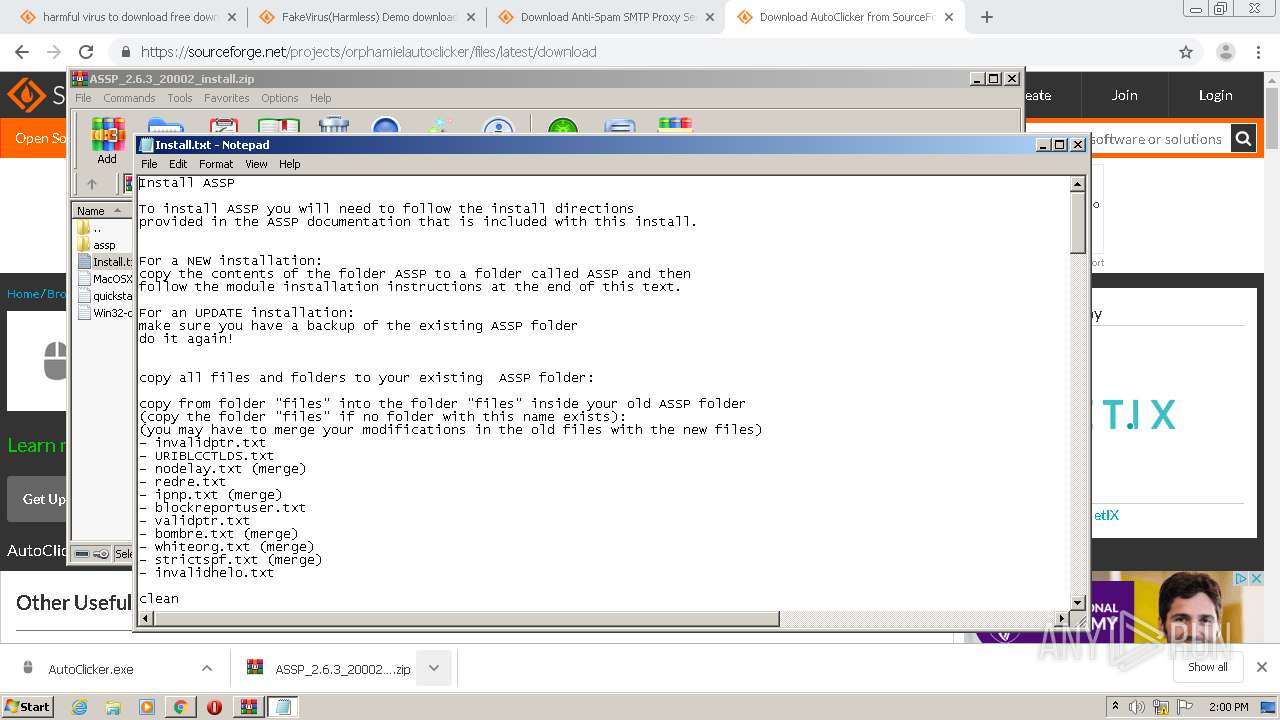
| 924 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Rar$DIa3080.28606\Install.txt | C:\Windows\system32\NOTEPAD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,18278771730369731740,13124697746291414453,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=646281570737938014 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2200 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,18278771730369731740,13124697746291414453,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=269368334093053404 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2316 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
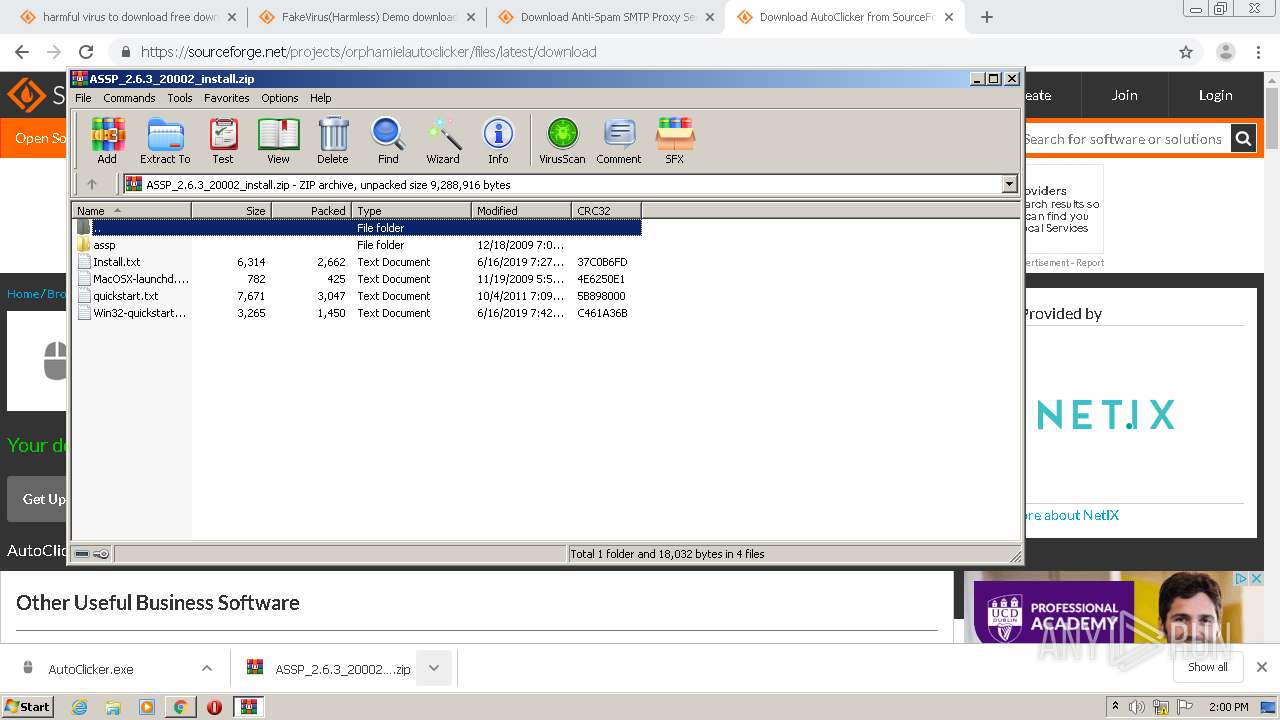
| 1188 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\ASSP_2.6.3_20002_install.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1740 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,18278771730369731740,13124697746291414453,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15118634784811558012 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3788 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,18278771730369731740,13124697746291414453,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5500670810461421860 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2940 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1792 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,18278771730369731740,13124697746291414453,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=13385033449264250711 --mojo-platform-channel-handle=1456 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,18278771730369731740,13124697746291414453,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10839416854556855028 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4204 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 342
Read events
2 186
Write events
153
Delete events
3
Modification events
| (PID) Process: | (2544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2696-13251131900743125 |
Value: 259 | |||
| (PID) Process: | (2696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2696) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
2
Suspicious files
530
Text files
188
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FC3A8FD-A88.pma | — | |
MD5:— | SHA256:— | |||
| 2696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d45cf2ec-41eb-4393-8af4-a490f96fe4b6.tmp | — | |
MD5:— | SHA256:— | |||
| 2696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF15459e.TMP | text | |
MD5:— | SHA256:— | |||
| 2696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF154669.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
290
DNS requests
187
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1792 | chrome.exe | 87.240.185.158:443 | sun9-55.userapi.com | VKontakte Ltd | RU | unknown |
1792 | chrome.exe | 87.240.185.169:443 | sun9-70.userapi.com | VKontakte Ltd | RU | unknown |
1792 | chrome.exe | 93.186.227.148:443 | sun9-41.userapi.com | VKontakte Ltd | RU | unknown |
1792 | chrome.exe | 87.240.185.161:443 | sun9-62.userapi.com | VKontakte Ltd | RU | unknown |
1792 | chrome.exe | 87.240.185.159:443 | sun9-56.userapi.com | VKontakte Ltd | RU | unknown |
1792 | chrome.exe | 93.186.227.144:443 | sun9-33.userapi.com | VKontakte Ltd | RU | unknown |
1792 | chrome.exe | 172.217.12.205:443 | accounts.google.com | Google Inc. | US | suspicious |
1792 | chrome.exe | 87.240.185.160:443 | sun9-61.userapi.com | VKontakte Ltd | RU | unknown |
1792 | chrome.exe | 95.142.206.3:443 | sun6-23.userapi.com | VKontakte Ltd | RU | unknown |
1792 | chrome.exe | 87.240.185.165:443 | sun9-66.userapi.com | VKontakte Ltd | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
vk.com |
| whitelisted |
accounts.google.com |
| shared |
sun6-21.userapi.com |
| whitelisted |
sun9-61.userapi.com |
| unknown |
sun6-23.userapi.com |
| unknown |
sun9-37.userapi.com |
| unknown |
sun9-3.userapi.com |
| unknown |
sun9-66.userapi.com |
| unknown |
sun9-25.userapi.com |
| unknown |
sun6-22.userapi.com |
| unknown |