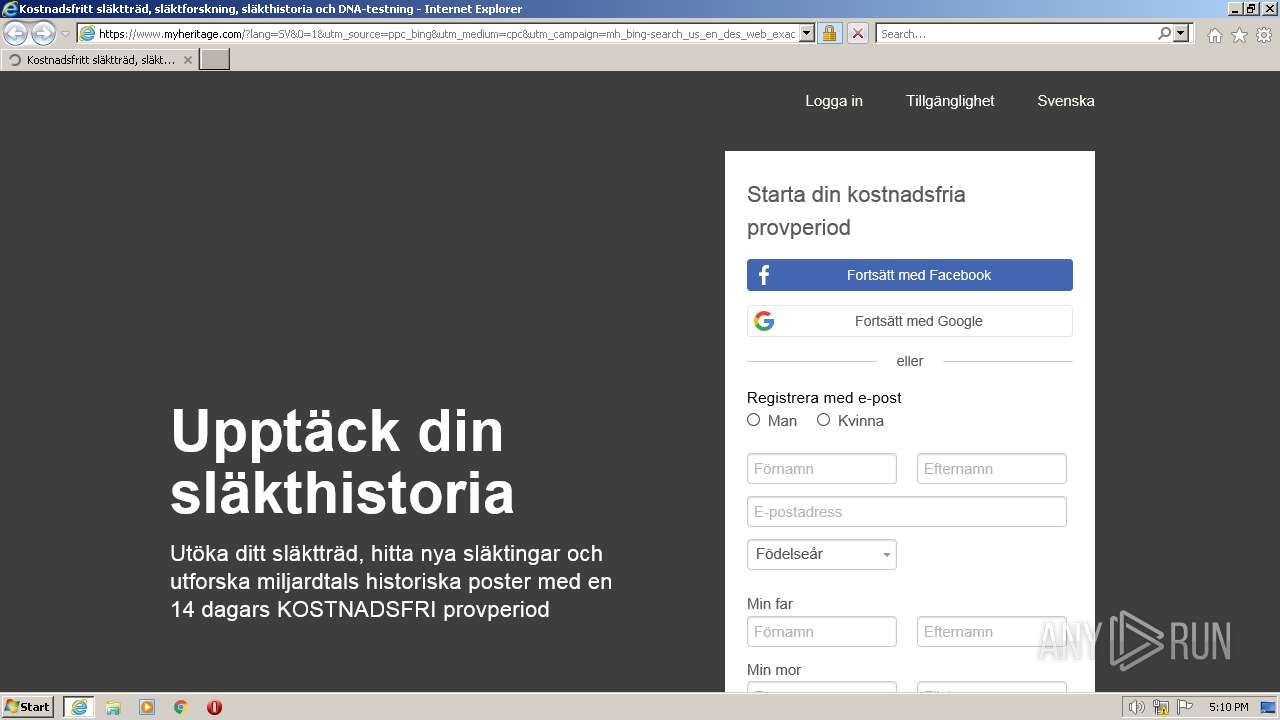
| URL: | https://www.bing.com/aclk?ld=e8dmpPxgbQ7KutyOz9R-ZKHjVUCUzotYqdKIu19vWOsCIegBZ8-ji9UJmLOVzvv4Xa7W78kM_zugerh9EjRQ0mn0zJgi5grb-hllGUMIFGp9OVqCukC_yEGzQEfg3G0qZ7d6jvFZ8G5M1YmDdS_kiOCxRZsX1dM7JAkkNQ9X0UKhcg8raOQi2BzeP74aPRvKh3lbhaEQ&u=aHR0cHMlM2ElMmYlMmZ3d3cubXloZXJpdGFnZS5jb20lM2YxJTNkMSUyNnV0bV9zb3VyY2UlM2RwcGNfYmluZyUyNnV0bV9tZWRpdW0lM2RjcGMlMjZ1dG1fY2FtcGFpZ24lM2RtaF9iaW5nLXNlYXJjaF91c19lbl9kZXNfd2ViX2V4YWN0X3dlYl9teWhlcml0YWdlLWRvbWFpbiUyNnV0bV9jb250ZW50JTNkNzMzMjM3OTE1NDk5NTQlMjZ1dG1fdGVybSUzZG15aGVyaXRhZ2UlMjUyMGNvbSUyNnRyX2NhbXBfaWQlM2QyNjg1MjU5OTElMjZ0cl9hZF9ncm91cCUzZG15aGVyaXRhZ2Vfc2l0ZV9pJTI2dHJfYWdfaWQlM2QxMTczMTc5Mzg3NTIwMDk3JTI2dHJfZGV2aWNlJTNkYyUyNnRyX2FjY291bnQlM2RGMTA3OVY4UyUyNm1zY2xraWQlM2RlOWNlNmE5NjE5YjcxNzQ5NDY4ODBlMTEwMTc2MGFmNA&rlid=e9ce6a9619b7174946880e1101760af4&ntb=1 |
| Full analysis: | https://app.any.run/tasks/37a46ec2-3cb0-4628-baf8-2b3225f9bdba |
| Verdict: | Malicious activity |
| Analysis date: | June 23, 2023, 16:08:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4A0F297C1A1494207A56536A1328801F |
| SHA1: | A977D52E1E31C2913820E7AE6A8E4A2A8636A8E1 |
| SHA256: | A4C22B5A8D0CFF5B0ABC456DE6EDFB78B244B9CA94BEEC30FD7D314C76D51824 |
| SSDEEP: | 24:2PRYtavaNYkFPeRZfC/+wCdDMwCAxoXuA8:wRYiMFMRZ6CxPCAe+A8 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 1160)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1160 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.bing.com/aclk?ld=e8dmpPxgbQ7KutyOz9R-ZKHjVUCUzotYqdKIu19vWOsCIegBZ8-ji9UJmLOVzvv4Xa7W78kM_zugerh9EjRQ0mn0zJgi5grb-hllGUMIFGp9OVqCukC_yEGzQEfg3G0qZ7d6jvFZ8G5M1YmDdS_kiOCxRZsX1dM7JAkkNQ9X0UKhcg8raOQi2BzeP74aPRvKh3lbhaEQ&u=aHR0cHMlM2ElMmYlMmZ3d3cubXloZXJpdGFnZS5jb20lM2YxJTNkMSUyNnV0bV9zb3VyY2UlM2RwcGNfYmluZyUyNnV0bV9tZWRpdW0lM2RjcGMlMjZ1dG1fY2FtcGFpZ24lM2RtaF9iaW5nLXNlYXJjaF91c19lbl9kZXNfd2ViX2V4YWN0X3dlYl9teWhlcml0YWdlLWRvbWFpbiUyNnV0bV9jb250ZW50JTNkNzMzMjM3OTE1NDk5NTQlMjZ1dG1fdGVybSUzZG15aGVyaXRhZ2UlMjUyMGNvbSUyNnRyX2NhbXBfaWQlM2QyNjg1MjU5OTElMjZ0cl9hZF9ncm91cCUzZG15aGVyaXRhZ2Vfc2l0ZV9pJTI2dHJfYWdfaWQlM2QxMTczMTc5Mzg3NTIwMDk3JTI2dHJfZGV2aWNlJTNkYyUyNnRyX2FjY291bnQlM2RGMTA3OVY4UyUyNm1zY2xraWQlM2RlOWNlNmE5NjE5YjcxNzQ5NDY4ODBlMTEwMTc2MGFmNA&rlid=e9ce6a9619b7174946880e1101760af4&ntb=1" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3612 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1160 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
13 938
Read events
13 785
Write events
151
Delete events
2
Modification events
| (PID) Process: | (1160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (1160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (1160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (1160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
1
Suspicious files
30
Text files
65
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3612 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 1160 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 3612 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:B4CF4F6DB7372E7B6AA7618CCE3F9737 | SHA256:E1898185690BA249B29EFCC4FDE2D8217FD2086B5990065C7427086CA7679327 | |||
| 1160 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 3612 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:E681A1FC5936A81C5F0406E81EB316E1 | SHA256:2BB778FCCEFFF488E949AFF1A0CDC41532AEAA75ED8828BA8CB93F1E0A6DD686 | |||
| 1160 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 3612 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:150EFED1F28E9817B30B542E6E943302 | SHA256:44473E97B821D7BB64F0EA01F166DAC23C04DC81114A91B2169E0B7991A33D0B | |||
| 3612 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_D93C575AD9E9AF9B95268A3CB953B5A1 | binary | |
MD5:8B0F591D403FCFDF7B9AFAE903514C9F | SHA256:0683187811E773C1B7F3C33987AAB0A37BC230A02235518551441A5570AD30C7 | |||
| 3612 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\5W45JIJ0.txt | text | |
MD5:62448E2FFFB01A3F582B8F35397B25EA | SHA256:D5754208A43691FFF4AF956918A2CDAA6E60E88A1164D3DB92F89C7A82116DEF | |||
| 3612 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\OLDSB354.txt | text | |
MD5:817CD0A486A9DFD2017CE9073247CB7B | SHA256:00807961312946DAEDB380E37A5BEFA0AC7D0FE32B980CEAD72B6799E8AA8A77 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
98
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3612 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | binary | 1.47 Kb | whitelisted |
1160 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
3612 | iexplore.exe | GET | 200 | 18.66.107.194:80 | http://crl.rootg2.amazontrust.com/rootg2.crl | US | binary | 713 b | whitelisted |
3612 | iexplore.exe | GET | 200 | 52.222.250.185:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | binary | 1.51 Kb | whitelisted |
3612 | iexplore.exe | GET | 200 | 108.138.2.173:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | binary | 2.02 Kb | whitelisted |
1160 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAqvpsXKY8RRQeo74ffHUxc%3D | US | binary | 471 b | whitelisted |
3612 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJaiu8Zb34NbCEEshrmcCs%3D | US | binary | 471 b | whitelisted |
3612 | iexplore.exe | GET | 200 | 52.222.250.42:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEkpLy9ROx7U76vGUhC06D6E%3D | US | binary | 1.39 Kb | shared |
3612 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?bc64329c8f00bbdc | US | compressed | 4.70 Kb | whitelisted |
1160 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
820 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3612 | iexplore.exe | 2.23.209.187:443 | — | Akamai International B.V. | GB | suspicious |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3612 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1160 | iexplore.exe | 2.23.209.187:443 | — | Akamai International B.V. | GB | suspicious |
1160 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
1160 | iexplore.exe | 2.23.209.133:443 | — | Akamai International B.V. | GB | suspicious |
3612 | iexplore.exe | 172.217.16.196:443 | www.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
www.myheritage.com |
| suspicious |
cf.mhcache.com |
| malicious |
www.google.com |
| malicious |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |