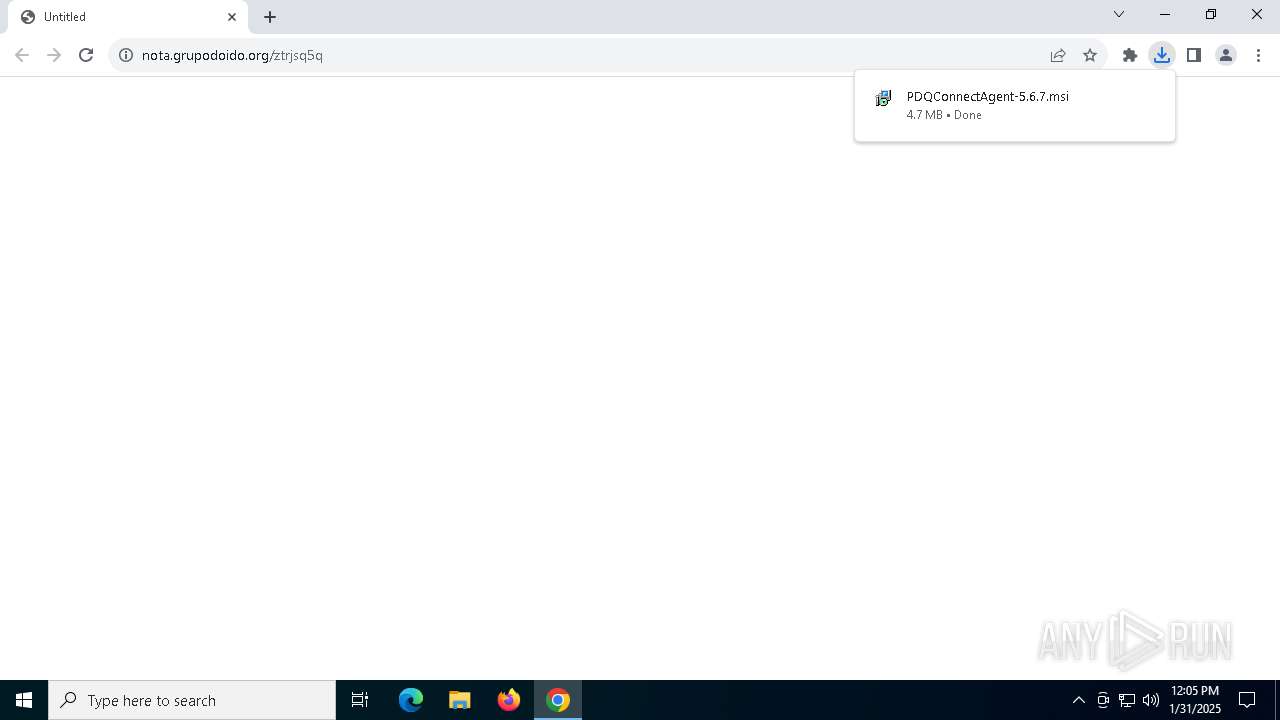
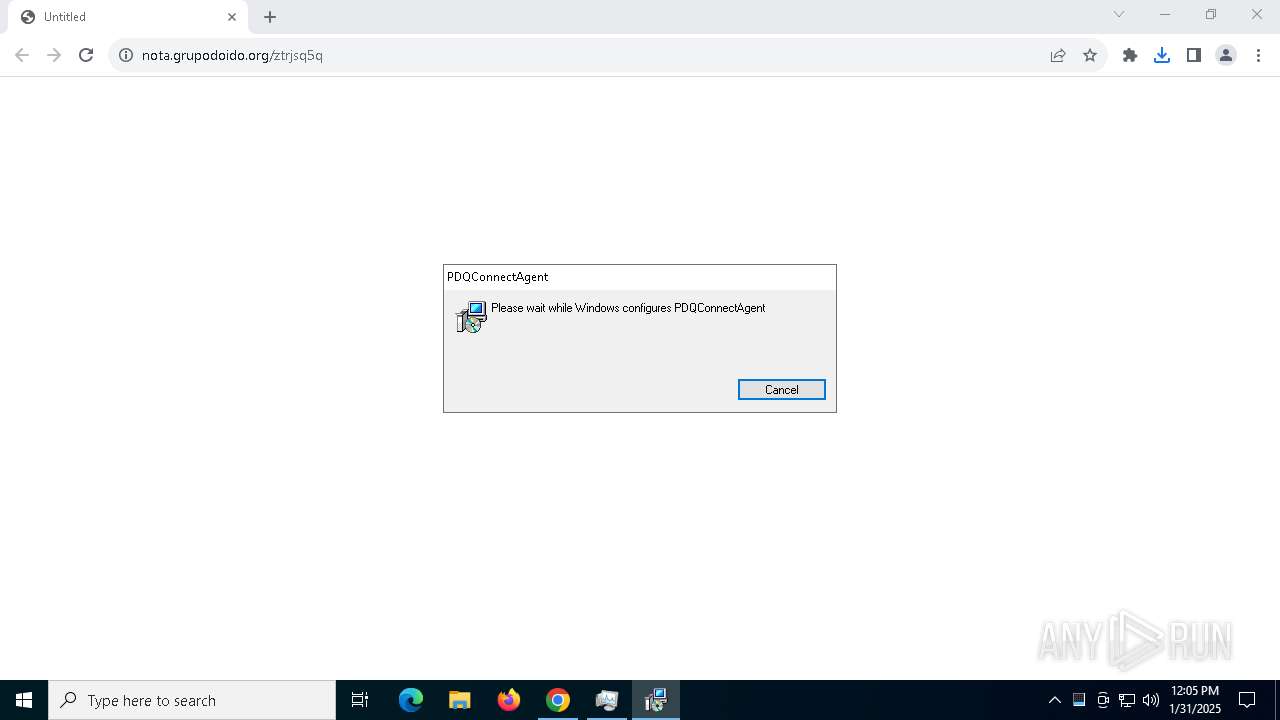
| URL: | https://nota.grupodoido.org/ztrjsq5q |
| Full analysis: | https://app.any.run/tasks/044f63e5-2631-499c-a431-327e03cf5573 |
| Verdict: | Malicious activity |
| Analysis date: | January 31, 2025, 12:05:06 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 235B96B62DBAE01286B7DE6EAD4A9202 |
| SHA1: | 6B053284B0EFC7A45D06C63D32C42127440D0866 |
| SHA256: | A4BFAFE7DCBE3743BE82B569F92535EBE6D0EC459D72944E1880F9E3F375B11A |
| SSDEEP: | 3:N8t2AVK8vf4rB:2cAVK8vfC |
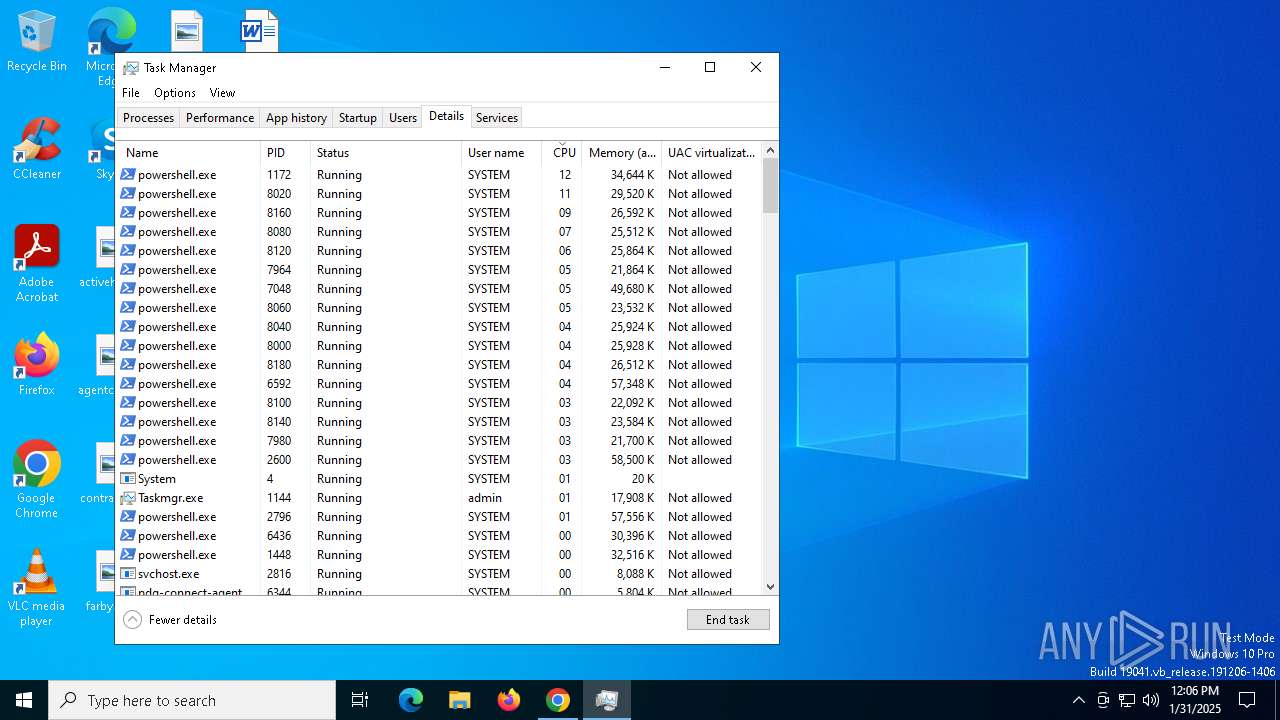
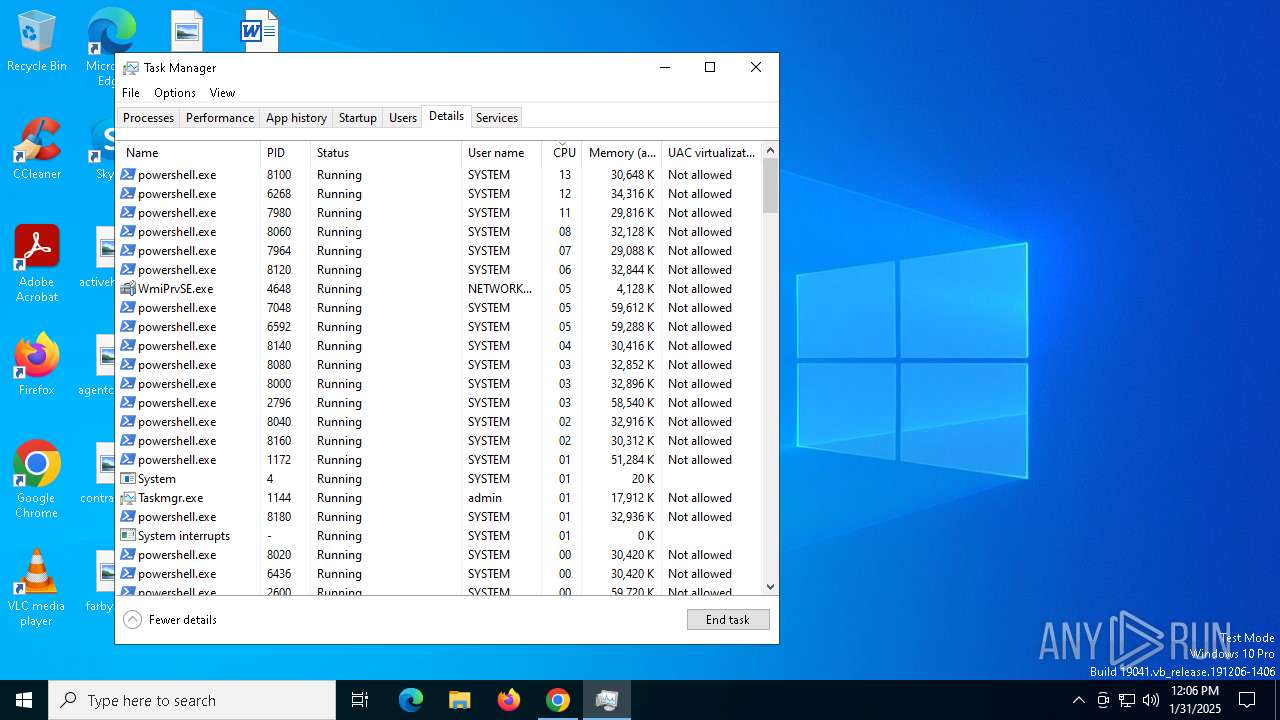
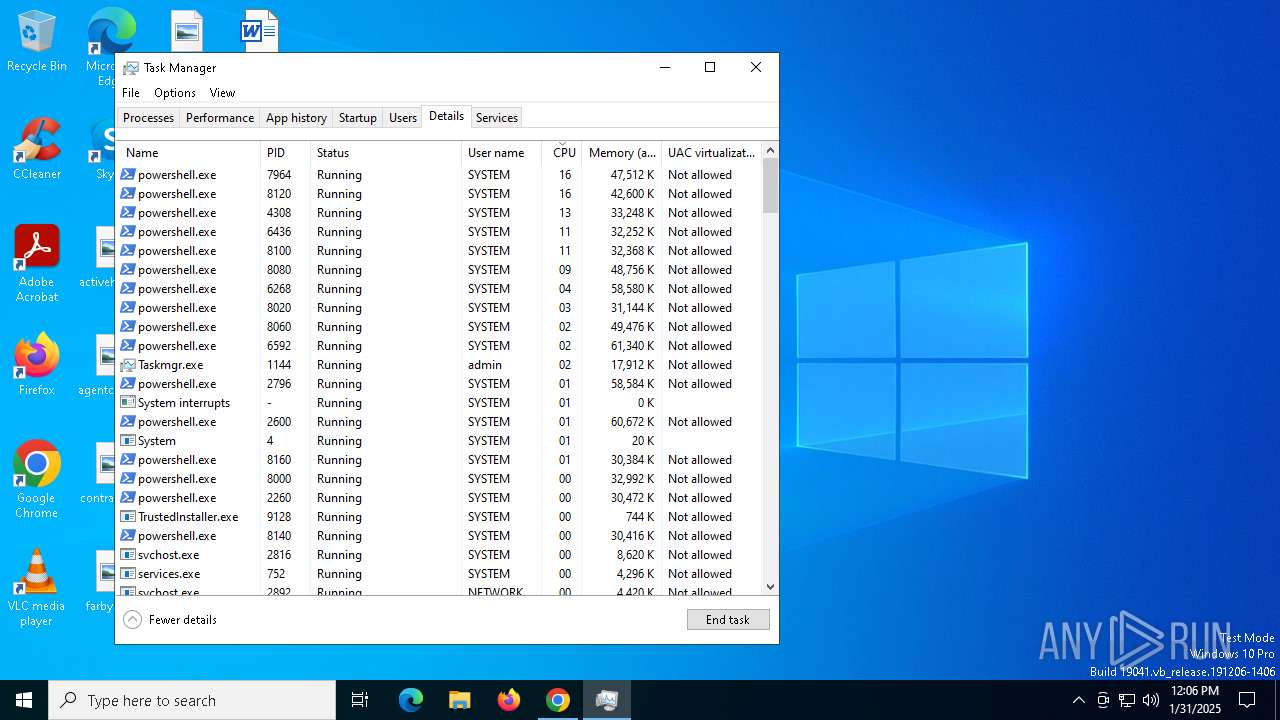
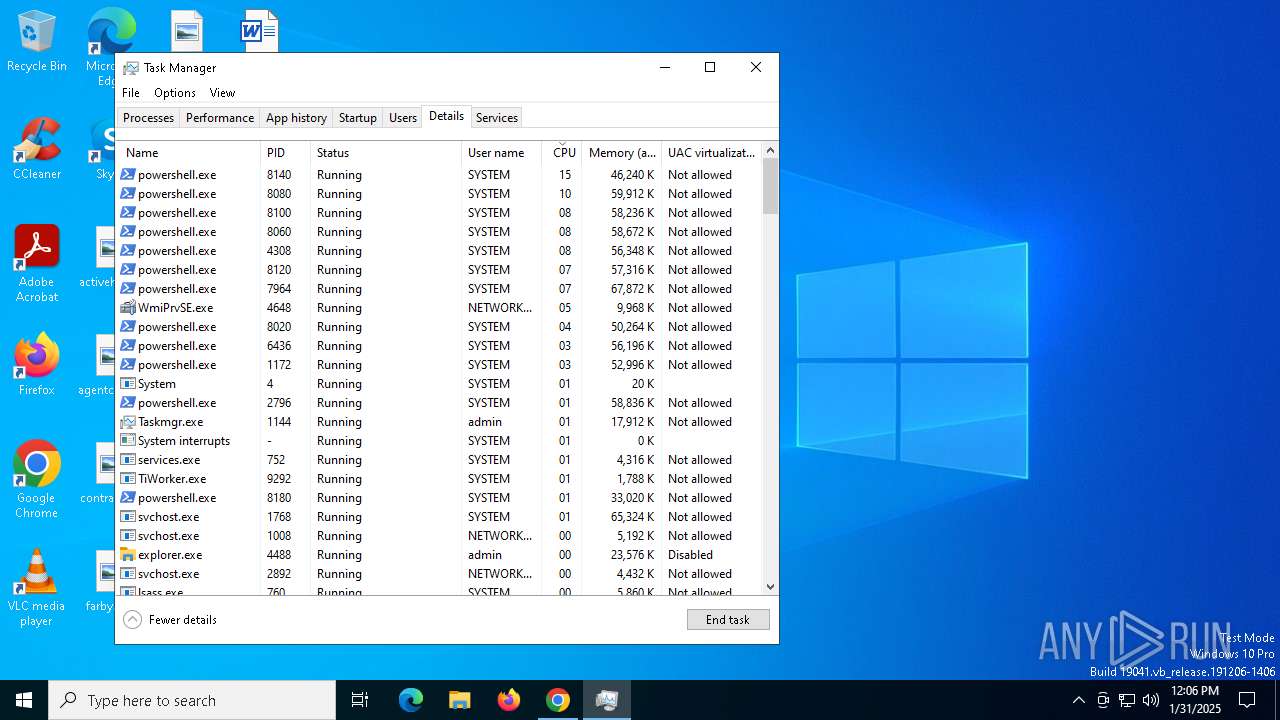
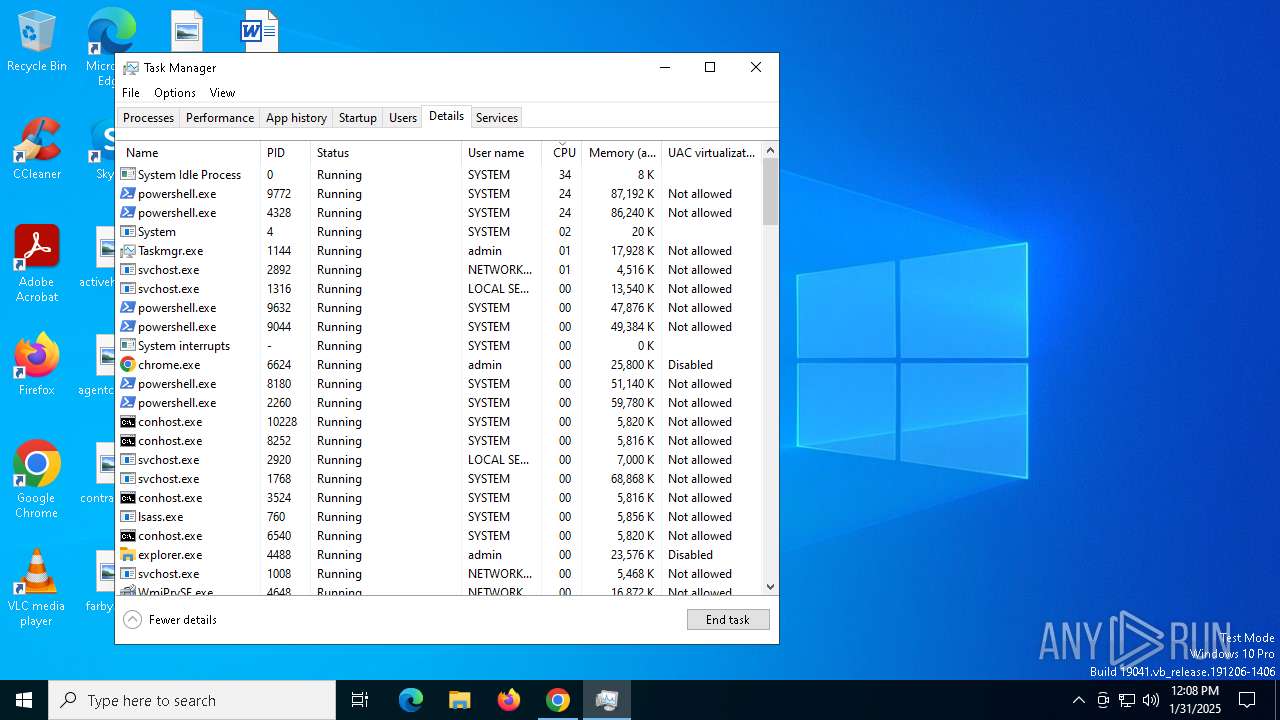
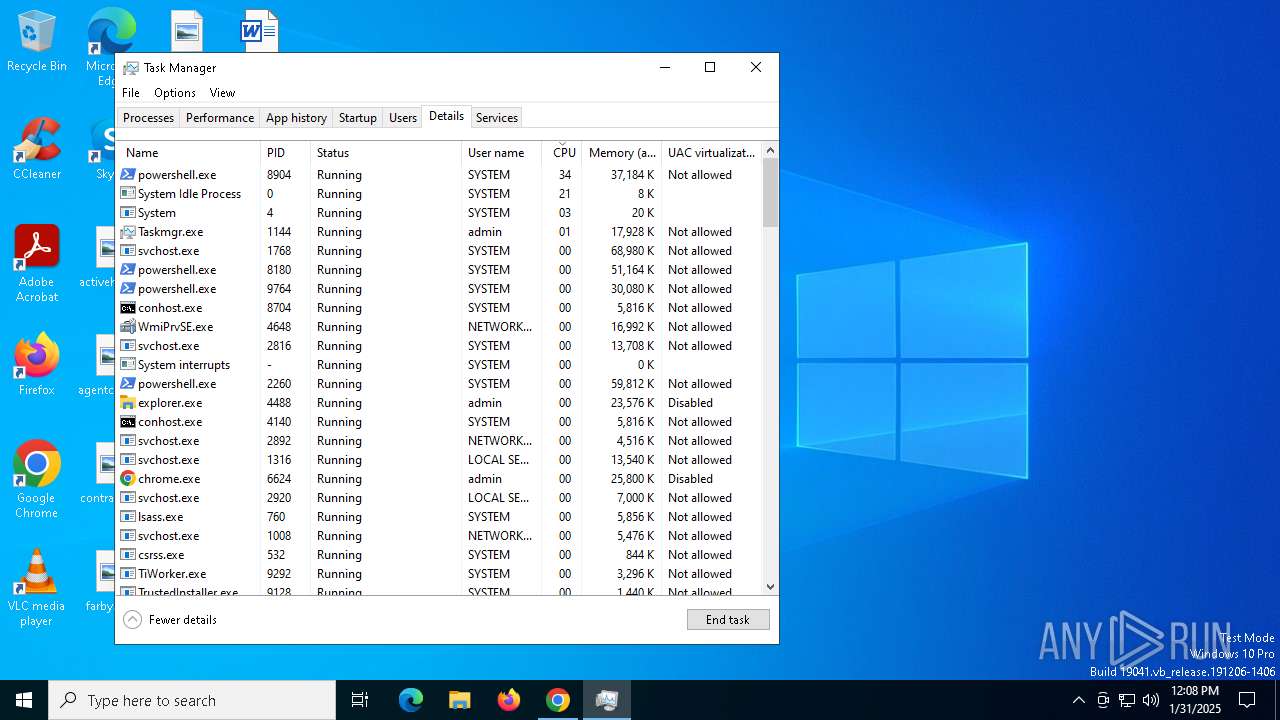
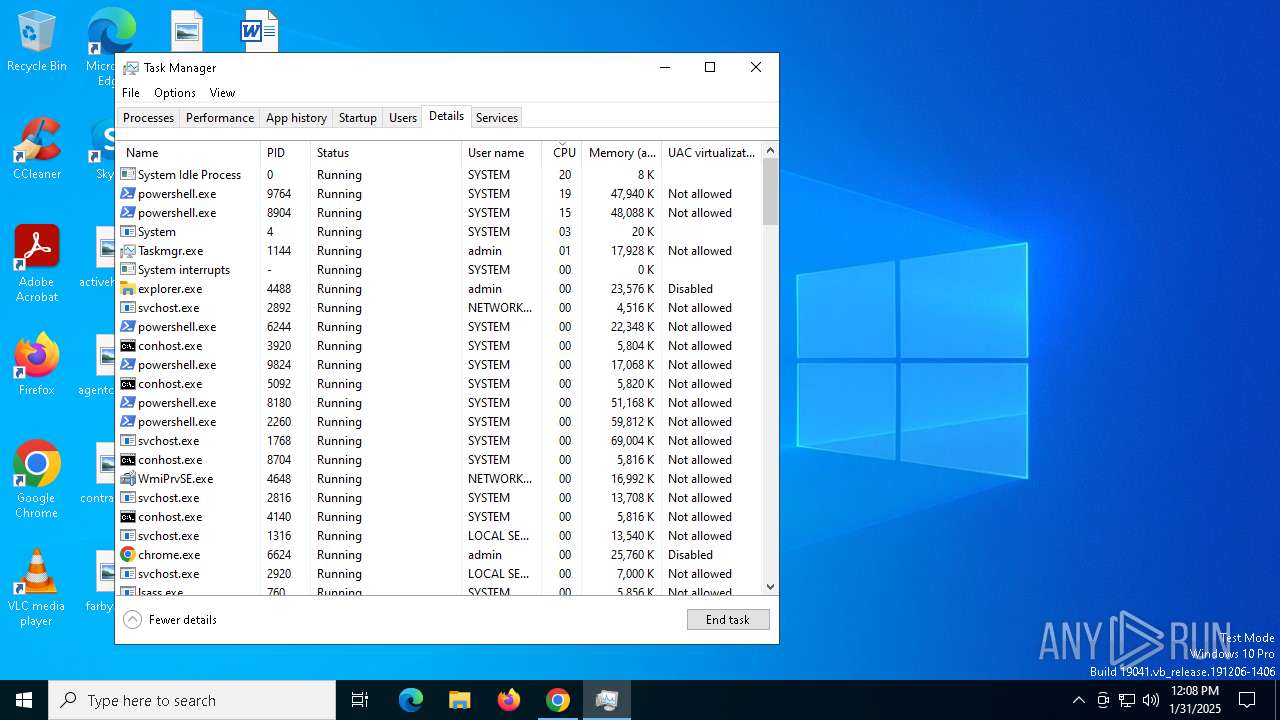
MALICIOUS
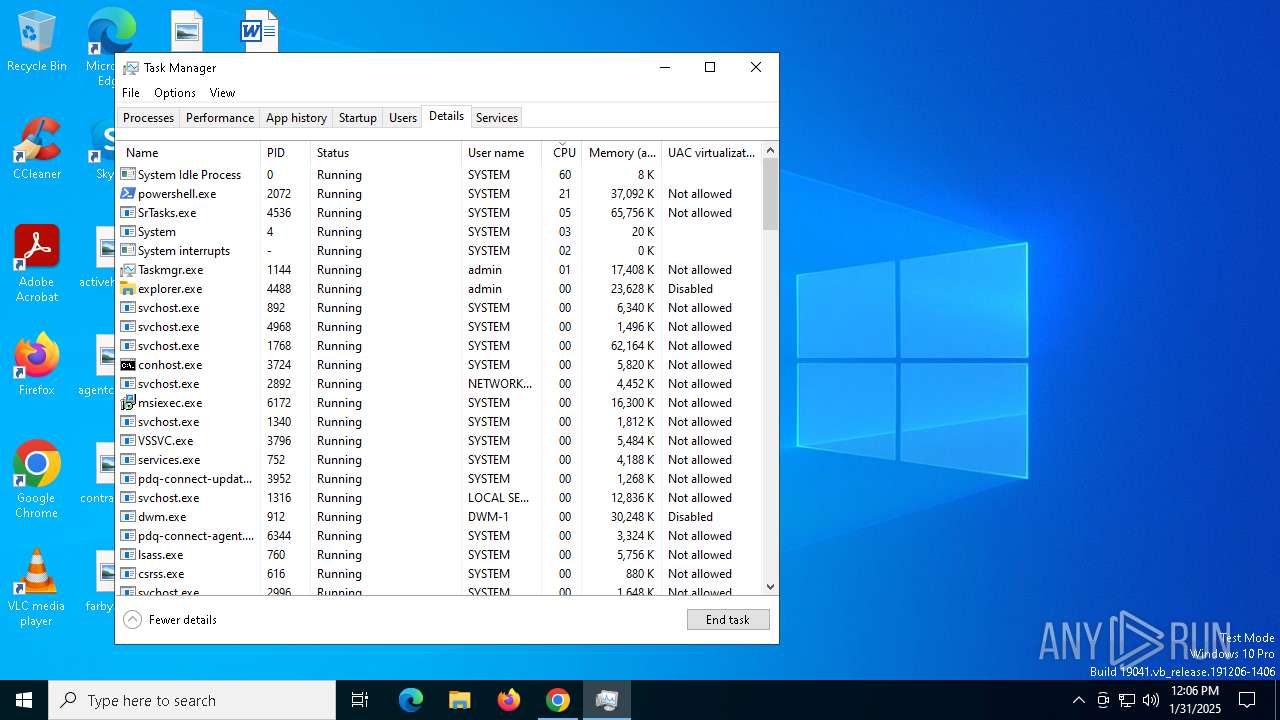
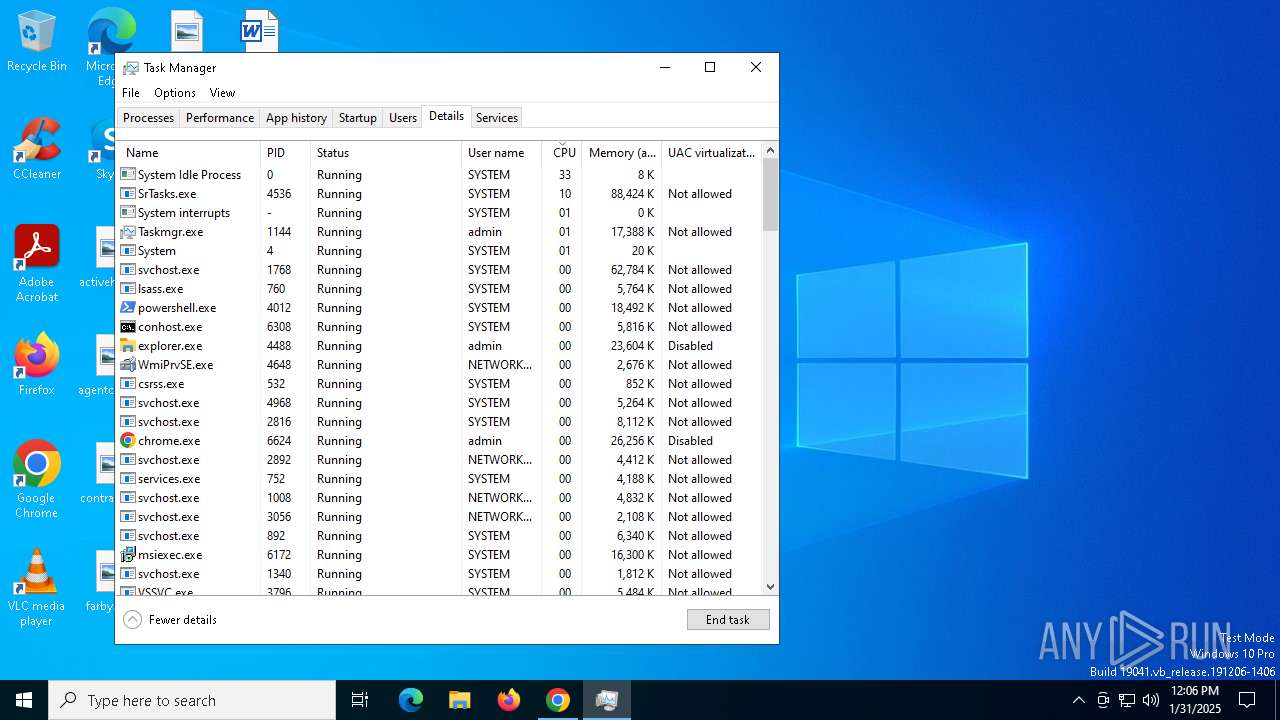
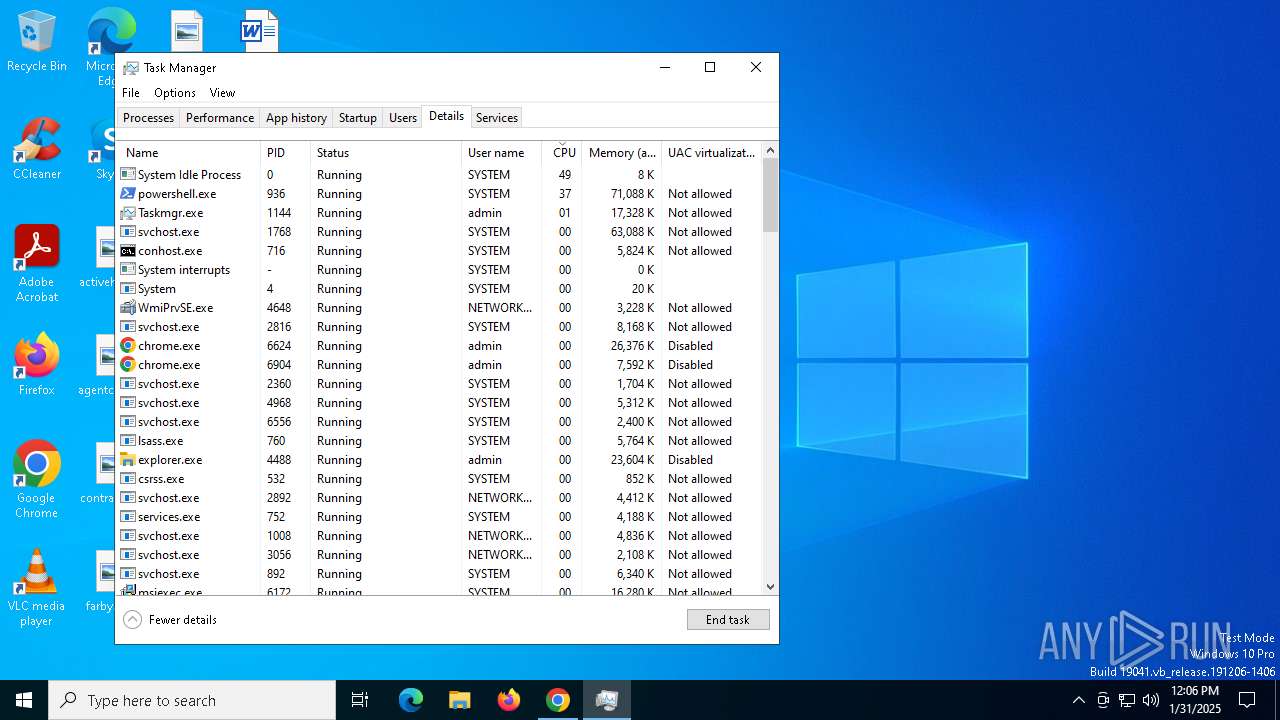
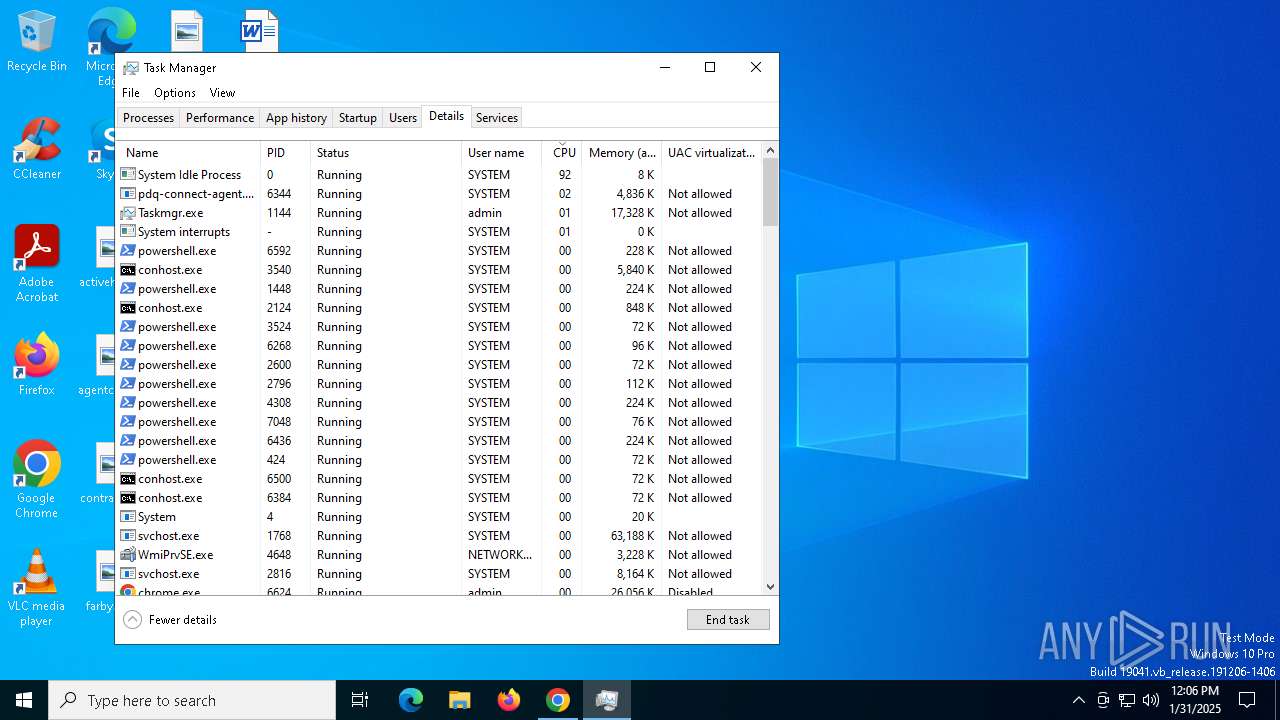
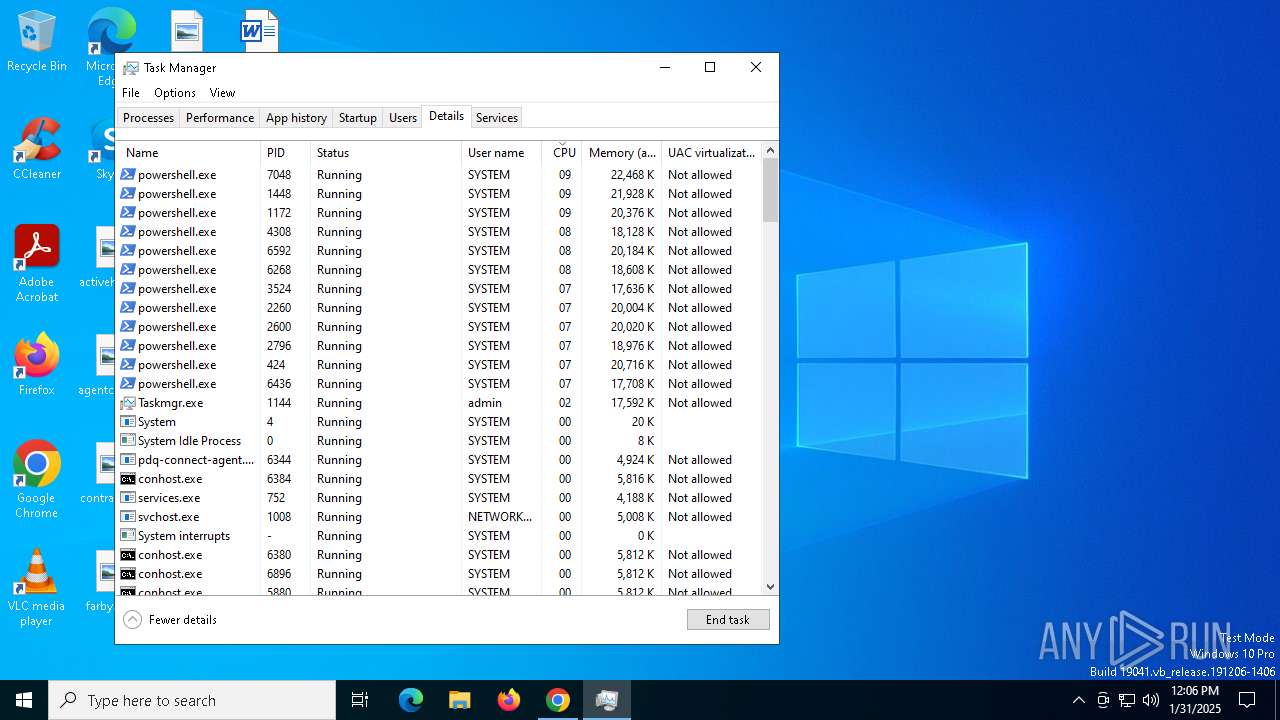
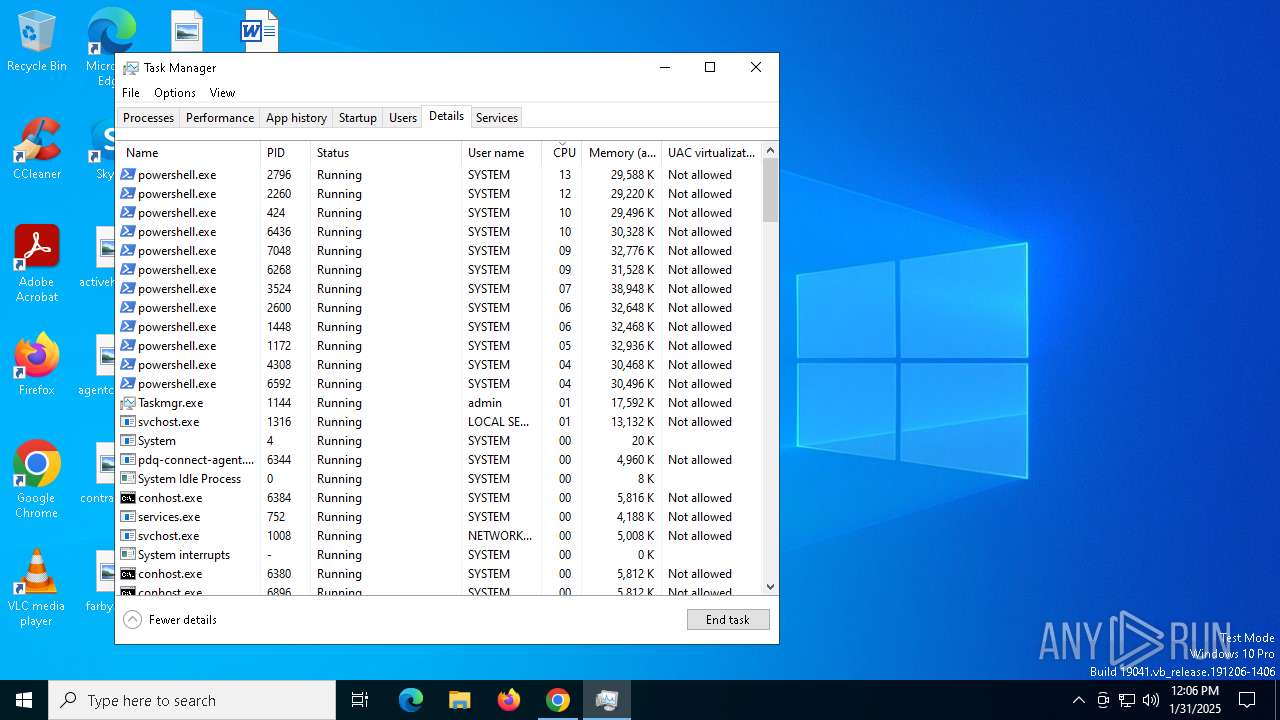
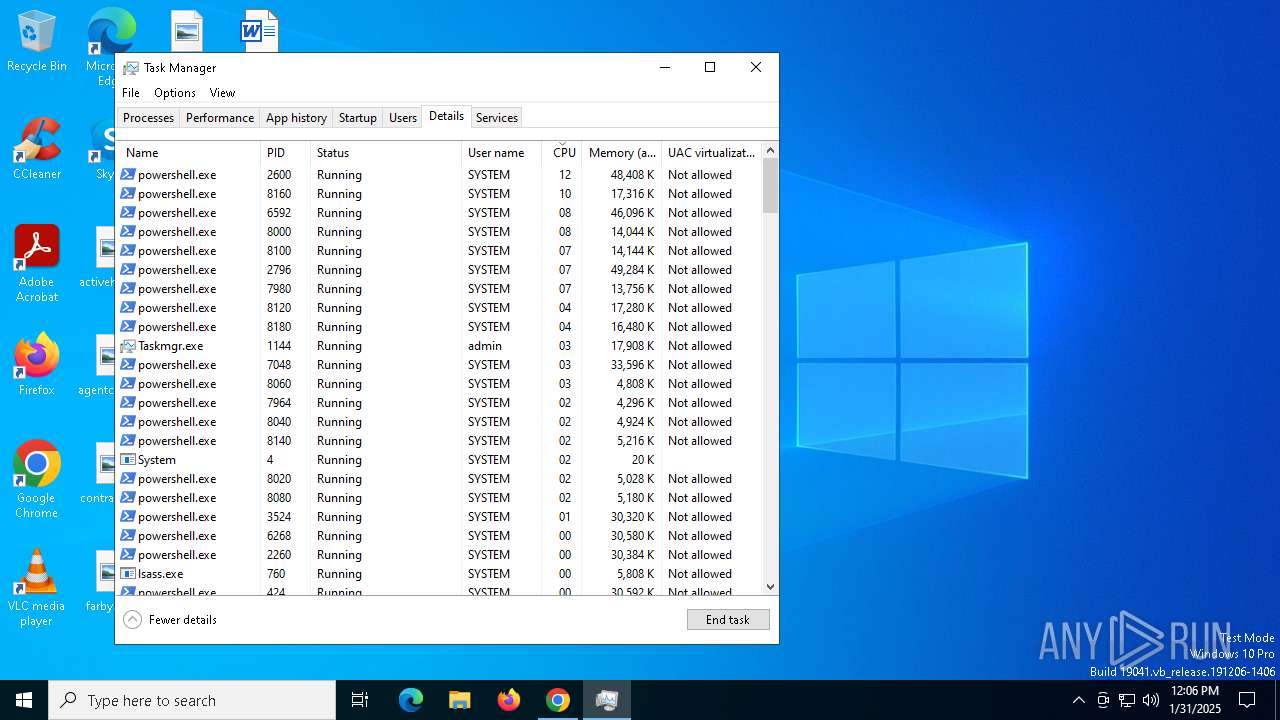
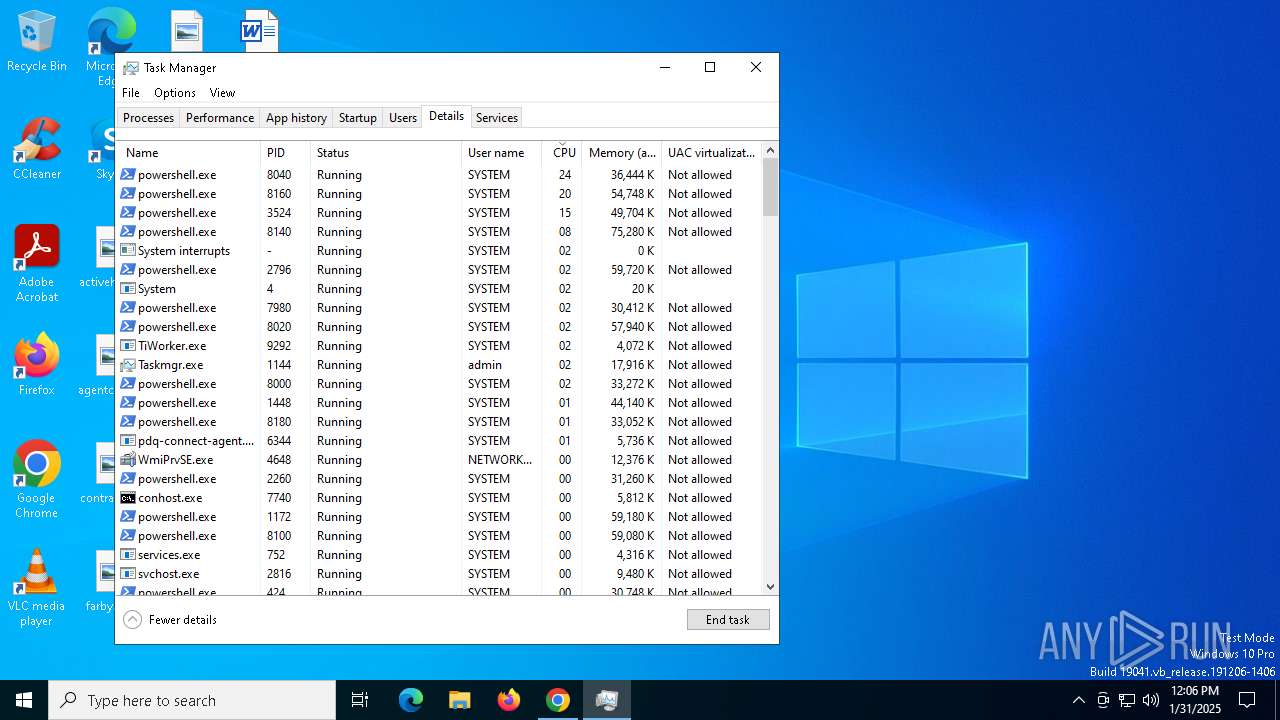
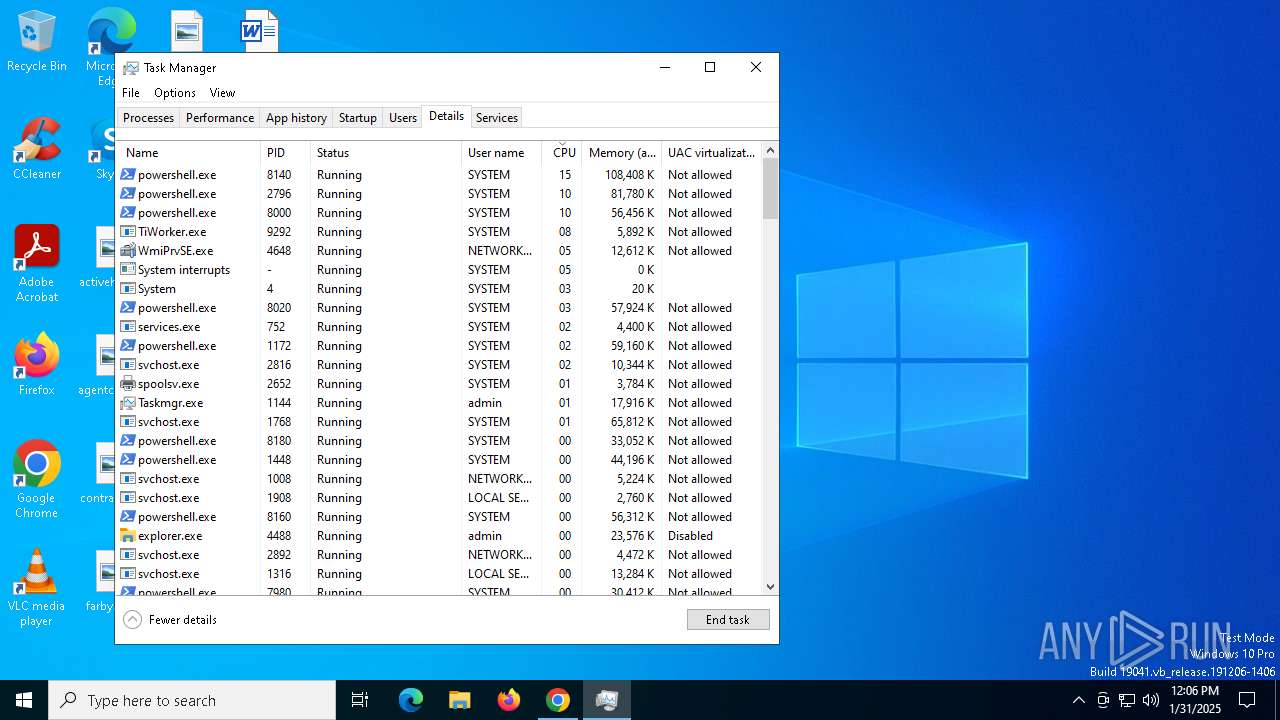
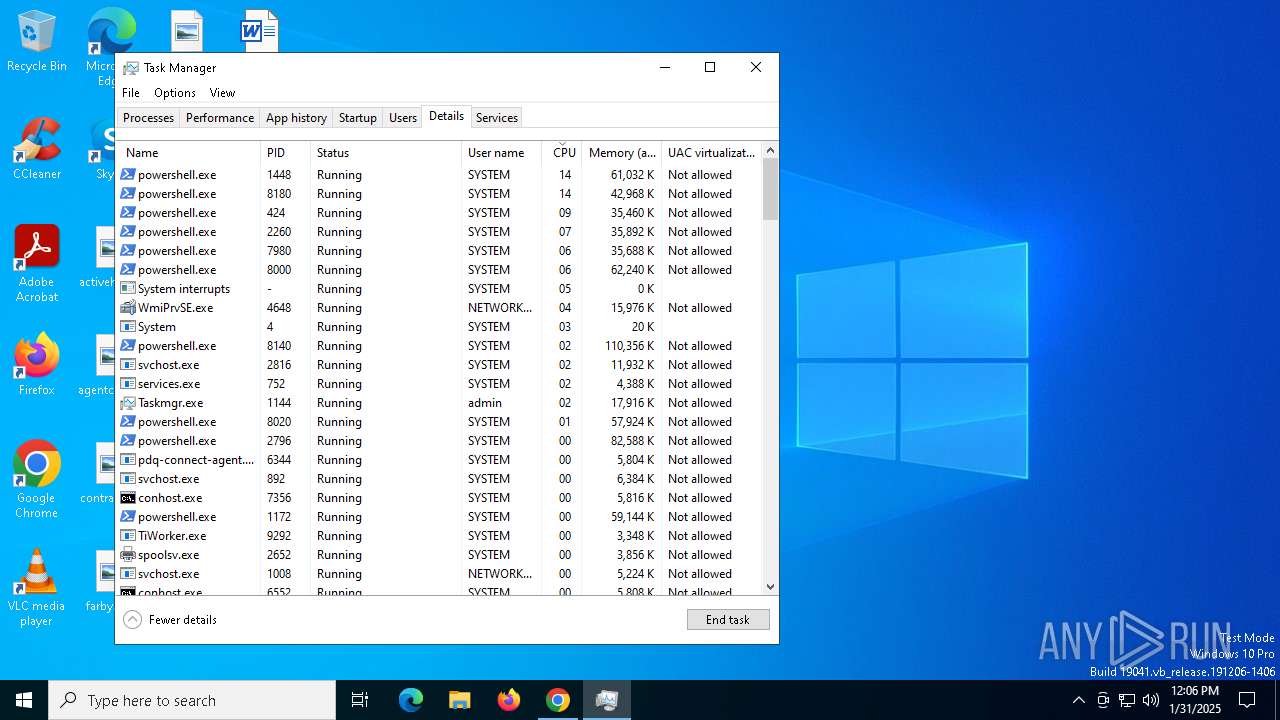
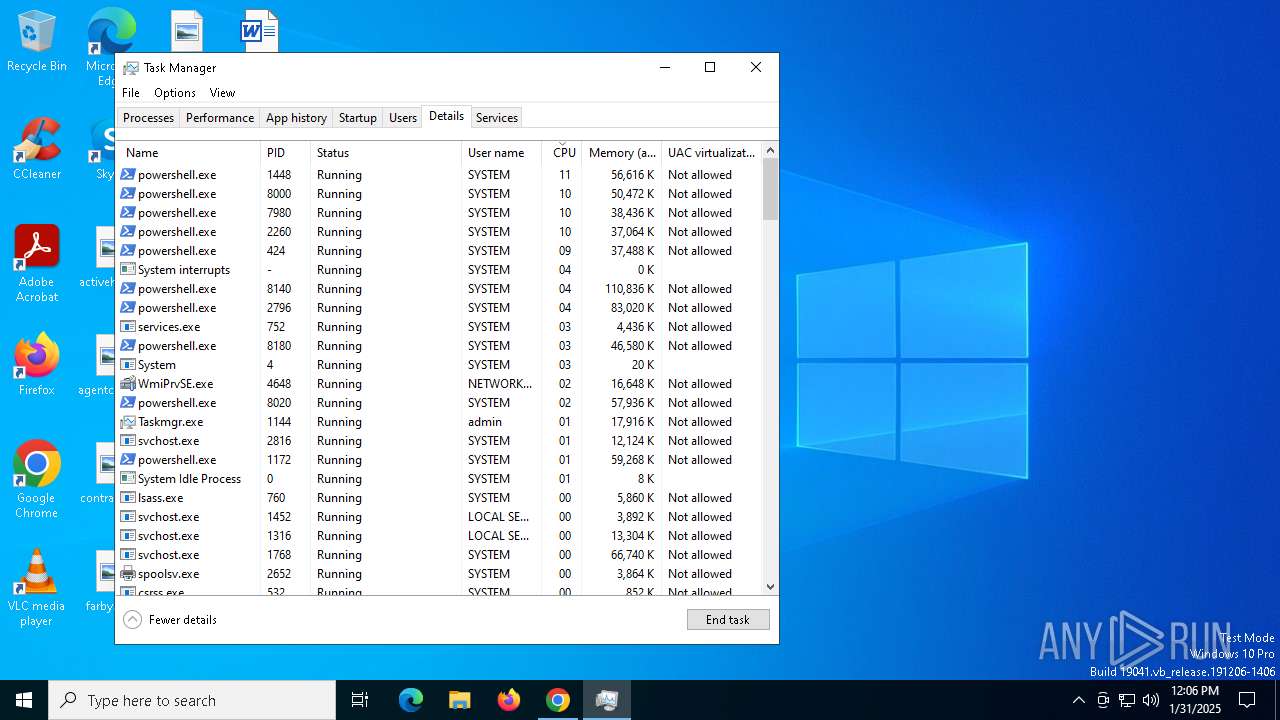
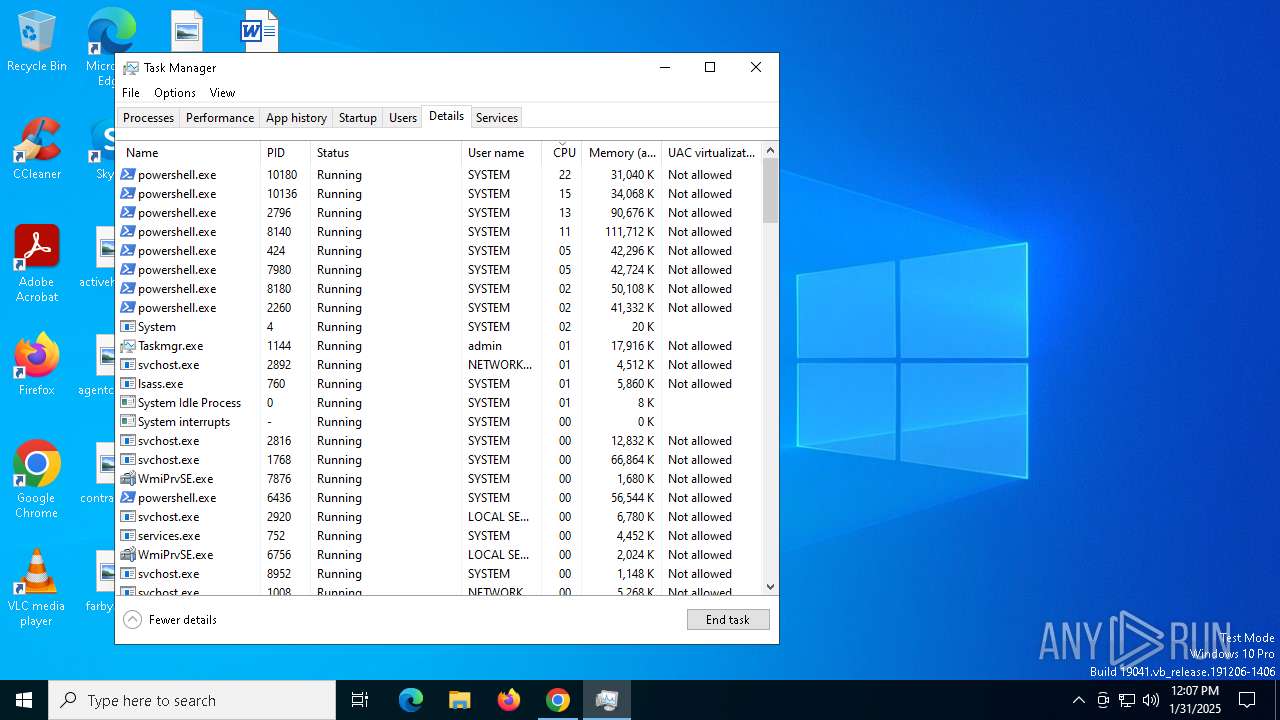
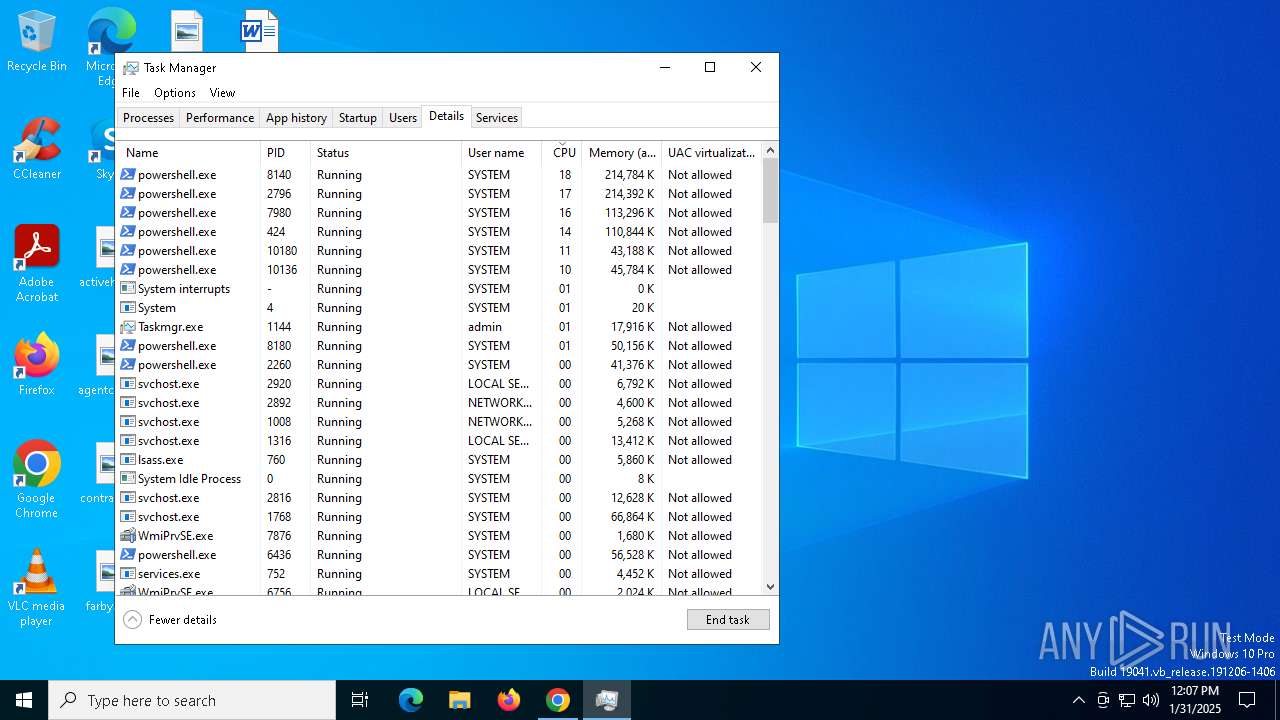
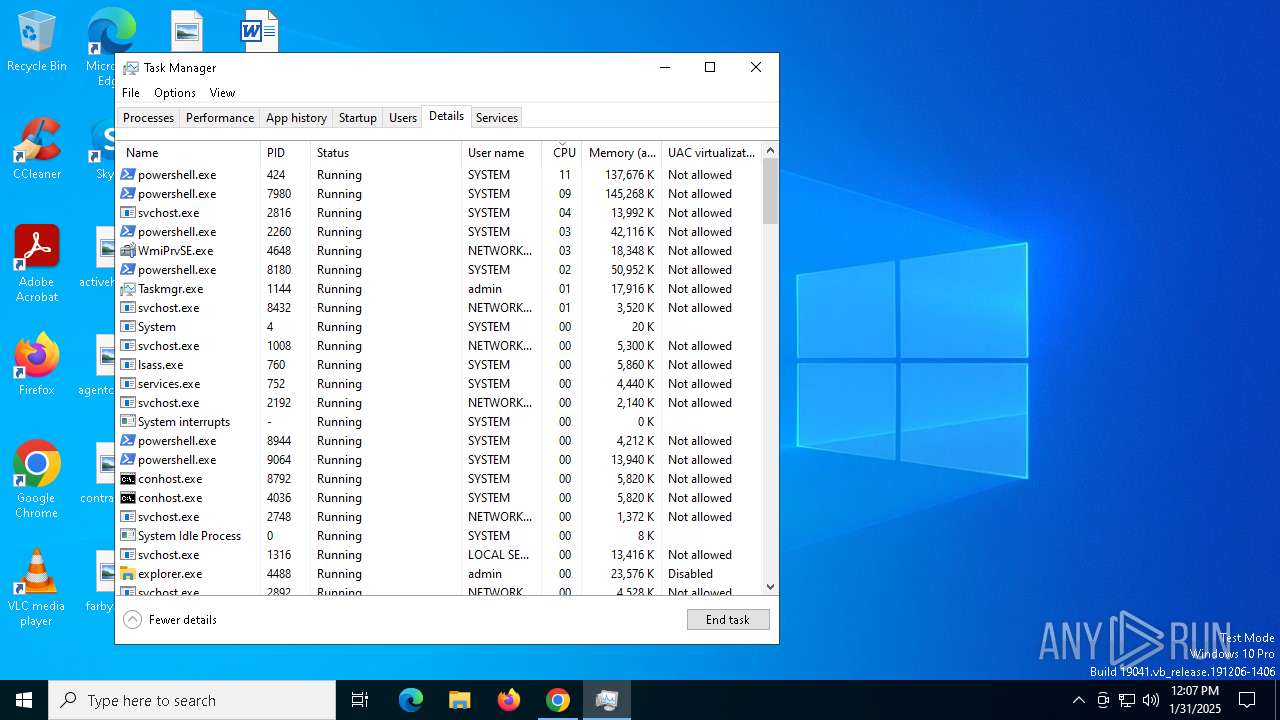
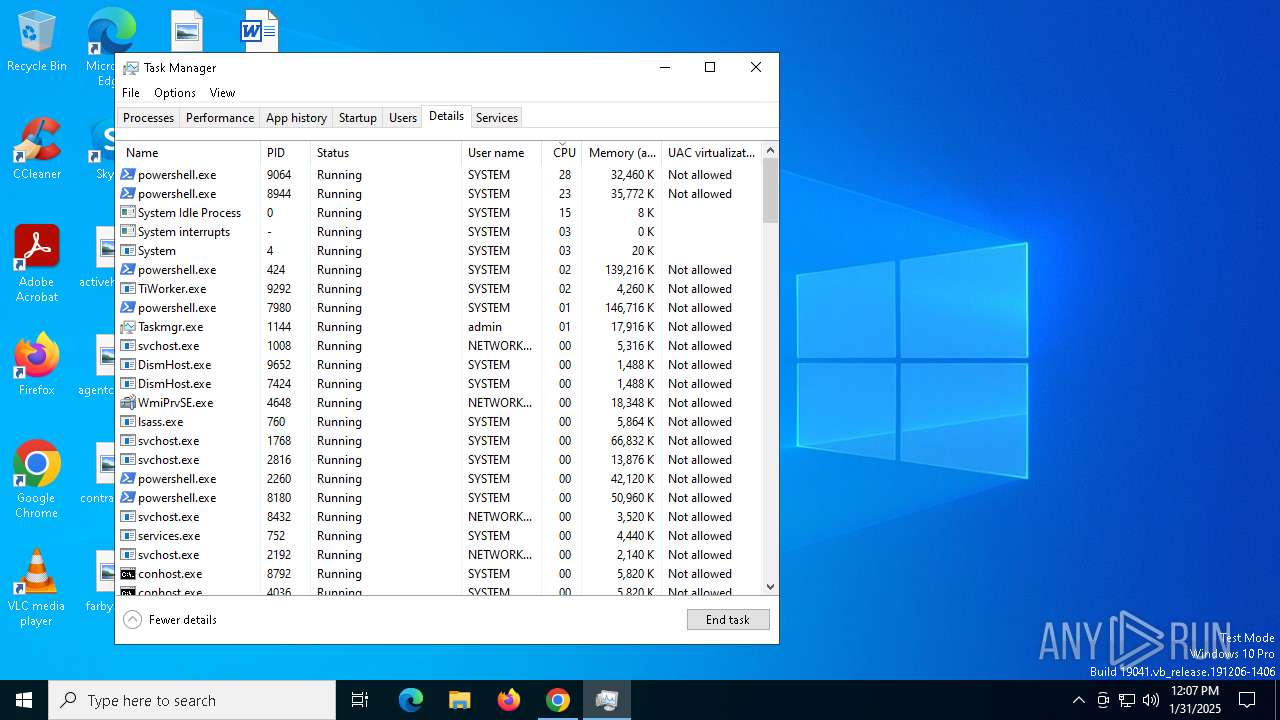
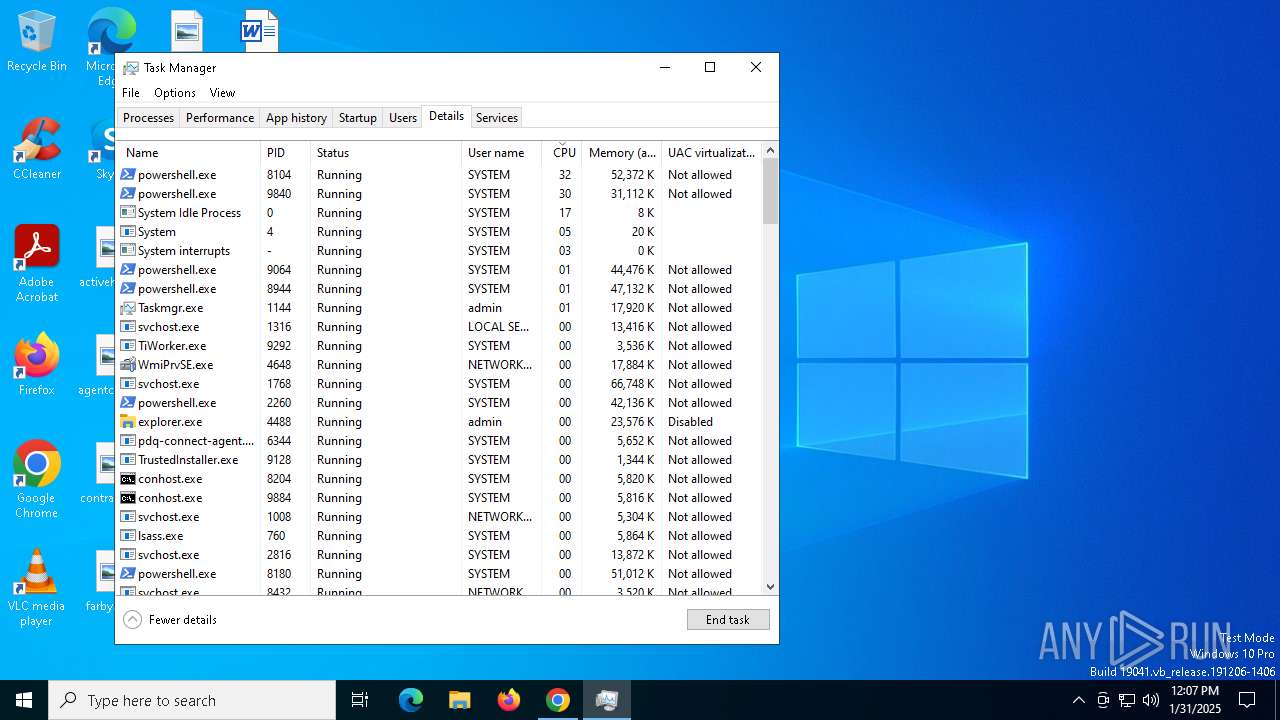
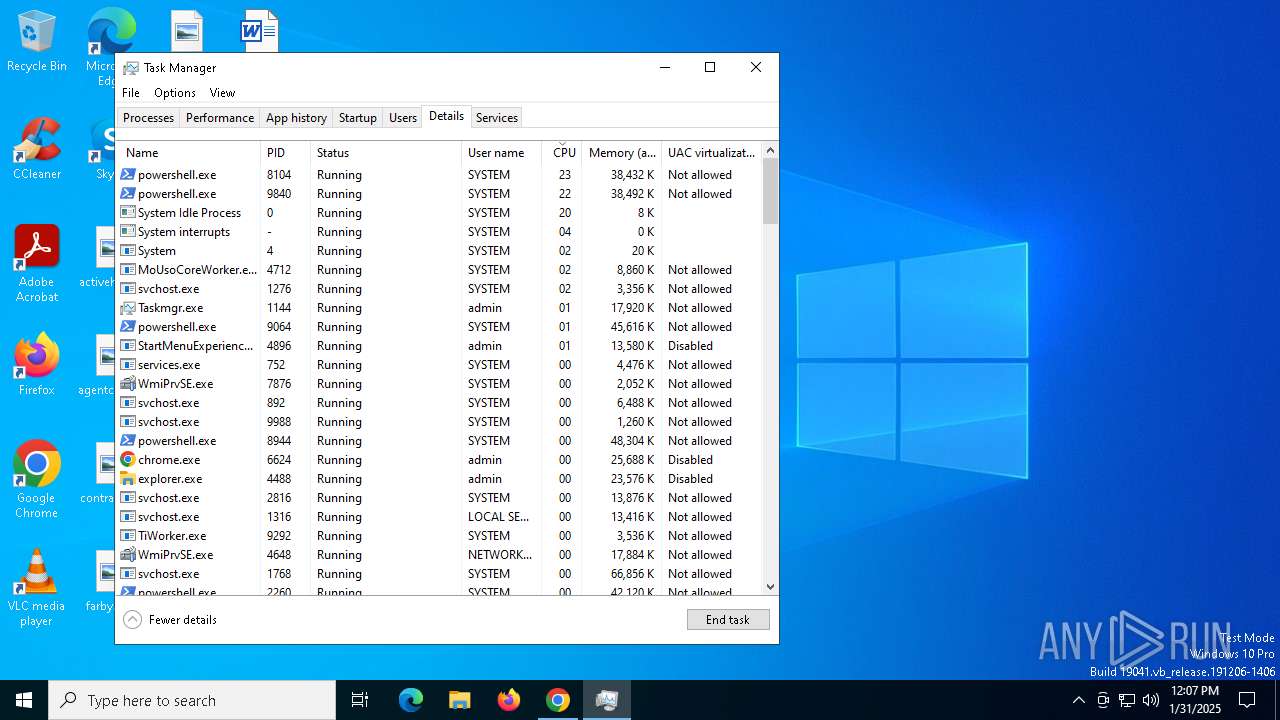
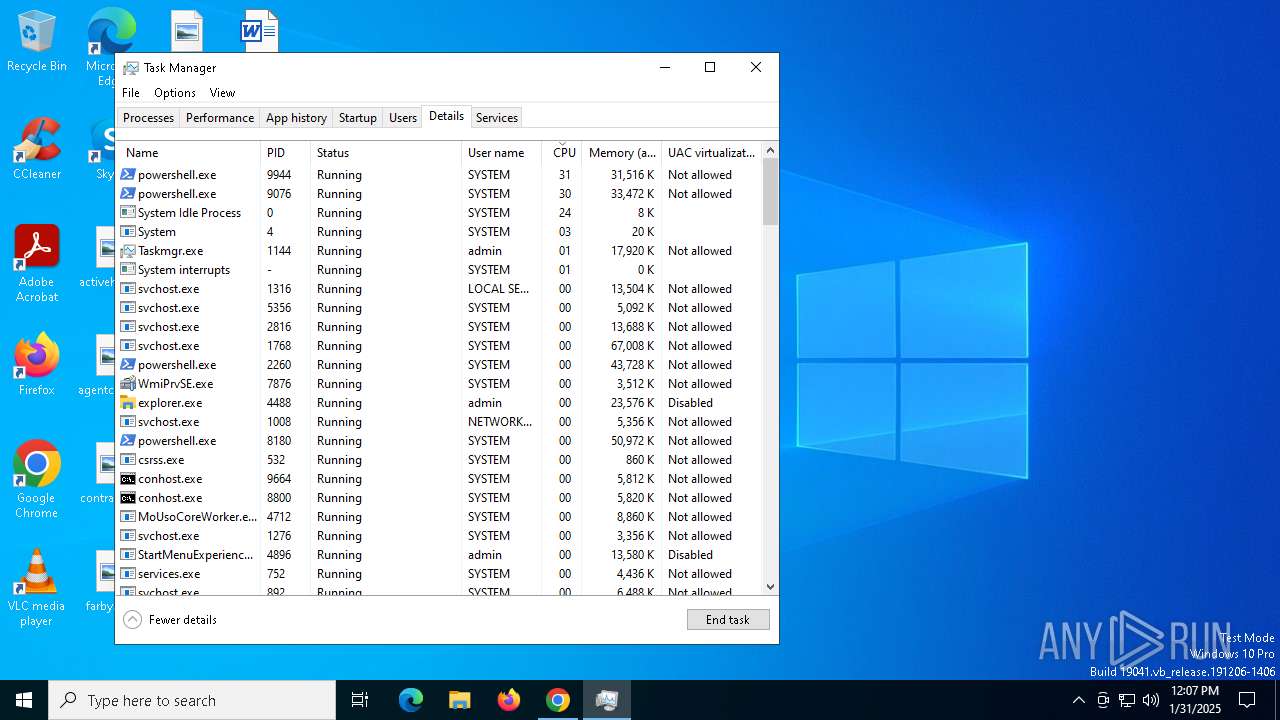
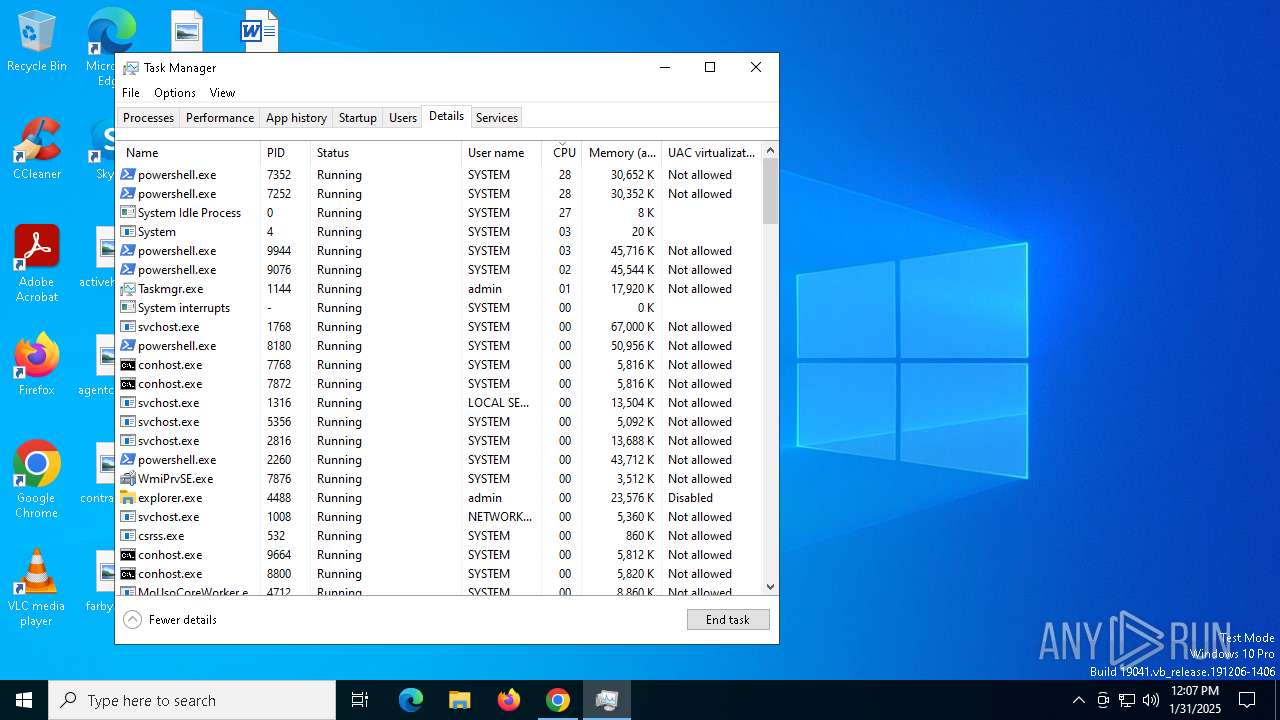
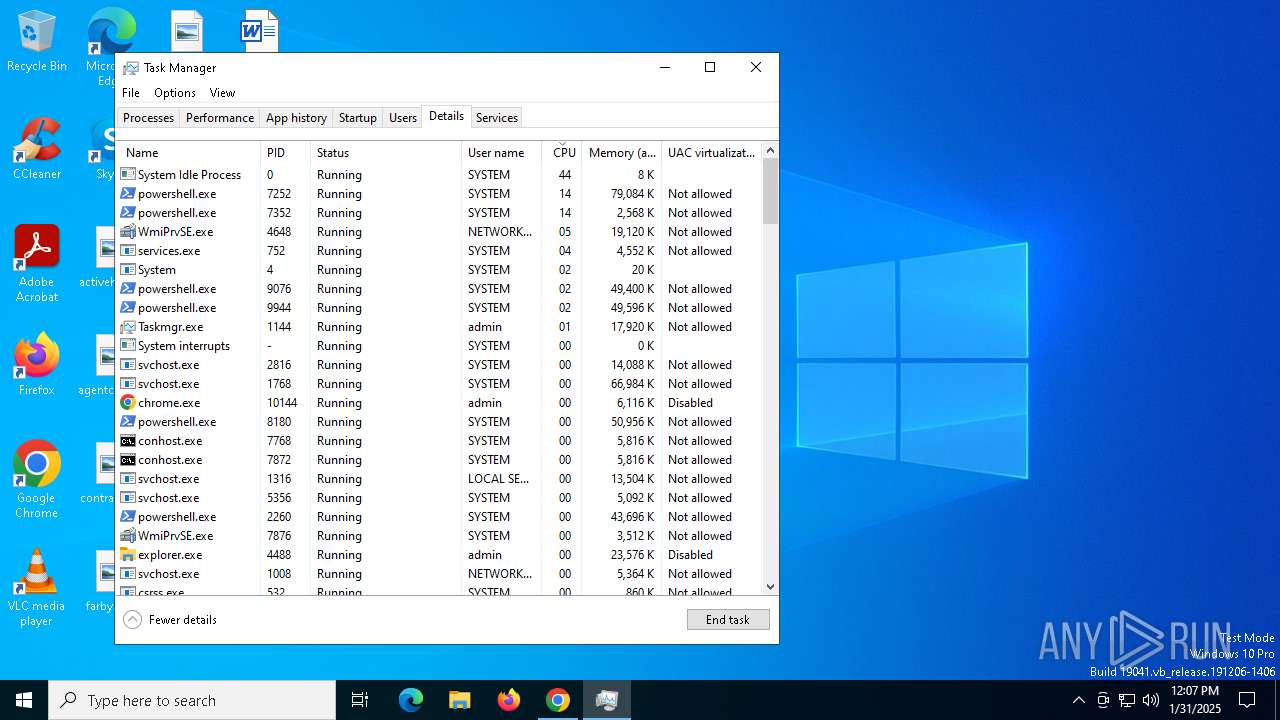
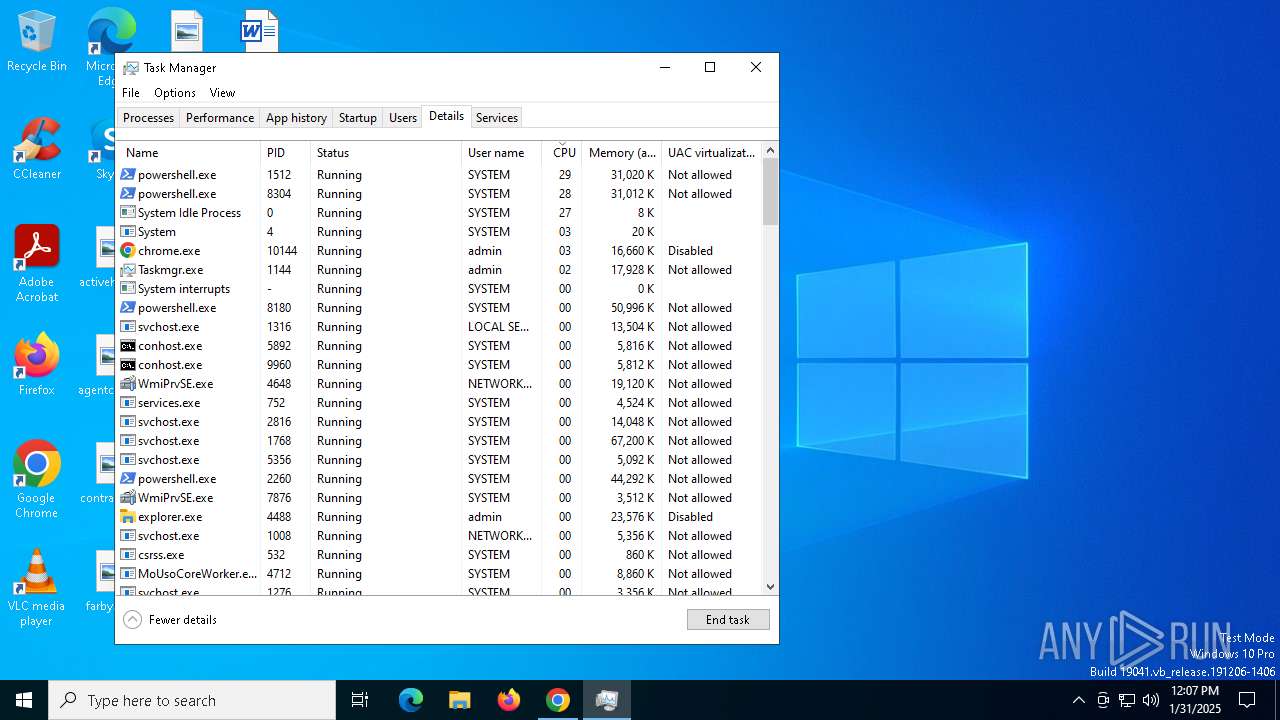
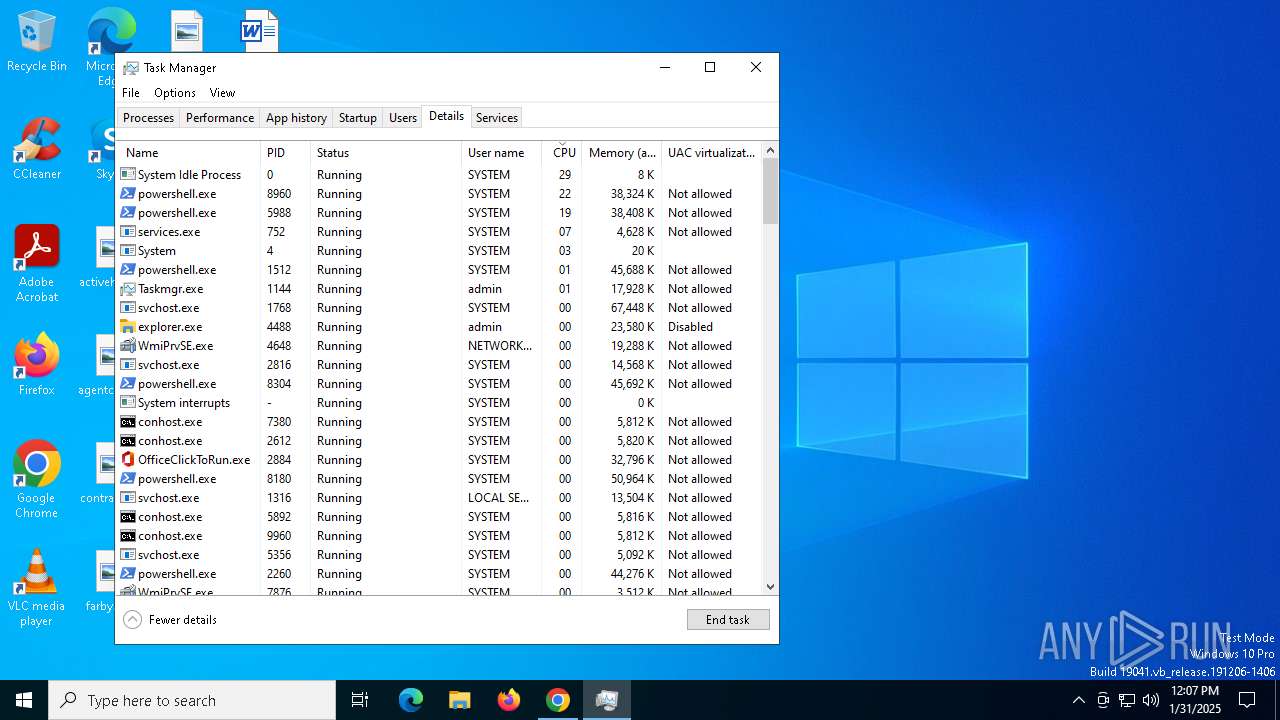
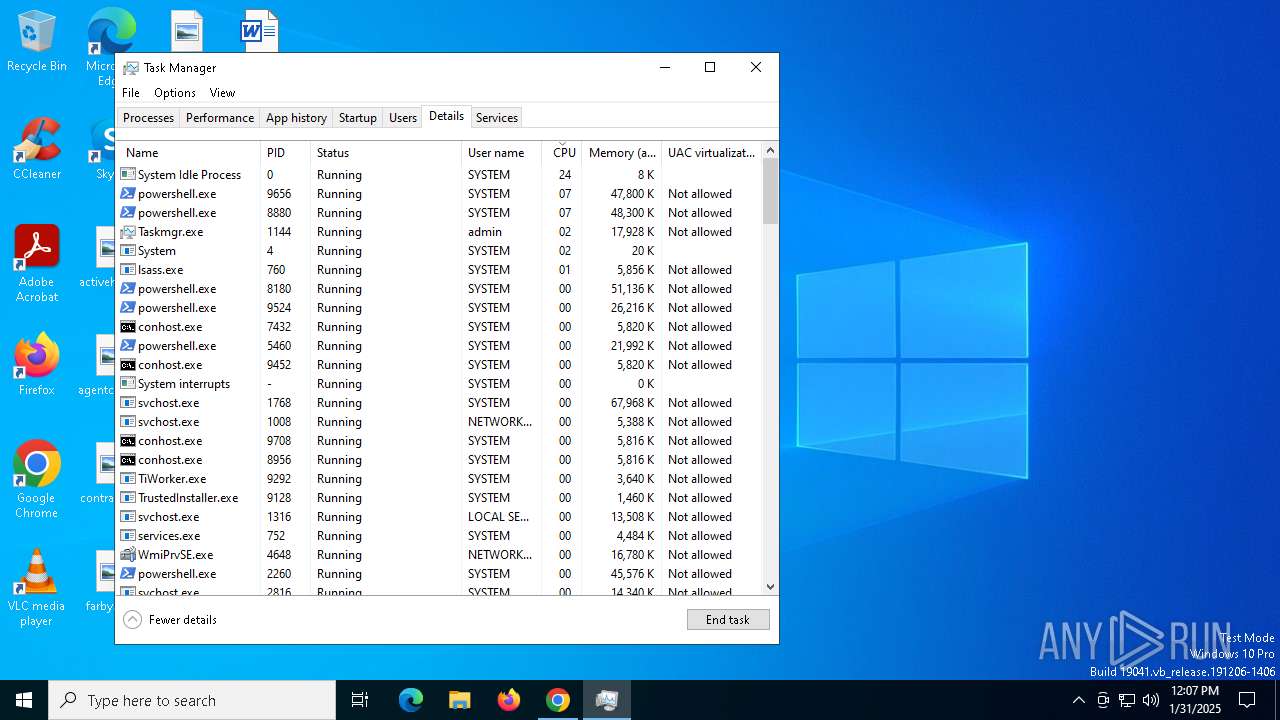
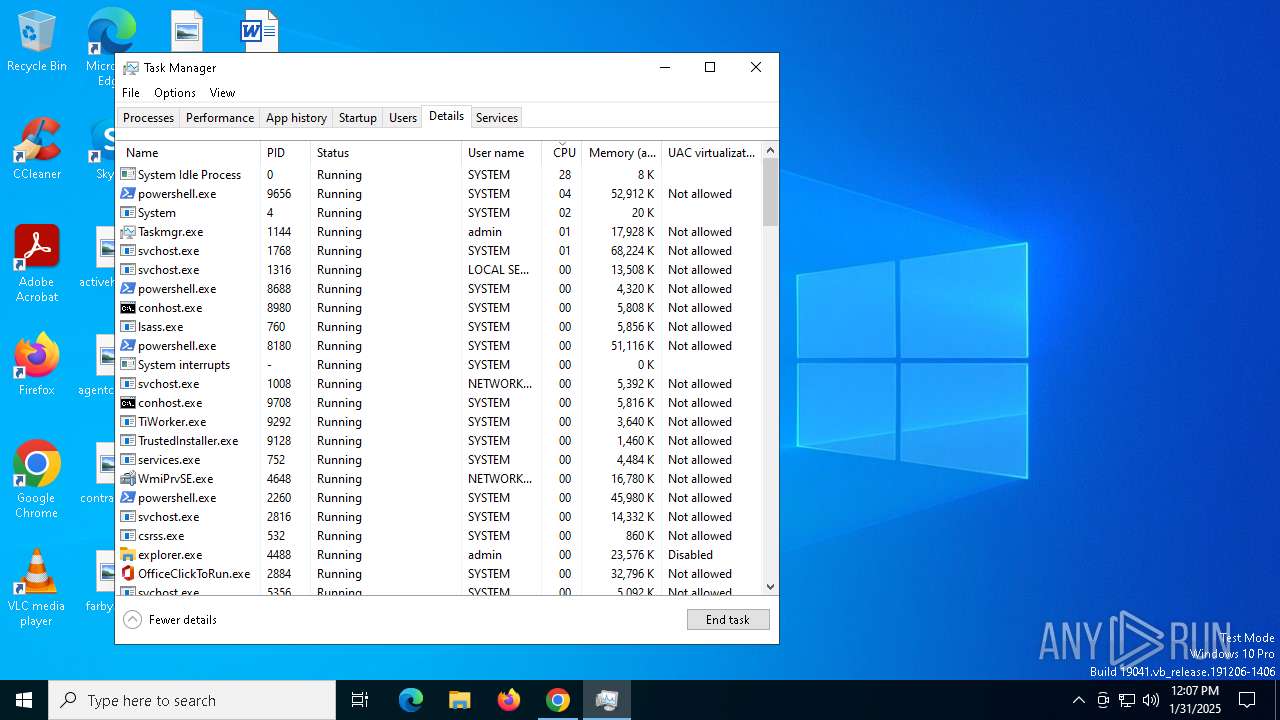
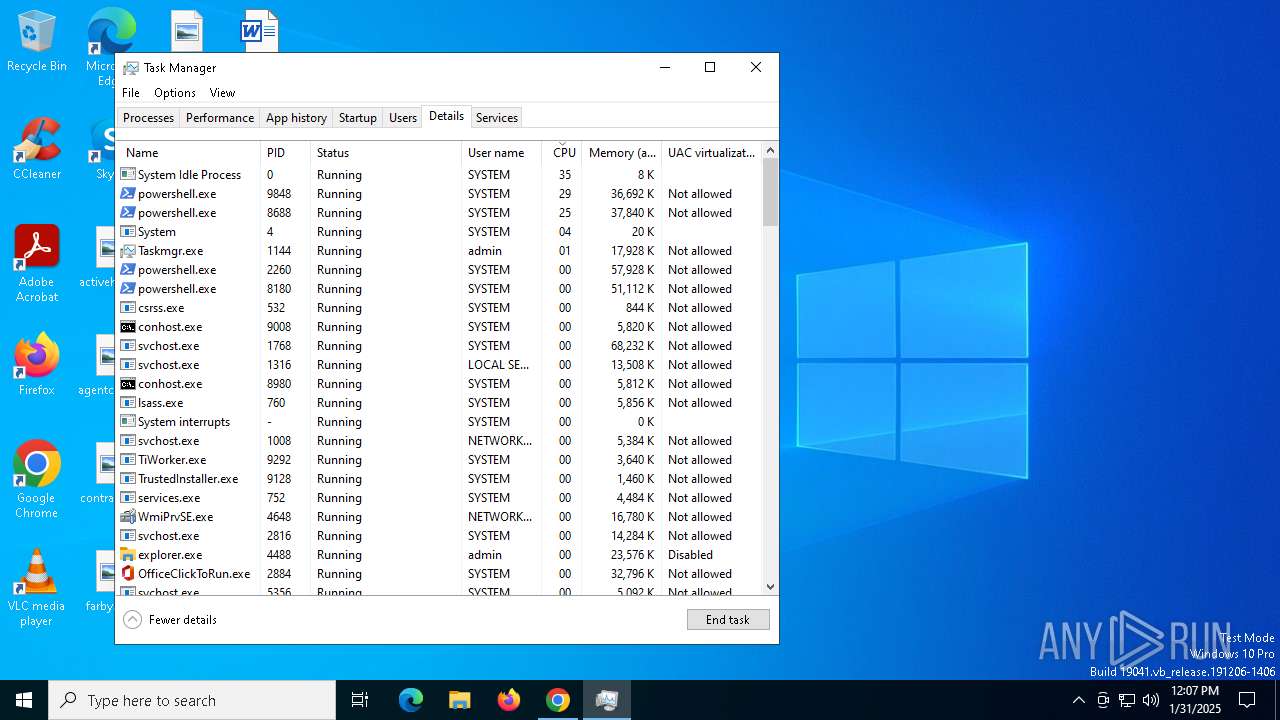
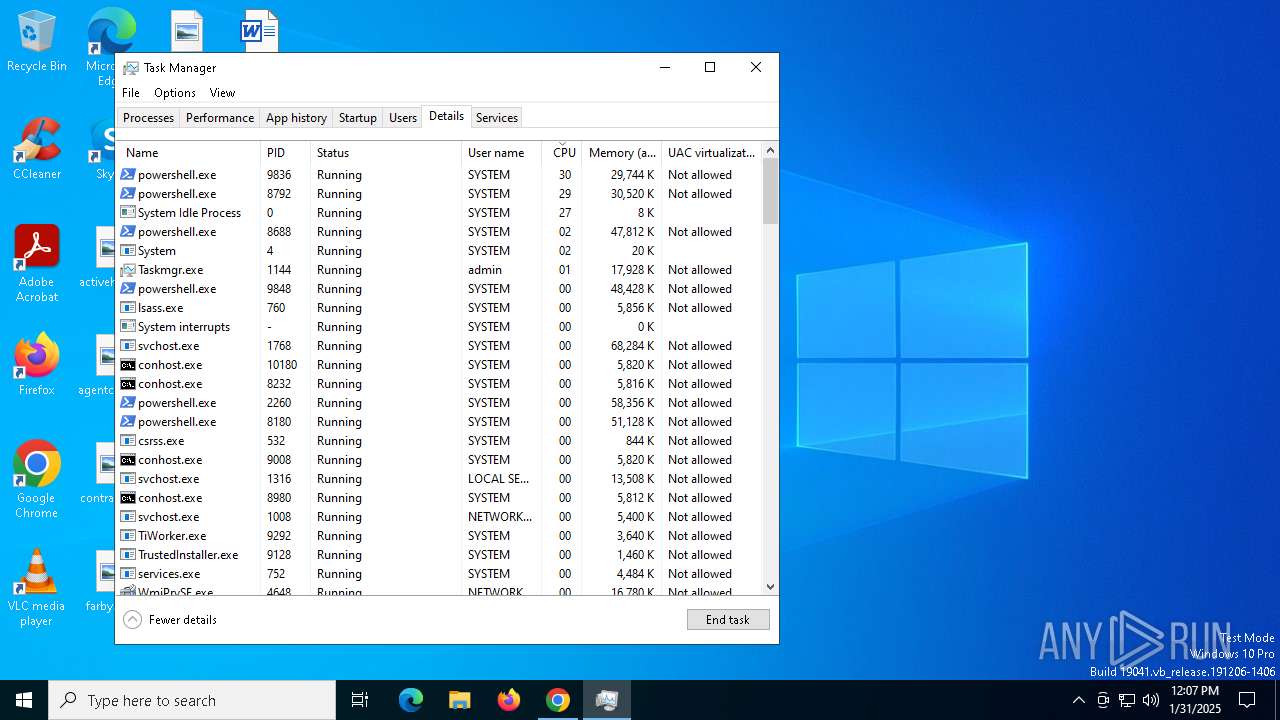
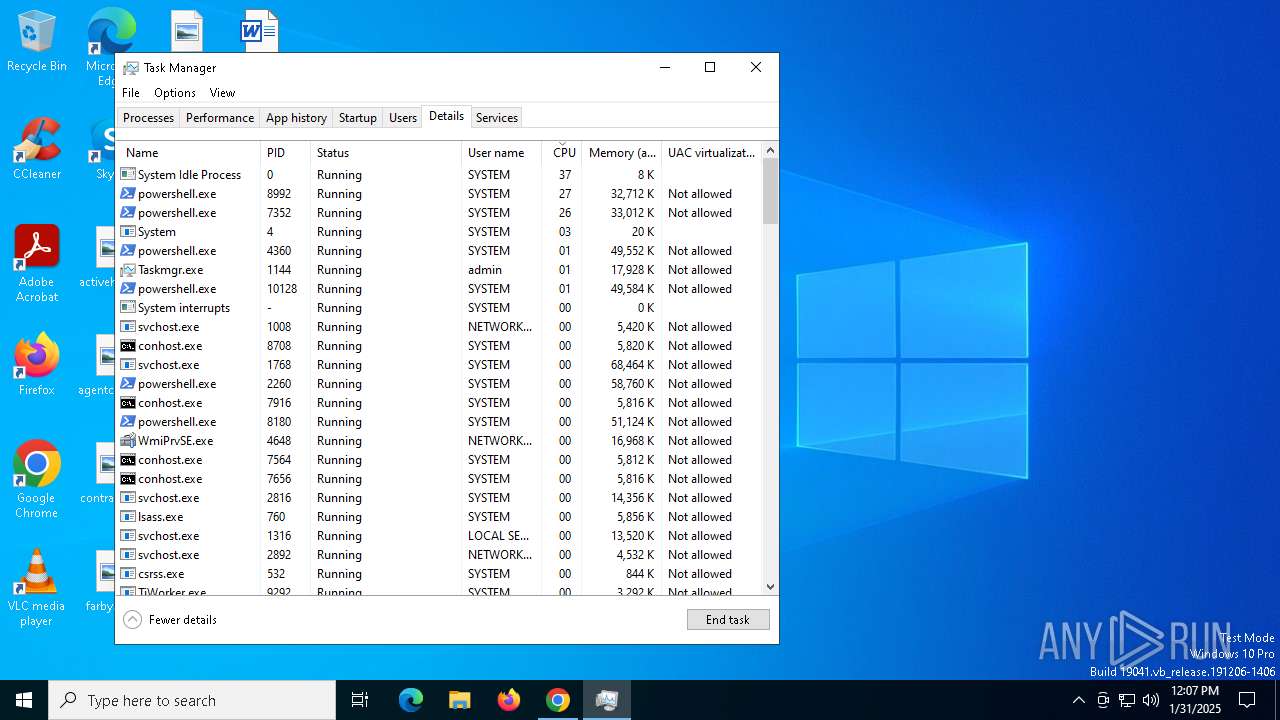
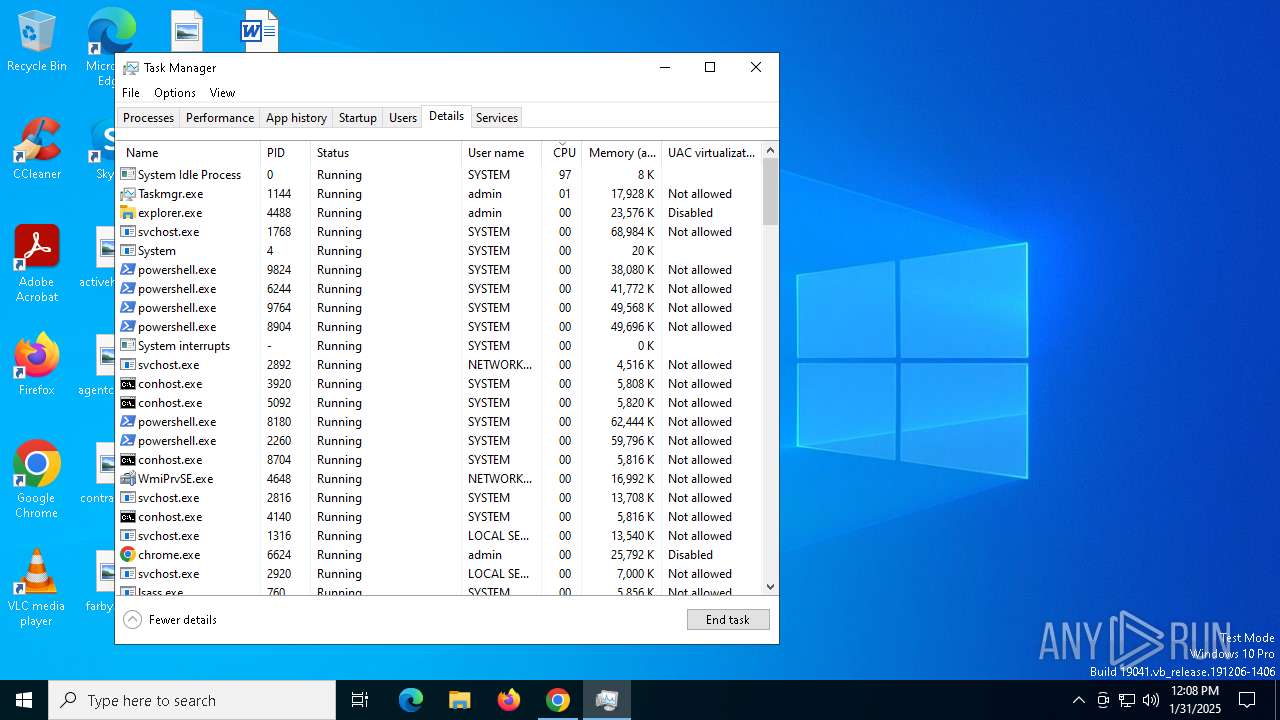
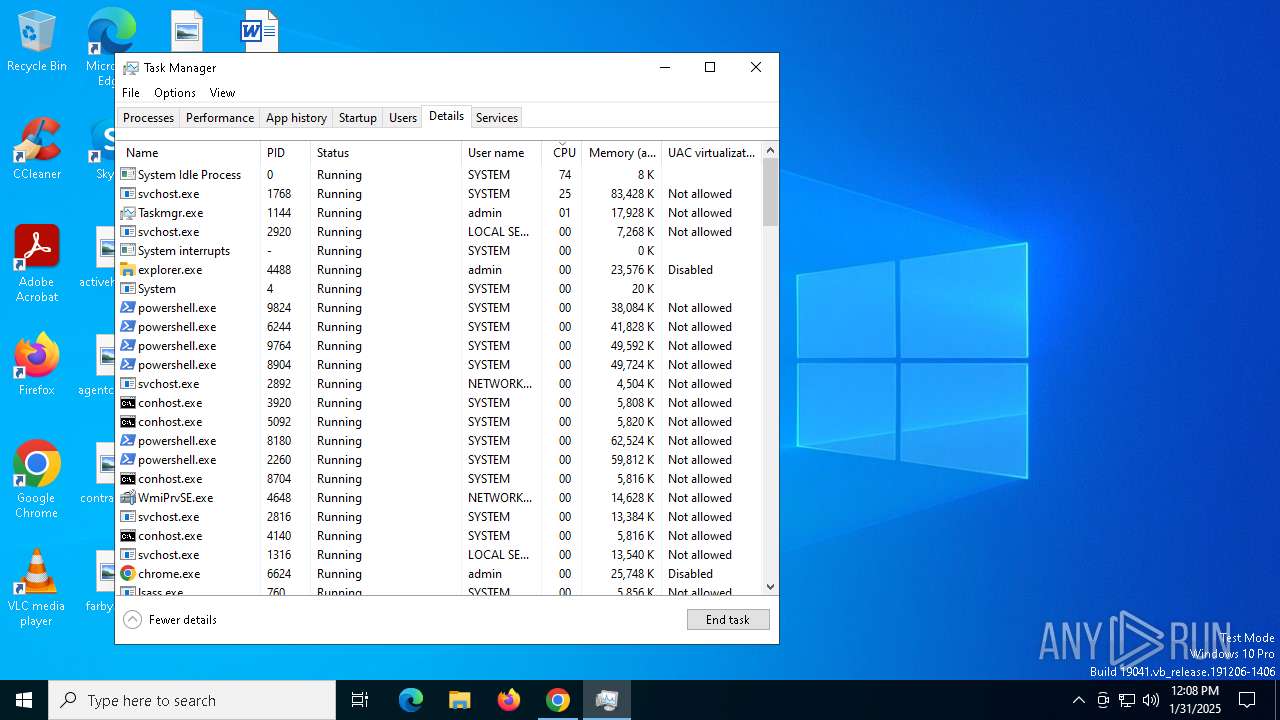
Bypass execution policy to execute commands
- powershell.exe (PID: 2072)
- powershell.exe (PID: 4908)
- powershell.exe (PID: 4012)
- powershell.exe (PID: 1828)
- powershell.exe (PID: 936)
- powershell.exe (PID: 7964)
- powershell.exe (PID: 1448)
- powershell.exe (PID: 2796)
- powershell.exe (PID: 3524)
- powershell.exe (PID: 6268)
- powershell.exe (PID: 2600)
- powershell.exe (PID: 4308)
- powershell.exe (PID: 6436)
- powershell.exe (PID: 7048)
- powershell.exe (PID: 424)
- powershell.exe (PID: 2260)
- powershell.exe (PID: 1172)
- powershell.exe (PID: 7980)
- powershell.exe (PID: 8000)
- powershell.exe (PID: 8020)
- powershell.exe (PID: 8040)
- powershell.exe (PID: 6592)
- powershell.exe (PID: 8100)
- powershell.exe (PID: 8160)
- powershell.exe (PID: 8140)
- powershell.exe (PID: 8180)
- powershell.exe (PID: 8060)
- powershell.exe (PID: 8080)
- powershell.exe (PID: 8120)
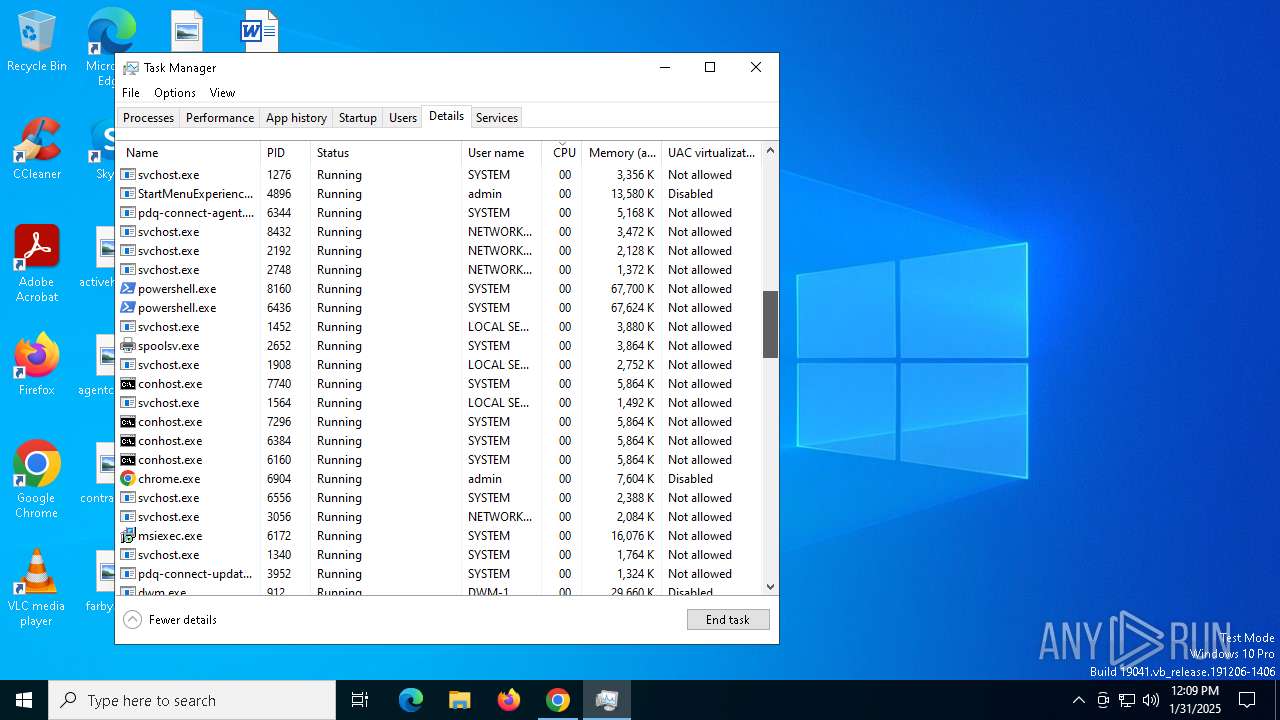
Changes powershell execution policy (Bypass)
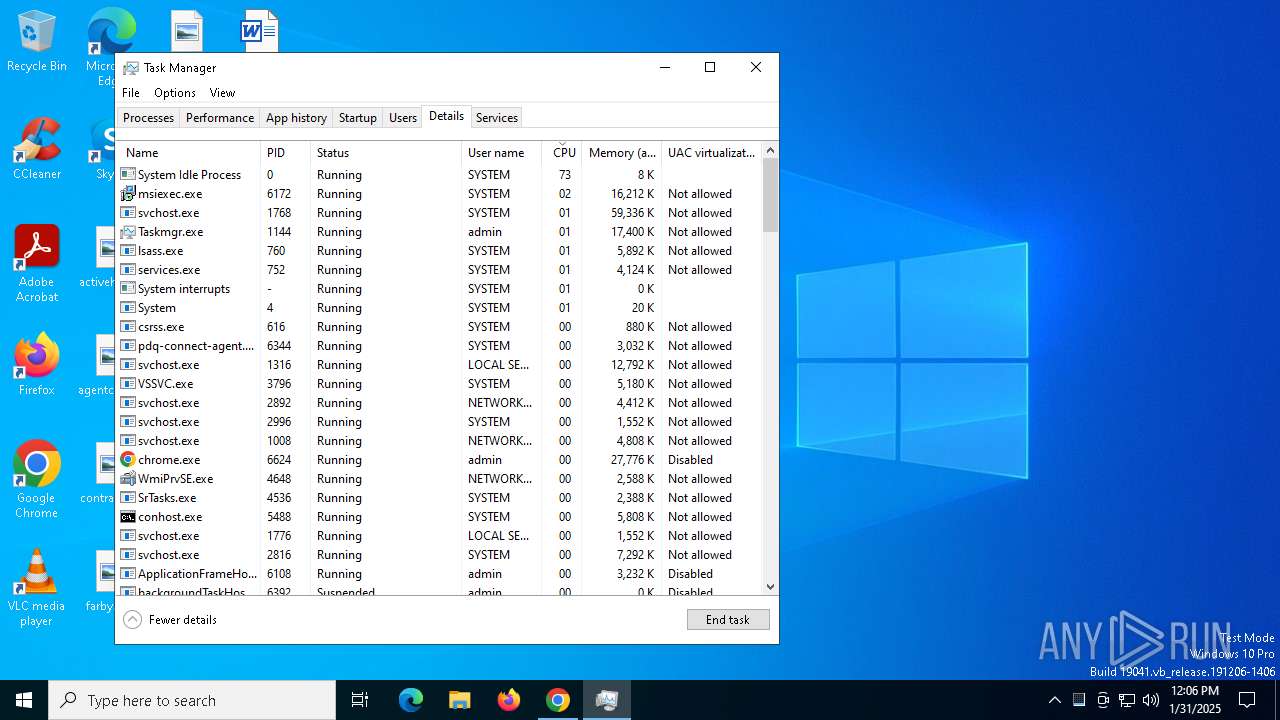
- pdq-connect-agent.exe (PID: 6344)
SUSPICIOUS
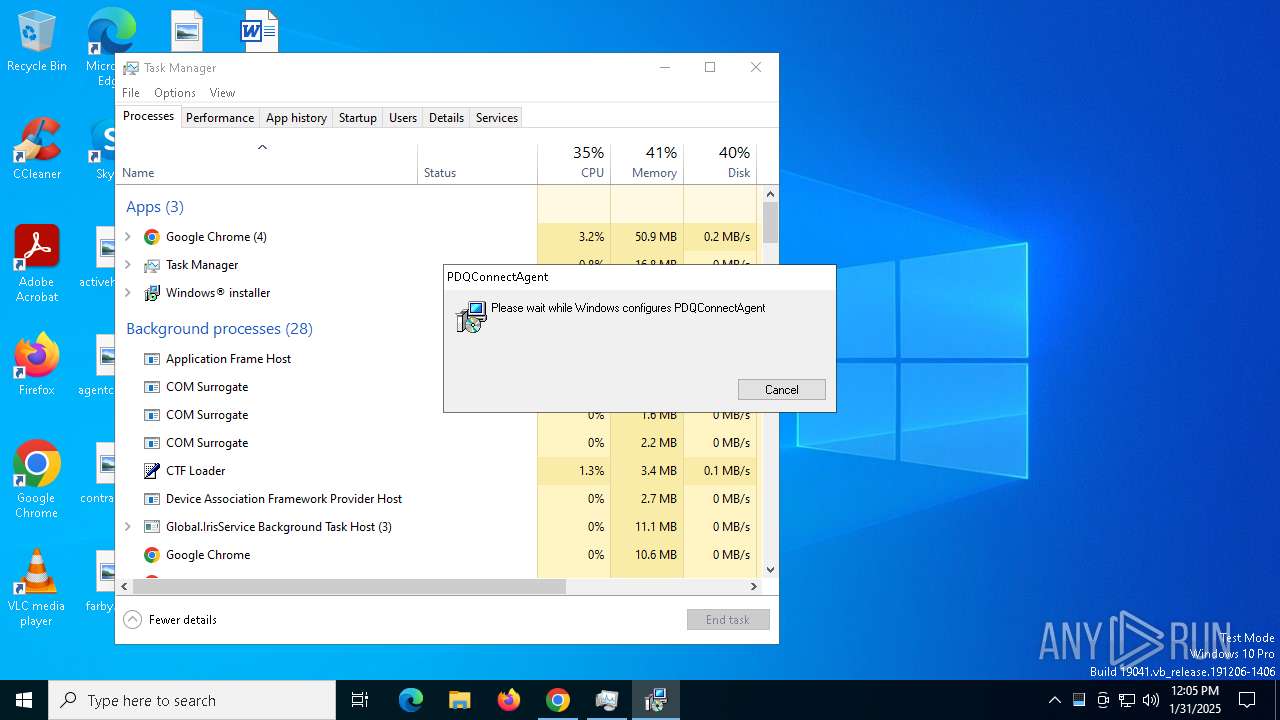
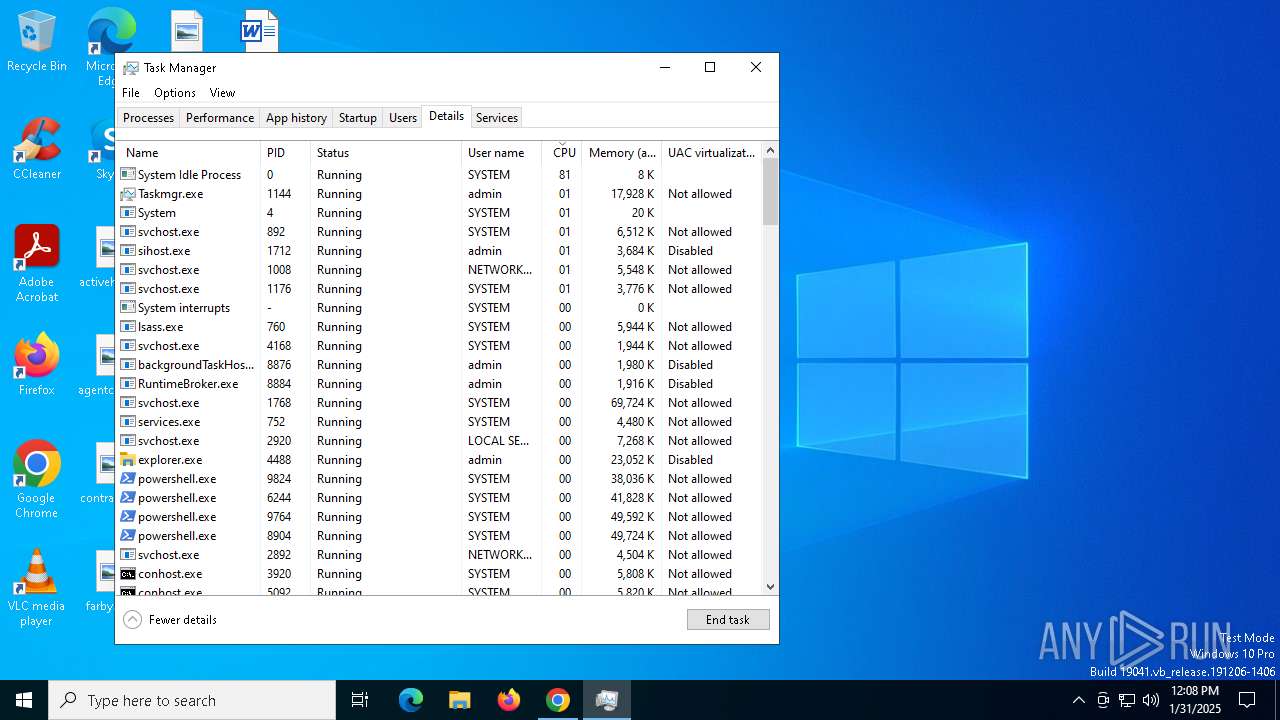
Executes as Windows Service
- VSSVC.exe (PID: 3796)
- pdq-connect-agent.exe (PID: 6344)
- pdq-connect-updater.exe (PID: 3952)
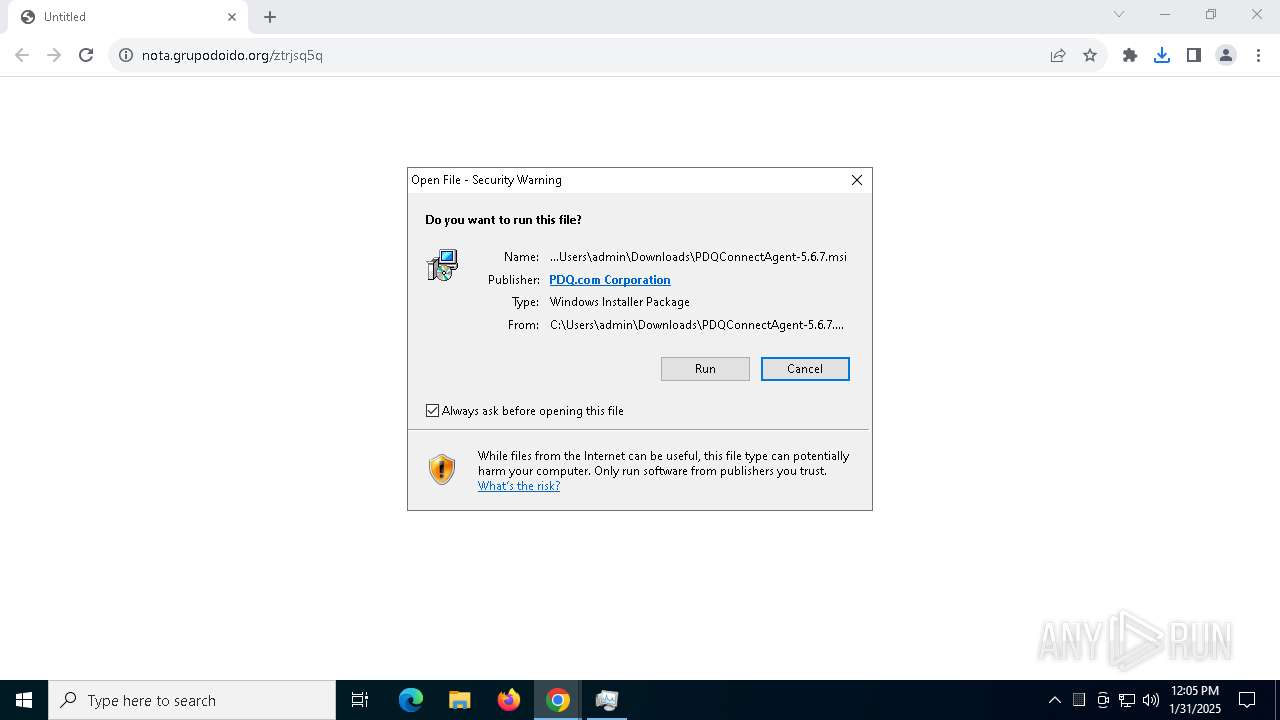
Checks Windows Trust Settings
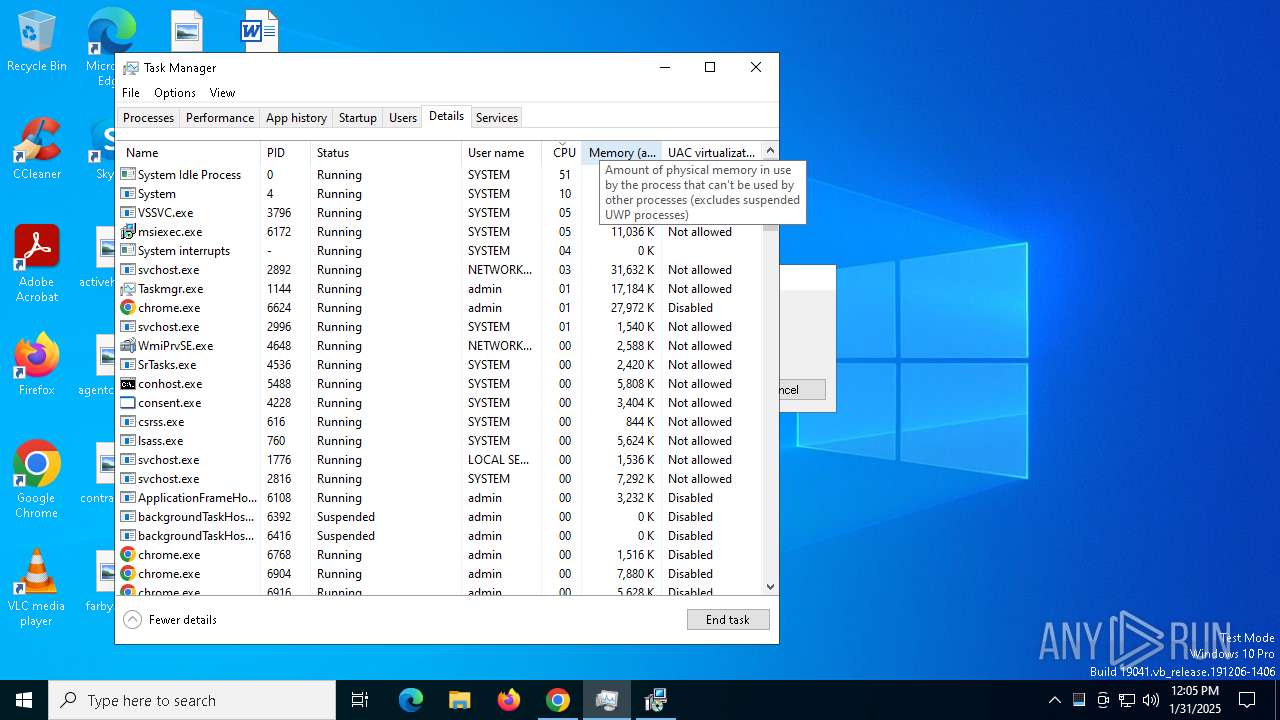
- msiexec.exe (PID: 6172)
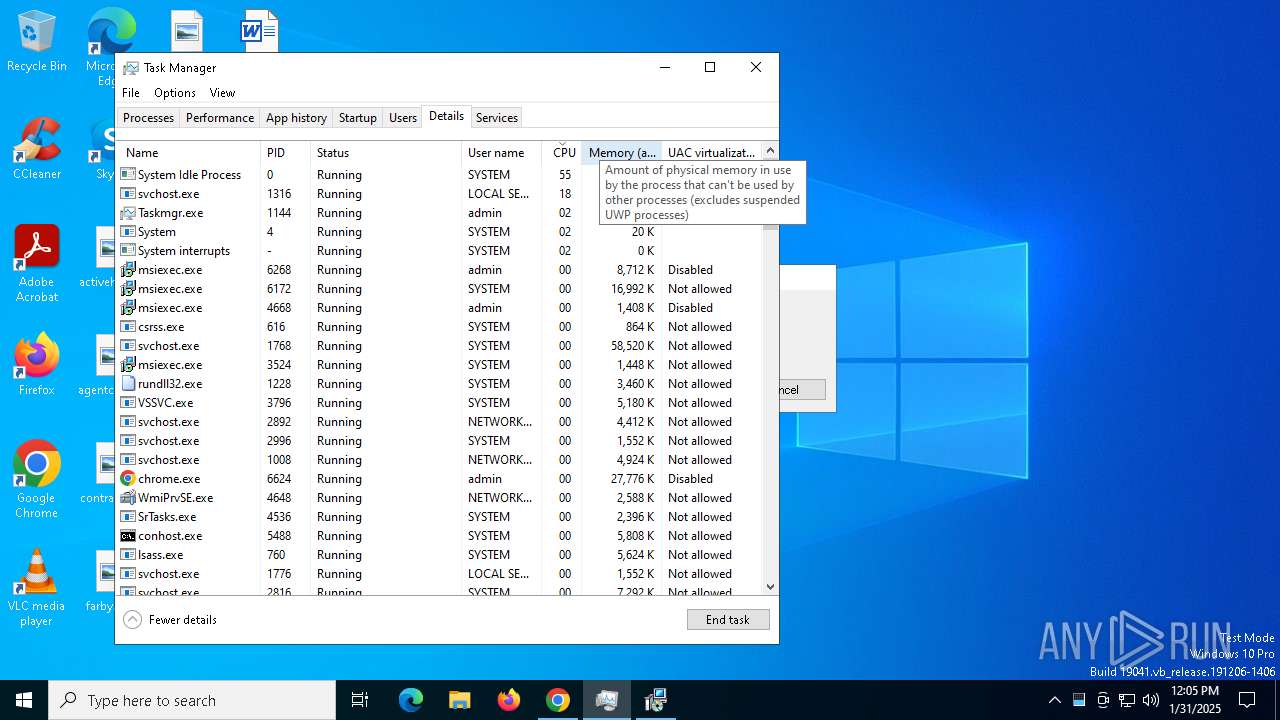
Uses RUNDLL32.EXE to load library
- msiexec.exe (PID: 4668)
- msiexec.exe (PID: 3524)
- msiexec.exe (PID: 6204)
Executable content was dropped or overwritten
- rundll32.exe (PID: 4716)
- rundll32.exe (PID: 4228)
- rundll32.exe (PID: 2804)
- rundll32.exe (PID: 5628)
- rundll32.exe (PID: 1228)
- rundll32.exe (PID: 5920)
- pdq-connect-agent.exe (PID: 6344)
- rundll32.exe (PID: 6284)
- csc.exe (PID: 9788)
- csc.exe (PID: 9960)
- powershell.exe (PID: 7980)
- powershell.exe (PID: 424)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6172)
PDQConnect is probably used for system patching and software deployment
- sc.exe (PID: 5576)
Windows service management via SC.EXE
- sc.exe (PID: 5576)
Starts SC.EXE for service management
- rundll32.exe (PID: 4228)
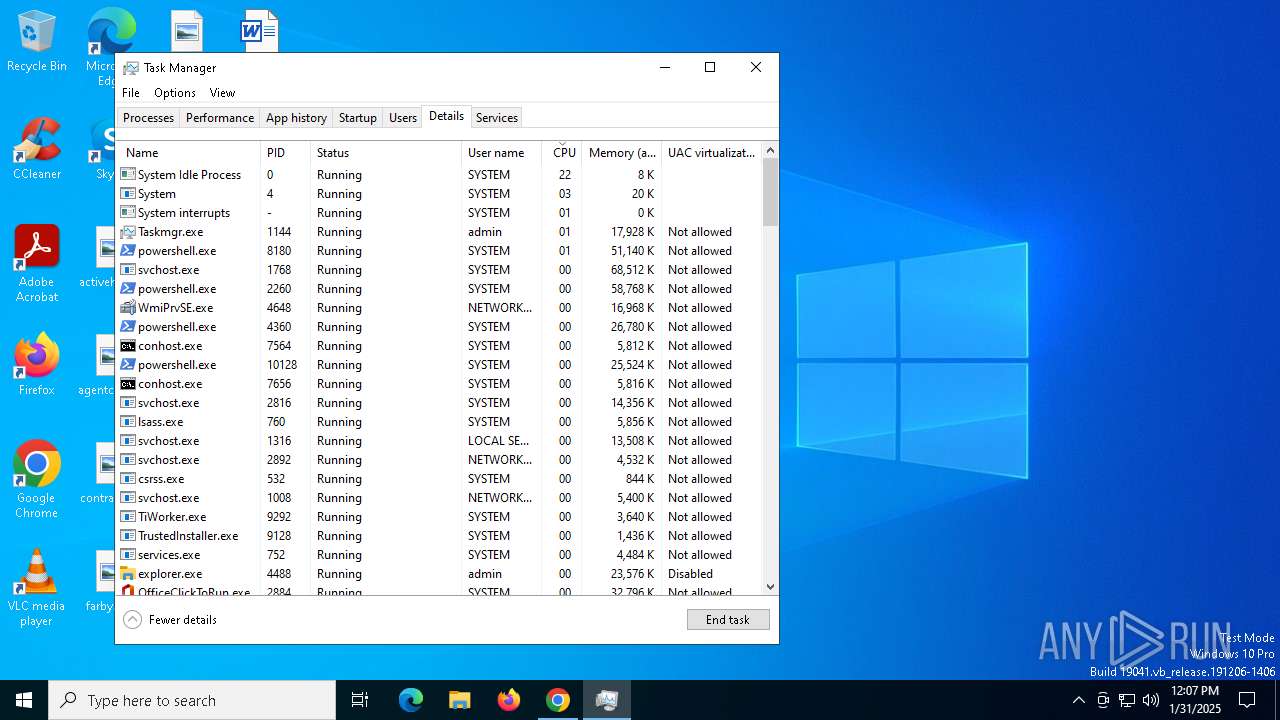
The process hides Powershell's copyright startup banner
- pdq-connect-agent.exe (PID: 6344)
- powershell.exe (PID: 2260)
- powershell.exe (PID: 10180)
- powershell.exe (PID: 10136)
- powershell.exe (PID: 8180)
- powershell.exe (PID: 8944)
- powershell.exe (PID: 9064)
- powershell.exe (PID: 9944)
- powershell.exe (PID: 9076)
- powershell.exe (PID: 9400)
- powershell.exe (PID: 8304)
- powershell.exe (PID: 8908)
- powershell.exe (PID: 1512)
- powershell.exe (PID: 9656)
- powershell.exe (PID: 8688)
- powershell.exe (PID: 9848)
- powershell.exe (PID: 8880)
- powershell.exe (PID: 8844)
- powershell.exe (PID: 6204)
- powershell.exe (PID: 4360)
- powershell.exe (PID: 10128)
- powershell.exe (PID: 8904)
- powershell.exe (PID: 9764)
- powershell.exe (PID: 9044)
- powershell.exe (PID: 9632)
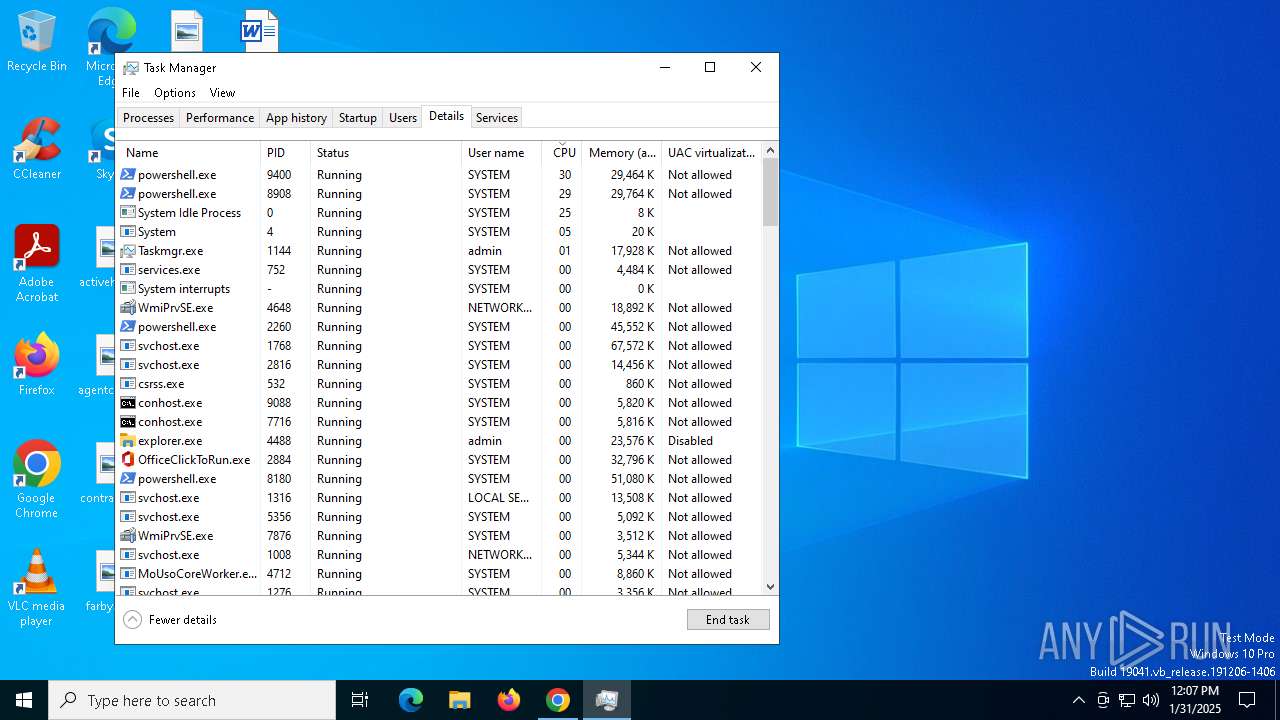
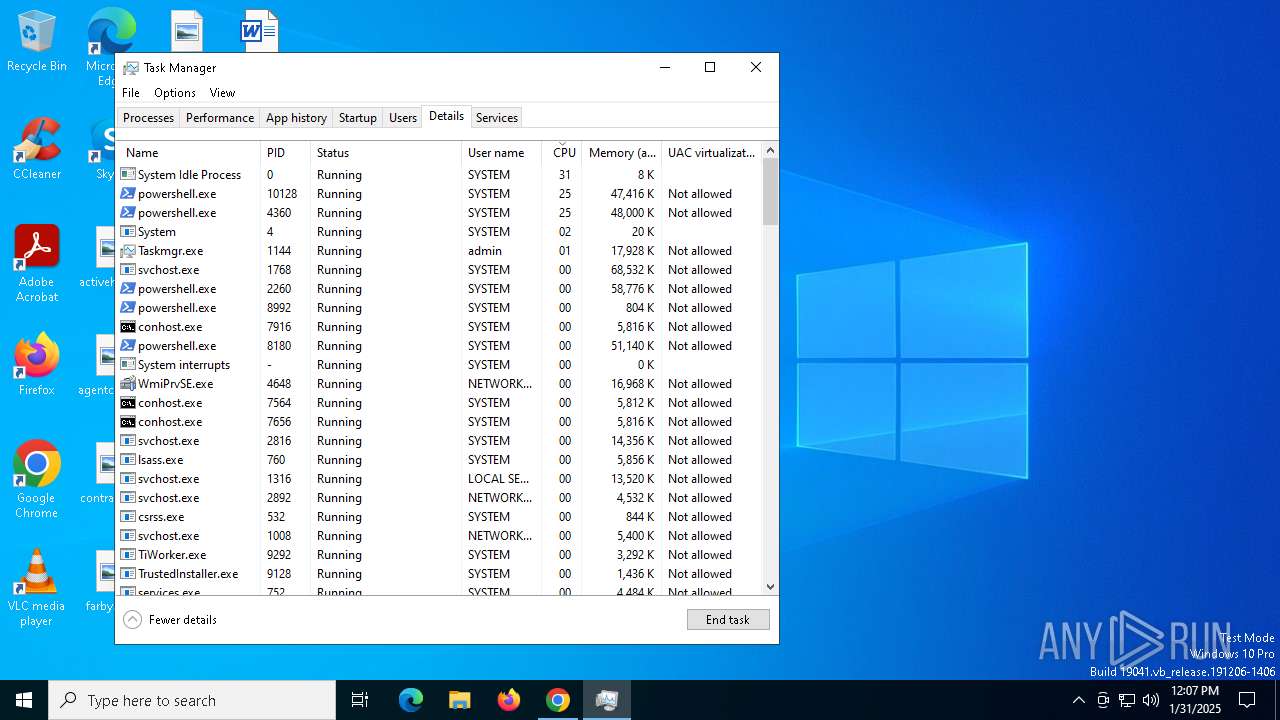
Starts POWERSHELL.EXE for commands execution
- pdq-connect-agent.exe (PID: 6344)
- powershell.exe (PID: 10136)
- powershell.exe (PID: 10180)
- powershell.exe (PID: 2260)
- powershell.exe (PID: 8180)
- powershell.exe (PID: 8944)
- powershell.exe (PID: 9944)
- powershell.exe (PID: 9076)
- powershell.exe (PID: 9064)
- powershell.exe (PID: 8908)
- powershell.exe (PID: 8304)
- powershell.exe (PID: 9400)
- powershell.exe (PID: 8880)
- powershell.exe (PID: 1512)
- powershell.exe (PID: 9656)
- powershell.exe (PID: 8688)
- powershell.exe (PID: 9848)
- powershell.exe (PID: 4360)
- powershell.exe (PID: 10128)
- powershell.exe (PID: 6204)
- powershell.exe (PID: 8844)
- powershell.exe (PID: 9632)
- powershell.exe (PID: 8904)
- powershell.exe (PID: 9764)
- powershell.exe (PID: 9044)
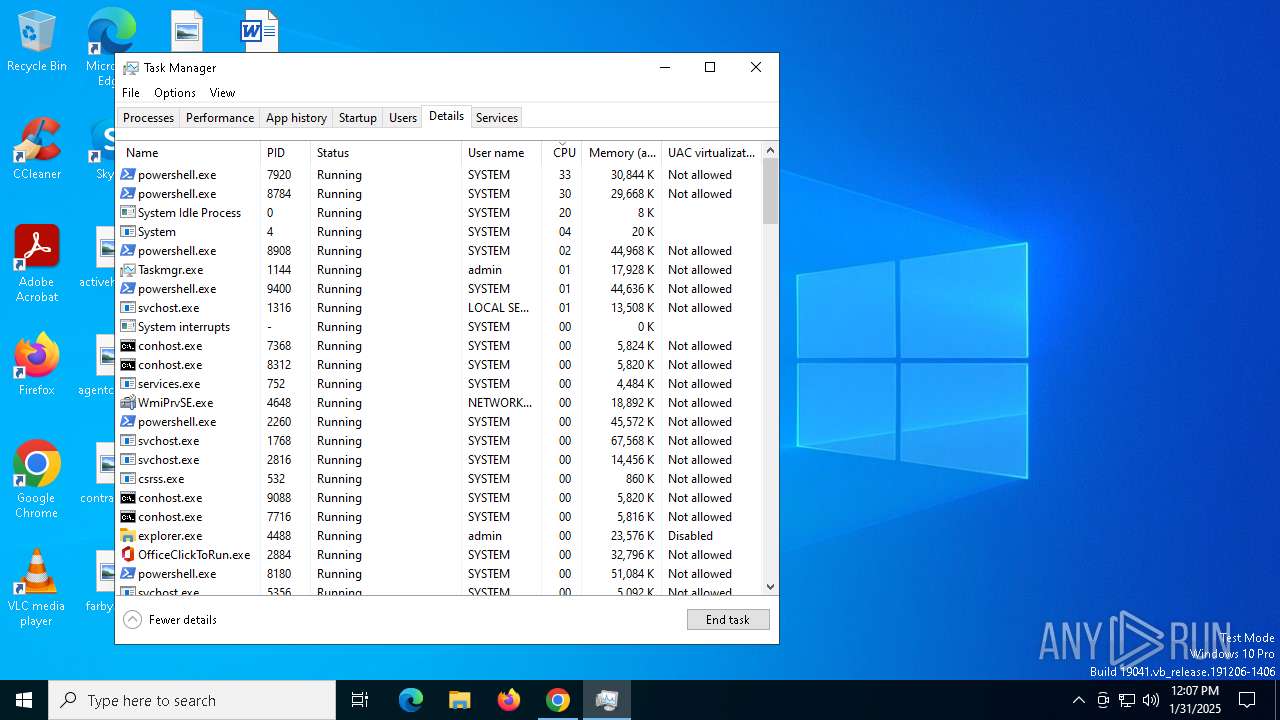
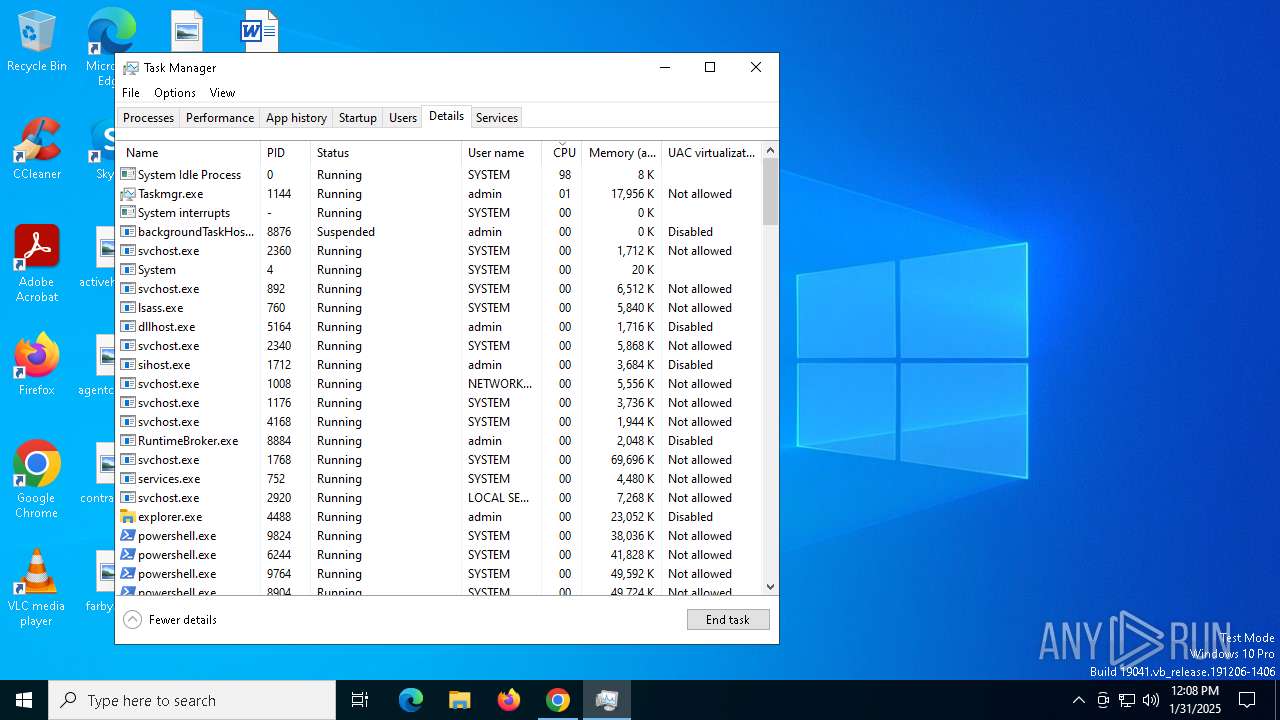
The process hide an interactive prompt from the user
- pdq-connect-agent.exe (PID: 6344)
The process bypasses the loading of PowerShell profile settings
- pdq-connect-agent.exe (PID: 6344)
- powershell.exe (PID: 2260)
- powershell.exe (PID: 10180)
- powershell.exe (PID: 8180)
- powershell.exe (PID: 10136)
- powershell.exe (PID: 8944)
- powershell.exe (PID: 9064)
- powershell.exe (PID: 9944)
- powershell.exe (PID: 9076)
- powershell.exe (PID: 8304)
- powershell.exe (PID: 8908)
- powershell.exe (PID: 8880)
- powershell.exe (PID: 1512)
- powershell.exe (PID: 9400)
- powershell.exe (PID: 9848)
- powershell.exe (PID: 8688)
- powershell.exe (PID: 9656)
- powershell.exe (PID: 10128)
- powershell.exe (PID: 8844)
- powershell.exe (PID: 6204)
- powershell.exe (PID: 9044)
- powershell.exe (PID: 4360)
- powershell.exe (PID: 9632)
- powershell.exe (PID: 8904)
- powershell.exe (PID: 9764)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 2072)
- powershell.exe (PID: 7980)
- powershell.exe (PID: 424)
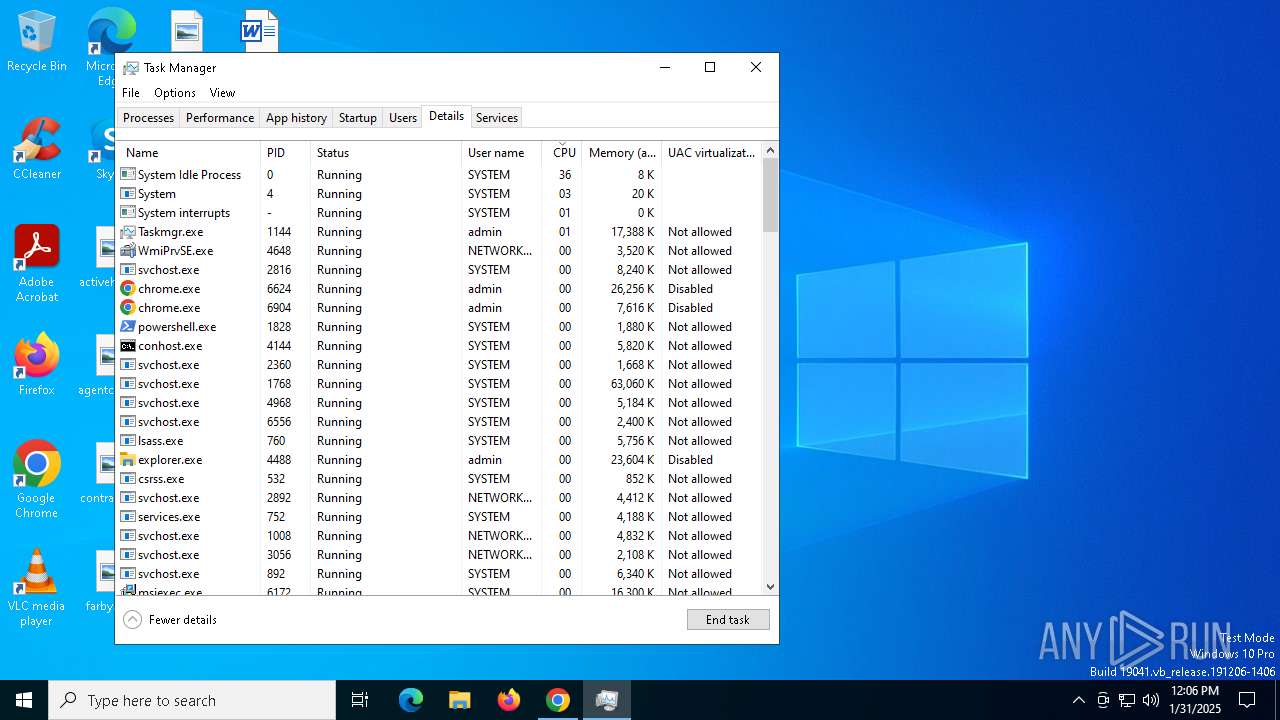
CSC.EXE is used to compile C# code
- csc.exe (PID: 9788)
- csc.exe (PID: 9960)
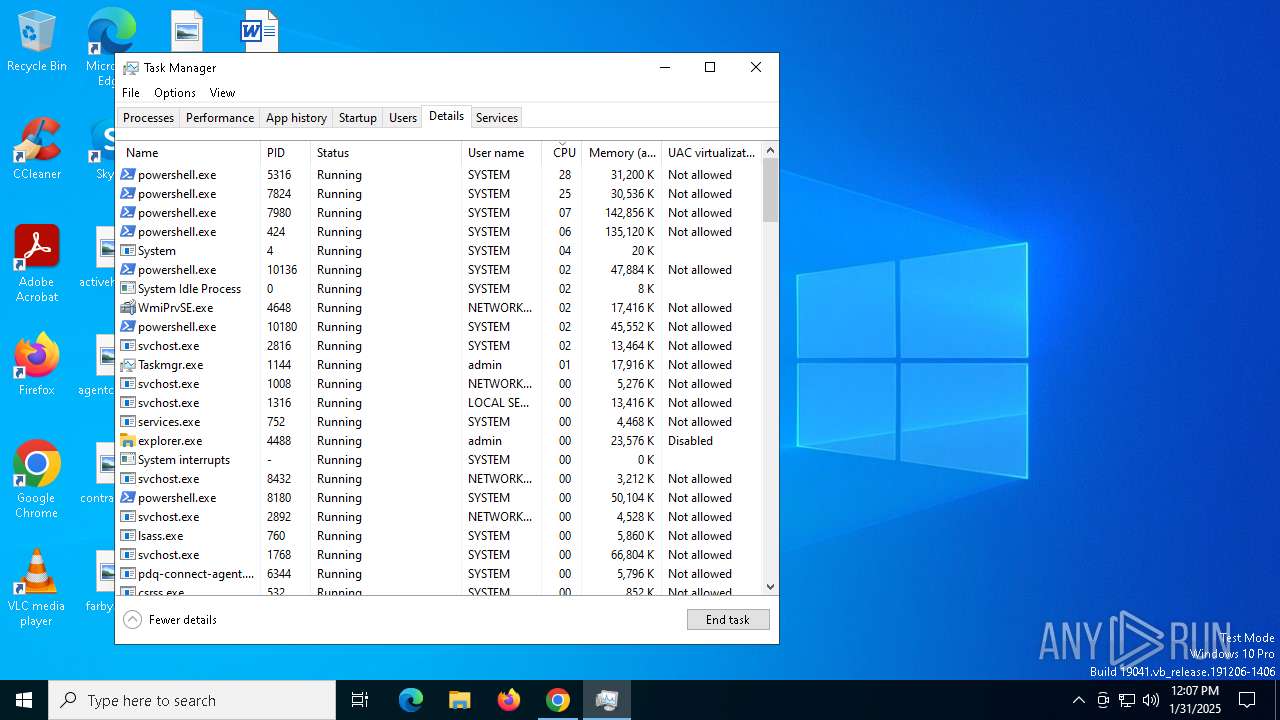
Application launched itself
- powershell.exe (PID: 2260)
- powershell.exe (PID: 8180)
- powershell.exe (PID: 10180)
- powershell.exe (PID: 10136)
- powershell.exe (PID: 8944)
- powershell.exe (PID: 9064)
- powershell.exe (PID: 9944)
- powershell.exe (PID: 1512)
- powershell.exe (PID: 9076)
- powershell.exe (PID: 8304)
- powershell.exe (PID: 8908)
- powershell.exe (PID: 9400)
- powershell.exe (PID: 8880)
- powershell.exe (PID: 8688)
- powershell.exe (PID: 9848)
- powershell.exe (PID: 4360)
- powershell.exe (PID: 9656)
- powershell.exe (PID: 10128)
- powershell.exe (PID: 8844)
- powershell.exe (PID: 9044)
- powershell.exe (PID: 6204)
- powershell.exe (PID: 9632)
- powershell.exe (PID: 8904)
- powershell.exe (PID: 9764)
The process creates files with name similar to system file names
- powershell.exe (PID: 7980)
- powershell.exe (PID: 424)
Detected use of alternative data streams (AltDS)
- powershell.exe (PID: 424)
Process drops legitimate windows executable
- powershell.exe (PID: 424)
- powershell.exe (PID: 7980)
Starts a Microsoft application from unusual location
- DismHost.exe (PID: 7424)
- DismHost.exe (PID: 9652)
INFO
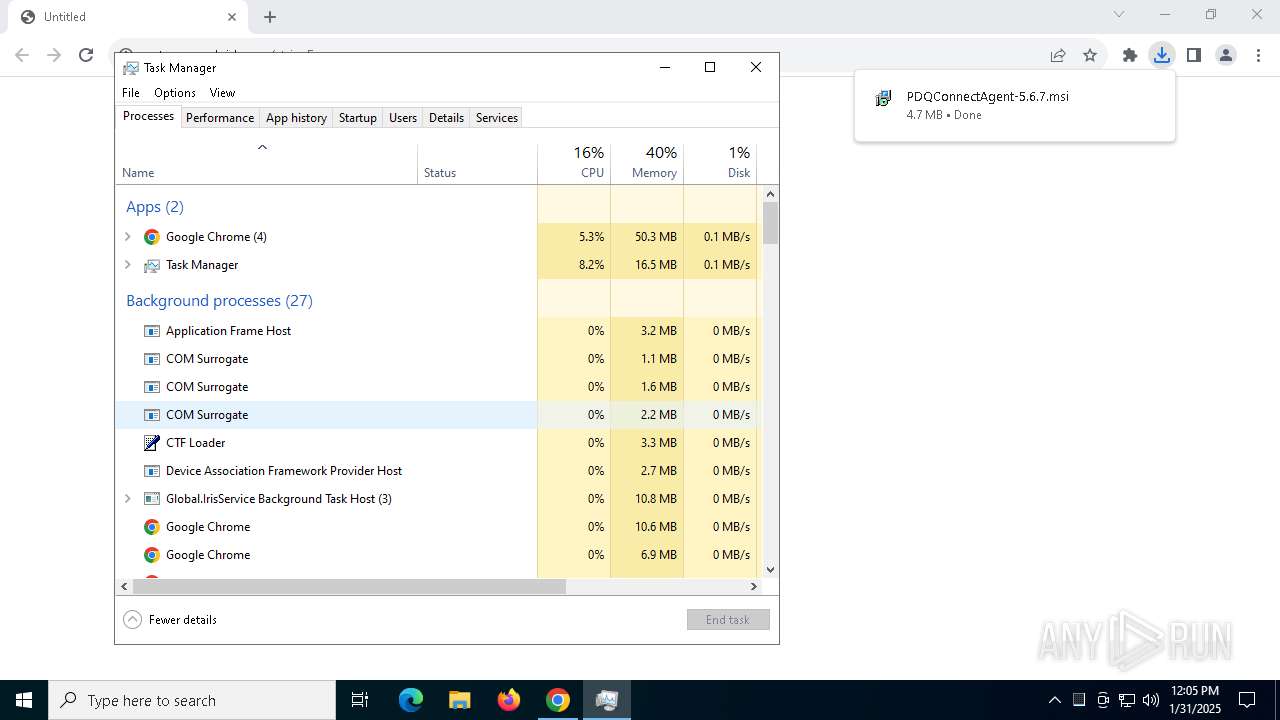
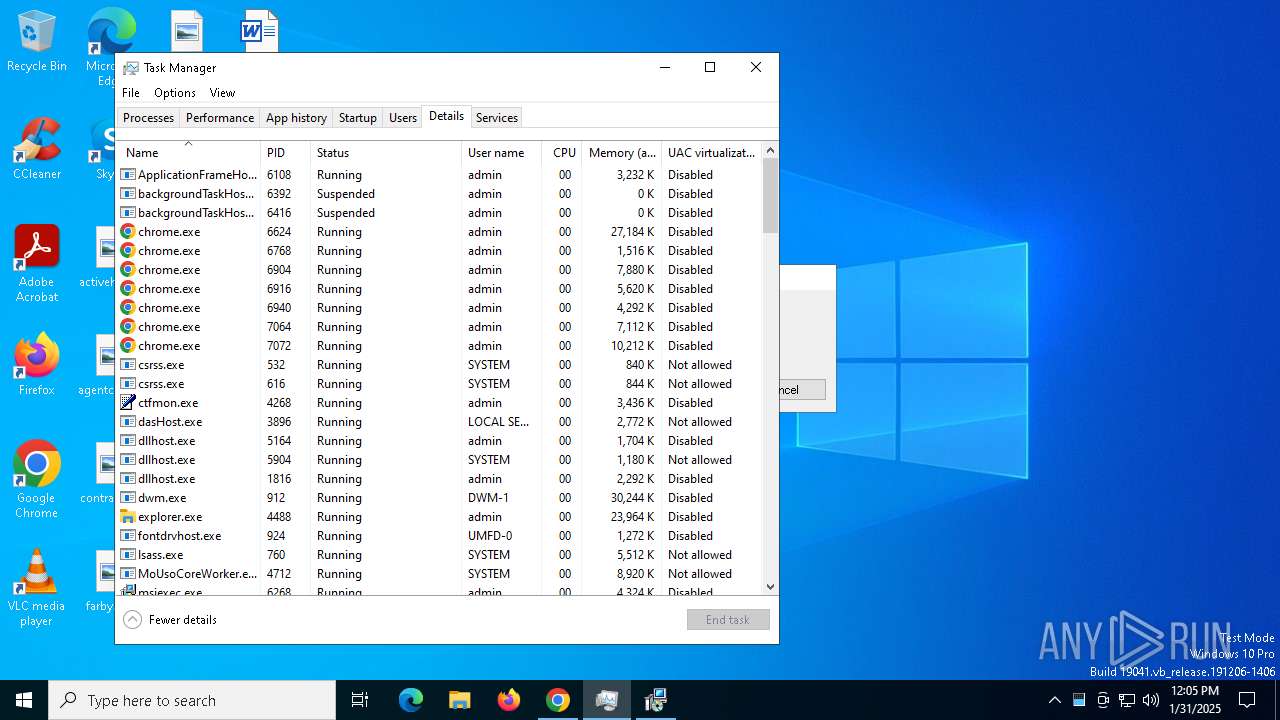
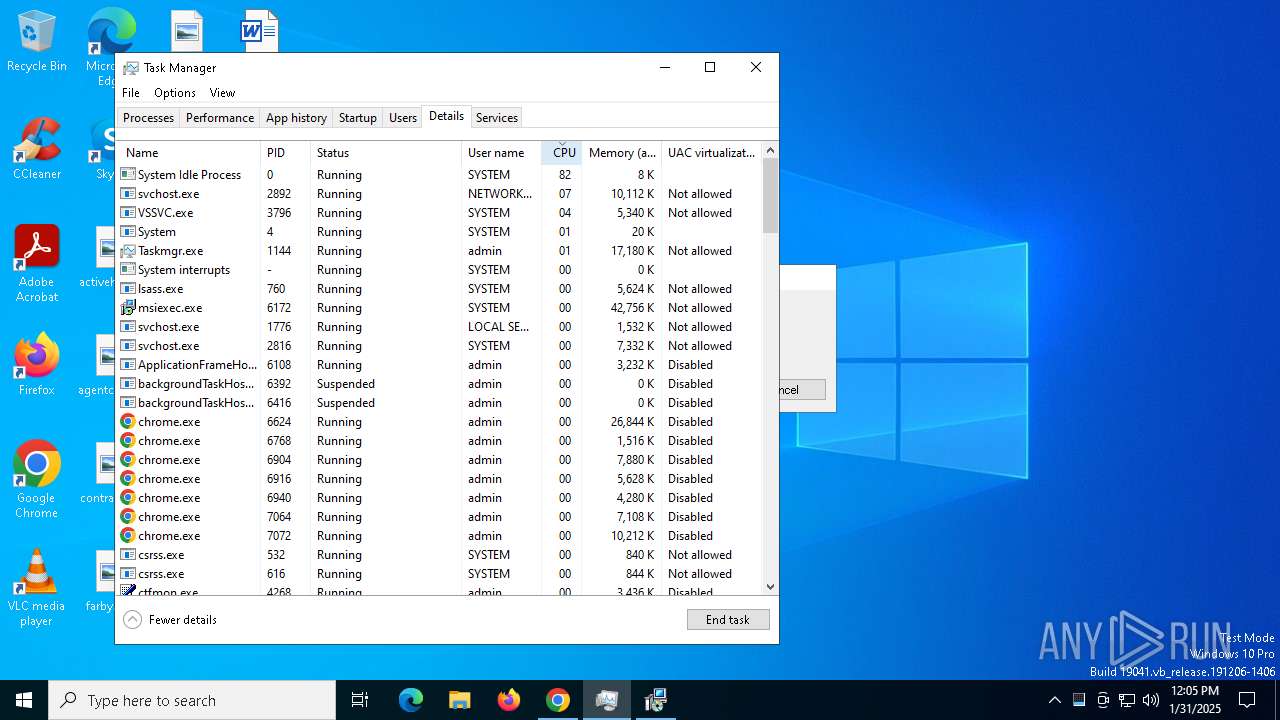
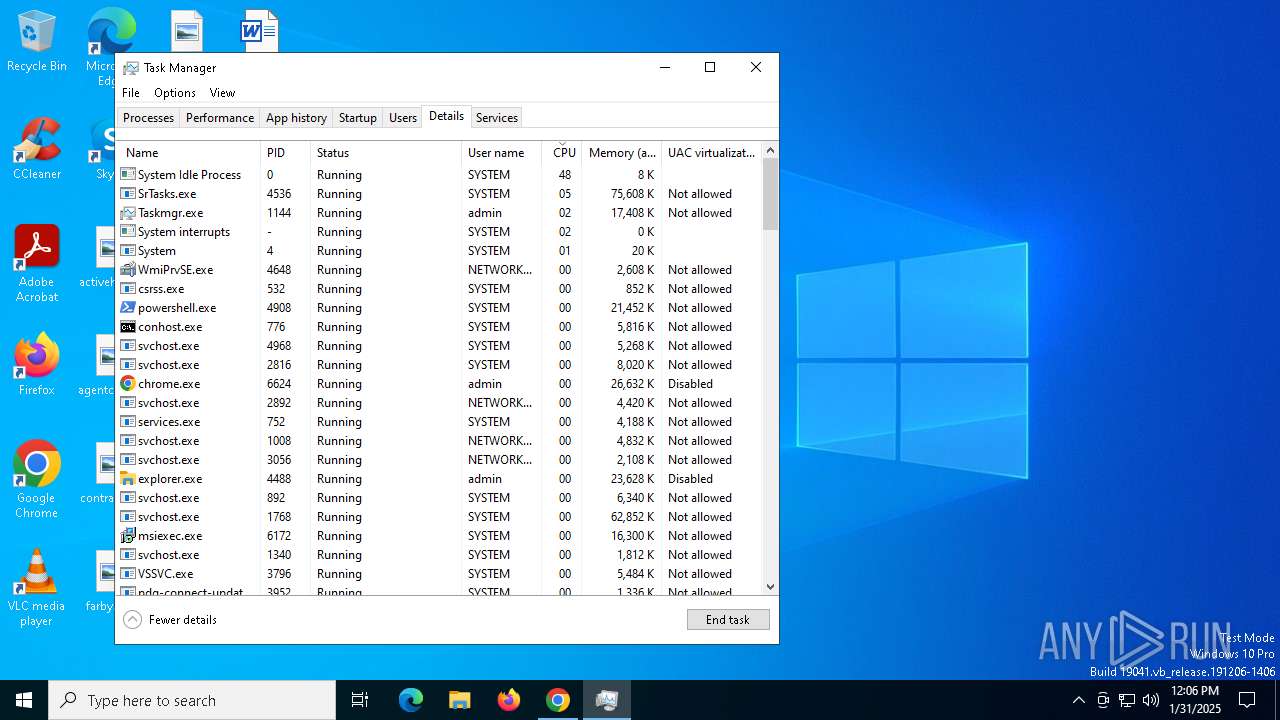
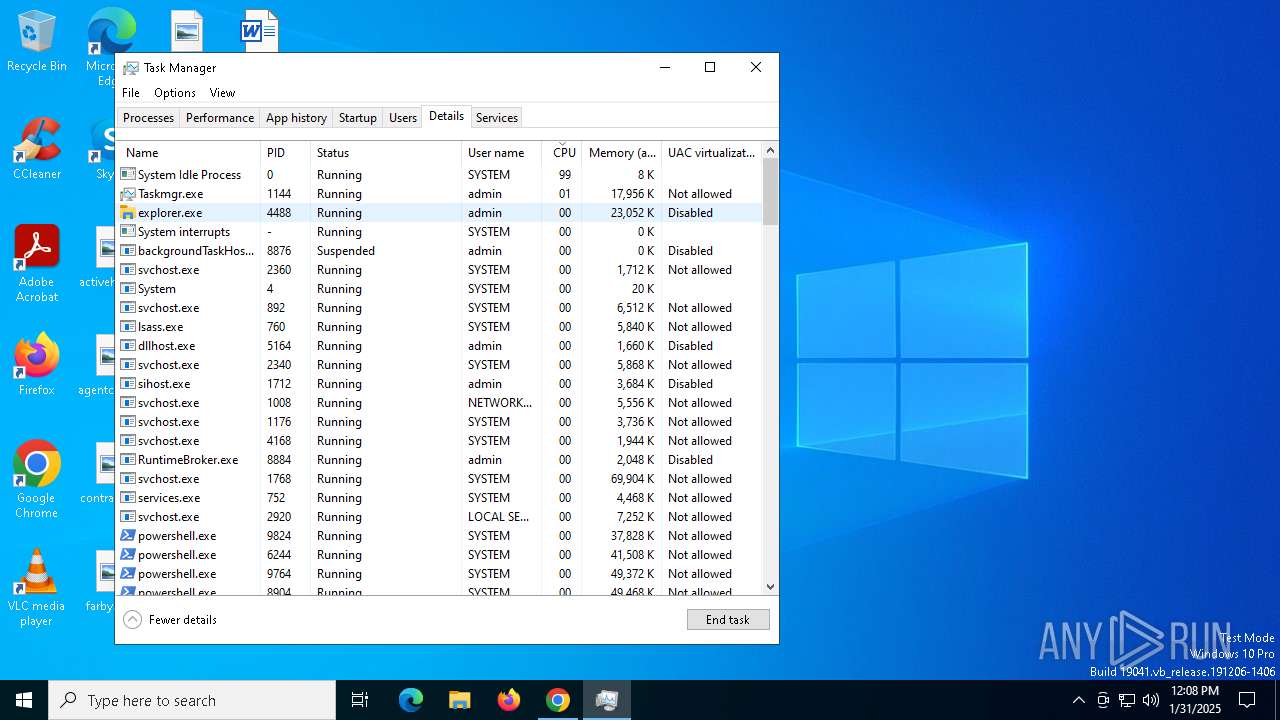
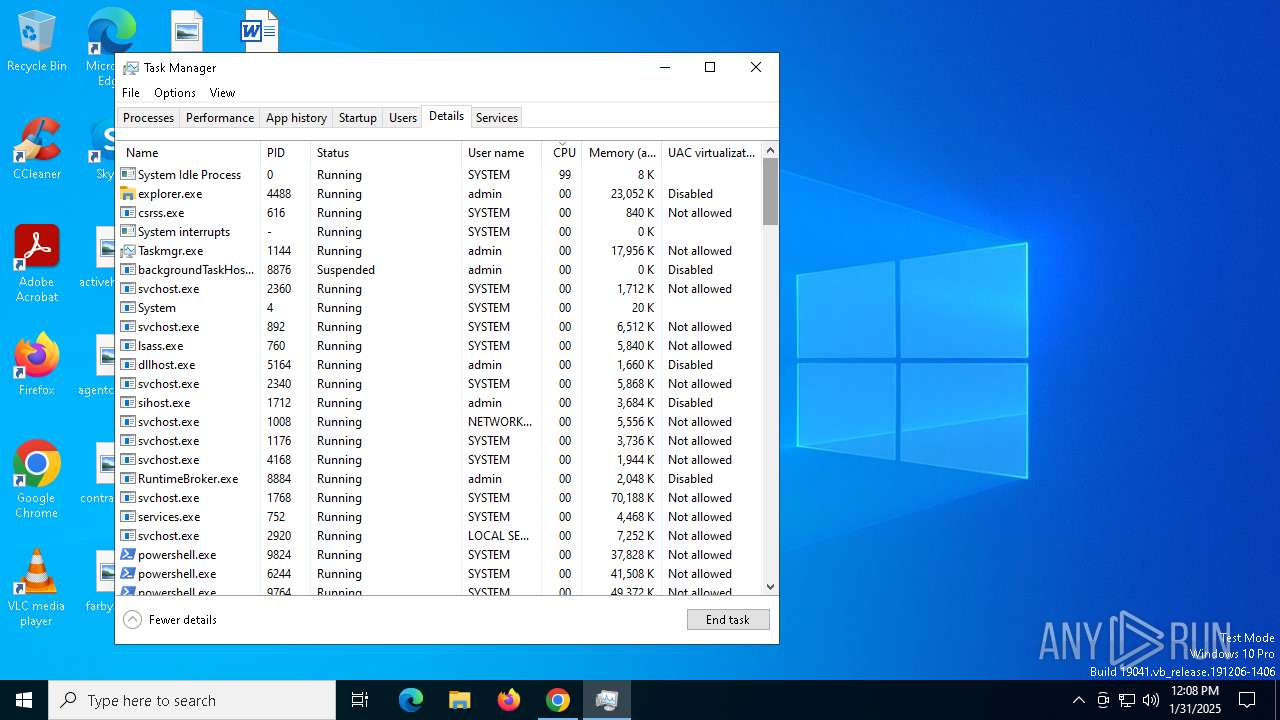
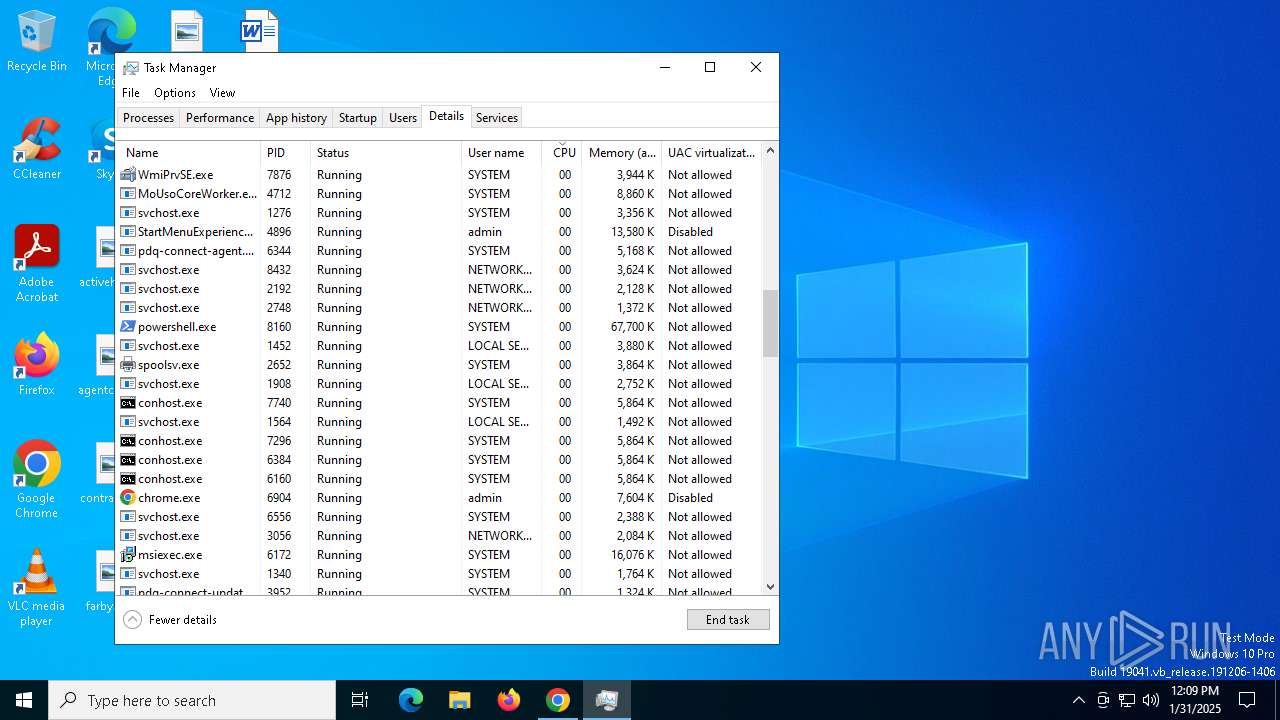
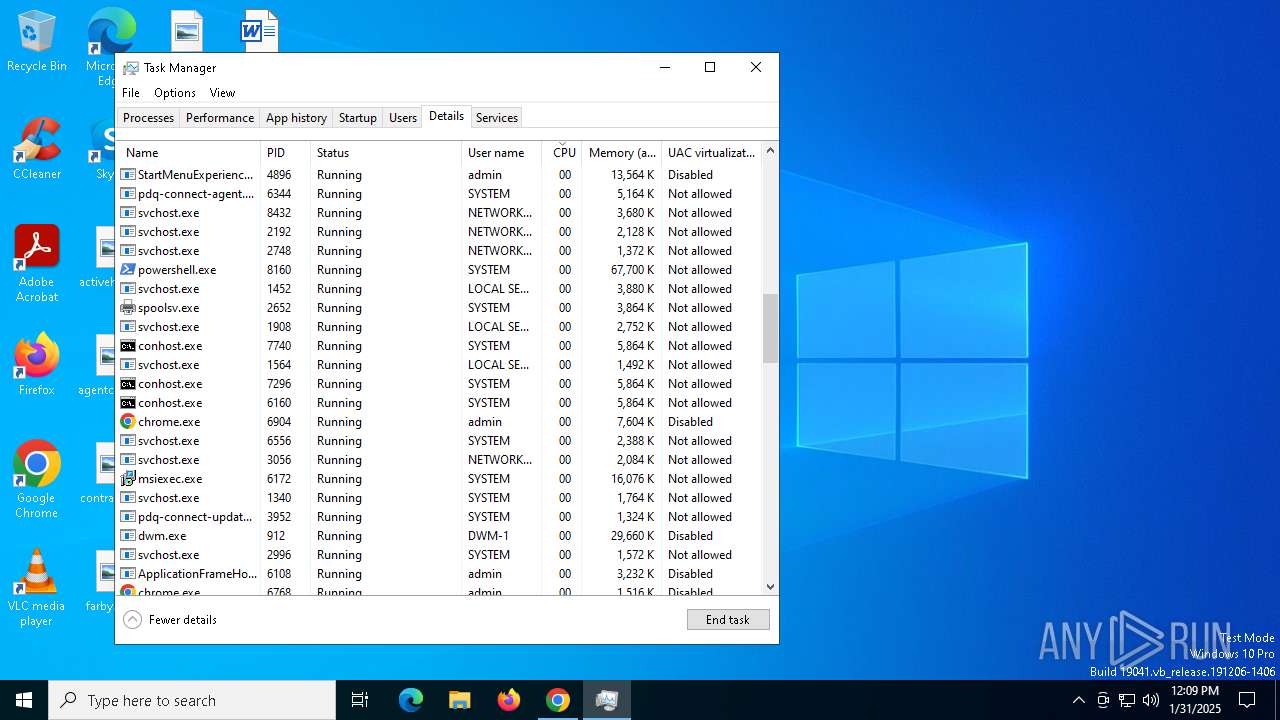
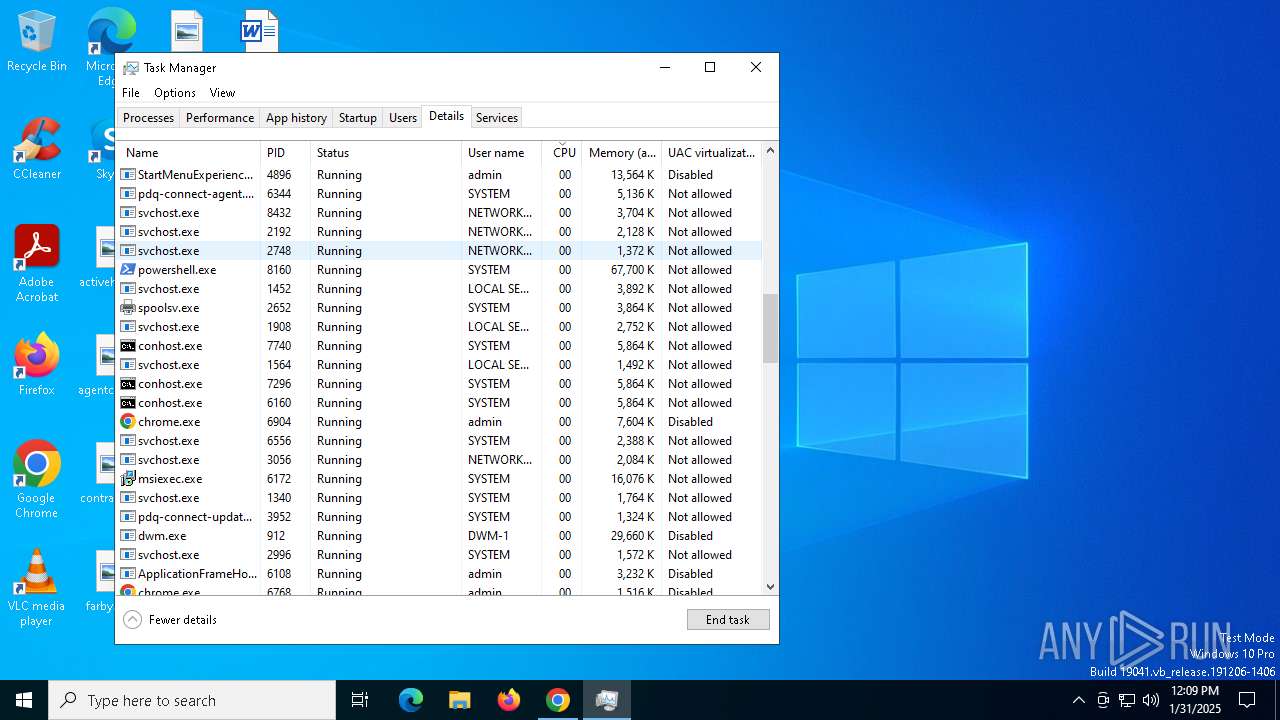
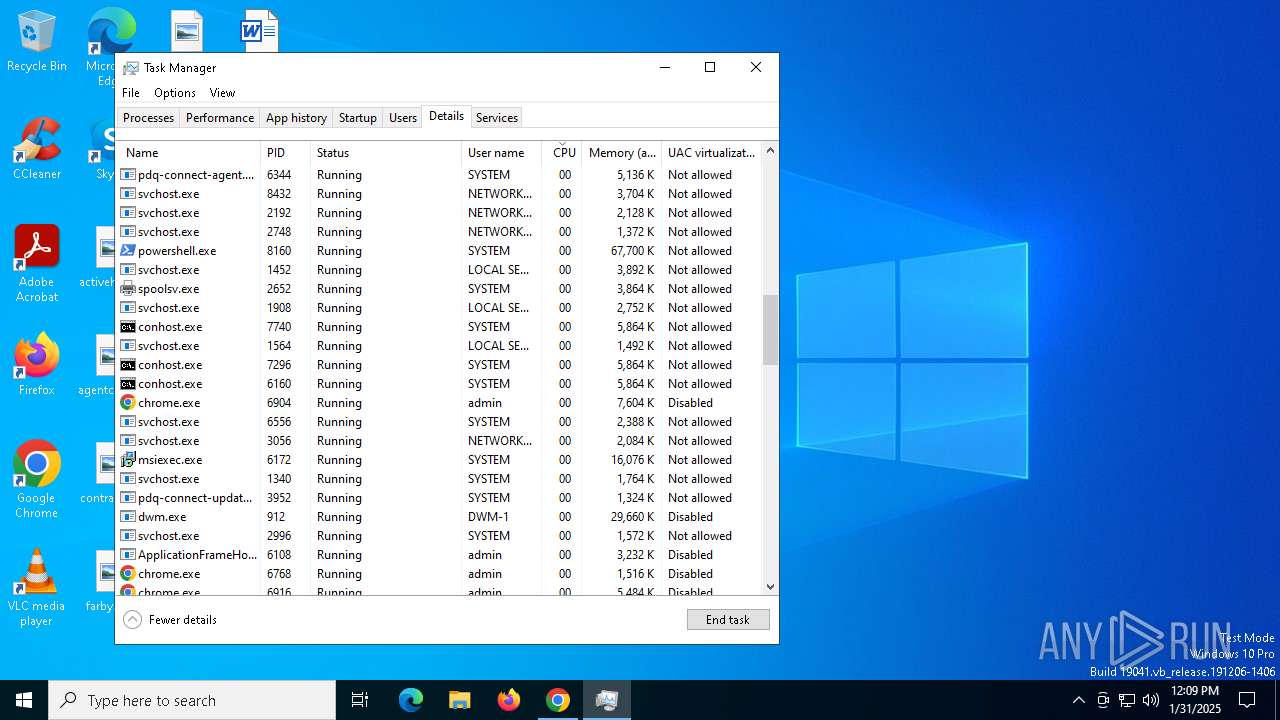
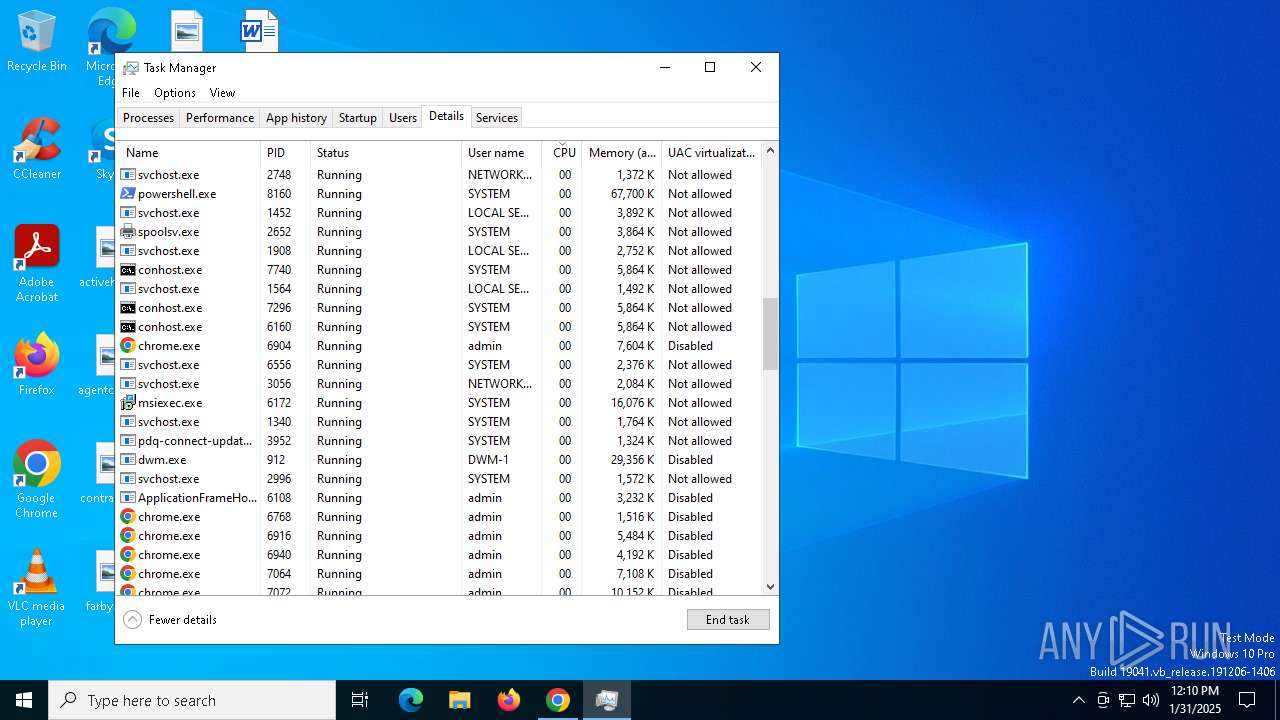
Manual execution by a user
- Taskmgr.exe (PID: 6528)
- Taskmgr.exe (PID: 1144)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 6268)
- Taskmgr.exe (PID: 1144)
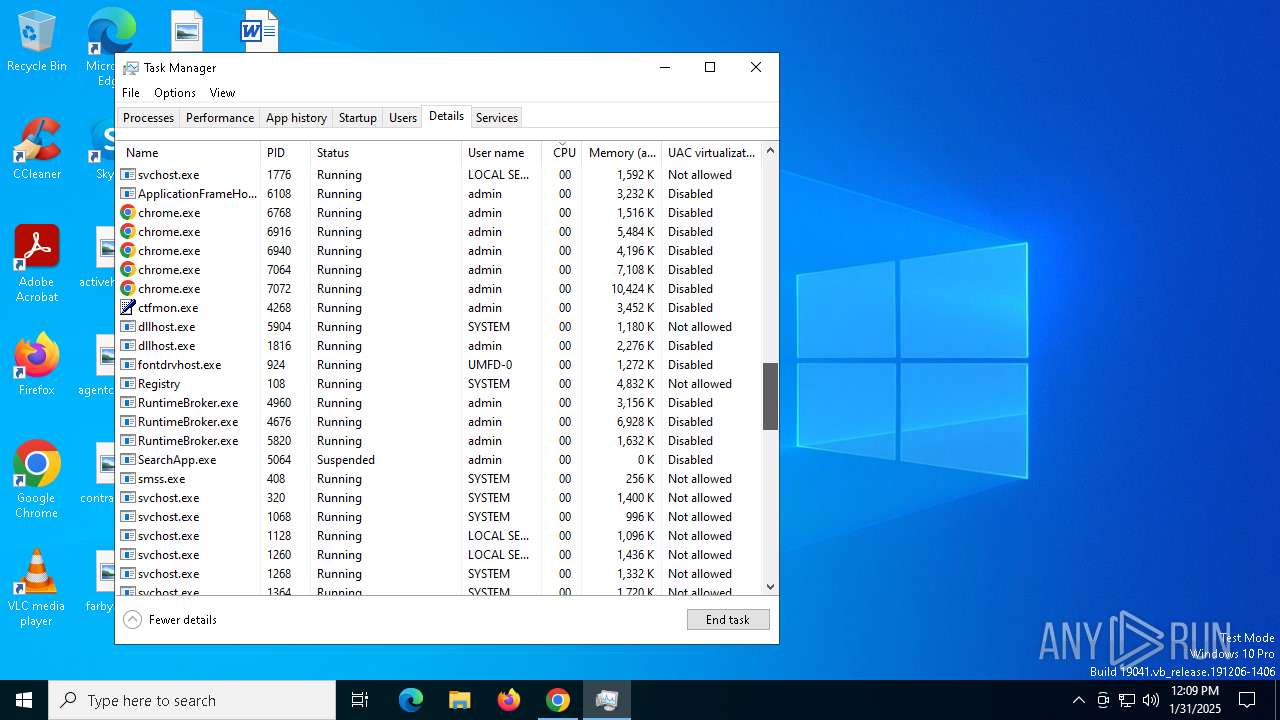
Application launched itself
- chrome.exe (PID: 6624)
- msiexec.exe (PID: 6172)
Reads Microsoft Office registry keys
- chrome.exe (PID: 6624)
Reads the computer name
- msiexec.exe (PID: 6172)
- msiexec.exe (PID: 3524)
- msiexec.exe (PID: 4668)
- pdq-connect-agent.exe (PID: 6344)
- msiexec.exe (PID: 6204)
- pdq-connect-updater.exe (PID: 3952)
- DismHost.exe (PID: 9652)
Checks supported languages
- msiexec.exe (PID: 6172)
- msiexec.exe (PID: 3524)
- msiexec.exe (PID: 4668)
- pdq-connect-agent.exe (PID: 6344)
- msiexec.exe (PID: 6204)
- pdq-connect-updater.exe (PID: 3952)
- csc.exe (PID: 9788)
- csc.exe (PID: 9960)
- DismHost.exe (PID: 9652)
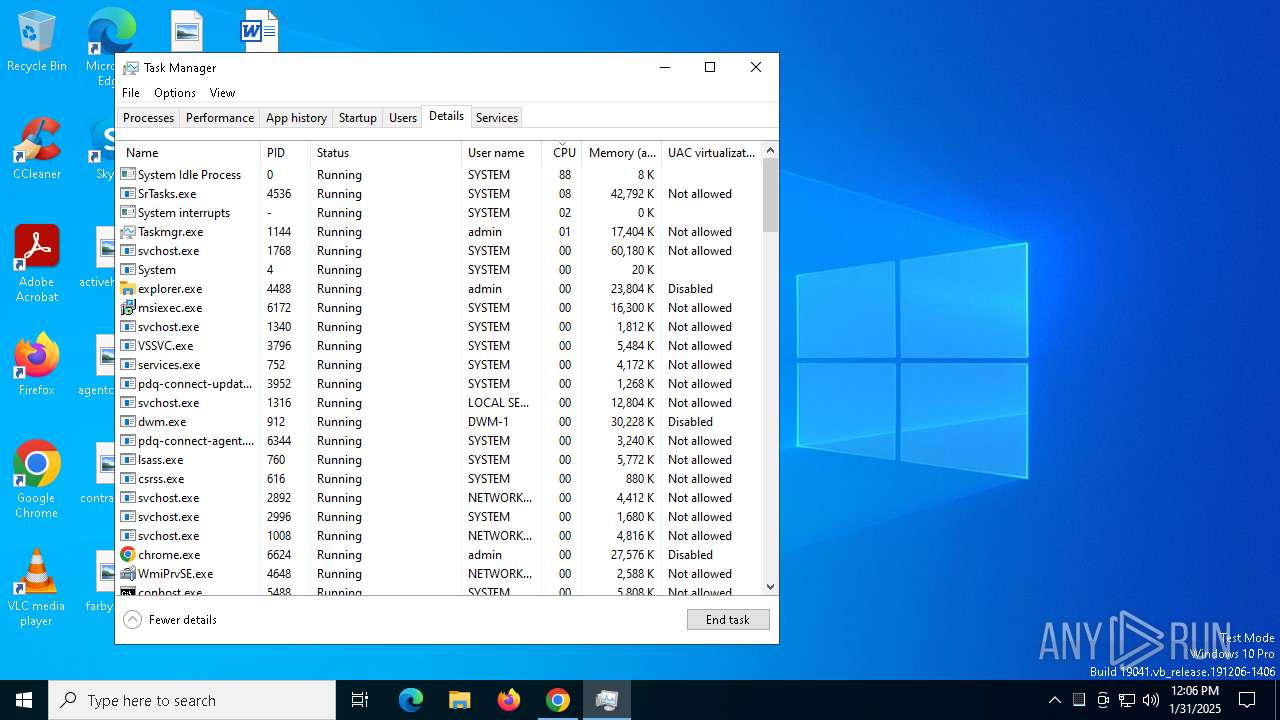
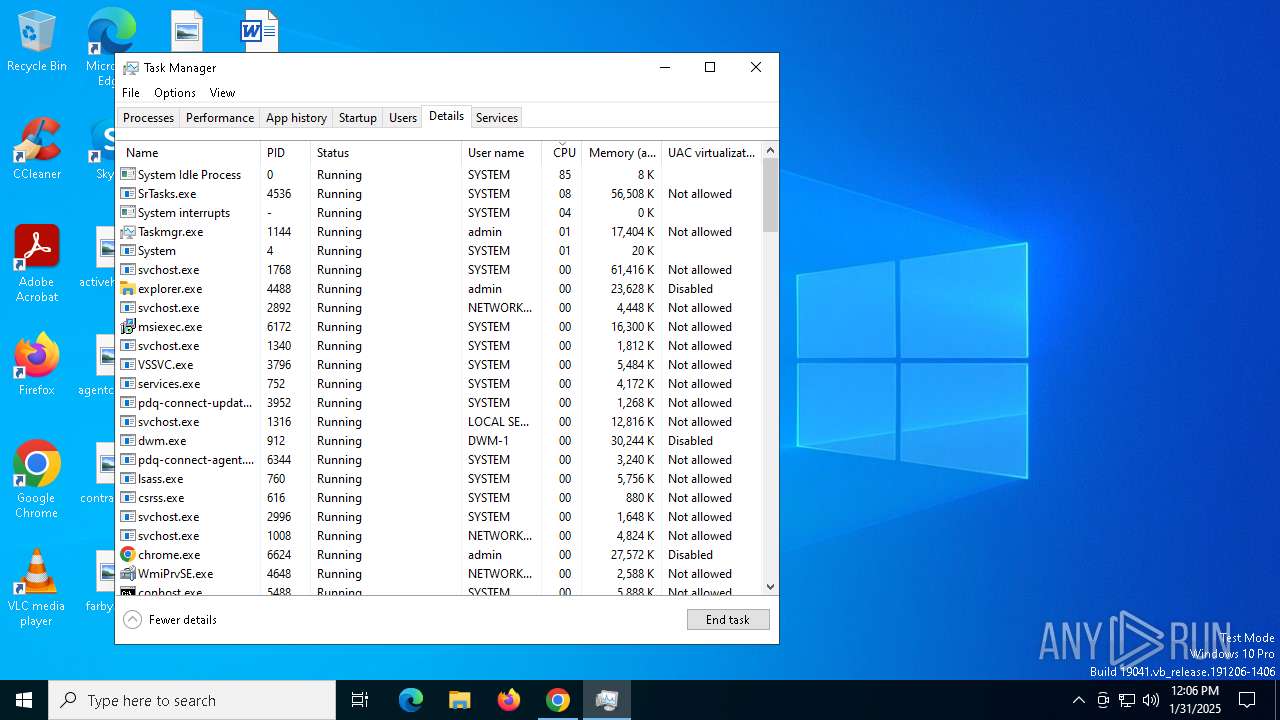
Manages system restore points
- SrTasks.exe (PID: 4536)
Reads the machine GUID from the registry
- msiexec.exe (PID: 6172)
- csc.exe (PID: 9788)
- csc.exe (PID: 9960)
Reads the software policy settings
- msiexec.exe (PID: 6268)
- msiexec.exe (PID: 6172)
- pdq-connect-agent.exe (PID: 6344)
- pdq-connect-updater.exe (PID: 3952)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6172)
Create files in a temporary directory
- rundll32.exe (PID: 4716)
- rundll32.exe (PID: 5628)
Creates files in the program directory
- rundll32.exe (PID: 2804)
- pdq-connect-agent.exe (PID: 6344)
- msiexec.exe (PID: 424)
The sample compiled with english language support
- msiexec.exe (PID: 6172)
- powershell.exe (PID: 424)
- powershell.exe (PID: 7980)
Creates a software uninstall entry
- msiexec.exe (PID: 6172)
Reads Environment values
- pdq-connect-agent.exe (PID: 6344)
- DismHost.exe (PID: 7424)
- DismHost.exe (PID: 9652)
Application based on Rust
- pdq-connect-agent.exe (PID: 6344)
- pdq-connect-updater.exe (PID: 3952)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 2072)
- powershell.exe (PID: 8000)
- powershell.exe (PID: 1448)
- powershell.exe (PID: 7980)
- powershell.exe (PID: 424)
- powershell.exe (PID: 7352)
- powershell.exe (PID: 8992)
Process checks computer location settings
- pdq-connect-agent.exe (PID: 6344)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 8140)
- powershell.exe (PID: 2796)
- powershell.exe (PID: 424)
- powershell.exe (PID: 7980)
- powershell.exe (PID: 8792)
- powershell.exe (PID: 9836)
- powershell.exe (PID: 4328)
- powershell.exe (PID: 9772)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 8000)
- powershell.exe (PID: 1448)
Reads Windows Product ID
- powershell.exe (PID: 424)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7980)
- powershell.exe (PID: 424)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 10128)
- powershell.exe (PID: 4360)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6436)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
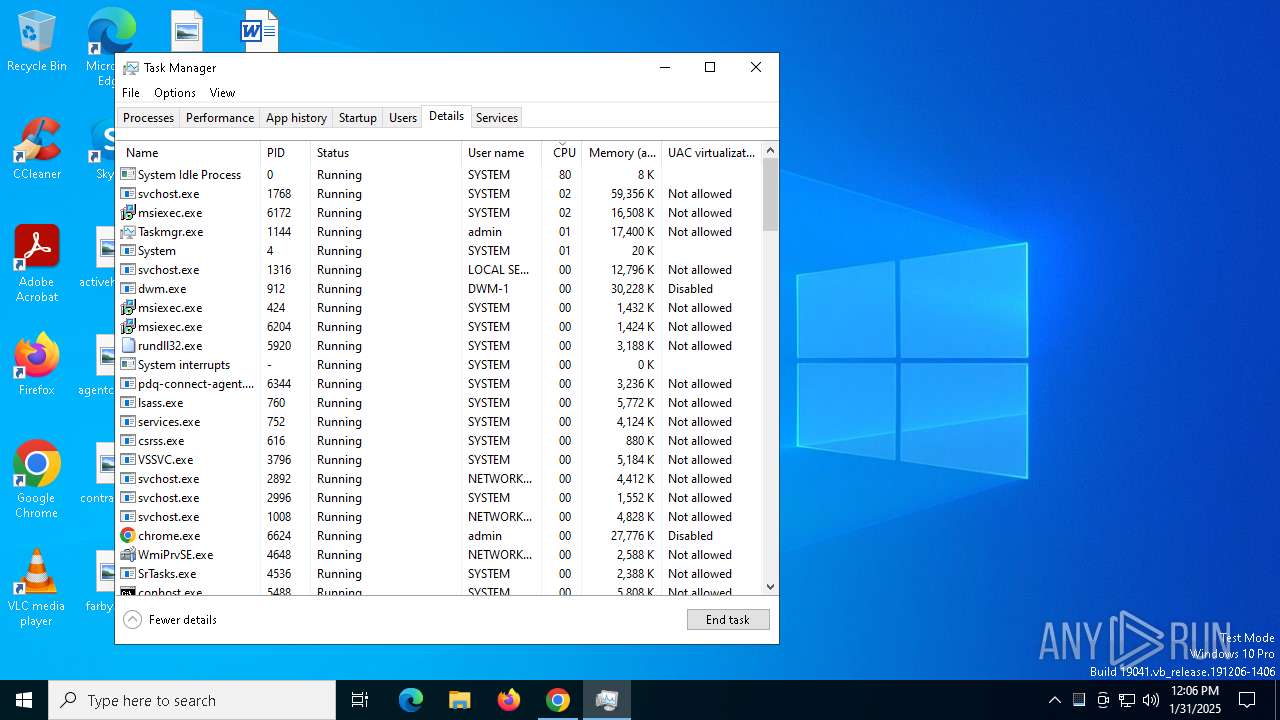
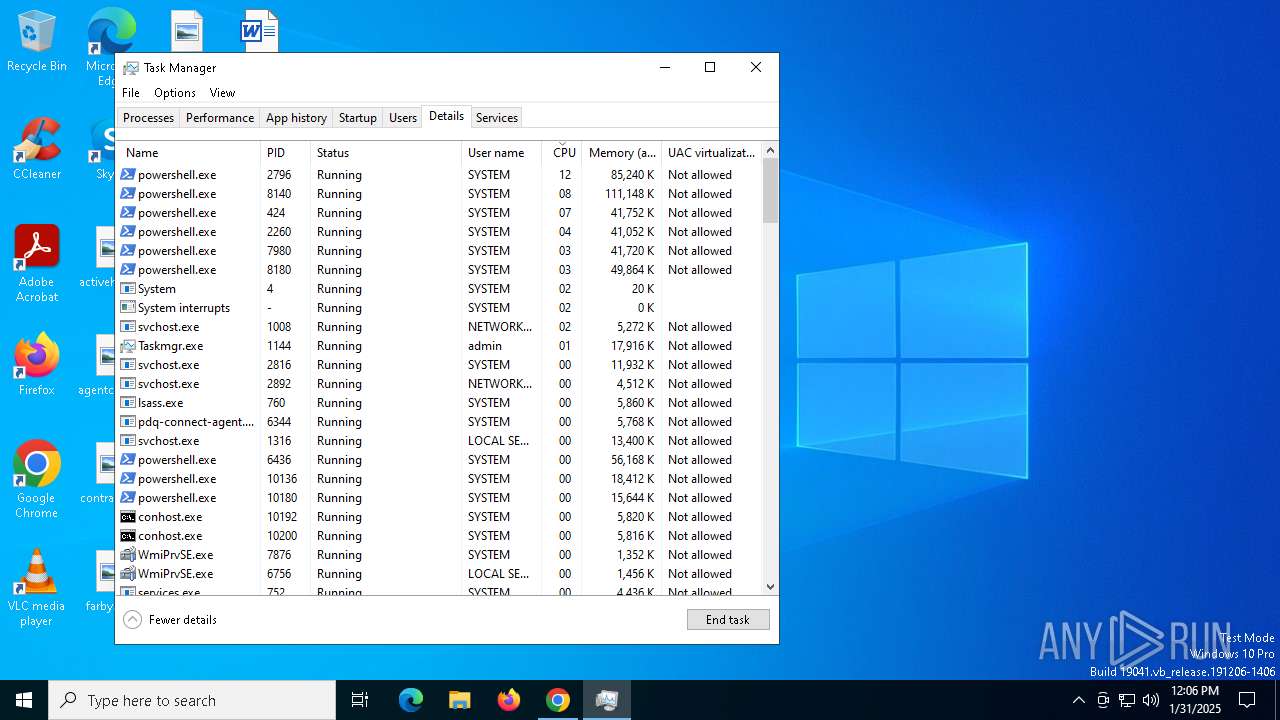
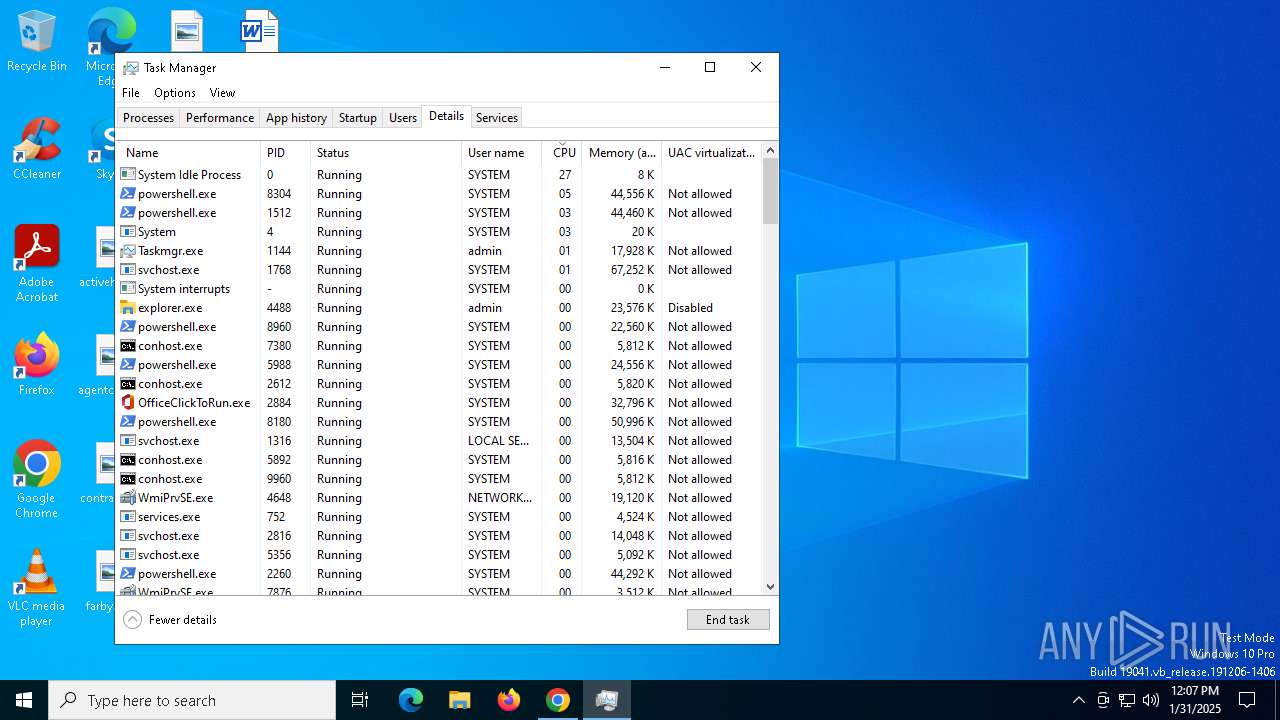
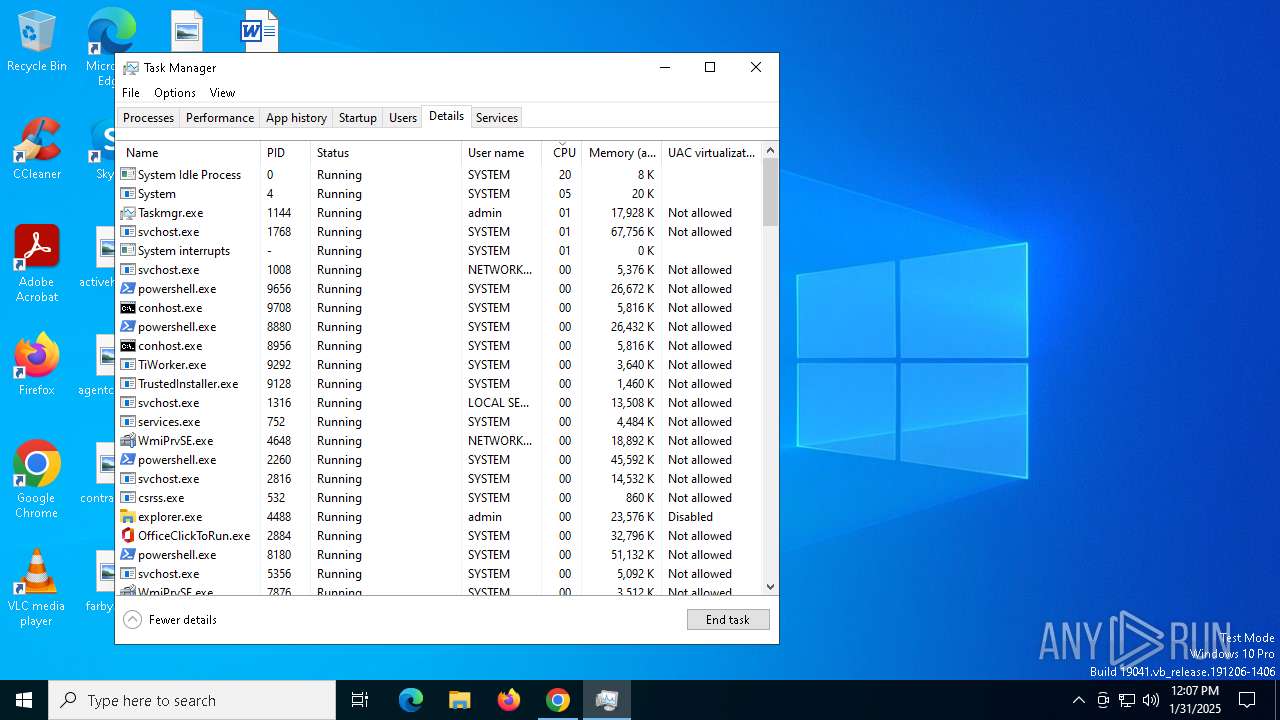
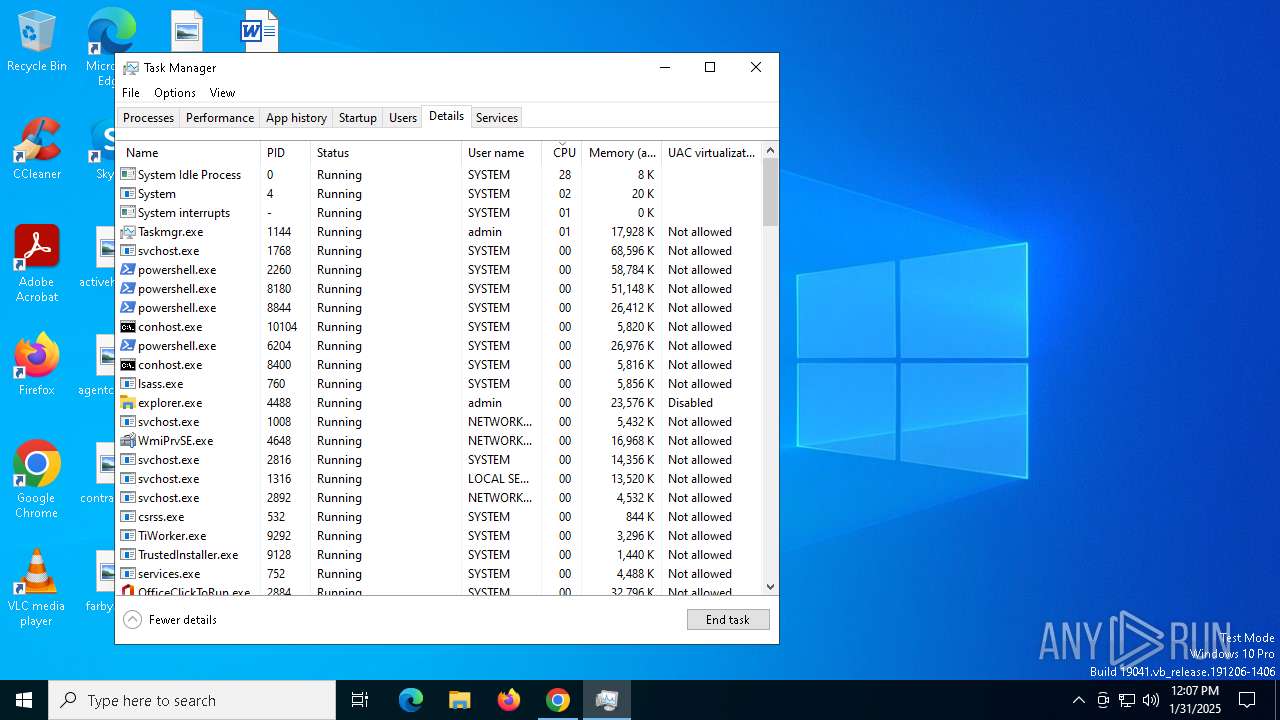
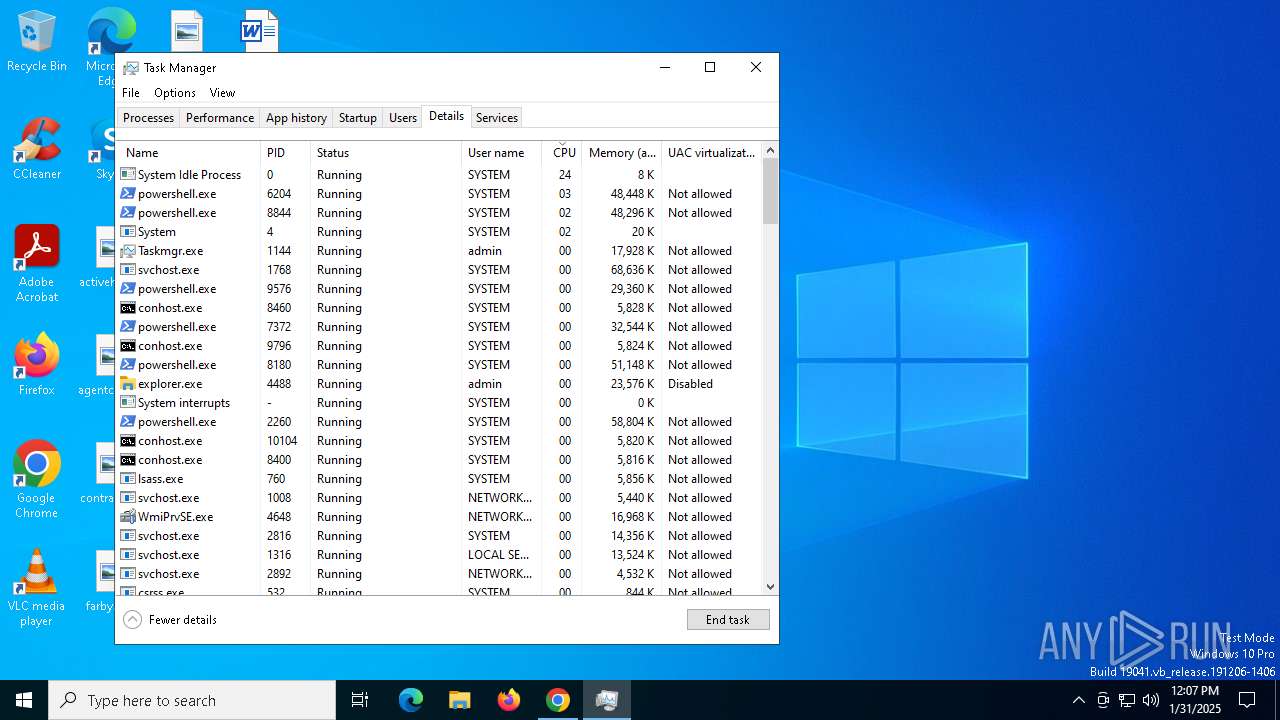
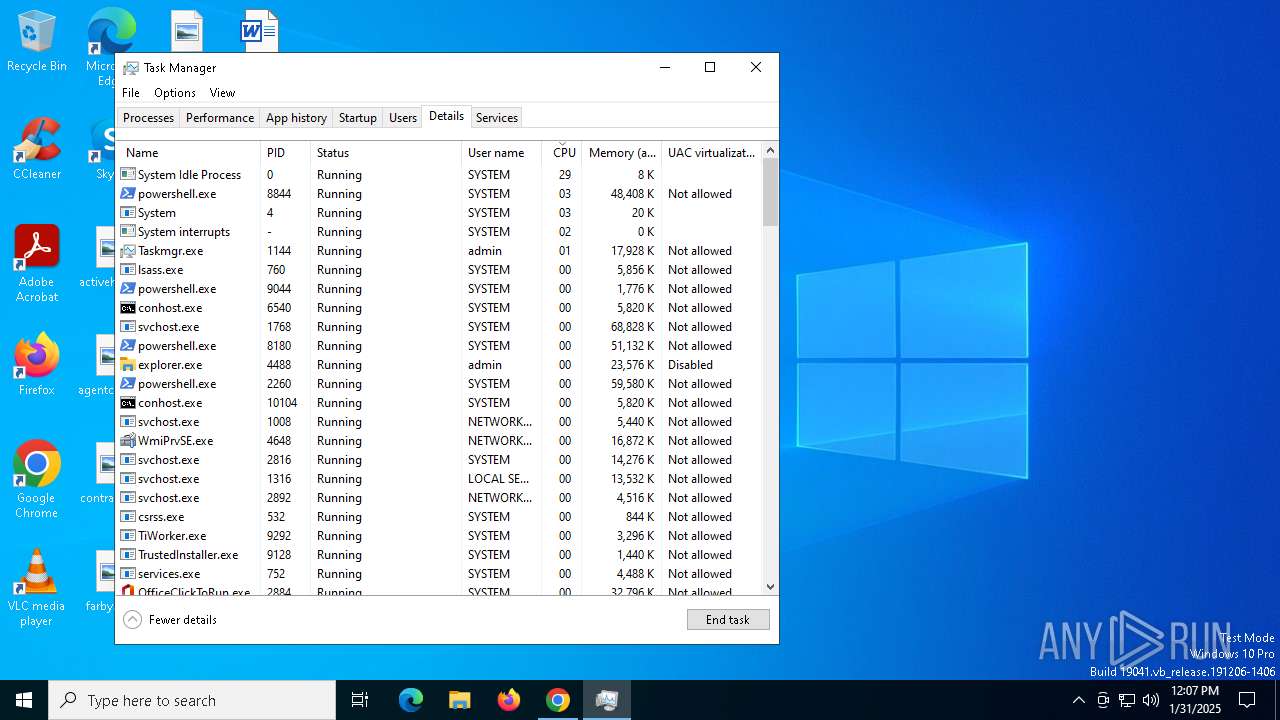
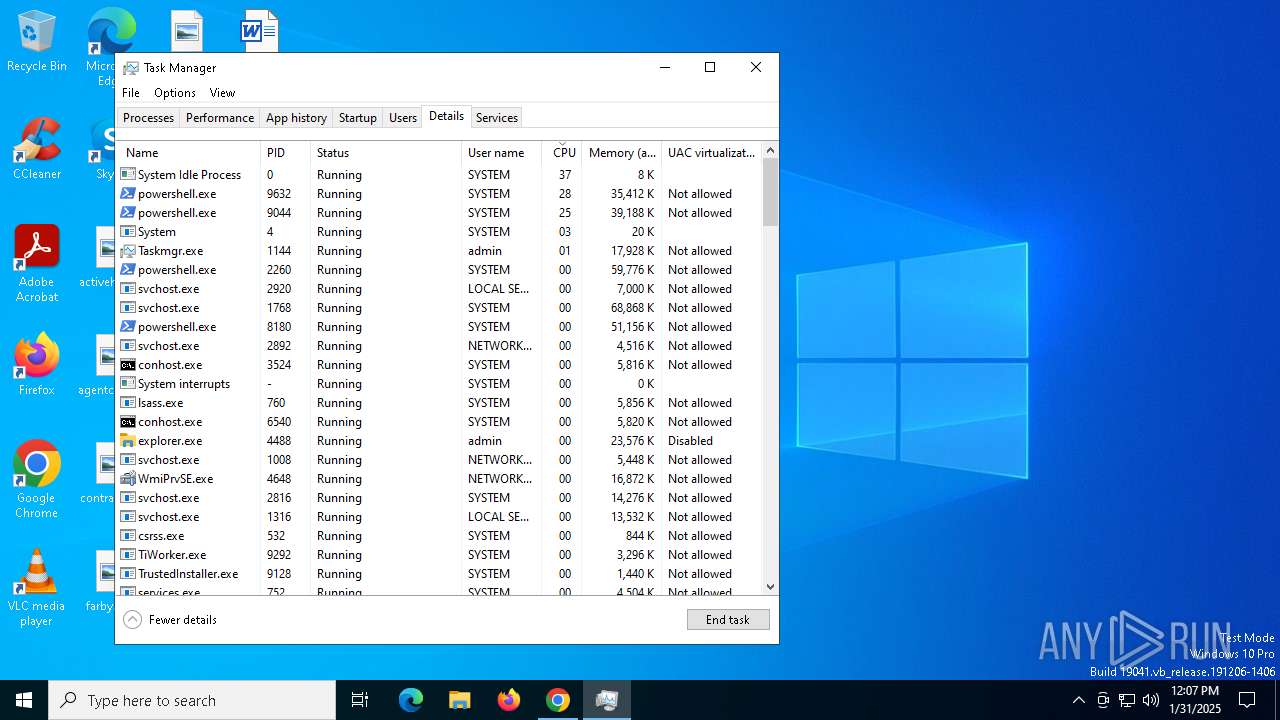
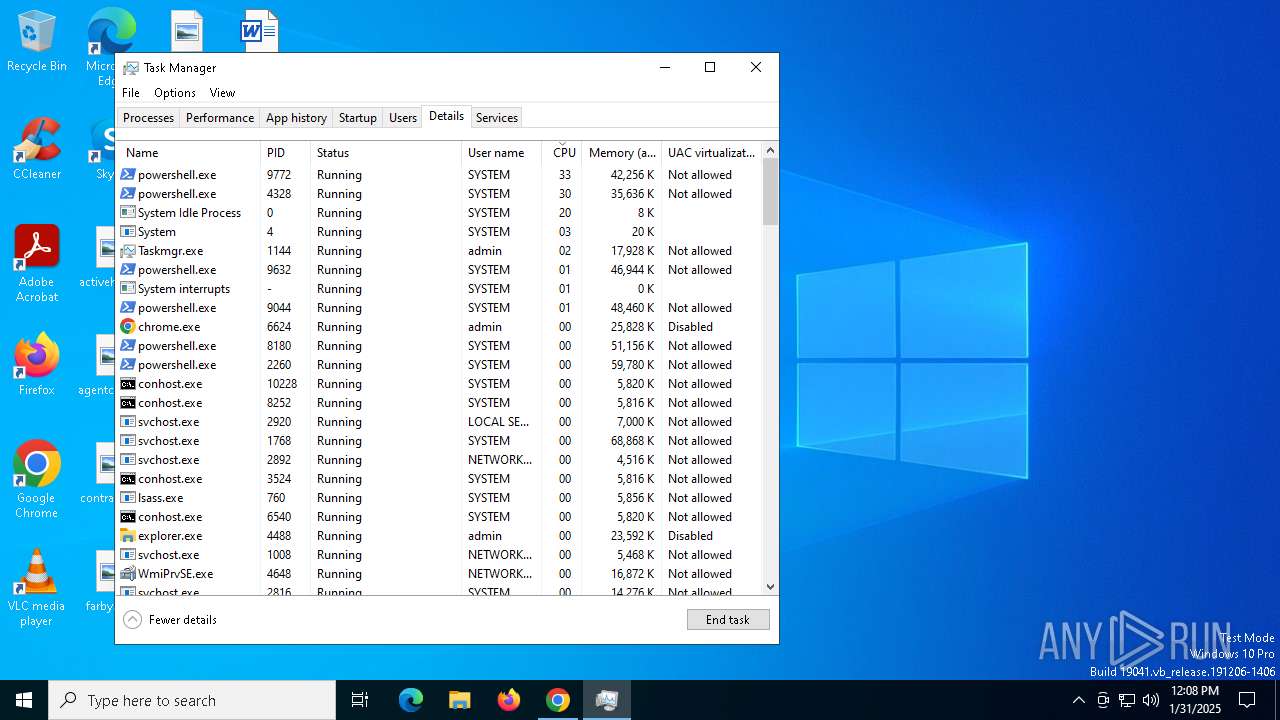
Total processes
332
Monitored processes
189
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 424 | "msiexec" /i C:\ProgramData\PDQ\PDQConnectAgent\Updates\PDQConnectUpdater-0.3.0.msi /quiet /qn /norestart /L*V C:\ProgramData\PDQ\PDQConnectAgent\Updates\updater_install.log | C:\Windows\System32\msiexec.exe | — | pdq-connect-agent.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 424 | "powershell.exe" -NoLogo -NonInteractive -NoProfile -ExecutionPolicy Bypass -Command - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | pdq-connect-agent.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 716 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 776 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 936 | "powershell.exe" -NoLogo -NonInteractive -NoProfile -ExecutionPolicy Bypass -Command - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | pdq-connect-agent.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1144 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1172 | "powershell.exe" -NoLogo -NonInteractive -NoProfile -ExecutionPolicy Bypass -Command - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | pdq-connect-agent.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | rundll32.exe "C:\WINDOWS\Installer\MSIDC0.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1314312 38 pdqconnectagent-setup!pdqconnectagent_setup.CustomActions.CreateEventSource | C:\Windows\System32\rundll32.exe | msiexec.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1448 | "powershell.exe" -NoLogo -NonInteractive -NoProfile -ExecutionPolicy Bypass -Command - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | pdq-connect-agent.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
407 326
Read events
406 903
Write events
385
Delete events
38
Modification events
| (PID) Process: | (6624) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6624) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6624) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6624) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6624) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (5008) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 01000000000000009FB6E668D873DB01 | |||
| (PID) Process: | (1144) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\TaskManager |
| Operation: | delete value | Name: | Preferences |
Value: | |||
| (PID) Process: | (1144) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\TaskManager |
| Operation: | write | Name: | Preferences |
Value: 0D00000060000000600000006800000068000000E3010000DC010000000001000000008000000080D8010080DF010080000100016B00000034000000130300008C020000E80300000000000000000000000000000F000000010000000000000058AA6C15F77F00000000000000000000000000002E0100001E0000008990000000000000FF00000001015002000000000D0000000000000098AA6C15F77F00000000000000000000FFFFFFFF960000001E0000008B900000010000000000000000101001000000000300000000000000B0AA6C15F77F00000000000000000000FFFFFFFF780000001E0000008C900000020000000000000001021200000000000400000000000000C8AA6C15F77F00000000000000000000FFFFFFFF960000001E0000008D900000030000000000000000011001000000000200000000000000E8AA6C15F77F00000000000000000000FFFFFFFF320000001E0000008A90000004000000000000000008200100000000050000000000000000AB6C15F77F00000000000000000000FFFFFFFFC80000001E0000008E90000005000000000000000001100100000000060000000000000028AB6C15F77F00000000000000000000FFFFFFFF040100001E0000008F90000006000000000000000001100100000000070000000000000050AB6C15F77F00000000000000000000FFFFFFFF49000000490000009090000007000000000000000004250000000000080000000000000080AA6C15F77F00000000000000000000FFFFFFFF49000000490000009190000008000000000000000004250000000000090000000000000070AB6C15F77F00000000000000000000FFFFFFFF490000004900000092900000090000000000000000042508000000000A0000000000000088AB6C15F77F00000000000000000000FFFFFFFF4900000049000000939000000A0000000000000000042508000000000B00000000000000A8AB6C15F77F00000000000000000000FFFFFFFF490000004900000039A000000B0000000000000000042509000000001C00000000000000C8AB6C15F77F00000000000000000000FFFFFFFFC8000000490000003AA000000C0000000000000000011009000000001D00000000000000F0AB6C15F77F00000000000000000000FFFFFFFF64000000490000004CA000000D0000000000000000021508000000001E0000000000000010AC6C15F77F00000000000000000000FFFFFFFF64000000490000004DA000000E000000000000000002150800000000030000000A000000010000000000000058AA6C15F77F0000000000000000000000000000D70000001E0000008990000000000000FF00000001015002000000000400000000000000C8AA6C15F77F0000000000000000000001000000960000001E0000008D900000010000000000000001011000000000000300000000000000B0AA6C15F77F00000000000000000000FFFFFFFF640000001E0000008C900000020000000000000000021000000000000C0000000000000040AC6C15F77F0000000000000000000003000000640000001E00000094900000030000000000000001021000000000000D0000000000000068AC6C15F77F00000000000000000000FFFFFFFF640000001E00000095900000040000000000000000011001000000000E0000000000000090AC6C15F77F0000000000000000000005000000320000001E00000096900000050000000000000001042001000000000F00000000000000B8AC6C15F77F0000000000000000000006000000320000001E00000097900000060000000000000001042001000000001000000000000000D8AC6C15F77F0000000000000000000007000000460000001E00000098900000070000000000000001011001000000001100000000000000F8AC6C15F77F00000000000000000000FFFFFFFF640000001E0000009990000008000000000000000001100100000000060000000000000028AB6C15F77F0000000000000000000009000000040100001E0000008F9000000900000000000000010110010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000040000000B000000010000000000000058AA6C15F77F0000000000000000000000000000D70000001E0000009E90000000000000FF0000000101500200000000120000000000000020AD6C15F77F00000000000000000000FFFFFFFF2D0000001E0000009B90000001000000000000000004200100000000140000000000000040AD6C15F77F00000000000000000000FFFFFFFF640000001E0000009D90000002000000000000000001100100000000130000000000000068AD6C15F77F00000000000000000000FFFFFFFF640000001E0000009C900000030000000000000000011001000000000300000000000000B0AA6C15F77F00000000000000000000FFFFFFFF640000001E0000008C90000004000000000000000102100000000000070000000000000050AB6C15F77F000000000000000000000500000049000000490000009090000005000000000000000104210000000000080000000000000080AA6C15F77F000000000000000000000600000049000000490000009190000006000000000000000104210000000000090000000000000070AB6C15F77F0000000000000000000007000000490000004900000092900000070000000000000001042108000000000A0000000000000088AB6C15F77F0000000000000000000008000000490000004900000093900000080000000000000001042108000000000B00000000000000A8AB6C15F77F0000000000000000000009000000490000004900000039A00000090000000000000001042109000000001C00000000000000C8AB6C15F77F000000000000000000000A00000064000000490000003AA000000A00000000000000000110090000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000200000008000000010000000000000058AA6C15F77F0000000000000000000000000000C60000001E000000B090000000000000FF0000000101500200000000150000000000000088AD6C15F77F00000000000000000000FFFFFFFF6B0000001E000000B1900000010000000000000000042500000000001600000000000000B8AD6C15F77F00000000000000000000FFFFFFFF6B0000001E000000B2900000020000000000000000042500000000001800000000000000E0AD6C15F77F00000000000000000000FFFFFFFF6B0000001E000000B490000003000000000000000004250000000000170000000000000008AE6C15F77F00000000000000000000FFFFFFFF6B0000001E000000B390000004000000000000000004250000000000190000000000000040AE6C15F77F00000000000000000000FFFFFFFFA00000001E000000B5900000050000000000000000042001000000001A0000000000000070AE6C15F77F00000000000000000000FFFFFFFF7D0000001E000000B6900000060000000000000000042001000000001B00000000000000A0AE6C15F77F00000000000000000000FFFFFFFF7D0000001E000000B790000007000000000000000004200100000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000DA00000000000000000000000000000000000000000000009D200000200000009100000064000000320000006400000050000000320000003200000028000000500000003C0000005000000050000000320000005000000050000000500000005000000050000000500000002800000050000000230000002300000023000000230000005000000050000000500000003200000032000000320000007800000078000000500000003C00000050000000500000009700000032000000780000003200000050000000500000005000000050000000000000000100000002000000030000000400000005000000060000000700000008000000090000000A0000000B0000000C0000000D0000000E0000000F000000100000001100000012000000130000001400000015000000160000001700000018000000190000001A0000001B0000001C0000001D0000001E0000001F000000200000002100000022000000230000002400000025000000260000002700000028000000290000002A0000002B0000002C00000000000000000000001F00000000000000B400000032000000D8000000640000006400000000000000000000000000000000000000000000000000000000000000000000000000000000000000DA000000000000000000000000000000000000009D200000200000009100000064000000320000009700000050000000320000003200000028000000500000003C000000500000005000000032000000500000005000000050000000500000005000000050000000500000002800000050000000230000002300000023000000230000005000000050000000500000003200000032000000320000007800000078000000500000003C0000005000000064000000780000003200000078000000780000003200000050000000500000005000000050000000C8000000000000000100000002000000030000000400000005000000060000000700000008000000090000000A0000000B0000000C0000000D0000000E0000000F000000100000001100000012000000130000001400000015000000160000001700000018000000190000001A0000001B0000001C0000001D0000001E0000001F000000200000002100000022000000230000002400000025000000260000002700000028000000290000002A0000002B0000002C0000002D0000002E0000002F00000000000000000000001F00000000000000B400000032000000D8000000640000006400000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000100000002000000030000000400000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000001000000000000000000000000000000 | |||
| (PID) Process: | (6624) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.msi\OpenWithProgids |
| Operation: | write | Name: | Msi.Package |
Value: | |||
| (PID) Process: | (6172) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 480000000000000009D46872D873DB011C18000020120000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
142
Suspicious files
172
Text files
221
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF137061.TMP | — | |
MD5:— | SHA256:— | |||
| 6624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF137061.TMP | — | |
MD5:— | SHA256:— | |||
| 6624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF137061.TMP | — | |
MD5:— | SHA256:— | |||
| 6624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF137061.TMP | — | |
MD5:— | SHA256:— | |||
| 6624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF137061.TMP | — | |
MD5:— | SHA256:— | |||
| 6624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
52
DNS requests
36
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6624 | chrome.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
6624 | chrome.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEA5NZ%2FZDFskqO3oXzEaXao8%3D | unknown | — | — | whitelisted |
6624 | chrome.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRhtVltVOu8OqBzmsd%2B%2FeFfks3xTQQUvGsiZZ2MaObmHgXx2HIl1LjgSMACEAvcoEuhCK%2FAlHGPdKmo6gs%3D | unknown | — | — | whitelisted |
5576 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5576 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4968 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
6416 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4968 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
4968 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 40.126.32.140:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1076 | svchost.exe | 184.28.89.167:443 | go.microsoft.com | AKAMAI-AS | US | whitelisted |
6624 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6916 | chrome.exe | 142.251.31.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
6916 | chrome.exe | 64.62.243.92:443 | nota.grupodoido.org | HURRICANE | US | unknown |
6916 | chrome.exe | 45.40.96.70:443 | mais1dia.scrapper-site.net | Canopus It Solutions Pvt Ltd | US | unknown |
3692 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
nota.grupodoido.org |
| unknown |
accounts.google.com |
| whitelisted |
mais1dia.scrapper-site.net |
| unknown |
settings-win.data.microsoft.com |
| whitelisted |
www.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6916 | chrome.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.scrapper-site .net Domain |
6916 | chrome.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.scrapper-site .net Domain |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare R2 Storage (r2 .cloudflarestorage .com) |
Process | Message |
|---|---|
powershell.exe | PID=7980 TID=9092 Lookup in table by path failed for: DummyPath-2BA51B78-C7F7-4910-B99D-BB7345357CDC - CTransactionalImageTable::LookupImagePath
|
powershell.exe | PID=7980 TID=9092 Initialized GlobalConfig - DismInitializeInternal
|
powershell.exe | PID=7980 TID=9092 DismApi.dll: - DismInitializeInternal
|
powershell.exe | PID=7980 TID=9092 DismApi.dll: - DismInitializeInternal
|
powershell.exe | PID=7980 TID=9092 DismApi.dll: API Version 10.0.19041.3758 - DismInitializeInternal
|
powershell.exe | PID=7980 TID=9092 DismApi.dll: Host machine information: OS Version=10.0.19045, Running architecture=amd64, Number of processors=4 - DismInitializeInternal
|
powershell.exe | PID=7980 TID=9092 Input parameters: LogLevel: 2, LogFilePath: C:\WINDOWS\Logs\DISM\dism.log, ScratchDirectory: (null) - DismInitializeInternal
|
powershell.exe | PID=7980 TID=9092 Initialized SessionTable - DismInitializeInternal
|
powershell.exe | PID=7980 TID=9092 DismApi.dll: <----- Starting DismApi.dll session -----> - DismInitializeInternal
|
powershell.exe | PID=7980 TID=9092 Enter DismInitializeInternal - DismInitializeInternal
|